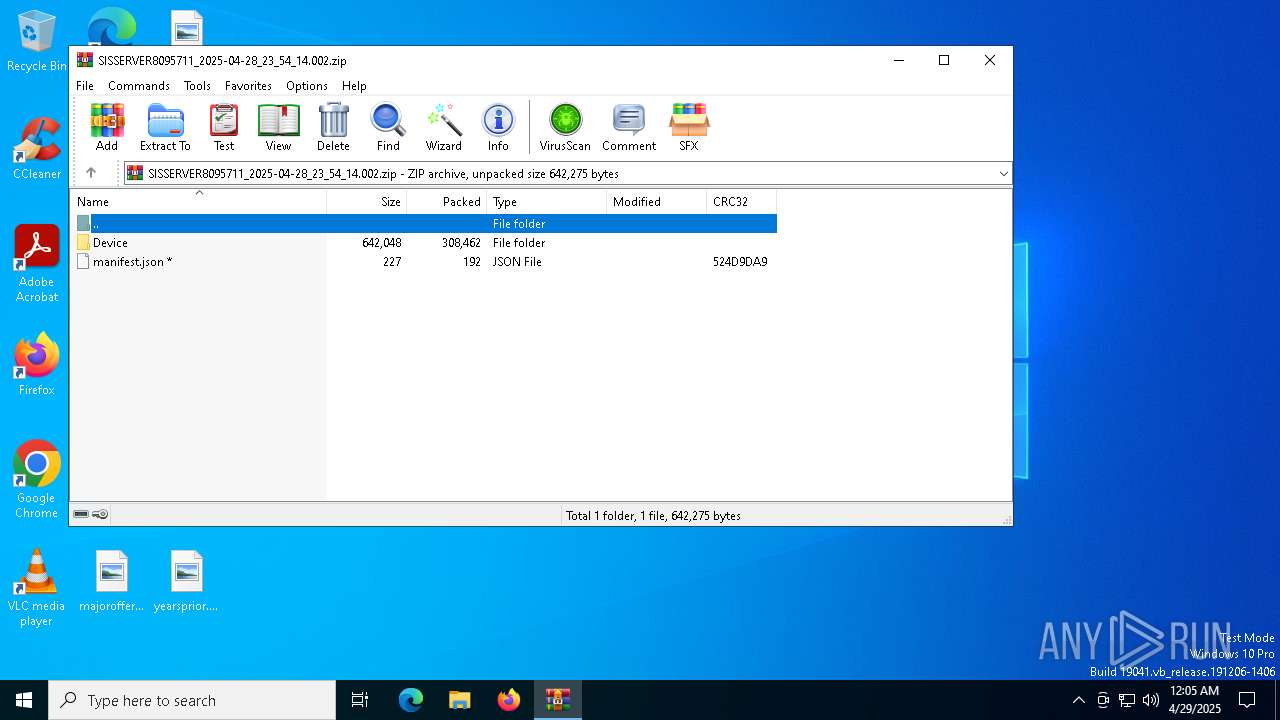
| File name: | SISSERVER8095711_2025-04-28_23_54_14.002.zip |
| Full analysis: | https://app.any.run/tasks/041b275b-3d1a-45d7-af50-23b80a17e621 |
| Verdict: | Malicious activity |
| Threats: | Mallox is a ransomware strain that emerged in 2021, known for its ability to encrypt files and target database servers using vulnerabilities like RDP. Often distributed through phishing campaigns and exploiting exposed SQL servers, it locks victims' data and demands a ransom. Mallox operates as a Ransomware-as-a-Service (RaaS), making it accessible to affiliates who use it to conduct attacks. |
| Analysis date: | April 29, 2025, 00:05:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
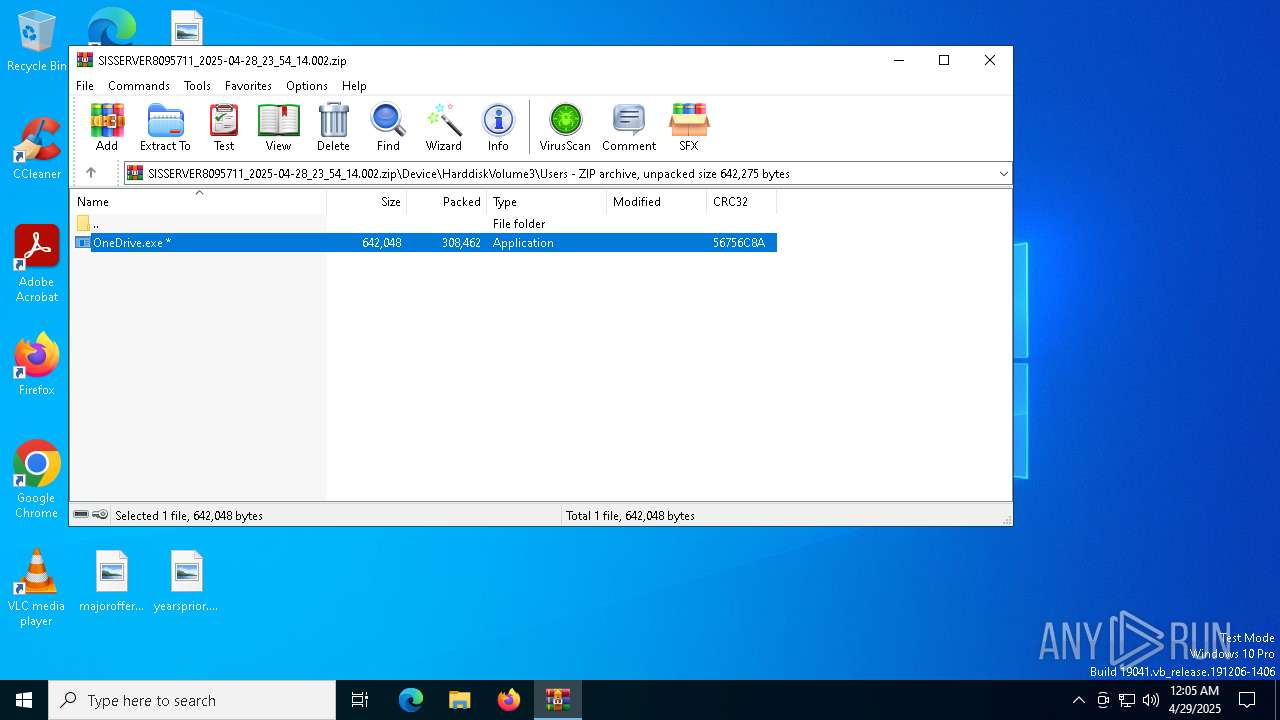
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 53880DA1AEC20B39D9EDEDE655FA1F98 |
| SHA1: | 396E871524C8B541EC1CE2CCDC82D57331BE75E5 |
| SHA256: | EF13A982EF3537A9388613C96934C08CF92B0B6D2BF947889B9F8A6CBB5828AC |
| SSDEEP: | 12288:re8TMN56vOJ8BvH1XIF9Pb0cfd0l629kRKFWU:y2MN5+OJ8BtYF9b0Ud0lPyRaWU |
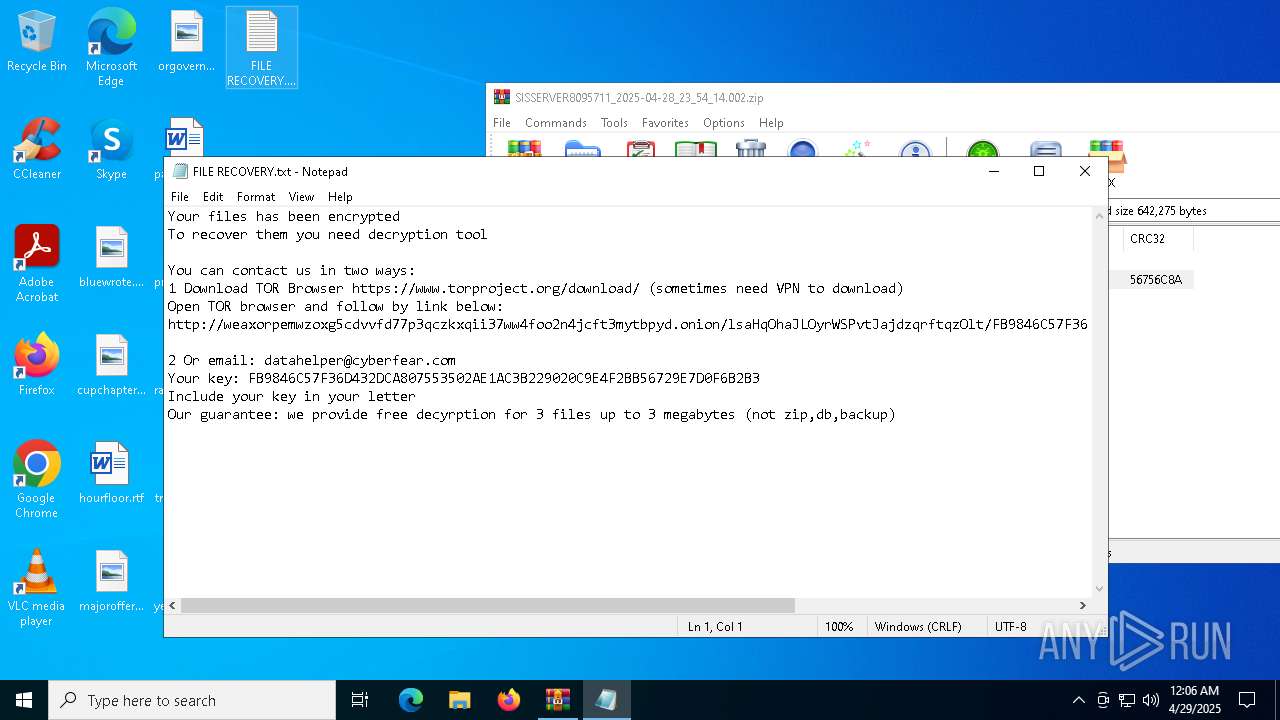
MALICIOUS
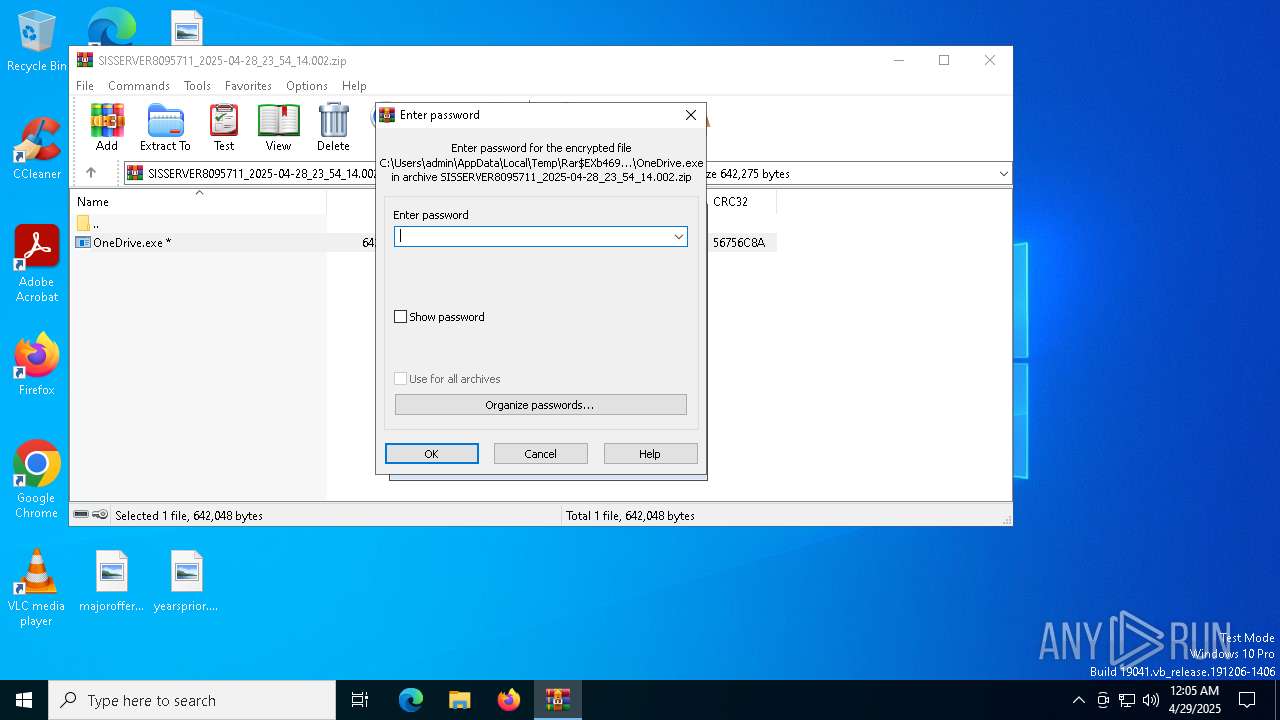
MALLOX mutex has been found
- OneDrive.exe (PID: 1196)
RANSOMWARE has been detected
- OneDrive.exe (PID: 1196)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4696)
Connects to the server without a host name
- OneDrive.exe (PID: 1196)
Checks for external IP
- OneDrive.exe (PID: 1196)
There is functionality for capture public ip (YARA)
- OneDrive.exe (PID: 1196)
INFO
Reads the computer name
- OneDrive.exe (PID: 1196)
Checks supported languages
- OneDrive.exe (PID: 1196)
Reads product name
- OneDrive.exe (PID: 1196)
Reads CPU info
- OneDrive.exe (PID: 1196)
Create files in a temporary directory
- OneDrive.exe (PID: 1196)
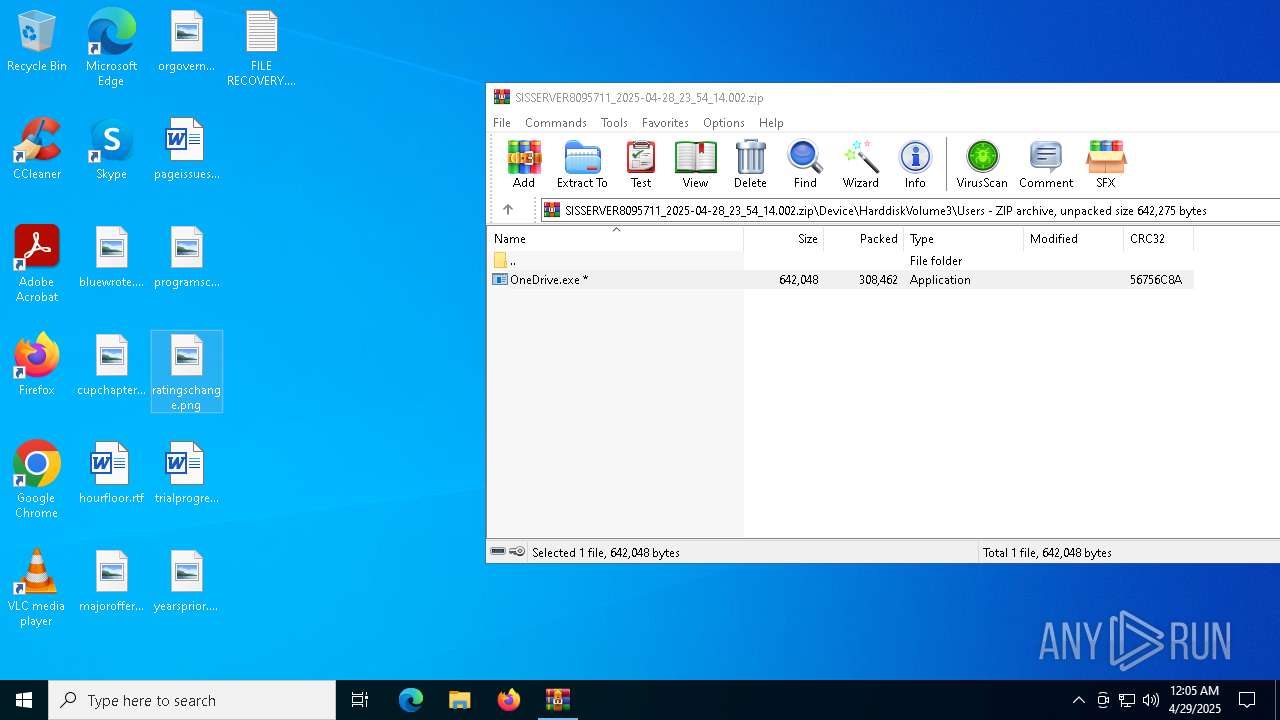
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4696)
Creates files in the program directory
- OneDrive.exe (PID: 1196)
Reads Environment values
- OneDrive.exe (PID: 1196)
Creates files or folders in the user directory
- OneDrive.exe (PID: 1196)
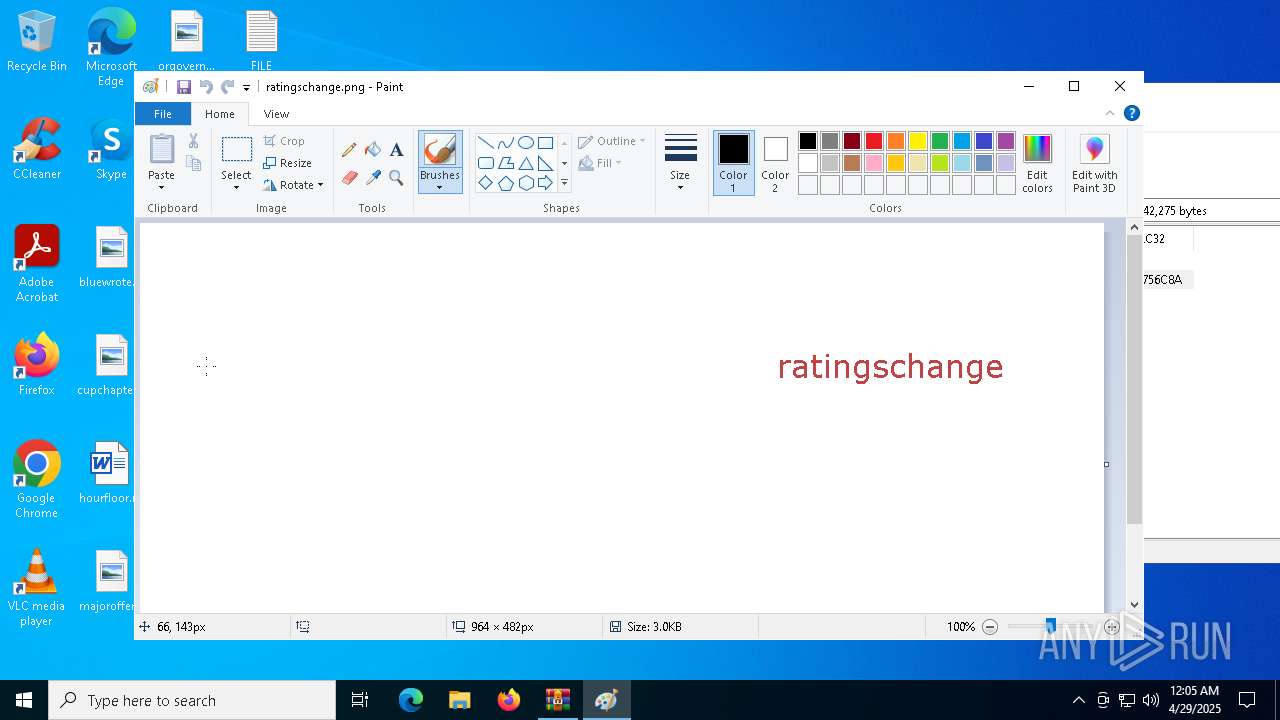
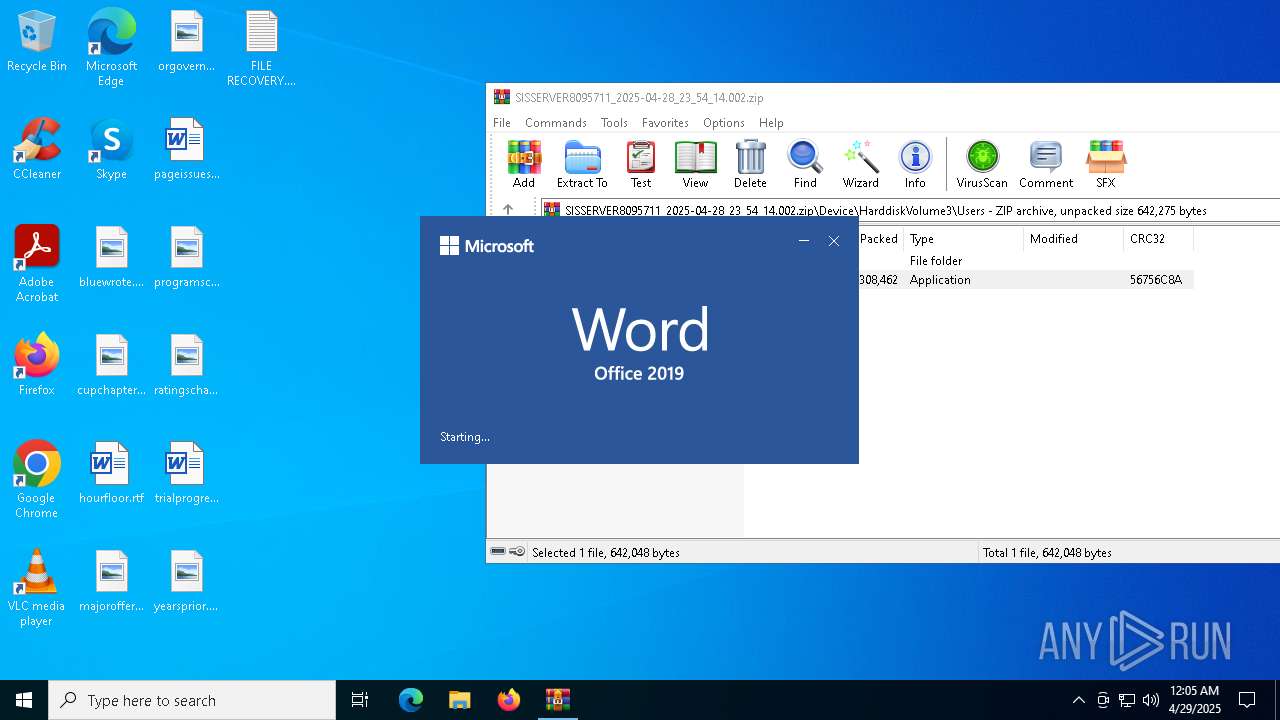
Manual execution by a user
- mspaint.exe (PID: 4944)
- WINWORD.EXE (PID: 2772)
- notepad.exe (PID: 4812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x56756c8a |
| ZipCompressedSize: | 308462 |
| ZipUncompressedSize: | 642048 |
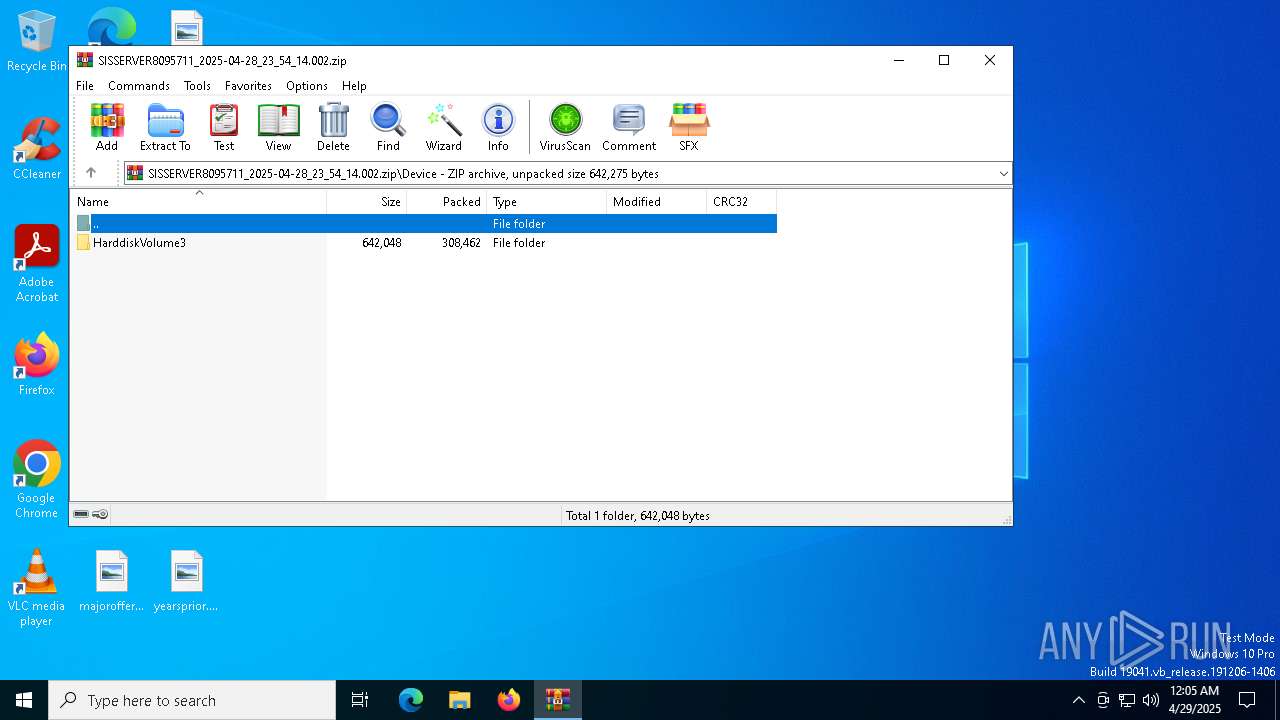
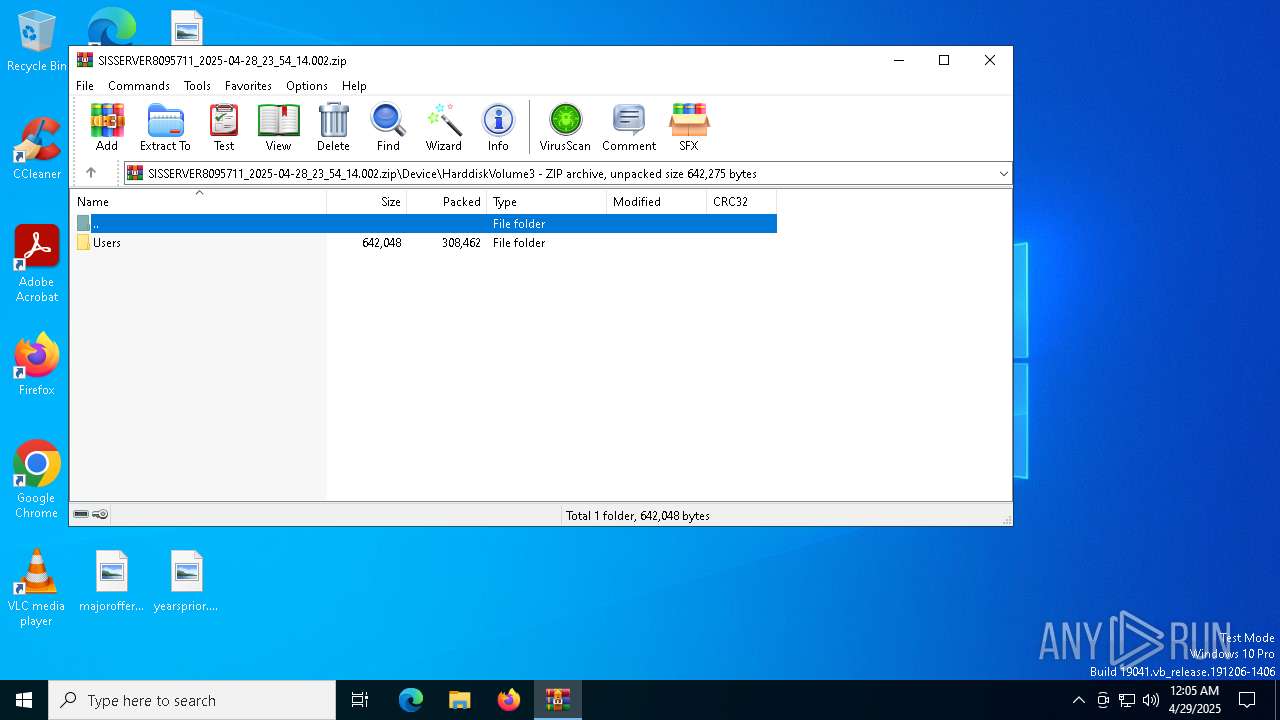
| ZipFileName: | Device/HarddiskVolume3/Users/OneDrive.exe |
Total processes
141
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4696.43765\Device\HarddiskVolume3\Users\OneDrive.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4696.43765\Device\HarddiskVolume3\Users\OneDrive.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "6C7C0CCD-6C16-4857-A068-83611B778389" "5A7B2141-FCBD-4DE8-B9F9-CF8DCBE12A09" "2772" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\hourfloor.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 4696 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\SISSERVER8095711_2025-04-28_23_54_14.002.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4812 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\FILE RECOVERY.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4944 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\ratingschange.png" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5512 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 413
Read events
13 101
Write events
287
Delete events
25
Modification events
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SISSERVER8095711_2025-04-28_23_54_14.002.zip | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4944) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | WindowPlacement |
Value: 2C00000000000000010000000000000000000000FFFFFFFFFFFFFFFF7F000000470000007F04000087020000 | |||
Executable files
2
Suspicious files
32
Text files
561
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1196 | OneDrive.exe | C:\Users\admin\Desktop\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
| 4696 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4696.43765\Device\HarddiskVolume3\Users\OneDrive.exe | executable | |
MD5:AD938C8AA558FF9A2332AC6A3E24705A | SHA256:495FCD1D824D75C53F325180AA2ED6EC03F88BD960362225C4193898B5B3A19E | |||
| 1196 | OneDrive.exe | C:\Users\admin\Pictures\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
| 1196 | OneDrive.exe | C:\Users\admin\Documents\OneNote Notebooks\My Notebook\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
| 1196 | OneDrive.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4696.43765\Device\HarddiskVolume3\Users\weax.txt | text | |
MD5:EF6214CDA04A83F706C13C63A12A4557 | SHA256:75710BDE21662E8B536A330EA18CC22E0AE98F3343AFFE200F4085573F382EBD | |||
| 1196 | OneDrive.exe | C:\Users\admin\Documents\Outlook Files\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
| 1196 | OneDrive.exe | C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\core\win-x64\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
| 1196 | OneDrive.exe | C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\x86\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
| 1196 | OneDrive.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
| 1196 | OneDrive.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\FILE RECOVERY.txt | text | |
MD5:D13B6D3E28F4DFBEC45EF4E0BEB66432 | SHA256:22877D65A8EE1C3BDFFFADA20F0FCF3ADFE32AFDF8E721907683F6D39D23F1AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
25
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1196 | OneDrive.exe | POST | 200 | 193.143.1.153:80 | http://193.143.1.153/Ujdu8jjooue/biweax.php | unknown | — | — | unknown |
6192 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6192 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1196 | OneDrive.exe | GET | 200 | 104.26.12.205:80 | http://api.ipify.org/ | unknown | — | — | malicious |
2772 | WINWORD.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.ipify.org |
| shared |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
1196 | OneDrive.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup api.ipify.org |
1196 | OneDrive.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External IP Lookup by HTTP (api .ipify .org) |
1196 | OneDrive.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
1196 | OneDrive.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 38 |
1196 | OneDrive.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |