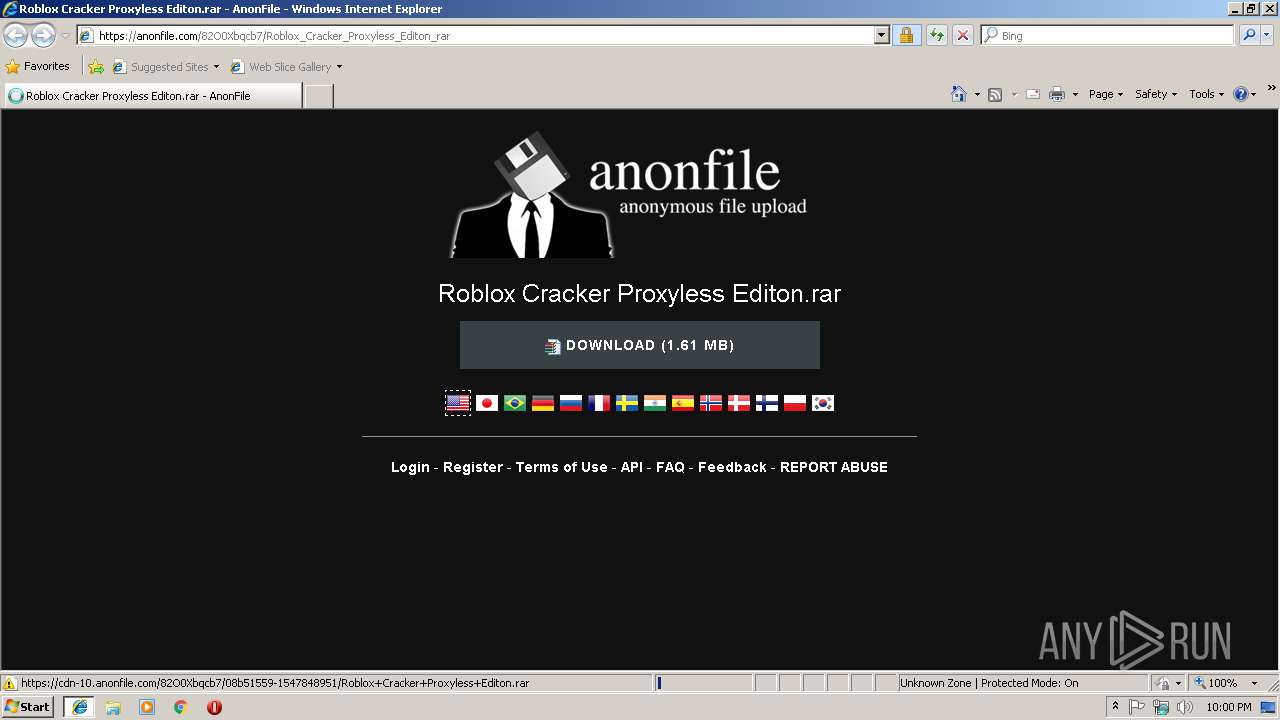
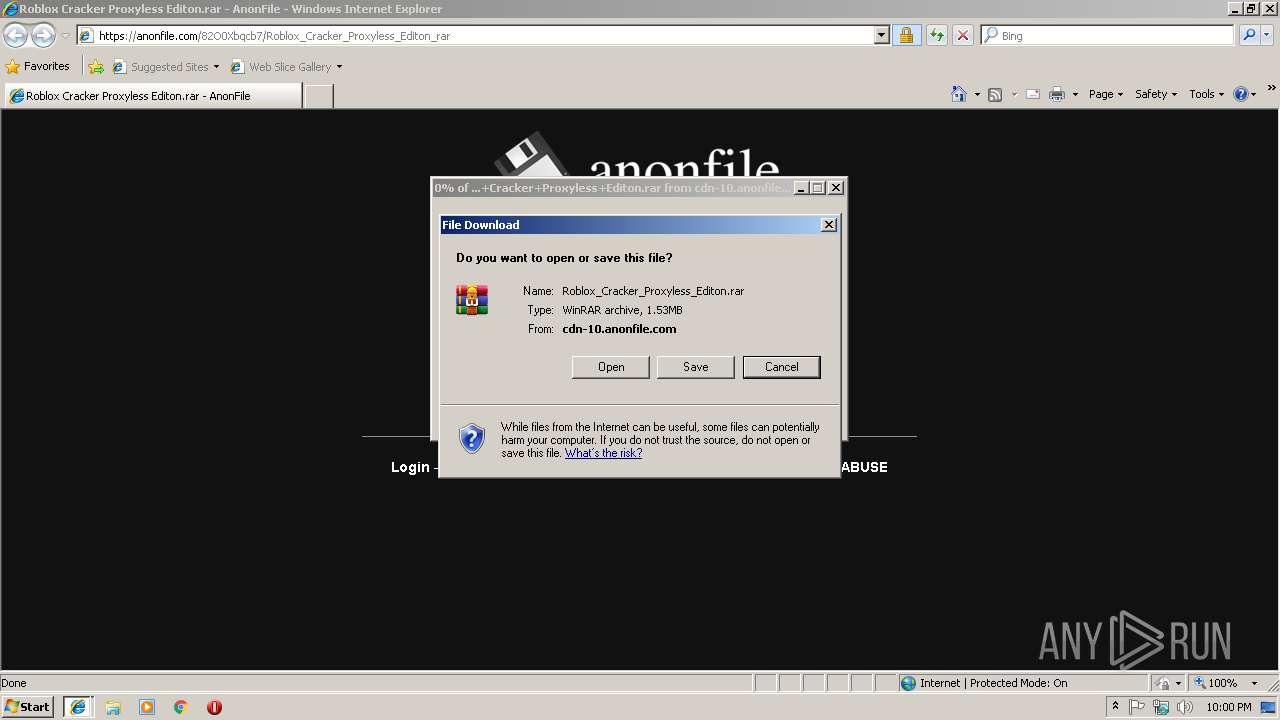
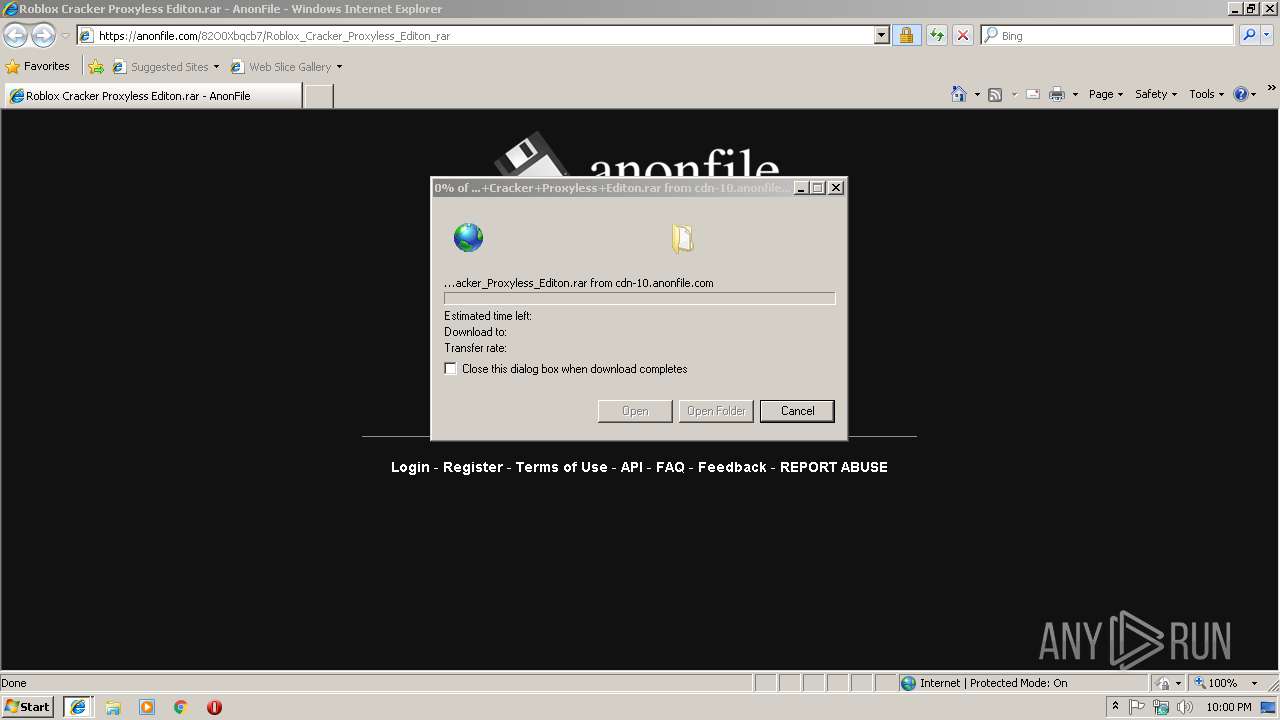
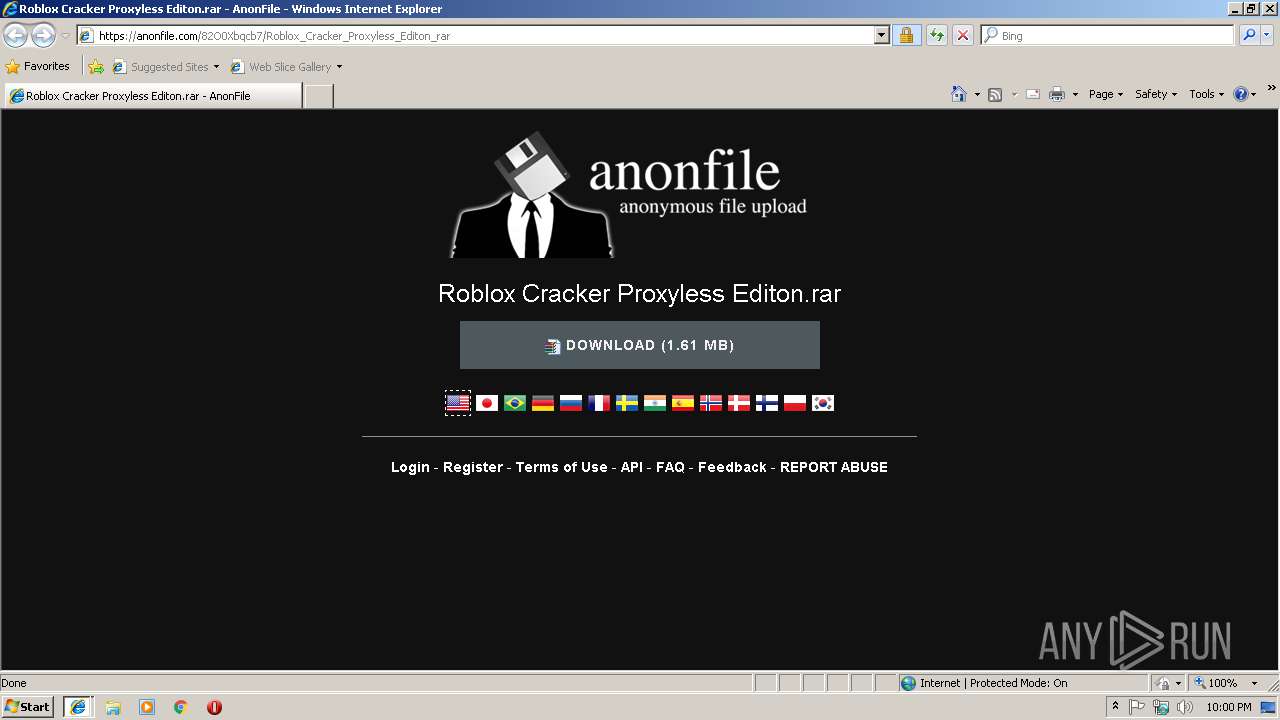
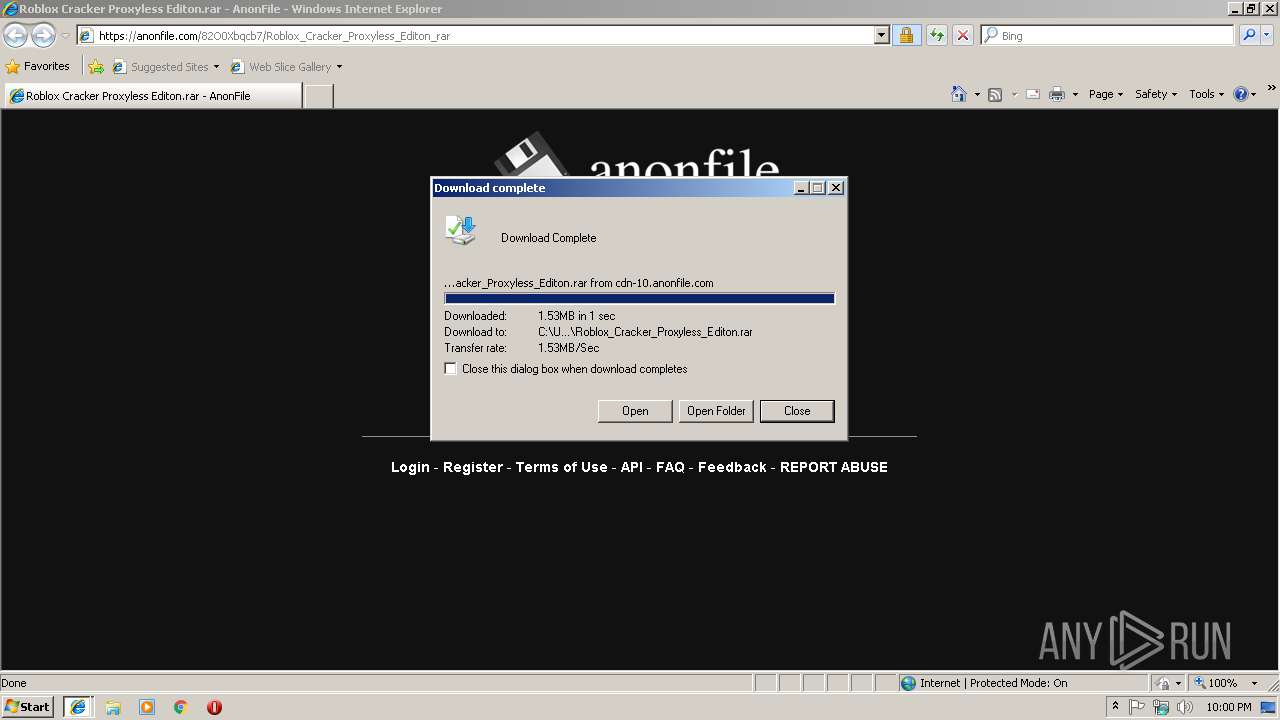
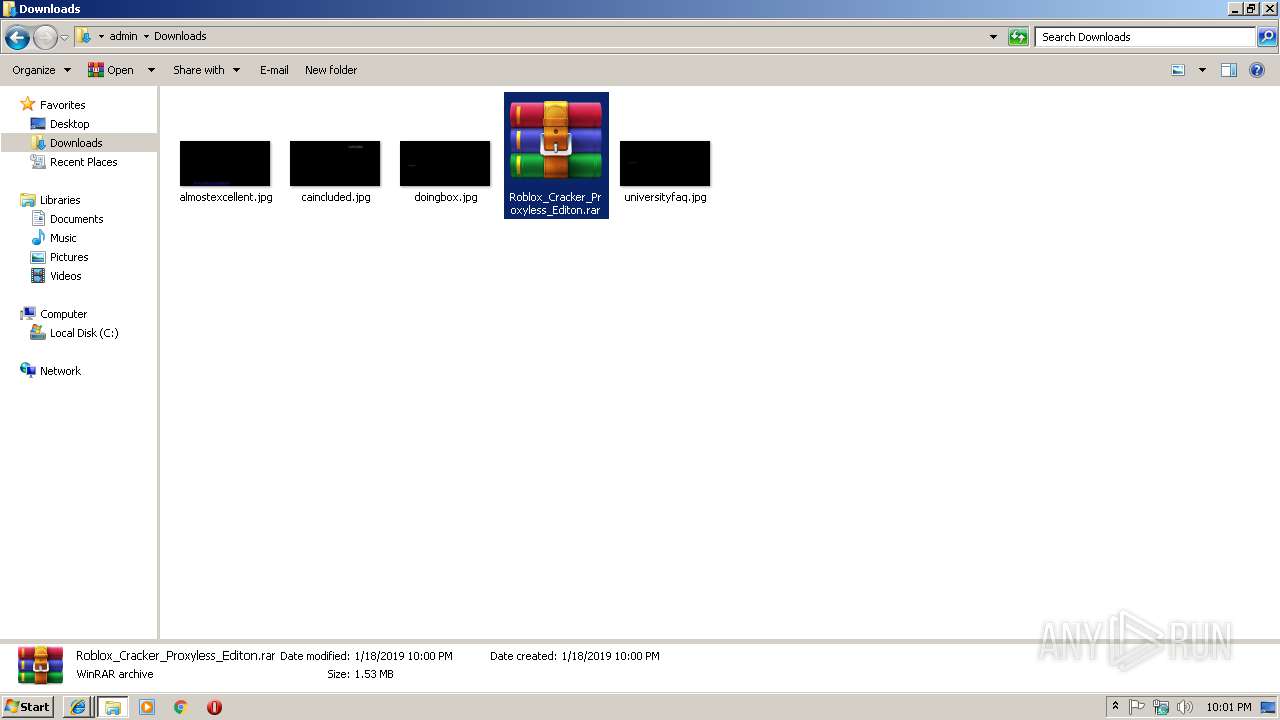
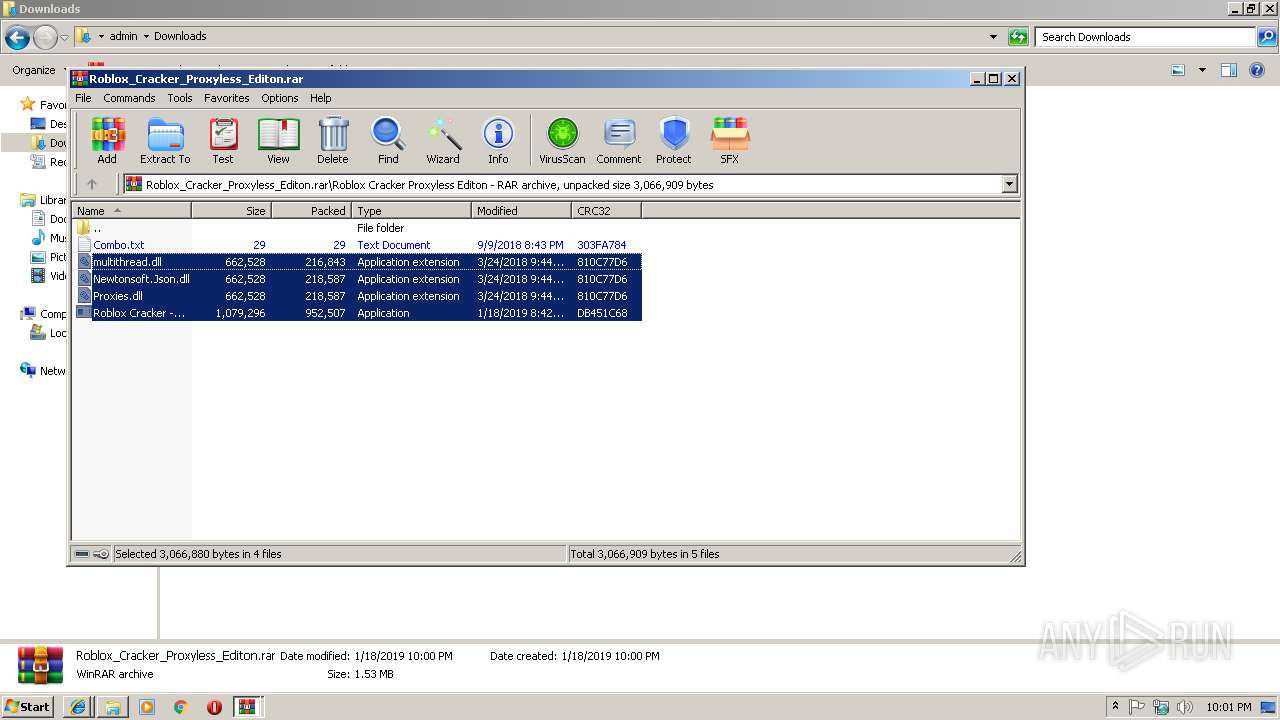
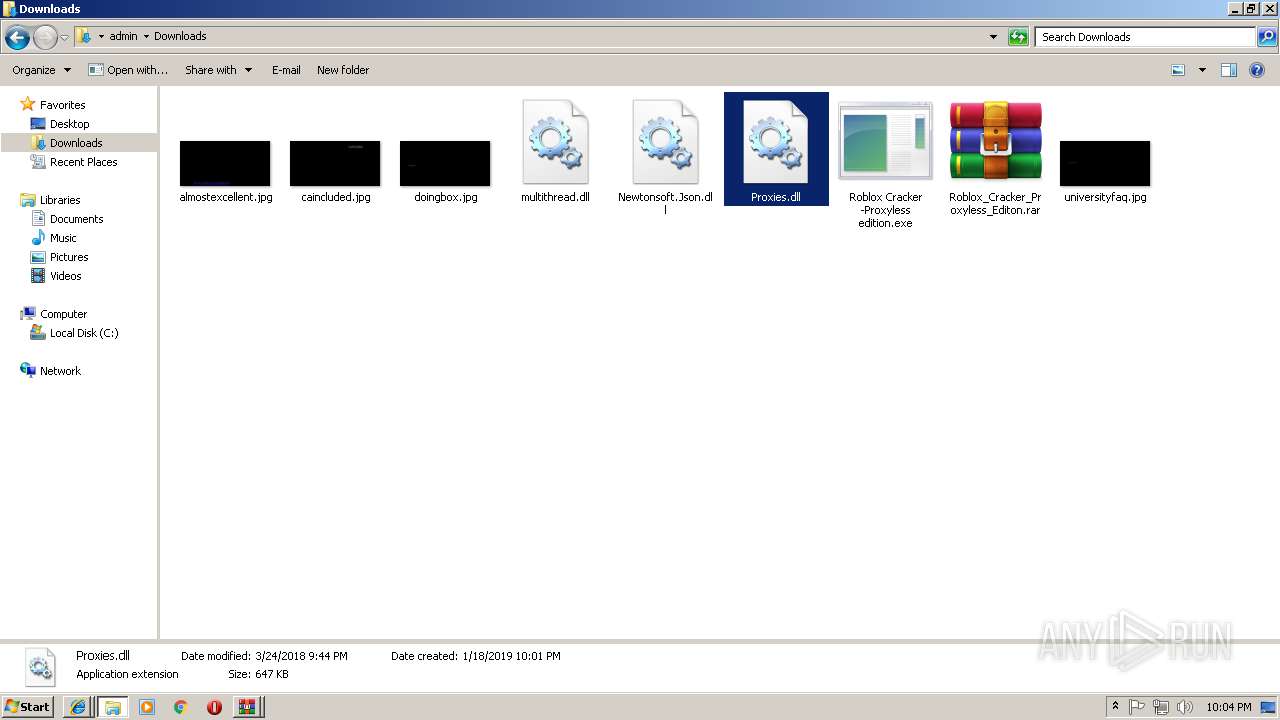
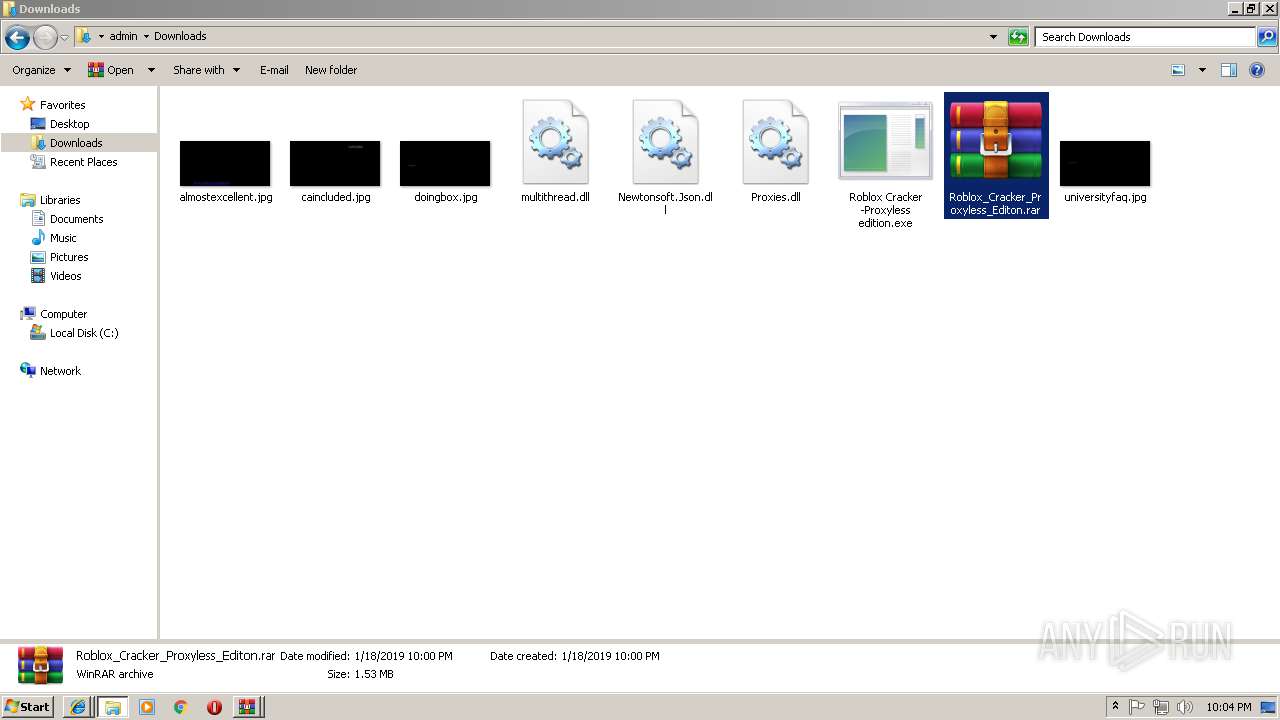
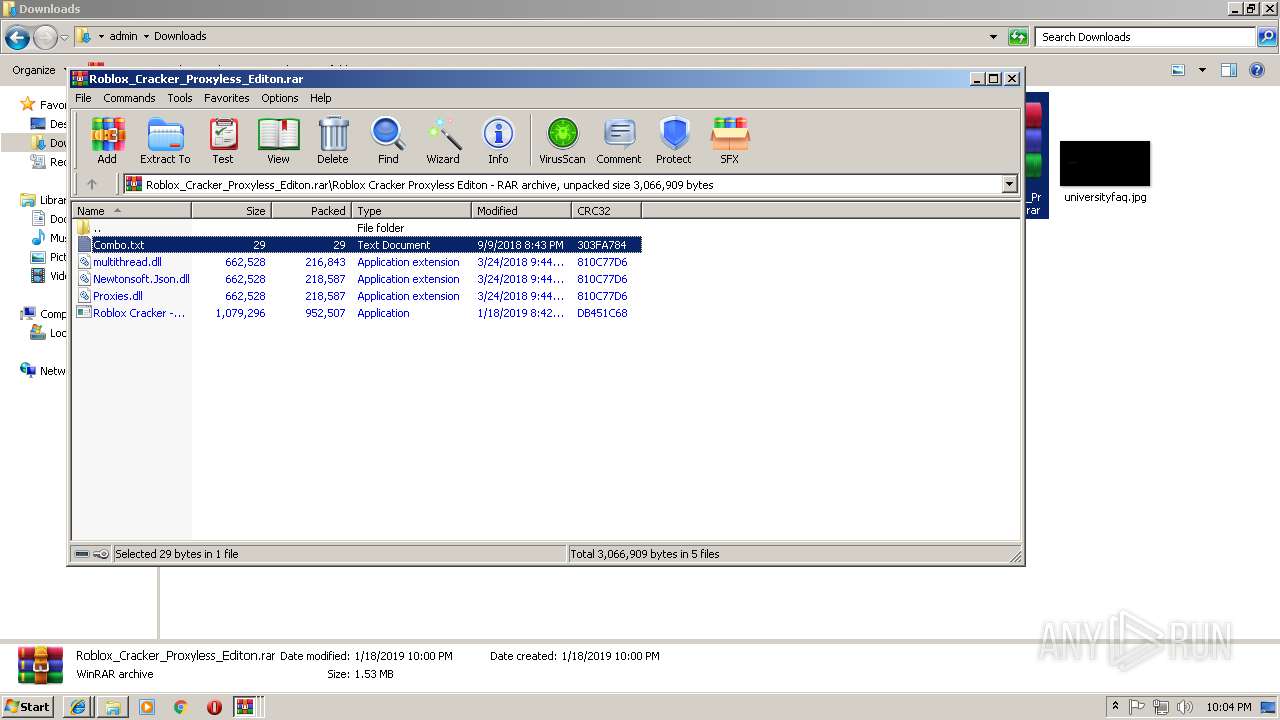
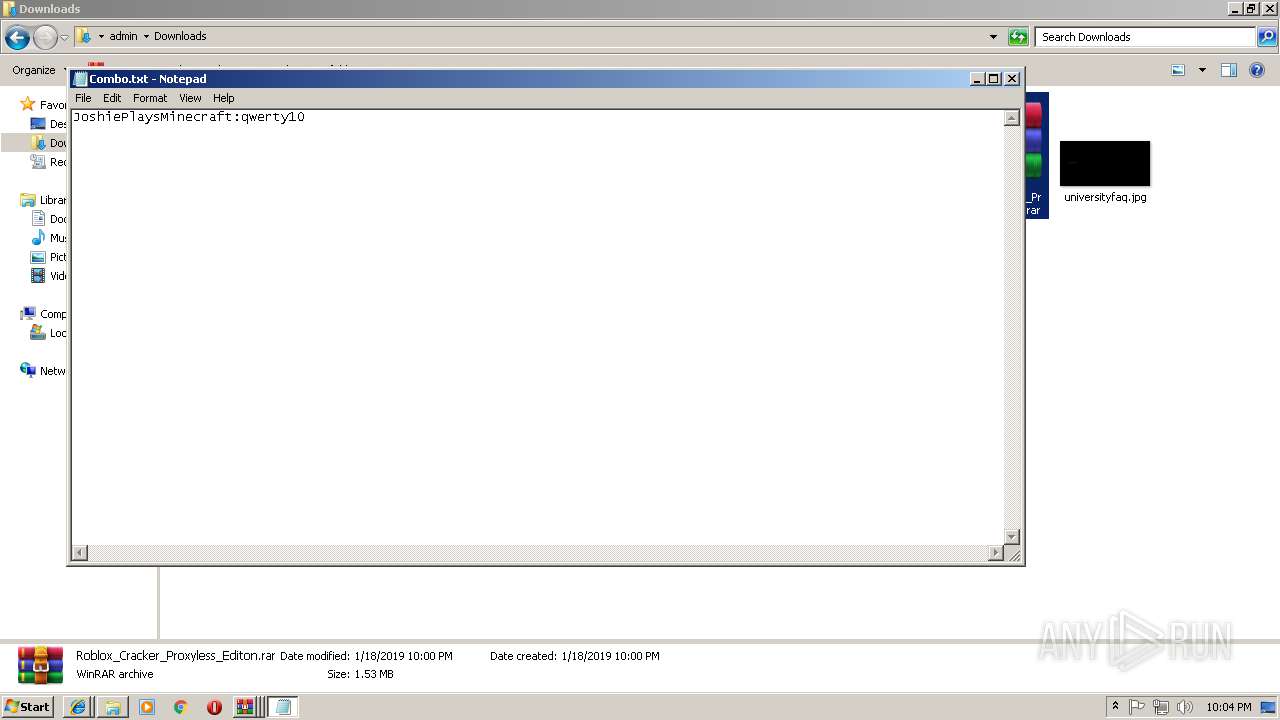
| URL: | https://anonfile.com/82O0Xbqcb7/Roblox_Cracker_Proxyless_Editon_rar |
| Full analysis: | https://app.any.run/tasks/0794ce15-027e-42f0-8840-11627f15f4d0 |
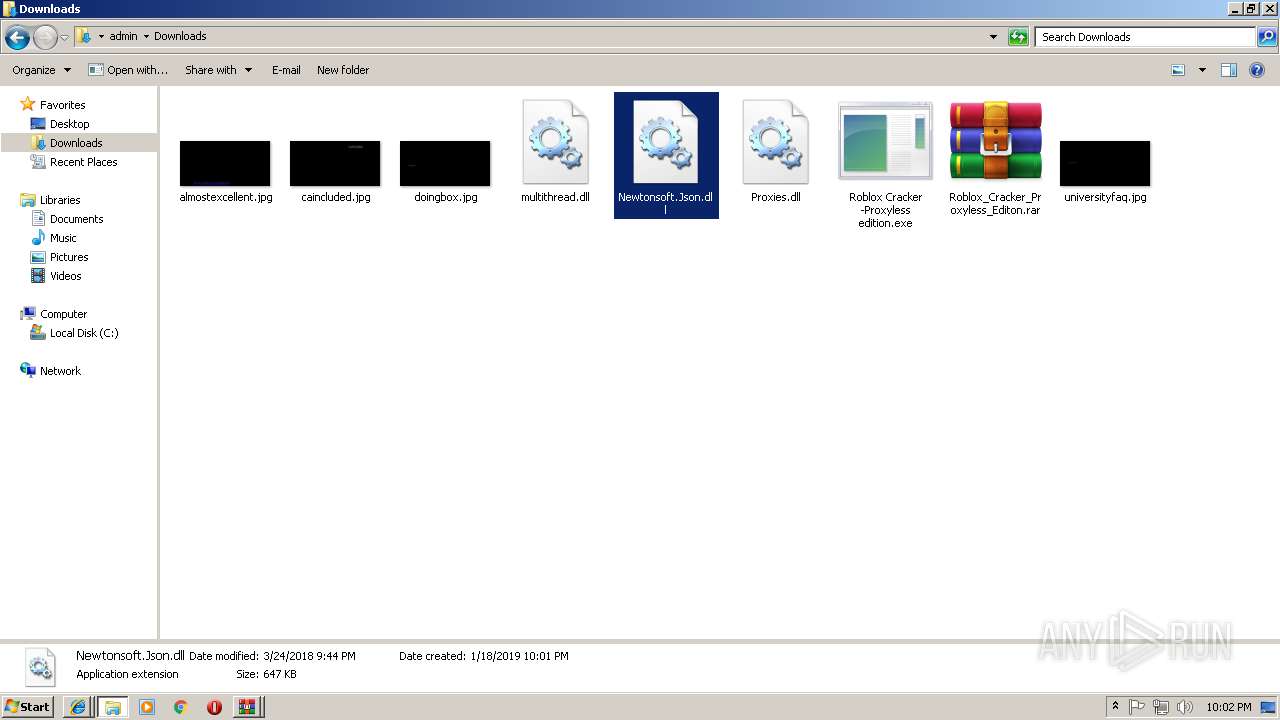
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | January 18, 2019, 22:00:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DED21298AC6F482776B5579E18E564B1 |
| SHA1: | BF05E019E5E6256FF2524A6DD9B01903A1E49539 |
| SHA256: | EC63EE6B78444B730D73609DE575BD5C19714B254C1E71F8174DA5DFE800BFA5 |
| SSDEEP: | 3:N8RGBOQGGCdGcJGd6O:2g4QGGCdGzd6O |
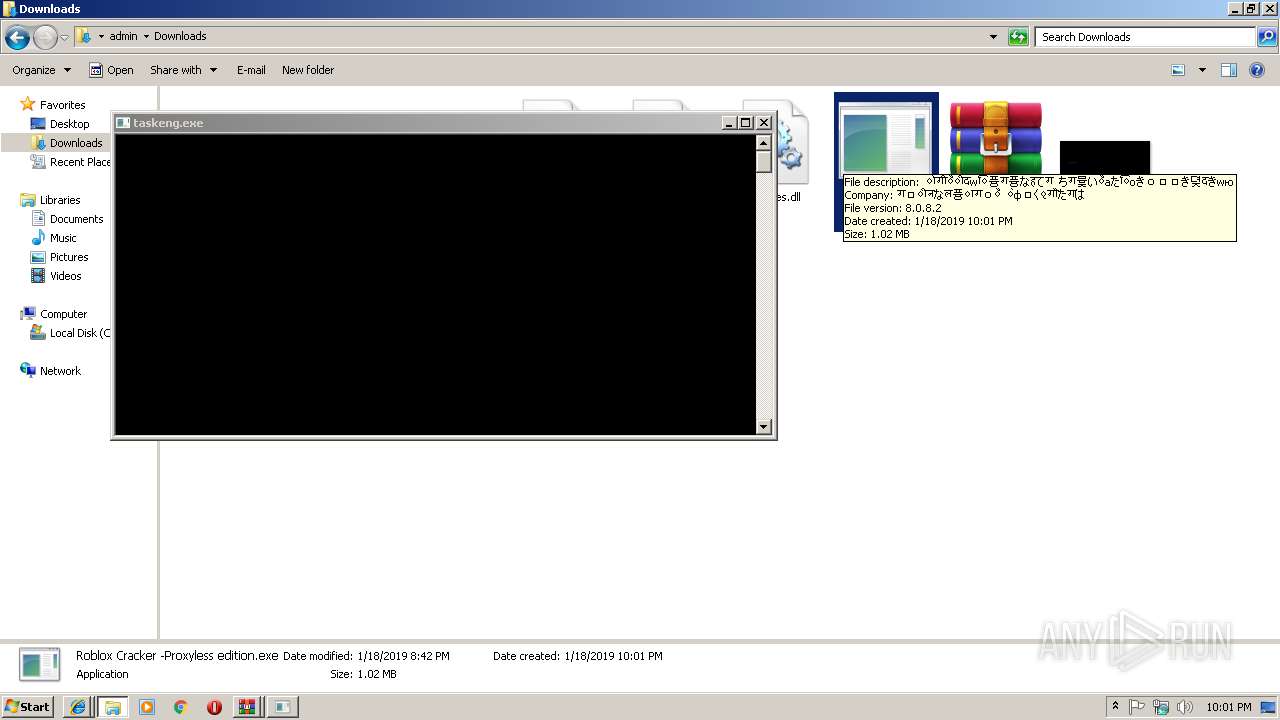
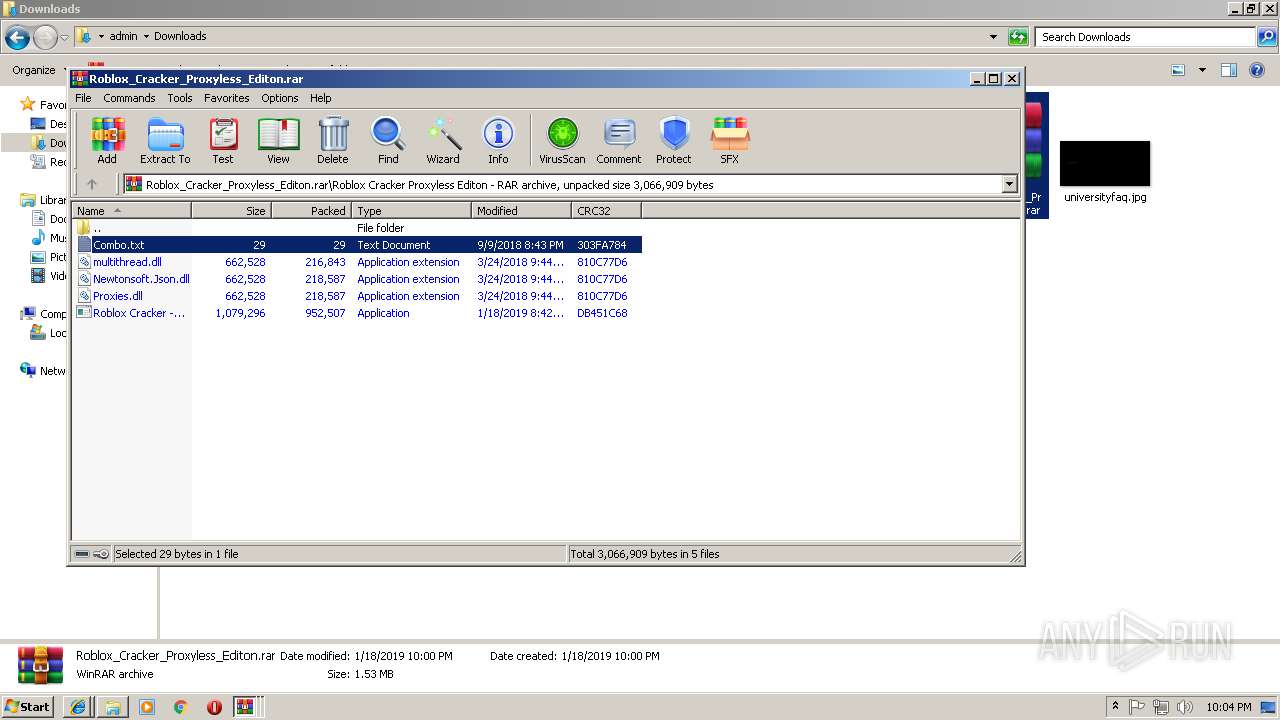
MALICIOUS
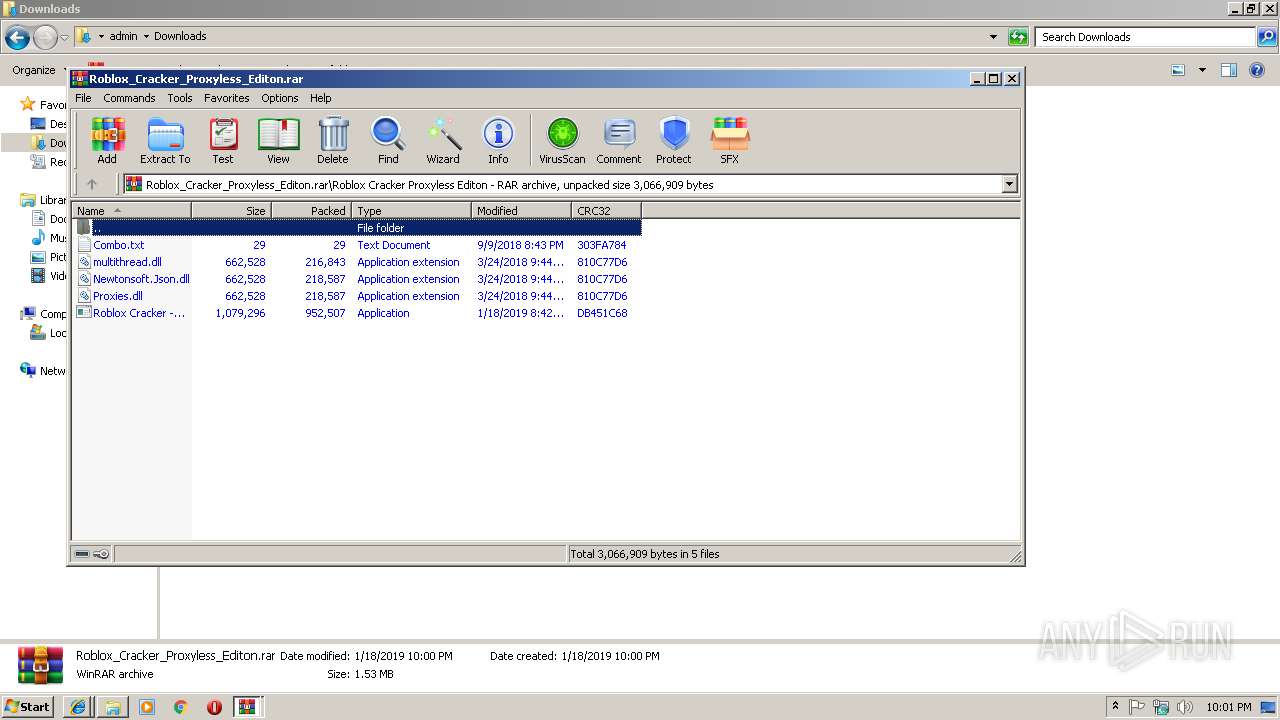
Loads dropped or rewritten executable
- explorer.exe (PID: 2028)
- SearchProtocolHost.exe (PID: 612)
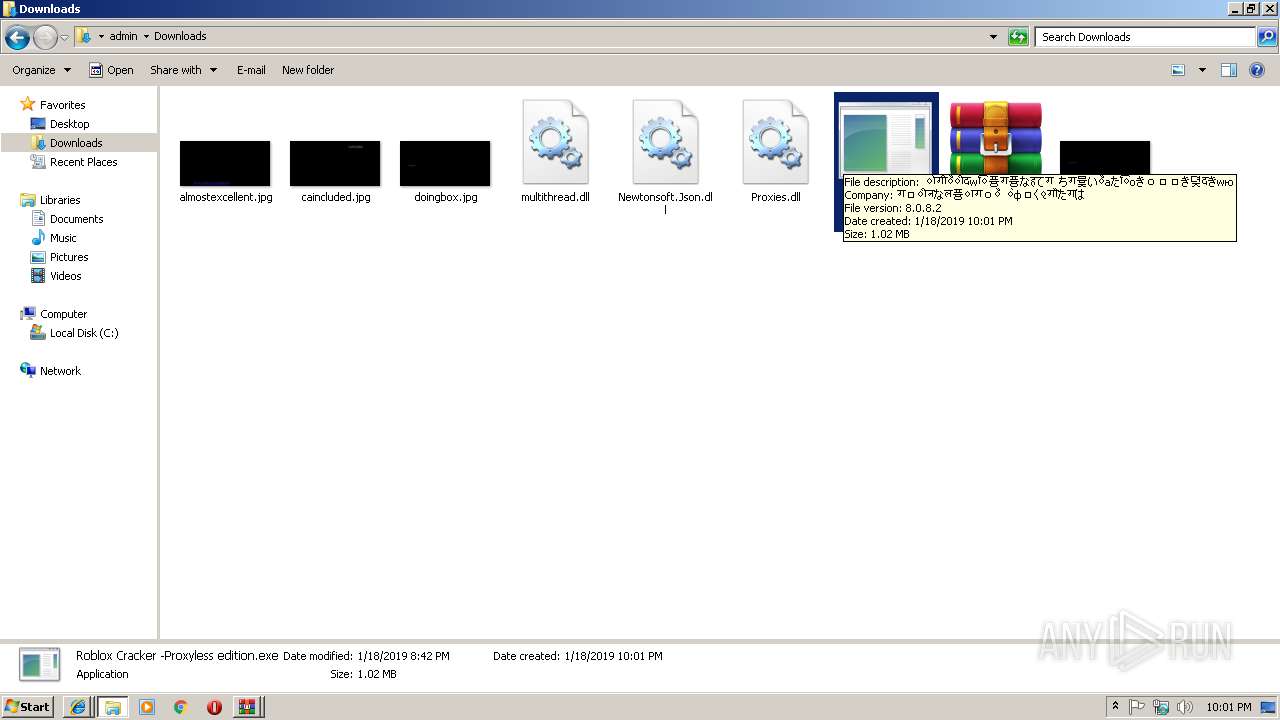
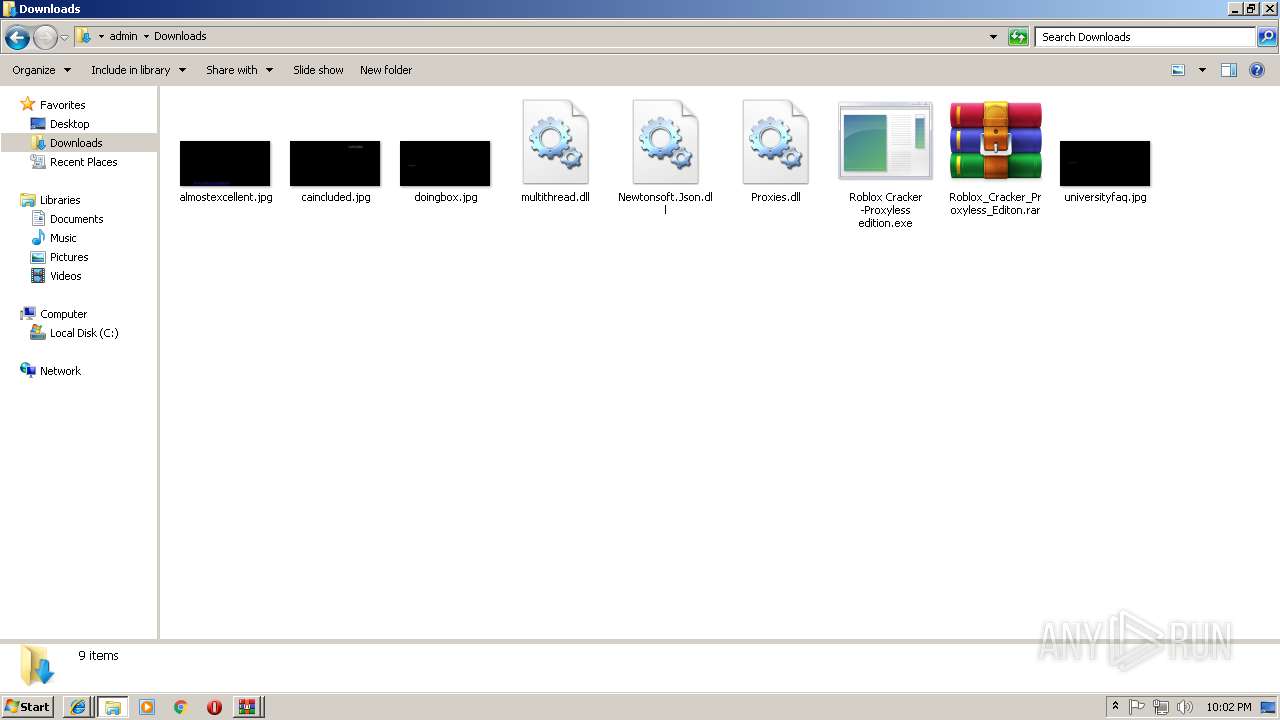
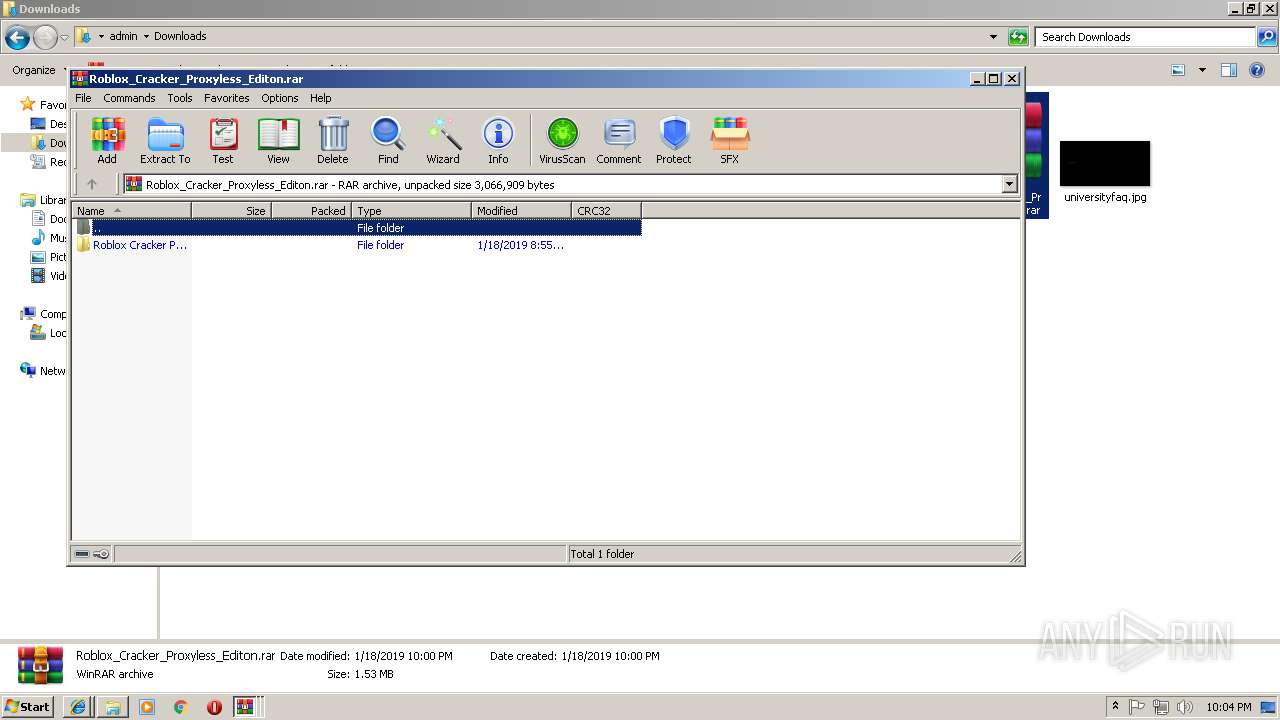
Application was dropped or rewritten from another process
- Roblox Cracker -Proxyless edition.exe (PID: 2684)
- ुग्पち.exe (PID: 3096)
- MemeReview.exe (PID: 2344)
- MemeReview.exe (PID: 2888)
- Roblox Cracker -Proxyless edition.exe (PID: 3056)
- ुग्पち.exe (PID: 3392)
Orcus was detected
- Regasm.exe (PID: 2856)
- Regasm.exe (PID: 1840)
Loads the Task Scheduler COM API
- Regasm.exe (PID: 2856)
Orcus RAT was detected
- MemeReview.exe (PID: 2344)
SUSPICIOUS
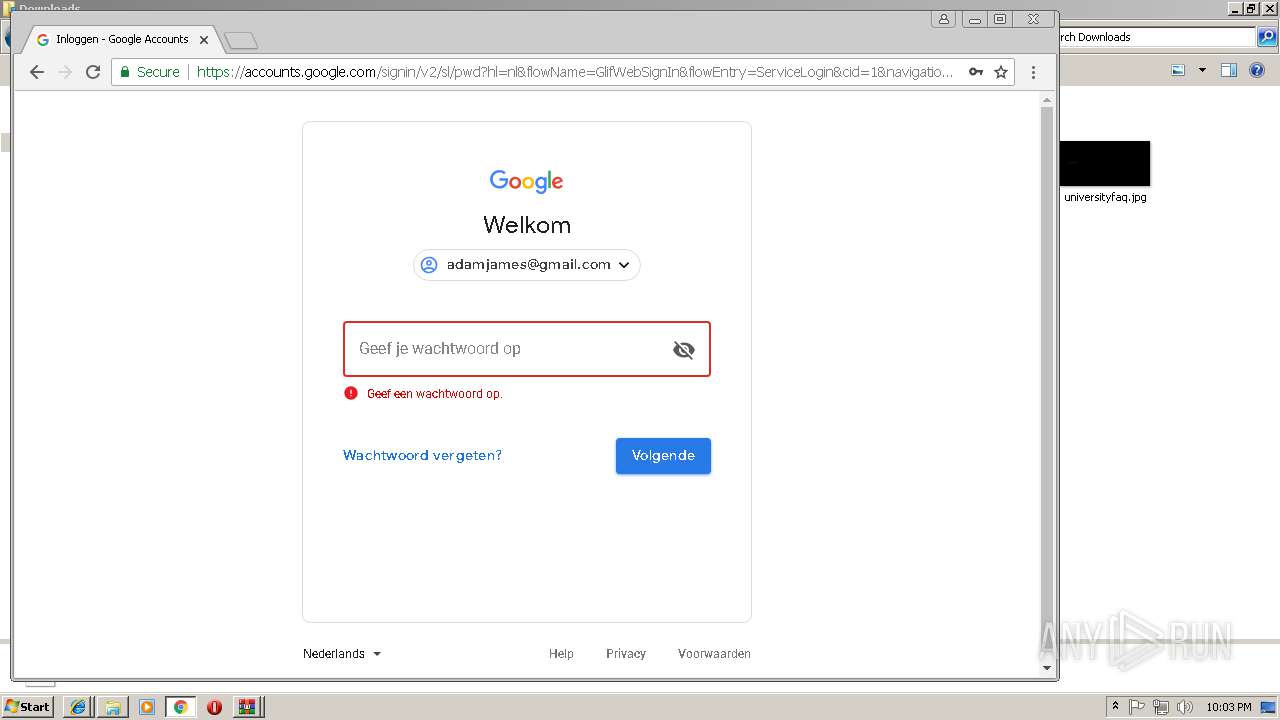
Starts Internet Explorer
- explorer.exe (PID: 2028)
Reads Internet Cache Settings
- explorer.exe (PID: 2028)
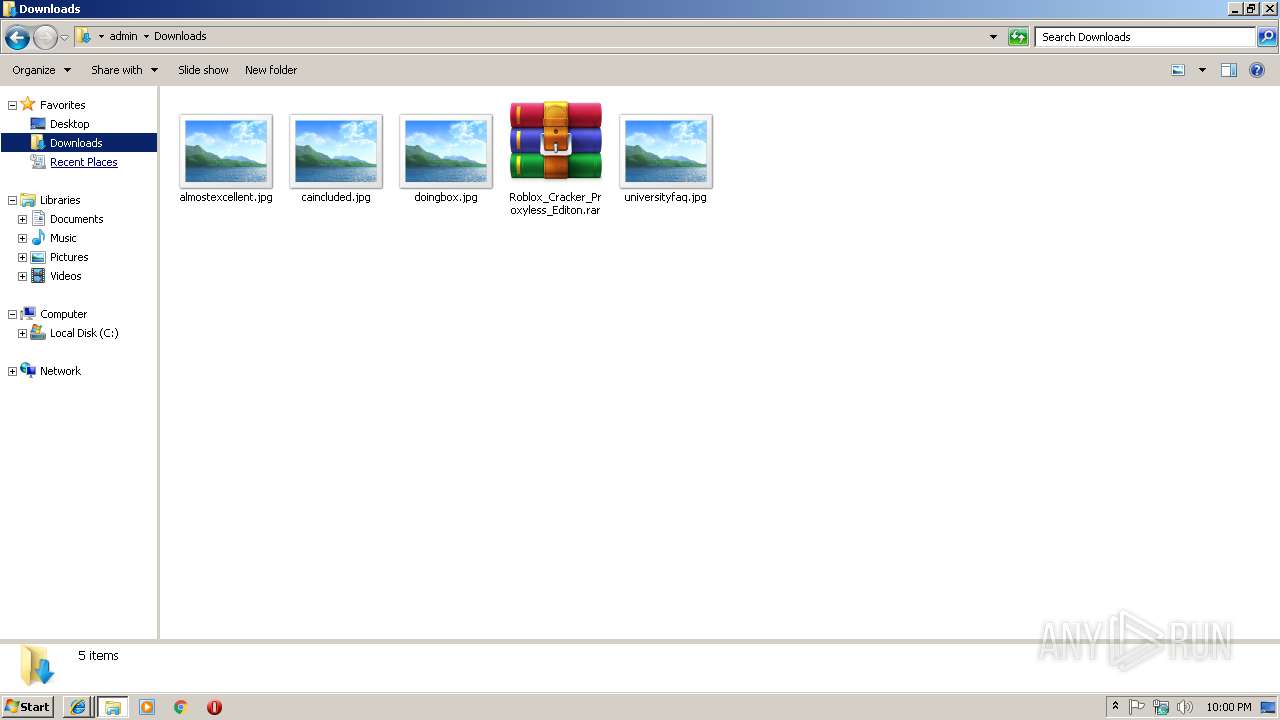
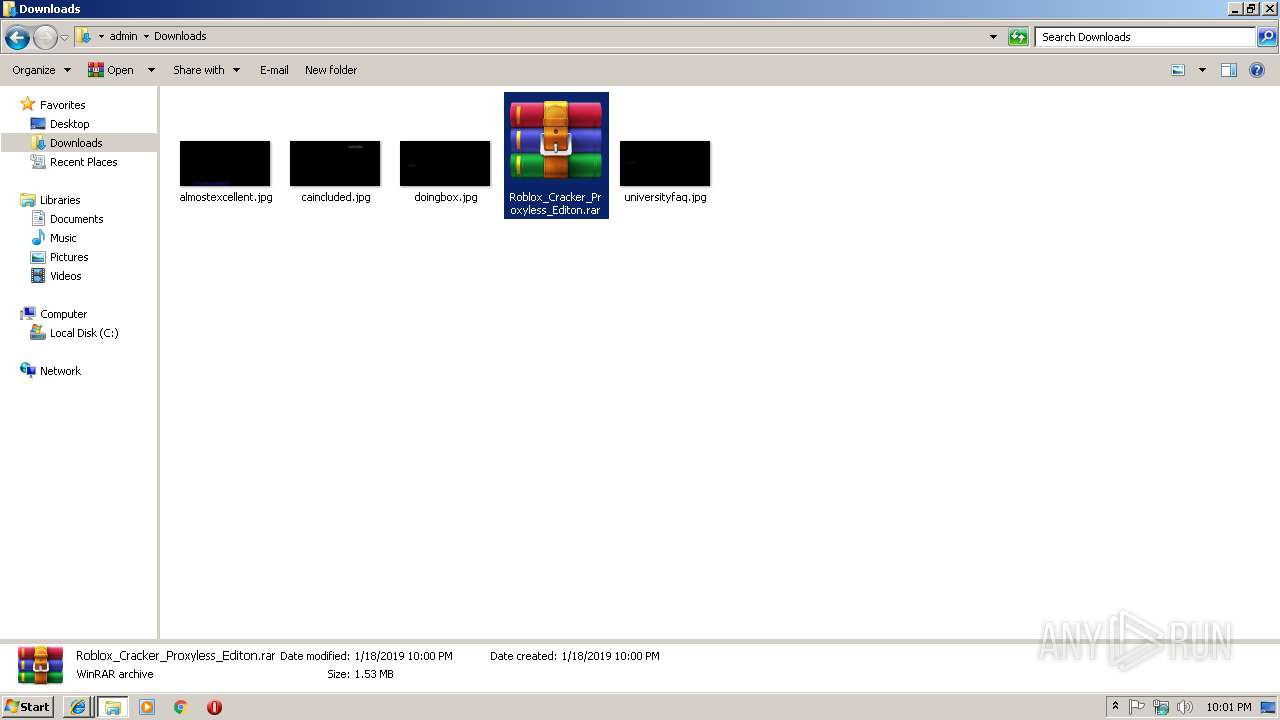
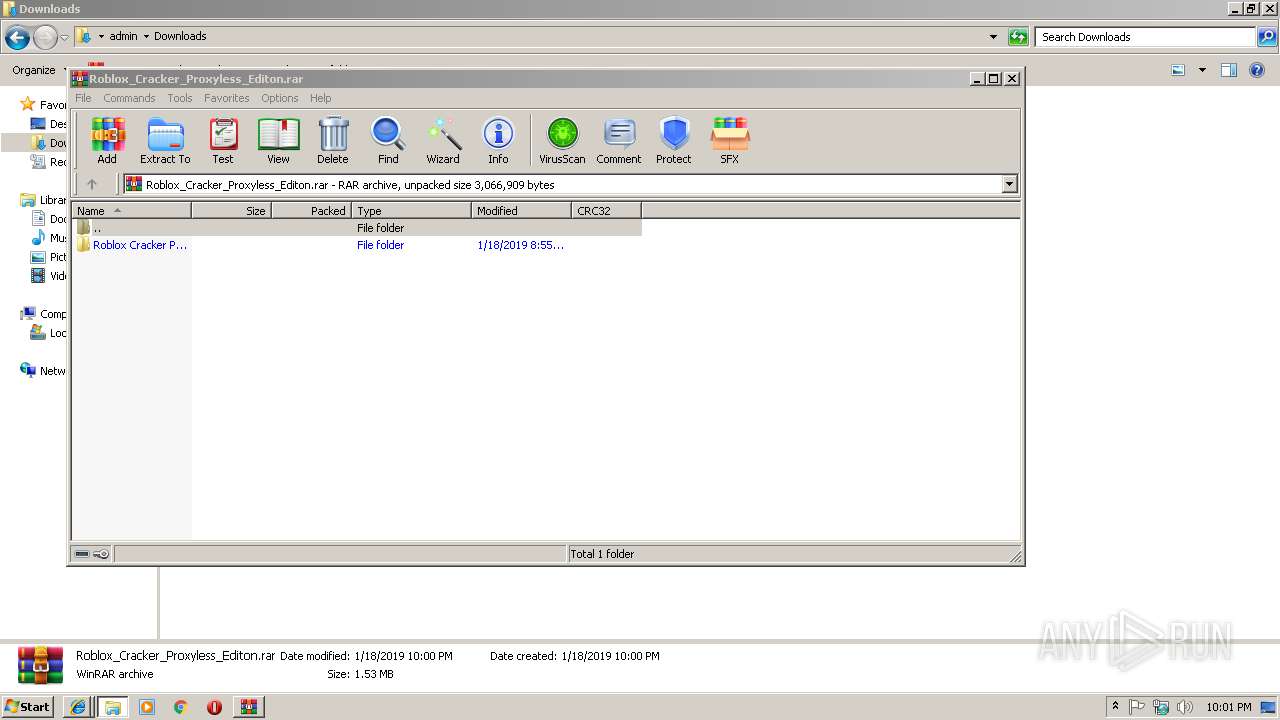
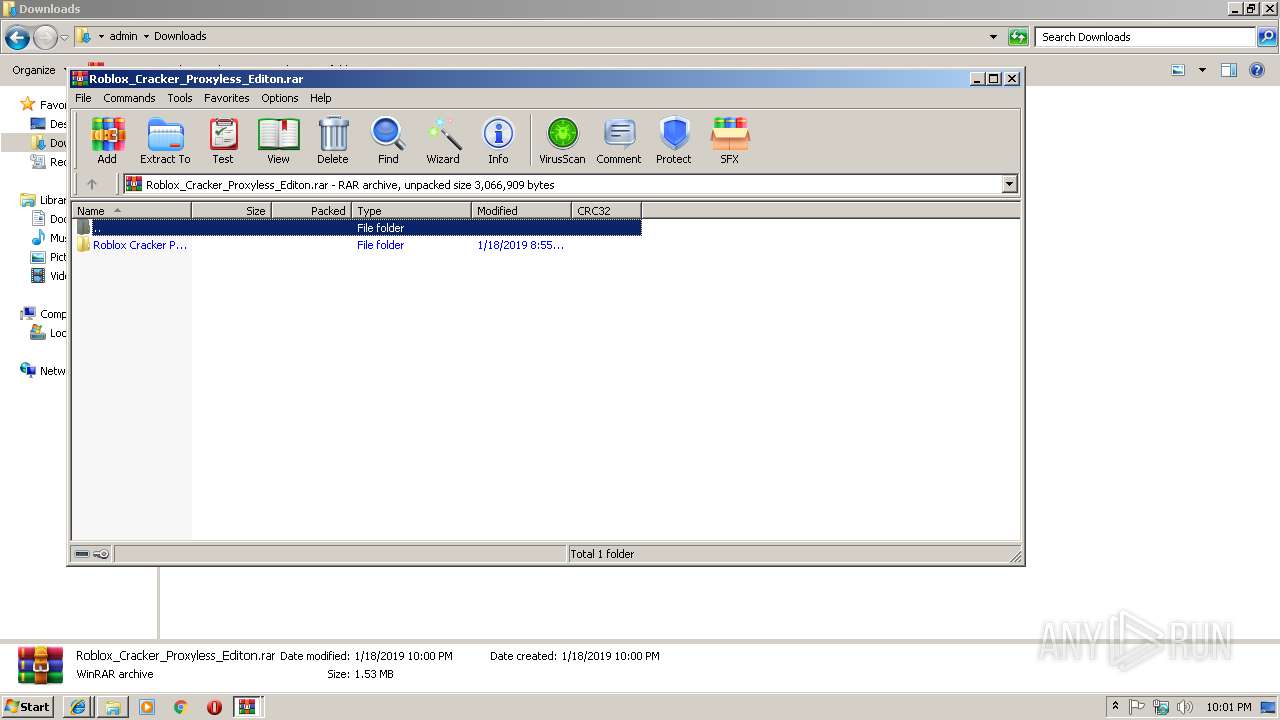
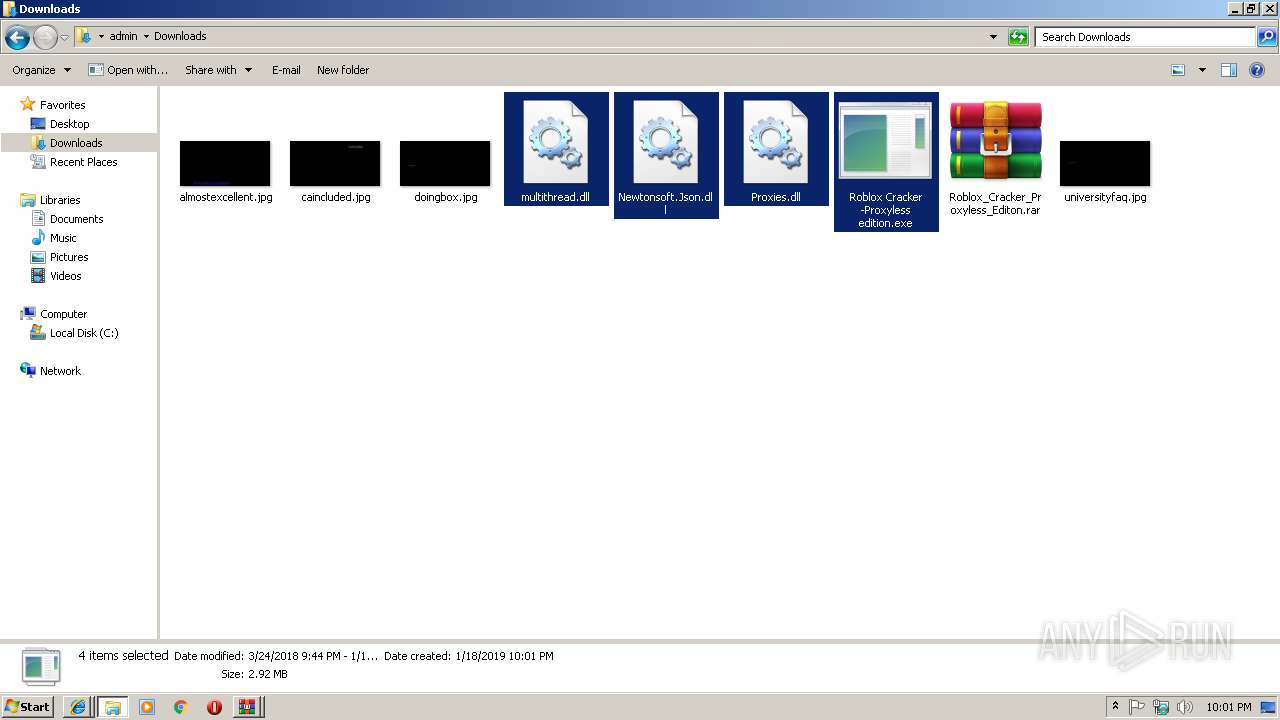
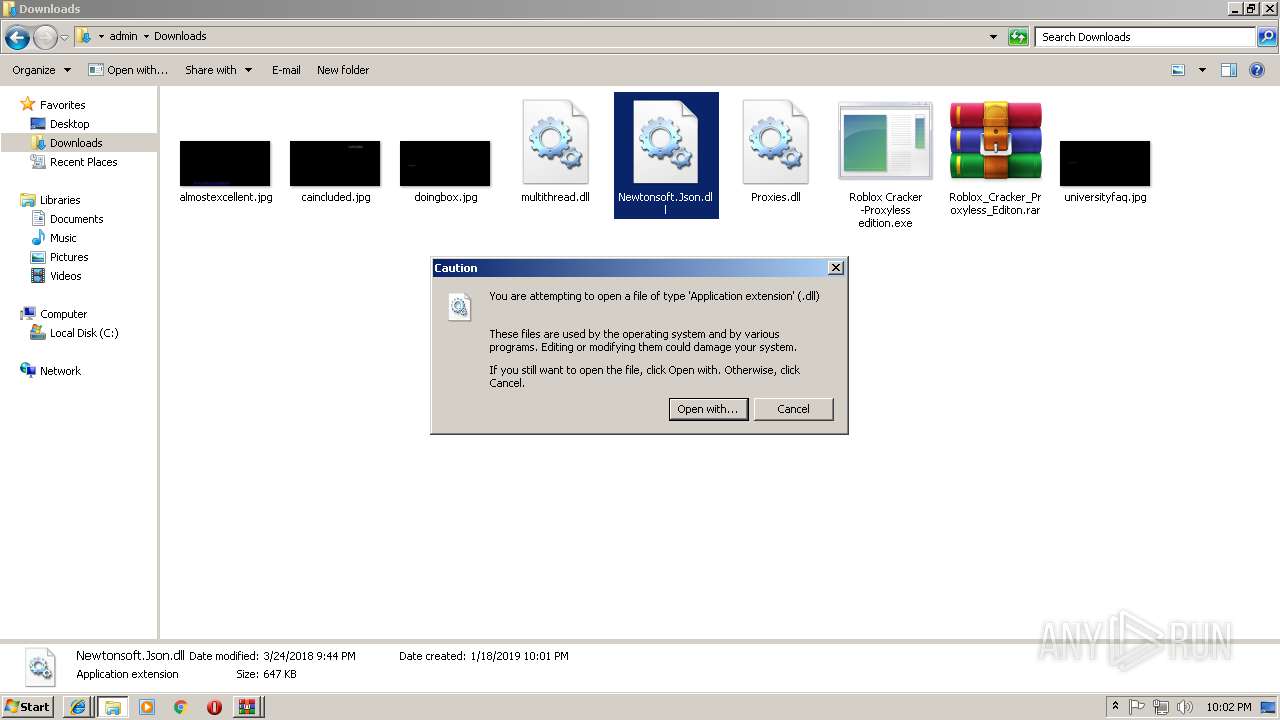
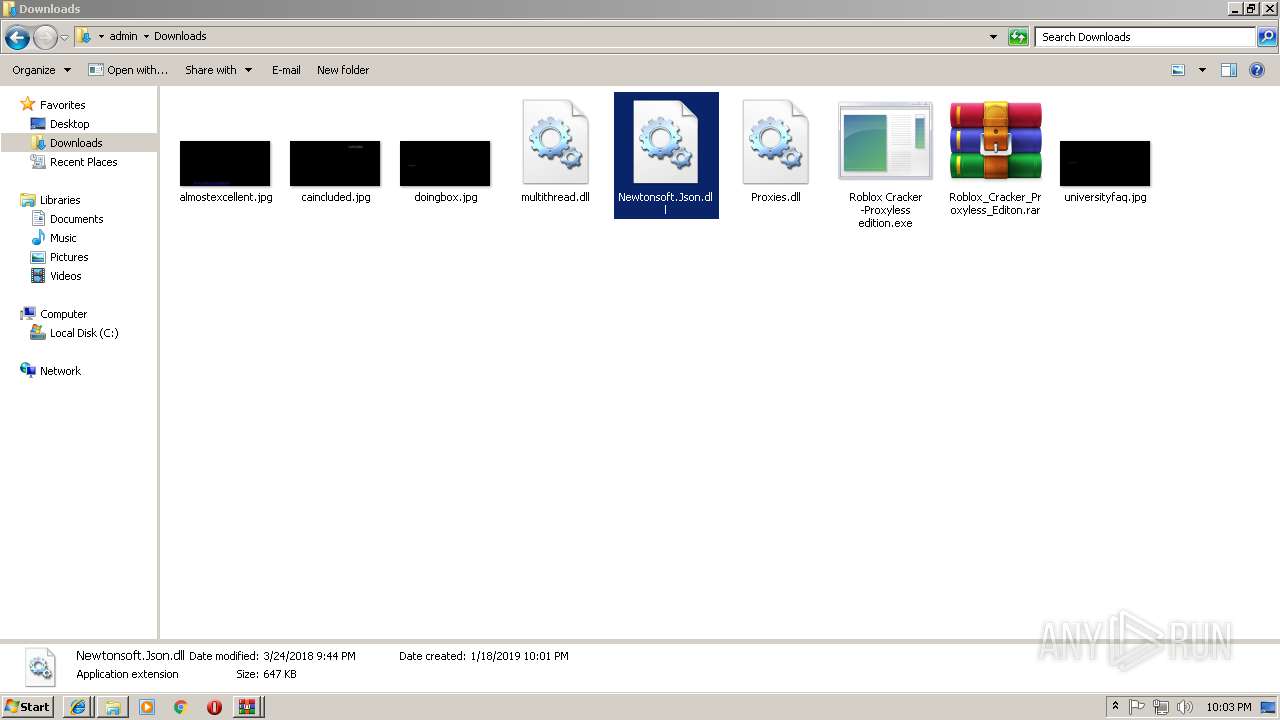
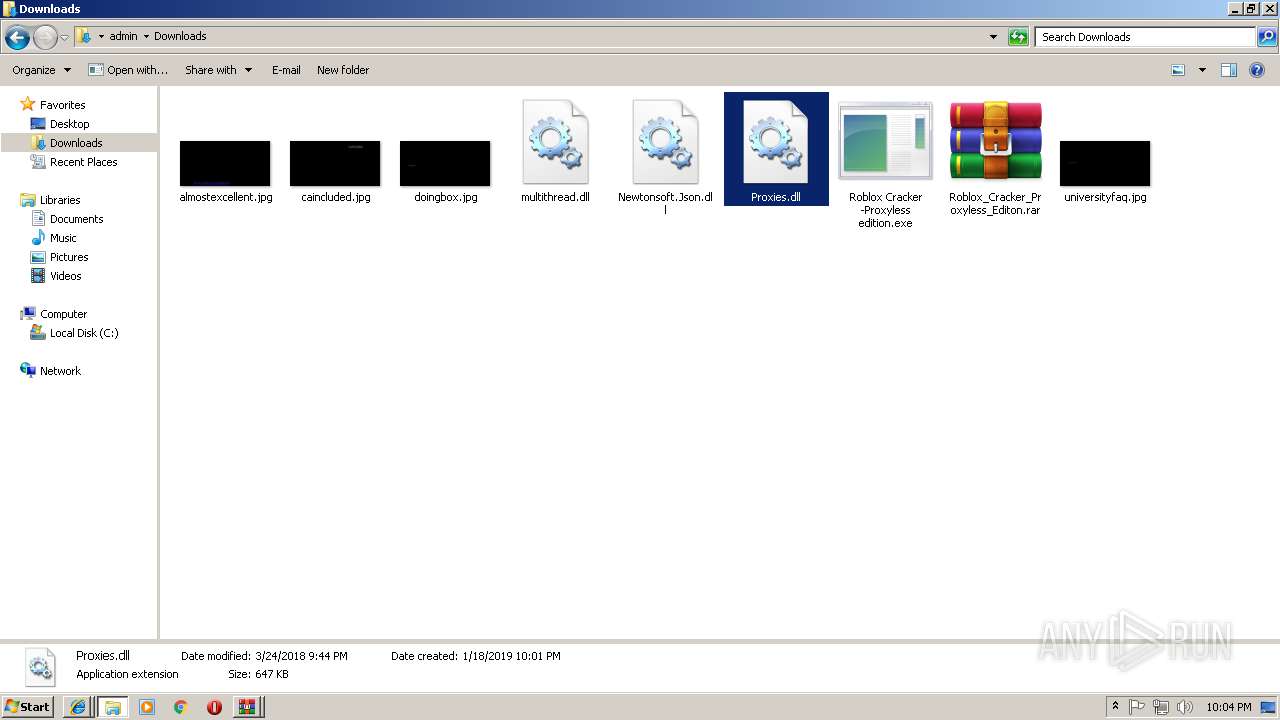
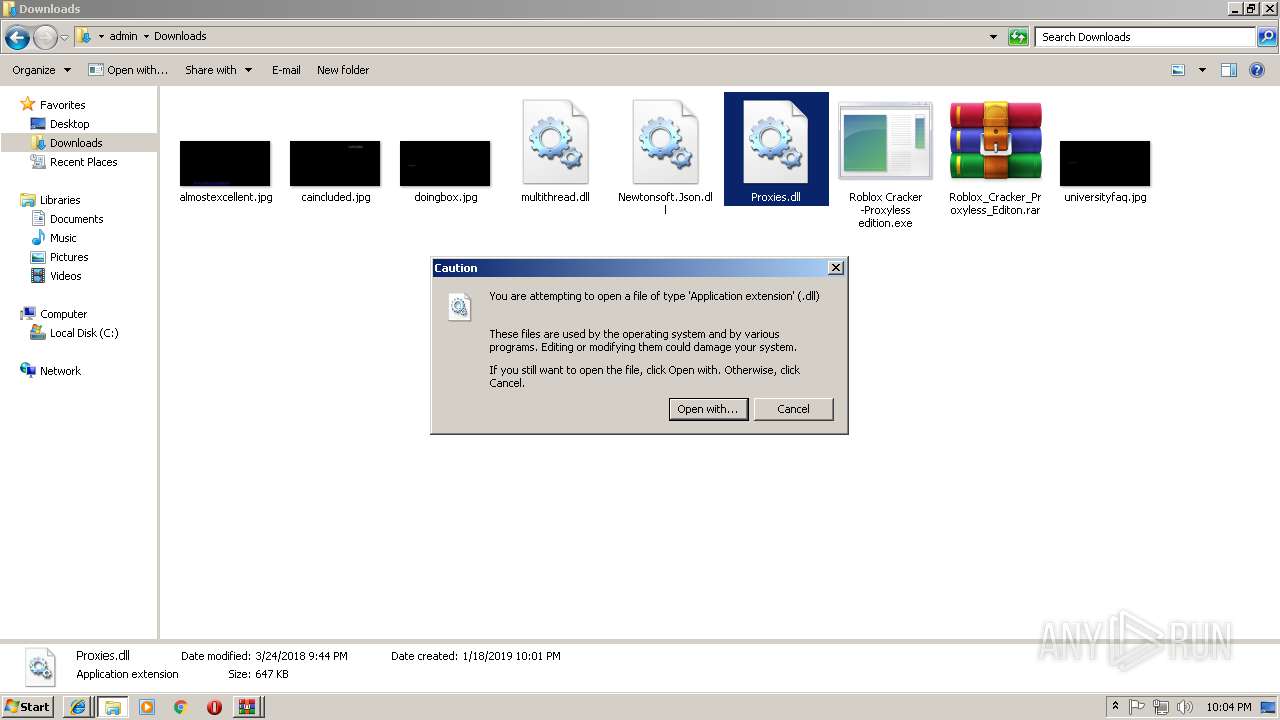
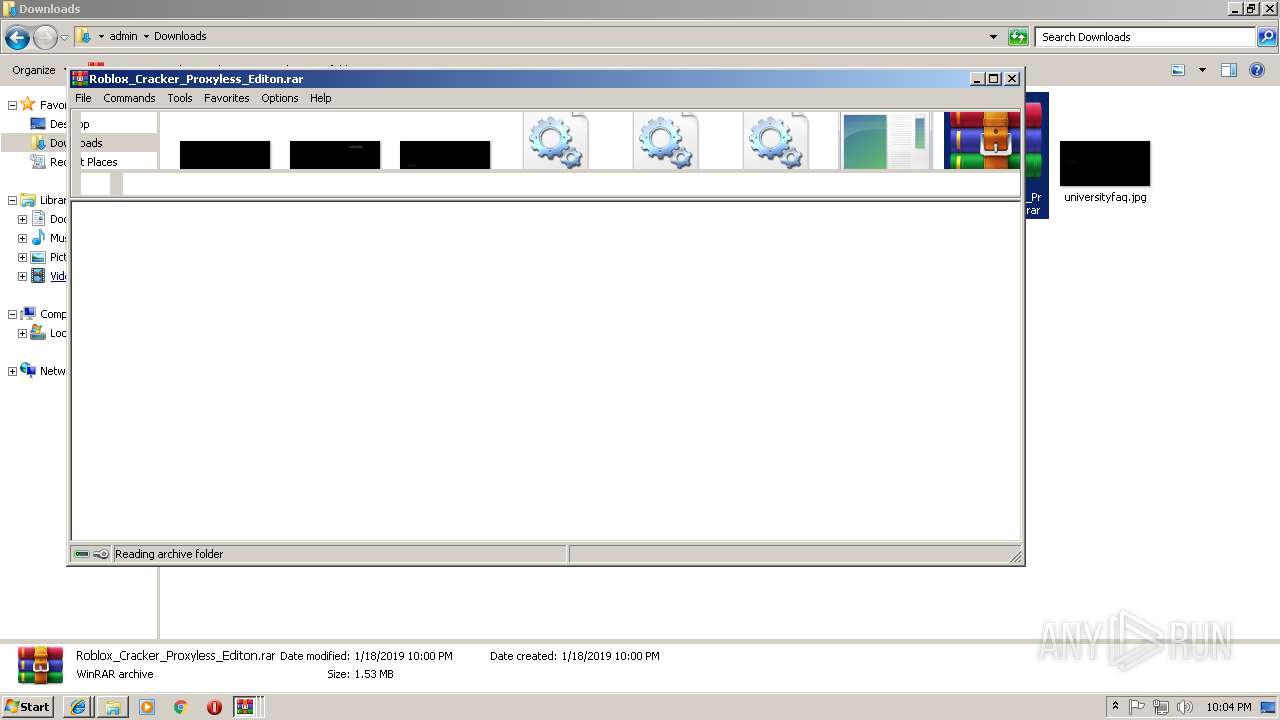
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2396)
- explorer.exe (PID: 2028)
- Roblox Cracker -Proxyless edition.exe (PID: 2684)
- Regasm.exe (PID: 2856)
- Roblox Cracker -Proxyless edition.exe (PID: 3056)
Creates files in the user directory
- explorer.exe (PID: 2028)
- Roblox Cracker -Proxyless edition.exe (PID: 2684)
- Regasm.exe (PID: 2856)
Starts itself from another location
- Roblox Cracker -Proxyless edition.exe (PID: 2684)
- Roblox Cracker -Proxyless edition.exe (PID: 3056)
Connects to unusual port
- Regasm.exe (PID: 2856)
Application launched itself
- MemeReview.exe (PID: 2344)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 2028)
INFO
Application launched itself
- iexplore.exe (PID: 2944)
- chrome.exe (PID: 3108)
Changes internet zones settings
- iexplore.exe (PID: 2944)
Reads internet explorer settings
- iexplore.exe (PID: 3068)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3520)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2944)
Reads settings of System Certificates
- iexplore.exe (PID: 2944)
- chrome.exe (PID: 3108)
Reads Internet Cache Settings
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 2944)
Changes settings of System certificates
- iexplore.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
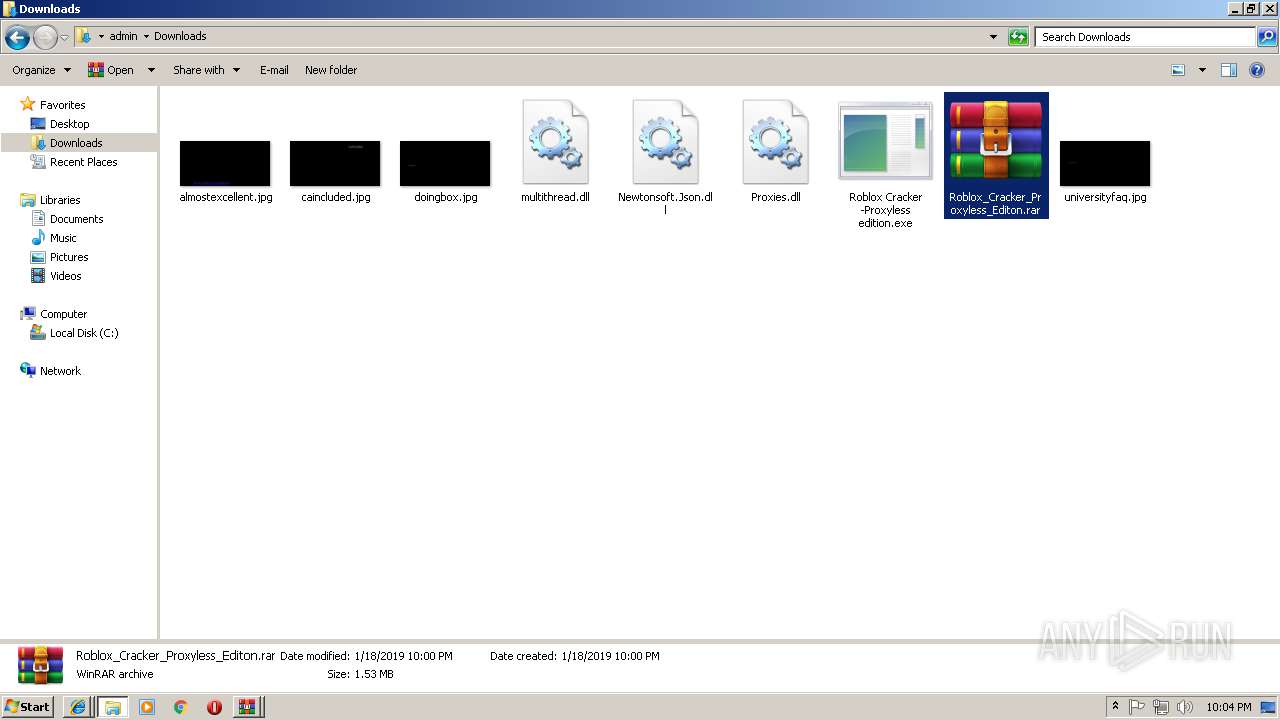
Total processes
69
Monitored processes
36
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,1325135931140595638,10464655703559107986,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=65A051FB499FB47B3D4E26A69A2E6781 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=65A051FB499FB47B3D4E26A69A2E6781 --renderer-client-id=8 --mojo-platform-channel-handle=3928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 612 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | — | ुग्पち.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1840 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | ुग्पち.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2028 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=888,1325135931140595638,10464655703559107986,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=D85C4108C247A45D8D21F128F09C3877 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,1325135931140595638,10464655703559107986,131072 --enable-features=PasswordImport --service-pipe-token=291FB9F4207AE3CA879EEBE19535273B --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=291FB9F4207AE3CA879EEBE19535273B --renderer-client-id=5 --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Roaming\MemeReview.exe" /launchSelfAndExit "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" 2856 /protectFile | C:\Users\admin\AppData\Roaming\MemeReview.exe | Regasm.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2888 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,1325135931140595638,10464655703559107986,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A78A5FB1F8E33C78753425E8A57443A0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A78A5FB1F8E33C78753425E8A57443A0 --renderer-client-id=10 --mojo-platform-channel-handle=3776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,1325135931140595638,10464655703559107986,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=662F515E761D940ACAC696C4A5C52DEF --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=662F515E761D940ACAC696C4A5C52DEF --renderer-client-id=6 --mojo-platform-channel-handle=2996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
6 223
Read events
5 639
Write events
566
Delete events
18
Modification events
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {77FBF171-1B6C-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010005001200160000001E00F602 | |||
Executable files
11
Suspicious files
79
Text files
133
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\Roblox_Cracker_Proxyless_Editon_rar[1].txt | — | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\Roblox_Cracker_Proxyless_Editon_rar[1].htm | html | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\d3ud741uvs727m_cloudfront_net[1] | text | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\anonfile[1].css | text | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\js[1] | text | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\app[1].js | text | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\logo-anonfile[1].png | image | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[2].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
78
DNS requests
36
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3068 | iexplore.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3068 | iexplore.exe | GET | 200 | 143.204.208.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3068 | iexplore.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3068 | iexplore.exe | 52.71.170.180:443 | expectorslapsino.info | Amazon.com, Inc. | US | unknown |
3068 | iexplore.exe | 143.204.208.222:80 | x.ss2.us | — | US | suspicious |
3068 | iexplore.exe | 143.204.214.30:443 | boudja.com | — | US | unknown |
3068 | iexplore.exe | 143.204.208.204:443 | drda5yf9kgz5p.cloudfront.net | — | US | unknown |
3068 | iexplore.exe | 185.147.237.250:443 | cdn-10.anonfile.com | Obenetwork AB | SE | unknown |
2944 | iexplore.exe | 46.227.68.134:443 | anonfile.com | Obenetwork AB | SE | unknown |
2856 | Regasm.exe | 152.44.44.237:9171 | — | Gardner-Webb University | US | malicious |
2856 | Regasm.exe | 104.128.234.104:9171 | notbloxy.duckdns.org | VooServers Ltd | US | malicious |
3108 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
anonfile.com |
| whitelisted |
vjs.zencdn.net |
| whitelisted |
oss.maxcdn.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
shermore.info |
| whitelisted |
d3ud741uvs727m.cloudfront.net |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
boudja.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |