| File name: | wannacry.exe |
| Full analysis: | https://app.any.run/tasks/06d7df20-0117-48b5-8a8f-1e1886181816 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 24, 2019, 21:42:29 |
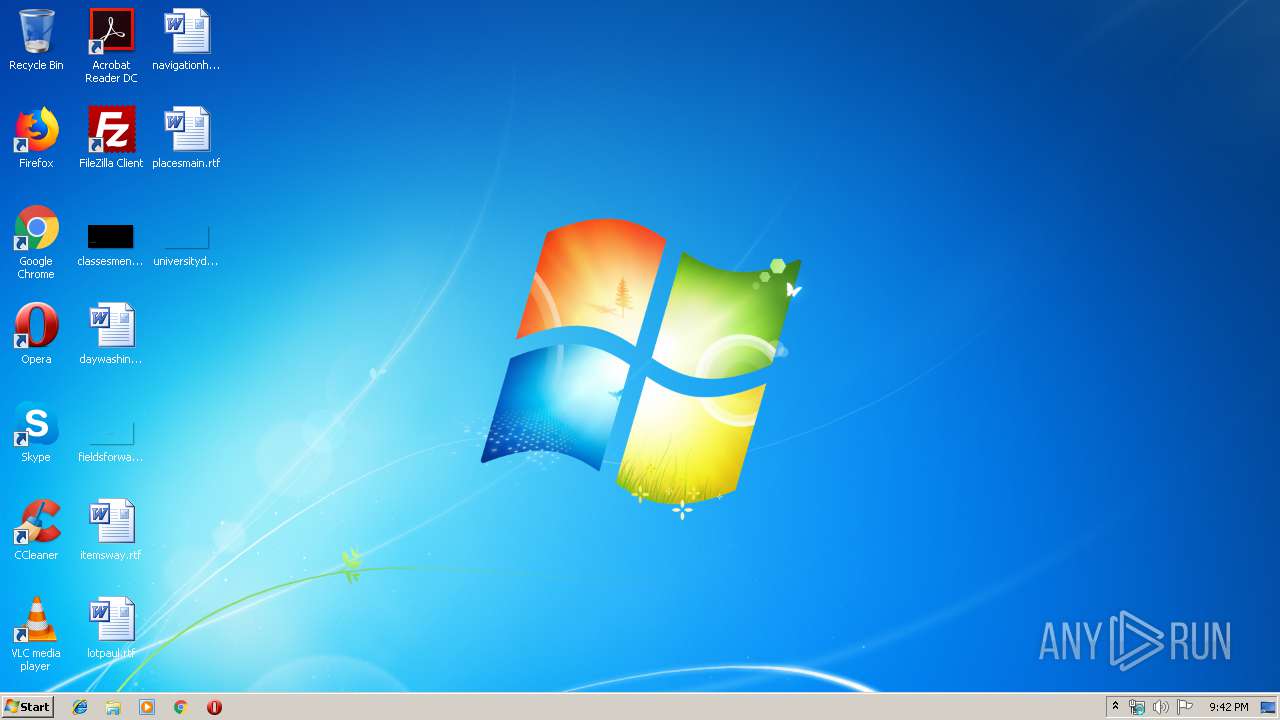
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 84C82835A5D21BBCF75A61706D8AB549 |
| SHA1: | 5FF465AFAABCBF0150D1A3AB2C2E74F3A4426467 |
| SHA256: | ED01EBFBC9EB5BBEA545AF4D01BF5F1071661840480439C6E5BABE8E080E41AA |
| SSDEEP: | 98304:QqPoBhz1aRxcSUDk36SAEdhvxWa9P593R8yAVp2g3x:QqPe1Cxcxk3ZAEUadzR8yc4gB |
MALICIOUS
Application was dropped or rewritten from another process
- taskdl.exe (PID: 640)
- @WanaDecryptor@.exe (PID: 2092)
- @WanaDecryptor@.exe (PID: 4012)
- taskhsvc.exe (PID: 2892)
- taskdl.exe (PID: 3232)
- @WanaDecryptor@.exe (PID: 2384)
- @WanaDecryptor@.exe (PID: 996)
- taskdl.exe (PID: 3324)
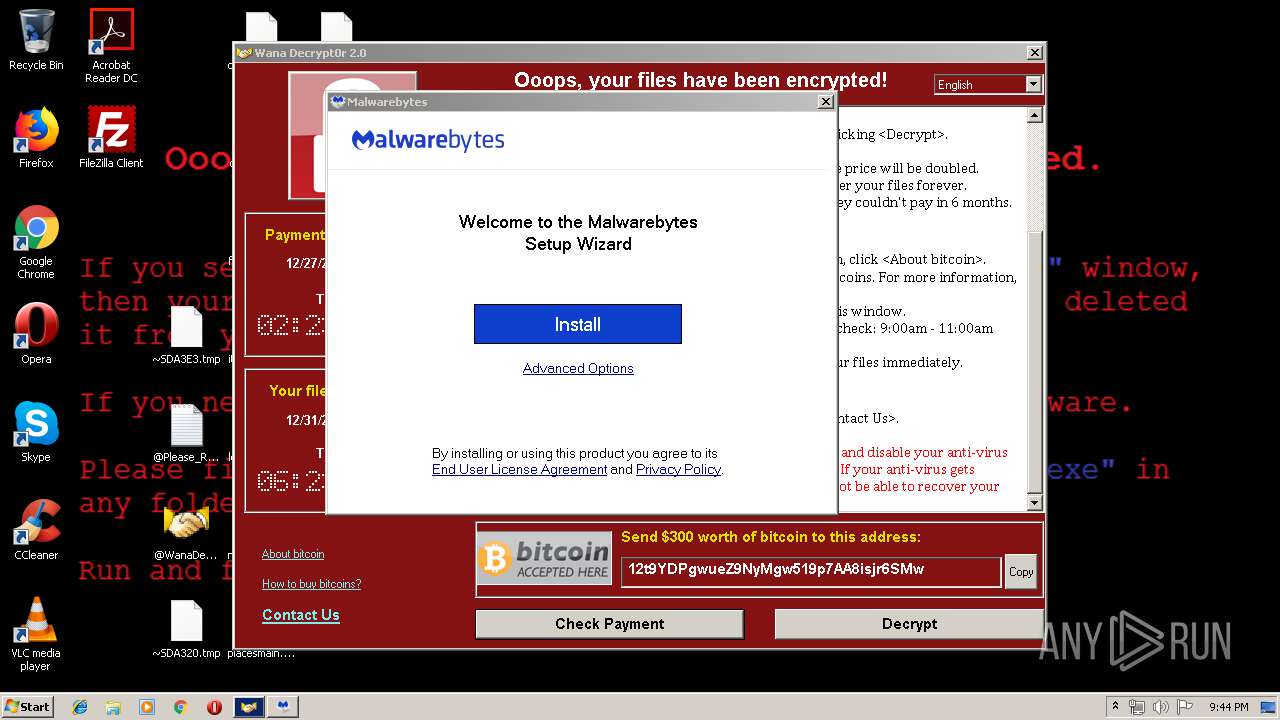
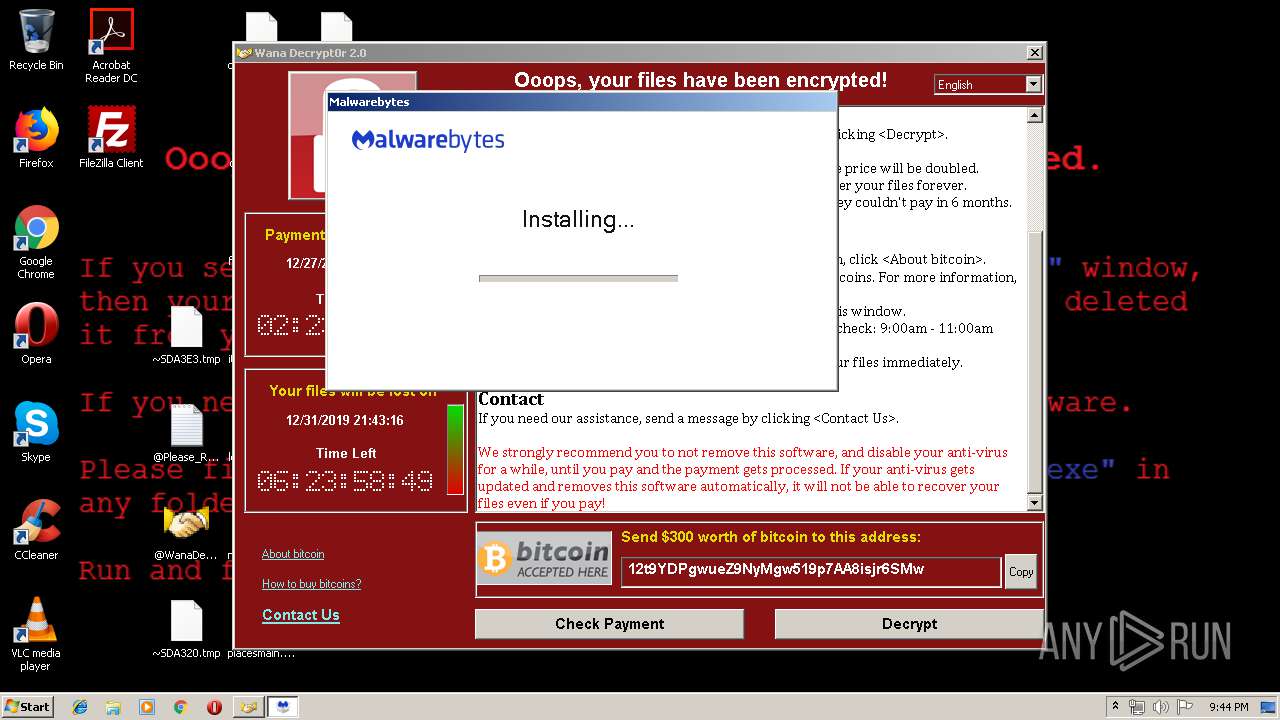
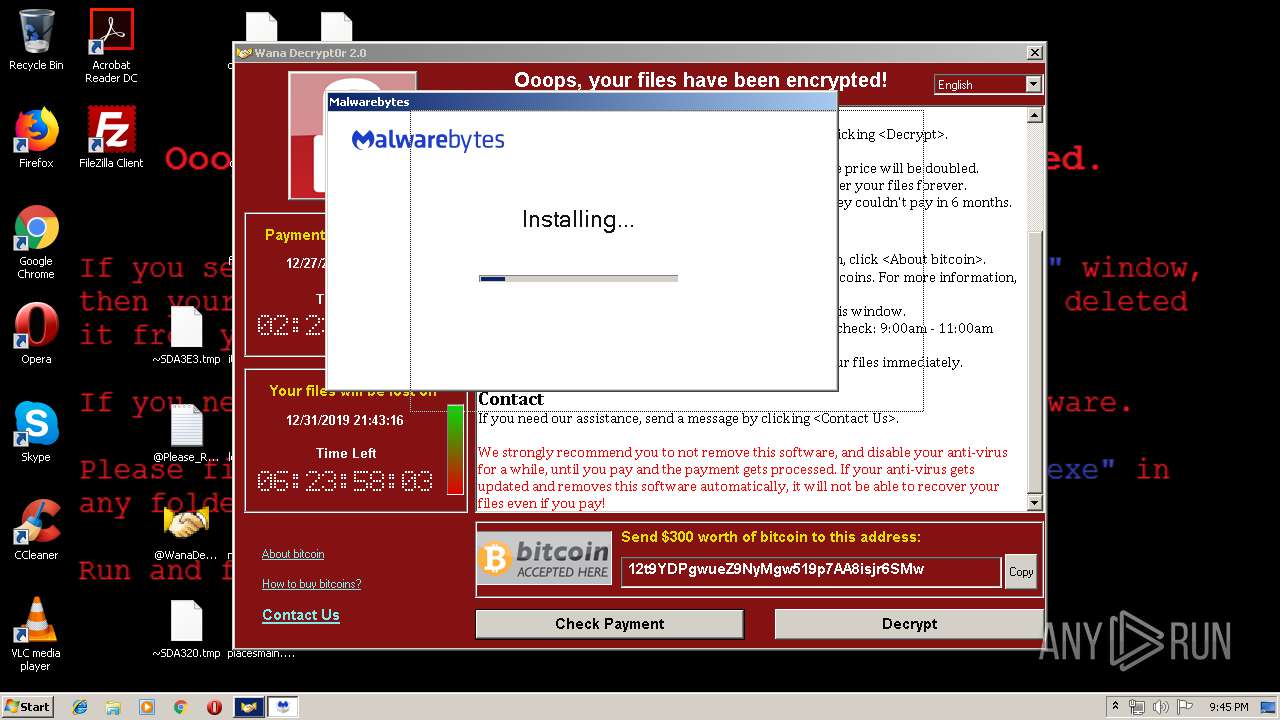
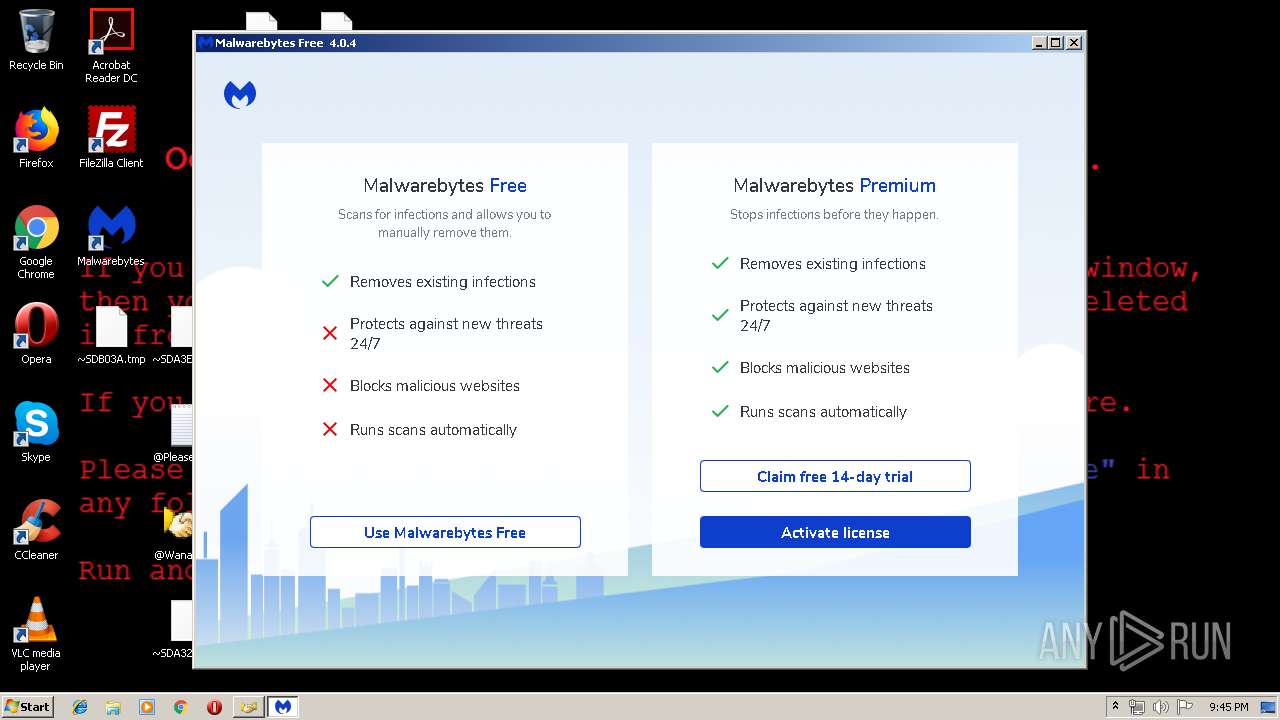
- MBSetup.exe (PID: 532)
- @WanaDecryptor@.exe (PID: 2556)
- MBSetup.exe (PID: 4084)
- taskdl.exe (PID: 2880)
- @WanaDecryptor@.exe (PID: 3592)
- MBAMInstallerService.exe (PID: 2660)
- taskdl.exe (PID: 2256)
- @WanaDecryptor@.exe (PID: 2252)
- taskdl.exe (PID: 2864)
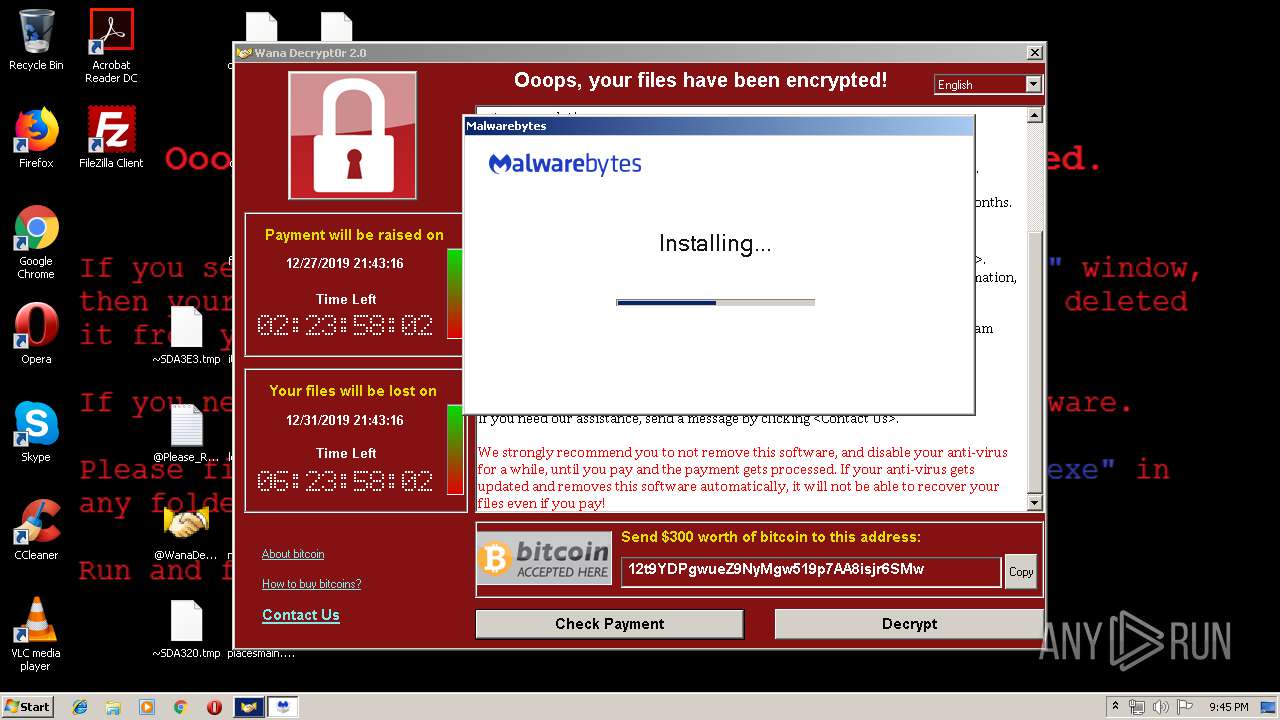
- MBAMService.exe (PID: 2560)
- MBAMService.exe (PID: 1248)
- mbam.exe (PID: 2428)
- mbamtray.exe (PID: 3320)
- @WanaDecryptor@.exe (PID: 3528)
- taskdl.exe (PID: 2612)
- @WanaDecryptor@.exe (PID: 1400)
- ig.exe (PID: 3372)
- ig-0.exe (PID: 1424)
- taskdl.exe (PID: 3576)
- ig.exe (PID: 3568)
- ig-2.exe (PID: 2920)
- ig-3.exe (PID: 4080)
- ig-1.exe (PID: 4080)
- ig-4.exe (PID: 292)
- ig-5.exe (PID: 2688)
- ig-6.exe (PID: 2608)
- ig-10.exe (PID: 320)
- ig-11.exe (PID: 3684)
- ig-7.exe (PID: 2872)
- ig-9.exe (PID: 3932)
- ig-12.exe (PID: 2924)
- ig-16.exe (PID: 3576)
- ig-13.exe (PID: 3948)
- ig-17.exe (PID: 3996)
- ig-19.exe (PID: 2712)
- ig-21.exe (PID: 4056)
- ig-15.exe (PID: 2760)
- ig-8.exe (PID: 2776)
- ig-23.exe (PID: 2488)
- ig-14.exe (PID: 3940)
- ig-18.exe (PID: 1608)
- ig-20.exe (PID: 996)
- ig-22.exe (PID: 2252)
- ig-25.exe (PID: 2172)
- ig-27.exe (PID: 2636)
- ig-28.exe (PID: 1544)
- ig-26.exe (PID: 3844)
- ig-29.exe (PID: 4056)
- ig-31.exe (PID: 3168)
- ig-30.exe (PID: 2844)
- ig-37.exe (PID: 3076)
- ig-32.exe (PID: 2472)
- ig-38.exe (PID: 2360)
- ig-33.exe (PID: 3544)
- ig-39.exe (PID: 4020)
- ig-42.exe (PID: 3072)
- ig-40.exe (PID: 2824)
- ig-41.exe (PID: 2404)
- ig-34.exe (PID: 3684)
- ig-36.exe (PID: 2040)
- ig-43.exe (PID: 4084)
- ig-45.exe (PID: 1024)
- ig-44.exe (PID: 2448)
- ig-46.exe (PID: 1744)
- @WanaDecryptor@.exe (PID: 2988)
- taskdl.exe (PID: 3060)
- ig-49.exe (PID: 1744)
- ig-47.exe (PID: 3480)
- ig-48.exe (PID: 2232)
- ig-24.exe (PID: 2276)
- ig-35.exe (PID: 1728)
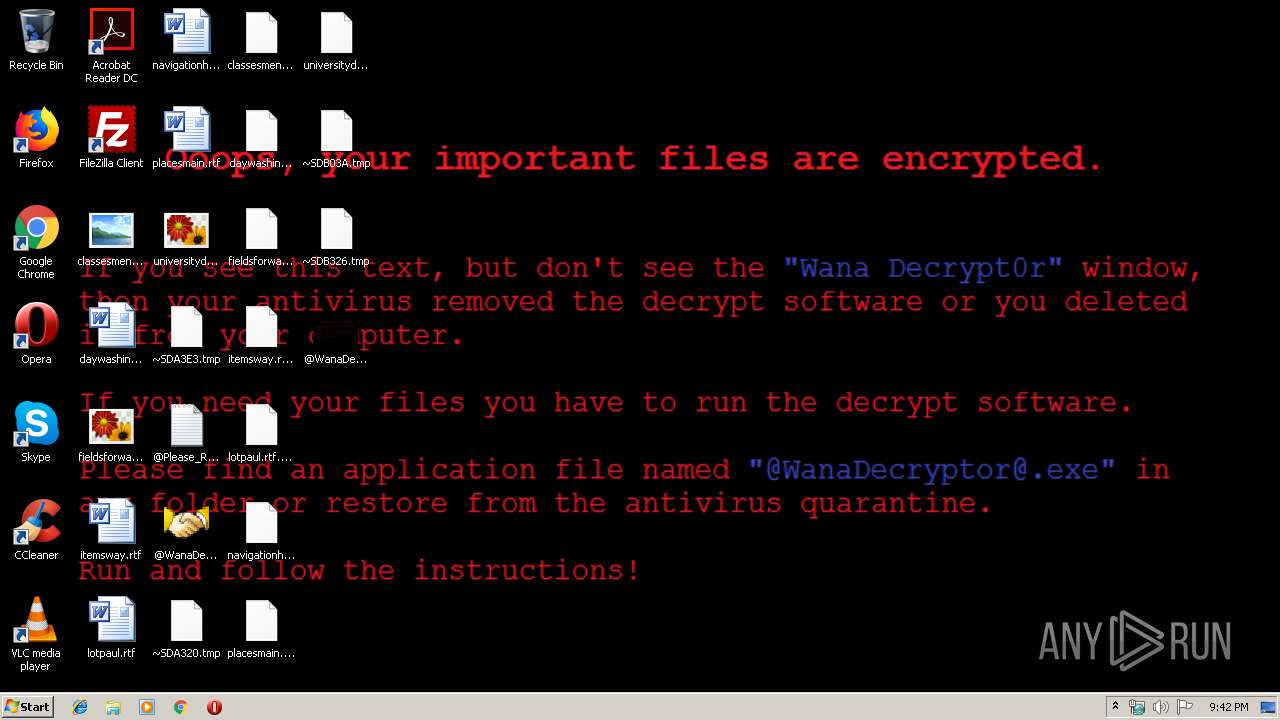
Dropped file may contain instructions of ransomware
- wannacry.exe (PID: 1268)
Writes file to Word startup folder
- wannacry.exe (PID: 1268)
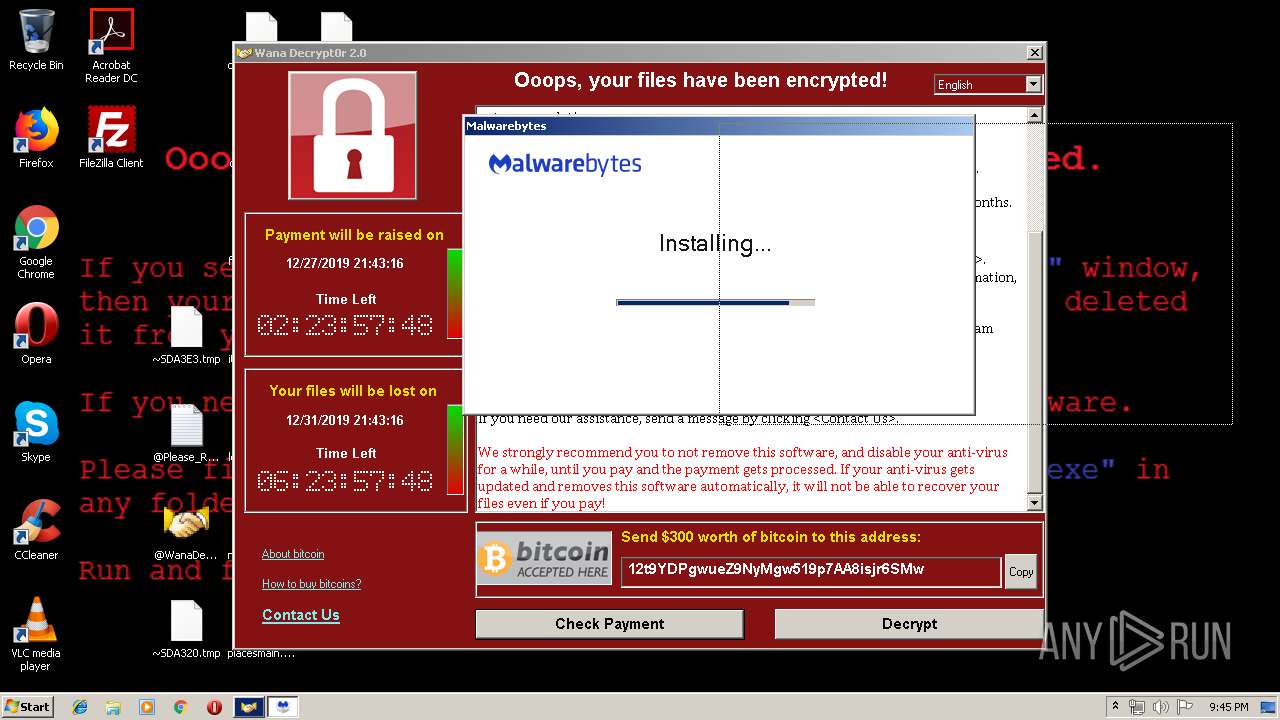
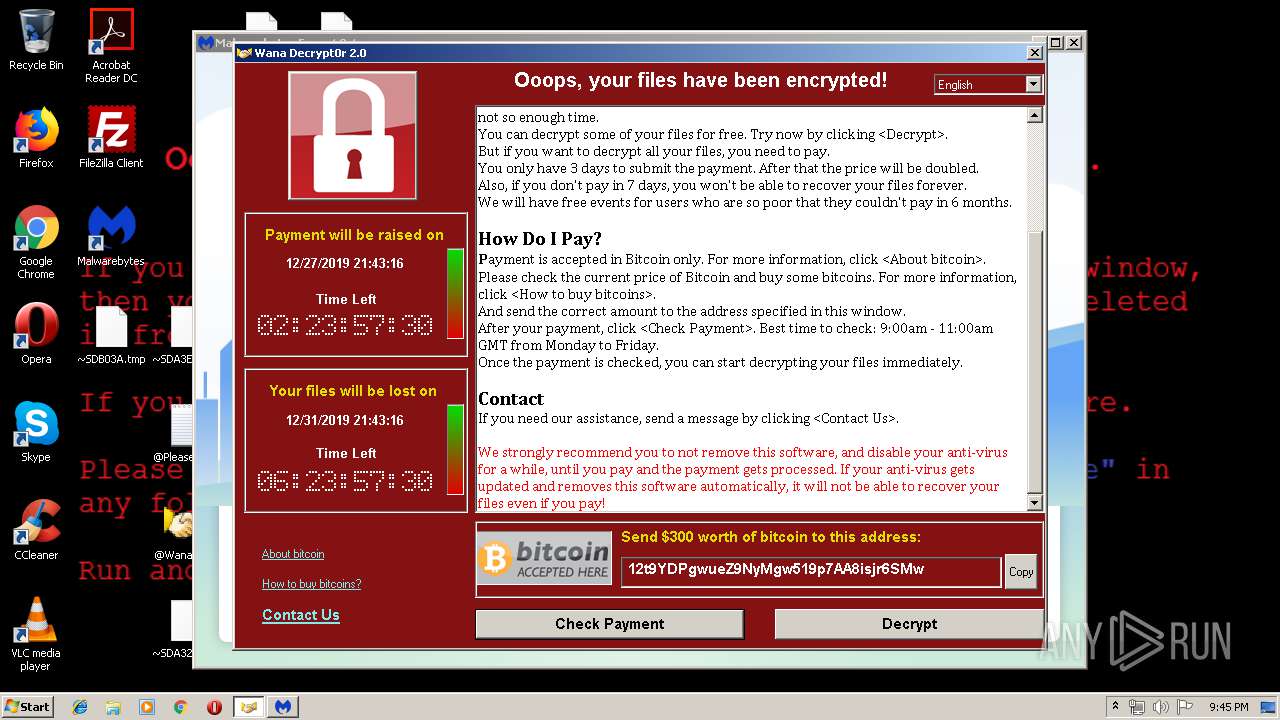
WannaCry Ransomware was detected
- wannacry.exe (PID: 1268)
- cmd.exe (PID: 564)
Modifies files in Chrome extension folder
- wannacry.exe (PID: 1268)
Loads dropped or rewritten executable
- taskhsvc.exe (PID: 2892)
- MBAMInstallerService.exe (PID: 2660)
- MBAMService.exe (PID: 1248)
- mbamtray.exe (PID: 3320)
- mbam.exe (PID: 2428)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3876)
Deletes shadow copies
- cmd.exe (PID: 3876)
Actions looks like stealing of personal data
- wannacry.exe (PID: 1268)
- MBAMService.exe (PID: 1248)
Loads the Task Scheduler COM API
- wbengine.exe (PID: 3152)
Changes the autorun value in the registry
- reg.exe (PID: 1016)
Changes settings of System certificates
- MBSetup.exe (PID: 532)
- certutil.exe (PID: 584)
- certutil.exe (PID: 3924)
- MBAMService.exe (PID: 1248)
AGENTTESLA was detected
- MBAMService.exe (PID: 1248)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- wannacry.exe (PID: 1268)
Executable content was dropped or overwritten
- wannacry.exe (PID: 1268)
- @WanaDecryptor@.exe (PID: 2092)
- chrome.exe (PID: 1956)
- chrome.exe (PID: 1928)
- MBSetup.exe (PID: 532)
- MBAMInstallerService.exe (PID: 2660)
- MBAMService.exe (PID: 1248)
Starts CMD.EXE for commands execution
- wannacry.exe (PID: 1268)
- @WanaDecryptor@.exe (PID: 4012)
- MBAMInstallerService.exe (PID: 2660)
Executes scripts
- cmd.exe (PID: 3464)
Creates files like Ransomware instruction
- wannacry.exe (PID: 1268)
Uses ICACLS.EXE to modify access control list
- wannacry.exe (PID: 1268)
Creates files in the program directory
- wannacry.exe (PID: 1268)
- MBSetup.exe (PID: 532)
- MBAMInstallerService.exe (PID: 2660)
- MBAMService.exe (PID: 1248)
Creates files in the user directory
- taskhsvc.exe (PID: 2892)
- wannacry.exe (PID: 1268)
- mbam.exe (PID: 2428)
Connects to unusual port
- taskhsvc.exe (PID: 2892)
Executed as Windows Service
- wbengine.exe (PID: 3152)
- vssvc.exe (PID: 2956)
- vds.exe (PID: 3792)
- MBAMInstallerService.exe (PID: 2660)
- MBAMService.exe (PID: 1248)
Creates files in the Windows directory
- wbadmin.exe (PID: 2180)
- certutil.exe (PID: 3924)
- certutil.exe (PID: 584)
- MBAMInstallerService.exe (PID: 2660)
- MBAMService.exe (PID: 2560)
- MBAMService.exe (PID: 1248)
Low-level read access rights to disk partition
- wbengine.exe (PID: 3152)
- vds.exe (PID: 3792)
Executed via COM
- vdsldr.exe (PID: 2248)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1956)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2180)
Adds / modifies Windows certificates
- MBSetup.exe (PID: 532)
Removes files from Windows directory
- certutil.exe (PID: 3924)
- certutil.exe (PID: 584)
- MBAMService.exe (PID: 1248)
- MBAMInstallerService.exe (PID: 2660)
Creates files in the driver directory
- MBAMInstallerService.exe (PID: 2660)
- MBAMService.exe (PID: 1248)
Creates COM task schedule object
- MBAMService.exe (PID: 1248)
Changes IE settings (feature browser emulation)
- MBAMInstallerService.exe (PID: 2660)
Modifies the open verb of a shell class
- MBAMInstallerService.exe (PID: 2660)
Creates or modifies windows services
- MBAMService.exe (PID: 1248)
Uses RUNDLL32.EXE to load library
- mbamtray.exe (PID: 3320)
- mbam.exe (PID: 2428)
Reads Internet Cache Settings
- rundll32.exe (PID: 2968)
- rundll32.exe (PID: 3840)
Creates a software uninstall entry
- MBAMInstallerService.exe (PID: 2660)
Searches for installed software
- MBAMService.exe (PID: 1248)
INFO
Dropped object may contain TOR URL's
- wannacry.exe (PID: 1268)
Dropped object may contain URL to Tor Browser
- wannacry.exe (PID: 1268)
Dropped object may contain Bitcoin addresses
- wannacry.exe (PID: 1268)
- taskhsvc.exe (PID: 2892)
- MBAMInstallerService.exe (PID: 2660)
- MBAMService.exe (PID: 1248)
Manual execution by user
- chrome.exe (PID: 1956)
Changes settings of System certificates
- chrome.exe (PID: 1928)
Application launched itself
- chrome.exe (PID: 1956)
Reads the hosts file
- chrome.exe (PID: 1928)
- chrome.exe (PID: 1956)
Reads settings of System Certificates
- chrome.exe (PID: 1956)
- MBAMService.exe (PID: 1248)
Reads Internet Cache Settings
- chrome.exe (PID: 1956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:20 10:05:05+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28672 |
| InitializedDataSize: | 3481600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x77ba |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.7601.17514 |
| ProductVersionNumber: | 6.1.7601.17514 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | DiskPart |
| FileVersion: | 6.1.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | diskpart.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | diskpart.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7601.17514 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Nov-2010 09:05:05 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | DiskPart |
| FileVersion: | 6.1.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | diskpart.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | diskpart.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7601.17514 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 20-Nov-2010 09:05:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000069B0 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40424 |
.rdata | 0x00008000 | 0x00005F70 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.66357 |
.data | 0x0000E000 | 0x00001958 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.45575 |
.rsrc | 0x00010000 | 0x00349FA0 | 0x0034A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99987 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.03919 | 1263 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2058 | 7.99991 | 3446325 | Latin 1 / Western European | English - United States | XIA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MSVCRT.dll |
USER32.dll |
Total processes
211
Monitored processes
152
Malicious processes
20
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,18020565065778002912,14239118002758886580,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4442583535619041211 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | C:\Windows\system32\cmd.exe /c certutil.exe -f -addstore root "C:\Windows\TEMP\InstallTemp\servicepkg\BaltimoreCyberTrustRoot.crt" | C:\Windows\system32\cmd.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 292 | ig.exe reseed | C:\PROGRAM FILES\MALWAREBYTES\ANTI-MALWARE\ig-4.exe | — | MBAMService.exe | |||||||||||
User: admin Company: MalwareBytes Integrity Level: LOW Description: Malware Scanner Exit code: 19850672 Version: 1.0.0.27 Modules
| |||||||||||||||
| 320 | ig.exe reseed | C:\PROGRAM FILES\MALWAREBYTES\ANTI-MALWARE\ig-10.exe | — | MBAMService.exe | |||||||||||
User: admin Integrity Level: LOW Exit code: 2876848 Modules
| |||||||||||||||
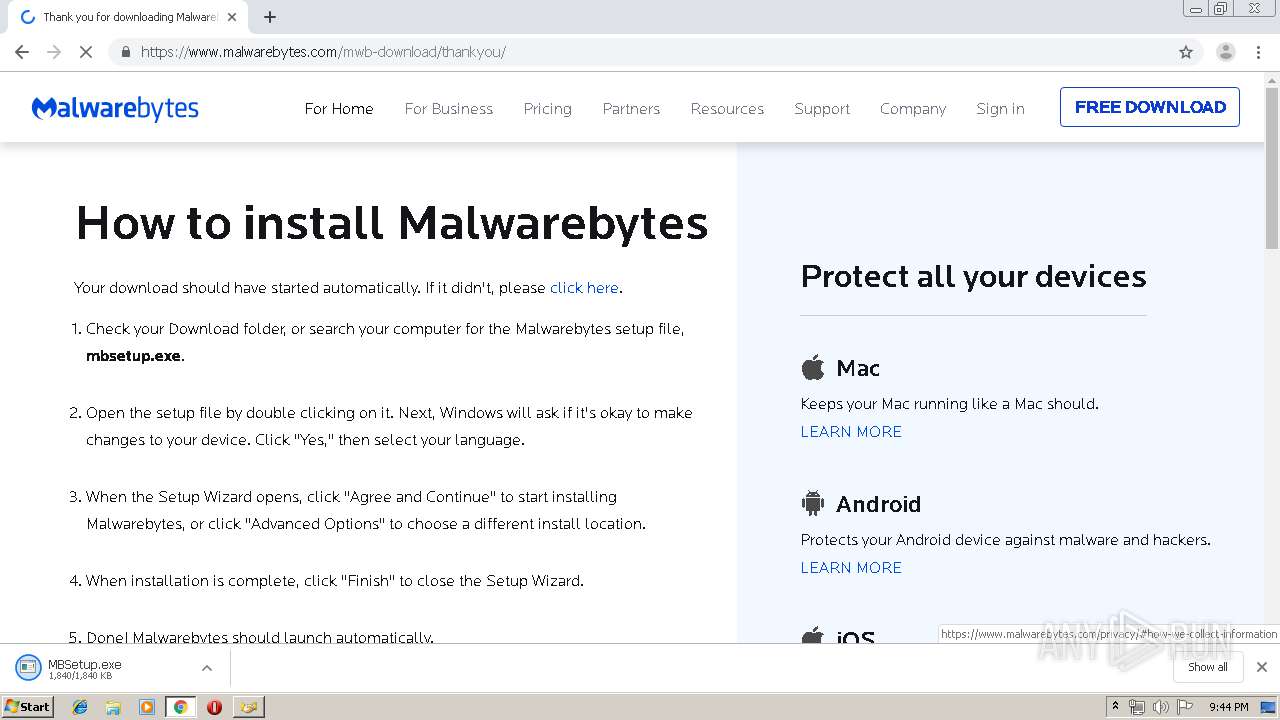
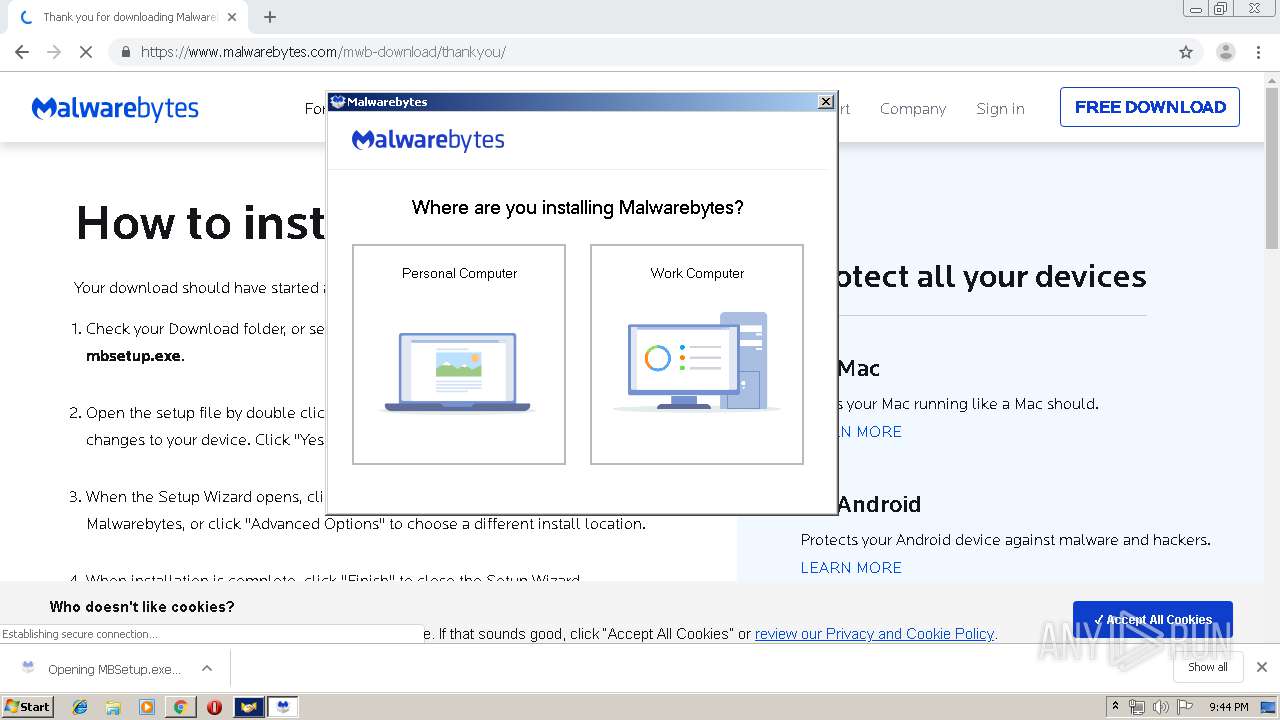
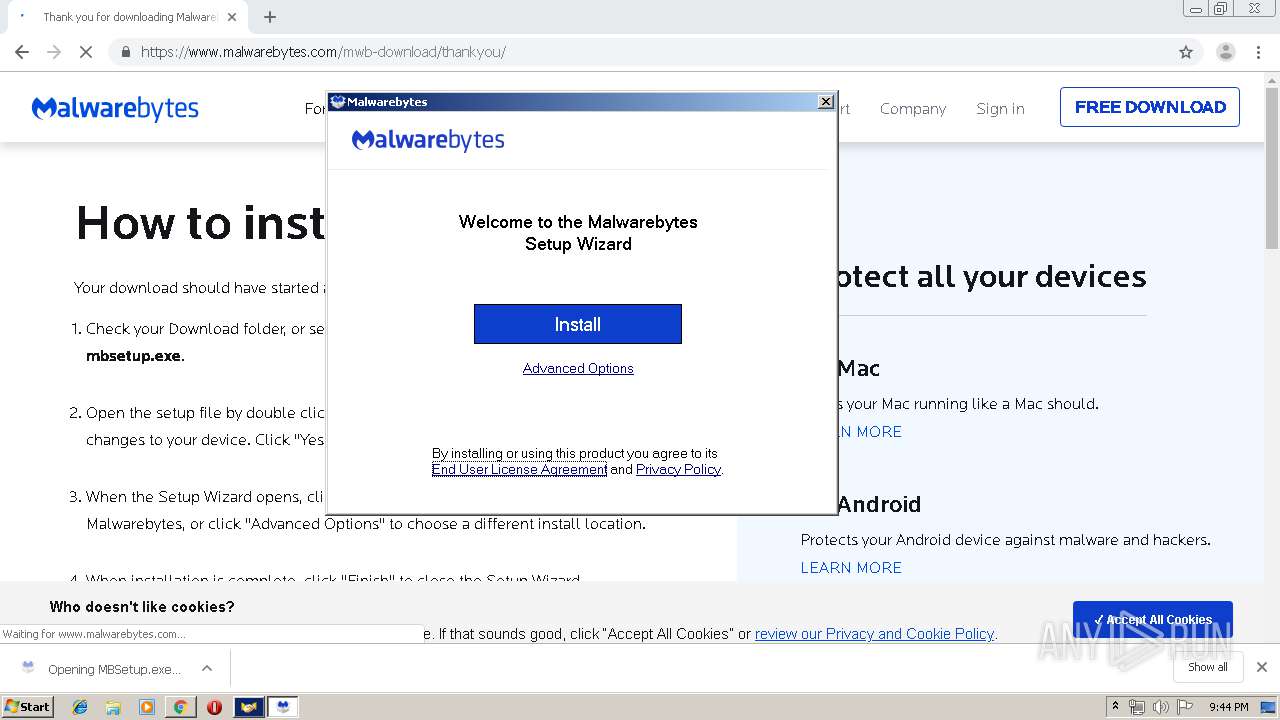
| 532 | "C:\Users\admin\Downloads\MBSetup.exe" | C:\Users\admin\Downloads\MBSetup.exe | chrome.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Exit code: 0 Version: 4.0.0.108 Modules
| |||||||||||||||
| 564 | cmd.exe /c start /b @WanaDecryptor@.exe vs | C:\Windows\system32\cmd.exe | wannacry.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 584 | certutil.exe -f -addstore root "C:\Windows\TEMP\InstallTemp\servicepkg\DigiCertEVRoot.crt" | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 640 | taskdl.exe | C:\Users\admin\AppData\Local\Temp\taskdl.exe | — | wannacry.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: SQL Client Configuration Utility EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | C:\Windows\system32\cmd.exe /c certutil.exe -f -addstore root "C:\Windows\TEMP\InstallTemp\servicepkg\DigiCertEVRoot.crt" | C:\Windows\system32\cmd.exe | — | MBAMInstallerService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,18020565065778002912,14239118002758886580,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=404303667290004705 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 661
Read events
2 141
Write events
1 508
Delete events
12
Modification events
| (PID) Process: | (1268) wannacry.exe | Key: | HKEY_CURRENT_USER\Software\WanaCrypt0r |
| Operation: | write | Name: | wd |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (4012) @WanaDecryptor@.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4012) @WanaDecryptor@.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2800) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\250000e0 |
| Operation: | write | Name: | Element |
Value: 0100000000000000 | |||
| (PID) Process: | (1324) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\16000009 |
| Operation: | write | Name: | Element |
Value: 00 | |||
| (PID) Process: | (1016) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | yyibsxxiapw107 |
Value: "C:\Users\admin\AppData\Local\Temp\tasksche.exe" | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1956-13221697440531375 |
Value: 259 | |||
| (PID) Process: | (1956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
Executable files
345
Suspicious files
803
Text files
1 929
Unknown types
119
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\b.wnry | image | |
MD5:C17170262312F3BE7027BC2CA825BF0C | SHA256:D5E0E8694DDC0548D8E6B87C83D50F4AB85C1DEBADB106D6A6A794C3E746F4FA | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_bulgarian.wnry | text | |
MD5:95673B0F968C0F55B32204361940D184 | SHA256:40B37E7B80CF678D7DD302AAF41B88135ADE6DDF44D89BDBA19CF171564444BD | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_chinese (traditional).wnry | text | |
MD5:2EFC3690D67CD073A9406A25005F7CEA | SHA256:5C7F6AD1EC4BC2C8E2C9C126633215DABA7DE731AC8B12BE10CA157417C97F3A | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\c.wnry | abr | |
MD5:AE08F79A0D800B82FCBE1B43CDBDBEFC | SHA256:055C7760512C98C8D51E4427227FE2A7EA3B34EE63178FE78631FA8AA6D15622 | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_danish.wnry | text | |
MD5:2C5A3B81D5C4715B7BEA01033367FCB5 | SHA256:A75BB44284B9DB8D702692F84909A7E23F21141866ADF3DB888042E9109A1CB6 | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_chinese (simplified).wnry | text | |
MD5:0252D45CA21C8E43C9742285C48E91AD | SHA256:845D0E178AEEBD6C7E2A2E9697B2BF6CF02028C50C288B3BA88FE2918EA2834A | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_english.wnry | text | |
MD5:FE68C2DC0D2419B38F44D83F2FCF232E | SHA256:26FD072FDA6E12F8C2D3292086EF0390785EFA2C556E2A88BD4673102AF703E5 | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_french.wnry | text | |
MD5:4E57113A6BF6B88FDD32782A4A381274 | SHA256:9BD38110E6523547AED50617DDC77D0920D408FAEED2B7A21AB163FDA22177BC | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_czech.wnry | text | |
MD5:537EFEECDFA94CC421E58FD82A58BA9E | SHA256:5AFA4753AFA048C6D6C39327CE674F27F5F6E5D3F2A060B7A8AED61725481150 | |||
| 1268 | wannacry.exe | C:\Users\admin\AppData\Local\Temp\msg\m_greek.wnry | text | |
MD5:FB4E8718FEA95BB7479727FDE80CB424 | SHA256:E13CC9B13AA5074DC45D50379ECEB17EE39A0C2531AB617D93800FE236758CA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
221
DNS requests
168
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1928 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 512 b | whitelisted |
1928 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
1248 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA%2BoSQYV1wCgviF2%2FcXsbb0%3D | US | der | 471 b | whitelisted |
1248 | MBAMService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSYagvY3tfizDNoybzVSPFZmSEm0wQUe2jOKarAF75JeuHlP9an90WPNTICEAii7E54oJ4XSxkuVTWYS1k%3D | US | der | 471 b | whitelisted |
1928 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 517 b | whitelisted |
1928 | chrome.exe | GET | 200 | 13.35.254.82:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
1928 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
1928 | chrome.exe | GET | 200 | 8.248.115.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
1928 | chrome.exe | GET | 200 | 8.248.115.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
1928 | chrome.exe | GET | 200 | 84.15.64.13:80 | http://r2---sn-cpux-8ovs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.206.175.219&mm=28&mn=sn-cpux-8ovs&ms=nvh&mt=1577223659&mv=u&mvi=1&pl=21&shardbypass=yes | LT | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | taskhsvc.exe | 217.79.179.177:9001 | — | myLoc managed IT AG | DE | suspicious |
2892 | taskhsvc.exe | 128.31.0.39:9101 | — | Massachusetts Institute of Technology | US | malicious |
2892 | taskhsvc.exe | 158.174.255.235:4430 | — | Bahnhof Internet AB | SE | suspicious |
2892 | taskhsvc.exe | 62.210.123.24:443 | — | Online S.a.s. | FR | suspicious |
2892 | taskhsvc.exe | 93.186.200.213:9001 | — | myLoc managed IT AG | DE | suspicious |
1928 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1928 | chrome.exe | 216.58.205.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
1928 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1928 | chrome.exe | 84.15.64.13:80 | r2---sn-cpux-8ovs.gvt1.com | UAB Bite Lietuva | LT | whitelisted |
1928 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-cpux-8ovs.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2892 | taskhsvc.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 376 |
2892 | taskhsvc.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
2892 | taskhsvc.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TOR SSL connection |
2892 | taskhsvc.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
2892 | taskhsvc.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 569 |
2892 | taskhsvc.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 190 |
2892 | taskhsvc.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 711 |
2892 | taskhsvc.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
2892 | taskhsvc.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
1928 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | Description:
|
mbamtray.exe | Connect to the exception(int,QString,QString,QString) signal to catch this exception
|
mbamtray.exe | Help :
|
mbamtray.exe | Code : -2147467259
|
mbamtray.exe | Description:
|
mbamtray.exe | QAxBase: Error calling IDispatch member GetLastActiveScanner: Exception thrown by server
|
mbamtray.exe | qt.scenegraph.general: Loading backend software
|
mbamtray.exe | class QUrl __thiscall PageStatusMonitor::processRedirectUrl(const class QUrl &,const class QUrl &) const Potential Redirect is: "https://cleo.mb-internal.com/?x-source=trial-avail&ADDITIONAL_x-source=inproduct&ADDITIONAL_machineid=81e0cbe954fffb2dd4e10325decf35d73a7107c5&x-action=comparison_chart&ADDITIONAL_x-token_secret=jgQTeomKKCX-ohzCvjCx3kBoFTSELqVEnjpdujhGKxAWwRzt4h-KGvWhgzcBqySel1QrviDIFDE68IPKpbLb7ko1J2BwQawW92xFs3ugUvGGJgZo5IPksPP4LK2lcK2w&x-token_secret=jgQTeomKKCX-ohzCvjCx3kBoFTSELqVEnjpdujhGKxAWwRzt4h-KGvWhgzcBqySel1QrviDIFDE68IPKpbLb7ko1J2BwQawW92xFs3ugUvGGJgZo5IPksPP4LK2lcK2w&x-prodcode=MBAM-C&LANG=en" Last Redirect is: ""
|
mbamtray.exe | void __thiscall PageStatusMonitor::OnRequestFinished(class QNetworkReply *) " Attempting redirect to: https://cleo.mb-internal.com/?x-source=trial-avail&ADDITIONAL_x-source=inproduct&ADDITIONAL_machineid=81e0cbe954fffb2dd4e10325decf35d73a7107c5&x-action=comparison_chart&ADDITIONAL_x-token_secret=jgQTeomKKCX-ohzCvjCx3kBoFTSELqVEnjpdujhGKxAWwRzt4h-KGvWhgzcBqySel1QrviDIFDE68IPKpbLb7ko1J2BwQawW92xFs3ugUvGGJgZo5IPksPP4LK2lcK2w&x-token_secret=jgQTeomKKCX-ohzCvjCx3kBoFTSELqVEnjpdujhGKxAWwRzt4h-KGvWhgzcBqySel1QrviDIFDE68IPKpbLb7ko1J2BwQawW92xFs3ugUvGGJgZo5IPksPP4LK2lcK2w&x-prodcode=MBAM-C&LANG=en"
|