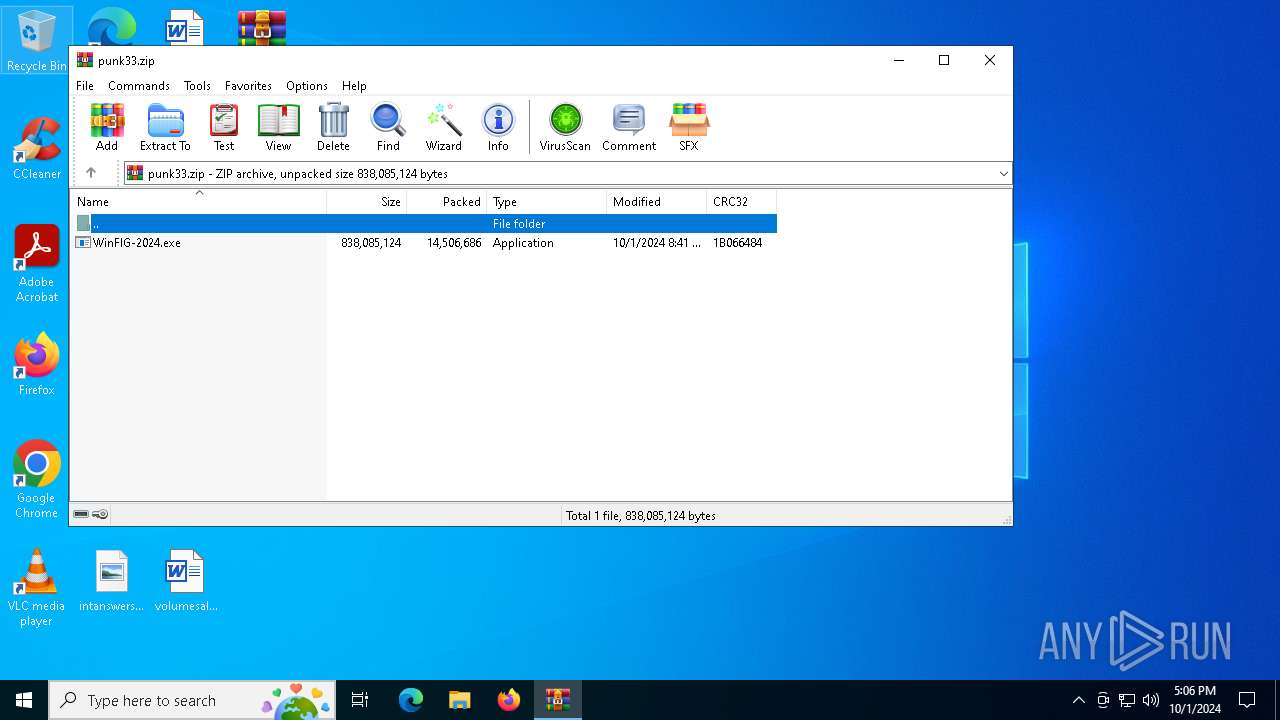
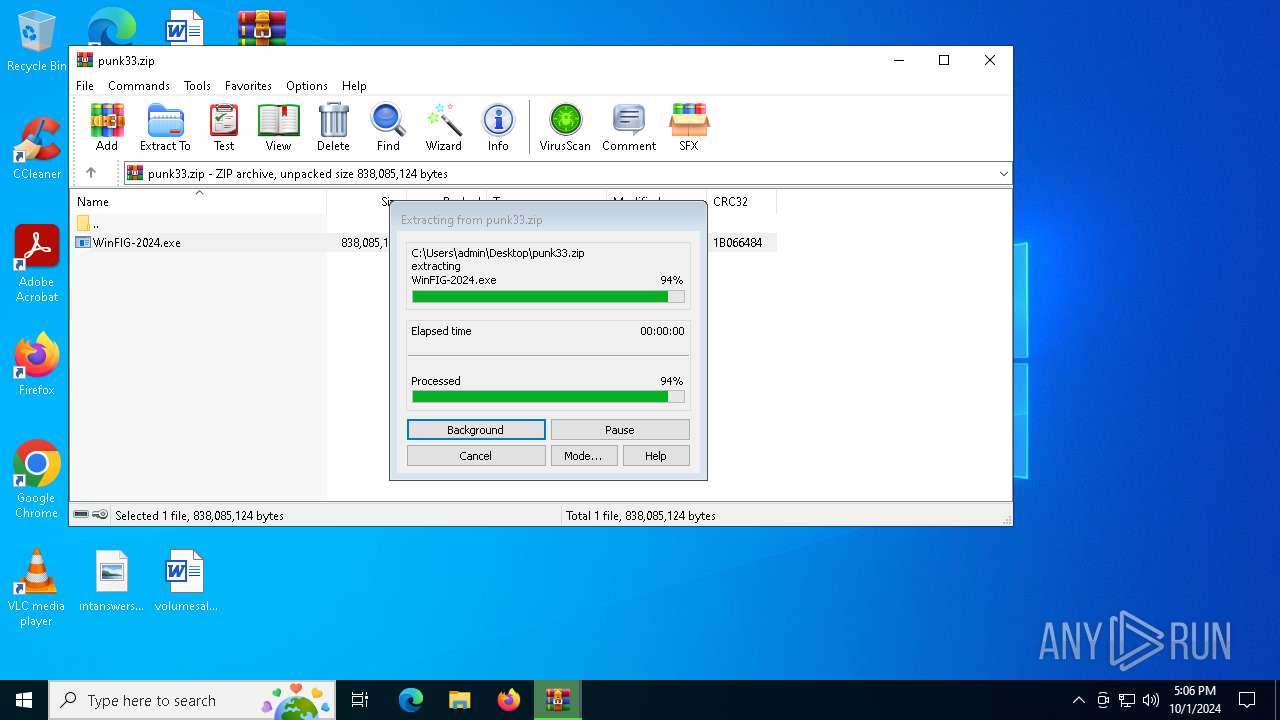
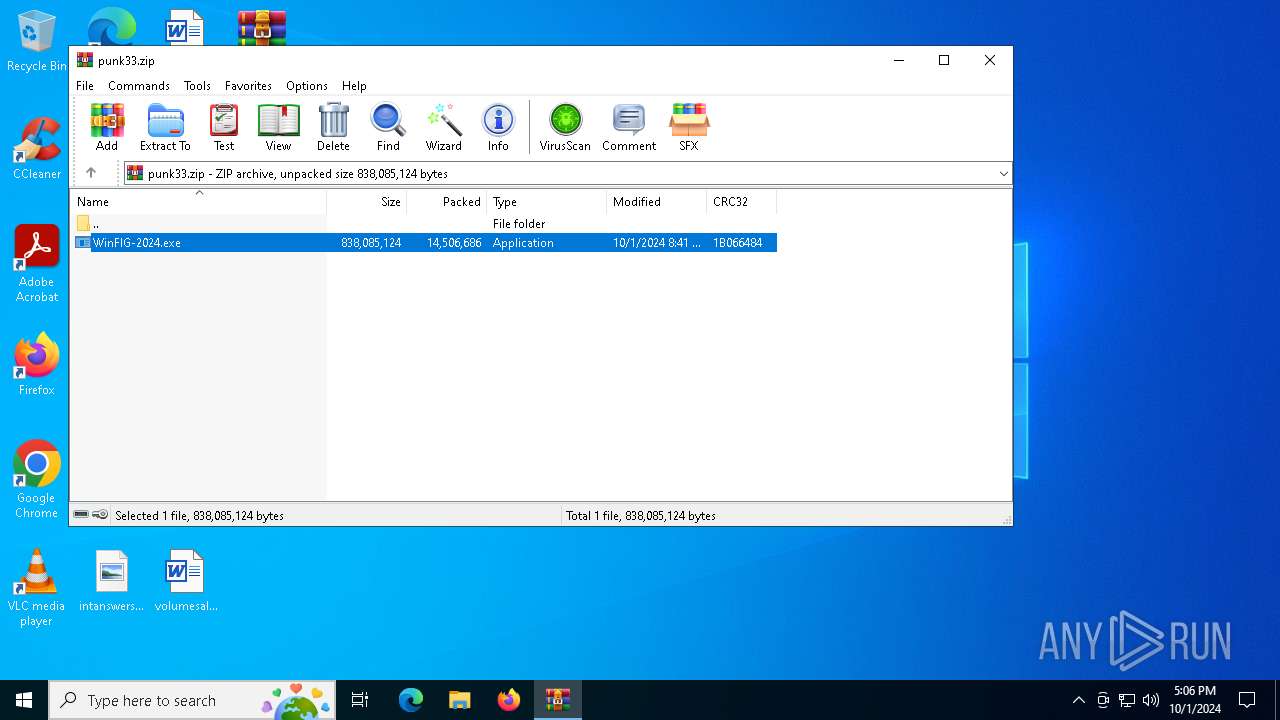
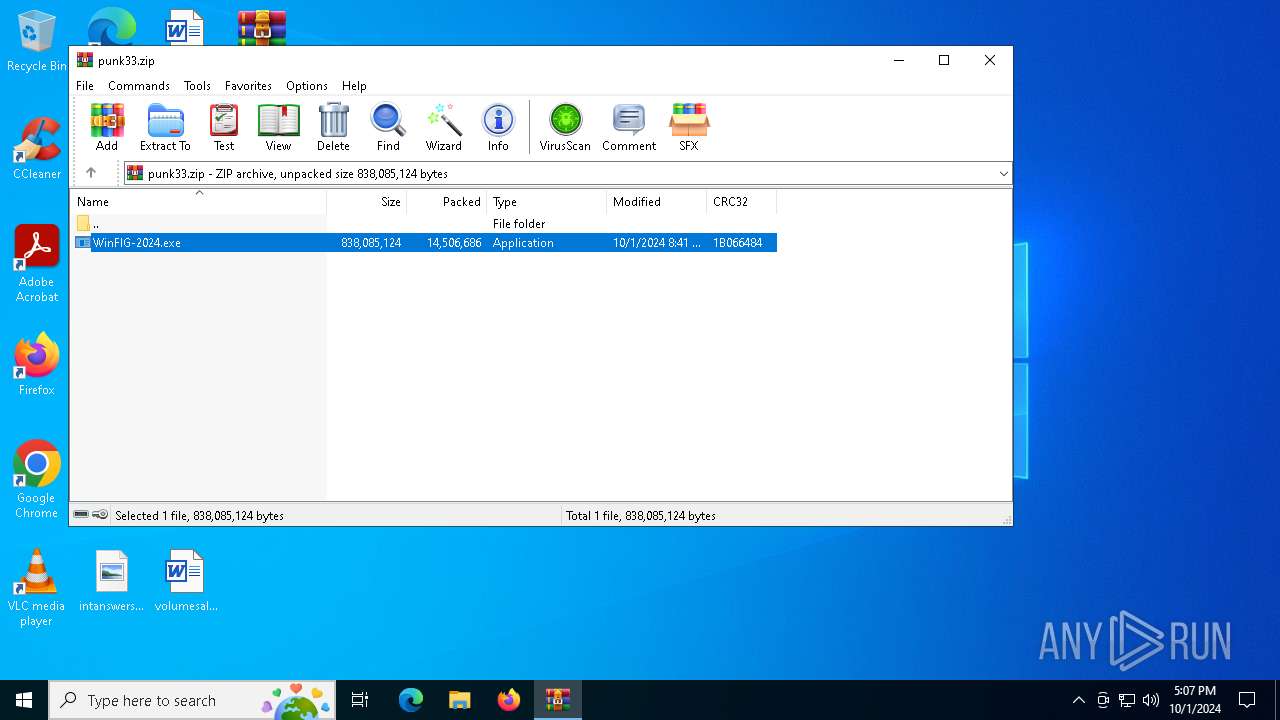
| File name: | punk33.zip |
| Full analysis: | https://app.any.run/tasks/b6818956-7bdb-450b-854d-2932fb02f456 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 01, 2024, 17:06:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E112BE4A8E3FEAE5D5937E1F9314C35D |
| SHA1: | 0102DB1C98A4CC550E5A1F094E8019C1298A5BE5 |
| SHA256: | EDFFDA27CAB787A462783AF40BAD3B3BE859930100F9BB637E7AEA3FA6102ED9 |
| SSDEEP: | 196608:gzs/sjwS0sMGwXUrecLcYEipCQ4mZiB597NWv:gz7jwVXm/YQ4mZiB5VNWv |
MALICIOUS
LUMMA has been detected (YARA)
- WinFIG-2024.exe (PID: 5092)
- BitLockerToGo.exe (PID: 696)
Connects to the CnC server
- svchost.exe (PID: 2256)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2256)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 696)
STEALC has been detected (YARA)
- BitLockerToGo.exe (PID: 3988)
- 9YBKCEUD30A550WLYUYS40Q9HB.exe (PID: 4684)
AutoIt loader has been detected (YARA)
- Voyuer.pif (PID: 6456)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5724)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2256)
Executable content was dropped or overwritten
- BitLockerToGo.exe (PID: 696)
- cmd.exe (PID: 6828)
- Voyuer.pif (PID: 6456)
Starts CMD.EXE for commands execution
- IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe (PID: 6028)
- cmd.exe (PID: 6828)
Executing commands from a ".bat" file
- IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe (PID: 6028)
Get information on the list of running processes
- cmd.exe (PID: 6828)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6828)
Application launched itself
- cmd.exe (PID: 6828)
- Voyuer.pif (PID: 6456)
Starts application with an unusual extension
- cmd.exe (PID: 6828)
- Voyuer.pif (PID: 6456)
The executable file from the user directory is run by the CMD process
- Voyuer.pif (PID: 6456)
There is functionality for communication over UDP network (YARA)
- 9YBKCEUD30A550WLYUYS40Q9HB.exe (PID: 4684)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 5724)
Checks supported languages
- BitLockerToGo.exe (PID: 696)
- WinFIG-2024.exe (PID: 5092)
Checks proxy server information
- WinFIG-2024.exe (PID: 5092)
Reads the computer name
- BitLockerToGo.exe (PID: 696)
- WinFIG-2024.exe (PID: 5092)
Reads the software policy settings
- BitLockerToGo.exe (PID: 696)
Manual execution by a user
- cmd.exe (PID: 7144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:01 01:41:26 |
| ZipCRC: | 0x1b066484 |
| ZipCompressedSize: | 14506686 |
| ZipUncompressedSize: | 838085124 |
| ZipFileName: | WinFIG-2024.exe |
Total processes
148
Monitored processes
21
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | WinFIG-2024.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | cmd /c md 10518 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2608 | findstr /I "avastui avgui bdservicehost nswscsvc sophoshealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2824 | C:\Users\admin\AppData\Local\Temp\10518\Voyuer.pif | C:\Users\admin\AppData\Local\Temp\10518\Voyuer.pif | — | Voyuer.pif | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 3 Modules
| |||||||||||||||
| 3988 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | 9YBKCEUD30A550WLYUYS40Q9HB.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4232 | findstr /V "BATHROOMSOFTENPAYCOMMERCIAL" Socket | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 809
Read events
5 800
Write events
9
Delete events
0
Modification events
| (PID) Process: | (5724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\punk33.zip | |||
| (PID) Process: | (5724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3988) BitLockerToGo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3988) BitLockerToGo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3988) BitLockerToGo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
4
Suspicious files
10
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5724 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5724.19065\WinFIG-2024.exe | — | |
MD5:— | SHA256:— | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Uniprotkb | binary | |
MD5:69D07759583AFA982405CEDF0B879B8E | SHA256:2B3F63621C8AE1EB1BC3DFC4683EC983277AC17AEA03ACECEBC54969A723AB72 | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Socket | binary | |
MD5:AB55FC08EAEF2F50565980B99511F625 | SHA256:5B4799EA6F20B4B5CF53A328E52A7ED1982E0C1A797CEED9F8A05D89985BA3BC | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Delegation | binary | |
MD5:E82A72CAE193B8525A968245FE8934CC | SHA256:3D701EA1DDC78F91919E733B8E8992C708A43B40DD58CE46E0500A6684456B06 | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Cherry | binary | |
MD5:4950C42897E4B4BE654BF6A0D6AD1874 | SHA256:83D0683945DCF8275E79D63424F3CF793820B9437A41E239D2BC758E25473110 | |||
| 696 | BitLockerToGo.exe | C:\Users\admin\AppData\Local\Temp\9YBKCEUD30A550WLYUYS40Q9HB.exe | executable | |
MD5:ACCCB5D6308487DA88B2F05B2F4F6234 | SHA256:F188AAF2E67A048F1CFA0AB7758AC80B0E4A1167042F55176E4AC0D273B26744 | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Explains | binary | |
MD5:D32CBD96F1A1A04DDCC9A1A208FB81E5 | SHA256:603230F8180F5D1D68621254976467ACEF4EAED5DD4193AA6C03F7384AD27DD1 | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Victor | binary | |
MD5:C823E5A74879DA9CBFF89361425B11B3 | SHA256:7B39896A8D5A68E5F3DA8EC64F9CEAB3F533D05FDB18754DB5B0A48ED308341B | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Killing | text | |
MD5:632076E43FF6F1C2EC3FC59D2AC115C5 | SHA256:432A473F21A57610DF93773A79AE94365D6C2B6AA1555123BFDD658A6F28CF2F | |||
| 6028 | IHTJ16X567IR4KA7ZWD9MGCMHYIEXF.exe | C:\Users\admin\AppData\Local\Temp\Www | binary | |
MD5:D7DB0C4F504D819DE277753119685589 | SHA256:AAF0659F2BFF006009684C04963CE6B4FD996FC341C96E1DB85CE9EA5332DAB4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
56
DNS requests
35
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
512 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1008 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1008 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2868 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2356 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6928 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2356 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
pianoswimen.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (gutterydhowi .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (vozmeatillu .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (ghostreedmnu .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (offensivedzvju .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (reinforcenh .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (vozmeatillu .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (fragnantbui .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (drawzhotdog .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (stogeneratmns .shop) |