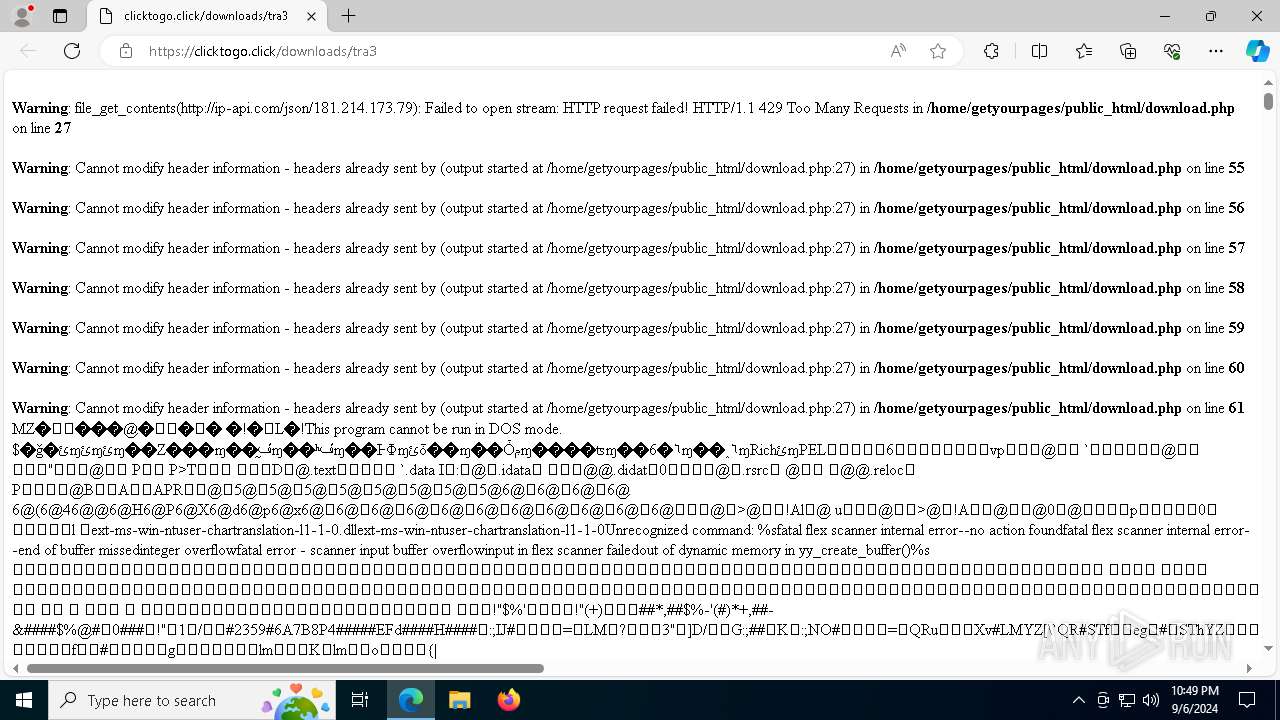
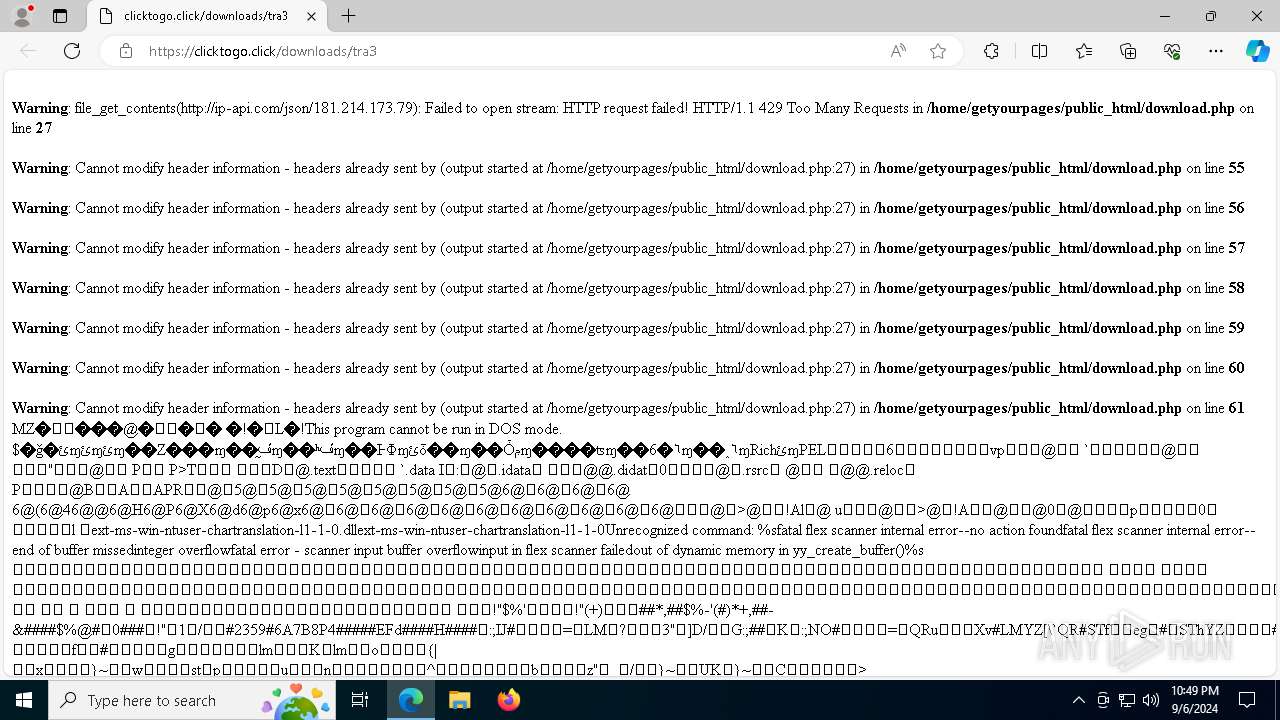
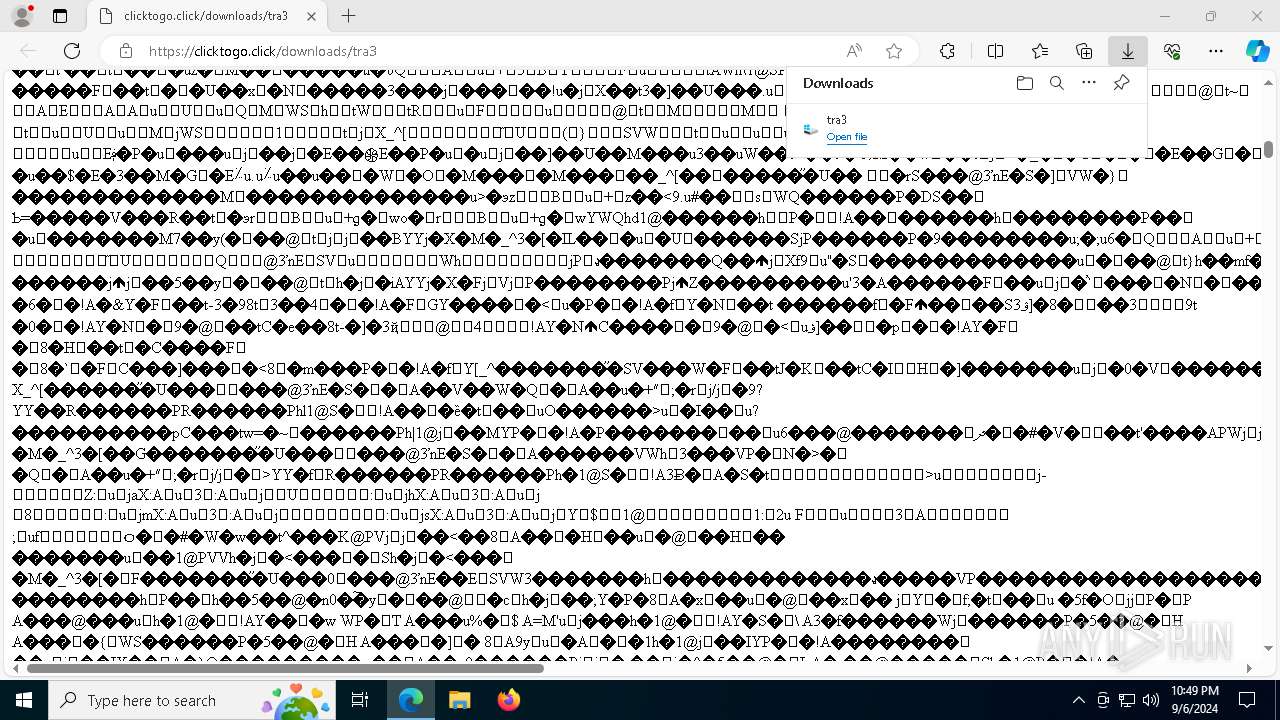
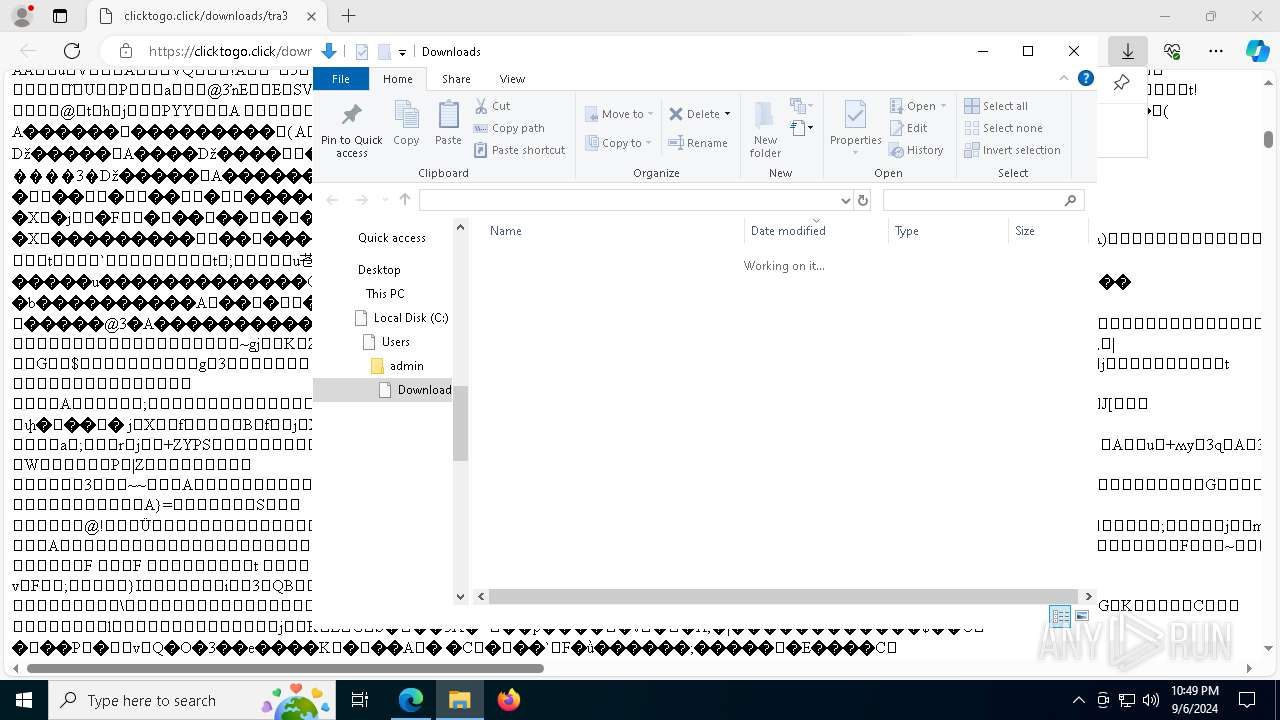
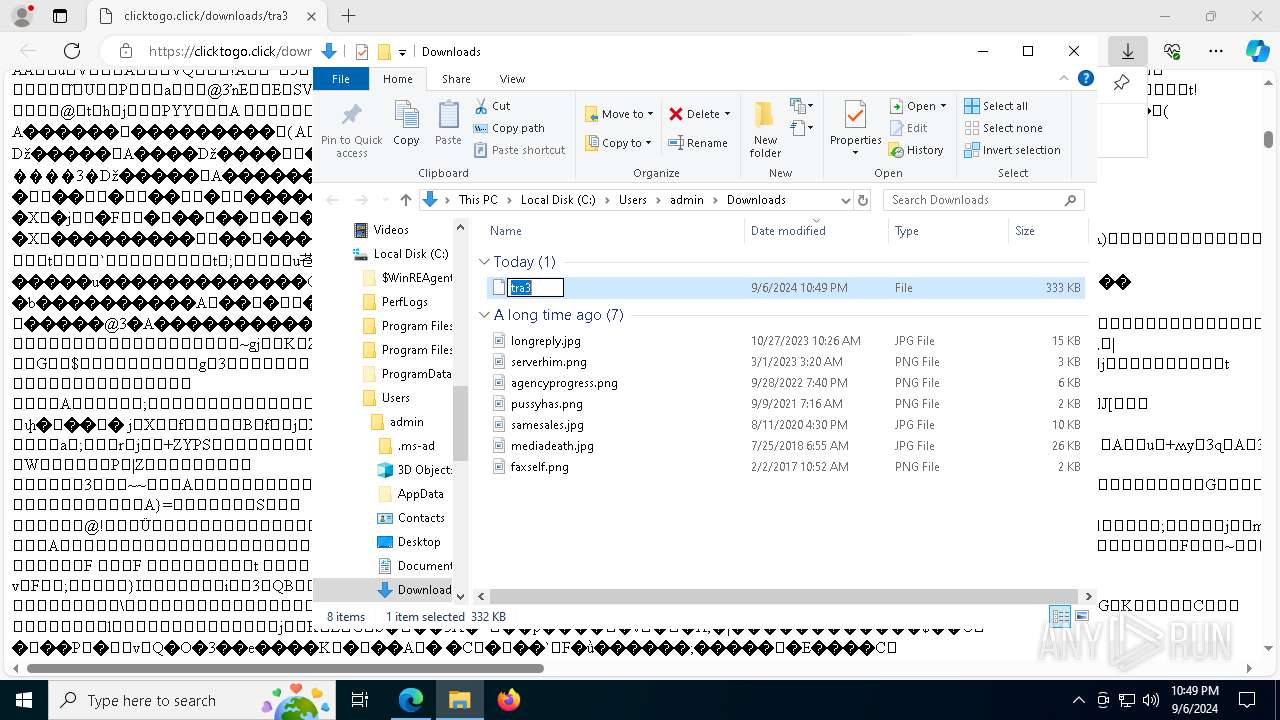
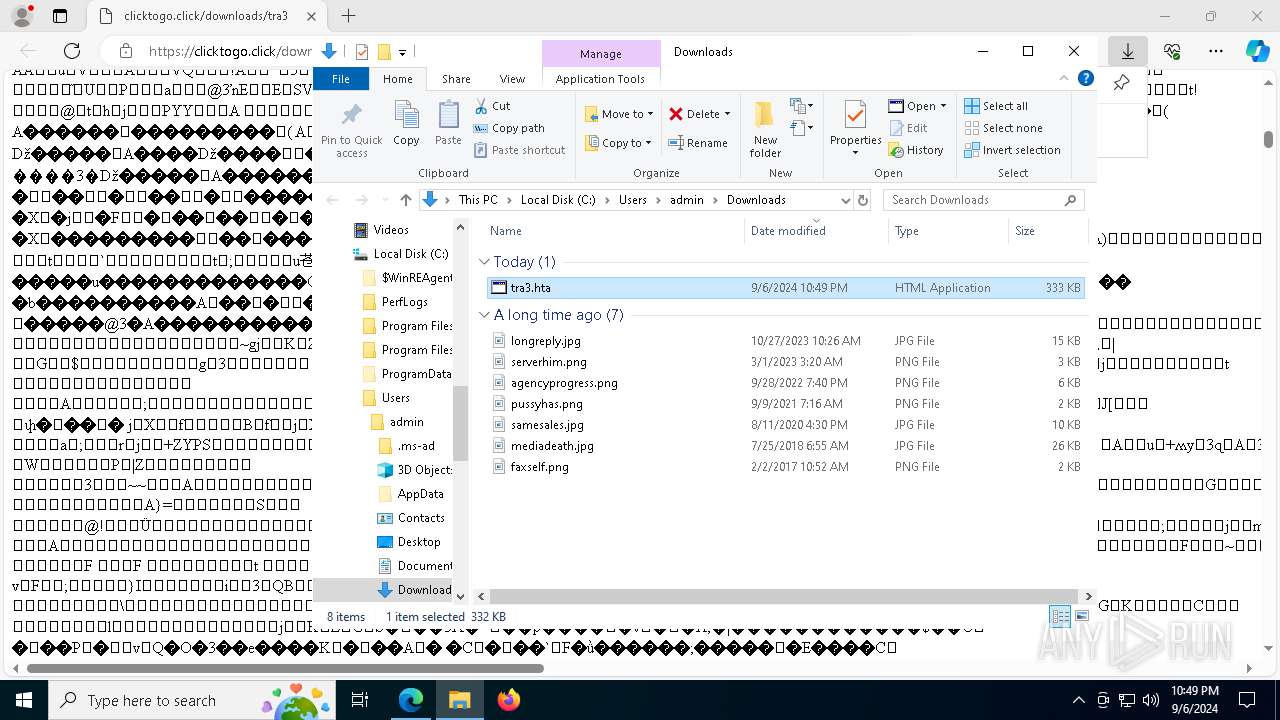
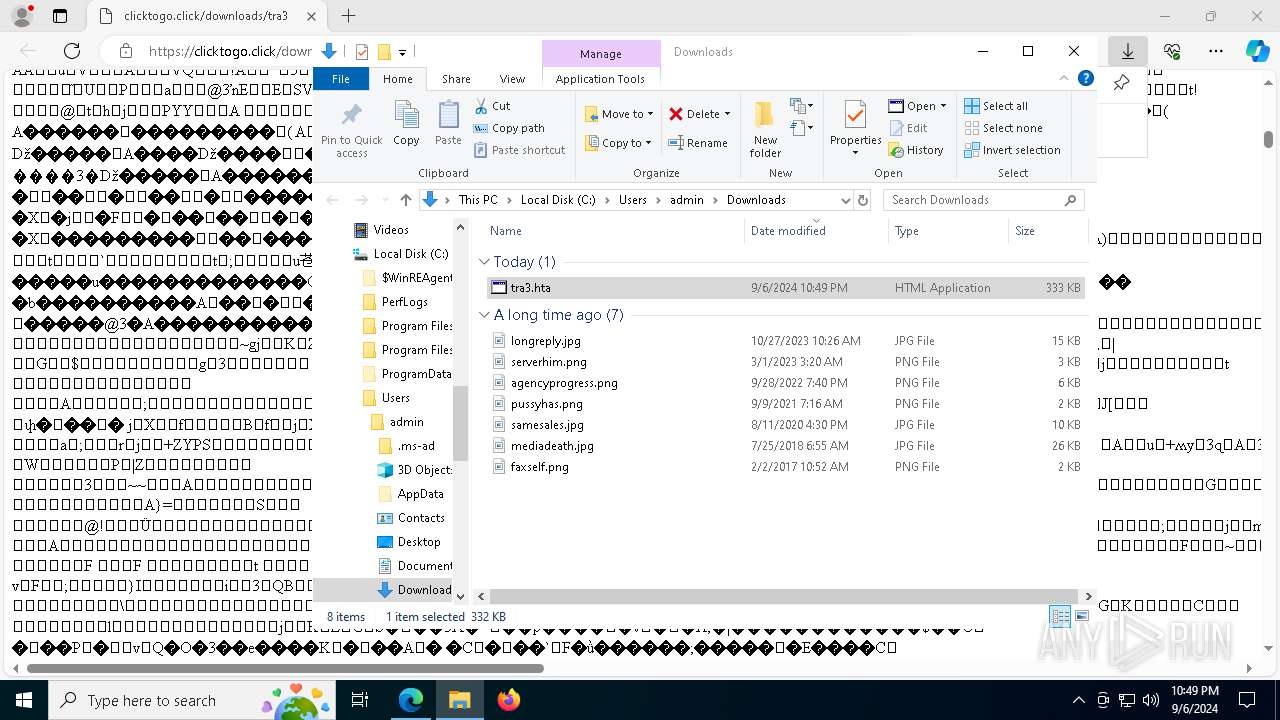
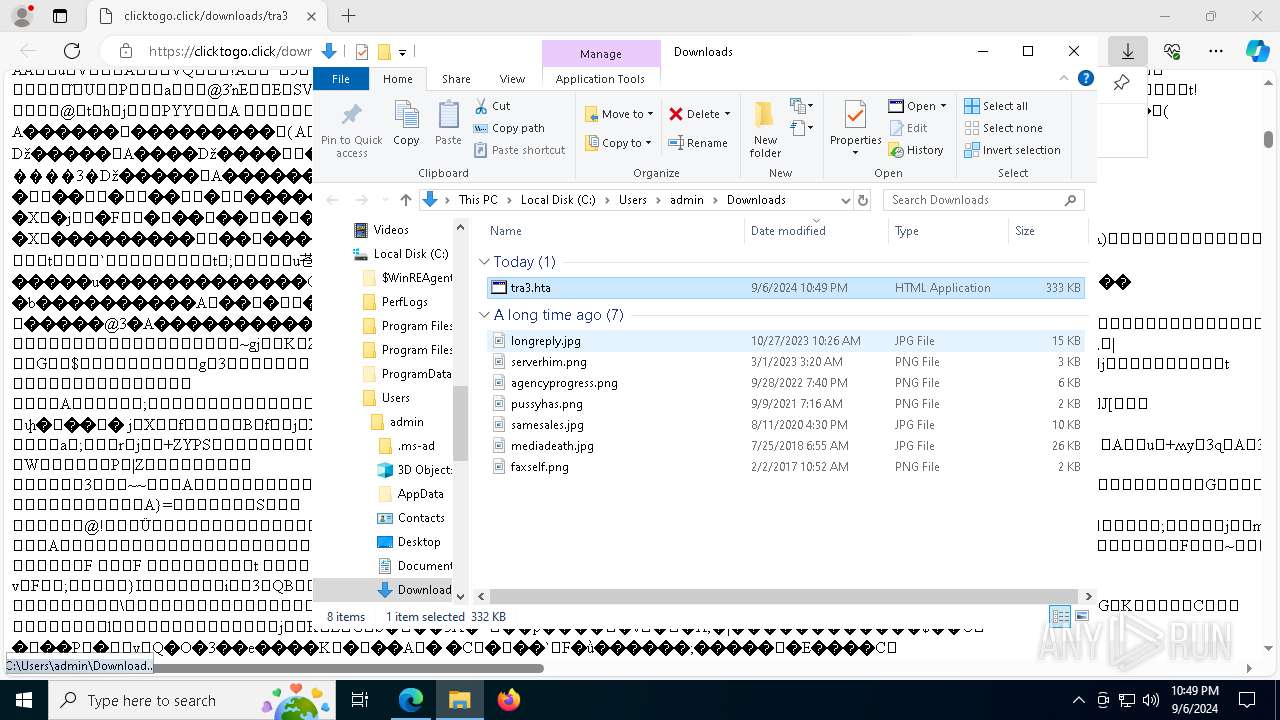
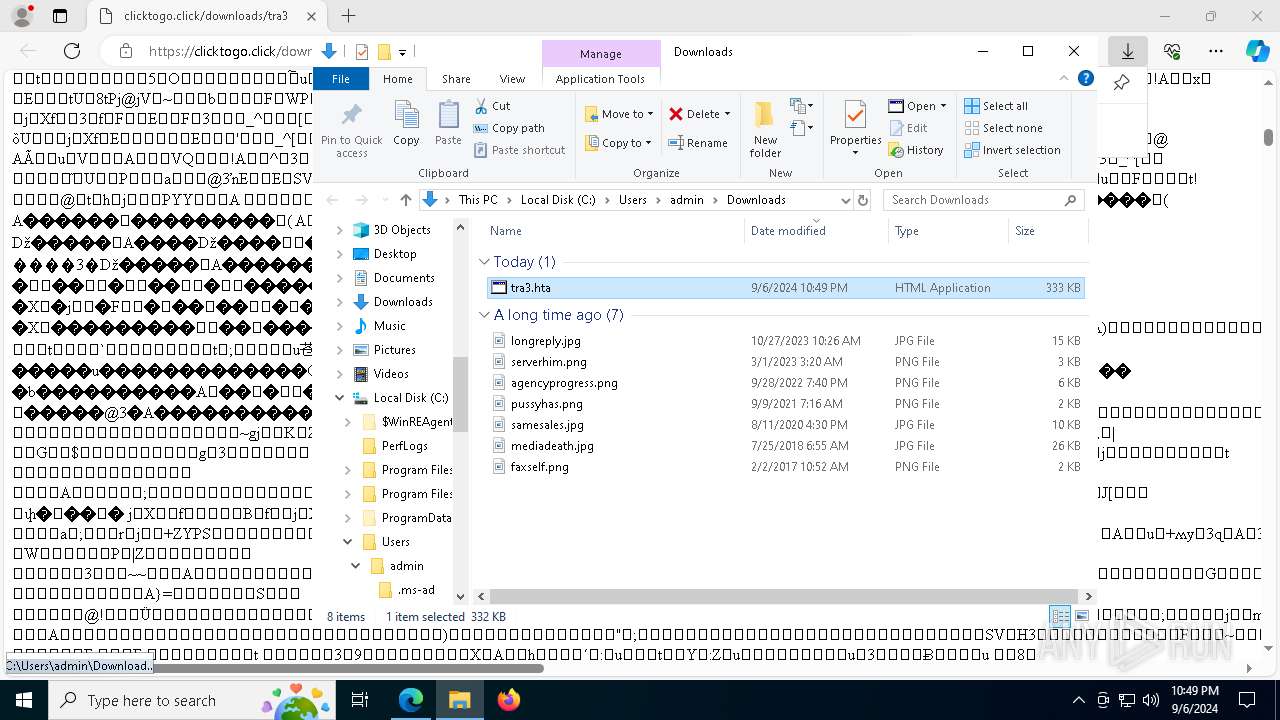
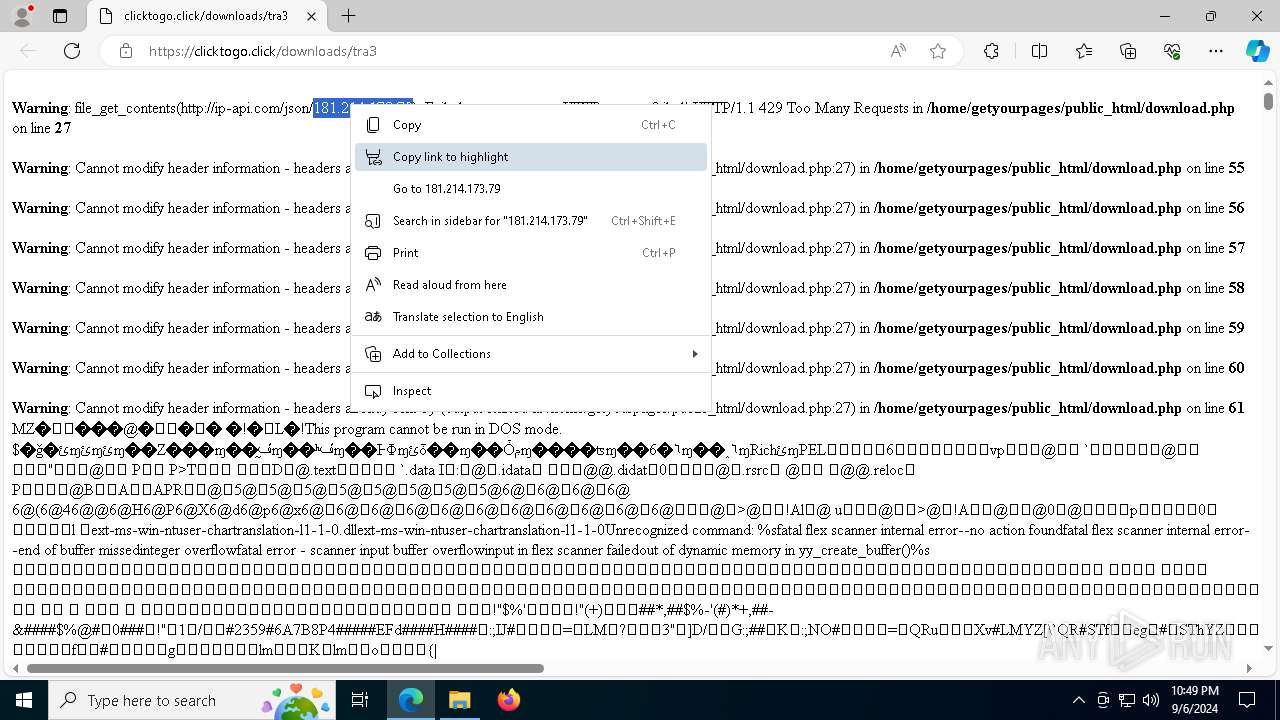
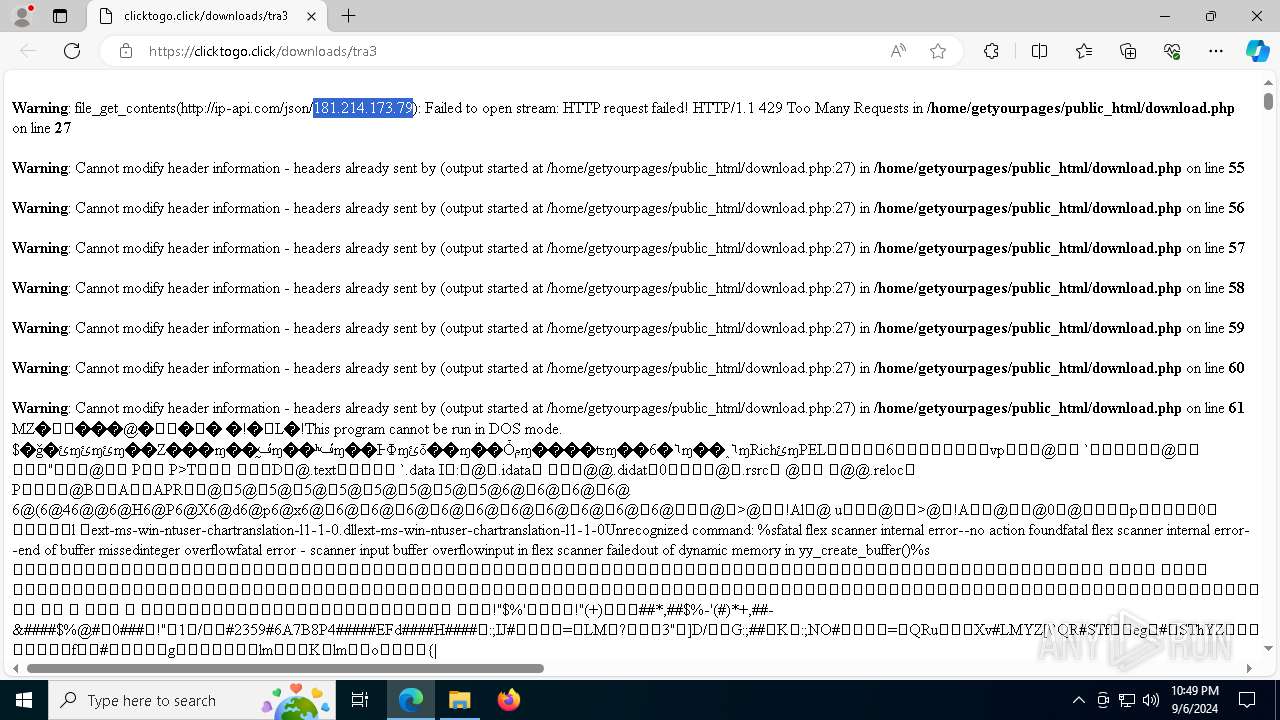
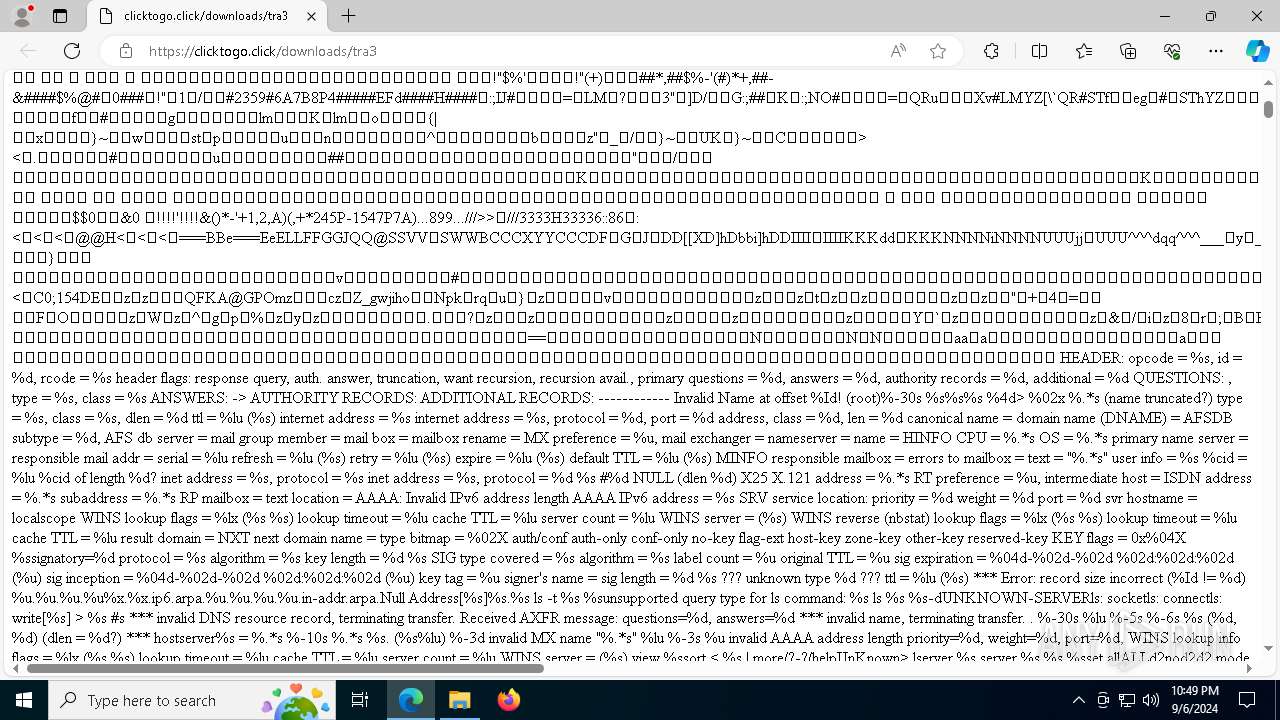
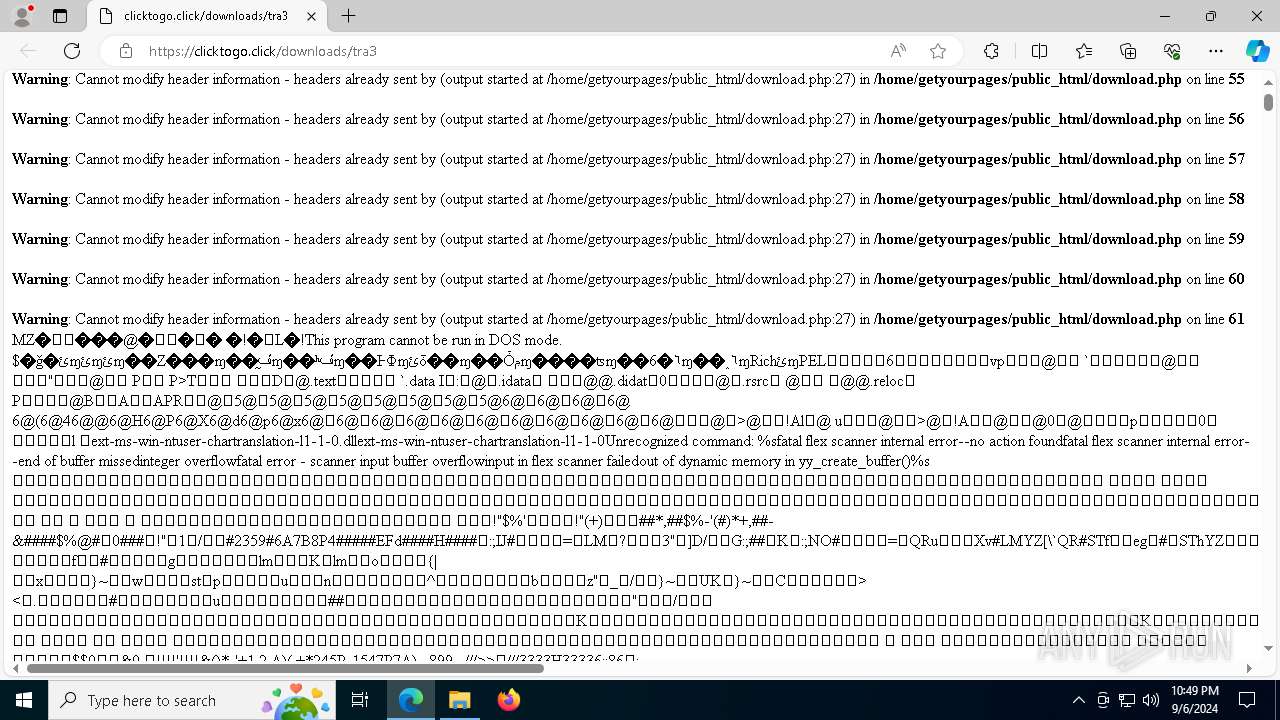
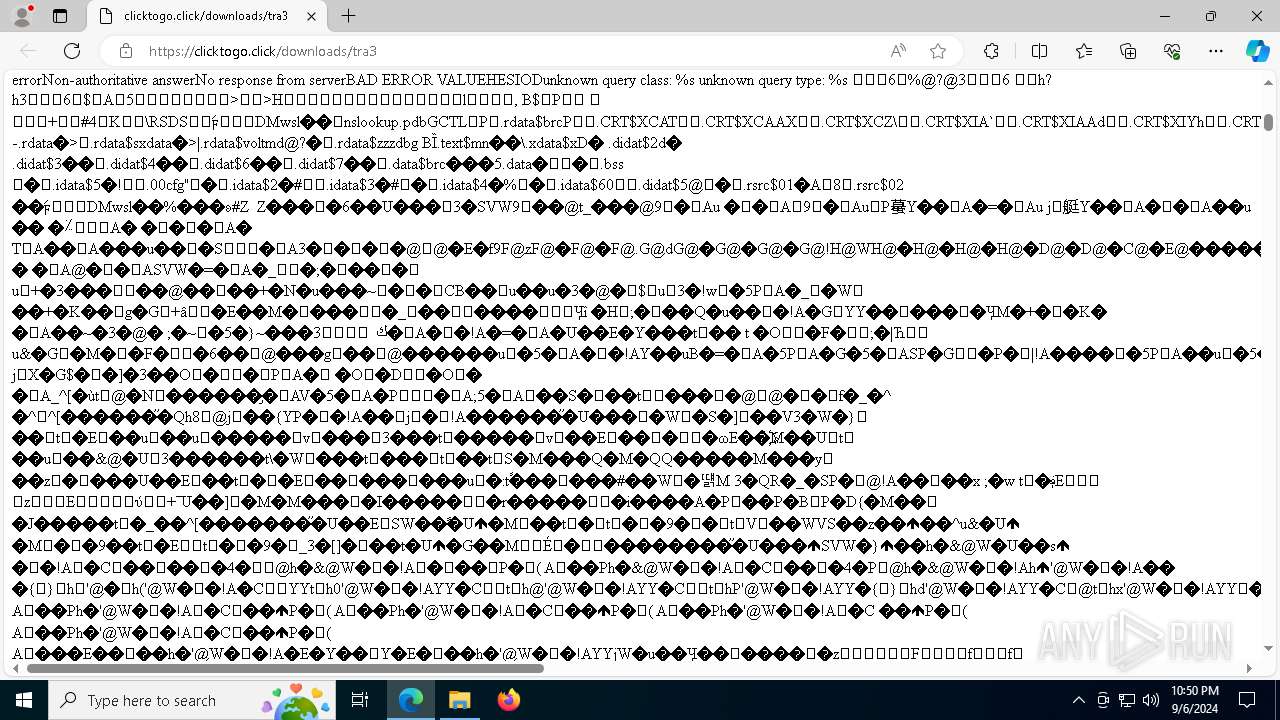
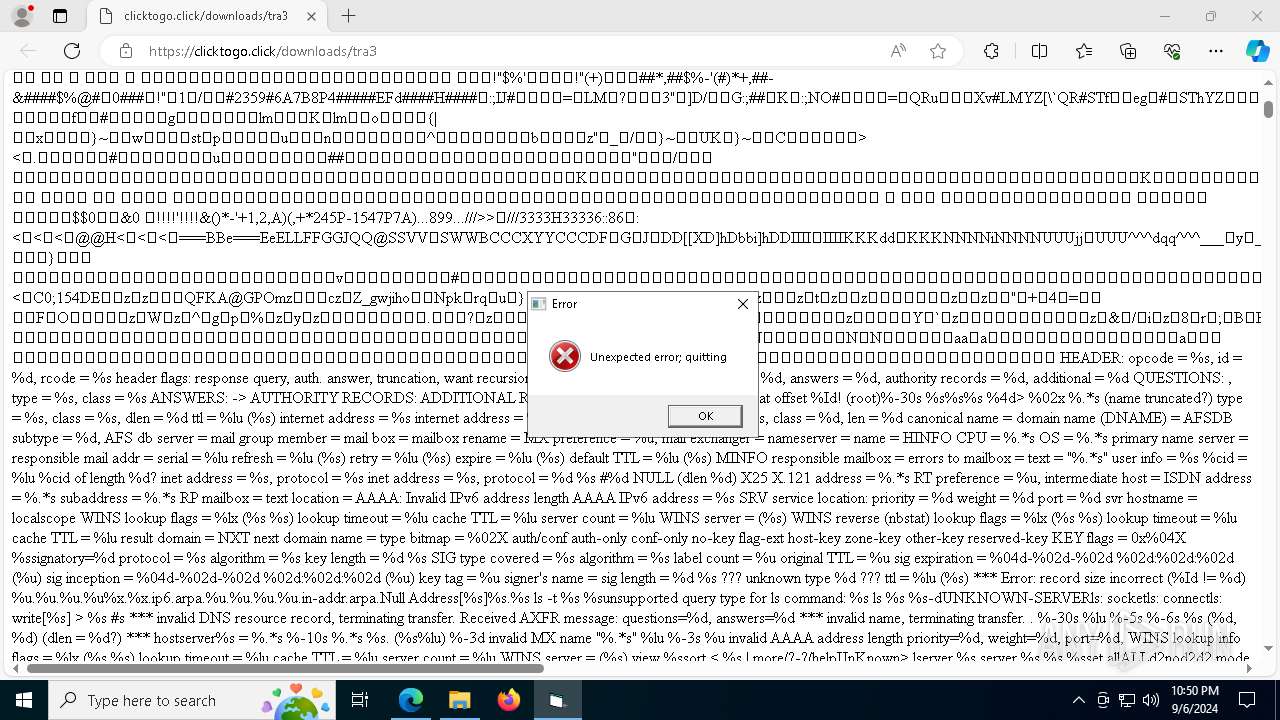
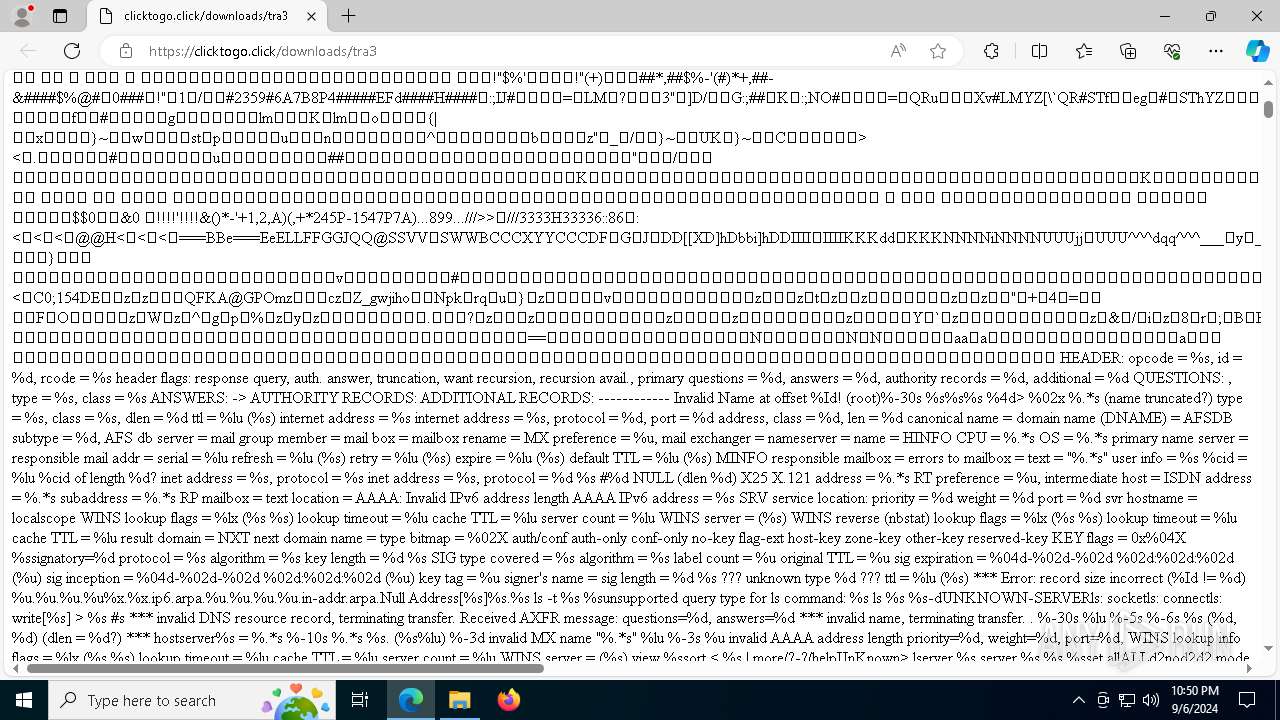
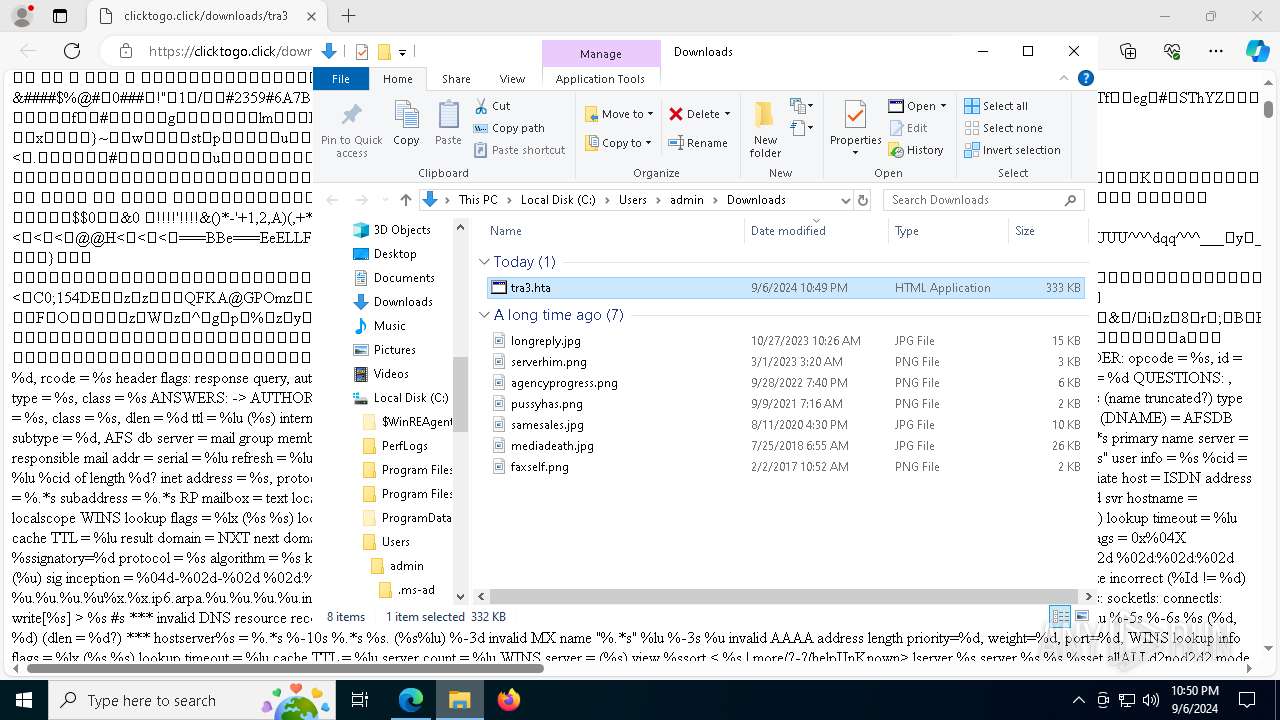
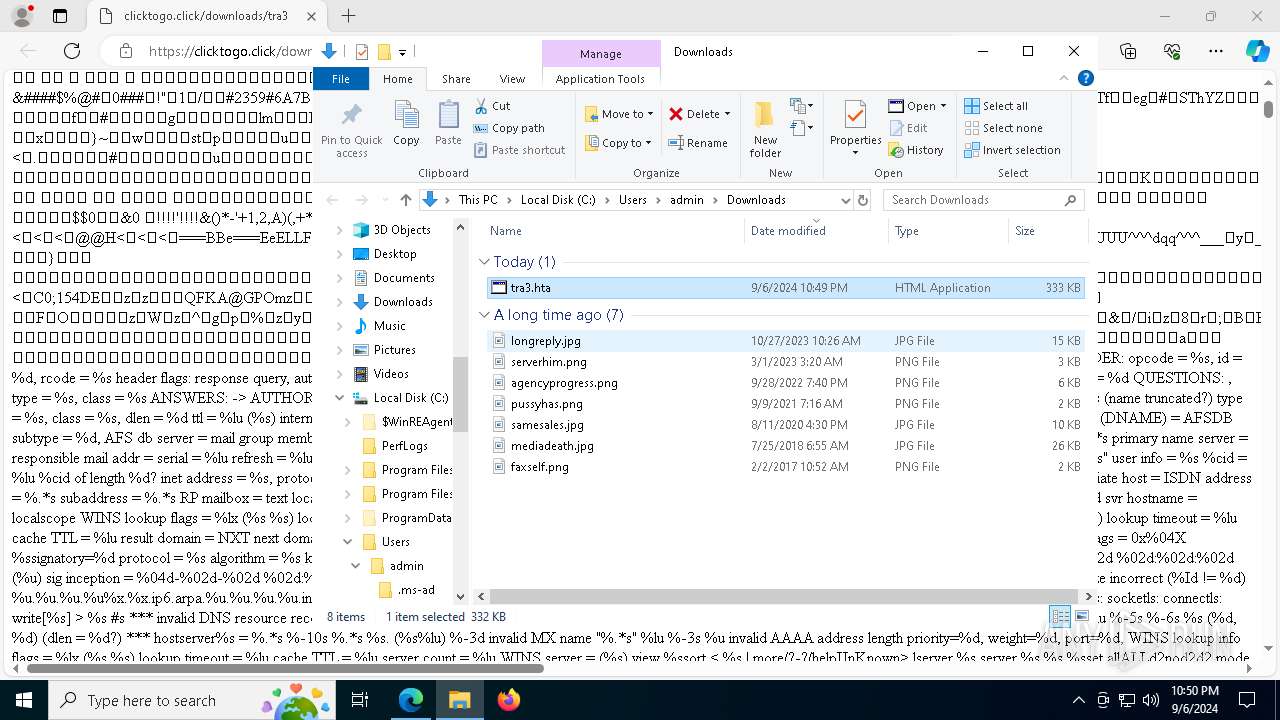
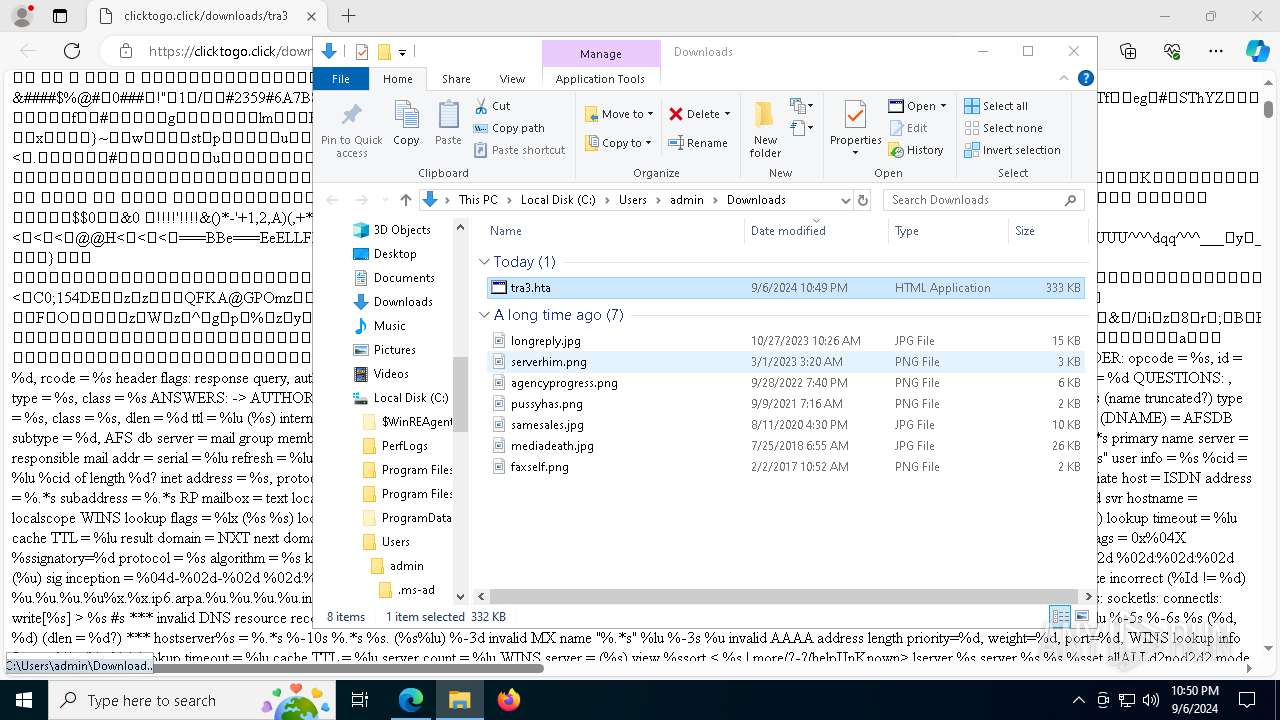
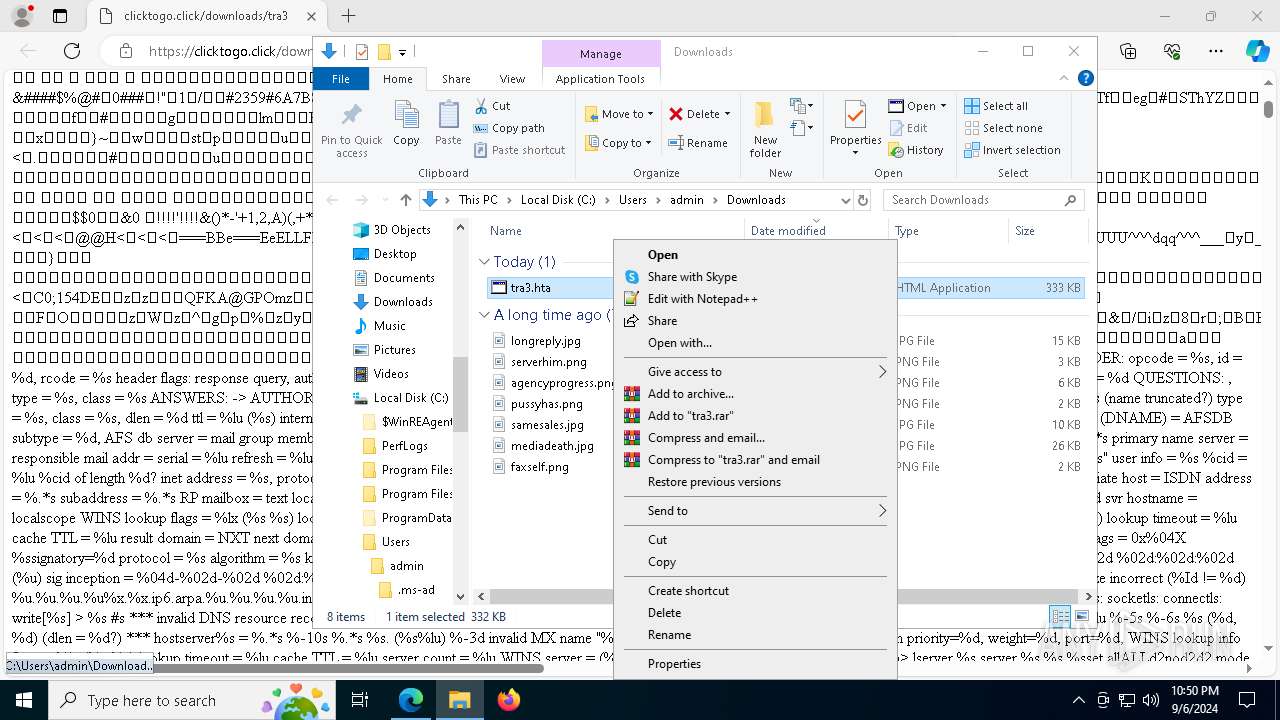
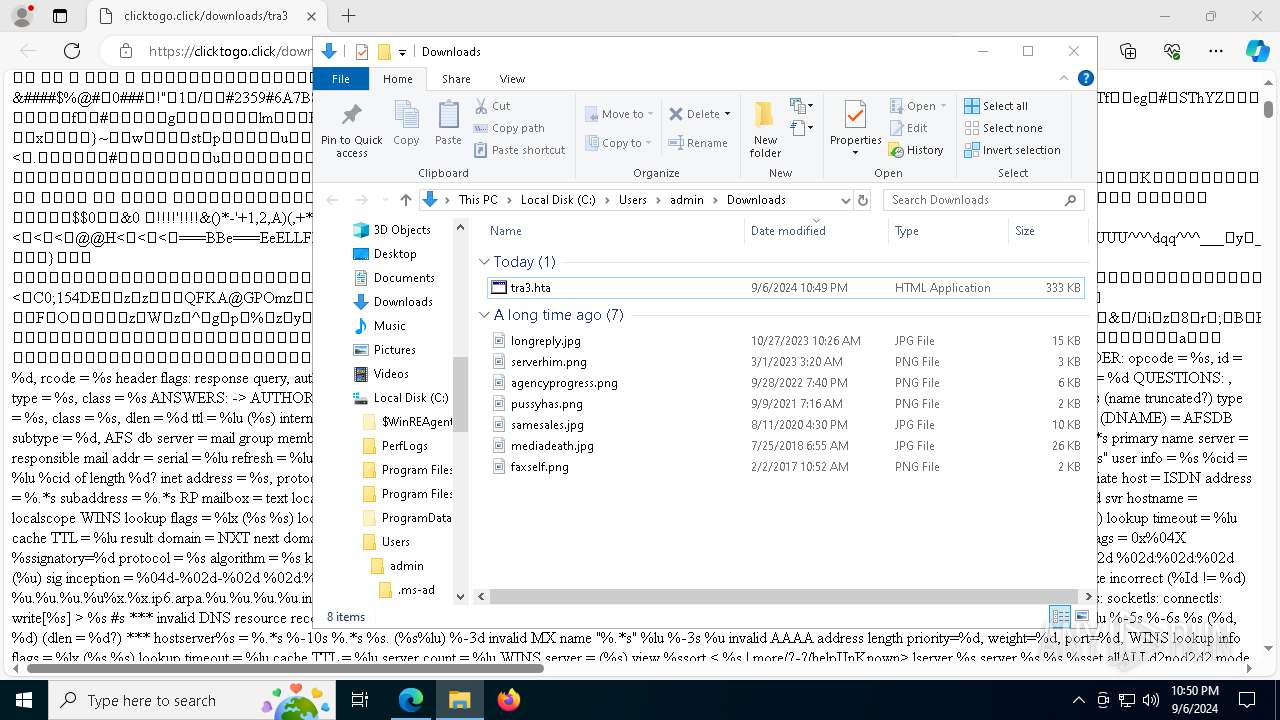
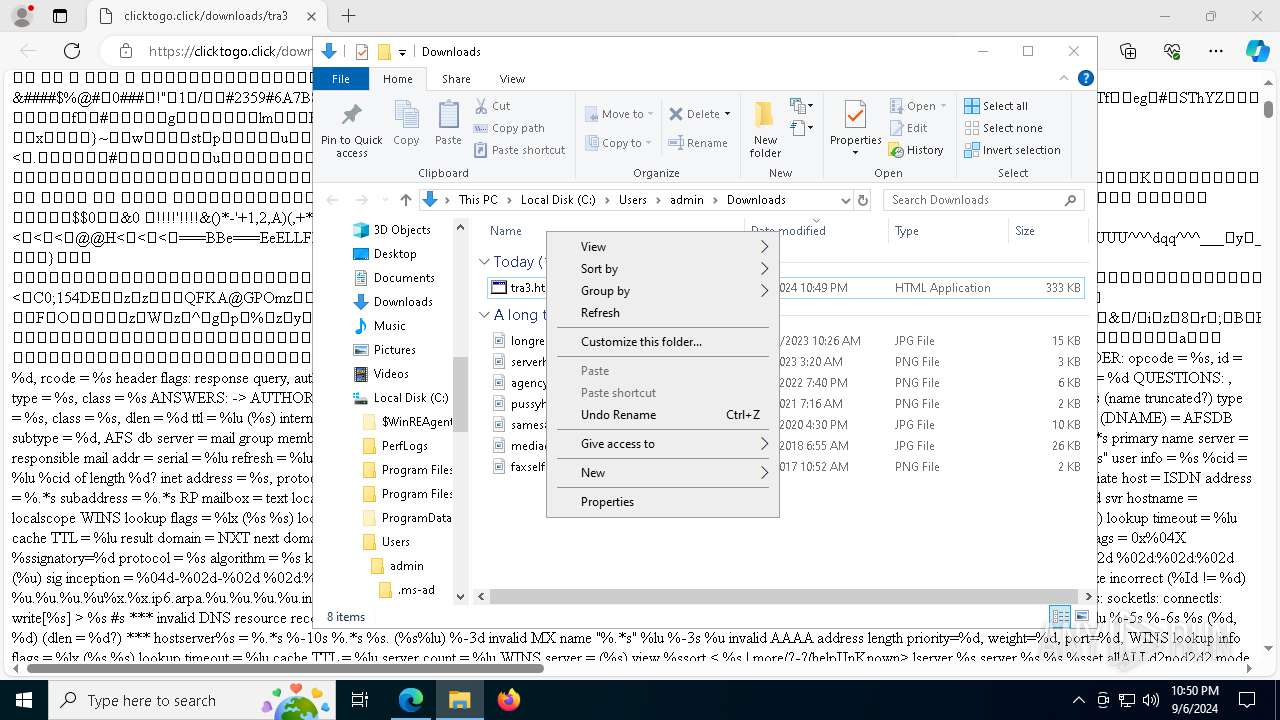
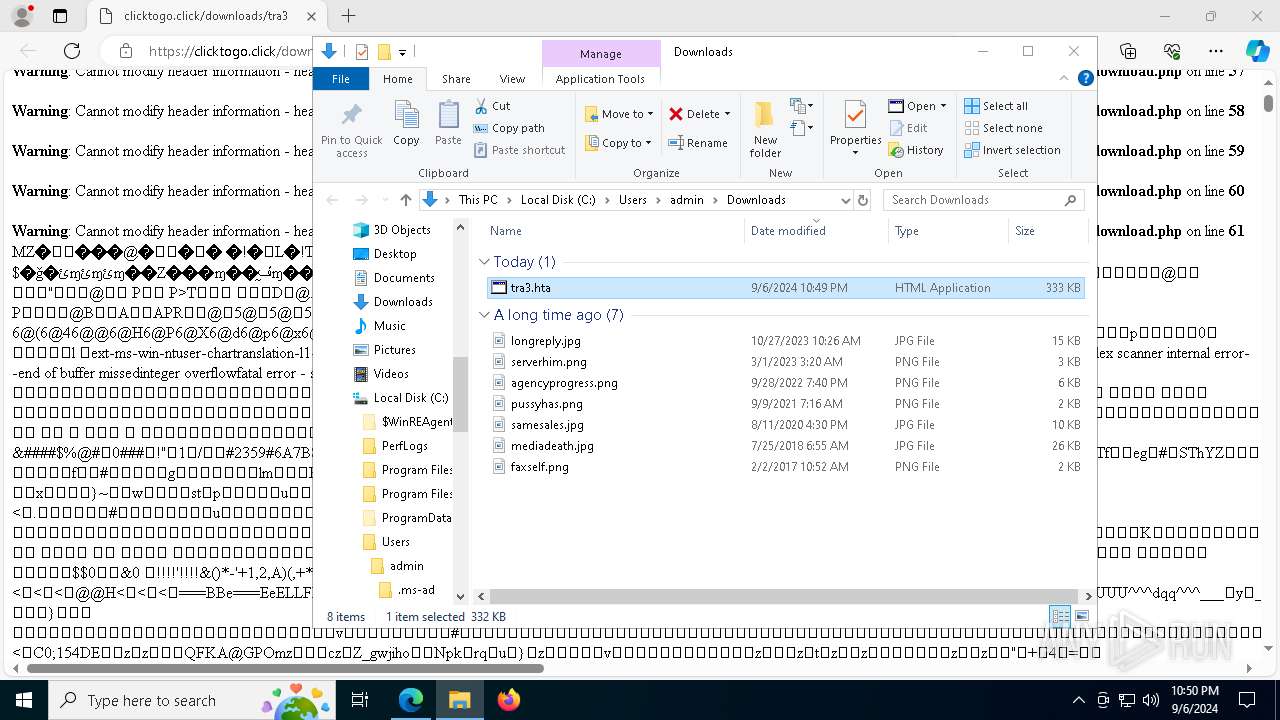
| URL: | https://clicktogo.click/downloads/tra3 |
| Full analysis: | https://app.any.run/tasks/d95b2760-2585-4f62-aaad-996fd0e9f006 |
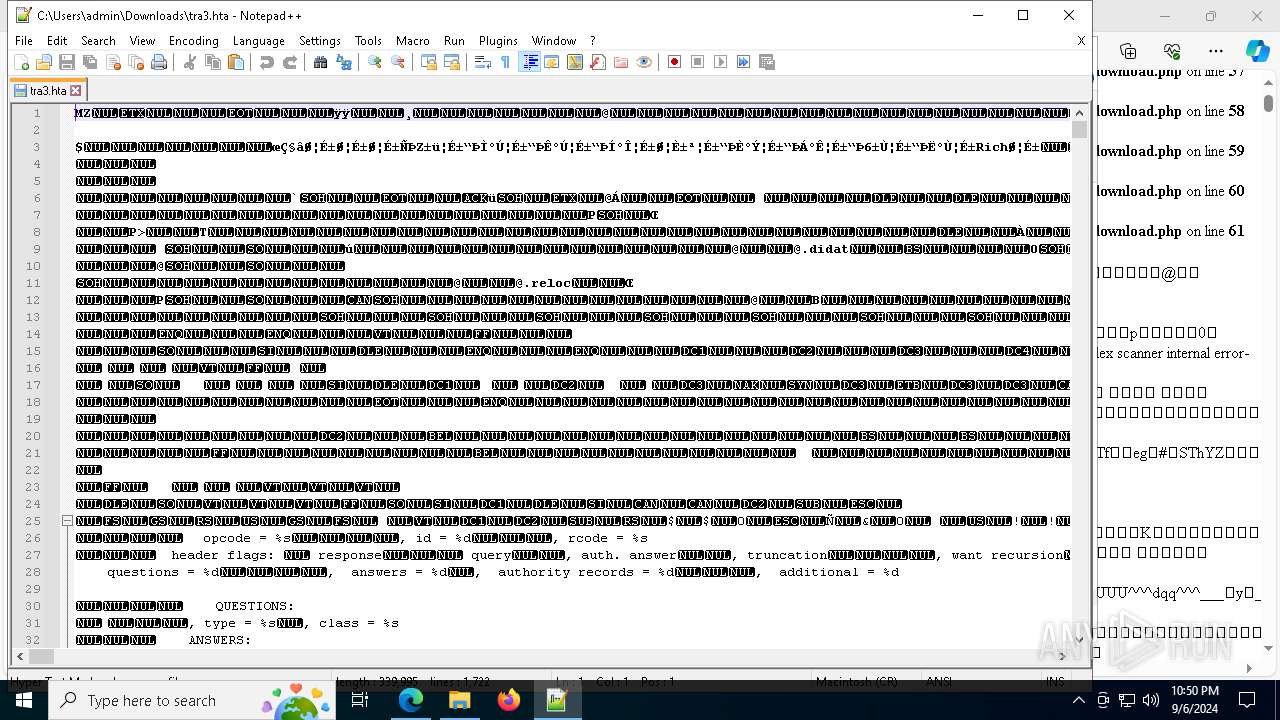
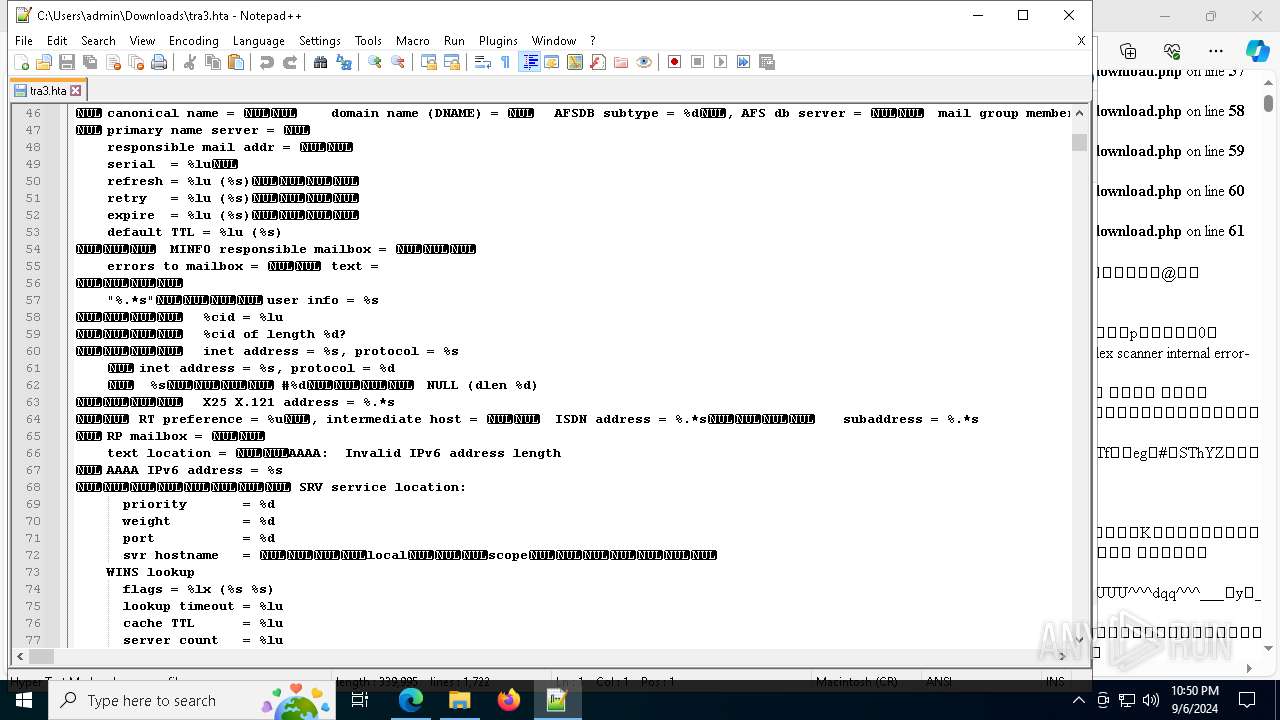
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 06, 2024, 22:48:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E22A23E7A38DECBE87F16433CF0615A8 |
| SHA1: | 35D4AEB0E40CA9DAF30307A9BA4D96A0DD0343C6 |
| SHA256: | EE27E0CB221D7B7A5D6A9D5E08E11E42181F7451399948222ED8C3C3C71AF7B2 |
| SSDEEP: | 3:N8UXLGJMZB4J4KxEW:2UXLeOaV |
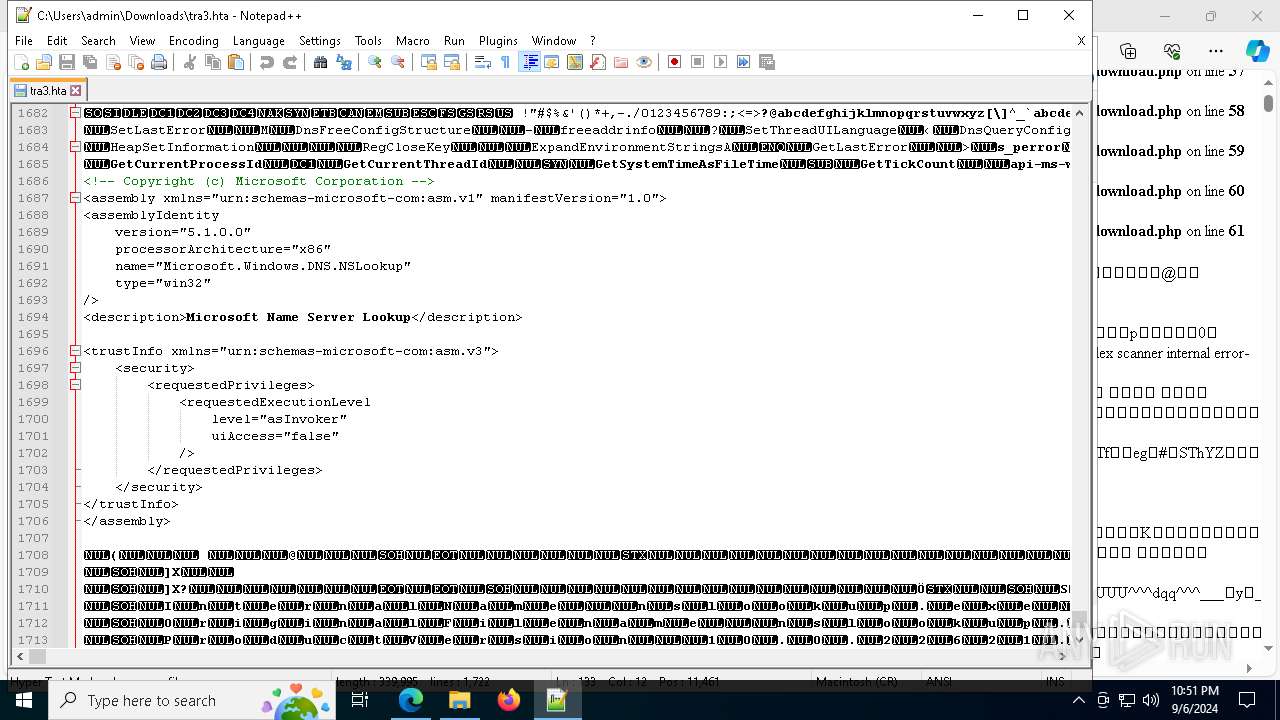
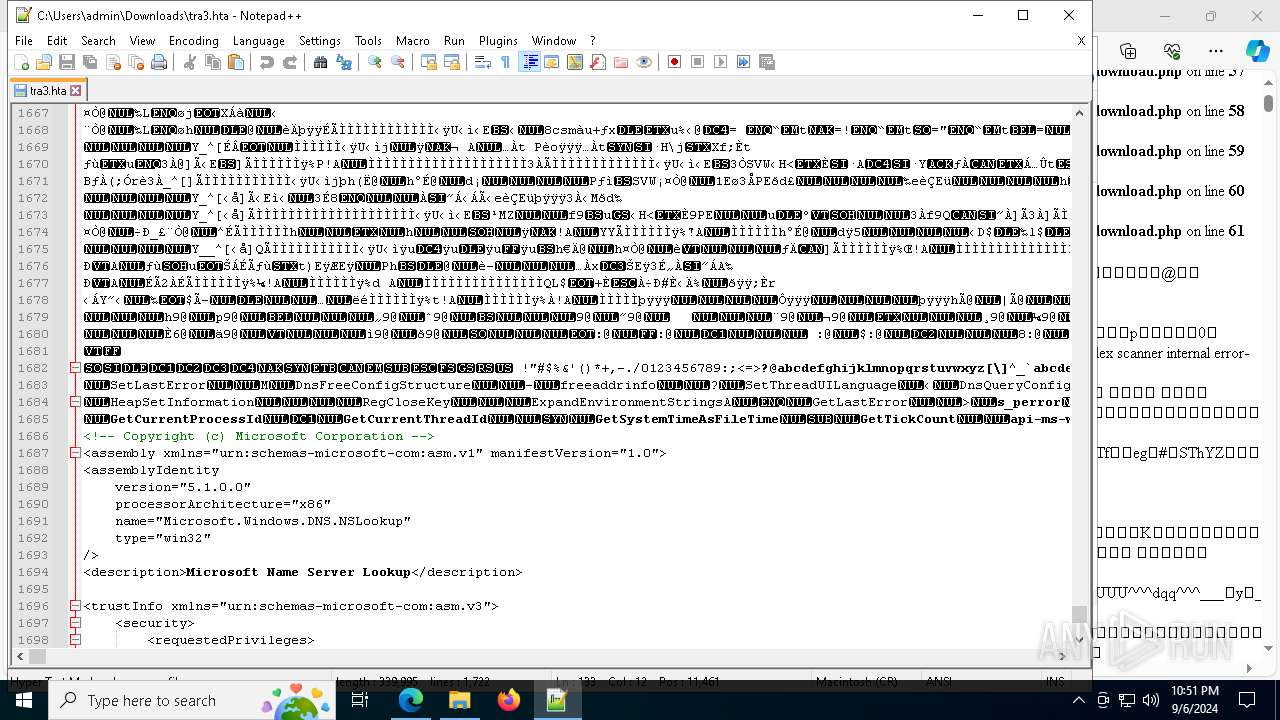
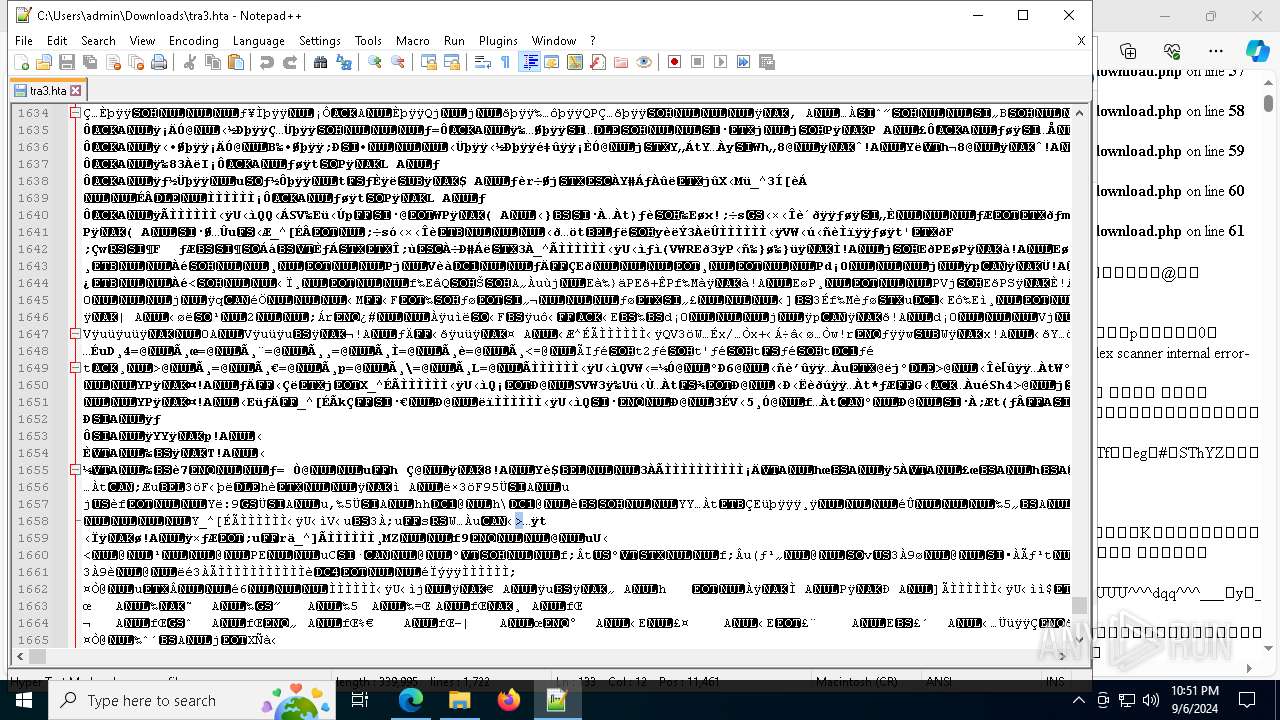
MALICIOUS
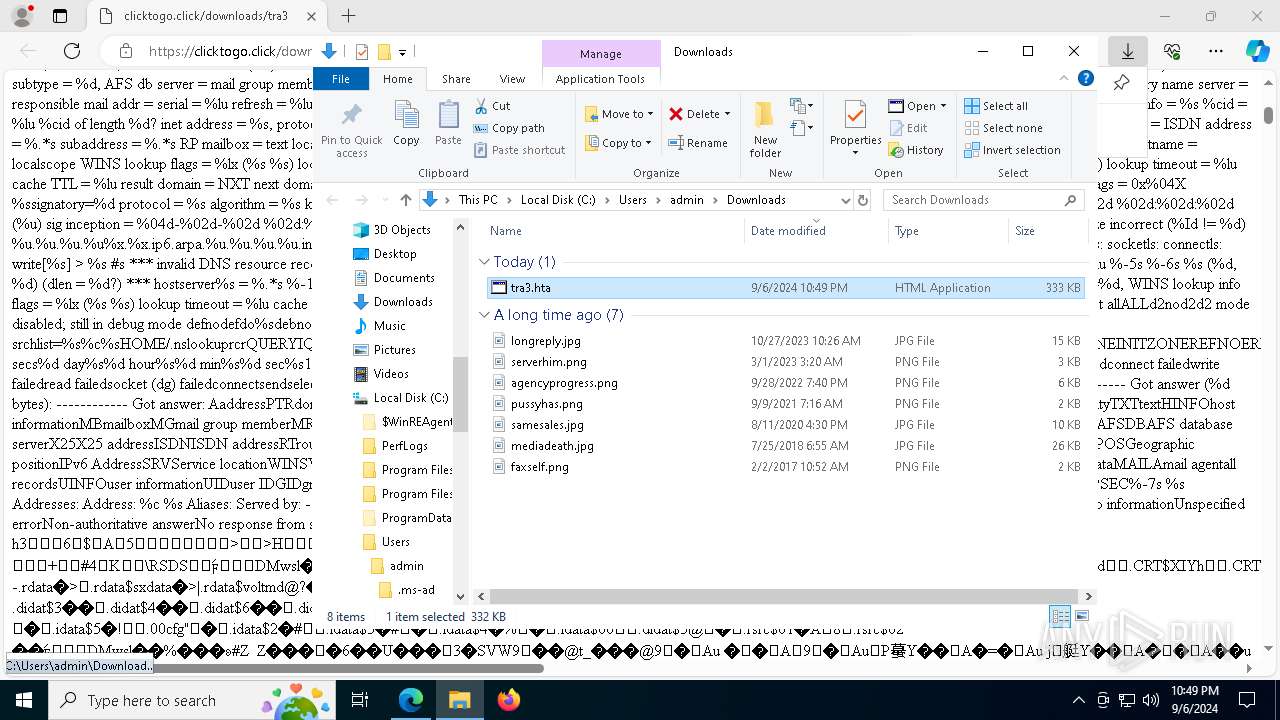
Run PowerShell with an invisible window
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 7736)
- mshta.exe (PID: 3352)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
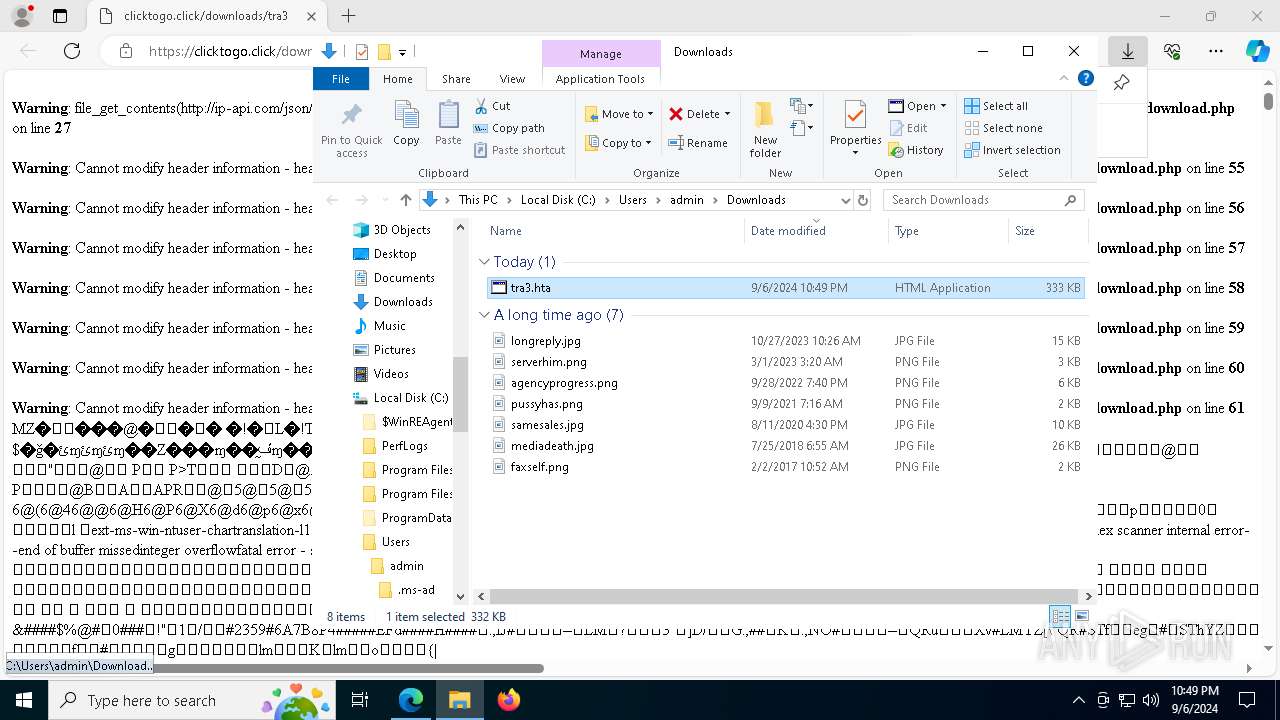
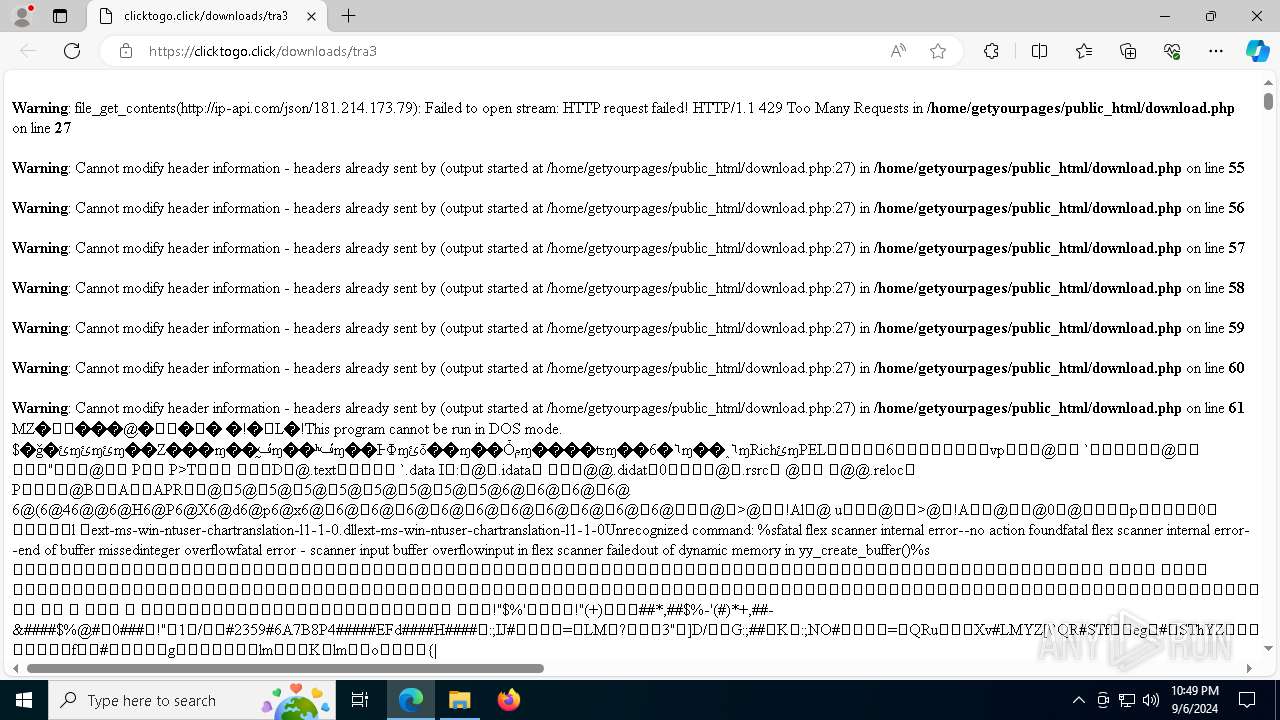
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7956)
Stealers network behavior
- RewardFlaccid.a3x (PID: 608)
- RewardFlaccid.a3x (PID: 300)
Actions looks like stealing of personal data
- RewardFlaccid.a3x (PID: 608)
- RewardFlaccid.a3x (PID: 300)
LUMMA has been detected (SURICATA)
- RewardFlaccid.a3x (PID: 608)
- RewardFlaccid.a3x (PID: 300)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 508)
- msedge.exe (PID: 4192)
- powershell.exe (PID: 7956)
- Setup.exe (PID: 7424)
Cryptography encrypted command line is found
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
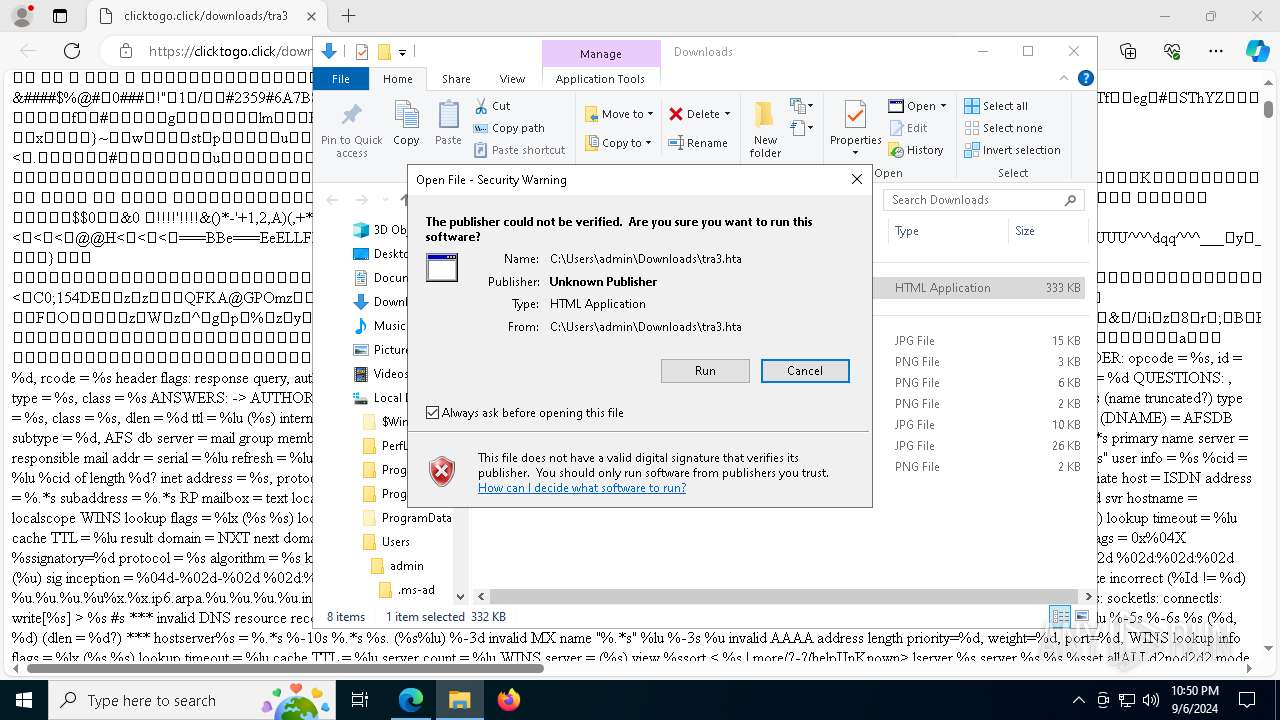
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7736)
- mshta.exe (PID: 3352)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 7736)
- mshta.exe (PID: 3352)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 7736)
- mshta.exe (PID: 3352)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Executable content was dropped or overwritten
- powershell.exe (PID: 7956)
- Setup.exe (PID: 7424)
- more.com (PID: 1496)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Starts application with an unusual extension
- Setup.exe (PID: 7424)
- Setup.exe (PID: 6784)
- more.com (PID: 1156)
- more.com (PID: 1496)
INFO
Reads the computer name
- identity_helper.exe (PID: 3972)
- Setup.exe (PID: 7424)
- StrCmp.exe (PID: 7520)
- Setup.exe (PID: 6784)
- more.com (PID: 1156)
- RewardFlaccid.a3x (PID: 608)
- RewardFlaccid.a3x (PID: 300)
- more.com (PID: 1496)
Application launched itself
- msedge.exe (PID: 4192)
Checks supported languages
- identity_helper.exe (PID: 3972)
- Setup.exe (PID: 7424)
- StrCmp.exe (PID: 7520)
- more.com (PID: 1496)
- Setup.exe (PID: 6784)
- more.com (PID: 1156)
- RewardFlaccid.a3x (PID: 608)
- RewardFlaccid.a3x (PID: 300)
Reads Environment values
- identity_helper.exe (PID: 3972)
Executable content was dropped or overwritten
- msedge.exe (PID: 4192)
- msedge.exe (PID: 508)
The process uses the downloaded file
- msedge.exe (PID: 208)
- mshta.exe (PID: 7736)
- powershell.exe (PID: 7956)
- mshta.exe (PID: 3352)
- powershell.exe (PID: 7724)
Manual execution by a user
- mshta.exe (PID: 7736)
- mshta.exe (PID: 3352)
- notepad++.exe (PID: 3356)
Reads Internet Explorer settings
- mshta.exe (PID: 7736)
- mshta.exe (PID: 3352)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
Disables trace logs
- powershell.exe (PID: 7956)
Checks proxy server information
- powershell.exe (PID: 7956)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 7724)
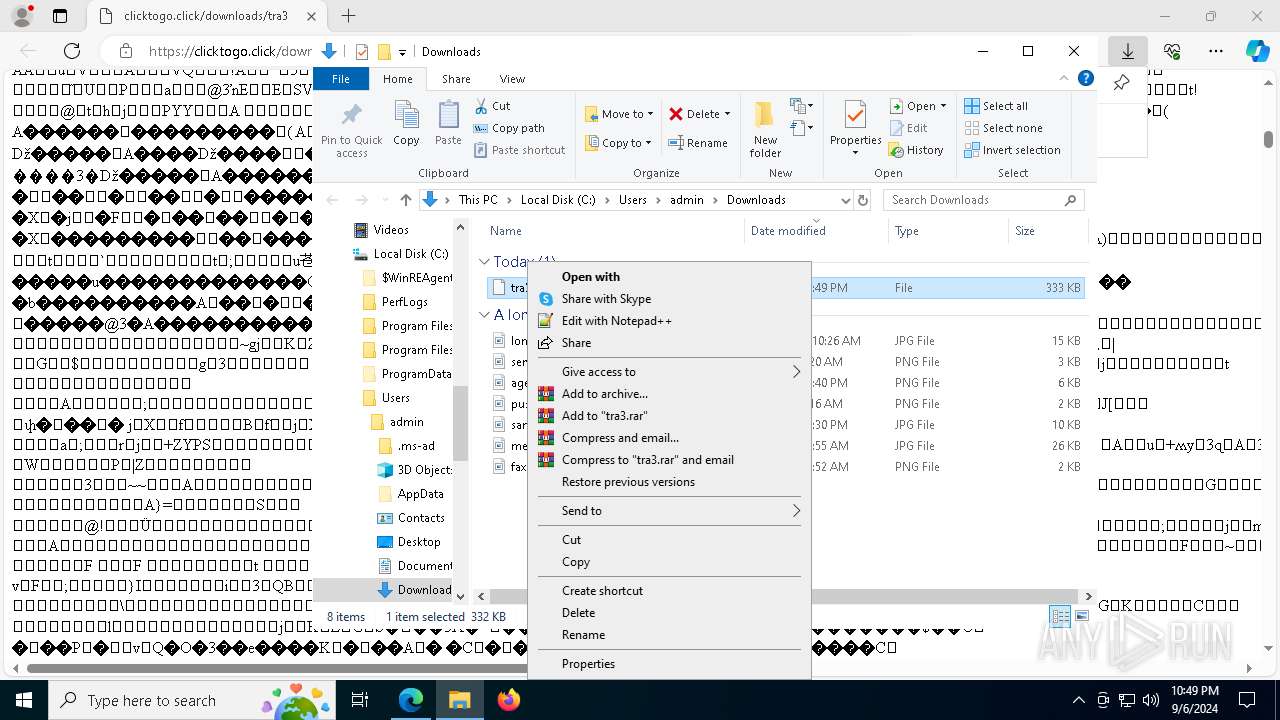
The executable file from the user directory is run by the Powershell process
- Setup.exe (PID: 7424)
- Setup.exe (PID: 6784)
Creates files or folders in the user directory
- Setup.exe (PID: 7424)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7724)
Create files in a temporary directory
- Setup.exe (PID: 7424)
- Setup.exe (PID: 6784)
- more.com (PID: 1496)
- more.com (PID: 1156)
Creates files in the program directory
- more.com (PID: 1496)
Sends debugging messages
- notepad++.exe (PID: 3356)
Reads the software policy settings
- RewardFlaccid.a3x (PID: 608)
- RewardFlaccid.a3x (PID: 300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
62
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
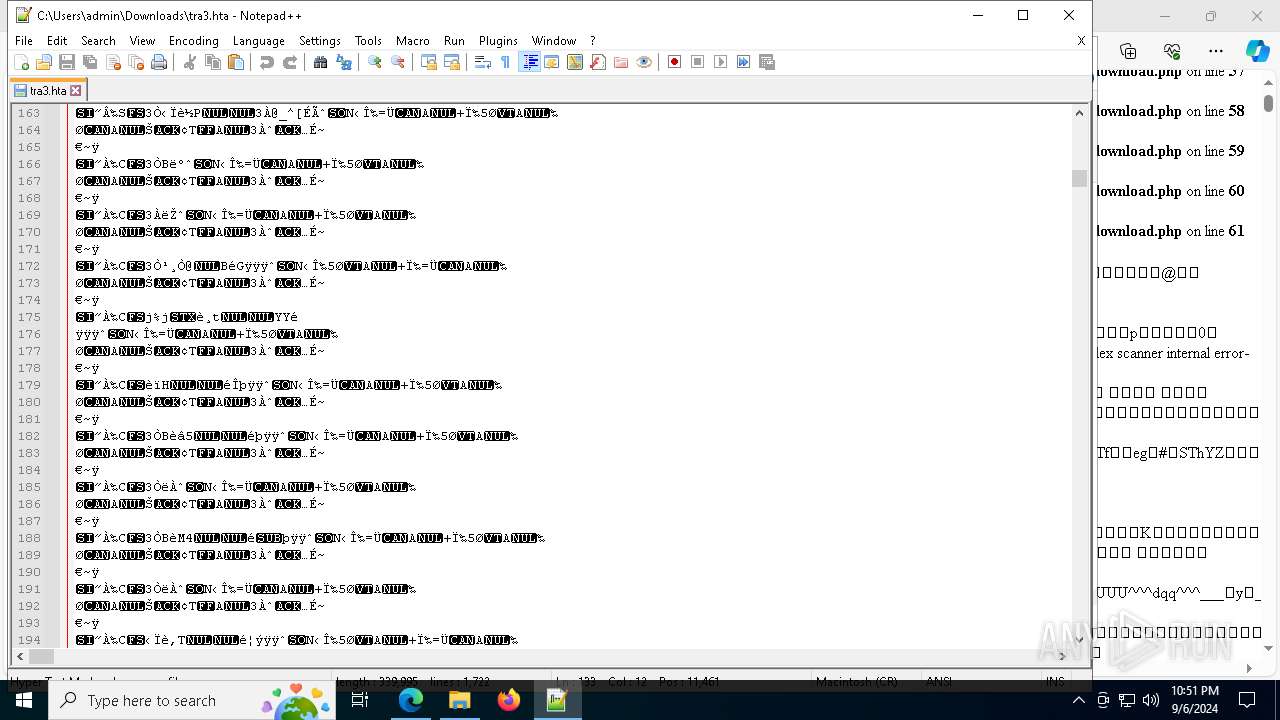
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5756 --field-trial-handle=2340,i,3896052898126183464,1520931552605055515,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6896 --field-trial-handle=2340,i,3896052898126183464,1520931552605055515,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5652 --field-trial-handle=2340,i,3896052898126183464,1520931552605055515,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 300 | C:\ProgramData\RewardFlaccid.a3x | C:\ProgramData\RewardFlaccid.a3x | more.com | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2556 --field-trial-handle=2340,i,3896052898126183464,1520931552605055515,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 608 | C:\ProgramData\RewardFlaccid.a3x | C:\ProgramData\RewardFlaccid.a3x | more.com | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 1156 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7548 --field-trial-handle=2340,i,3896052898126183464,1520931552605055515,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1496 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3704 --field-trial-handle=2340,i,3896052898126183464,1520931552605055515,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
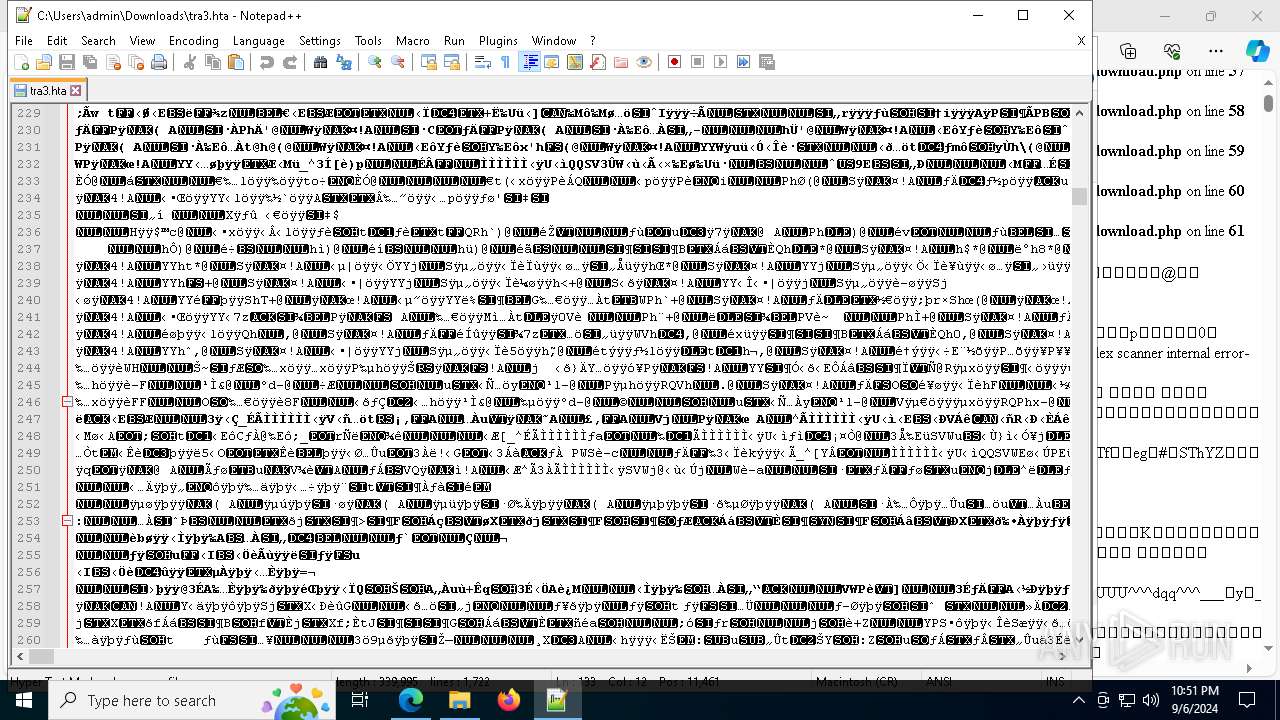
Total events
20 677
Read events
20 630
Write events
47
Delete events
0
Modification events
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1307227F11802F00 | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E4BD337F11802F00 | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394460 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E21FC550-E82F-47F5-959E-6F75742AA98B} | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394460 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ECFEB90C-FCAD-49BC-BB4C-1104594099A7} | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A01FE67F11802F00 | |||
| (PID) Process: | (4192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
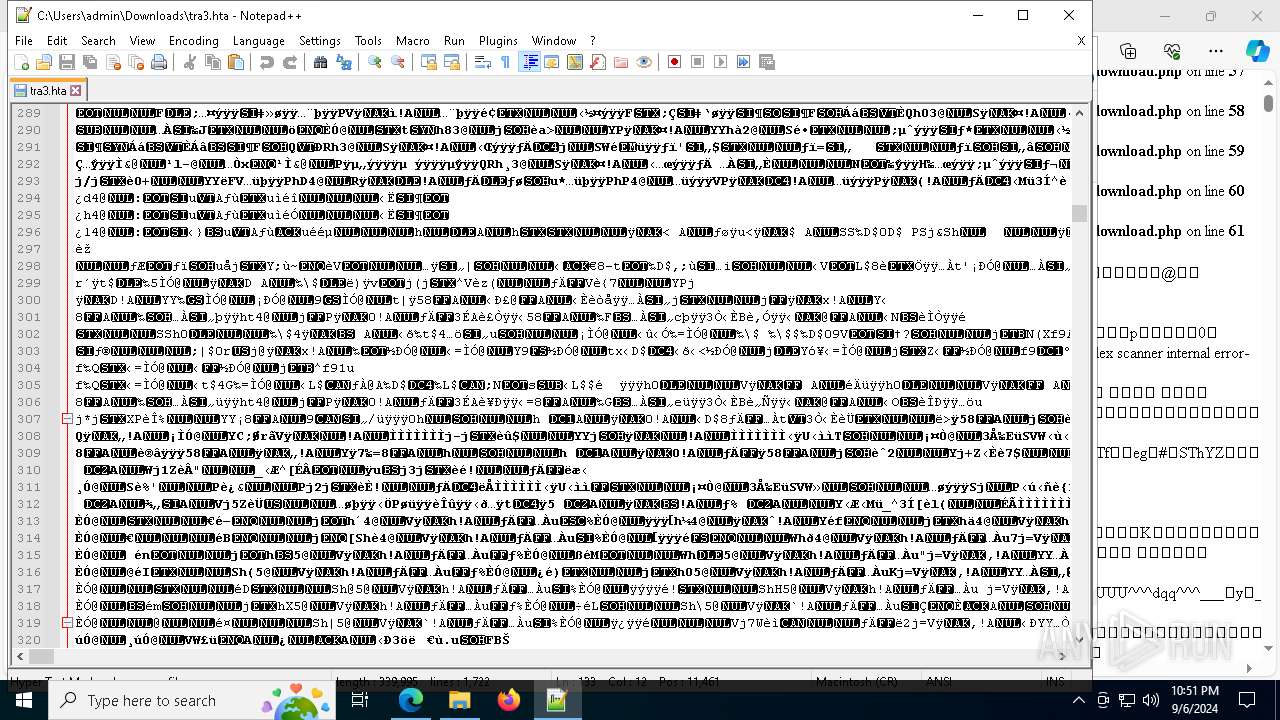
Executable files
49
Suspicious files
412
Text files
147
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129d80.TMP | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129daf.TMP | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129dde.TMP | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF129dde.TMP | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129d80.TMP | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129dbf.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
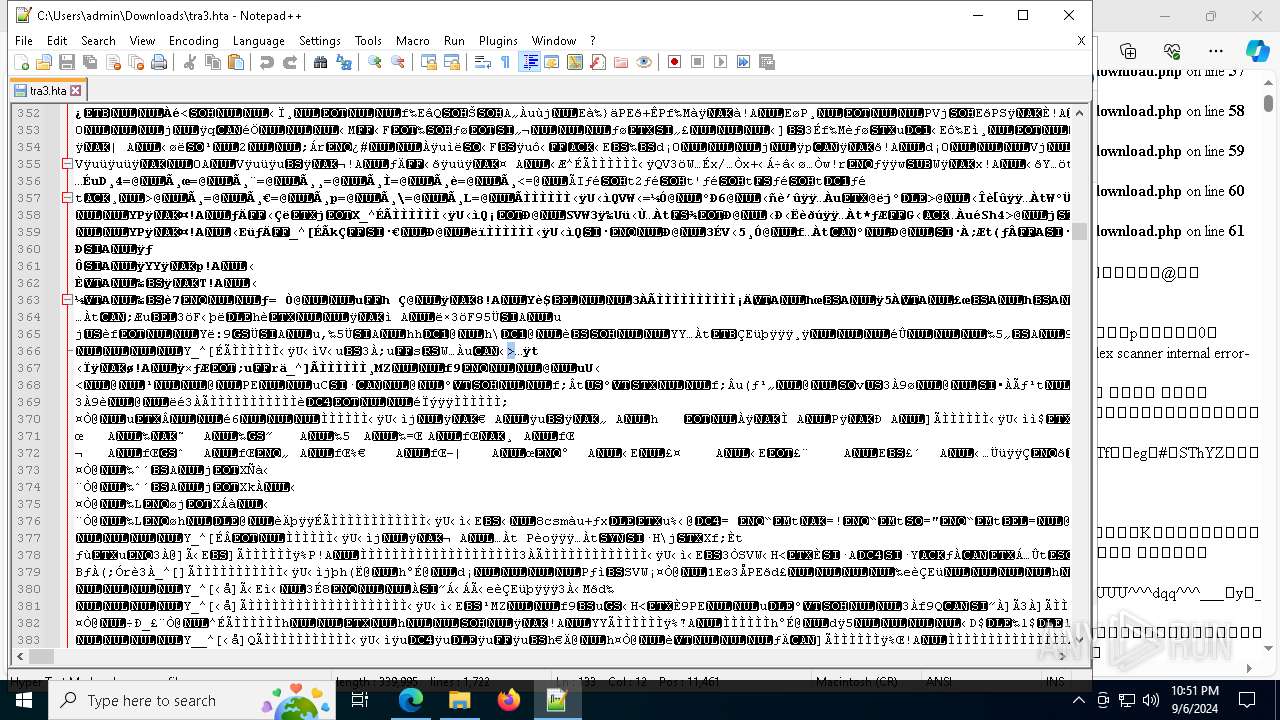
HTTP(S) requests
37
TCP/UDP connections
80
DNS requests
62
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1060 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
568 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7600 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7600 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8180 | svchost.exe | HEAD | 200 | 84.201.210.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726202665&P2=404&P3=2&P4=DpQGfQBKnHkeM8zFYTnsTDe2Uxj19UxyoOW7ZYaYUmi7oMeGniKU7f%2bz9s1XZjBfrAFHBMY2WQ%2fRBxrRaVDlgA%3d%3d | unknown | — | — | whitelisted |
8180 | svchost.exe | GET | 206 | 84.201.210.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726202665&P2=404&P3=2&P4=DpQGfQBKnHkeM8zFYTnsTDe2Uxj19UxyoOW7ZYaYUmi7oMeGniKU7f%2bz9s1XZjBfrAFHBMY2WQ%2fRBxrRaVDlgA%3d%3d | unknown | — | — | whitelisted |
8180 | svchost.exe | GET | 206 | 84.201.210.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726202665&P2=404&P3=2&P4=DpQGfQBKnHkeM8zFYTnsTDe2Uxj19UxyoOW7ZYaYUmi7oMeGniKU7f%2bz9s1XZjBfrAFHBMY2WQ%2fRBxrRaVDlgA%3d%3d | unknown | — | — | whitelisted |
8180 | svchost.exe | GET | 206 | 84.201.210.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726202665&P2=404&P3=2&P4=DpQGfQBKnHkeM8zFYTnsTDe2Uxj19UxyoOW7ZYaYUmi7oMeGniKU7f%2bz9s1XZjBfrAFHBMY2WQ%2fRBxrRaVDlgA%3d%3d | unknown | — | — | whitelisted |
8180 | svchost.exe | GET | 206 | 84.201.210.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726202665&P2=404&P3=2&P4=DpQGfQBKnHkeM8zFYTnsTDe2Uxj19UxyoOW7ZYaYUmi7oMeGniKU7f%2bz9s1XZjBfrAFHBMY2WQ%2fRBxrRaVDlgA%3d%3d | unknown | — | — | whitelisted |
8180 | svchost.exe | GET | 206 | 84.201.210.22:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726202665&P2=404&P3=2&P4=DpQGfQBKnHkeM8zFYTnsTDe2Uxj19UxyoOW7ZYaYUmi7oMeGniKU7f%2bz9s1XZjBfrAFHBMY2WQ%2fRBxrRaVDlgA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
568 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6124 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
508 | msedge.exe | 188.114.97.3:443 | clicktogo.click | — | — | unknown |
508 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4192 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
508 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
508 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
508 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
clicktogo.click |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
508 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
508 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
608 | RewardFlaccid.a3x | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
300 | RewardFlaccid.a3x | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
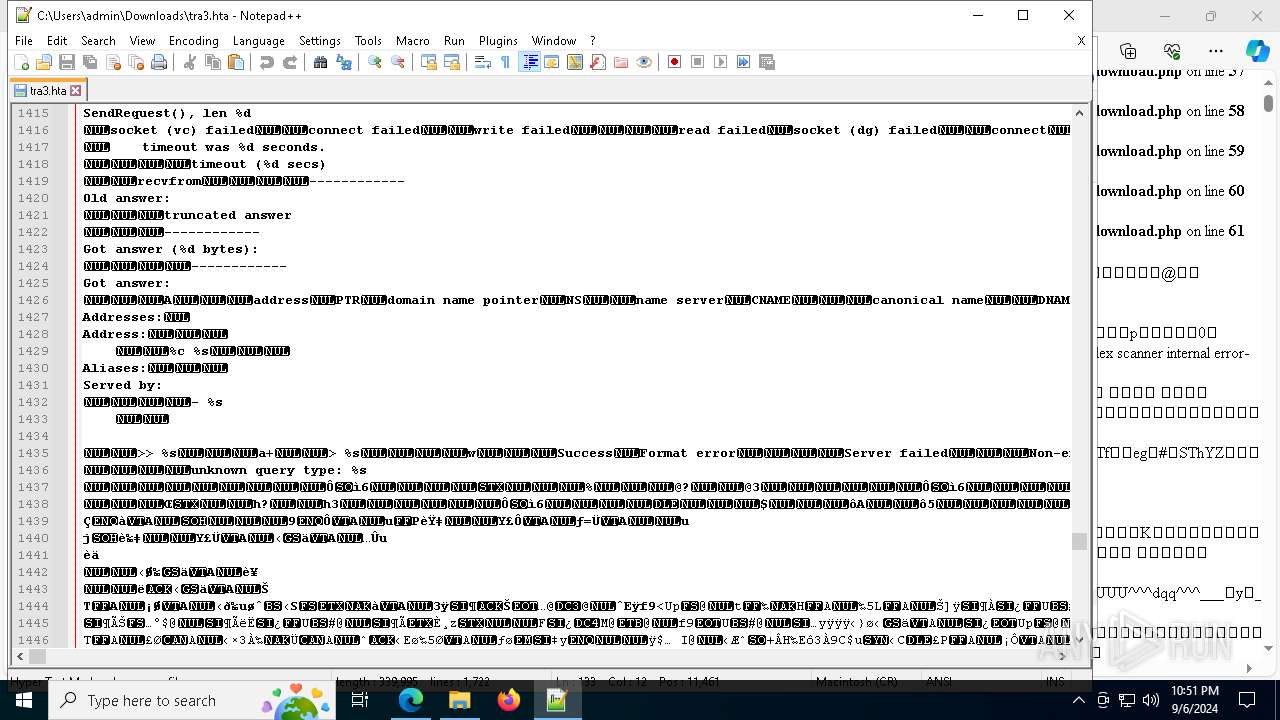
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|