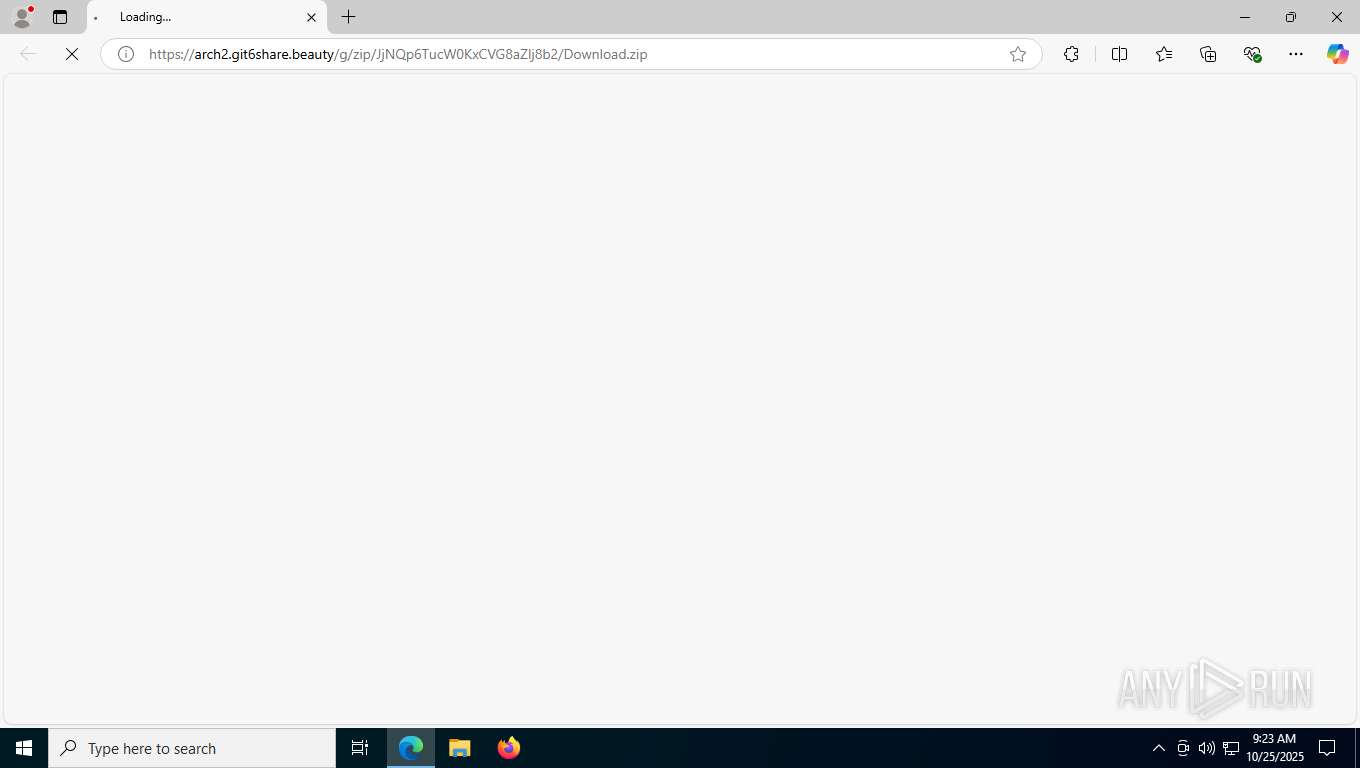
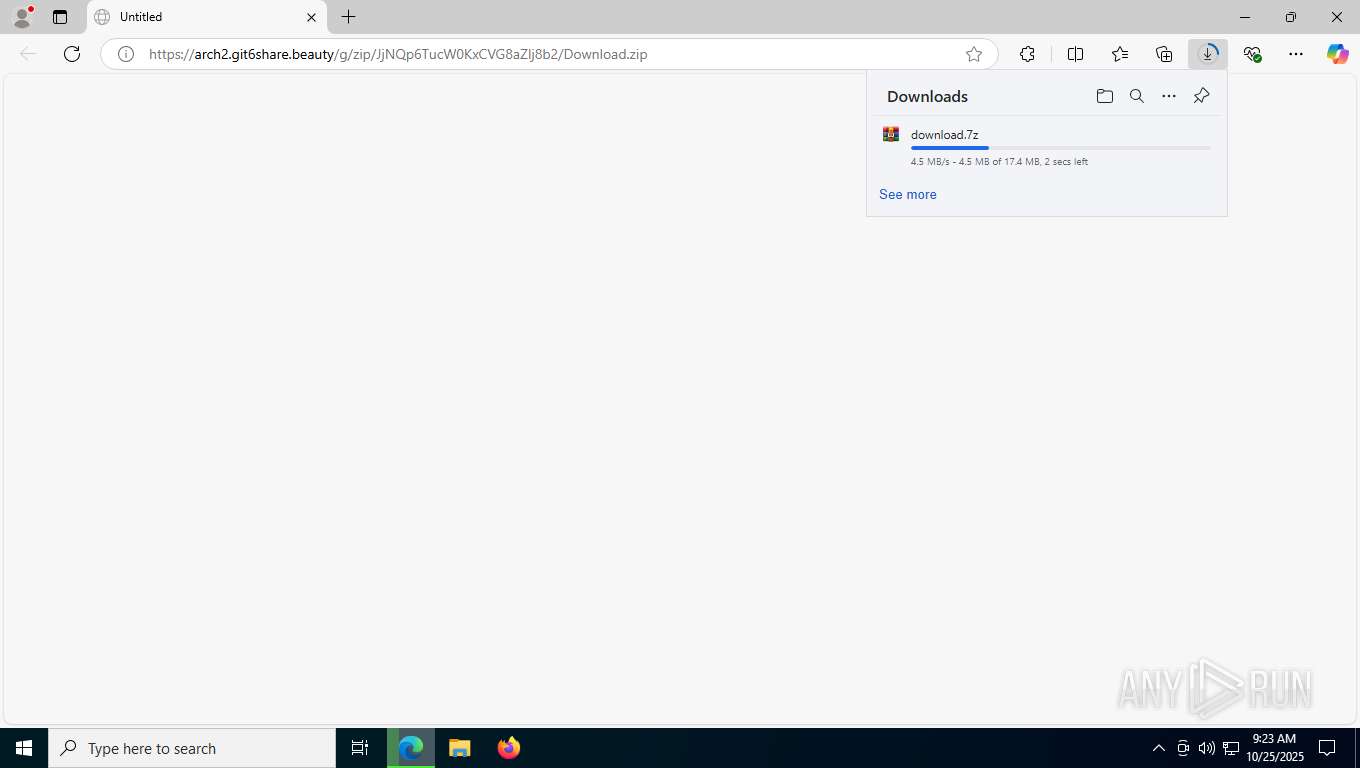
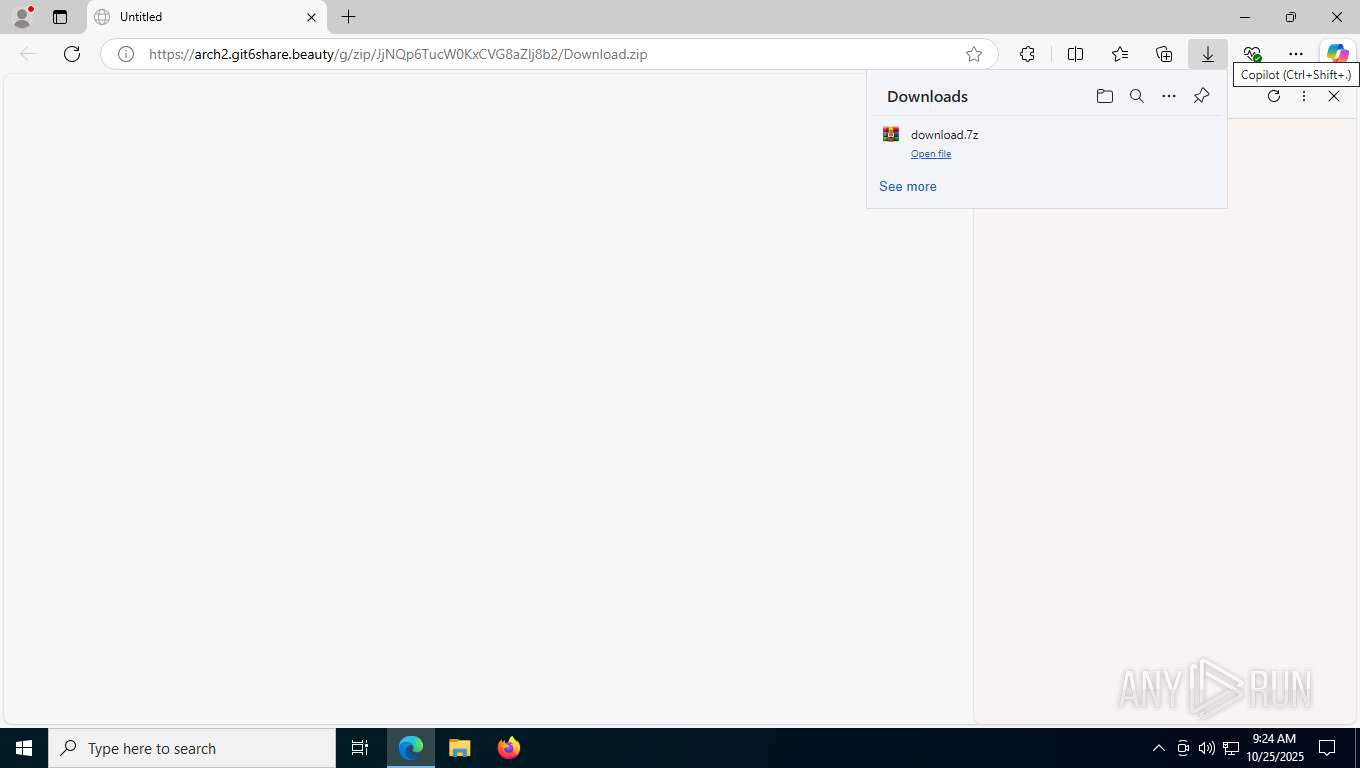
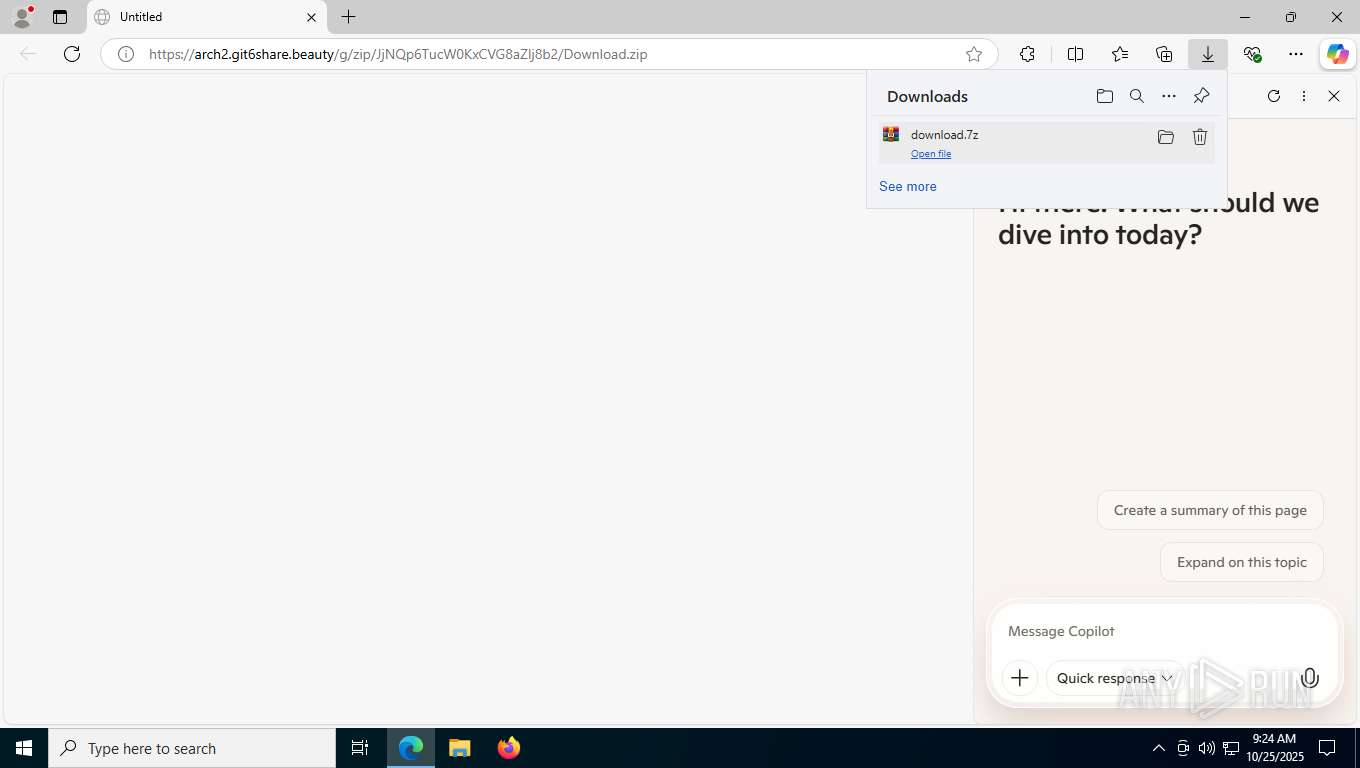
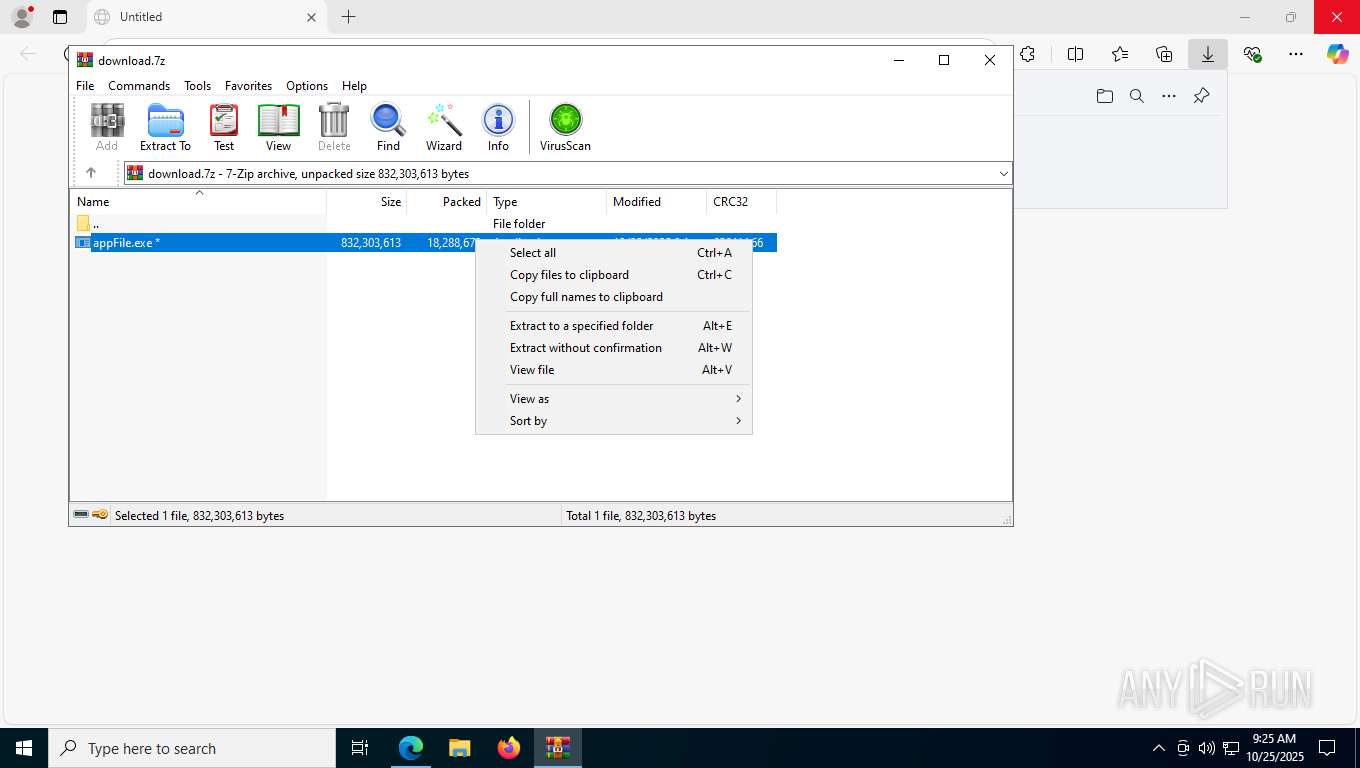
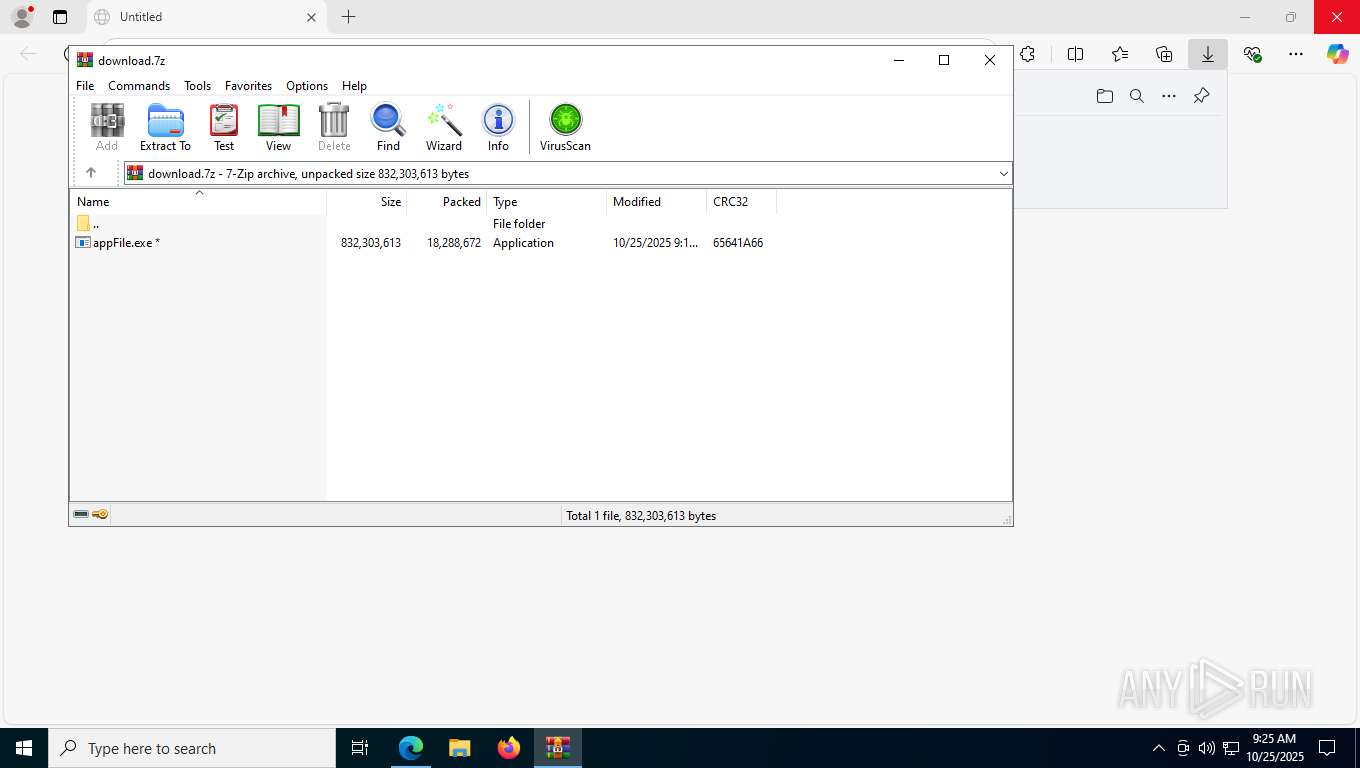
| URL: | https://arch2.git6share.beauty/g/zip/JjNQp6TucW0KxCVG8aZlj8b2/Download.zip |
| Full analysis: | https://app.any.run/tasks/77268ccb-2c55-4ff6-bb7e-23c86c2e1470 |
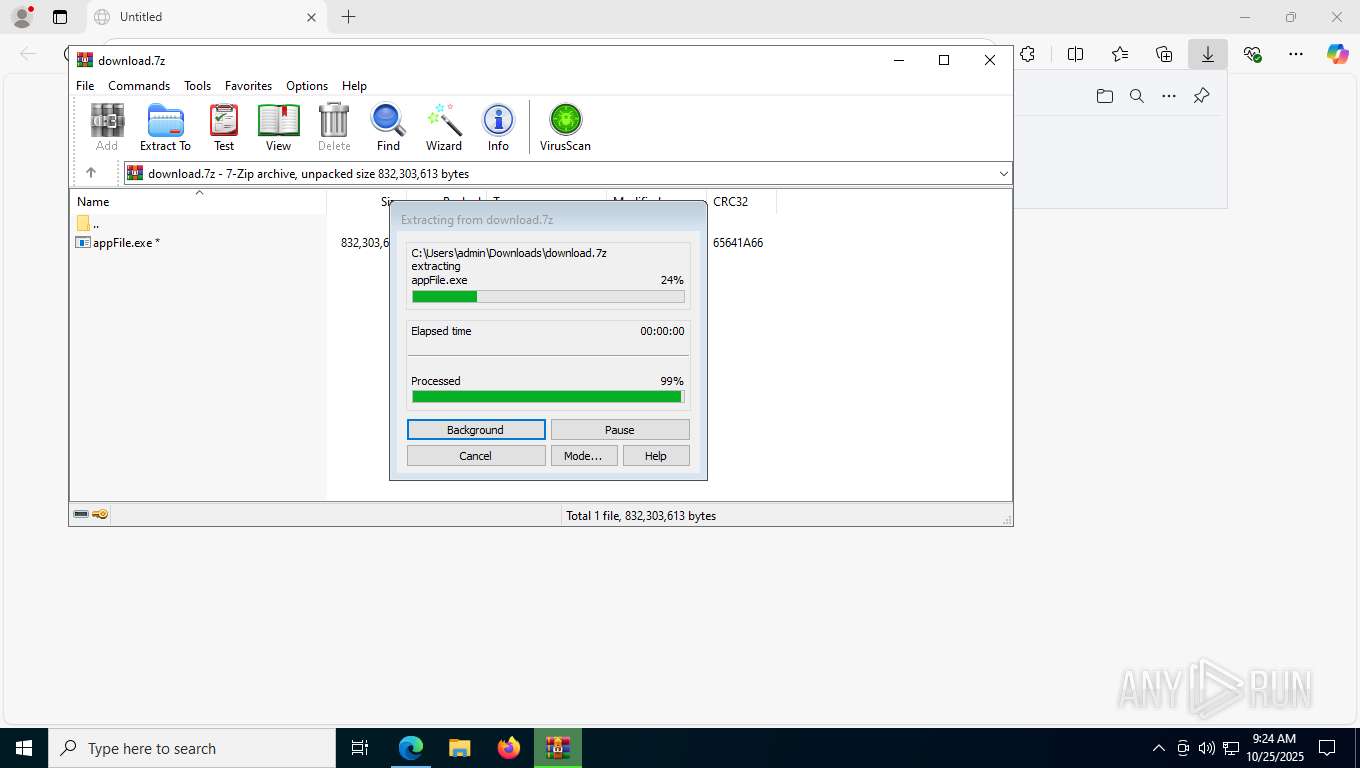
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 25, 2025, 09:23:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 359A1D00851FEF4405C700BDEA3A7C8C |
| SHA1: | 4668109A6BF59D93FFB2AFBEA02CC036614287C9 |
| SHA256: | EC52FAD943D20A4AB9321F821352AE2B347B09B1E172A119FB2B08DC58017A08 |
| SSDEEP: | 3:N8n2HGcKJrT05xQGybid1JZ9kVn:2n2C4vQGYid1JZ9c |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2276)
Changes the autorun value in the registry
- appFile.exe (PID: 7336)
Actions looks like stealing of personal data
- OpenWith.exe (PID: 2324)
- OpenWith.exe (PID: 2588)
- OpenWith.exe (PID: 7548)
- OpenWith.exe (PID: 6256)
- OpenWith.exe (PID: 1508)
SUSPICIOUS
Executing commands from a ".bat" file
- appFile.exe (PID: 1092)
- WinRAR.exe (PID: 4384)
- appFile.exe (PID: 6412)
- appFile.exe (PID: 4220)
- appFile.exe (PID: 1584)
- appFile.exe (PID: 7336)
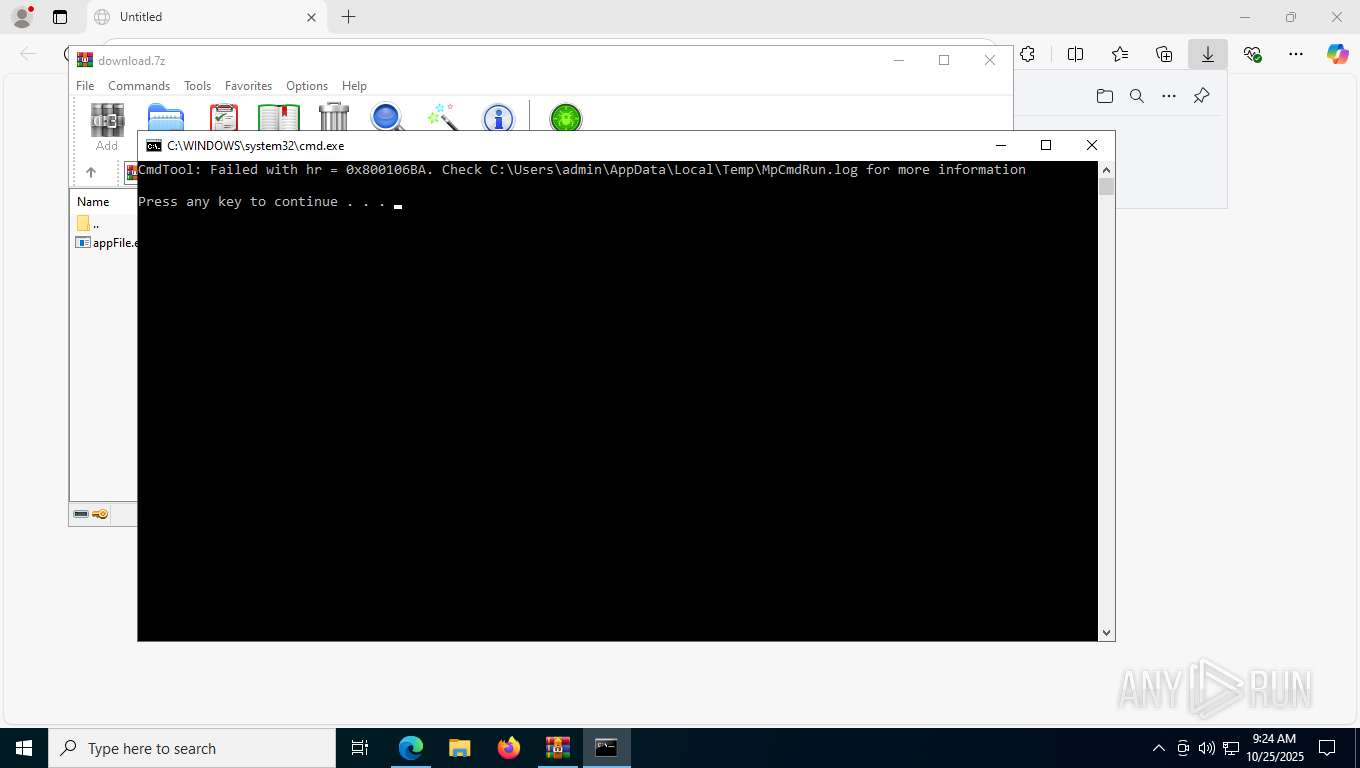
Starts CMD.EXE for commands execution
- appFile.exe (PID: 1092)
- WinRAR.exe (PID: 4384)
- appFile.exe (PID: 6412)
- appFile.exe (PID: 4220)
- appFile.exe (PID: 1584)
- appFile.exe (PID: 7336)
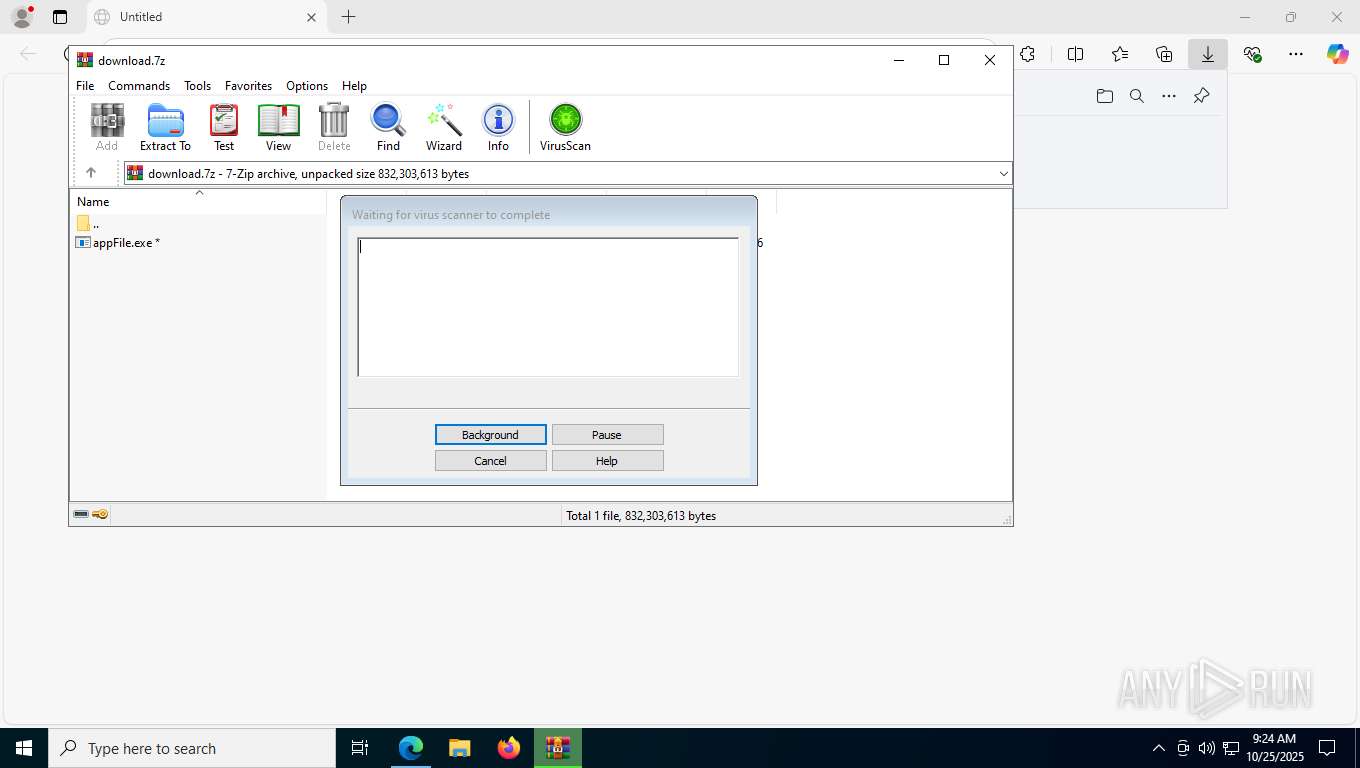
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4384)
Get information on the list of running processes
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 876)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7520)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 876)
The executable file from the user directory is run by the CMD process
- Leone.scr (PID: 2376)
- Leone.scr (PID: 7376)
- Leone.scr (PID: 6128)
- Leone.scr (PID: 8488)
- Leone.scr (PID: 1236)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7520)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 876)
- Leone.scr (PID: 1236)
Starts application with an unusual extension
- cmd.exe (PID: 7520)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 876)
- Leone.scr (PID: 1236)
Executes application which crashes
- Leone.scr (PID: 8848)
- Leone.scr (PID: 7496)
- Leone.scr (PID: 9212)
- Leone.scr (PID: 8672)
- Leone.scr (PID: 8448)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 2324)
- OpenWith.exe (PID: 2588)
- OpenWith.exe (PID: 6256)
- OpenWith.exe (PID: 7548)
- OpenWith.exe (PID: 1508)
Searches for installed software
- OpenWith.exe (PID: 2324)
- OpenWith.exe (PID: 7548)
- OpenWith.exe (PID: 2588)
Loads DLL from Mozilla Firefox
- OpenWith.exe (PID: 2324)
- OpenWith.exe (PID: 7548)
- OpenWith.exe (PID: 2588)
Application launched itself
- Leone.scr (PID: 1236)
INFO
Application launched itself
- msedge.exe (PID: 7832)
- chrome.exe (PID: 8740)
- msedge.exe (PID: 3300)
- chrome.exe (PID: 4168)
- chrome.exe (PID: 10008)
- chrome.exe (PID: 9712)
- msedge.exe (PID: 5576)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 7660)
- msedge.exe (PID: 10404)
- msedge.exe (PID: 7536)
- msedge.exe (PID: 4772)
- chrome.exe (PID: 8948)
Checks supported languages
- identity_helper.exe (PID: 8836)
- extrac32.exe (PID: 6676)
- appFile.exe (PID: 1092)
- Leone.scr (PID: 2376)
- MpCmdRun.exe (PID: 8368)
- appFile.exe (PID: 6412)
- appFile.exe (PID: 4220)
- Leone.scr (PID: 8848)
- extrac32.exe (PID: 7580)
- appFile.exe (PID: 1584)
- Leone.scr (PID: 7376)
- Leone.scr (PID: 8488)
- extrac32.exe (PID: 6360)
- Leone.scr (PID: 6128)
- extrac32.exe (PID: 7176)
- appFile.exe (PID: 7336)
- extrac32.exe (PID: 9440)
- Leone.scr (PID: 1236)
- Leone.scr (PID: 7496)
- Leone.scr (PID: 9212)
- Leone.scr (PID: 8448)
- Leone.scr (PID: 8672)
- identity_helper.exe (PID: 1924)
- identity_helper.exe (PID: 9228)
Reads Environment values
- identity_helper.exe (PID: 8836)
- identity_helper.exe (PID: 1924)
- identity_helper.exe (PID: 9228)
Reads the computer name
- identity_helper.exe (PID: 8836)
- extrac32.exe (PID: 6676)
- Leone.scr (PID: 2376)
- MpCmdRun.exe (PID: 8368)
- extrac32.exe (PID: 7580)
- Leone.scr (PID: 7376)
- extrac32.exe (PID: 7176)
- extrac32.exe (PID: 6360)
- Leone.scr (PID: 8488)
- extrac32.exe (PID: 9440)
- Leone.scr (PID: 6128)
- Leone.scr (PID: 1236)
- identity_helper.exe (PID: 1924)
- identity_helper.exe (PID: 9228)
Create files in a temporary directory
- appFile.exe (PID: 1092)
- extrac32.exe (PID: 6676)
- MpCmdRun.exe (PID: 8368)
- appFile.exe (PID: 6412)
- appFile.exe (PID: 4220)
- extrac32.exe (PID: 7580)
- appFile.exe (PID: 1584)
- extrac32.exe (PID: 7176)
- extrac32.exe (PID: 6360)
- OpenWith.exe (PID: 2324)
- extrac32.exe (PID: 9440)
- appFile.exe (PID: 7336)
- OpenWith.exe (PID: 2588)
- OpenWith.exe (PID: 1508)
- OpenWith.exe (PID: 7548)
- OpenWith.exe (PID: 6256)
Reads mouse settings
- Leone.scr (PID: 2376)
- Leone.scr (PID: 7376)
- Leone.scr (PID: 8488)
- Leone.scr (PID: 6128)
- Leone.scr (PID: 1236)
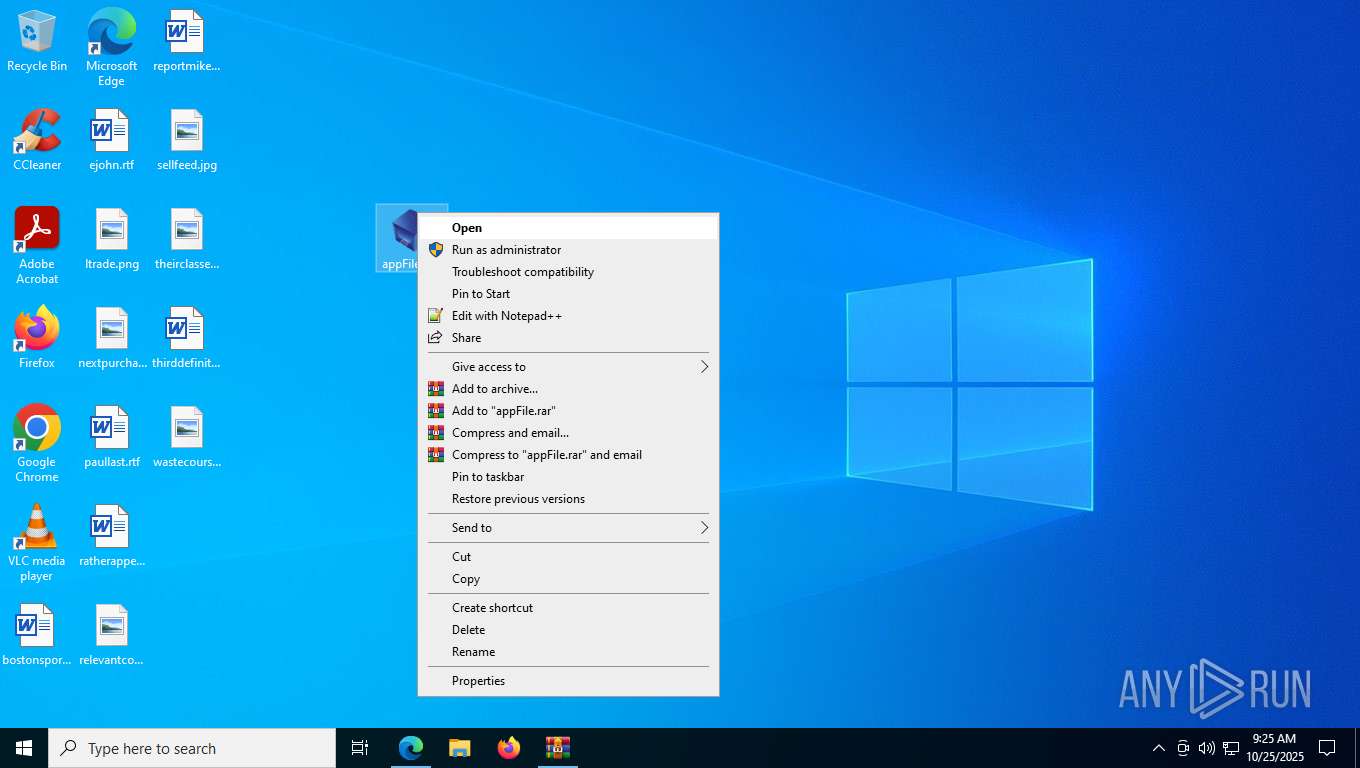
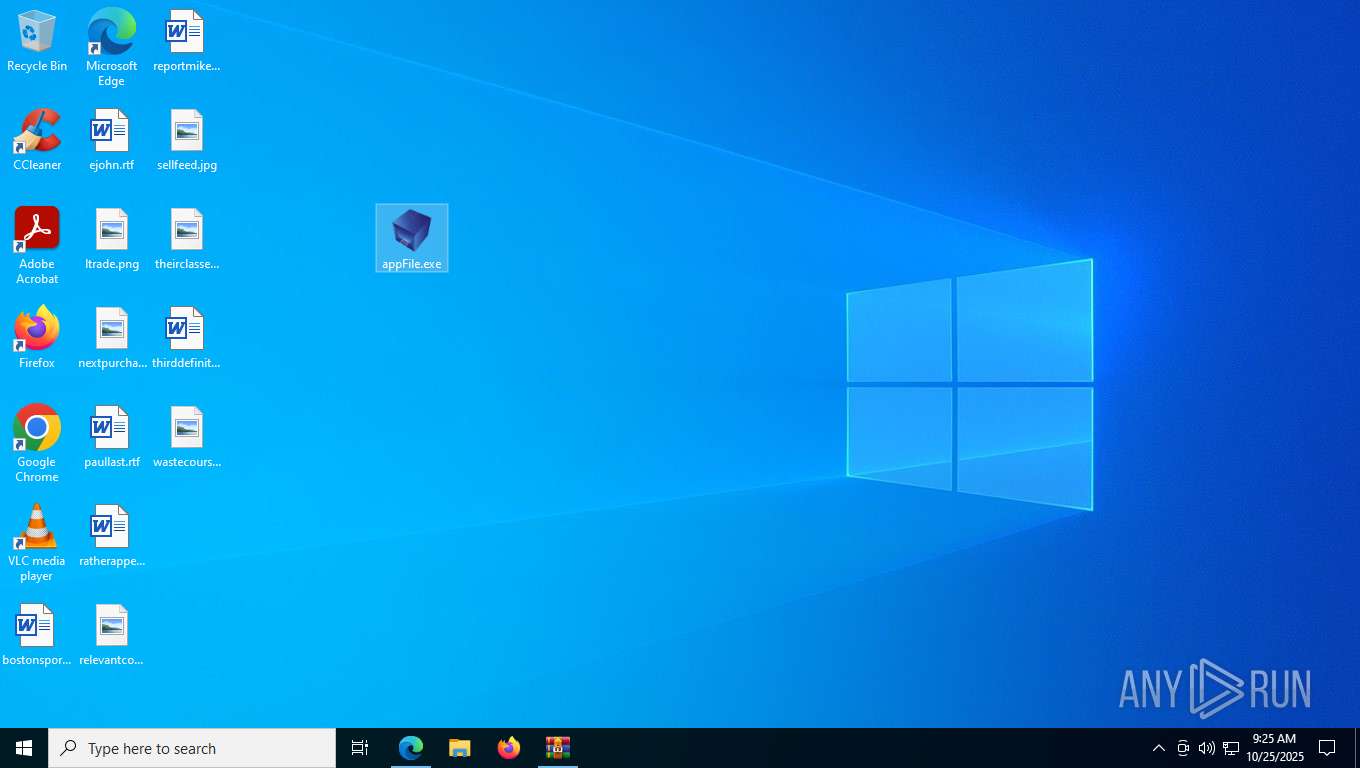
Manual execution by a user
- OpenWith.exe (PID: 2324)
- Leone.scr (PID: 8848)
- appFile.exe (PID: 6412)
- appFile.exe (PID: 4220)
- appFile.exe (PID: 1584)
- appFile.exe (PID: 7336)
- Leone.scr (PID: 7496)
- Leone.scr (PID: 9212)
- OpenWith.exe (PID: 2588)
- Leone.scr (PID: 8672)
- OpenWith.exe (PID: 1508)
- OpenWith.exe (PID: 6256)
- msedge.exe (PID: 9248)
Launching a file from a Registry key
- appFile.exe (PID: 7336)
Checks proxy server information
- slui.exe (PID: 2636)
Reads the software policy settings
- slui.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
567
Monitored processes
412
Malicious processes
5
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | waitfor /T 5 CZEfADeQPCSdaPNgpmXPEbtTbfSisFFKE | C:\Windows\System32\waitfor.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: waitfor - wait/send a signal over a network Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --string-annotations --field-trial-handle=6788,i,9893478403719920900,14728523185814054775,262144 --variations-seed-version --mojo-platform-channel-handle=7072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | at.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | cmd /c move Wales.aif Wales.aif.bat && Wales.aif.bat | C:\Windows\System32\cmd.exe | — | appFile.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --string-annotations --field-trial-handle=2144,i,11711239603865042696,17372562120271536349,262144 --variations-seed-version --mojo-platform-channel-handle=2160 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
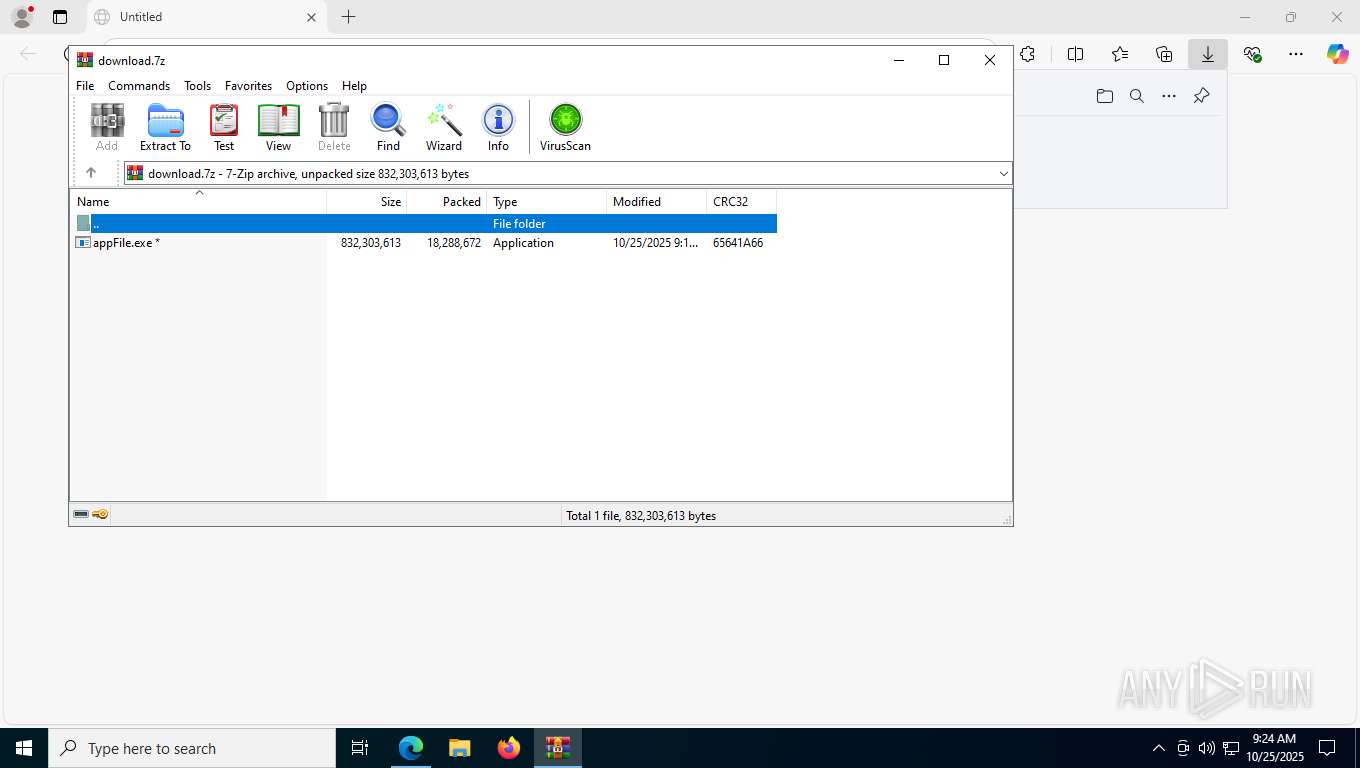
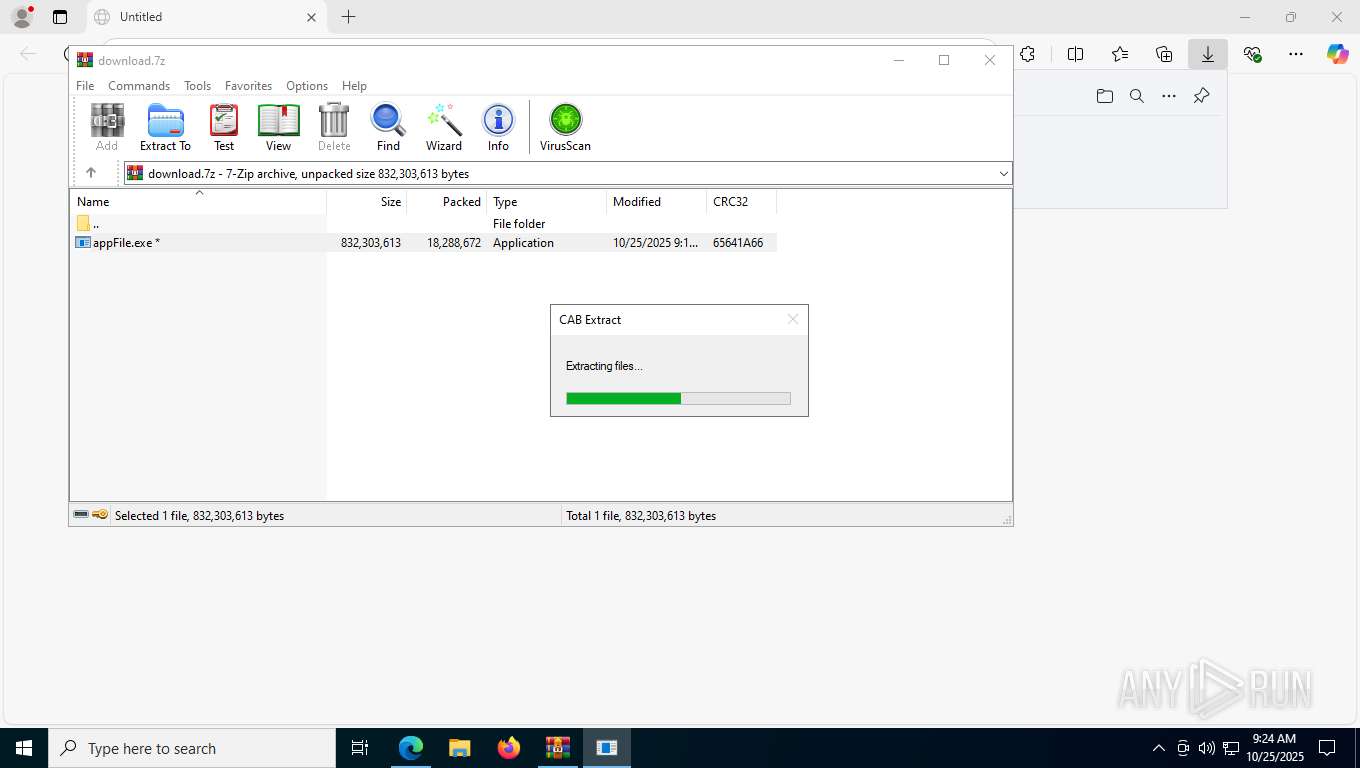
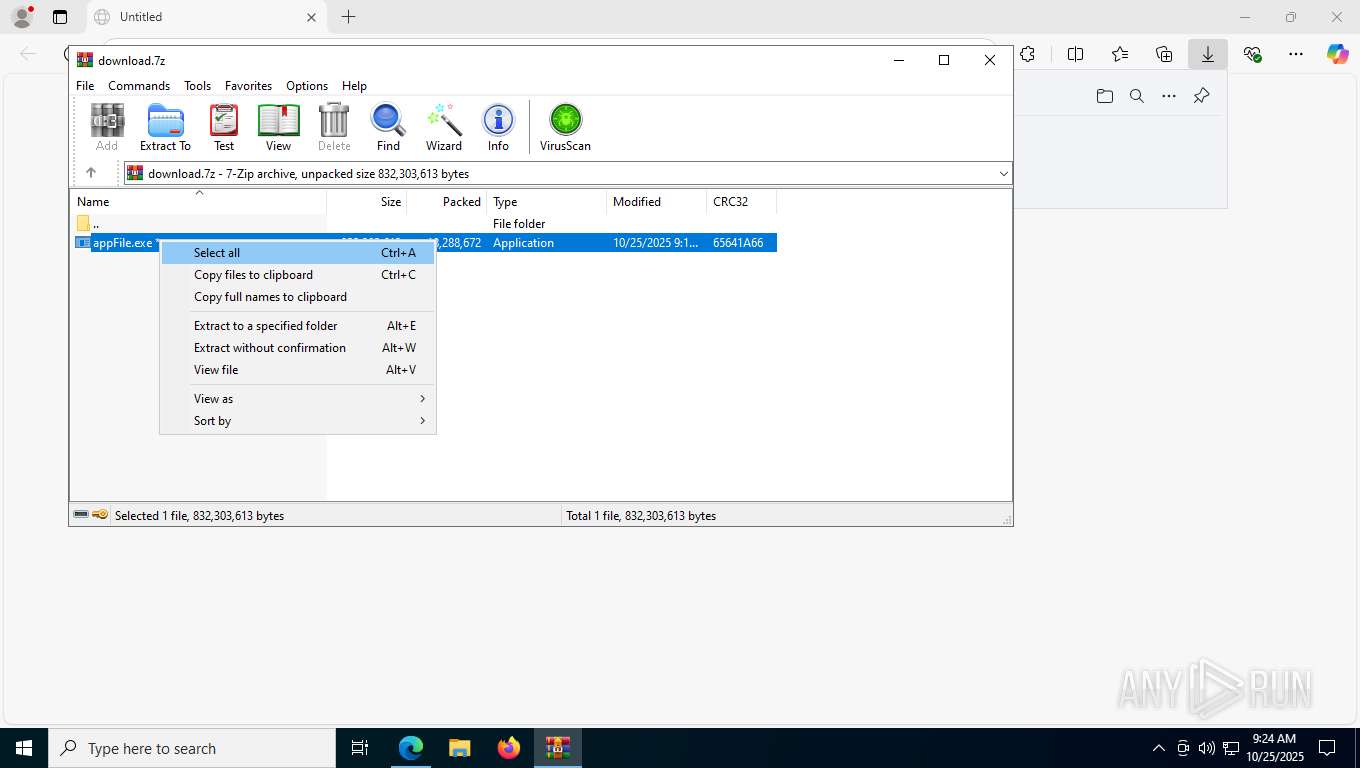
| 1092 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4384.41258\appFile.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4384.41258\appFile.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1092 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=14 --always-read-main-dll --field-trial-handle=4592,i,11188831304923022275,9867490289859686430,262144 --variations-seed-version --mojo-platform-channel-handle=4600 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=2936,i,16104267480827966053,2494599602665053771,262144 --variations-seed-version --mojo-platform-channel-handle=3856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --string-annotations --field-trial-handle=2176,i,17027119029749858623,7414508701810323984,262144 --variations-seed-version --mojo-platform-channel-handle=1956 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=3784,i,11711239603865042696,17372562120271536349,262144 --variations-seed-version --mojo-platform-channel-handle=3920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
17 282
Read events
17 270
Write events
11
Delete events
1
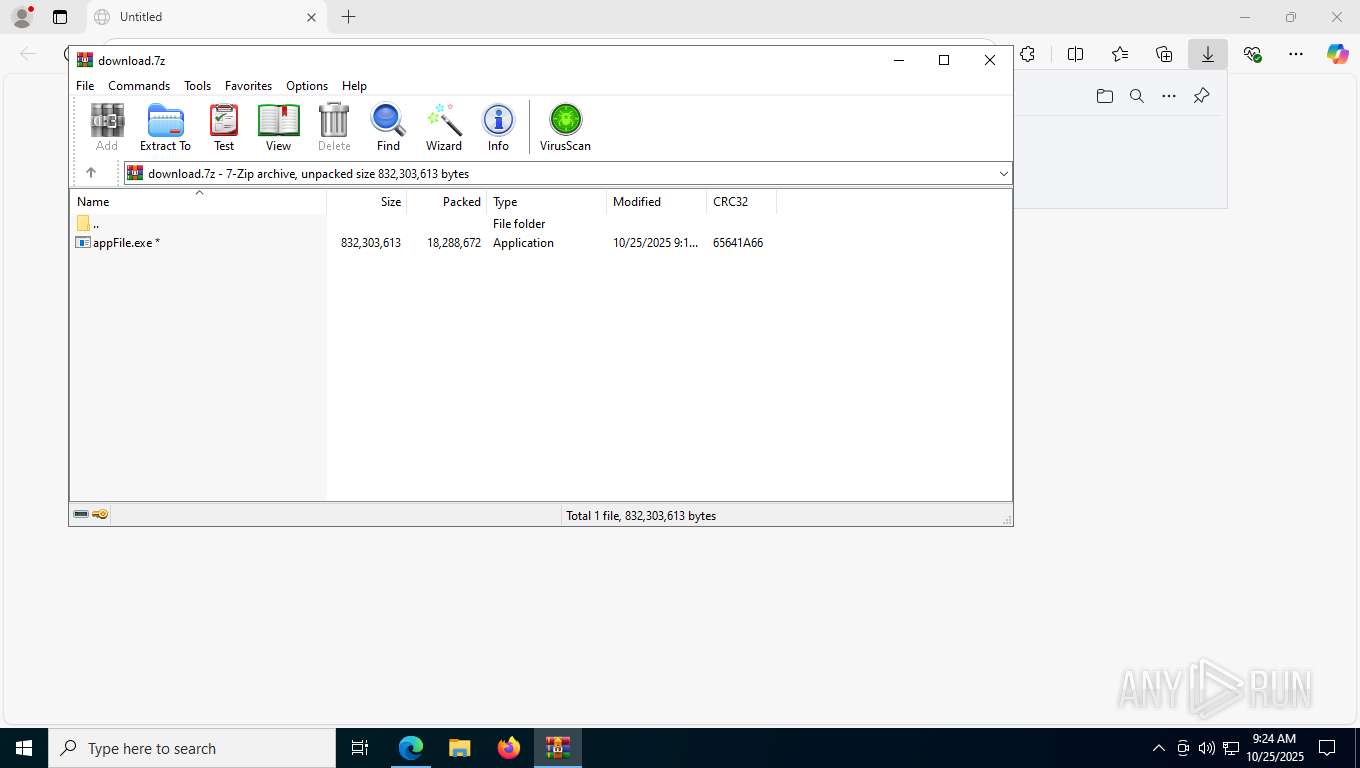
Modification events
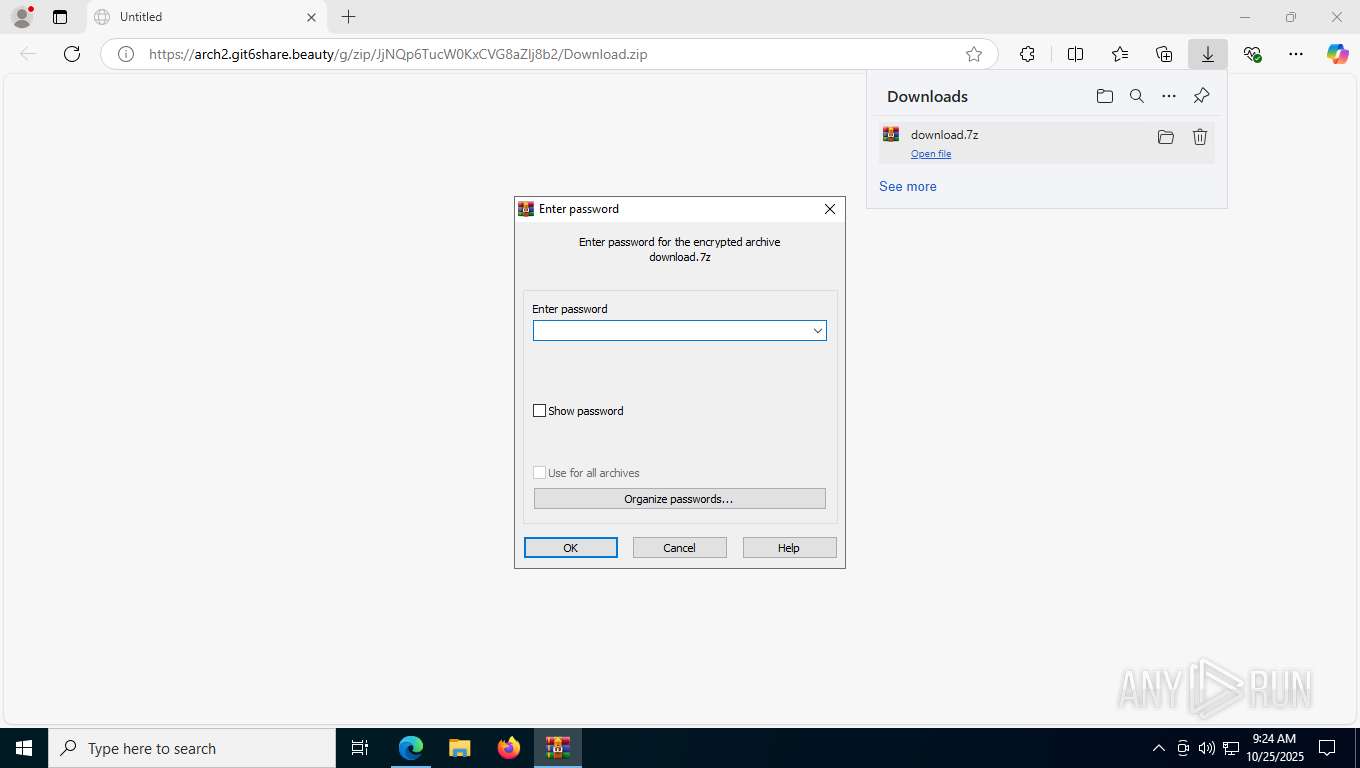
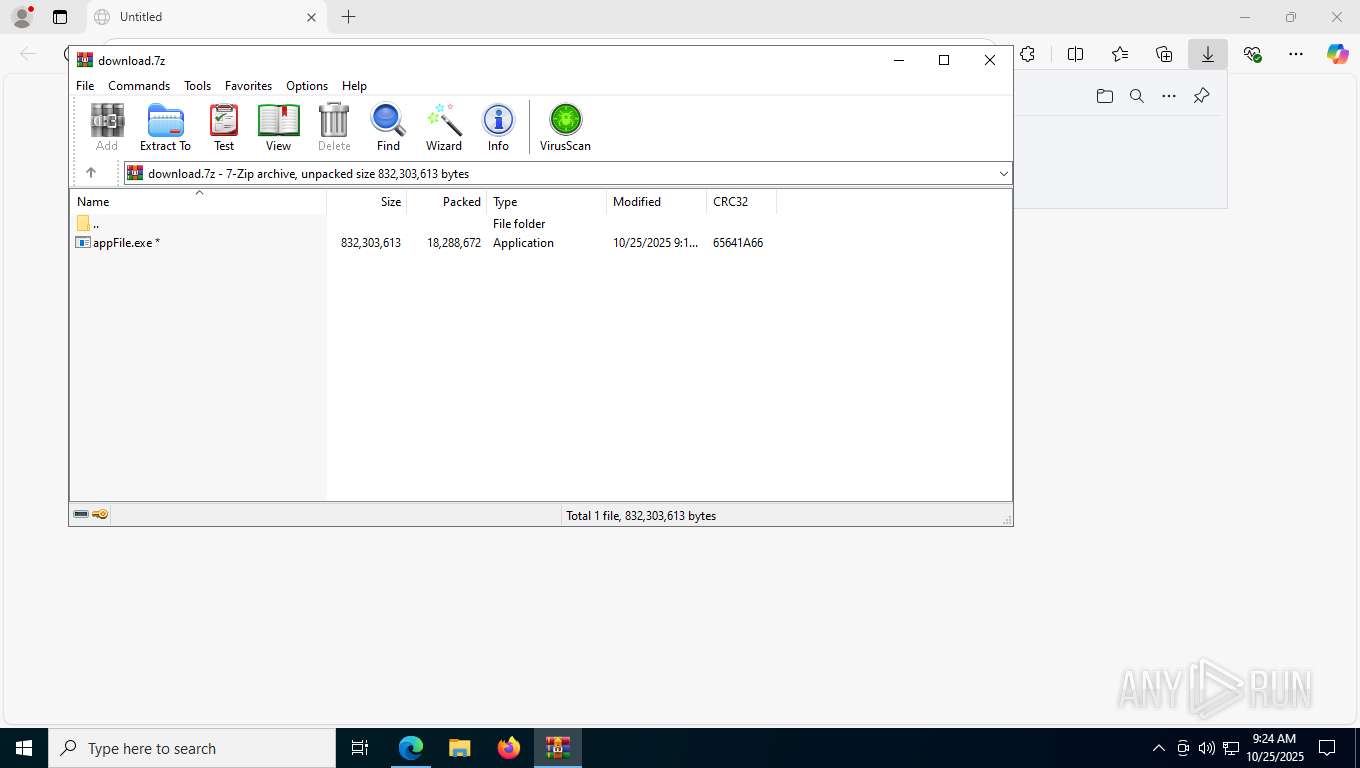
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
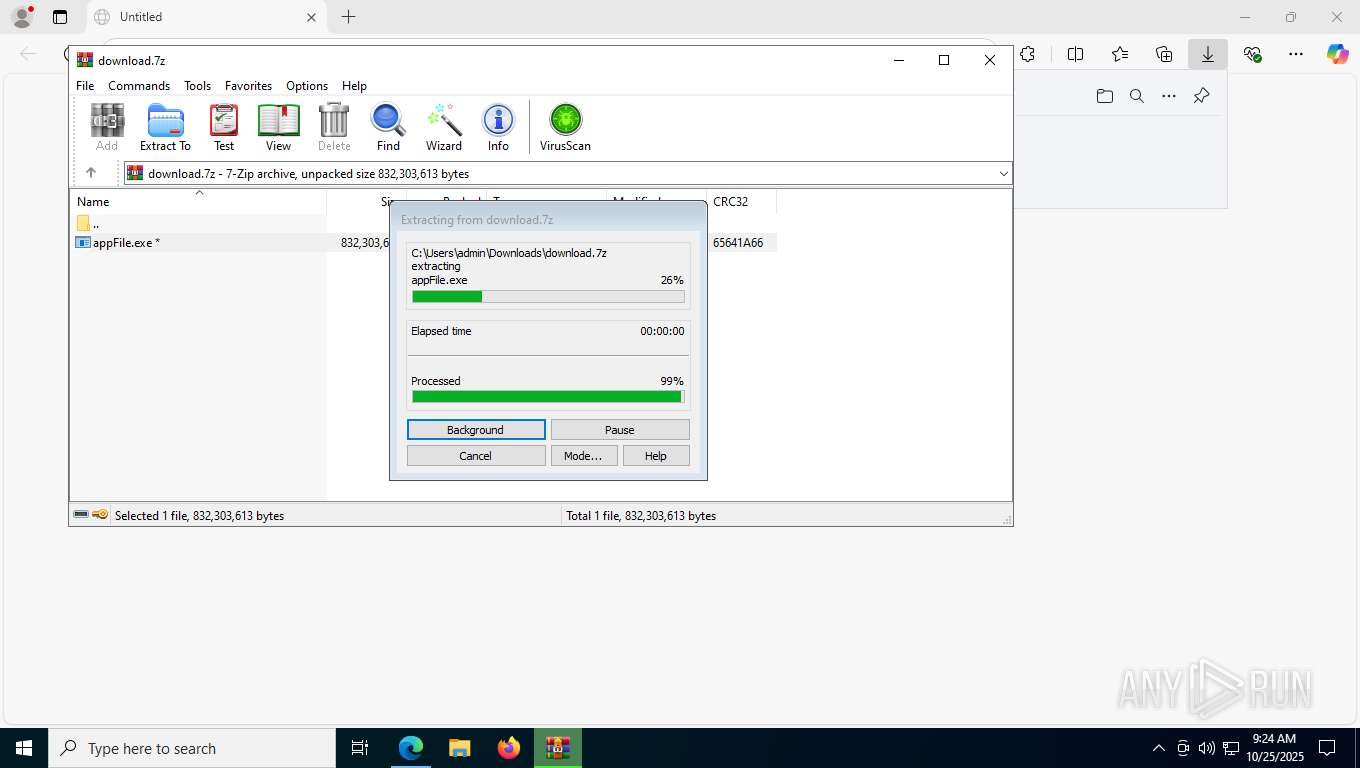
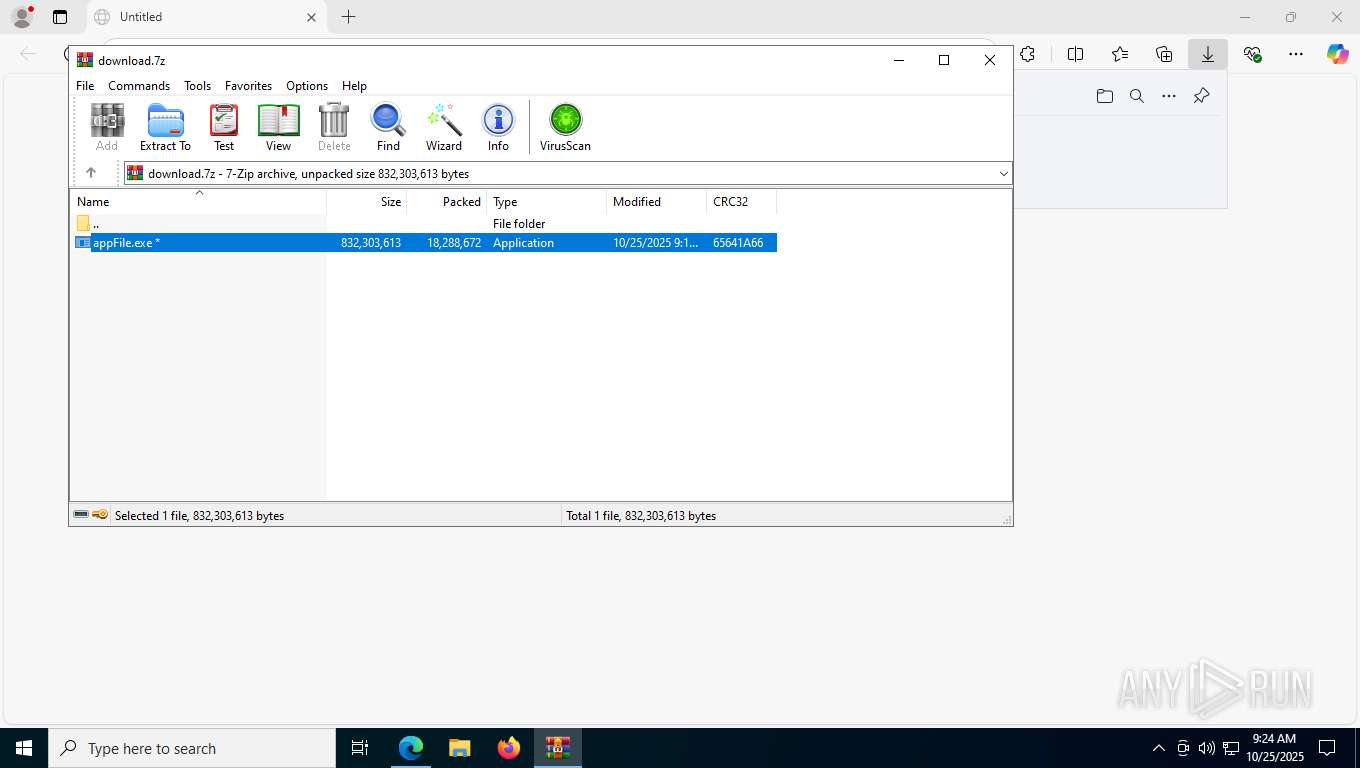
Value: C:\Users\admin\Downloads\download.7z | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
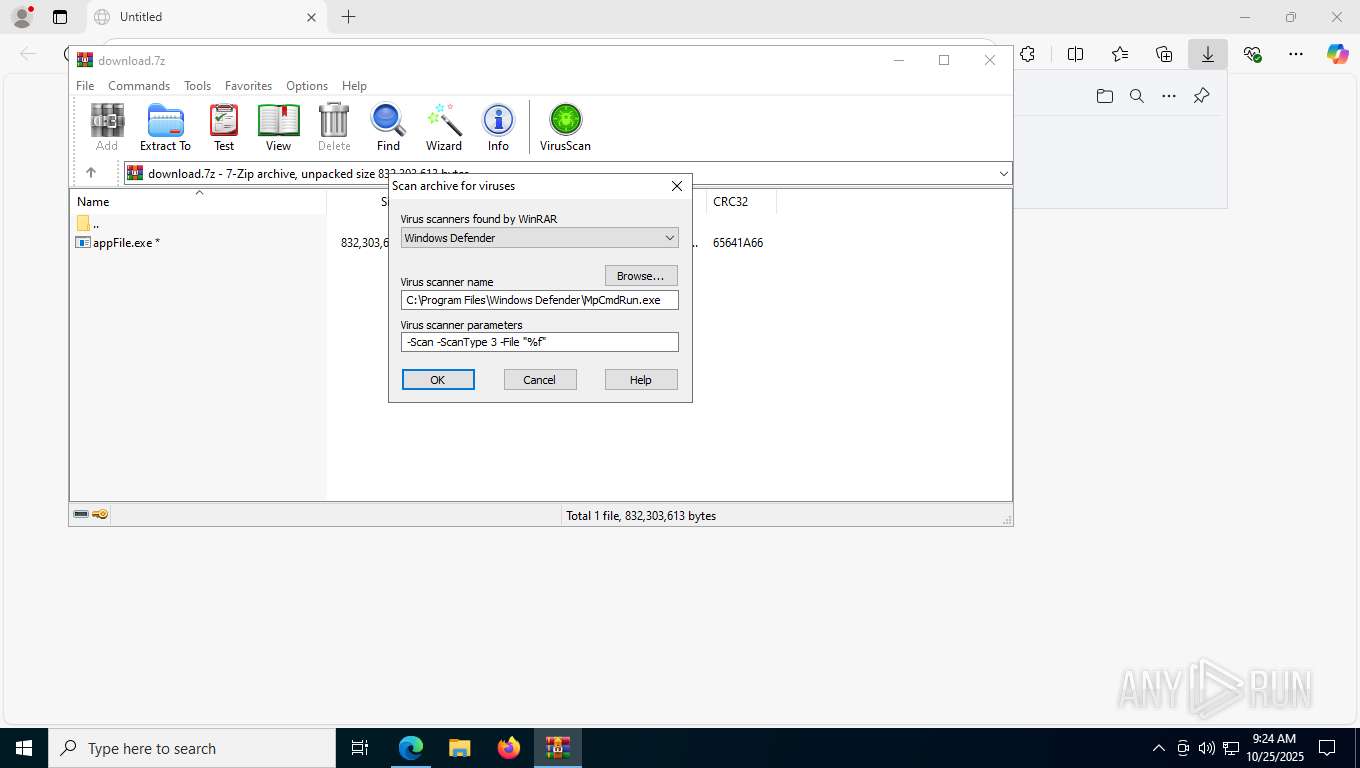
| (PID) Process: | (4384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
51
Suspicious files
2 496
Text files
610
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfb339.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfb368.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfb349.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfb397.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfb3a7.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
281
DNS requests
310
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5948 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7328 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5948 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7280 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8168 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:j2V7XTslcrBoEIQKjyQvPjcRUAqKouMSZKPOiDixiQA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1676 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
4164 | backgroundTaskHost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7300 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1761932931&P2=404&P3=2&P4=h2z9J7OXjOLfrWPtQpgxycxyWSxaDsIRBAVA%2bA57jnz1k7BccdfKPpBnAPVQtAbJoxKReajQK7sWUna%2fqTAs%2fw%3d%3d | unknown | — | — | whitelisted |
7300 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1761932931&P2=404&P3=2&P4=h2z9J7OXjOLfrWPtQpgxycxyWSxaDsIRBAVA%2bA57jnz1k7BccdfKPpBnAPVQtAbJoxKReajQK7sWUna%2fqTAs%2fw%3d%3d | unknown | — | — | whitelisted |
7300 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1761932931&P2=404&P3=2&P4=h2z9J7OXjOLfrWPtQpgxycxyWSxaDsIRBAVA%2bA57jnz1k7BccdfKPpBnAPVQtAbJoxKReajQK7sWUna%2fqTAs%2fw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2784 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5948 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5948 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3440 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7280 | backgroundTaskHost.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7280 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2276 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Lumma DNS Activity observed |
2276 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Lumma DNS Activity observed |
2276 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Lumma DNS Activity observed |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr5919.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr638A.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrDA6F.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrE0C8.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrE3A7.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrE750.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr75.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr808.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr11FC.tmp directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr1E41.tmp directory exists )
|