| File name: | Bestellung.jar |
| Full analysis: | https://app.any.run/tasks/e83e633e-9d19-4719-aee7-2abe3d167257 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | May 15, 2019, 05:58:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 25664A73A3A1DDC5FCC76E2A5A49AEFE |
| SHA1: | 9F33F07D280C25FF7CE487C98A85D3204ACEAA96 |
| SHA256: | ED13AEEA867D246D97D8E05E50449939B5C80EF2A2BAEB4FFC8C6103757A178B |
| SSDEEP: | 12288:Sfp42N5ZRy2XMT6OUr93KpAx0B1U3Fcm8sjqOQKSEYQohzvEUpqzz:eXN5ZRy24FTSMO1VRocJop2zz |
MALICIOUS
Writes to a start menu file
- WScript.exe (PID: 1968)
Changes the autorun value in the registry
- WScript.exe (PID: 1968)
- reg.exe (PID: 1276)
AdWind was detected
- java.exe (PID: 3224)
- java.exe (PID: 4088)
Loads dropped or rewritten executable
- javaw.exe (PID: 2708)
- java.exe (PID: 3224)
- javaw.exe (PID: 3308)
- java.exe (PID: 4088)
- wscript.exe (PID: 2532)
- javaw.exe (PID: 2948)
- svchost.exe (PID: 812)
- explorer.exe (PID: 2036)
- opera.exe (PID: 2936)
Application was dropped or rewritten from another process
- javaw.exe (PID: 2948)
- java.exe (PID: 3224)
- java.exe (PID: 4088)
- javaw.exe (PID: 2708)
- javaw.exe (PID: 3308)
Turns off system restore
- regedit.exe (PID: 2632)
UAC/LUA settings modification
- regedit.exe (PID: 2632)
ADWIND was detected
- javaw.exe (PID: 3308)
Uses TASKKILL.EXE to kill security tools
- javaw.exe (PID: 3308)
Changes Image File Execution Options
- regedit.exe (PID: 2632)
SUSPICIOUS
Executes scripts
- javaw.exe (PID: 2948)
- wscript.exe (PID: 2532)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 292)
- cmd.exe (PID: 1832)
- cmd.exe (PID: 3468)
- cmd.exe (PID: 3988)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 3364)
Executes JAVA applets
- explorer.exe (PID: 2036)
- wscript.exe (PID: 2532)
- javaw.exe (PID: 2708)
Creates files in the user directory
- wscript.exe (PID: 2532)
- javaw.exe (PID: 2708)
- WScript.exe (PID: 1968)
- xcopy.exe (PID: 3804)
- explorer.exe (PID: 2036)
Application launched itself
- wscript.exe (PID: 2532)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2708)
- java.exe (PID: 3224)
- javaw.exe (PID: 3308)
- java.exe (PID: 4088)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 2708)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 2708)
Starts itself from another location
- javaw.exe (PID: 2708)
Executable content was dropped or overwritten
- xcopy.exe (PID: 3804)
- javaw.exe (PID: 3308)
Uses TASKKILL.EXE to kill process
- javaw.exe (PID: 3308)
Reads Internet Cache Settings
- explorer.exe (PID: 2036)
INFO
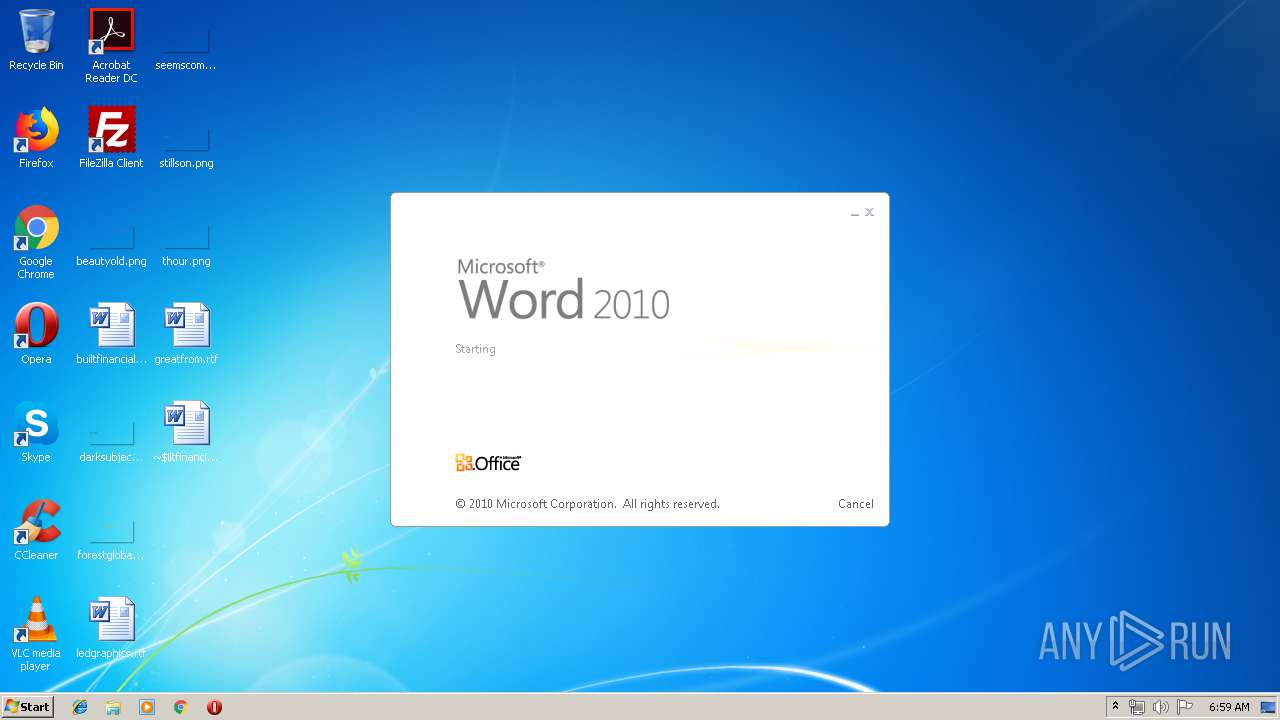
Starts Microsoft Office Application
- explorer.exe (PID: 2036)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3524)
- WINWORD.EXE (PID: 3440)
- WINWORD.EXE (PID: 3512)
Creates files in the user directory
- WINWORD.EXE (PID: 3440)
- WINWORD.EXE (PID: 3524)
- WINWORD.EXE (PID: 3512)
- opera.exe (PID: 2936)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:15 05:44:27 |
| ZipCRC: | 0x7cf3c163 |
| ZipCompressedSize: | 664965 |
| ZipUncompressedSize: | 1014909 |
| ZipFileName: | paqzomyspw/resources/lzgpusxodo |
Total processes
188
Monitored processes
87
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive7877283023523043323.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 404 | attrib +h "C:\Users\admin\Oracle Corporations\*.*" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | taskkill /IM text2pcap.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 812 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | taskkill /IM BullGuardBhvScanner.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive388730630540033475.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1076 | taskkill /IM ProcessHacker.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | taskkill /IM V3Proxy.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1096 | taskkill /IM editcap.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | taskkill /IM MWAGENT.EXE /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
13 636
Read events
13 029
Write events
566
Delete events
41
Modification events
| (PID) Process: | (2532) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2532) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\BMmbWyYJuO |
| Operation: | write | Name: | |
Value: false - 15/5/2019 | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | BMmbWyYJuO |
Value: wscript.exe //B "C:\Users\admin\AppData\Roaming\BMmbWyYJuO.js" | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | BMmbWyYJuO |
Value: wscript.exe //B "C:\Users\admin\AppData\Roaming\BMmbWyYJuO.js" | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1968) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
112
Suspicious files
36
Text files
96
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2948 | javaw.exe | C:\Users\admin\ecsbvnzsau.js | text | |
MD5:— | SHA256:— | |||
| 3224 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2708 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2532 | wscript.exe | C:\Users\admin\AppData\Roaming\BMmbWyYJuO.js | text | |
MD5:— | SHA256:— | |||
| 2532 | wscript.exe | C:\Users\admin\AppData\Roaming\khxvvtf.txt | java | |
MD5:— | SHA256:— | |||
| 1968 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\BMmbWyYJuO.js | text | |
MD5:— | SHA256:— | |||
| 2708 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 3804 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\LICENSE | text | |
MD5:98F46AB6481D87C4D77E0E91A6DBC15F | SHA256:23F9A5C12FA839650595A32872B7360B9E030C7213580FB27DD9185538A5828C | |||
| 3804 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\THIRDPARTYLICENSEREADME-JAVAFX.txt | text | |
MD5:AB9DB8D553033C0326BD2D38D77F84C1 | SHA256:38995534DF44E0526F8C8C8D479C778A4B34627CFD69F19213CFBE019A7261BA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
15
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2936 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1968 | WScript.exe | 184.75.209.163:7800 | unknownsoft.duckdns.org | Amanah Tech Inc. | CA | malicious |
3308 | javaw.exe | 185.244.31.160:7075 | olavroy.duckdns.org | — | — | malicious |
2936 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2936 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
unknownsoft.duckdns.org |
| malicious |
olavroy.duckdns.org |
| malicious |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1048 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
3308 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
3308 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |
3308 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
3308 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |