| File name: | WannaCry.exe |
| Full analysis: | https://app.any.run/tasks/1a6451e4-cb3e-4439-aa15-4bb44cce1066 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
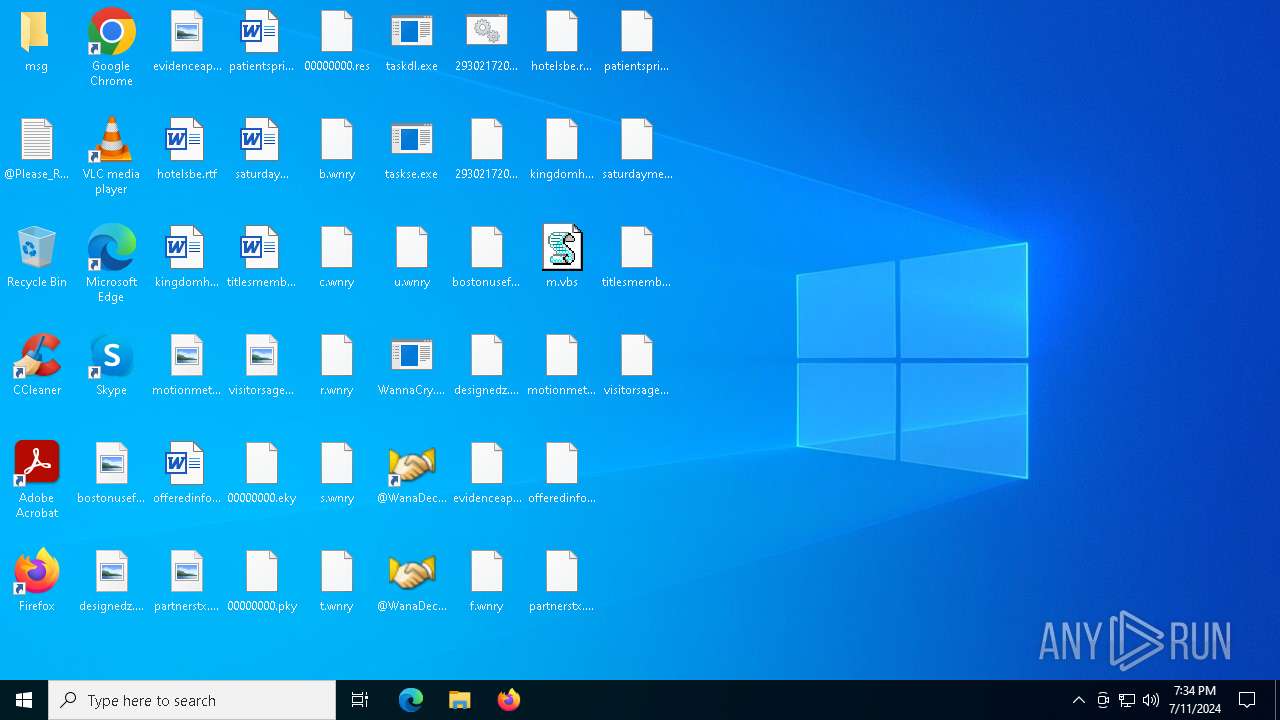
| Analysis date: | July 11, 2024, 19:34:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 84C82835A5D21BBCF75A61706D8AB549 |
| SHA1: | 5FF465AFAABCBF0150D1A3AB2C2E74F3A4426467 |
| SHA256: | ED01EBFBC9EB5BBEA545AF4D01BF5F1071661840480439C6E5BABE8E080E41AA |
| SSDEEP: | 98304:QqPoBhz1aRxcSUDk36SAEdhvxWa9P593R8yAVp2g3x:QqPe1Cxcxk3ZAEUadzR8yc4gB |
MALICIOUS
Drops the executable file immediately after the start
- WannaCry.exe (PID: 4136)
Writes a file to the Word startup folder
- WannaCry.exe (PID: 4136)
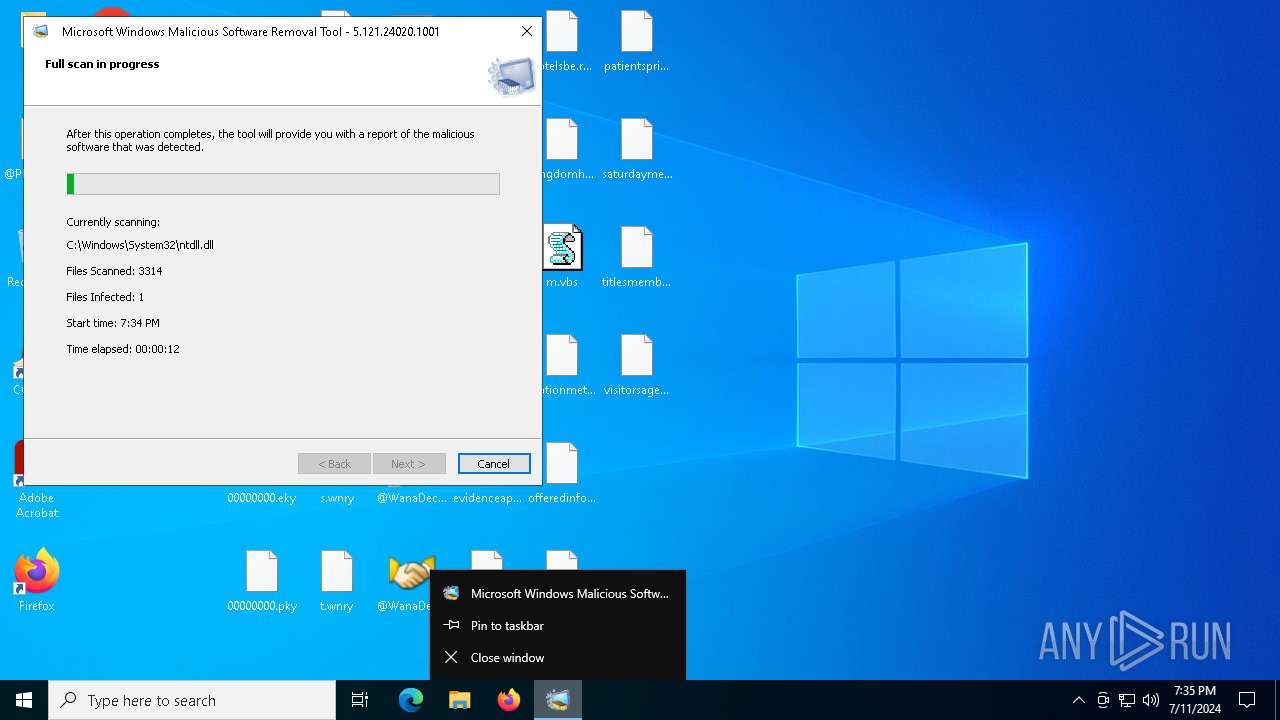
Creates a writable file in the system directory
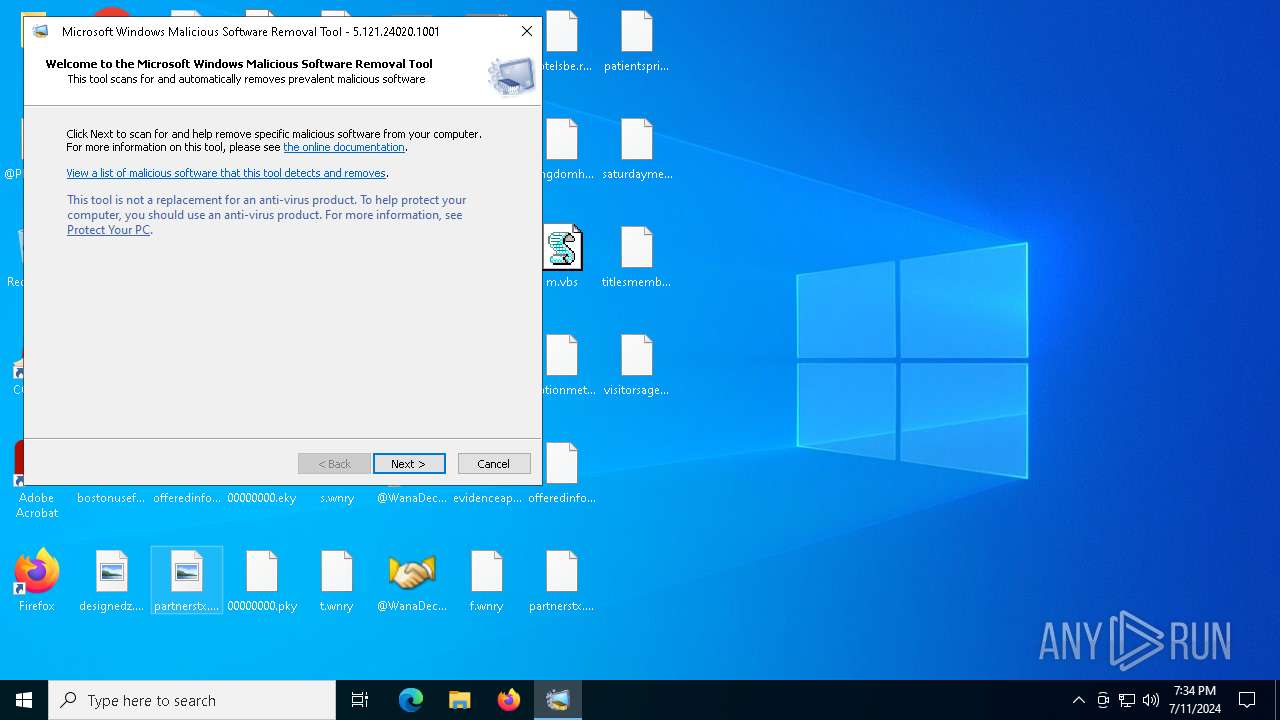
- MRT.exe (PID: 1440)
Actions looks like stealing of personal data
- MRT.exe (PID: 1440)
- WannaCry.exe (PID: 4136)
Modifies files in the Chrome extension folder
- WannaCry.exe (PID: 4136)
DCRAT has been detected (YARA)
- MRT.exe (PID: 1440)
COBALTSTRIKE has been detected (YARA)
- MRT.exe (PID: 1440)
Drops known malicious image
- WannaCry.exe (PID: 4136)
M0YV has been detected (YARA)
- MRT.exe (PID: 1440)
MIMIKATZ has been detected (YARA)
- MRT.exe (PID: 1440)
CVE-2022-30190 detected
- MRT.exe (PID: 1440)
MASSLOGGER has been detected (YARA)
- MRT.exe (PID: 1440)
SUSPICIOUS
Process drops legitimate windows executable
- WannaCry.exe (PID: 4136)
- MRT.exe (PID: 1440)
Starts a Microsoft application from unusual location
- WannaCry.exe (PID: 4136)
- taskdl.exe (PID: 1496)
- taskdl.exe (PID: 6184)
- taskdl.exe (PID: 3516)
- taskdl.exe (PID: 3228)
Uses ATTRIB.EXE to modify file attributes
- WannaCry.exe (PID: 4136)
Executable content was dropped or overwritten
- WannaCry.exe (PID: 4136)
- MRT.exe (PID: 1440)
Uses ICACLS.EXE to modify access control lists
- WannaCry.exe (PID: 4136)
Starts CMD.EXE for commands execution
- WannaCry.exe (PID: 4136)
Executing commands from a ".bat" file
- WannaCry.exe (PID: 4136)
The process executes VB scripts
- cmd.exe (PID: 2400)
Creates files like ransomware instruction
- WannaCry.exe (PID: 4136)
Application launched itself
- MRT.exe (PID: 5764)
The process verifies whether the antivirus software is installed
- MRT.exe (PID: 1440)
Detected use of alternative data streams (AltDS)
- MRT.exe (PID: 1440)
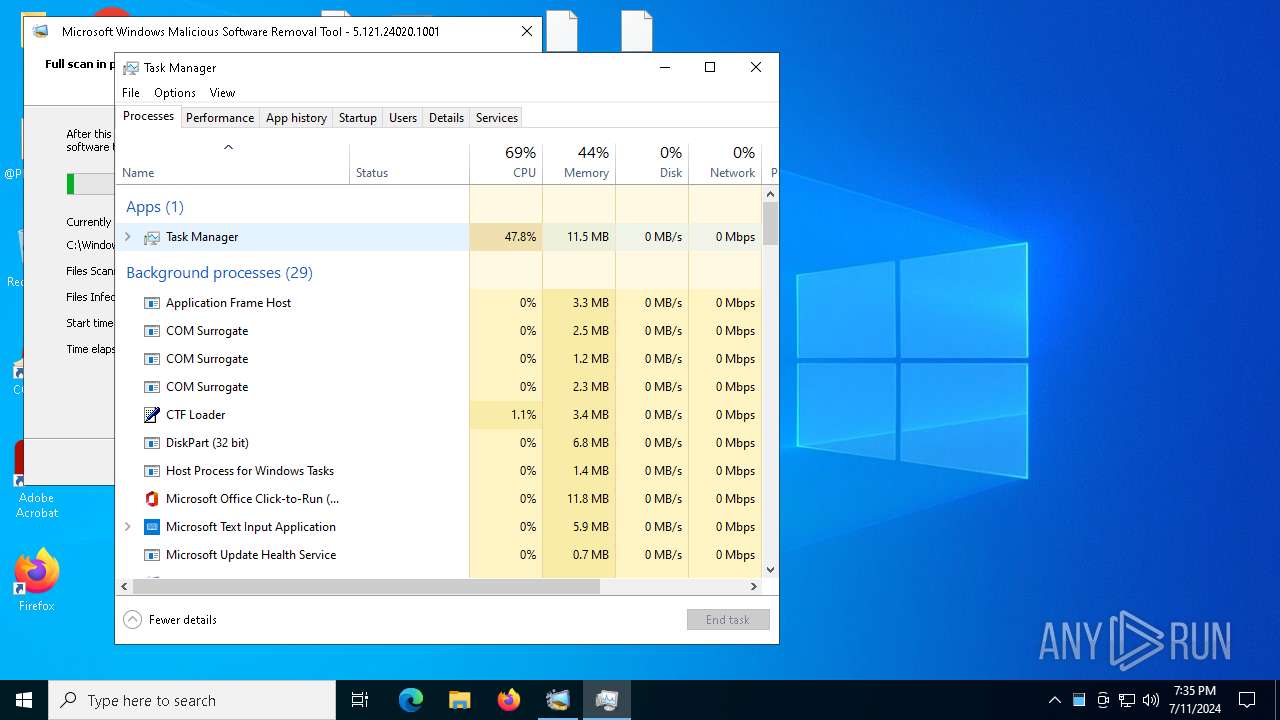
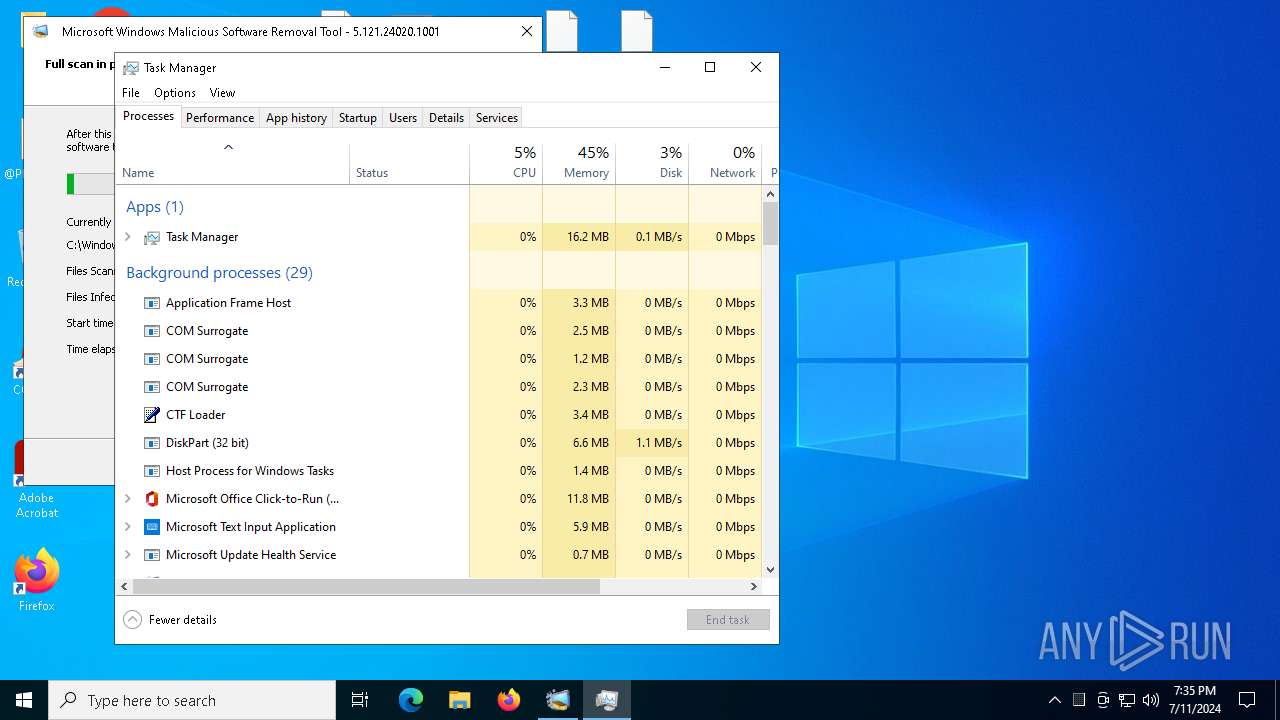
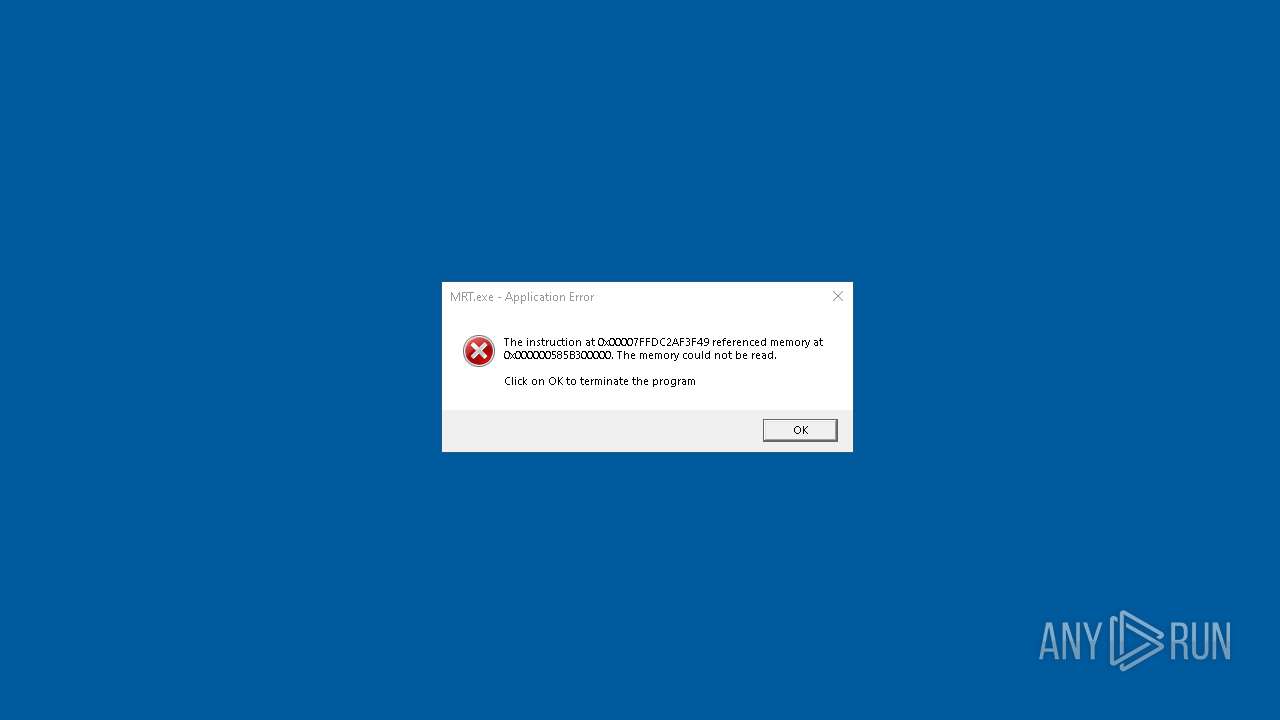
Executes application which crashes
- MRT.exe (PID: 1440)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 700)
Found regular expressions for crypto-addresses (YARA)
- MRT.exe (PID: 1440)
There is functionality for VM detection (antiVM strings)
- MRT.exe (PID: 1440)
INFO
Checks supported languages
- WannaCry.exe (PID: 4136)
- taskdl.exe (PID: 1496)
- taskdl.exe (PID: 6184)
- taskdl.exe (PID: 3516)
- ShellExperienceHost.exe (PID: 700)
- taskdl.exe (PID: 3228)
Reads the computer name
- WannaCry.exe (PID: 4136)
- ShellExperienceHost.exe (PID: 700)
Reads the machine GUID from the registry
- WannaCry.exe (PID: 4136)
The dropped object may contain a URL to Tor Browser
- WannaCry.exe (PID: 4136)
Dropped object may contain TOR URL's
- WannaCry.exe (PID: 4136)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3908)
- MRT.exe (PID: 5764)
- MRT.exe (PID: 1440)
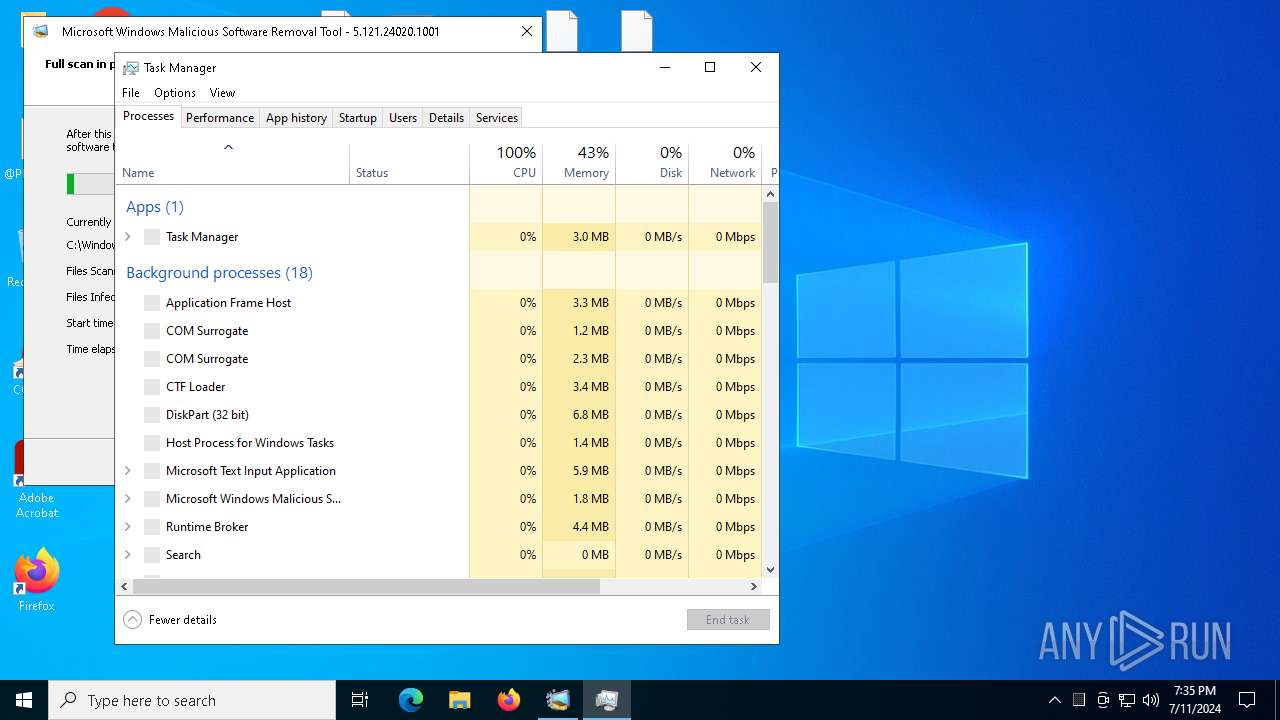
- Taskmgr.exe (PID: 6488)
Creates files or folders in the user directory
- WannaCry.exe (PID: 4136)
- Taskmgr.exe (PID: 6488)
Creates files in the program directory
- WannaCry.exe (PID: 4136)
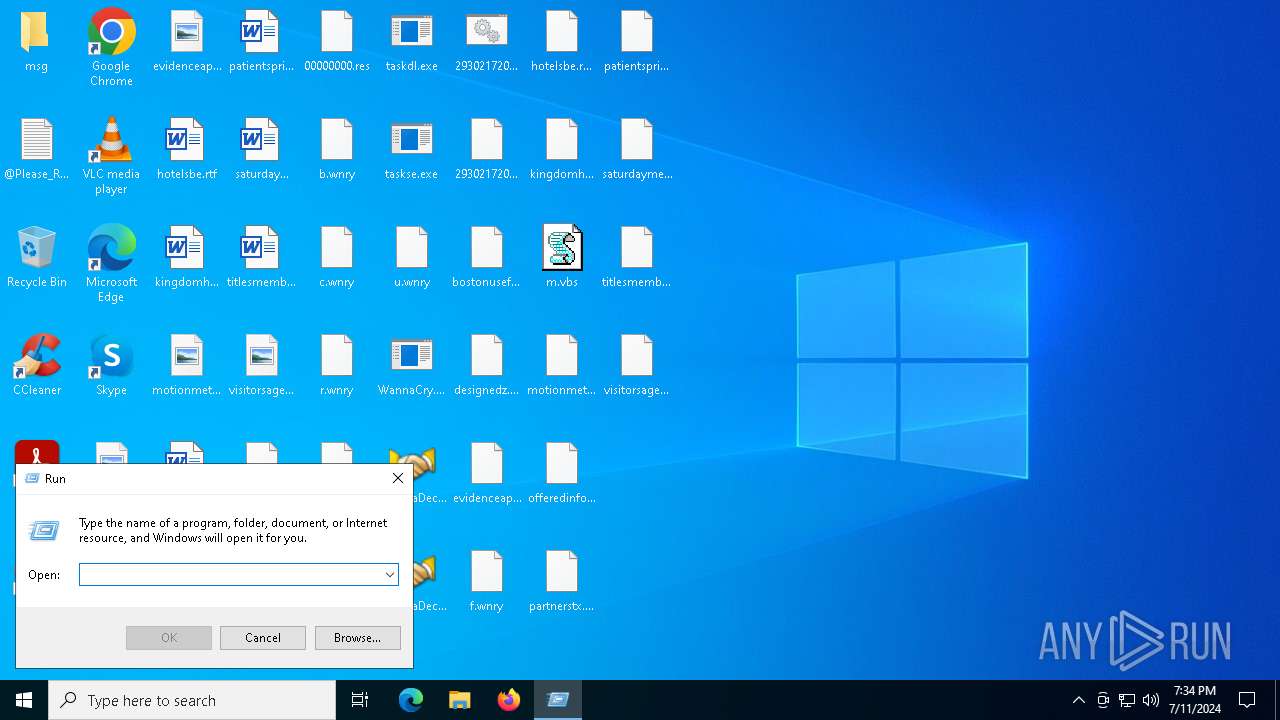
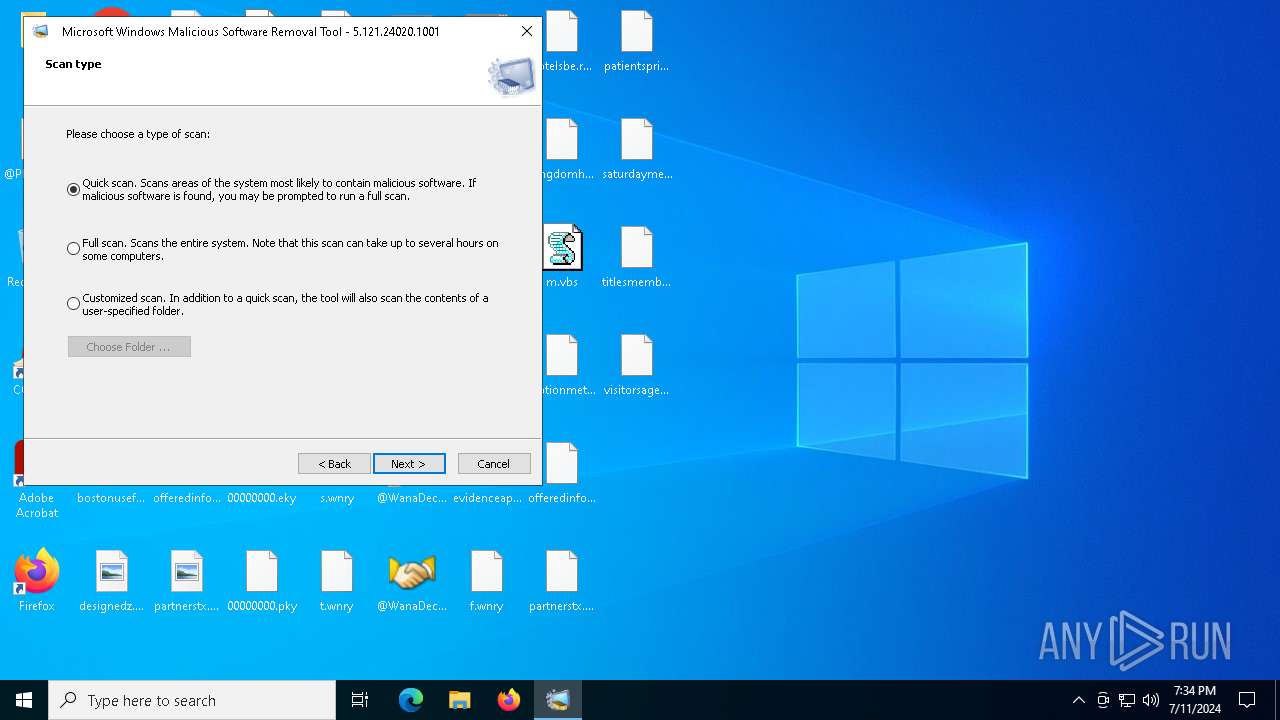
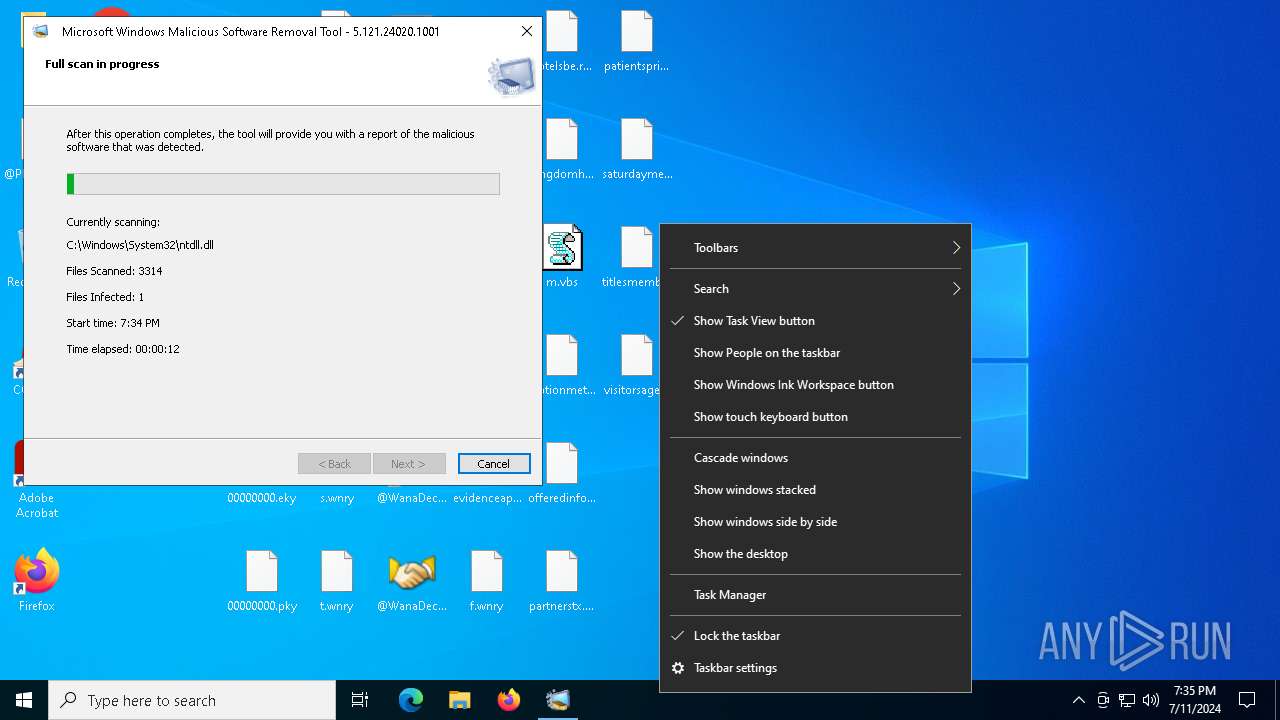
Manual execution by a user
- MRT.exe (PID: 5764)
- Taskmgr.exe (PID: 6064)
- Taskmgr.exe (PID: 6488)
Drops the executable file immediately after the start
- MRT.exe (PID: 1440)
Reads the software policy settings
- MRT.exe (PID: 1440)
Reads Microsoft Office registry keys
- MRT.exe (PID: 1440)
Found Base64 encoded access to environment variables via PowerShell (YARA)
- MRT.exe (PID: 1440)
Found Base64 encoded network access via PowerShell (YARA)
- MRT.exe (PID: 1440)
Found Base64 encoded reflection usage via PowerShell (YARA)
- MRT.exe (PID: 1440)
Found Base64 encoded file access via PowerShell (YARA)
- MRT.exe (PID: 1440)
UPX packer has been detected
- MRT.exe (PID: 1440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:20 09:05:05+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28672 |
| InitializedDataSize: | 3481600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x77ba |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.7601.17514 |
| ProductVersionNumber: | 6.1.7601.17514 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | DiskPart |
| FileVersion: | 6.1.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | diskpart.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | diskpart.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7601.17514 |
Total processes
160
Monitored processes
18
Malicious processes
3
Suspicious processes
0
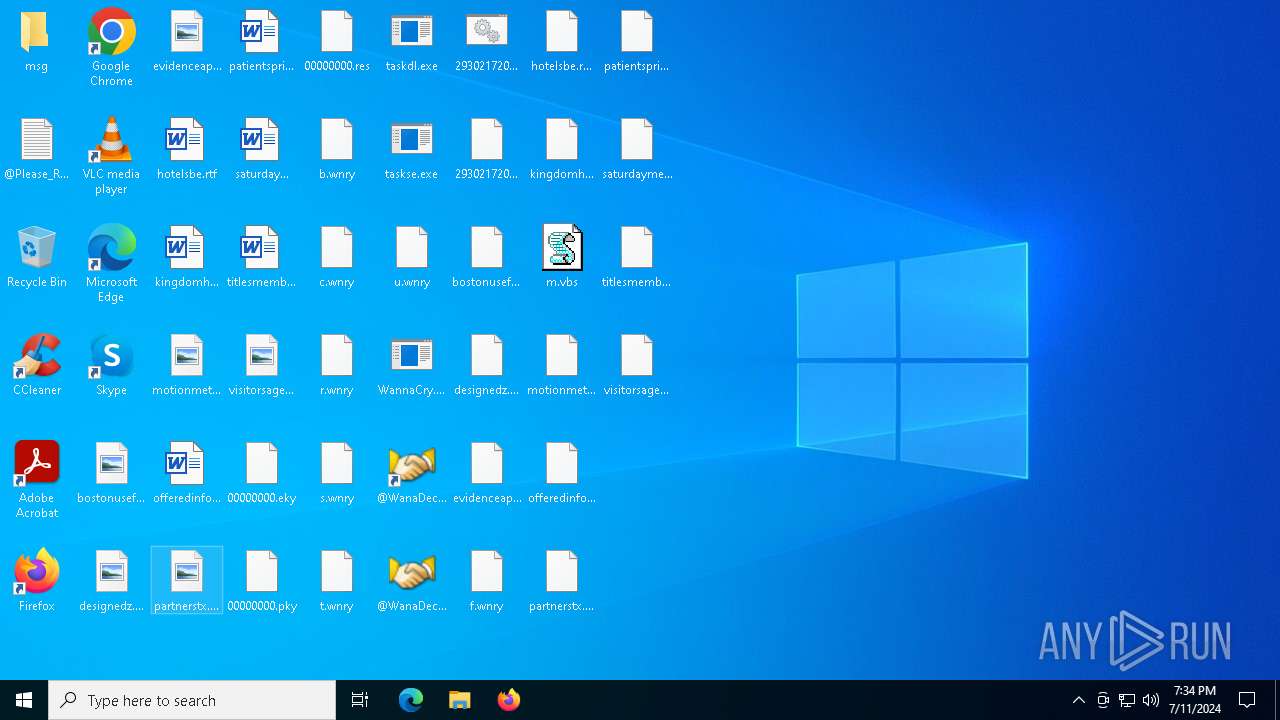
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1440 | "C:\WINDOWS\system32\mrt.exe" /RE | C:\Windows\System32\MRT.exe | MRT.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Malicious Software Removal Tool Exit code: 3221225477 Version: 5.121.24020.1001 (77154edc63260f9a920d54b3c1590ee8e588a395) Modules
| |||||||||||||||
| 1496 | taskdl.exe | C:\Users\admin\Desktop\taskdl.exe | — | WannaCry.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | C:\WINDOWS\system32\WerFault.exe -u -p 1440 -s 1832 | C:\Windows\System32\WerFault.exe | — | MRT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2400 | C:\WINDOWS\system32\cmd.exe /c 293021720726454.bat | C:\Windows\SysWOW64\cmd.exe | — | WannaCry.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | attrib.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2832 | attrib +h . | C:\Windows\SysWOW64\attrib.exe | — | WannaCry.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3228 | taskdl.exe | C:\Users\admin\Desktop\taskdl.exe | — | WannaCry.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | taskdl.exe | C:\Users\admin\Desktop\taskdl.exe | — | WannaCry.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3908 | cscript.exe //nologo m.vbs | C:\Windows\SysWOW64\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
16 710
Read events
16 686
Write events
19
Delete events
5
Modification events
| (PID) Process: | (4136) WannaCry.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WanaCrypt0r |
| Operation: | write | Name: | wd |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (5764) MRT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5764) MRT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5764) MRT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5764) MRT.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1440) MRT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RemovalTools\MpGears |
| Operation: | write | Name: | SpyNetReportingLocation |
Value: SOAP:https://wdcp.microsoft.com/WdCpSrvc.asmx | |||
| (PID) Process: | (1700) WerFault.exe | Key: | \REGISTRY\A\{4b5e7a6b-e829-594d-0a28-3e1ddff83837}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (1700) WerFault.exe | Key: | \REGISTRY\A\{4b5e7a6b-e829-594d-0a28-3e1ddff83837}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1700) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsSelfHost\FIDs |
| Operation: | delete value | Name: | AllFlights |
Value: | |||
| (PID) Process: | (6488) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
Executable files
10
Suspicious files
1 521
Text files
470
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_french.wnry | text | |
MD5:4E57113A6BF6B88FDD32782A4A381274 | SHA256:9BD38110E6523547AED50617DDC77D0920D408FAEED2B7A21AB163FDA22177BC | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_filipino.wnry | text | |
MD5:08B9E69B57E4C9B966664F8E1C27AB09 | SHA256:D8489F8C16318E524B45DE8B35D7E2C3CD8ED4821C136F12F5EF3C9FC3321324 | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_english.wnry | text | |
MD5:FE68C2DC0D2419B38F44D83F2FCF232E | SHA256:26FD072FDA6E12F8C2D3292086EF0390785EFA2C556E2A88BD4673102AF703E5 | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_finnish.wnry | text | |
MD5:35C2F97EEA8819B1CAEBD23FEE732D8F | SHA256:1ADFEE058B98206CB4FBE1A46D3ED62A11E1DEE2C7FF521C1EEF7C706E6A700E | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_czech.wnry | text | |
MD5:537EFEECDFA94CC421E58FD82A58BA9E | SHA256:5AFA4753AFA048C6D6C39327CE674F27F5F6E5D3F2A060B7A8AED61725481150 | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_chinese (traditional).wnry | text | |
MD5:2EFC3690D67CD073A9406A25005F7CEA | SHA256:5C7F6AD1EC4BC2C8E2C9C126633215DABA7DE731AC8B12BE10CA157417C97F3A | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_danish.wnry | text | |
MD5:2C5A3B81D5C4715B7BEA01033367FCB5 | SHA256:A75BB44284B9DB8D702692F84909A7E23F21141866ADF3DB888042E9109A1CB6 | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_croatian.wnry | text | |
MD5:17194003FA70CE477326CE2F6DEEB270 | SHA256:3F33734B2D34CCE83936CE99C3494CD845F1D2C02D7F6DA31D42DFC1CA15A171 | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\msg\m_bulgarian.wnry | text | |
MD5:95673B0F968C0F55B32204361940D184 | SHA256:40B37E7B80CF678D7DD302AAF41B88135ADE6DDF44D89BDBA19CF171564444BD | |||
| 4136 | WannaCry.exe | C:\Users\admin\Desktop\c.wnry | abr | |
MD5:AE08F79A0D800B82FCBE1B43CDBDBEFC | SHA256:055C7760512C98C8D51E4427227FE2A7EA3B34EE63178FE78631FA8AA6D15622 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
73
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3716 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4392 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4392 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4084 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2204 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1292 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4656 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4392 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4392 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4392 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |