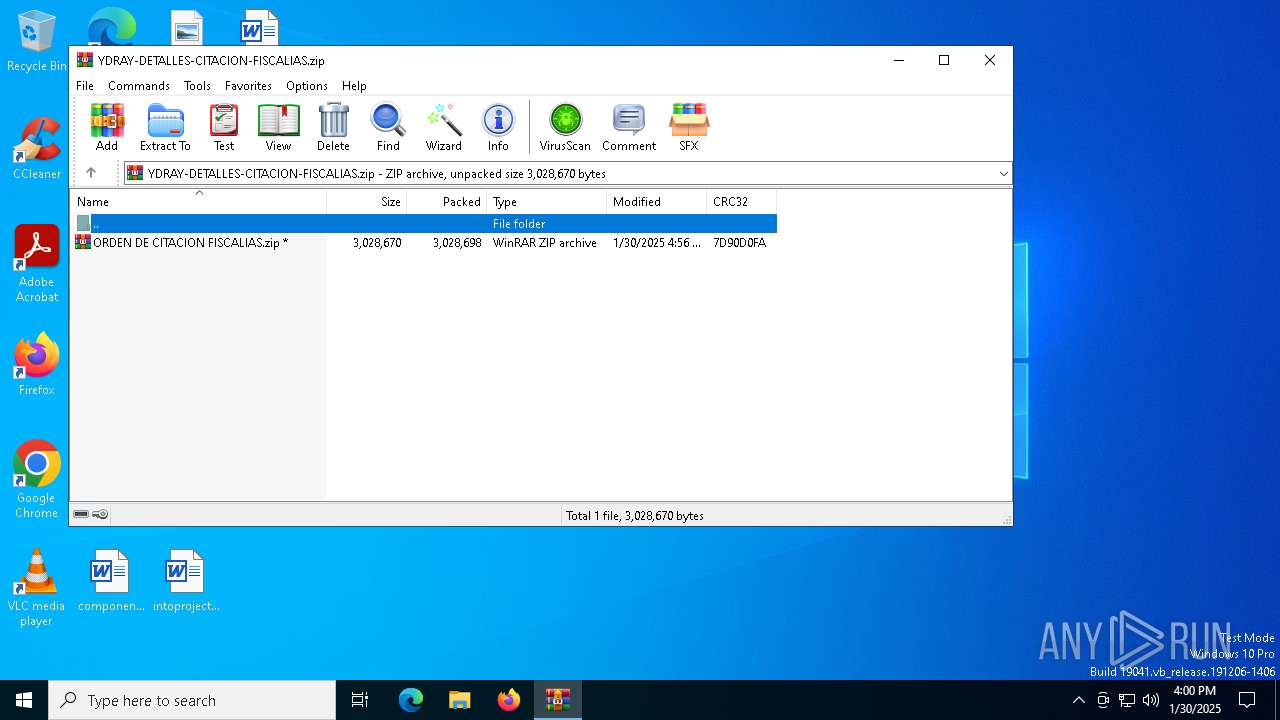
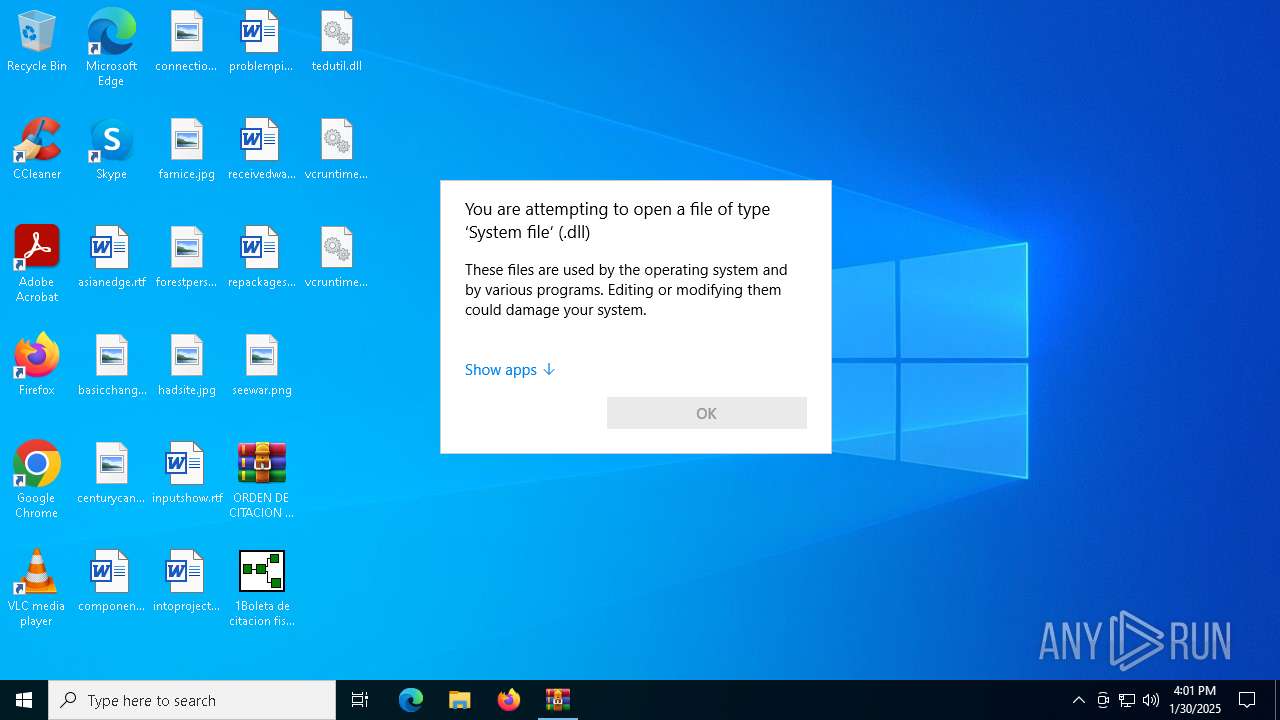
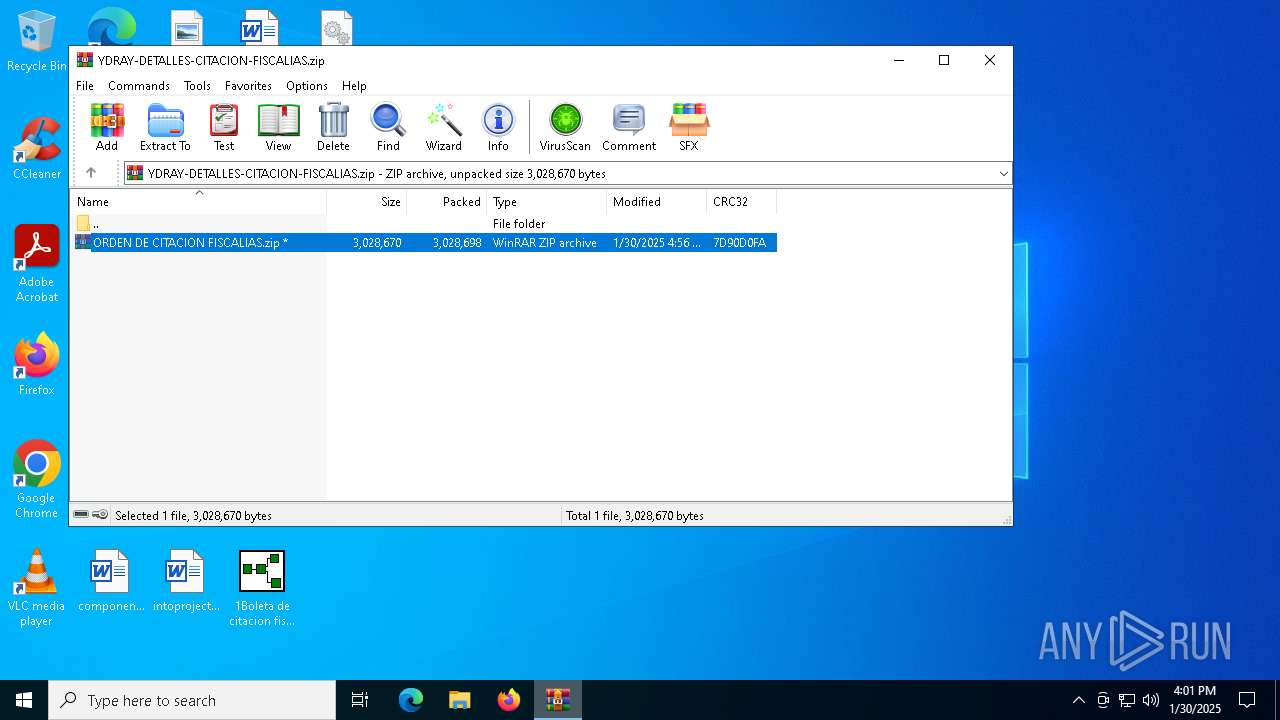
| File name: | YDRAY-DETALLES-CITACION-FISCALIAS.zip |
| Full analysis: | https://app.any.run/tasks/c1a0f36f-4f24-46fa-a29a-e0a8374e7a03 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 30, 2025, 16:00:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=AES Encrypted |
| MD5: | 9CD0E7B8E7A66CED71DDF041B9D409B8 |
| SHA1: | 74CB0D42FE9561CF563E6249141C743AC82D2995 |
| SHA256: | EDD914273349D507EAC1DCD6DE06B04353DFC5C9730AF82B843D0BF980CA967D |
| SSDEEP: | 98304:wh15kh43SVP4nFHC6p8W8ED1yptndmXmfvWAWvr85NEGaWUPVO7yA2ljHUffG6wY:Ol+WoFjhzT |
MALICIOUS
DCRAT mutex has been found
- AddInProcess32.exe (PID: 4052)
ASYNCRAT has been detected (YARA)
- AddInProcess32.exe (PID: 4052)
ASYNCRAT has been detected (SURICATA)
- AddInProcess32.exe (PID: 4052)
SUSPICIOUS
Executes application which crashes
- 1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe (PID: 2928)
Connects to unusual port
- AddInProcess32.exe (PID: 4052)
Contacting a server suspected of hosting an CnC
- AddInProcess32.exe (PID: 4052)
Executing commands from a ".bat" file
- AddInProcess32.exe (PID: 4052)
Starts CMD.EXE for commands execution
- AddInProcess32.exe (PID: 4052)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2792)
Deletes system .NET executable
- cmd.exe (PID: 2792)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 6428)
- WinRAR.exe (PID: 3620)
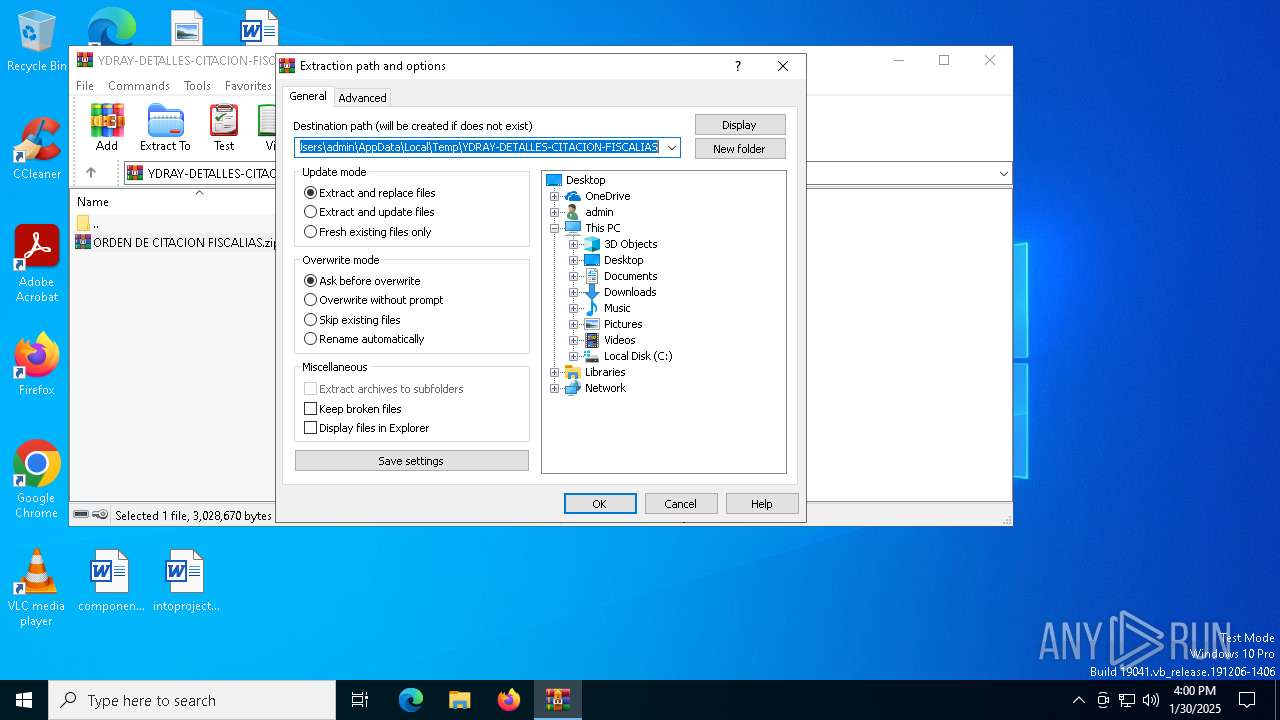
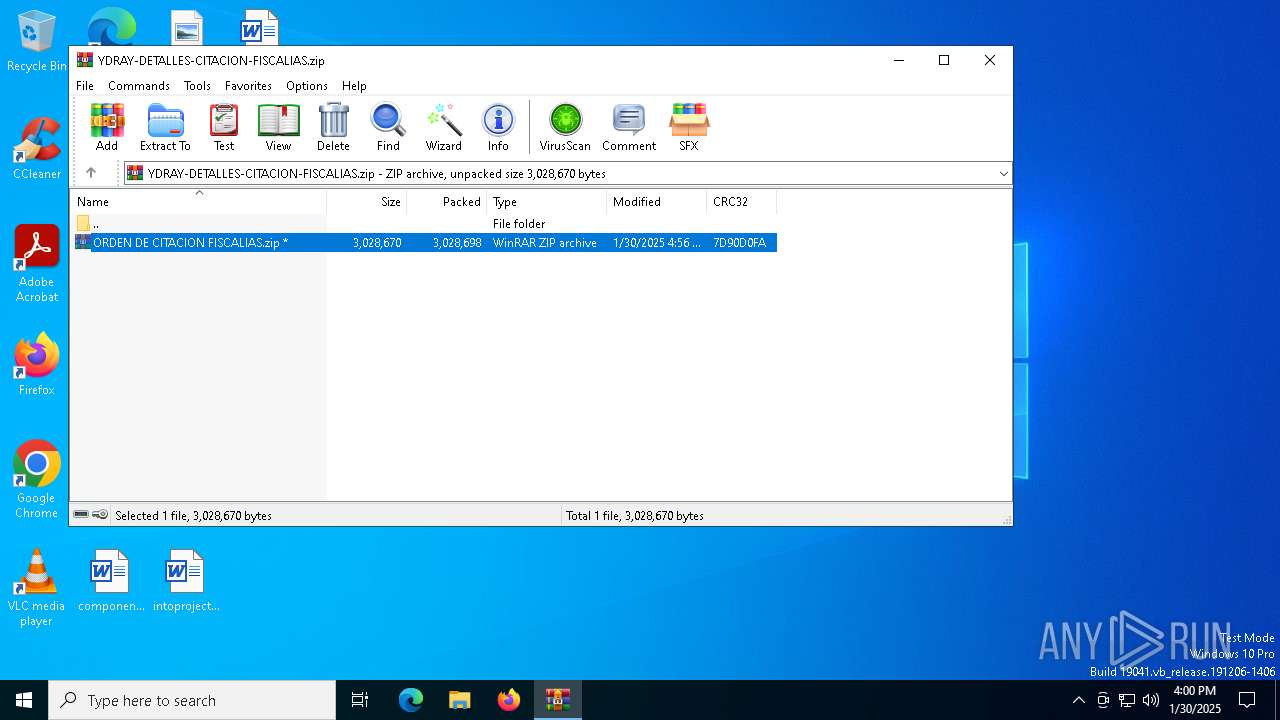
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3620)
Reads the software policy settings
- WerFault.exe (PID: 4740)
- AddInProcess32.exe (PID: 4052)
Reads the machine GUID from the registry
- AddInProcess32.exe (PID: 4052)
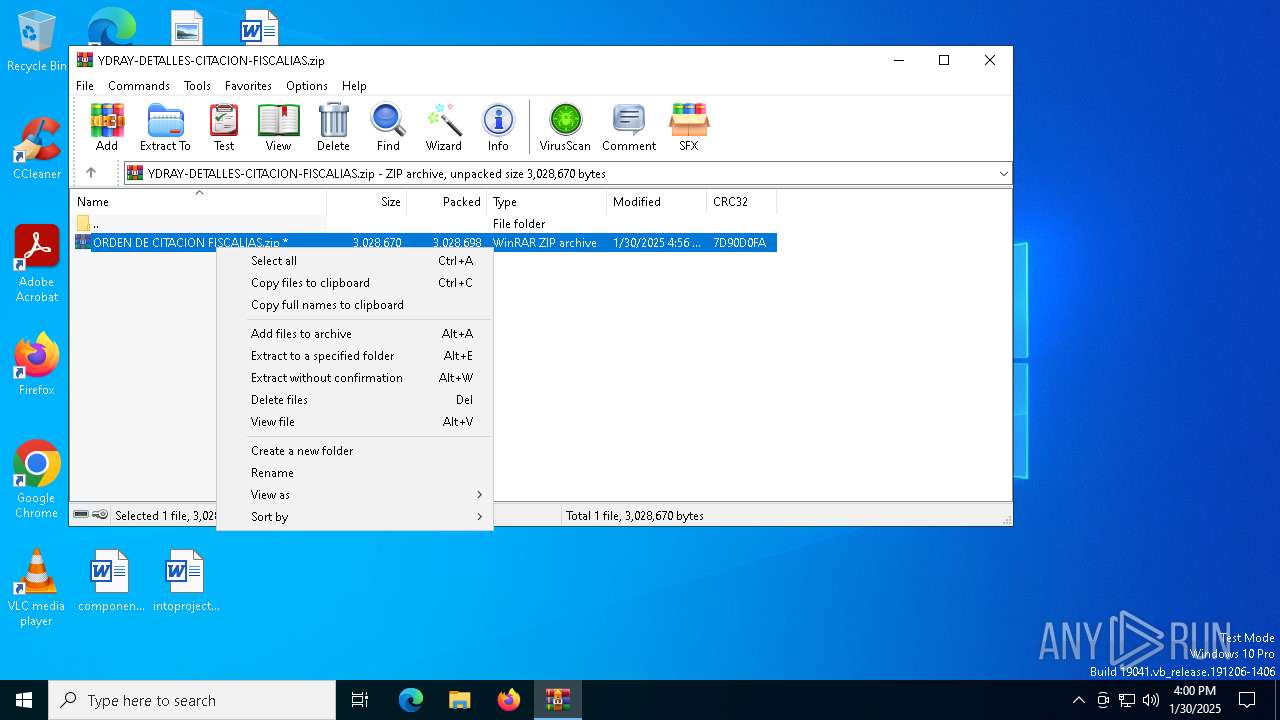
Manual execution by a user
- WinRAR.exe (PID: 3620)
- 1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe (PID: 2928)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 2996)
- OpenWith.exe (PID: 1520)
Creates files or folders in the user directory
- WerFault.exe (PID: 4740)
- WerFault.exe (PID: 5748)
Checks supported languages
- 1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe (PID: 2928)
- AddInProcess32.exe (PID: 4052)
Reads the computer name
- AddInProcess32.exe (PID: 4052)
Checks proxy server information
- WerFault.exe (PID: 4740)
Create files in a temporary directory
- AddInProcess32.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(4052) AddInProcess32.exe
C2 (1)pasto2025.duckdns.org
Ports (1)3333
Version1.0.7
Options
AutoRunfalse
MutexDcRatMutex_qwqdanchun4634tfdhfg
InstallFolder%AppData%
Certificates
Cert1MIICKzCCAZSgAwIBAgIVAKBgFhql6o2v14nWIx79lpt+pSsTMA0GCSqGSIb3DQEBDQUAMF8xEDAOBgNVBAMMB3N2Y2hvc3QxEzARBgNVBAsMCnF3cWRhbmNodW4xHDAaBgNVBAoME0RjUmF0IEJ5IHF3cWRhbmNodW4xCzAJBgNVBAcMAlNIMQswCQYDVQQGEwJDTjAeFw0yMTA0MTAxNDM3NTlaFw0zMjAxMTgxNDM3NTlaMBAxDjAMBgNVBAMMBURjUmF0MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKB...
Server_Signatureab6bpU2urOT/J+cNzlb8KIlYoW3Q/LHeuYbiXnCzPCstNnHwlSsEaR8buZNurT5PTaWiB4PnoShLbkkAziihGe2MWmn7OPkrC8/2BQ24u3hyDQ7Dw85W6pXfJsqe07XcFuP6VZ2po/v8IOVbmvoYO5KCBqpqUhqlM2Mick6a14E=
Keys
AESfa6661f48dc2ce0789cfe81cebd5ff72a99e9e6467f5cb662094b77d114ac95b
SaltDcRatByqwqdanchun
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:01:29 23:56:24 |
| ZipCRC: | 0x7d90d0fa |
| ZipCompressedSize: | 3028698 |
| ZipUncompressedSize: | 3028670 |
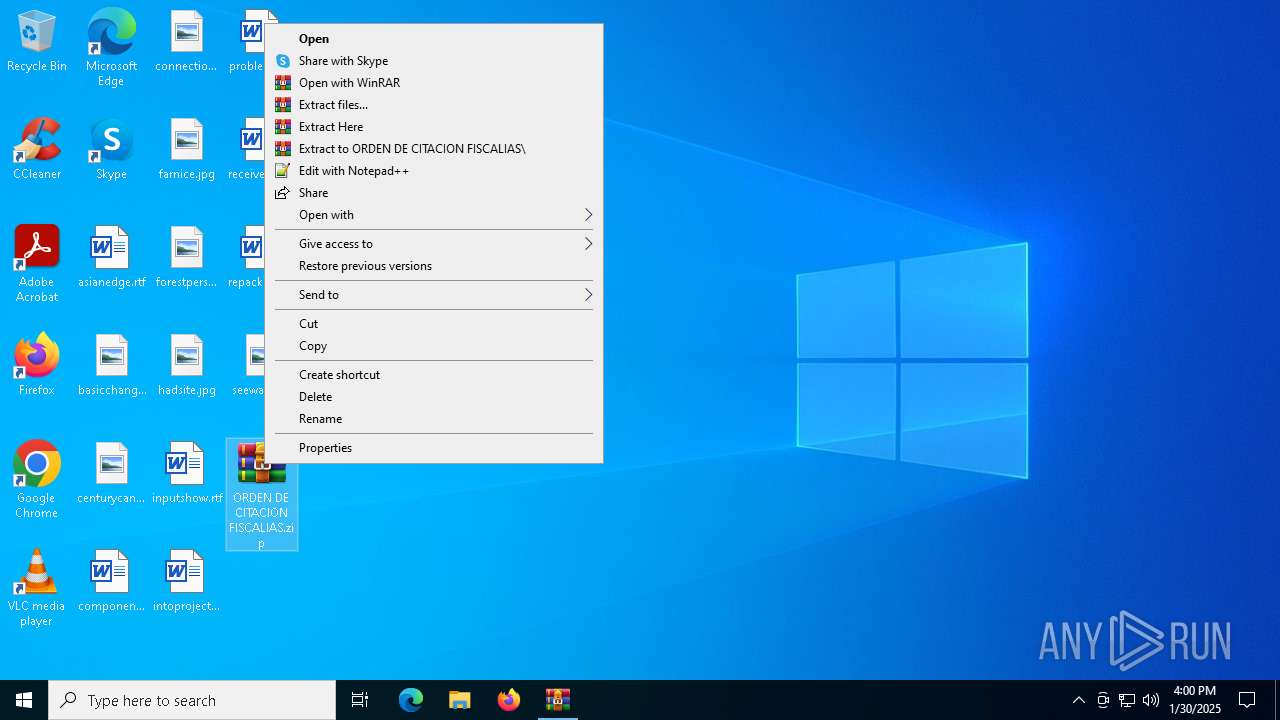
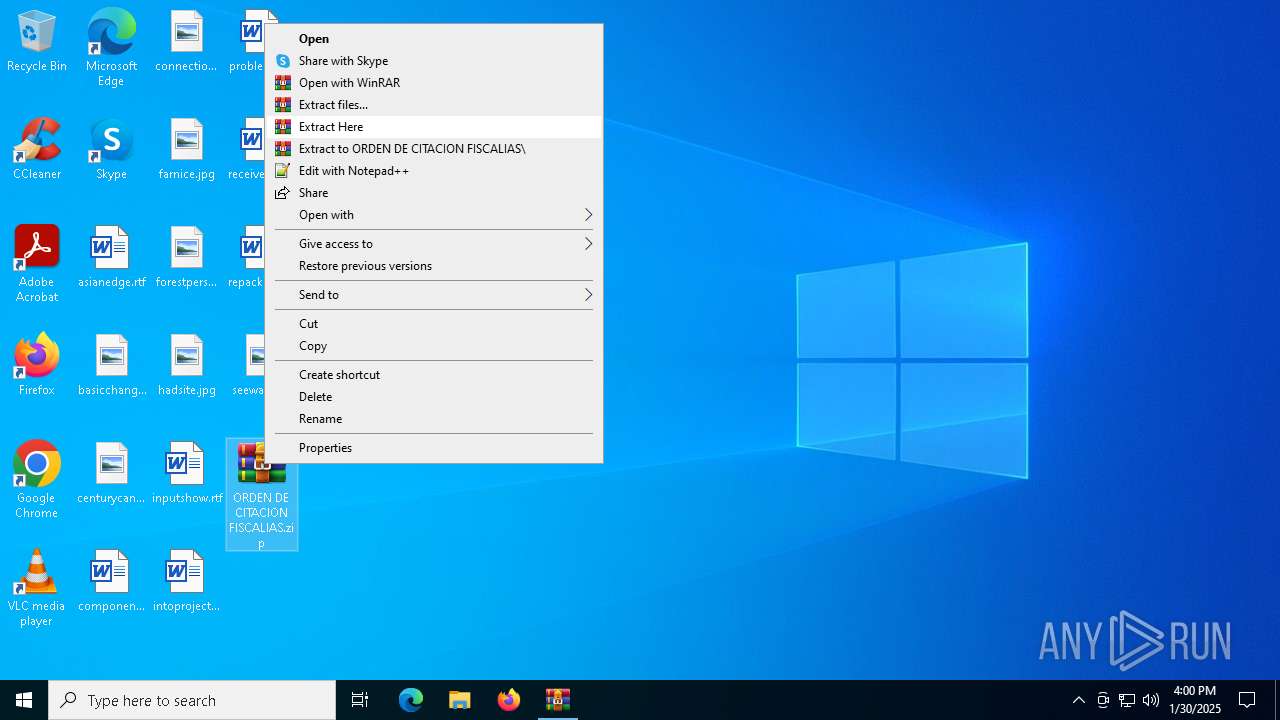
| ZipFileName: | ORDEN DE CITACION FISCALIAS.zip |
Total processes
142
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | timeout 3 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2792 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp853C.tmp.bat"" | C:\Windows\SysWOW64\cmd.exe | — | AddInProcess32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\Desktop\1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe" | C:\Users\admin\Desktop\1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Topology Editor Exit code: 3221226525 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2996 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\ORDEN DE CITACION FISCALIAS.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4052 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | 1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(4052) AddInProcess32.exe C2 (1)pasto2025.duckdns.org Ports (1)3333 Version1.0.7 Options AutoRunfalse MutexDcRatMutex_qwqdanchun4634tfdhfg InstallFolder%AppData% Certificates Cert1MIICKzCCAZSgAwIBAgIVAKBgFhql6o2v14nWIx79lpt+pSsTMA0GCSqGSIb3DQEBDQUAMF8xEDAOBgNVBAMMB3N2Y2hvc3QxEzARBgNVBAsMCnF3cWRhbmNodW4xHDAaBgNVBAoME0RjUmF0IEJ5IHF3cWRhbmNodW4xCzAJBgNVBAcMAlNIMQswCQYDVQQGEwJDTjAeFw0yMTA0MTAxNDM3NTlaFw0zMjAxMTgxNDM3NTlaMBAxDjAMBgNVBAMMBURjUmF0MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKB... Server_Signatureab6bpU2urOT/J+cNzlb8KIlYoW3Q/LHeuYbiXnCzPCstNnHwlSsEaR8buZNurT5PTaWiB4PnoShLbkkAziihGe2MWmn7OPkrC8/2BQ24u3hyDQ7Dw85W6pXfJsqe07XcFuP6VZ2po/v8IOVbmvoYO5KCBqpqUhqlM2Mick6a14E= Keys AESfa6661f48dc2ce0789cfe81cebd5ff72a99e9e6467f5cb662094b77d114ac95b SaltDcRatByqwqdanchun | |||||||||||||||
| 4740 | C:\WINDOWS\system32\WerFault.exe -u -p 2928 -s 896 | C:\Windows\System32\WerFault.exe | 1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 064
Read events
14 029
Write events
21
Delete events
14
Modification events
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\YDRAY-DETALLES-CITACION-FISCALIAS.zip | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6428) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
2
Suspicious files
13
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4740 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_1Boleta de citac_604a4ef9799c5f9d6160494fe1f9f319239ce9_2de895cc_d63e7883-7c90-4355-8b57-d682b4f6e144\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5748 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_1Boleta de citac_594fdf6a3d185f54ae7bb7867721053d3bce1a_2de895cc_88b07974-d628-4ce8-84b2-7519869afbad\Report.wer | — | |
MD5:— | SHA256:— | |||
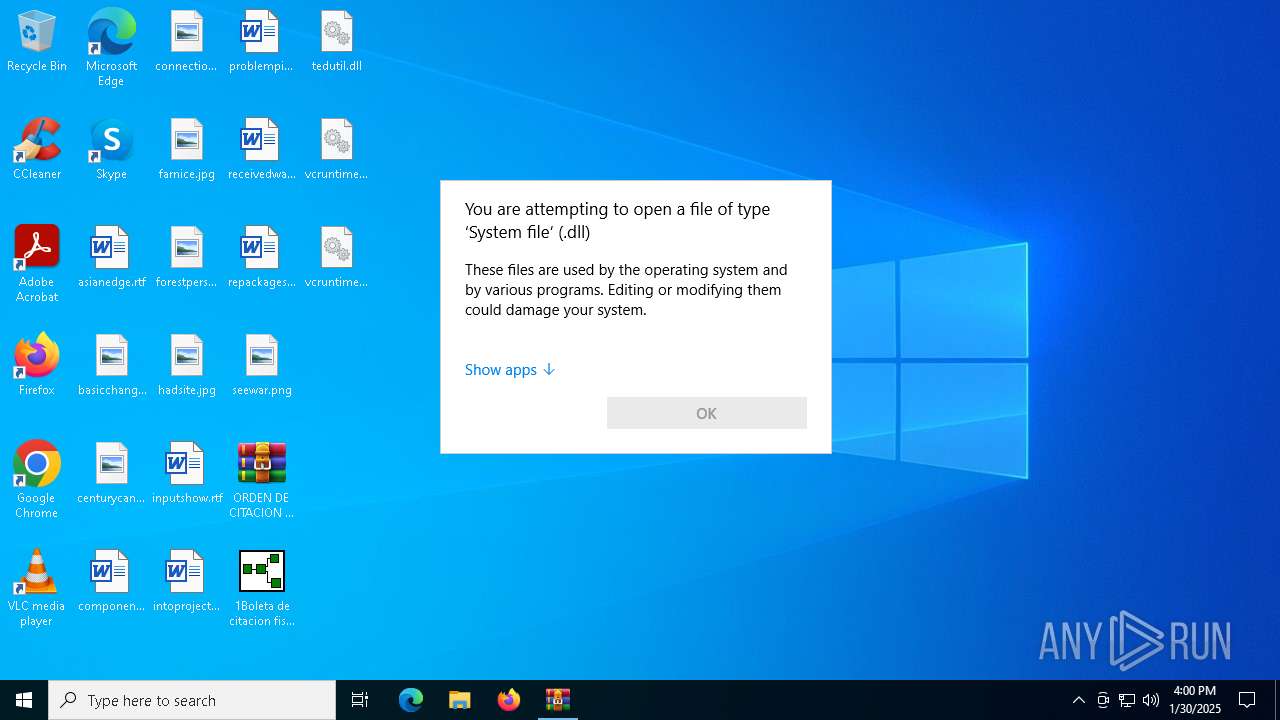
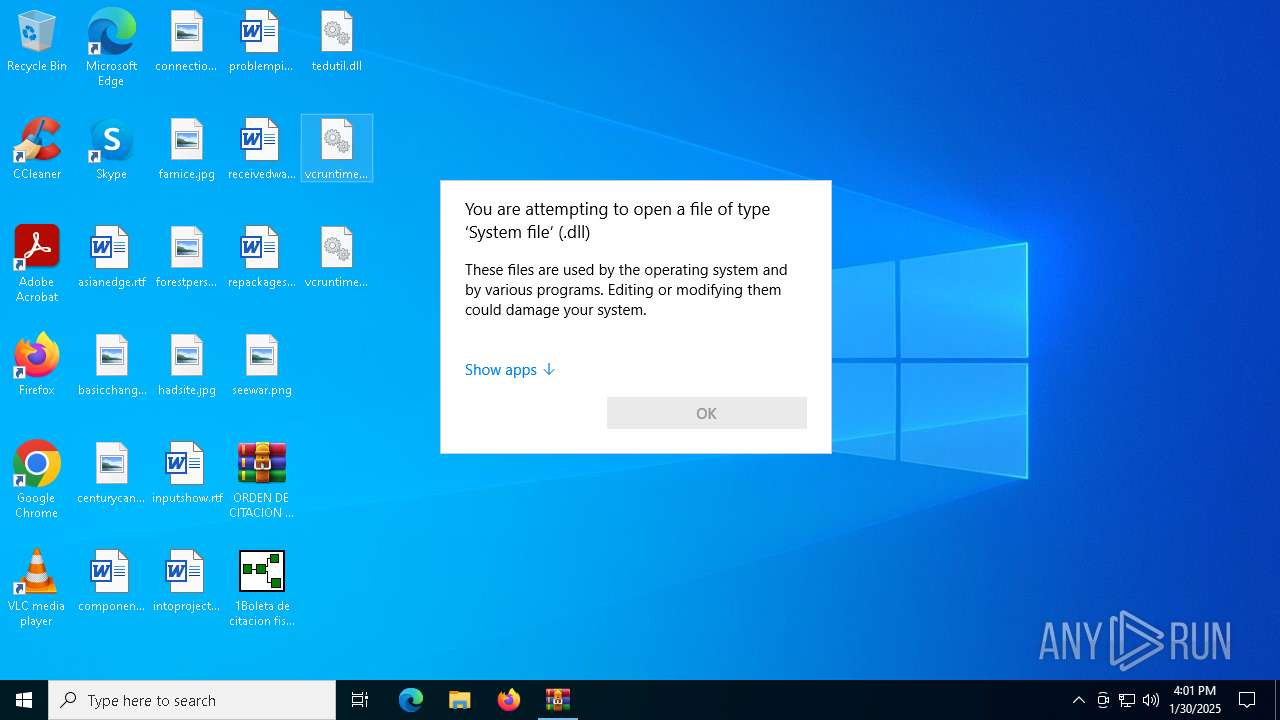
| 3620 | WinRAR.exe | C:\Users\admin\Desktop\vcruntime210.dll | binary | |
MD5:7DD19FE7DDB2AAC4A986746906F9BCD7 | SHA256:4F0D9FAA83C578B9E6FCD57ACEA885320A83AFD45820EC616EE7ADC9705B9F8A | |||
| 3620 | WinRAR.exe | C:\Users\admin\Desktop\tedutil.dll | executable | |
MD5:C8EB780FC226CE6004C0D6F25F1A967E | SHA256:DAD8E518B02D27D4813183AE880BA99184D06805ABF165DCCF9A9DFF0993CE3B | |||
| 4740 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER773.tmp.xml | xml | |
MD5:DD0D4933D77076AF71CD2E4488C17027 | SHA256:8FAC155457A19FEDD90A1D2567A7D595FFEAD9241614852B7DF1772717F335EB | |||
| 4740 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:2F84E3B05CD65F94386D41ADCCD1D87A | SHA256:E47AED1DB02E6F8F6B6B7A190E5E9F30E5875D710122D01D1B2C0B7023B91061 | |||
| 4740 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER696.tmp.dmp | binary | |
MD5:25D1D867975A75EB683B1C49C0FFA39F | SHA256:B21B0D54C41FE6DD59E406B658E7182C9F68A9226508B577187DAFB7F0B98B0A | |||
| 4740 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:680B0331A3CC8FCCE16367586EC7A721 | SHA256:19F1B5D2C7F62663C14D97578411DC610E5F33E6CE4165977314442435F15305 | |||
| 4740 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe.2928.dmp | binary | |
MD5:F40B43F1BC4A76463AE287F349C2F27D | SHA256:B8193A114562D198BCB1DA3A32D0499DD7A800C5D3831B9179456885FD4E763A | |||
| 5748 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\1Boleta de citacion fiscalia detalle radicado#002325-996596-PDF.exe(1).2928.dmp | binary | |
MD5:C4818915DC790A2C8EA169AB98568711 | SHA256:250B839C1358BBEDE7C66800E6F6840717C9F24A218A2356838C208D121BD565 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
20
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6208 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7156 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4740 | WerFault.exe | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4740 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7156 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
3508 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7156 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
4052 | AddInProcess32.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
4052 | AddInProcess32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |