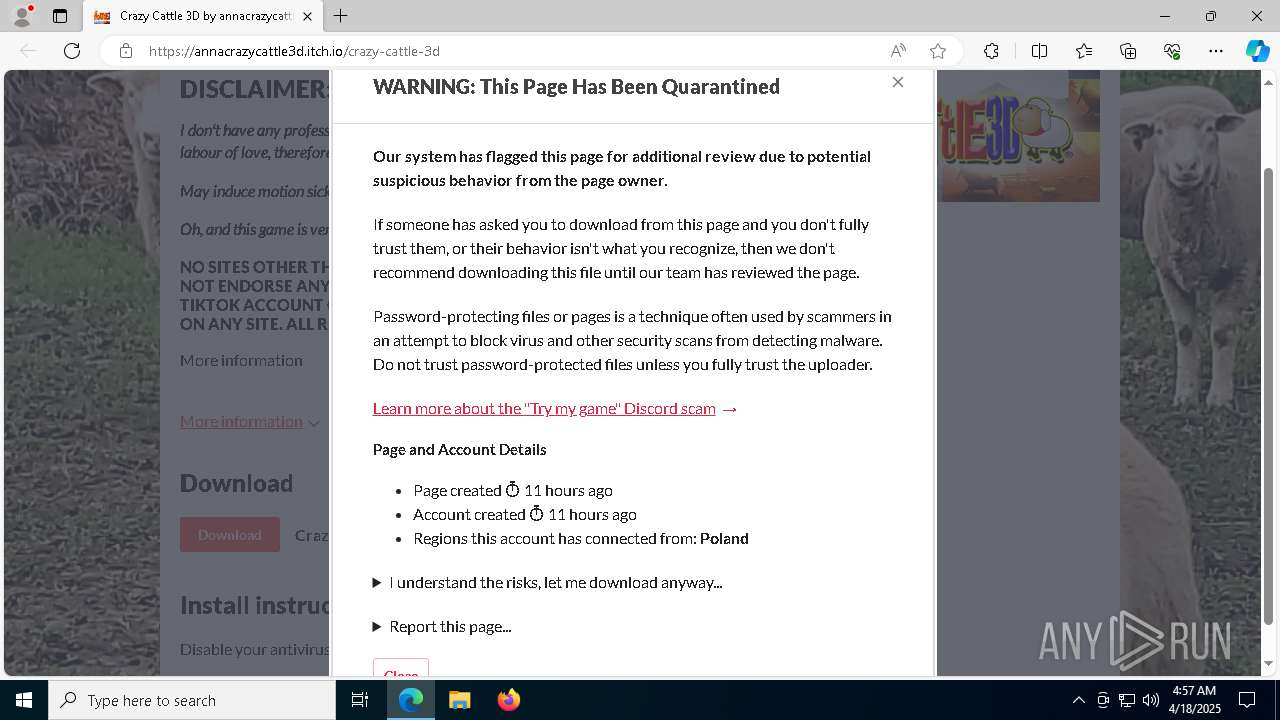
| URL: | https://annacrazycattle3d.itch.io/crazy-cattle-3d |
| Full analysis: | https://app.any.run/tasks/740cc4e5-0fc5-41bf-815b-287c6890b939 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
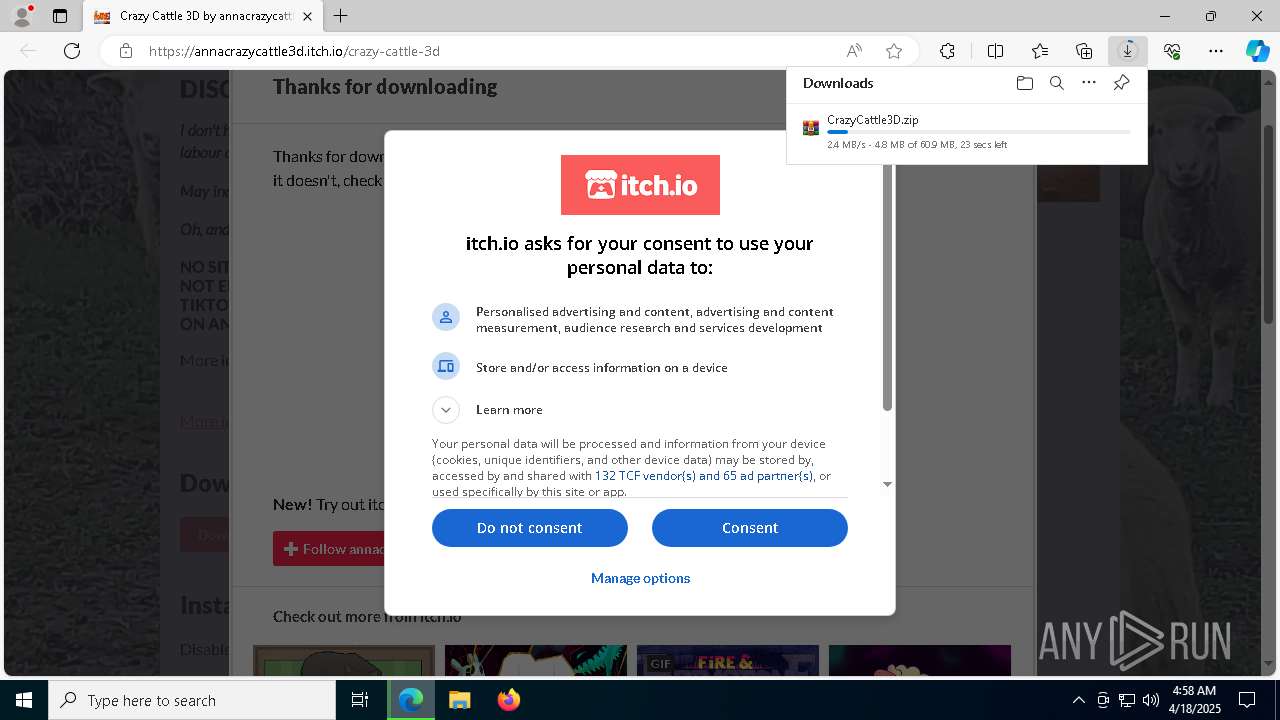
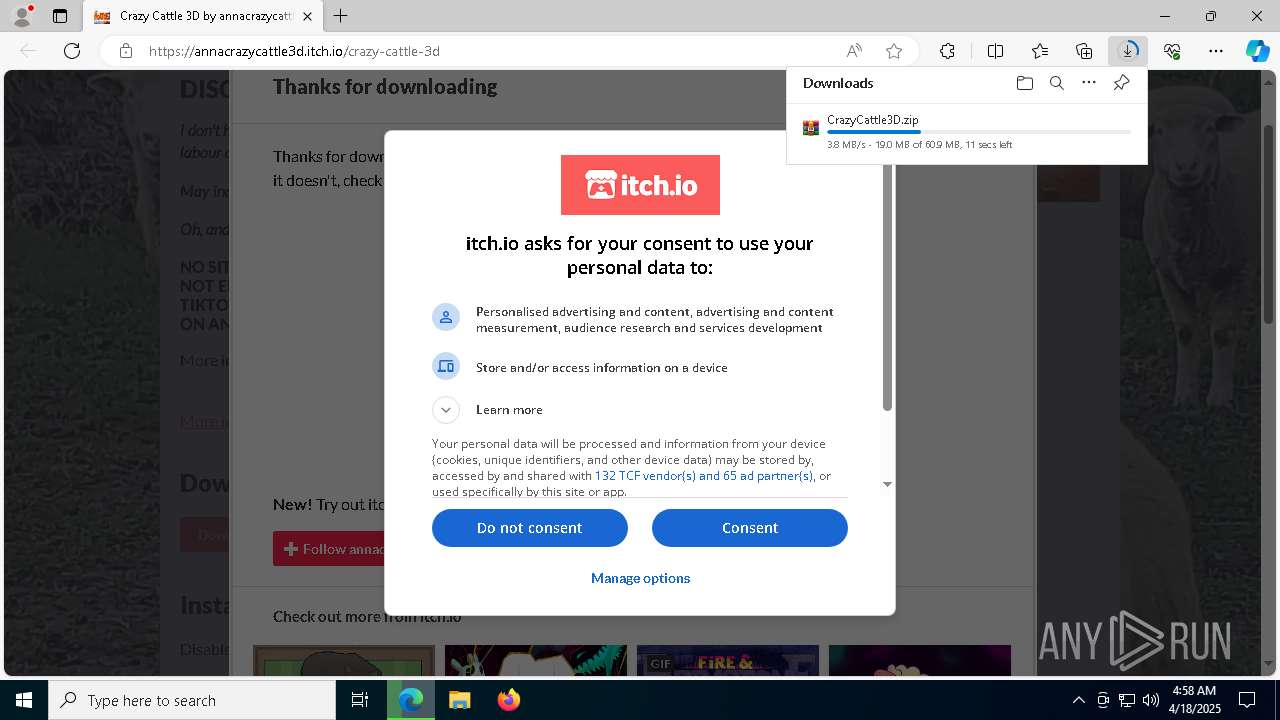
| Analysis date: | April 18, 2025, 04:57:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DC07E429377568B5EF1CD3E58CDC43EF |
| SHA1: | 3F62A2E2625BBE9DC3E616D6B1FE01B43C2D35FC |
| SHA256: | ED8CBE57A8EE9F237AEC1AEB7657F393B490EDFC4598D05545A951F83ADB2404 |
| SSDEEP: | 3:N8dMJA9gZ5X4kB:263T |
MALICIOUS
Executing a file with an untrusted certificate
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 6564)
- CrazyCattle3D.exe (PID: 4212)
- CrazyCattle3D.exe (PID: 5868)
BlankGrabber has been detected
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 4212)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7680)
Changes Windows Defender settings
- cmd.exe (PID: 3024)
- cmd.exe (PID: 872)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 8724)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7680)
Changes settings for real-time protection
- powershell.exe (PID: 7680)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7680)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7680)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 3024)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7680)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7680)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 872)
- CrazyCattle3D.exe (PID: 5868)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 8724)
Create files in the Startup directory
- CrazyCattle3D.exe (PID: 5868)
Steals credentials from Web Browsers
- CrazyCattle3D.exe (PID: 5868)
Actions looks like stealing of personal data
- CrazyCattle3D.exe (PID: 5868)
Bypass execution policy to execute commands
- powershell.exe (PID: 8428)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 9208)
SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6828)
- CrazyCattle3D.exe (PID: 6564)
Starts a Microsoft application from unusual location
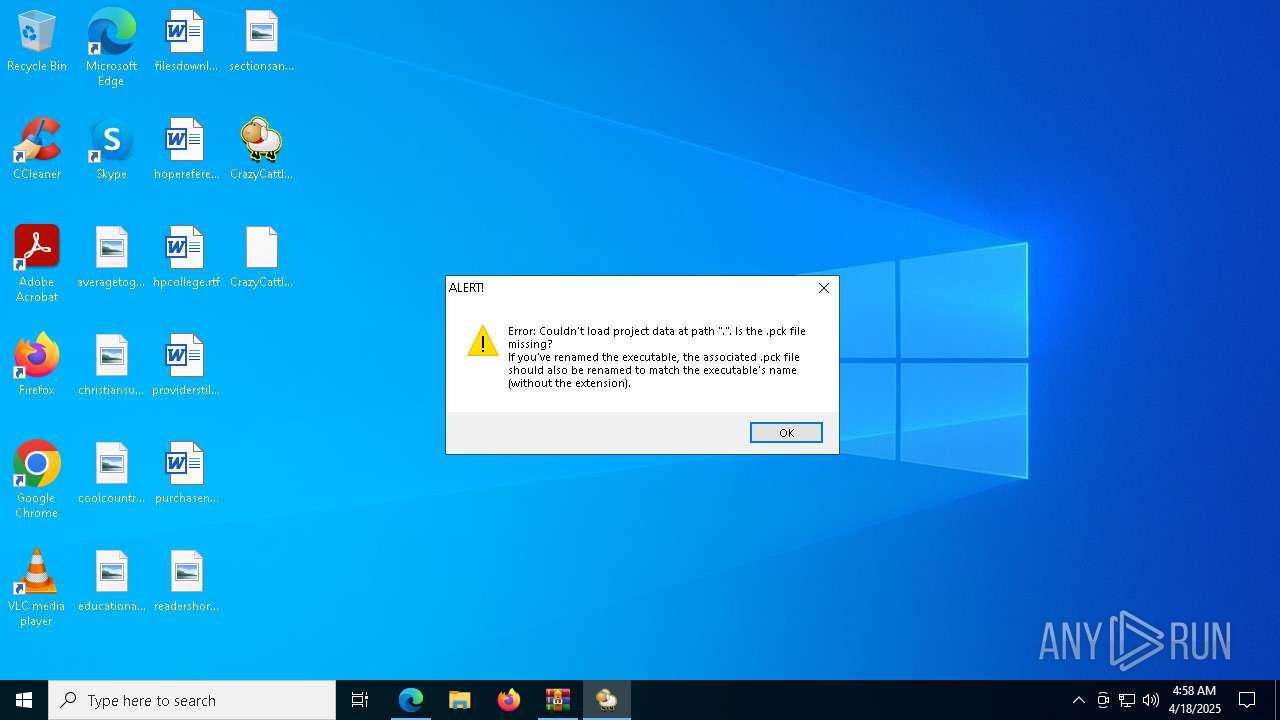
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 4212)
- CrazyCattle3D.exe (PID: 5868)
- CrazyCattle3D.exe (PID: 6564)
Process drops python dynamic module
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 4212)
The process drops C-runtime libraries
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 4212)
Executable content was dropped or overwritten
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 4212)
Process drops legitimate windows executable
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 4212)
Application launched itself
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 6564)
- CrazyCattle3D.exe (PID: 4212)
Reads the date of Windows installation
- CrazyCattle3D.exe (PID: 6564)
Found strings related to reading or modifying Windows Defender settings
- CrazyCattle3D.exe (PID: 5868)
Script disables Windows Defender's IPS
- cmd.exe (PID: 3024)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 3024)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3024)
- cmd.exe (PID: 872)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 8988)
- cmd.exe (PID: 9208)
Starts CMD.EXE for commands execution
- CrazyCattle3D.exe (PID: 5868)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 872)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 8724)
Get information on the list of running processes
- CrazyCattle3D.exe (PID: 5868)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 8876)
- cmd.exe (PID: 8856)
- cmd.exe (PID: 9016)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5036)
- cmd.exe (PID: 8972)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 8044)
Checks for external IP
- svchost.exe (PID: 2196)
- CrazyCattle3D.exe (PID: 5868)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 8524)
- cmd.exe (PID: 8624)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 8580)
- WMIC.exe (PID: 8676)
The executable file from the user directory is run by the CMD process
- bound.exe (PID: 8256)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 9140)
Starts application with an unusual extension
- cmd.exe (PID: 8712)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 9052)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 9208)
Base64-obfuscated command line is found
- cmd.exe (PID: 9208)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 9208)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 8360)
INFO
Checks supported languages
- identity_helper.exe (PID: 7884)
- ShellExperienceHost.exe (PID: 6828)
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 6564)
- CrazyCattle3D.exe (PID: 4212)
- CrazyCattle3D.exe (PID: 5868)
- bound.exe (PID: 8256)
- tree.com (PID: 5624)
- tree.com (PID: 8500)
- tree.com (PID: 8508)
Application launched itself
- msedge.exe (PID: 7216)
Reads the computer name
- ShellExperienceHost.exe (PID: 6828)
- identity_helper.exe (PID: 7884)
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 6564)
- CrazyCattle3D.exe (PID: 4212)
- CrazyCattle3D.exe (PID: 5868)
- bound.exe (PID: 8256)
Reads Environment values
- identity_helper.exe (PID: 7884)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7216)
Manual execution by a user
- CrazyCattle3D.exe (PID: 8044)
The sample compiled with english language support
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 4212)
Create files in a temporary directory
- CrazyCattle3D.exe (PID: 8044)
- CrazyCattle3D.exe (PID: 6564)
- CrazyCattle3D.exe (PID: 4212)
- CrazyCattle3D.exe (PID: 5868)
Process checks computer location settings
- CrazyCattle3D.exe (PID: 6564)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8044)
- WMIC.exe (PID: 8580)
- WMIC.exe (PID: 8676)
- WMIC.exe (PID: 8360)
Creates files in the program directory
- CrazyCattle3D.exe (PID: 5868)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 7200)
- powershell.exe (PID: 7212)
The Powershell gets current clipboard
- powershell.exe (PID: 8448)
Checks the directory tree
- tree.com (PID: 5624)
- tree.com (PID: 8500)
- tree.com (PID: 8508)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 7200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
252
Monitored processes
118
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\Desktop\CrazyCattle3D.exe'" | C:\Windows\System32\cmd.exe | — | CrazyCattle3D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7360 --field-trial-handle=2312,i,15542563615480731544,16743258239285486202,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7316 --field-trial-handle=2312,i,15542563615480731544,16743258239285486202,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\Windows\System32\SystemSettingsBroker.exe -Embedding | C:\Windows\System32\SystemSettingsBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Settings Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
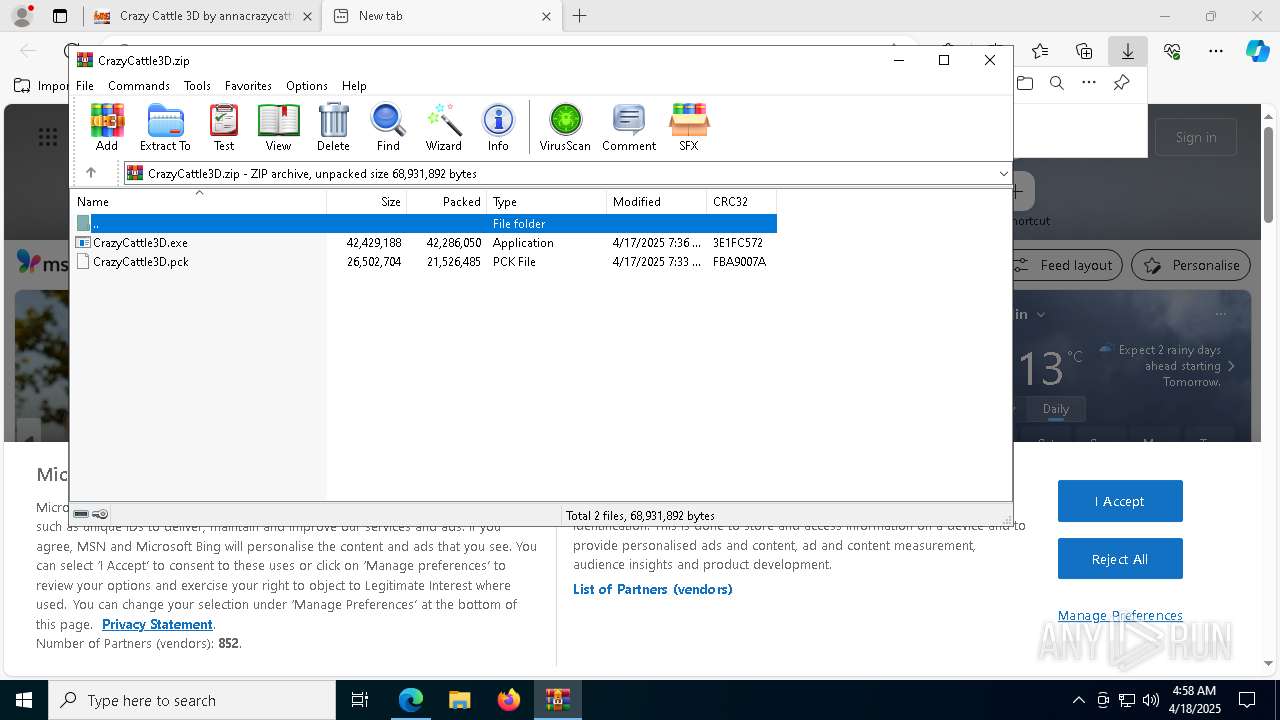
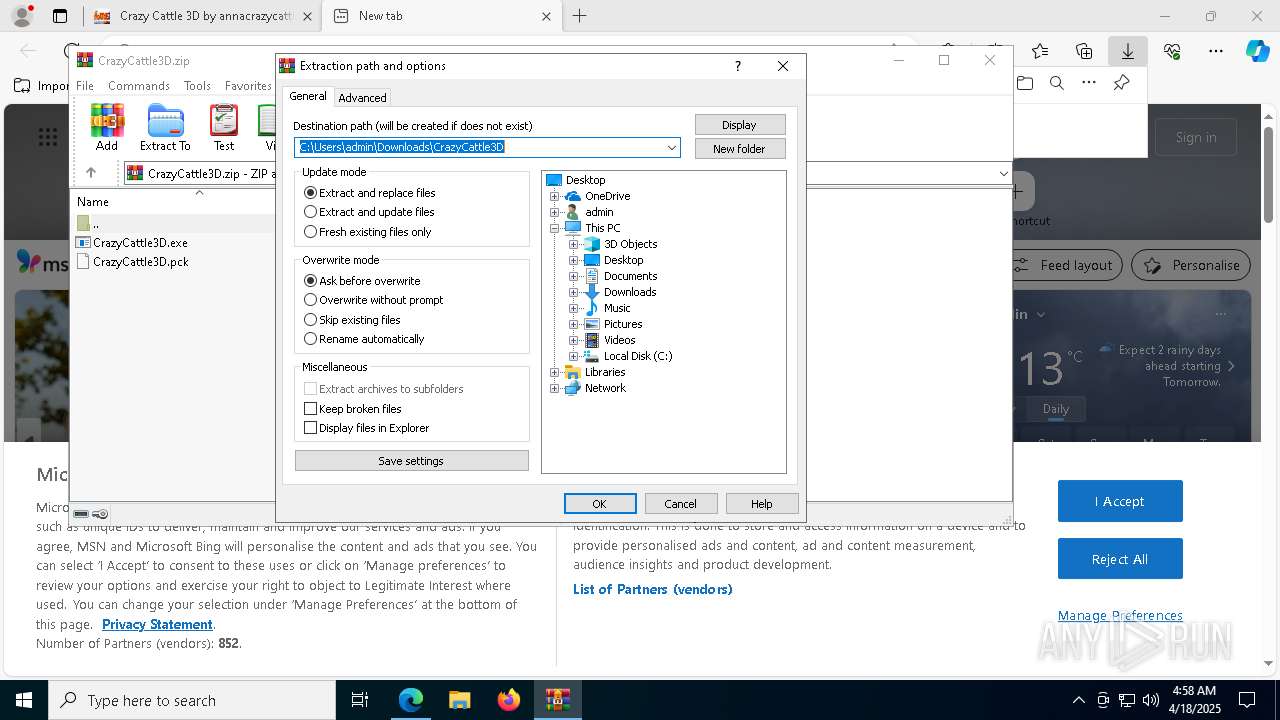
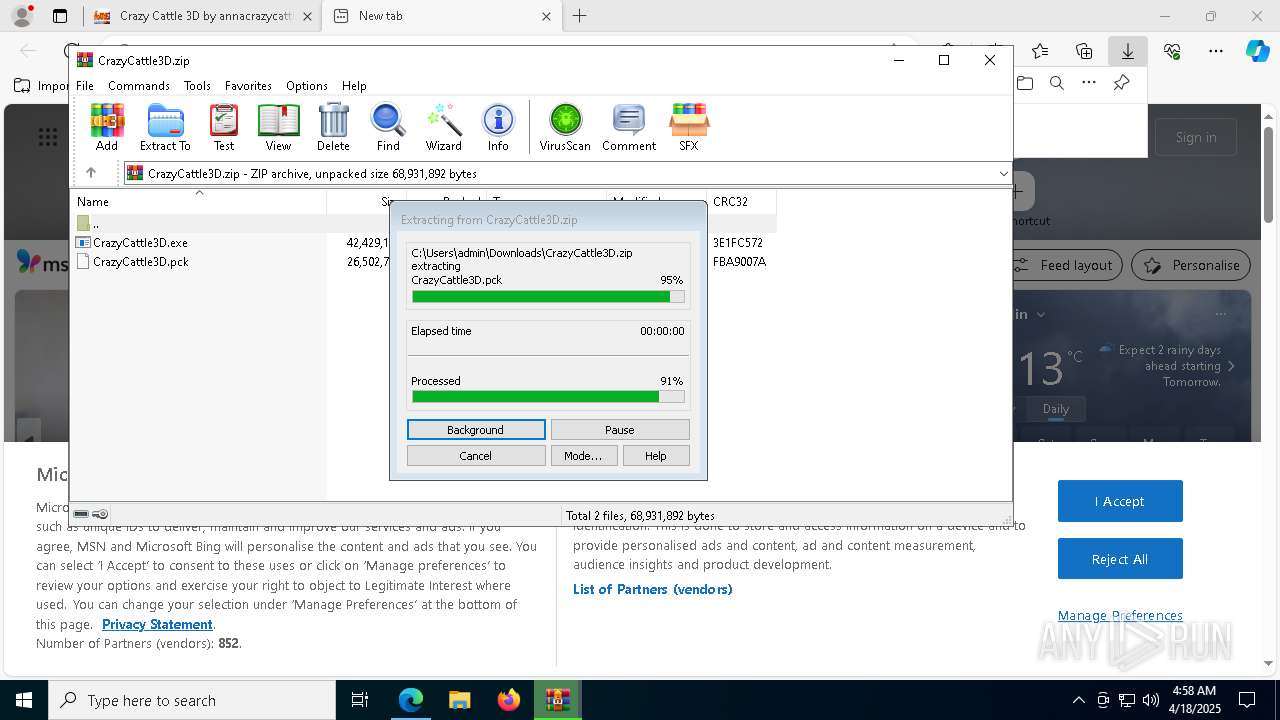
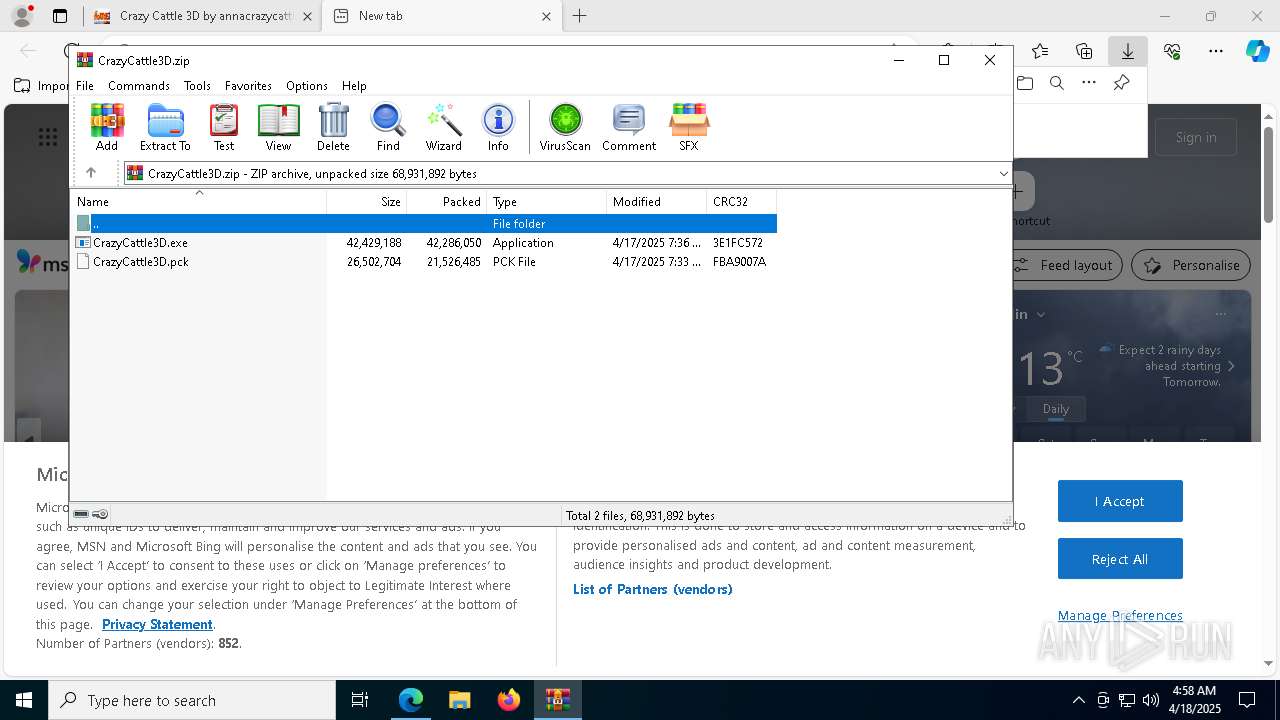
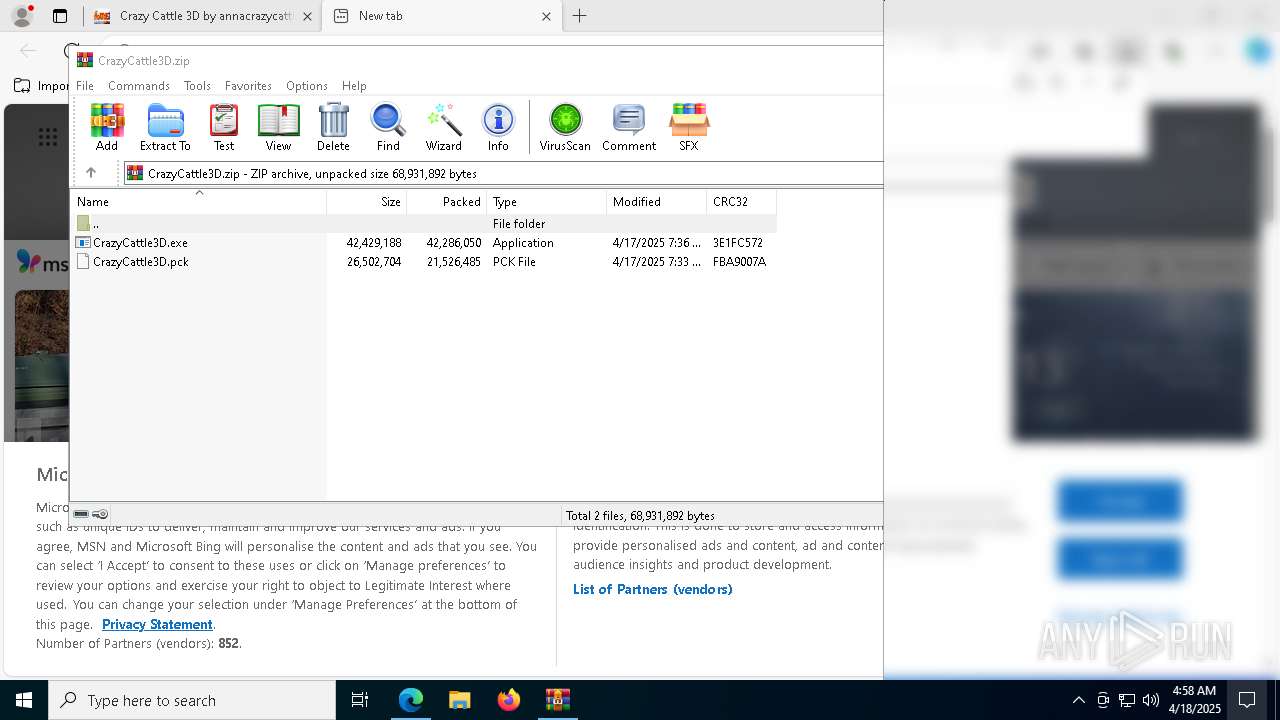
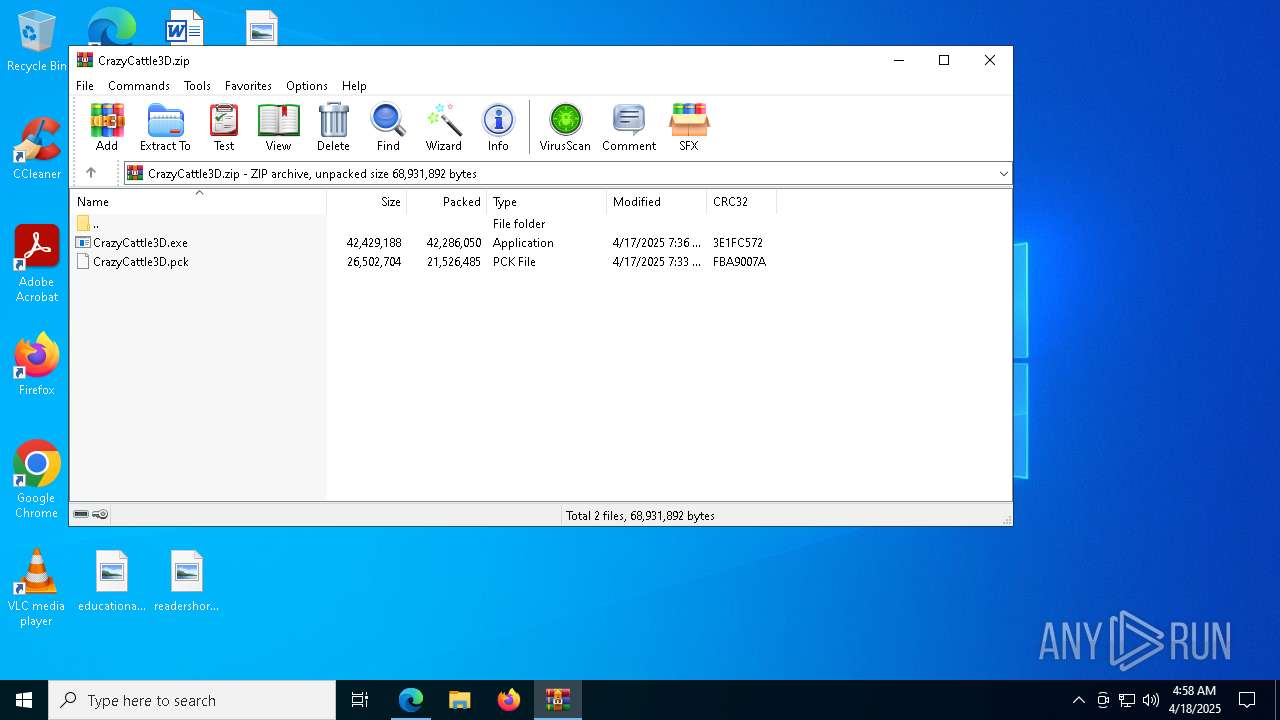
| 1616 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\CrazyCattle3D.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1672 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\bound.exe'" | C:\Windows\System32\cmd.exe | — | CrazyCattle3D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5484 --field-trial-handle=2312,i,15542563615480731544,16743258239285486202,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
42 112
Read events
42 042
Write events
57
Delete events
13
Modification events
| (PID) Process: | (2384) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2384) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2384) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2384) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2384) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2384) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7216) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
157
Suspicious files
496
Text files
143
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc7c.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc7c.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bc7c.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc8b.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bc8b.TMP | — | |
MD5:— | SHA256:— | |||
| 7216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
115
DNS requests
120
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | — | 471 b | whitelisted |
3896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
5868 | CrazyCattle3D.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | US | text | 6 b | whitelisted |
3896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7216 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7444 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7444 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7444 | msedge.exe | 45.79.115.66:443 | annacrazycattle3d.itch.io | Linode, LLC | US | whitelisted |
7444 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
annacrazycattle3d.itch.io |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
static.itch.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7444 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
7444 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
5868 | CrazyCattle3D.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |