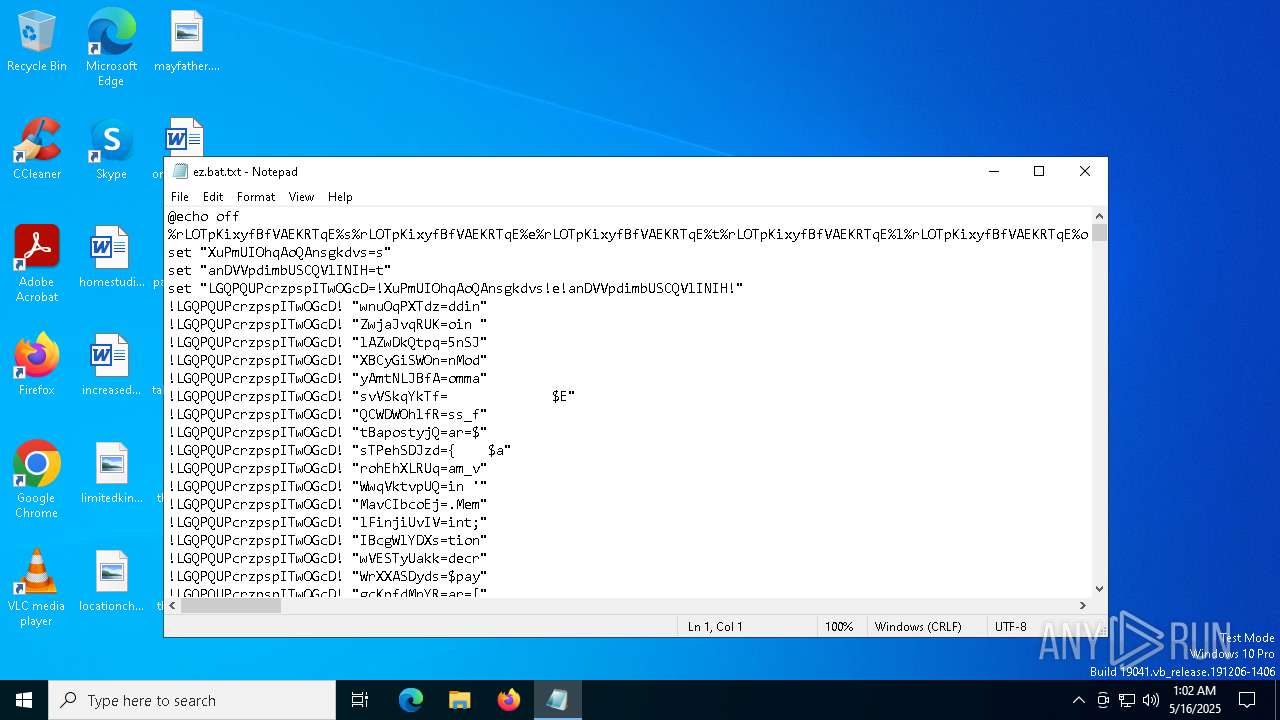
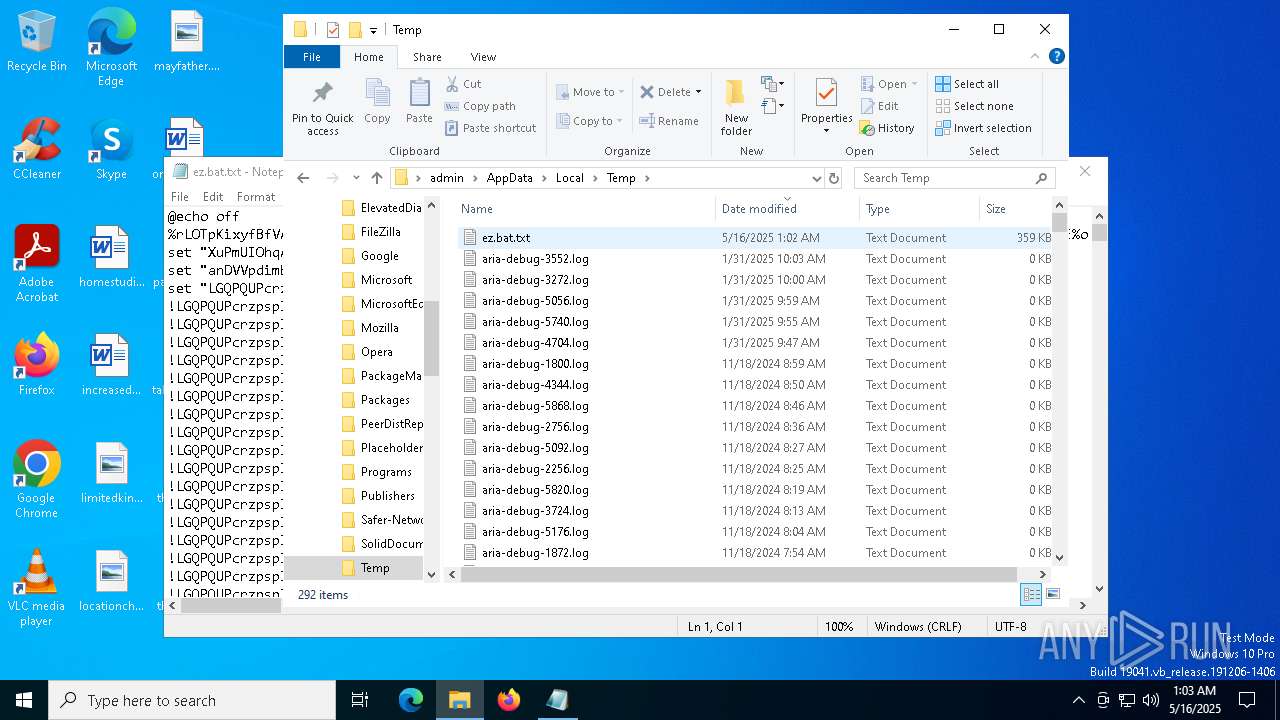
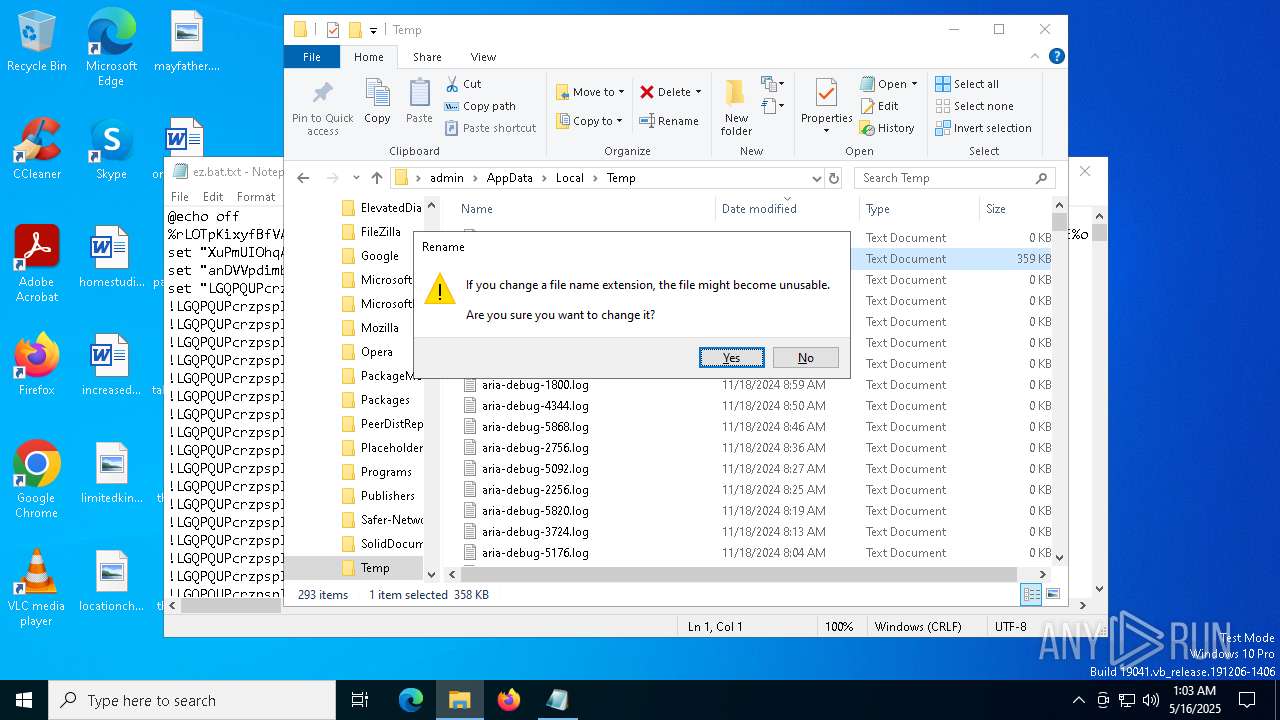
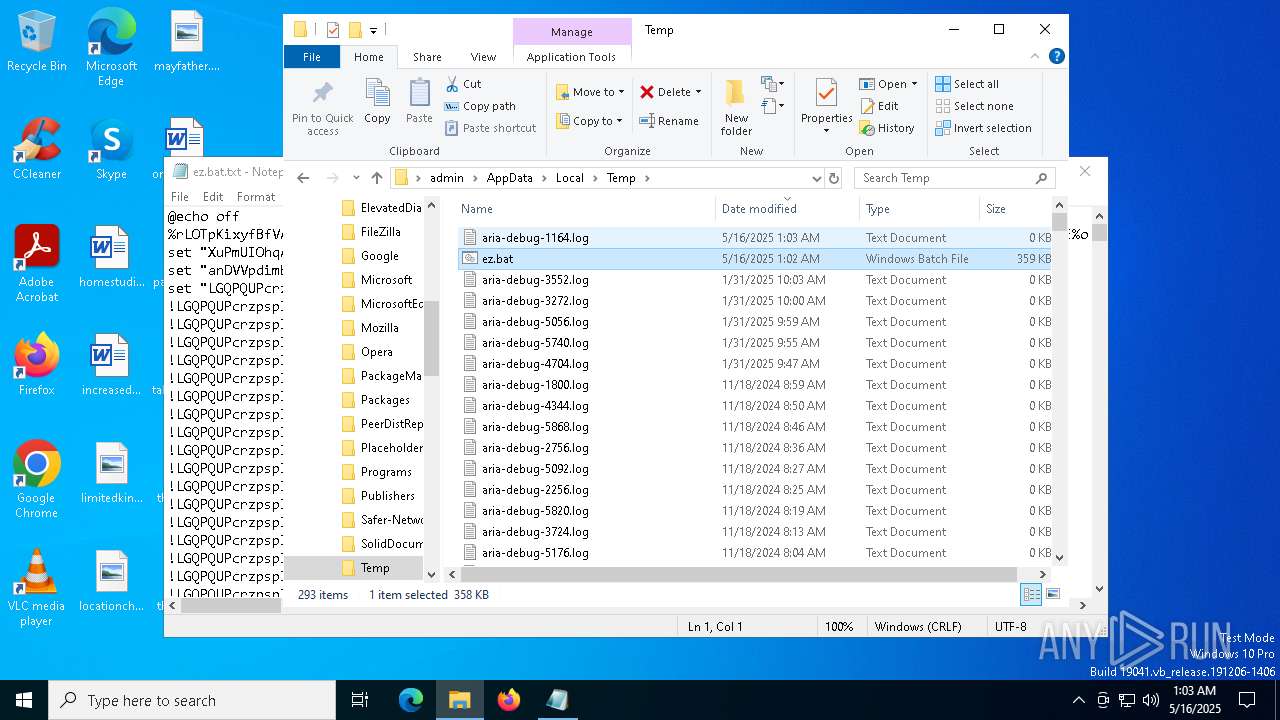
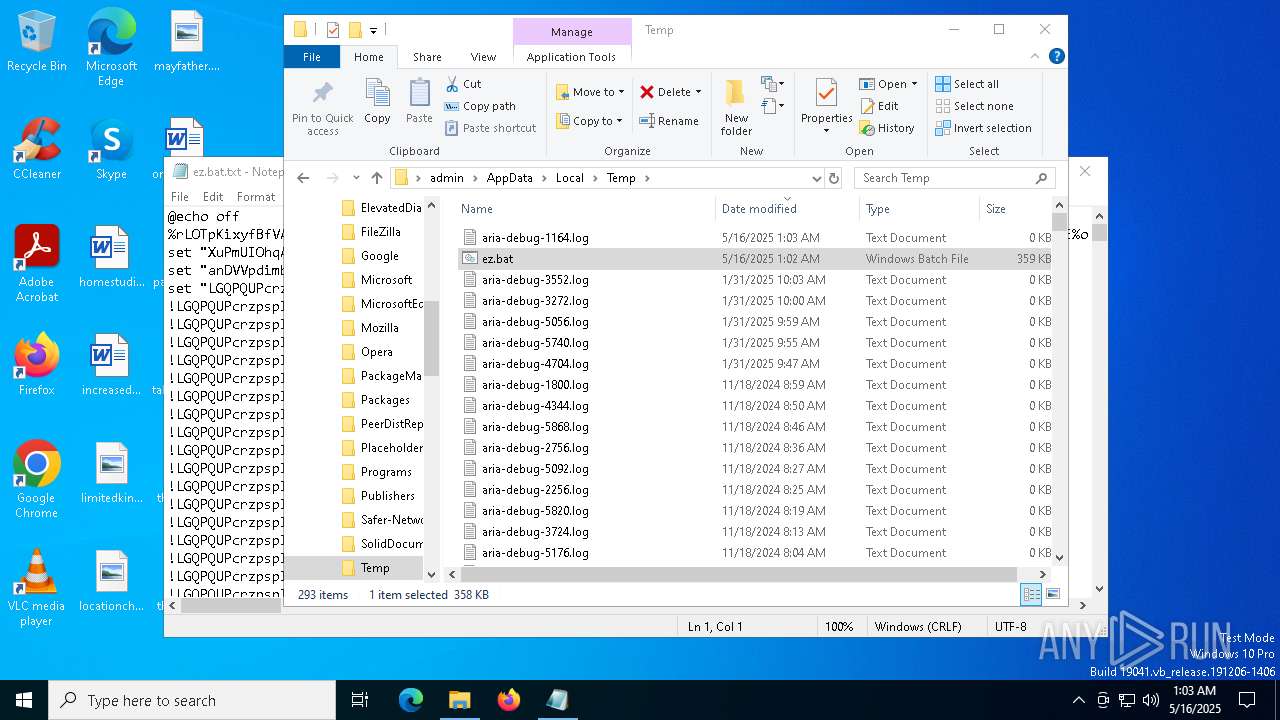
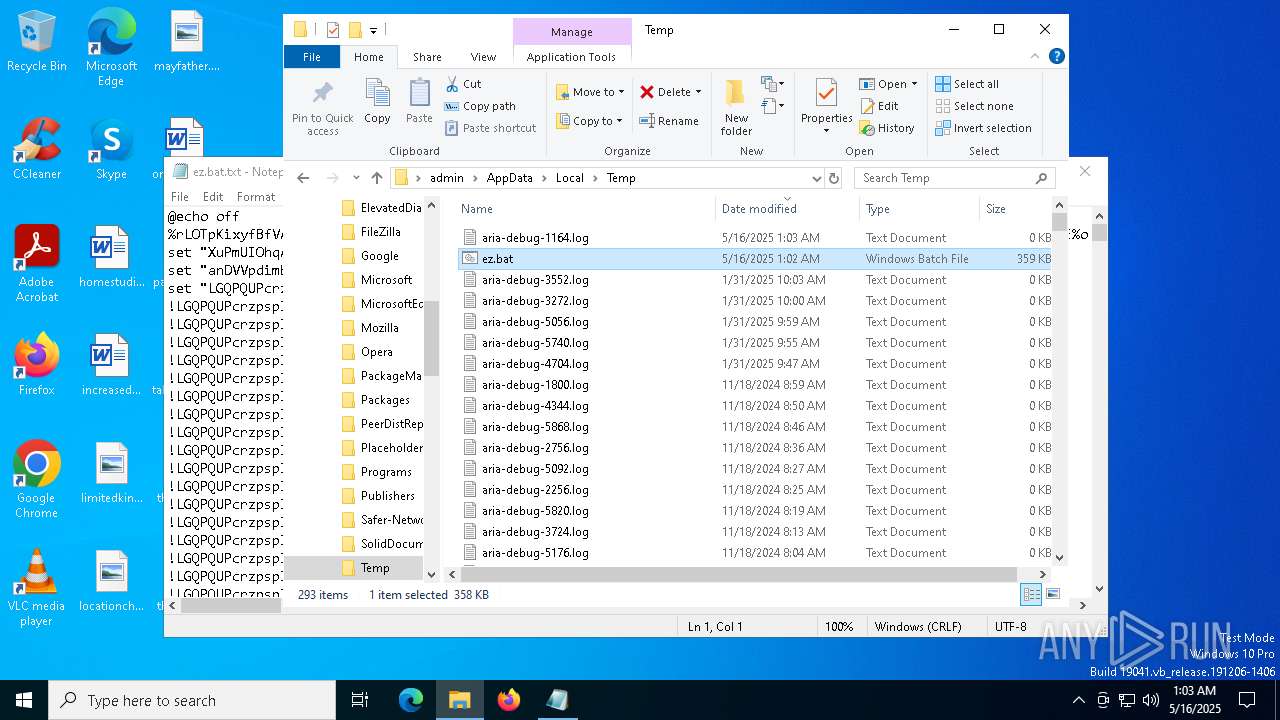
| File name: | ez.bat.txt |
| Full analysis: | https://app.any.run/tasks/25d35eac-07f4-41c1-8133-472bb6d7283f |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | May 16, 2025, 01:02:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (47892), with CRLF line terminators |
| MD5: | EF76A4810C2D60537EC4445F016BE9F7 |
| SHA1: | 94DC9F665FD4253317C3C25D6C0367E0A2BAD7B8 |
| SHA256: | EAD3E4E40F66DDD6F8B0A0A80FC566D8EA47CEBE6EAC4436156883DD9B228D77 |
| SSDEEP: | 6144:n42d4uimRJhpTwp28u7udi0706wIiQfls9z7nK5pWRsjstDozmzJ7:n444u/fhpI1gudT701UW/KIsSWOF |
MALICIOUS
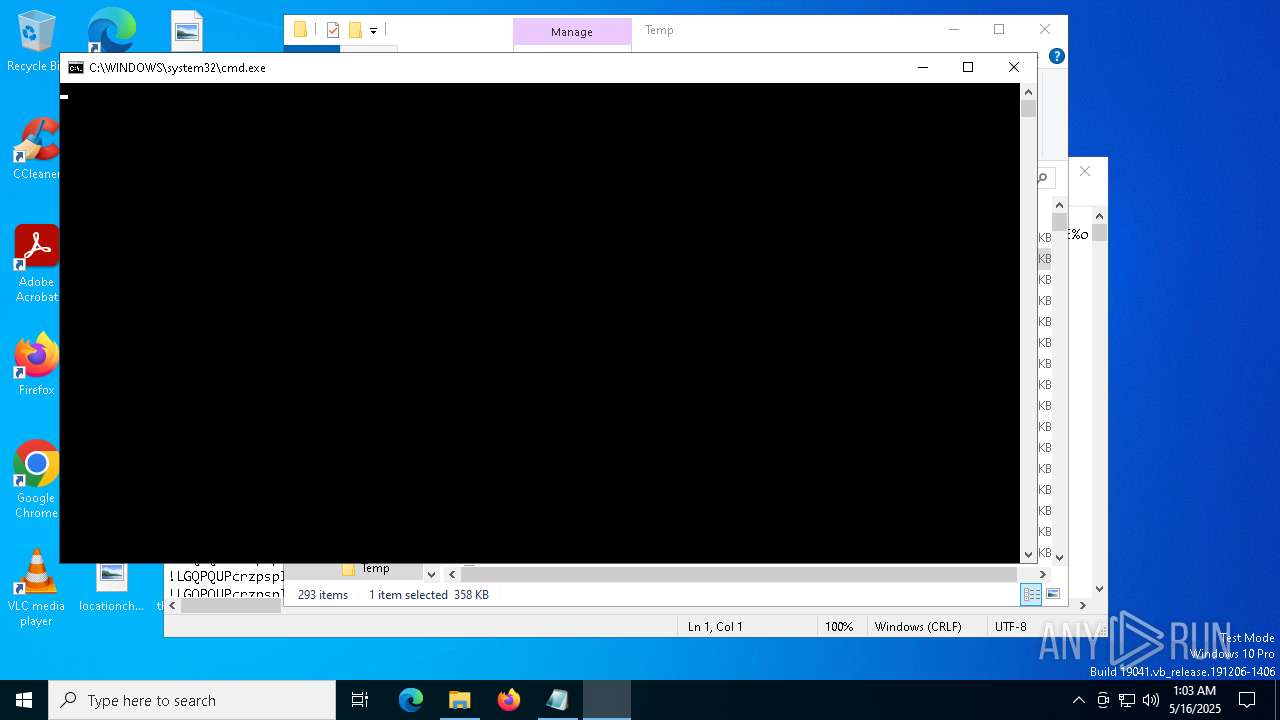
Run PowerShell with an invisible window
- powershell.exe (PID: 2568)
- powershell.exe (PID: 1616)
- powershell.exe (PID: 3332)
Bypass execution policy to execute commands
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3332)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 3140)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3332)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3332)
BOTNET has been found (auto)
- powershell.exe (PID: 2568)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3332)
Changes Windows Defender settings
- powershell.exe (PID: 3332)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 3332)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 5596)
Changes settings for real-time protection
- powershell.exe (PID: 5596)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 5596)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 5596)
Changes Controlled Folder Access settings
- powershell.exe (PID: 5596)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 5596)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 5596)
Actions looks like stealing of personal data
- powershell.exe (PID: 3332)
Steals credentials from Web Browsers
- powershell.exe (PID: 3332)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3332)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5436)
- cmd.exe (PID: 3140)
Cryptography encrypted command line is found
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3332)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5436)
- cmd.exe (PID: 3140)
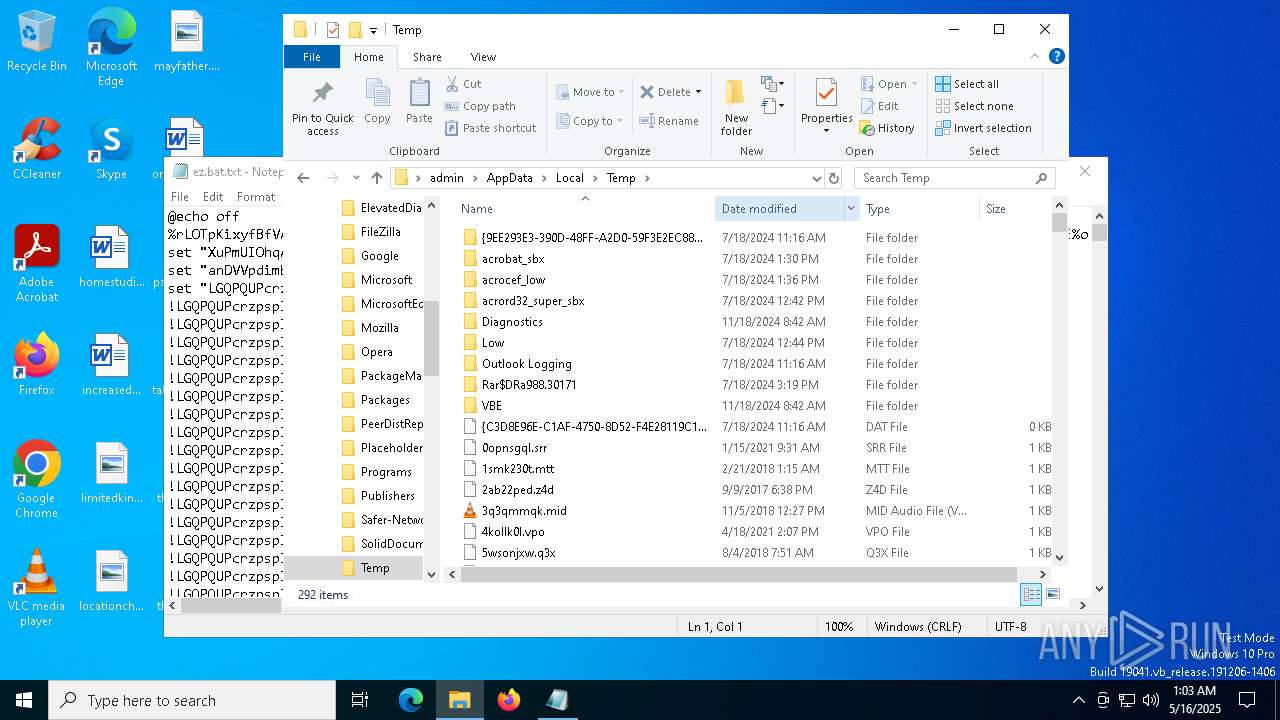
Executable content was dropped or overwritten
- powershell.exe (PID: 2568)
Process drops legitimate windows executable
- powershell.exe (PID: 2568)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 1616)
Starts POWERSHELL.EXE for commands execution
- wusa.exe (PID: 6132)
- cmd.exe (PID: 3140)
- powershell.exe (PID: 3332)
- cmd.exe (PID: 5436)
Executing commands from a ".bat" file
- powershell.exe (PID: 1616)
Application launched itself
- powershell.exe (PID: 3332)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 3332)
Script disables Windows Defender's IPS
- powershell.exe (PID: 3332)
Script disables Windows Defender's real-time protection
- powershell.exe (PID: 3332)
Uses WMIC.EXE to obtain operating system information
- powershell.exe (PID: 3332)
Uses WMIC.EXE to obtain computer system information
- powershell.exe (PID: 3332)
Uses WMIC.EXE to obtain Windows Installer data
- powershell.exe (PID: 3332)
Checks for external IP
- powershell.exe (PID: 3332)
- svchost.exe (PID: 2196)
The process connected to a server suspected of theft
- powershell.exe (PID: 3332)
Uses WMIC.EXE to obtain a list of video controllers
- powershell.exe (PID: 3332)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 6108)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3332)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3332)
The sample compiled with english language support
- powershell.exe (PID: 2568)
Checks supported languages
- wusa.exe (PID: 6132)
Disables trace logs
- powershell.exe (PID: 3332)
Checks proxy server information
- powershell.exe (PID: 3332)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 5596)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5744)
Manual execution by a user
- cmd.exe (PID: 5436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
163
Monitored processes
34
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "powershell.exe" start -windowstyle hidden -filepath 'C:\Users\admin\AppData\Local\Temp\ez.bat' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wusa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | "wmic.exe" os get Caption | C:\Windows\System32\wbem\WMIC.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
36 583
Read events
36 583
Write events
0
Delete events
0
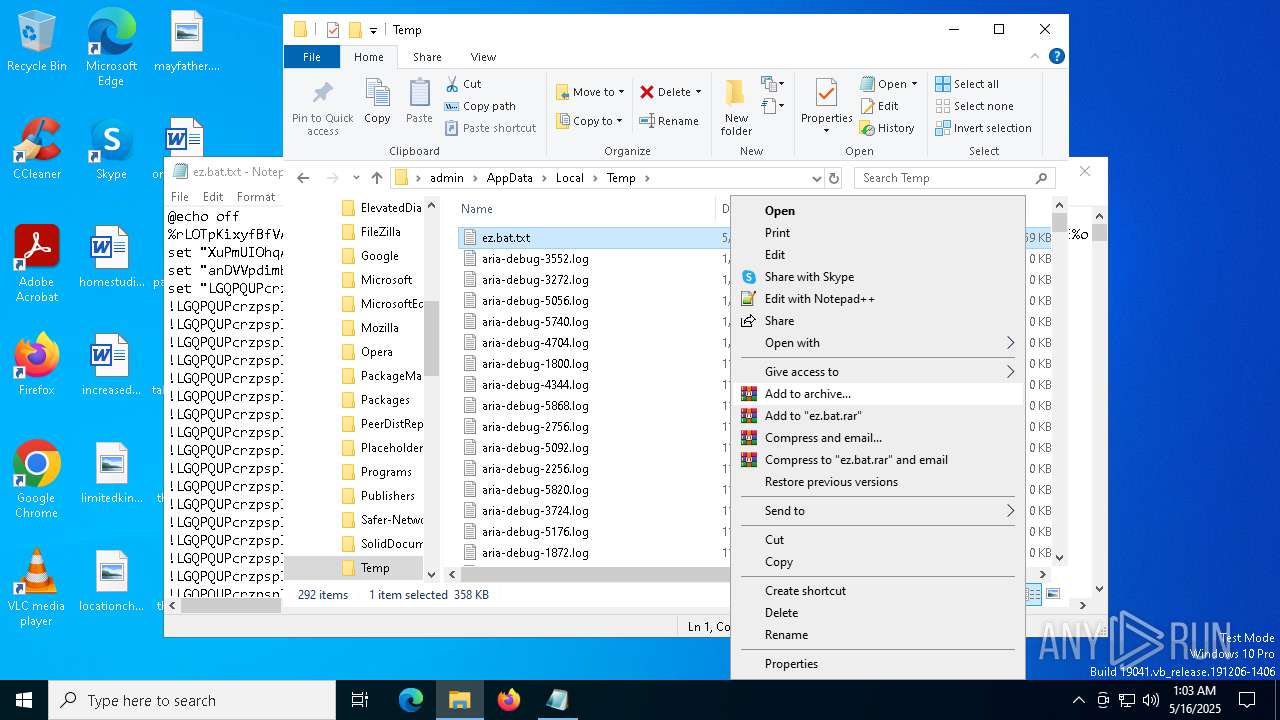
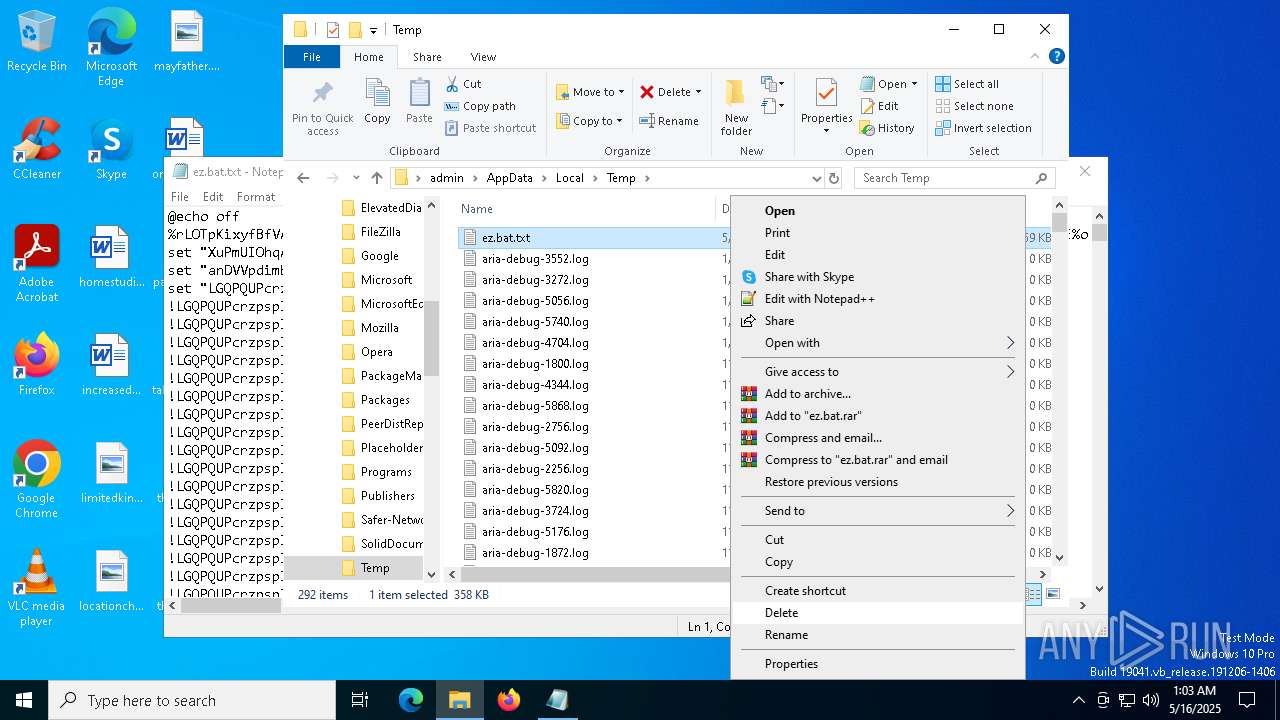
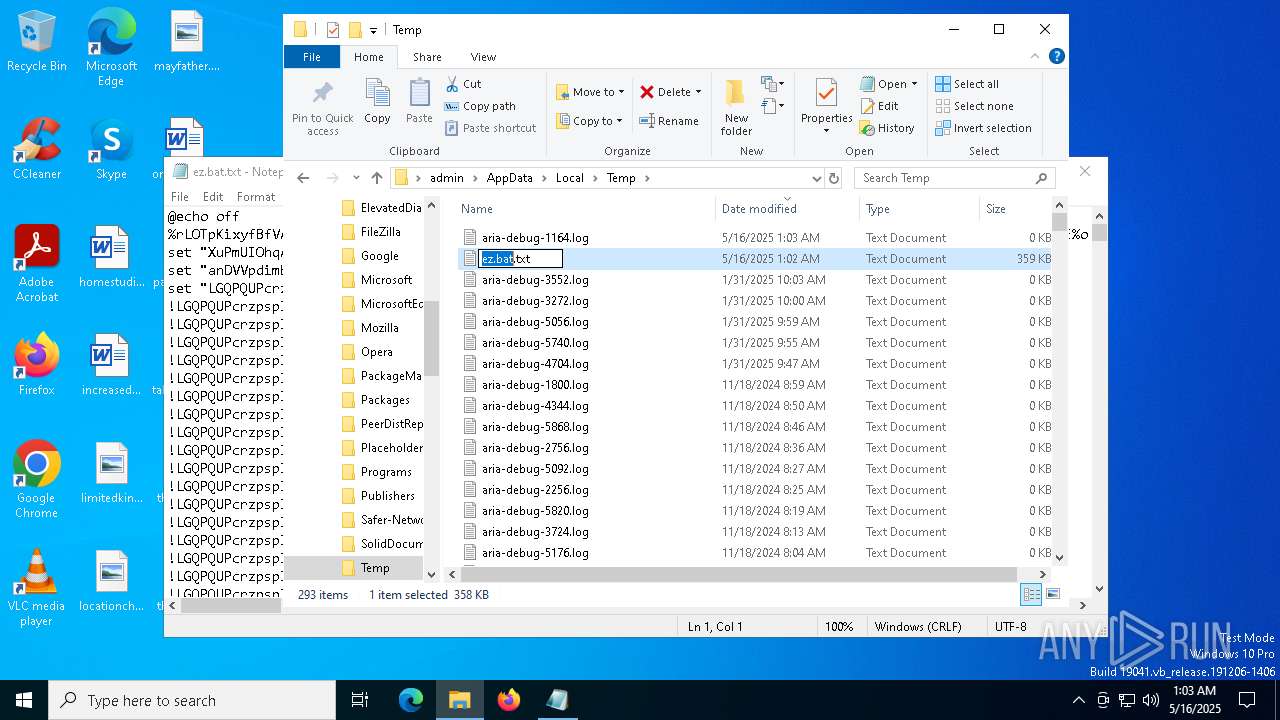
Modification events
Executable files
2
Suspicious files
7
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_idip3gfp.xhx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_avyfdun0.ir3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eytnqwxg.ake.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a2nhdgb3.iaf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2568 | powershell.exe | C:\Windows \System32\WTSAPI32.dll | executable | |
MD5:130553CE2E4112CF59F9CFECFB81FE75 | SHA256:1ABD799BA4BFEE25737243568AE048C0B50F1892B41D7E0F7B3C3AF8410BABDE | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5wltff1b.kpq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\YzPJHzk5rlwdvEs | binary | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\8HQAHGQjM3SErcy | binary | |
MD5:09A22B1BCD9725DF5B3591EBBD2CEBD6 | SHA256:4F81904A9B06C58572A0E5769B3B4FFB99E7BD4BE88EE8C2B64A804F483D9DC6 | |||
| 2568 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:04F412471640BEEE4CACD7B350846322 | SHA256:A3DAC121C58D6D501FE7AC25175F31B1210F6D89EA9E4379EC346C9F4C42FEB9 | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_obp013tv.f3c.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
18
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4120 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3332 | powershell.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
4120 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3332 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
3332 | powershell.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |