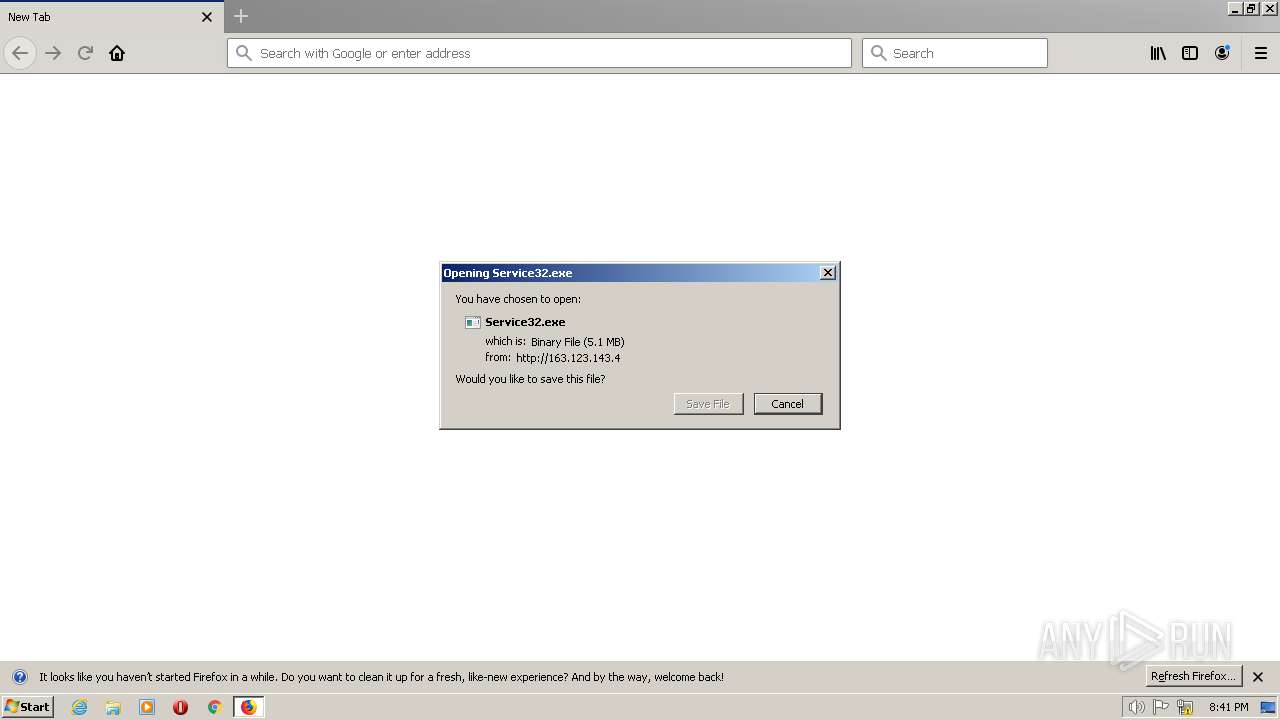
| URL: | http://163.123.143.4/download/Service32.exe |
| Full analysis: | https://app.any.run/tasks/3632aacb-f5f9-4416-a435-d898e5f00ce5 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 14, 2023, 20:41:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CC451D1F4C477BCFB8FF14B9428A67A5 |
| SHA1: | 72B453D54A947047FAE614602EE13C3EF5CE4A33 |
| SHA256: | EE5F3D45DFEEED44CEBA65BCFCC476C6DDC7166F9F2B7085C288F3AC03535678 |
| SSDEEP: | 3:N1KrMOWUQkLJknEAn:CIOWUbL2p |
MALICIOUS
Application was dropped or rewritten from another process
- Service32.exe (PID: 1768)
- Service32.exe (PID: 2880)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- ioxrc55KZWdsB4OsQtoTi5jv.exe (PID: 3068)
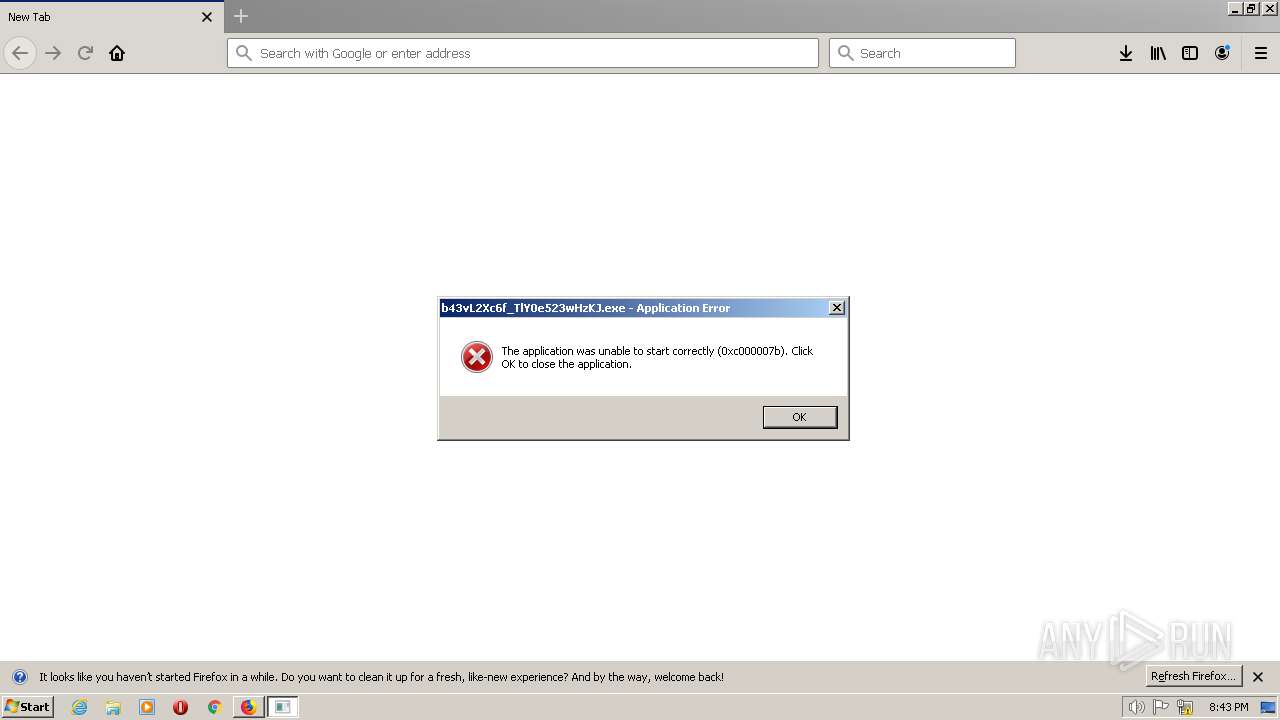
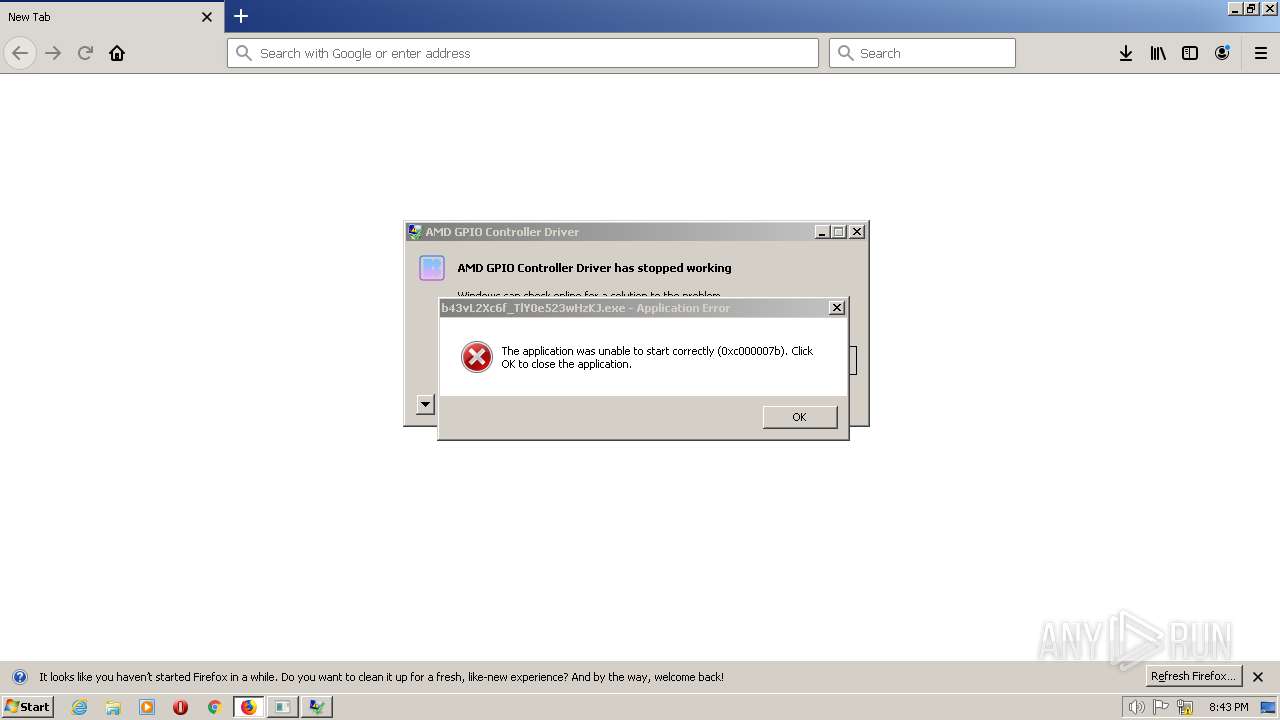
- b43vL2Xc6f_TlY0e523wHzKJ.exe (PID: 2220)
- CL_a7BpeoKbmXr_oFD0IeXbt.exe (PID: 3064)
- Install.exe (PID: 2636)
- p9ZMvhDo4_iDi4J1hKUHPinQ.exe (PID: 2976)
- Install.exe (PID: 3852)
- ss41.exe (PID: 3076)
- 2a344302.exe (PID: 1440)
- newplayer.exe (PID: 2412)
- oneetx.exe (PID: 3656)
- QCKUSzjmUzLmc.exe (PID: 4052)
- oneetx.exe (PID: 3384)
- DXQzpm.exe (PID: 3496)
- 6QCFV8x13t.exe (PID: 3704)
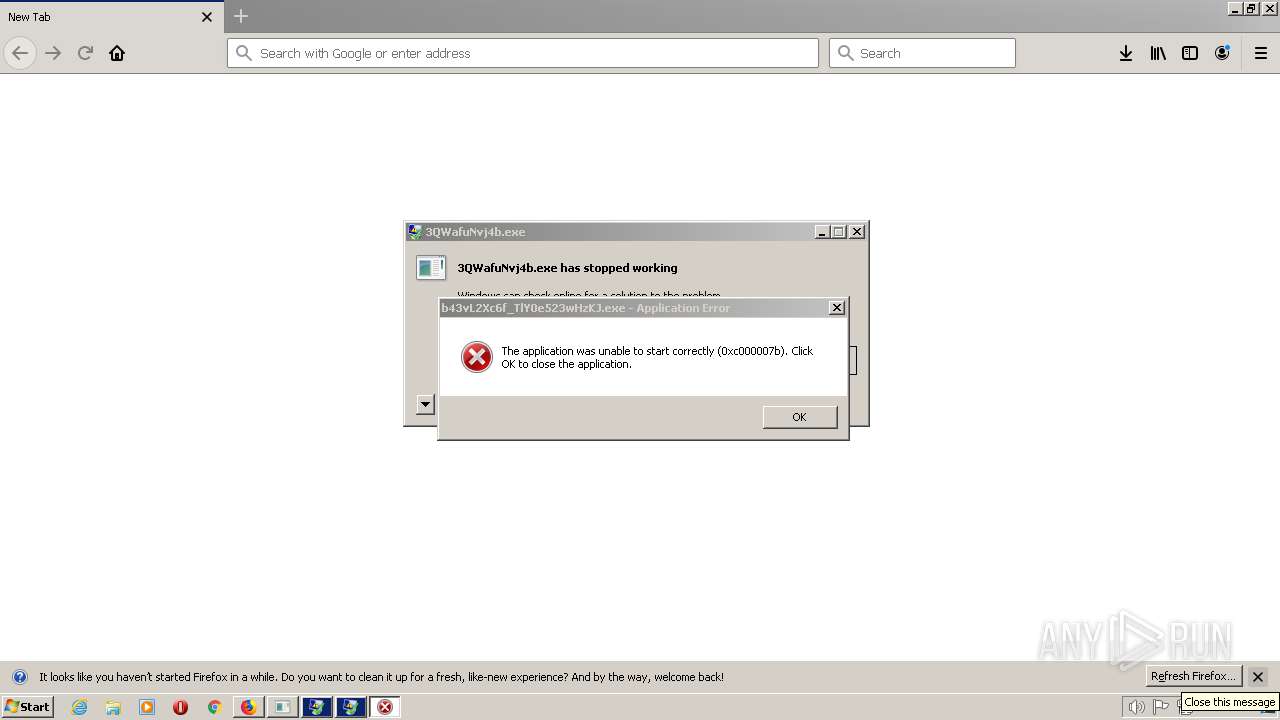
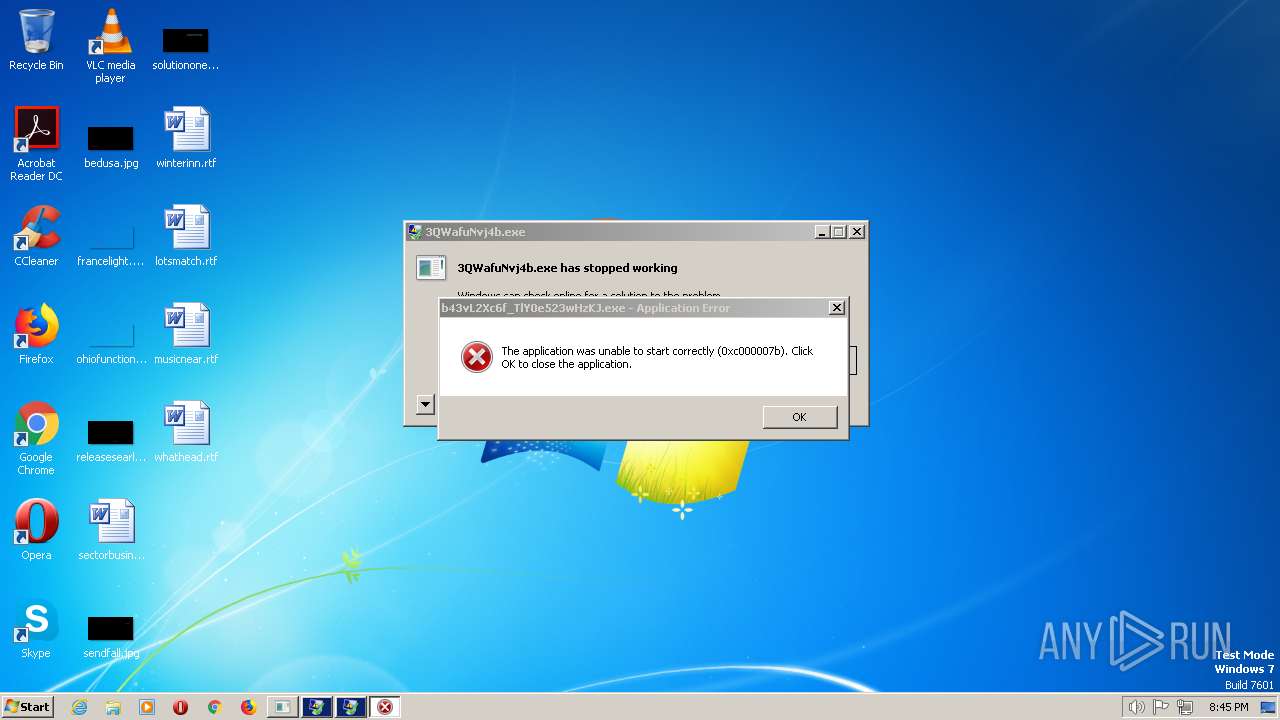
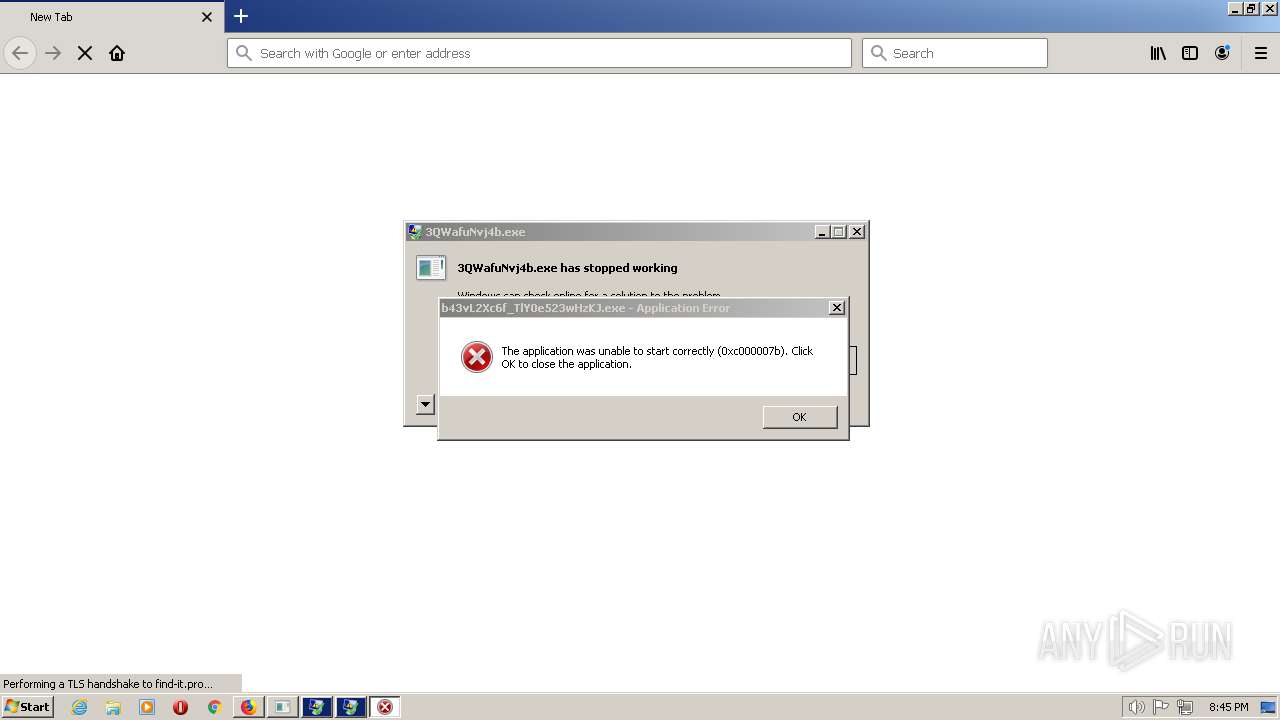
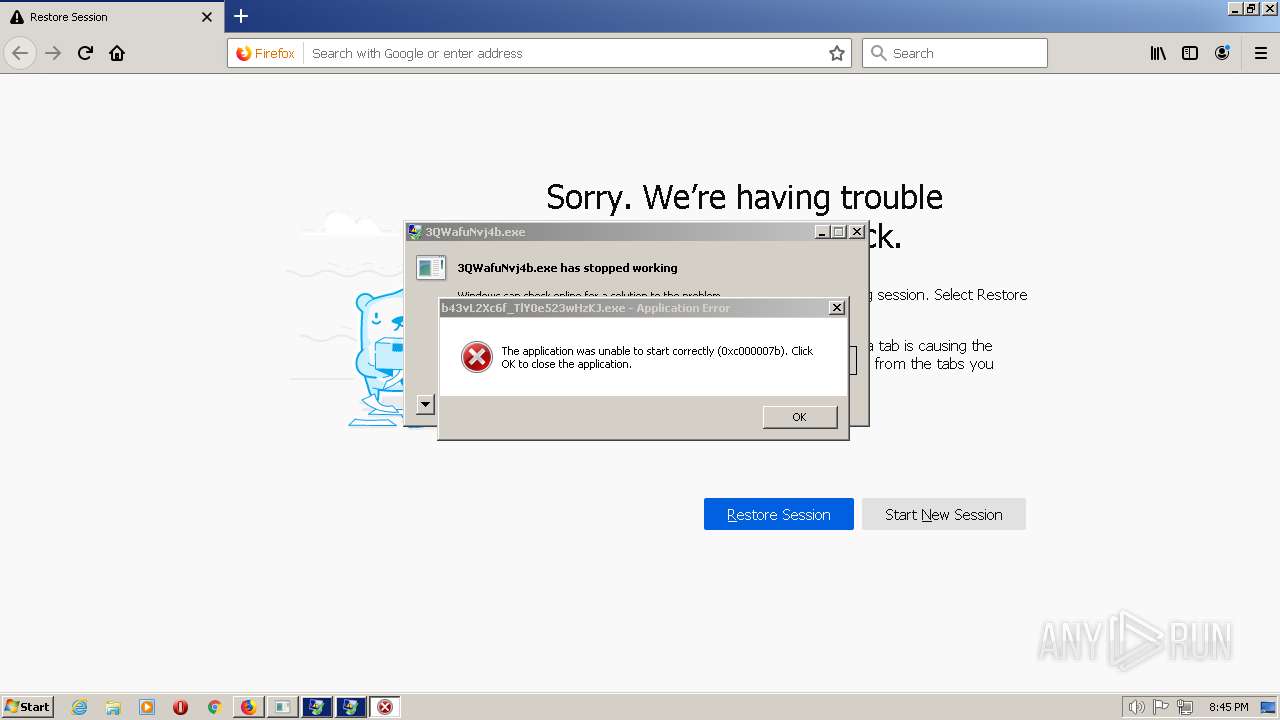
- 3QWafuNvj4b.exe (PID: 1720)
- YhLLgTr.exe (PID: 3060)
- oneetx.exe (PID: 3736)
- FjBavdM.exe (PID: 4060)
- oneetx.exe (PID: 2152)
Connects to the CnC server
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- oneetx.exe (PID: 3656)
- Rec614.exe (PID: 3348)
- AppLaunch.exe (PID: 3208)
- explorer.exe (PID: 1960)
PRIVATELOADER was detected
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
Uses Task Scheduler to run other applications
- Service32.exe (PID: 1768)
- oneetx.exe (PID: 3656)
- Install.exe (PID: 3852)
- YhLLgTr.exe (PID: 3060)
- FjBavdM.exe (PID: 4060)
- rundll32.exe (PID: 3048)
Creates a writable file the system directory
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- FjBavdM.exe (PID: 4060)
Uses Task Scheduler to autorun other applications
- Service32.exe (PID: 1768)
- FjBavdM.exe (PID: 4060)
Actions looks like stealing of personal data
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- xEGBzXp68dxyGyQGQ34EDKn4.exe (PID: 1624)
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- AppLaunch.exe (PID: 3208)
- YhLLgTr.exe (PID: 3060)
- FjBavdM.exe (PID: 4060)
- 6QCFV8x13t.exe (PID: 3704)
Steals credentials from Web Browsers
- xEGBzXp68dxyGyQGQ34EDKn4.exe (PID: 1624)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- AppLaunch.exe (PID: 3208)
- 6QCFV8x13t.exe (PID: 3704)
- YhLLgTr.exe (PID: 3060)
- FjBavdM.exe (PID: 4060)
Loads dropped or rewritten executable
- is-HQC8F.tmp (PID: 2880)
- 6QCFV8x13t.exe (PID: 3704)
- rundll32.exe (PID: 3048)
Changes the autorun value in the registry
- oneetx.exe (PID: 3656)
REDLINE was detected
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- AppLaunch.exe (PID: 3208)
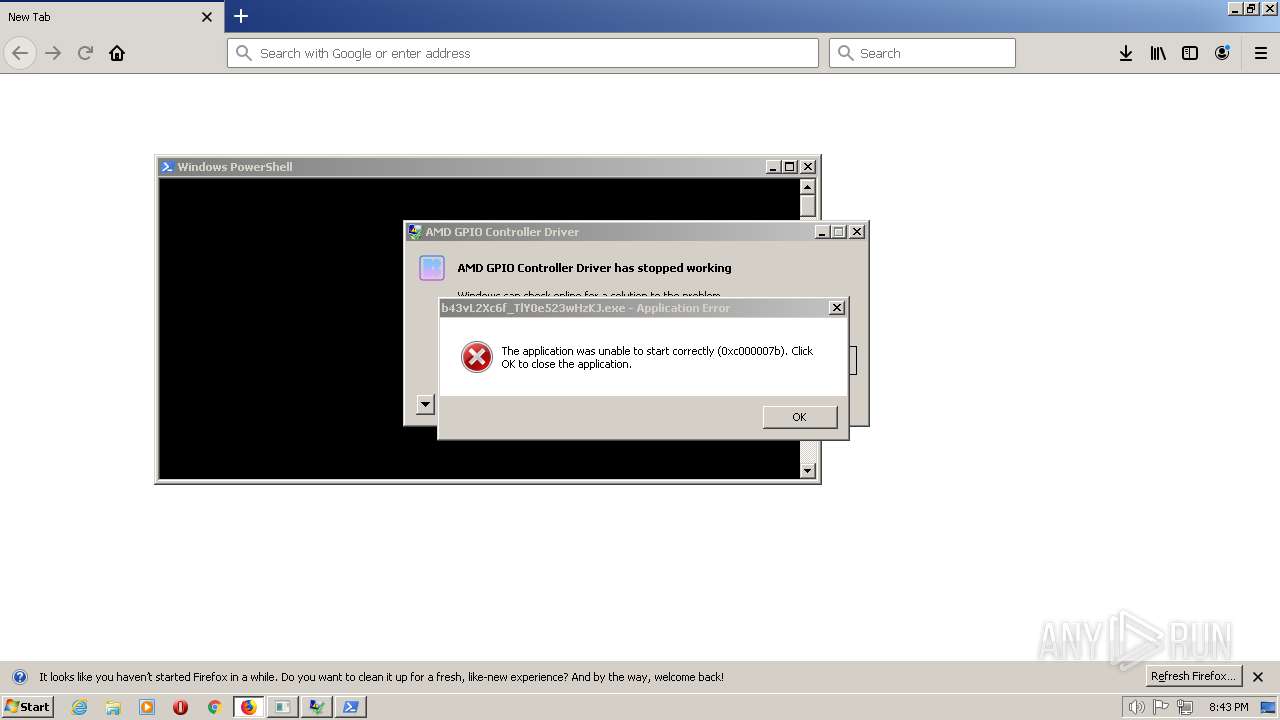
Run PowerShell with an invisible window
- powershell.EXE (PID: 3596)
- powershell.EXE (PID: 2928)
Application was injected by another process
- explorer.exe (PID: 1960)
AMADEY was detected
- oneetx.exe (PID: 3656)
Runs injected code in another process
- 2a344302.exe (PID: 1440)
GCLEANER was detected
- Rec614.exe (PID: 3348)
SMOKE was detected
- explorer.exe (PID: 1960)
GCLEANER detected by memory dumps
- Rec614.exe (PID: 3348)
PRIVATELOADER detected by memory dumps
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
Starts CMD.EXE for self-deleting
- Rec614.exe (PID: 3348)
Steals credentials
- 6QCFV8x13t.exe (PID: 3704)
ARKEI was detected
- 6QCFV8x13t.exe (PID: 3704)
AMADEY detected by memory dumps
- oneetx.exe (PID: 3656)
REDLINE detected by memory dumps
- 3QWafuNvj4b.exe (PID: 1720)
Modifies exclusions in Windows Defender
- reg.exe (PID: 2900)
Modifies files in the Chrome extension folder
- FjBavdM.exe (PID: 4060)
Unusual connection from system programs
- rundll32.exe (PID: 3048)
SUSPICIOUS
Executable content was dropped or overwritten
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- CL_a7BpeoKbmXr_oFD0IeXbt.exe (PID: 3064)
- is-HQC8F.tmp (PID: 2880)
- p9ZMvhDo4_iDi4J1hKUHPinQ.exe (PID: 2976)
- Install.exe (PID: 2636)
- TVdcEz00S_ENiezpTZSi9Ewj.exe (PID: 1840)
- newplayer.exe (PID: 2412)
- Rec614.exe (PID: 3348)
- DXQzpm.exe (PID: 3496)
- cmd.exe (PID: 1216)
- explorer.exe (PID: 1960)
- Install.exe (PID: 3852)
- 6QCFV8x13t.exe (PID: 3704)
- YhLLgTr.exe (PID: 3060)
- FjBavdM.exe (PID: 4060)
Checks for external IP
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
Reads settings of System Certificates
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- 6QCFV8x13t.exe (PID: 3704)
- AppLaunch.exe (PID: 3208)
Adds/modifies Windows certificates
- firefox.exe (PID: 2432)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Service32.exe (PID: 1768)
Connects to the server without a host name
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- oneetx.exe (PID: 3656)
- Rec614.exe (PID: 3348)
Process requests binary or script from the Internet
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
Reads the Internet Settings
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- Install.exe (PID: 3852)
- TVdcEz00S_ENiezpTZSi9Ewj.exe (PID: 1840)
- newplayer.exe (PID: 2412)
- oneetx.exe (PID: 3656)
- powershell.EXE (PID: 3596)
- Rec614.exe (PID: 3348)
- explorer.exe (PID: 1960)
- AppLaunch.exe (PID: 3208)
- powershell.EXE (PID: 2928)
- 6QCFV8x13t.exe (PID: 3704)
Reads security settings of Internet Explorer
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- 6QCFV8x13t.exe (PID: 3704)
Checks Windows Trust Settings
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- 6QCFV8x13t.exe (PID: 3704)
- FjBavdM.exe (PID: 4060)
Executes as Windows Service
- raserver.exe (PID: 764)
- raserver.exe (PID: 3996)
- raserver.exe (PID: 2624)
- raserver.exe (PID: 3268)
Reads the Windows owner or organization settings
- is-HQC8F.tmp (PID: 2880)
Starts itself from another location
- p9ZMvhDo4_iDi4J1hKUHPinQ.exe (PID: 2976)
- newplayer.exe (PID: 2412)
Reads Microsoft Outlook installation path
- Rec614.exe (PID: 3348)
Reads the BIOS version
- Install.exe (PID: 3852)
Starts CMD.EXE for commands execution
- forfiles.exe (PID: 3096)
- forfiles.exe (PID: 988)
- oneetx.exe (PID: 3656)
- cmd.exe (PID: 4088)
- xEGBzXp68dxyGyQGQ34EDKn4.exe (PID: 1624)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- DXQzpm.exe (PID: 3496)
- Rec614.exe (PID: 3348)
- YhLLgTr.exe (PID: 3060)
- FjBavdM.exe (PID: 4060)
Found strings related to reading or modifying Windows Defender settings
- forfiles.exe (PID: 3096)
- forfiles.exe (PID: 988)
- YhLLgTr.exe (PID: 3060)
- FjBavdM.exe (PID: 4060)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3068)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 352)
- cmd.exe (PID: 3480)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 2876)
- wscript.exe (PID: 2400)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 1988)
- cmd.exe (PID: 116)
Reads browser cookies
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- AppLaunch.exe (PID: 3208)
Application launched itself
- cmd.exe (PID: 4088)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 4088)
Connects to unusual port
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- AppLaunch.exe (PID: 3208)
- 6QCFV8x13t.exe (PID: 3704)
Searches for installed software
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- AppLaunch.exe (PID: 3208)
- 6QCFV8x13t.exe (PID: 3704)
The process executes via Task Scheduler
- powershell.EXE (PID: 3596)
- oneetx.exe (PID: 3384)
- YhLLgTr.exe (PID: 3060)
- oneetx.exe (PID: 3736)
- powershell.EXE (PID: 2928)
- FjBavdM.exe (PID: 4060)
- rundll32.exe (PID: 2492)
- firefox.exe (PID: 1672)
- oneetx.exe (PID: 2152)
Executing commands from a ".bat" file
- DXQzpm.exe (PID: 3496)
Process communicates with Telegram (possibly using it as an attacker's C2 server)_update
- 6QCFV8x13t.exe (PID: 3704)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3100)
INFO
Application launched itself
- firefox.exe (PID: 2432)
- firefox.exe (PID: 1672)
Executable content was dropped or overwritten
- firefox.exe (PID: 2432)
The process uses the downloaded file
- firefox.exe (PID: 2432)
- Service32.exe (PID: 1768)
Checks supported languages
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- ioxrc55KZWdsB4OsQtoTi5jv.exe (PID: 3068)
- xEGBzXp68dxyGyQGQ34EDKn4.exe (PID: 1624)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- CL_a7BpeoKbmXr_oFD0IeXbt.exe (PID: 3064)
- TVdcEz00S_ENiezpTZSi9Ewj.exe (PID: 1840)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- p9ZMvhDo4_iDi4J1hKUHPinQ.exe (PID: 2976)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- is-HQC8F.tmp (PID: 2880)
- Install.exe (PID: 2636)
- Rec614.exe (PID: 3348)
- Install.exe (PID: 3852)
- 2a344302.exe (PID: 1440)
- newplayer.exe (PID: 2412)
- oneetx.exe (PID: 3656)
- QCKUSzjmUzLmc.exe (PID: 4052)
- oneetx.exe (PID: 3384)
- DXQzpm.exe (PID: 3496)
- 6QCFV8x13t.exe (PID: 3704)
- fqjkbbgwj.exe (PID: 968)
- 3QWafuNvj4b.exe (PID: 1720)
- AppLaunch.exe (PID: 3208)
- YhLLgTr.exe (PID: 3060)
- oneetx.exe (PID: 3736)
- FjBavdM.exe (PID: 4060)
- oneetx.exe (PID: 2152)
Reads the computer name
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- TVdcEz00S_ENiezpTZSi9Ewj.exe (PID: 1840)
- is-HQC8F.tmp (PID: 2880)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- ioxrc55KZWdsB4OsQtoTi5jv.exe (PID: 3068)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- Install.exe (PID: 3852)
- newplayer.exe (PID: 2412)
- oneetx.exe (PID: 3656)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- xEGBzXp68dxyGyQGQ34EDKn4.exe (PID: 1624)
- Rec614.exe (PID: 3348)
- fqjkbbgwj.exe (PID: 968)
- 6QCFV8x13t.exe (PID: 3704)
- AppLaunch.exe (PID: 3208)
- FjBavdM.exe (PID: 4060)
The process checks LSA protection
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- is-HQC8F.tmp (PID: 2880)
- ioxrc55KZWdsB4OsQtoTi5jv.exe (PID: 3068)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- TVdcEz00S_ENiezpTZSi9Ewj.exe (PID: 1840)
- Install.exe (PID: 3852)
- newplayer.exe (PID: 2412)
- oneetx.exe (PID: 3656)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- Rec614.exe (PID: 3348)
- fqjkbbgwj.exe (PID: 968)
- 6QCFV8x13t.exe (PID: 3704)
- AppLaunch.exe (PID: 3208)
- explorer.exe (PID: 1960)
- taskkill.exe (PID: 1592)
- FjBavdM.exe (PID: 4060)
- rundll32.exe (PID: 3048)
Creates files in the program directory
- Service32.exe (PID: 1768)
- is-HQC8F.tmp (PID: 2880)
- 6QCFV8x13t.exe (PID: 3704)
- FjBavdM.exe (PID: 4060)
Reads the machine GUID from the registry
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- ioxrc55KZWdsB4OsQtoTi5jv.exe (PID: 3068)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- gCuNVROgqQq_uSfqpqFTIwKH.exe (PID: 2320)
- Install.exe (PID: 3852)
- newplayer.exe (PID: 2412)
- oneetx.exe (PID: 3656)
- kS6oQglo7r9mHvJVvTyvEZAK.exe (PID: 2872)
- NrzbMZpO7HVzZzyP6jkcL9c6.exe (PID: 2380)
- Rec614.exe (PID: 3348)
- fqjkbbgwj.exe (PID: 968)
- 6QCFV8x13t.exe (PID: 3704)
- AppLaunch.exe (PID: 3208)
- FjBavdM.exe (PID: 4060)
Checks proxy server information
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- oneetx.exe (PID: 3656)
- Rec614.exe (PID: 3348)
- 6QCFV8x13t.exe (PID: 3704)
Creates files or folders in the user directory
- Service32.exe (PID: 1768)
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- xEGBzXp68dxyGyQGQ34EDKn4.exe (PID: 1624)
- Rec614.exe (PID: 3348)
- 6QCFV8x13t.exe (PID: 3704)
- explorer.exe (PID: 1960)
- FjBavdM.exe (PID: 4060)
Process checks computer location settings
- 9mzRWDEV6dUF7Kpm1VIrbgt8.exe (PID: 2544)
- FjBavdM.exe (PID: 4060)
Create files in a temporary directory
- CL_a7BpeoKbmXr_oFD0IeXbt.exe (PID: 3064)
- p9ZMvhDo4_iDi4J1hKUHPinQ.exe (PID: 2976)
- is-HQC8F.tmp (PID: 2880)
- Install.exe (PID: 2636)
- TVdcEz00S_ENiezpTZSi9Ewj.exe (PID: 1840)
- newplayer.exe (PID: 2412)
- DXQzpm.exe (PID: 3496)
- Install.exe (PID: 3852)
- AppLaunch.exe (PID: 3208)
Application was dropped or rewritten from another process
- is-HQC8F.tmp (PID: 2880)
Reads Environment values
- 6etjm_2ktl7GlyQAUtrFCASm.exe (PID: 3032)
- c2YYW4Fsb4u6oq72BftpVlv0.exe (PID: 272)
- j26ObnSG1Dn55hqHx8kAh67i.exe (PID: 2148)
- AppLaunch.exe (PID: 3208)
- 6QCFV8x13t.exe (PID: 3704)
Reads CPU info
- fqjkbbgwj.exe (PID: 968)
- 6QCFV8x13t.exe (PID: 3704)
The executable file from the user directory is run by the CMD process
- fqjkbbgwj.exe (PID: 968)
Reads product name
- 6QCFV8x13t.exe (PID: 3704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
GCleaner
(PID) Process(3348) Rec614.exe
C2 (4)45.12.253.564
5.12.253.724
5.12.253.98
45.12.253.75
Amadey
(PID) Process(3656) oneetx.exe
C2 (1)http://45.9.74.80
Version3.83
Options
Drop directory207aa4515d
Drop nameoneetx.exe
Strings (116)SCHTASKS
/Create /SC MINUTE /MO 1 /TN
/TR "
" /F
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
Startup
Rem
cmd /C RMDIR /s/q
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
rundll32
/Delete /TN "
Programs
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%USERPROFILE%
\App
POST
GET
id=
&vs=
&sd=
&os=
&bi=
&ar=
&pc=
&un=
&dm=
&av=
&lv=
&og=
cred.dll|clip.dll|
d1
e1
e0
Main
http://
https://
exe
dll
cmd
ps1
<c>
<d>
Plugins/
+++
#
|
&unit=
=
shell32.dll
kernel32.dll
GetNativeSystemInfo
ProgramData\
AVAST Software
Avira
Kaspersky Lab
ESET
Panda Security
Doctor Web
AVG
360TotalSecurity
Bitdefender
Norton
Sophos
Comodo
WinDefender
0123456789
rb
wb
Content-Type: multipart/form-data; boundary=----
------
Content-Disposition: form-data; name="data"; filename="
"
Content-Type: application/octet-stream
------
--
?scr=1
.jpg
Content-Type: application/x-www-form-urlencoded
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
ComputerName
abcdefghijklmnopqrstuvwxyz0123456789-_
-unicode-
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
SYSTEM\ControlSet001\Services\BasicDisplay\Video
VideoID
\0000
DefaultSettings.XResolution
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
2019
2022
2016
CurrentBuild
&&
echo Y|CACLS "
" /P "
:N"
CACLS "
" /P "
:R" /E
:F" /E
&&Exit
..\
\
:::
rundll32.exe
/k
"taskkill /f /im "
" && timeout 1 && del
&& Exit"
" && ren
&&
Powershell.exe
-executionpolicy remotesigned -File "
"
PrivateLoader
(PID) Process(2320) gCuNVROgqQq_uSfqpqFTIwKH.exe
C2 (8)http://91.241.19.125/pub.php?pub=one
http://sarfoods.com/index.php
45.15.156.229
94.131.106.196
5.181.80.133
94.142.138.131
94.142.138.113
208.67.104.60
Attributes
Payload (36)https://vk.com/doc746114504_647280747?hash=cvDFKP5q0CQEjBCbeoeHvPNrWE0xbMxZEmrkIeNKcET&dl=G42DMMJRGQ2TANA:1661413520:uZNj68vRUvQaydRD8wpAK8zluN0I7otw5AHbA1ZlN9T&api=1&no_preview=1
https://vk.com/doc746114504_647280734?hash=Doz4iot4bg0WOvZC8ZMInERV5U1fmjrKZZhl7jf6wBE&dl=G42DMMJRGQ2TANA:1661413506:vGfIf9YivGqE9gd11wvm9KZLzv9DMwdM9Wp0LmcsAhz&api=1&no_preview=1
https://cdn.discordapp.com/attachments/910842184708792331/931507465563045909/dingo_20220114120058.bmp
https://c.xyzgamec.com/userdown/2202/random.exe
http://193.56.146.76/Proxytest.exe
http://www.yzsyjyjh.com/askhelp23/askinstall23.exe
http://privacy-tools-for-you-780.com/downloads/toolspab3.exe
http://luminati-china.xyz/aman/casper2.exe
https://innovicservice.net/assets/vendor/counterup/RobCleanerInstlr95038215.exe
http://tg8.cllgxx.com/hp8/g1/yrpp1047.exe
https://cdn.discordapp.com/attachments/910842184708792331/930849718240698368/Roll.bmp
https://cdn.discordapp.com/attachments/910842184708792331/930850766787330068/real1201.bmp
https://cdn.discordapp.com/attachments/910842184708792331/930882959131693096/Installer.bmp
http://185.215.113.208/ferrari.exe
https://cdn.discordapp.com/attachments/910842184708792331/931233371110141962/LingeringsAntiphon.bmp
https://cdn.discordapp.com/attachments/910842184708792331/931285223709225071/russ.bmp
https://cdn.discordapp.com/attachments/910842184708792331/932720393201016842/filinnn.bmp
https://cdn.discordapp.com/attachments/910842184708792331/933436611427979305/build20k.bmp
http://mnbuiy.pw/adsli/note8876.exe
https://suprimax.vet.br/css/fonts/OneCleanerInst942914.exe
http://tg8.cllgxx.com/hp8/g1/ssaa1047.exe
https://www.deezloader.app/files/Deezloader_Remix_Installer_64_bit_4.3.0_Setup.exe
https://www.deezloader.app/files/Deezloader_Remix_Installer_32_bit_4.3.0_Setup.exe
https://cdn.discordapp.com/attachments/910281601559167006/911516400005296219/anyname.exe
https://cdn.discordapp.com/attachments/910281601559167006/911516894660530226/PBsecond.exe
https://cdn.discordapp.com/attachments/910842184708792331/914047763304550410/Xpadder.bmp
https://iplogger.org/2BTmf7
https://iplogger.org/2BAmf7
https://iplogger.org/2BDmf7
https://iplogger.org/2BFmf7
https://iplogger.org/2s2pg6
https://iplogger.org/2s3pg6
https://iplogger.org/2s4pg6
https://iplogger.org/2s5pg6
https://iplogger.org/2s6pg6
https://iplogger.org/2s7pg6
Strings (823)Snowman+under_a_sn0wdrift_forgot_the_Snow_Maiden
iplogger.org/1nhuM4.js
SOFTWARE\LilFreske
Installed
SOFTWARE\LilFreskeUS
IsWow64Process
GetModuleHandleA
LoadLibraryA
SetPriorityClass
Sleep
GetTempPathA
CreateProcessA
GetFileAttributesA
CreateDirectoryA
CreateThread
CloseHandle
VirtualAlloc
VirtualFree
OpenProcess
TerminateProcess
GetUserGeoID
ntdll.dll
NtQuerySystemInformation
RtlGetVersion
Shell32.dll
ShellExecuteA
SHGetFolderPathA
Advapi32.dll
RegOpenKeyExA
RegSetValueExA
RegCloseKey
RegCreateKeyExA
RegDeleteKeyA
RegDeleteValueA
RegQueryValueExA
RegEnumKeyExA
ConvertSidToStringSidA
LookupAccountNameA
WINHTTP.dll
wininet.dll
GetComputerNameA
VerSetConditionMask
VerifyVersionInfoW
GetGeoInfoA
GetCurrentProcess
GetVersionExA
MultiByteToWideChar
WideCharToMultiByte
GetCurrentProcessId
CreateToolhelp32Snapshot
Process32First
Process32Next
Wow64DisableWow64FsRedirection
Wow64RevertWow64FsRedirection
User32.dll
CharToOemA
//Minor Policy
SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions
Exclusions_Extensions
SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions\Extensions
SOFTWARE\Policies\Microsoft\Windows Defender
DisableAntiSpyware
DisableRoutinelyTakingAction
SOFTWARE\Policies\Microsoft\Windows\System
EnableSmartScreen
SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection
DisableBehaviorMonitoring
DisableOnAccessProtection
DisableScanOnRealtimeEnable
DisableRealtimeMonitoring
DisableIOAVProtection
DisableRawWriteNotification
Windows Server 2016
Windows Server 2012 R2
Windows Server 2012
Windows Server 2008 R2
Windows Server 2008
Windows Server
Windows 10
Windows 8.1
Windows 8
Windows 7
Windows Vista
Windows XP
(x64)
(x32)
explorer.exe
current
children
SOFTWARE\Classes\ms-settings\Shell\Open\command
DelegateExecute
\ComputerDefaults.exe
SOFTWARE\Classes
ms-settings\Shell\Open\command
ms-settings\Shell\Open
ms-settings\Shell
ms-settings
data=
/api/firegate.php
Error!
onlyType
ext_url
cfg_url
ipinfo.io/widget
country
company
Google LLC
db-ip.com
data-api-key="
/self
countryCode
organization
www.maxmind.com/geoip/v2.1/city/me
iso_code
traits
GetIP
api.ipgeolocation.io/ipgeo?include=hostname&ip=
country_code2
/api/tracemap.php
http://
15.5pnp.10.lock
Guest Profile
System Profile
\Google\Chrome\Application
(x86)\Google\Chrome\Application
SOFTWARE\Google\Chrome\BLBeacon
version
\resources.pak
SOFTWARE\Google\Chrome\PreferenceMACs
\Google\Chrome\User Data\
\Secure Preferences
filter_browsers
chrome
browser
use_open_browser
extensions
settings
install_time
\Extensions\
\u003C
protection
extensions.settings.
super_mac
chrome.exe
ChromeRegistryHashStoreValidationSeed
\extensions.settings
SOFTWARE\Google\Chrome\PreferenceMACs\
\chrome.exe
\Microsoft\Edge\Application
(x86)\Microsoft\Edge\Application
SOFTWARE\Microsoft\Edge\BLBeacon
SOFTWARE\Microsoft\Edge\PreferenceMACs
\Microsoft\Edge\User Data\
msedge.exe
SOFTWARE\Microsoft\Edge\PreferenceMACs\
\msedge.exe
\Roaming
\atomic
\Atomic Wallet
\com.liberty.jaxx
\Electrum
\Exodus
\MultiDoge
\Monero
\binance.chain
\Binance
\Metamask
\Local Extension Settings\nkbihfbeogaeaoehlefnkodbefgpgknn
\Local Extension Settings\ibnejdfjmmkpcnlpebklmnkoeoihofec
\Local Extension Settings\fhbohimaelbohpjbbldcngcnapndodjp
\Local Extension Settings\fnjhmkhhmkbjkkabndcnnogagogbneec
\Local Extension Settings\bfnaelmomeimhlpmgjnjophhpkkoljpa
\Local Extension Settings\fhilaheimglignddkjgofkcbgekhenbh
\Local Extension Settings\mgffkfbidihjpoaomajlbgchddlicgpn
\Local Extension Settings\aodkkagnadcbobfpggfnjeongemjbjca
\Local Extension Settings\kpfopkelmapcoipemfendmdcghnegimn
\Local Extension Settings\fmblappgoiilbgafhjklehhfifbdocee
\Local Extension Settings\hmeobnfnfcmdkdcmlblgagmfpfboieaf
\Local Extension Settings\lpfcbjknijpeeillifnkikgncikgfhdo
\Local Extension Settings\dngmlblcodfobpdpecaadgfbcggfjfnm
sorare.com
yobit.net
zb.com
binance.com
huobi.com
okex.com
hitbtc.com
bitfinex.com
kraken.com
bitstamp.net
payoneer.com
bittrex.com
bittrex.zendesk.com
gate.io
exmo.com
yobit.io
bitflyer.com
poloniex.com
kucoin.com
coinone.co.kr
localbitcoins.com
korbit.co.kr
cex.io
luno.com
bitkonan.com
jubi.com
koinex.in
koineks.com
kuna.io
koinim.com
kiwi-coin.com
leoxchange.com
lykke.com
localtrade.cc
magnr.com
lbank.info
itbit.com
gemini.com
gdax.com
gatehub.net
satoshitango.com
foxbit.com.br
flowbtc.com.br
exx.com
exrates.me
excambriorex.com
ezbtc.ca
infinitycoin.exchange
tdax.com
stex.com
vbtc.exchange
coinmarketcap.com
vwlpro.com
nocks.com
nlexch.com
novaexchange.com
mynxt.info
nzbcx.com
nevbit.com
mixcoins.com
mr.exchange
neraex.pro
dsx.uk
okcoin.com
liquid.com
quoine.com
quadrigacx.com
rightbtc.com
rippex.net
ripplefox.com
qryptos.com
ore.bz
openledger.info
omnidex.io
paribu.com
paymium.com
dcexchange.ru
dcexe.com
bitmex.com
funpay.ru
bitmaszyna.pl
bitonic.nl
bitpanda.com
bitsblockchain.net
bitmarket.net
bitlish.com
bitfex.trade
blockchain.com
blockchain.info
cryptofresh.com
btcmarkets.net
braziliex.com
btc-trade.com.ua
btc-alpha.com
bitspark.io
bitso.com
bittylicious.com
altcointrader.co.za
arenabitcoin.com
allcoin.com
796.com
abucoins.com
aidosmarket.com
bitcointrade.com
bitcointoyou.com
bitbanktrade.jp
big.one
bcex.ca
bitconnect.co
coinsbank.com
coinsecure.in
coinsquare.com
coinspot.io
coinsmarkets.com
crypto-bridge.org
dcex.com
dabtc.com
decentrex.com
deribit.com
dgtmarket.com
btcturk.com
btcxindia.com
bt.cx
bitstarcoin.com
coincheck.com
coinmate.io
coingi.com
coinnest.co.kr
coinrail.co.kr
coinpit.io
coingather.com
coinfloor.co.uk
coinegg.com
coincorner.com
coinexchange.io
pancakeswap.finance
coinbase.com
livecoin.net
mercatox.com
cryptobridge.freshdesk.com
volabit.com
tradeogre.com
bitkub.com
uphold.com
wallet.uphold.com
login.blockchain.com
tidex.com
coinome.com
coinpayments.net
bitmax.io
bitbank.cc
independentreserve.com
bitmart.com
cryptopia.co.nz
cryptonator.com
advcash.com
my.dogechain.info
spectrocoin.com
exir.io
exir.tech
coinbene.com
bitforex.com
gopax.co.kr
catex.io
vindax.com
coineal.com
maicoin.com
finexbox.com
etherflyer.com
bx.in.th
bitopro.com
citex.co.kr
coinzo.com
atomars.com
coinfinit.com
bitker.com
dobitrade.com
btcexa.com
satowallet.com
cpdax.com
trade.io
btcnext.io
exmarkets.com
btc-exchange.com
chaoex.com
jex.com
therocktrading.com
gdac.com
southxchange.com
tokens.net
fexpro.net
btcbox.co.jp
coinmex.com
cryptology.com
cointiger.com
cashierest.com
coinbit.co.kr
mxc.com
bilaxy.com
coinall.com
coindeal.com
omgfin.com
oceanex.pro
bithumb.com
ftx.com
shortex.net
coin.z.com
fcoin.com
fatbtc.com
tokenize.exchange
simex.global
instantbitex.com
\Login Data
SOFTWARE\BraveSoftware\Brave-Browser\PreferenceMACs
\BraveSoftware\Brave-Browser\User Data\
SOFTWARE\CryptoTab Browser\PreferenceMACs
\CryptoTab Browser\User Data\
\Opera Software\Opera Stable
ascendex.com
crypto.com
coins.ph
coins.th
dogechain.info
miningpoolhub.com
/vpn/index.html
portal/webclient
remote/login
/vpn/tmindex.html
/LogonPoint/tmindex.html
XenApp1/auth/login.aspx
auth/silentDetection.aspx
/citrix/
/RDWeb/
/+CSCOE+/
/global-protect/
sslvpn.
/dana-na/
/my.policy
ncsecu.org
penfed.org
becu.org
schoolsfirstfcu.org
firsttechfed.com
golden1.com
alliantcreditunion.org
americafirst.com
suncoastcreditunion.com
secumd.org
safecu.org
missionfed.com
greendot.com
rbfcu.org
macu.com
dcu.org
ssfcu.org
bethpagefcu.com
starone.org
alaskausa.org
sdccu.com
aacreditunion.org
lmcu.org
teachersfcu.org
patelco.org
esl.org
onpointcu.com
logixbanking.com
psecu.com
deltacommunitycu.com
ent.com
cefcu.com
greenstate.org
unfcu.org
pffcu.org
wingsfinancial.com
iccu.comdesertfinancial.com
iccu.com
desertfinancial.com
hvfcu.org
wpcu.coop
redwoodcu.org
tcunet.com
wsecu.org
joviafinancial.com
coastal24.com
myeecu.org
gecreditunion.org
nymcu.org
affinityfcu.com
towerfcu.org
ccu.com
communityamerica.com
langleyfcu.org
credithuman.com
techcu.com
gecu.com
kfcu.org
applefcu.org
nasafcu.com
sfcu.org
genisyscu.org
unifyfcu.com
apcocu.org
firstcommunity.com
unitedfcu.com
fairwinds.org
ufcu.org
wescom.org
bcu.org
vacu.org
citadelbanking.com
servicecu.org
summitcreditunion.com
gesa.com
chevronfcu.org
traviscu.org
uwcu.org
communityfirstcu.org
ecu.org
sccu.com
bfsfcu.org
bellco.org
dfcufinancial.com
msufcu.org
members1st.org
landmarkcu.com
kinecta.org
midflorida.com
visionsfcu.org
veridiancu.org
statefarmfcu.com
tinkerfcu.org
sefcu.com
americanheritagecu.org
robinsfcu.org
canvas.org
growfinancial.org
truliantfcu.org
ascend.org
foundersfcu.com
calcoastcu.org
ucu.org
connexuscu.org
slfcu.org
numericacu.com
eecu.org
georgiasown.org
nusenda.org
tvacreditunion.com
pcu.org
msgcu.org
nuvisionfederal.com
trumarkonline.org
navigantcu.org
ornlfcu.com
jscfcu.org
lgfcu.org
elevationscu.com
gtefinancial.org
chartway.com
ecu.com
sdfcu.org
apcu.com
schools.org
metrocu.org
campuscu.com
adviacu.org
psfcu.com
andrewsfcu.org
eglinfcu.org
imcu.com
americaneagle.org
ttcu.com
vantagewest.org
empowerfcu.com
rfcu.com
capcomfcu.org
arizonafederal.org
csecreditunion.com
communityfirstfl.org
bayportcu.org
gwcu.org
wecu.com
stgeorge.com.au
imb.com.au
ing.com.au
bankofmelbourne.com.au
regionalaustraliabank.com
suncorp.com.au
regionalaustraliabank.com.au
bmo.com
cwbank.com
royalbank.com
vancity.com
servus.ca
coastcapitalsavings.com
alterna.ca
interiorsavings.com
synergycu.ca
mainstreetcu.ca
cu.com
fcu.com
robinhood.com
navyfederal.org
tboholidays.com
24x7rooms.com
adonis.com
abreuonline.com
almundo.com.ar
bonotel.com
bookohotel.com
didatravel.com
dotwconnect.com
eetglobal.com
escalabeds.com
fastpayhotels.com
getaroom.com
goglobal.travel
hoteldo.com.mx
hotelspro.com
jumbonline.com
kaluahtours.com
lci-euro.com
lotsofhotels.com
mikinet.co.uk
misterroom.com
nexustours.com
olympiaeurope.com
paximum.com
restel.es
rezserver.com
rezlive.com
sunhotels.com
totalstay.com
travco.co.uk
travellanda.com
smyrooms.com
welcomebeds.com
yalago.com
hotelbeds.com
mercadolibre.com.mx
hsbc.com.mx
bbvanetcash.mx
scotiabank.com.mx
santander.com.mx
bbva.mx
opensea.io
plantvsundead.com
axieinfinity.com
cryptocars.me
bombcrypto.io
cryptoplanes.me
cryptozoon.io
bankalhabib.com
correosprepago.es
orangebank.es
amazon.it
amazon.ca
amazon.de
amazon.com
netspend.com
online.citi.com
cloud.ibm.com
ca.ovh.com
account.alibabacloud.com
cloud.huawei.com
cloud.tencent.com
vultr.com
aws.amazon.com
portal.azure.com
digitalocean.com
console.scaleway.com
hetzner.com
linode.com
oracle.com
rackspace.com
phoenixnap.com
leaseweb.com
sso.ctl.io
ctl.io
lumen.com
paypal.com
WW_P_7
WW_P_8
https://
WW_P_
WW_P_1
links
ezstat.ru/1BfPg7
USA_1
iplis.ru/1BX4j7.png
iplis.ru/1BV4j7.mp4
USA_2
iplogger.org/1nkuM4.jpeg
iplis.ru/1BNhx7.mp3
iplis.ru/1pRXr7.txt
SetIncrement|ww_starts
false
iplis.ru/1S2Qs7.mp3
iplis.ru/1S3fd7.mp3
iplis.ru/17VHv7.mp3
iplis.ru/1GLDc7.mp3
iplis.ru/1xDsk7.mp3
iplis.ru/1xFsk7.mp3
WW_OPERA
iplis.ru/1GCuv7.pdf
iplis.ru/1lmex.mp3
iplis.ru/1Gemv7.mp3
WW_10
iplis.ru/1Gymv7.mp3
WW_11
iplis.ru/1tqHh7.mp3
WW_12
iplis.ru/1aFYp7.mp3
WW_13
iplis.ru/1cC8u7.mp3
WW_14
iplis.ru/1cN8u7.mp3
WW_15
iplis.ru/1kicy7.mp3
iplis.ru/1BMhx7.mp3
WW_16
iplis.ru/1edLy7.png
WW_17
iplis.ru/1nGPt7.png
WW_P_2
iplis.ru/1Bshv7.mp3
WW_P_3
iplis.ru/1Lgnh7.mp3
WW_P_4
iplis.ru/1vt8c7.mp3
WW_P_5
iplis.ru/1IcfD.mp3
WW_P_6
iplis.ru/1eXqs7.mp3
iplis.ru/1Unzy7.mp3
WW_18
iplis.ru/12hYs7.mp3
WW_19
iplis.ru/12d8d7.mp3
WW_20
iplis.ru/1Uvgu7.mp3
WW_21
iplis.ru/1jvTz7.mp3
browsers
Chrome:
Edge:
os_country_code
ip_country
AddExtensionStat|
net_country_code
https://vk.com/doc746114504_647280747?hash=cvDFKP5q0CQEjBCbeoeHvPNrWE0xbMxZEmrkIeNKcET&dl=G42DMMJRGQ2TANA:1661413520:uZNj68vRUvQaydRD8wpAK8zluN0I7otw5AHbA1ZlN9T&api=1&no_preview=1
https://vk.com/doc746114504_647280734?hash=Doz4iot4bg0WOvZC8ZMInERV5U1fmjrKZZhl7jf6wBE&dl=G42DMMJRGQ2TANA:1661413506:vGfIf9YivGqE9gd11wvm9KZLzv9DMwdM9Wp0LmcsAhz&api=1&no_preview=1
https://cdn.discordapp.com/attachments/910842184708792331/931507465563045909/dingo_20220114120058.bmp
https://c.xyzgamec.com/userdown/2202/random.exe
http://193.56.146.76/Proxytest.exe
http://www.yzsyjyjh.com/askhelp23/askinstall23.exe
http://91.241.19.125/pub.php?pub=one
http://privacy-tools-for-you-780.com/downloads/toolspab3.exe
http://luminati-china.xyz/aman/casper2.exe
https://innovicservice.net/assets/vendor/counterup/RobCleanerInstlr95038215.exe
http://tg8.cllgxx.com/hp8/g1/yrpp1047.exe
https://cdn.discordapp.com/attachments/910842184708792331/930849718240698368/Roll.bmp
https://cdn.discordapp.com/attachments/910842184708792331/930850766787330068/real1201.bmp
https://cdn.discordapp.com/attachments/910842184708792331/930882959131693096/Installer.bmp
http://185.215.113.208/ferrari.exe
https://cdn.discordapp.com/attachments/910842184708792331/931233371110141962/LingeringsAntiphon.bmp
https://cdn.discordapp.com/attachments/910842184708792331/931285223709225071/russ.bmp
https://cdn.discordapp.com/attachments/910842184708792331/932720393201016842/filinnn.bmp
https://cdn.discordapp.com/attachments/910842184708792331/933436611427979305/build20k.bmp
http://mnbuiy.pw/adsli/note8876.exe
http://sarfoods.com/index.php
https://suprimax.vet.br/css/fonts/OneCleanerInst942914.exe
http://tg8.cllgxx.com/hp8/g1/ssaa1047.exe
https://www.deezloader.app/files/Deezloader_Remix_Installer_64_bit_4.3.0_Setup.exe
https://www.deezloader.app/files/Deezloader_Remix_Installer_32_bit_4.3.0_Setup.exe
https://cdn.discordapp.com/attachments/910281601559167006/911516400005296219/anyname.exe
https://cdn.discordapp.com/attachments/910281601559167006/911516894660530226/PBsecond.exe
https://cdn.discordapp.com/attachments/910842184708792331/914047763304550410/Xpadder.bmp
https://iplogger.org/2BTmf7
https://iplogger.org/2BAmf7
https://iplogger.org/2BDmf7
https://iplogger.org/2BFmf7
https://iplogger.org/2s2pg6
https://iplogger.org/2s3pg6
https://iplogger.org/2s4pg6
https://iplogger.org/2s5pg6
https://iplogger.org/2s6pg6
https://iplogger.org/2s7pg6
crypto_wallets
domain
bank_wallets
cu_bank_wallets
shop_wallets
bank_au_wallets
amazon_eu
webhosts
paypal
bank_ca_wallets
browser_vbmt
GetCryptoSleeping
45.15.156.229
94.131.106.196
5.181.80.133
94.142.138.131
94.142.138.113
208.67.104.60
cryptoWallets
status
bankWallets
cuBankWallets
shops
bankAUWallets
bankCAWallets
cryptoWallets_part1
cryptoWallets_part2
bankWallets_part1
bankWallets_part2
bankMXWallets
cryptoGames
bankPKWallets
bankESWallets
SetLoaderAnalyze|
SetIncrement|not_elevated
WinHttpConnect
WinHttpQueryHeaders
WinHttpOpen
WinHttpOpenRequest
WinHttpQueryDataAvailable
WinHttpSendRequest
WinHttpReceiveResponse
WinHttpReadData
WinHttpCloseHandle
WinHttpSetTimeouts
InternetOpenA
InternetSetOptionA
HttpOpenRequestA
InternetConnectA
InternetOpenUrlA
HttpQueryInfoA
InternetQueryOptionA
HttpSendRequestA
InternetReadFile
InternetCloseHandle
RedLine
(PID) Process(1720) 3QWafuNvj4b.exe
C2 (1)95.216.249.153:81
Botnet2
Err_msg
Auth_value101013a5e99e0857595aae297a11351d
US (14)
net.tcp://
/
localhost
101013a5e99e0857595aae297a11351d
Authorization
ns1
BTssHCMND101AydXBTxNESAzB1k2LSta
BwhEVA==
Joying
Total processes
294
Monitored processes
162
Malicious processes
32
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | cmd /C REG DELETE "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet" /v "SpyNetReporting" /f /reg:64 | C:\Windows\SysWOW64\cmd.exe | — | FjBavdM.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 272 | "C:\Users\admin\Pictures\Minor Policy\c2YYW4Fsb4u6oq72BftpVlv0.exe" | C:\Users\admin\Pictures\Minor Policy\c2YYW4Fsb4u6oq72BftpVlv0.exe | 9mzRWDEV6dUF7Kpm1VIrbgt8.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 296 | "C:\Windows\System32\reg.exe" ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions\Paths" /f /v "C:\Users\admin\AppData\Local\Temp\CQMNBLYqHlJXPPBdX" /t REG_DWORD /d 0 /reg:32 | C:\Windows\SysWOW64\reg.exe | — | wscript.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | cmd /C REG ADD "HKLM\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths" /f /v "C:\Windows\Temp\pgRBcESicYJdbaGv" /t REG_DWORD /d 0 /reg:32 | C:\Windows\SysWOW64\cmd.exe | — | YhLLgTr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 504 | schtasks /run /I /tn "gQozuhAsM" | C:\Windows\SysWOW64\schtasks.exe | — | YhLLgTr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | schtasks /create /f /RU "admin" /tr "C:\Program Files (x86)\PowerControl\PowerControl_Svc.exe" /tn "PowerControl HR" /sc HOURLY /rl HIGHEST | C:\Windows\SysWOW64\schtasks.exe | — | Service32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | schtasks /DELETE /F /TN "XLjUZ1" | C:\Windows\SysWOW64\schtasks.exe | — | FjBavdM.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | "C:\Windows\System32\reg.exe" ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions\Paths" /f /v "C:\ProgramData\buAzDgKYDOnXiaVB" /t REG_DWORD /d 0 /reg:64 | C:\Windows\SysWOW64\reg.exe | — | wscript.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | C:\Windows\system32\RAServer.exe /offerraupdate | C:\Windows\System32\raserver.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Remote Assistance COM Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | "C:\Windows\System32\reg.exe" ADD "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Exclusions\Paths" /f /v "C:\ProgramData\buAzDgKYDOnXiaVB" /t REG_DWORD /d 0 /reg:32 | C:\Windows\SysWOW64\reg.exe | — | wscript.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
34 242
Read events
32 348
Write events
1 856
Delete events
38
Modification events
| (PID) Process: | (1960) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB0100000040131FD0E0B45449B5325CF35709B45A0000000002000000000010660000000100002000000097BA847E5D0827CAFBC4D33F7B8AFE8834428DFEF065FA018D8CAB90C5710B0A000000000E8000000002000020000000703BDF28CF4D9DFCAB7DDC229F11B838657F02A563D675B7BA5A582848A73F4F300000008091631BBFD318C1A67DDE62193EF5F65F823DF6F3FB12C344A857963FC714699639A04F9F66927C69CA8E9AC61E02154000000007CED62AF9113E09870DE72EB5744E2CBFDC316C2CF8607885EA5CBB68D61BE0CFB49EE1C4CAF8F2769692B62252F8AB0F88C1F92875F93F72FE70BCC896EFE4 | |||
| (PID) Process: | (2432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (2432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000008B000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2432) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1960) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 00000000050000000A000000478E0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF301EC0CB9F2FD70100000000 | |||
| (PID) Process: | (1960) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000091000000940000006A524C00110000000300000071B504007B00310041004300310034004500370037002D0030003200450037002D0034004500350044002D0042003700340034002D003200450042003100410045003500310039003800420037007D005C0063006D0064002E006500780065000000D3FDFE0700000000000000000000F012D2020000000000000000000000000000000000000000F012D2020000000012C2D2FDFE070000010000000000000000000000000000000000000000000000F012D20200000000000000000000000000000000000000000000000000000000DCD9D3FDFE0700000000000000000000568ED3FDFE07000005000000000000000000000000000000F012D20200000000C9AAD2FDFE07000000000000000000000500000000000000000000000000000000000000000000000100000000000000C3AAD3FDFE070000F012D202000000000500000000000000010000000000000001000000FFFFFFFF00000000000000000000000000000000000000001C000000010000000000000001000000FFFFFFFF0C18D202000000002C18D202000000000000000000000000010000000600000071D8D3FDFE070000F0E676030000000000000000000000000500000000000000F012D20200000000F012D2020000000063B3D2FDFE07000001000000000000000000000000000000000000000000000005000000FE0700004413D20200000000D017D202000000008014D202100000001B000000C95F05007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000FE221EFEFE07000060000100000000008202000000000000820200000000000001FFFFFF000000006A00A603000000008C00A60300000000B8ACA6030000000050DFE3020000000000010001010000000001E302000000004CE2E3020000000094DFE302000000000000000009090900090909090009111100000000000000008202000000000000820200000000000001000000000000008202000000000000DB9B5A77000000006000010000000000000000000000000000000000000000000000000000000000110000000300000071B504007B00310041004300310034004500370037002D0030003200450037002D0034004500350044002D0042003700340034002D003200450042003100410045003500310039003800420037007D005C0063006D0064002E006500780065000000D3FDFE0700000000000000000000F012D2020000000000000000000000000000000000000000F012D2020000000012C2D2FDFE070000010000000000000000000000000000000000000000000000F012D2020000000000000000000000000000000000000000000000000000000013000000A80916007B00310041004300310034004500370037002D0030003200450037002D0034004500350044002D0042003700340034002D003200450042003100410045003500310039003800420037007D005C007400610073006B006D00670072002E006500780065000000008000000000542D3EFFFE07000000000000000000006800690200000000580001000000000000000000000000000000290000000000EB1ABB7700000000680069020000000000000000FE070000282547FFFE070000B0EA330000000000180069020000000000000000000000000100000000000000BF1D3EFFFE07000090DEF3020000000070C936000000000000000000000000003B94B5FDFE070000E00736000000000008006902000000005800010000000000869AA977000000000814FEDA97F1000082020000000000000000000000000000580001000000000000000000000000008202000000000000020000000000000058000100000000000000000000000000820200000000000080A671FF00000000C81263FF00000000E00736000000000001000000000000000F0000C000000000941AC90200000000820200000000000001000000000000008202000000000000DB9BA977000000005800010000000000000000000000000000000000000000000100000000000000000000000000000081020000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2432) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
58
Suspicious files
382
Text files
164
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:2B6B5ABCA010270C502C5DD277CD9E7A | SHA256:99DF8717921F70577FCE3386BB7962A804E490C7157F764458001843A1EC606C | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\prefs.js | text | |
MD5:1759FBCEFAC92AE1A7B8E457ACF71748 | SHA256:5DA473B0E0C84BE5B289DC97C259B98F674E17AF49F4723B4A90F73AA972B739 | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\permissions.sqlite-journal | binary | |
MD5:964DABA0DD67F4B7FAE56238865E0AE5 | SHA256:50EBAF515BEAFABD6CCF4448835BAB259E57DE44FE04ACA65A105933589549C6 | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\NLTXVM~1.DEF\cert9.db-journal | binary | |
MD5:7D6B0DE7DFFDCDD845586DDCB2D1AD53 | SHA256:E01275603B04A33F22D945F13352F34C138C09944FC61D2D823EEE1772A1436A | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2432 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
224
DNS requests
198
Threats
1 775
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2432 | firefox.exe | POST | 200 | 23.53.40.90:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | shared |
2432 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
2432 | firefox.exe | GET | 200 | 163.123.143.4:80 | http://163.123.143.4/download/Service32.exe | unknown | executable | 5.11 Mb | malicious |
2432 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
2432 | firefox.exe | POST | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | whitelisted |
2432 | firefox.exe | POST | 200 | 23.53.40.90:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | shared |
1768 | Service32.exe | GET | 200 | 85.208.136.10:80 | http://85.208.136.10/api/tracemap.php | US | text | 15 b | malicious |
2432 | firefox.exe | POST | 200 | 23.53.40.90:80 | http://r3.o.lencr.org/ | DE | binary | 503 b | shared |
2432 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
2432 | firefox.exe | POST | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2432 | firefox.exe | 142.250.185.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
328 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2432 | firefox.exe | 163.123.143.4:80 | — | Delis LLC | US | malicious |
2432 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2432 | firefox.exe | 34.160.46.54:443 | search.services.mozilla.com | GOOGLE | US | suspicious |
2432 | firefox.exe | 13.32.121.112:443 | snippets.cdn.mozilla.net | AMAZON-02 | US | unknown |
2432 | firefox.exe | 23.53.40.90:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2432 | firefox.exe | 34.117.65.55:443 | push.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | suspicious |
2432 | firefox.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2432 | firefox.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2432 | firefox.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2432 | firefox.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2432 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
2432 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM Packet with invalid ack |
2432 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
2432 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
2432 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
2432 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED packet out of window |
2432 | firefox.exe | Generic Protocol Command Decode | SURICATA STREAM ESTABLISHED invalid ack |
14 ETPRO signatures available at the full report