| File name: | qrypted.BIG.jar |
| Full analysis: | https://app.any.run/tasks/d09517eb-c0b9-49e5-9fa9-131b975e92b2 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | February 19, 2019, 13:02:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | C1C89AE6EC499D0C763B1EC1A6FFB964 |
| SHA1: | 4C188E233710A48916367C2B0023ED6401D2876D |
| SHA256: | EA512270C8876BA9B32243267B178DF422FB5D9CE56127E4E797B6E365CDB313 |
| SSDEEP: | 12288:mzd7wdLiSJByRxil3h3HVhHp02ZMpEZ3Y8R5ShLFI/+GollONq/3hkFfHJhCT:4wdmiBKkz1ha2s03xynG0lOMhkFPJhu |
MALICIOUS
Loads dropped or rewritten executable
- java.exe (PID: 3196)
- explorer.exe (PID: 284)
- javaw.exe (PID: 3592)
- java.exe (PID: 3172)
- javaw.exe (PID: 3776)
AdWind was detected
- java.exe (PID: 3196)
- java.exe (PID: 3172)
Application was dropped or rewritten from another process
- java.exe (PID: 3196)
- javaw.exe (PID: 3592)
- java.exe (PID: 3172)
- javaw.exe (PID: 3776)
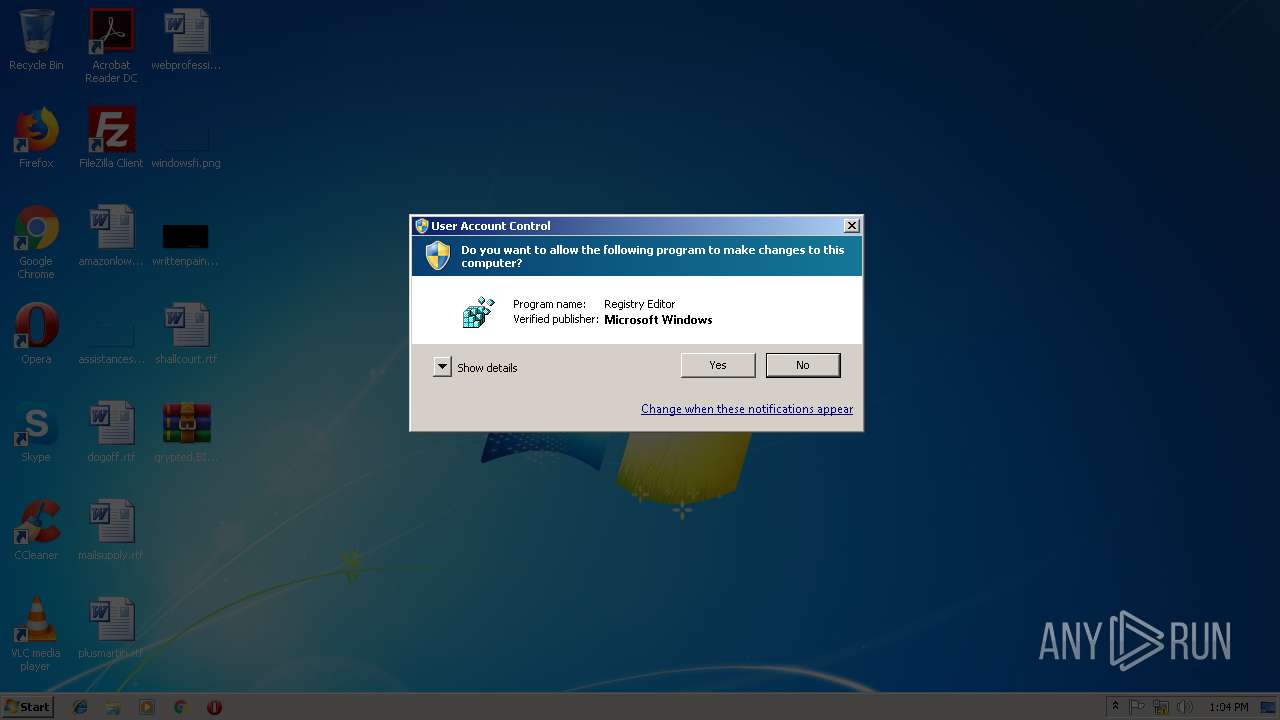
Changes the autorun value in the registry
- reg.exe (PID: 3296)
ADWIND was detected
- javaw.exe (PID: 3776)
Uses TASKKILL.EXE to kill antiviruses
- javaw.exe (PID: 3776)
Changes Image File Execution Options
- regedit.exe (PID: 2680)
Actions looks like stealing of personal data
- javaw.exe (PID: 3776)
Runs app for hidden code execution
- javaw.exe (PID: 3776)
SUSPICIOUS
Starts CMD.EXE for commands execution
- java.exe (PID: 3196)
- javaw.exe (PID: 3592)
- java.exe (PID: 3172)
- javaw.exe (PID: 3776)
Executes JAVA applets
- javaw.exe (PID: 3592)
- explorer.exe (PID: 284)
Executes scripts
- cmd.exe (PID: 3880)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 876)
- cmd.exe (PID: 352)
- cmd.exe (PID: 3656)
- cmd.exe (PID: 352)
- cmd.exe (PID: 4064)
Creates files in the user directory
- javaw.exe (PID: 3592)
- xcopy.exe (PID: 3700)
Executable content was dropped or overwritten
- xcopy.exe (PID: 3700)
- javaw.exe (PID: 3776)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 3592)
- cmd.exe (PID: 4072)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 1912)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 3104)
- cmd.exe (PID: 3120)
- cmd.exe (PID: 1088)
- cmd.exe (PID: 2212)
- cmd.exe (PID: 3348)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 996)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 3368)
Starts itself from another location
- javaw.exe (PID: 3592)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 3592)
Connects to unusual port
- javaw.exe (PID: 3776)
Uses TASKKILL.EXE to kill process
- javaw.exe (PID: 3776)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:02:19 07:52:25 |
| ZipCRC: | 0xba58cbd7 |
| ZipCompressedSize: | 64 |
| ZipUncompressedSize: | 62 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
143
Monitored processes
68
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | reg query "HKEY_CURRENT_USER\Software\HeidiSQL\Servers" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5895766500417377413.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 352 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive630742370207967698.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 876 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive8182916517174984640.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 996 | cmd.exe | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1088 | cmd.exe | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1856 | reg query "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\00000003" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | taskkill /IM Taskmgr.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1912 | cmd.exe | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 337
Read events
1 316
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3296) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | hvLJTTSXfPD |
Value: "C:\Users\admin\AppData\Roaming\Oracle\bin\javaw.exe" -jar "C:\Users\admin\KExirswmxQT\AuQkVrasjrU.zTdvfw" | |||
| (PID) Process: | (2412) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2412) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (284) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3776) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2680) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Taskmgr.exe |
| Operation: | write | Name: | debugger |
Value: svchost.exe | |||
| (PID) Process: | (2680) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 2 | |||
| (PID) Process: | (2680) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe |
| Operation: | write | Name: | debugger |
Value: svchost.exe | |||
| (PID) Process: | (2680) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MsMpEng.exe |
| Operation: | write | Name: | debugger |
Value: svchost.exe | |||
| (PID) Process: | (2680) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpUXSrv.exe |
| Operation: | write | Name: | debugger |
Value: svchost.exe | |||
Executable files
113
Suspicious files
10
Text files
73
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | java.exe | C:\Users\admin\AppData\Local\Temp\Retrive2640238630834956895.vbs | — | |
MD5:— | SHA256:— | |||
| 3592 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3196 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3700 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\COPYRIGHT | text | |
MD5:89F660D2B7D58DA3EFD2FECD9832DA9C | SHA256:F6A08C9CC04D7C6A86576C1EF50DD0A690AE5CB503EFD205EDB2E408BD8D557B | |||
| 3700 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\LICENSE | text | |
MD5:98F46AB6481D87C4D77E0E91A6DBC15F | SHA256:23F9A5C12FA839650595A32872B7360B9E030C7213580FB27DD9185538A5828C | |||
| 3700 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\Welcome.html | html | |
MD5:27CF299B6D93FACA73FBCDCF4AECFD93 | SHA256:3F1F0EE75588DBBA3B143499D08AA9AB431E4A34E483890CFAC94A8E1061B7CF | |||
| 3700 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\bin\dt_socket.dll | executable | |
MD5:138F156057245747692A68EBE50D52C2 | SHA256:F0FD0268D6E410C05E7EE71AD9C96744CD5E4A97329F608041D7078FAEE24ED0 | |||
| 3700 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\bin\bci.dll | executable | |
MD5:6D8D8A26450EE4BA0BE405629EA0A511 | SHA256:7945365A3CD40D043DAE47849E6645675166920958300E64DEA76A865BC479AF | |||
| 3700 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\bin\dcpr.dll | executable | |
MD5:682CFD9431E5675900B04FEBE6CD4EB9 | SHA256:80111E1D706741F5EF7F661835C3AA46664666425AA1B5F93103410F2BEE1213 | |||
| 3700 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\bin\dt_shmem.dll | executable | |
MD5:0744E6A5145AA945D89A16EAC835FAB2 | SHA256:C417390F681276EC0D55D81A91B87EAE75CA245045F5C23E9B43550B708FB1A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
6
Threats
7
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3776 | javaw.exe | 91.192.100.13:7777 | joewhizz.duckdns.org | SOFTplus Entwicklungen GmbH | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
joewhizz.duckdns.org |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
3776 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
3776 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |
3776 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |
3776 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
3776 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
1064 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |