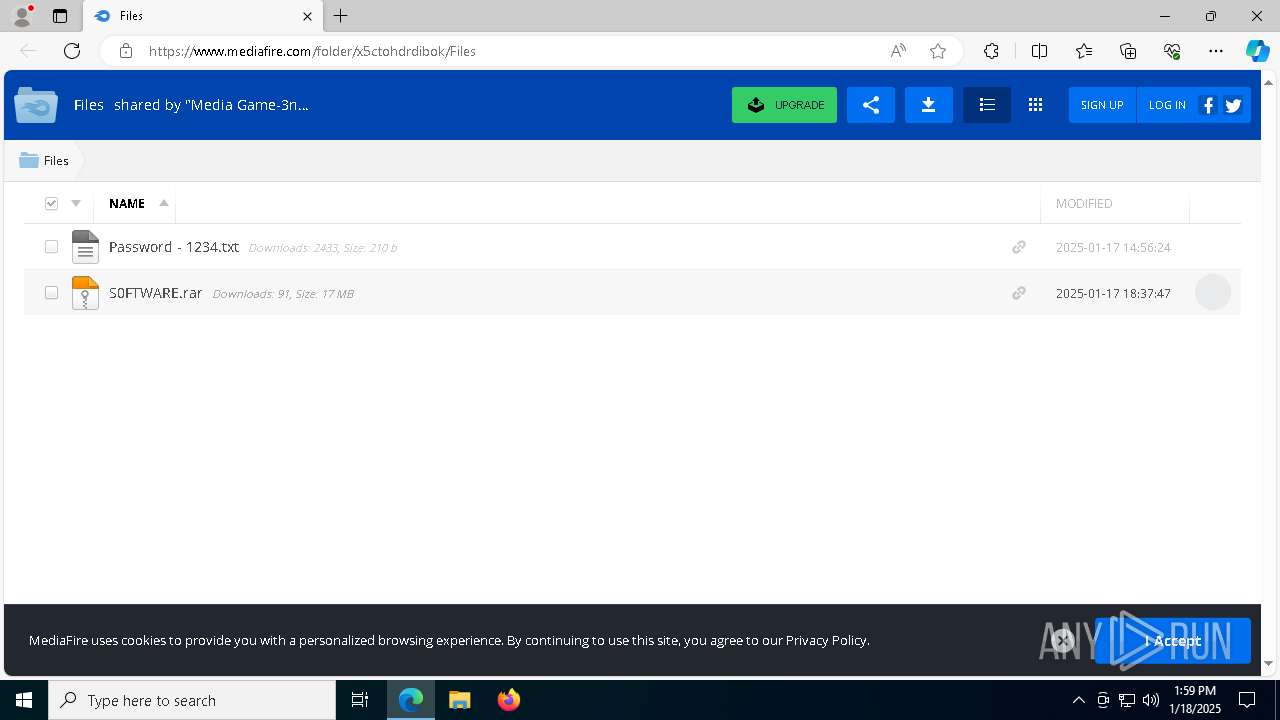
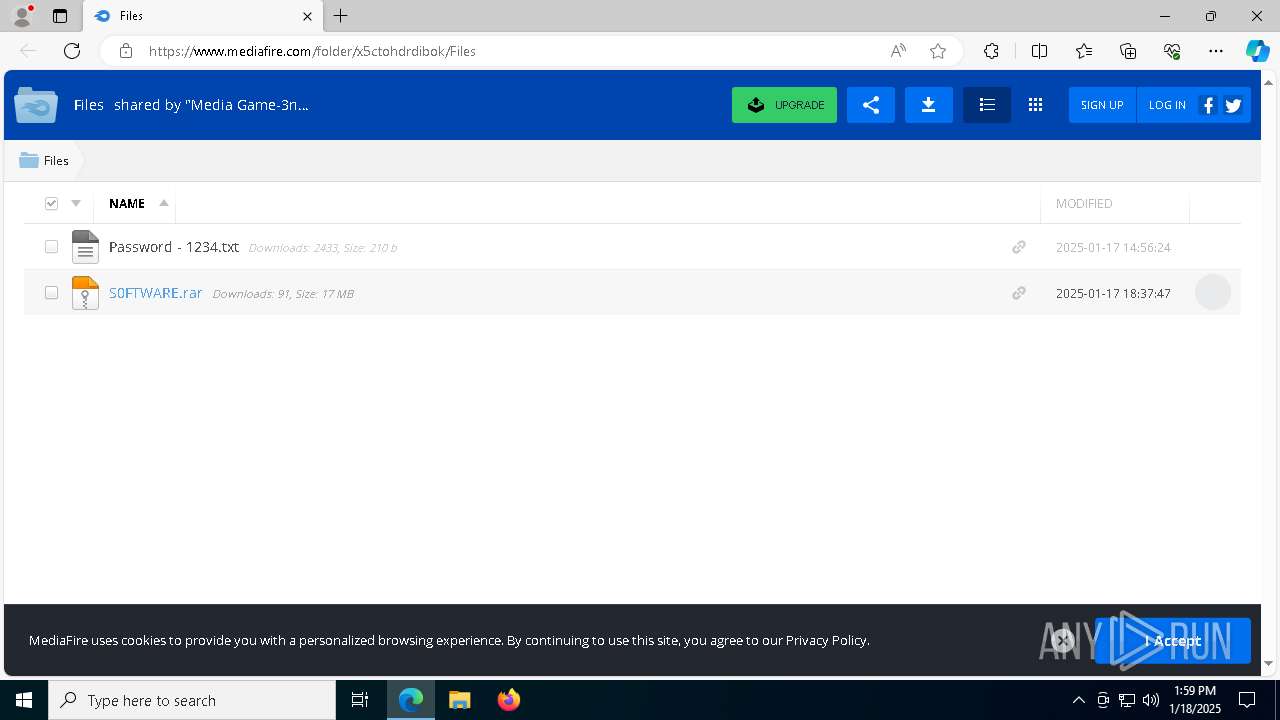
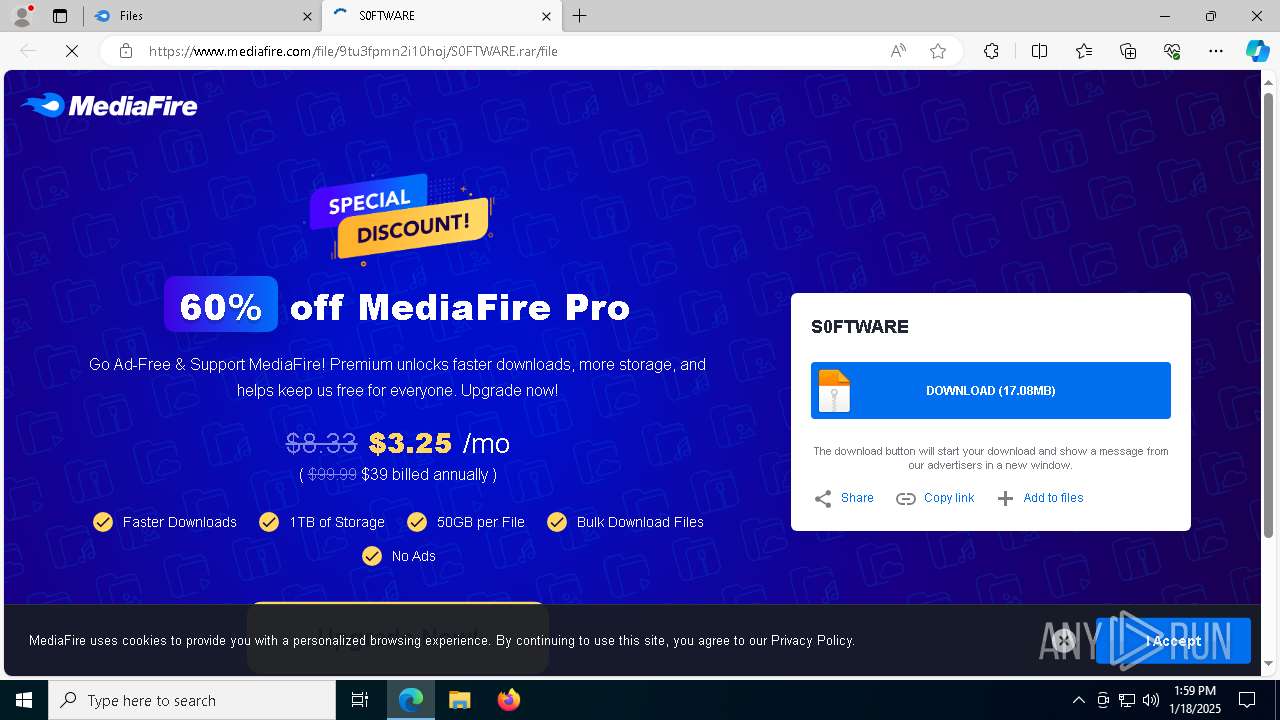
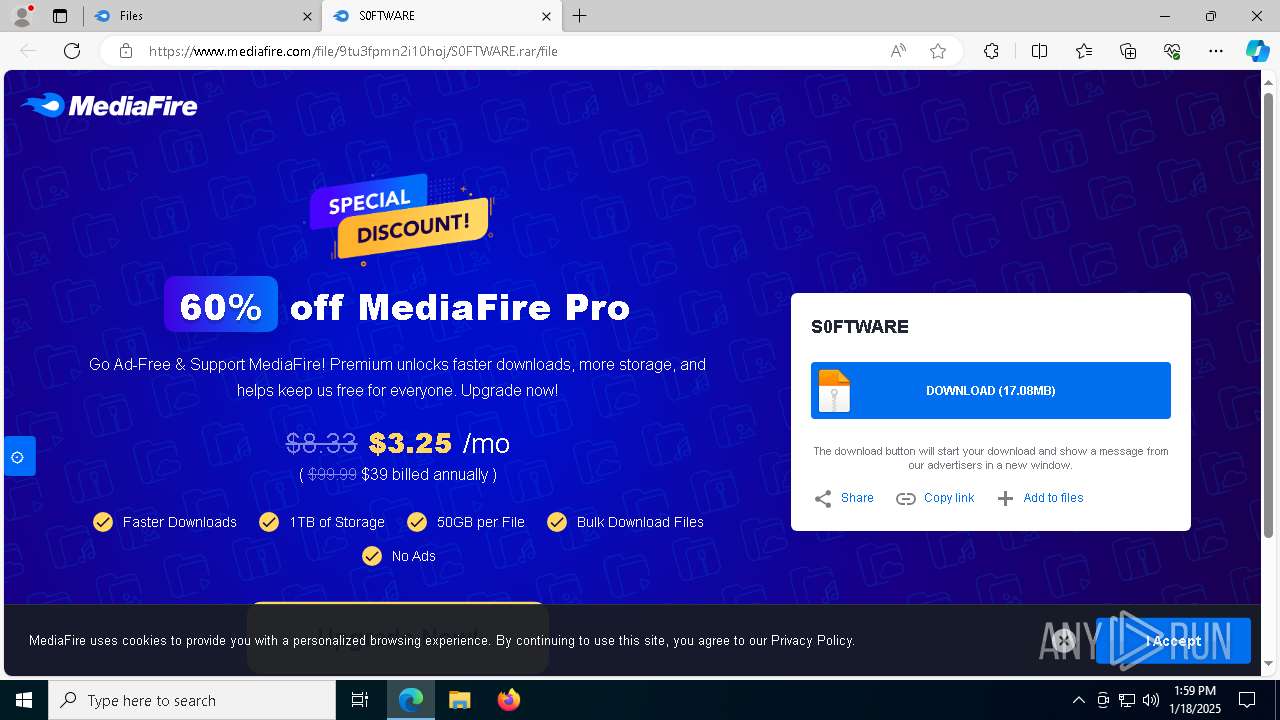
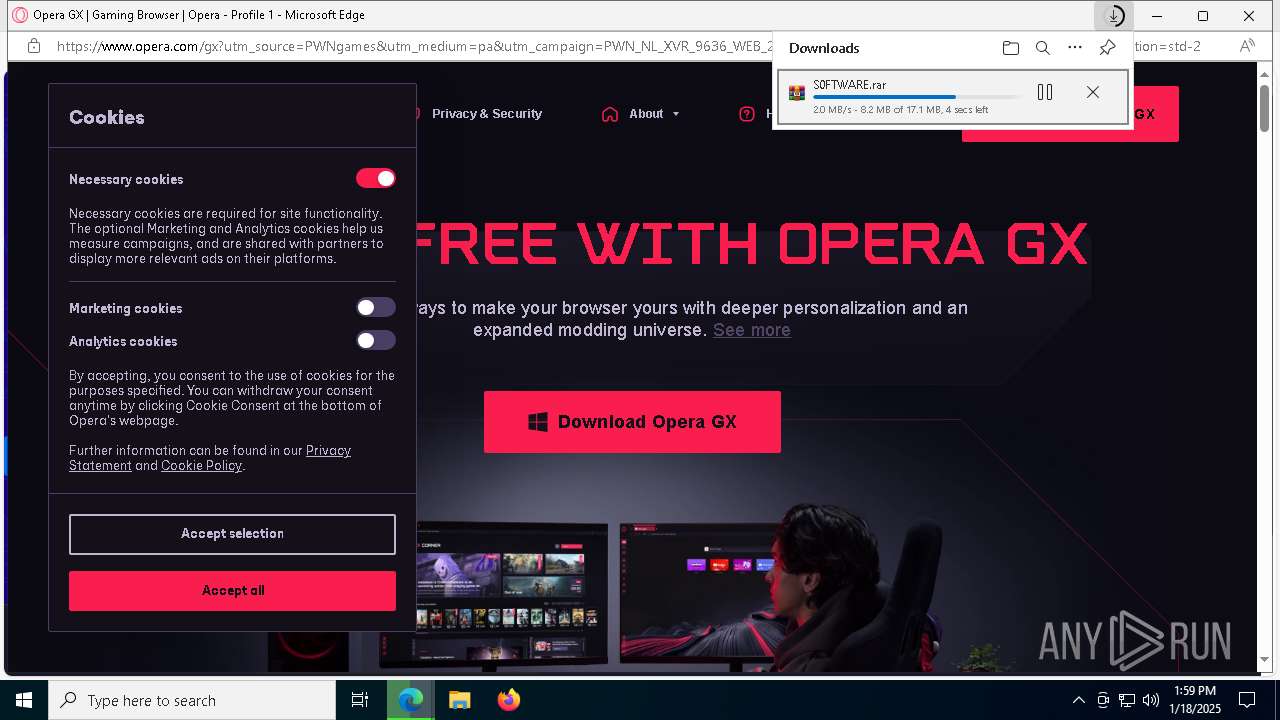
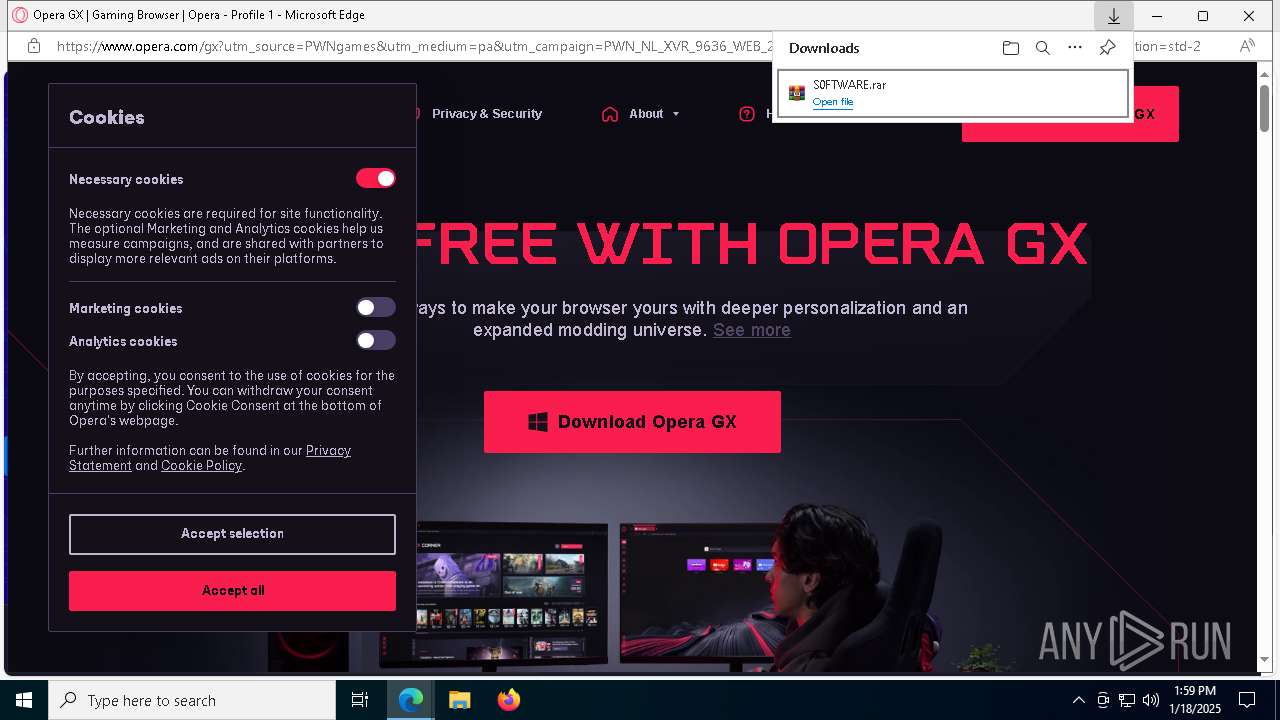
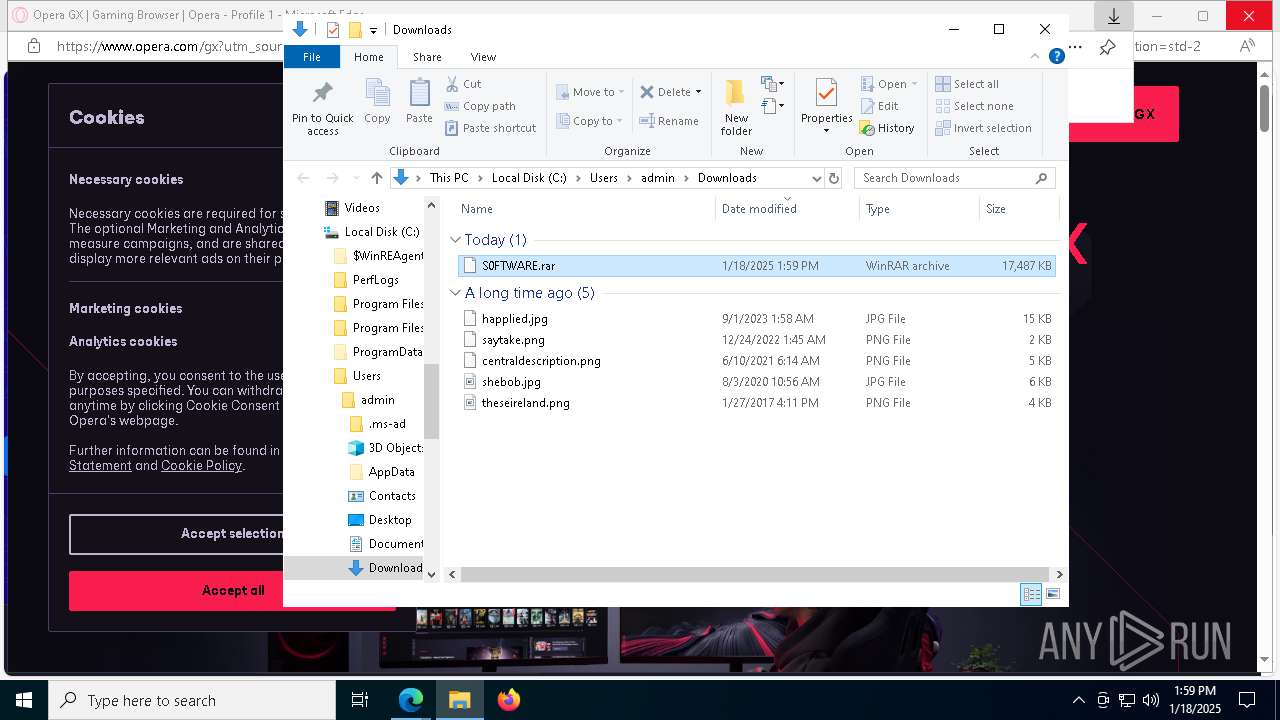
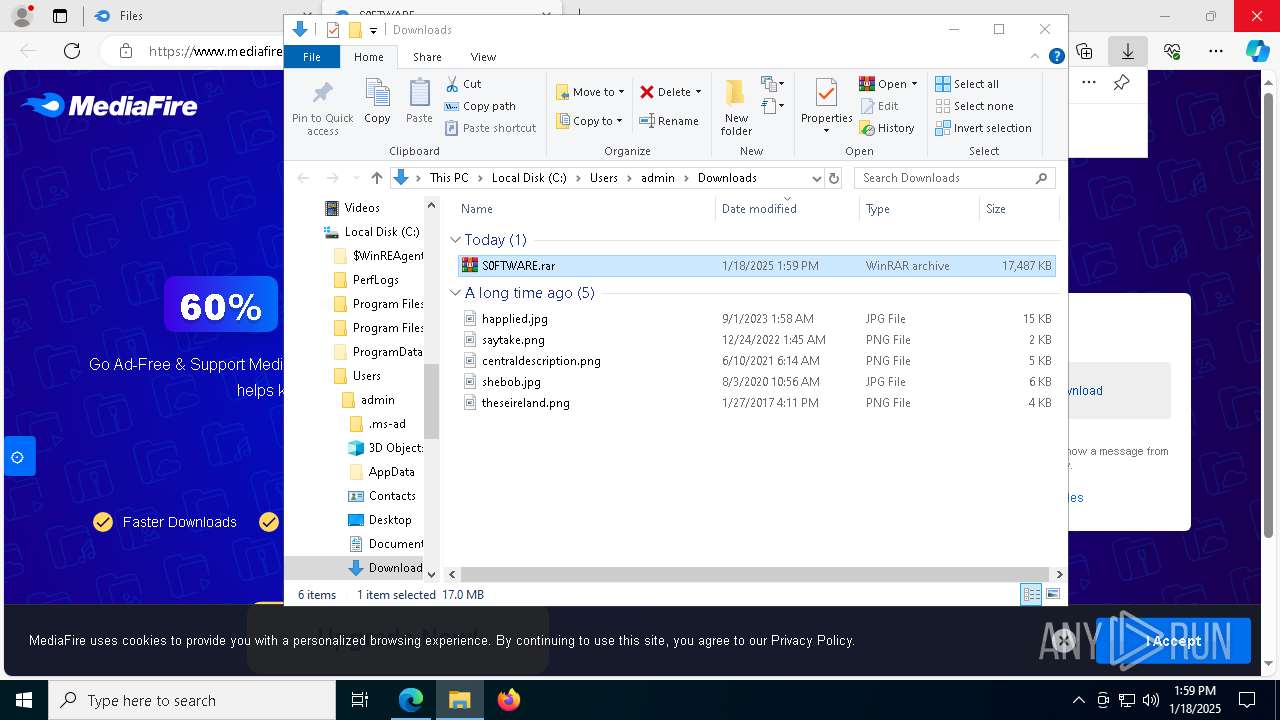
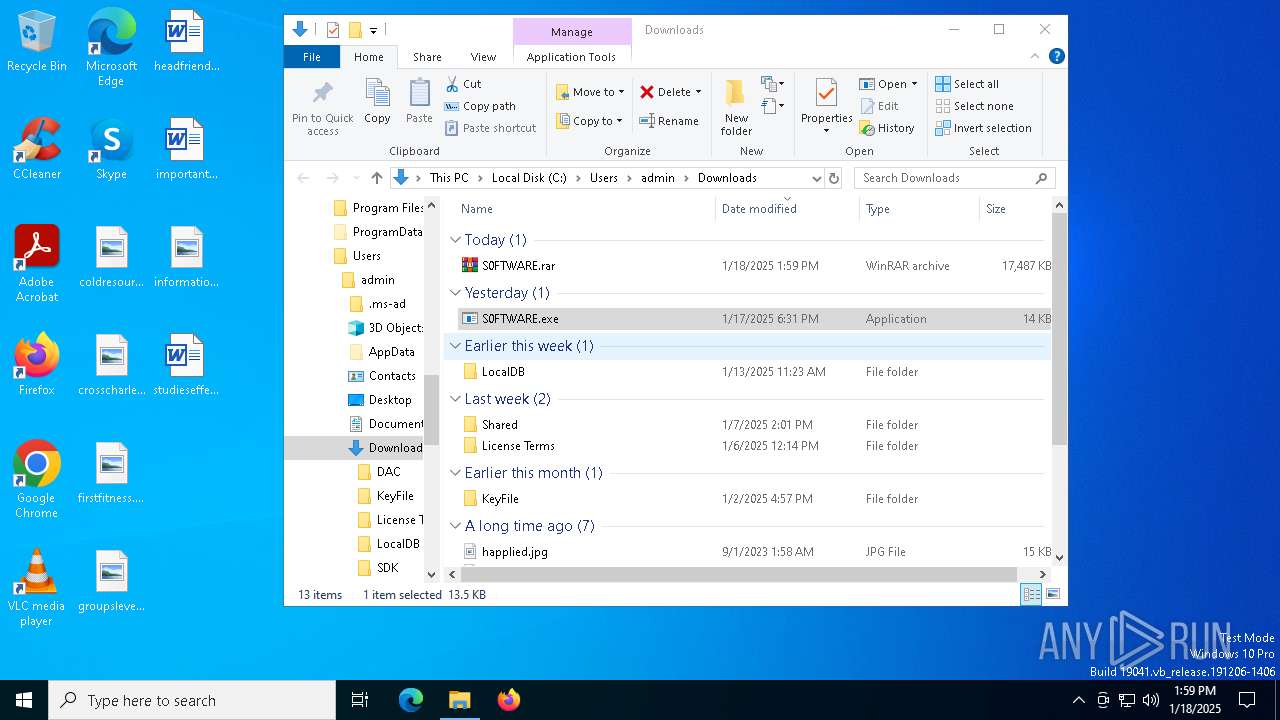
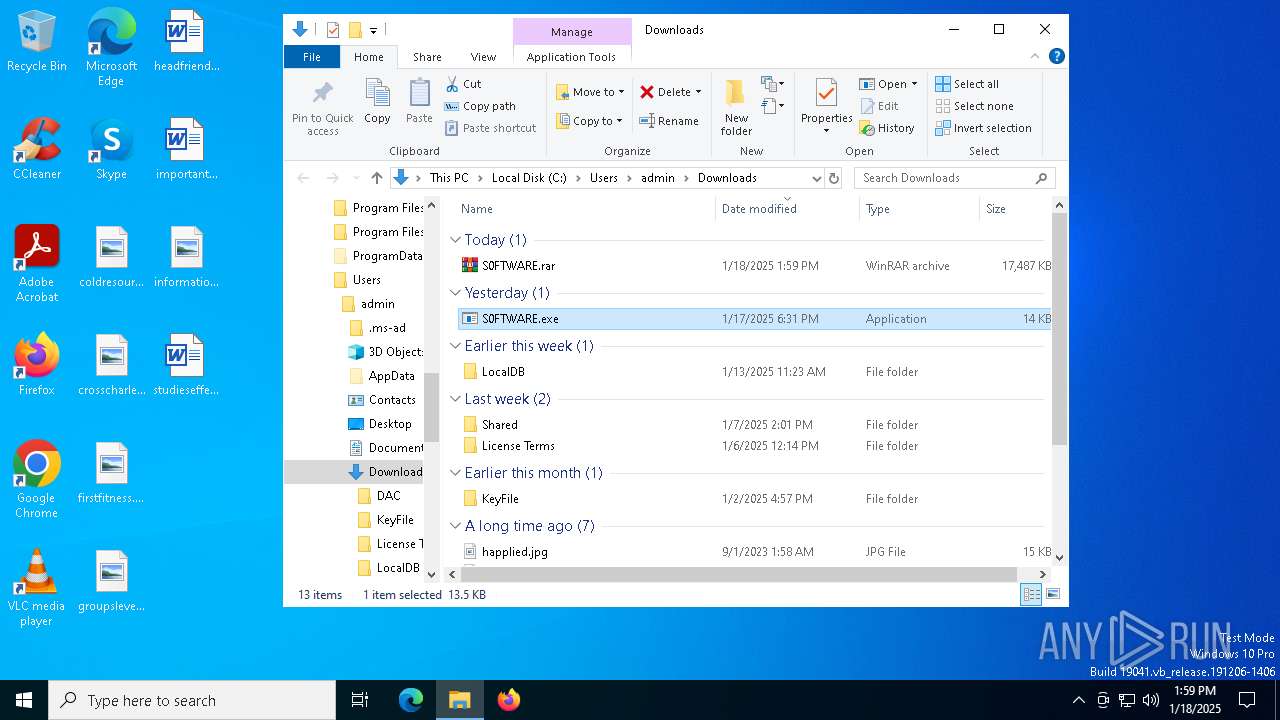
| URL: | https://www.mediafire.com/folder/x5ctohdrdibok/Files |
| Full analysis: | https://app.any.run/tasks/44528e6c-2464-46bf-be6f-c7671f3d9427 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
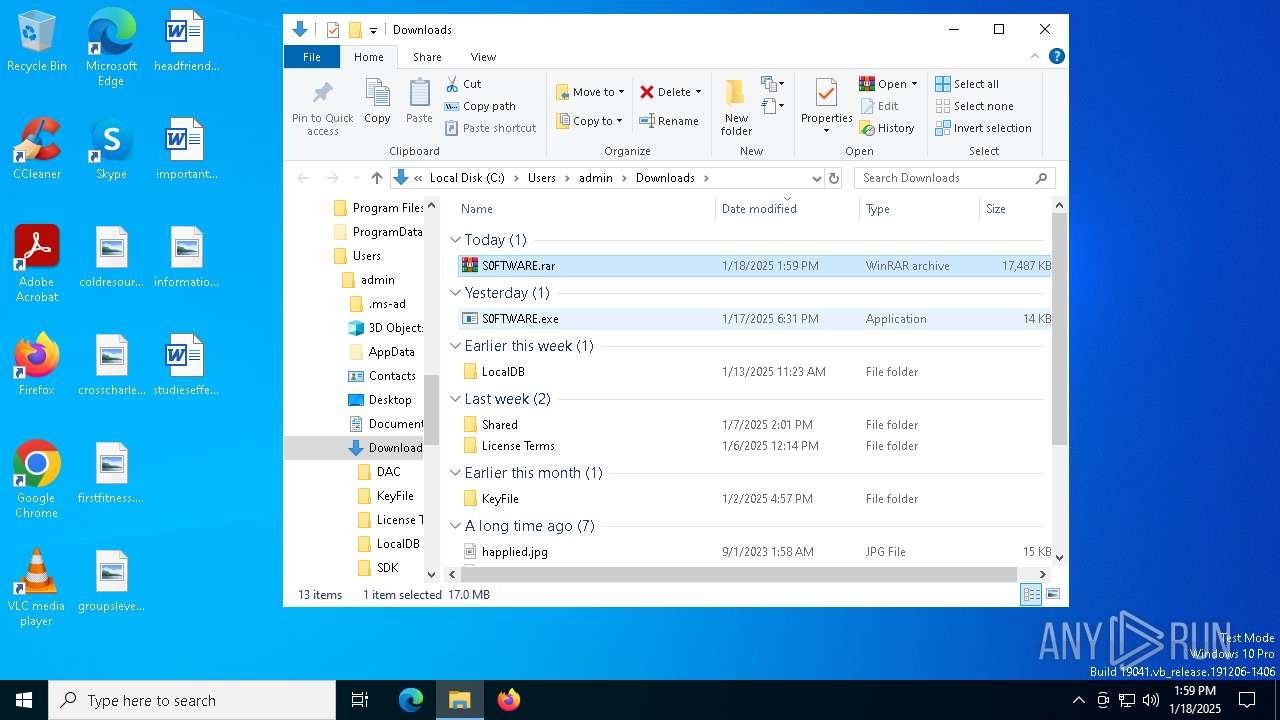
| Analysis date: | January 18, 2025, 13:59:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D3ECFF252B3EE125FF2920B102E97F79 |
| SHA1: | AB64C7DC44A78D474AC69830243B8CCAA746957E |
| SHA256: | EEEBBE2EABDA70D863C04025498CB666E86C0F4003D4455EBF06047975248F65 |
| SSDEEP: | 3:N8DSLw3eGUbKCBRMqO40:2OLw3eG+ZbO40 |
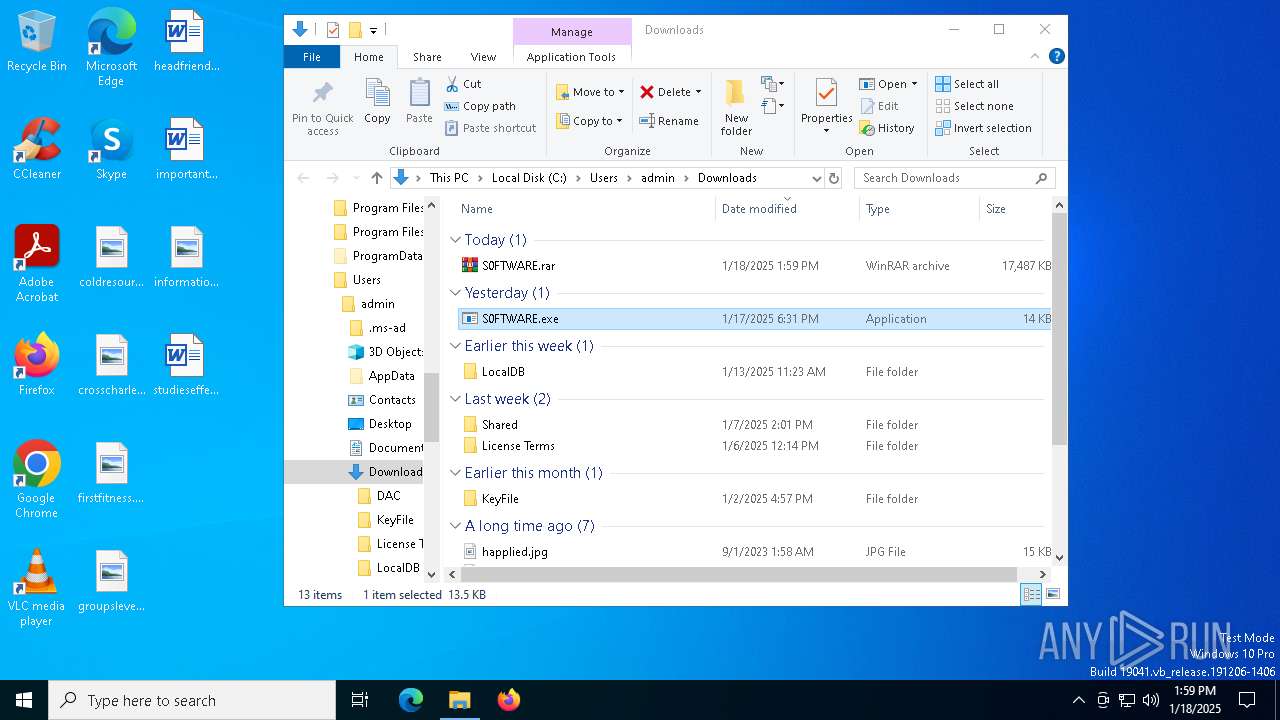
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7660)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 7376)
Adds path to the Windows Defender exclusion list
- S0FTWARE.exe (PID: 7620)
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7008)
- S0FTWARE.exe (PID: 7312)
Changes powershell execution policy (Bypass)
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7008)
- S0FTWARE.exe (PID: 7312)
- S0FTWARE.exe (PID: 7620)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7276)
- cmd.exe (PID: 8128)
Executing a file with an untrusted certificate
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
Actions looks like stealing of personal data
- file1.exe (PID: 6352)
Adds extension to the Windows Defender exclusion list
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7152)
Steals credentials from Web Browsers
- file1.exe (PID: 6352)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2192)
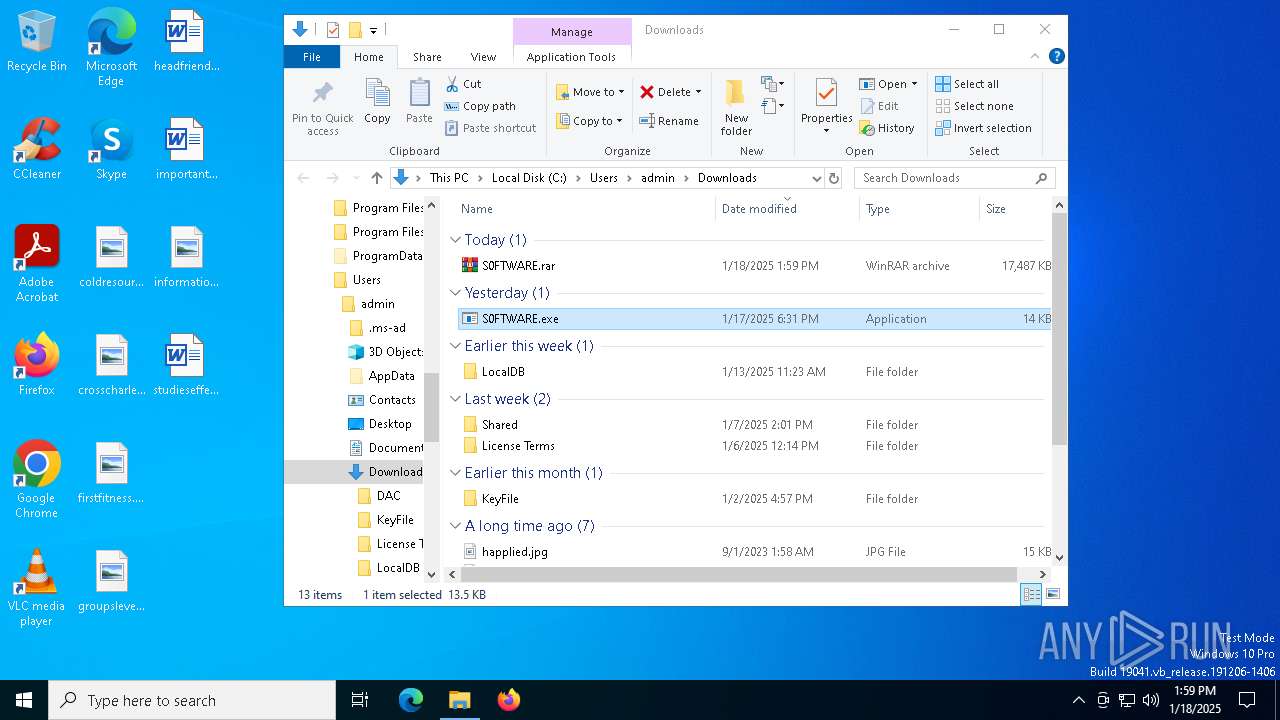
SUSPICIOUS
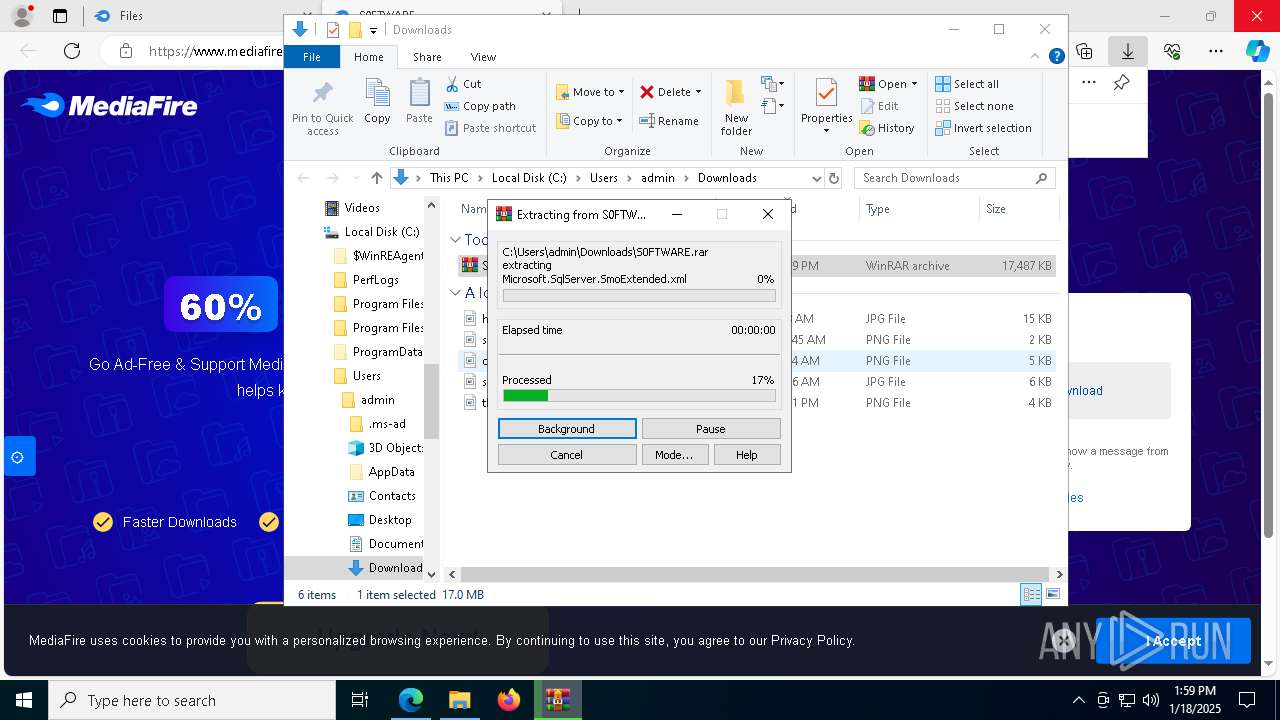
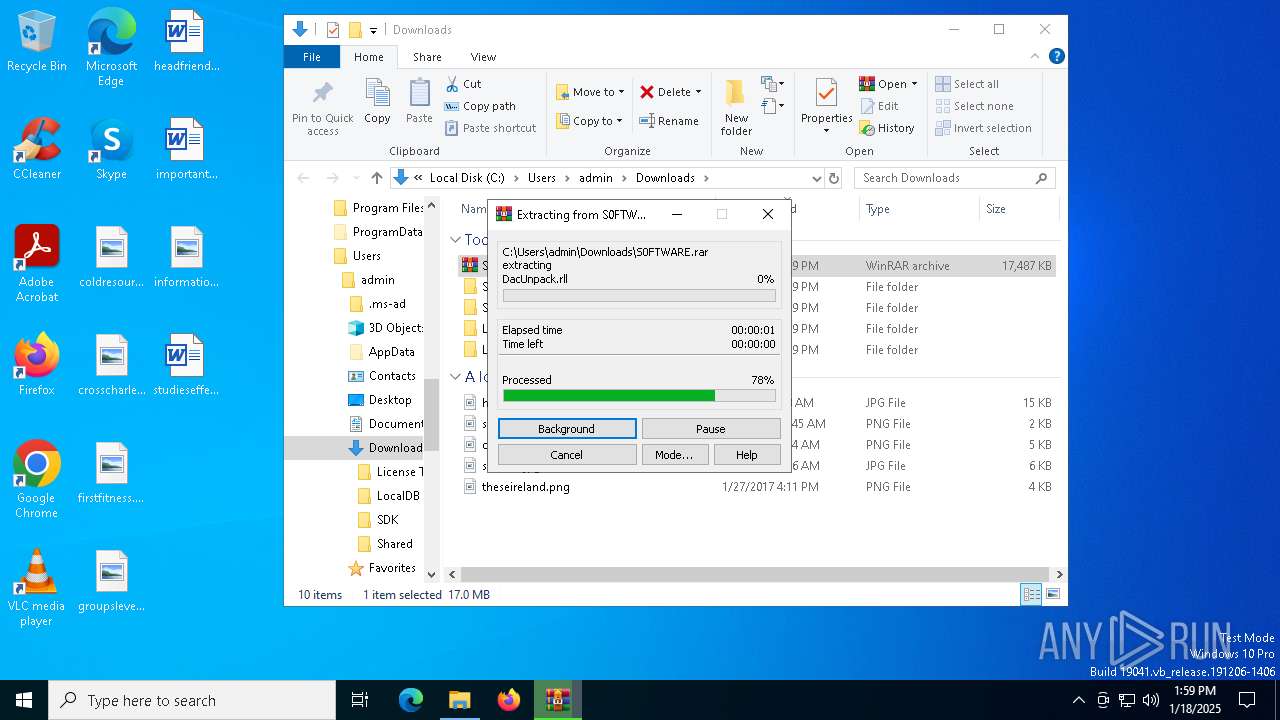
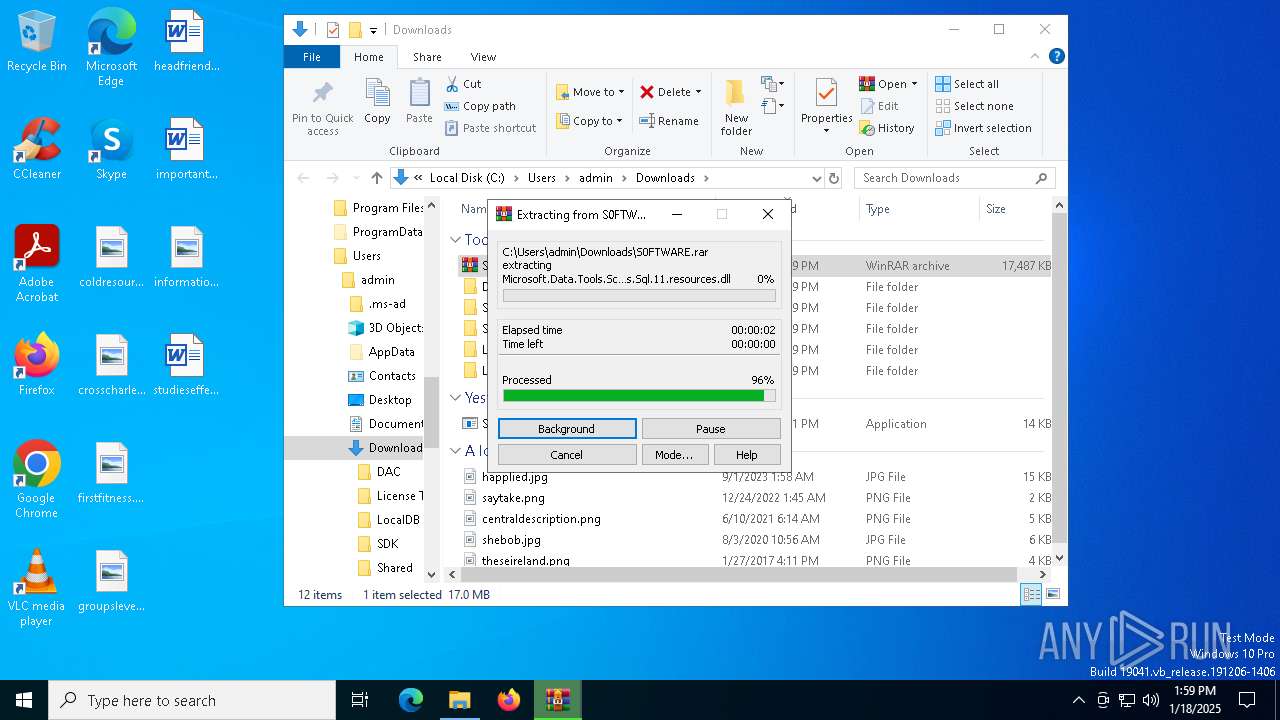
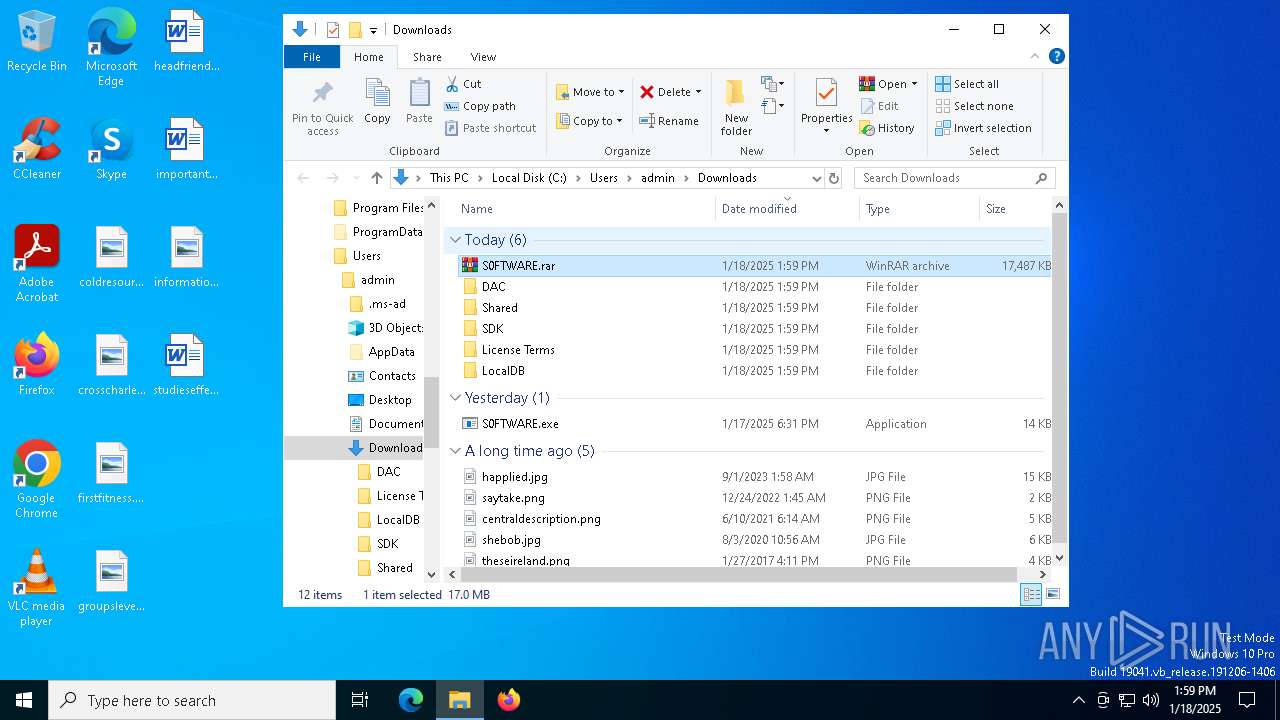
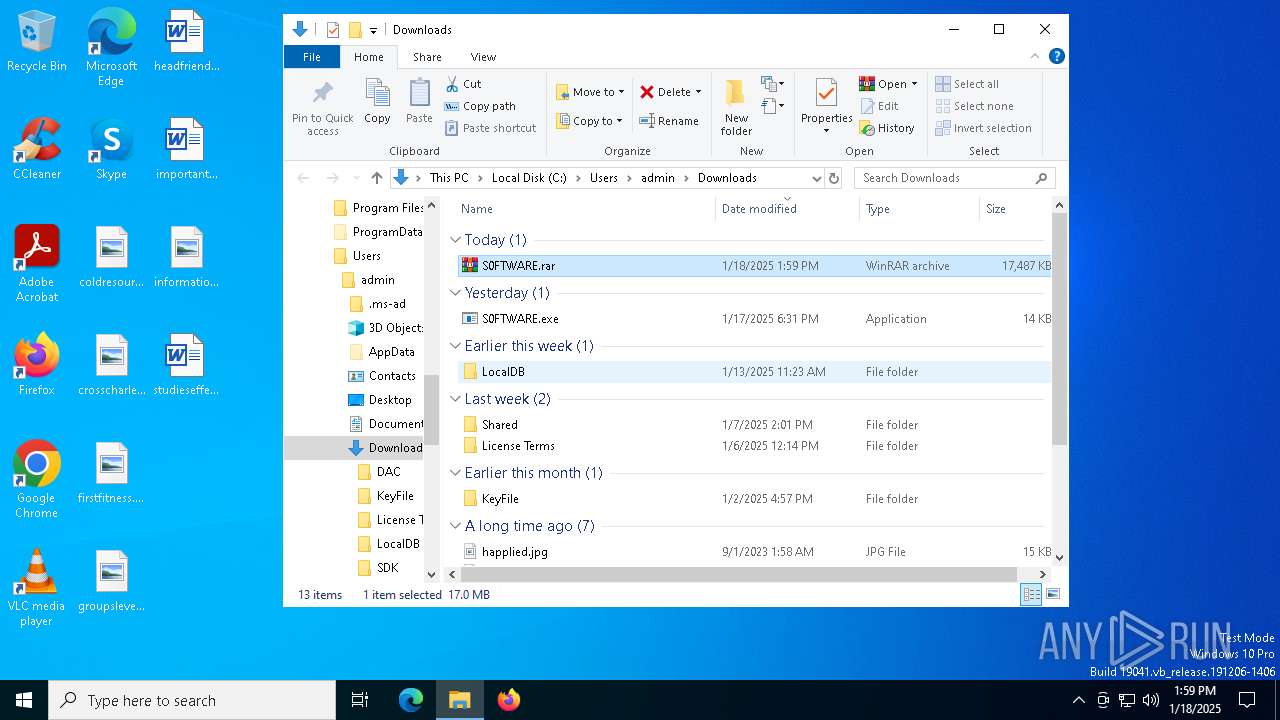
Process drops legitimate windows executable
- WinRAR.exe (PID: 7440)
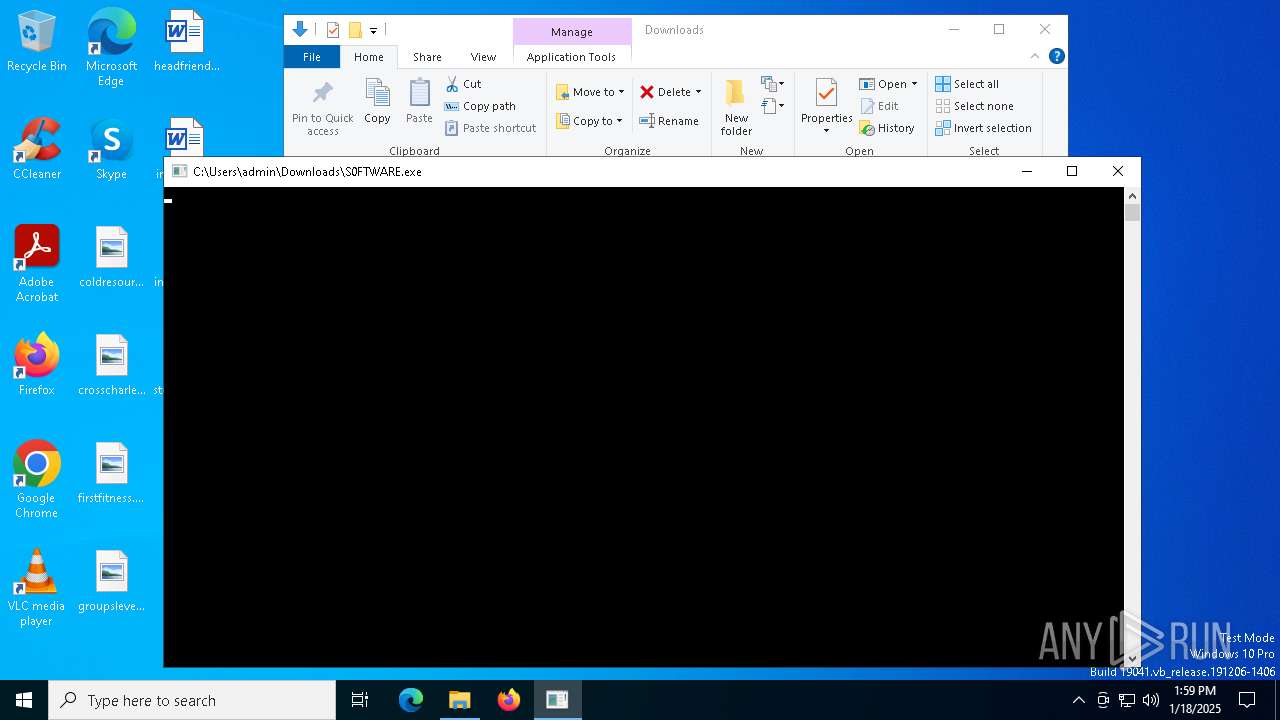
Application launched itself
- S0FTWARE.exe (PID: 7724)
- S0FTWARE.exe (PID: 6320)
- S0FTWARE.exe (PID: 6648)
Reads security settings of Internet Explorer
- S0FTWARE.exe (PID: 7724)
- S0FTWARE.exe (PID: 6320)
- S0FTWARE.exe (PID: 6648)
- S0FTWARE.exe (PID: 7620)
- file2.exe (PID: 6280)
- file1.exe (PID: 6352)
- service.exe (PID: 5556)
Script adds exclusion path to Windows Defender
- S0FTWARE.exe (PID: 7620)
- S0FTWARE.exe (PID: 7008)
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7312)
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
The process bypasses the loading of PowerShell profile settings
- S0FTWARE.exe (PID: 7620)
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7008)
- S0FTWARE.exe (PID: 7312)
Starts POWERSHELL.EXE for commands execution
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7620)
- S0FTWARE.exe (PID: 7008)
- S0FTWARE.exe (PID: 7312)
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
Executable content was dropped or overwritten
- S0FTWARE.exe (PID: 7620)
- file2.exe (PID: 6280)
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
Starts CMD.EXE for commands execution
- file2.exe (PID: 6280)
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
- service.exe (PID: 5556)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- file1.exe (PID: 6352)
Checks Windows Trust Settings
- file1.exe (PID: 6352)
Searches for installed software
- file1.exe (PID: 6352)
Manipulates environment variables
- powershell.exe (PID: 8028)
- powershell.exe (PID: 7928)
Process uninstalls Windows update
- wusa.exe (PID: 1916)
- wusa.exe (PID: 640)
Stops a currently running service
- sc.exe (PID: 8120)
- sc.exe (PID: 4516)
- sc.exe (PID: 4444)
- sc.exe (PID: 6380)
- sc.exe (PID: 6184)
- sc.exe (PID: 5920)
- sc.exe (PID: 520)
- sc.exe (PID: 540)
- sc.exe (PID: 1944)
- sc.exe (PID: 6716)
- sc.exe (PID: 6372)
Windows service management via SC.EXE
- sc.exe (PID: 7172)
- sc.exe (PID: 6712)
Uses powercfg.exe to modify the power settings
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
Creates a new Windows service
- sc.exe (PID: 7416)
Starts SC.EXE for service management
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
Executes as Windows Service
- Updater.exe (PID: 6428)
Script adds exclusion extension to Windows Defender
- Updater.exe (PID: 6428)
- file3.exe (PID: 7000)
Drops a system driver (possible attempt to evade defenses)
- Updater.exe (PID: 6428)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2192)
Connects to unusual port
- explorer.exe (PID: 8044)
The process executes via Task Scheduler
- service.exe (PID: 5556)
INFO
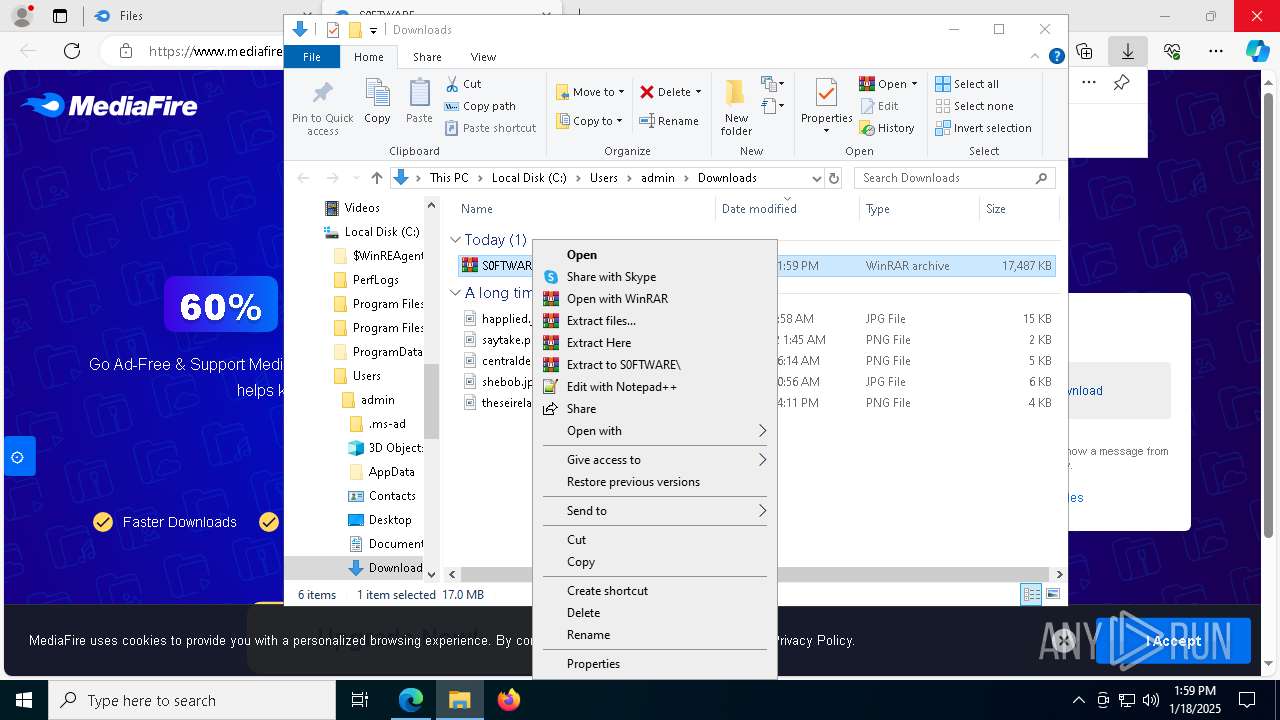
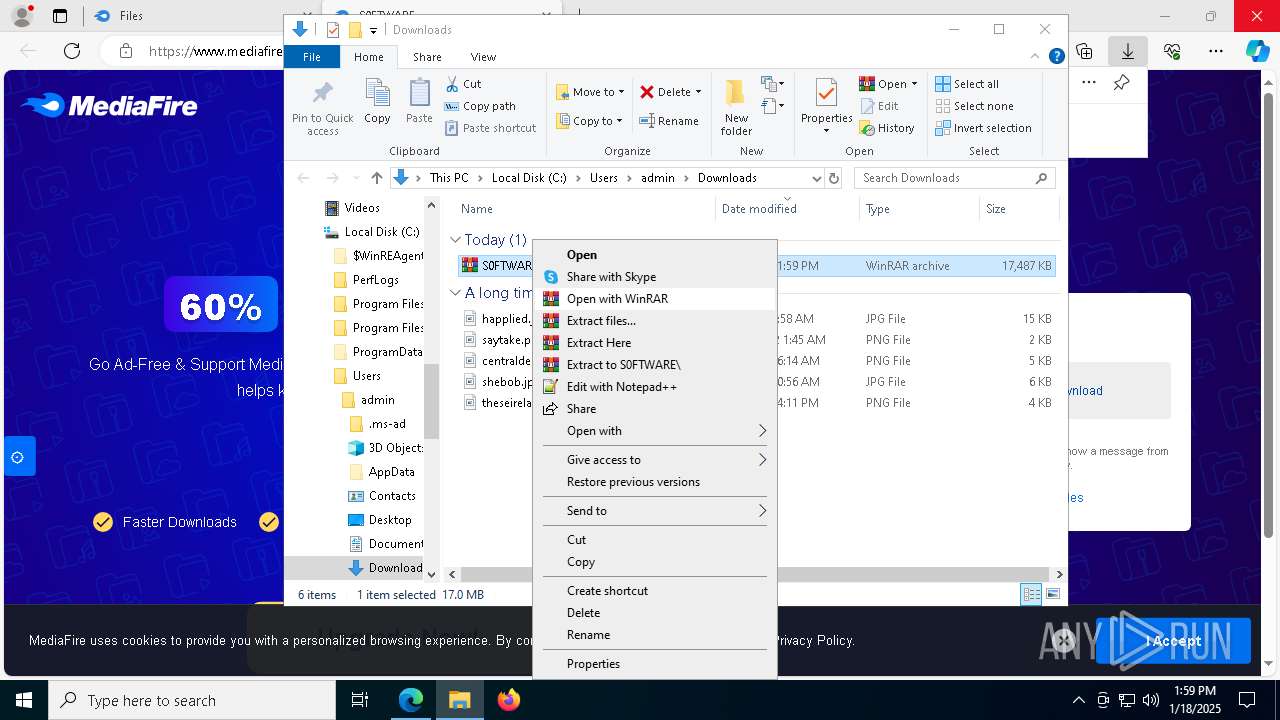
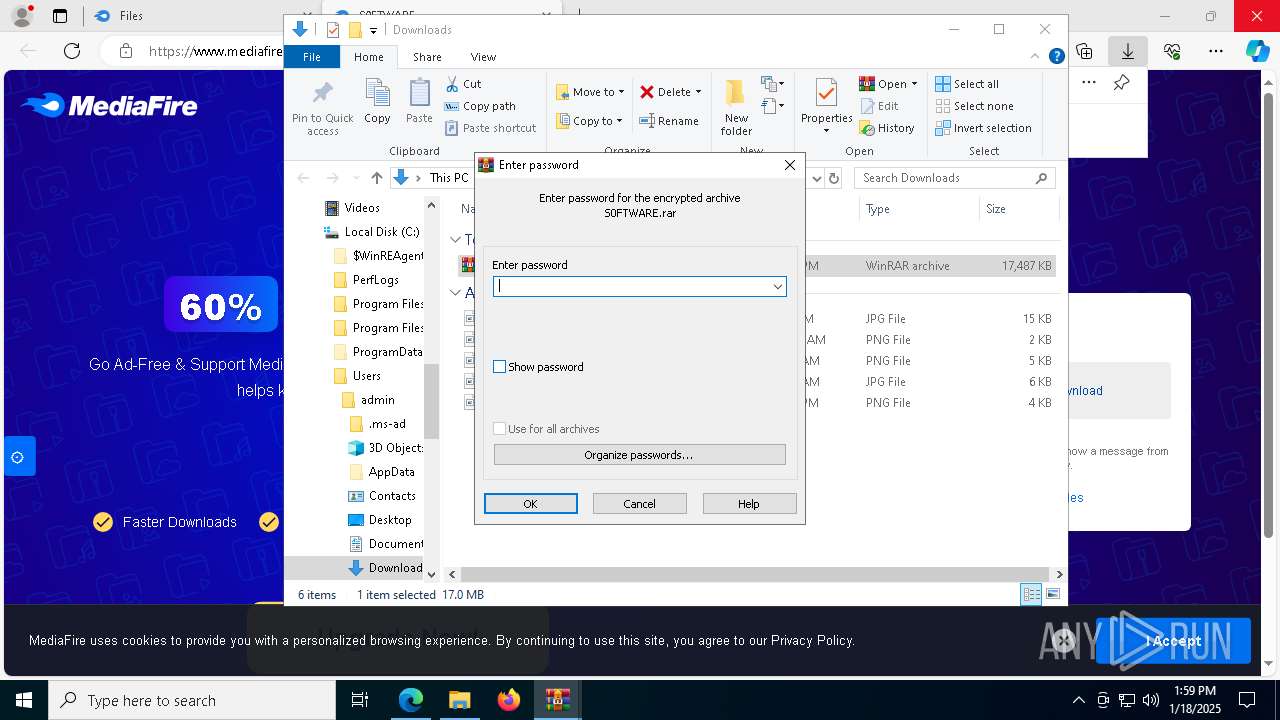
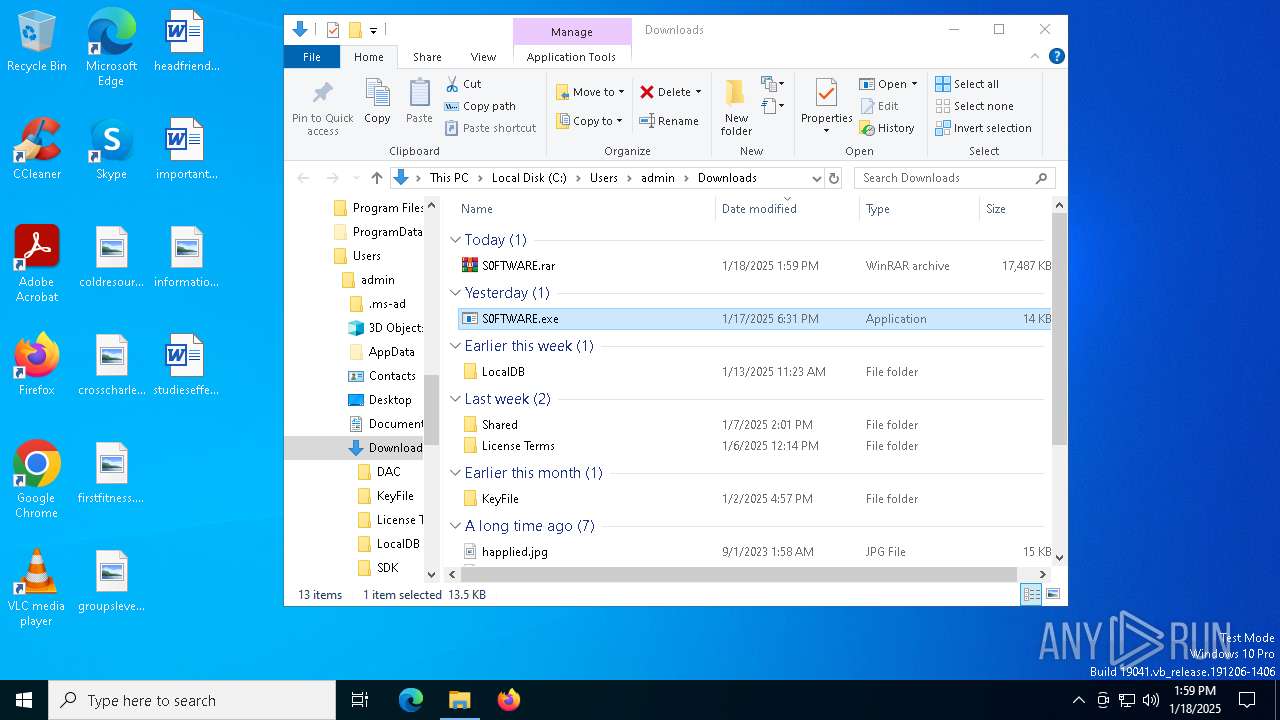
The process uses the downloaded file
- msedge.exe (PID: 8144)
- S0FTWARE.exe (PID: 7724)
- S0FTWARE.exe (PID: 6320)
- S0FTWARE.exe (PID: 6648)
- WinRAR.exe (PID: 7440)
- powershell.exe (PID: 7660)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 7376)
- file2.exe (PID: 6280)
- S0FTWARE.exe (PID: 7620)
- powershell.exe (PID: 7928)
- service.exe (PID: 5556)
The sample compiled with german language support
- WinRAR.exe (PID: 7440)
The sample compiled with spanish language support
- WinRAR.exe (PID: 7440)
Checks supported languages
- identity_helper.exe (PID: 8100)
- identity_helper.exe (PID: 6352)
- S0FTWARE.exe (PID: 7724)
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7620)
- S0FTWARE.exe (PID: 6320)
- S0FTWARE.exe (PID: 7008)
- S0FTWARE.exe (PID: 6648)
- S0FTWARE.exe (PID: 7312)
- file1.exe (PID: 6352)
- file2.exe (PID: 6280)
- file3.exe (PID: 7000)
- Updater.exe (PID: 6428)
- identity_helper.exe (PID: 7596)
- service.exe (PID: 5556)
Reads Environment values
- identity_helper.exe (PID: 8100)
- identity_helper.exe (PID: 6352)
- file1.exe (PID: 6352)
- identity_helper.exe (PID: 7596)
The sample compiled with french language support
- WinRAR.exe (PID: 7440)
The sample compiled with korean language support
- WinRAR.exe (PID: 7440)
The sample compiled with chinese language support
- WinRAR.exe (PID: 7440)
The sample compiled with russian language support
- WinRAR.exe (PID: 7440)
The sample compiled with japanese language support
- WinRAR.exe (PID: 7440)
- Updater.exe (PID: 6428)
The sample compiled with portuguese language support
- WinRAR.exe (PID: 7440)
Application launched itself
- msedge.exe (PID: 6432)
- msedge.exe (PID: 936)
- msedge.exe (PID: 3992)
- msedge.exe (PID: 4932)
- msedge.exe (PID: 7852)
- chrome.exe (PID: 6836)
Reads the computer name
- identity_helper.exe (PID: 8100)
- S0FTWARE.exe (PID: 7620)
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7724)
- identity_helper.exe (PID: 6352)
- S0FTWARE.exe (PID: 6320)
- S0FTWARE.exe (PID: 7008)
- S0FTWARE.exe (PID: 6648)
- S0FTWARE.exe (PID: 7312)
- file1.exe (PID: 6352)
- file2.exe (PID: 6280)
- identity_helper.exe (PID: 7596)
- service.exe (PID: 5556)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7440)
- msedge.exe (PID: 5912)
The sample compiled with Italian language support
- WinRAR.exe (PID: 7440)
The sample compiled with english language support
- WinRAR.exe (PID: 7440)
- S0FTWARE.exe (PID: 7620)
- file3.exe (PID: 7000)
- msedge.exe (PID: 5912)
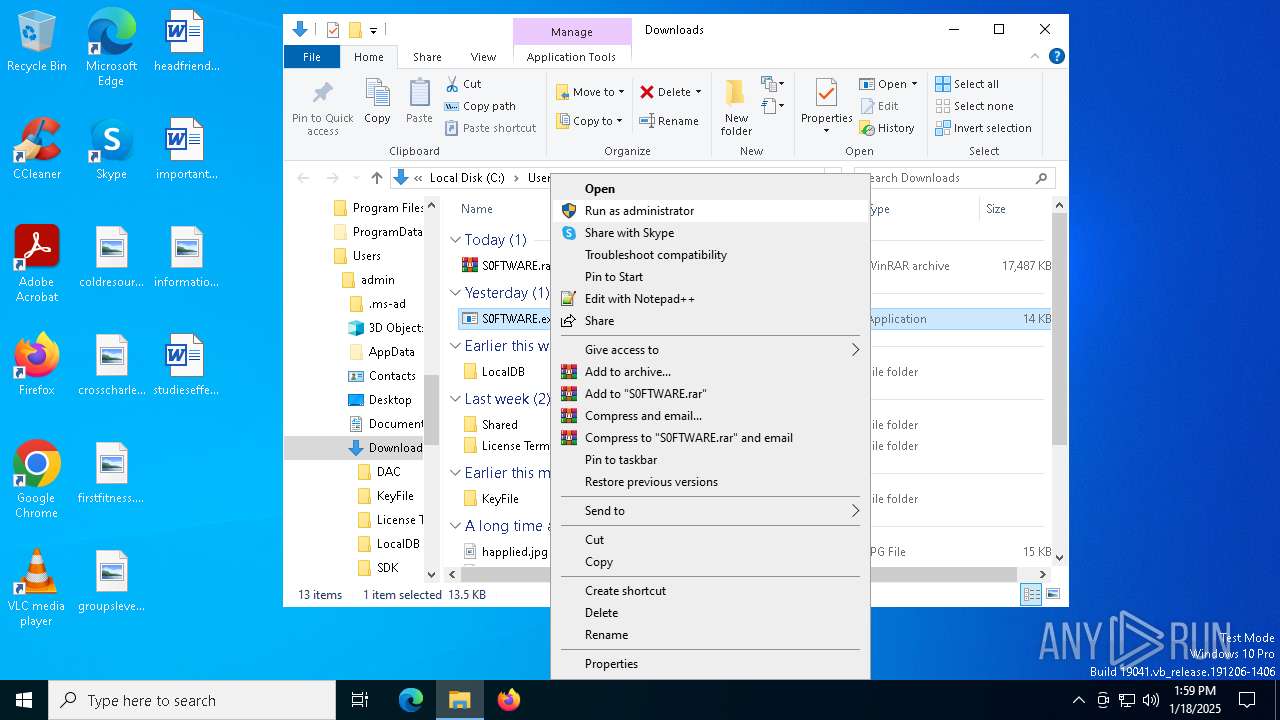
Manual execution by a user
- S0FTWARE.exe (PID: 7620)
- S0FTWARE.exe (PID: 7724)
- S0FTWARE.exe (PID: 6320)
- S0FTWARE.exe (PID: 6648)
- WinRAR.exe (PID: 7440)
- msedge.exe (PID: 3508)
- msedge.exe (PID: 4932)
Process checks computer location settings
- S0FTWARE.exe (PID: 7724)
- S0FTWARE.exe (PID: 6320)
- S0FTWARE.exe (PID: 6648)
- file2.exe (PID: 6280)
- S0FTWARE.exe (PID: 7620)
- service.exe (PID: 5556)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7660)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 8028)
- powershell.exe (PID: 7928)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7660)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 1412)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 8028)
- powershell.exe (PID: 7928)
Reads the machine GUID from the registry
- S0FTWARE.exe (PID: 7620)
- file1.exe (PID: 6352)
- S0FTWARE.exe (PID: 7428)
- S0FTWARE.exe (PID: 7312)
- S0FTWARE.exe (PID: 7008)
Disables trace logs
- S0FTWARE.exe (PID: 7620)
Checks proxy server information
- S0FTWARE.exe (PID: 7620)
- file1.exe (PID: 6352)
Reads the software policy settings
- S0FTWARE.exe (PID: 7620)
- file1.exe (PID: 6352)
Creates files in the program directory
- file1.exe (PID: 6352)
- file3.exe (PID: 7000)
Attempting to use instant messaging service
- file1.exe (PID: 6352)
Creates files or folders in the user directory
- file2.exe (PID: 6280)
- file1.exe (PID: 6352)
Reads product name
- file1.exe (PID: 6352)
Reads CPU info
- file1.exe (PID: 6352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
350
Monitored processes
213
Malicious processes
7
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3864 --field-trial-handle=1448,i,12043419518351926939,13393528093342559782,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2268 --field-trial-handle=2272,i,1788573974719074320,1919874961955735597,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 520 | C:\WINDOWS\system32\sc.exe stop UsoSvc | C:\Windows\System32\sc.exe | — | Updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1061 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | C:\WINDOWS\system32\sc.exe stop WaaSMedicSvc | C:\Windows\System32\sc.exe | — | Updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2448 --field-trial-handle=2476,i,15491177066518365120,6320498123243809892,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 640 | wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\wusa.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update Standalone Installer Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6900 --field-trial-handle=2476,i,15491177066518365120,6320498123243809892,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --remote-debugging-port=9223 --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3932 --field-trial-handle=2476,i,15491177066518365120,6320498123243809892,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1412 | "powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command "Add-MpPreference -ExclusionPath 'C:\Fasyer', 'C:\Users', 'C:\ProgramData'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | S0FTWARE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
58 614
Read events
58 521
Write events
93
Delete events
0
Modification events
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BE19A6B6918A2F00 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 68D6BAB6918A2F00 | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328452 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2D0A6F60-03EB-47F7-9CBB-1DF3E156BCFB} | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328452 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {916630CF-C60B-40B0-AEF4-C6D974FAD0B9} | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328452 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {77BBED30-CCC2-4811-855D-08BA006877E3} | |||
| (PID) Process: | (6432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328452 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {314A0025-14EA-4FCC-96DA-AE02F5CAC899} | |||
Executable files
210
Suspicious files
1 119
Text files
309
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13549b.TMP | — | |
MD5:— | SHA256:— | |||
| 6432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
309
DNS requests
295
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6092 | svchost.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6092 | svchost.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 304 | 23.209.209.135:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
7572 | msedge.exe | GET | 304 | 23.209.209.135:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
7572 | msedge.exe | GET | 200 | 2.19.198.57:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1737537131&P2=404&P3=2&P4=ROjLn8xmKWxRTETvMjFy9TMShytq%2bVn54w4gAVYVD3fMM4bcFJJnh75y2078cLxie32Xi9wQHH7c1AN4u4qFqA%3d%3d | unknown | — | — | whitelisted |
7572 | msedge.exe | GET | 200 | 2.19.198.57:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1737540727&P2=404&P3=2&P4=HdfgZDyMP8cgrwSvc13mjG1%2f%2bLIJyF4ApE7G0PLEf87lUKDBSnsRrHnCN2LVRUNVDwDtmvkj61Pbp%2f%2bRjfnKIg%3d%3d | unknown | — | — | whitelisted |
7572 | msedge.exe | GET | 200 | 2.19.198.57:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1737540728&P2=404&P3=2&P4=EYuWLWlO4iPKBL865GvfeJedy4rZ1VPMzmz1Qw8EdiNMDV77Scb7xYL%2bTFCw0bvm87Br9my19XD7g%2bGsRmY80g%3d%3d | unknown | — | — | whitelisted |
7572 | msedge.exe | GET | 200 | 2.19.198.57:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1737537128&P2=404&P3=2&P4=l6FZfIdb%2f2t7yf7gJ7ZVRQZ7bcCIR4JTs%2fhVKCfRQceX%2fCgMPCpsSbxKvsurUNoBX49MzwltYvOQ%2b17b6TMPAg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6092 | svchost.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6092 | svchost.exe | 23.209.214.100:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.19.122.12:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6788 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6432 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6788 | msedge.exe | 104.17.150.117:443 | www.mediafire.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.mediafire.com |
| shared |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6788 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6788 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6788 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6788 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6788 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6788 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6788 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
1 ETPRO signatures available at the full report