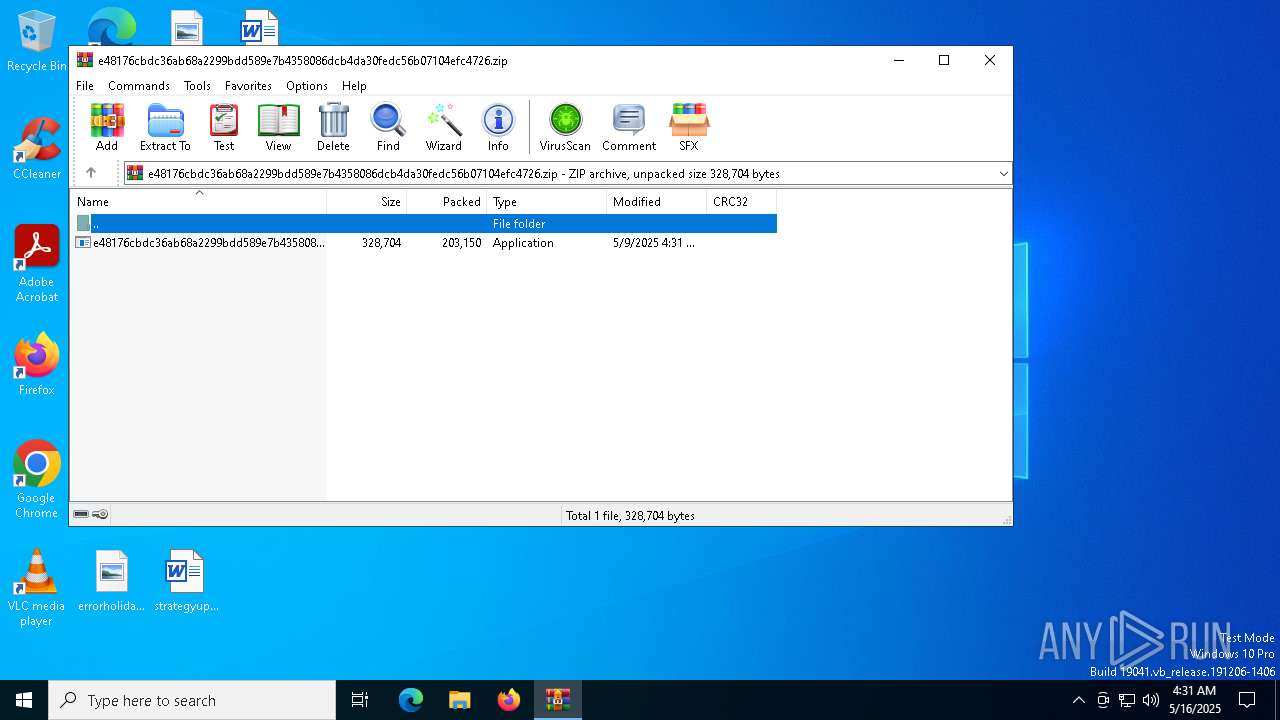
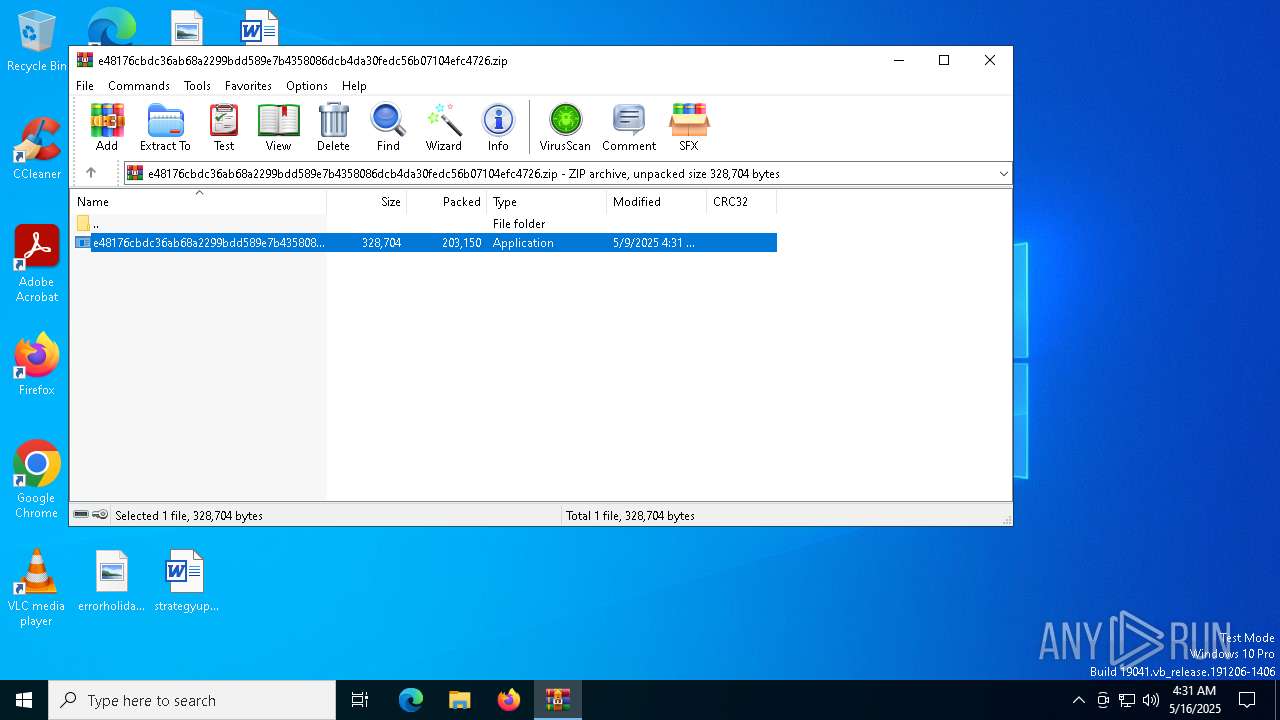
| File name: | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.zip |
| Full analysis: | https://app.any.run/tasks/863ce3a0-5606-4dac-9e37-3356950c04da |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | May 16, 2025, 04:31:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | EFBA149E8DB76AF8D0531256C07D9BDB |
| SHA1: | 809EBCAD2CF4C4AAE87D1DFB575BE43B3EE621B8 |
| SHA256: | EEEC222DCCBCDD401387A3856744CE153B2563E6ADB98FA6D8C6E2C858427026 |
| SSDEEP: | 6144:x8bewvbb/u5C+OJcud+CIL3oe728AwVbqmQjBnnbo6n:x8bew/u5CdGud+Xoe5VbqxjBbo6n |
MALICIOUS
COBALTSTRIKE has been found (auto)
- WinRAR.exe (PID: 1532)
COBALTSTRIKE has been detected (YARA)
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
COBALTSTRIKE has been detected (SURICATA)
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1532)
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
Connects to unusual port
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1532)
Checks supported languages
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
Reads the computer name
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
Reads the machine GUID from the registry
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
Checks proxy server information
- e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe (PID: 7828)
- slui.exe (PID: 8016)
Reads the software policy settings
- slui.exe (PID: 7336)
- slui.exe (PID: 8016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
CobalStrike
(PID) Process(7828) e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe
C2 (1)89.197.154.116/cm
BeaconTypeHTTP
Port7810
SleepTime60000
MaxGetSize1048576
Jitter0
PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCyCm3eiVuYdkFc4zlvTmnM5Yv3
7zNHBgd+jtoytL3ld90WCLrG8gq1gXNxTn++gAapxKM4dQVLZYoBxjvKBJjdH1ki
3ZkZ+q86VAP1hT/kAjRnh7eKV9vjZOgl2oGI5Aa9z3rWayWVdUTJ4ffE3inAfIe1
sEXbsST76lZlUOlPUwIDAQAB
-----END PUBLIC KEY-----
DNS_strategyround-robin
DNS_strategy_rotate_seconds-1
DNS_strategy_fail_x-1
DNS_strategy_fail_seconds-1
SpawnTo00000000000000000000000000000000
Spawnto_x86%windir%\syswow64\rundll32.exe
Spawnto_x64%windir%\sysnative\rundll32.exe
CryptoScheme0
HttpGet_VerbGET
HttpPost_VerbPOST
HttpPostChunk0
Watermark987654321
bStageCleanupFalse
bCFGCautionFalse
UserAgentMozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0; NP06)
HttpPostUri/submit.php
HttpGet_Metadata
SessionId (2)base64
header: Cookie
HttpPost_Metadata
ConstHeaders (1)Content-Type: application/octet-stream
SessionId (1)parameter: id
Output (1)print
bUsesCookies0001
Proxy_BehaviorUse IE settings
tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
KillDate0-0-0
bProcInject_StartRWXTrue
bProcInject_UseRWXTrue
bProcInject_MinAllocSize0
ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000...
ProcInject_Stub0b34150c342e35d2ffacb2227620d91c
ProcInject_AllocationMethodVirtualAllocEx
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:09 04:31:36 |
| ZipCRC: | 0xb5e5d65f |
| ZipCompressedSize: | 203150 |
| ZipUncompressedSize: | 328704 |
| ZipFileName: | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe |
Total processes
139
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1532 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7304 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7336 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7828 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1532.22196\e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1532.22196\e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
CobalStrike(PID) Process(7828) e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe C2 (1)89.197.154.116/cm BeaconTypeHTTP Port7810 SleepTime60000 MaxGetSize1048576 Jitter0 PublicKey-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCyCm3eiVuYdkFc4zlvTmnM5Yv3
7zNHBgd+jtoytL3ld90WCLrG8gq1gXNxTn++gAapxKM4dQVLZYoBxjvKBJjdH1ki
3ZkZ+q86VAP1hT/kAjRnh7eKV9vjZOgl2oGI5Aa9z3rWayWVdUTJ4ffE3inAfIe1
sEXbsST76lZlUOlPUwIDAQAB
-----END PUBLIC KEY----- DNS_strategyround-robin DNS_strategy_rotate_seconds-1 DNS_strategy_fail_x-1 DNS_strategy_fail_seconds-1 SpawnTo00000000000000000000000000000000 Spawnto_x86%windir%\syswow64\rundll32.exe Spawnto_x64%windir%\sysnative\rundll32.exe CryptoScheme0 HttpGet_VerbGET HttpPost_VerbPOST HttpPostChunk0 Watermark987654321 bStageCleanupFalse bCFGCautionFalse UserAgentMozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0; NP06) HttpPostUri/submit.php HttpGet_Metadata SessionId (2)base64 header: Cookie HttpPost_Metadata ConstHeaders (1)Content-Type: application/octet-stream SessionId (1)parameter: id Output (1)print bUsesCookies0001 Proxy_BehaviorUse IE settings tcpFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 smbFrameHeader0004000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 KillDate0-0-0 bProcInject_StartRWXTrue bProcInject_UseRWXTrue bProcInject_MinAllocSize0 ProcInject_PrependAppend_x86000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_PrependAppend_x64000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000... ProcInject_Stub0b34150c342e35d2ffacb2227620d91c ProcInject_AllocationMethodVirtualAllocEx | |||||||||||||||
| 8016 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 122
Read events
3 113
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.zip | |||
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
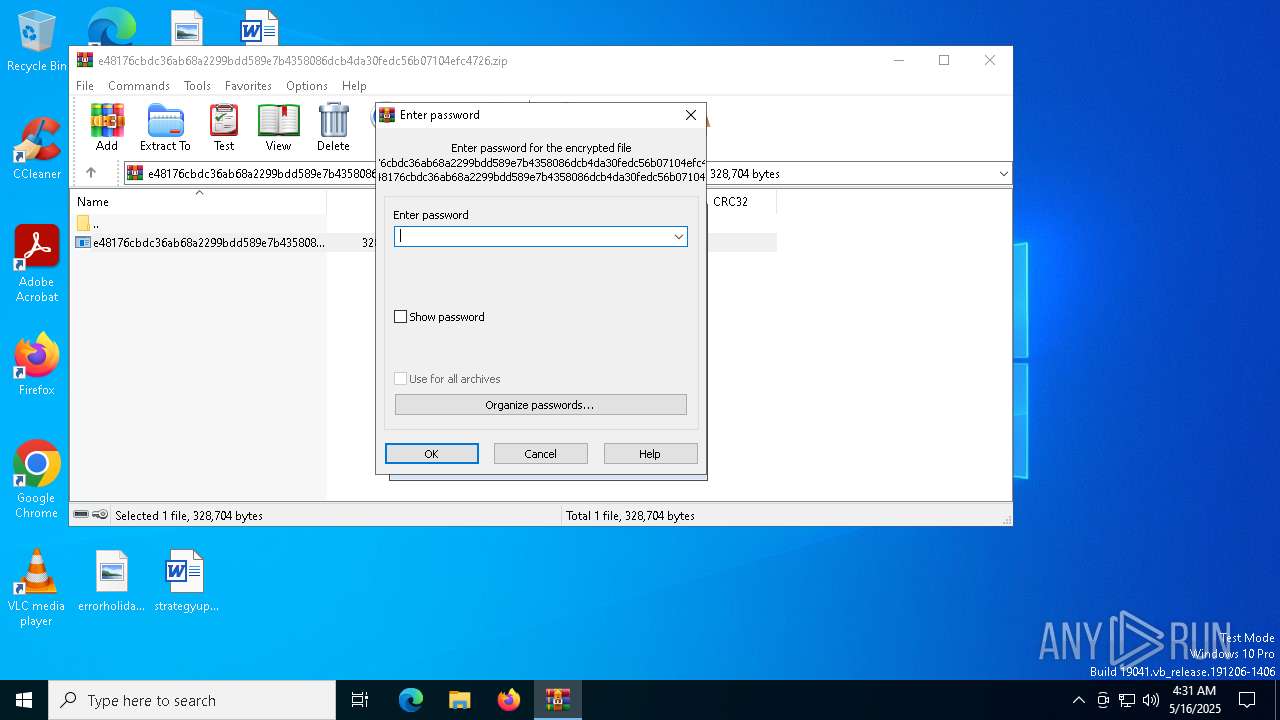
| (PID) Process: | (1532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb1532.22196\e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | executable | |
MD5:C22C689CCAE2A765155CEF2E64D12BBA | SHA256:E48176CBDC36AB68A2299BDD589E7B4358086DCB4DA30FEDC56B07104EFC4726 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
27
DNS requests
13
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.18.244.216:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4164 | RUXIMICS.exe | GET | 200 | 2.18.244.216:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.18.244.216:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4164 | RUXIMICS.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6108 | firefox.exe | GET | — | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | GET | — | 89.197.154.116:7810 | http://89.197.154.116:7810/cm | unknown | — | — | malicious |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | GET | — | 89.197.154.116:7810 | http://89.197.154.116:7810/cm | unknown | — | — | malicious |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | GET | — | 89.197.154.116:7810 | http://89.197.154.116:7810/cm | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4164 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.18.244.216:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
2104 | svchost.exe | 2.18.244.216:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
4164 | RUXIMICS.exe | 2.18.244.216:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
5496 | MoUsoCoreWorker.exe | 173.223.117.131:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 173.223.117.131:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4164 | RUXIMICS.exe | 173.223.117.131:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | Targeted Malicious Activity was Detected | ET MALWARE Cobalt Strike Beacon Observed |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | A Network Trojan was detected | BACKDOOR [ANY.RUN] Possible Cobalt Strike Beacon |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | Targeted Malicious Activity was Detected | ET MALWARE Cobalt Strike Beacon Observed |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | A Network Trojan was detected | BACKDOOR [ANY.RUN] Possible Cobalt Strike Beacon |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | Targeted Malicious Activity was Detected | ET MALWARE Cobalt Strike Beacon Observed |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | A Network Trojan was detected | BACKDOOR [ANY.RUN] Possible Cobalt Strike Beacon |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | Targeted Malicious Activity was Detected | ET MALWARE Cobalt Strike Beacon Observed |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | A Network Trojan was detected | BACKDOOR [ANY.RUN] Possible Cobalt Strike Beacon |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | Targeted Malicious Activity was Detected | ET MALWARE Cobalt Strike Beacon Observed |
7828 | e48176cbdc36ab68a2299bdd589e7b4358086dcb4da30fedc56b07104efc4726.exe | A Network Trojan was detected | BACKDOOR [ANY.RUN] Possible Cobalt Strike Beacon |