| File name: | PbzVeQP.txt |
| Full analysis: | https://app.any.run/tasks/51e7aff6-410a-4696-a1e3-462ac653b120 |
| Verdict: | Malicious activity |
| Threats: | Hancitor was created in 2014 to drop other malware on infected machines. It is also known as Tordal and Chanitor. This malware is available as a service which makes it accessible tools to criminals and contributes to the popularity of this virus. |
| Analysis date: | December 02, 2019, 20:26:08 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | DAA9B06974FA5963B39E0120BABE138C |
| SHA1: | 4CC4588D284BEAD0D6DAE54761DE42CD048F77A1 |
| SHA256: | F01881DBFF4546BD2D66A49CC01EE09E306C025AAA4DF16022EB826426F2E004 |
| SSDEEP: | 1536:T2OE+c3NMobaWpNtnHW5TyqOp+JVrvUaDBiiW:TmFK+aW5n25uqOpkvB0iW |
MALICIOUS
Connects to CnC server
- svchost.exe (PID: 2032)
- svchost.exe (PID: 4528)
Loads dropped or rewritten executable
- rundll32.exe (PID: 444)
Uses SVCHOST.EXE for hidden code execution
- rundll32.exe (PID: 444)
- svchost.exe (PID: 2032)
HANCITOR was detected
- svchost.exe (PID: 2032)
Actions looks like stealing of personal data
- svchost.exe (PID: 4528)
- svchost.exe (PID: 2032)
PONY was detected
- svchost.exe (PID: 4528)
Detected Pony/Fareit Trojan
- svchost.exe (PID: 2032)
SUSPICIOUS
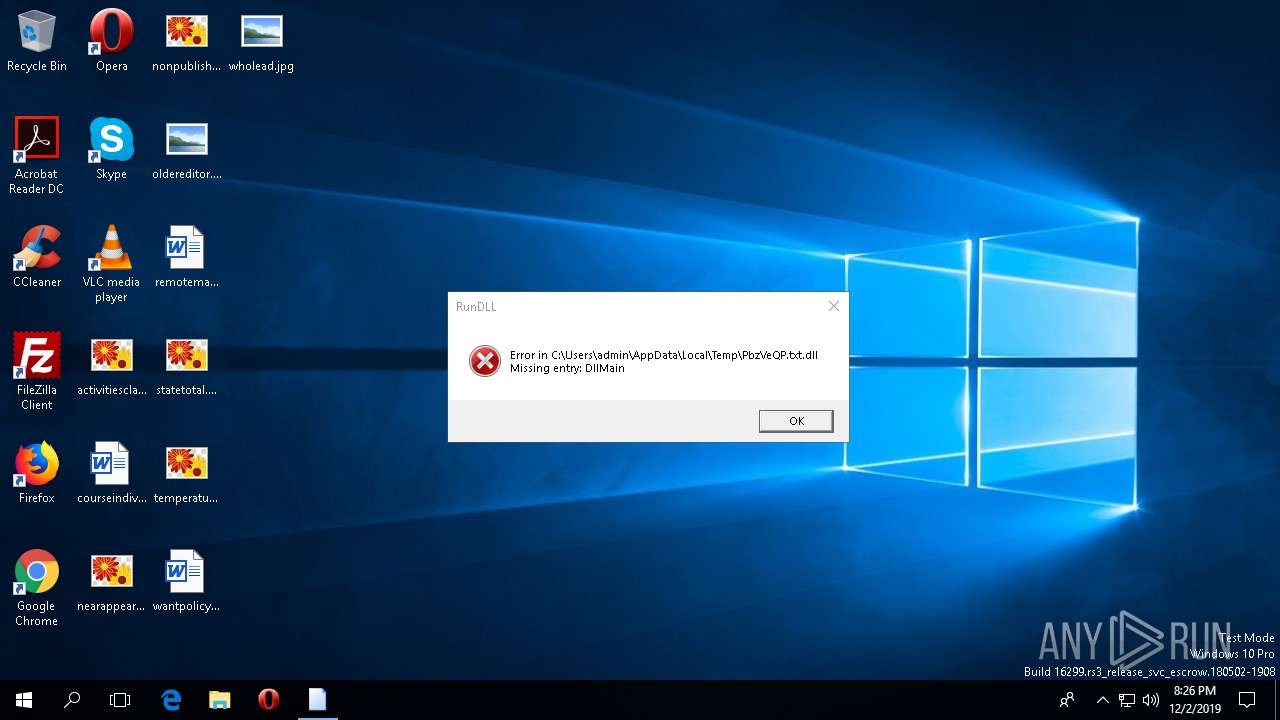
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 2000)
Checks for external IP
- svchost.exe (PID: 2032)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 2032)
Application launched itself
- svchost.exe (PID: 2032)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:02 15:37:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 70144 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x125a0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.4.686 |
| ProductVersionNumber: | 1.3.4.686 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Everything |
| FileVersion: | 1.3.4.686 |
| InternalName: | Everything |
| LegalCopyright: | Copyright (C) 2014 David Carpenter |
| OriginalFileName: | Everything.exe |
| ProductName: | Everything |
| ProductVersion: | 1.3.4.686 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Dec-2019 14:37:54 |
| Detected languages: |
|
| FileDescription: | Everything |
| FileVersion: | 1.3.4.686 |
| InternalName: | Everything |
| LegalCopyright: | Copyright (C) 2014 David Carpenter |
| OriginalFilename: | Everything.exe |
| ProductName: | Everything |
| ProductVersion: | 1.3.4.686 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 02-Dec-2019 14:37:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.pop | 0x00001000 | 0x0001039C | 0x00010400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.76895 |
.text | 0x00012000 | 0x00000DDA | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.50446 |
.rdata | 0x00013000 | 0x000007D0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.93605 |
.data | 0x00014000 | 0x000002A0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.59945 |
.rsrc | 0x00015000 | 0x0000FFCC | 0x00010000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.84606 |
.reloc | 0x00025000 | 0x00000260 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.68212 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40981 | 684 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.24442 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 6.04982 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.7124 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 4.30858 | 9640 | UNKNOWN | English - United States | RT_ICON |
6 | 4.60428 | 4264 | UNKNOWN | English - United States | RT_ICON |
7 | 4.78201 | 1128 | UNKNOWN | English - United States | RT_ICON |
101 | 2.73419 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
102 | 5.25619 | 34884 | UNKNOWN | English - United States | RT_BITMAP |
103 | 4.93757 | 1572 | UNKNOWN | English - United States | RT_RCDATA |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
99
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\PbzVeQP.txt.dll", DllMain | C:\WINDOWS\SysWOW64\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | cmd /K | C:\WINDOWS\SysWOW64\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2000 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\PbzVeQP.txt.dll", DllMain | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | C:\WINDOWS\System32\svchost.exe | C:\WINDOWS\SysWOW64\svchost.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4528 | C:\WINDOWS\System32\svchost.exe | C:\WINDOWS\SysWOW64\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
95
Read events
87
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2032) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2032) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2032) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2032) svchost.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | HWID |
Value: 7B36464230313745302D454137362D343131452D393244362D3737423333374446313146367D | |||
| (PID) Process: | (2032) svchost.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | Client Hash |
Value: D46740324AEF711495C8D12CFDF823A0 | |||
| (PID) Process: | (4528) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4528) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4528) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
6
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | svchost.exe | POST | — | 178.170.248.82:80 | http://laticivue.com/mlu/forum.php | RU | — | — | malicious |
4528 | svchost.exe | POST | — | 178.170.248.82:80 | http://laticivue.com/d2/about.php | RU | — | — | malicious |
2032 | svchost.exe | GET | 200 | 54.243.147.226:80 | http://api.ipify.org/ | US | text | 15 b | shared |
2032 | svchost.exe | GET | 200 | 2.57.89.115:80 | http://www.laadlifashionworld.com/1 | unknown | binary | 45.2 Kb | malicious |
2032 | svchost.exe | POST | 200 | 178.170.248.82:80 | http://laticivue.com/4/forum.php | RU | text | 420 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2032 | svchost.exe | 54.243.147.226:80 | api.ipify.org | Amazon.com, Inc. | US | malicious |
4528 | svchost.exe | 178.170.248.82:80 | laticivue.com | Electrics Ltd | RU | malicious |
2032 | svchost.exe | 178.170.248.82:80 | laticivue.com | Electrics Ltd | RU | malicious |
2032 | svchost.exe | 2.57.89.115:80 | www.laadlifashionworld.com | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
api.ipify.org |
| shared |
laticivue.com |
| malicious |
www.laadlifashionworld.com |
| malicious |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2032 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
2032 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2032 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony/Hancitor Payload (Zeus) |
2032 | svchost.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
2032 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted POST Data Request |
4528 | svchost.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
4528 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted POST Data Request |
2032 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony/Hancitor Payload (Zeus) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |