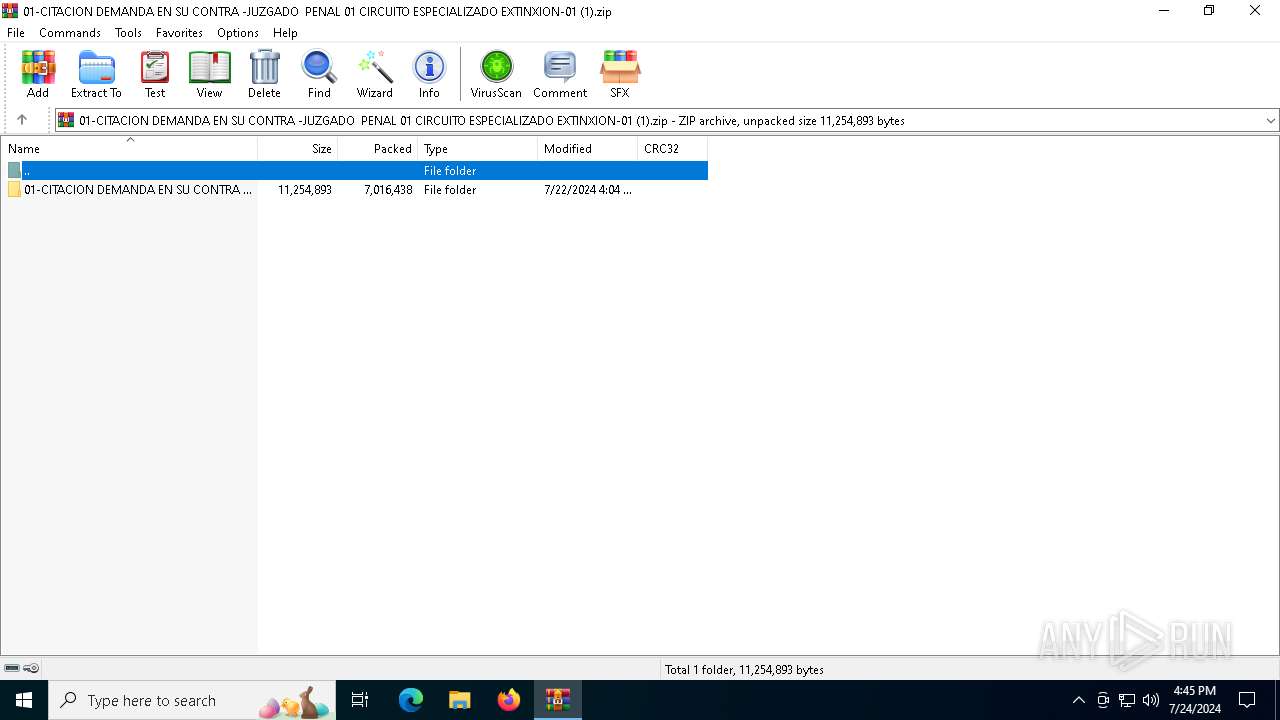
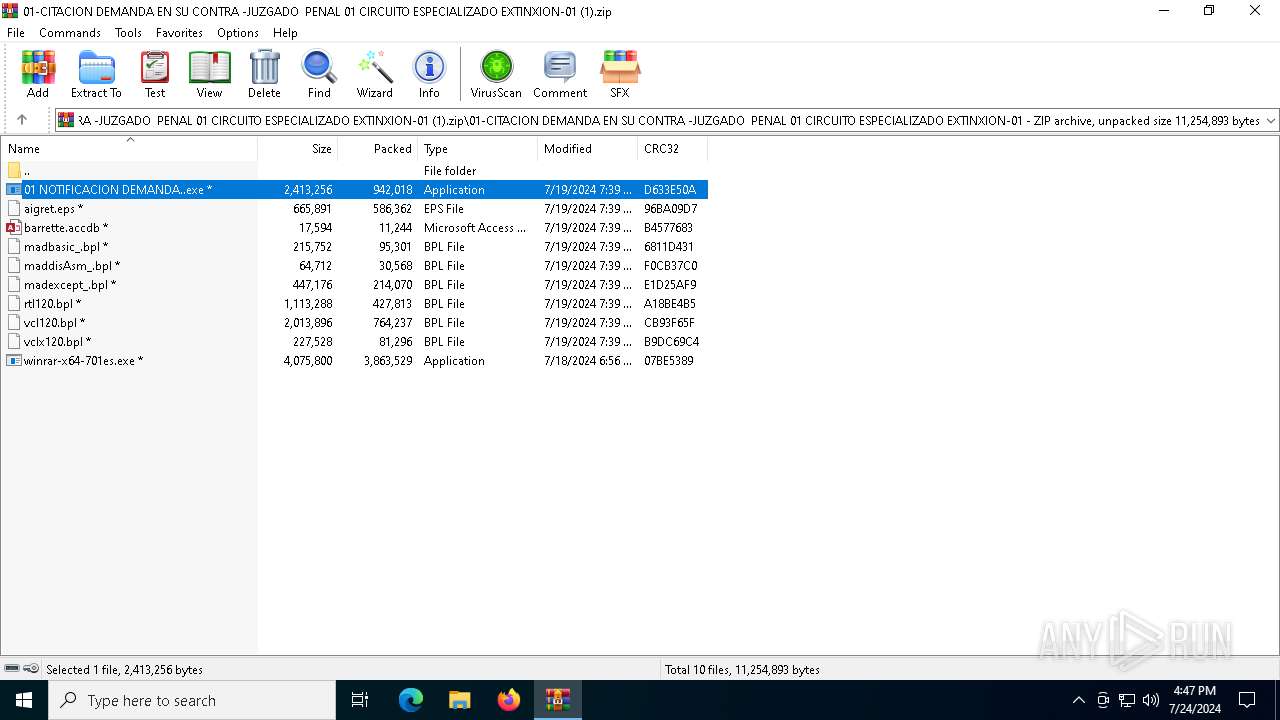
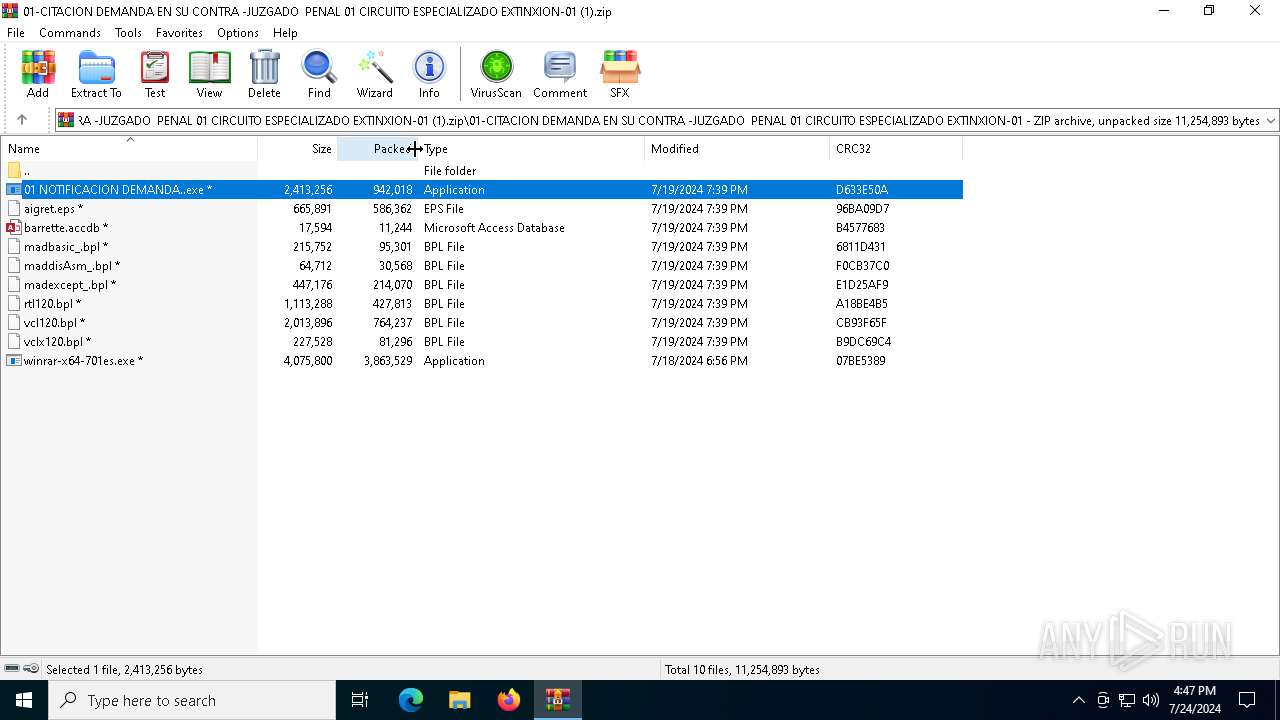
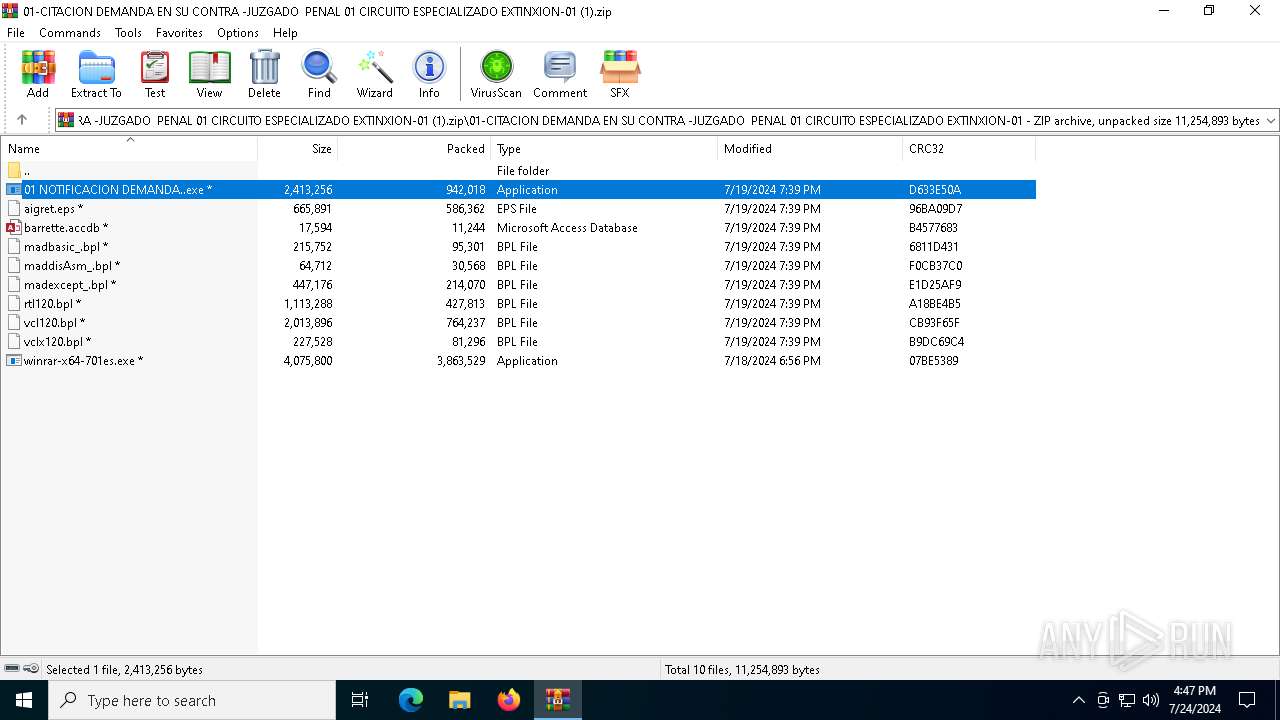
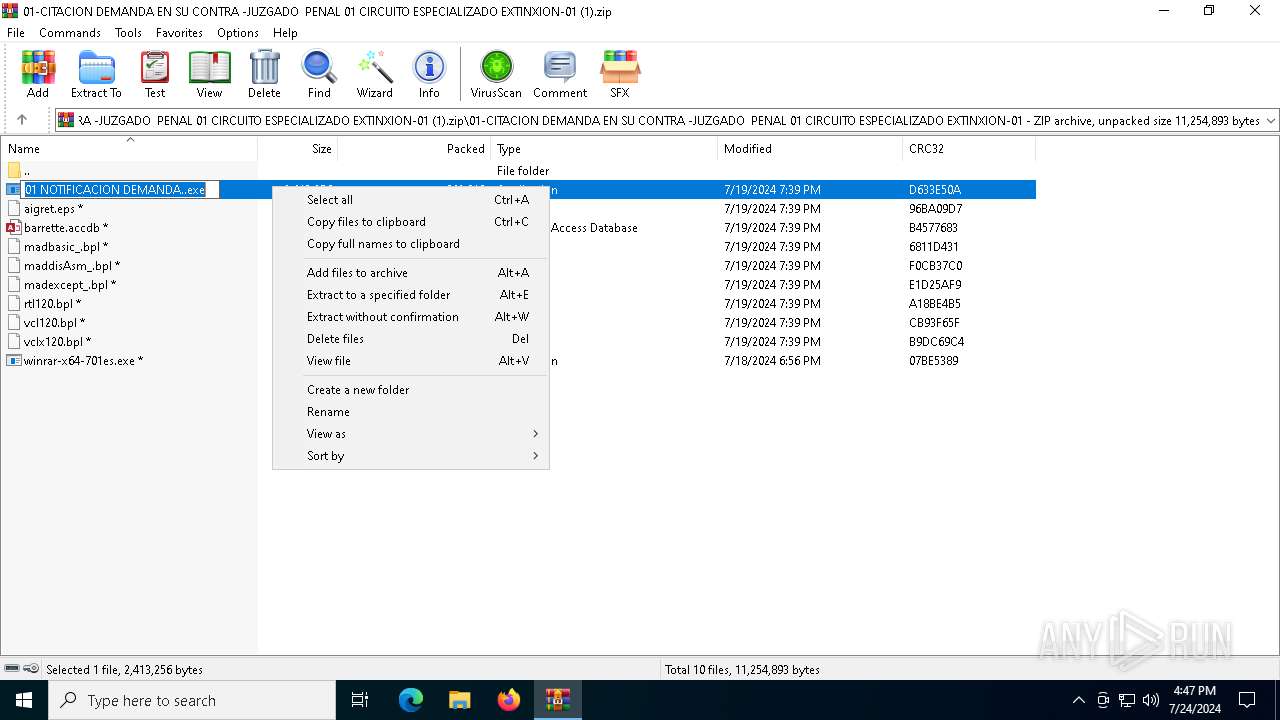
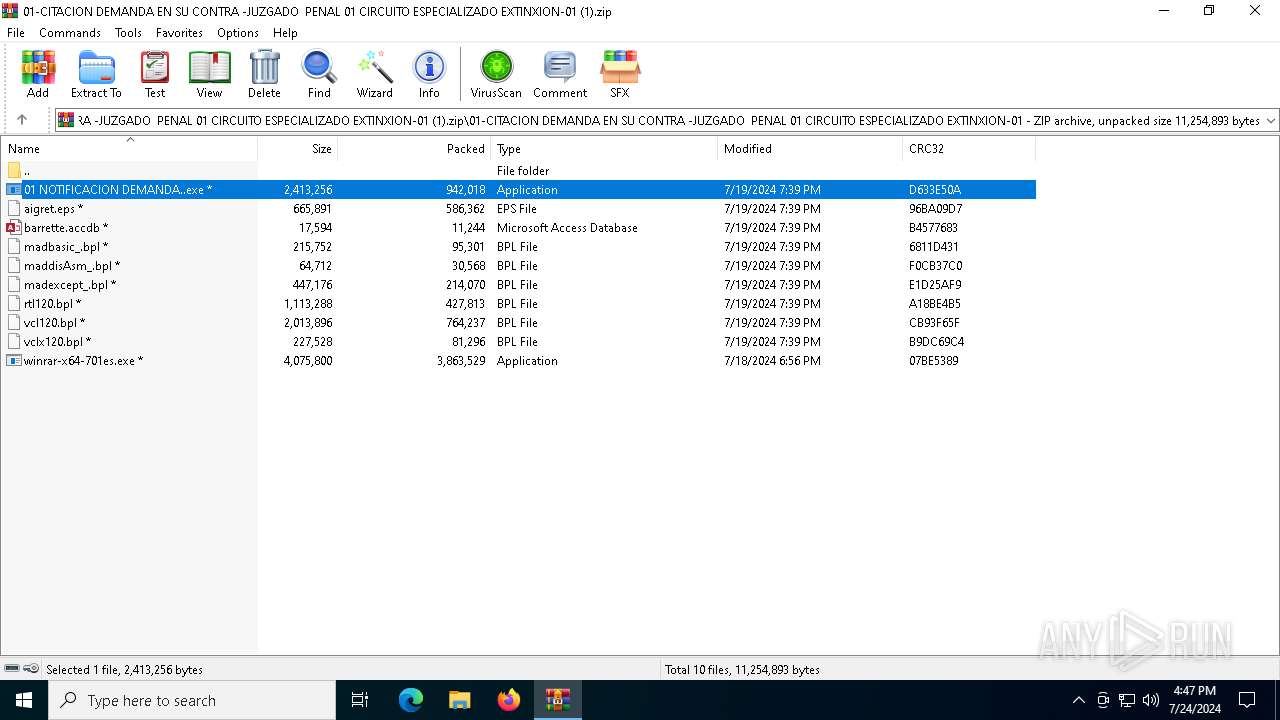
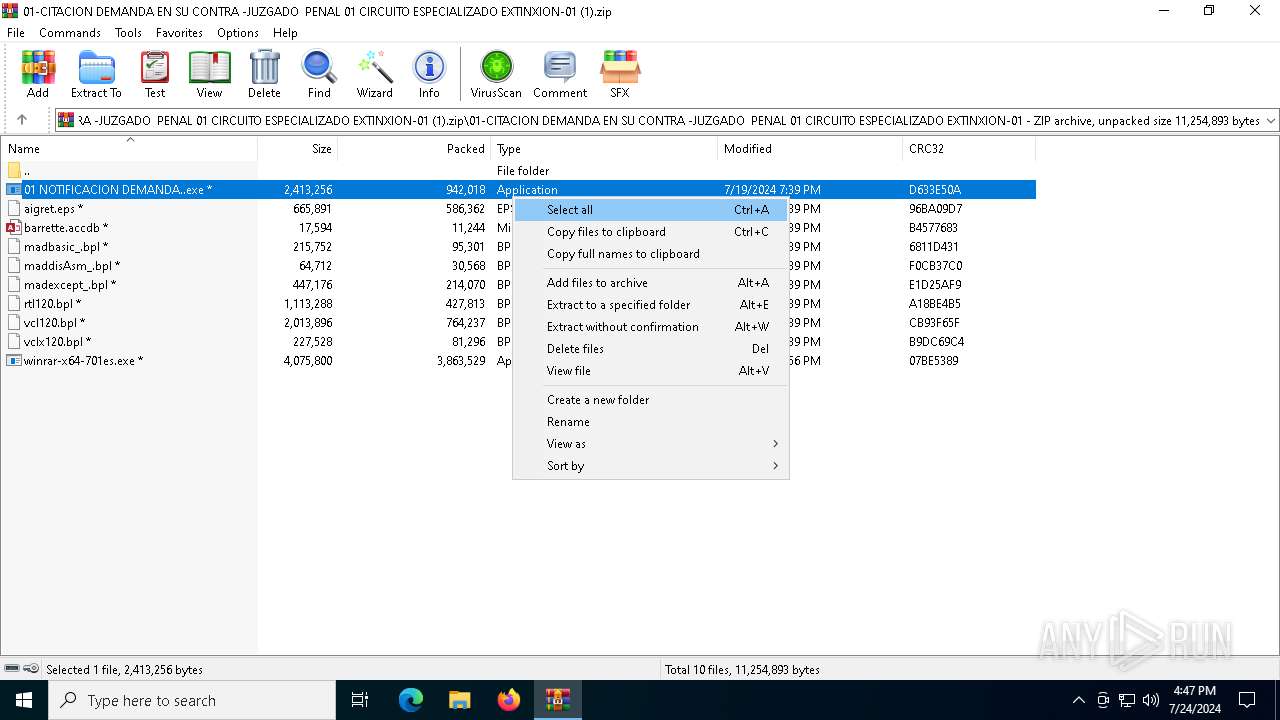
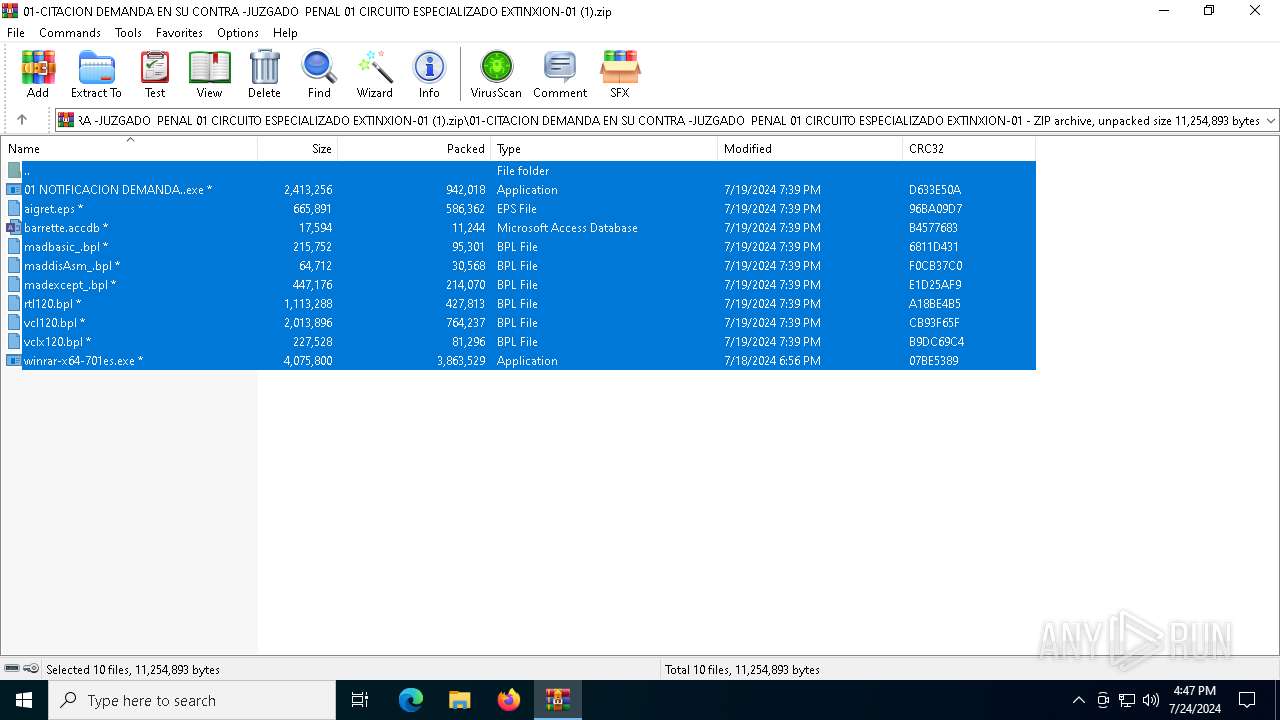
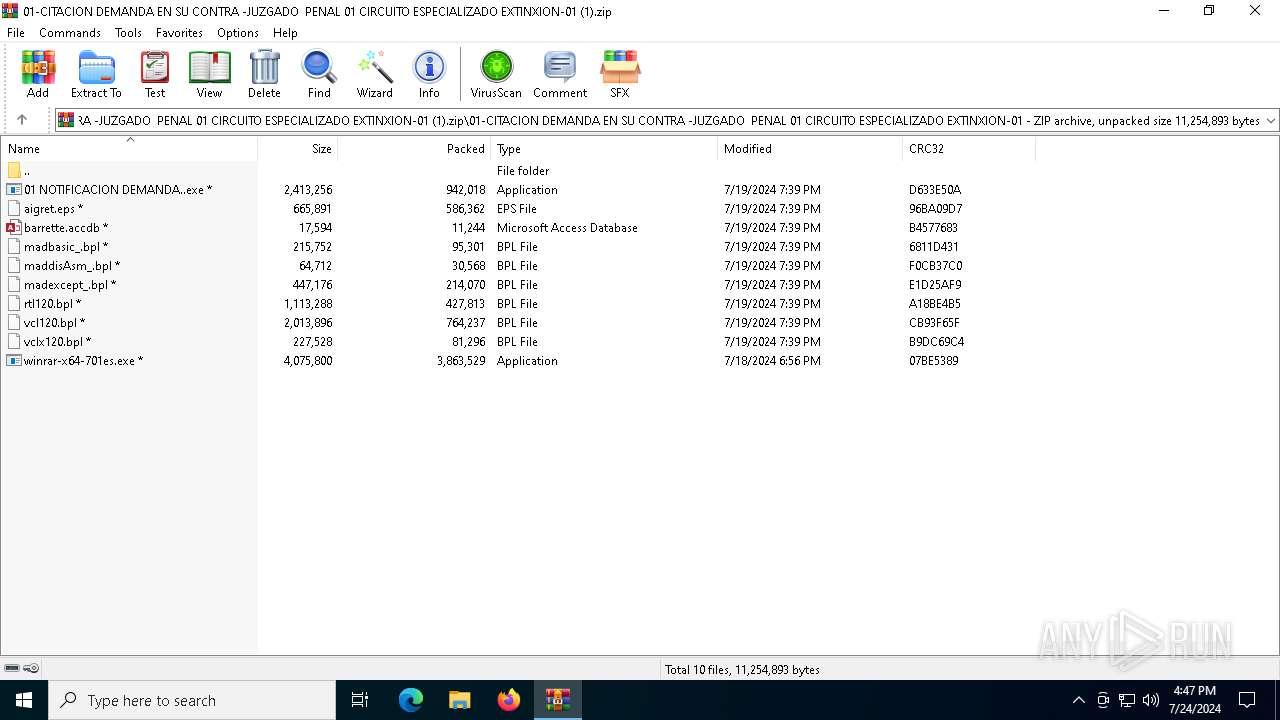
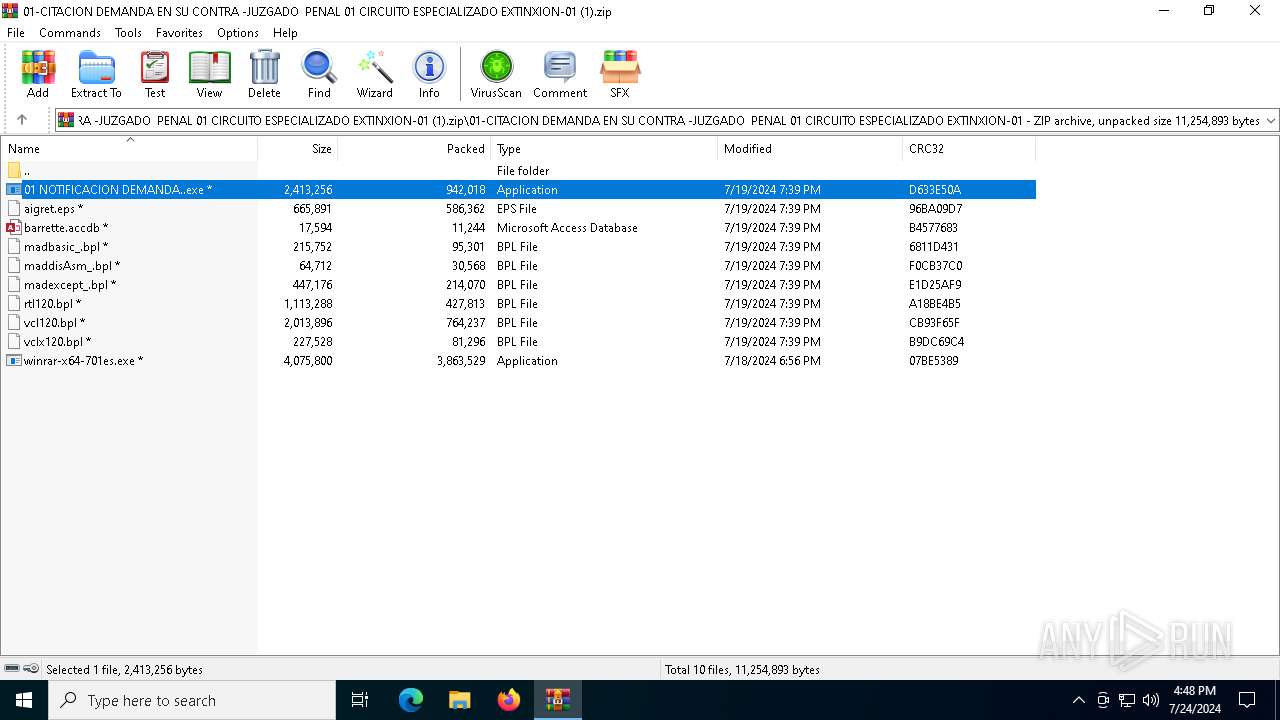
| File name: | 01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01 (1).zip |
| Full analysis: | https://app.any.run/tasks/42950214-9a4f-40a0-8246-7b0b404bbf19 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | July 24, 2024, 16:45:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | DA0F823B67BC093B75D381F2A105ECB6 |
| SHA1: | 11E82222F4070FBADC8C4C2F194BA65D9FA60AC5 |
| SHA256: | ED88B5C4A8BE75F5DA0400817A9514BDCB38E602AA3FE463D39CEC523DCD3268 |
| SSDEEP: | 98304:kInWxz+YsV+RTsLnKdoRRJJx4U1HEbuzDPPlEvFE8MQ+vA61bUCRFSwFypndZQB4:tVR77Ji4VDFk6gVYG |
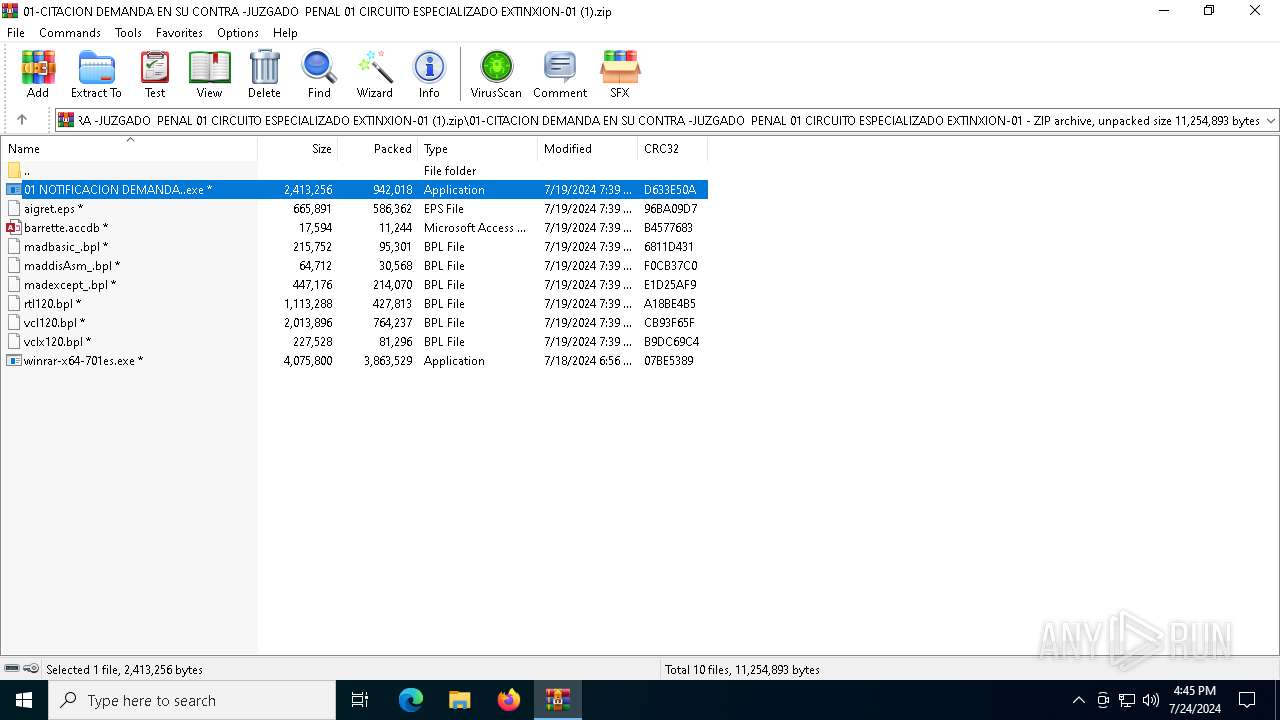
MALICIOUS
ASYNCRAT has been detected (SURICATA)
- MSBuild.exe (PID: 2872)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 2872)
ASYNCRAT has been detected (MUTEX)
- MSBuild.exe (PID: 2872)
ASYNCRAT has been detected (YARA)
- MSBuild.exe (PID: 2872)
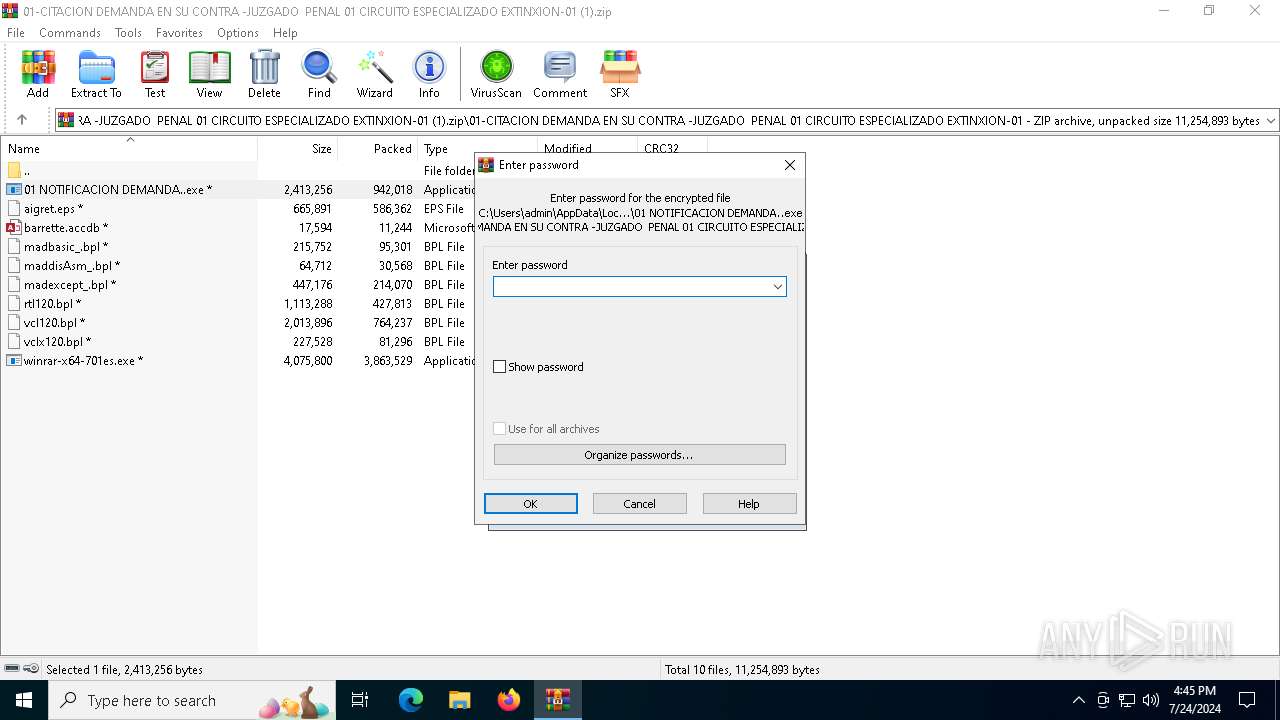
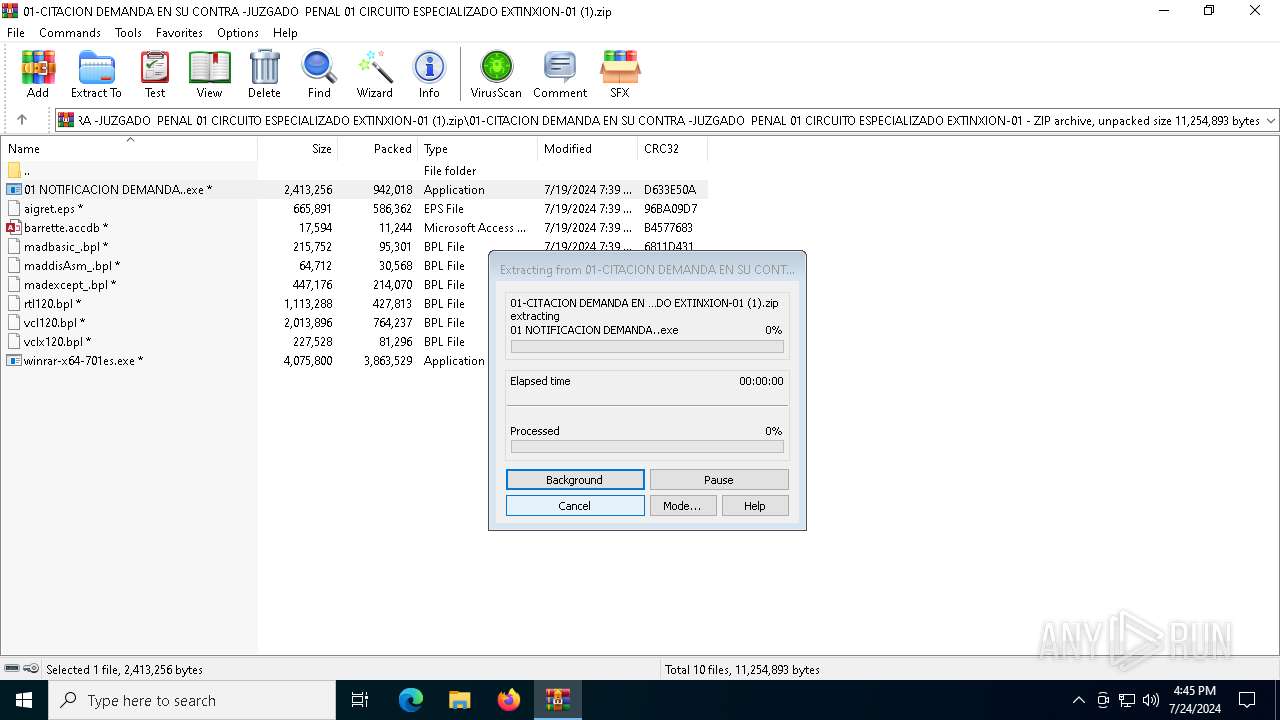
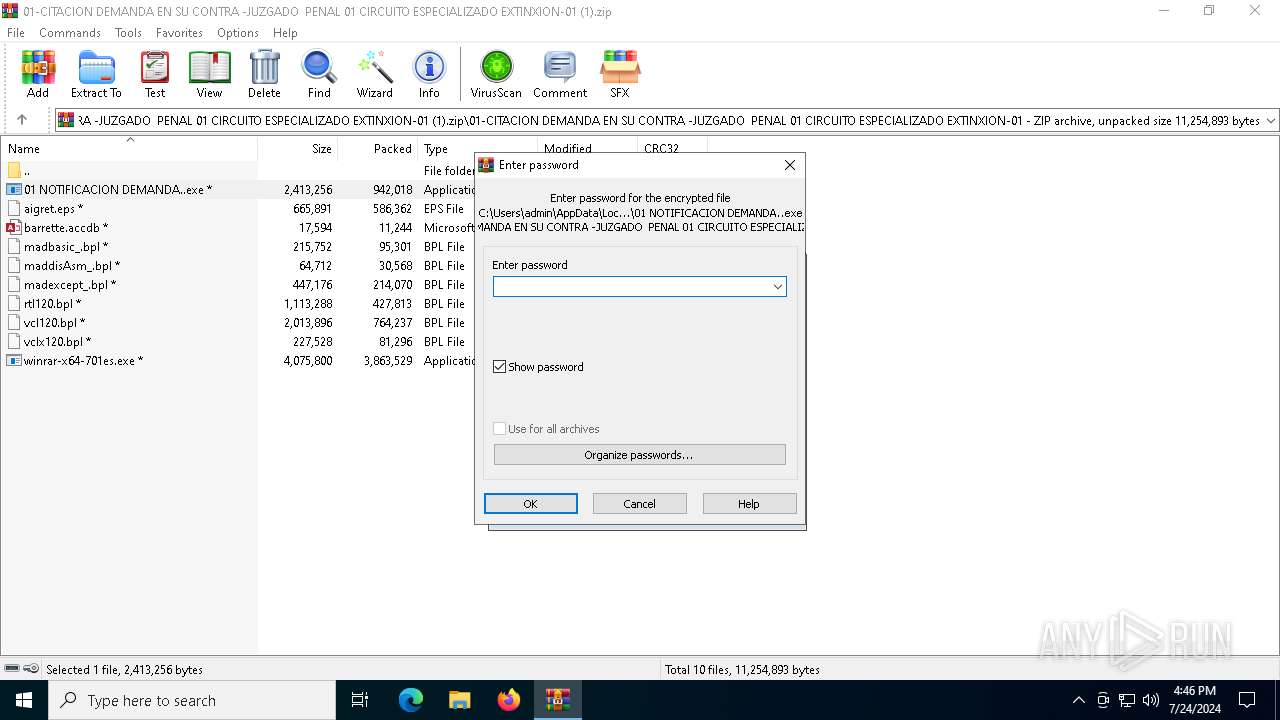
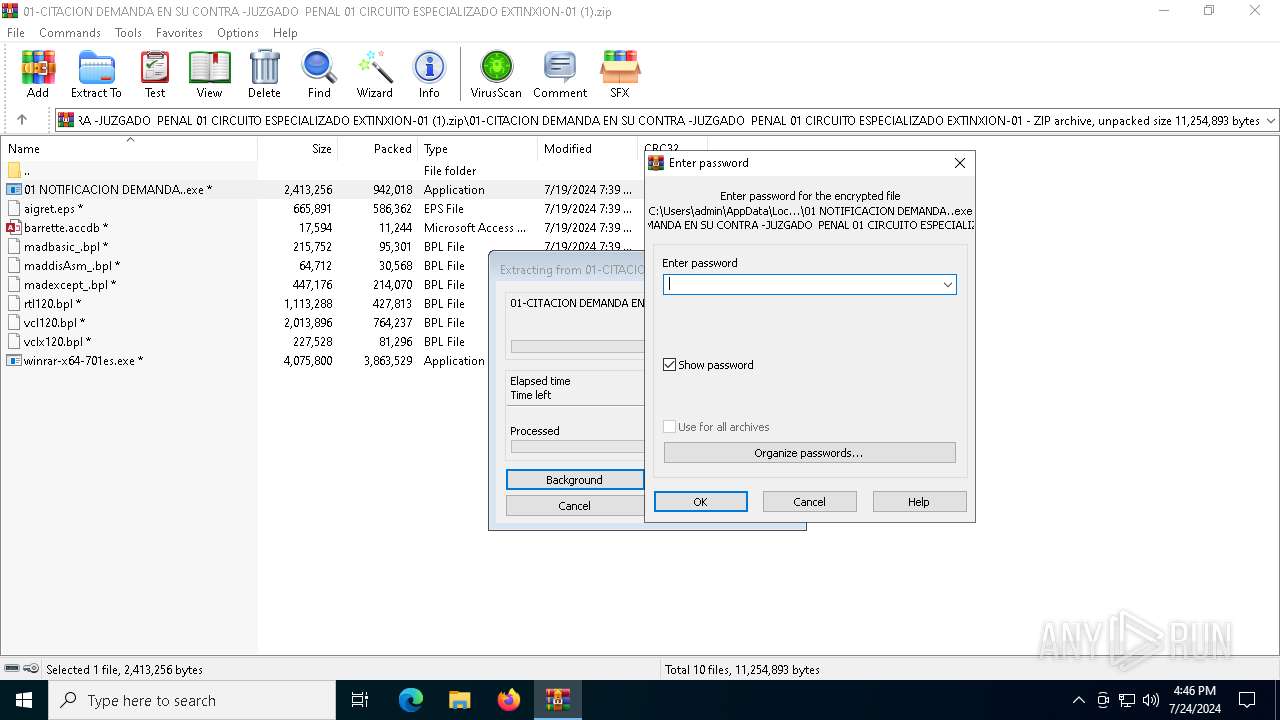
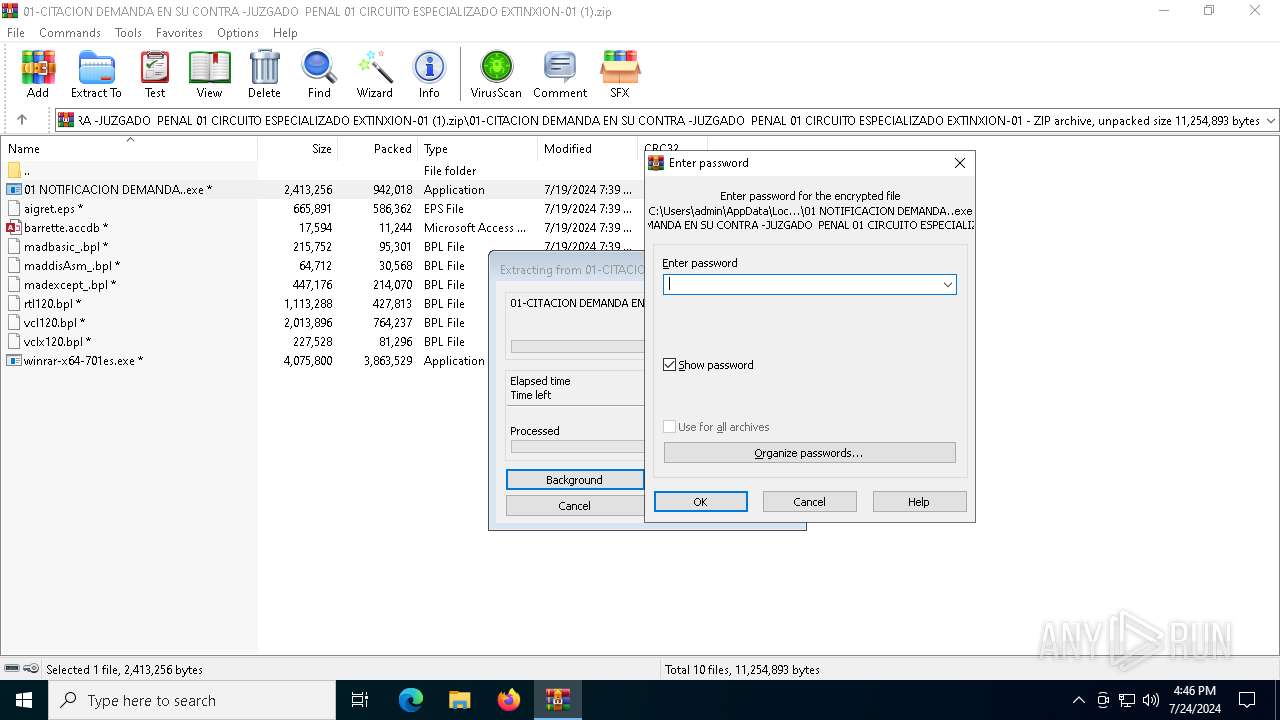
Drops the executable file immediately after the start
- 01 NOTIFICACION DEMANDA..exe (PID: 4104)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4188)
Starts CMD.EXE for commands execution
- 01 NOTIFICACION DEMANDA..exe (PID: 4104)
Connects to unusual port
- MSBuild.exe (PID: 2872)
Executable content was dropped or overwritten
- 01 NOTIFICACION DEMANDA..exe (PID: 4104)
Contacting a server suspected of hosting an CnC
- MSBuild.exe (PID: 2872)
INFO
Creates files or folders in the user directory
- 01 NOTIFICACION DEMANDA..exe (PID: 4104)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4188)
Reads the computer name
- 01 NOTIFICACION DEMANDA..exe (PID: 4104)
- TextInputHost.exe (PID: 6548)
- MSBuild.exe (PID: 2872)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4188)
Reads Environment values
- MSBuild.exe (PID: 2872)
Create files in a temporary directory
- 01 NOTIFICACION DEMANDA..exe (PID: 4104)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 2872)
Checks supported languages
- MSBuild.exe (PID: 2872)
- TextInputHost.exe (PID: 6548)
- 01 NOTIFICACION DEMANDA..exe (PID: 4104)
Reads the software policy settings
- MSBuild.exe (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(2872) MSBuild.exe
C2 (1)melo2024.kozow.com
Ports (1)8000
Version| CRACKED BY https://t.me/xworm_v2
Options
AutoRunfalse
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz...
Server_SignatureVDW90fot0UJzaNczUi0kDNApIr64dBioK/nQB9y7Rd4q0FrktdyhSFDErXPfi/Zv4rPByVXnBqci278oG8gV3+4cXIVpfkR/2UTL/5fU1P9Dfack2HTVz6T+MHXHn+RCdX7vIhK/tXRasVMoWCJKUsNlzrsXtHtu22EHiLSv+c51ch5zBK9anp3vPjKcb6Mz6K5lQGqrGxAlLvwx5/jjKJkCnUE7Bj8nGXsa8zrIBQYot50U8L7ZrMy4zOdruFDGUjQkuJNTIAkb7oh4zs5OWgA30M9thKnaCPS0MaLsvQ66...
Keys
AESef3a6e00a19a29644d1a0e1b56039abc50b3764a83e580ef7441c861f069fe20
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:22 11:04:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | 01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01/ |
Total processes
141
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2872 | C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(2872) MSBuild.exe C2 (1)melo2024.kozow.com Ports (1)8000 Version| CRACKED BY https://t.me/xworm_v2 Options AutoRunfalse MutexAsyncMutex_6SI8OkPnk InstallFolder%AppData% Certificates Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz... Server_SignatureVDW90fot0UJzaNczUi0kDNApIr64dBioK/nQB9y7Rd4q0FrktdyhSFDErXPfi/Zv4rPByVXnBqci278oG8gV3+4cXIVpfkR/2UTL/5fU1P9Dfack2HTVz6T+MHXHn+RCdX7vIhK/tXRasVMoWCJKUsNlzrsXtHtu22EHiLSv+c51ch5zBK9anp3vPjKcb6Mz6K5lQGqrGxAlLvwx5/jjKJkCnUE7Bj8nGXsa8zrIBQYot50U8L7ZrMy4zOdruFDGUjQkuJNTIAkb7oh4zs5OWgA30M9thKnaCPS0MaLsvQ66... Keys AESef3a6e00a19a29644d1a0e1b56039abc50b3764a83e580ef7441c861f069fe20 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 3304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
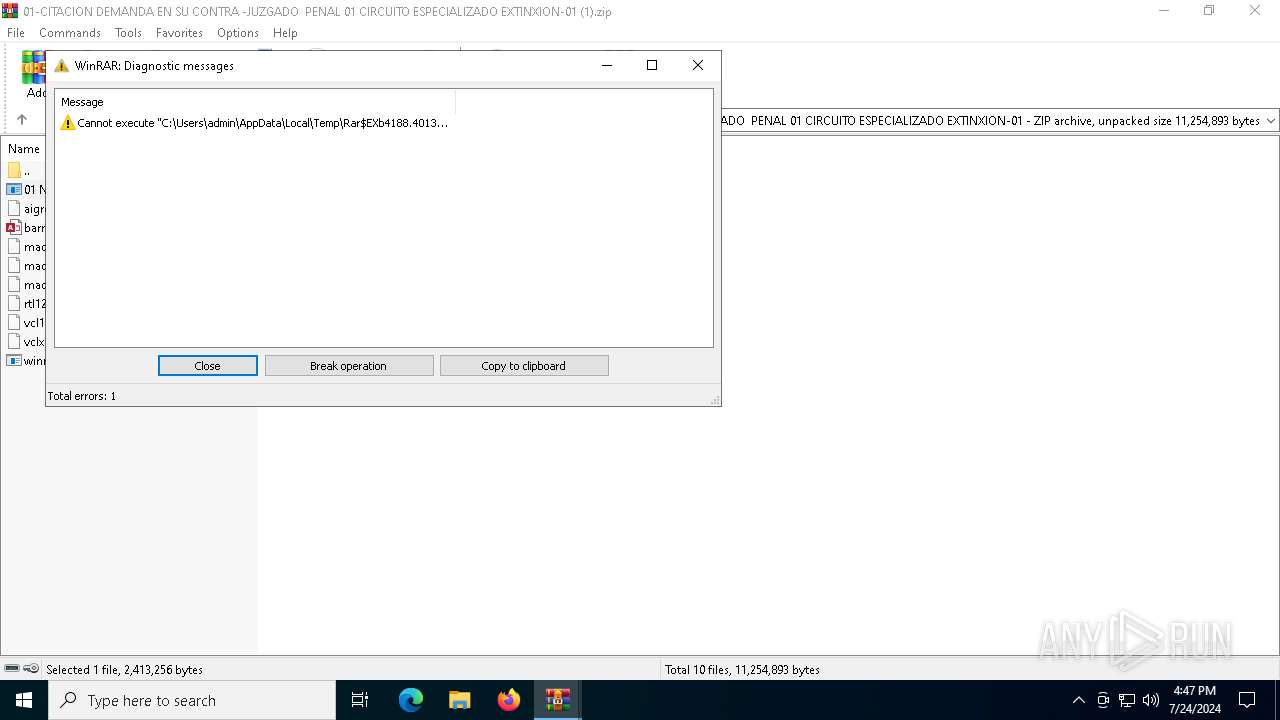
| 4104 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4188.32447\01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01\01 NOTIFICACION DEMANDA..exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4188.32447\01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01\01 NOTIFICACION DEMANDA..exe | WinRAR.exe | ||||||||||||
User: admin Company: iTop Inc. Integrity Level: MEDIUM Description: DualSafe Password Manager Exit code: 1 Version: 1.4.0.3 Modules
| |||||||||||||||
| 4160 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | 01 NOTIFICACION DEMANDA..exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4188 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01 (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6312 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6548 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6936 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 610
Read events
14 593
Write events
17
Delete events
0
Modification events
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01 (1).zip | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (4188) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
12
Suspicious files
5
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4188.32447\01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01\vcl120.bpl | bpl | |
MD5:1384DCC24A52CF63786848C0ED4A4D1B | SHA256:D19F51871484CC4A737196BDB048193AD73F7F6BD061EC813766516EBA26E406 | |||
| 4160 | cmd.exe | C:\Users\admin\AppData\Local\Temp\irjc | — | |
MD5:— | SHA256:— | |||
| 4104 | 01 NOTIFICACION DEMANDA..exe | C:\Users\admin\AppData\Roaming\apppower\madbasic_.bpl | executable | |
MD5:E03A0056E75D3A5707BA199BC2EA701F | SHA256:7826395127E791A883359EA81308174700DA0AF8052CC9853B19FD29C2E4BADB | |||
| 4104 | 01 NOTIFICACION DEMANDA..exe | C:\Users\admin\AppData\Roaming\apppower\barrette.accdb | binary | |
MD5:3DE728173727B206FE14724BA05A28C2 | SHA256:F923B85549CF4D2F87C11F4CDEB5ABB408974AEA8235AA68ACC849736EBDDE28 | |||
| 4104 | 01 NOTIFICACION DEMANDA..exe | C:\Users\admin\AppData\Roaming\apppower\rtl120.bpl | executable | |
MD5:1681F93E11A7ED23612A55BCEF7F1023 | SHA256:7ED5369FCF0283EA18974C43DBFF80E6006B155B76DA7C72FA9619EB03F54CEF | |||
| 4104 | 01 NOTIFICACION DEMANDA..exe | C:\Users\admin\AppData\Roaming\apppower\vcl120.bpl | bpl | |
MD5:1384DCC24A52CF63786848C0ED4A4D1B | SHA256:D19F51871484CC4A737196BDB048193AD73F7F6BD061EC813766516EBA26E406 | |||
| 4160 | cmd.exe | C:\Users\admin\AppData\Local\Temp\jjt | lnk | |
MD5:60E490040A26FA01EBC58AAB983A9D8B | SHA256:9693B3CE17A21F6F20D8F1E320CE895190721AEEDBF1CBCEAFFFAF518964CC0C | |||
| 4188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4188.32447\01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01\vclx120.bpl | executable | |
MD5:3CB8F7606940C9B51C45EBAEB84AF728 | SHA256:2FEEC33D1E3F3D69C717F4528B8F7F5C030CAAE6FB37C2100CB0B5341367D053 | |||
| 4188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4188.32447\01-CITACION DEMANDA EN SU CONTRA -JUZGADO PENAL 01 CIRCUITO ESPECIALIZADO EXTINXION-01\madexcept_.bpl | executable | |
MD5:98E59596EDD9B888D906C5409E515803 | SHA256:A6CA13AF74A64E4AB5EBB2D12B757CECF1A683CB9CD0AE7906DB1B4B2C8A90C0 | |||
| 4104 | 01 NOTIFICACION DEMANDA..exe | C:\Users\admin\AppData\Roaming\apppower\vclx120.bpl | executable | |
MD5:3CB8F7606940C9B51C45EBAEB84AF728 | SHA256:2FEEC33D1E3F3D69C717F4528B8F7F5C030CAAE6FB37C2100CB0B5341367D053 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
53
DNS requests
28
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5272 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4120 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6344 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3488 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4512 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 92.123.104.11:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4204 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2864 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.kozow .com Domain |
2872 | MSBuild.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
2872 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
2872 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
1 ETPRO signatures available at the full report