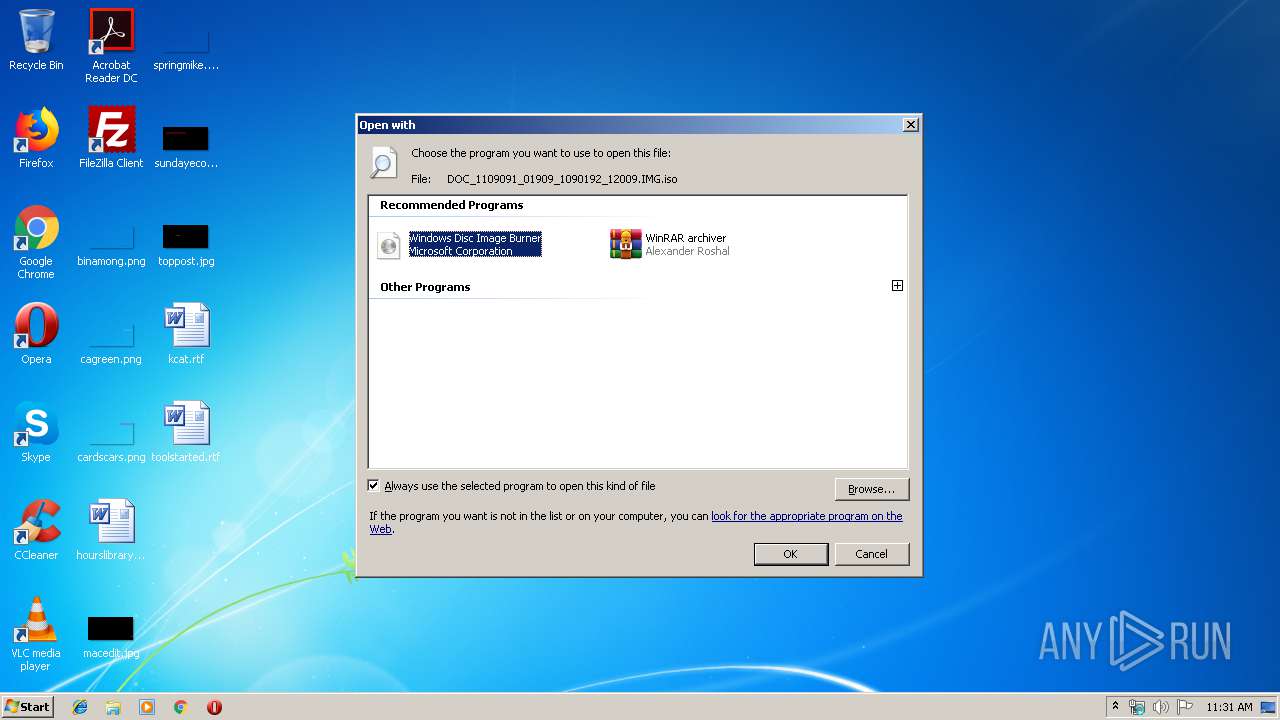
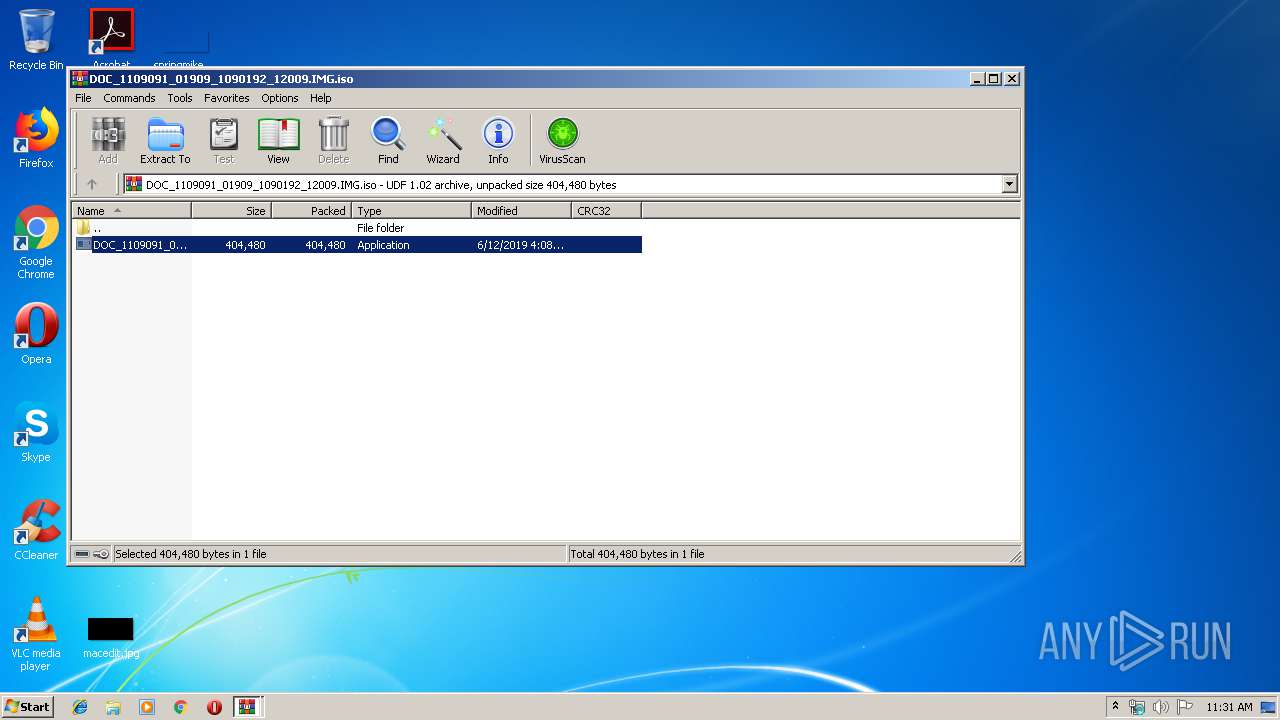
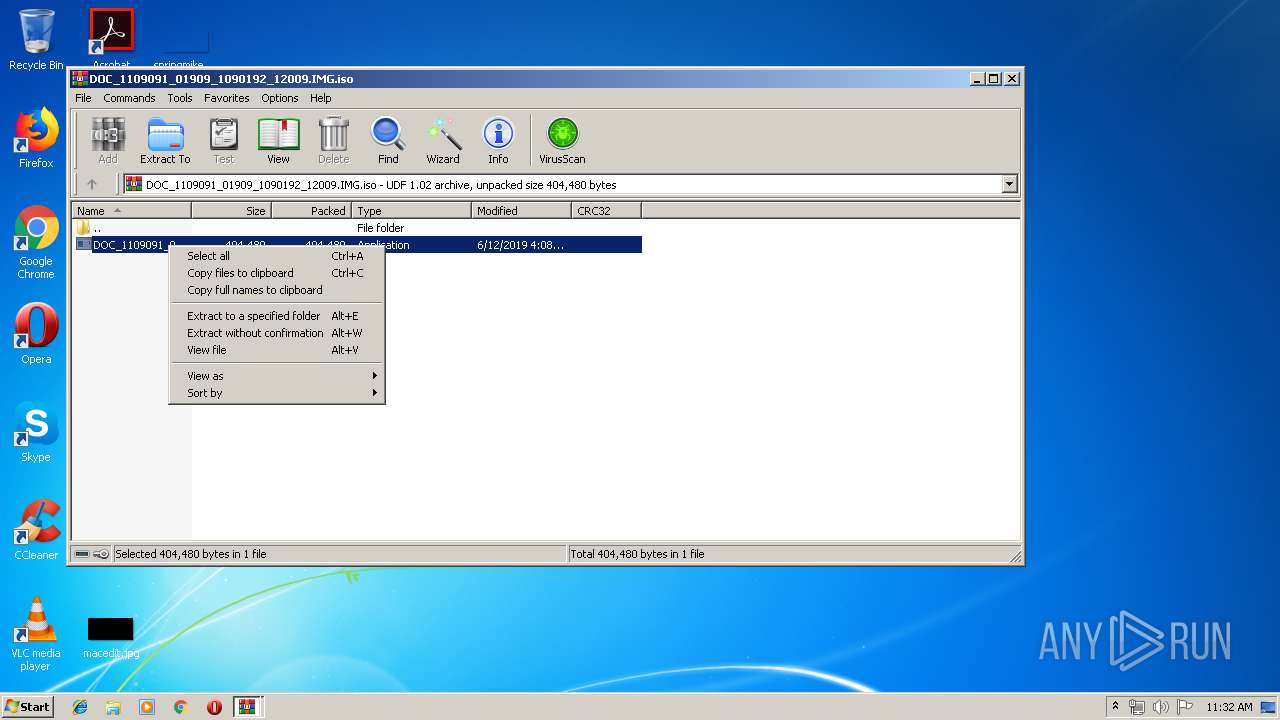
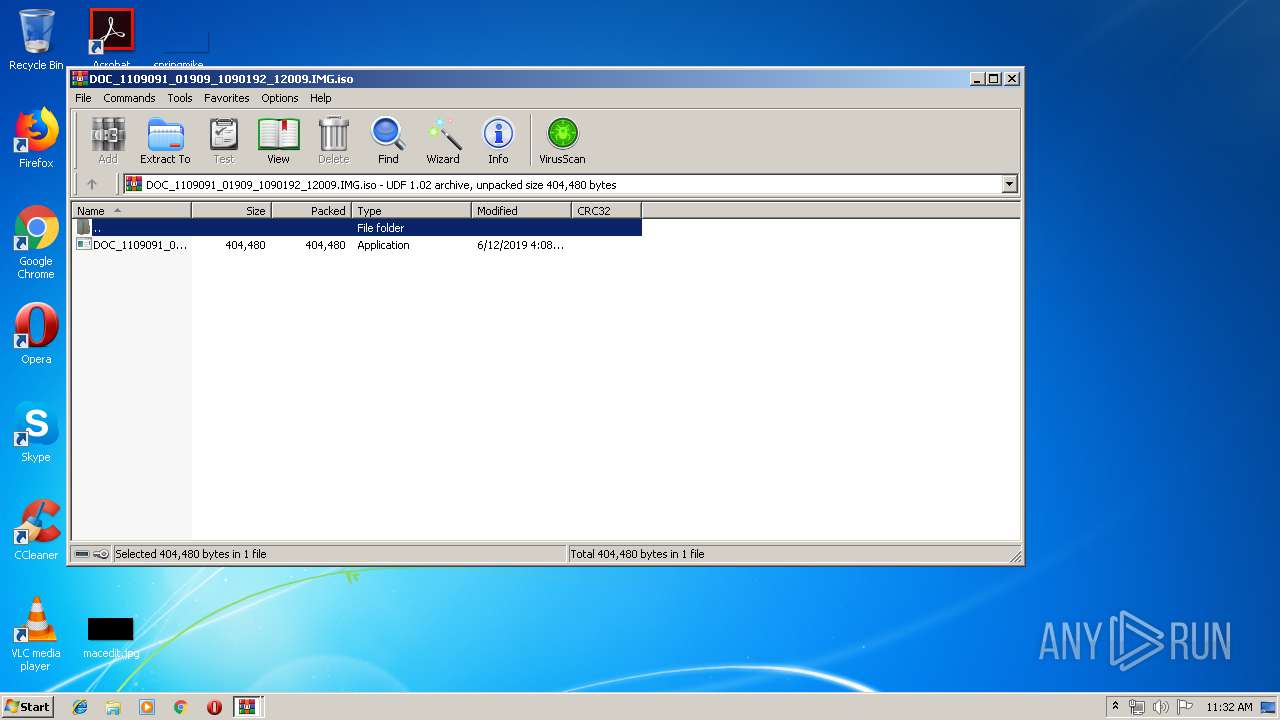
| File name: | DOC_1109091_01909_1090192_12009.IMG |
| Full analysis: | https://app.any.run/tasks/62cfb5ec-6e3b-43f3-bb4c-c3ffdc4ac13c |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | June 12, 2019, 10:31:22 |
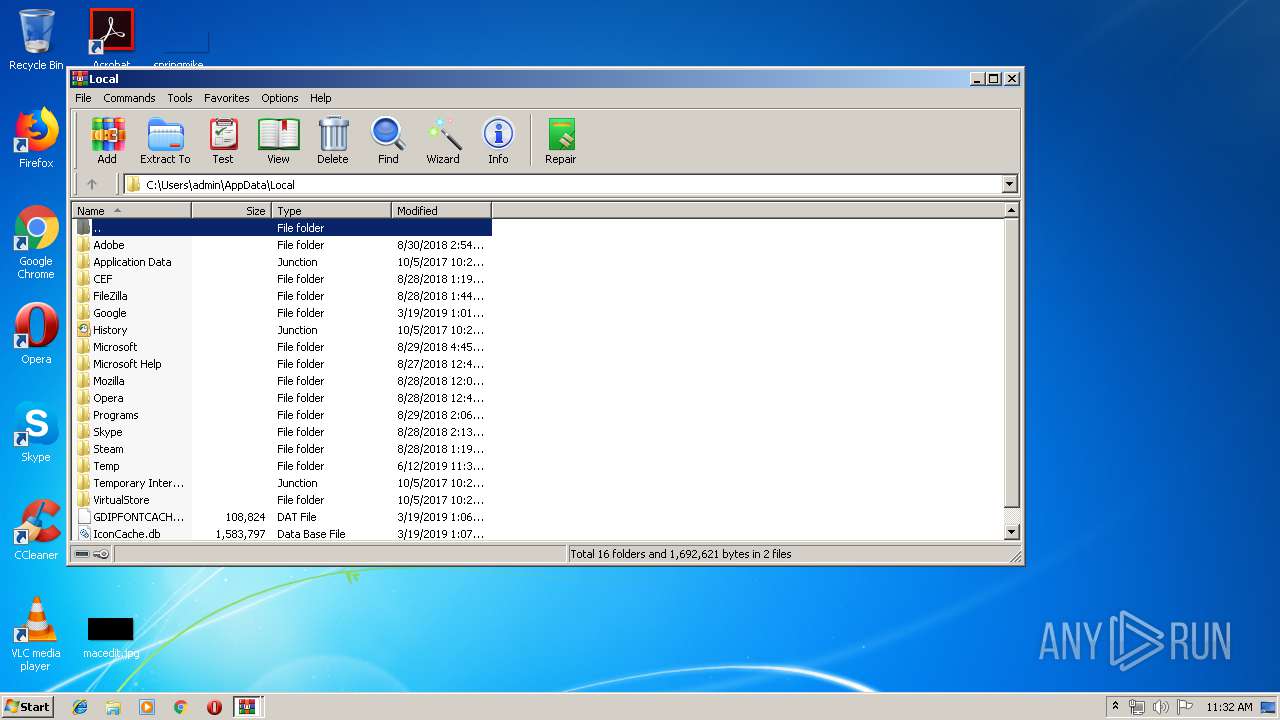
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | UDF filesystem data (version 1.5) 'DESKTOP' |
| MD5: | 1F7F826D3A2BBAA219BCB267E9C61761 |
| SHA1: | EF9542A3C04398381F58ABB1E3CBDE55C9A8F1B0 |
| SHA256: | EFB0C4B4D5A571DBF47A7850F6009B97F0B4D83AD712206F1E6216F857F857B5 |
| SSDEEP: | 6144:7E2AYl6JBWAetbxNnzXoSvFRGb1WXjikr:7lMKRVnzDoxWXWkr |
MALICIOUS
Application was dropped or rewritten from another process
- DOC_1109091_01909_1090192_1209.exe (PID: 4016)
- DOC_1109091_01909_1090192_1209.exe (PID: 3644)
- DOC_1109091_01909_1090192_1209.exe (PID: 1492)
- DOC_1109091_01909_1090192_1209.exe (PID: 2628)
NJRAT was detected
- RegAsm.exe (PID: 1744)
SUSPICIOUS
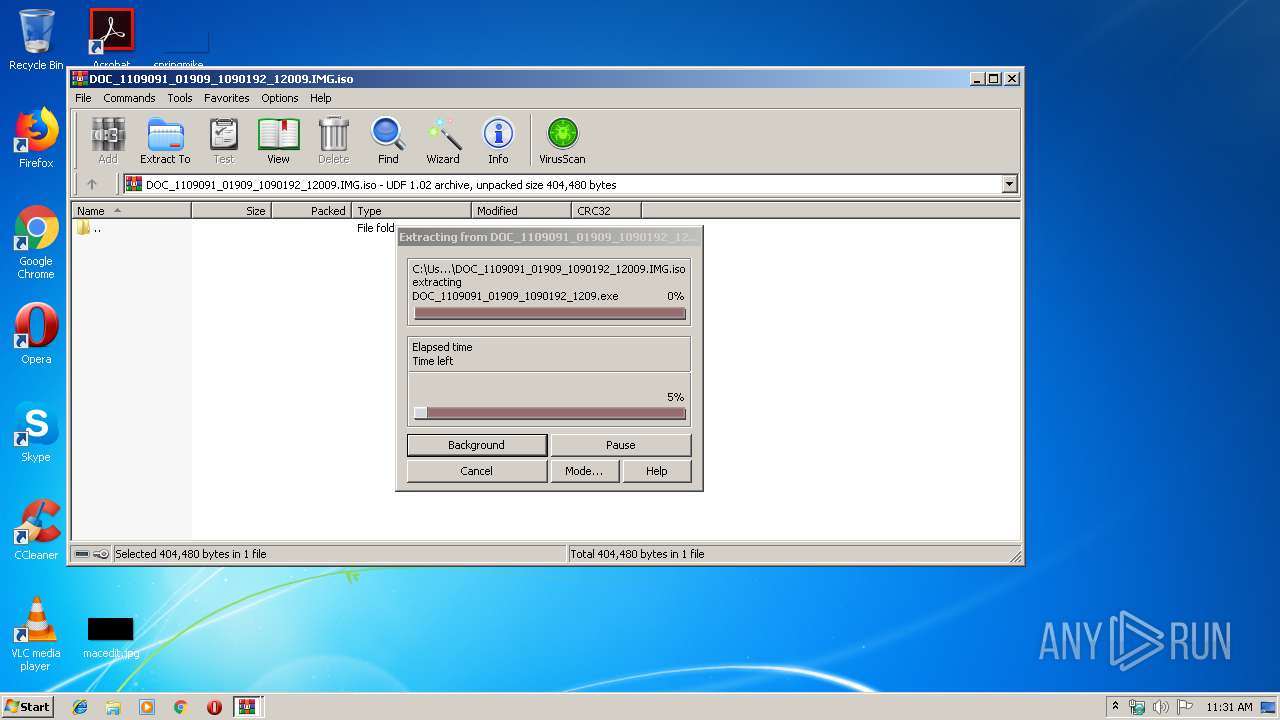
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3800)
Starts CMD.EXE for commands execution
- DOC_1109091_01909_1090192_1209.exe (PID: 2628)
- DOC_1109091_01909_1090192_1209.exe (PID: 1492)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 2944)
- cmd.exe (PID: 2084)
Uses NETSH.EXE for network configuration
- RegAsm.exe (PID: 1744)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
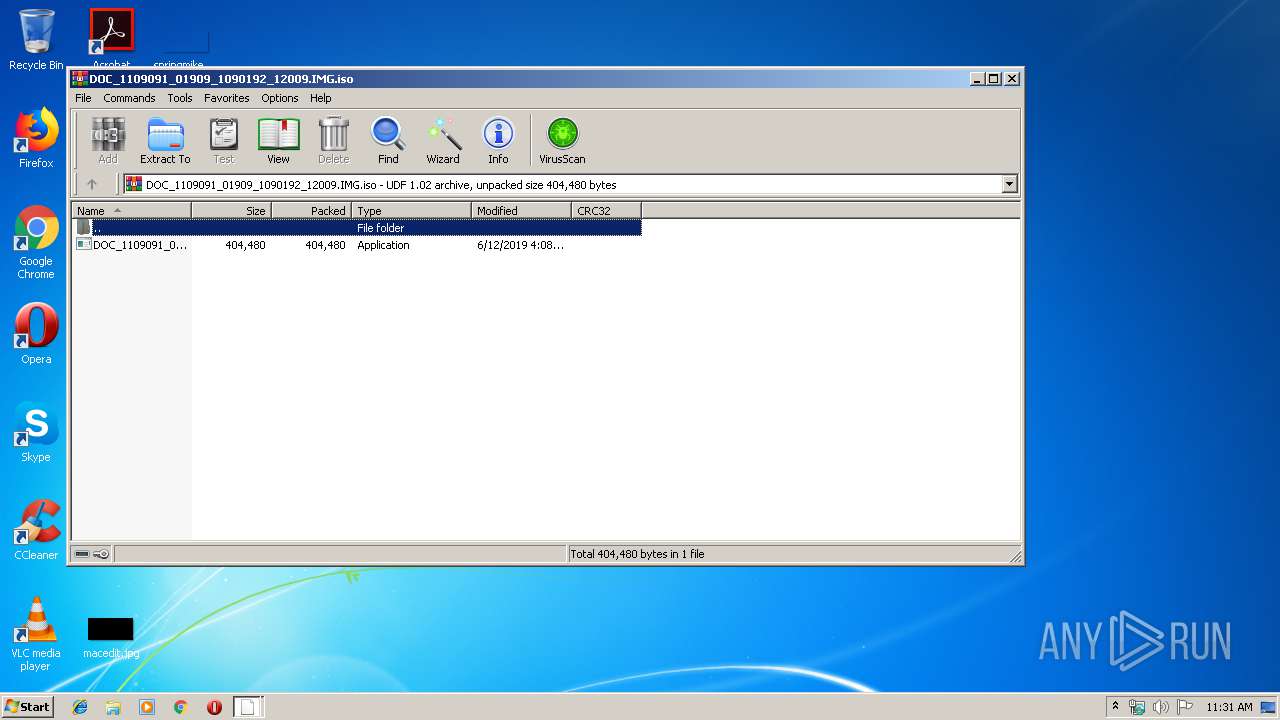
| VolumeName: | DESKTOP |
|---|---|
| VolumeBlockCount: | 599 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2019:06:12 07:18:15+08:00 |
| VolumeSetName: | UNDEFINED |
| Software: | IMGBURN V2.5.8.0 - THE ULTIMATE IMAGE BURNER! |
| VolumeCreateDate: | 2019:06:12 07:18:15.00+08:00 |
| VolumeModifyDate: | 2019:06:12 07:18:15.00+08:00 |
Composite
| VolumeSize: | 1198 kB |
|---|
Total processes
65
Monitored processes
26
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.1891\DOC_1109091_01909_1090192_1209.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.1891\DOC_1109091_01909_1090192_1209.exe | WinRAR.exe | ||||||||||||
User: admin Company: Maxthon International ltd. Integrity Level: HIGH Description: Maxthon Installer Exit code: 1 Version: 5.2.7.3000 Modules
| |||||||||||||||
| 1572 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | DOC_1109091_01909_1090192_1209.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1632 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | DOC_1109091_01909_1090192_1209.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1744 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | DOC_1109091_01909_1090192_1209.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2084 | "C:\Windows\System32\cmd.exe" /C choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.1891\DOC_1109091_01909_1090192_1209.exe" | C:\Windows\System32\cmd.exe | — | DOC_1109091_01909_1090192_1209.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2312 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | DOC_1109091_01909_1090192_1209.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2392 | netsh firewall add allowedprogram "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" "RegAsm.exe" ENABLE | C:\Windows\system32\netsh.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | DOC_1109091_01909_1090192_1209.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2472 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | DOC_1109091_01909_1090192_1209.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.1929\DOC_1109091_01909_1090192_1209.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.1929\DOC_1109091_01909_1090192_1209.exe | WinRAR.exe | ||||||||||||
User: admin Company: Maxthon International ltd. Integrity Level: HIGH Description: Maxthon Installer Exit code: 0 Version: 5.2.7.3000 Modules
| |||||||||||||||
Total events
1 636
Read events
1 391
Write events
244
Delete events
1
Modification events
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\isoburn.exe,-350 |
Value: Disc Image File | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iso\OpenWithProgids |
| Operation: | write | Name: | Windows.IsoFile |
Value: | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\isoburn.exe,-352 |
Value: Windows Disc Image Burner | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\System32\isoburn.exe |
Value: Windows Disc Image Burner | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\WinRAR\WinRAR.exe |
Value: WinRAR archiver | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
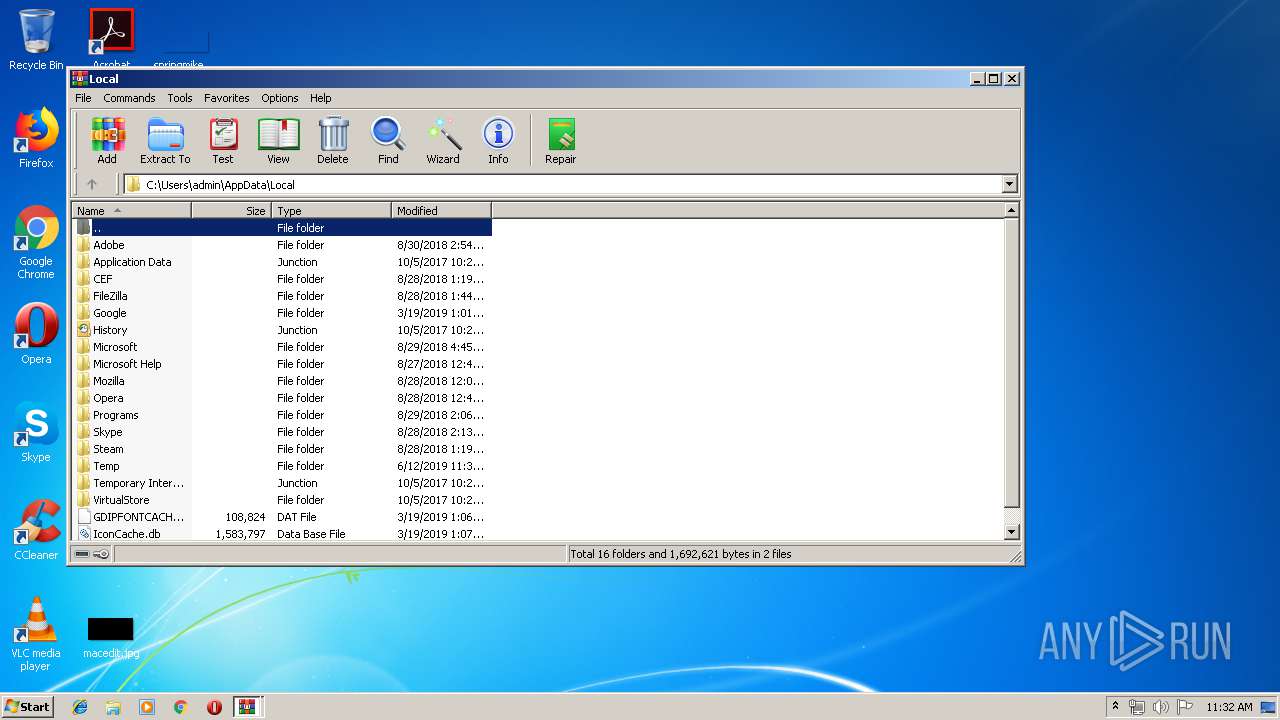
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.1891\DOC_1109091_01909_1090192_1209.exe | executable | |
MD5:— | SHA256:— | |||
| 3800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.1929\DOC_1109091_01909_1090192_1209.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1744 | RegAsm.exe | 213.208.129.205:5500 | 1934.duckdns.org | Next Layer Telekommunikationsdienstleistungs- und Beratungs GmbH | AT | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
1934.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |