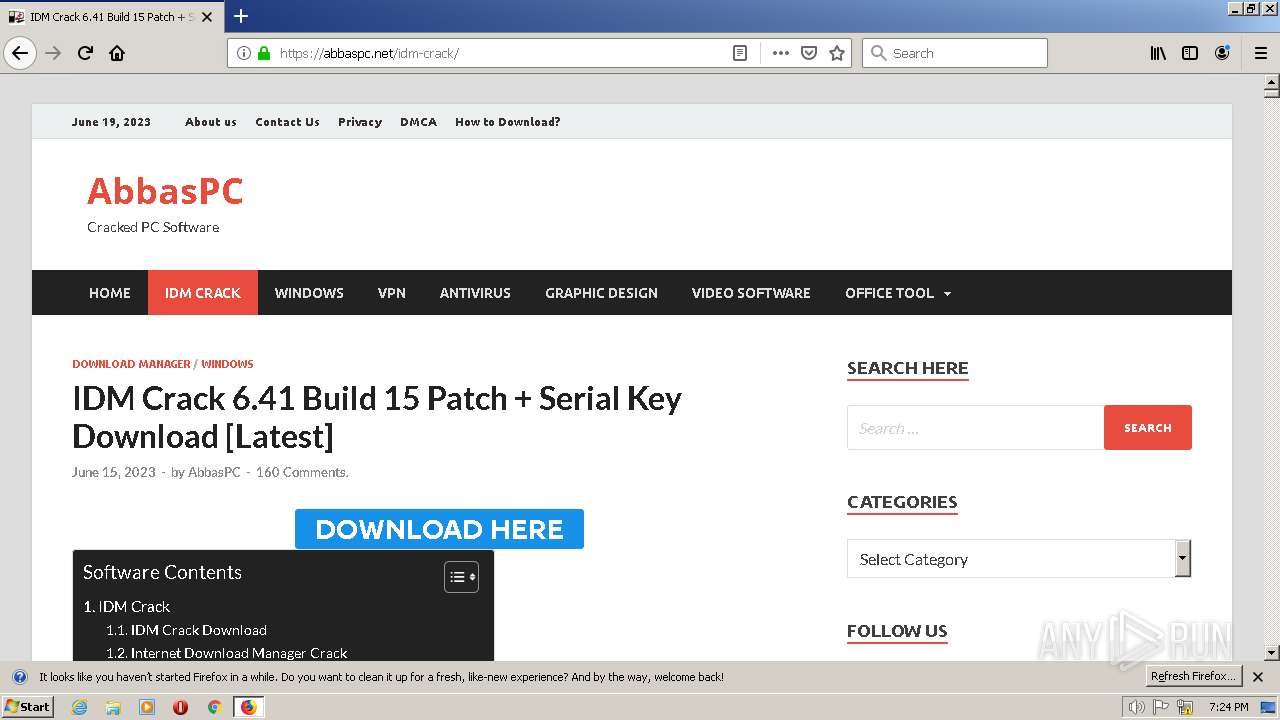
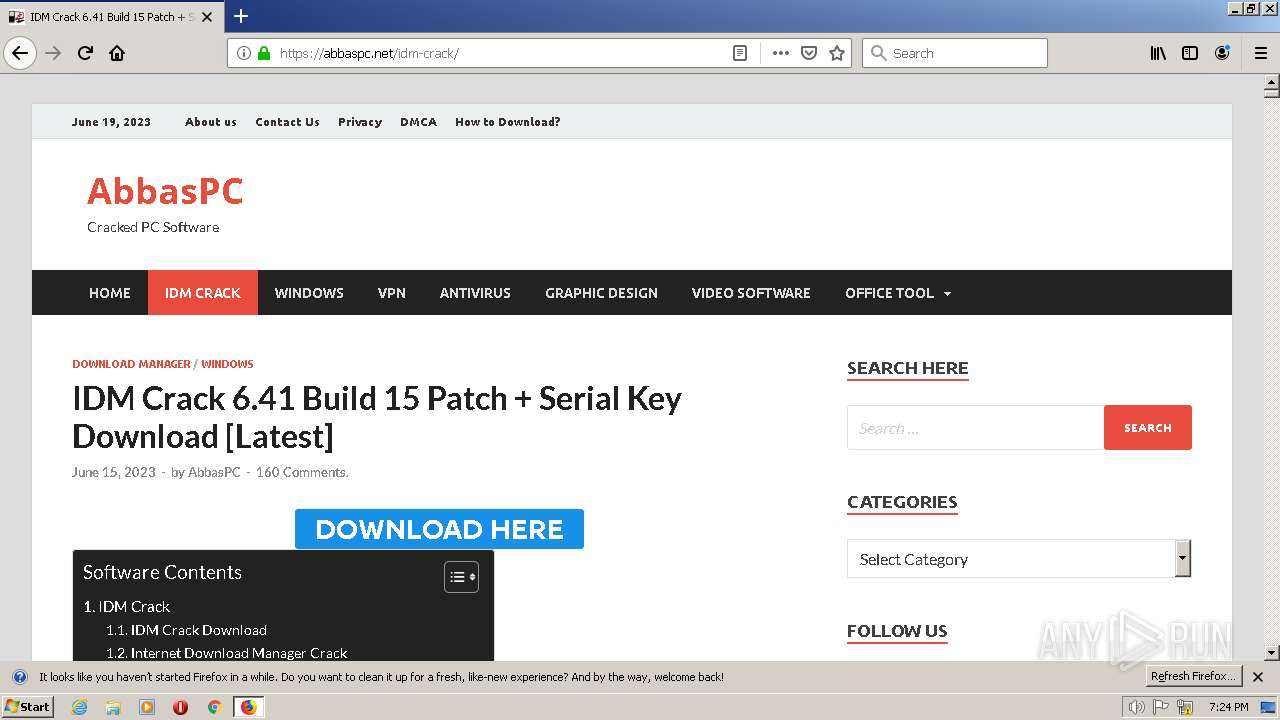
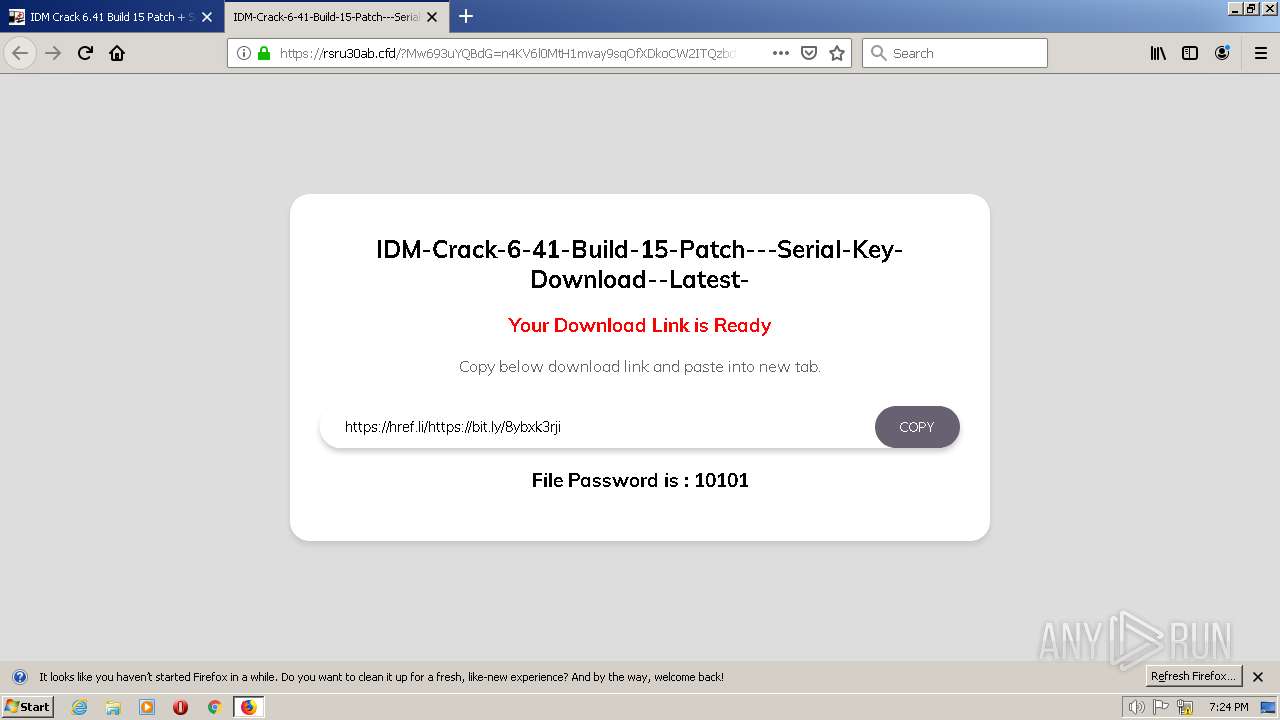
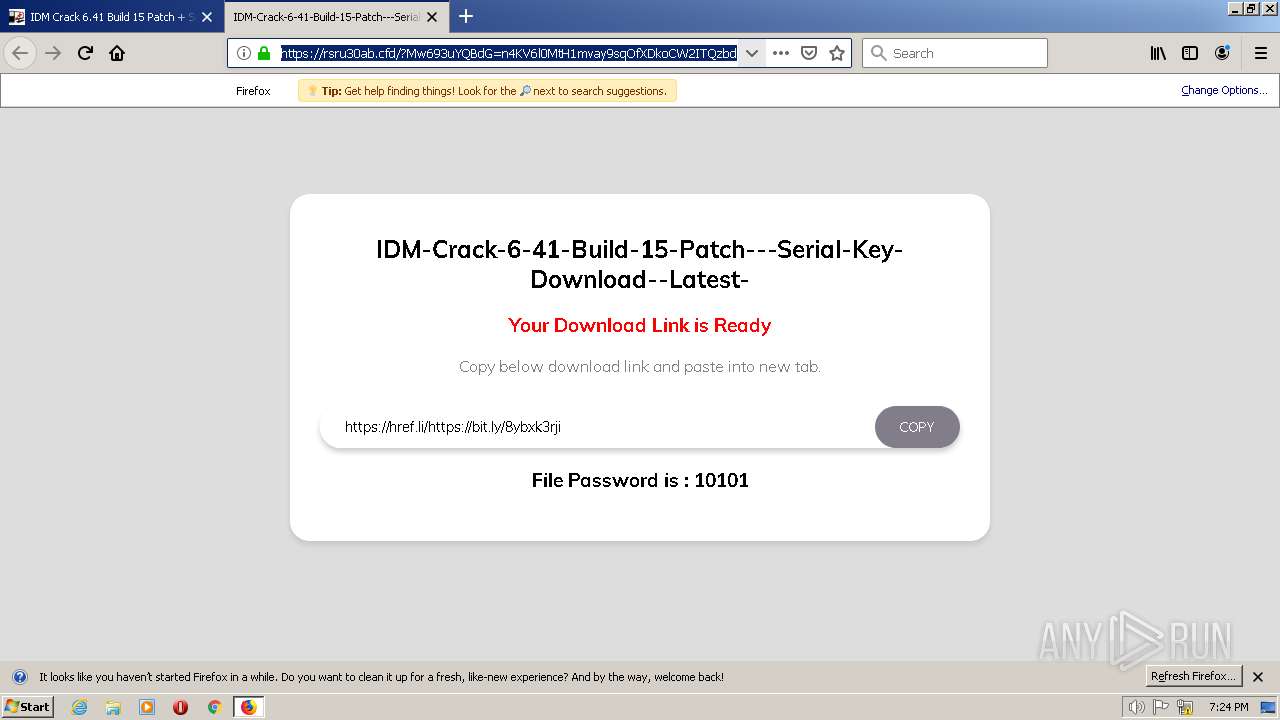
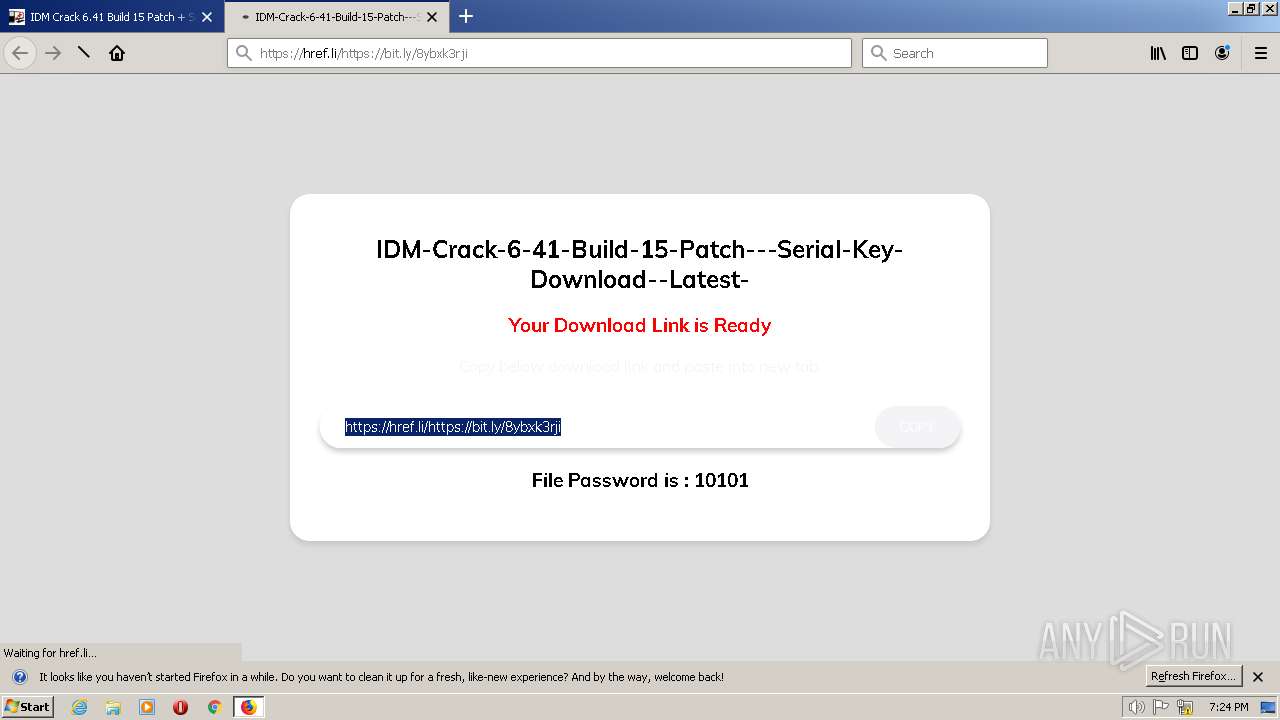
| URL: | https://abbaspc.net |
| Full analysis: | https://app.any.run/tasks/25d79905-1f64-4412-a89c-b6b7b9ae1465 |
| Verdict: | Malicious activity |
| Threats: | CryptBot is an advanced Windows-targeting infostealer delivered via pirate sites with "cracked" software. It has been first observed in the wild in 2019. |
| Analysis date: | June 19, 2023, 19:24:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E1EE041D9D4D2E7E2736E95DEA432F98 |
| SHA1: | DDBD88A9CE2CA47C7115782AE47C042D980E9B30 |
| SHA256: | EE1062B2B1AED2A130CD1E646AE306935384D1632CE069B1F3F5FB41F87825A6 |
| SSDEEP: | 3:N8lLAR:2RAR |
MALICIOUS
Steals credentials
- FullSetup.exe (PID: 2712)
Actions looks like stealing of personal data
- FullSetup.exe (PID: 2712)
Connects to the CnC server
- FullSetup.exe (PID: 2712)
Application was dropped or rewritten from another process
- srvrast.exe (PID: 2268)
Starts CMD.EXE for self-deleting
- FullSetup.exe (PID: 2712)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 404)
SUSPICIOUS
Reads the Internet Settings
- FullSetup.exe (PID: 2712)
Searches for installed software
- FullSetup.exe (PID: 2712)
Executable content was dropped or overwritten
- FullSetup.exe (PID: 2712)
Drops the AutoIt3 executable file
- FullSetup.exe (PID: 2712)
Starts CMD.EXE for commands execution
- FullSetup.exe (PID: 2712)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 972)
The process executes via Task Scheduler
- srvrast.exe (PID: 2268)
INFO
Reads CPU info
- FullSetup.exe (PID: 2712)
The process uses the downloaded file
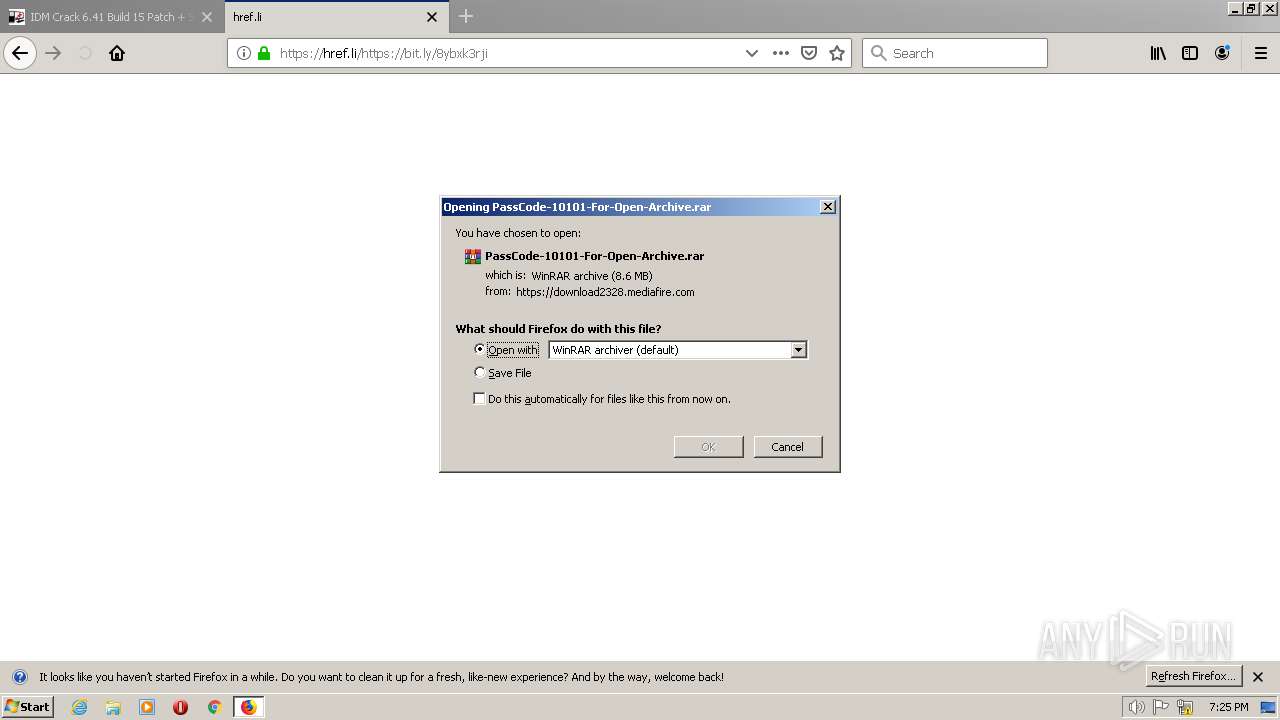
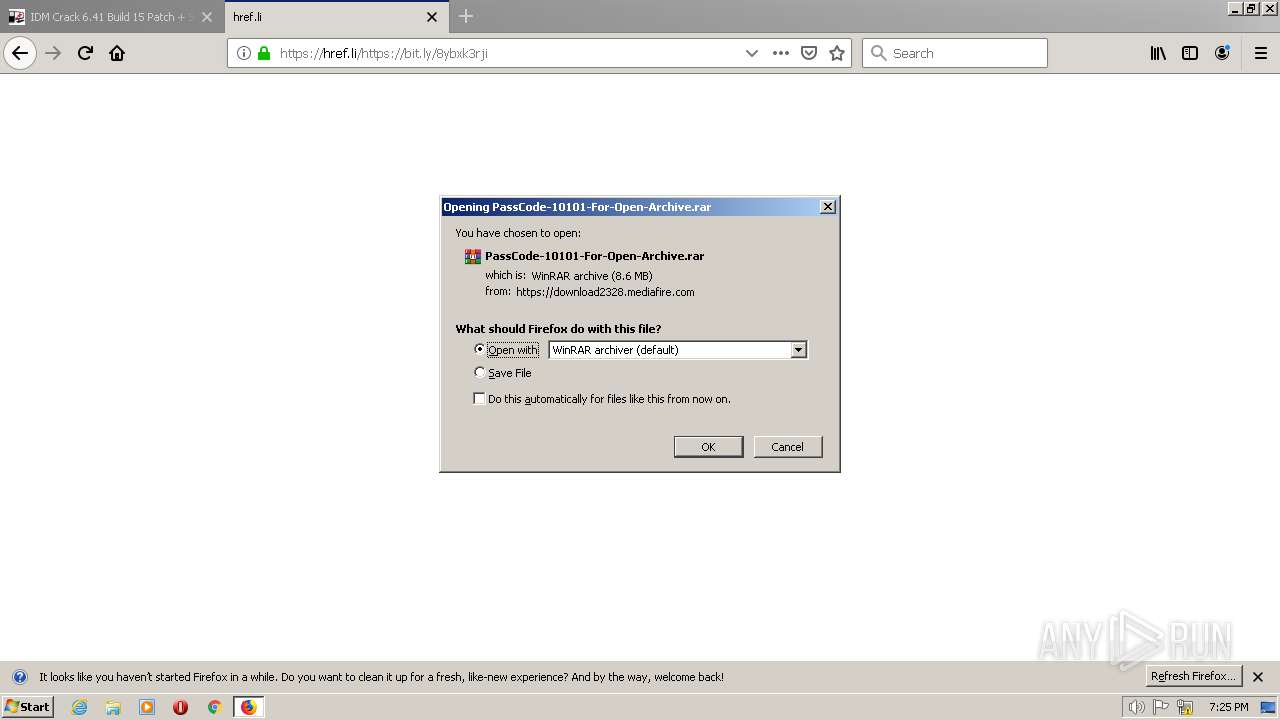
- firefox.exe (PID: 2448)
- WinRAR.exe (PID: 1480)
Reads Environment values
- FullSetup.exe (PID: 2712)
Create files in a temporary directory
- FullSetup.exe (PID: 2712)
Creates files or folders in the user directory
- FullSetup.exe (PID: 2712)
Checks supported languages
- FullSetup.exe (PID: 2712)
- srvrast.exe (PID: 2268)
Reads the computer name
- FullSetup.exe (PID: 2712)
Reads Windows Product ID
- FullSetup.exe (PID: 2712)
The process checks LSA protection
- FullSetup.exe (PID: 2712)
Reads the machine GUID from the registry
- FullSetup.exe (PID: 2712)
Checks proxy server information
- FullSetup.exe (PID: 2712)
Application launched itself
- firefox.exe (PID: 2448)
Reads mouse settings
- srvrast.exe (PID: 2268)
Executable content was dropped or overwritten
- firefox.exe (PID: 2448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | timeout -t 4 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 404 | "C:\Windows\System32\cmd.exe" /c schtasks /create /tn \SekrX\D85 /tr """"C:\Users\admin\AppData\Roaming\0D445946394EFC3C\srvrast.exe""" """C:\Users\admin\AppData\Roaming\0D445946394EFC3C\srvrast.chm"""" /st 00:01 /du 9422:23 /sc once /ri 1 /f | C:\Windows\SysWOW64\cmd.exe | — | FullSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 972 | "C:\Windows\System32\cmd.exe" /C timeout -t 4 && del "C:\Users\admin\AppData\Local\Temp\Rar$EXb1480.22104\FullSetup.exe" | C:\Windows\SysWOW64\cmd.exe | — | FullSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
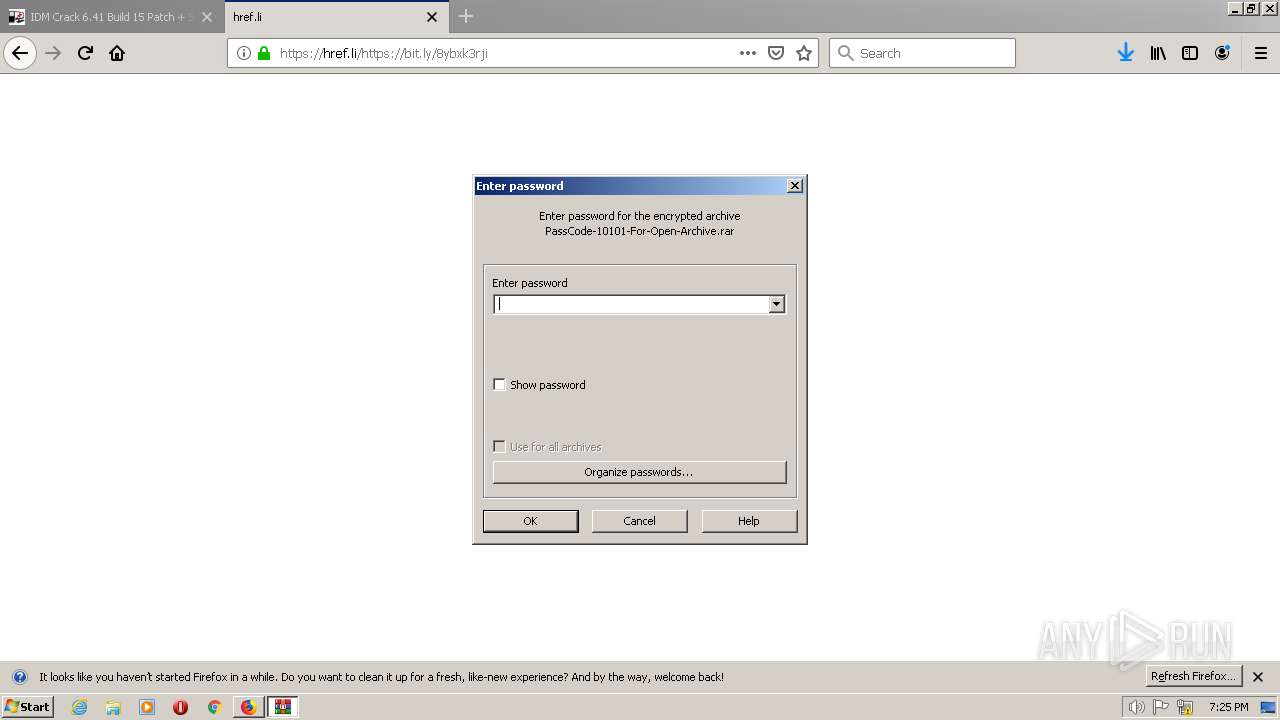
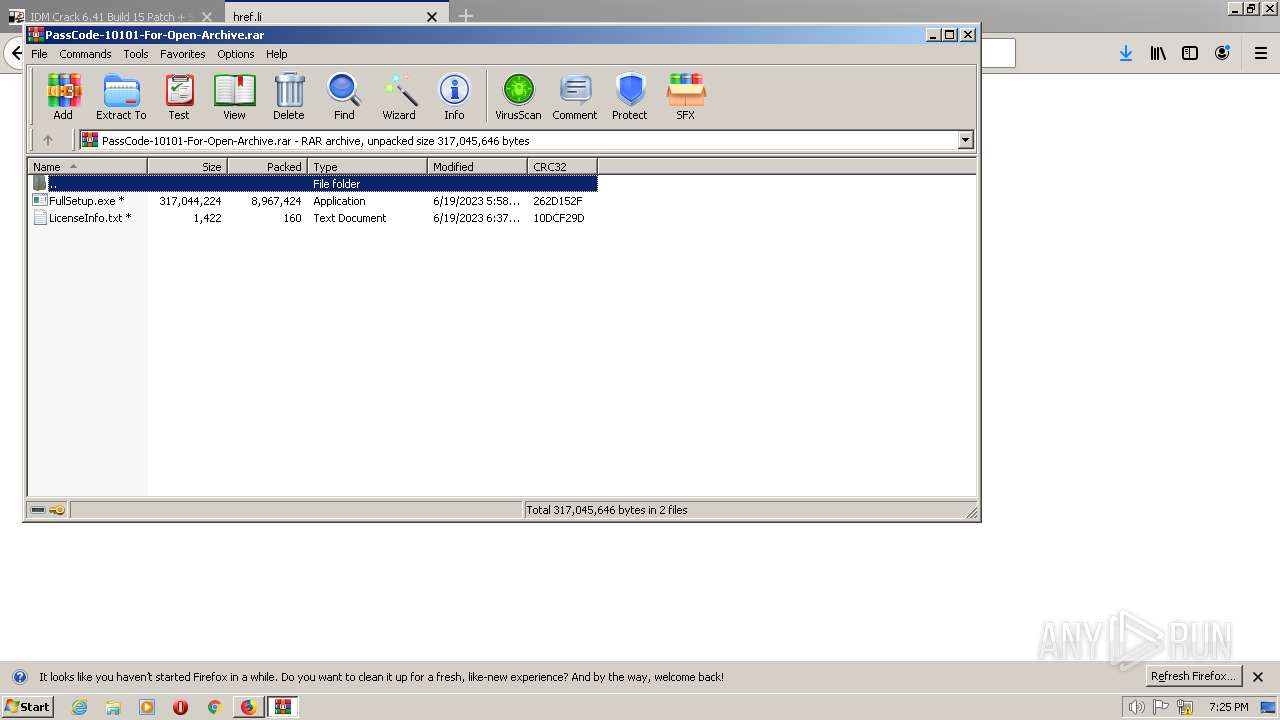
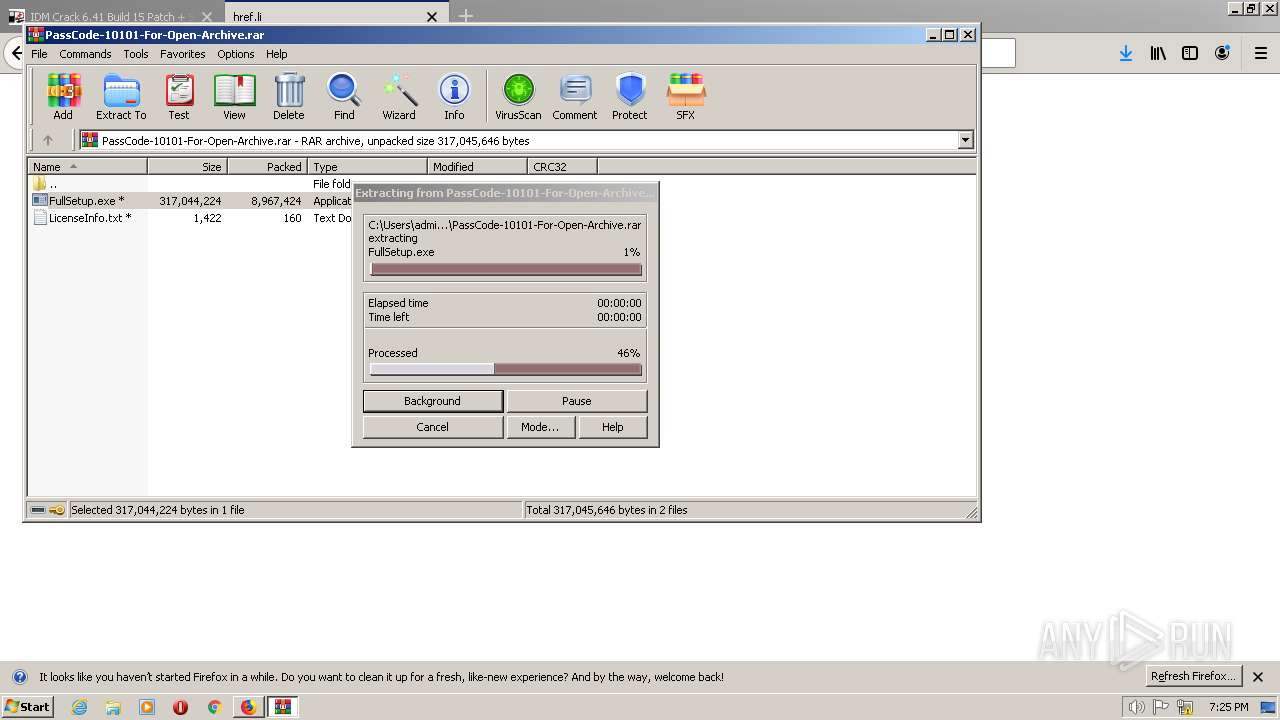
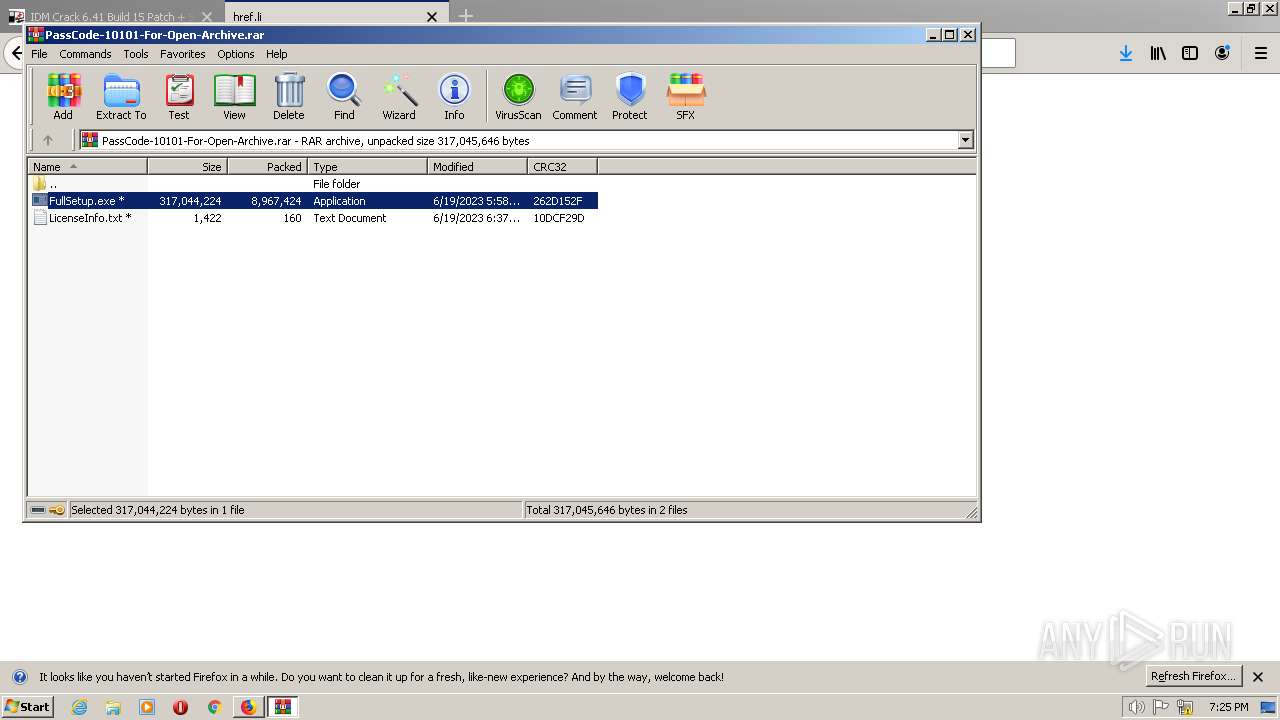
| 1480 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\PassCode-10101-For-Open-Archive.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | firefox.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2448.0.1240642811\1846926680" -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2448 "\\.\pipe\gecko-crash-server-pipe.2448" 1148 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2268 | C:\Users\admin\AppData\Roaming\0D445946394EFC3C\srvrast.exe "C:\Users\admin\AppData\Roaming\0D445946394EFC3C\srvrast.chm" | C:\Users\admin\AppData\Roaming\0D445946394EFC3C\srvrast.exe | — | taskeng.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 2372 | schtasks /create /tn \SekrX\D85 /tr """"C:\Users\admin\AppData\Roaming\0D445946394EFC3C\srvrast.exe""" """C:\Users\admin\AppData\Roaming\0D445946394EFC3C\srvrast.chm"""" /st 00:01 /du 9422:23 /sc once /ri 1 /f | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
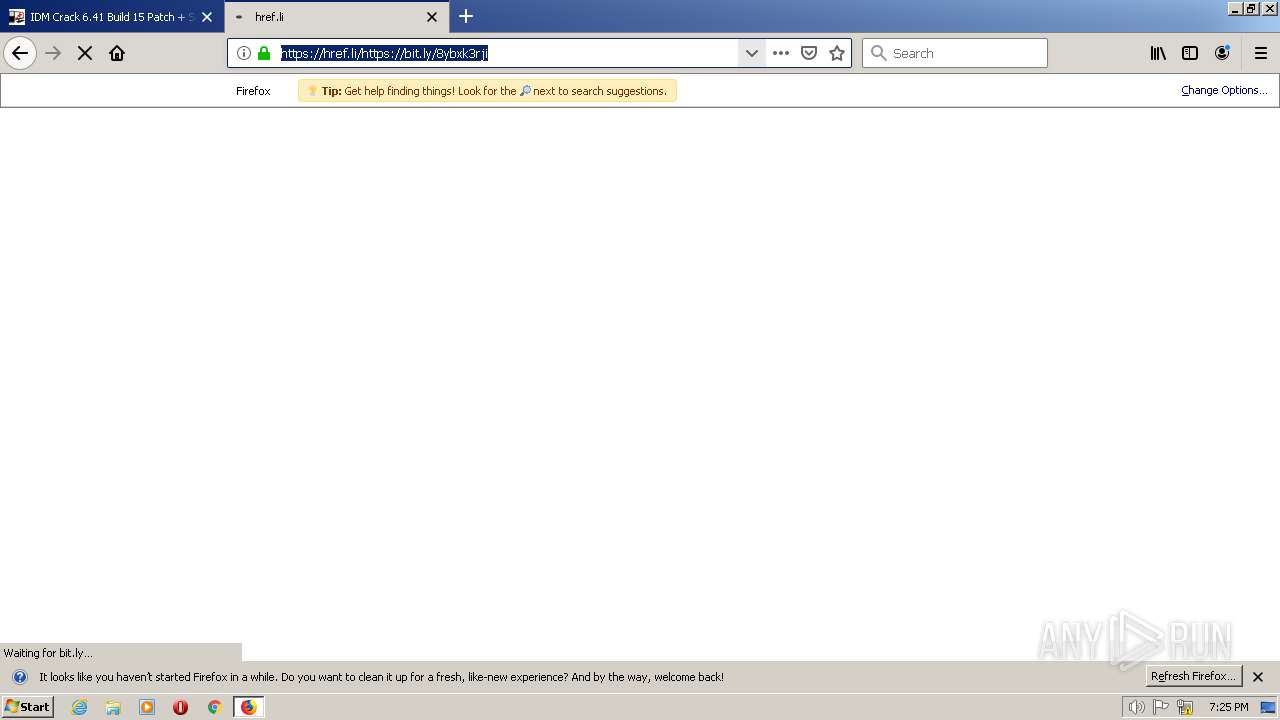
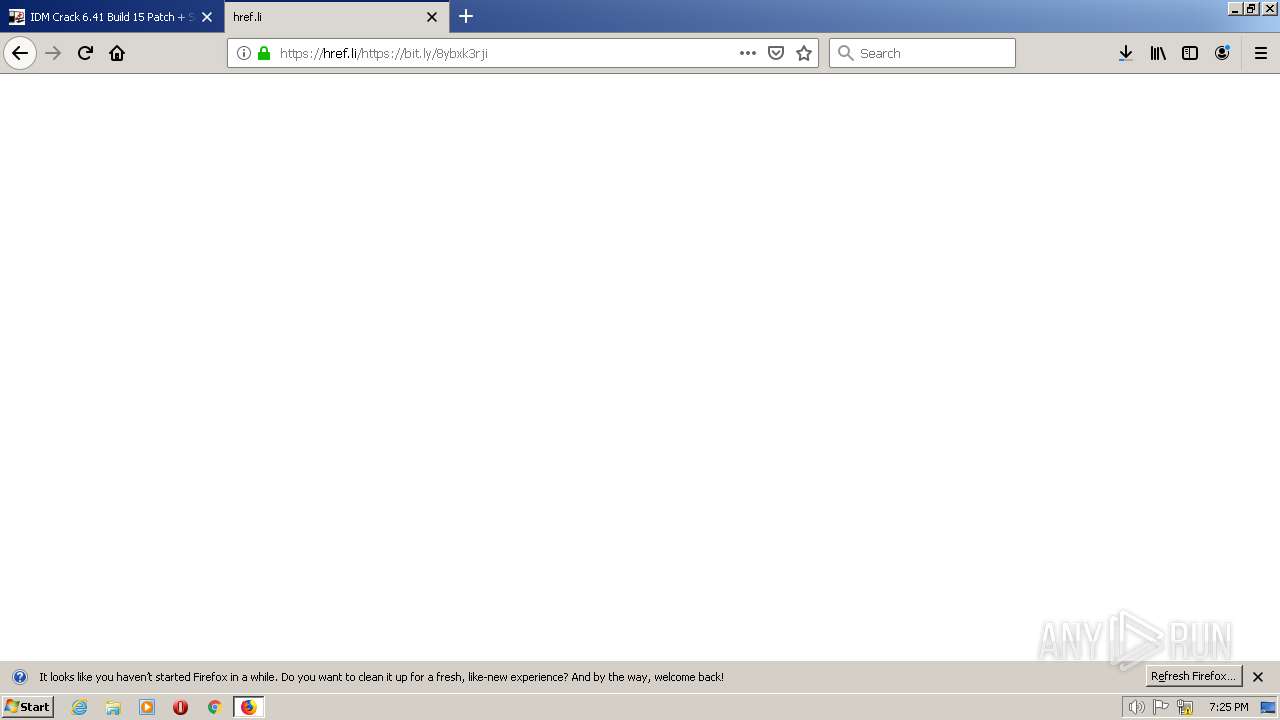
| 2448 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://abbaspc.net" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2448.13.1041131666\688977819" -childID 2 -isForBrowser -prefsHandle 2680 -prefMapHandle 2684 -prefsLen 5823 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2448 "\\.\pipe\gecko-crash-server-pipe.2448" 2708 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2712 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1480.22104\FullSetup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb1480.22104\FullSetup.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 148
Read events
7 108
Write events
40
Delete events
0
Modification events
| (PID) Process: | (2448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (2448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000008B000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2448) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7AndW2K8R2-KB3191566-x64.zip | |||
Executable files
9
Suspicious files
304
Text files
91
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2448 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\urlCache-current.bin | binary | |
MD5:6BED2A248268034CA1F73B2925365DE2 | SHA256:A45996AA907815E86366A17ED448F75A584D7B600AA9398E14DE21DFAD3D613A | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:2B6B5ABCA010270C502C5DD277CD9E7A | SHA256:99DF8717921F70577FCE3386BB7962A804E490C7157F764458001843A1EC606C | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\places.sqlite-wal | binary | |
MD5:F7D1CDDCCE6C9ED1645B897C17C7F4F0 | SHA256:59A0F6482D2956B69367F42F711E85A72A4AE9EAA91D90D1D21A4A8C48134917 | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\nltxvmn2.default\cache2\entries\16B5602581B11A25DD19099252E24416C2A0035C | binary | |
MD5:335BD73CE629136488A1AEABEF3FA5EA | SHA256:42AB95467A02D6CB69F71BD541823865D83BCD3090940E43315513E1ABC08B55 | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\prefs.js | text | |
MD5:1759FBCEFAC92AE1A7B8E457ACF71748 | SHA256:5DA473B0E0C84BE5B289DC97C259B98F674E17AF49F4723B4A90F73AA972B739 | |||
| 2448 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\permissions.sqlite-journal | binary | |
MD5:BB3A150D51F9DD1E3B1A41287E728A0B | SHA256:84B172E80E9C472CC4FCF66A5E8F87D36AC60CF4BBCA142BCCDD4BF42B4470F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
107
DNS requests
224
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2448 | firefox.exe | GET | 301 | 104.26.14.242:80 | http://abbaspc.net/wp-content/uploads/2019/04/logo_AbbasPC.Net_.png | US | — | — | malicious |
2448 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
2448 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | whitelisted |
2448 | firefox.exe | GET | 200 | 104.26.14.242:80 | http://abbaspc.net/.well-known/http-opportunistic | US | binary | 92 b | malicious |
2448 | firefox.exe | POST | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
2448 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 471 b | whitelisted |
2448 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | whitelisted |
2448 | firefox.exe | POST | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
2448 | firefox.exe | POST | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/ | US | binary | 503 b | shared |
2448 | firefox.exe | POST | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1c3 | US | binary | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
328 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
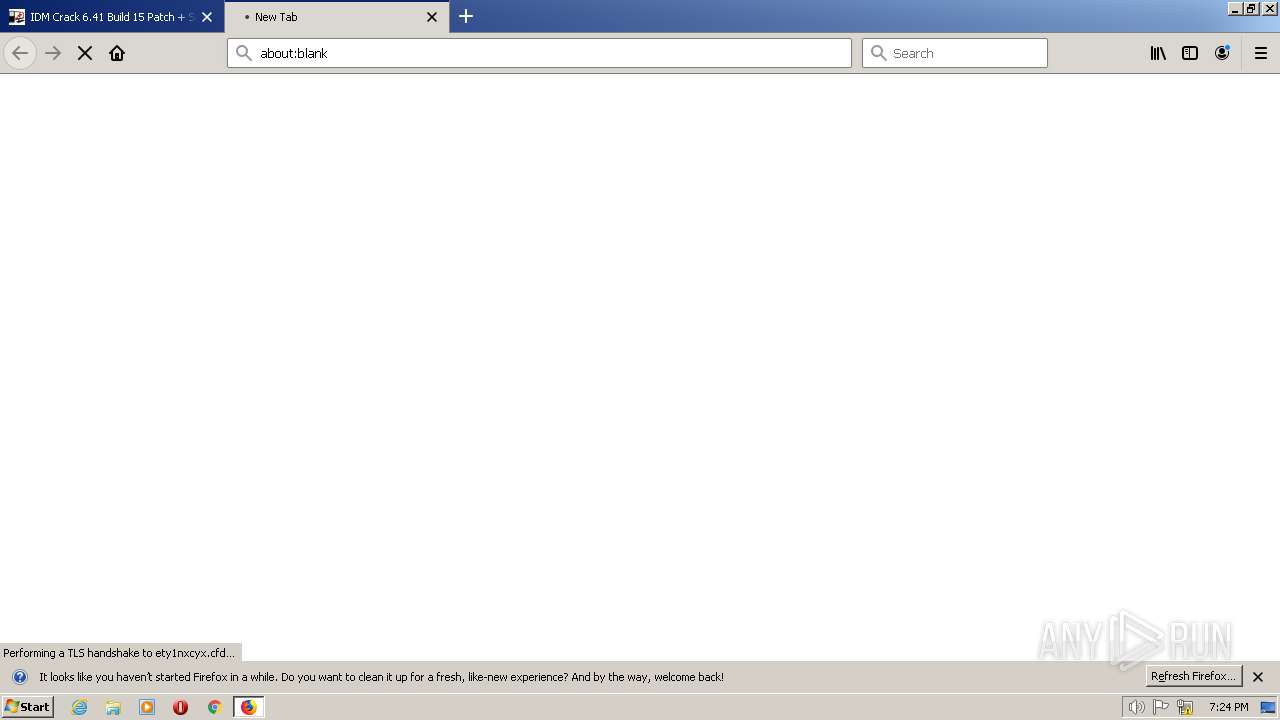
2448 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2448 | firefox.exe | 172.67.69.237:443 | abbaspc.net | CLOUDFLARENET | US | unknown |
2448 | firefox.exe | 192.0.76.3:443 | stats.wp.com | AUTOMATTIC | US | suspicious |
2448 | firefox.exe | 192.0.77.37:443 | c0.wp.com | AUTOMATTIC | US | suspicious |
2448 | firefox.exe | 52.41.158.136:443 | shavar.services.mozilla.com | AMAZON-02 | US | unknown |
2448 | firefox.exe | 192.0.77.2:443 | i0.wp.com | AUTOMATTIC | US | suspicious |
2448 | firefox.exe | 142.250.184.200:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
2448 | firefox.exe | 104.26.14.242:80 | abbaspc.net | CLOUDFLARENET | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
abbaspc.net |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
stats.wp.com |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
328 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
328 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2712 | FullSetup.exe | A Network Trojan was detected | ET MALWARE Trojan Generic - POST To gate.php with no referer |
2712 | FullSetup.exe | A Network Trojan was detected | ET MALWARE Trojan Generic - POST To gate.php with no accept headers |
2712 | FullSetup.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |