| File name: | 7vgMI-Rk_geHx0xHeALIbNfZFWiLh5OHCRGQH8d99oQ.bin |
| Full analysis: | https://app.any.run/tasks/e3344d20-839a-4679-bac9-c44ac0859036 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 18, 2019, 12:40:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
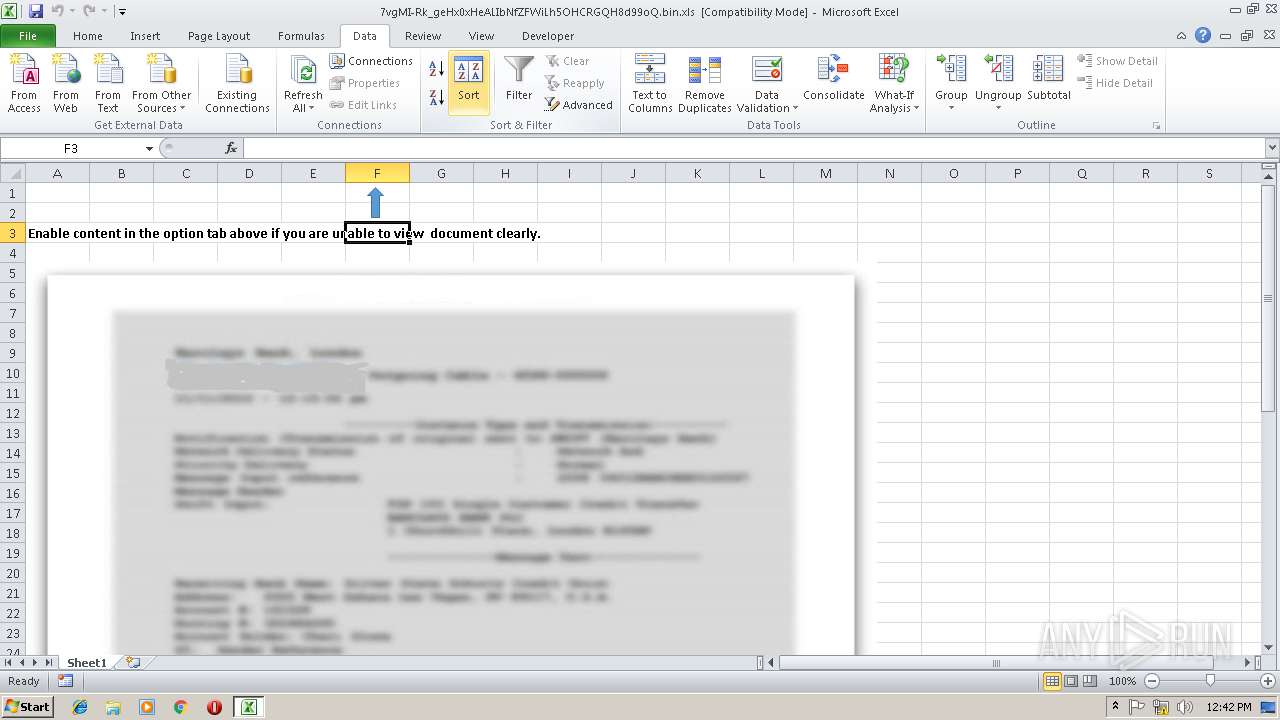
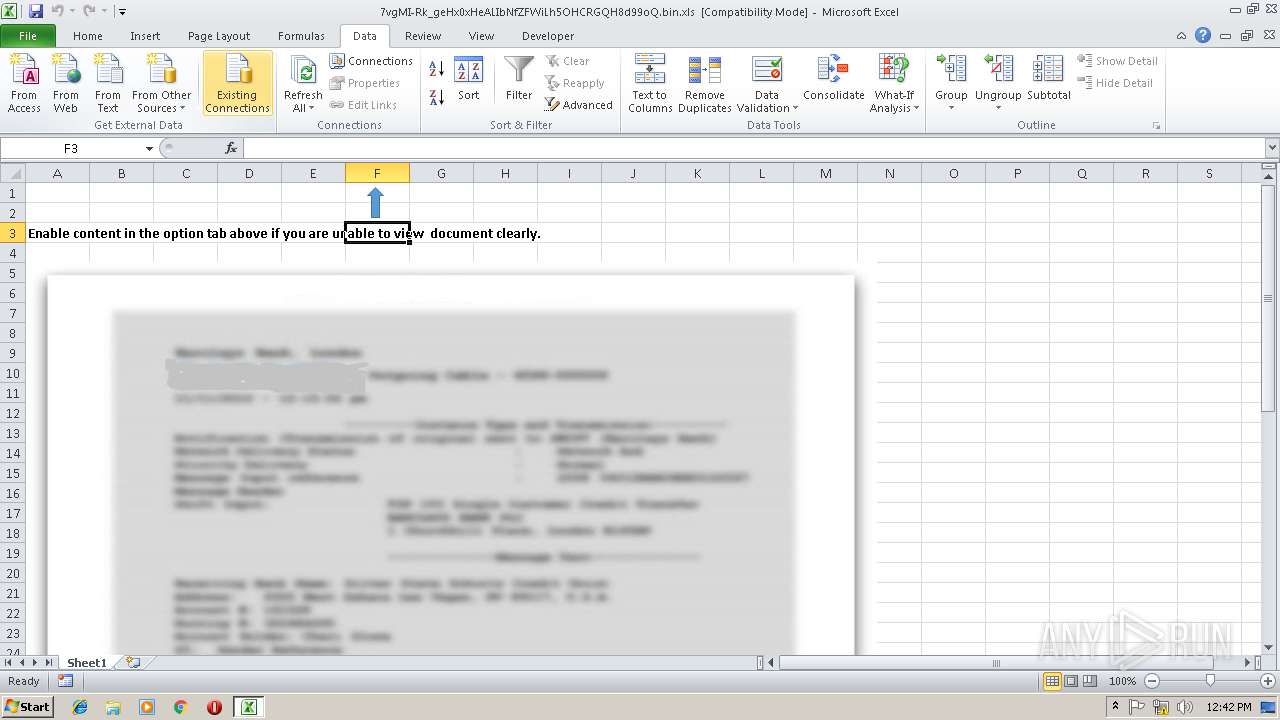
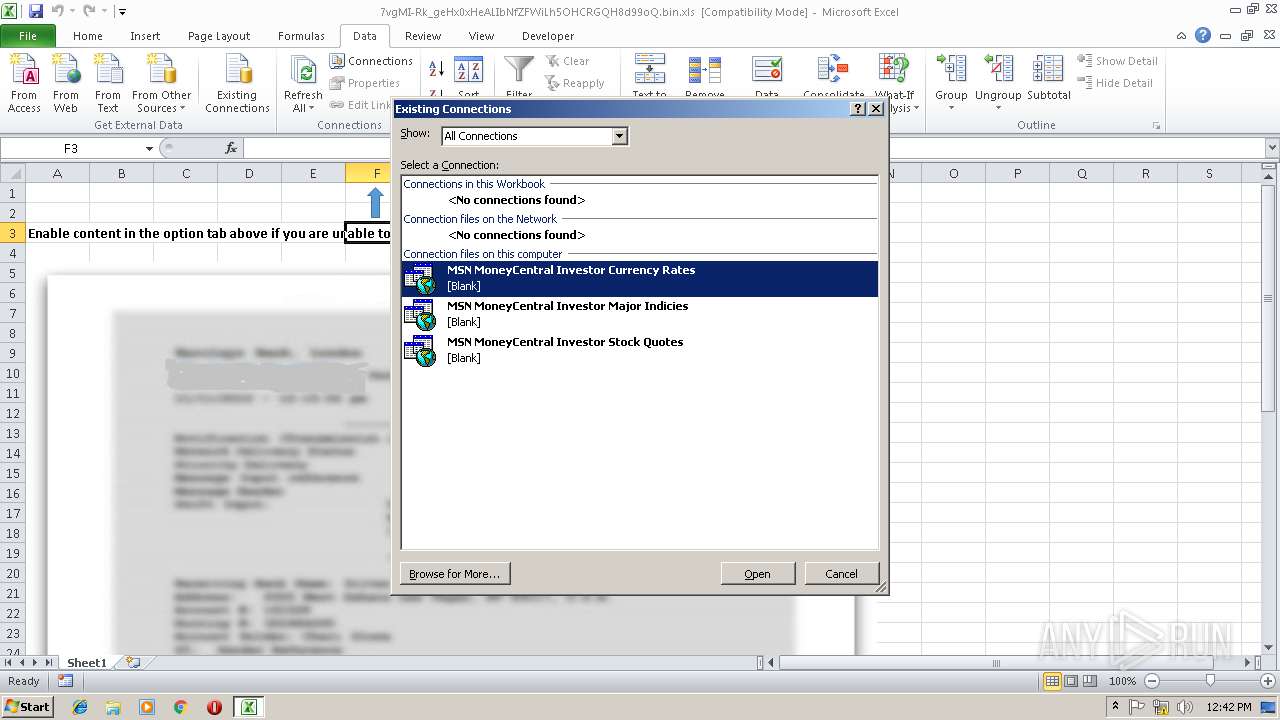
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Name of Creating Application: Microsoft Excel, Create Time/Date: Fri Jan 18 01:21:35 2019, Last Saved Time/Date: Fri Jan 18 01:26:47 2019, Security: 0 |
| MD5: | 78616C87C1AE77BED4D5265D9A937B98 |
| SHA1: | 6A973607EB3D3CC7EDE0BD2C0C48C238FDF18E50 |
| SHA256: | EEF80C23F464FA0787C74C477802C86CD7D915688B8793870911901FC77DF684 |
| SSDEEP: | 1536:Fk3hOdsylKlgryzc4bNhZFGzE+cL2knAEsjRUPcspcwucbHcAgcJXcHhcN6kca0D:Fk3hOdsylKlgryzc4bNhZFGzE+cL2kn8 |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2996)
Application was dropped or rewritten from another process
- tempora.com (PID: 3972)
- regsvcyvvhdblp.exe (PID: 1636)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2996)
FORMBOOK was detected
- explorer.exe (PID: 284)
Changes the autorun value in the registry
- wlanext.exe (PID: 2500)
Actions looks like stealing of personal data
- wlanext.exe (PID: 2500)
Formbook was detected
- wlanext.exe (PID: 2500)
- Firefox.exe (PID: 3800)
Connects to CnC server
- explorer.exe (PID: 284)
Stealing of credential data
- wlanext.exe (PID: 2500)
SUSPICIOUS
Starts CMD.EXE for commands execution
- wlanext.exe (PID: 2500)
Starts application with an unusual extension
- EXCEL.EXE (PID: 2996)
Writes to a desktop.ini file (may be used to cloak folders)
- EXCEL.EXE (PID: 2996)
Creates files in the user directory
- wlanext.exe (PID: 2500)
Executable content was dropped or overwritten
- explorer.exe (PID: 284)
- DllHost.exe (PID: 3104)
Loads DLL from Mozilla Firefox
- wlanext.exe (PID: 2500)
Creates files in the program directory
- DllHost.exe (PID: 3104)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 284)
Creates files in the user directory
- EXCEL.EXE (PID: 2996)
- Firefox.exe (PID: 3800)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2019:01:18 01:21:35 |
| ModifyDate: | 2019:01:18 01:26:47 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Sheet1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
44
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Mhdrl9xmx\regsvcyvvhdblp.exe" | C:\Program Files\Mhdrl9xmx\regsvcyvvhdblp.exe | — | explorer.exe | |||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet and Rlogin client Exit code: 0 Version: Release 0.70 Modules
| |||||||||||||||
| 2412 | "C:\Windows\System32\taskhost.exe" | C:\Windows\System32\taskhost.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | "C:\Windows\System32\wlanext.exe" | C:\Windows\System32\wlanext.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wireless LAN 802.11 Extensibility Framework Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2656 | /c del "C:\Users\admin\AppData\Local\Temp\tempora.com" | C:\Windows\System32\cmd.exe | — | wlanext.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3104 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3800 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wlanext.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3972 | C:\Users\admin\AppData\Local\Temp\tempora.com | C:\Users\admin\AppData\Local\Temp\tempora.com | — | EXCEL.EXE | |||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet and Rlogin client Exit code: 0 Version: Release 0.70 Modules
| |||||||||||||||
Total events
971
Read events
903
Write events
56
Delete events
12
Modification events
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 2 , |
Value: 32202C00B40B0000010000000000000000000000 | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: B40B0000CE503E062BAFD40100000000 | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | 2 , |
Value: 32202C00B40B0000010000000000000000000000 | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2996) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\20ECC6 |
| Operation: | write | Name: | 20ECC6 |
Value: 04000000B40B00005500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C003700760067004D0049002D0052006B005F006700650048007800300078004800650041004C00490062004E0066005A004600570069004C00680035004F0048004300520047005100480038006400390039006F0051002E00620069006E002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000F06150072BAFD401C6EC2000C6EC200000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
73
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE812.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2996 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF79A1B283A41A5E77.TMP | — | |
MD5:— | SHA256:— | |||
| 2996 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF475DA05B0D0C4D21.TMP | — | |
MD5:— | SHA256:— | |||
| 2996 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\raw[1].txt | text | |
MD5:— | SHA256:— | |||
| 2996 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\tempora.com | executable | |
MD5:— | SHA256:— | |||
| 2996 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@friendpaste[1].txt | text | |
MD5:— | SHA256:— | |||
| 2996 | EXCEL.EXE | C:\Users\admin\Documents\My Data Sources\+NewSQLServerConnection.odc | html | |
MD5:149E8C684B9EA9887DD2E7E596E7187C | SHA256:43B12E68FB3B5BCC4099D796FA670A62B116A894437454A20050661DEF9D8816 | |||
| 2996 | EXCEL.EXE | C:\Users\admin\Documents\My Data Sources\+Connect to New Data Source.odc | html | |
MD5:16A8A9A2B0A8B65FAF28E1007DB6733F | SHA256:3A13080059292811E5AC3F9E8B04B2C8EEA95D6A5538116AD751D11C834E6056 | |||
| 2996 | EXCEL.EXE | C:\Users\admin\Documents\My Data Sources\FOLDER.ICO | image | |
MD5:A6DDCCFDAD18D5CA7AAEB168B6D02253 | SHA256:3114451F95C7FB8D7D884A19C724F6C7FF906B6D9BEC1BF7C6300D2CCA4F43A6 | |||
| 2500 | wlanext.exe | C:\Users\admin\AppData\Roaming\219N9U6T\219logrc.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
8
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
284 | explorer.exe | GET | 404 | 104.224.194.71:80 | http://dongtuowuliu.com/results/?PPx=7Mvu92GYn4tIazjtcfKayTEFRroaK2fU8iZ5/2vm2ExSO7v6alsh9Lmitu79FuMzmWqjNg==&3fs=Jz9L_rT&sql=1 | US | html | 3.56 Kb | malicious |
284 | explorer.exe | POST | — | 104.224.194.71:80 | http://dongtuowuliu.com/results/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 104.224.194.71:80 | http://dongtuowuliu.com/results/ | US | — | — | malicious |
284 | explorer.exe | POST | — | 104.224.194.71:80 | http://dongtuowuliu.com/results/ | US | — | — | malicious |
284 | explorer.exe | GET | 301 | 216.240.142.110:80 | http://njglzz.com/results/?PPx=8L2vQcrtVFY/QcmEKf92S2XLzICAFQHLgUP8SFiAXSz/GMz/pfv4N7UqO/Kh0sFO9bMxAw==&3fs=Jz9L_rT | US | html | 178 b | malicious |
284 | explorer.exe | GET | 404 | 185.175.208.69:80 | http://svashizlle.com/results/?PPx=6VZYsfE18WLgC5WOYWZI4Sx28VPTt5qeDW90/KxIEykO4UWir6SNykU/u3el9+OkYLp0qQ==&3fs=Jz9L_rT&sql=1 | DE | html | 331 b | malicious |
284 | explorer.exe | POST | 404 | 185.175.208.69:80 | http://svashizlle.com/results/ | DE | html | 277 b | malicious |
284 | explorer.exe | POST | — | 185.175.208.69:80 | http://svashizlle.com/results/ | DE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2996 | EXCEL.EXE | 149.202.176.20:443 | friendpaste.com | OVH SAS | FR | unknown |
284 | explorer.exe | 216.240.142.110:80 | njglzz.com | MULTACOM CORPORATION | US | malicious |
284 | explorer.exe | 104.224.194.71:80 | dongtuowuliu.com | eSited Solutions | US | malicious |
284 | explorer.exe | 185.175.208.69:80 | svashizlle.com | Hydra Communications Ltd | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
friendpaste.com |
| unknown |
andichain.com |
| unknown |
mkcose.com |
| unknown |
njglzz.com |
| malicious |
dongtuowuliu.com |
| malicious |
pemjoladgroup.com |
| unknown |
surgeonelderlaw.com |
| unknown |
svashizlle.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
6 ETPRO signatures available at the full report