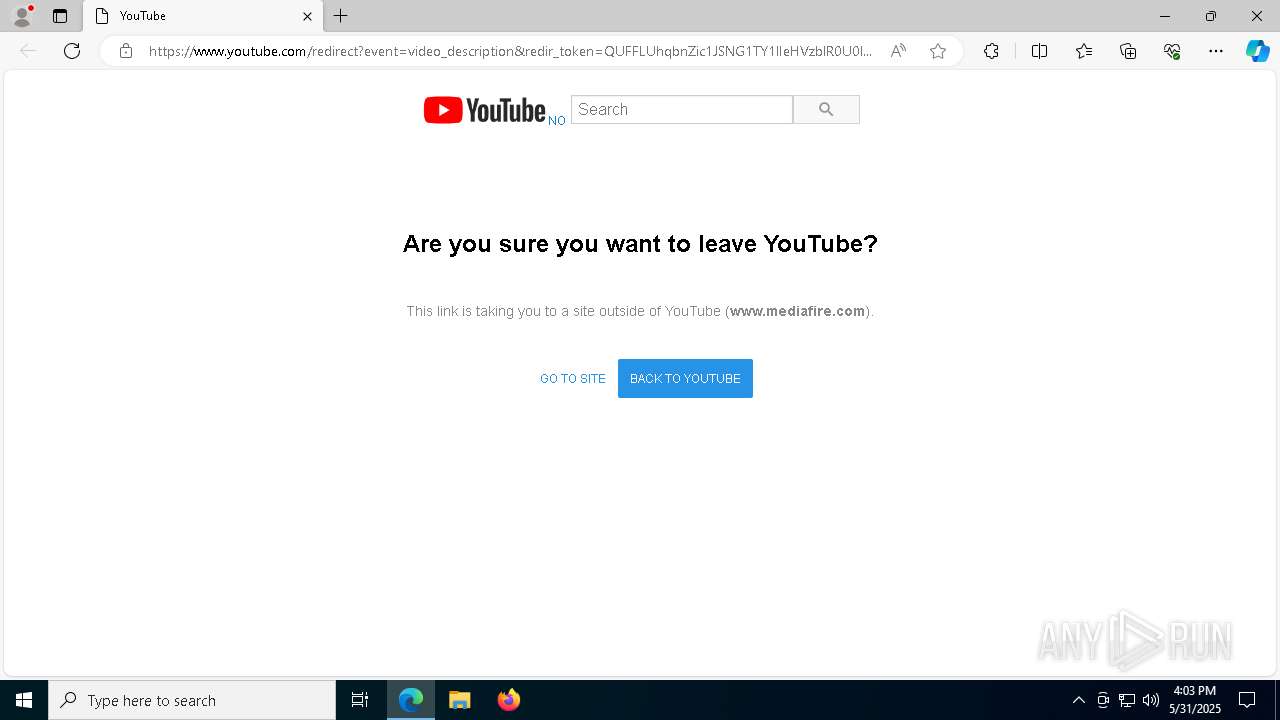
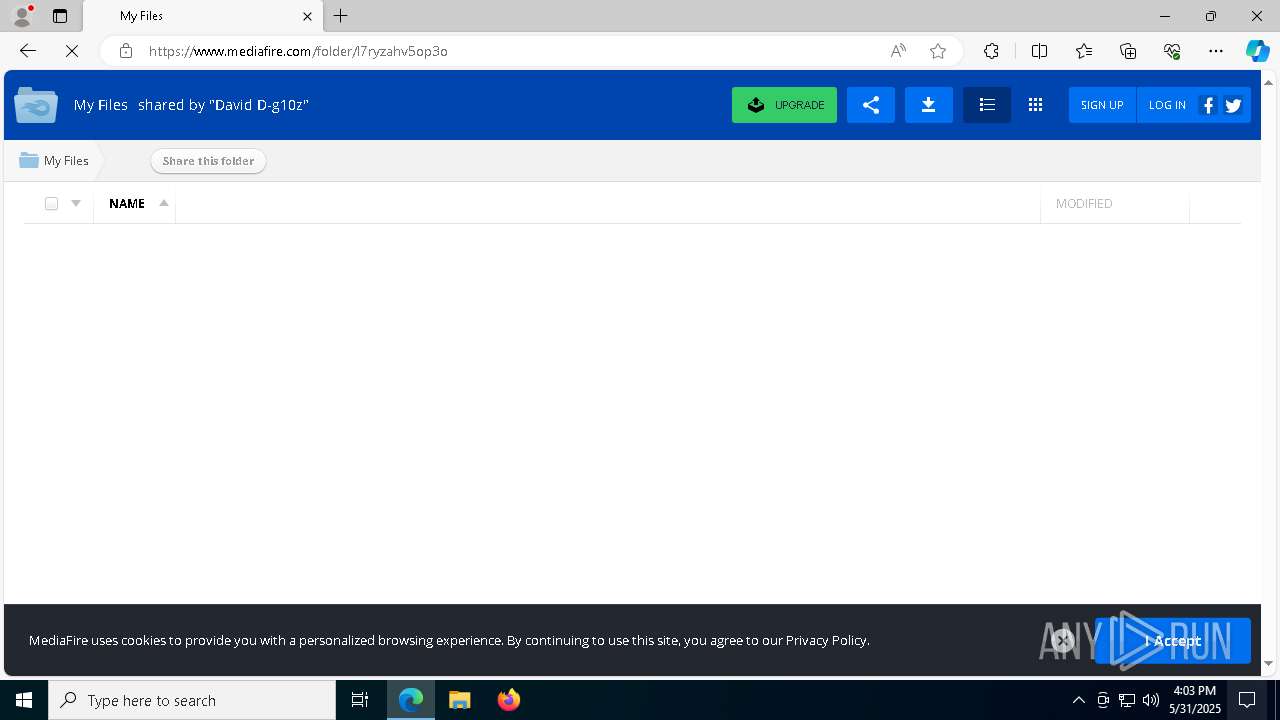
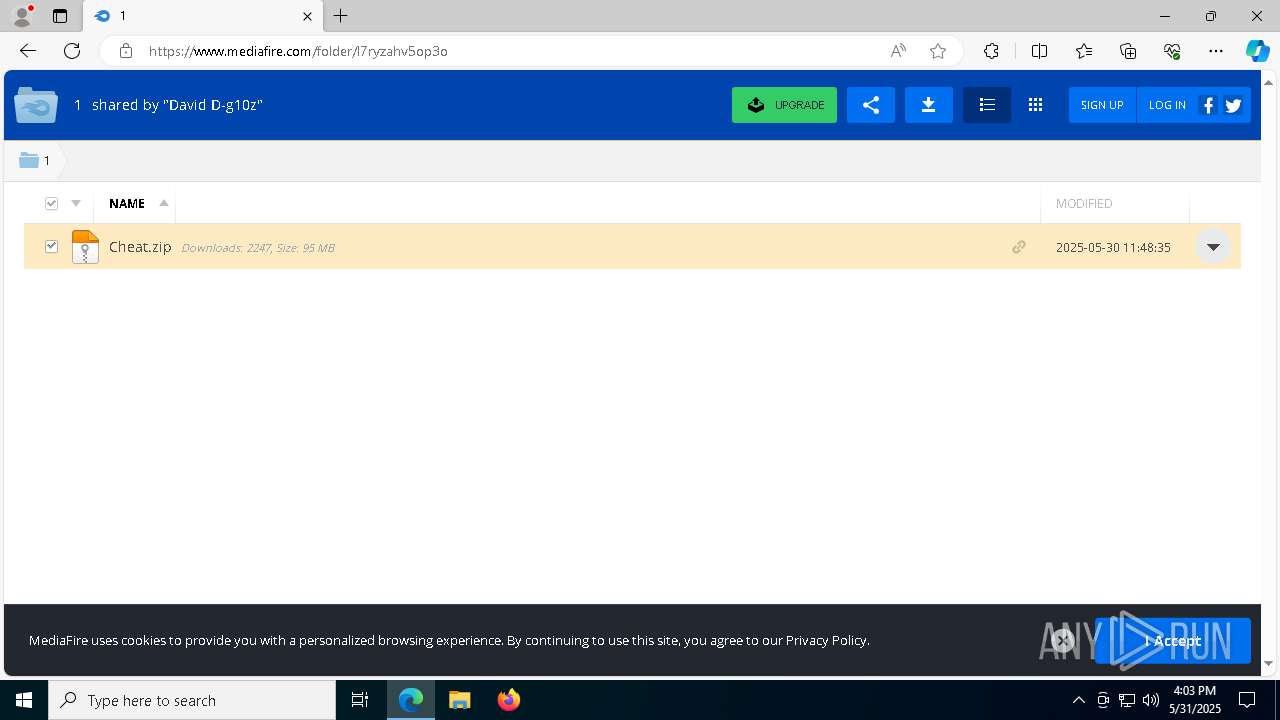
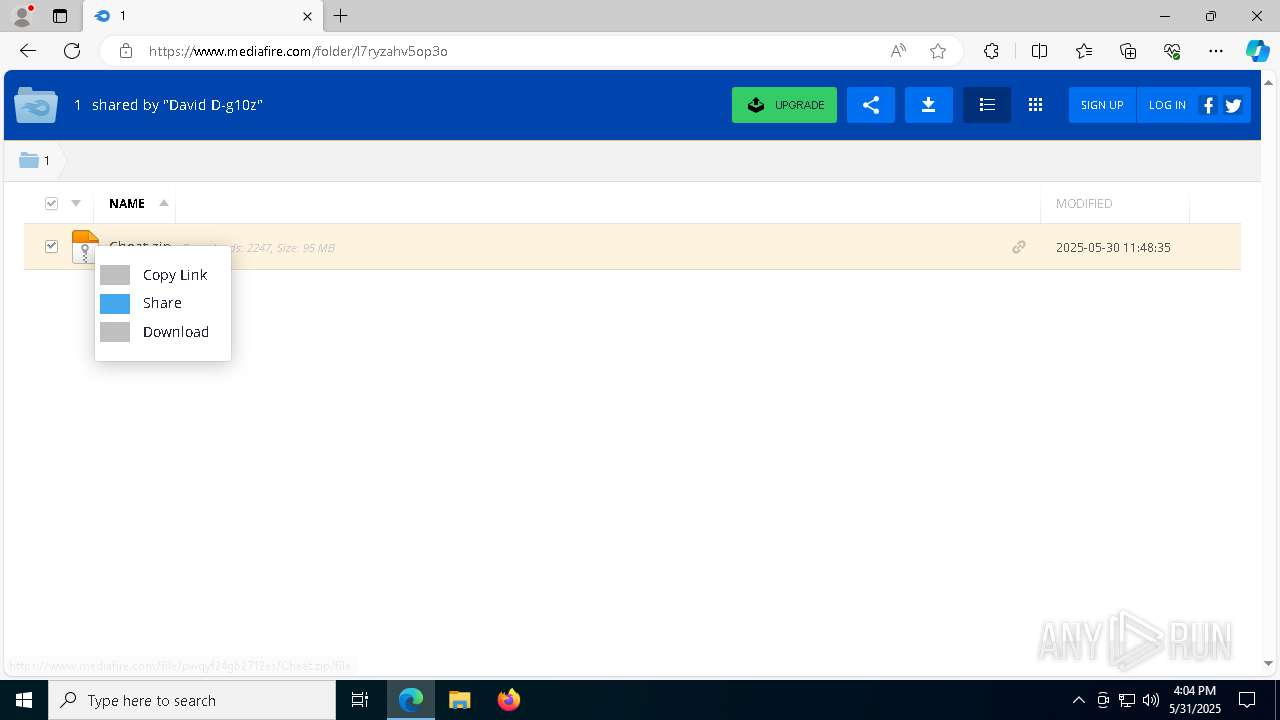
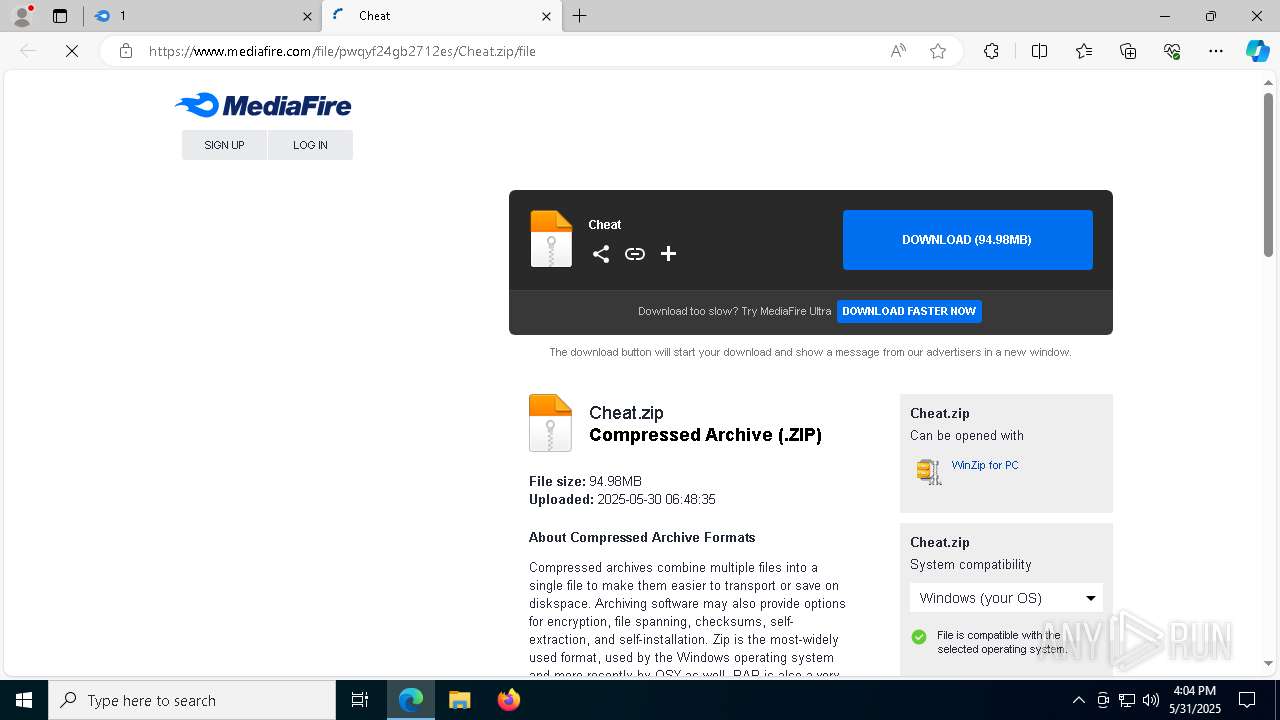
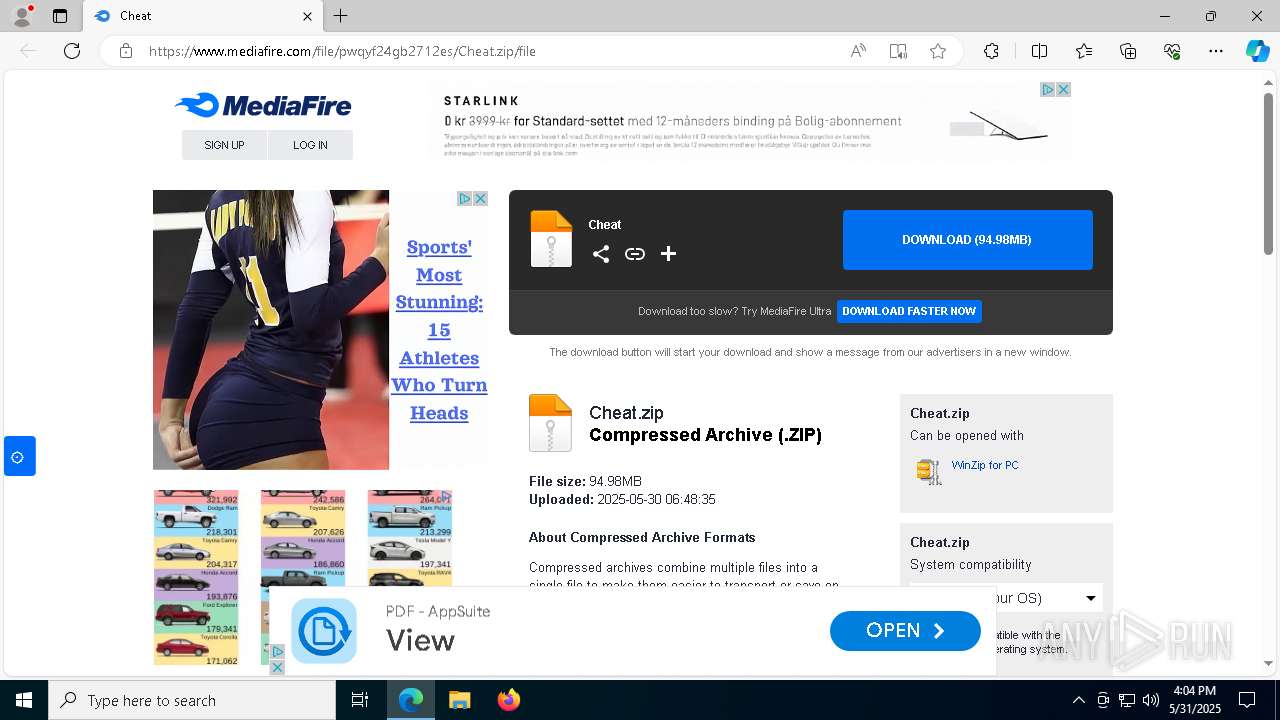
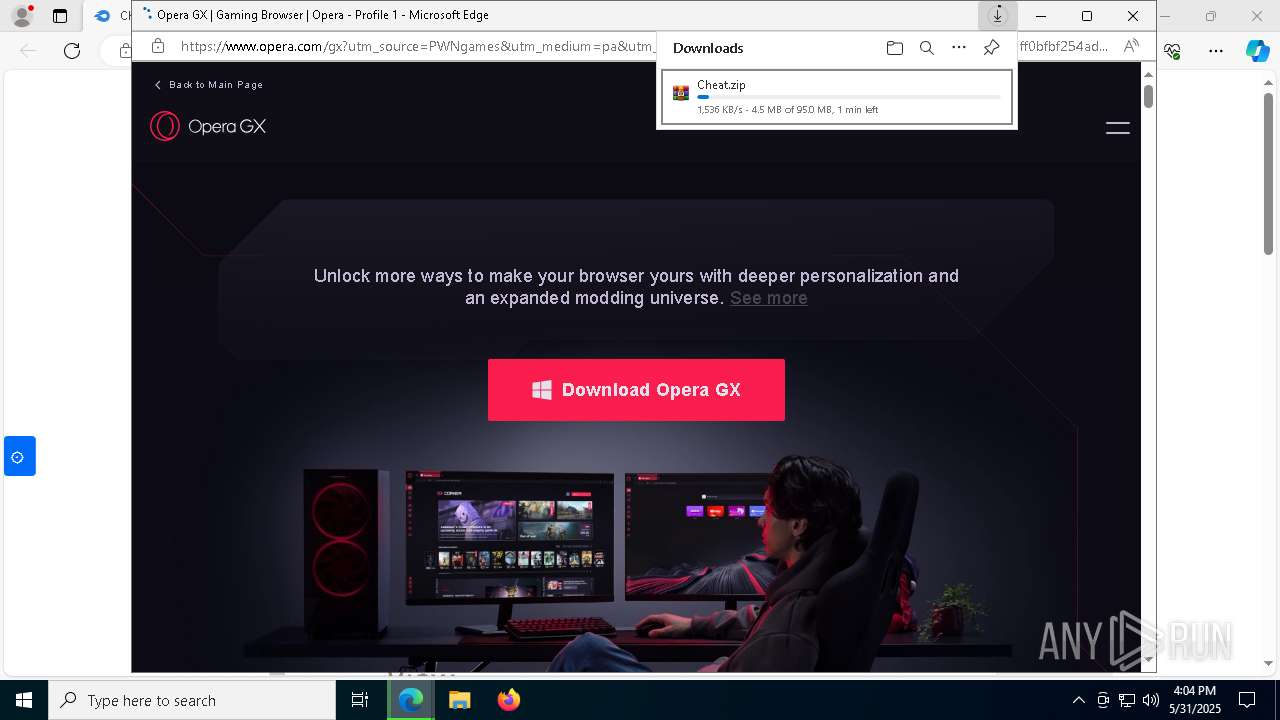
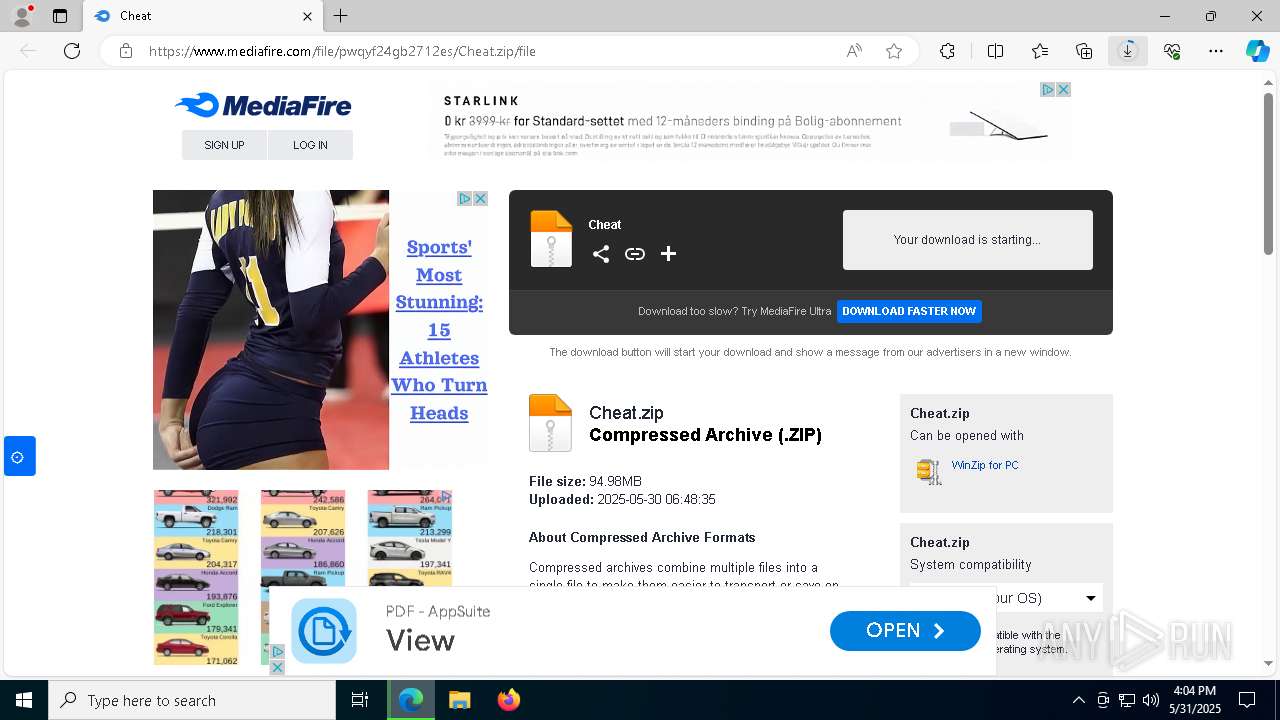
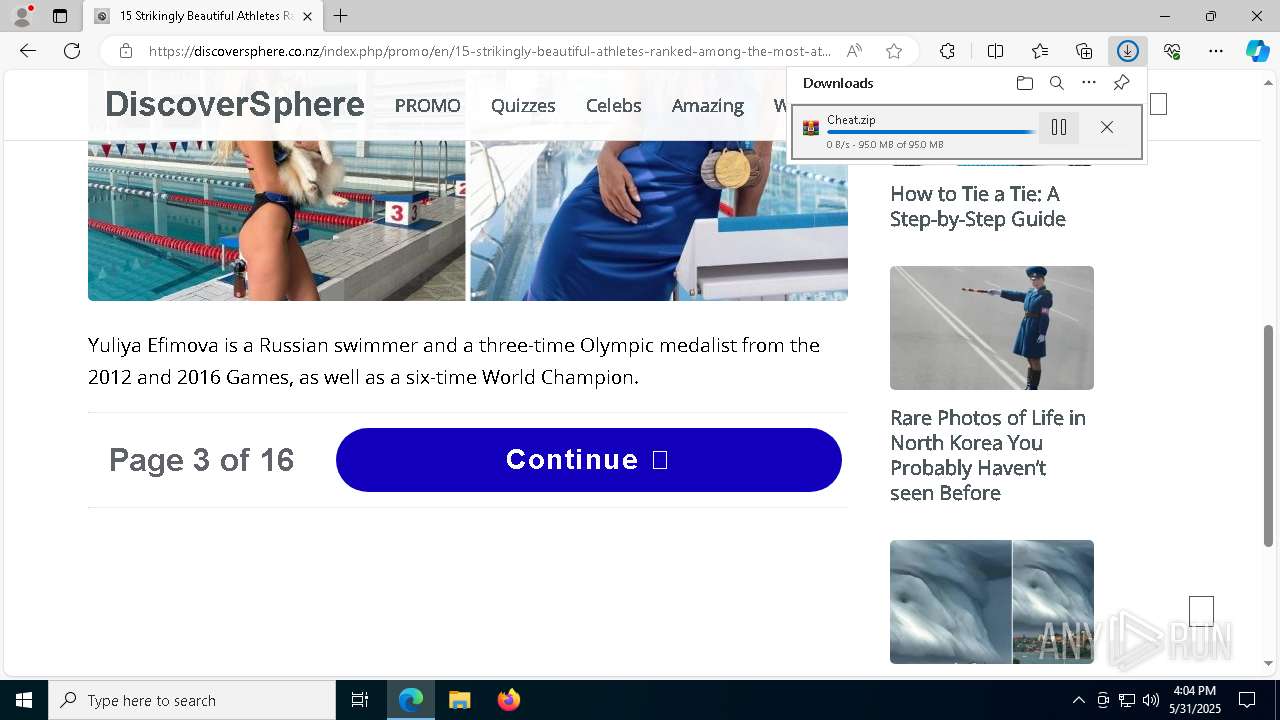
| URL: | https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqbnZic1JSNG1TY1lIeHVzblR0U0lsbGdBU3BTUXxBQ3Jtc0tsOFBHMjhPV3NfdUZwR1RjM25oNHBsY1VrM1piZVpzMkFiM0xTZzJaY3V4M3lndk1aM2pzQ1EtdVpsdmV3d3pXaGc0SGN4ZEpmREhqTlJWNGFtcnVndm8wSHJ6eTVtVk9DZ2tjWHVPVm4yazVZOUhxTQ&q=https%3A%2F%2Fwww.mediafire.com%2Ffolder%2Fl7ryzahv5op3o&v=t0B0l2r7sWk |
| Full analysis: | https://app.any.run/tasks/dc6b2599-57a9-43a1-ac3e-a47098b099e1 |
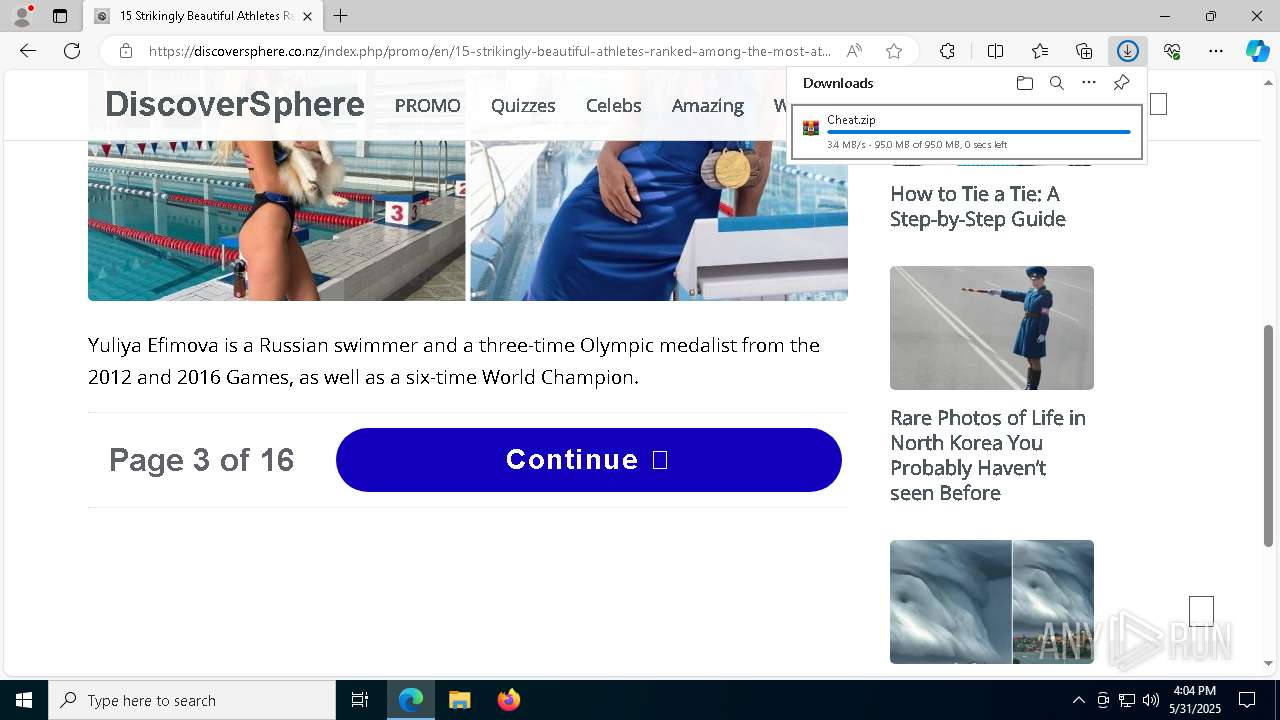
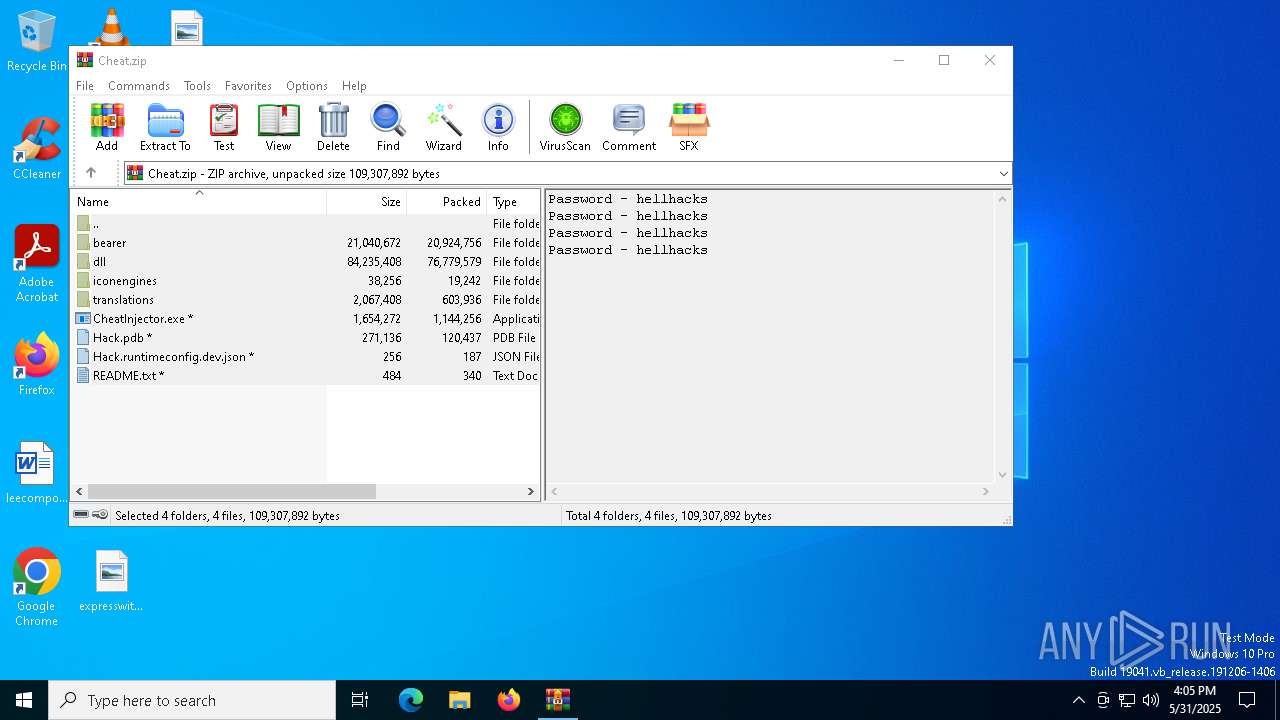
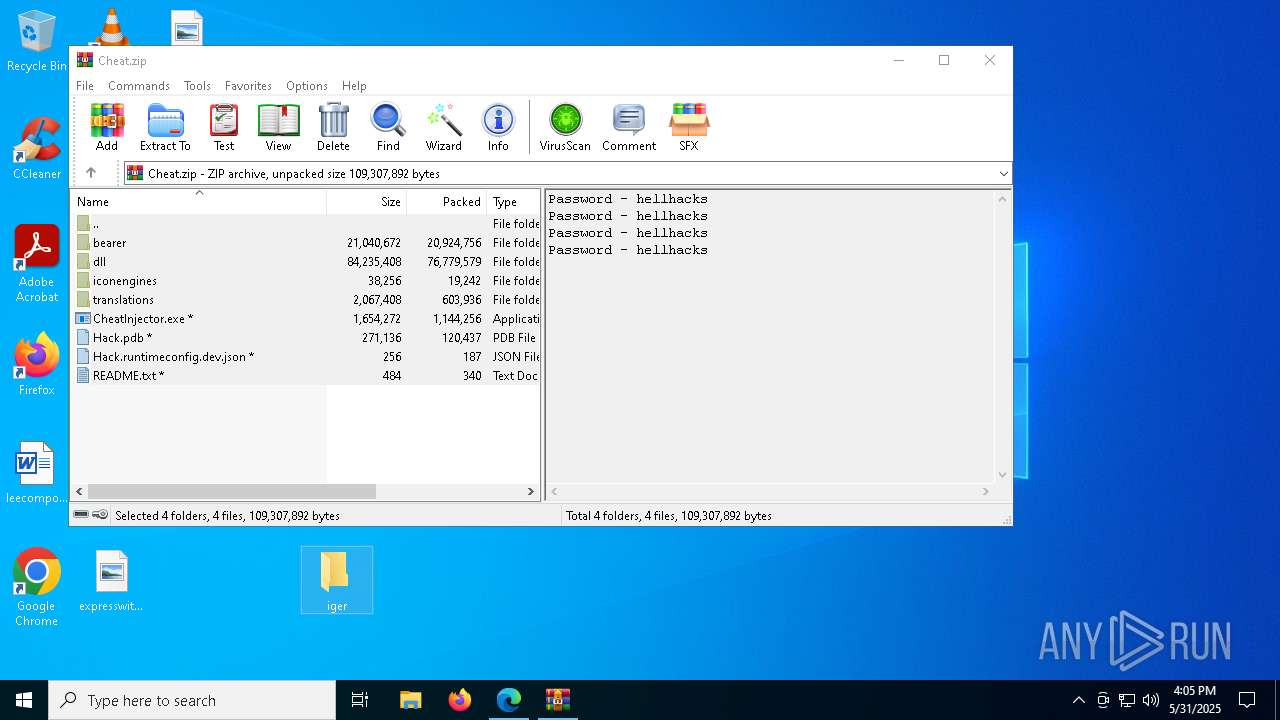
| Verdict: | Malicious activity |
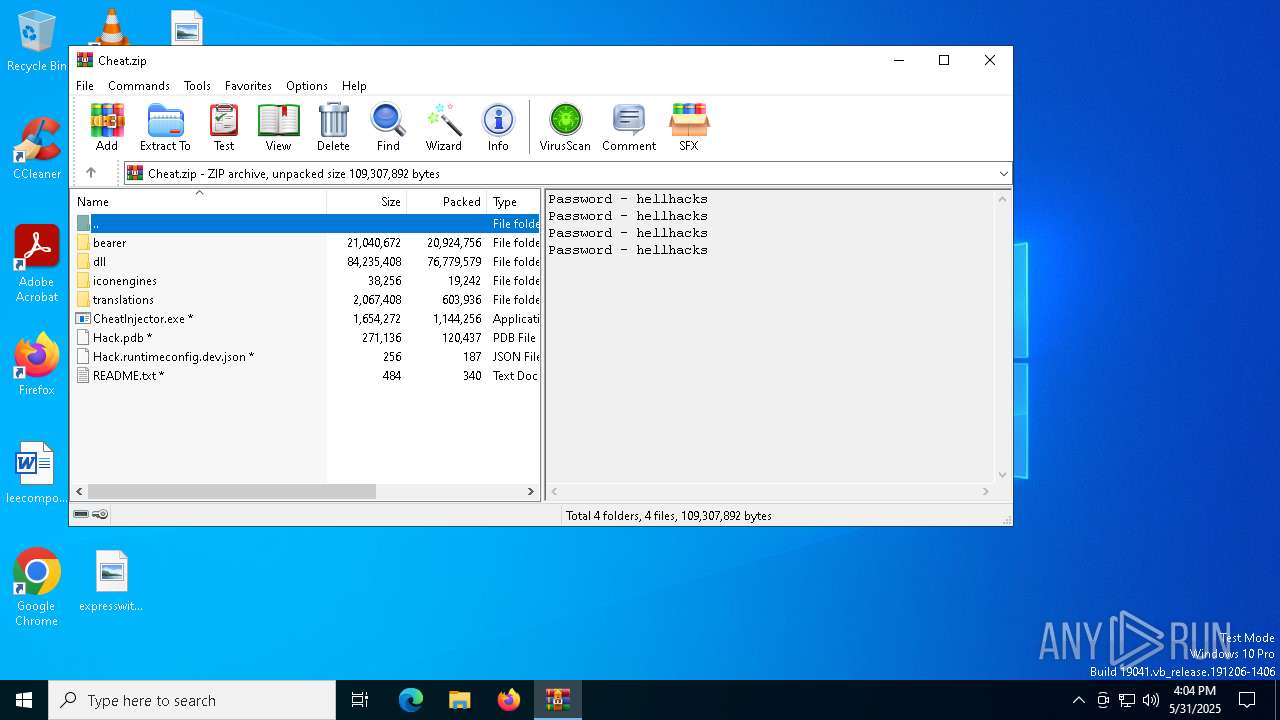
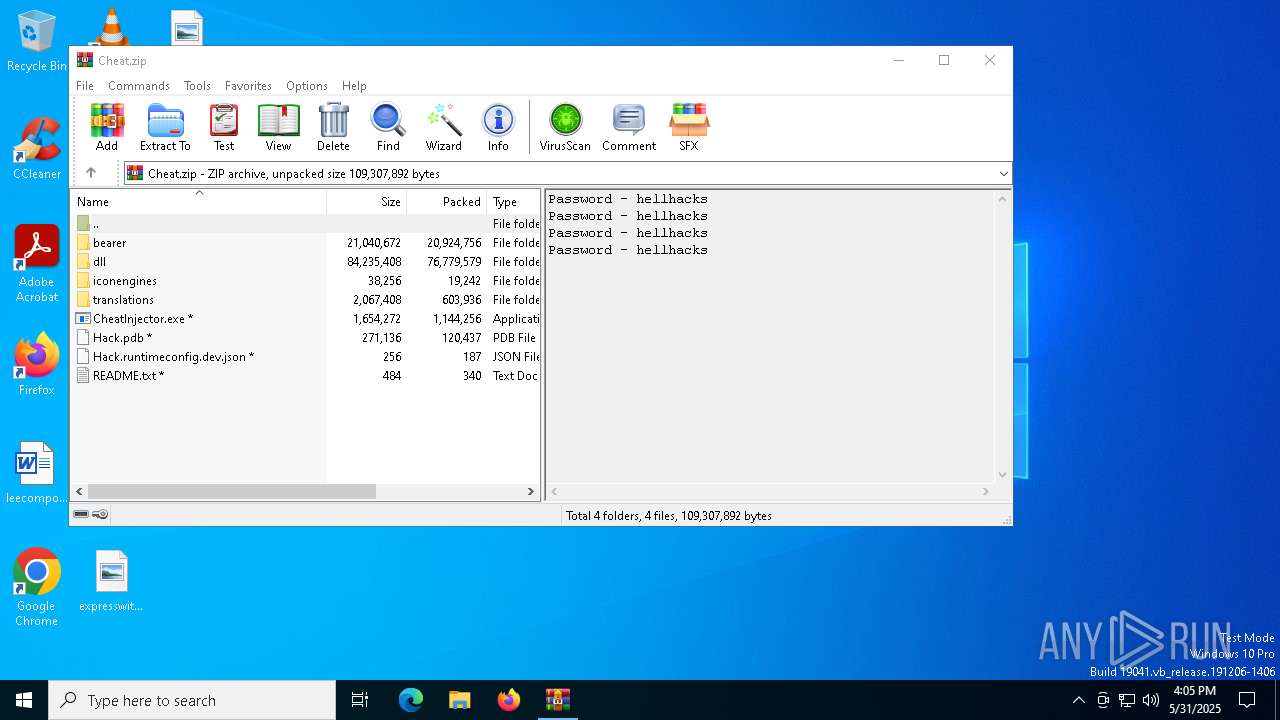
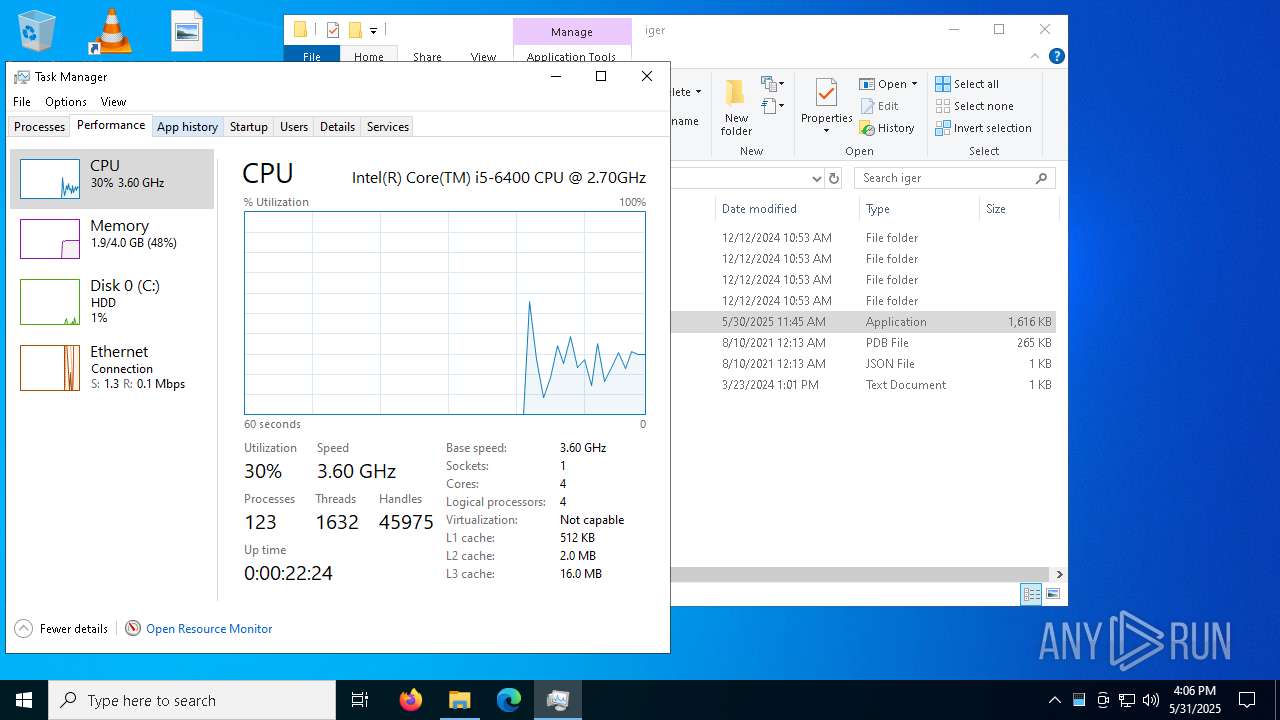
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 31, 2025, 16:03:39 |
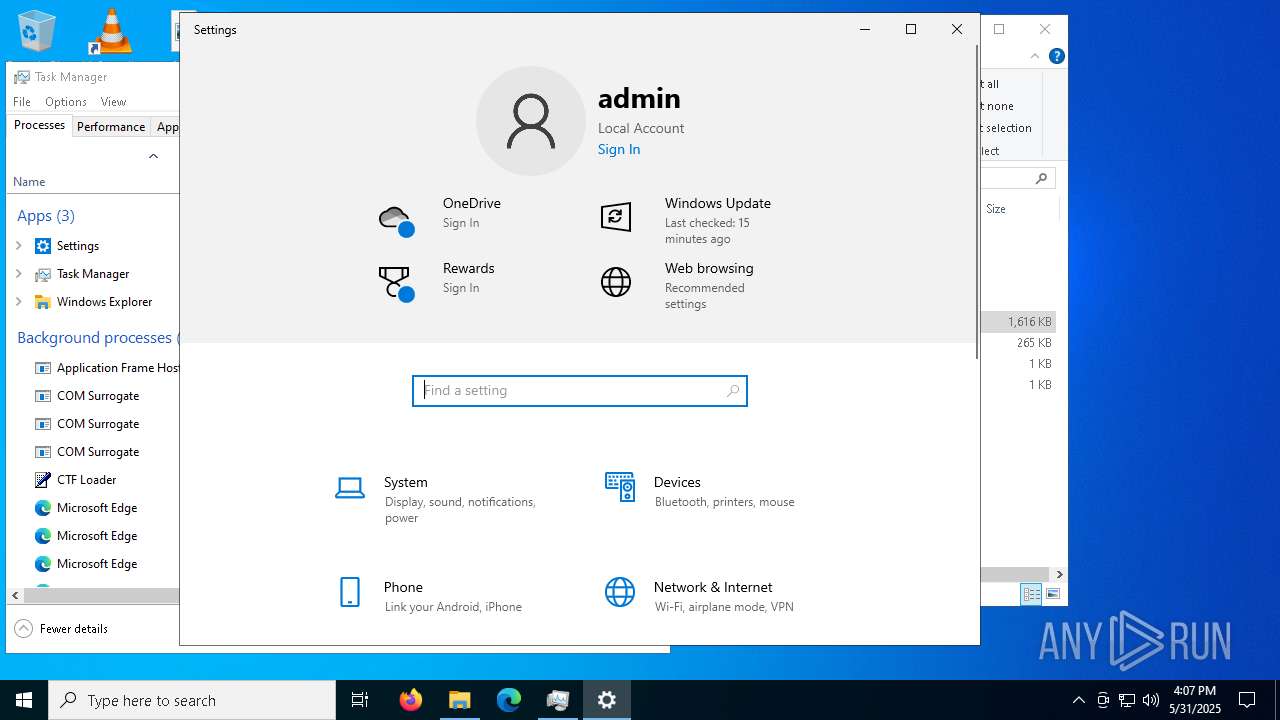
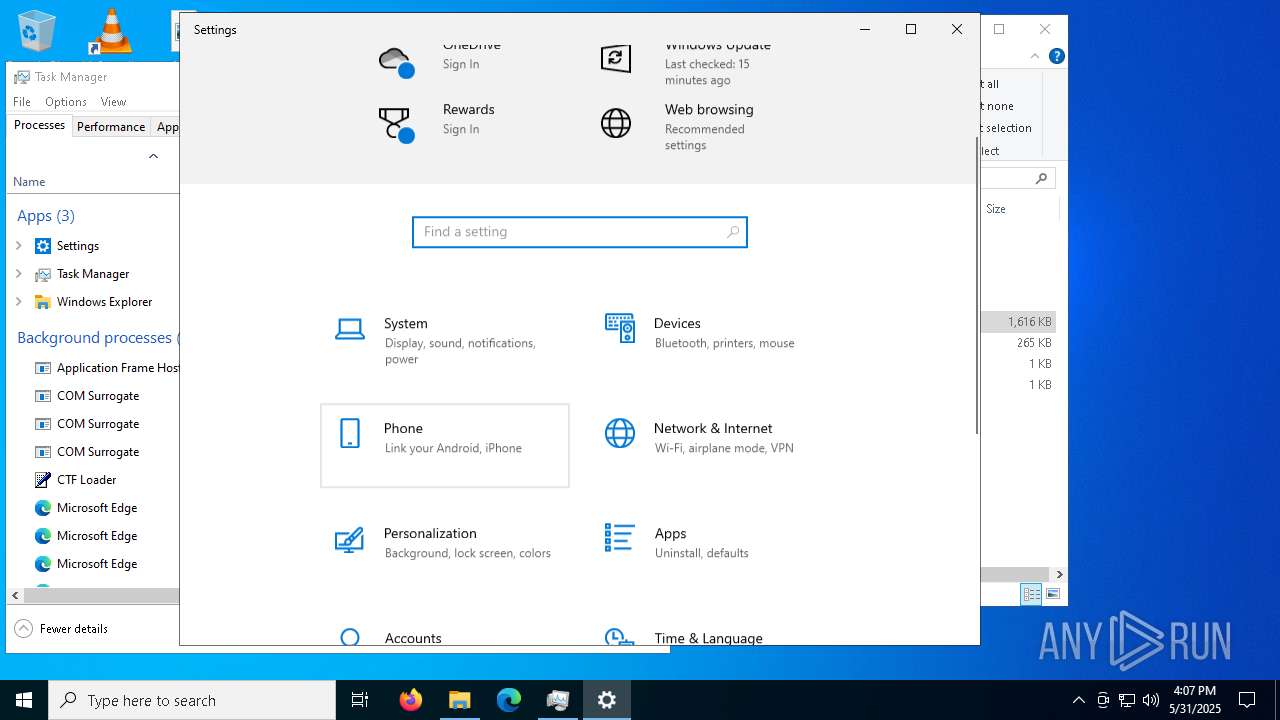
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
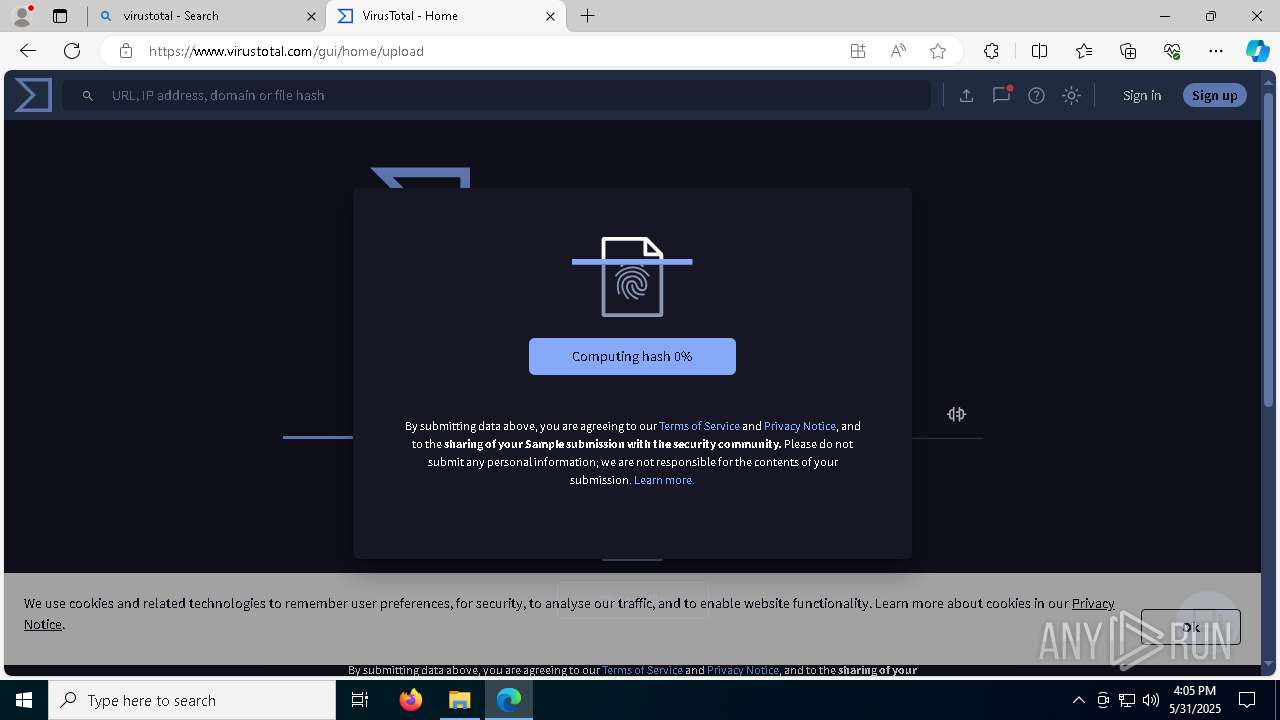
| MD5: | 3974292D7DC68252E66FF85902836008 |
| SHA1: | C69AEDA6BC324D6B090C6E06D05D54B9DAC63766 |
| SHA256: | EDEA33521872AB5808A8E85EB7B4B32DA1AD22CD5F2294439EF1AE758FDCF2A2 |
| SSDEEP: | 6:2OLUxGKmKLqZr8frgn0WvCtKKVD+Afsa6g1V20+XLUK12TLK3zh3eGHv:2jGRfr8fri0F8KVD6UV20Eo2m8F3eWv |
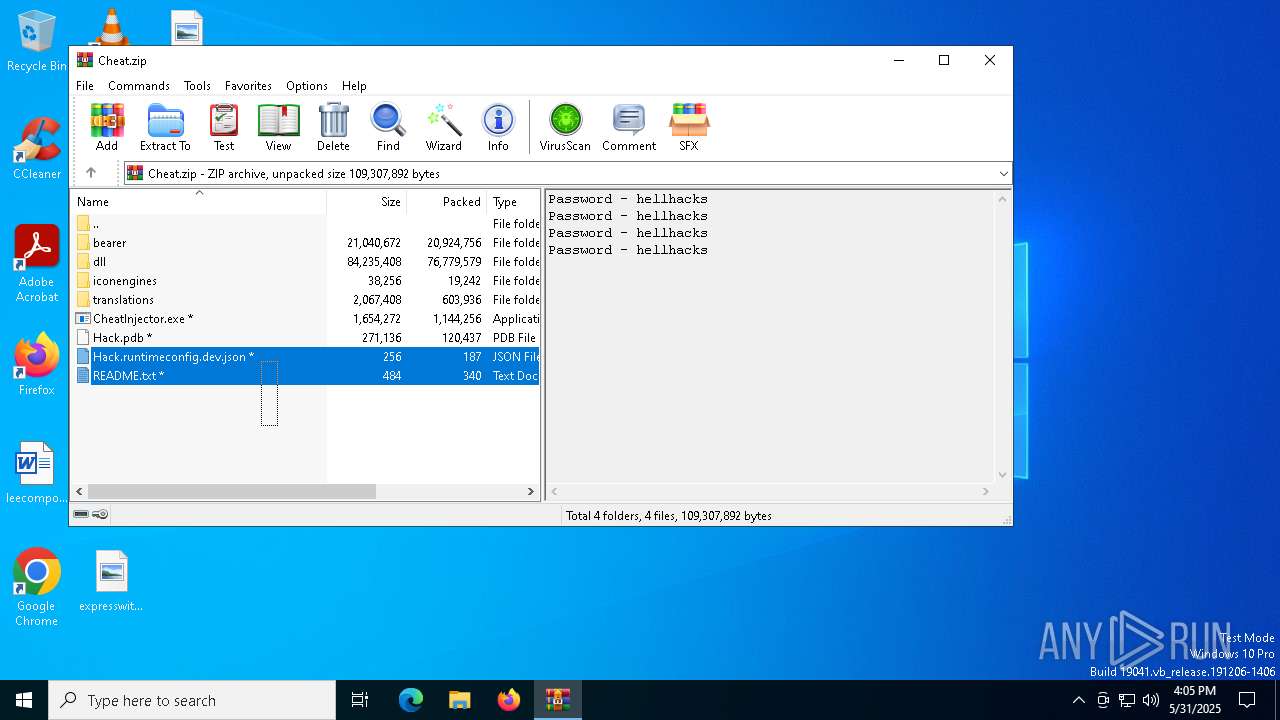
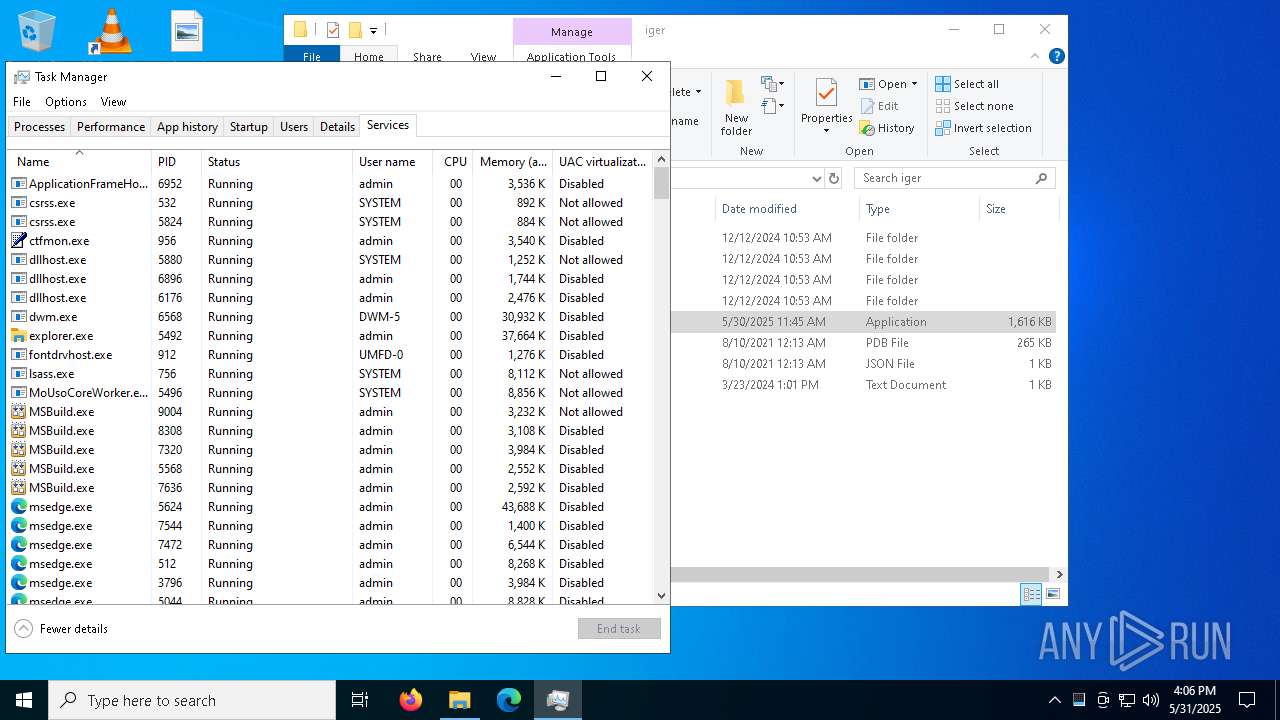
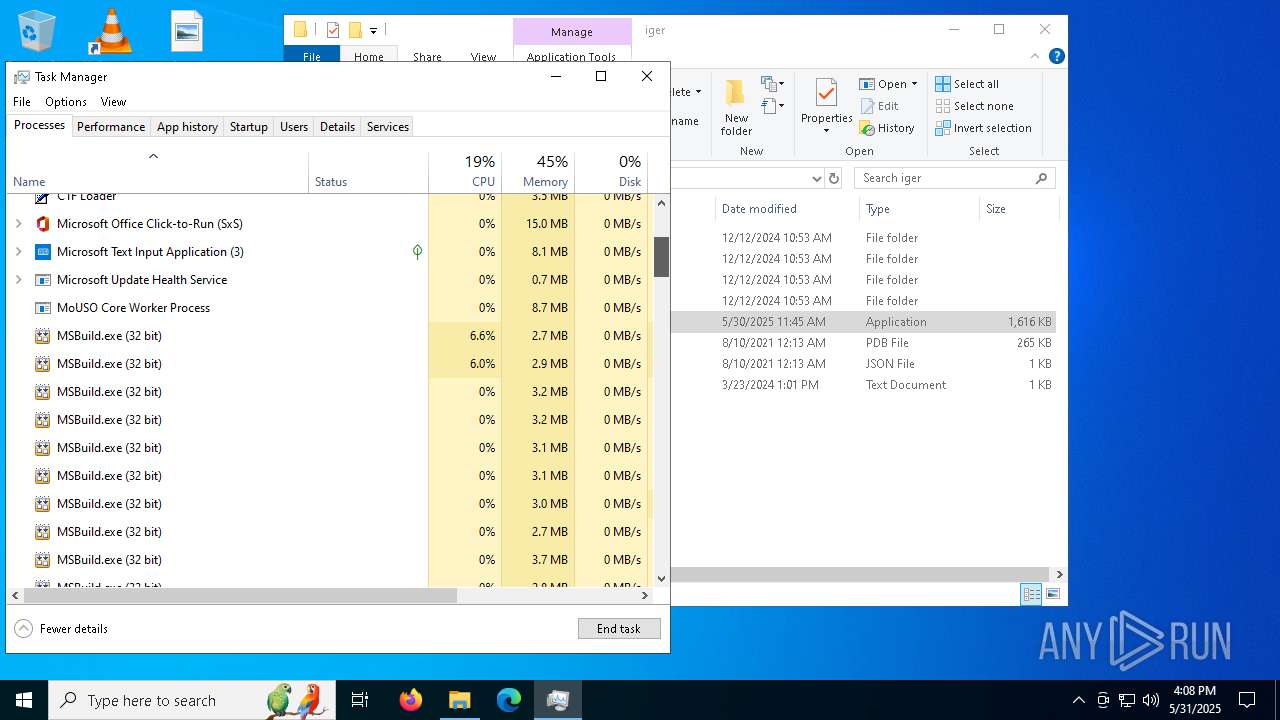
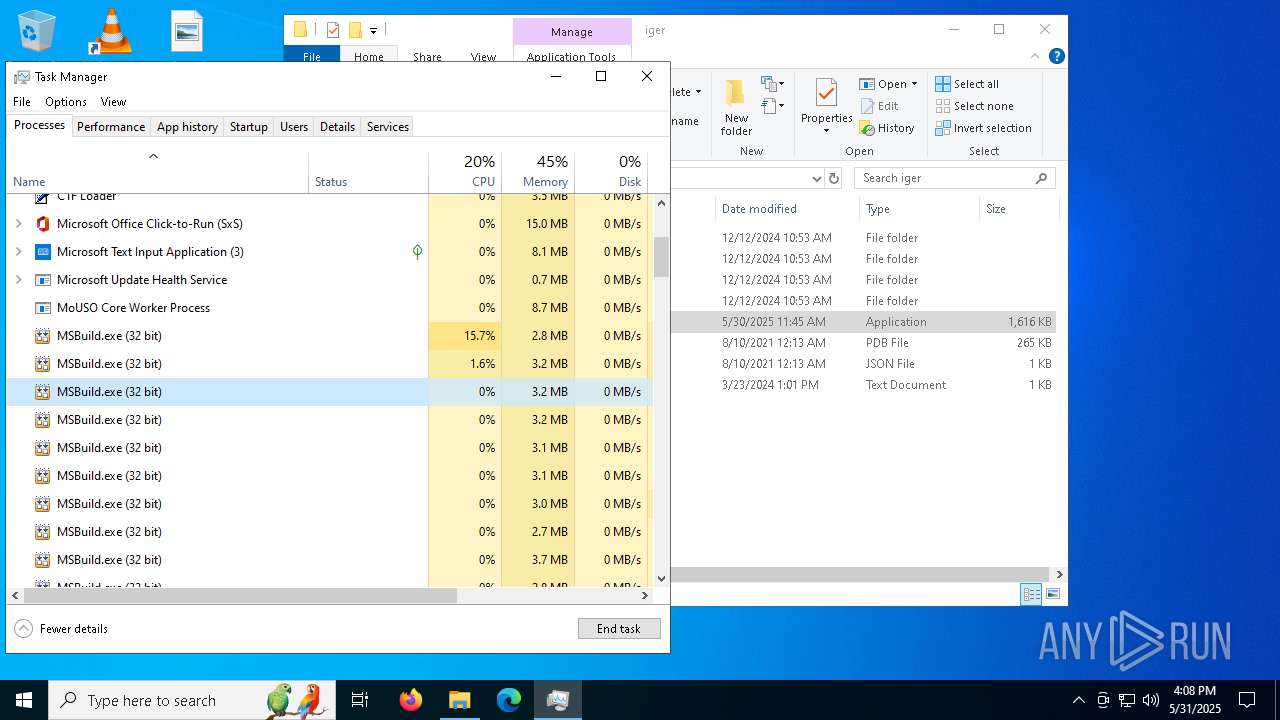
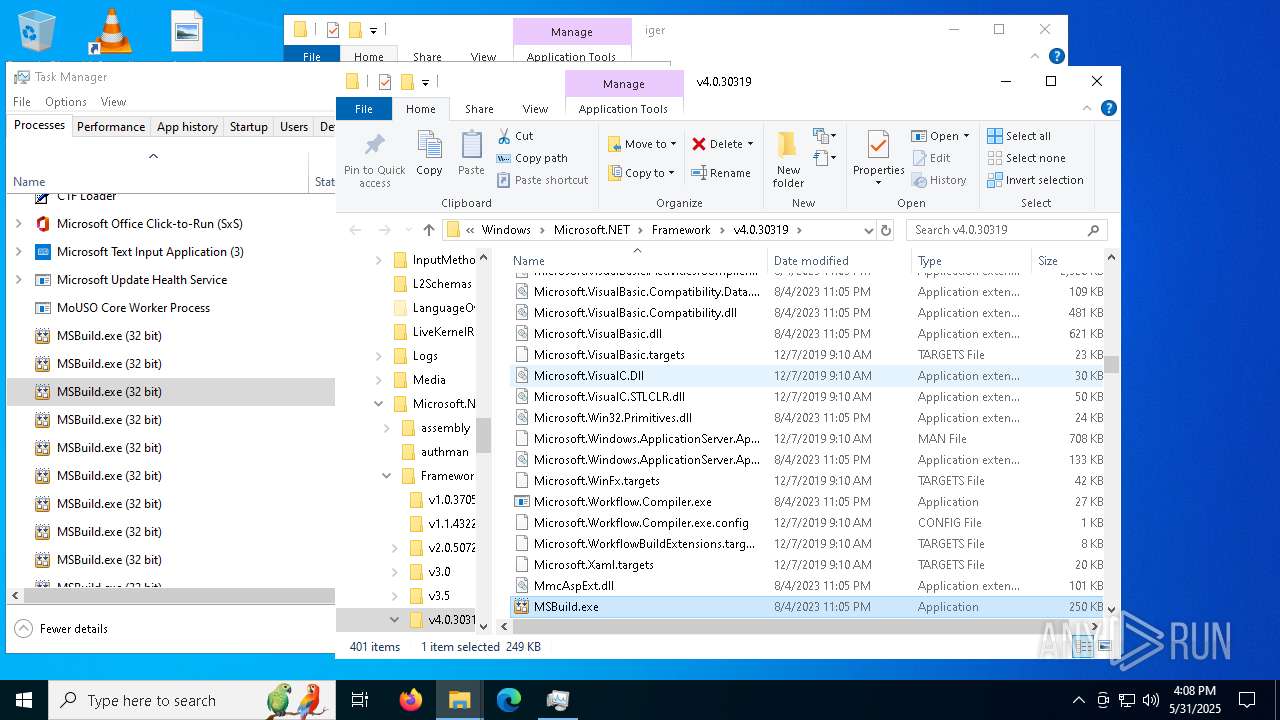
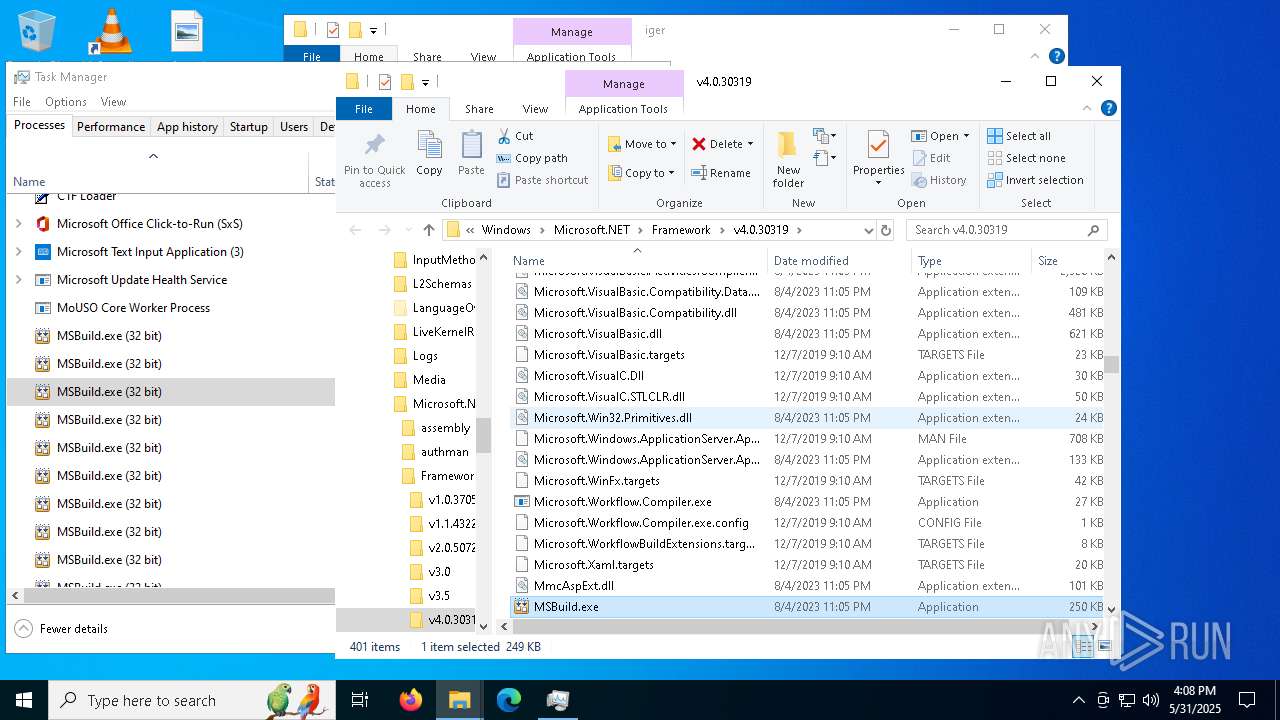
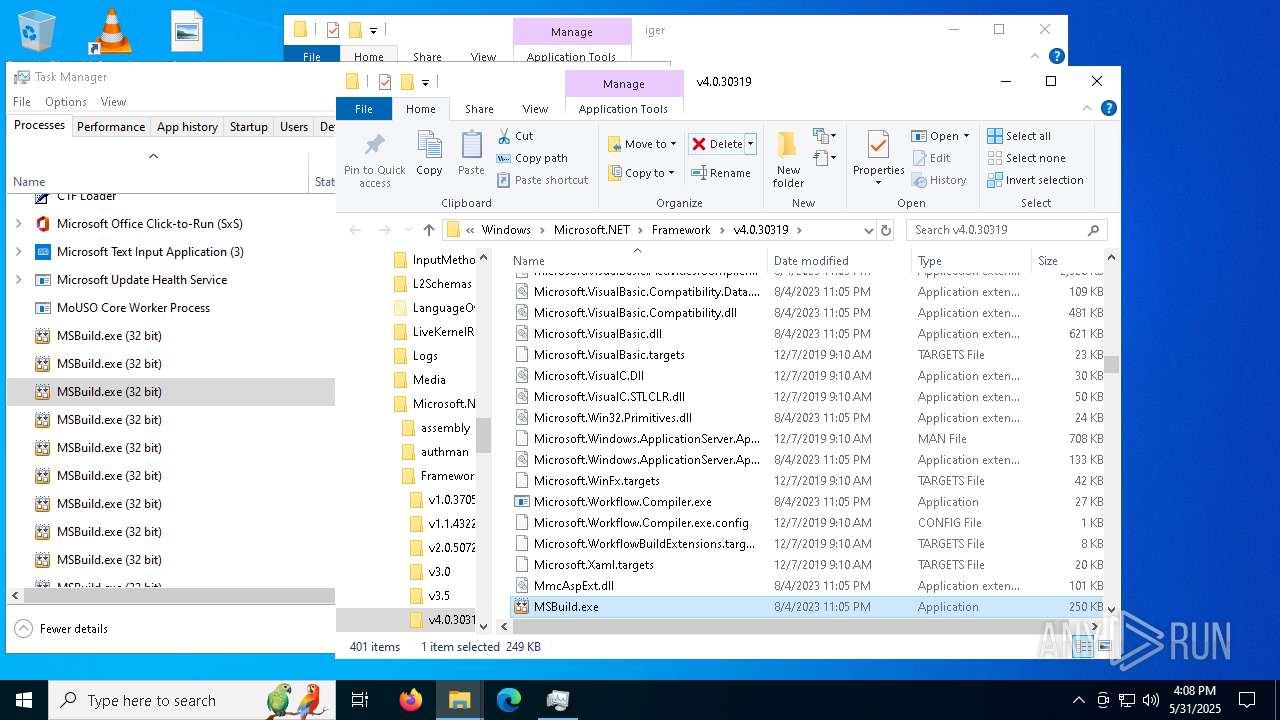
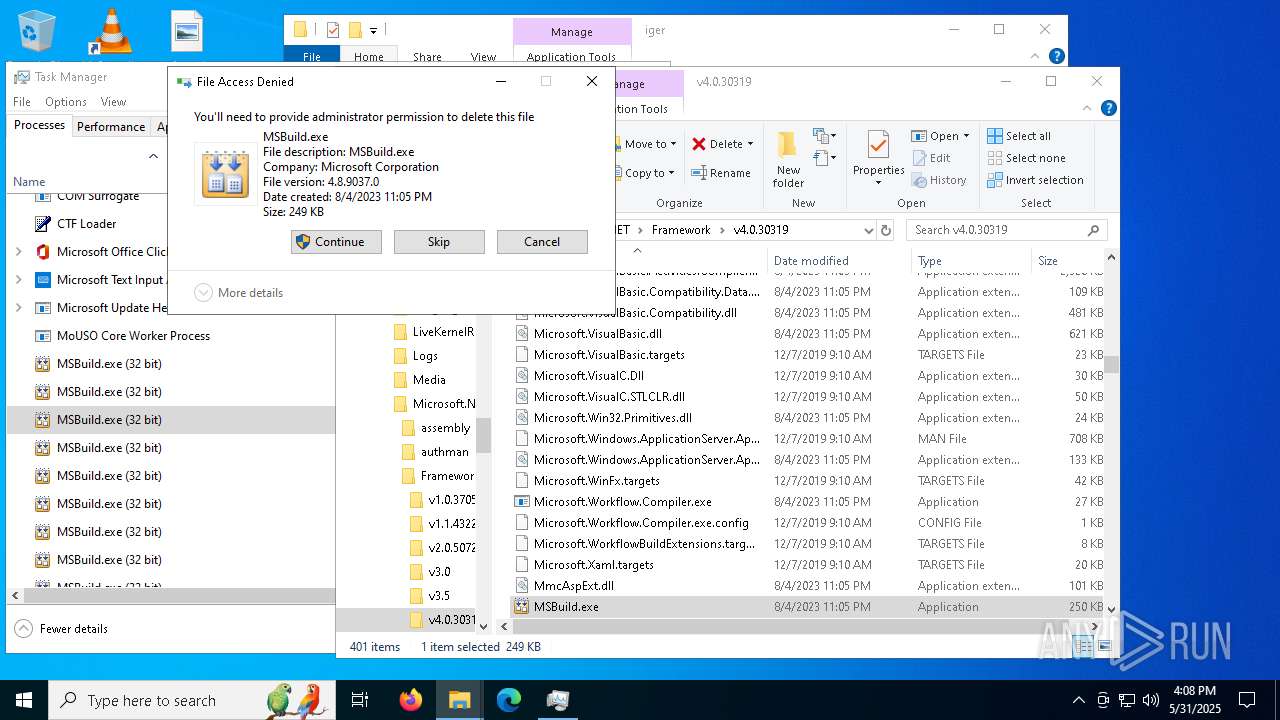
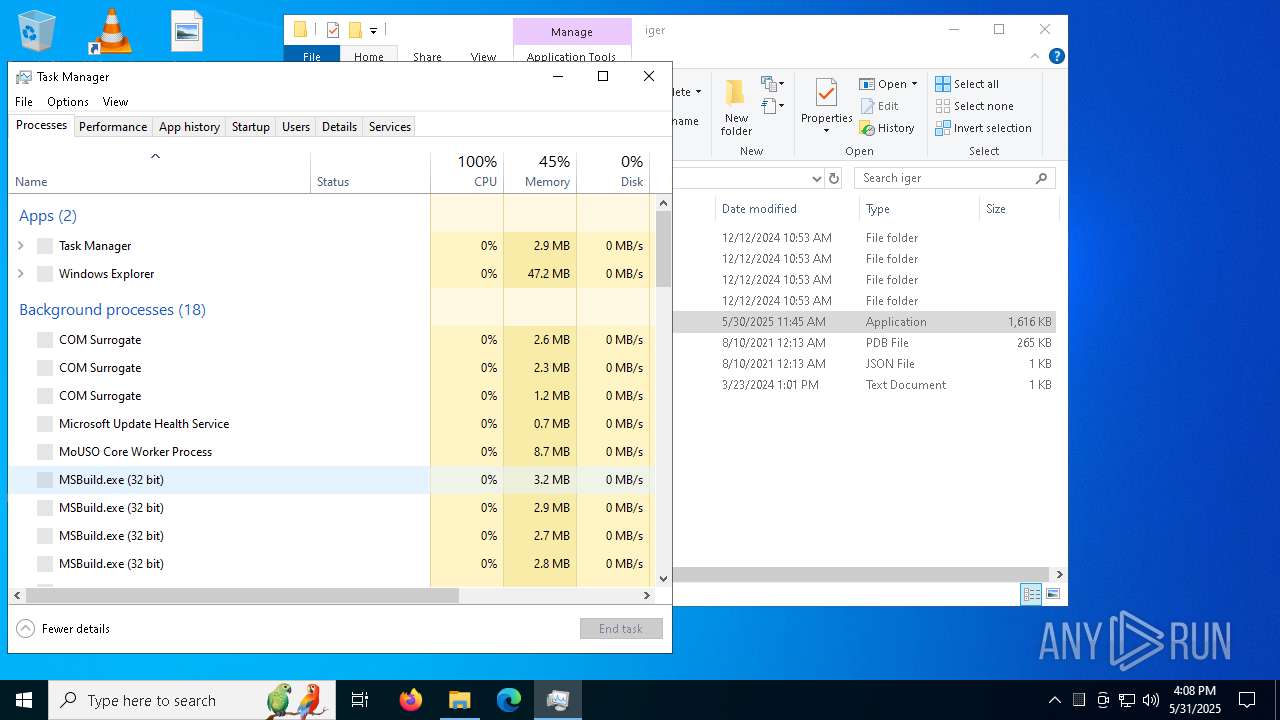
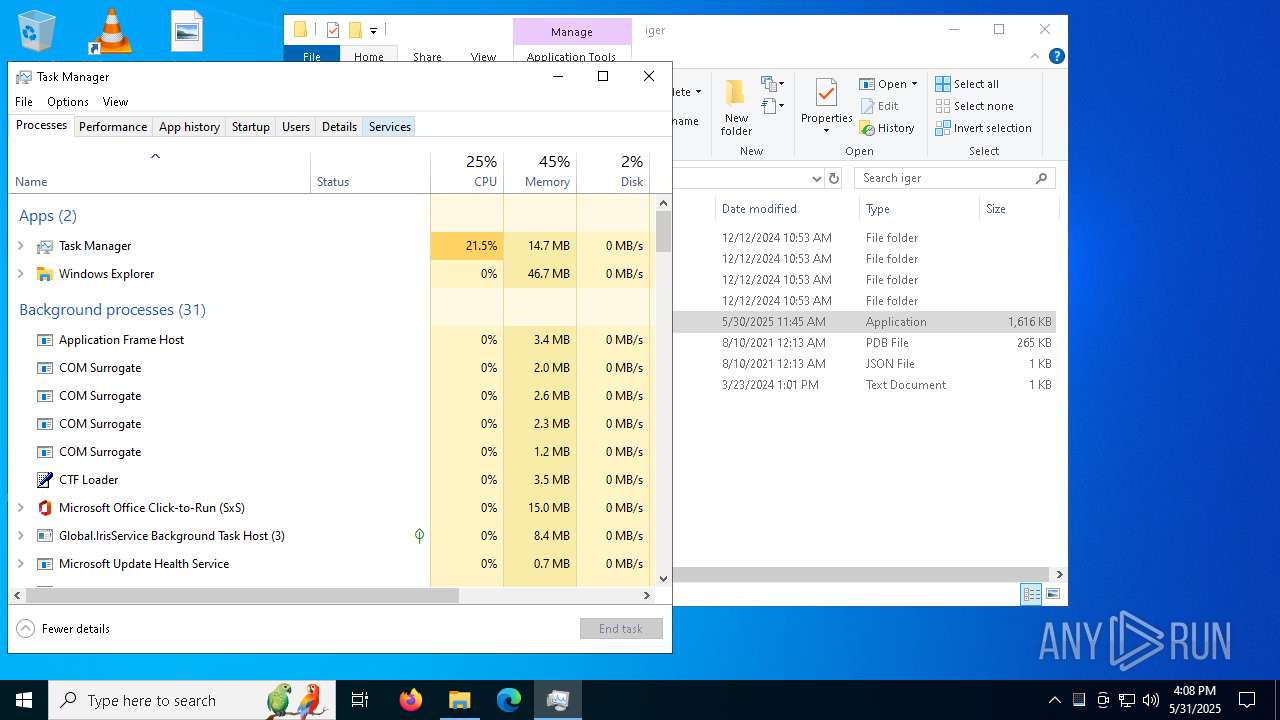
MALICIOUS
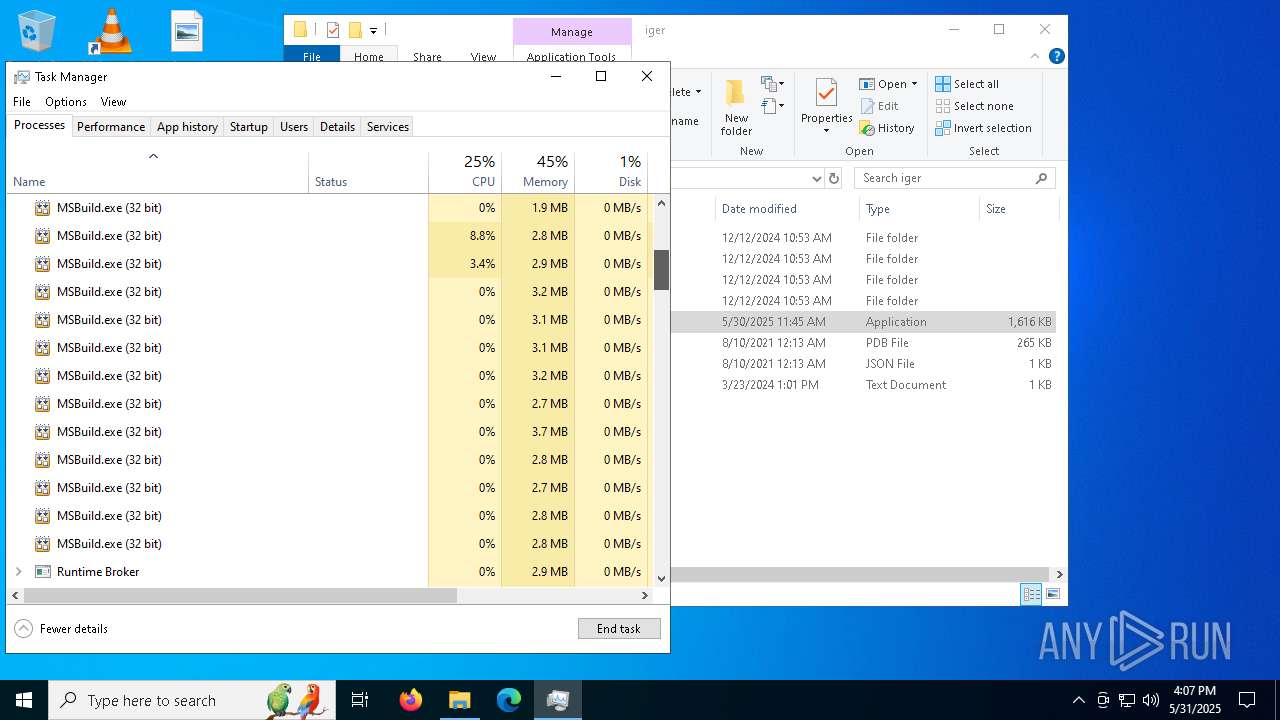
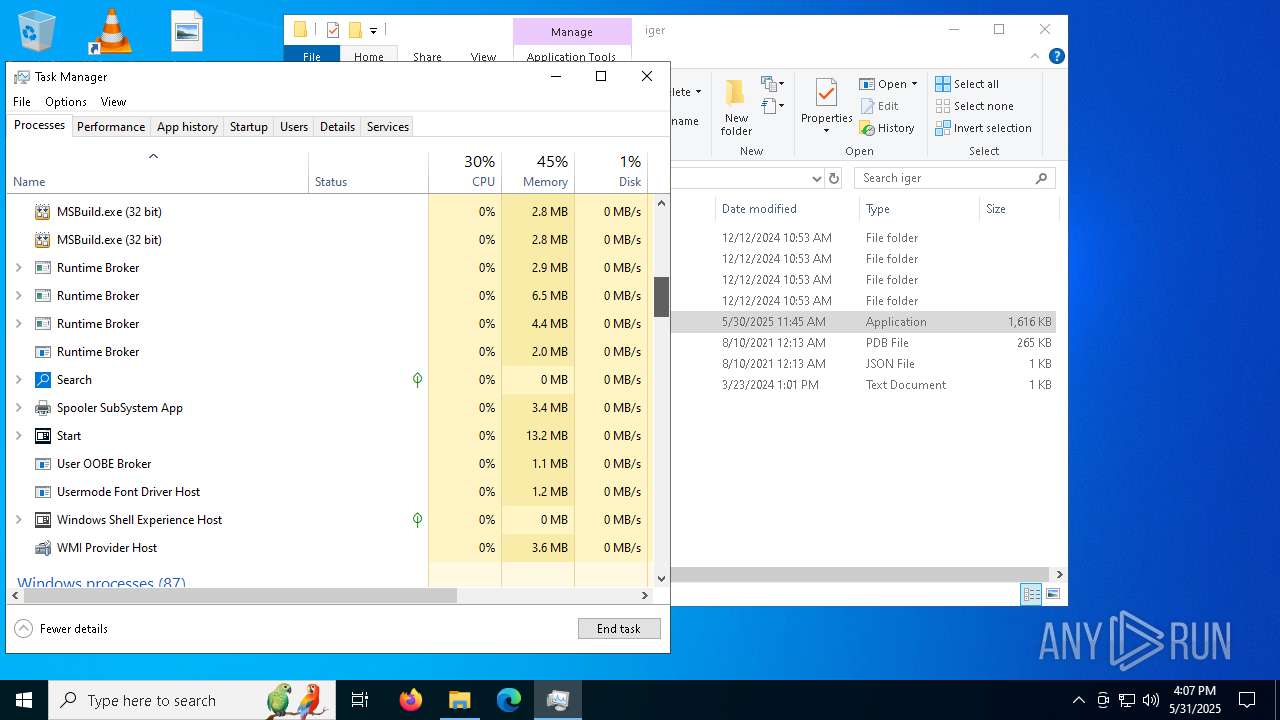
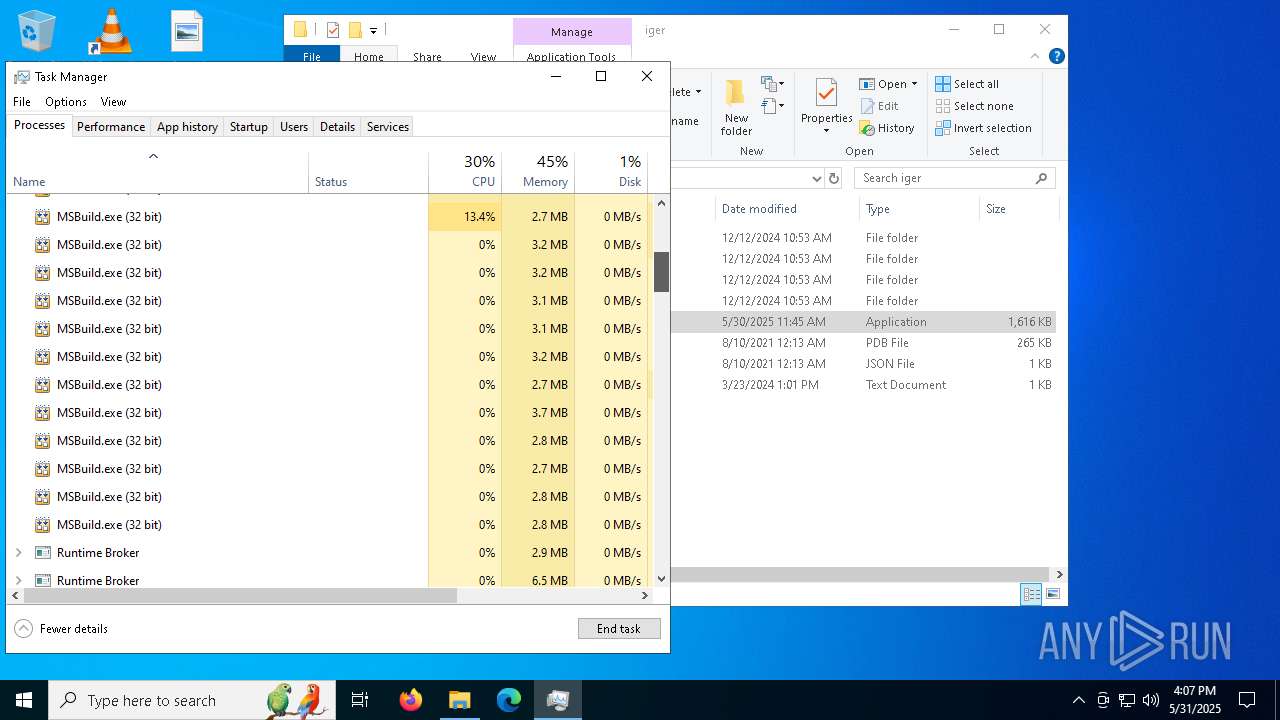
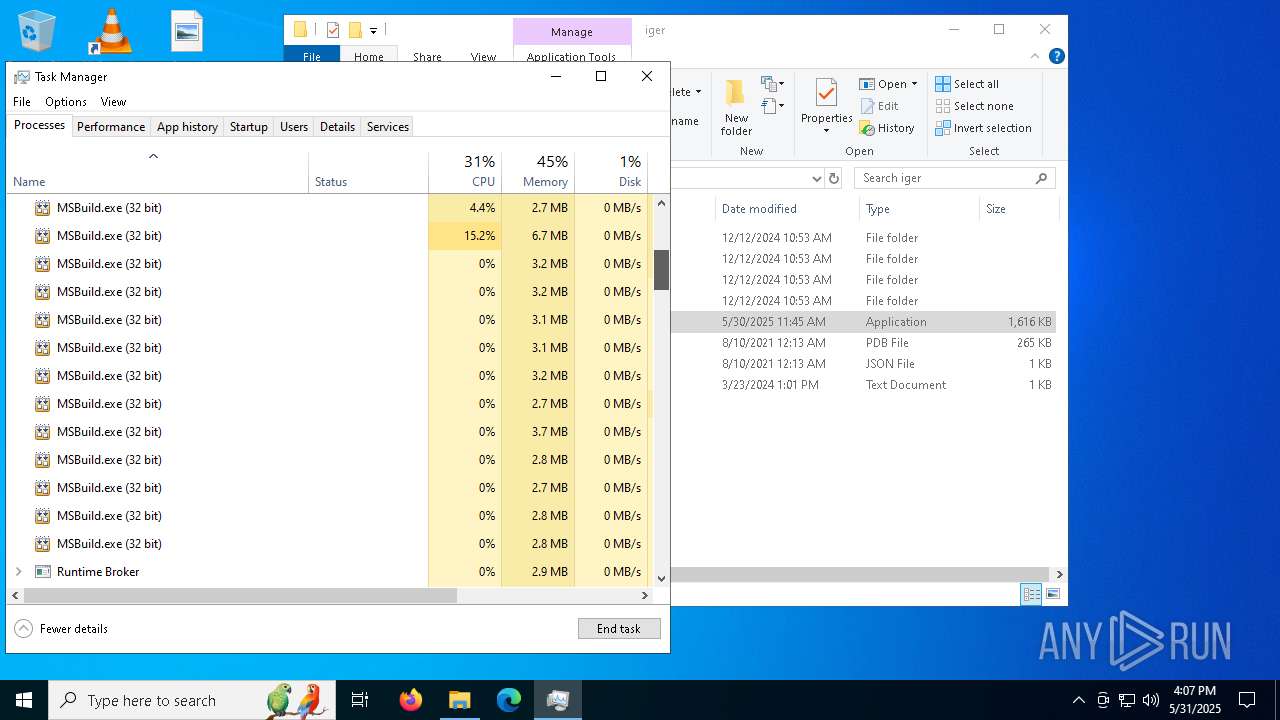
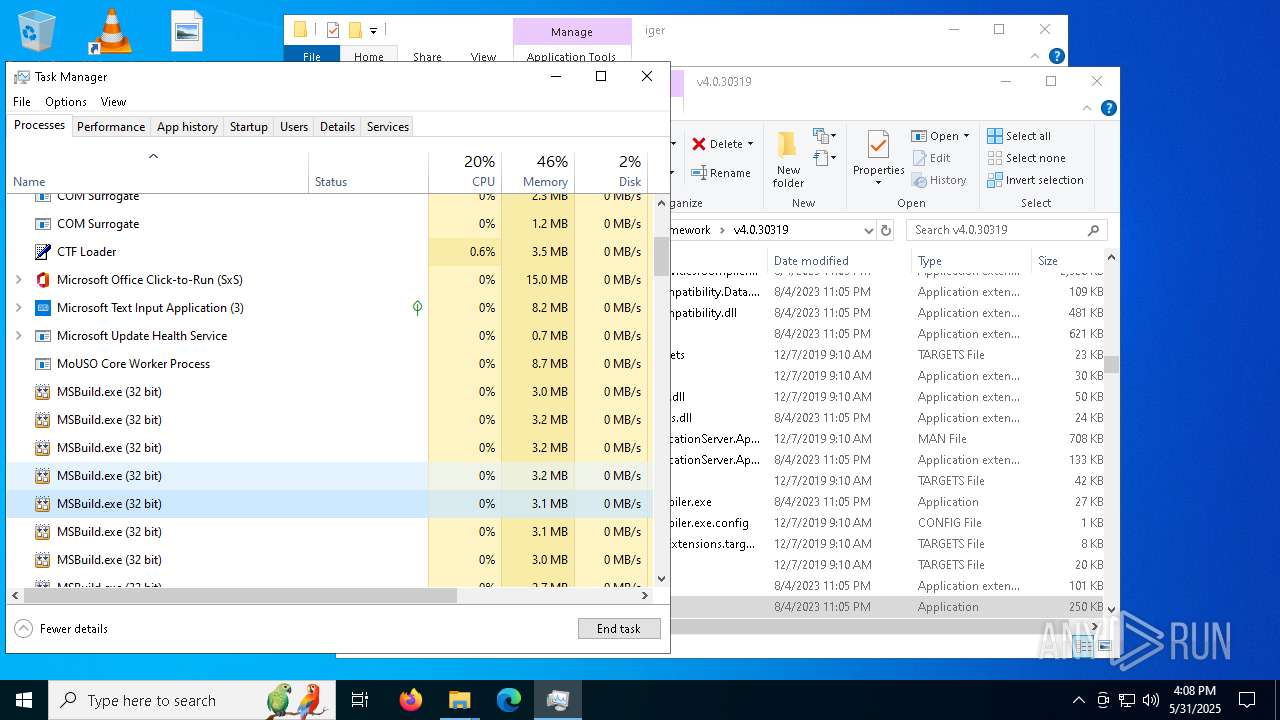
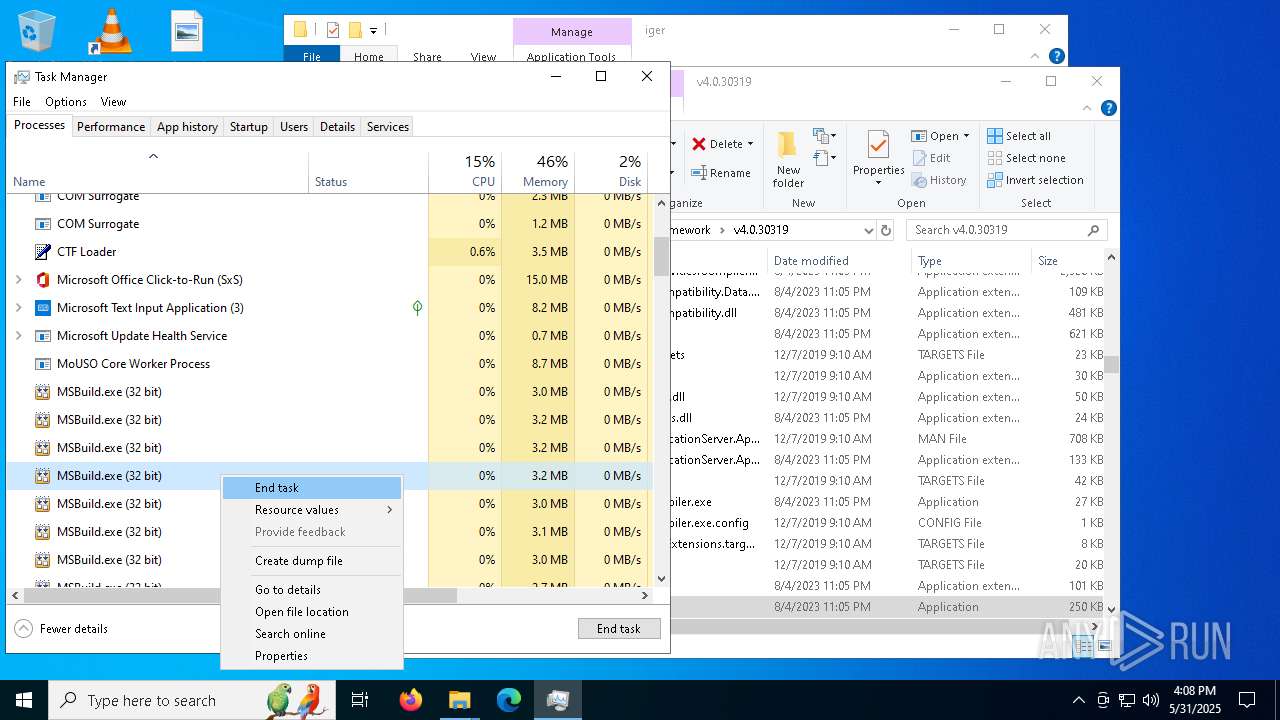
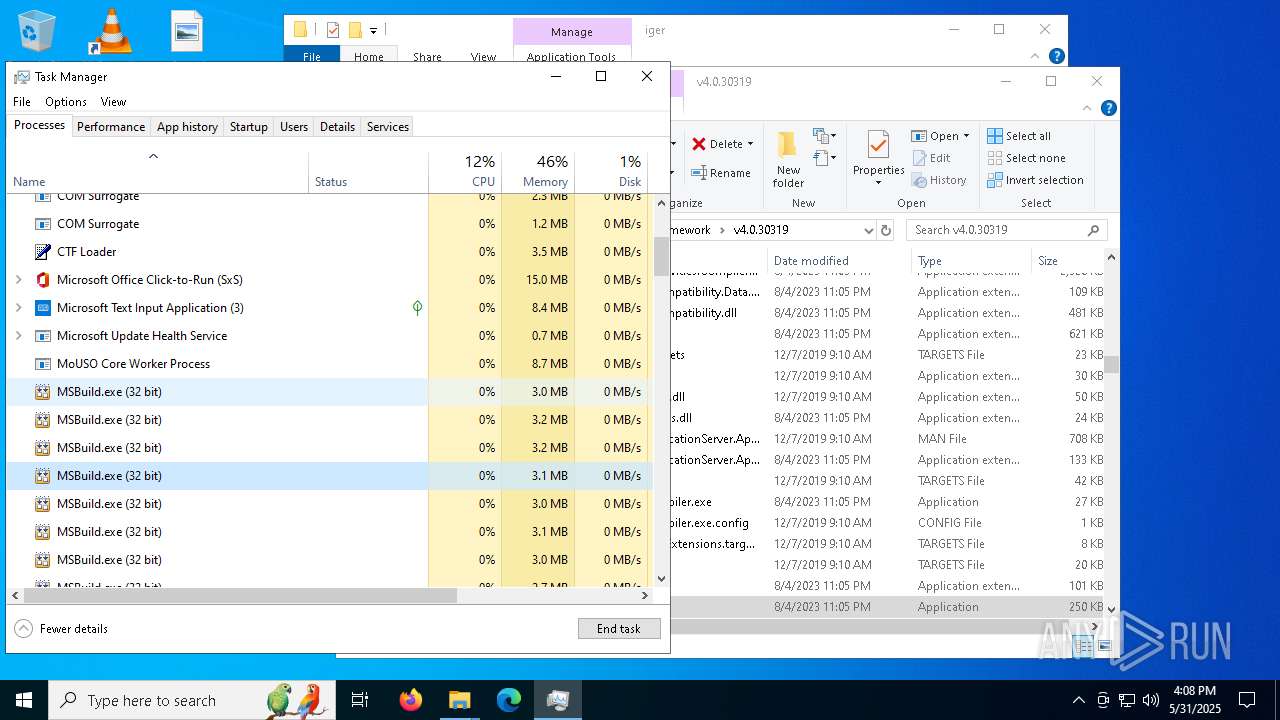
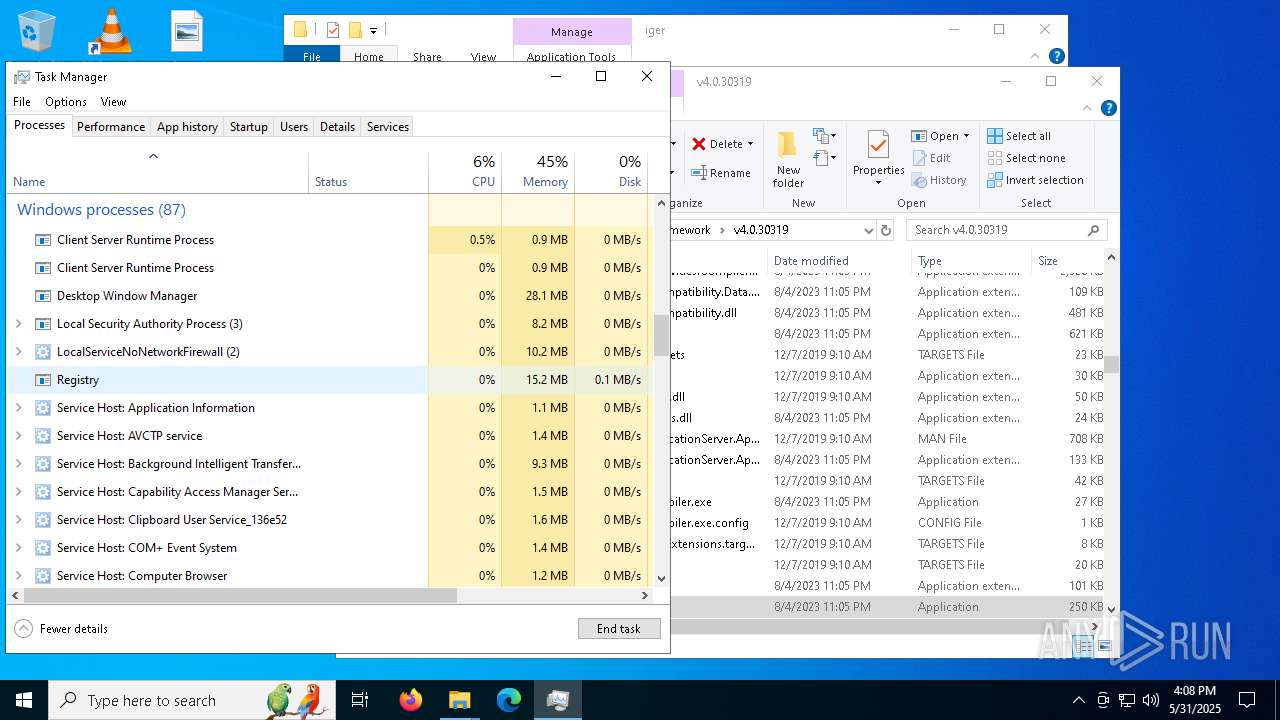
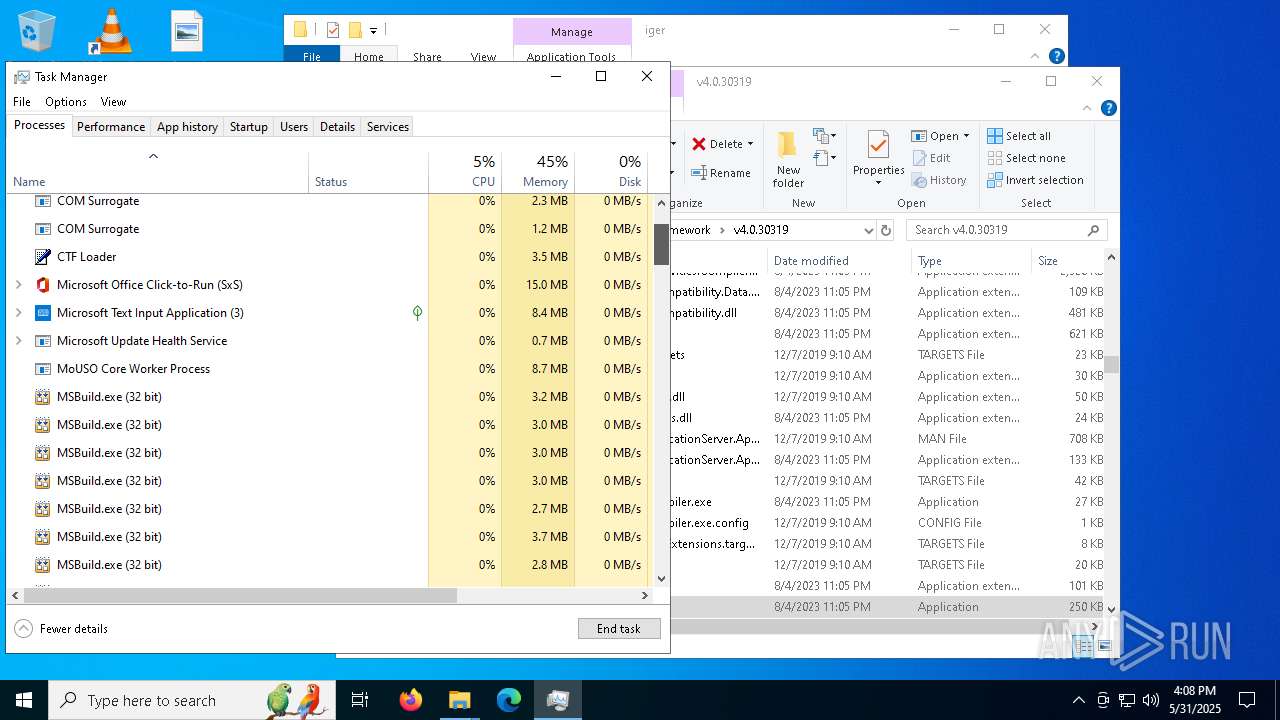
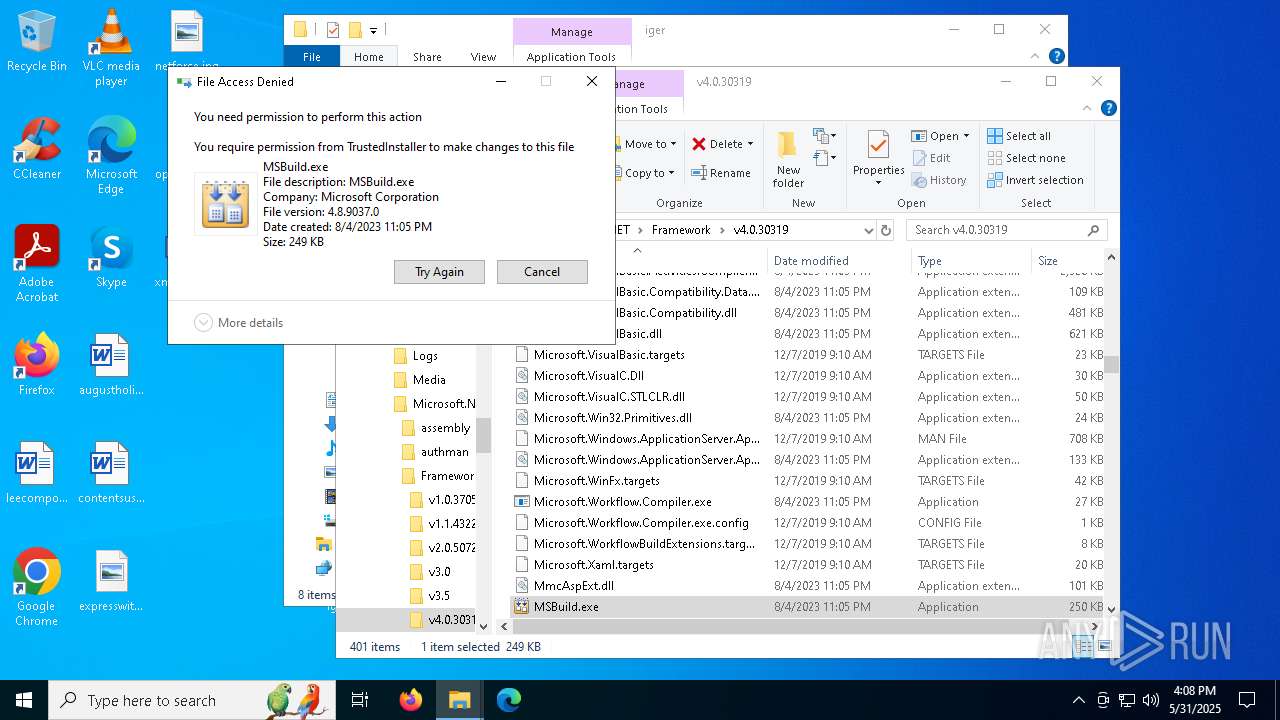
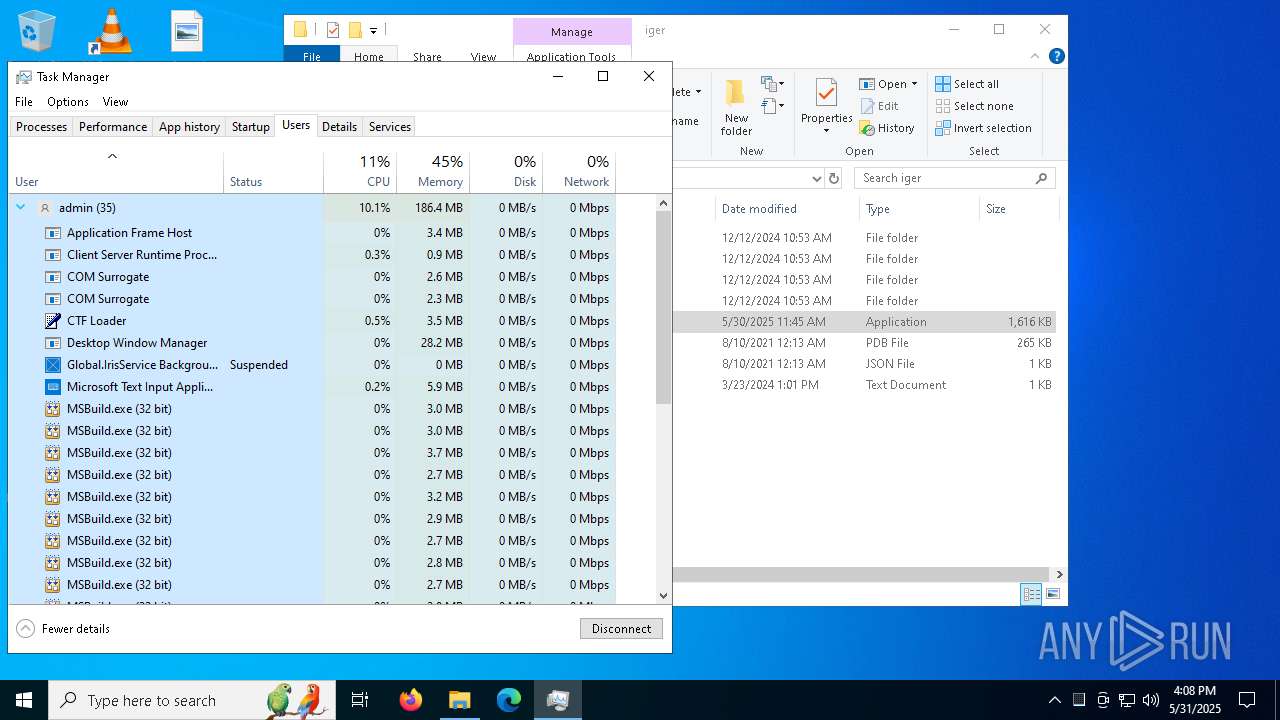
LUMMA has been detected (YARA)
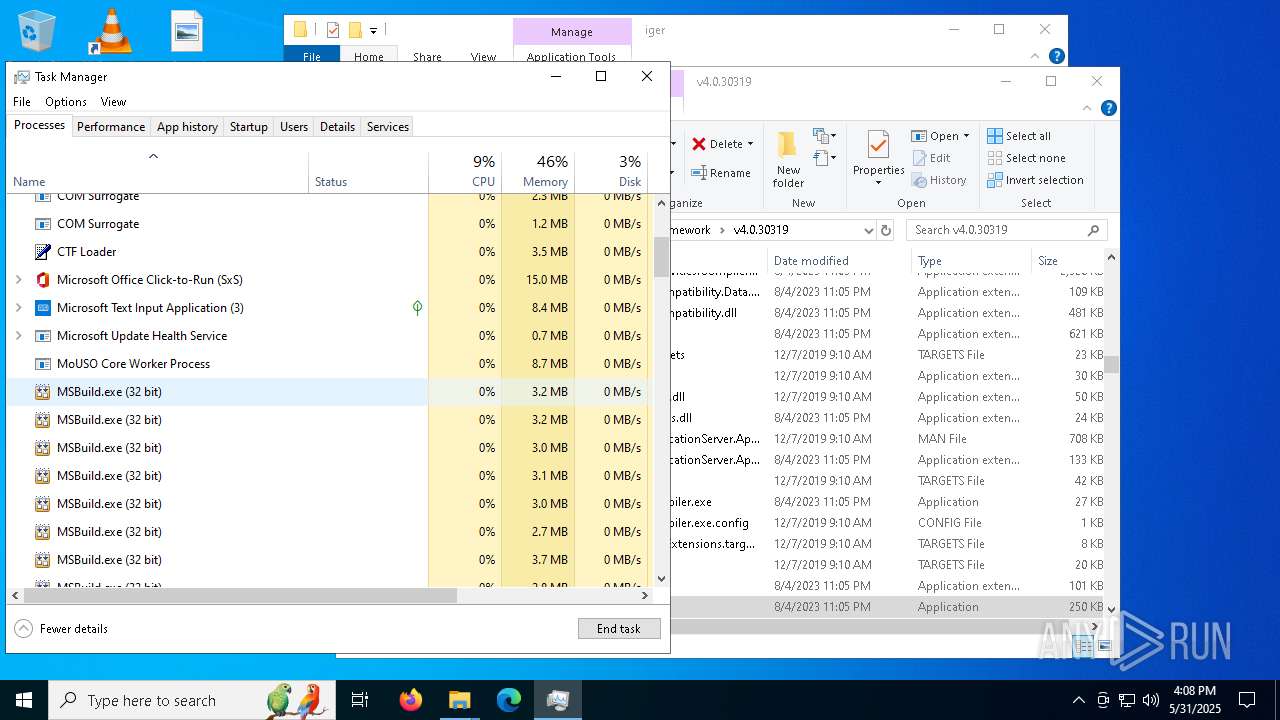
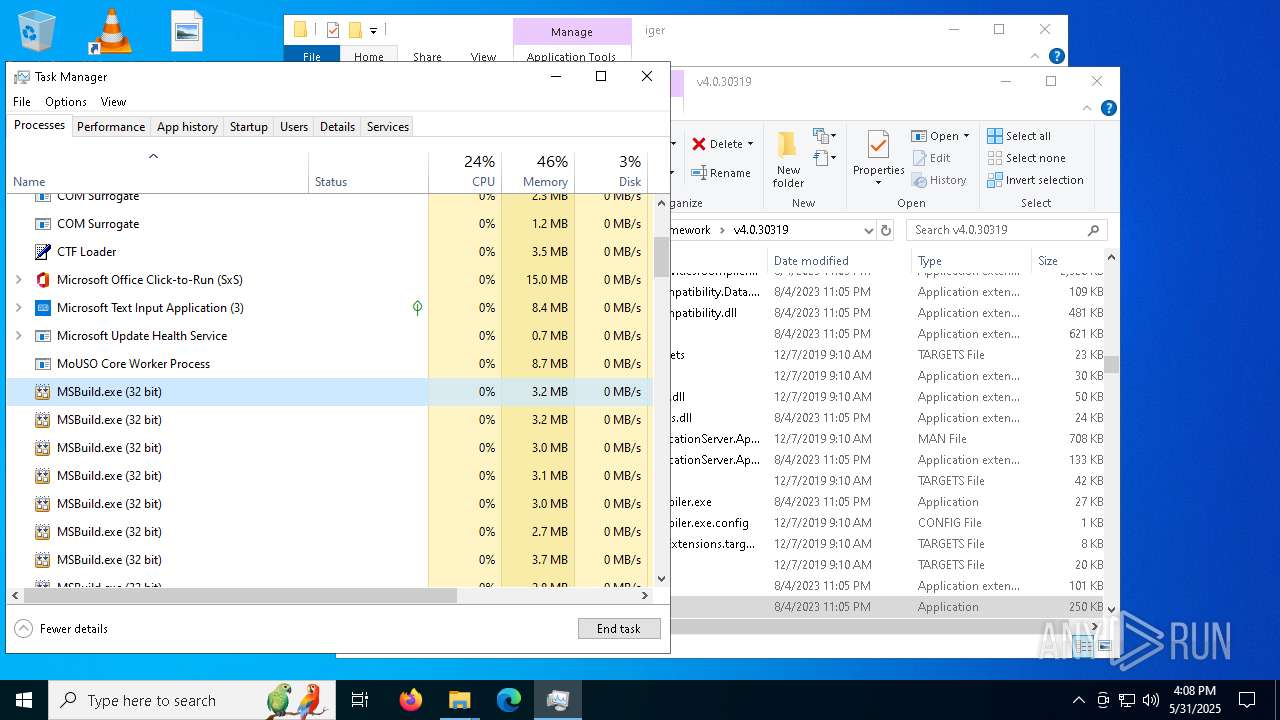
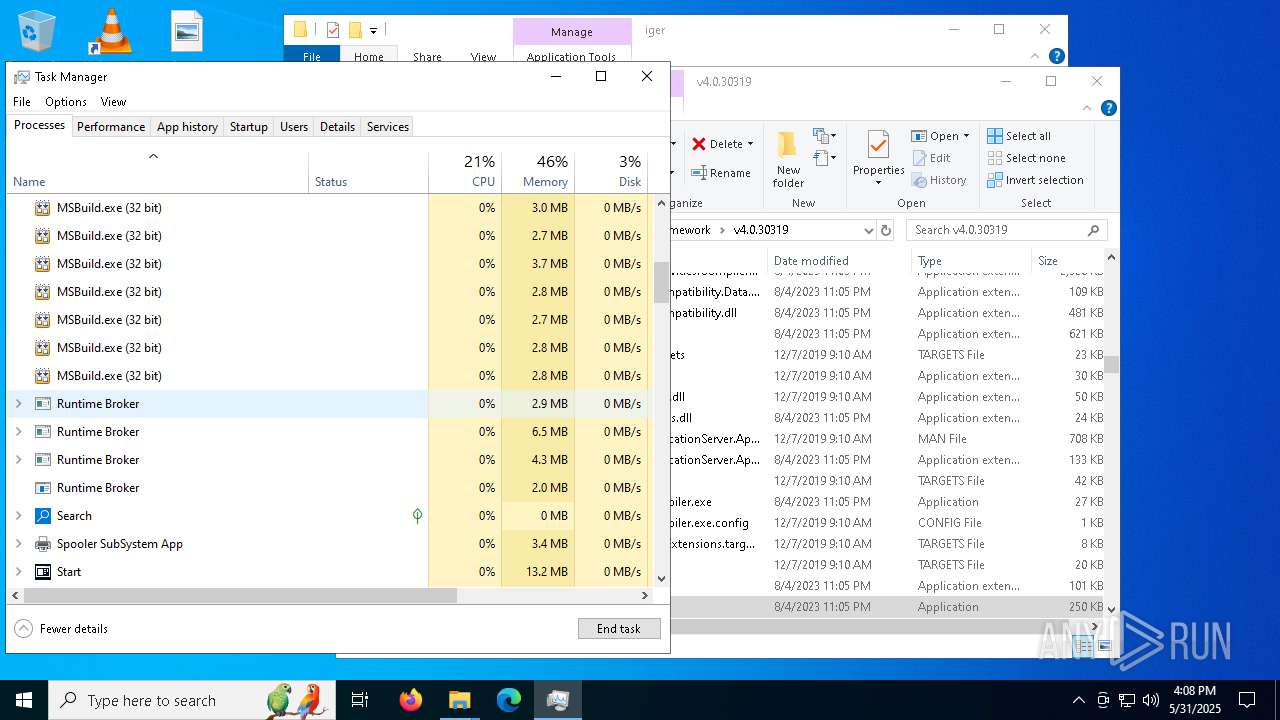
- MSBuild.exe (PID: 7320)
- MSBuild.exe (PID: 9004)
- MSBuild.exe (PID: 7636)
- MSBuild.exe (PID: 5568)
- MSBuild.exe (PID: 8308)
- MSBuild.exe (PID: 7776)
SUSPICIOUS
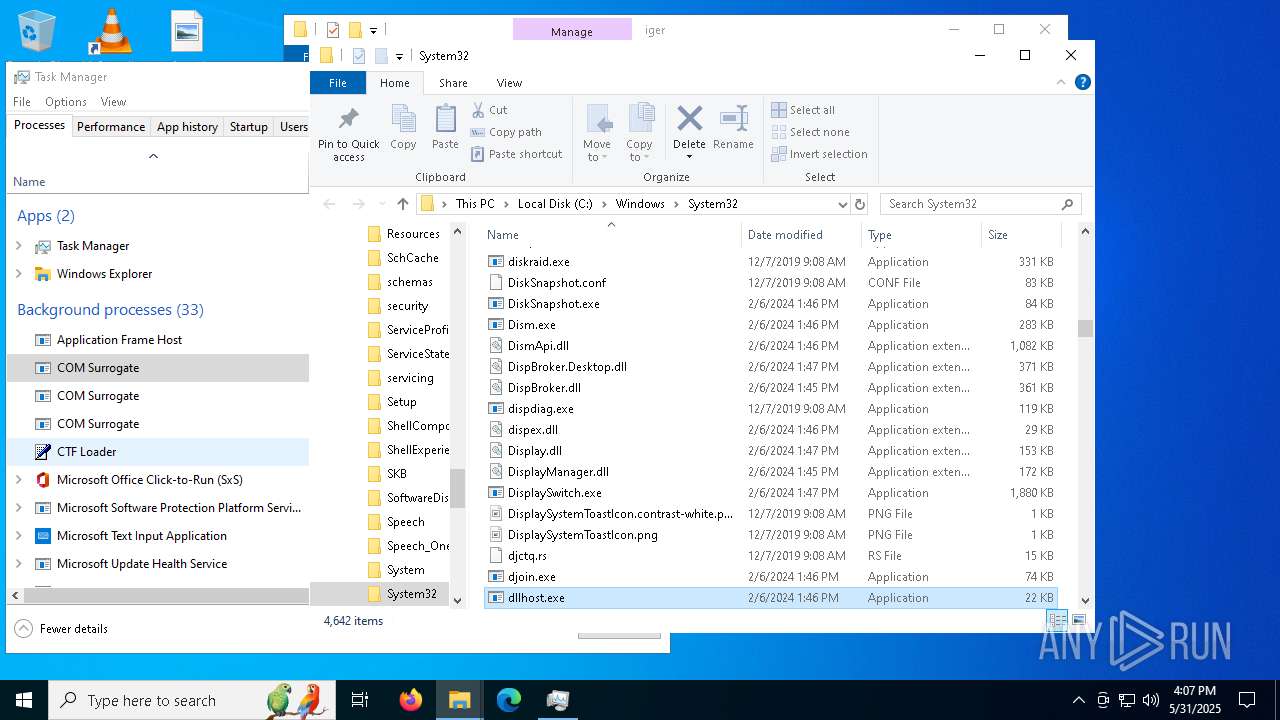
Process drops legitimate windows executable
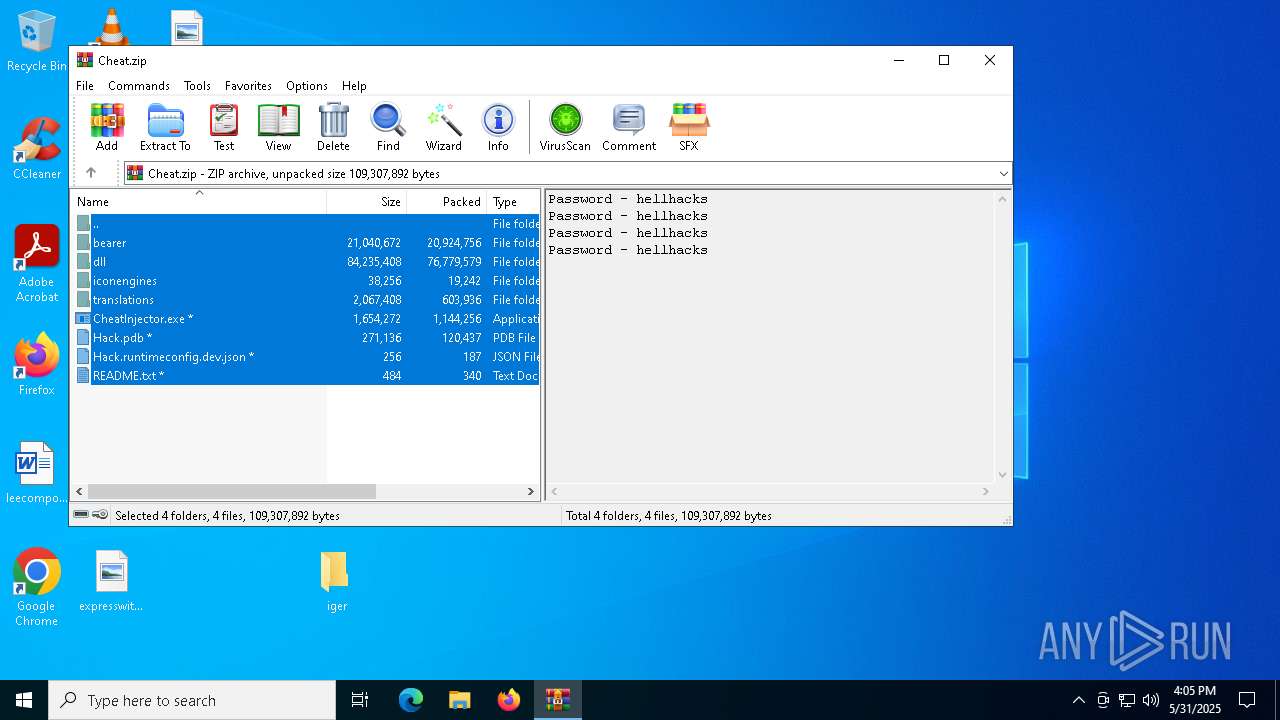
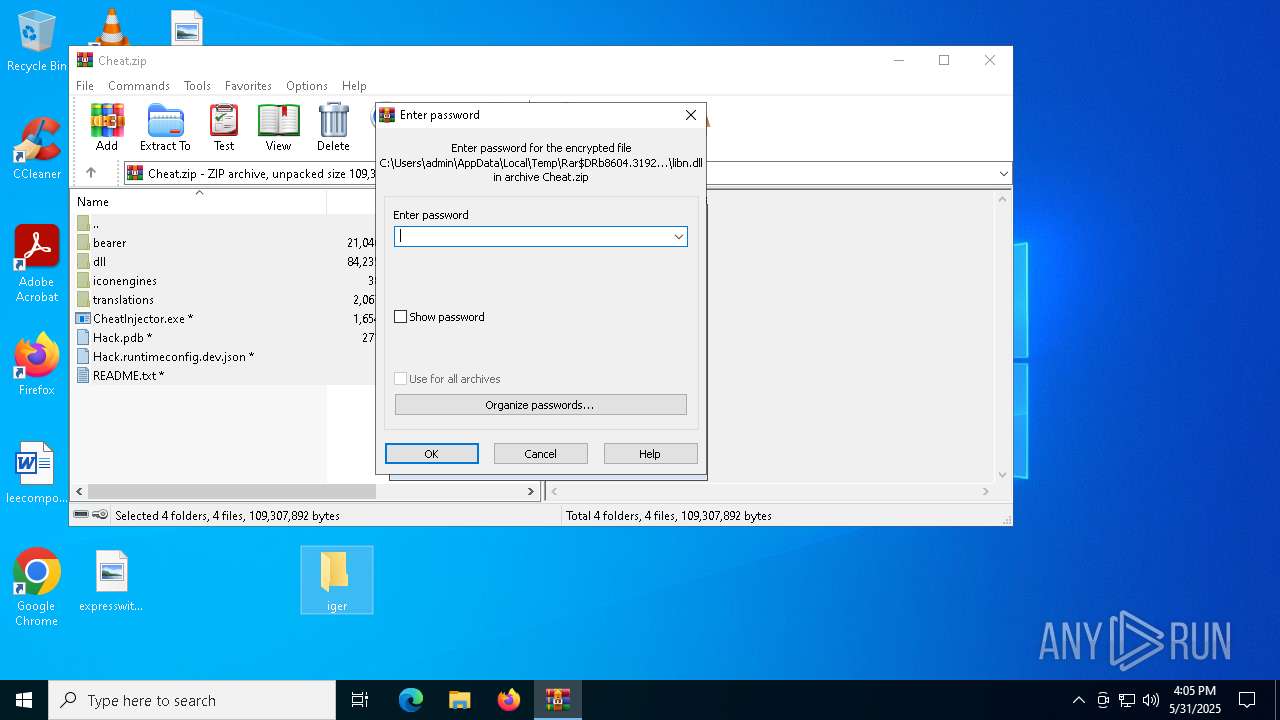
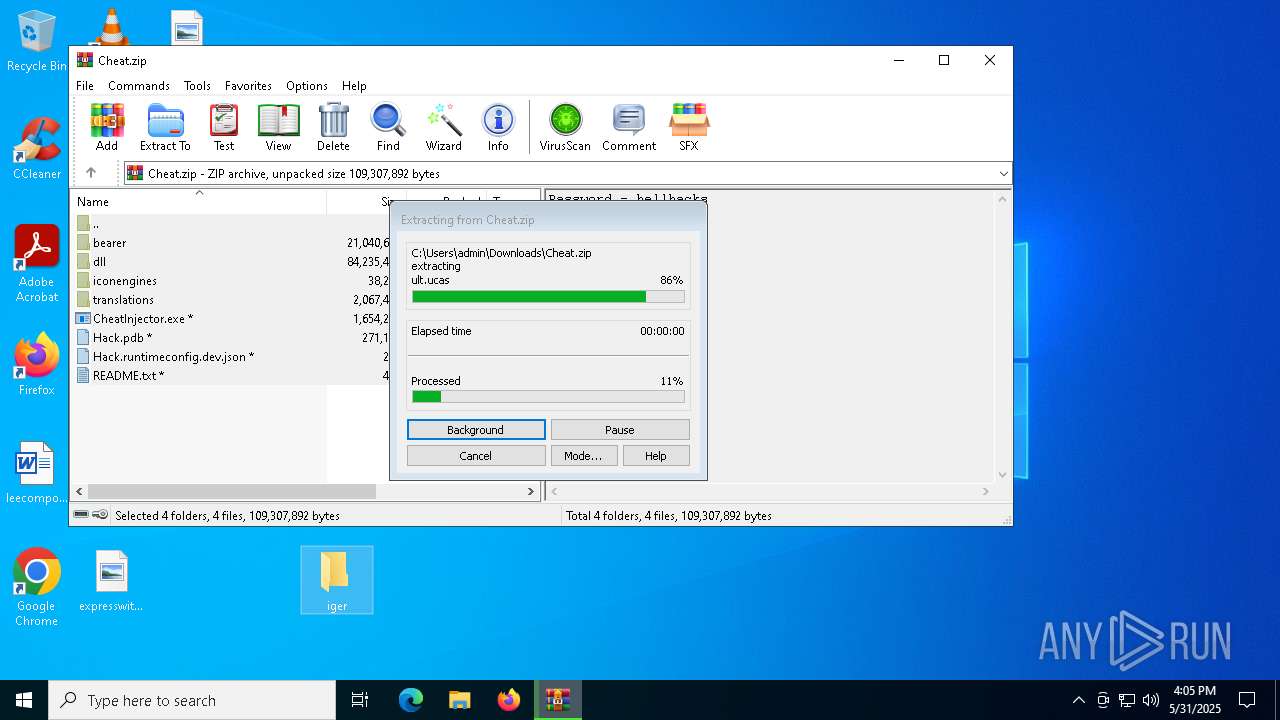
- WinRAR.exe (PID: 8604)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 8308)
- MSBuild.exe (PID: 9004)
- MSBuild.exe (PID: 7636)
- MSBuild.exe (PID: 7776)
- MSBuild.exe (PID: 7320)
- MSBuild.exe (PID: 2908)
- MSBuild.exe (PID: 9076)
- MSBuild.exe (PID: 7444)
- MSBuild.exe (PID: 5568)
- MSBuild.exe (PID: 5232)
- MSBuild.exe (PID: 7332)
- MSBuild.exe (PID: 7936)
- MSBuild.exe (PID: 872)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 9004)
- MSBuild.exe (PID: 7320)
- MSBuild.exe (PID: 5568)
- MSBuild.exe (PID: 8308)
- MSBuild.exe (PID: 7776)
- MSBuild.exe (PID: 7636)
Multiple wallet extension IDs have been found
- MSBuild.exe (PID: 5568)
- MSBuild.exe (PID: 7776)
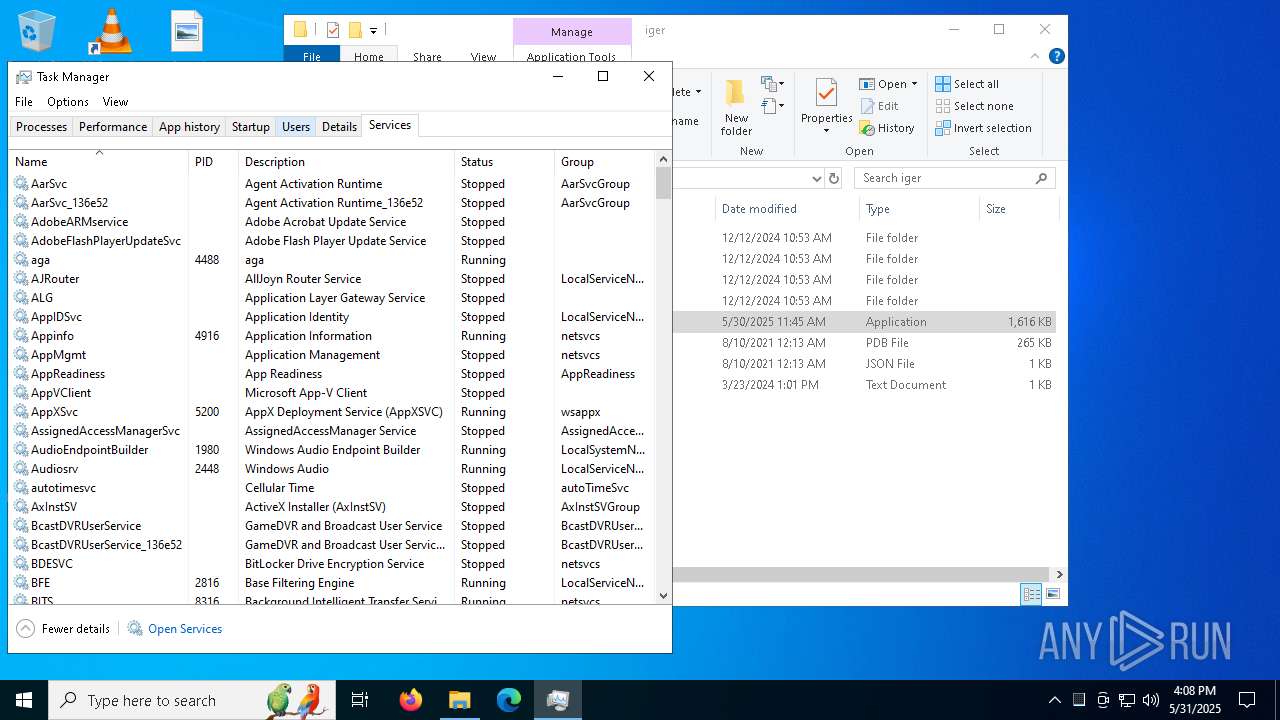
INFO
Checks supported languages
- identity_helper.exe (PID: 2384)
- identity_helper.exe (PID: 9052)
- identity_helper.exe (PID: 7844)
- identity_helper.exe (PID: 8296)
Reads Environment values
- identity_helper.exe (PID: 2384)
- identity_helper.exe (PID: 9052)
- identity_helper.exe (PID: 7844)
- identity_helper.exe (PID: 8296)
Reads the computer name
- identity_helper.exe (PID: 9052)
- identity_helper.exe (PID: 7844)
- identity_helper.exe (PID: 2384)
- identity_helper.exe (PID: 8296)
Reads the software policy settings
- slui.exe (PID: 7728)
The sample compiled with english language support
- WinRAR.exe (PID: 8604)
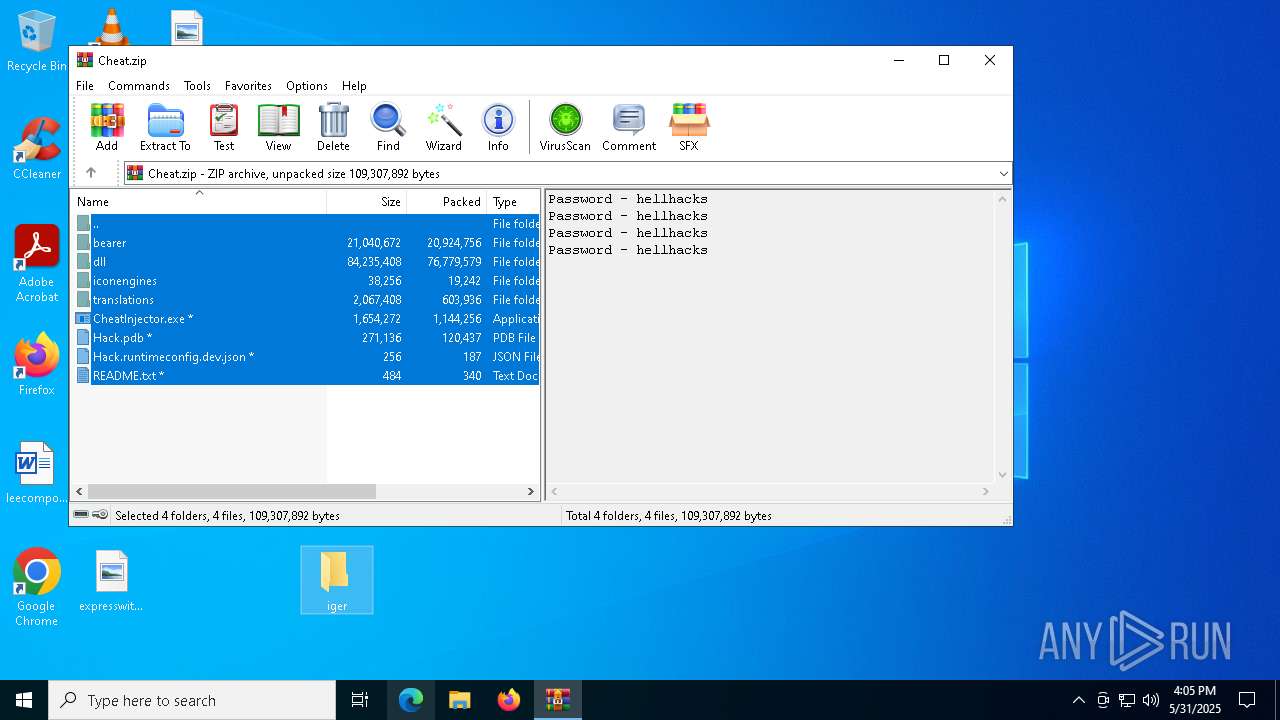
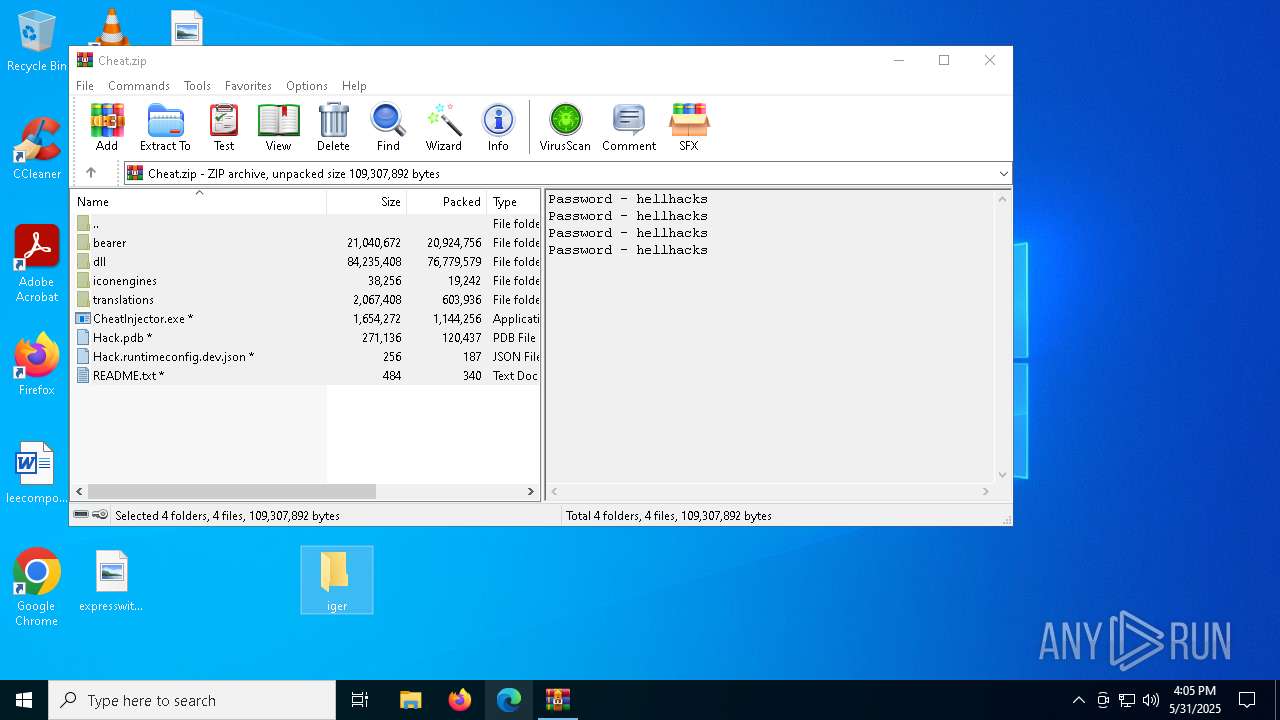
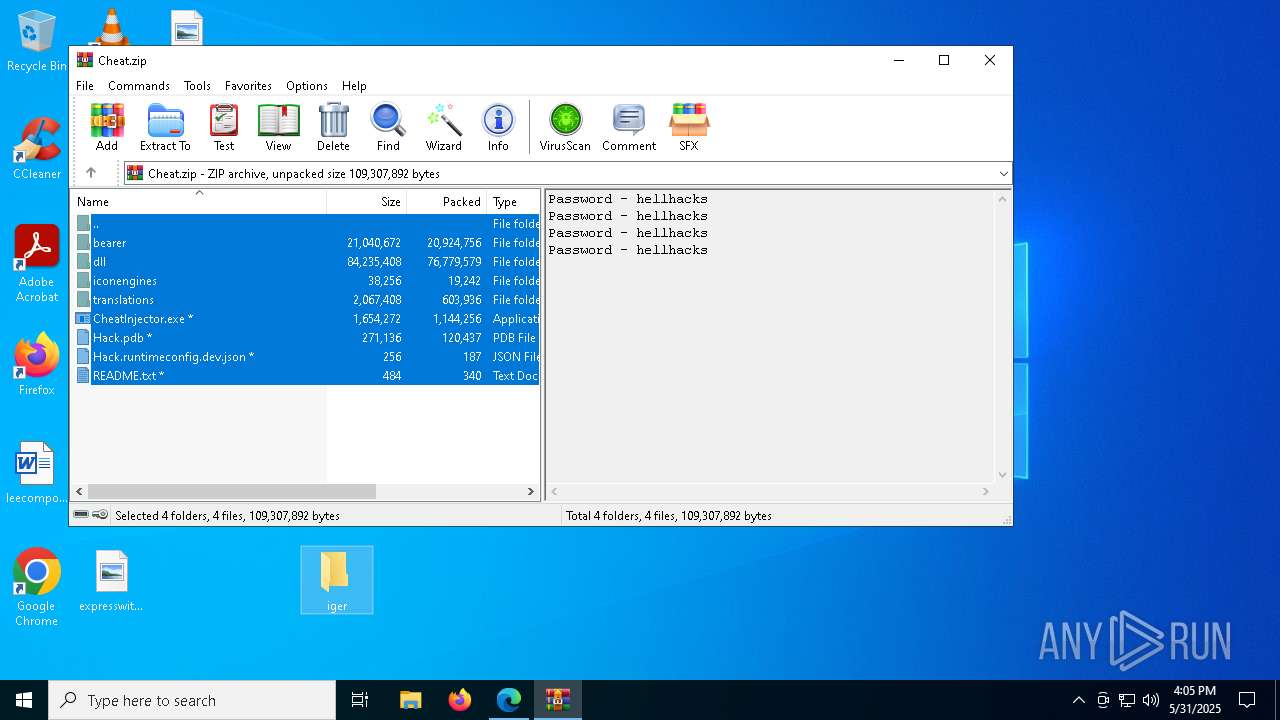
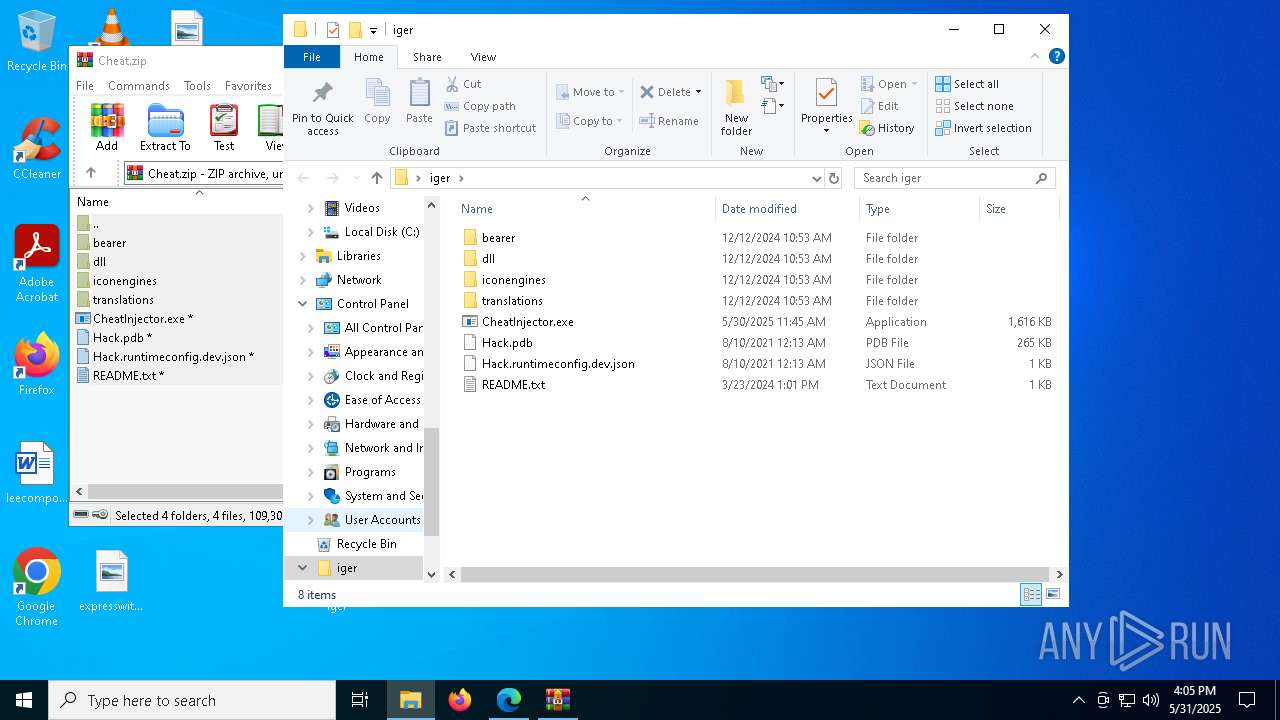
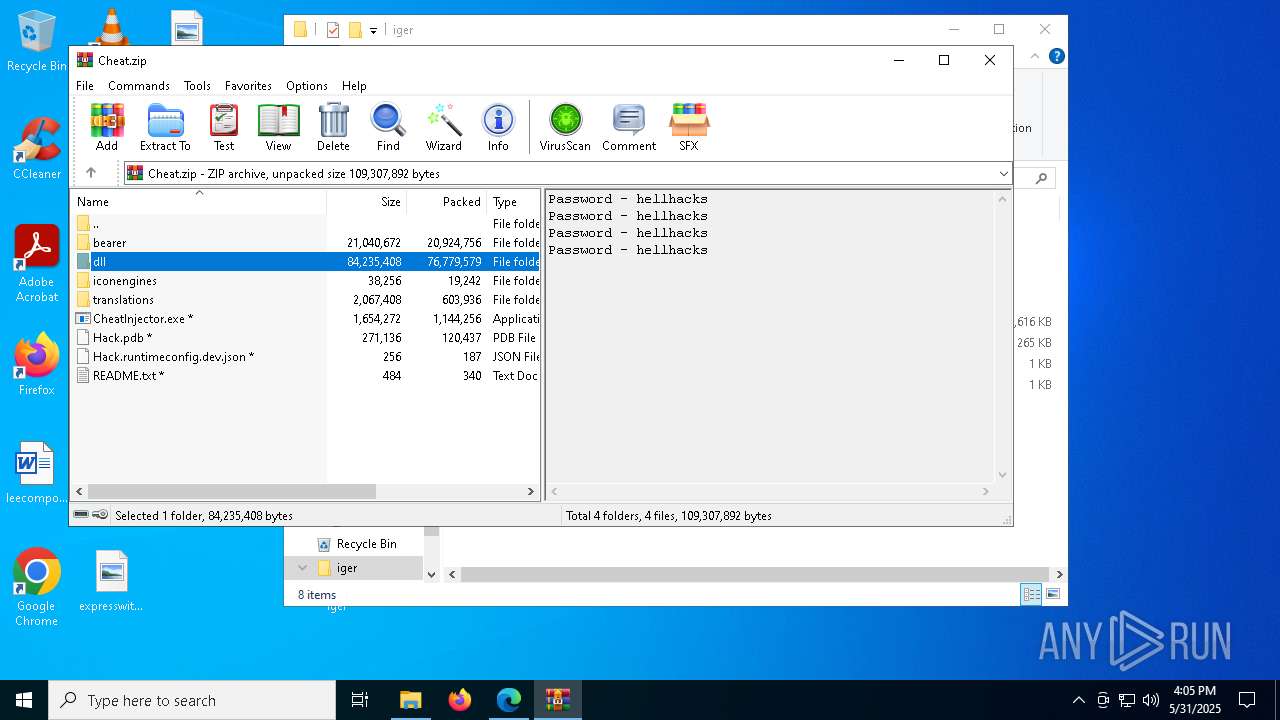
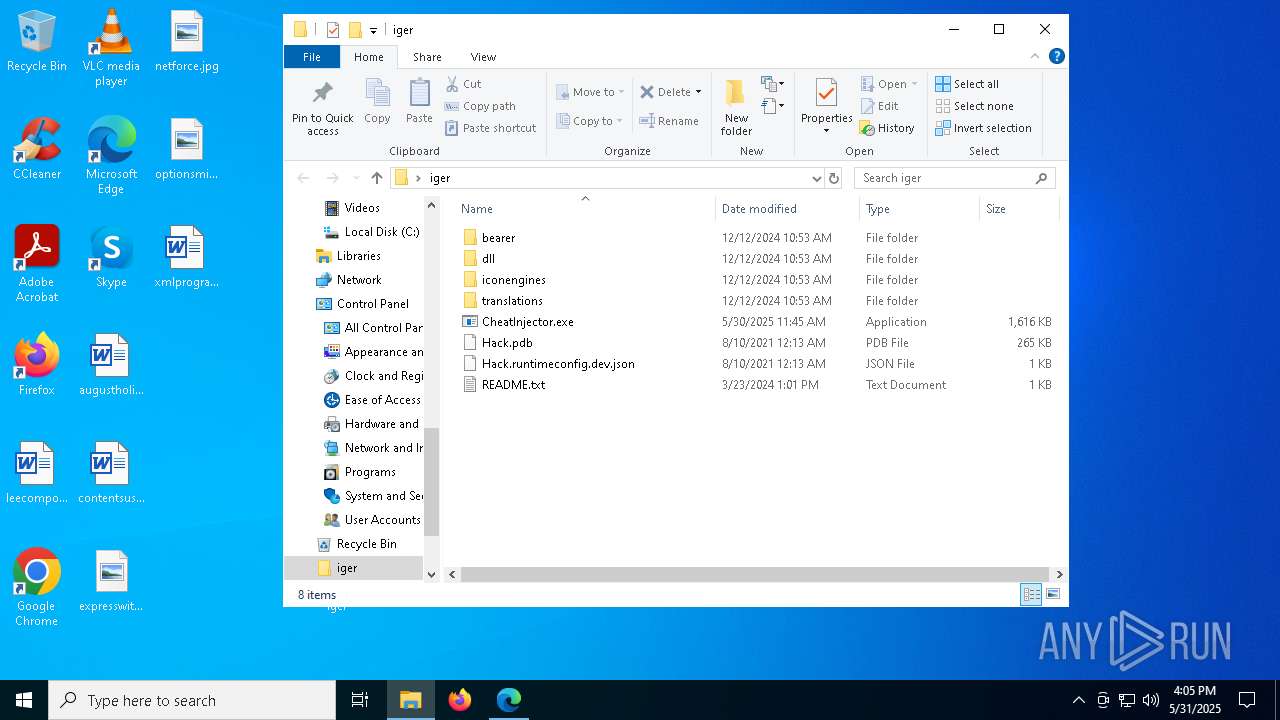
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8604)
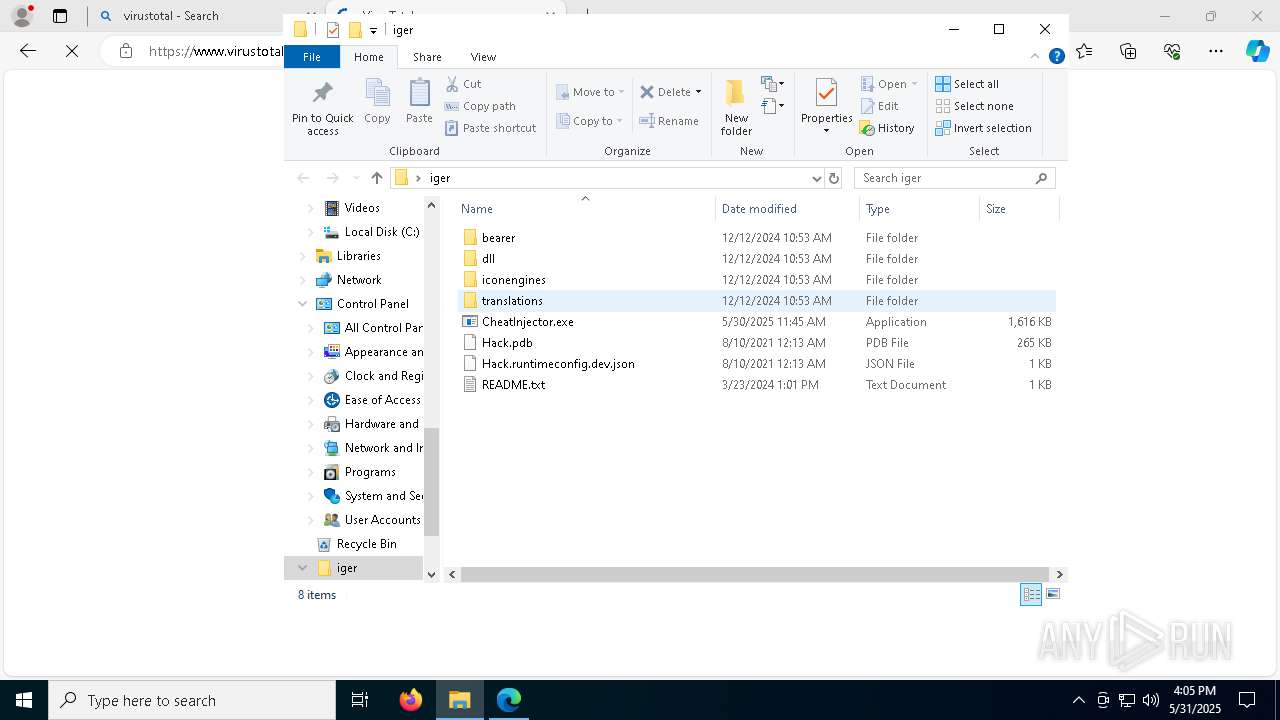
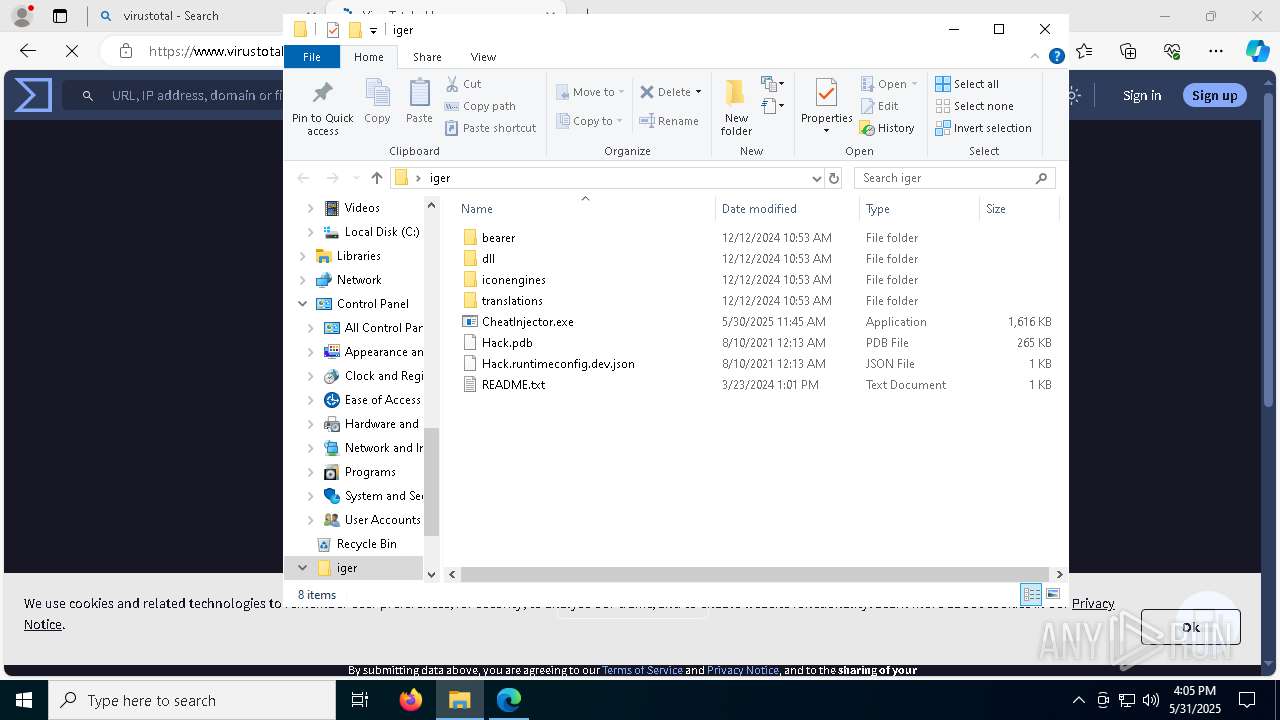
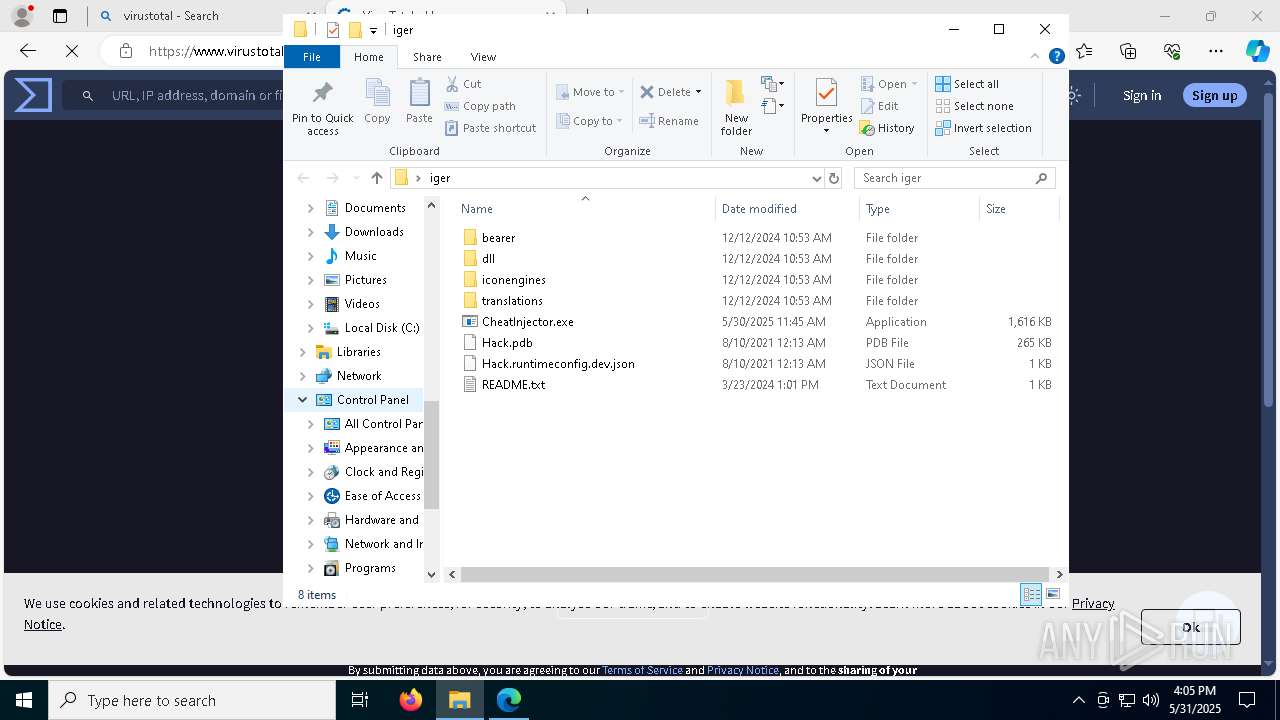
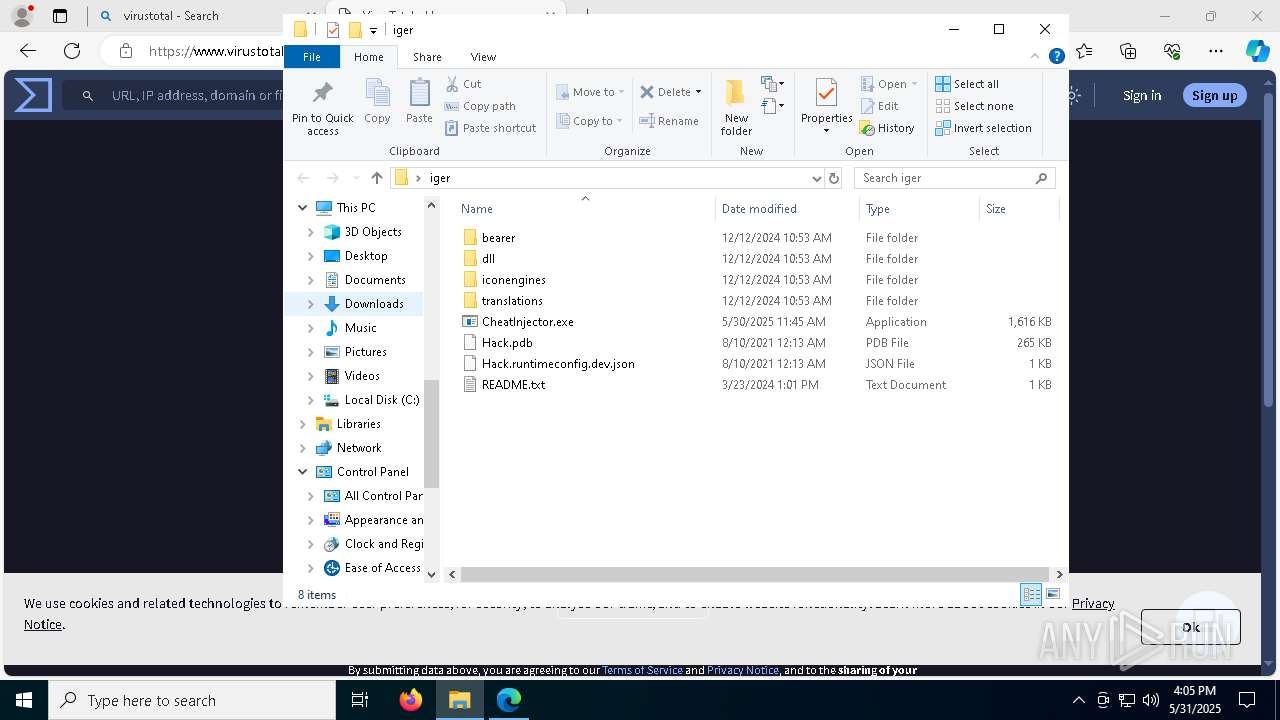
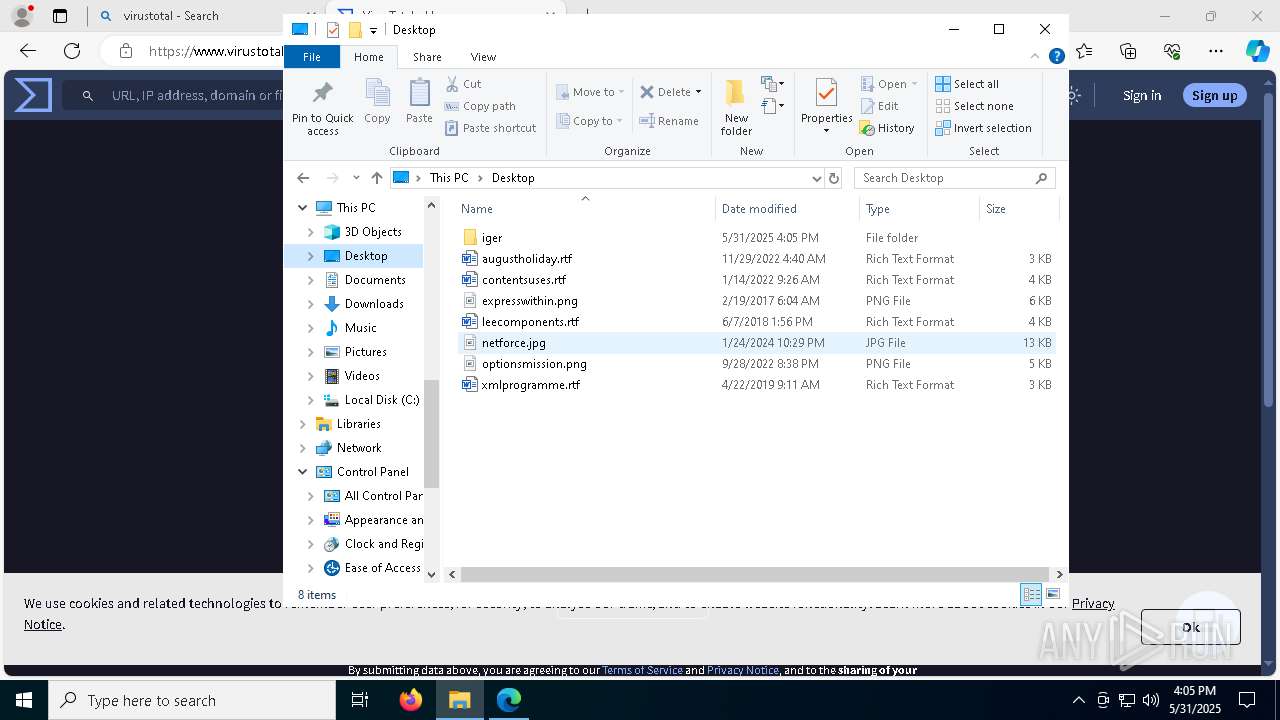
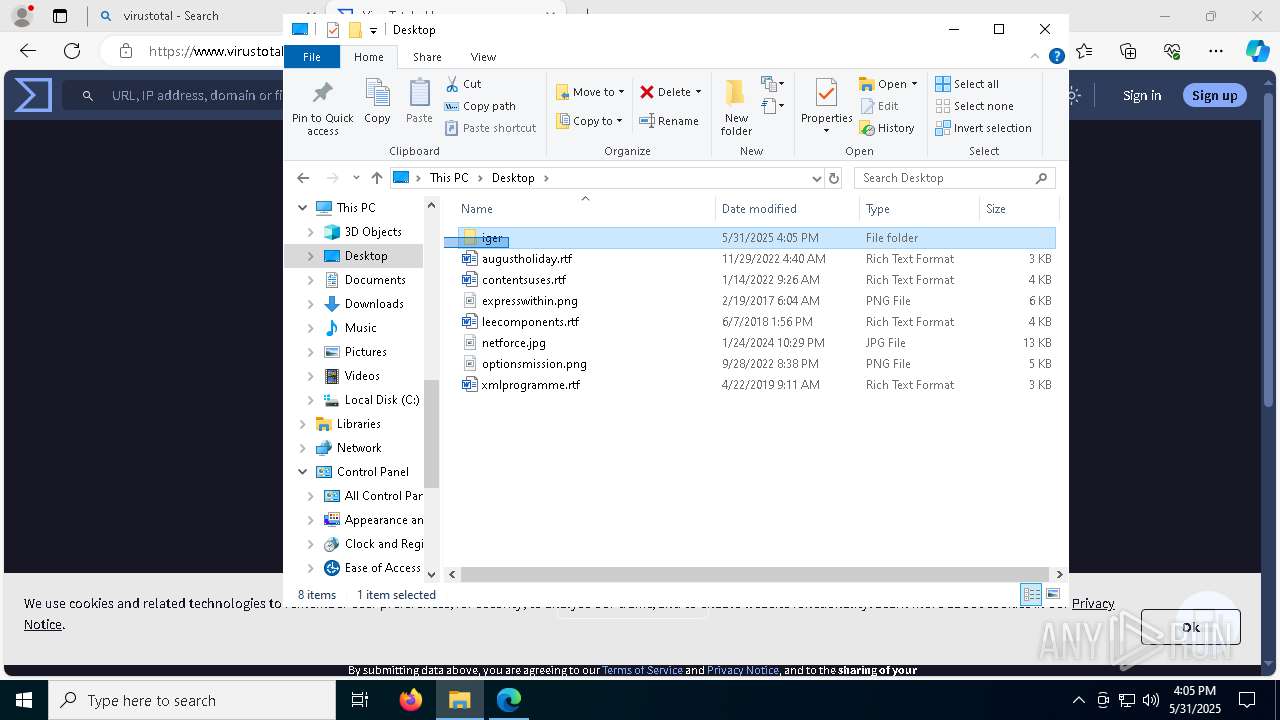
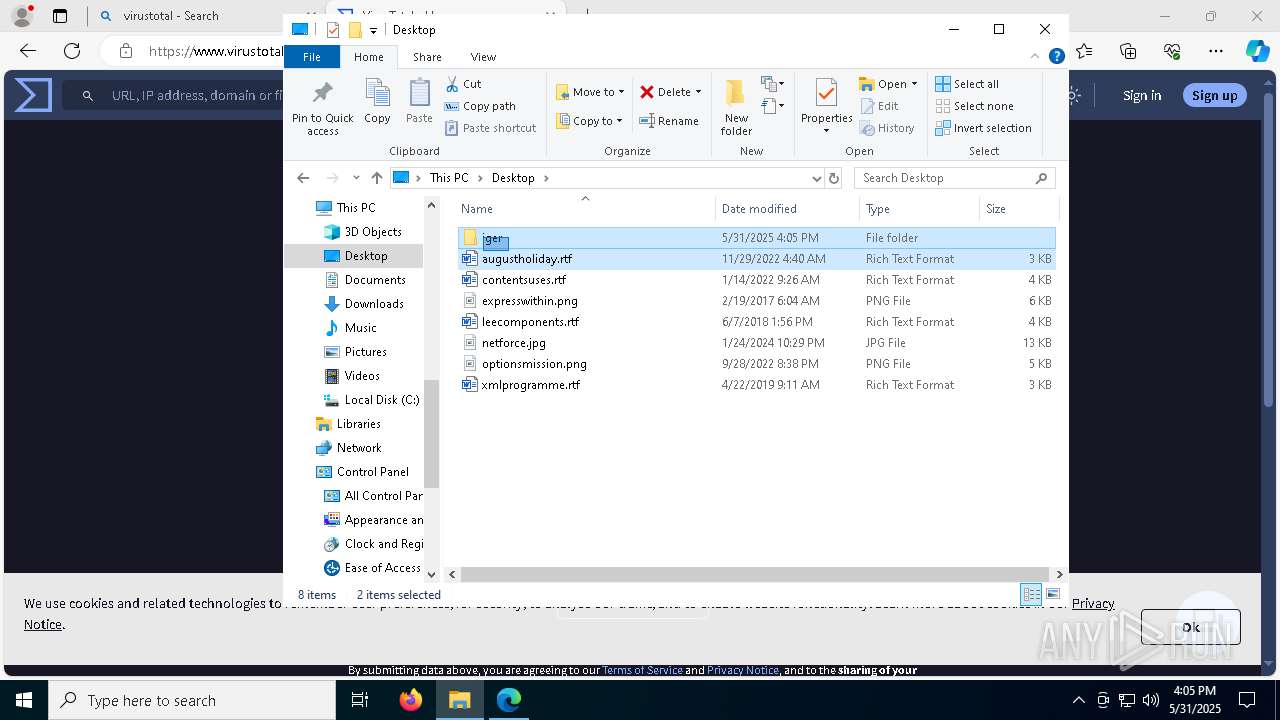
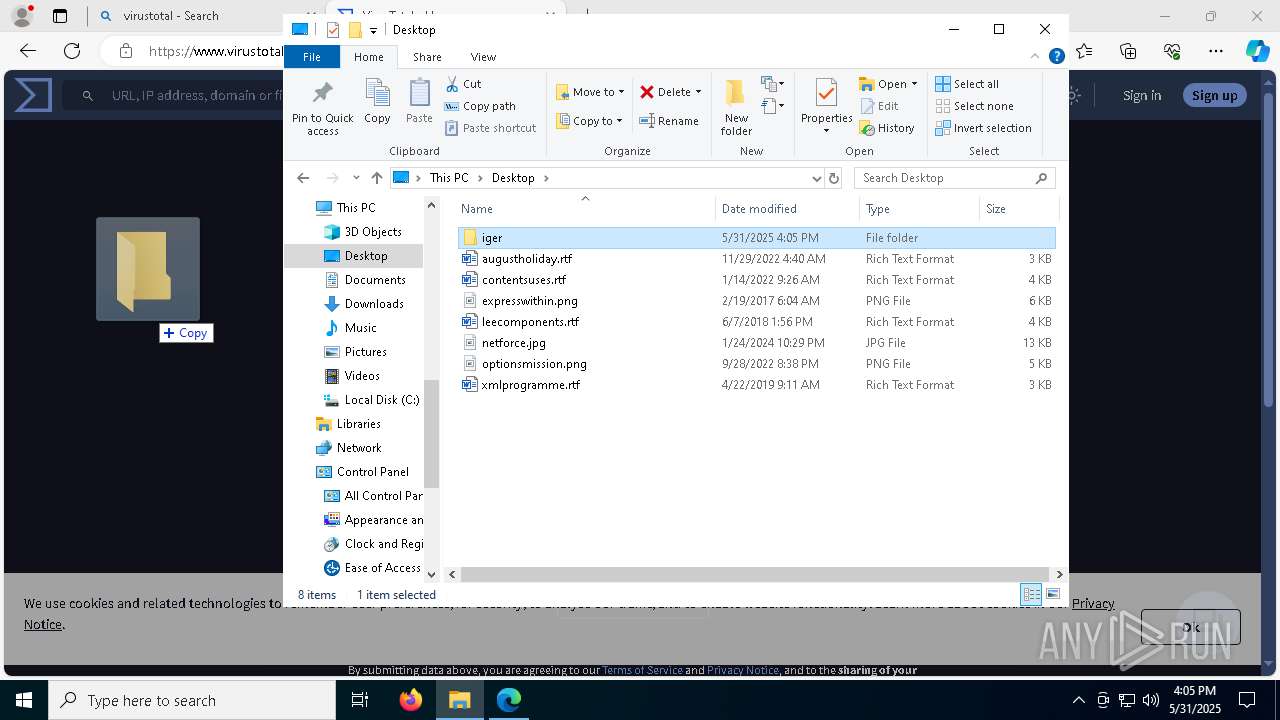
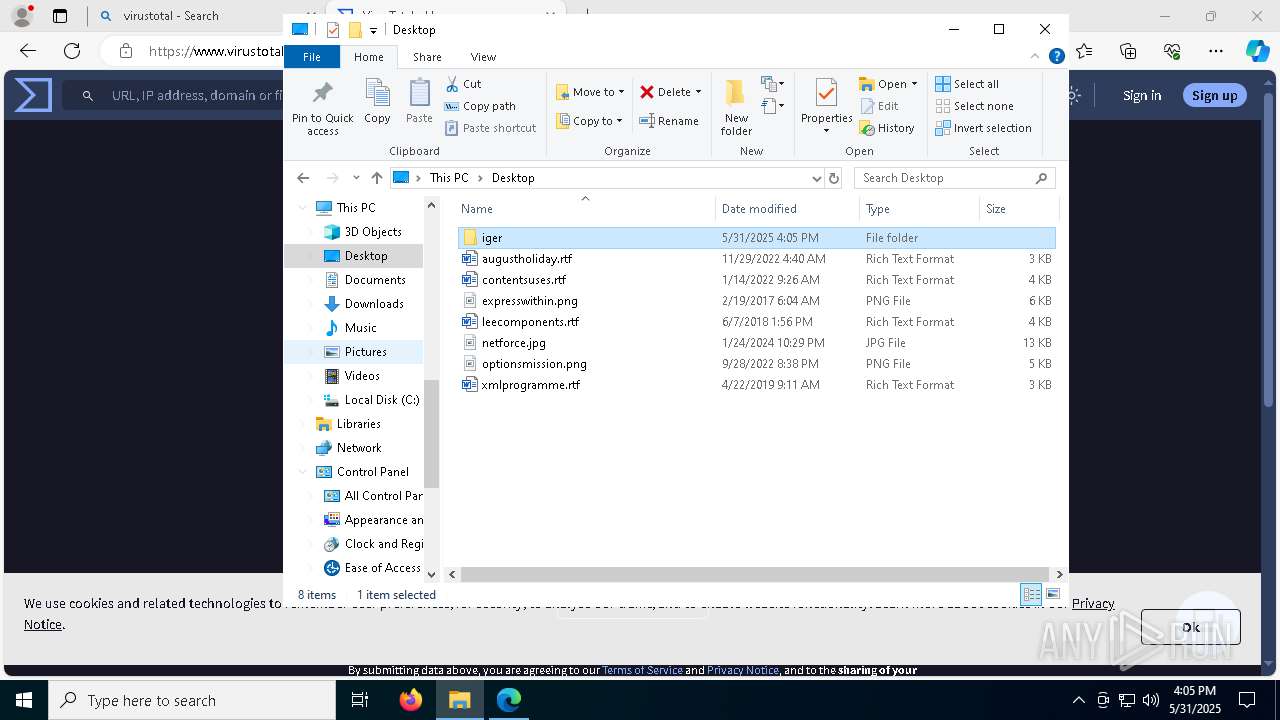
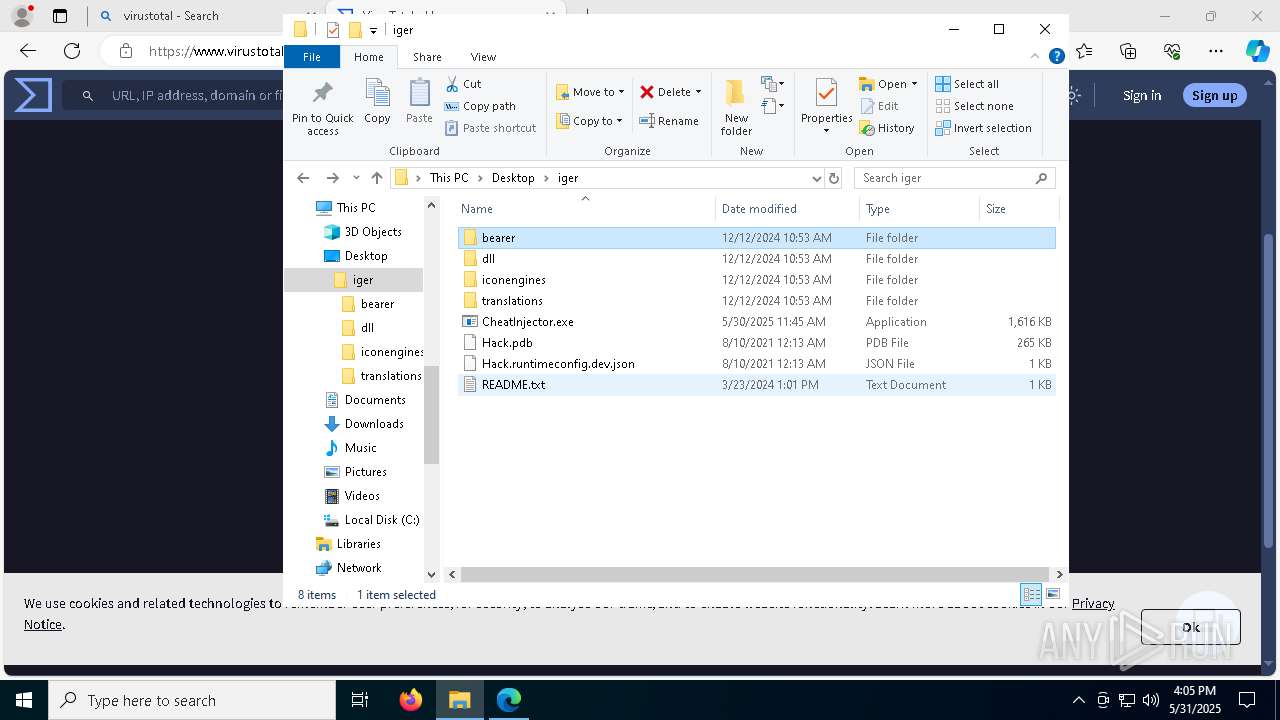
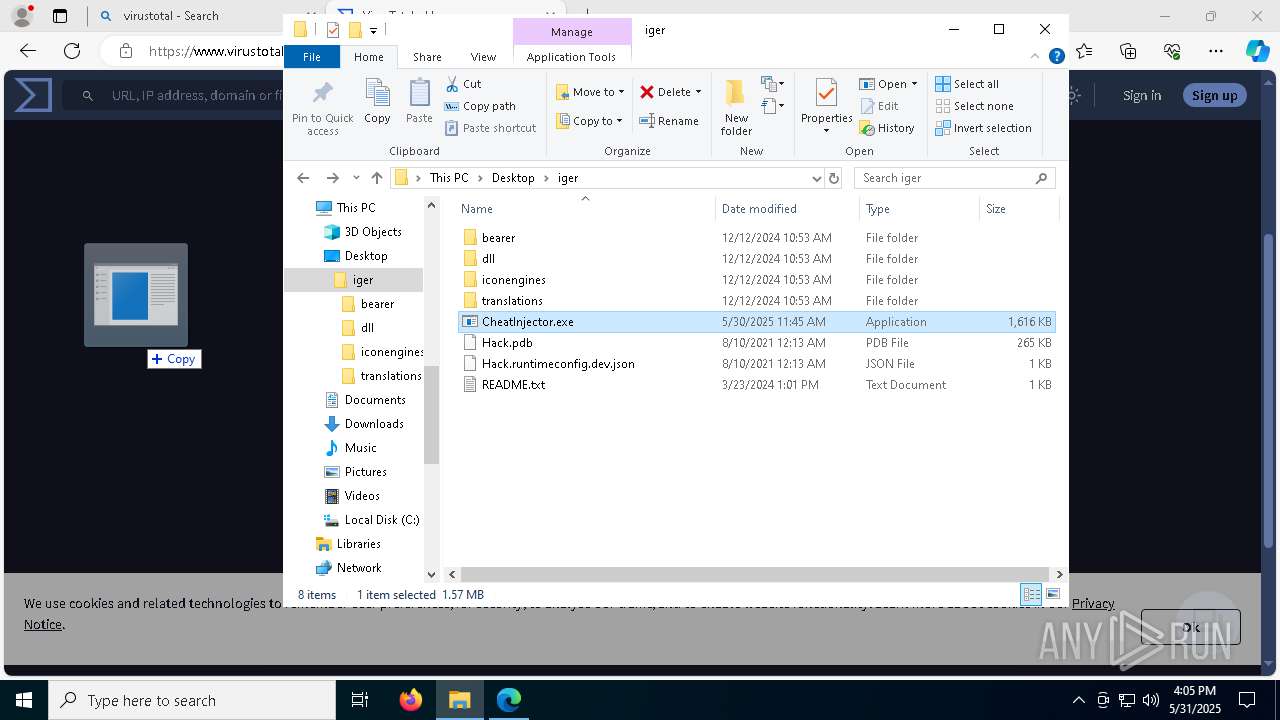
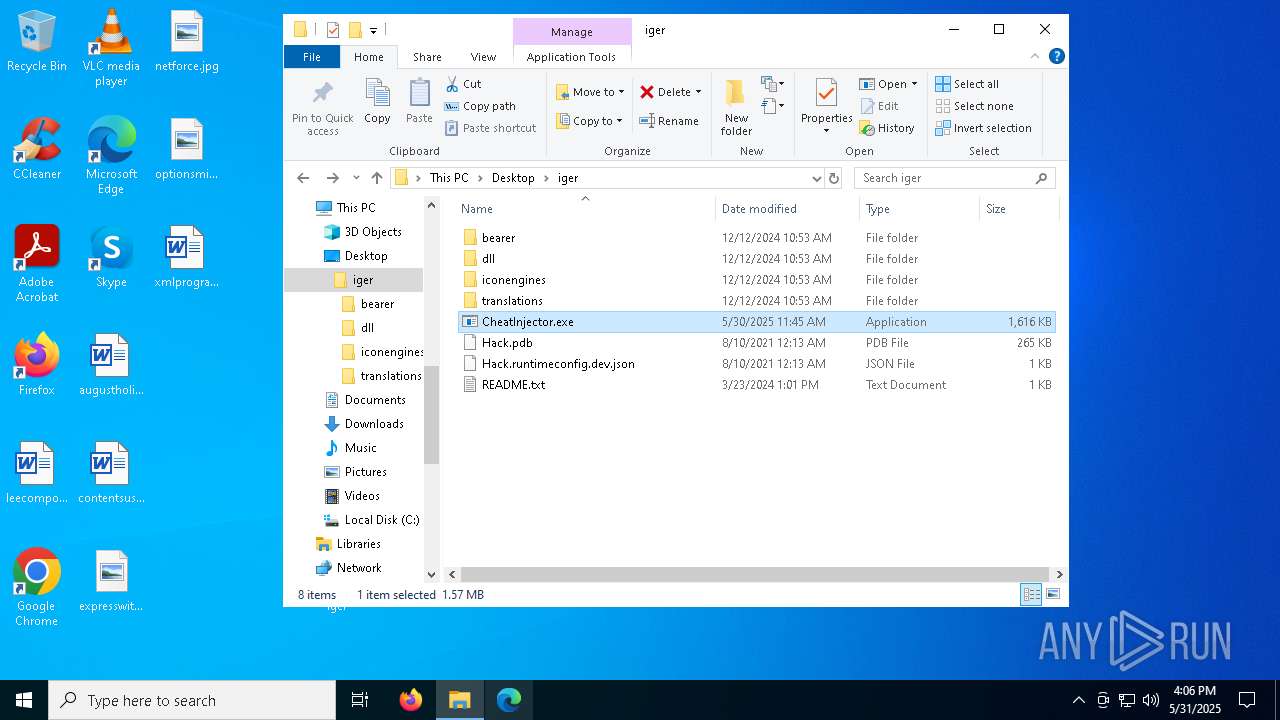
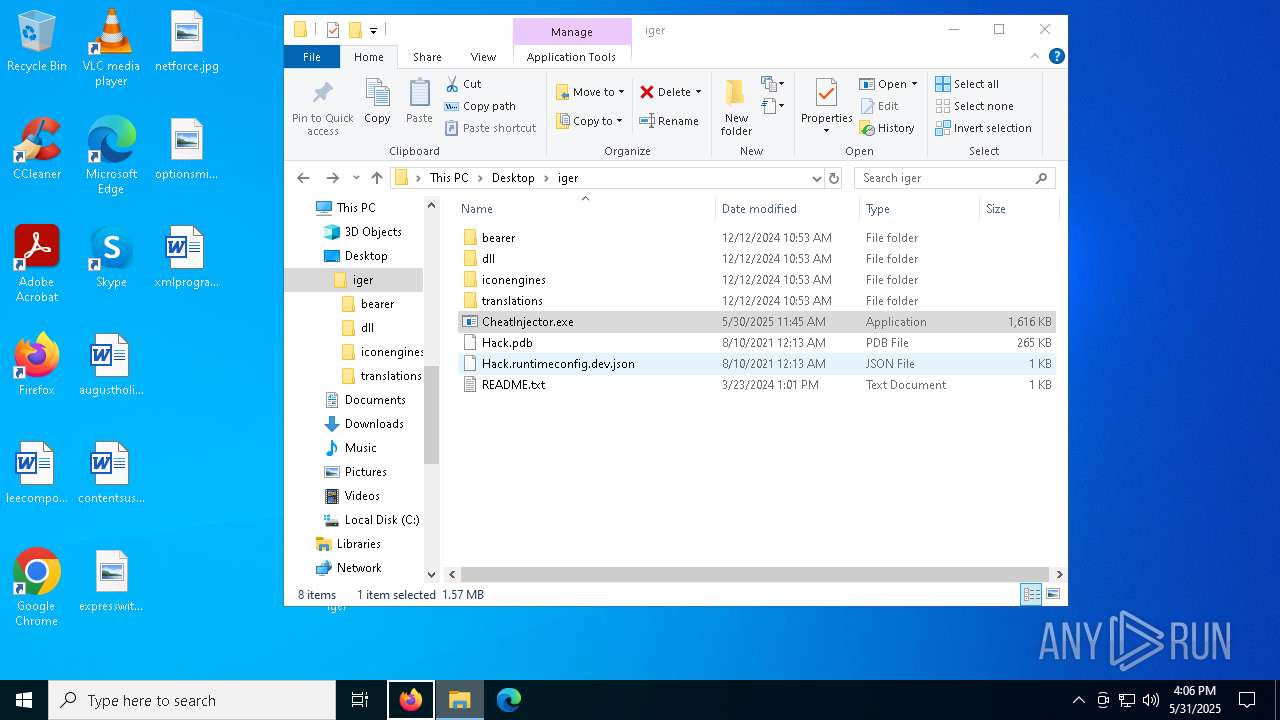
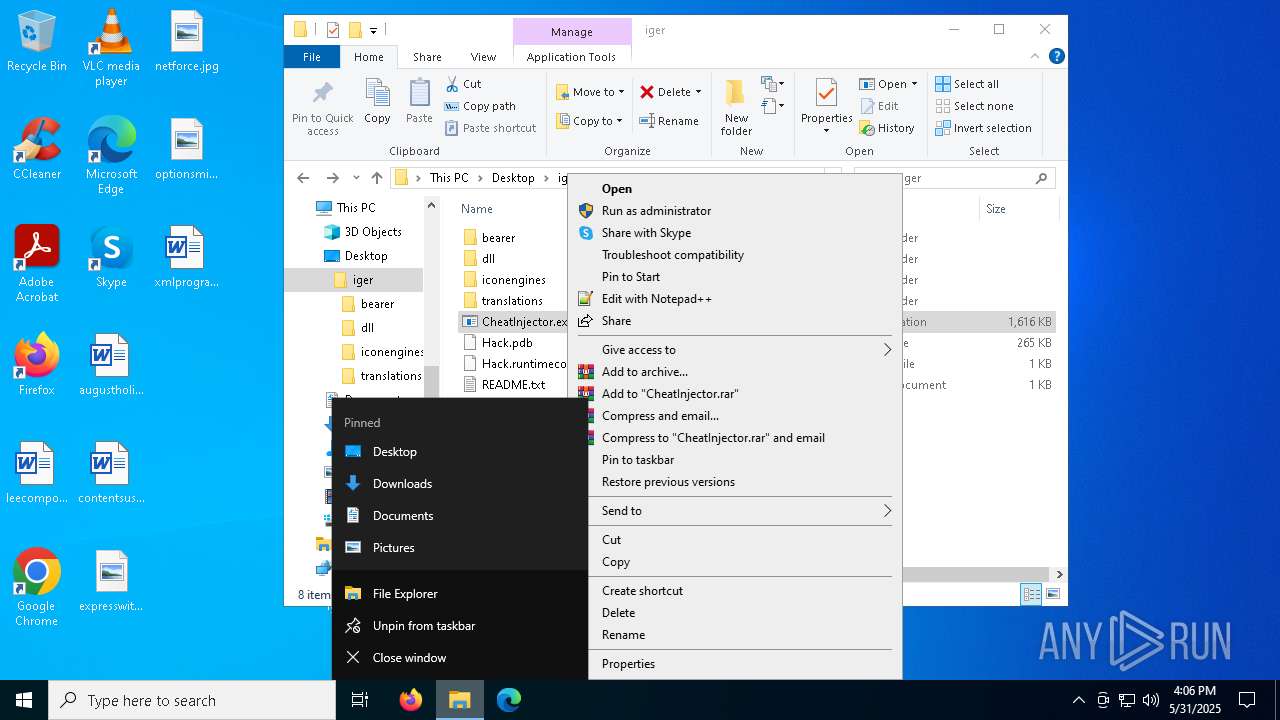
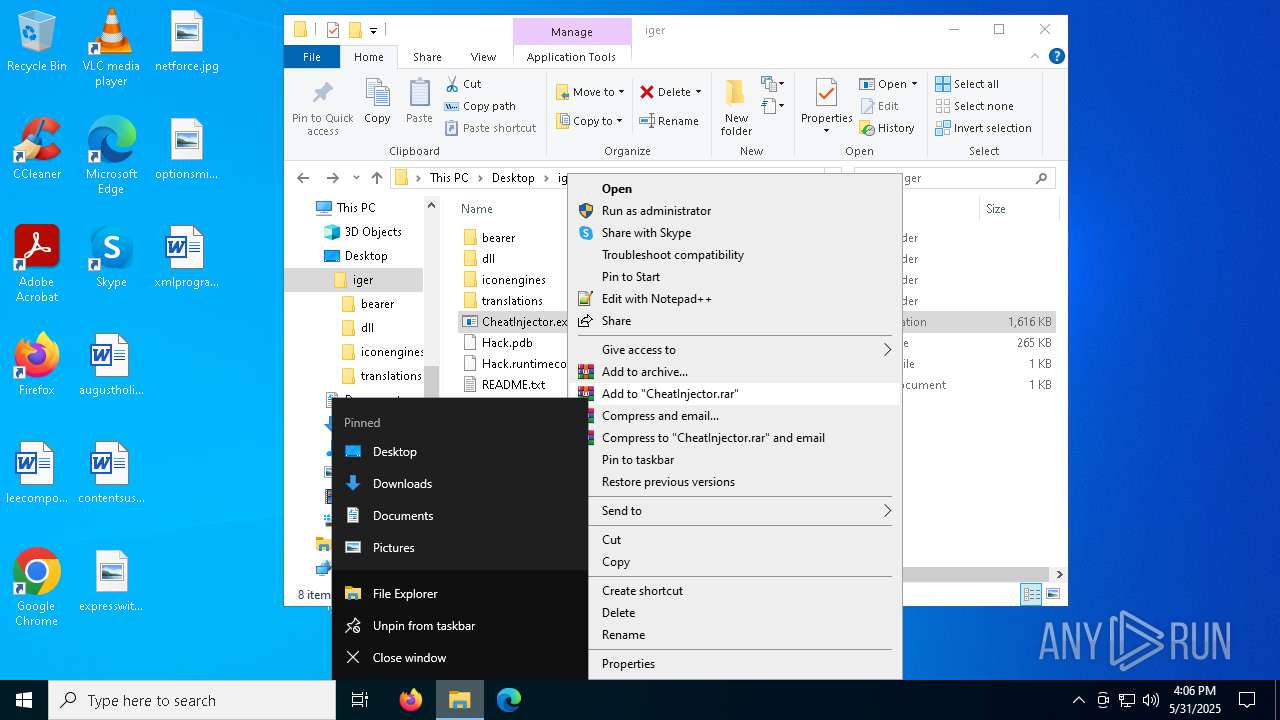
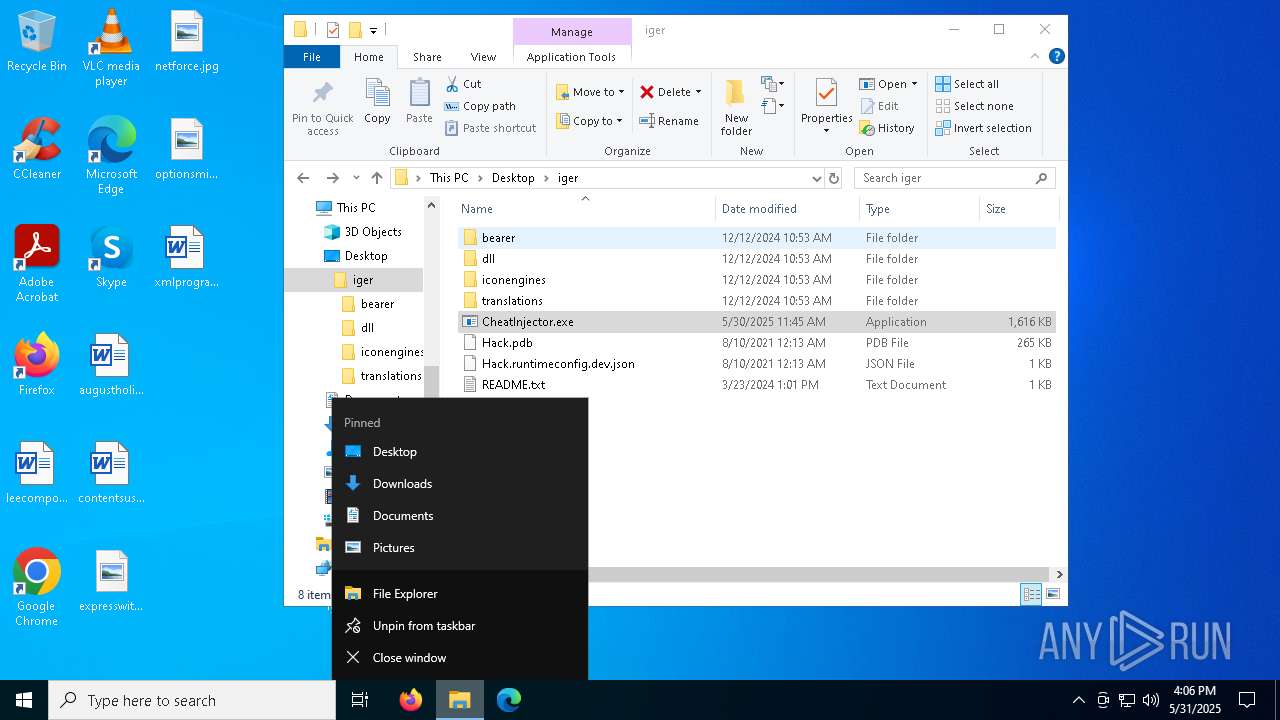
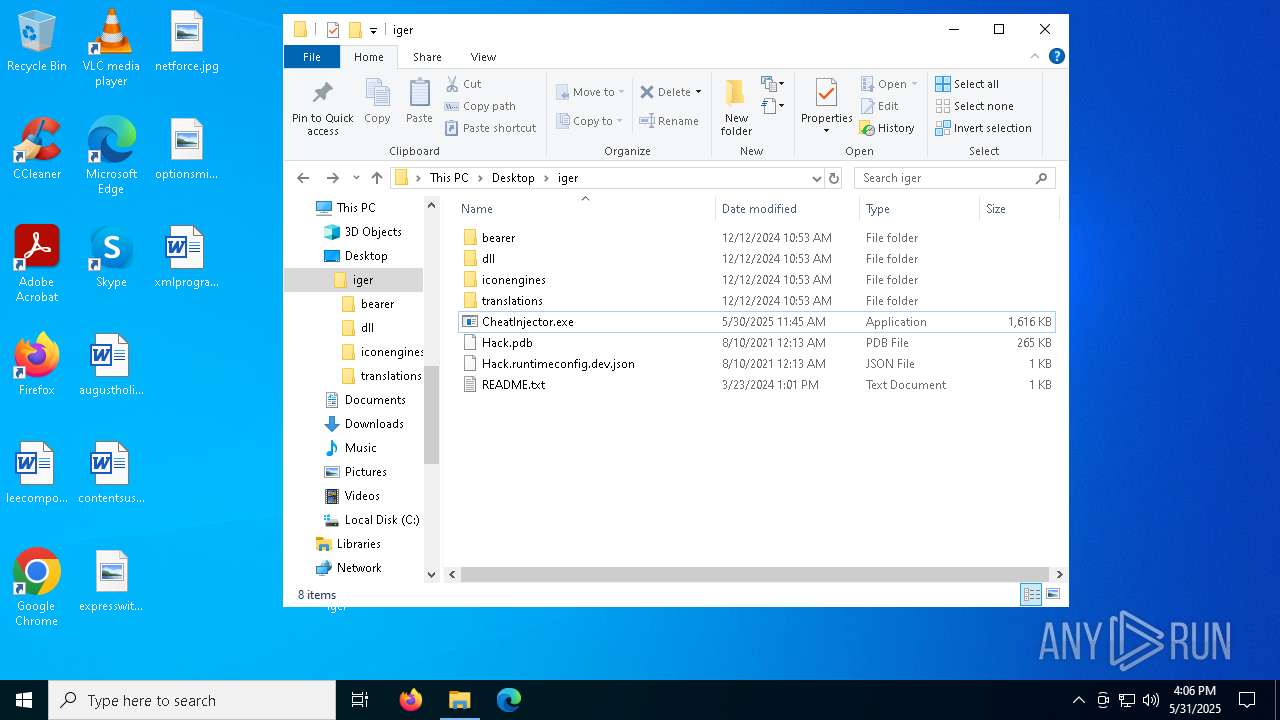
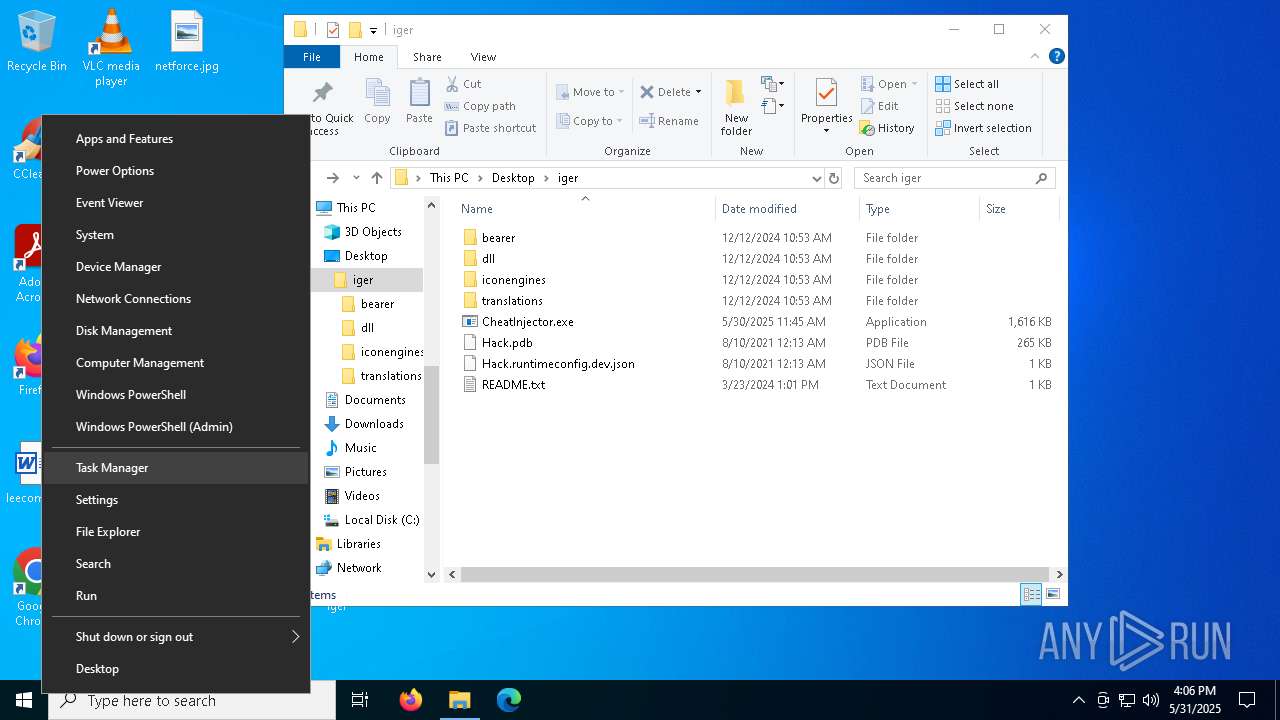
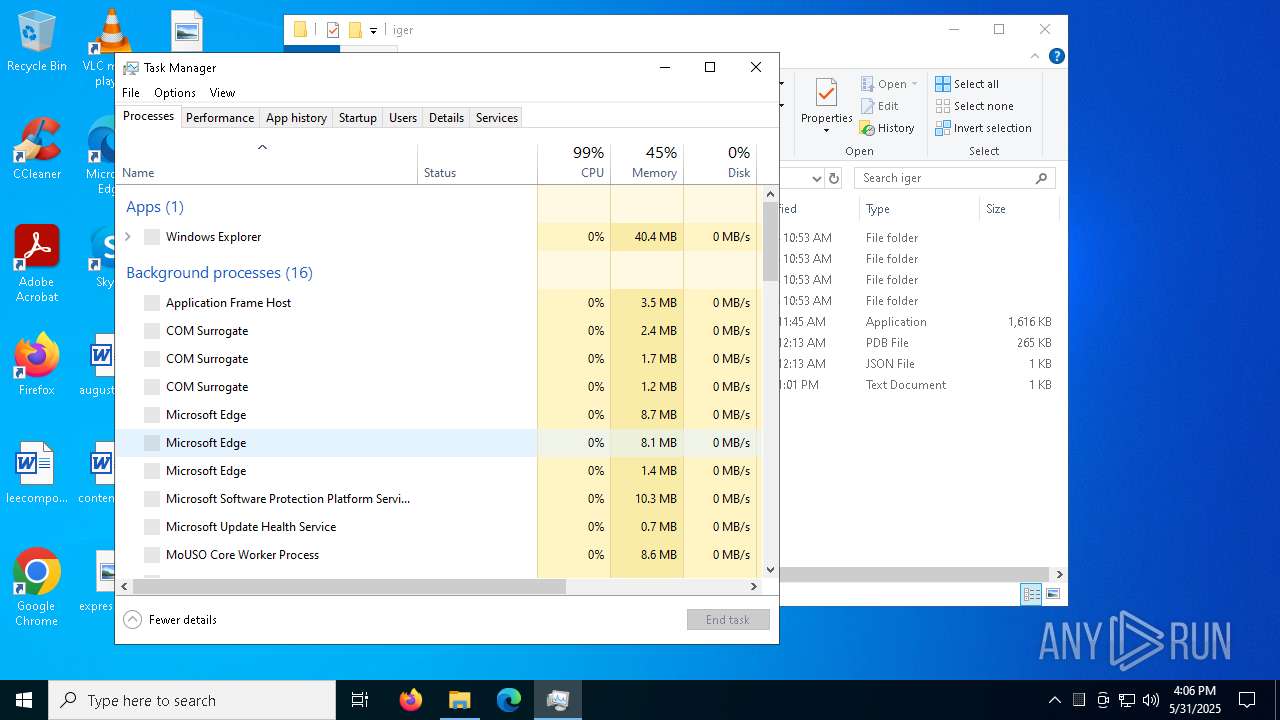
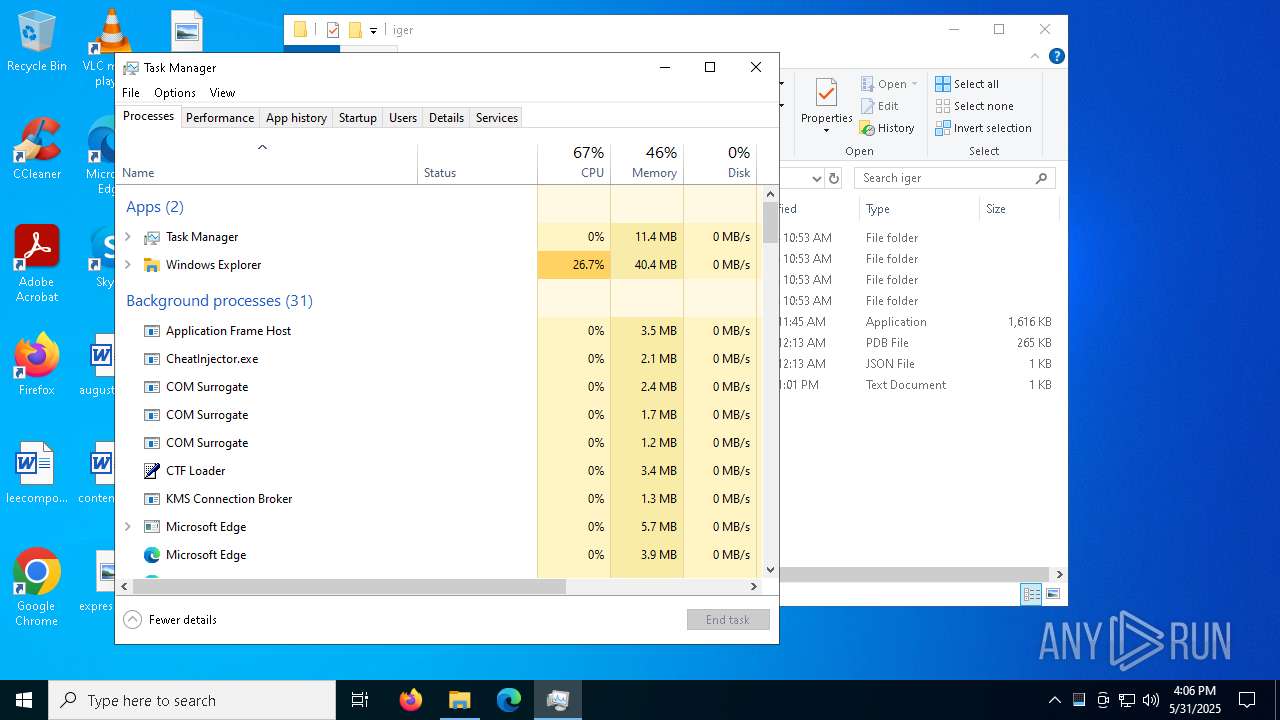
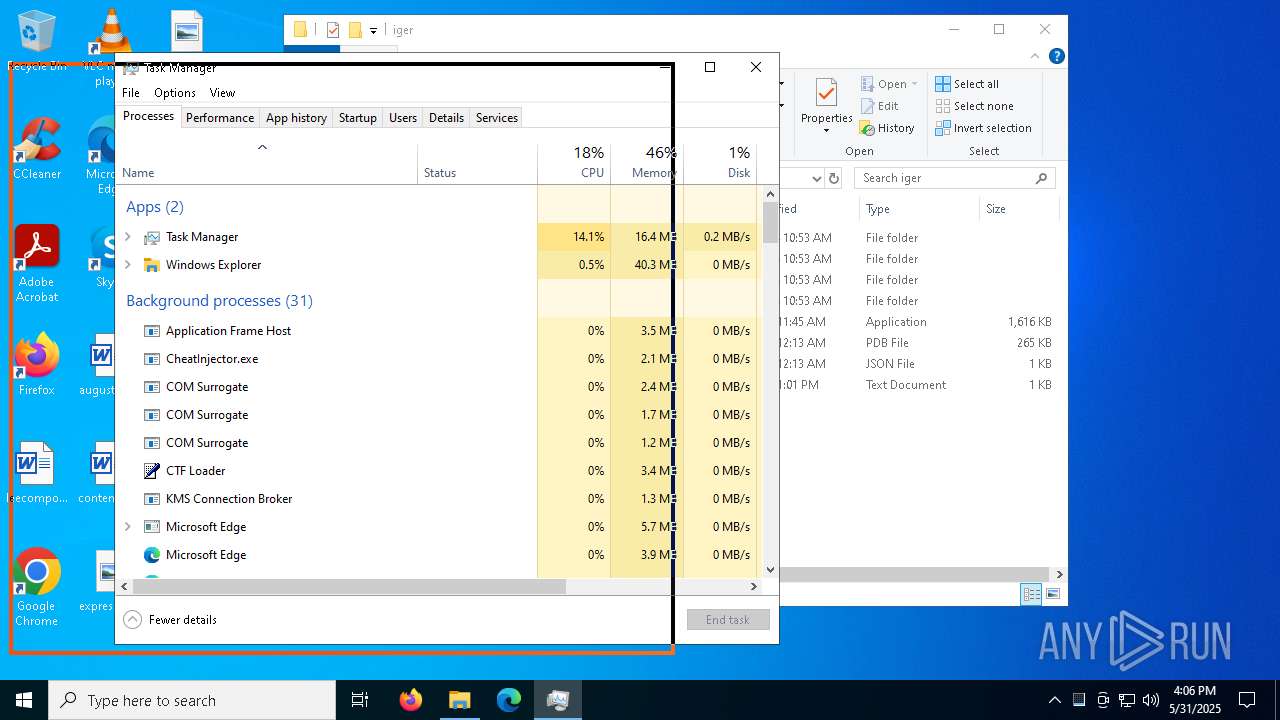
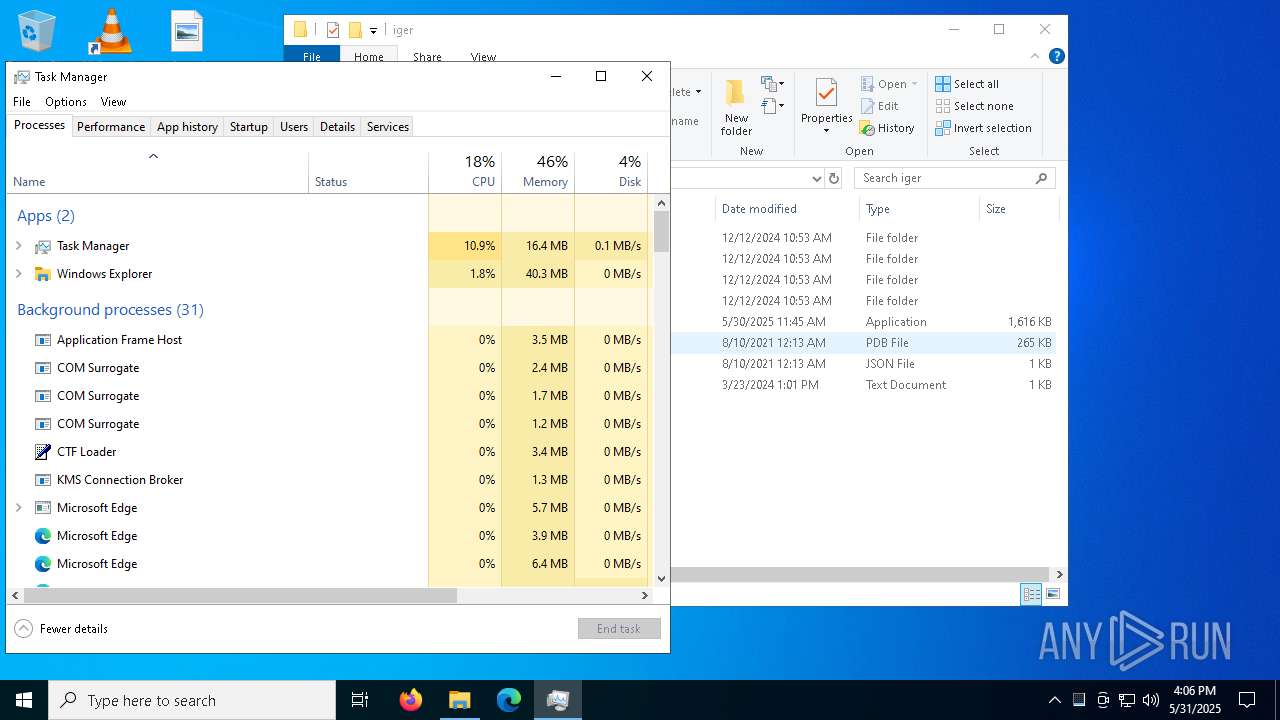
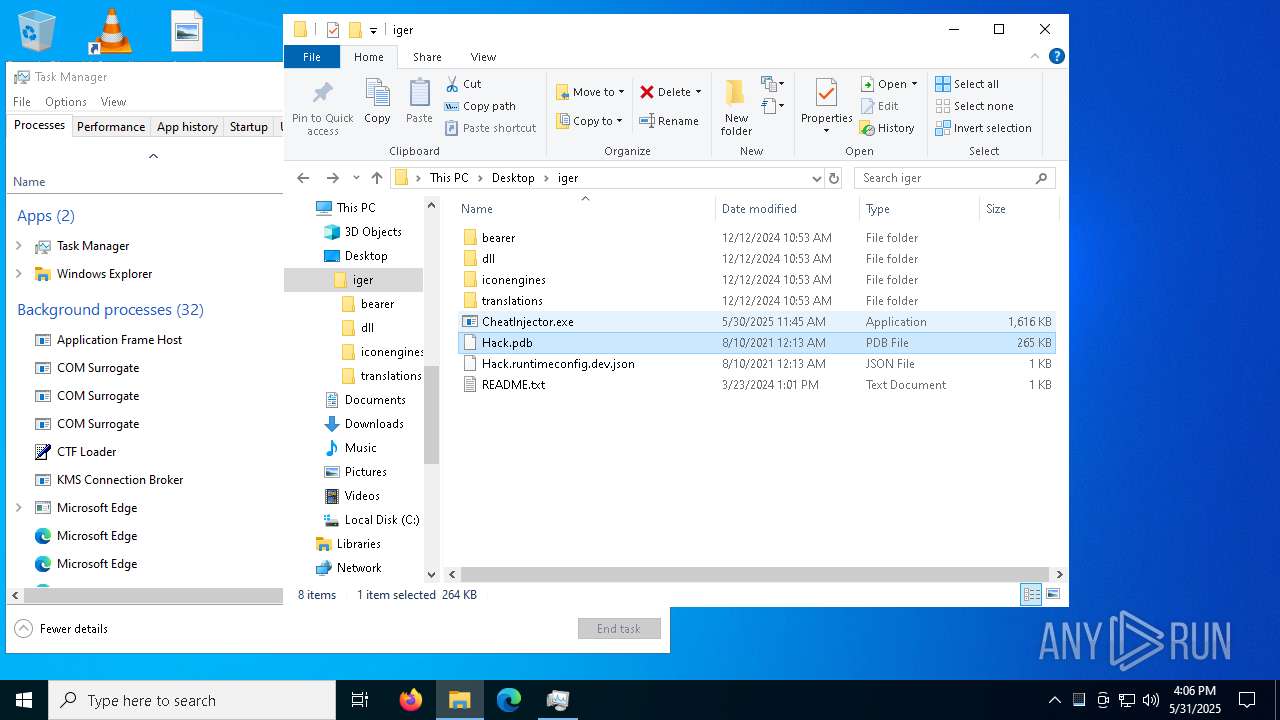
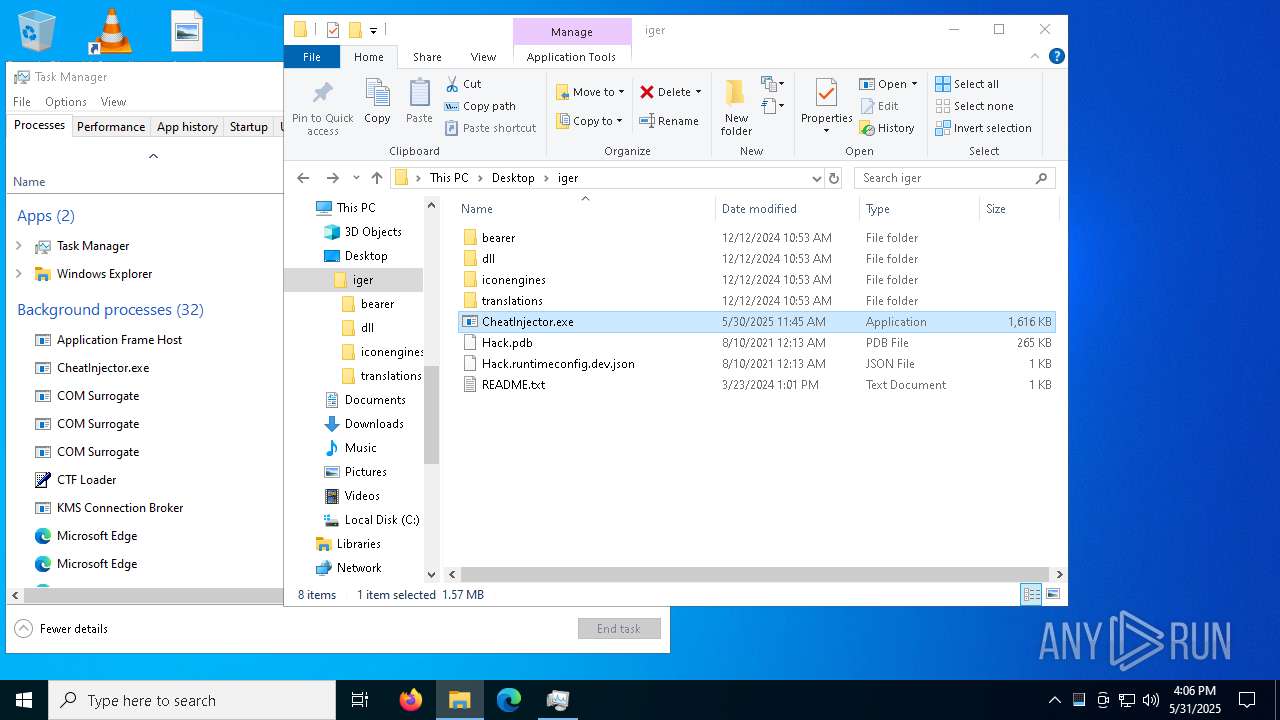
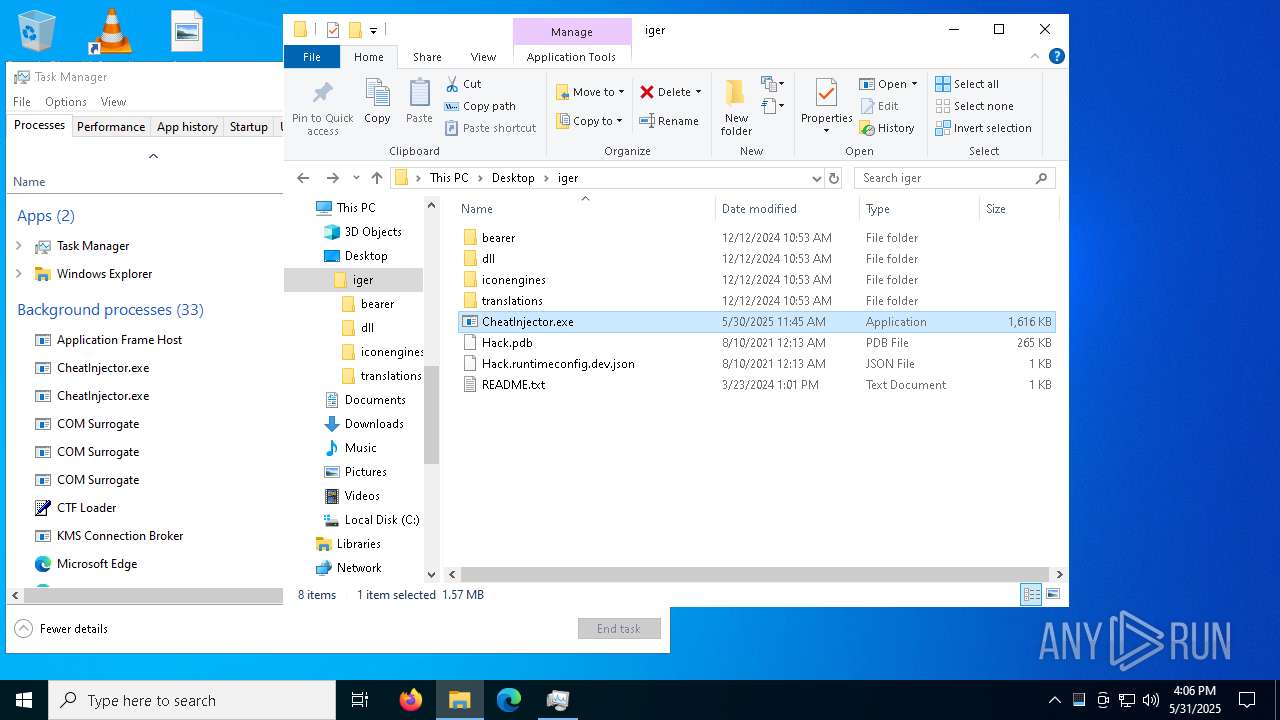
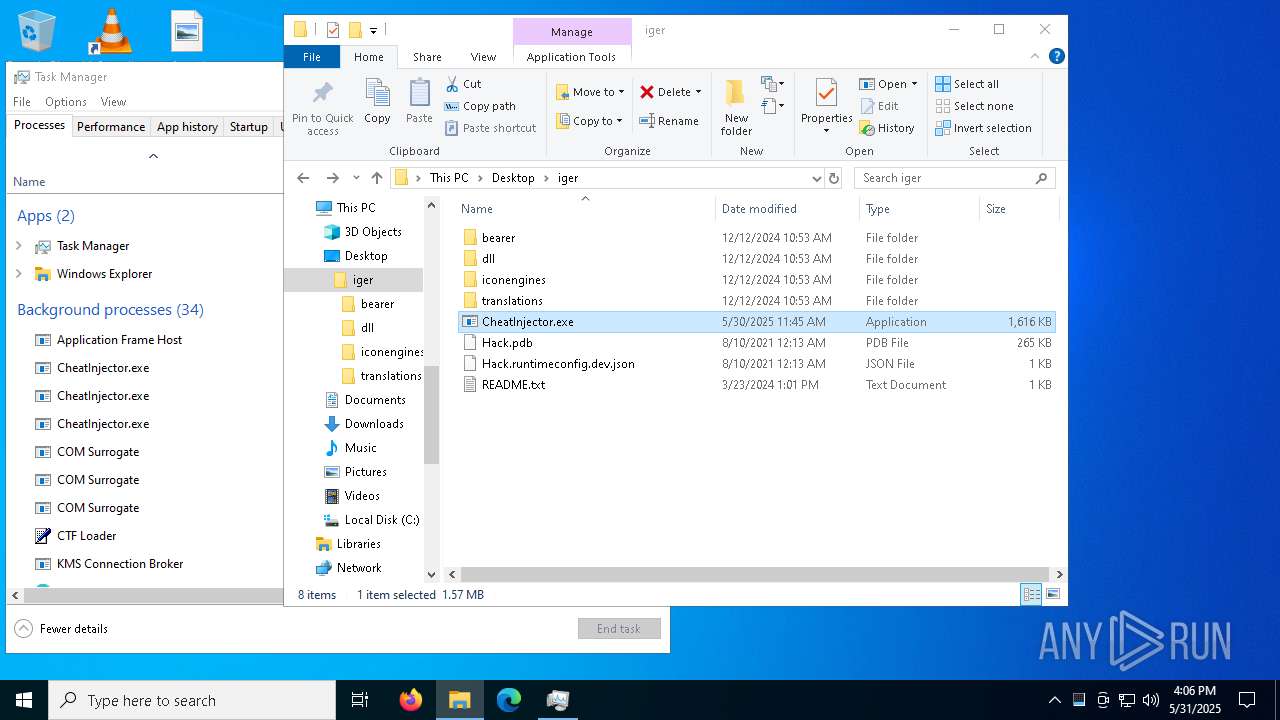
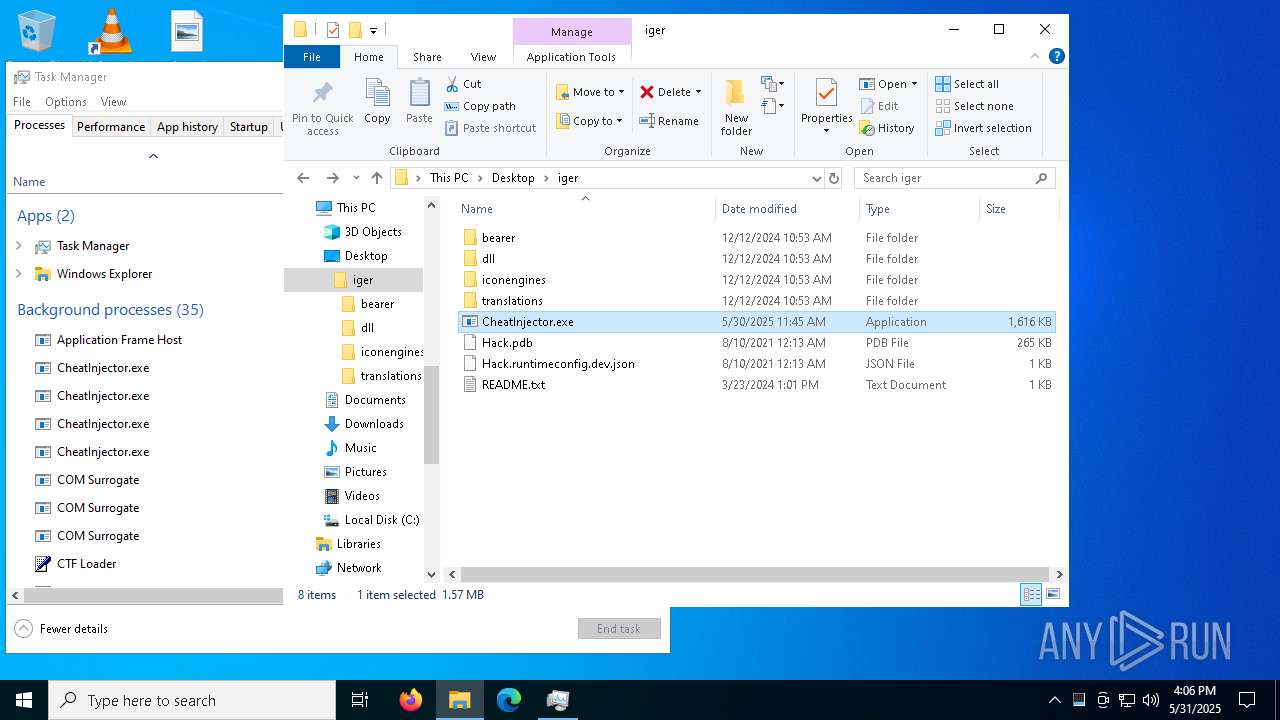
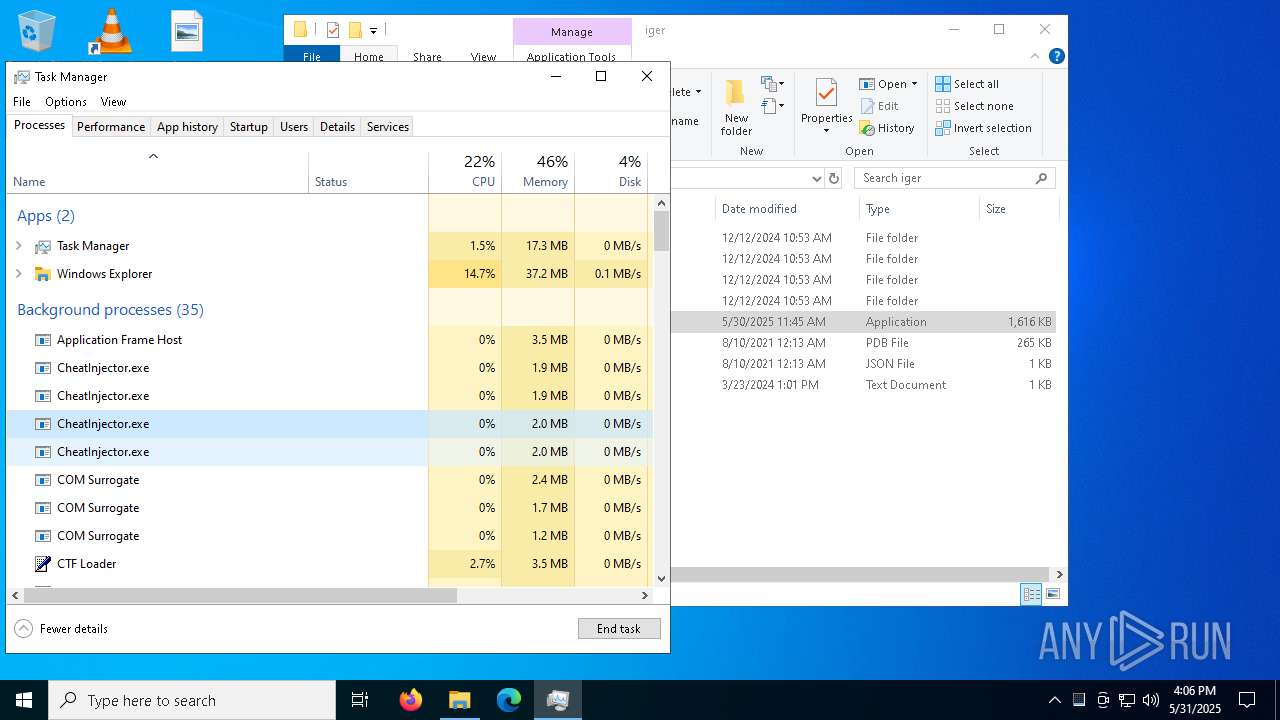
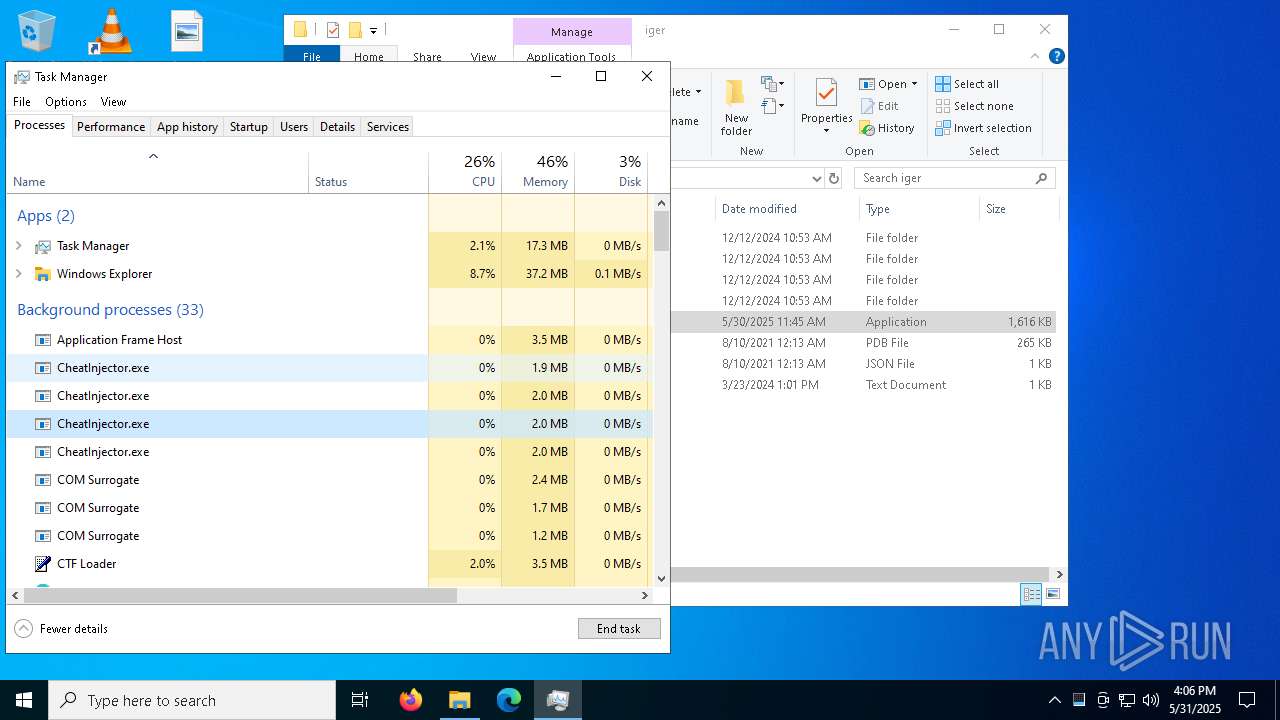
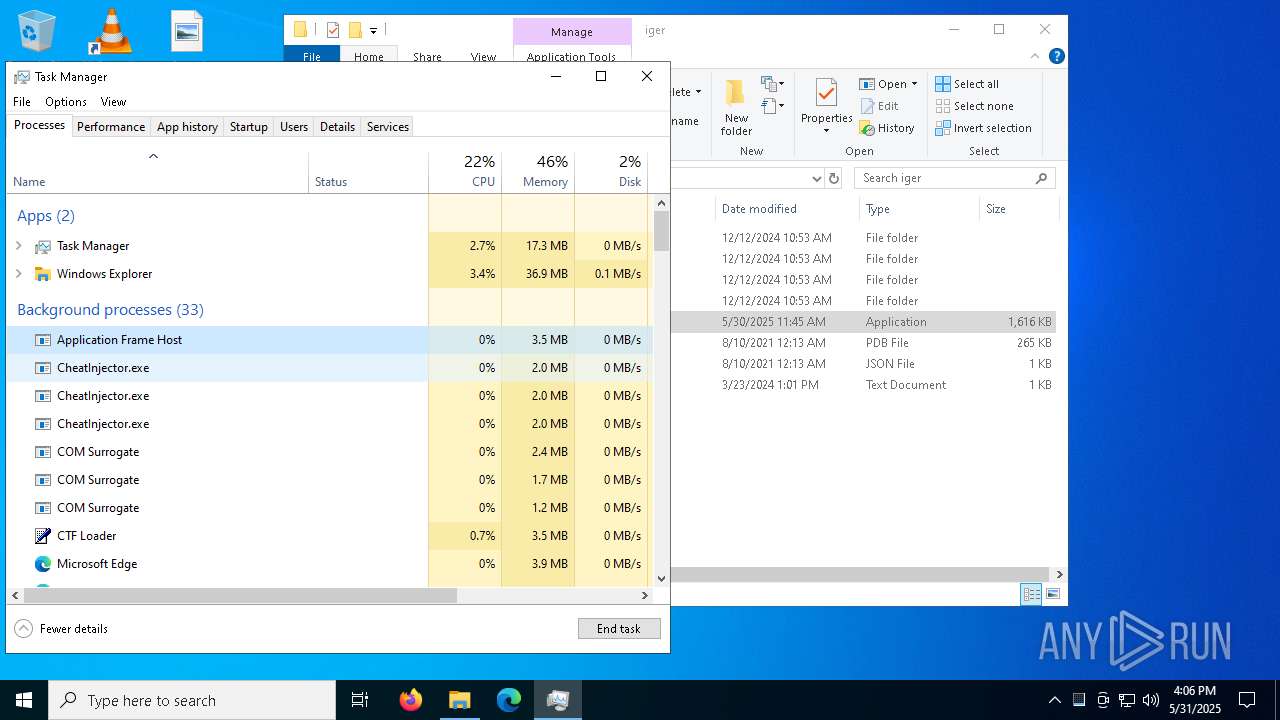
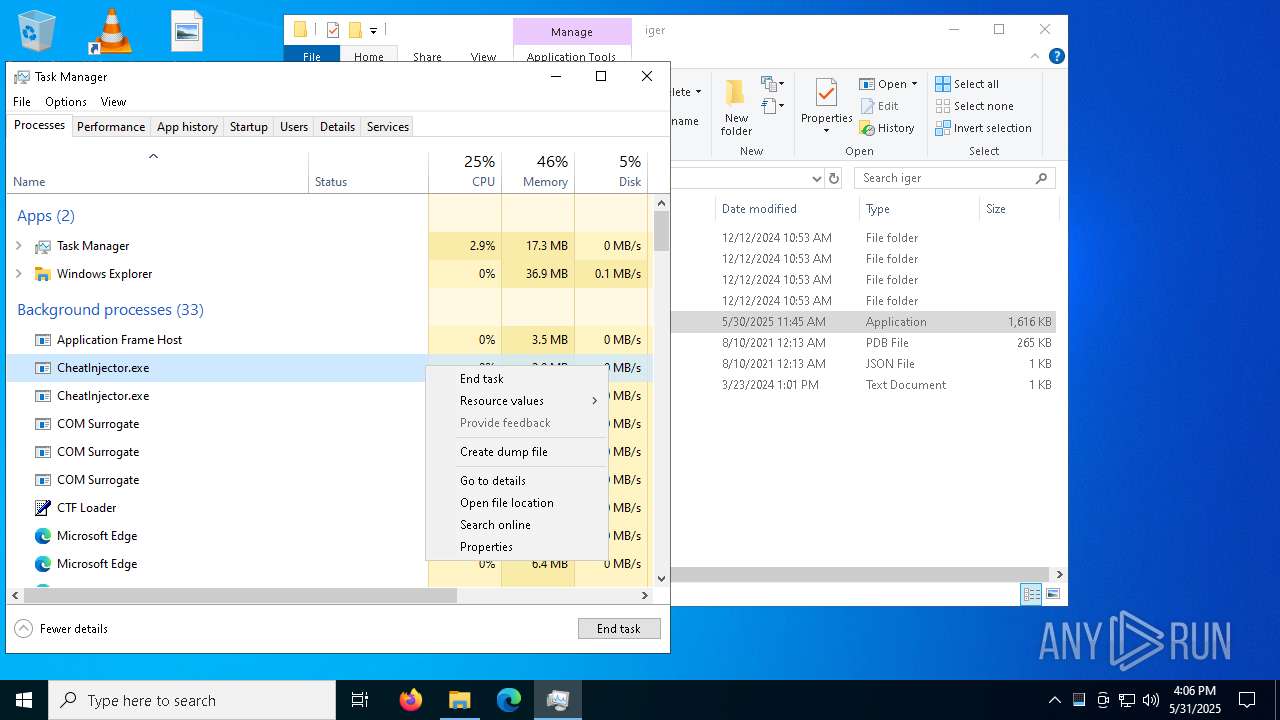
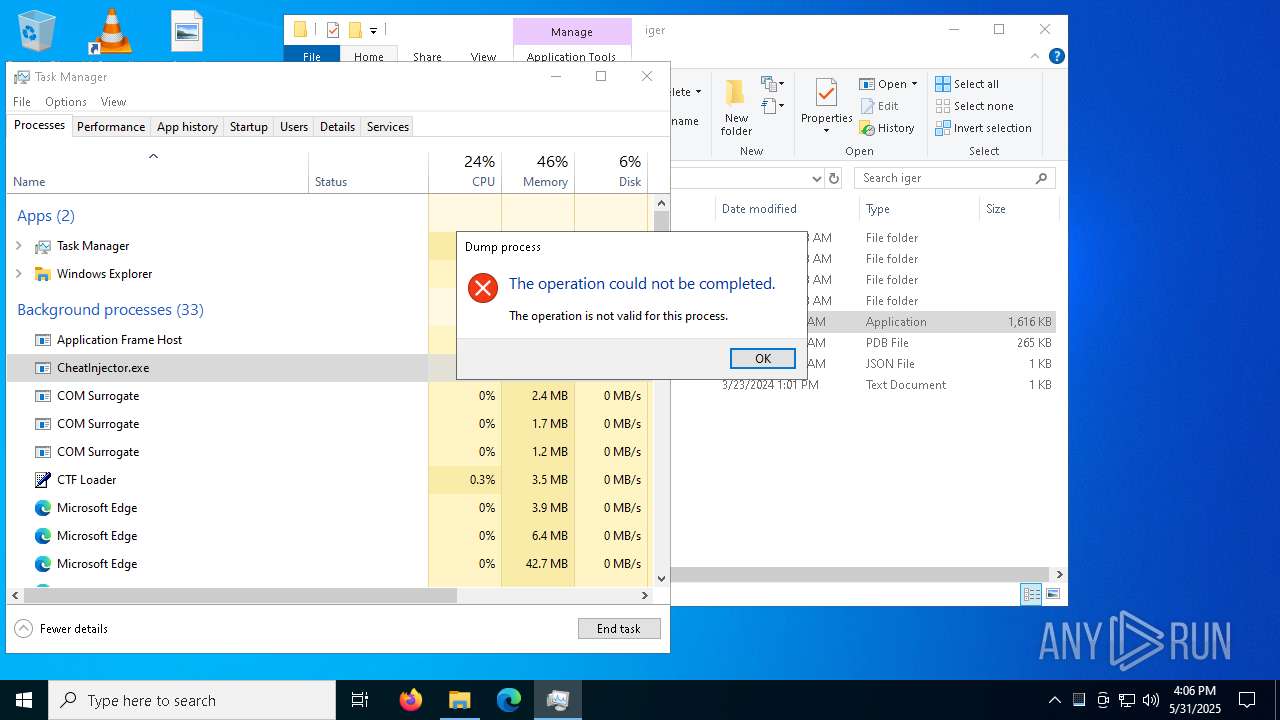
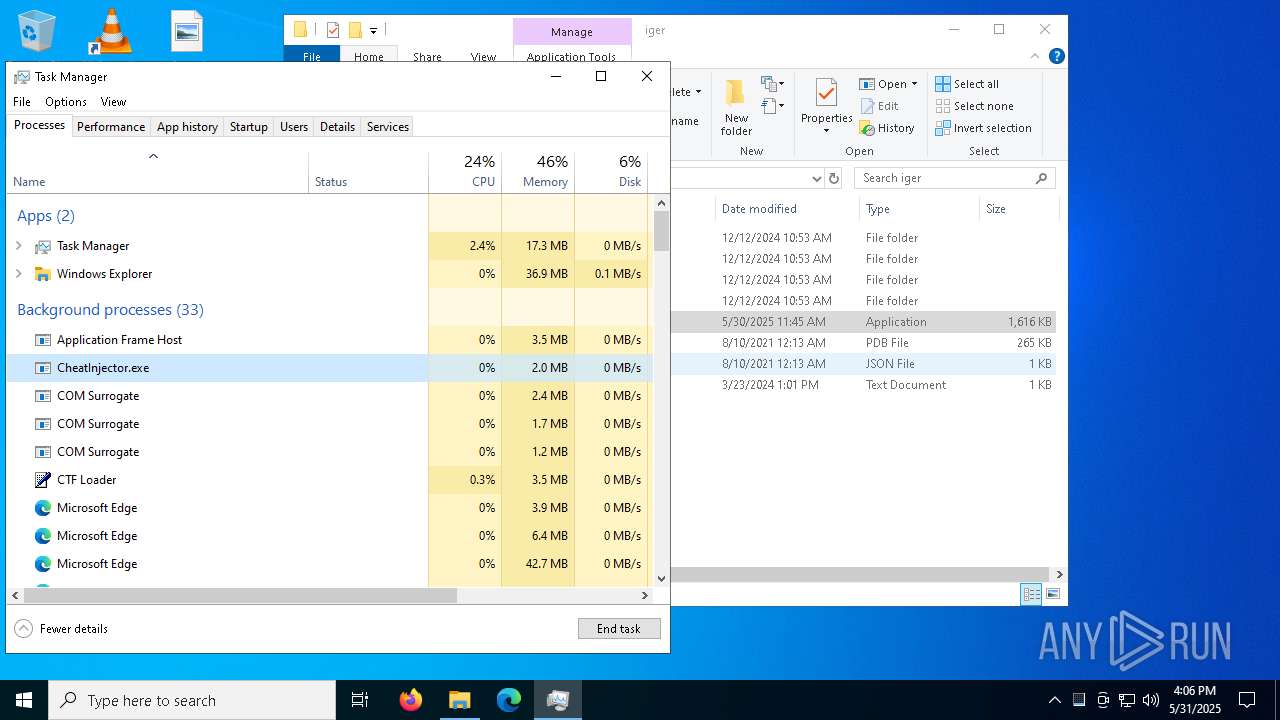
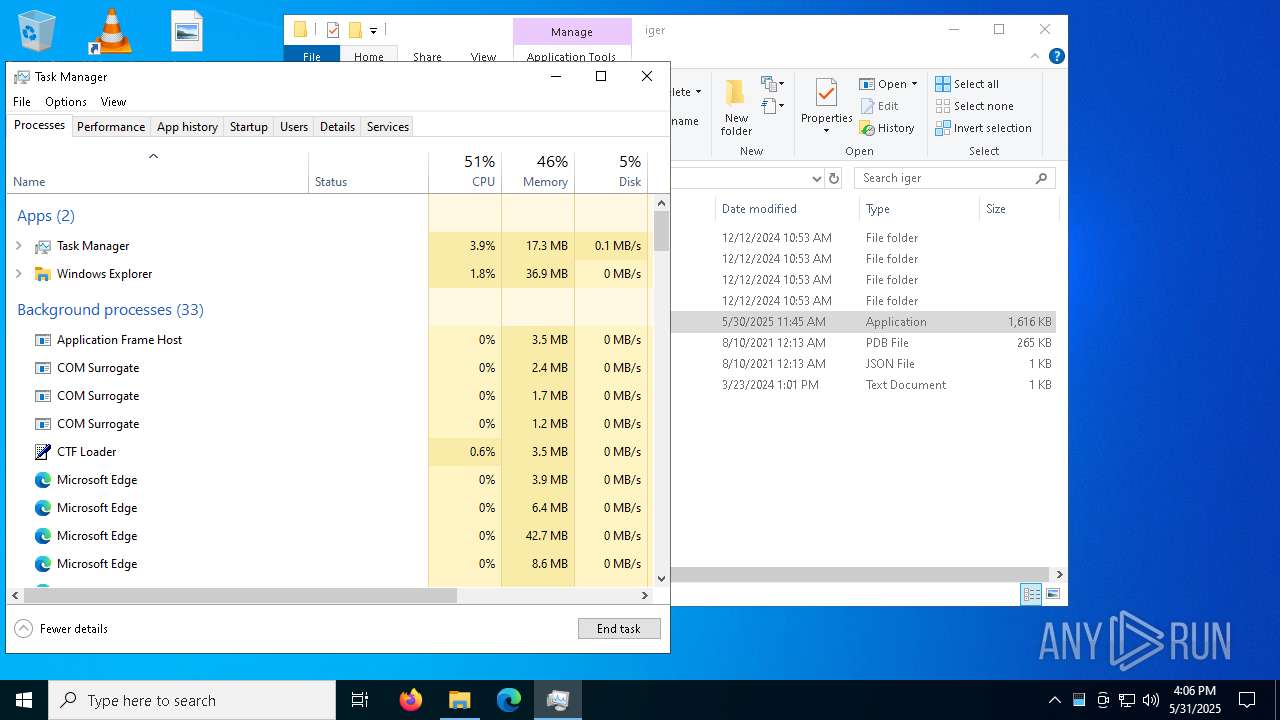
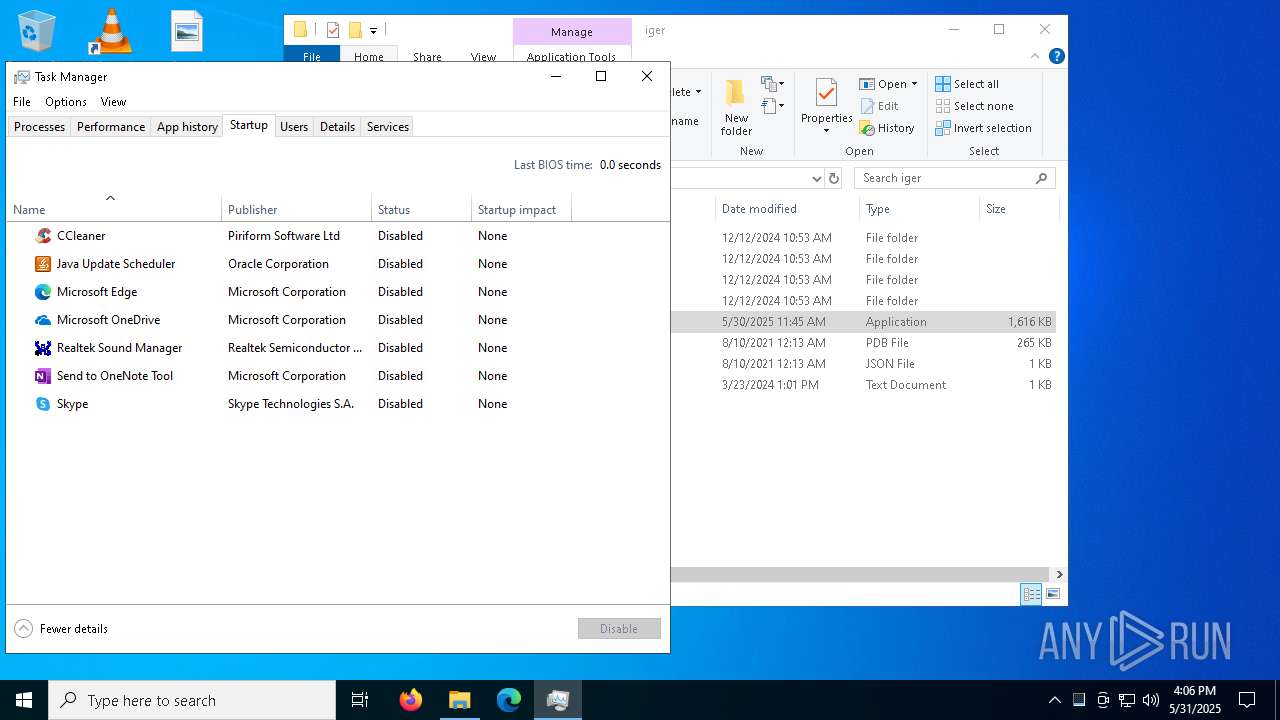
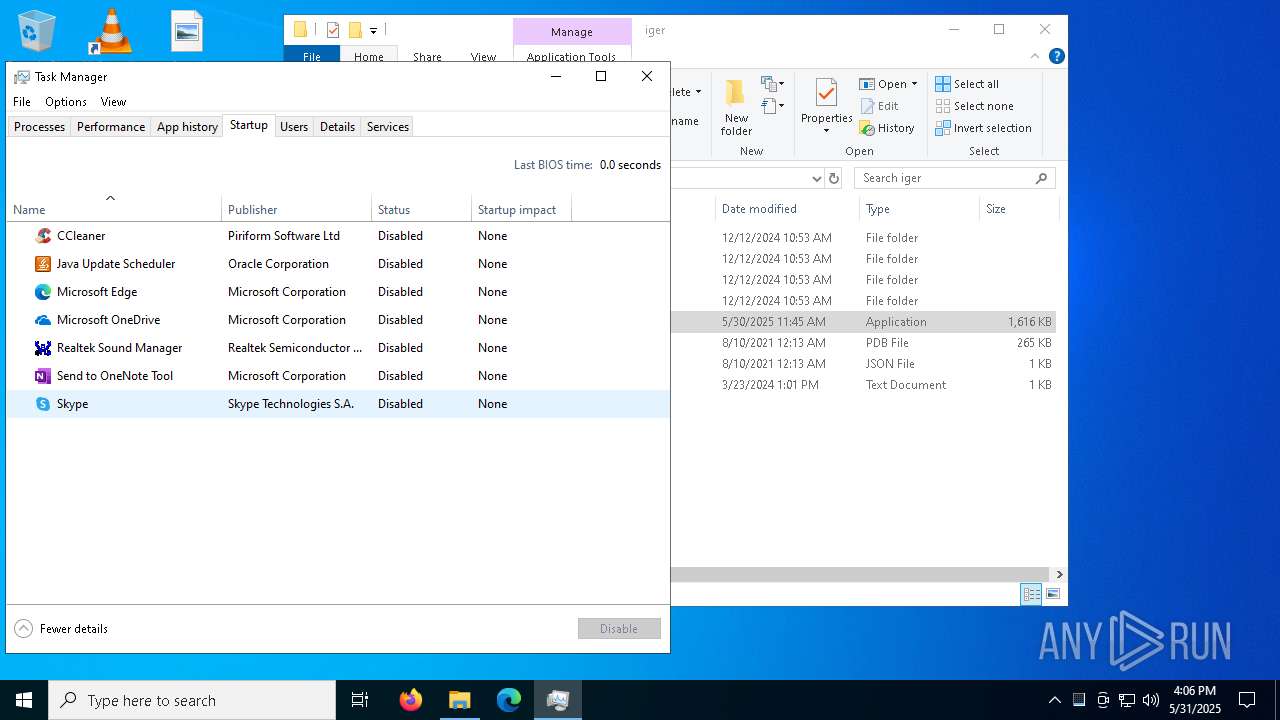
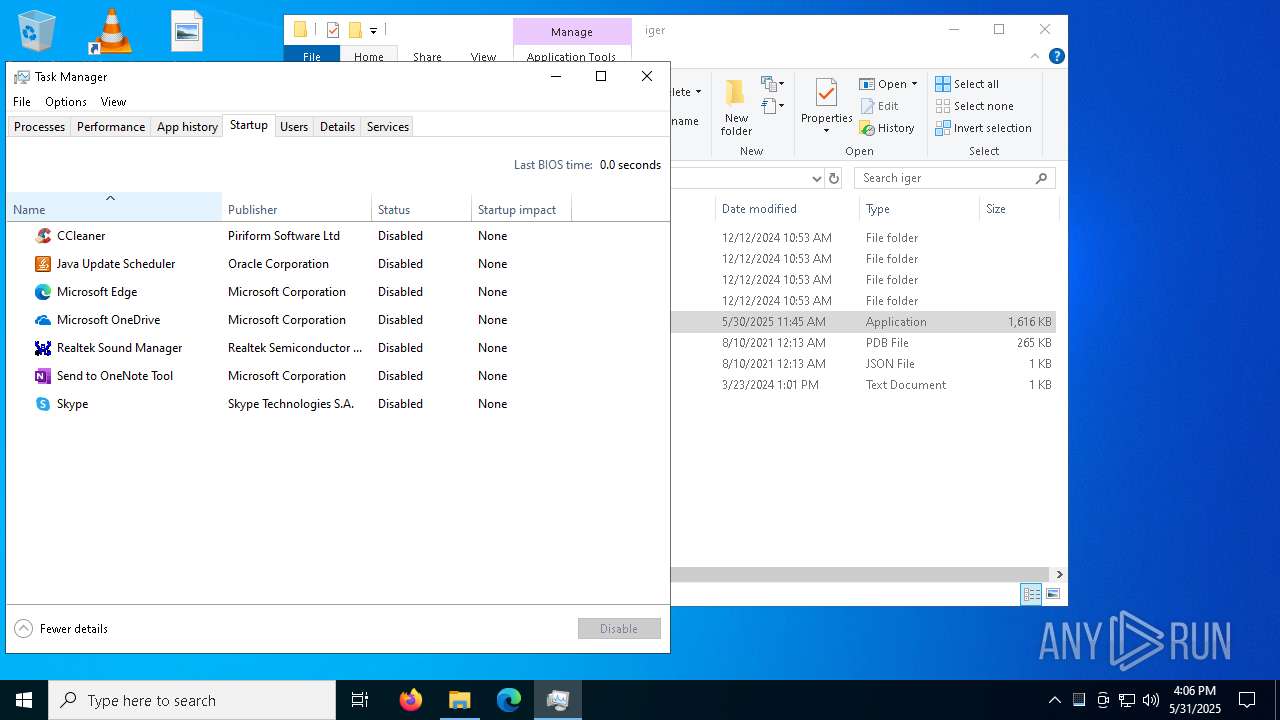
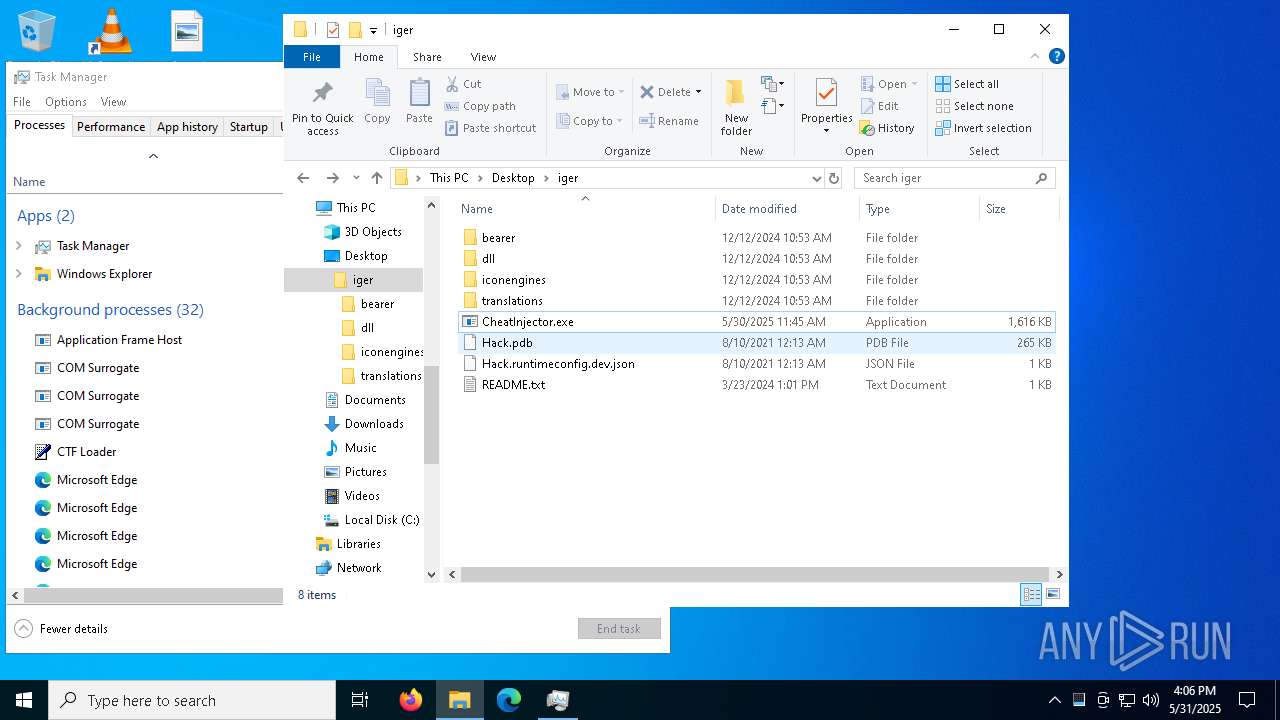
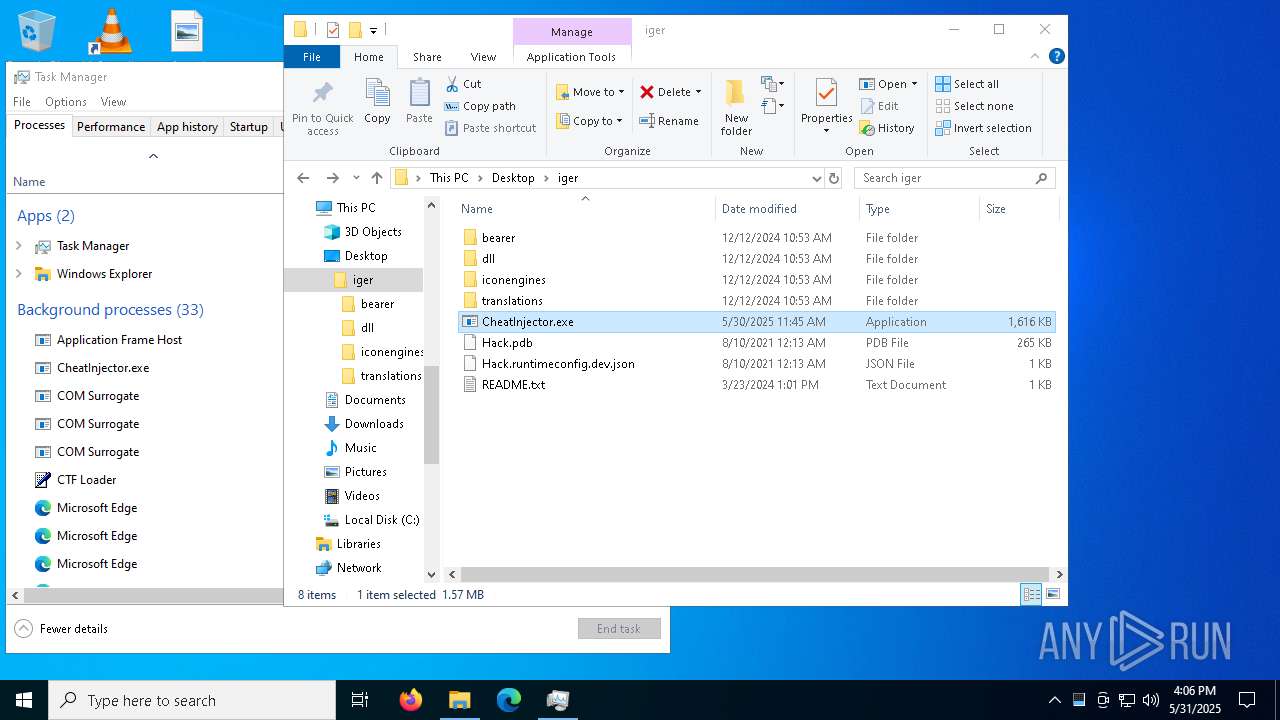
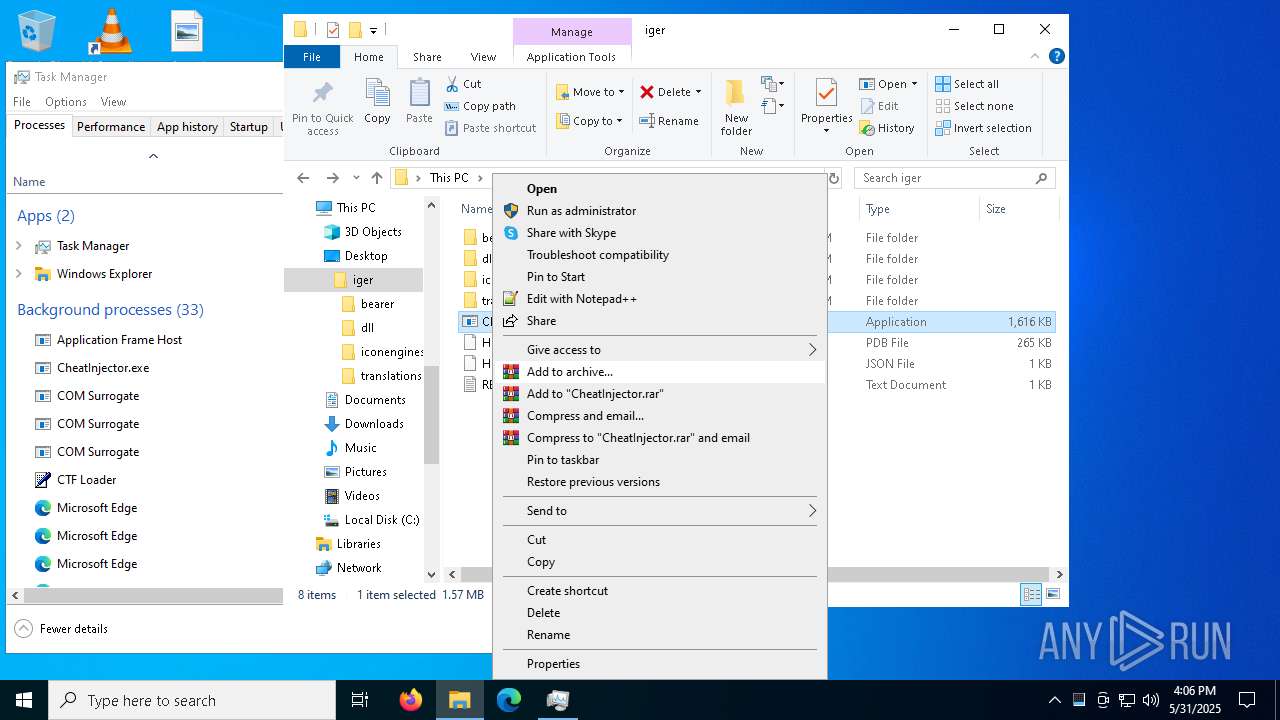
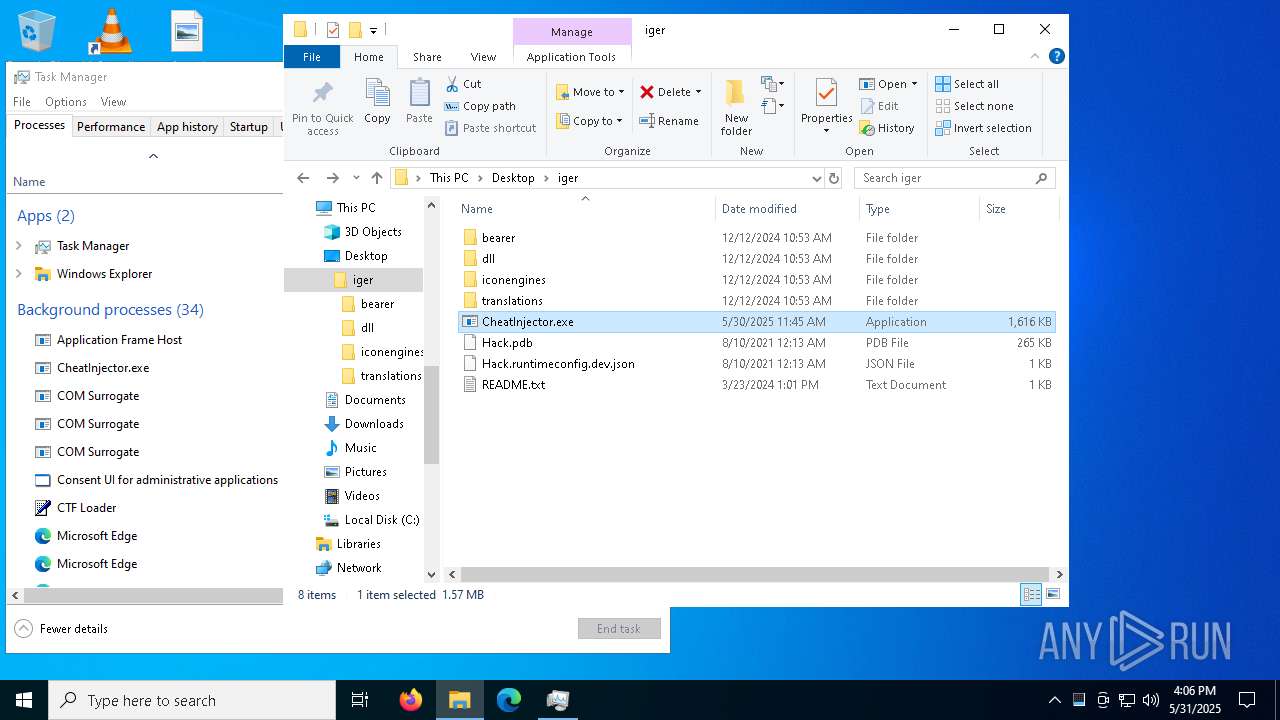
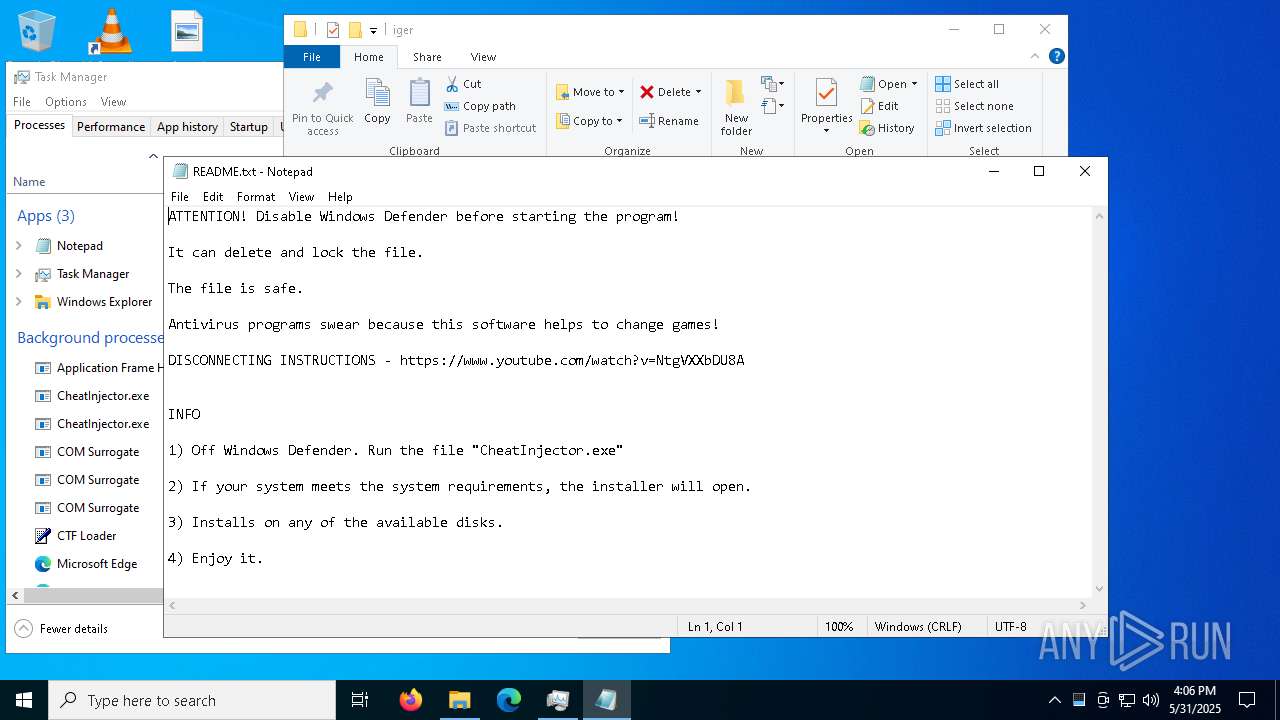
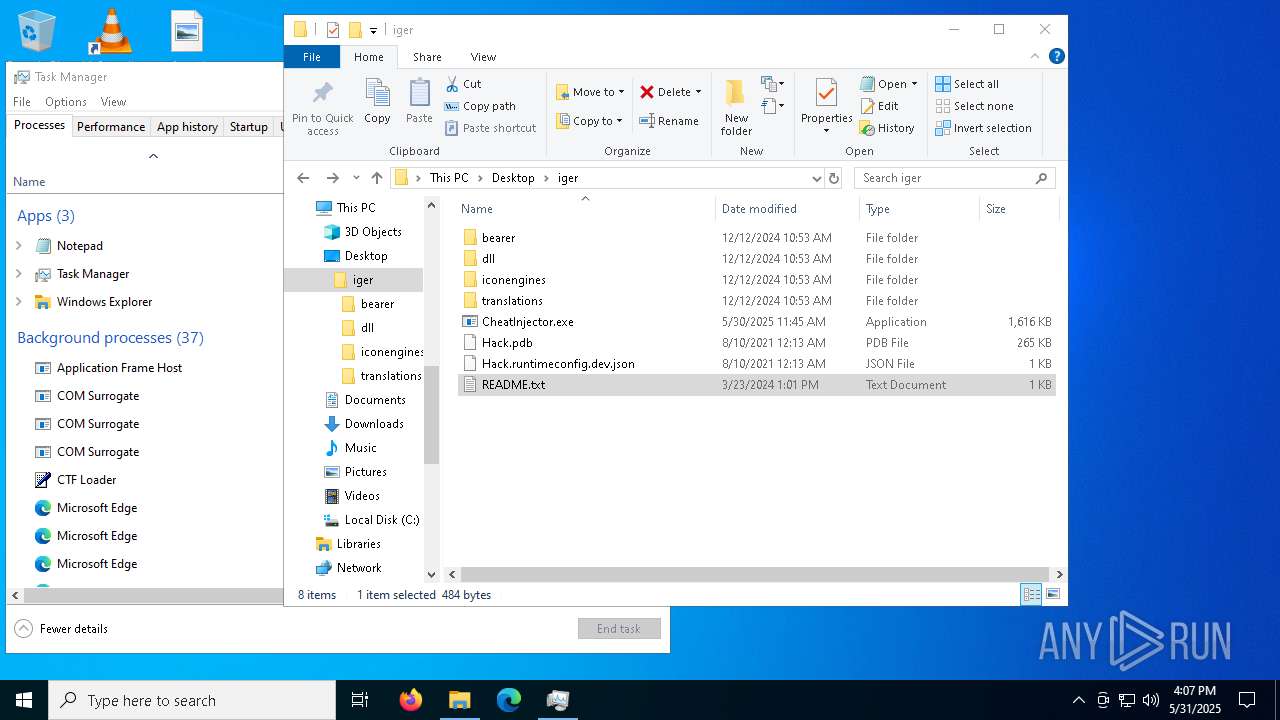
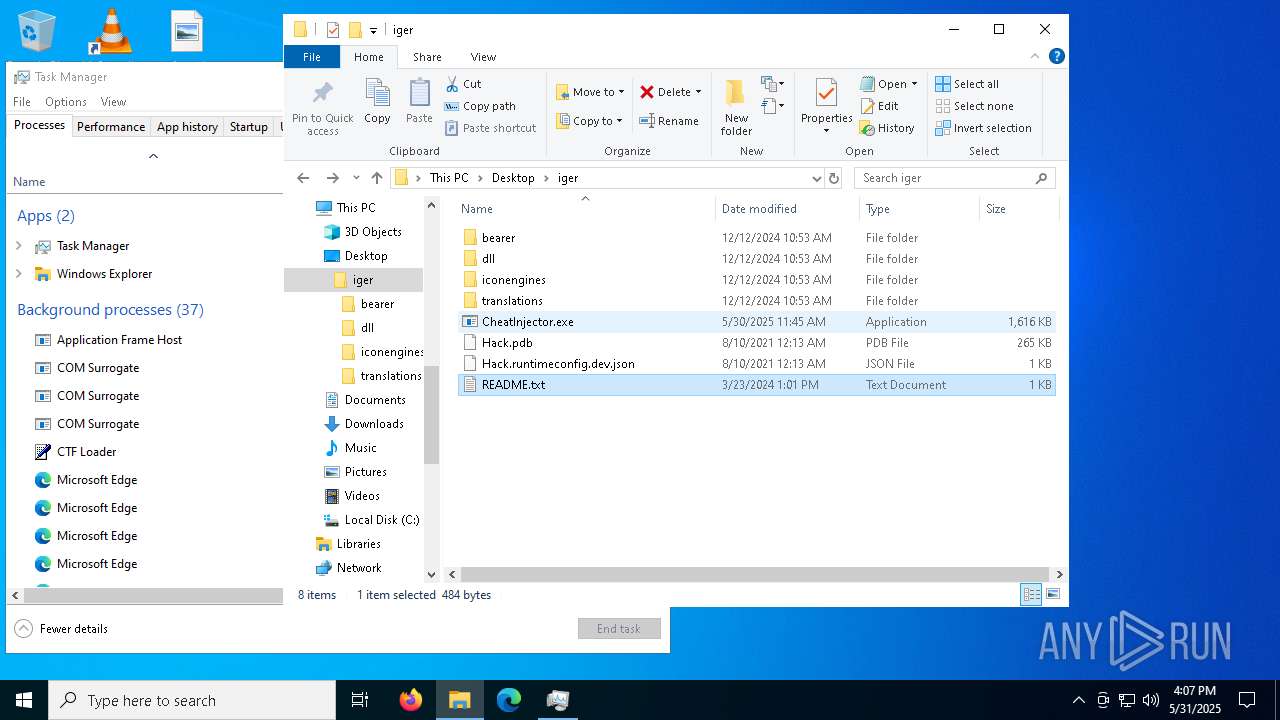
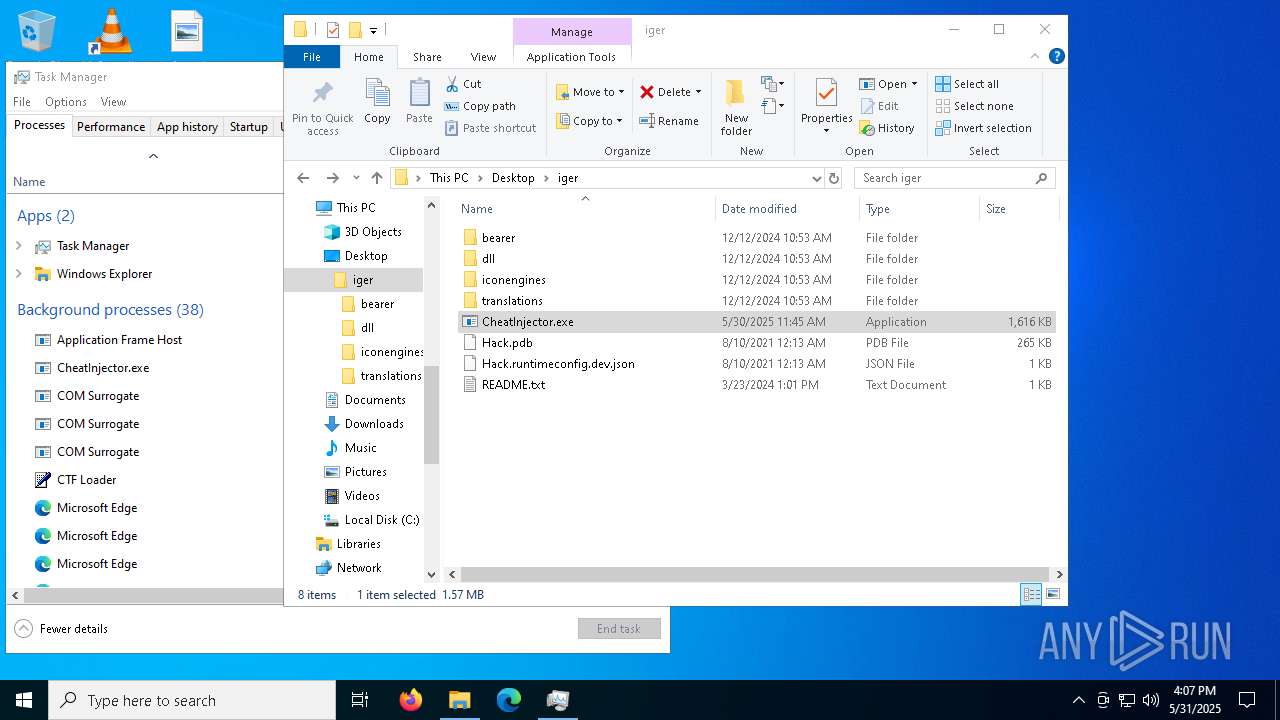
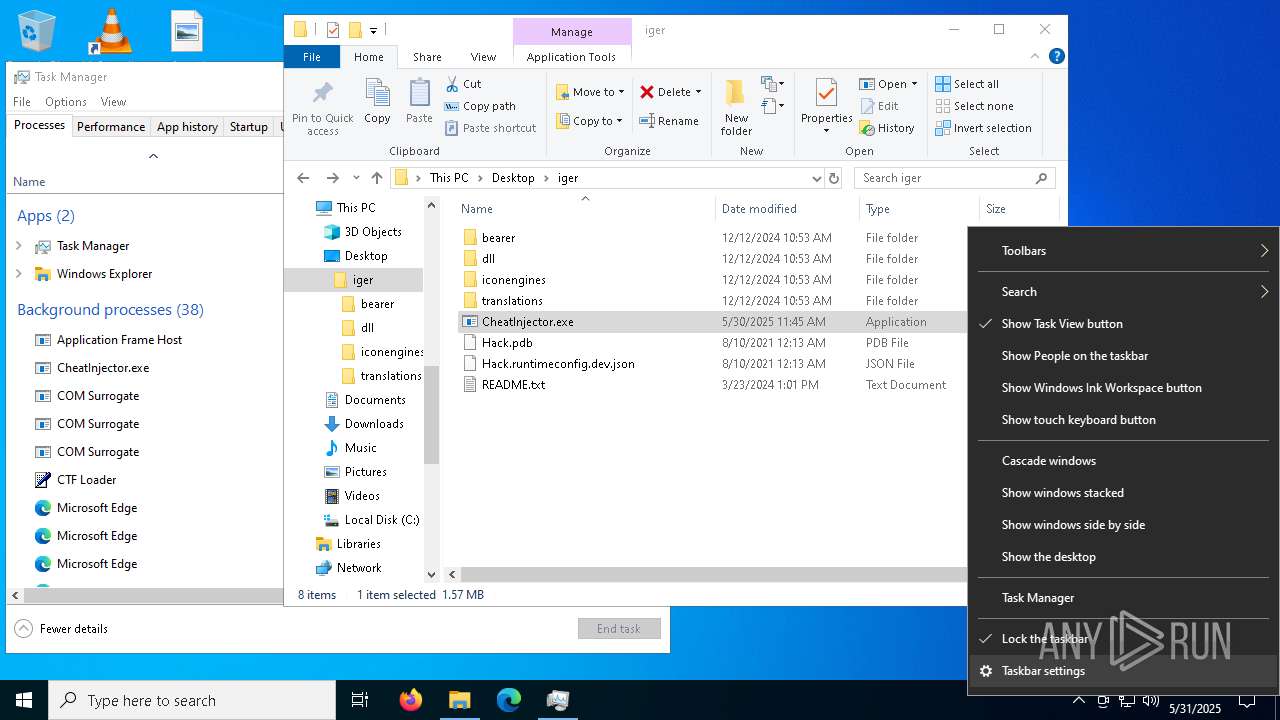
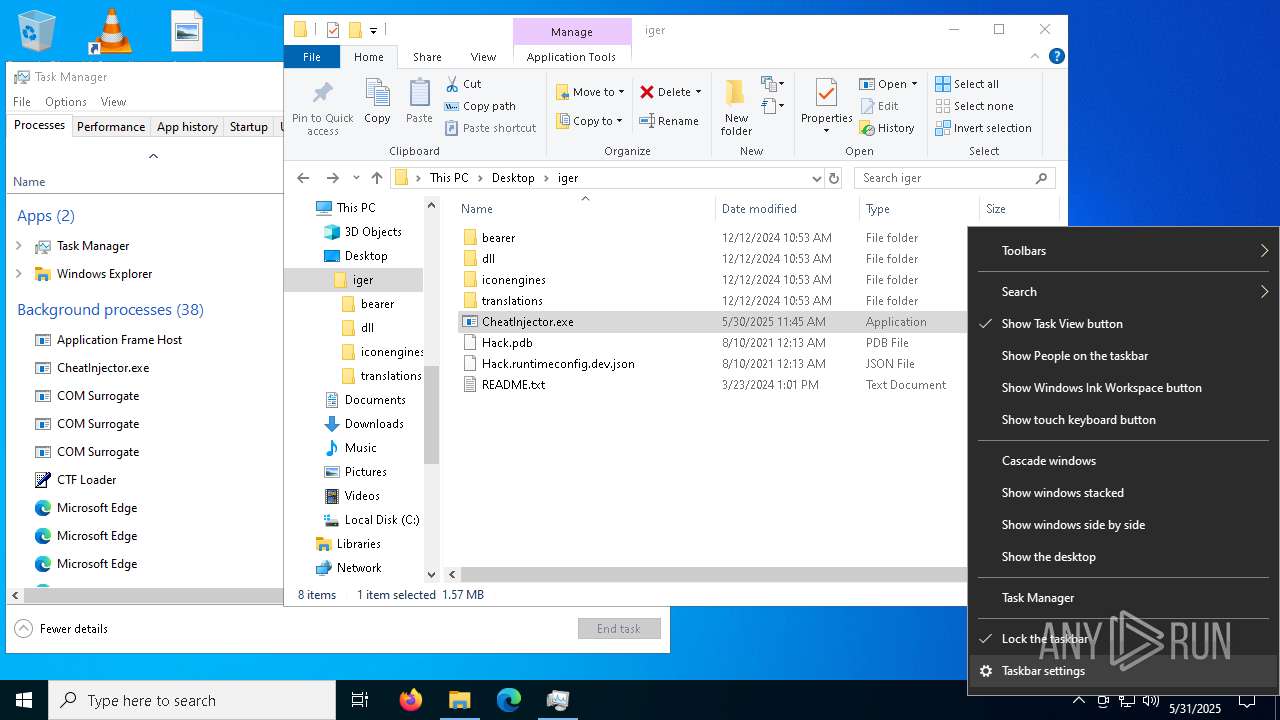
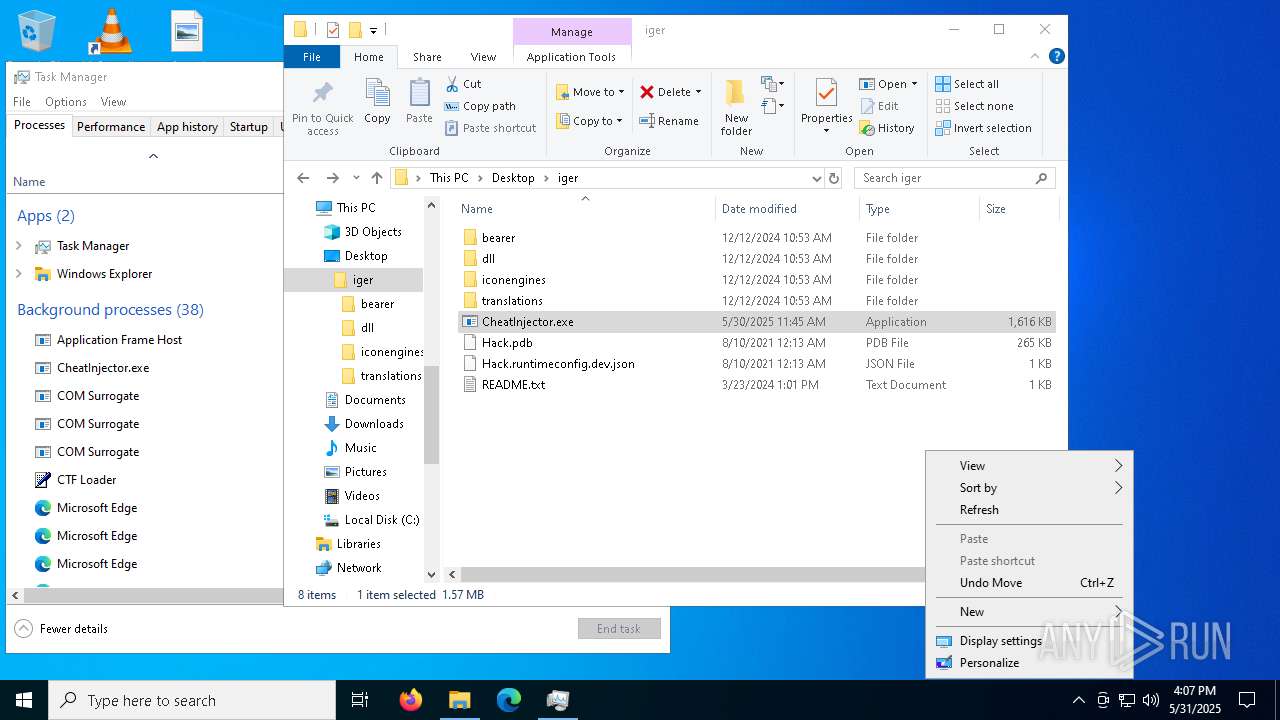
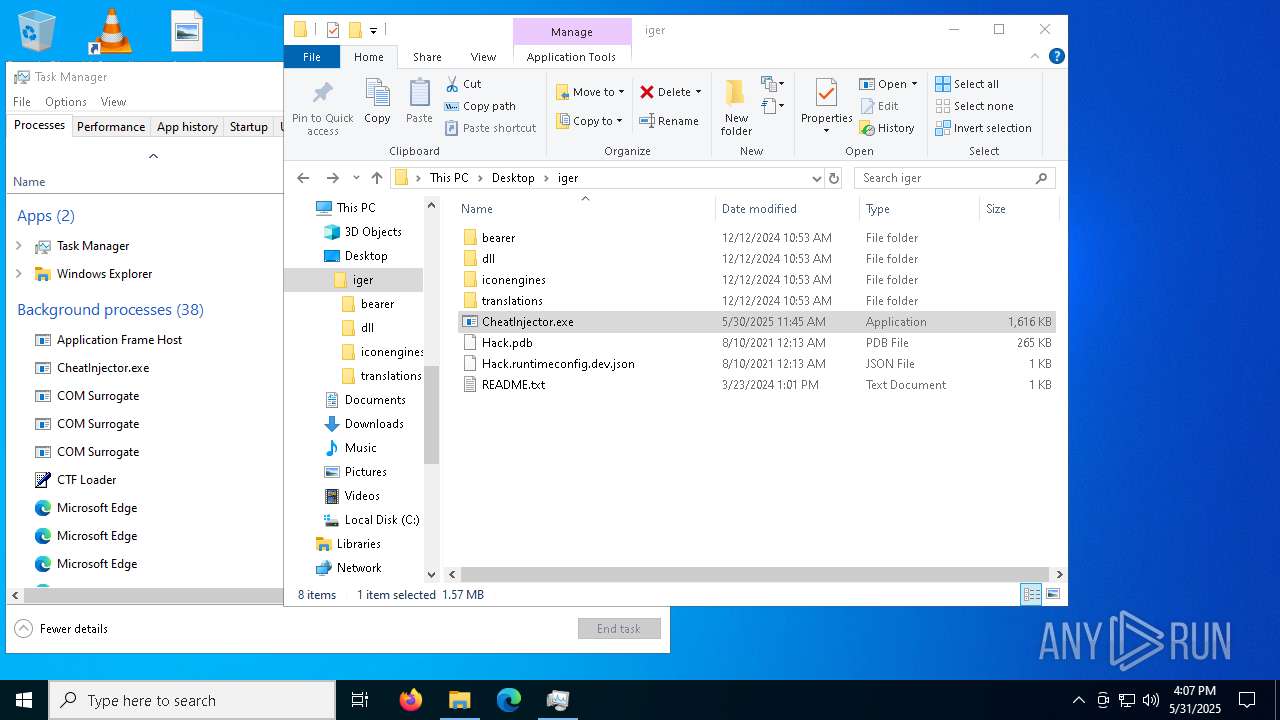
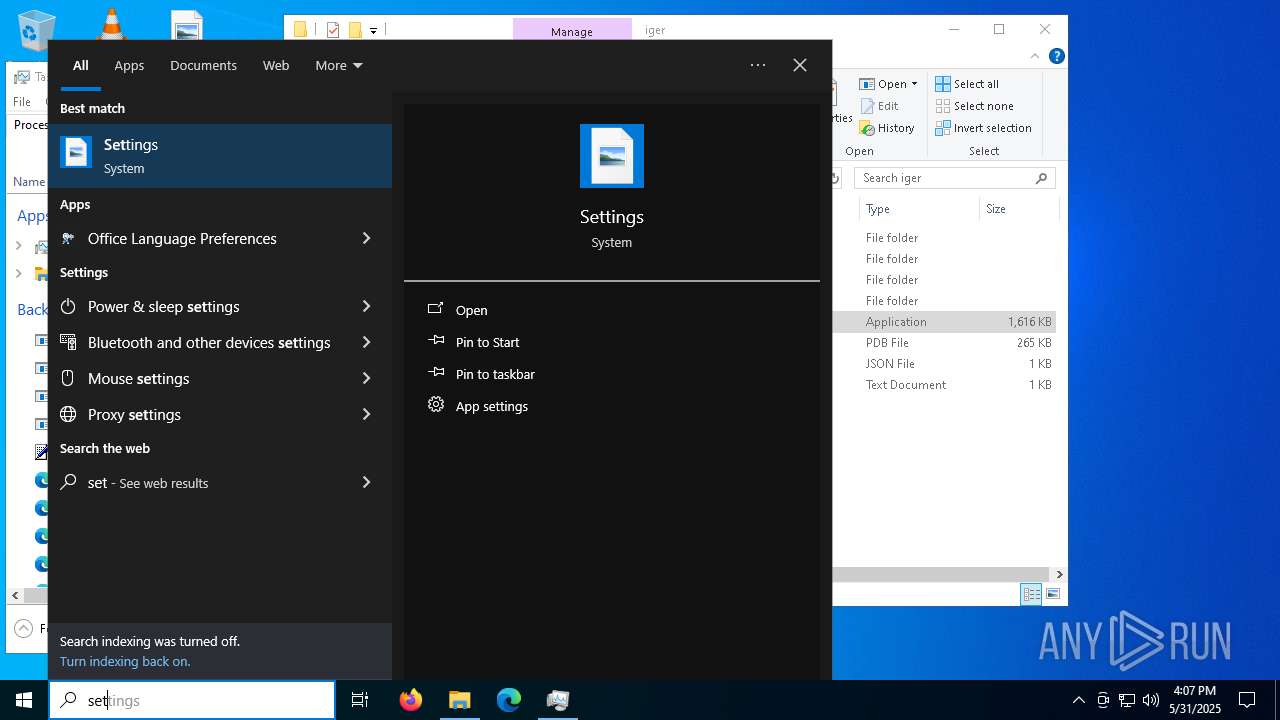
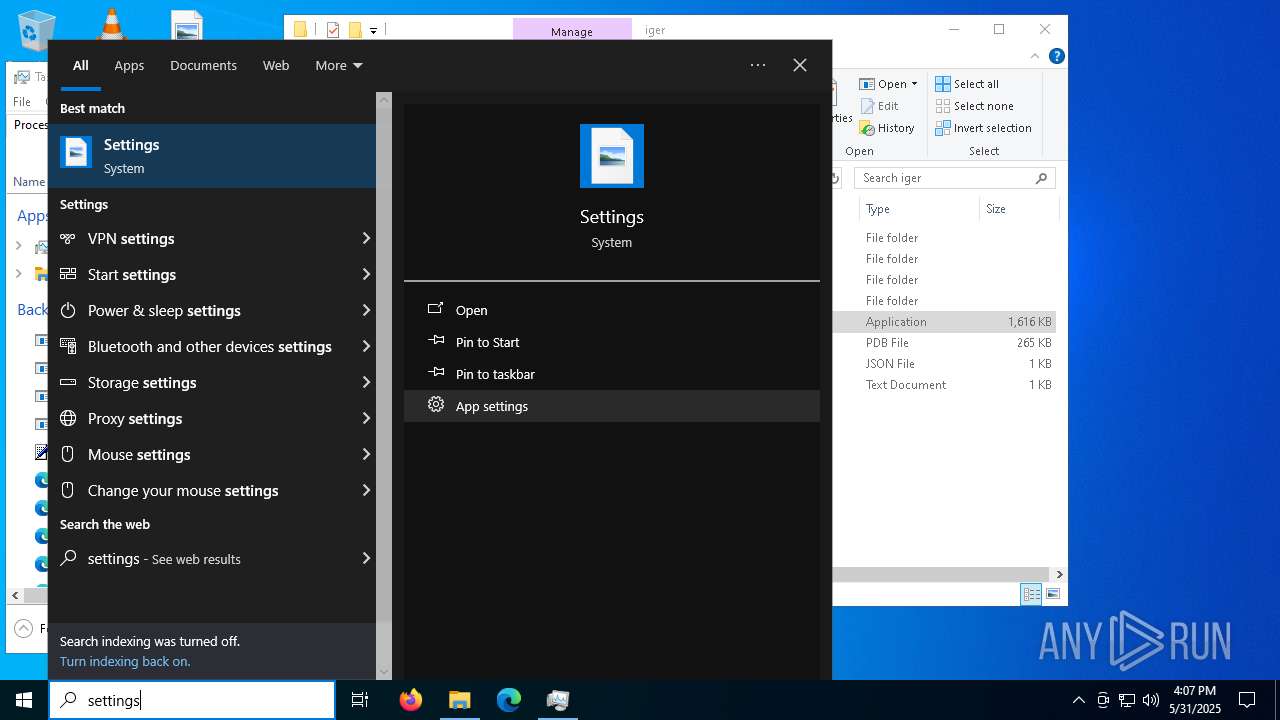
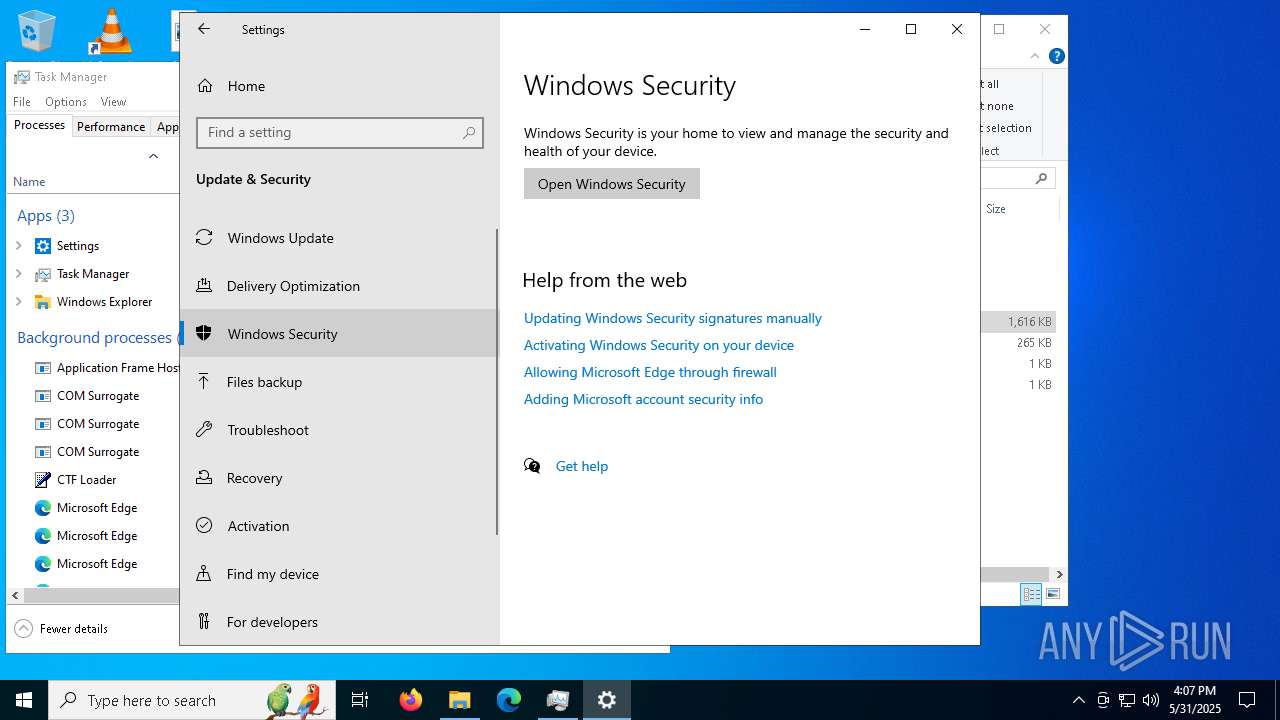
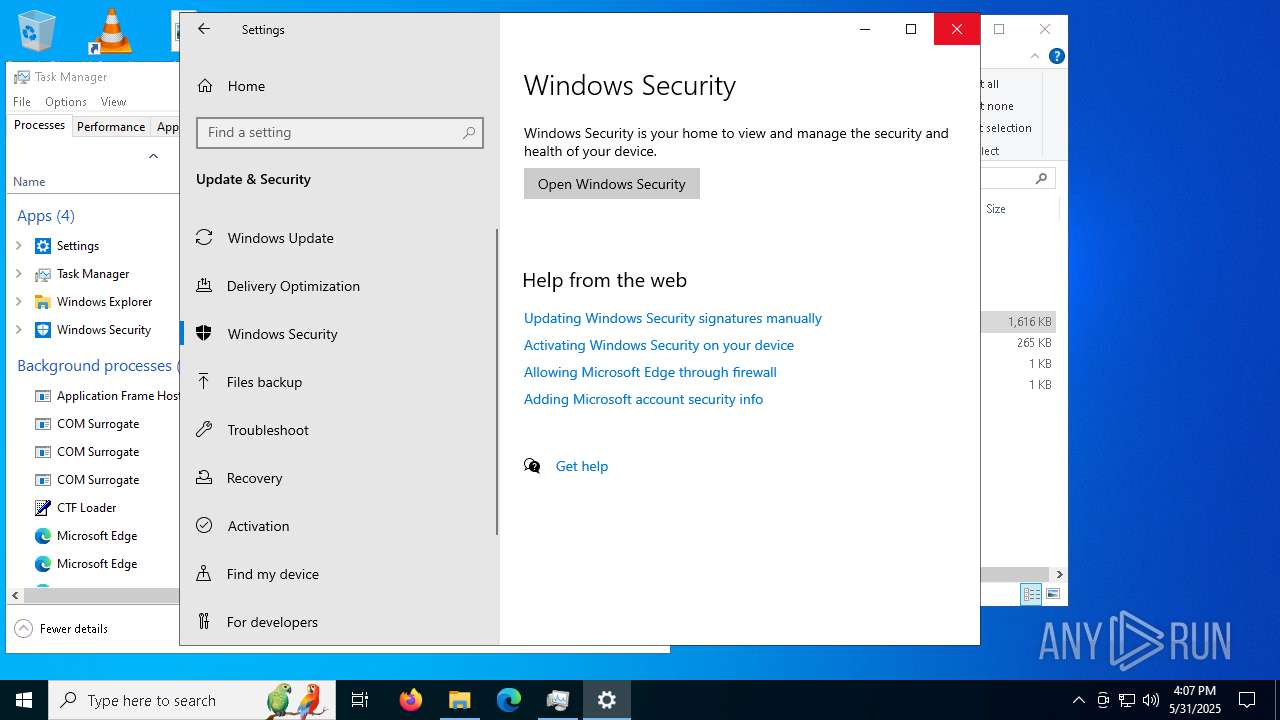
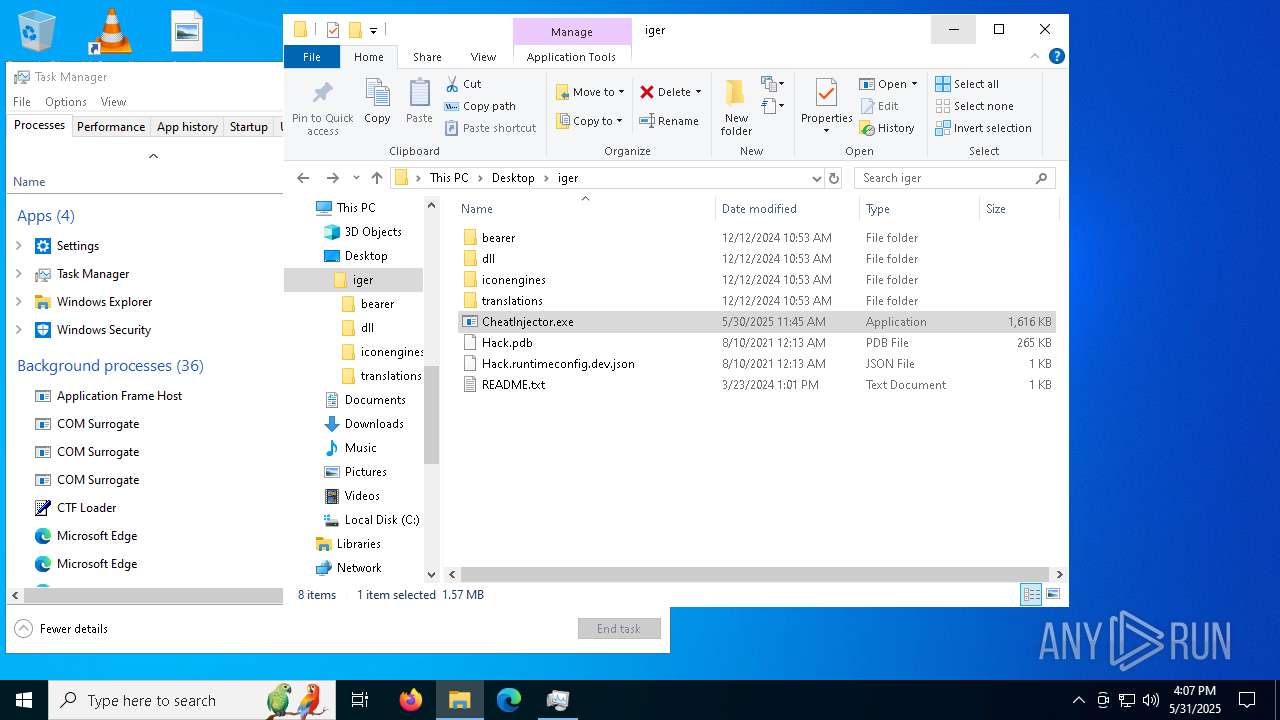
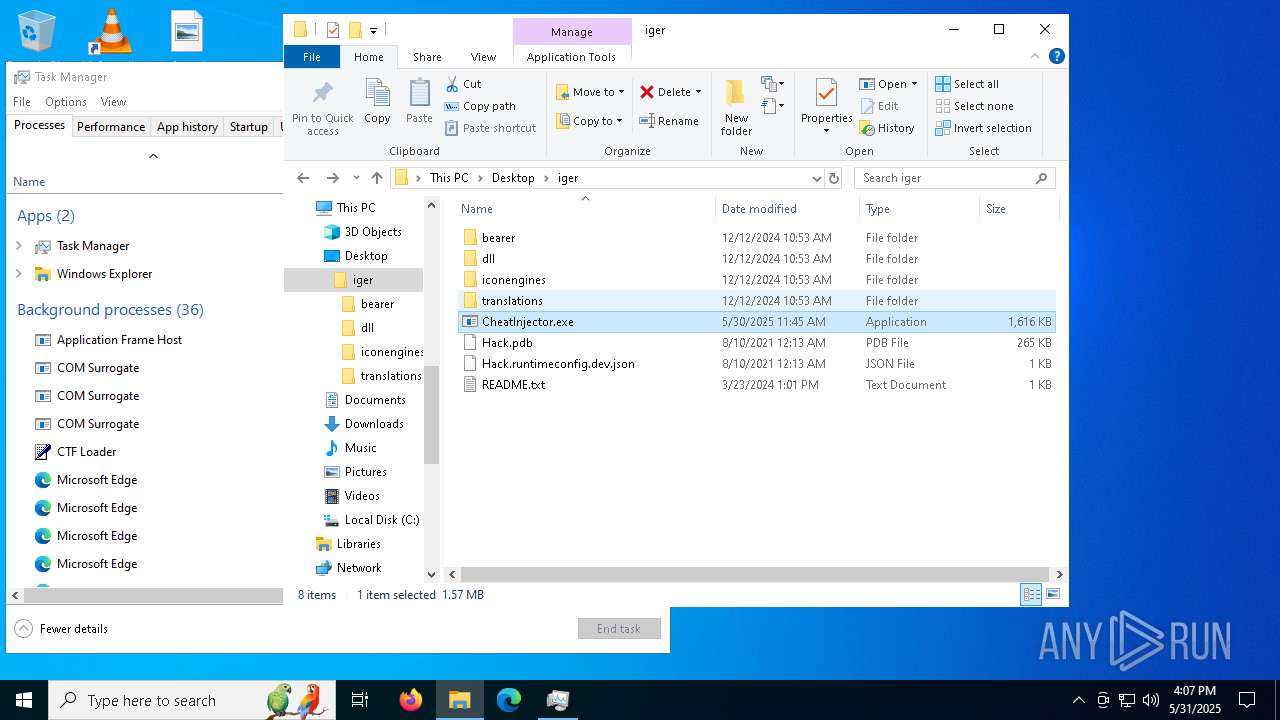
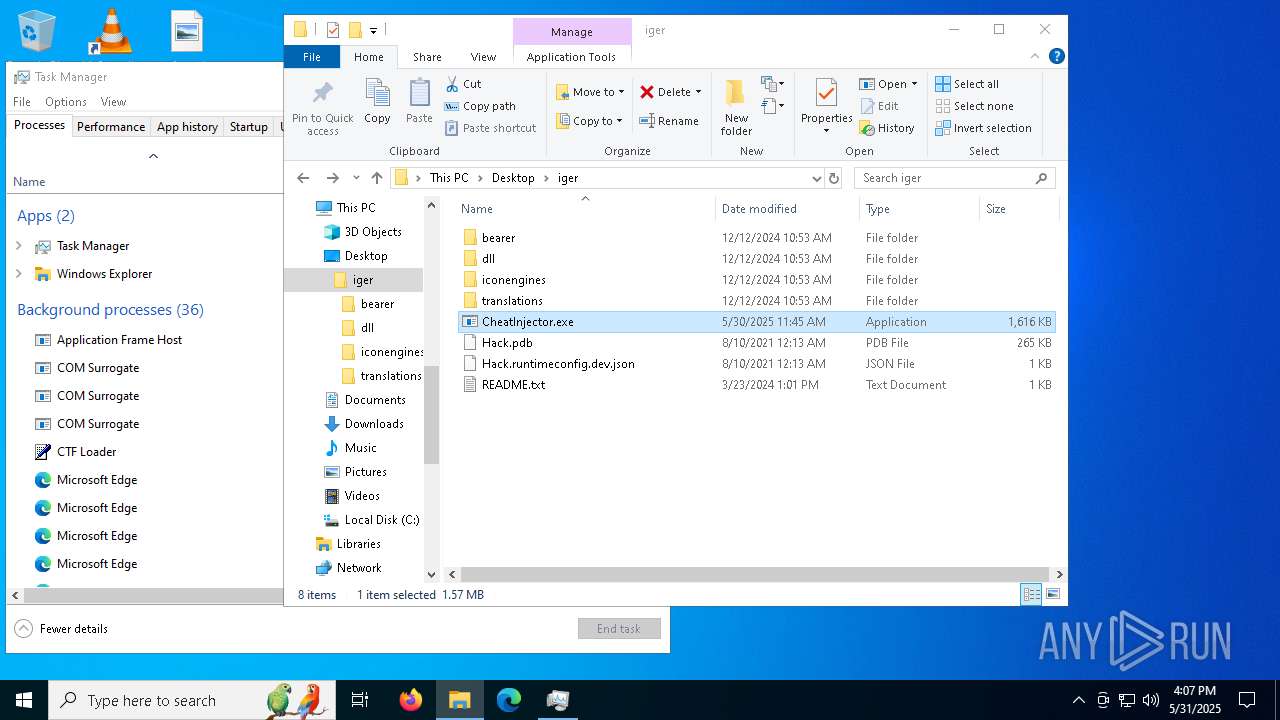
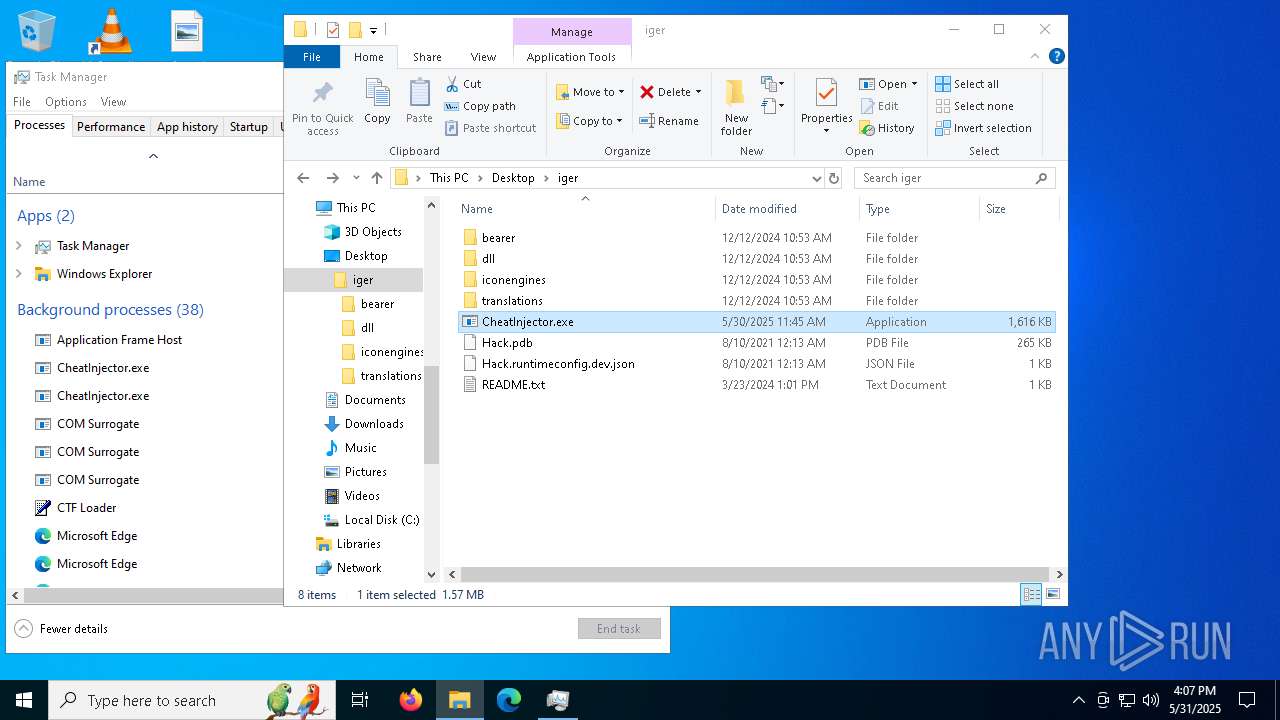
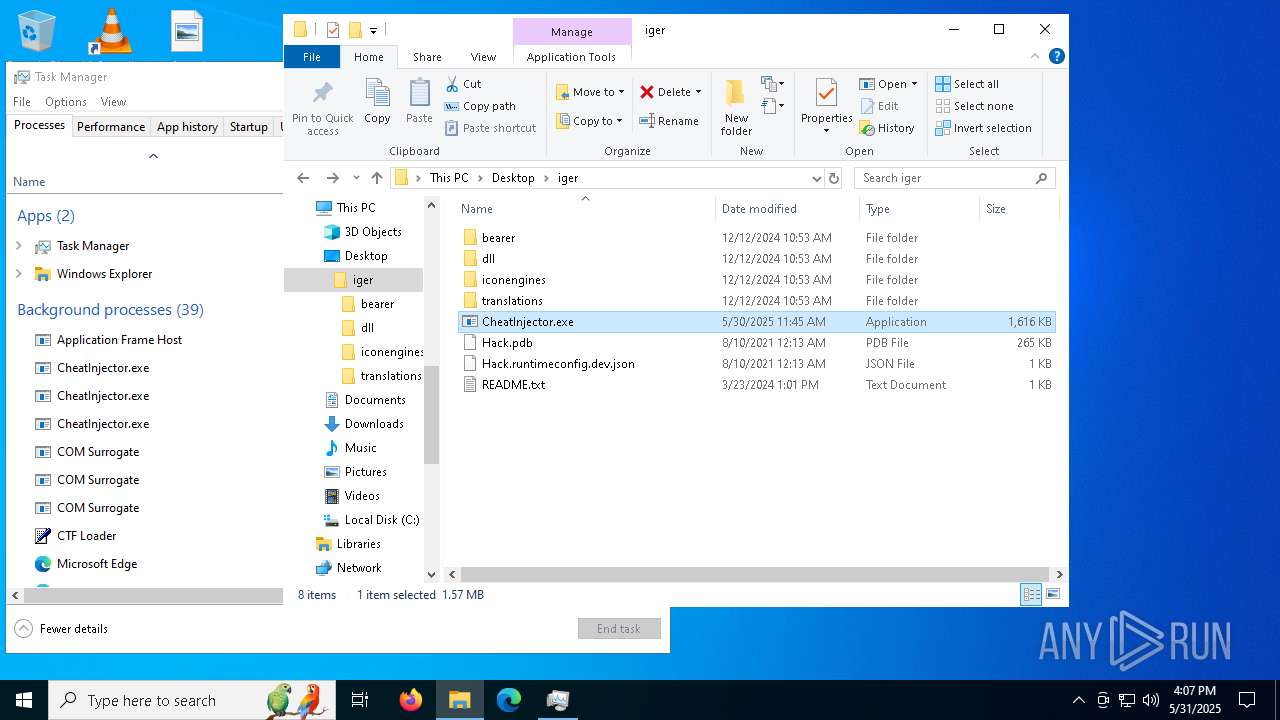
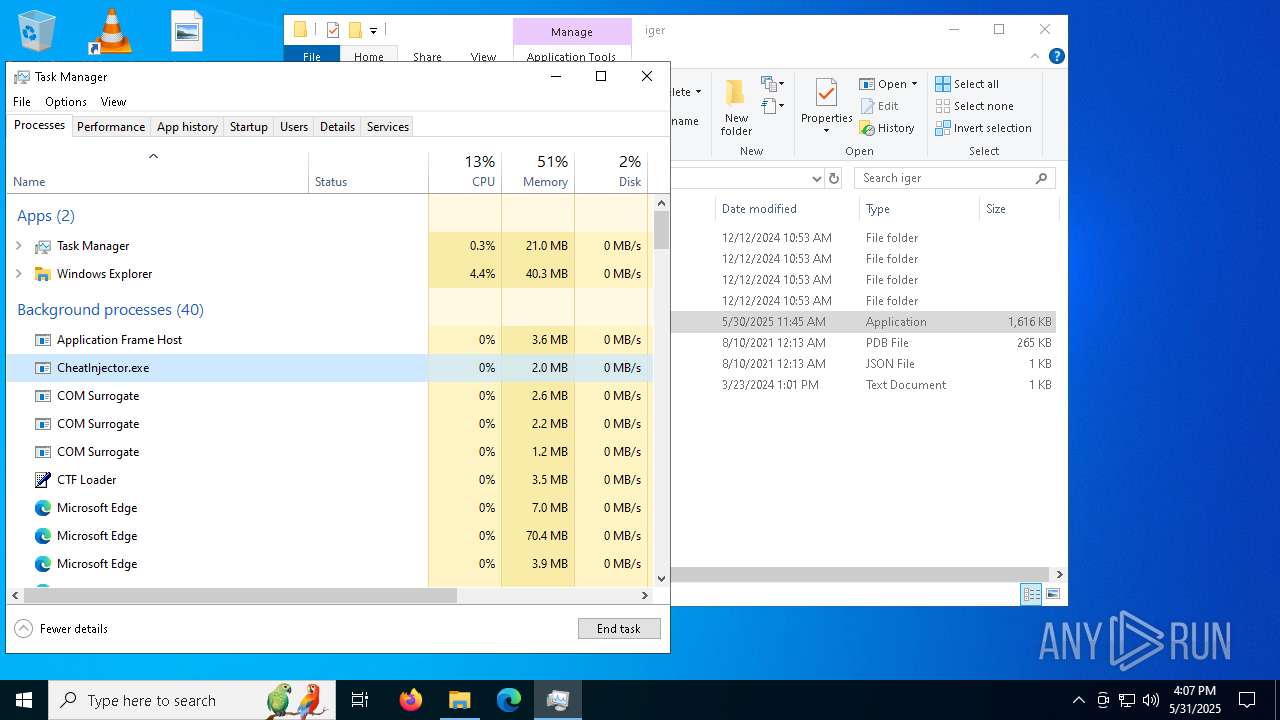
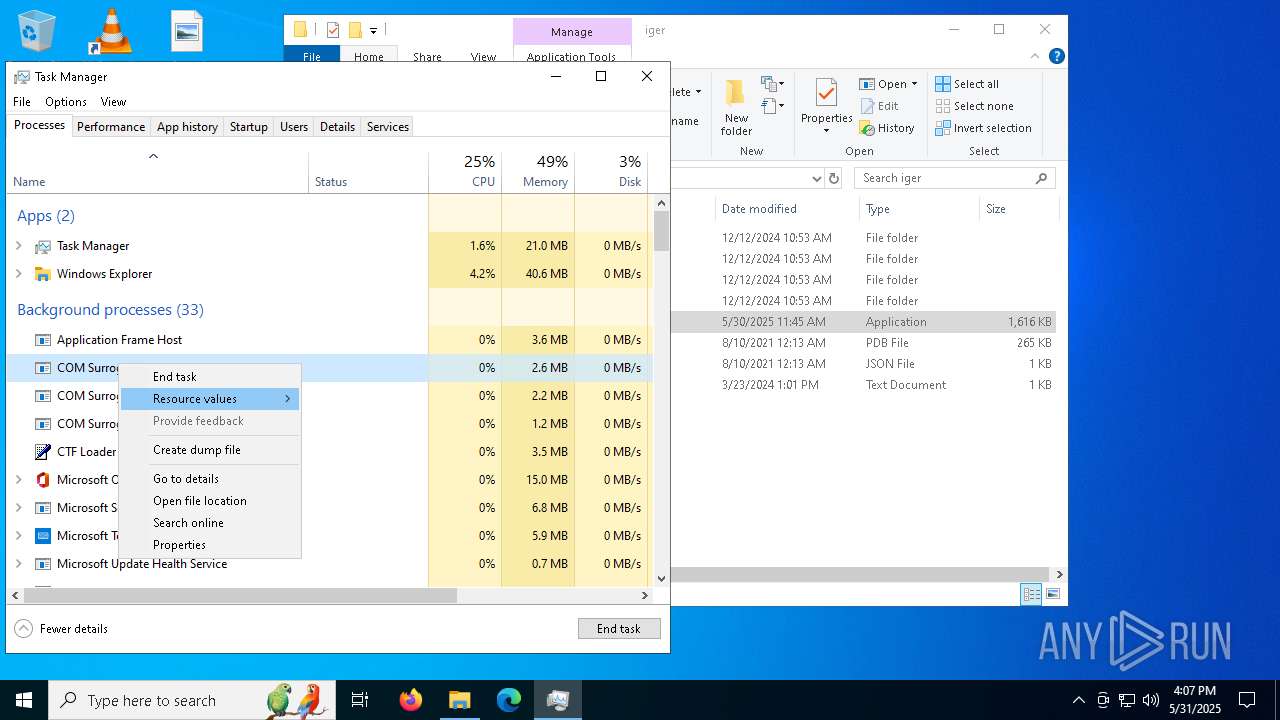
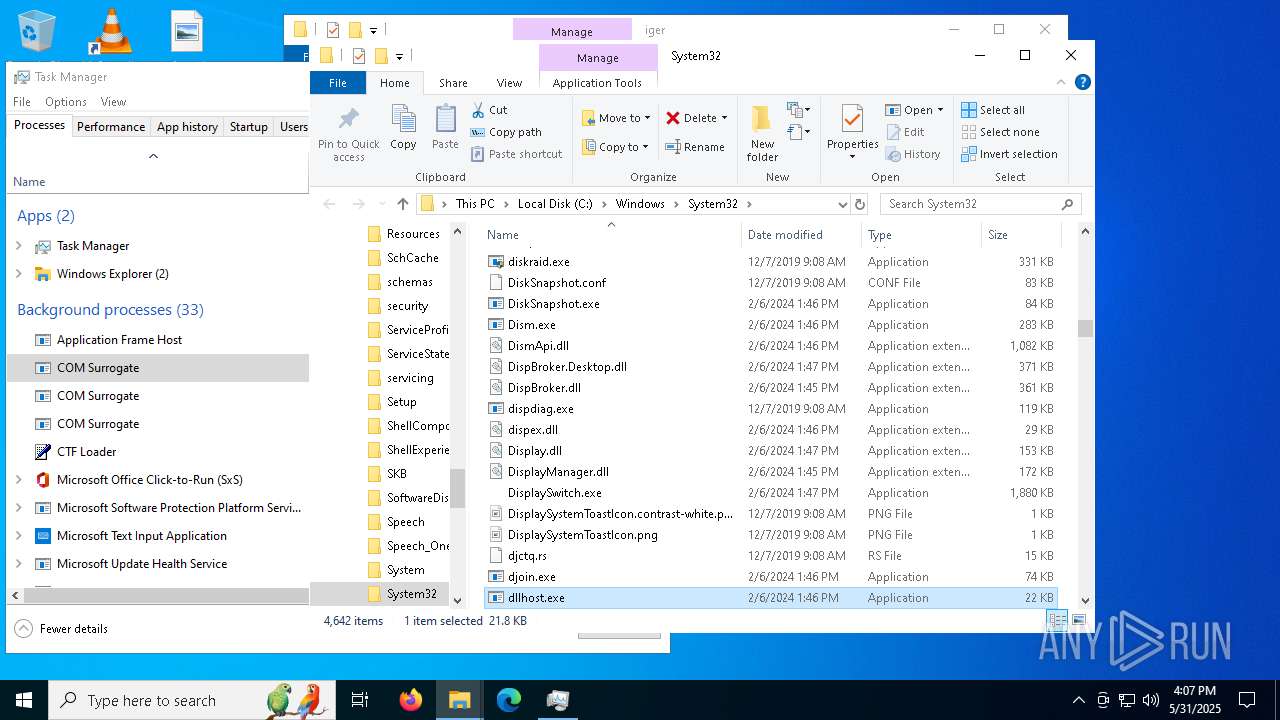
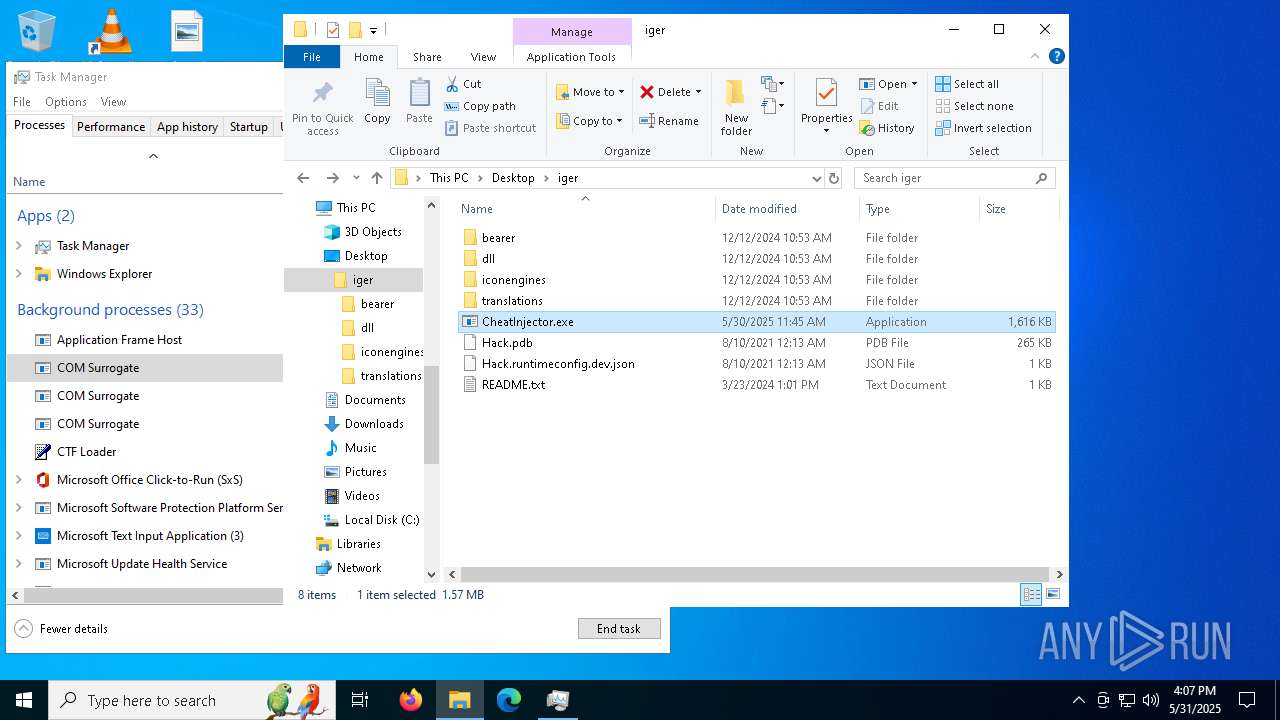
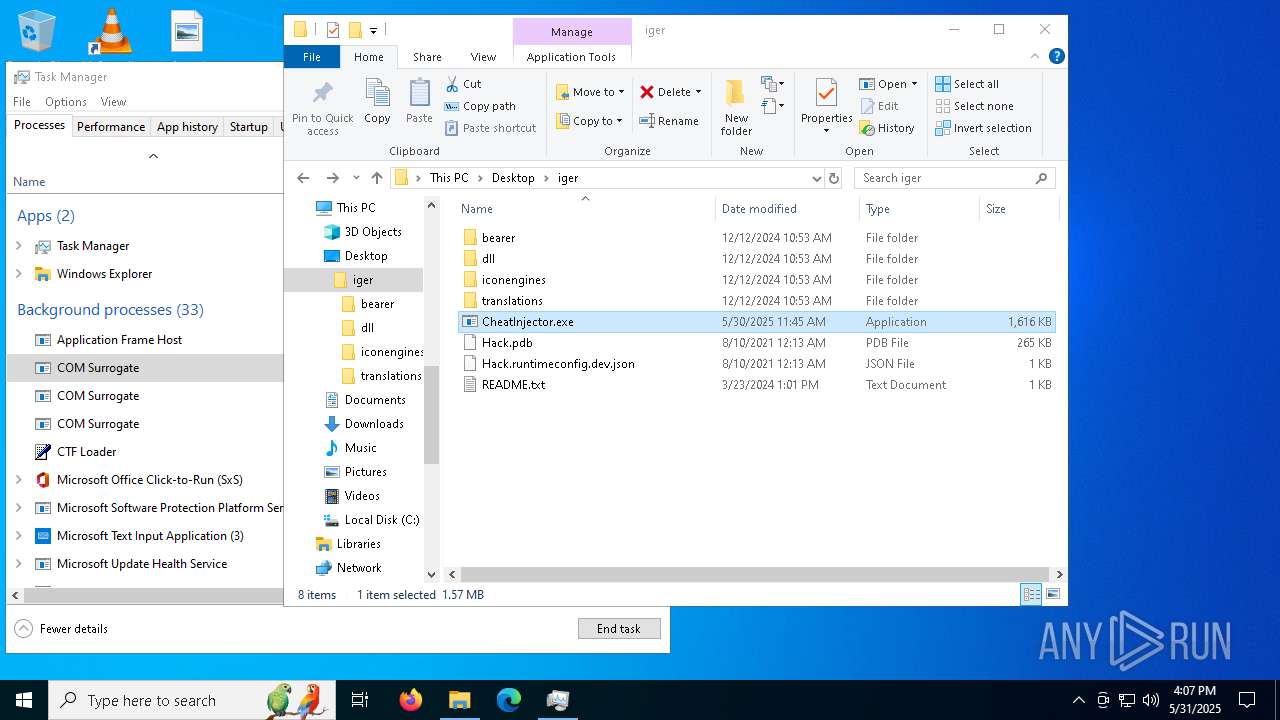
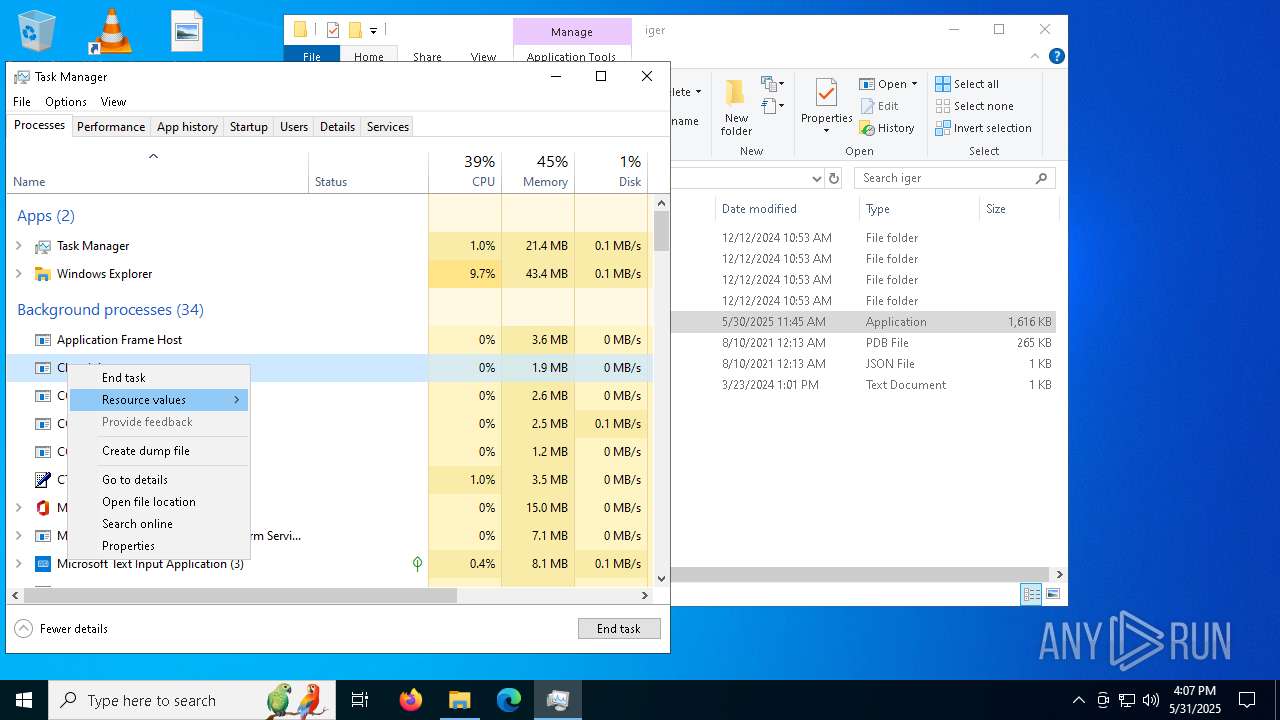
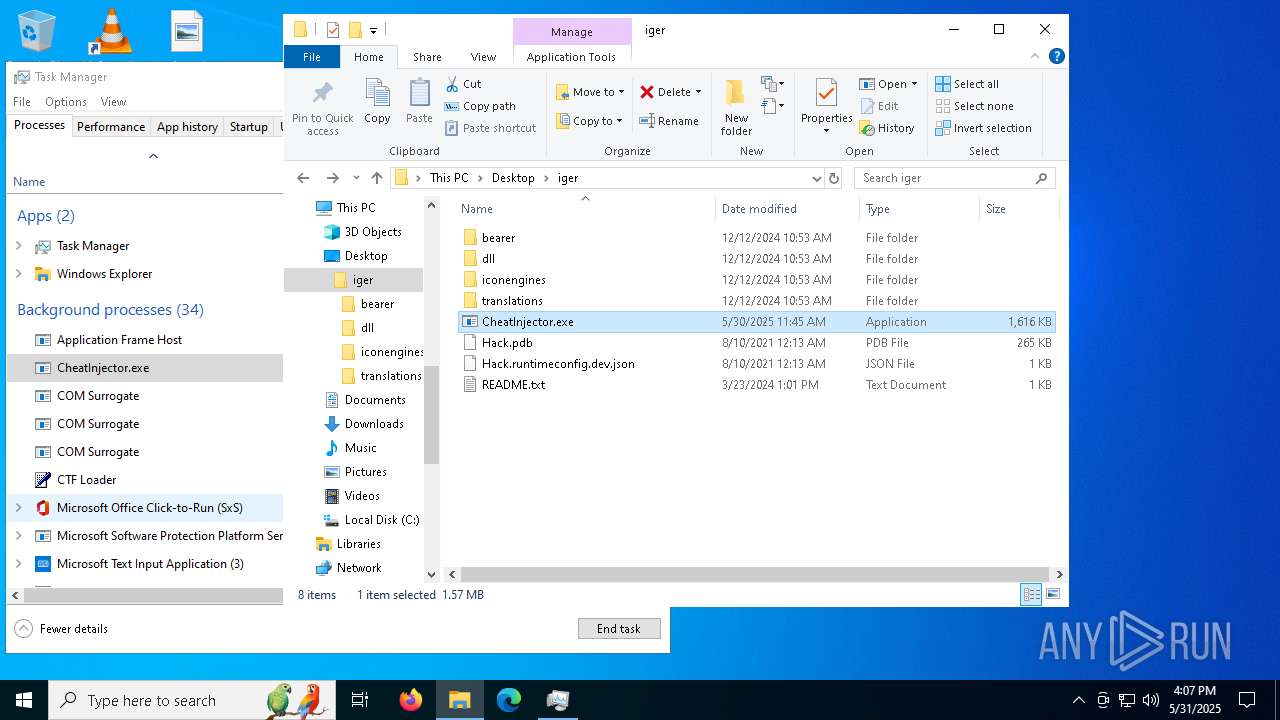
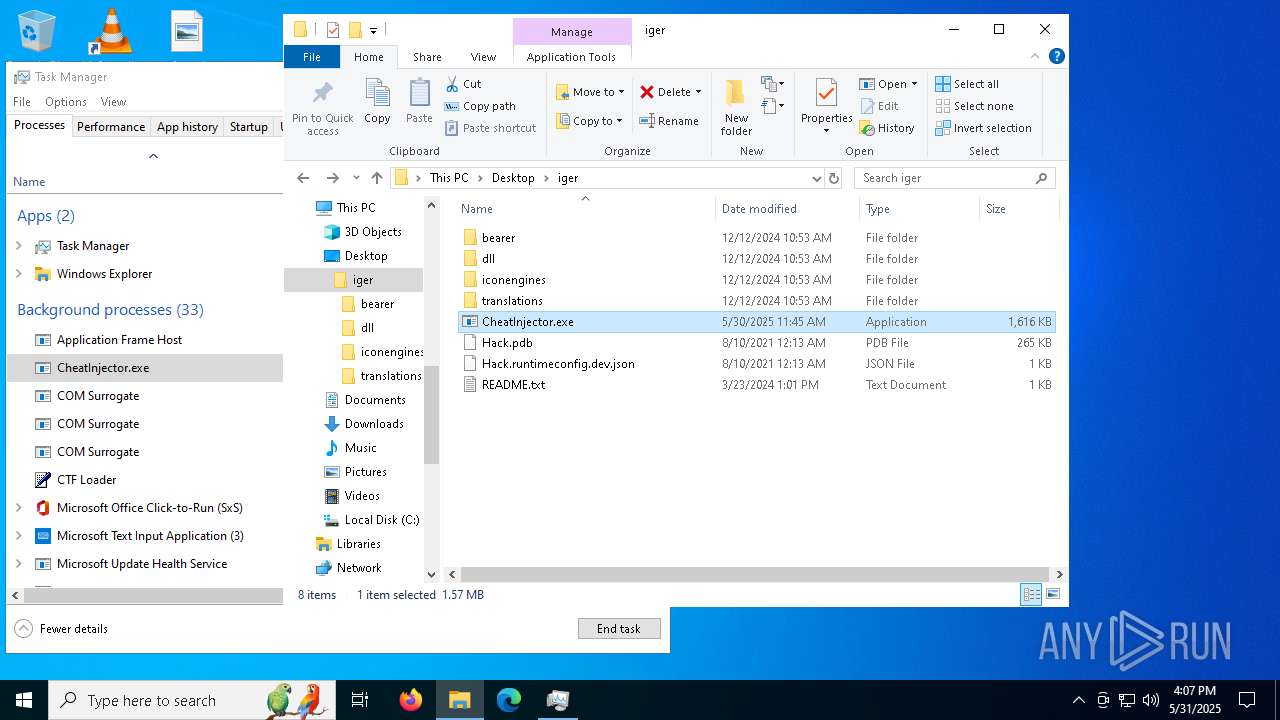
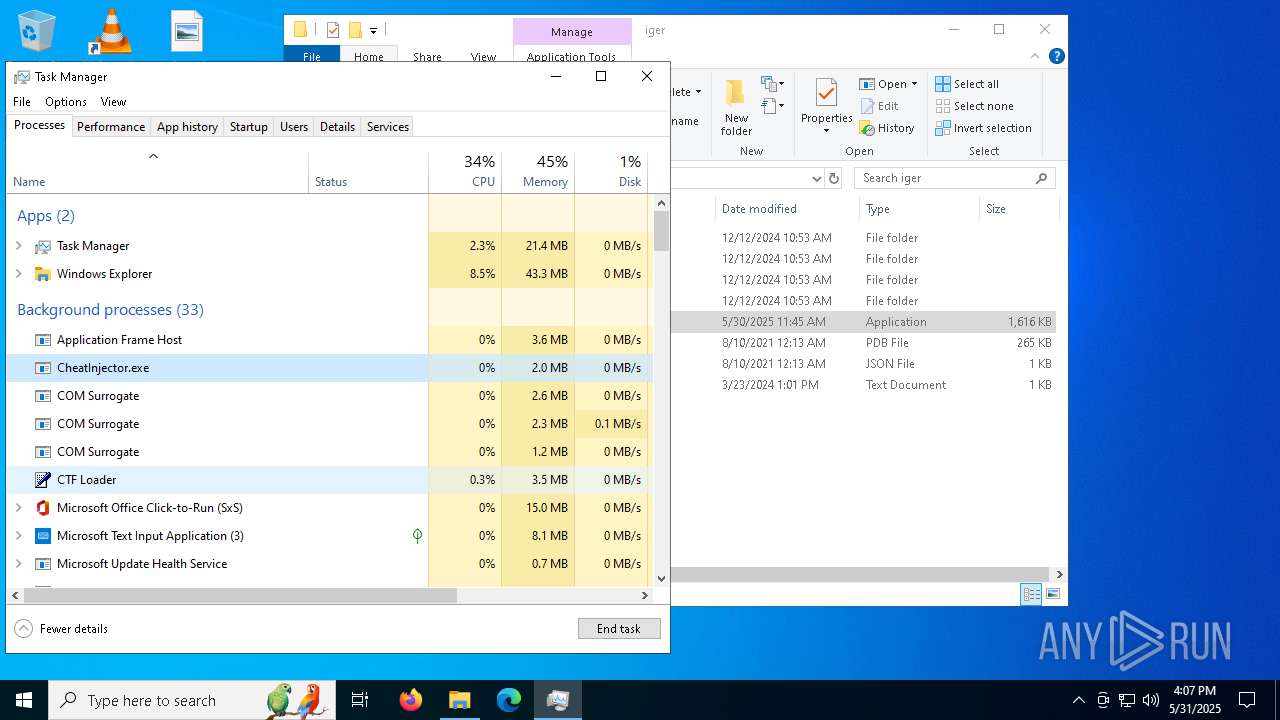
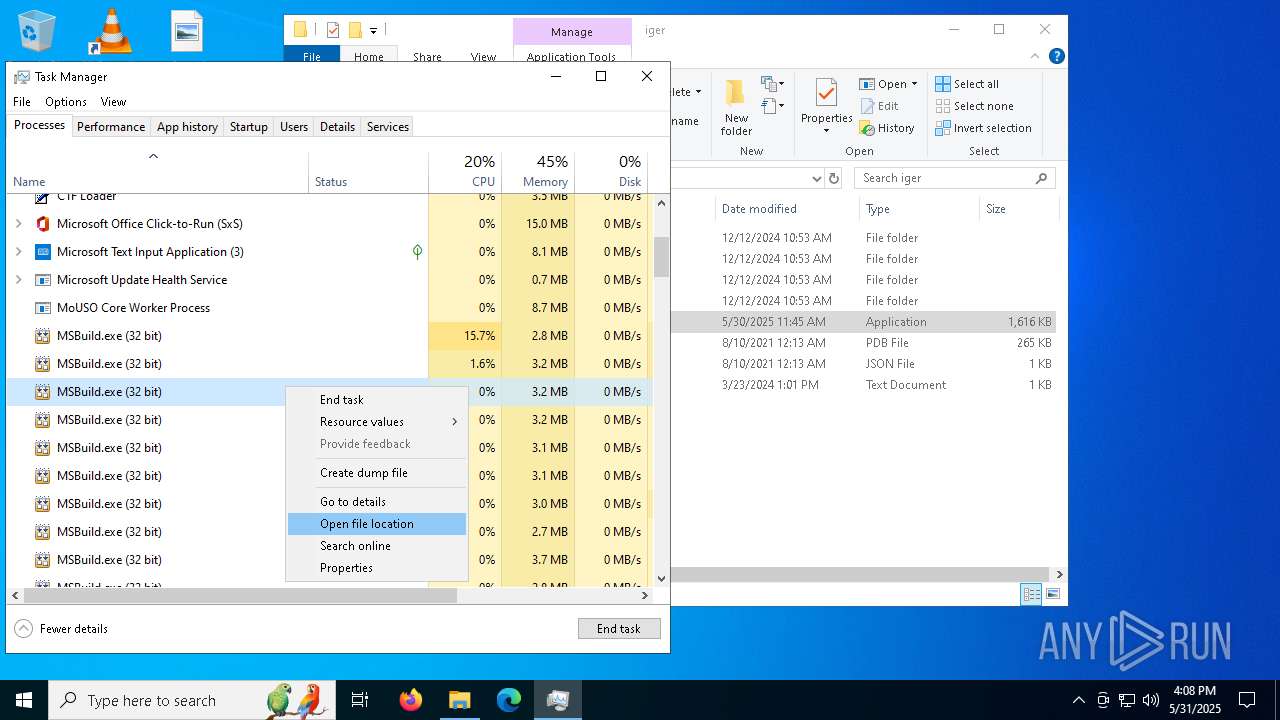
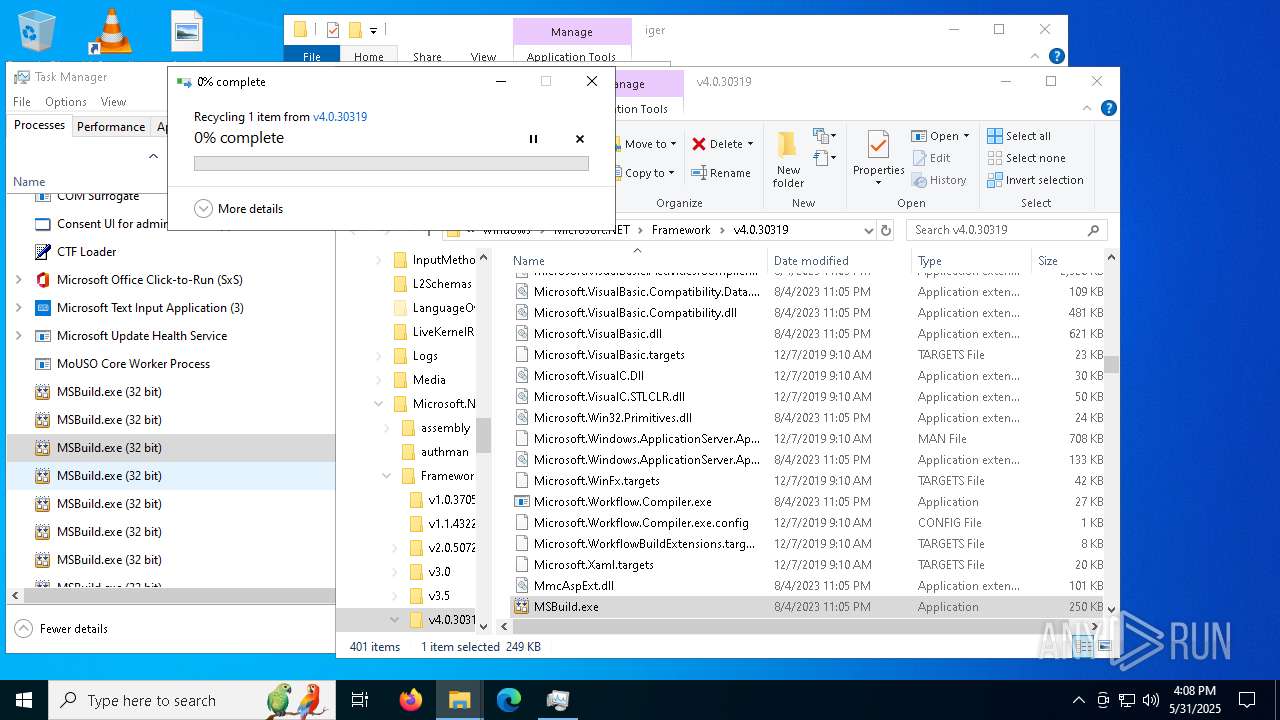
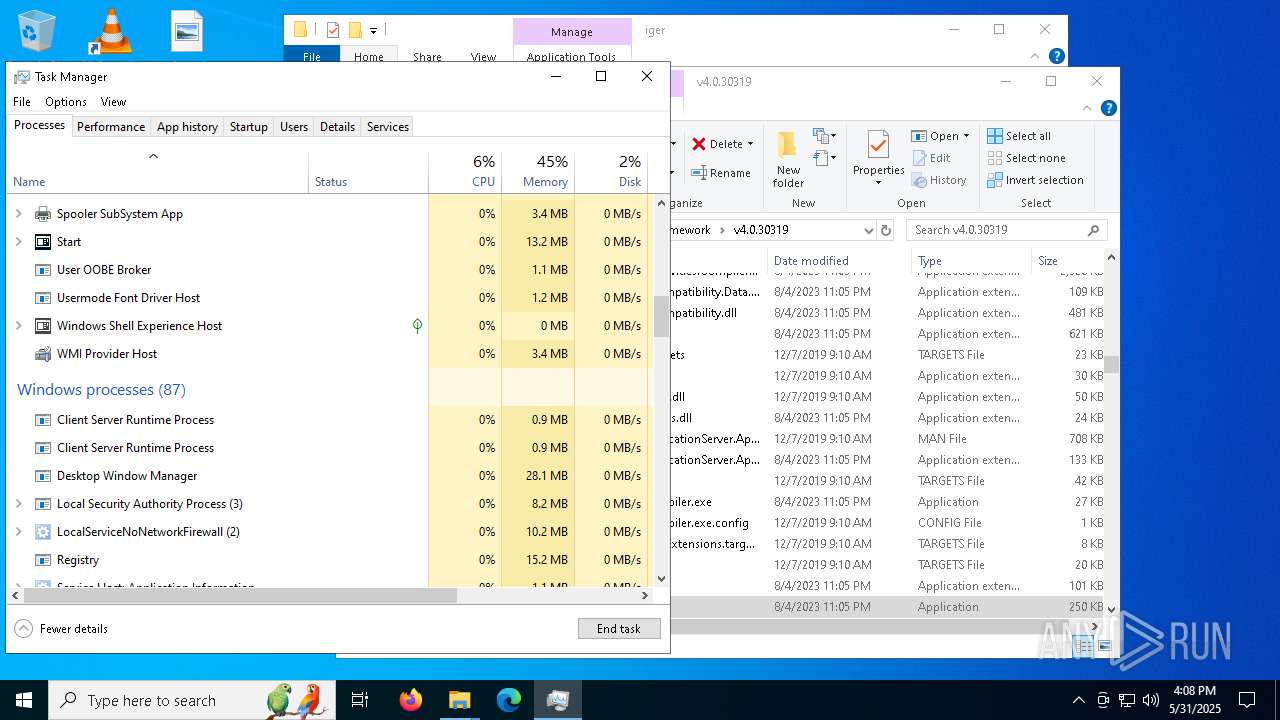
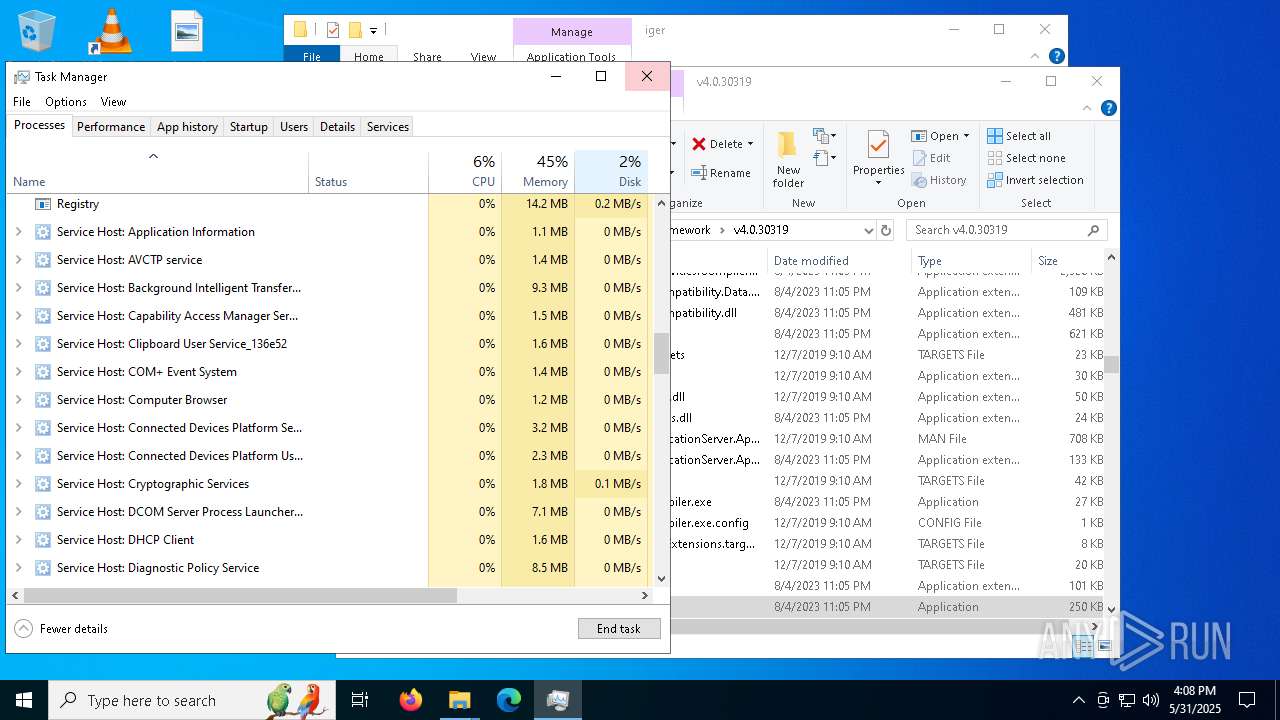
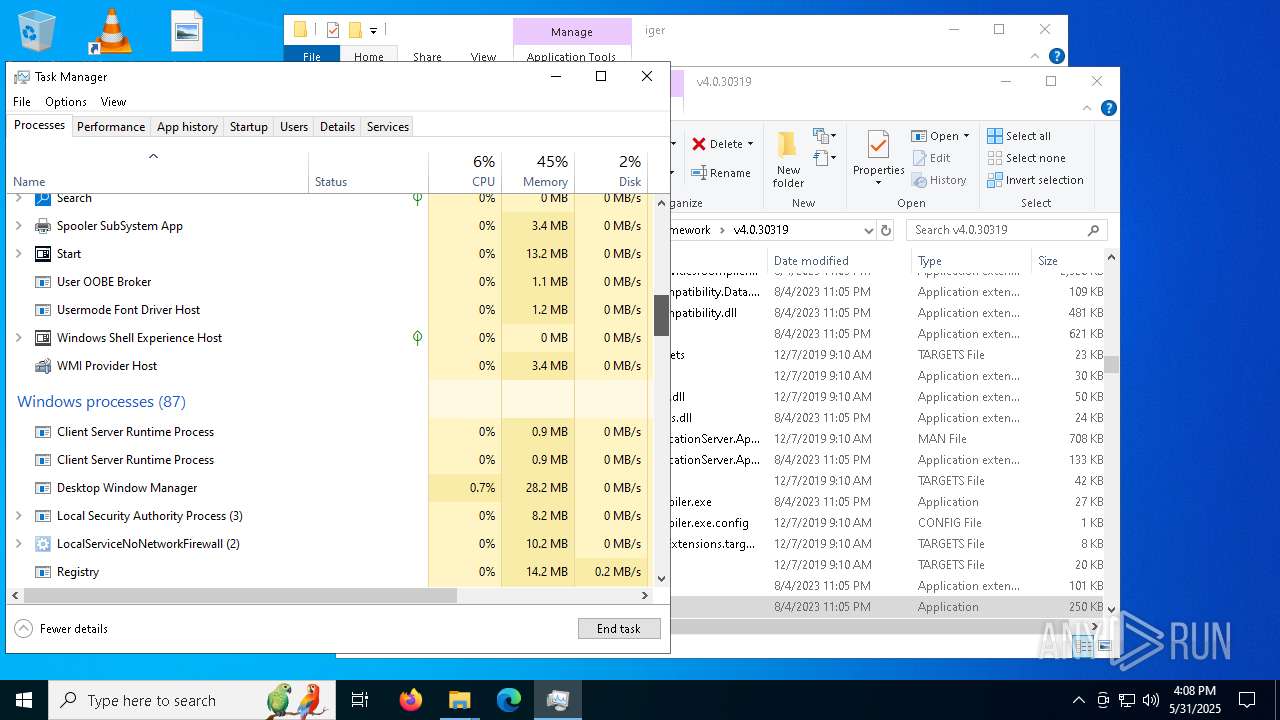
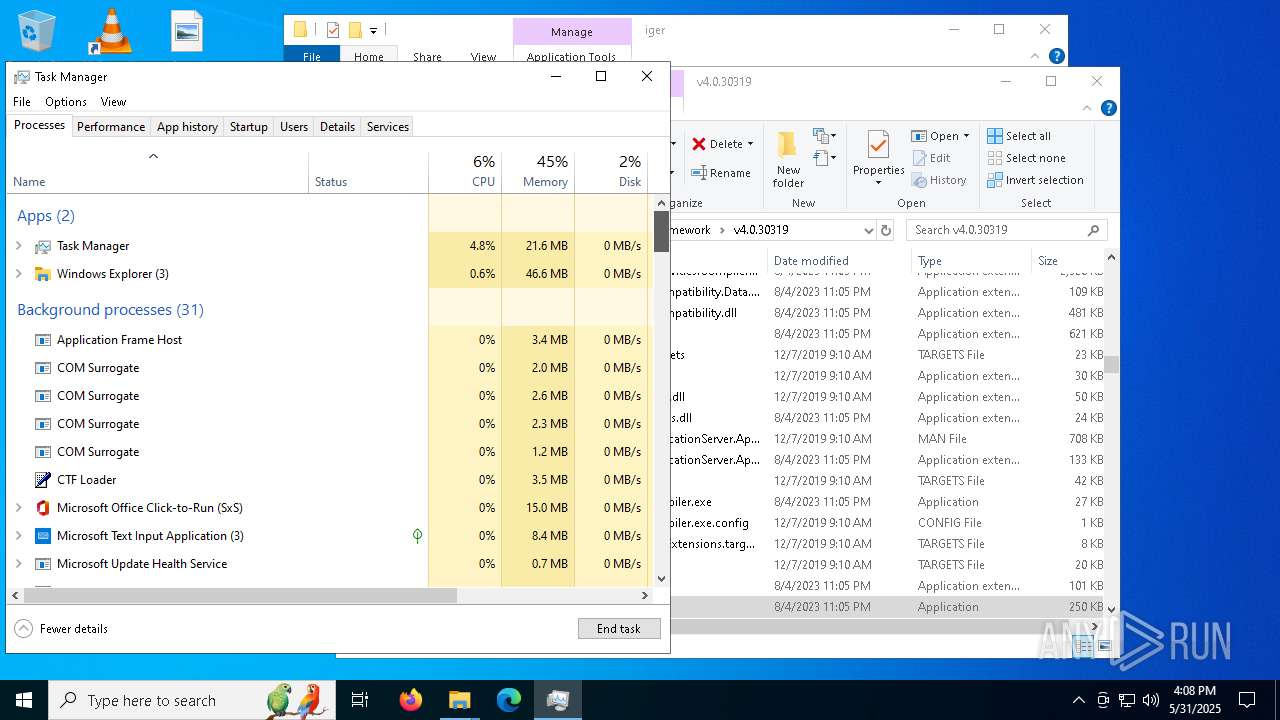
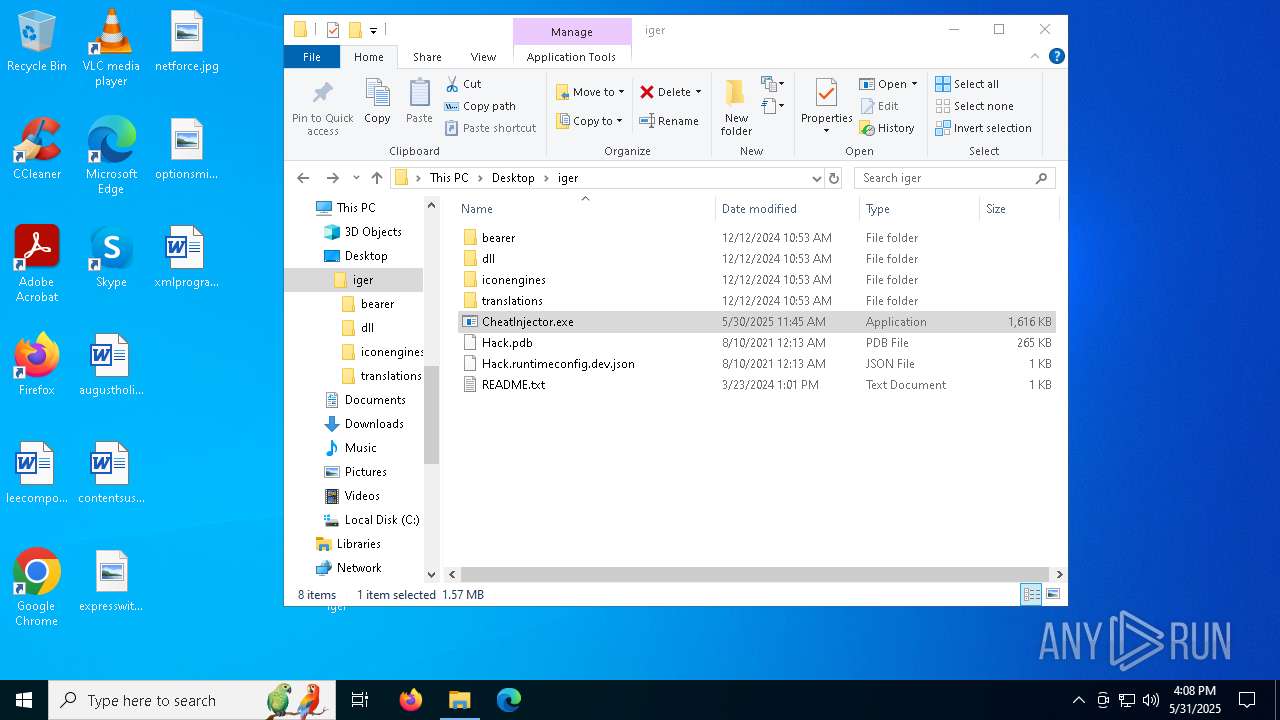
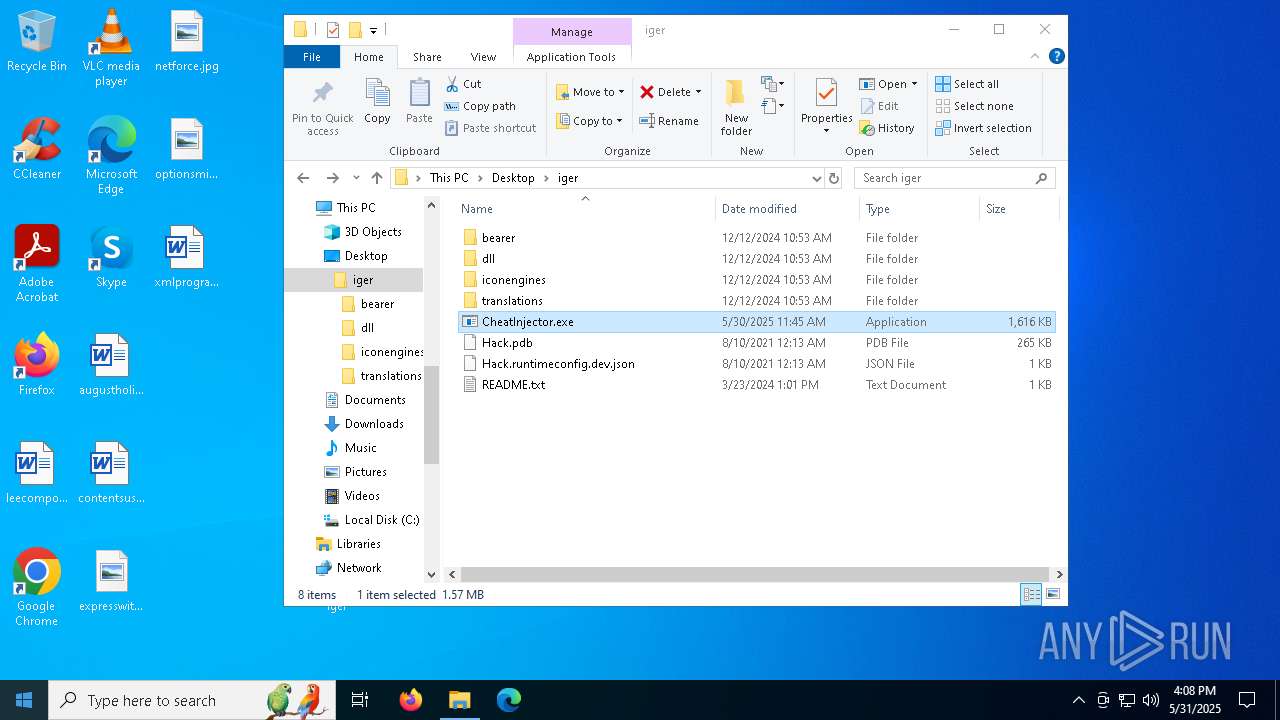
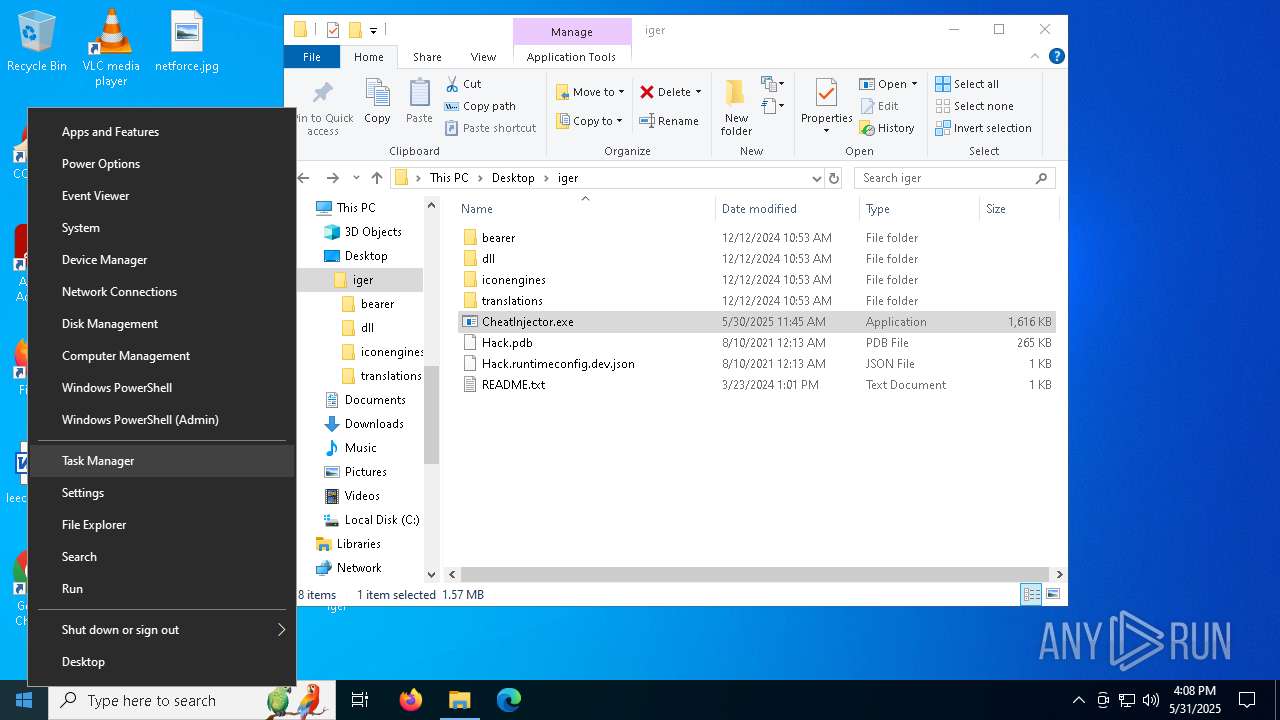
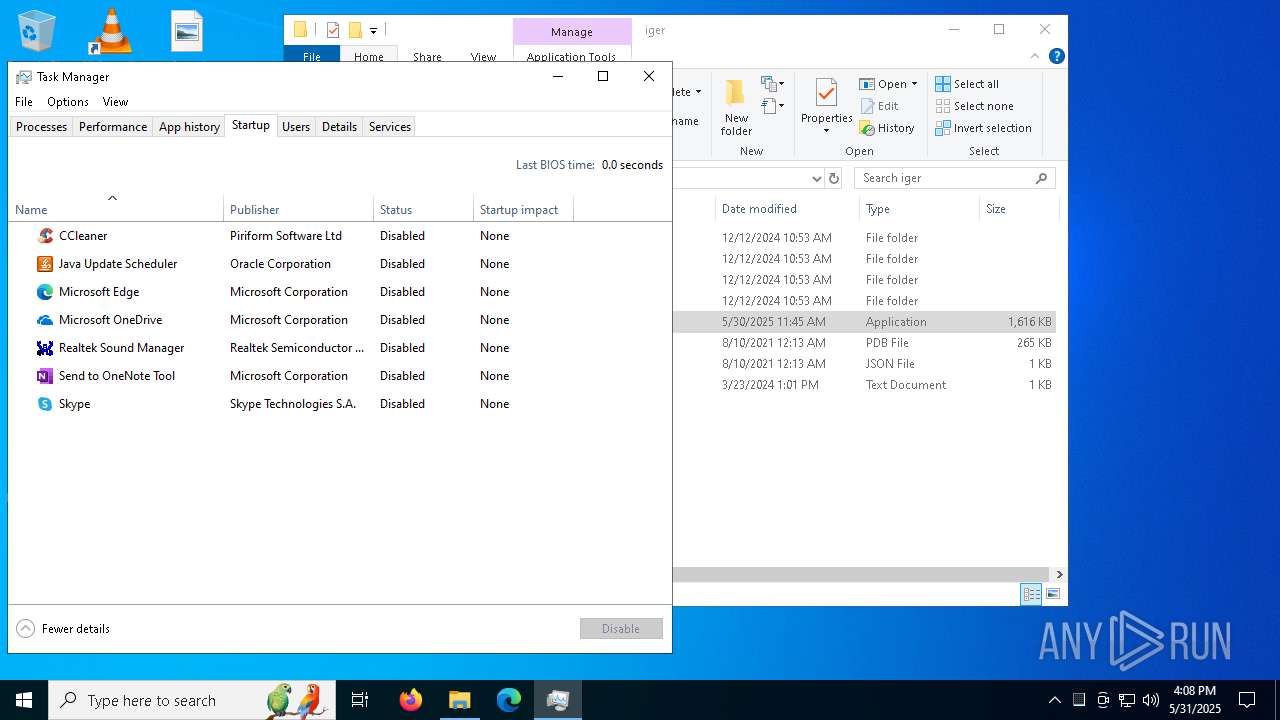
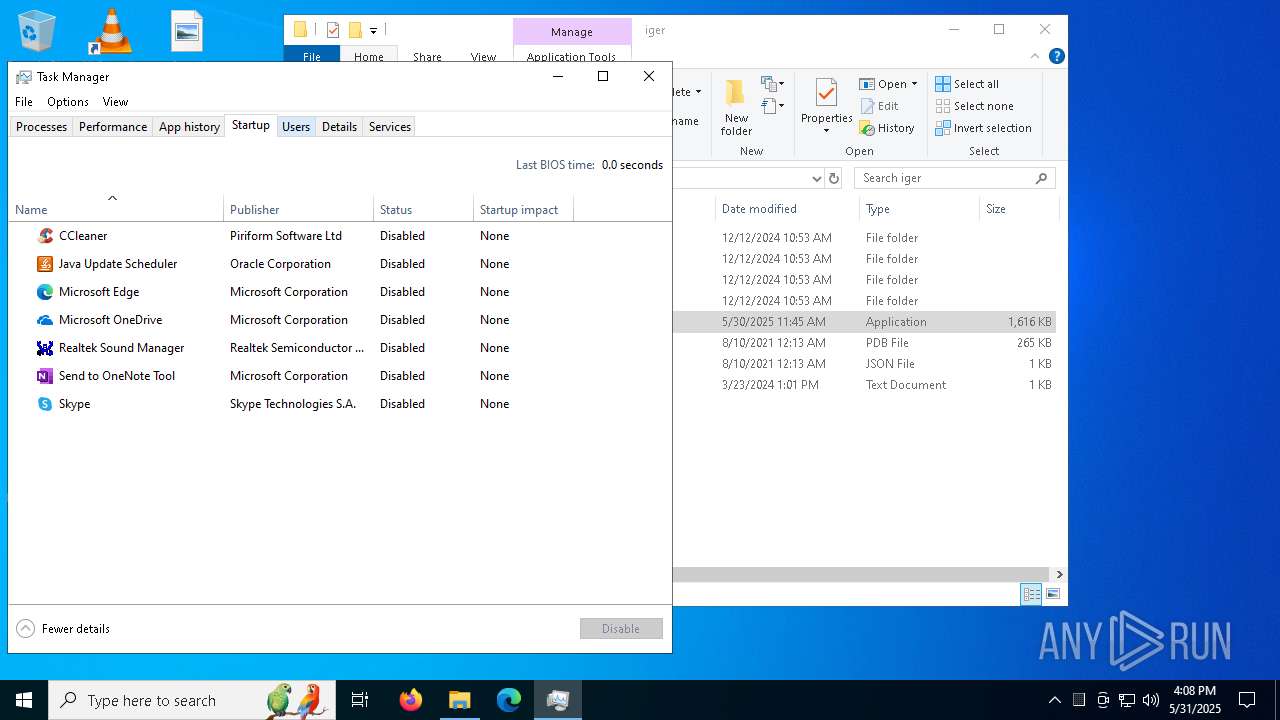
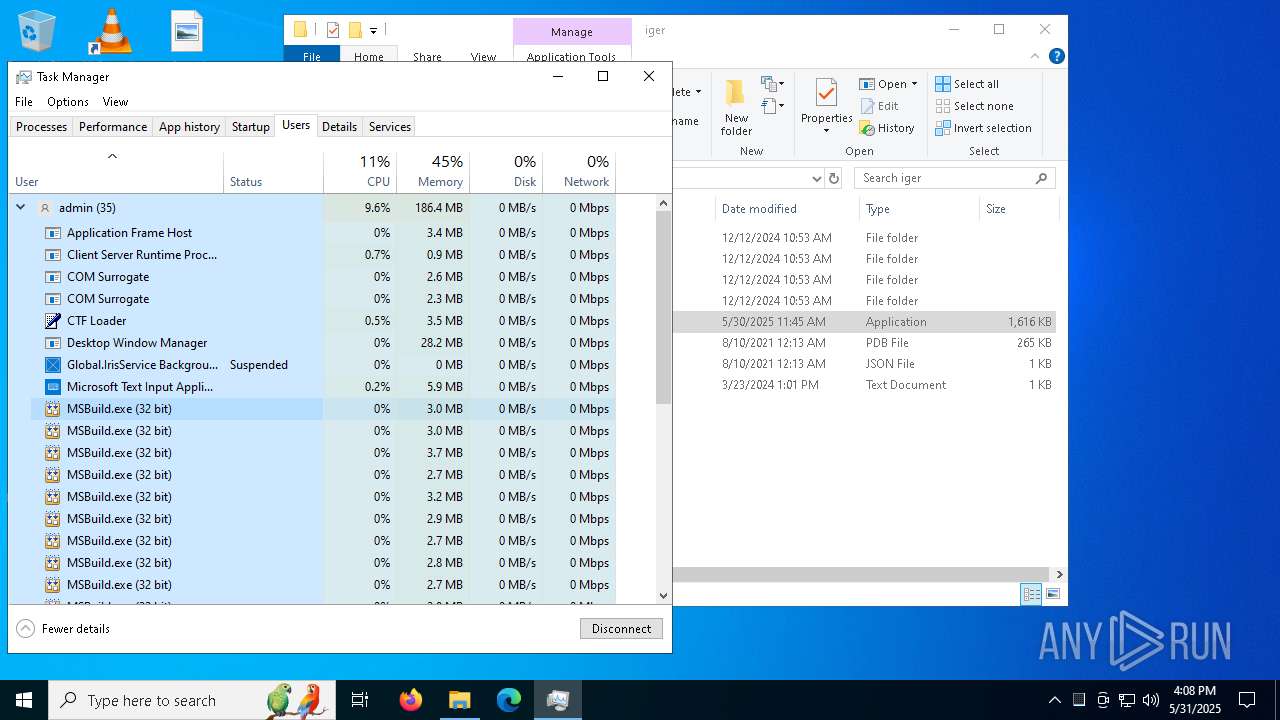
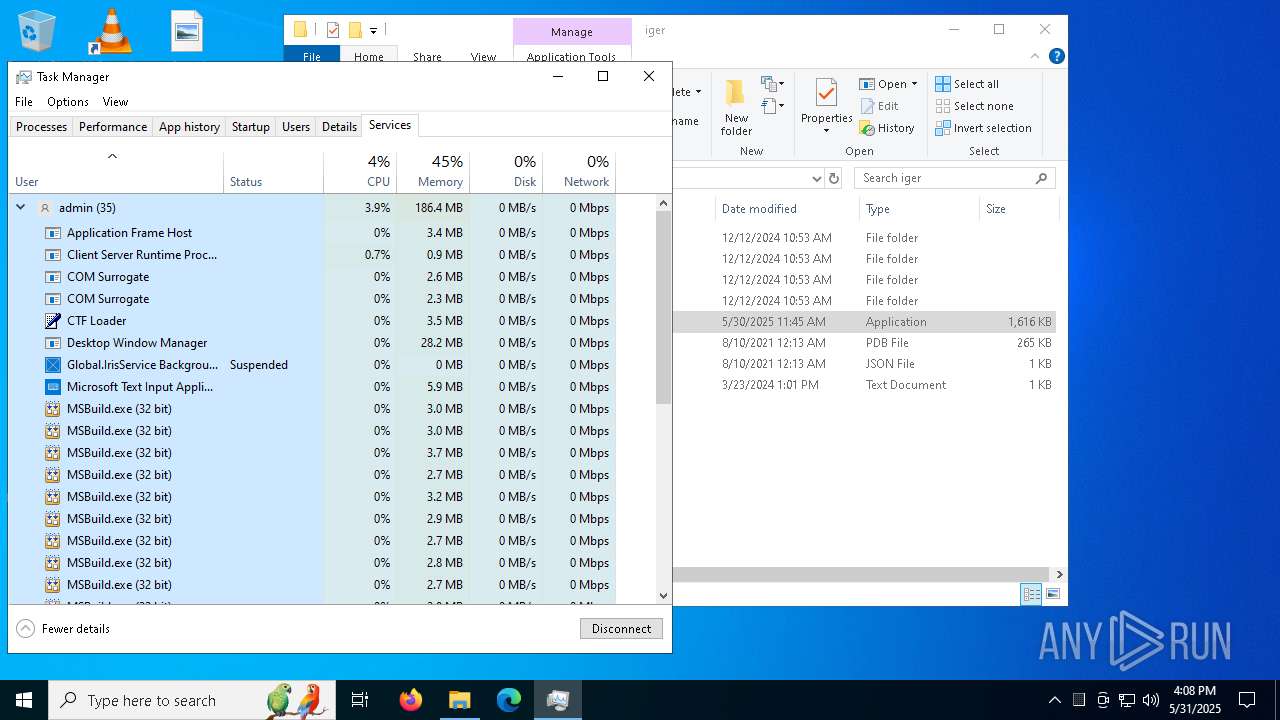
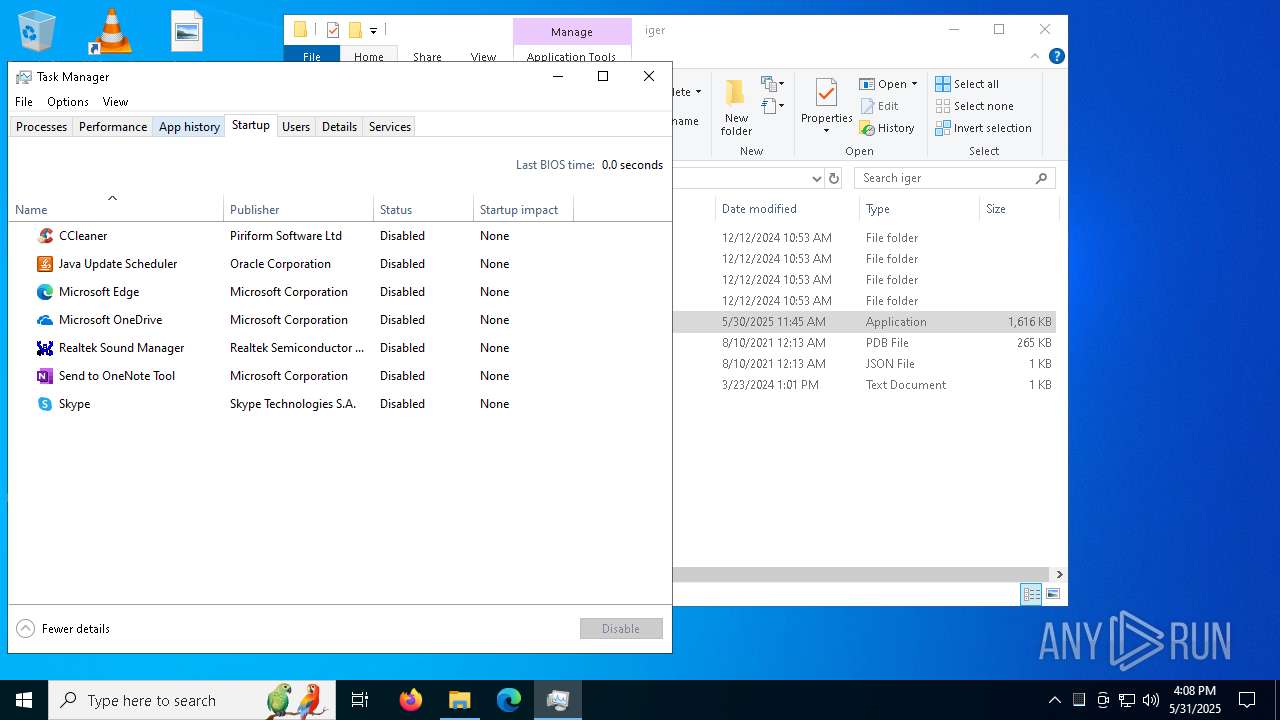
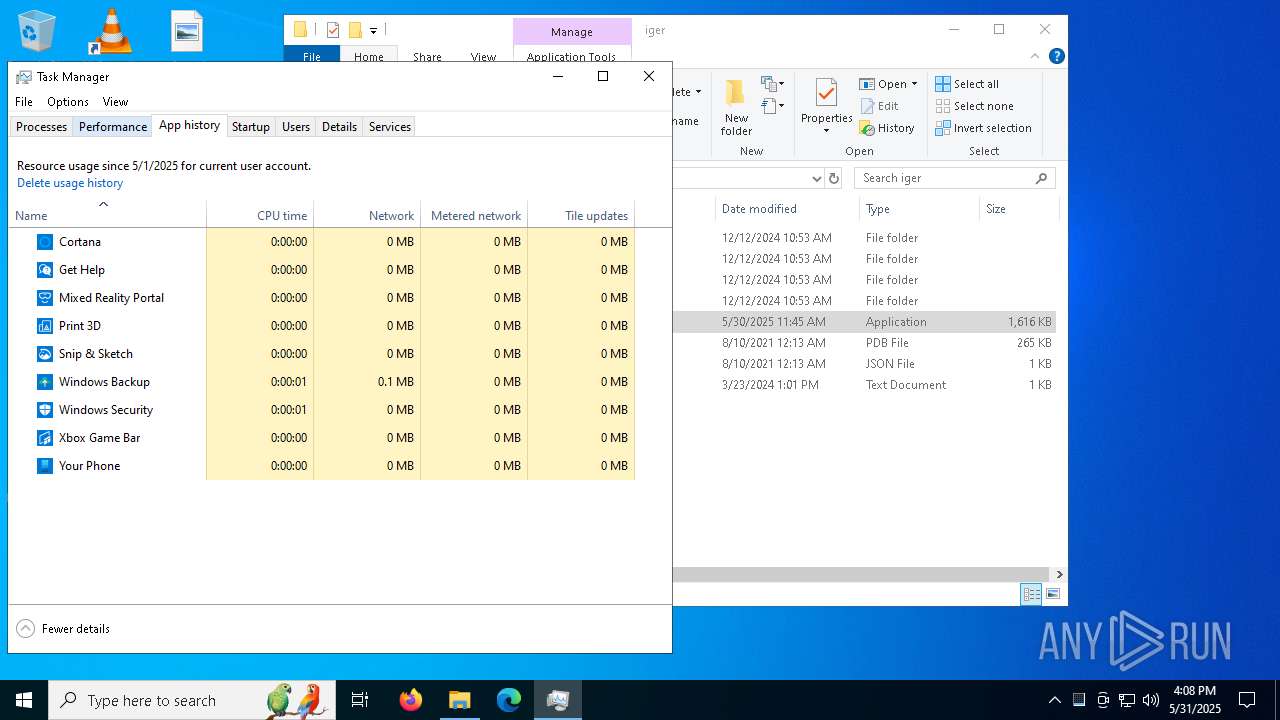
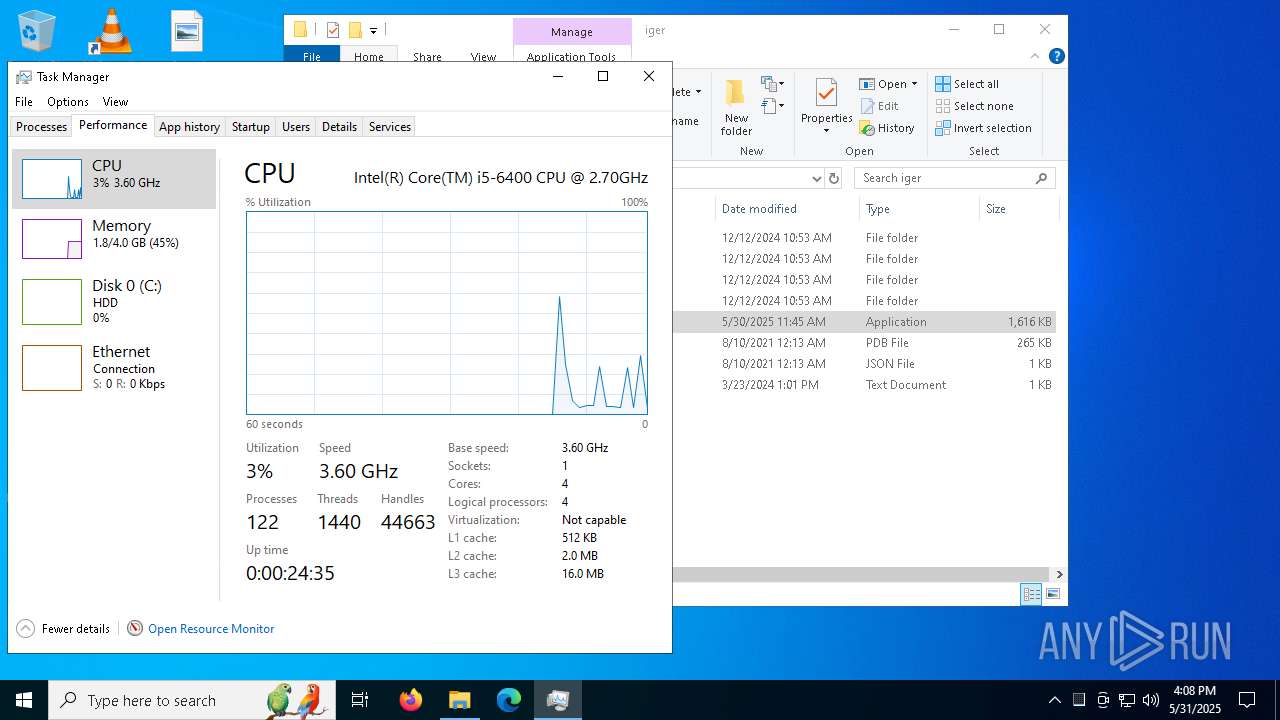
Manual execution by a user
- msedge.exe (PID: 8652)
- Taskmgr.exe (PID: 8392)
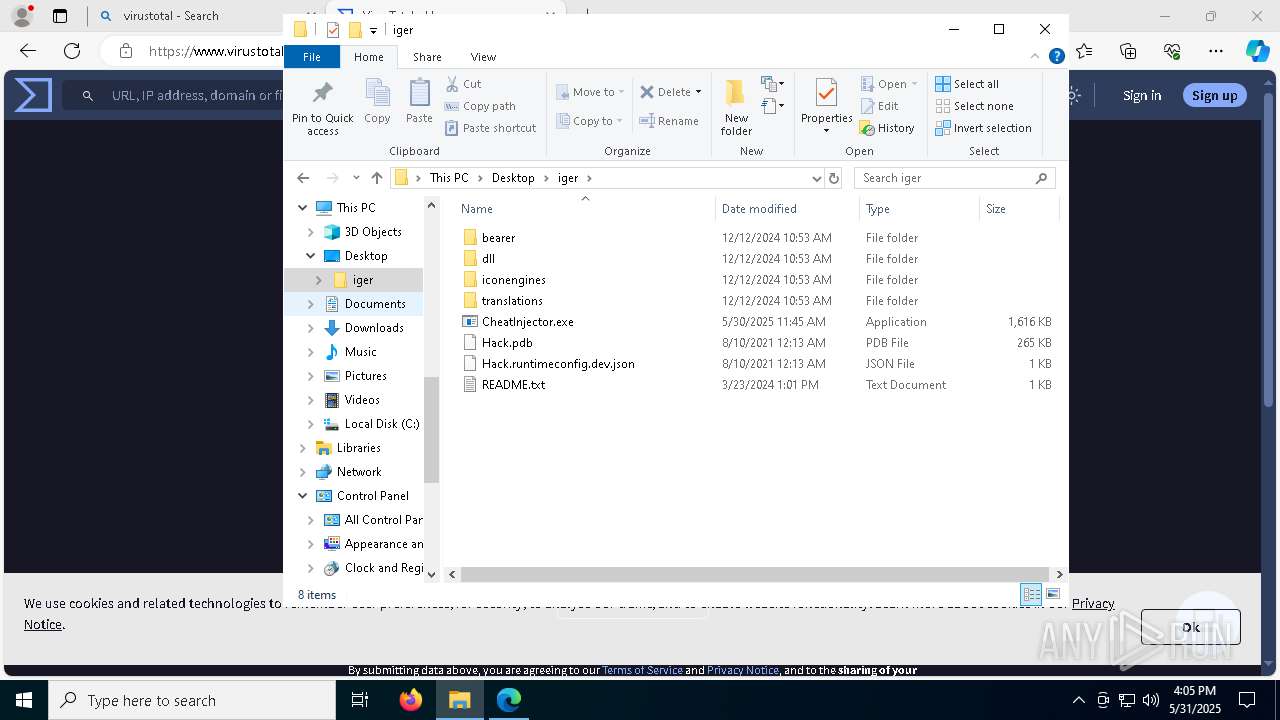
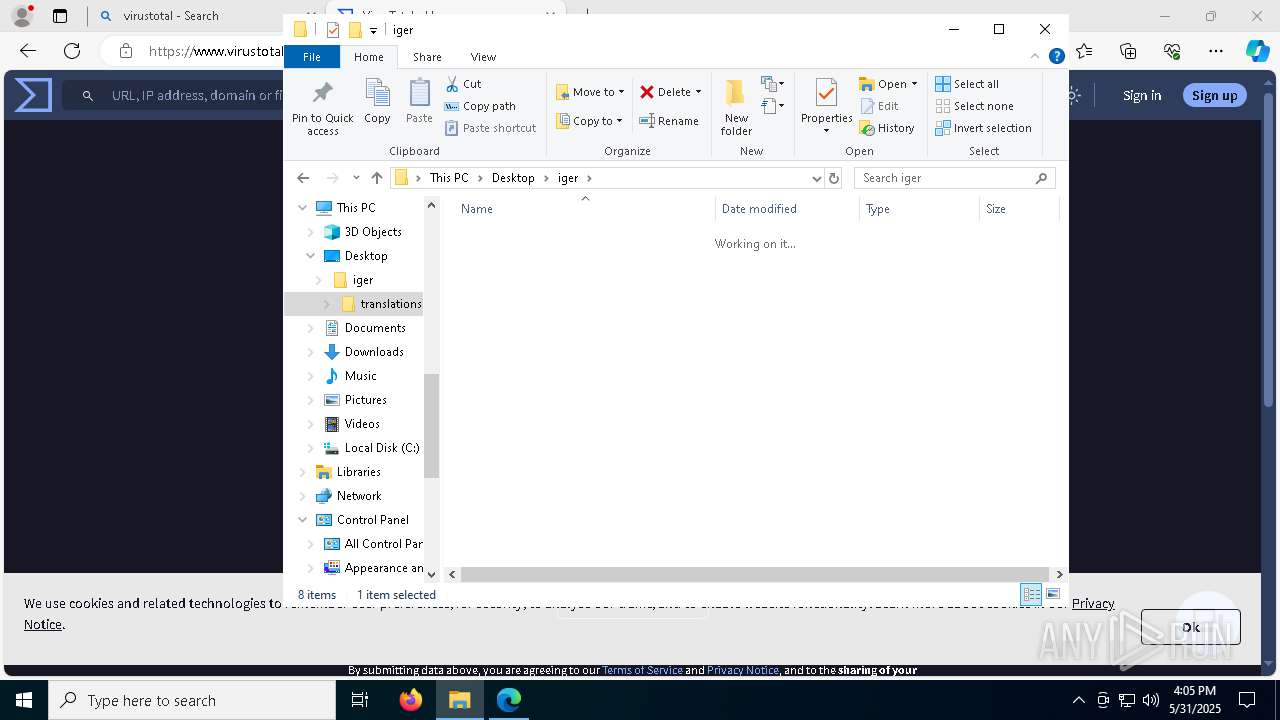
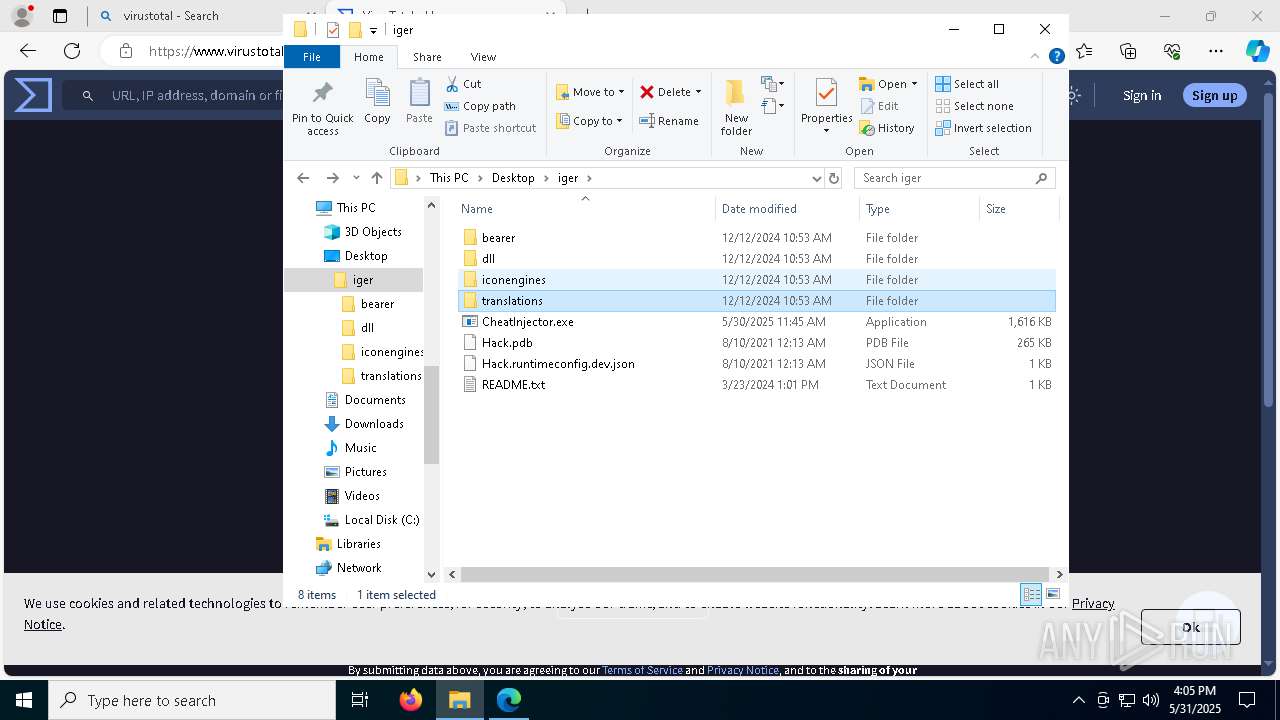
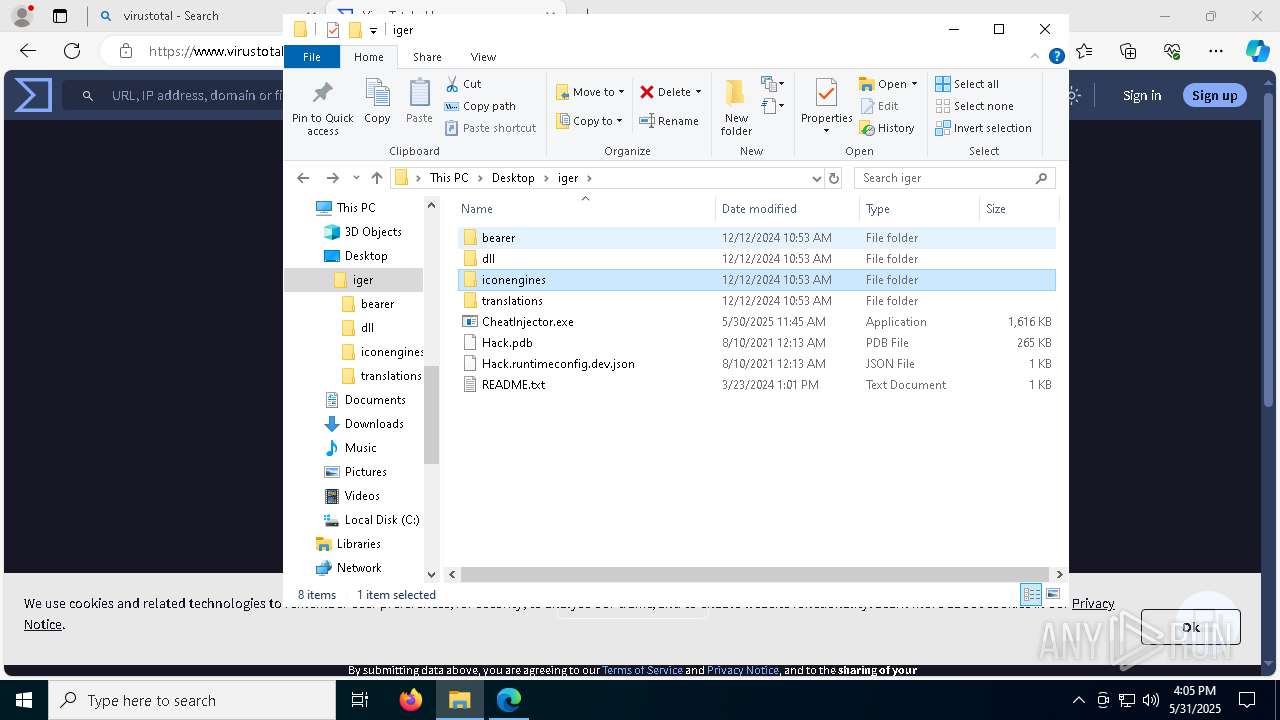
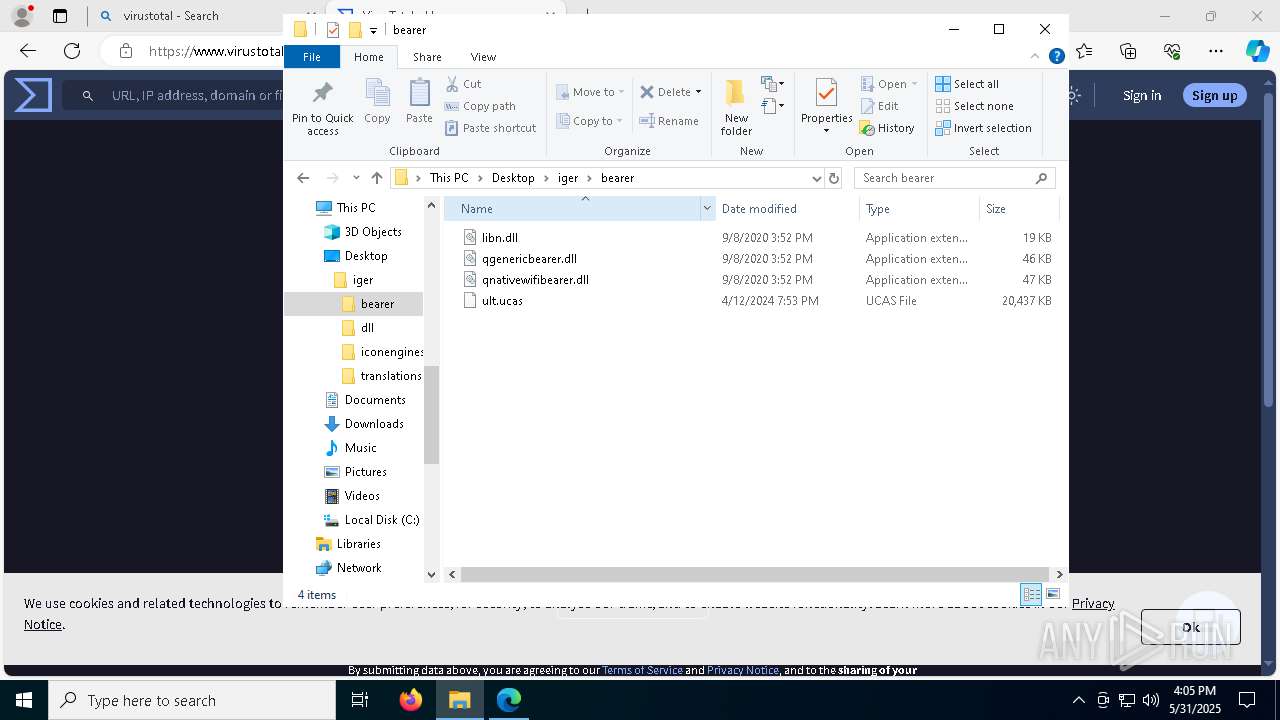
- CheatInjector.exe (PID: 1512)
- CheatInjector.exe (PID: 2740)
- CheatInjector.exe (PID: 6240)
- CheatInjector.exe (PID: 7420)
- Taskmgr.exe (PID: 8272)
- notepad.exe (PID: 2420)
- CheatInjector.exe (PID: 8800)
- CheatInjector.exe (PID: 2108)
- CheatInjector.exe (PID: 7676)
- CheatInjector.exe (PID: 8020)
- CheatInjector.exe (PID: 5576)
- CheatInjector.exe (PID: 1072)
- CheatInjector.exe (PID: 8024)
- Taskmgr.exe (PID: 5960)
- Taskmgr.exe (PID: 6188)
- CheatInjector.exe (PID: 8508)
- CheatInjector.exe (PID: 456)
Application launched itself
- msedge.exe (PID: 4428)
- msedge.exe (PID: 5624)
- msedge.exe (PID: 4996)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(9004) MSBuild.exe
C2 (10)escczlv.top/bufi
pavpwe.run/ptla
https://t.me/vstalnasral555
citellcagt.top/gjtu
thundeqqbw.bet/aznd
korxddl.top/qidz
narrathfpt.top/tekq
localixbiw.top/zlpa
harumseeiw.top/tqmn
diecam.top/laur
(PID) Process(8308) MSBuild.exe
C2 (10)escczlv.top/bufi
pavpwe.run/ptla
https://t.me/vstalnasral555
citellcagt.top/gjtu
thundeqqbw.bet/aznd
korxddl.top/qidz
narrathfpt.top/tekq
localixbiw.top/zlpa
harumseeiw.top/tqmn
diecam.top/laur
(PID) Process(7320) MSBuild.exe
C2 (10)escczlv.top/bufi
pavpwe.run/ptla
https://t.me/vstalnasral555
citellcagt.top/gjtu
thundeqqbw.bet/aznd
korxddl.top/qidz
narrathfpt.top/tekq
localixbiw.top/zlpa
harumseeiw.top/tqmn
diecam.top/laur
(PID) Process(5568) MSBuild.exe
C2 (10)escczlv.top/bufi
pavpwe.run/ptla
https://t.me/vstalnasral555
citellcagt.top/gjtu
thundeqqbw.bet/aznd
korxddl.top/qidz
narrathfpt.top/tekq
localixbiw.top/zlpa
harumseeiw.top/tqmn
diecam.top/laur
(PID) Process(7636) MSBuild.exe
C2 (10)escczlv.top/bufi
pavpwe.run/ptla
https://t.me/vstalnasral555
citellcagt.top/gjtu
thundeqqbw.bet/aznd
korxddl.top/qidz
narrathfpt.top/tekq
localixbiw.top/zlpa
harumseeiw.top/tqmn
diecam.top/laur
(PID) Process(7776) MSBuild.exe
C2 (10)escczlv.top/bufi
pavpwe.run/ptla
https://t.me/vstalnasral555
citellcagt.top/gjtu
thundeqqbw.bet/aznd
korxddl.top/qidz
narrathfpt.top/tekq
localixbiw.top/zlpa
harumseeiw.top/tqmn
diecam.top/laur
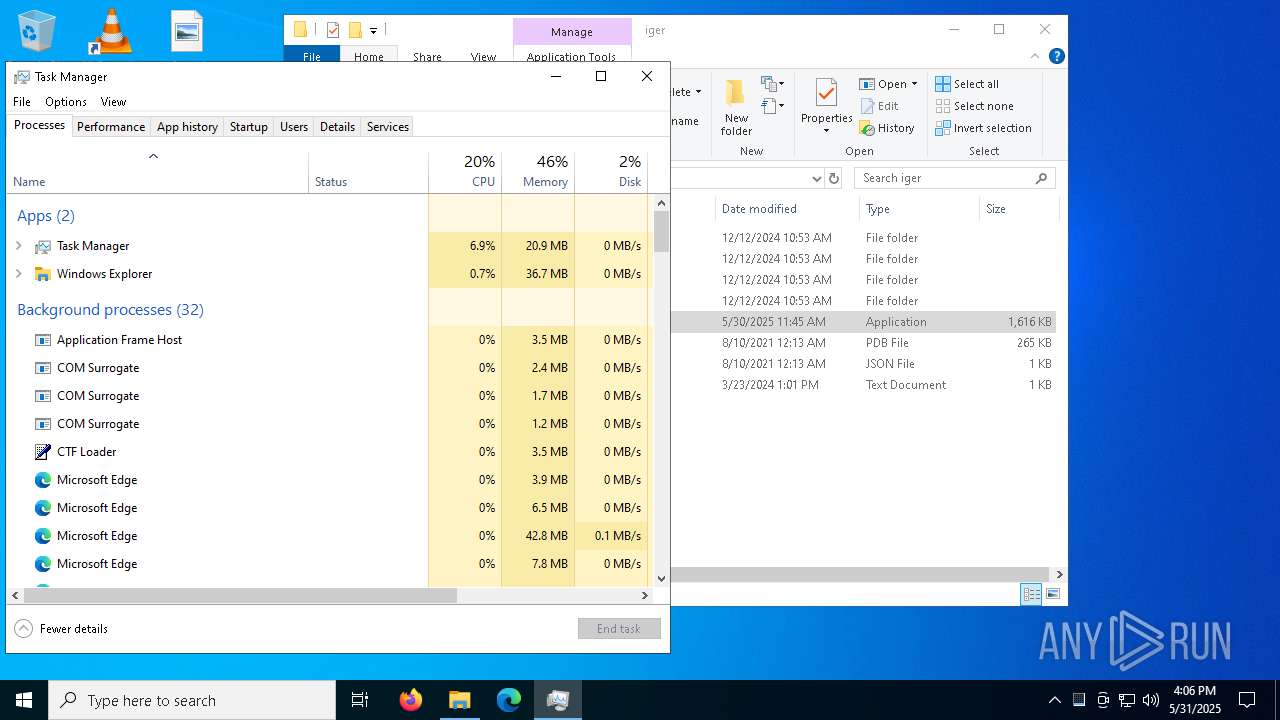
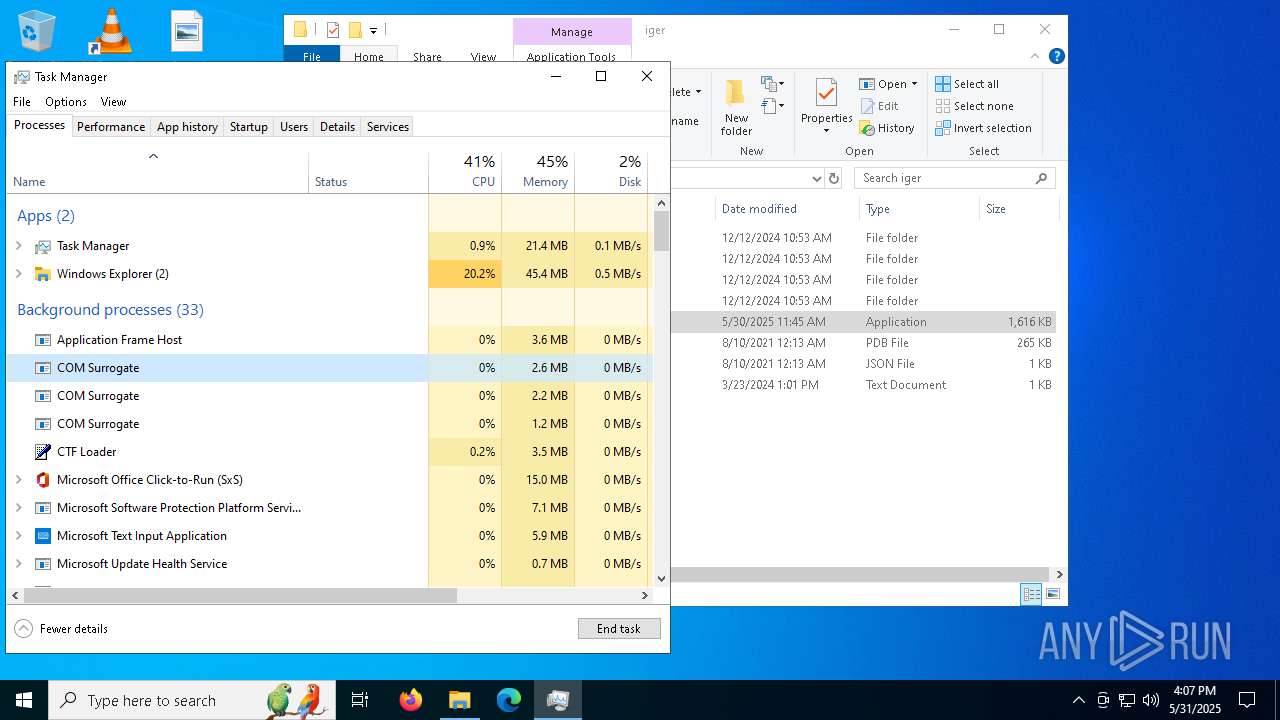
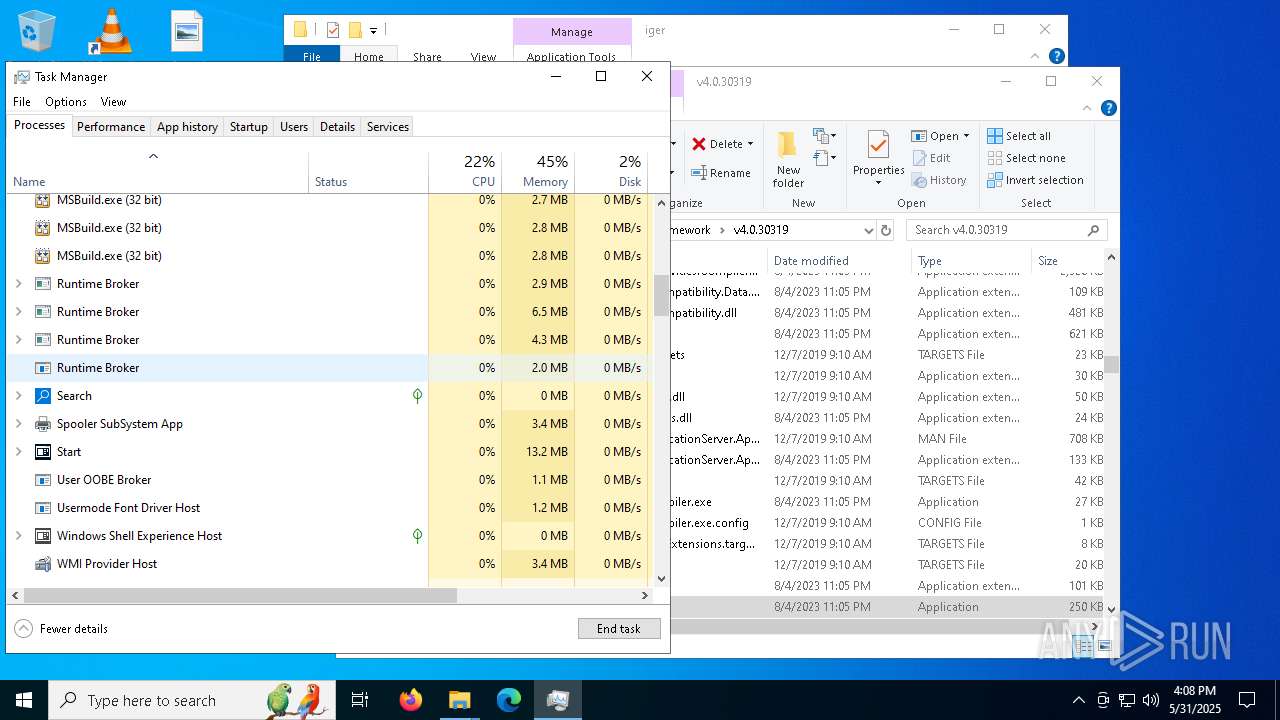
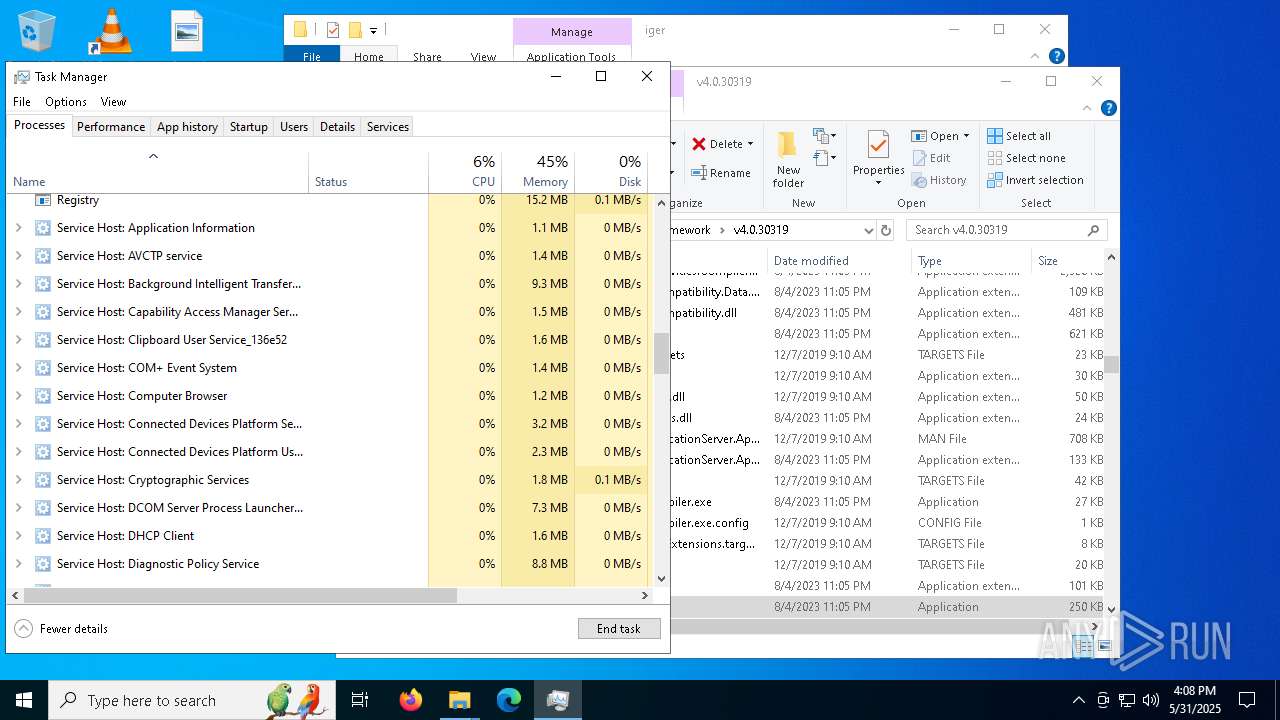
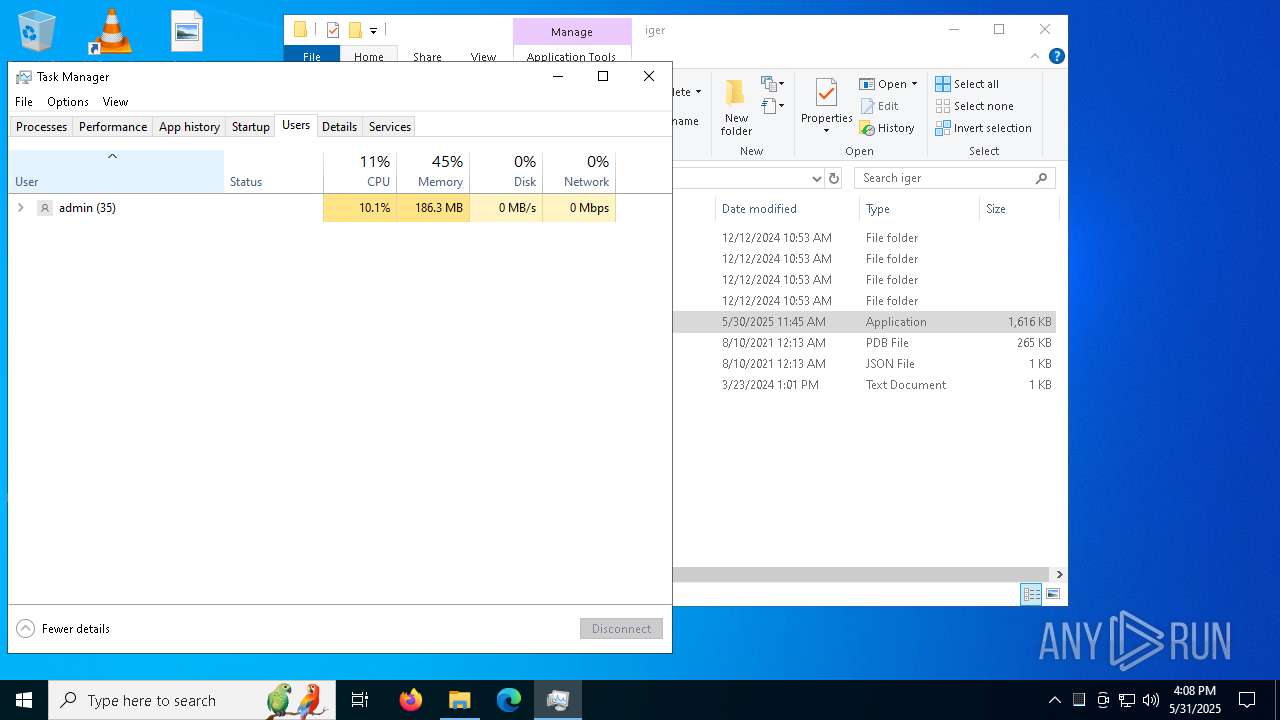
Total processes
338
Monitored processes
184
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=6636 --field-trial-handle=2380,i,11623598062688006982,11687020942864998832,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1488 --field-trial-handle=2316,i,18373926559861621514,13464482193755054036,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | "C:\Users\admin\Desktop\iger\CheatInjector.exe" | C:\Users\admin\Desktop\iger\CheatInjector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2628 --field-trial-handle=2356,i,17607573408494599873,10010930430825491219,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=57 --mojo-platform-channel-handle=3452 --field-trial-handle=2380,i,11623598062688006982,11687020942864998832,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --mojo-platform-channel-handle=7560 --field-trial-handle=2380,i,11623598062688006982,11687020942864998832,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
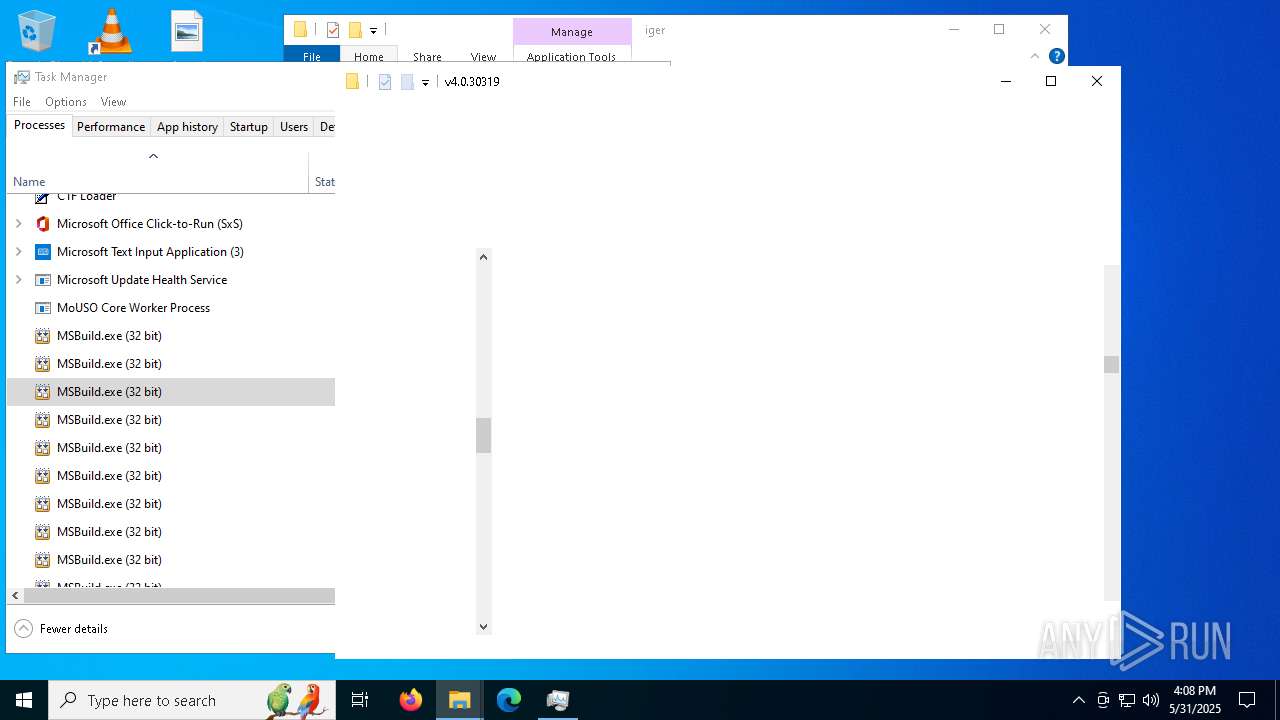
| 872 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | CheatInjector.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 1 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4064 --field-trial-handle=2380,i,11623598062688006982,11687020942864998832,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\Desktop\iger\CheatInjector.exe" | C:\Users\admin\Desktop\iger\CheatInjector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5196 --field-trial-handle=2356,i,17607573408494599873,10010930430825491219,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
32 829
Read events
32 688
Write events
139
Delete events
2
Modification events
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2A8753F506952F00 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1A2F5DF506952F00 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6B910B25-05BD-45FC-95E5-CFFB832257FC} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F303113C-620B-400A-990F-2FE5539F763E} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B5D3125D-9879-4265-9A6F-77AE2BD9FD7C} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B0E780F506952F00 | |||
Executable files
100
Suspicious files
1 183
Text files
198
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f54a.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f559.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f569.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f569.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11f579.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f579.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
508
DNS requests
500
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6252 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8316 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748971632&P2=404&P3=2&P4=izzX%2b3zw8YWdUXun36Dx3l114m%2bGJzfD%2brhqVn0sRJS0hwQyC1BAQSW6rCSZbD2%2bfP343pSzzz12u6DdEF4%2bKg%3d%3d | unknown | — | — | whitelisted |
8316 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/46df2db5-82ac-46a7-9d9e-cf1580d73a96?P1=1749088782&P2=404&P3=2&P4=Icm1qqcBLiYdS%2bGlTGB8f3Br4XsoZwOK39OpEgDSKM7o80NgENJp9ATWNGD5P%2faeRtwkgU2GDVKKm9iVg2SV8g%3d%3d | unknown | — | — | whitelisted |
8316 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/46df2db5-82ac-46a7-9d9e-cf1580d73a96?P1=1749088782&P2=404&P3=2&P4=Icm1qqcBLiYdS%2bGlTGB8f3Br4XsoZwOK39OpEgDSKM7o80NgENJp9ATWNGD5P%2faeRtwkgU2GDVKKm9iVg2SV8g%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8316 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748971632&P2=404&P3=2&P4=izzX%2b3zw8YWdUXun36Dx3l114m%2bGJzfD%2brhqVn0sRJS0hwQyC1BAQSW6rCSZbD2%2bfP343pSzzz12u6DdEF4%2bKg%3d%3d | unknown | — | — | whitelisted |
8316 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748971632&P2=404&P3=2&P4=izzX%2b3zw8YWdUXun36Dx3l114m%2bGJzfD%2brhqVn0sRJS0hwQyC1BAQSW6rCSZbD2%2bfP343pSzzz12u6DdEF4%2bKg%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8316 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/46df2db5-82ac-46a7-9d9e-cf1580d73a96?P1=1749088782&P2=404&P3=2&P4=Icm1qqcBLiYdS%2bGlTGB8f3Br4XsoZwOK39OpEgDSKM7o80NgENJp9ATWNGD5P%2faeRtwkgU2GDVKKm9iVg2SV8g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2088 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5408 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4428 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2616 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2616 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.youtube.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2616 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2616 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2616 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2616 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2616 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |