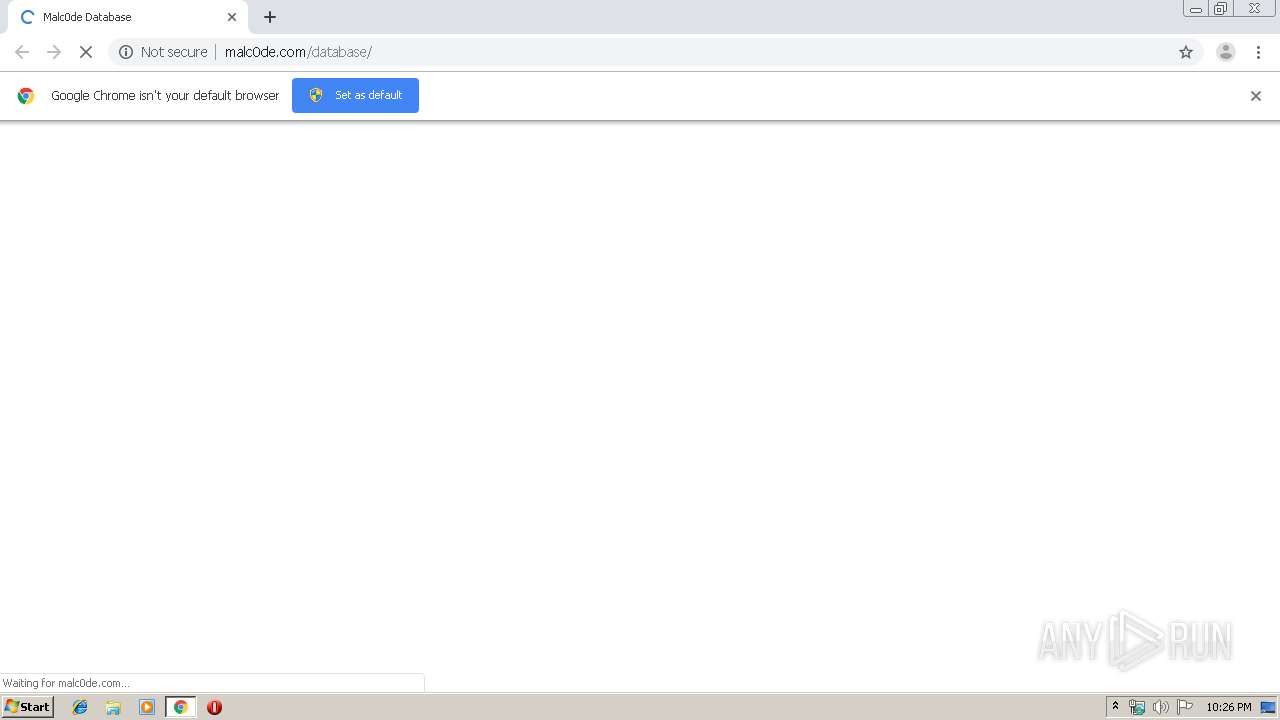
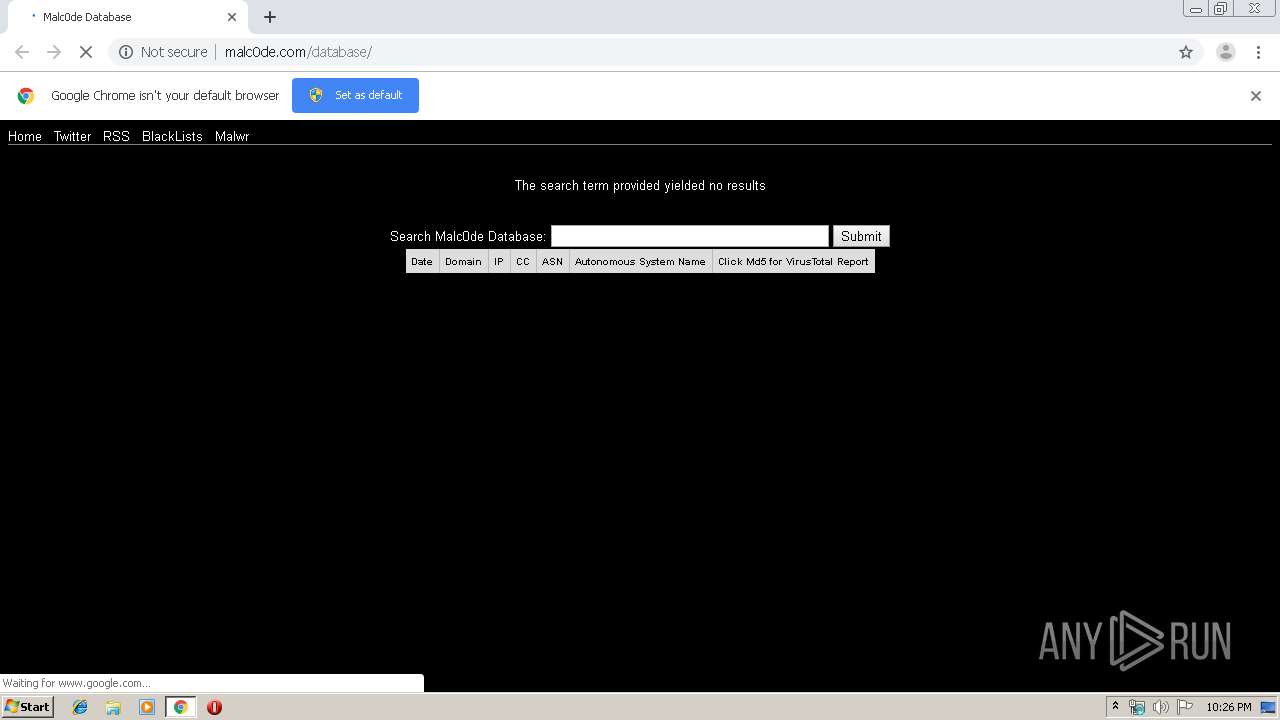
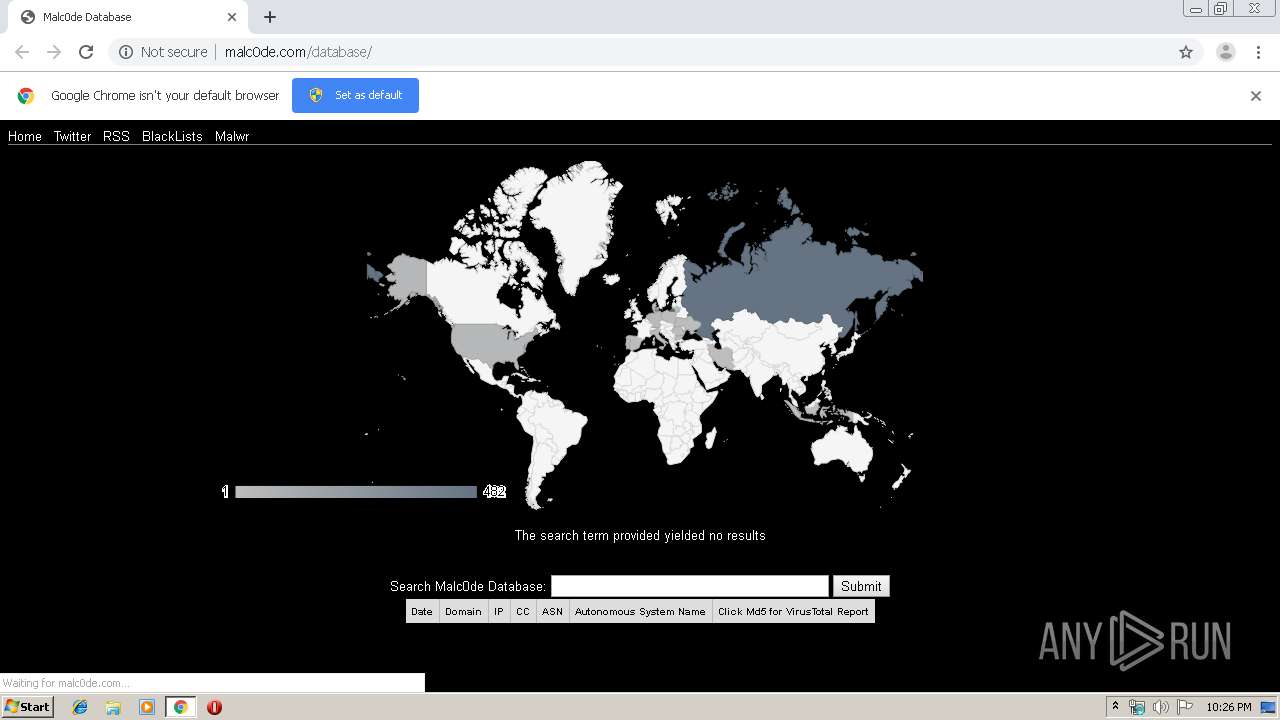
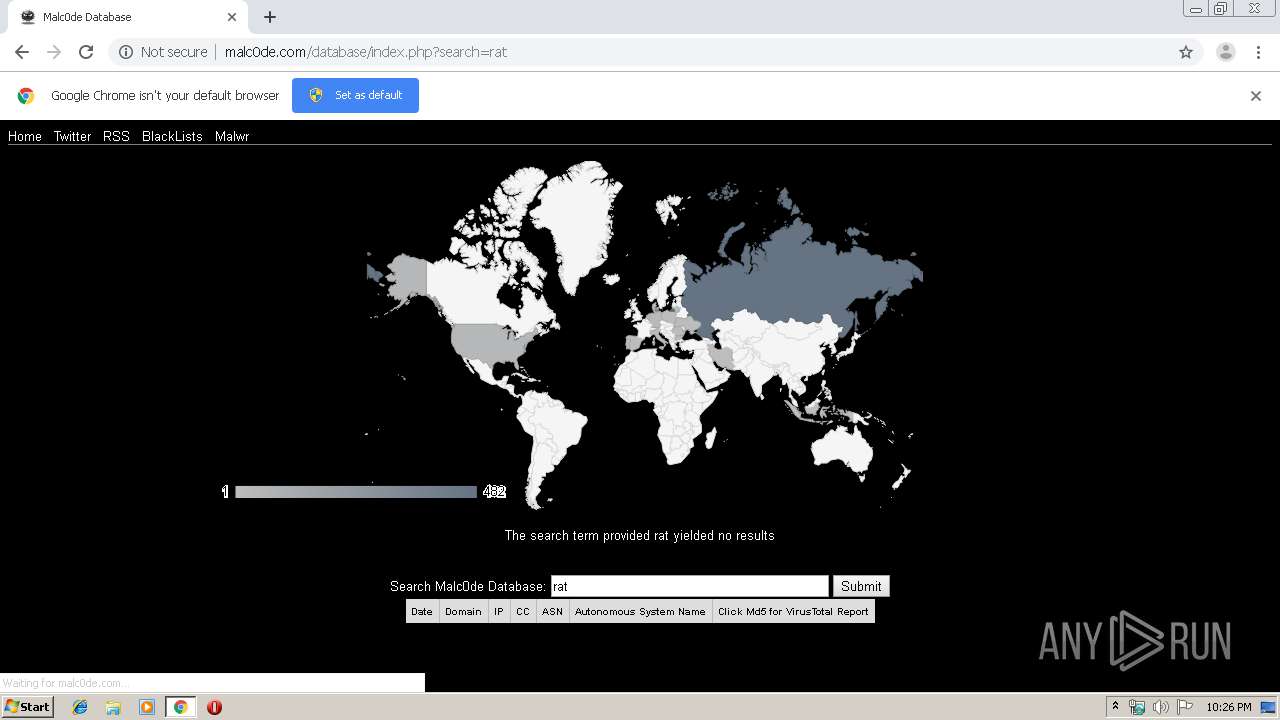
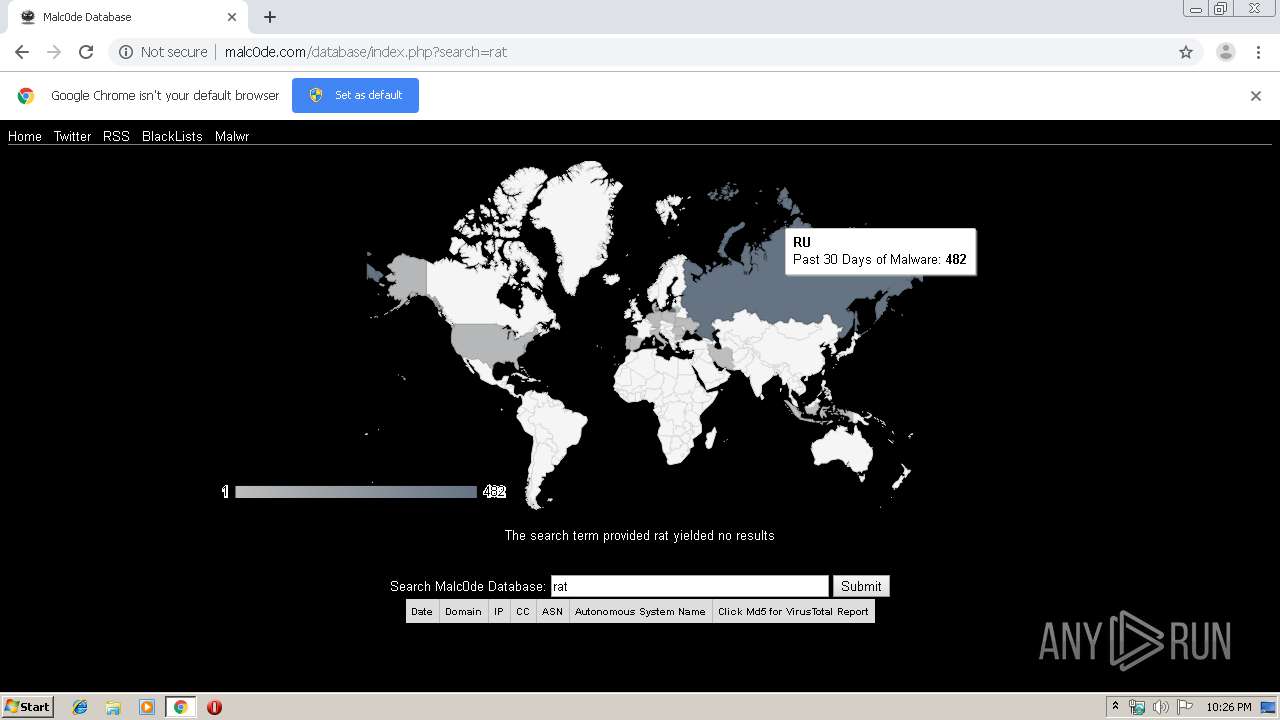
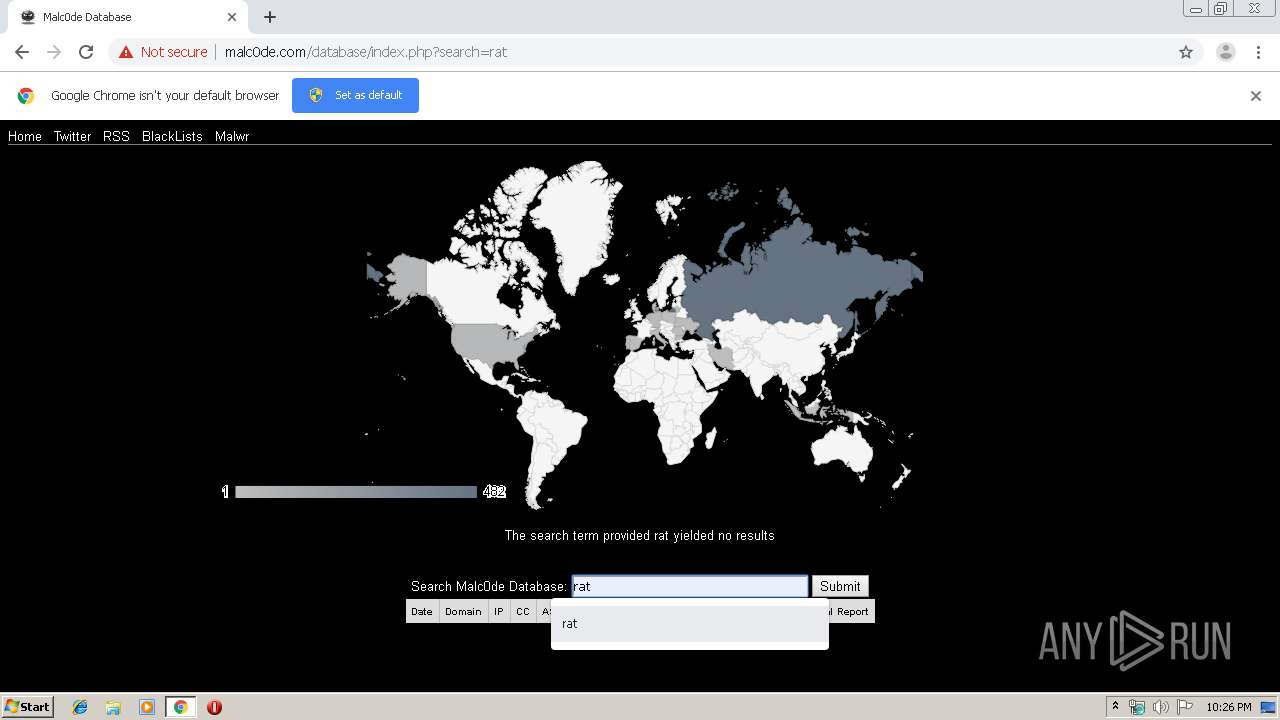
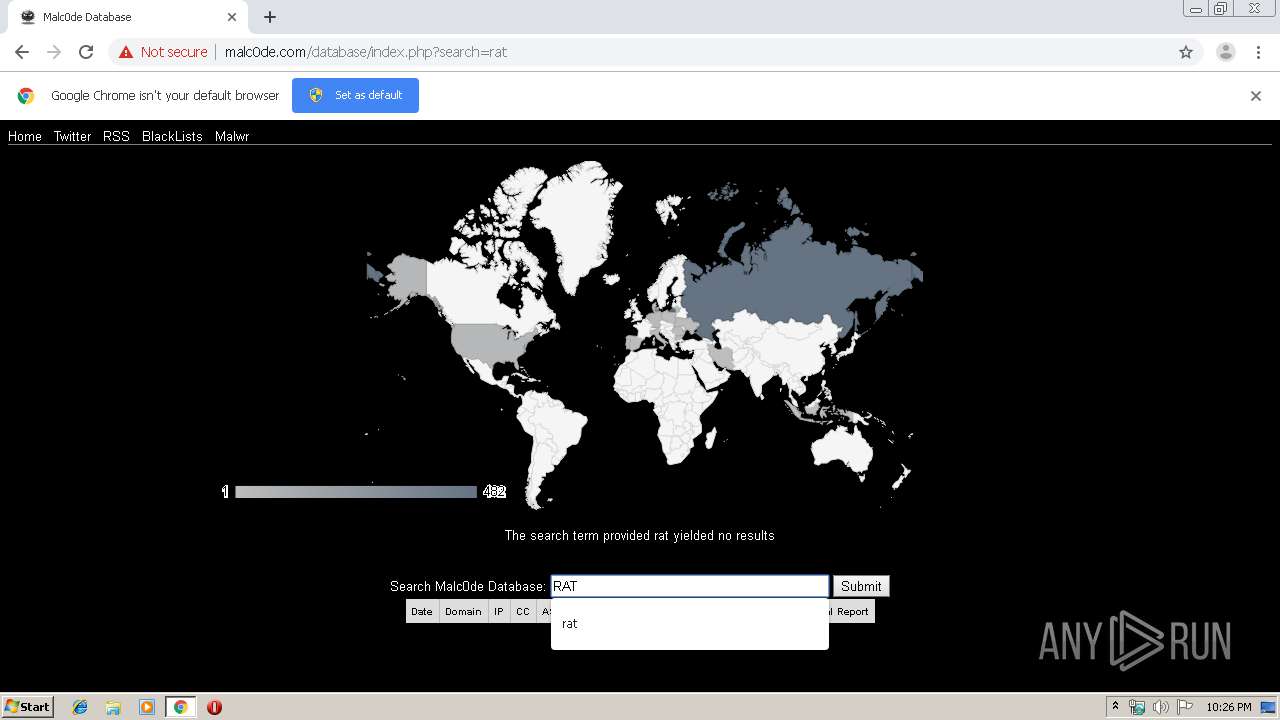
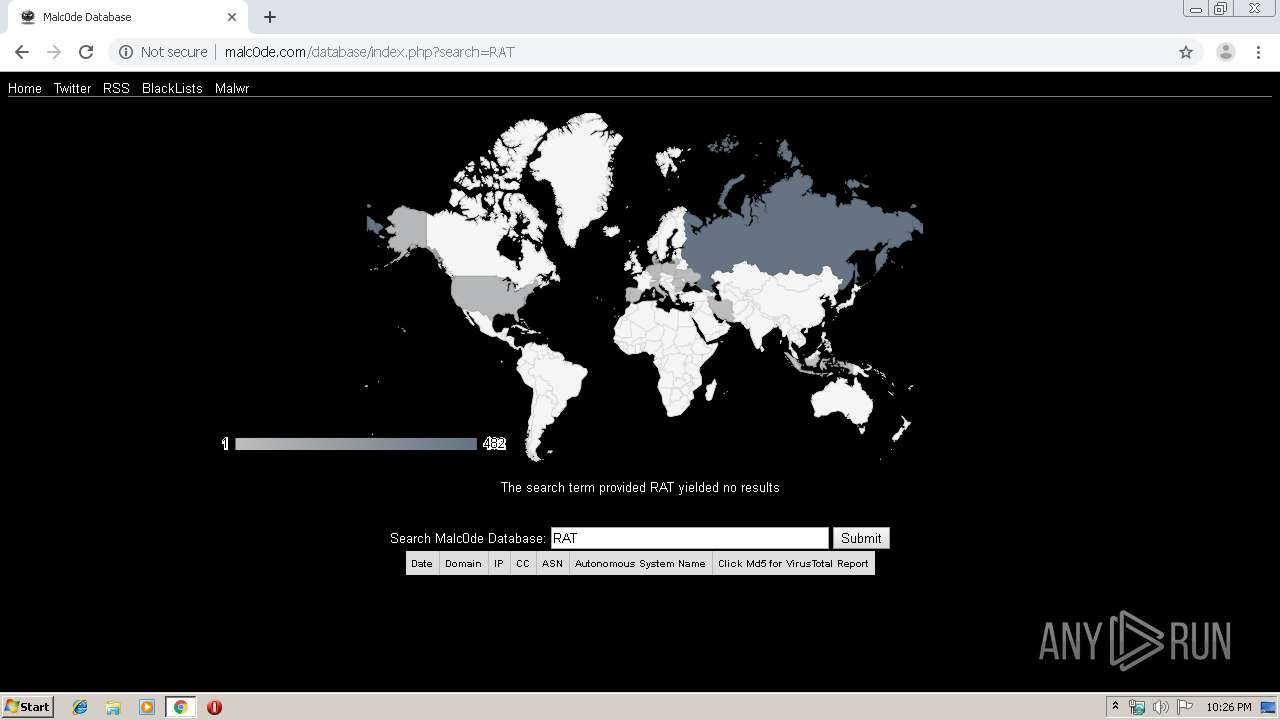
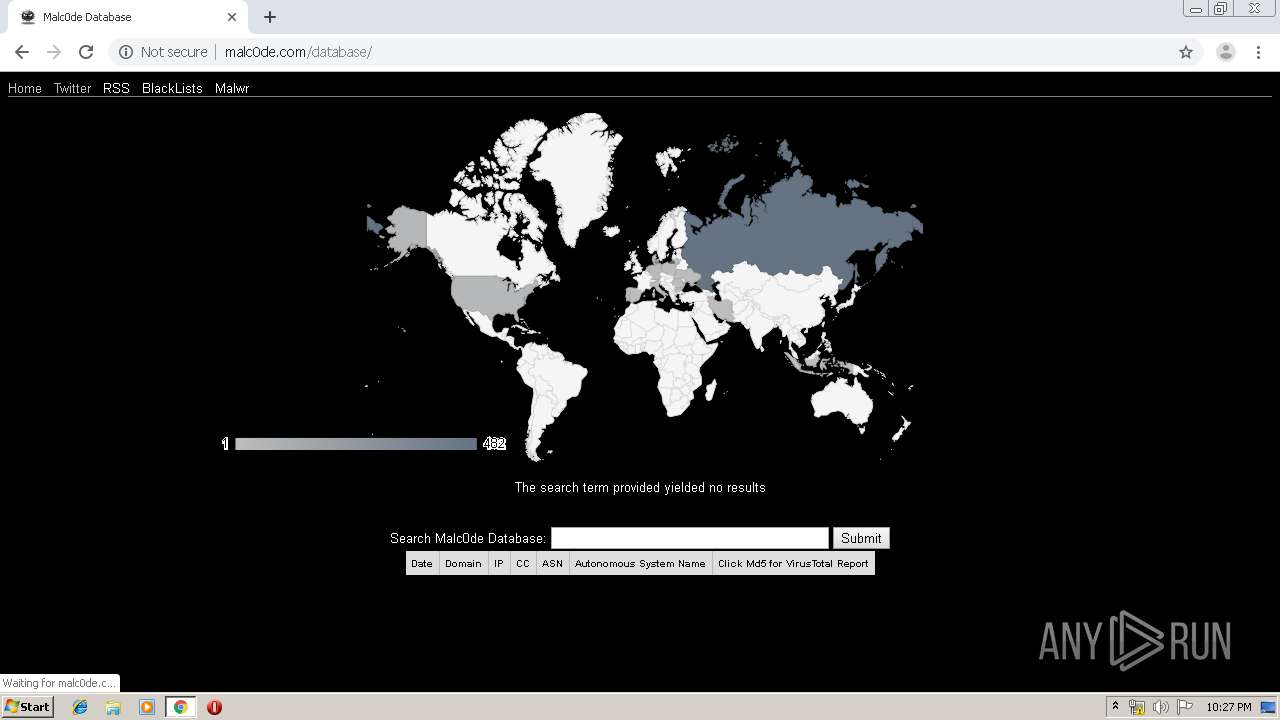
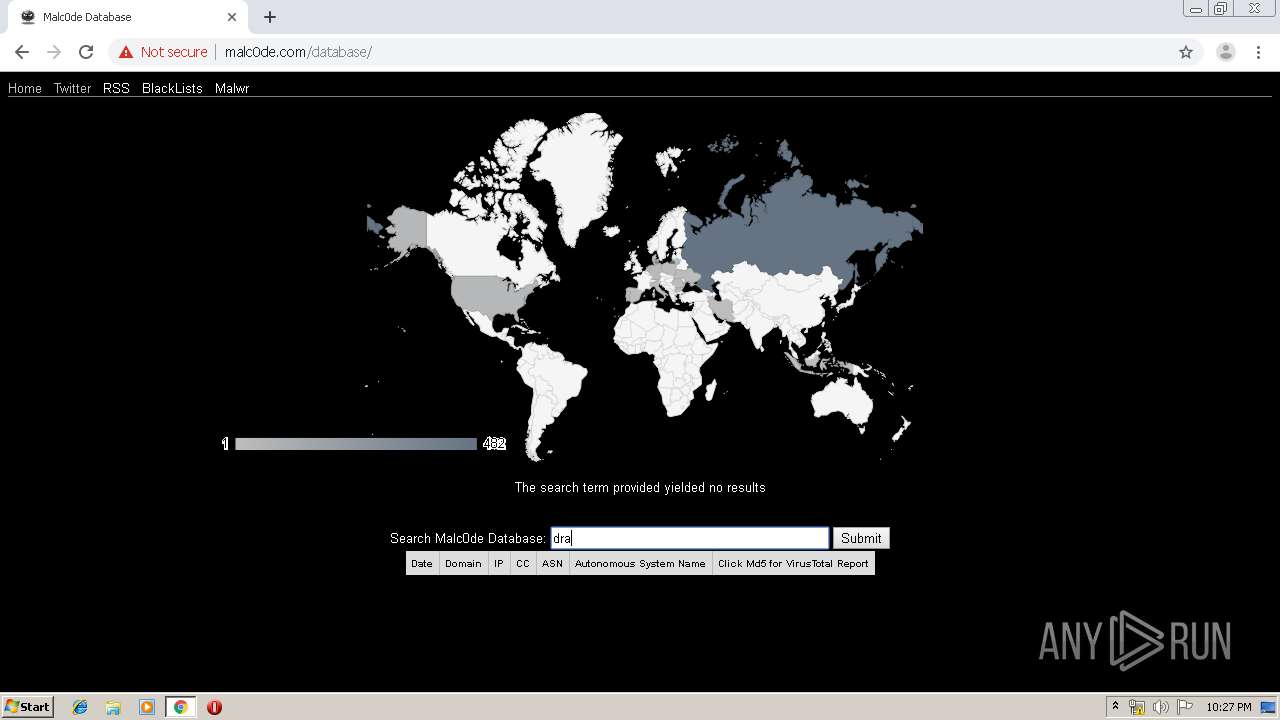
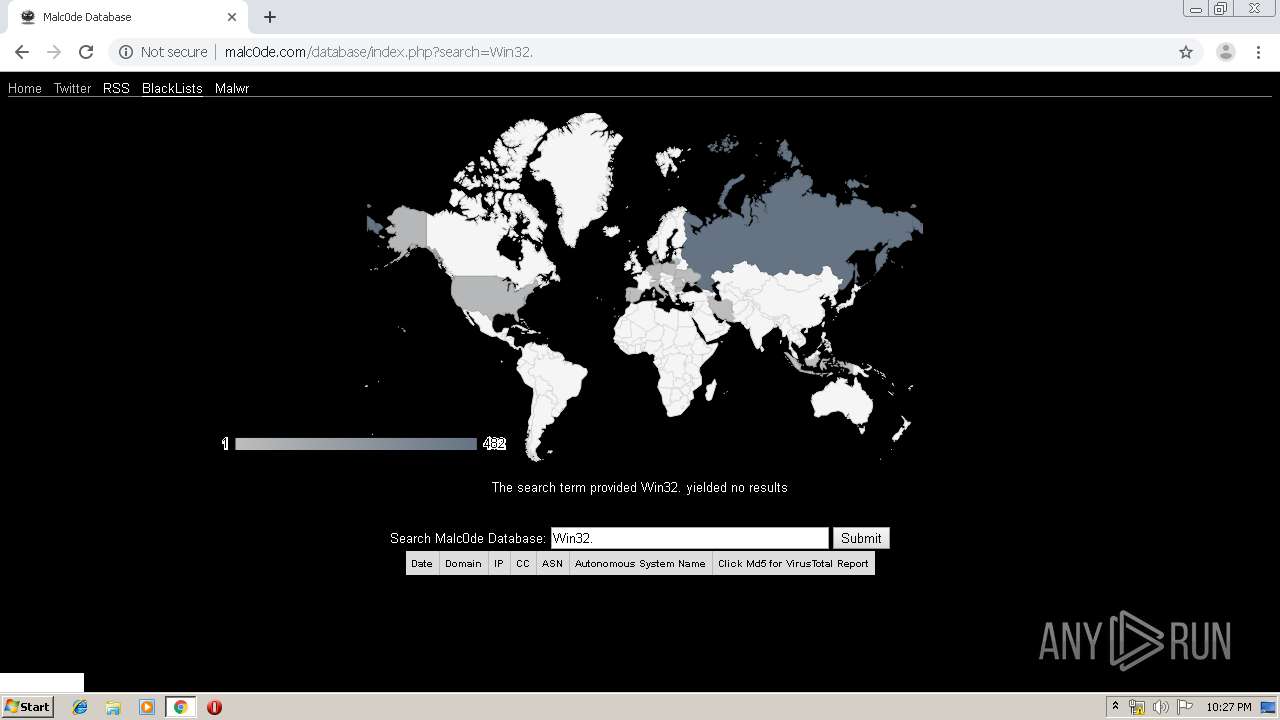
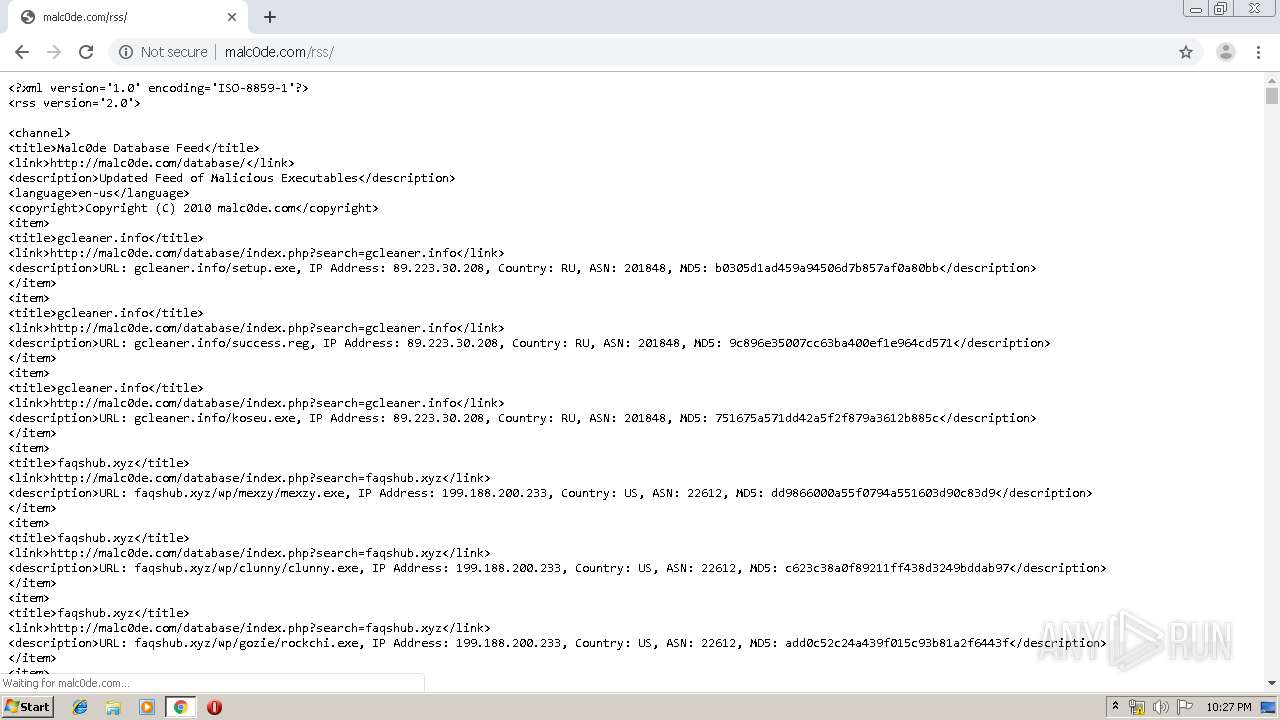
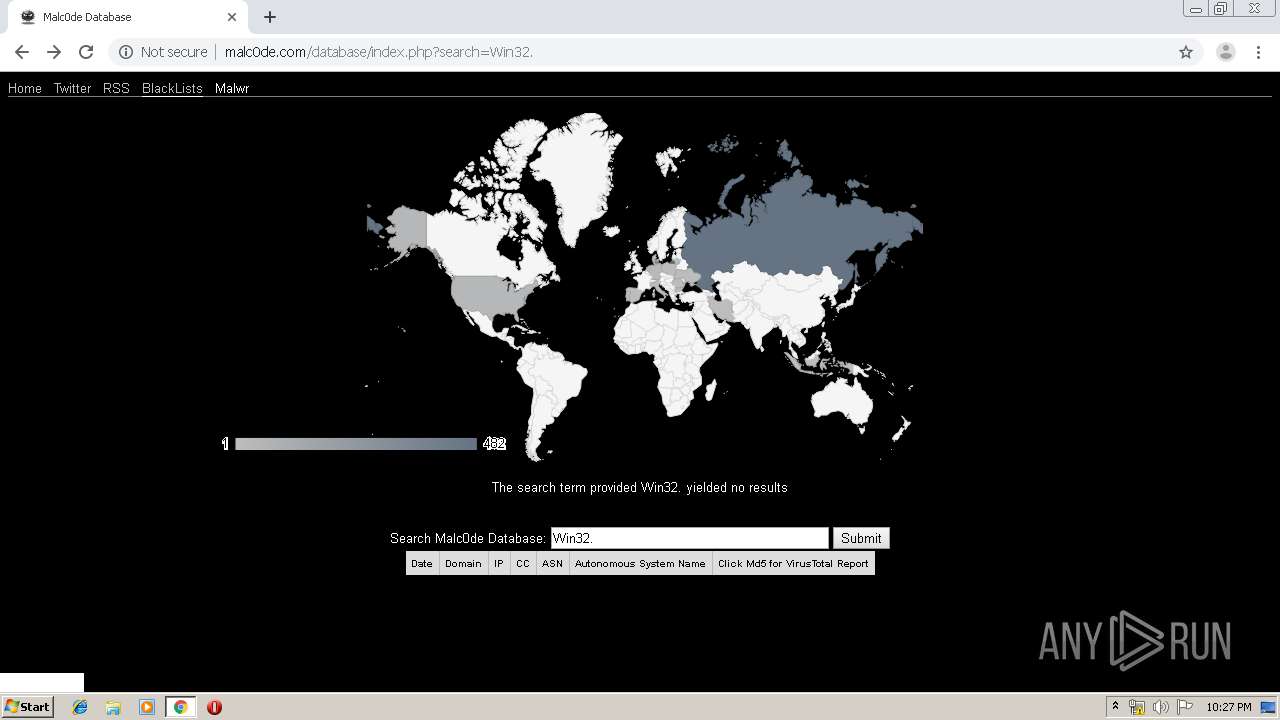
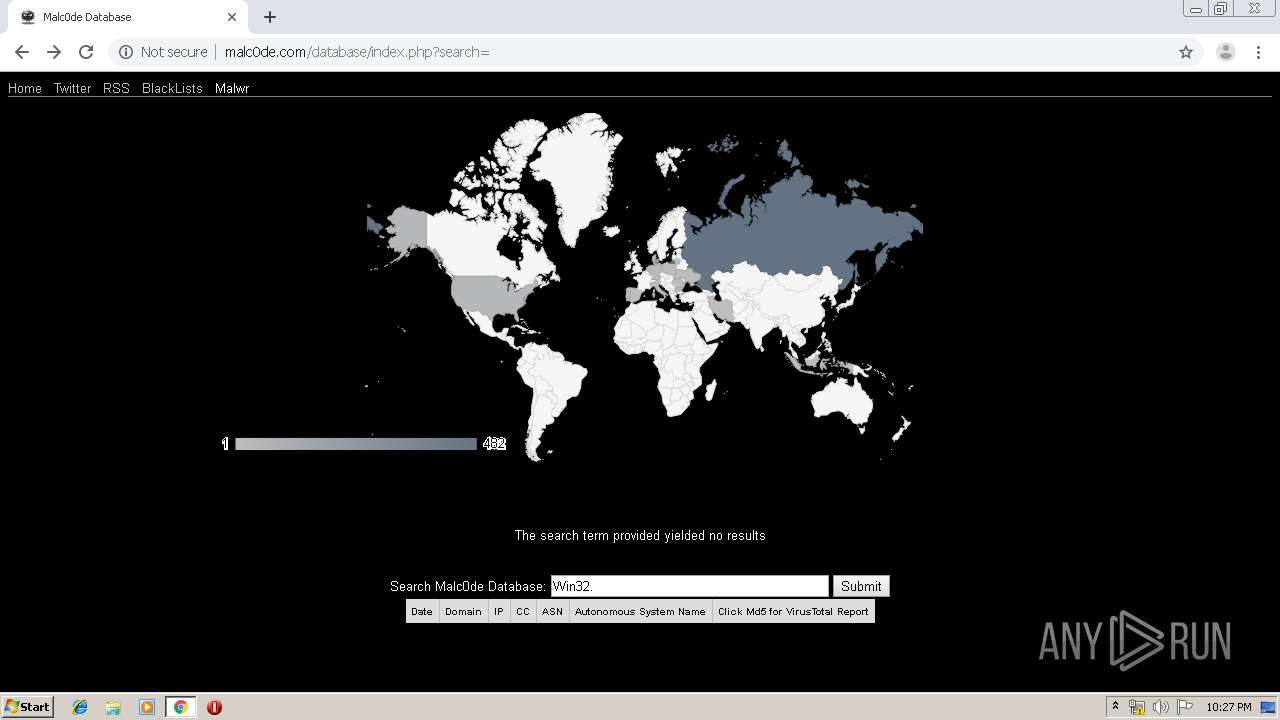
| URL: | http://malc0de.com/database/ |
| Full analysis: | https://app.any.run/tasks/18a4cdf2-8d5a-42af-86a1-b9b64bb3255d |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | August 25, 2019, 21:25:56 |
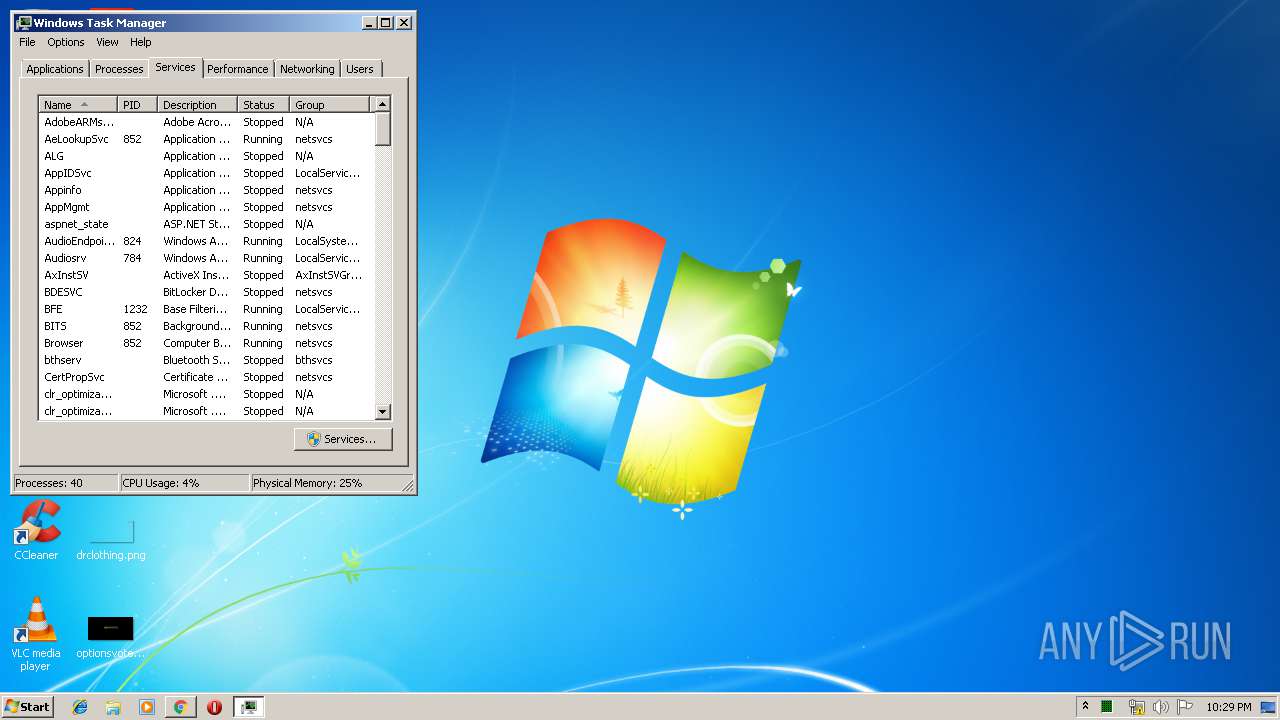
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7B0436732B86337CD7DD3B64A8E2FDA6 |
| SHA1: | C9C392C300AA705FD5B7EB9044DDD04BE68A8977 |
| SHA256: | EED7F59F1CC35CFF9EA319297B065E5122A1B90859596E41D664B60DA8D2A20C |
| SSDEEP: | 3:N1KTJsRBEREHEqn:CdsERuEq |
MALICIOUS
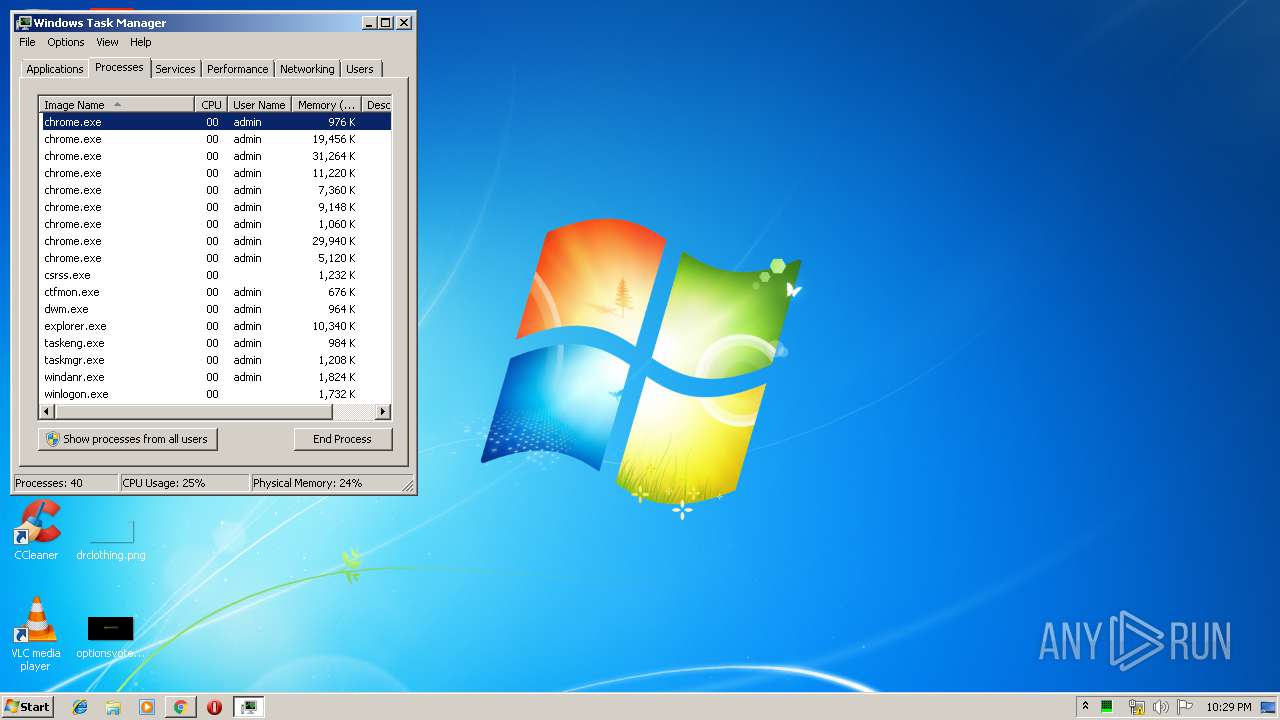
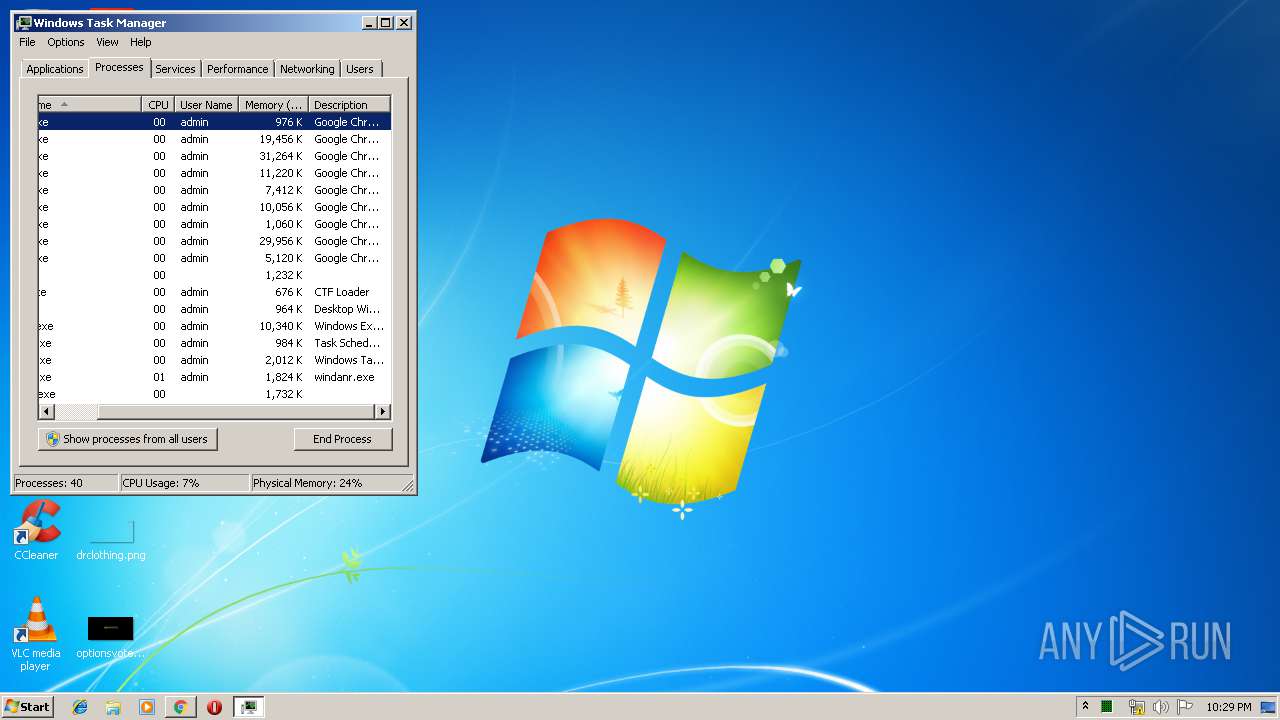
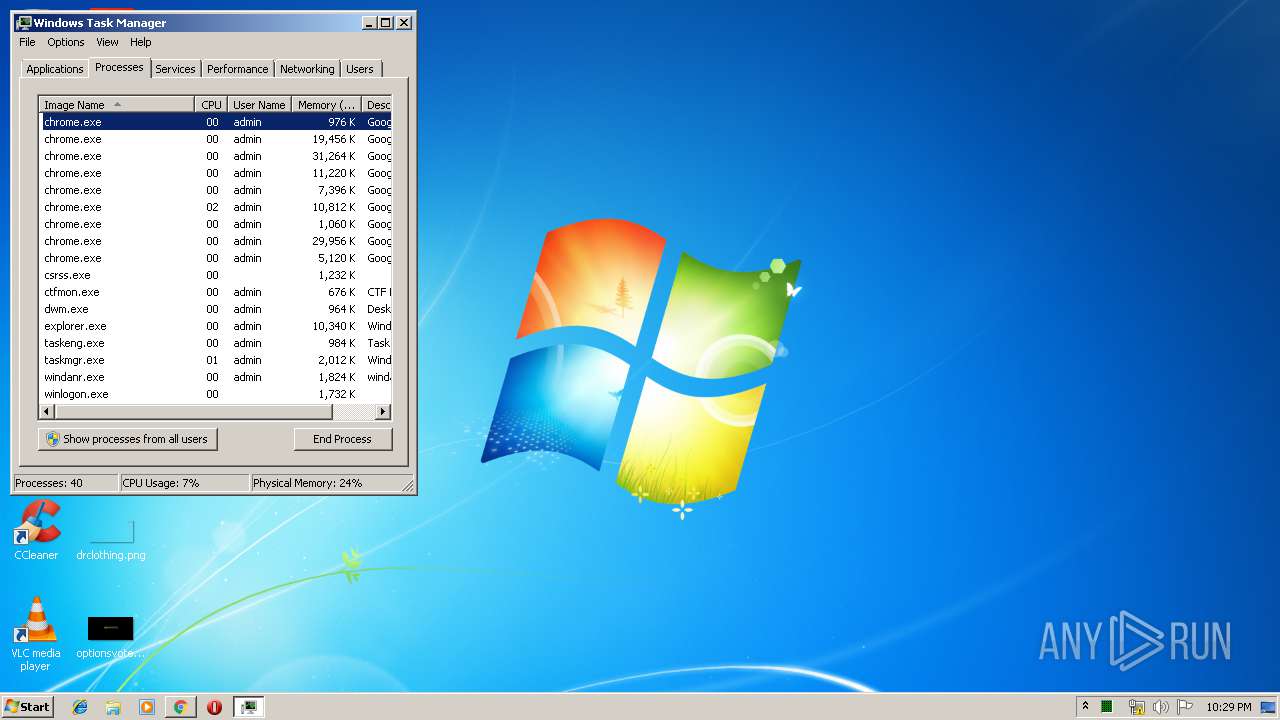
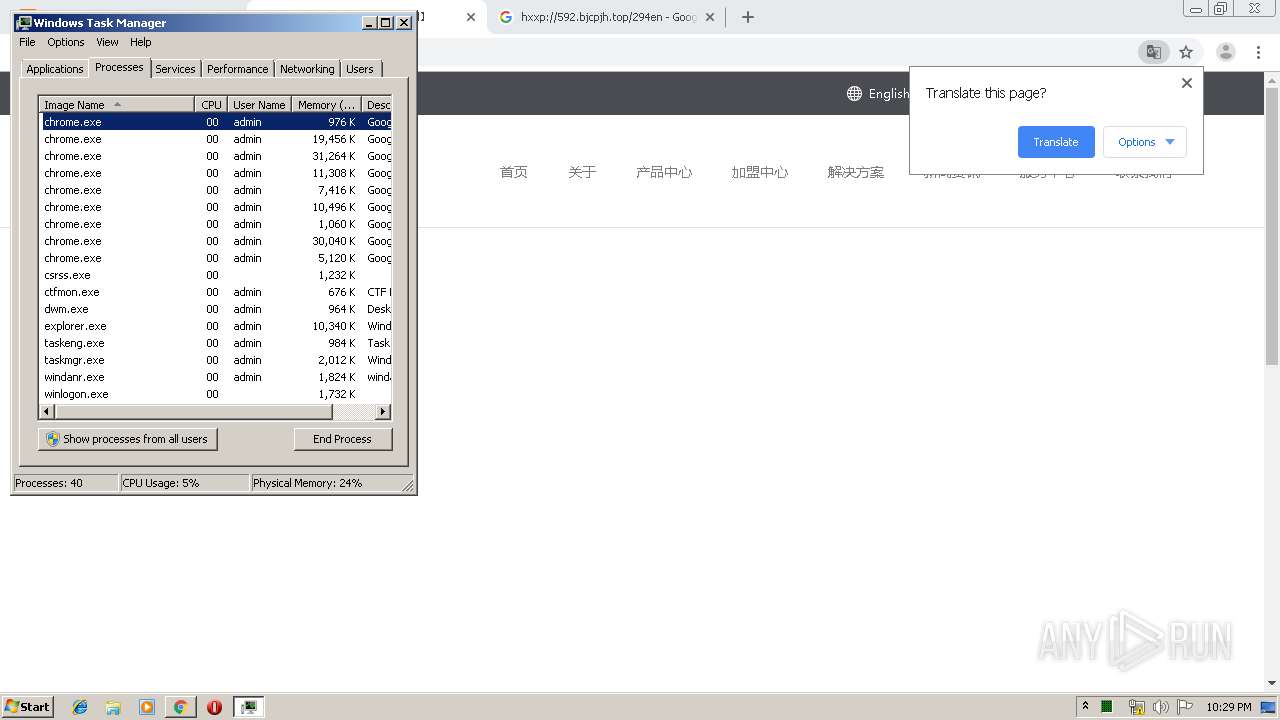
RAMNIT was detected
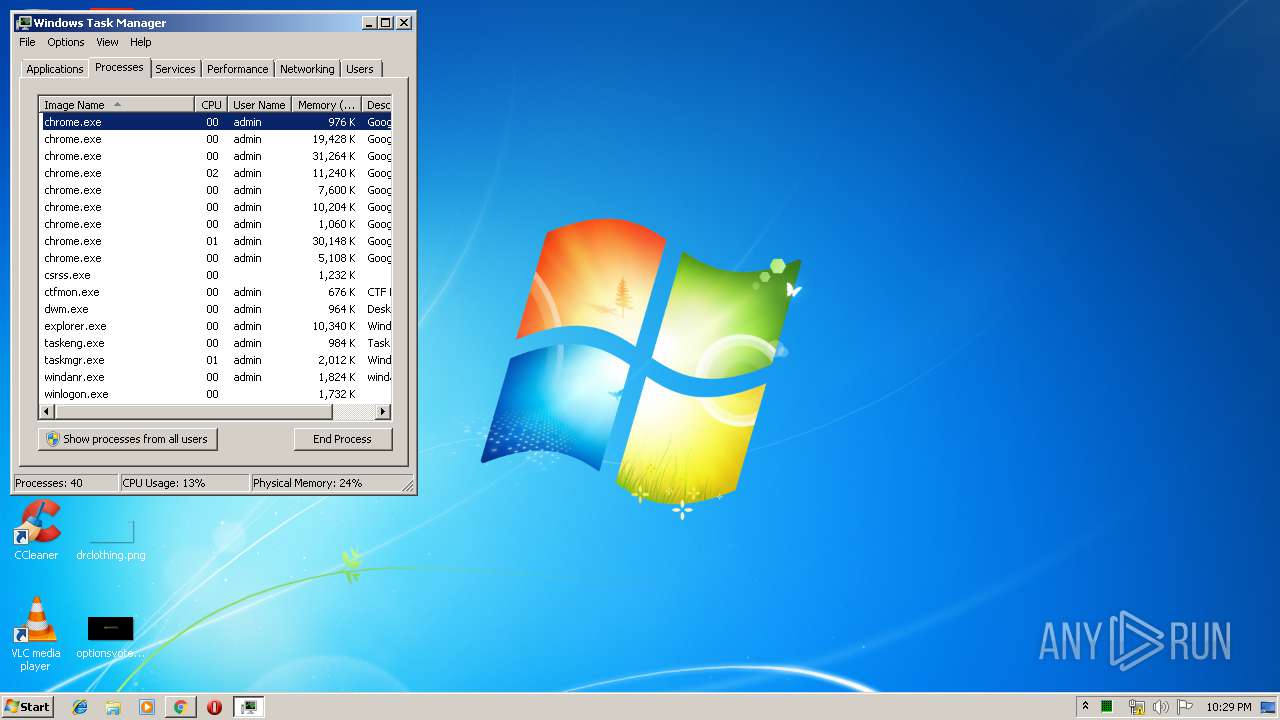
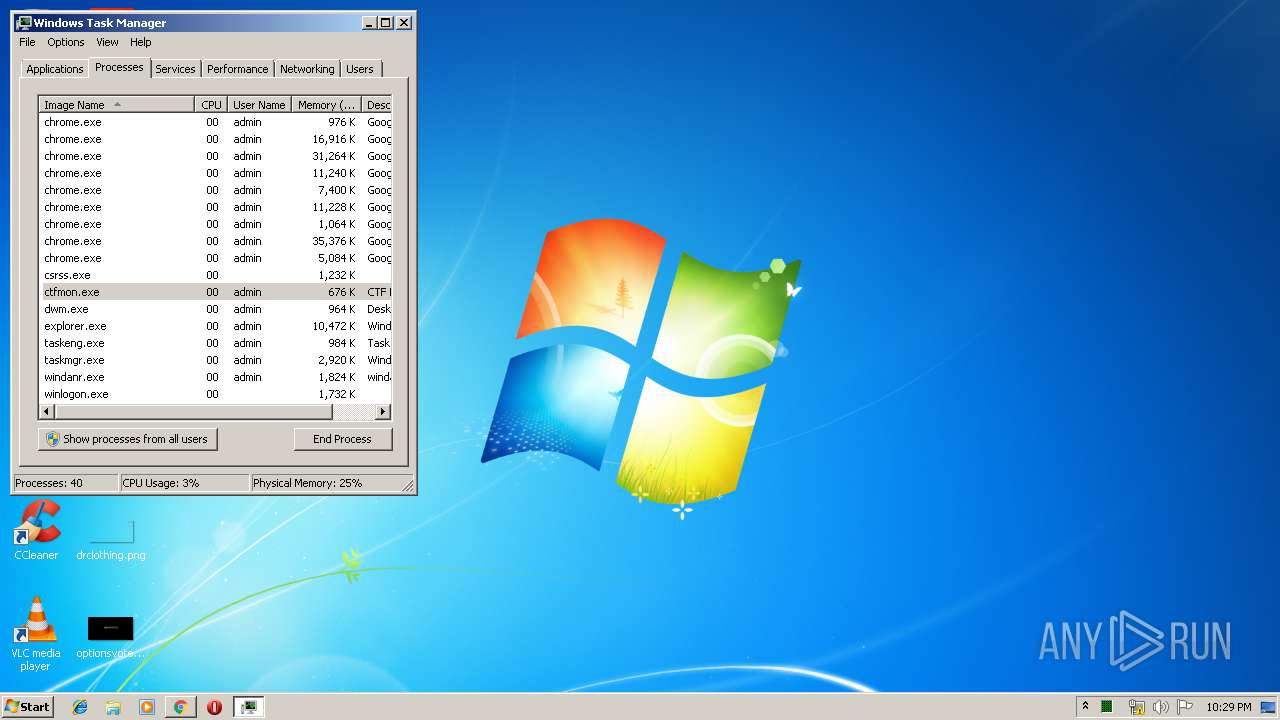
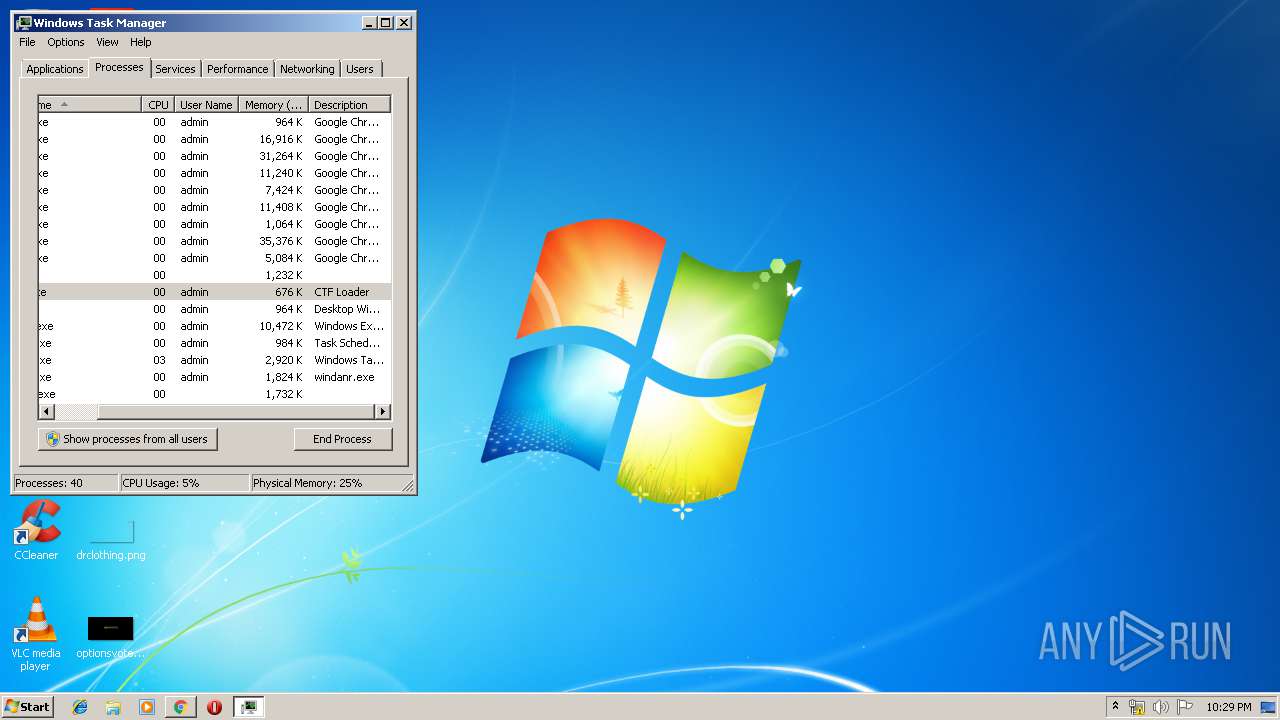
- chrome.exe (PID: 2952)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3544)
INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2952)
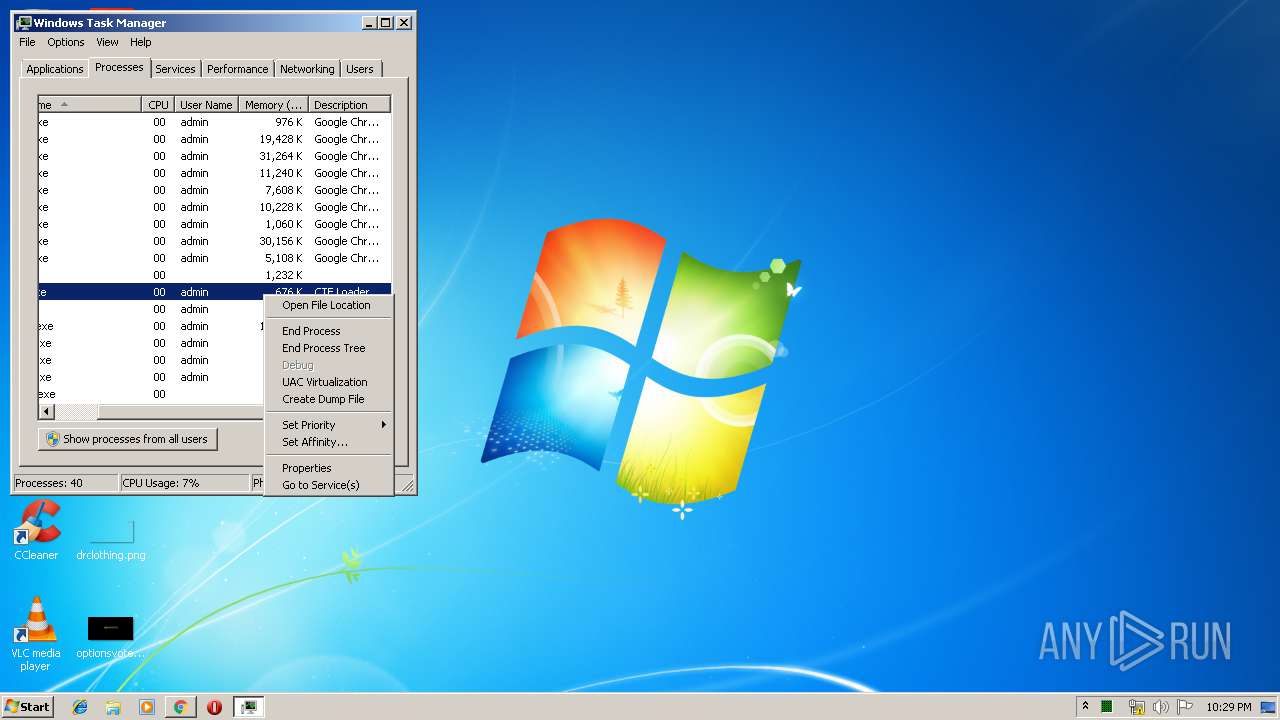
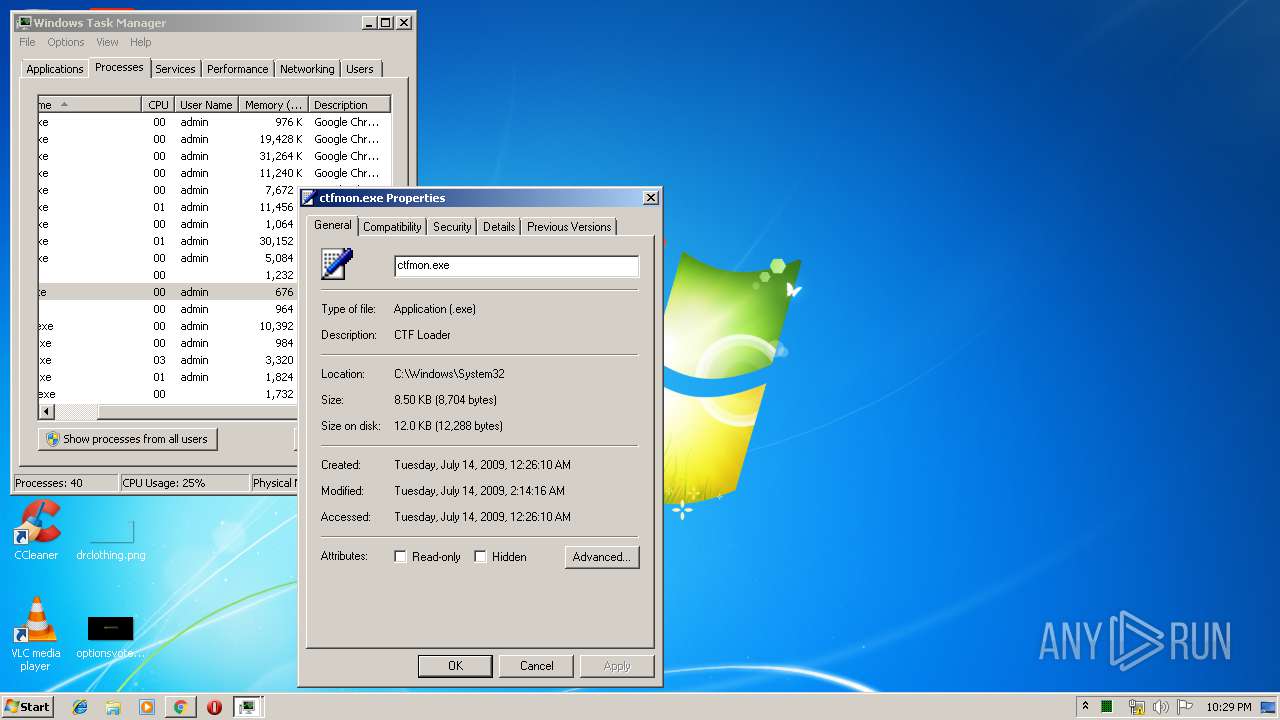
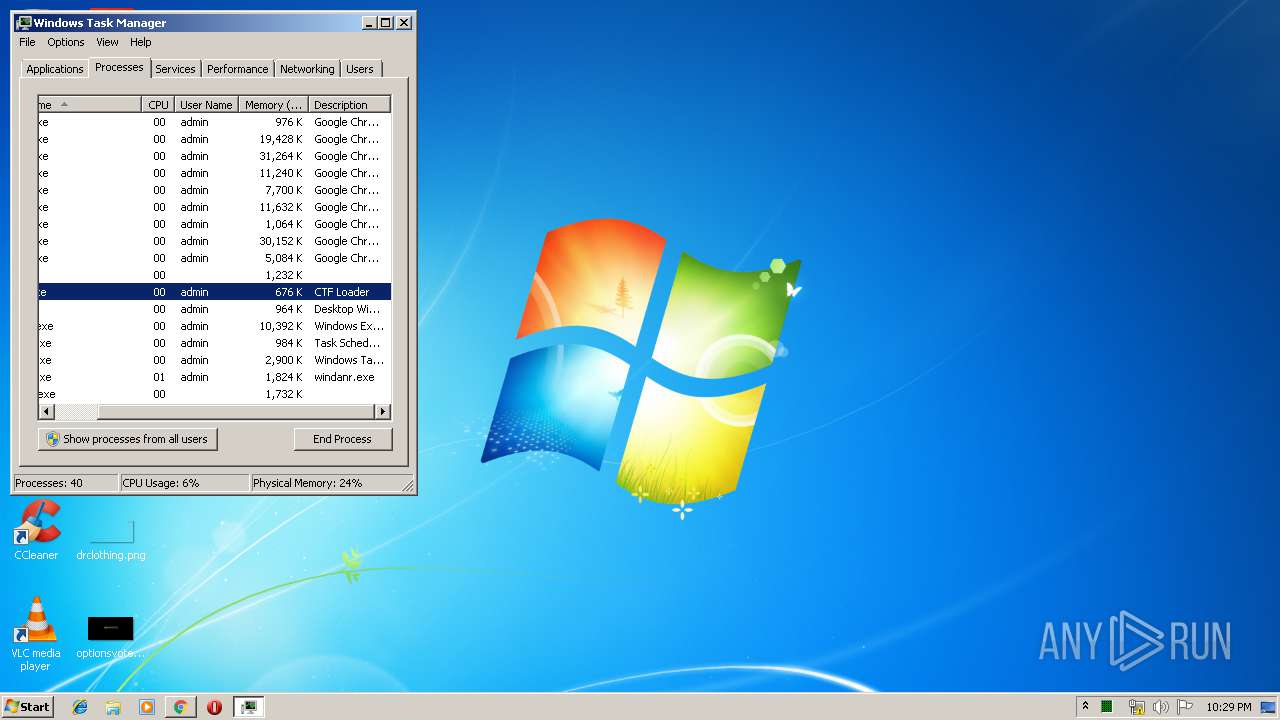
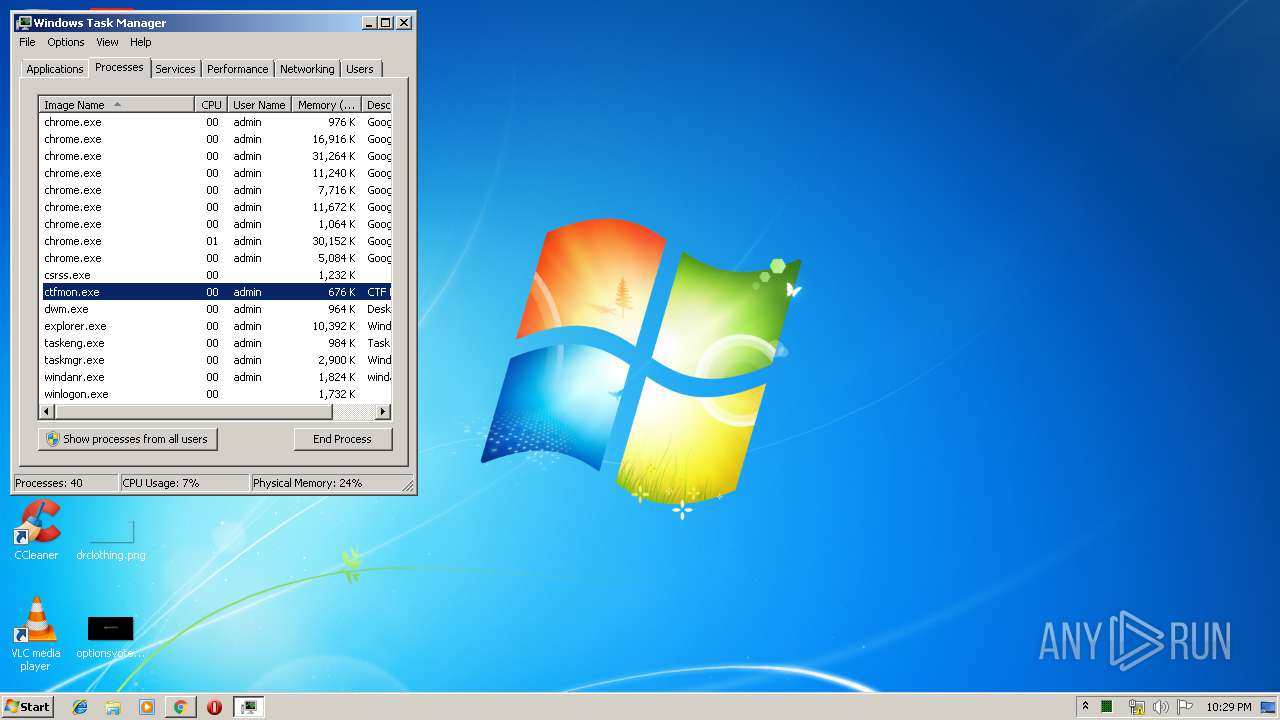
Manual execution by user
- taskmgr.exe (PID: 2828)
Application launched itself
- chrome.exe (PID: 3544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
33
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9765633566985081041 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11942360465023660998 --mojo-platform-channel-handle=3348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fd9a9d0,0x6fd9a9e0,0x6fd9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1082383470075662914 --mojo-platform-channel-handle=3636 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14494266099960833030 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2794042268938748870 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2320 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5207560324721369234 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17193482832663842045 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3088513189101425317 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1376938203652317761,6422762406210255118,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4195073951421452613 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
687
Read events
586
Write events
96
Delete events
5
Modification events
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3444) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3544-13211241969849500 |
Value: 259 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
151
Text files
273
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169bc7.TMP | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4552f2ee-56e9-462d-974c-9bef3118b409.tmp | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169bc7.TMP | text | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
83
DNS requests
73
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/cdn-cgi/apps/head/Q9VRfZD6cQzSVYmvp-L2XWFYdW4.js | US | text | 1.98 Kb | shared |
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/database/ | US | html | 1.84 Kb | shared |
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/database/css/pagestyle.css | US | text | 321 b | shared |
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/jq/colorbox/colorbox/jquery.colorbox-min.js | US | text | 3.71 Kb | shared |
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/database/css/greyscale.css | US | text | 546 b | shared |
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/database/index.php?search=rat | US | html | 1.85 Kb | shared |
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/jq/colorbox/modal/colorbox.css | US | text | 1.26 Kb | shared |
2952 | chrome.exe | GET | 302 | 172.217.22.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/database/index.php?search=RAT | US | html | 1.85 Kb | shared |
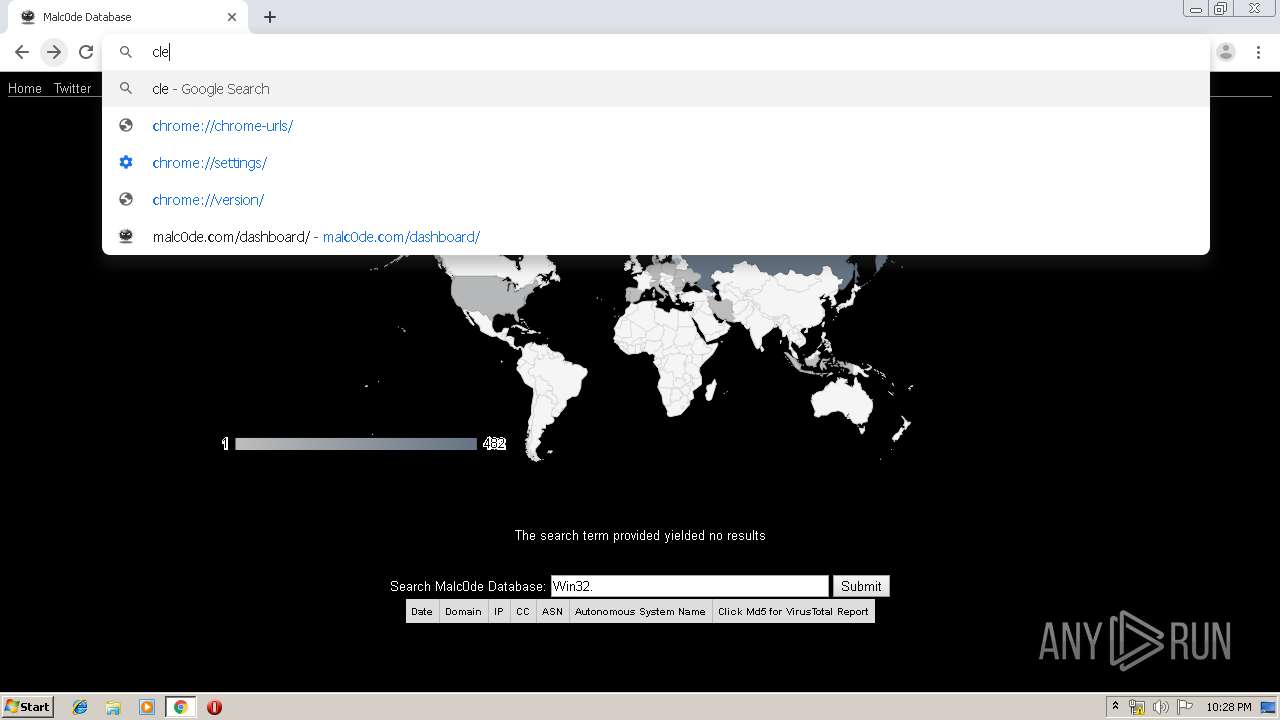
2952 | chrome.exe | GET | 200 | 104.27.202.88:80 | http://malc0de.com/dashboard/ | US | html | 2.68 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 104.27.202.88:80 | malc0de.com | Cloudflare Inc | US | shared |
2952 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 216.58.207.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.23.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 216.58.207.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.22.99:80 | www.gstatic.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
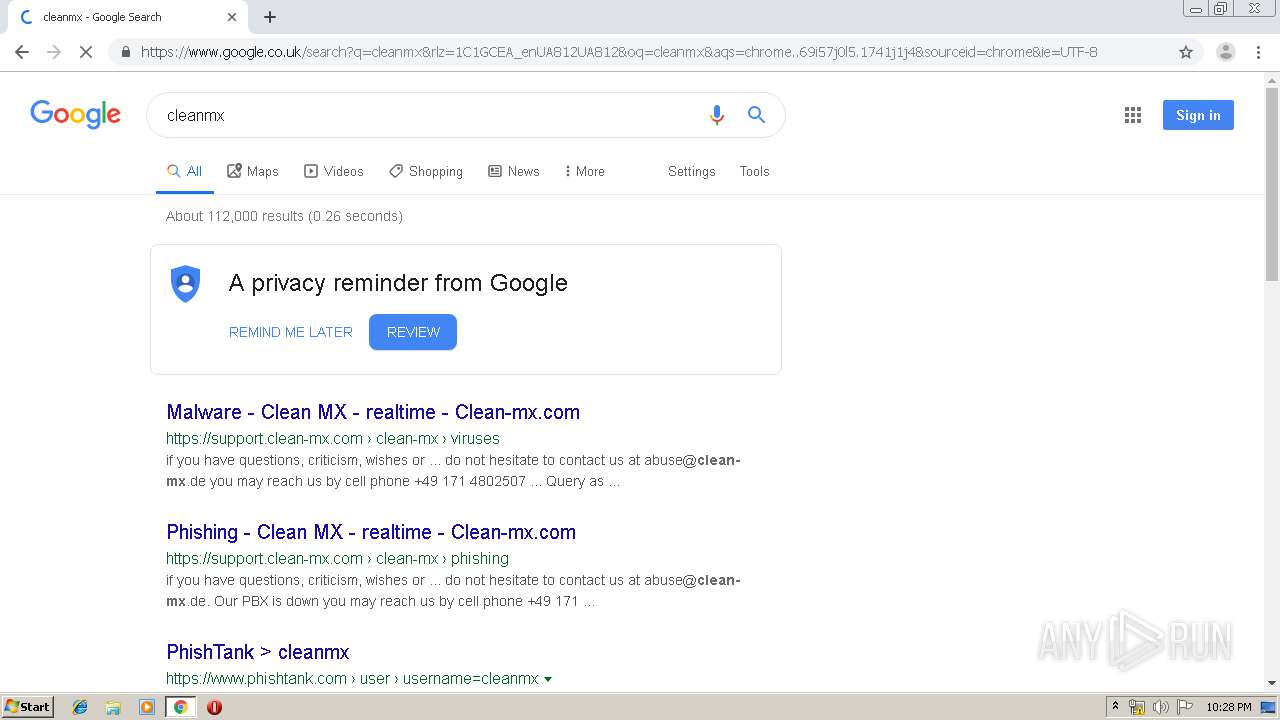
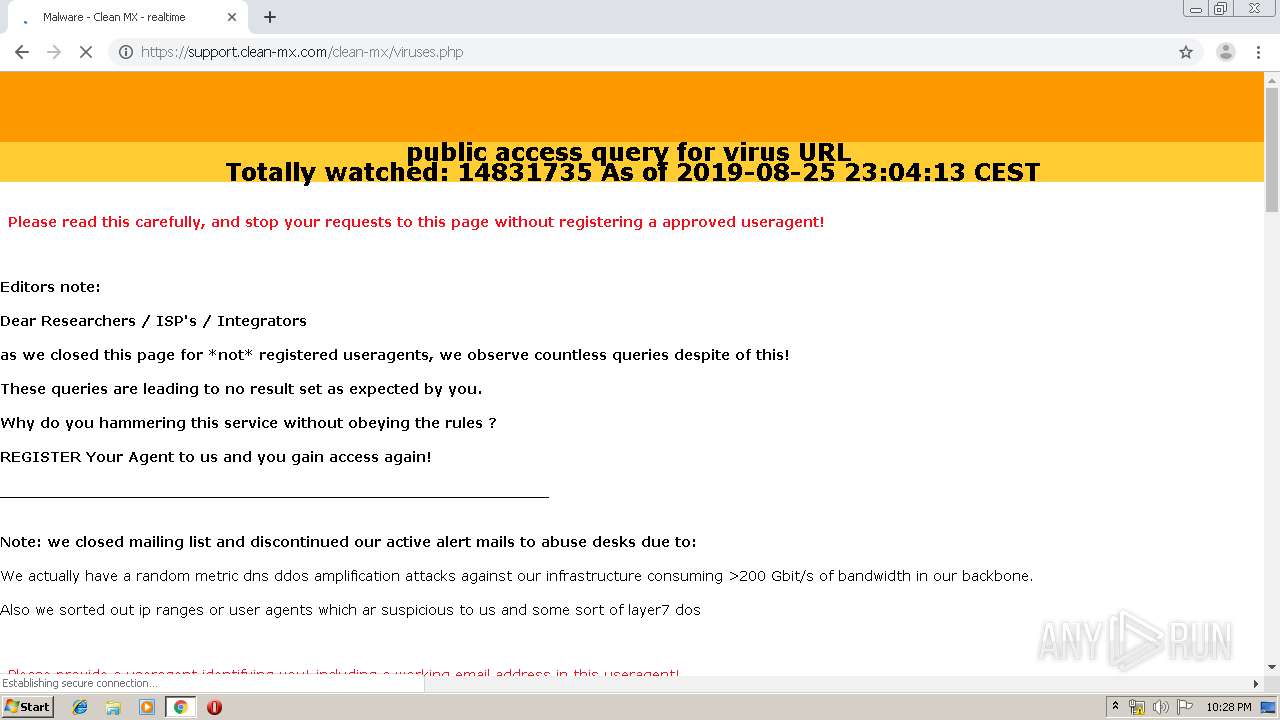
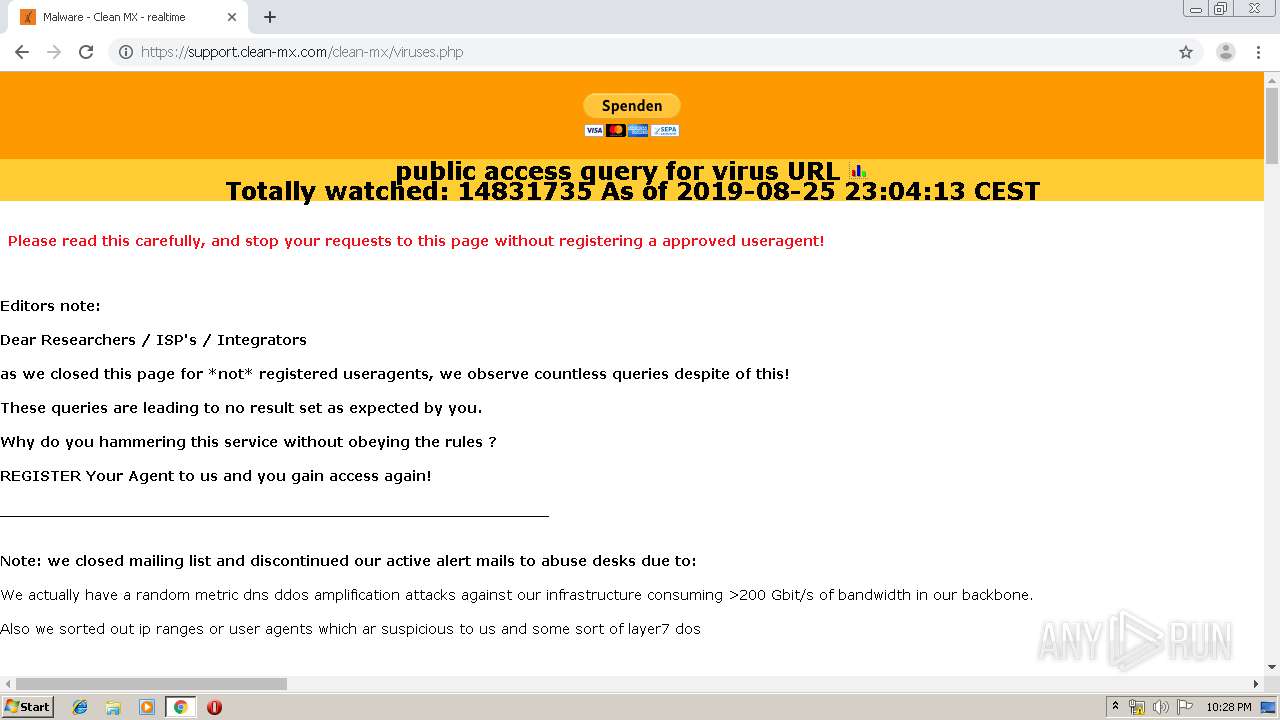
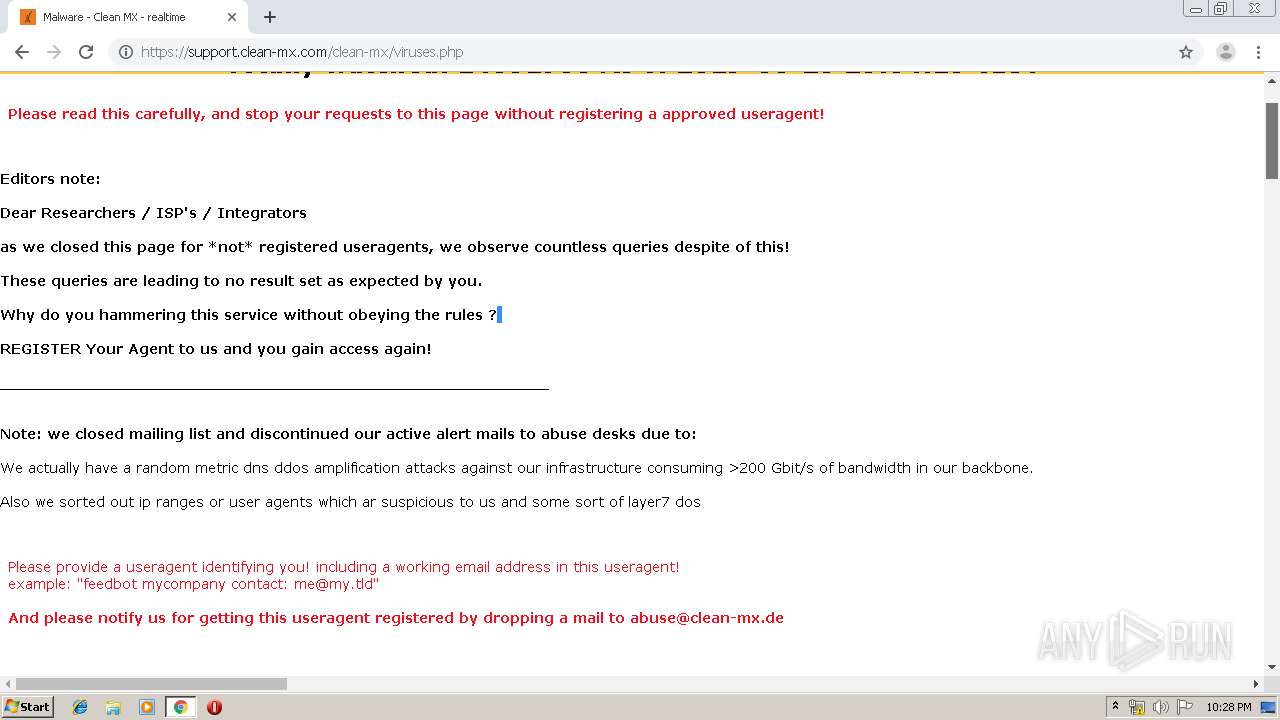
malc0de.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
www.google-analytics.com |
| whitelisted |
malwr.com |
| unknown |
twitter.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
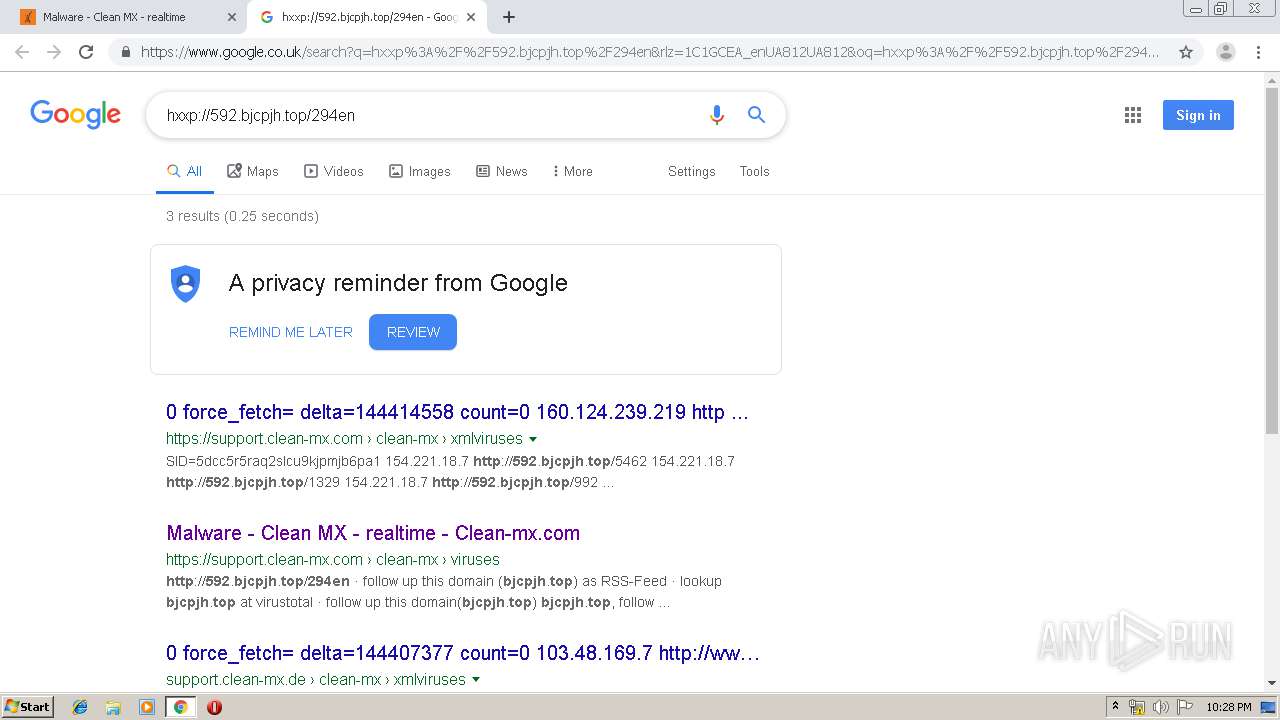
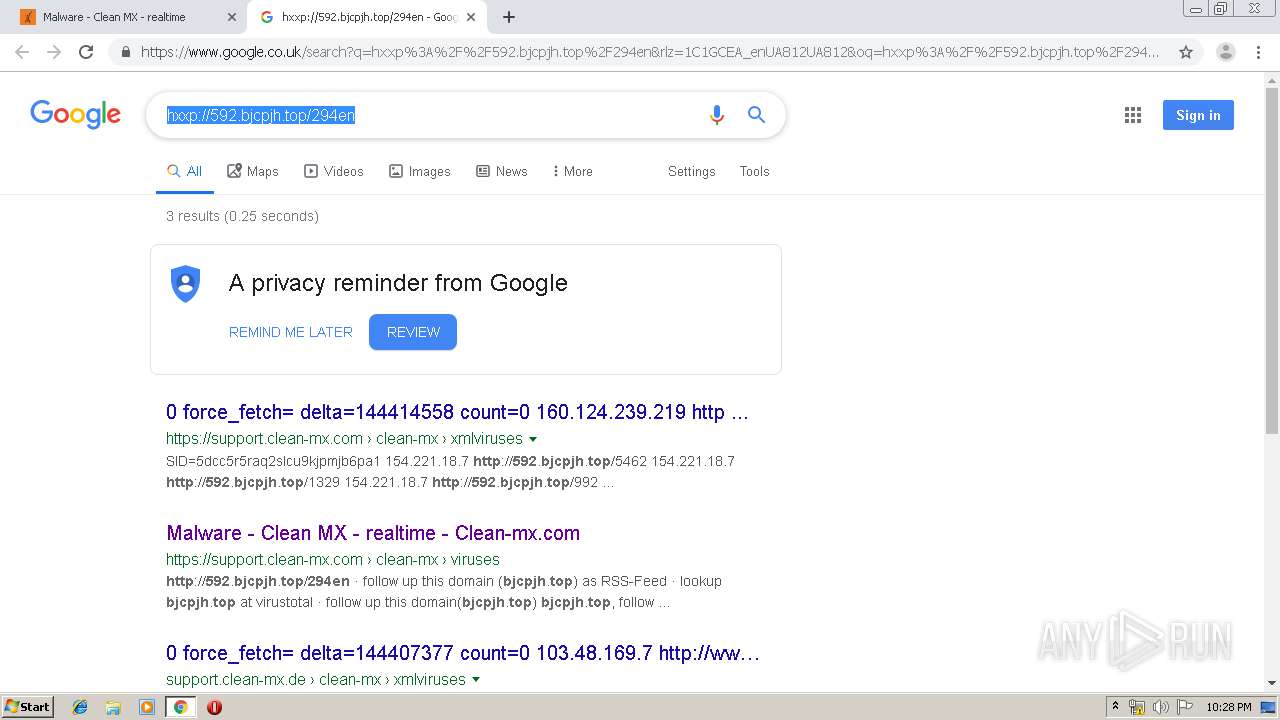
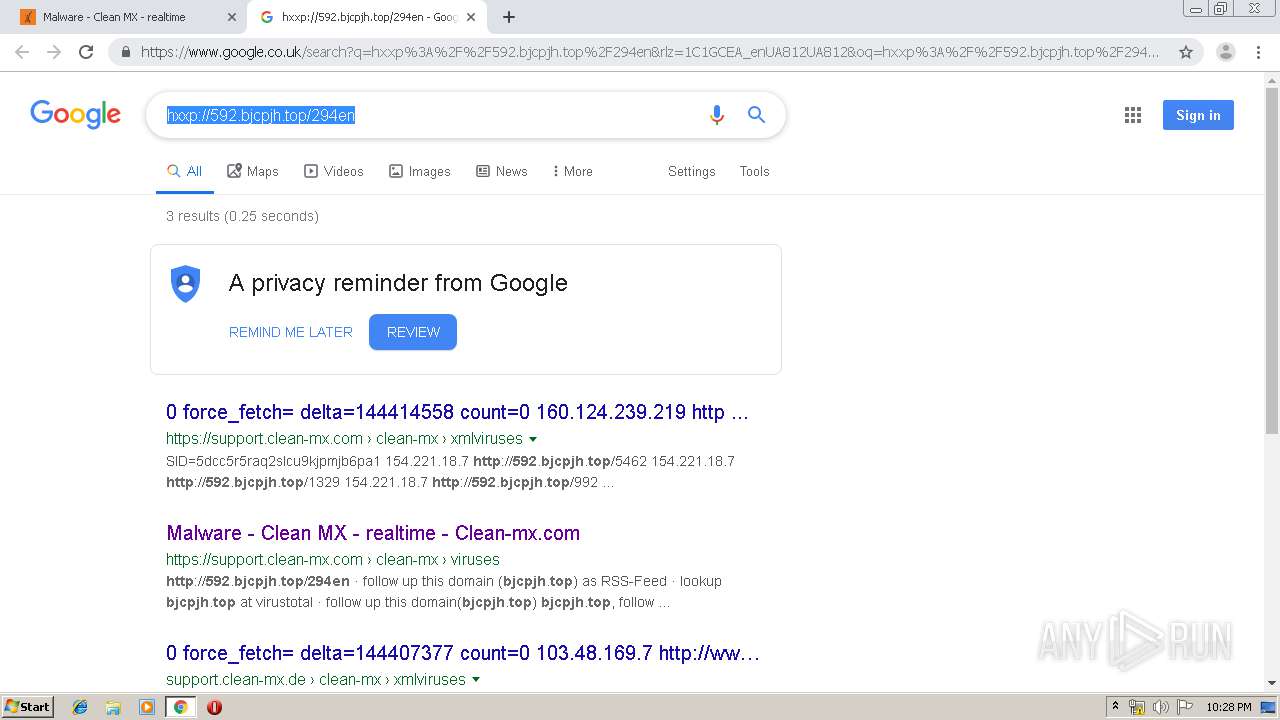
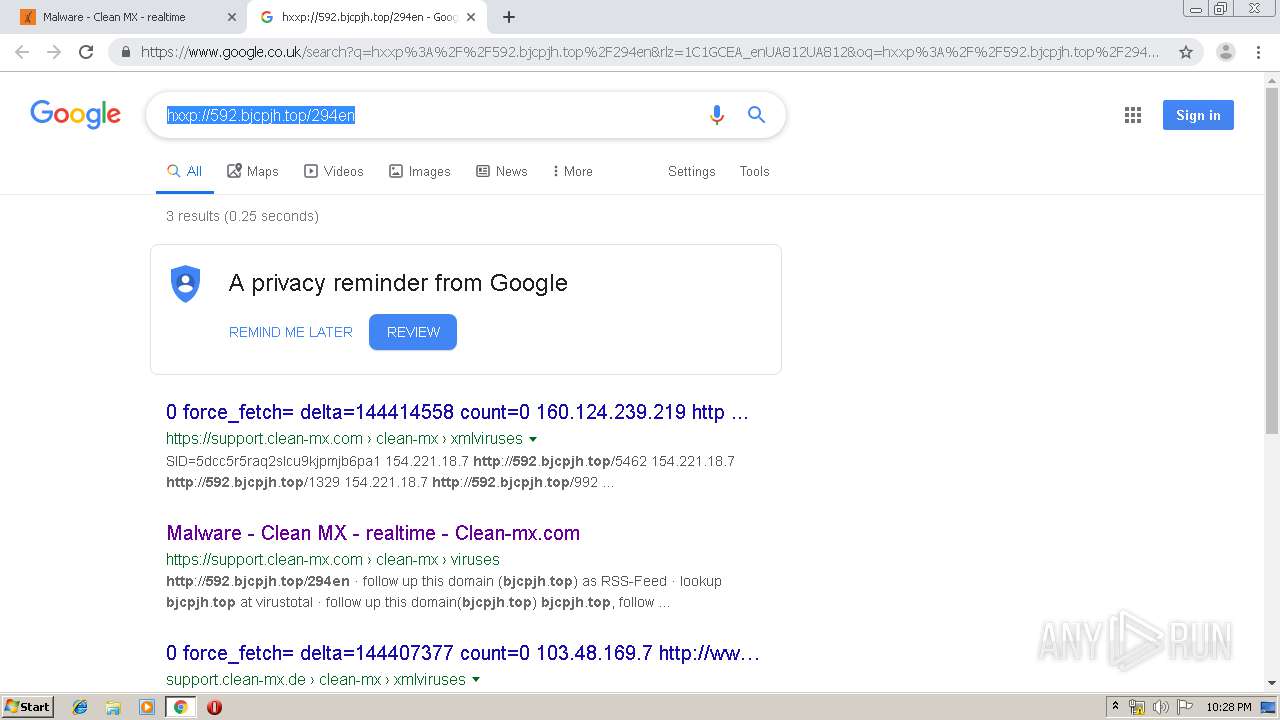
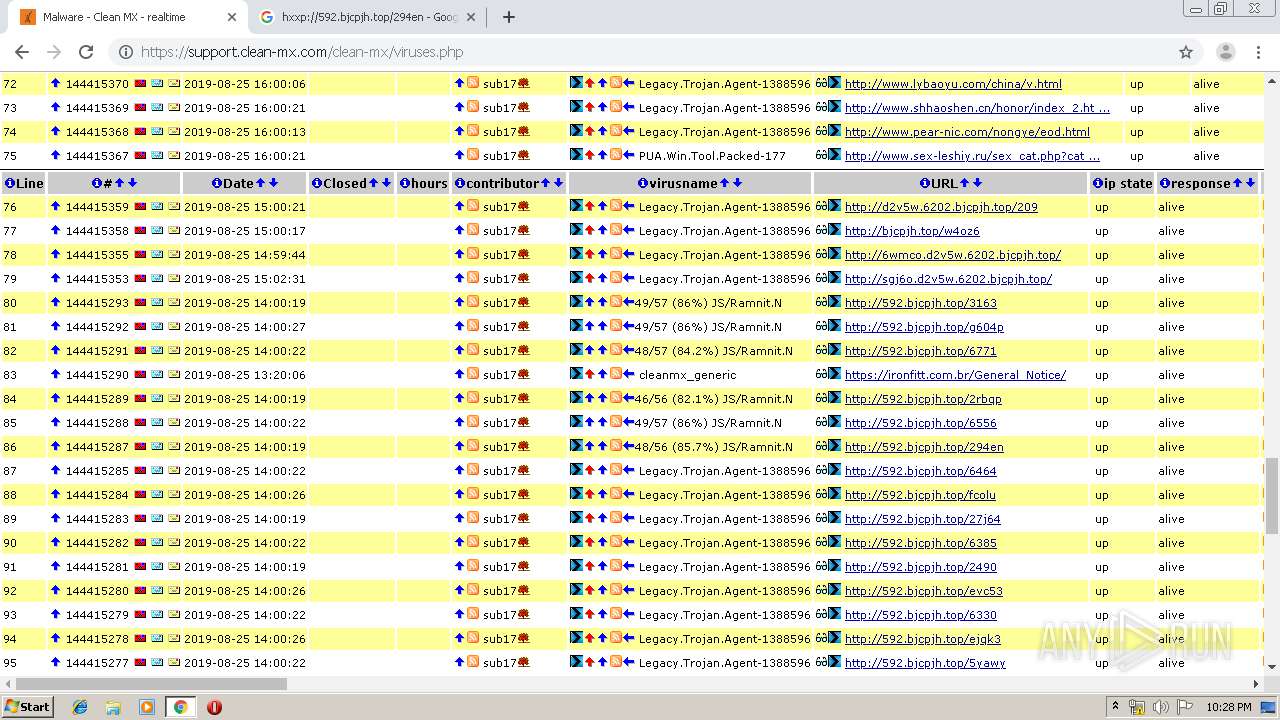
Threats
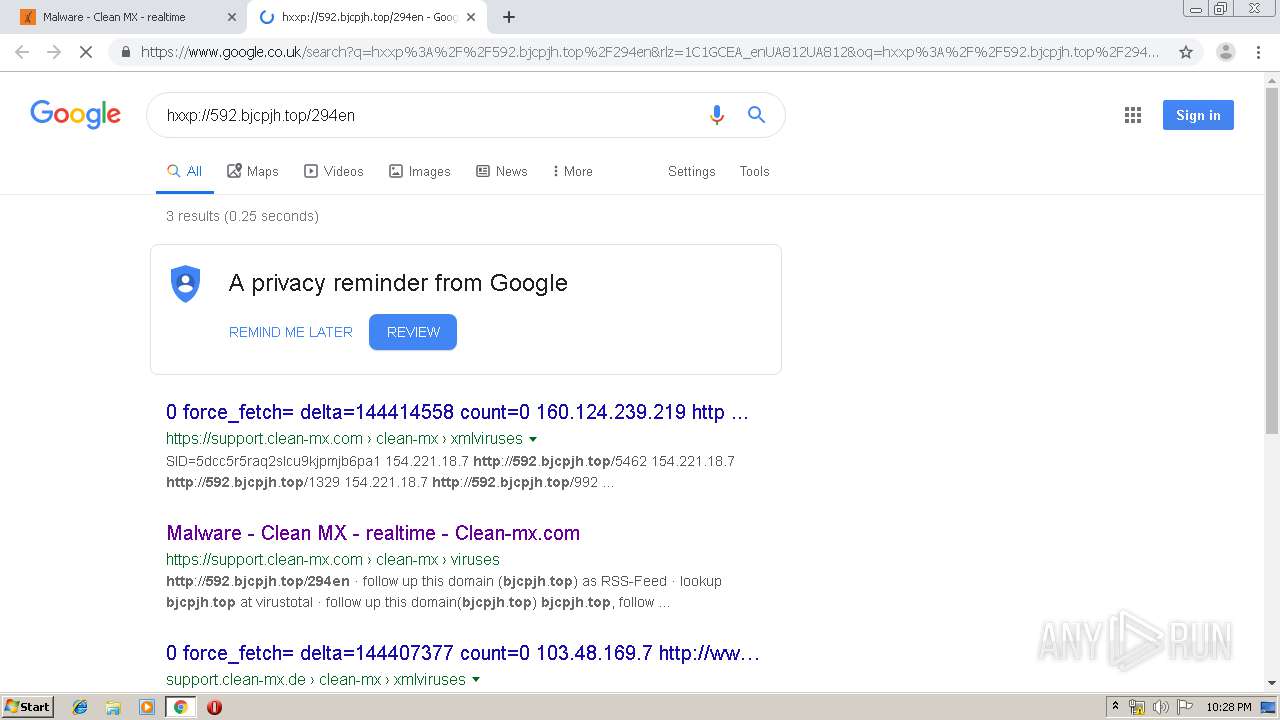
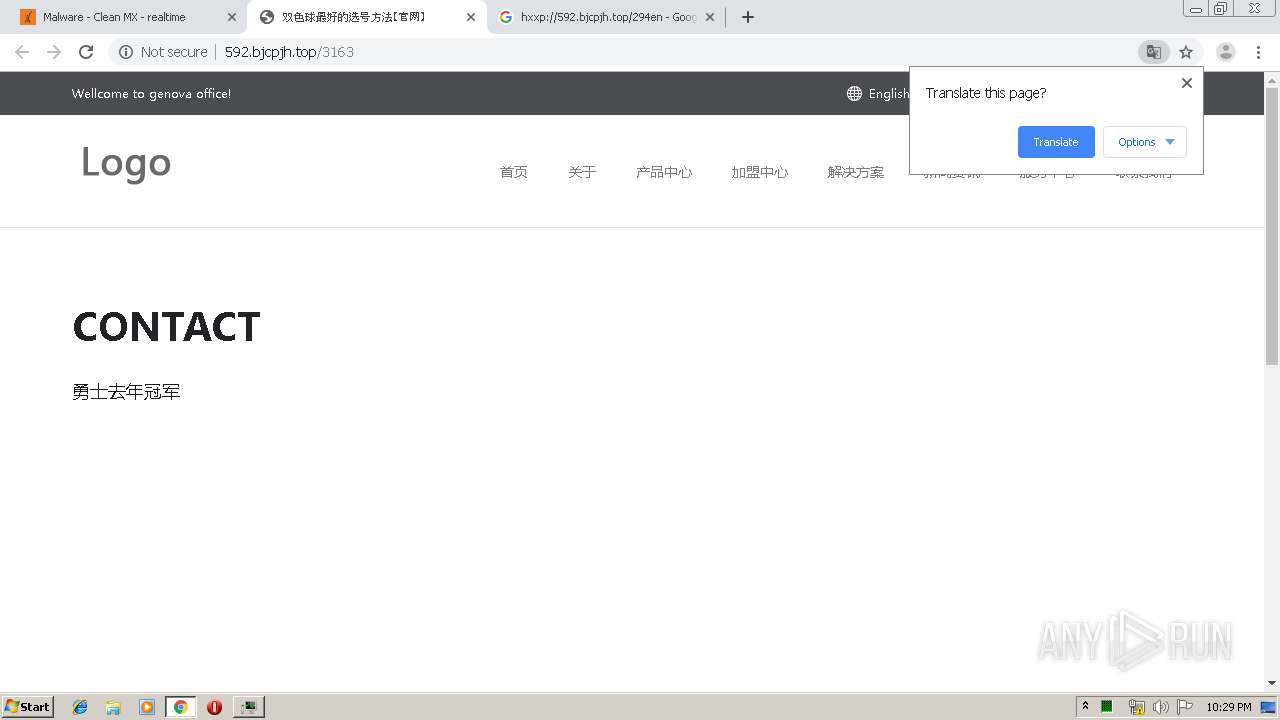
PID | Process | Class | Message |
|---|---|---|---|
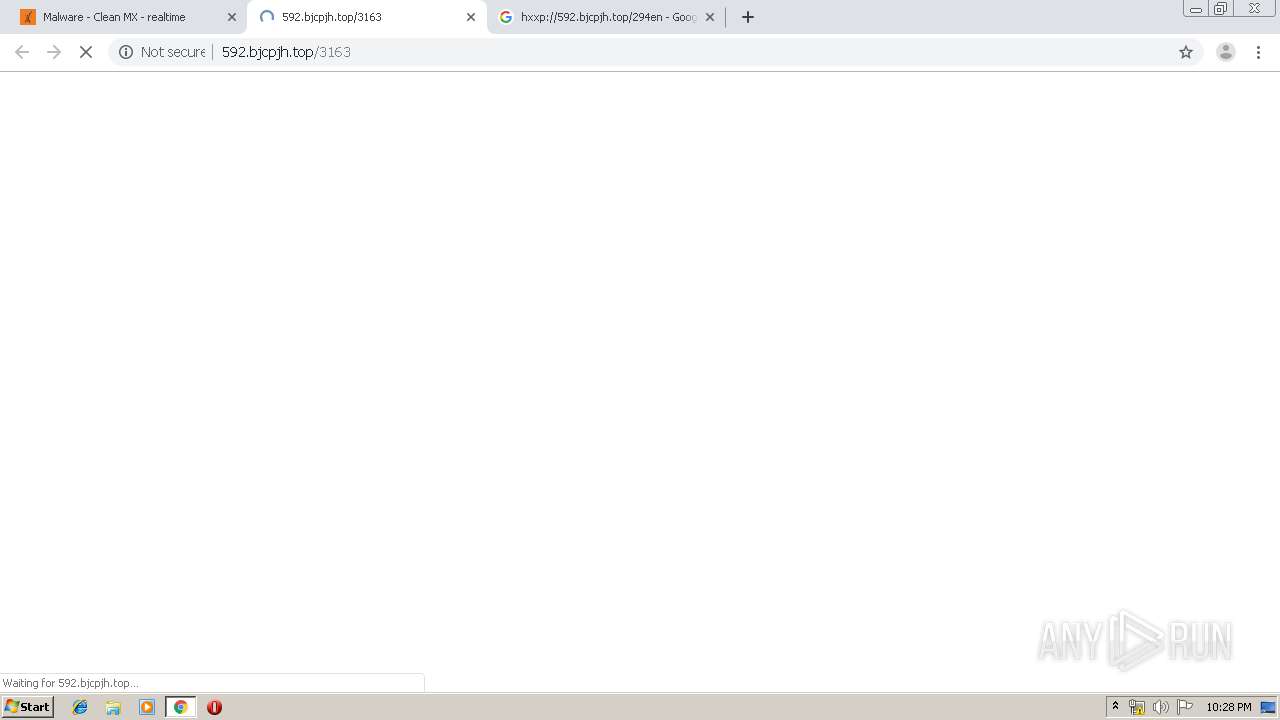
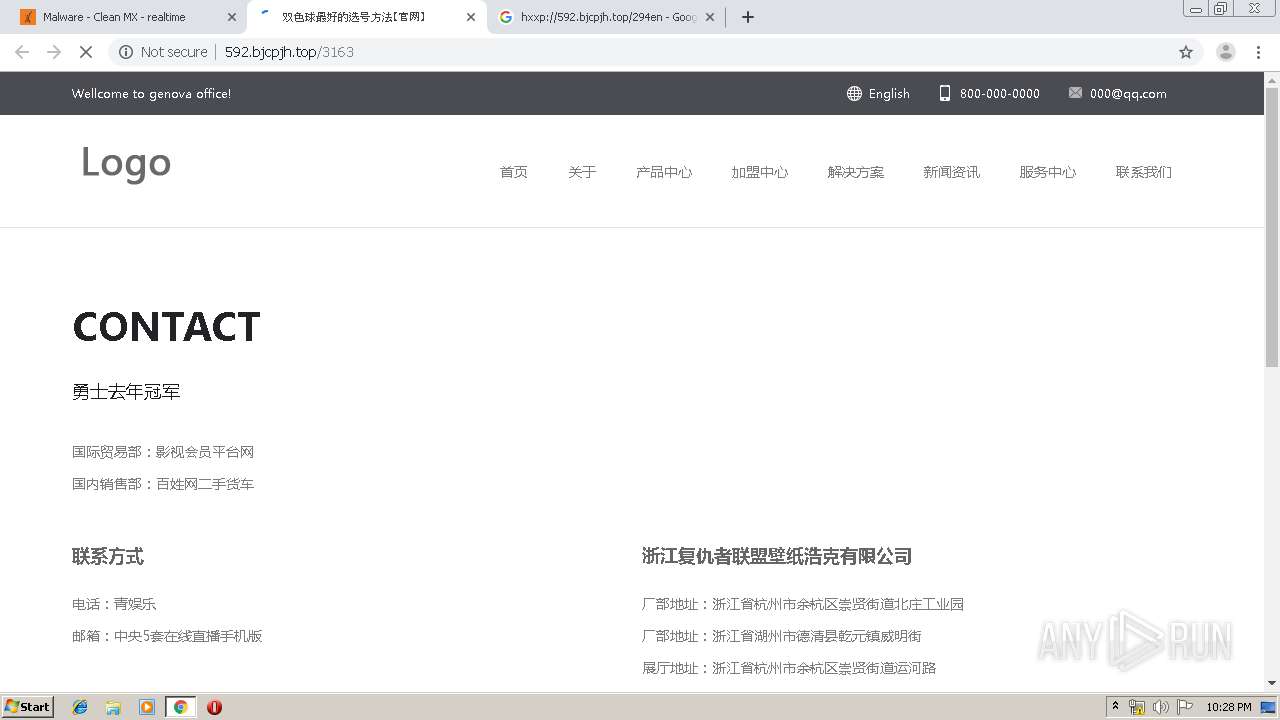
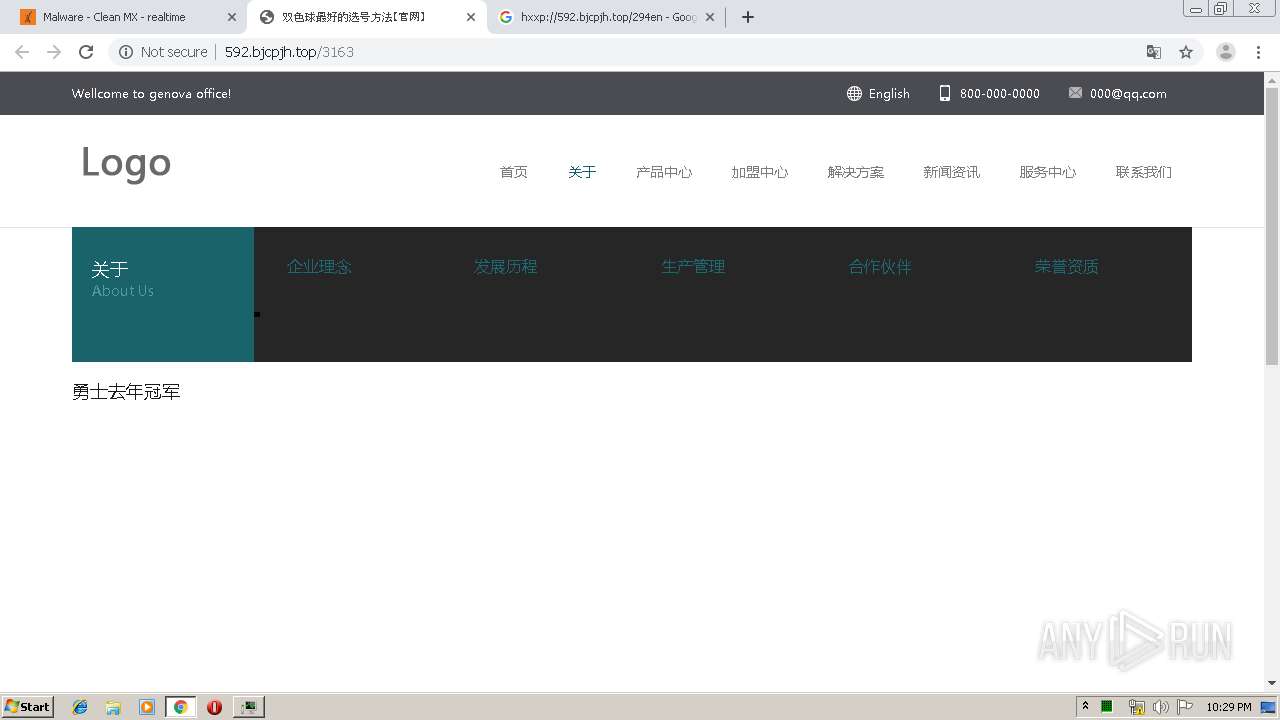
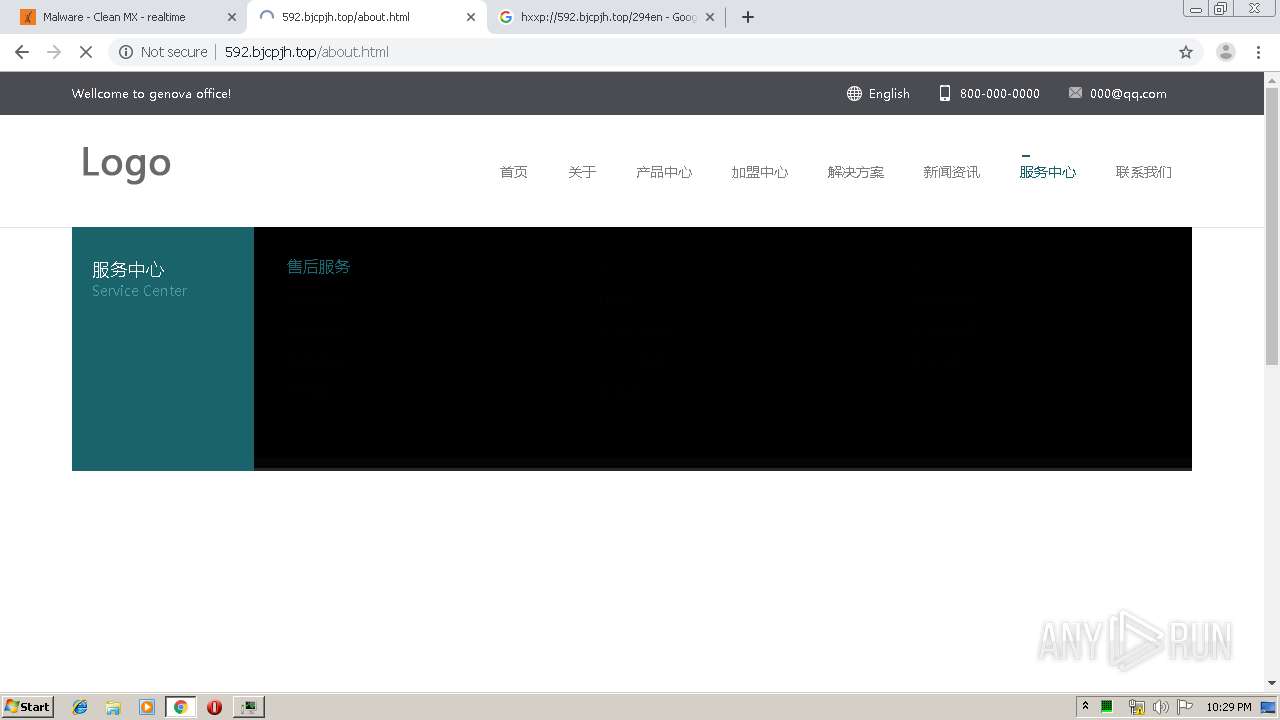
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2952 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2952 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS DRIVEBY EXE Embeded in Page Likely Evil M1 |
2952 | chrome.exe | A Network Trojan was detected | ET TROJAN PE EXE or DLL Windows file download Text |
2952 | chrome.exe | A Network Trojan was detected | ET TROJAN RAMNIT.A M2 |
2952 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS DRIVEBY EXE Embeded in Page Likely Evil M1 |
2952 | chrome.exe | A Network Trojan was detected | ET TROJAN PE EXE or DLL Windows file download Text |
2952 | chrome.exe | A Network Trojan was detected | ET TROJAN RAMNIT.A M2 |
2952 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2952 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS DRIVEBY EXE Embeded in Page Likely Evil M1 |