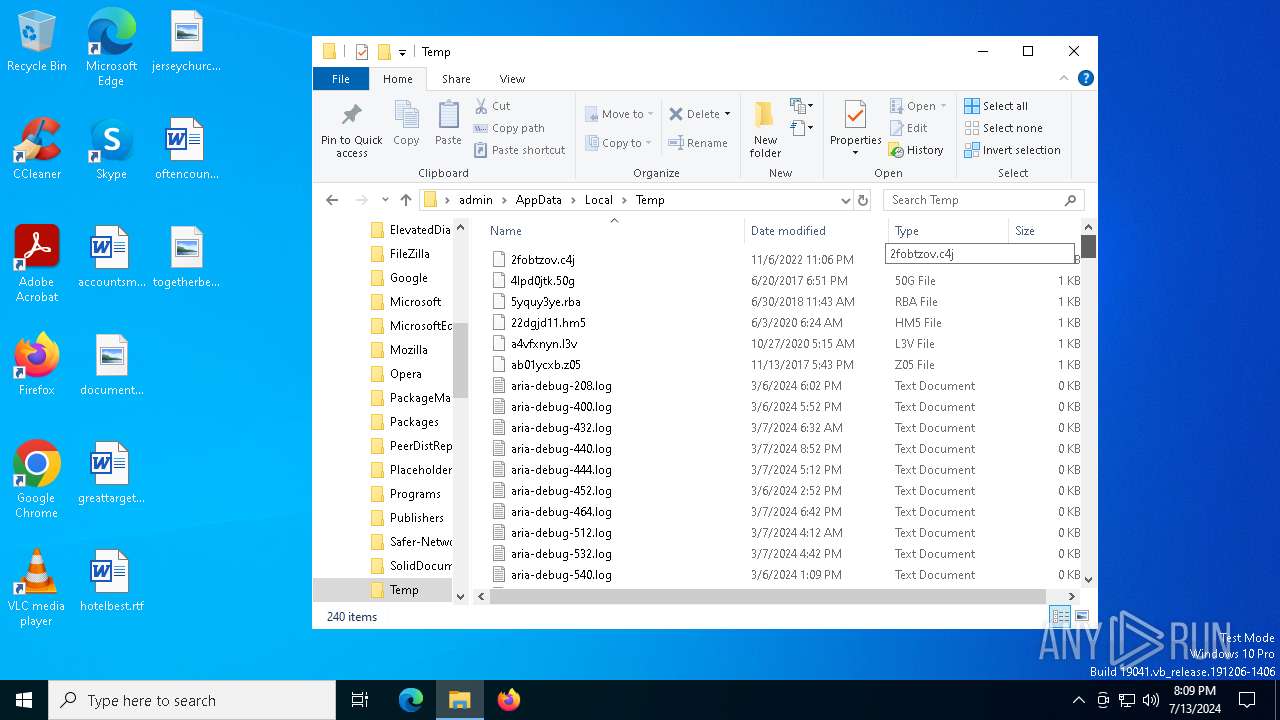
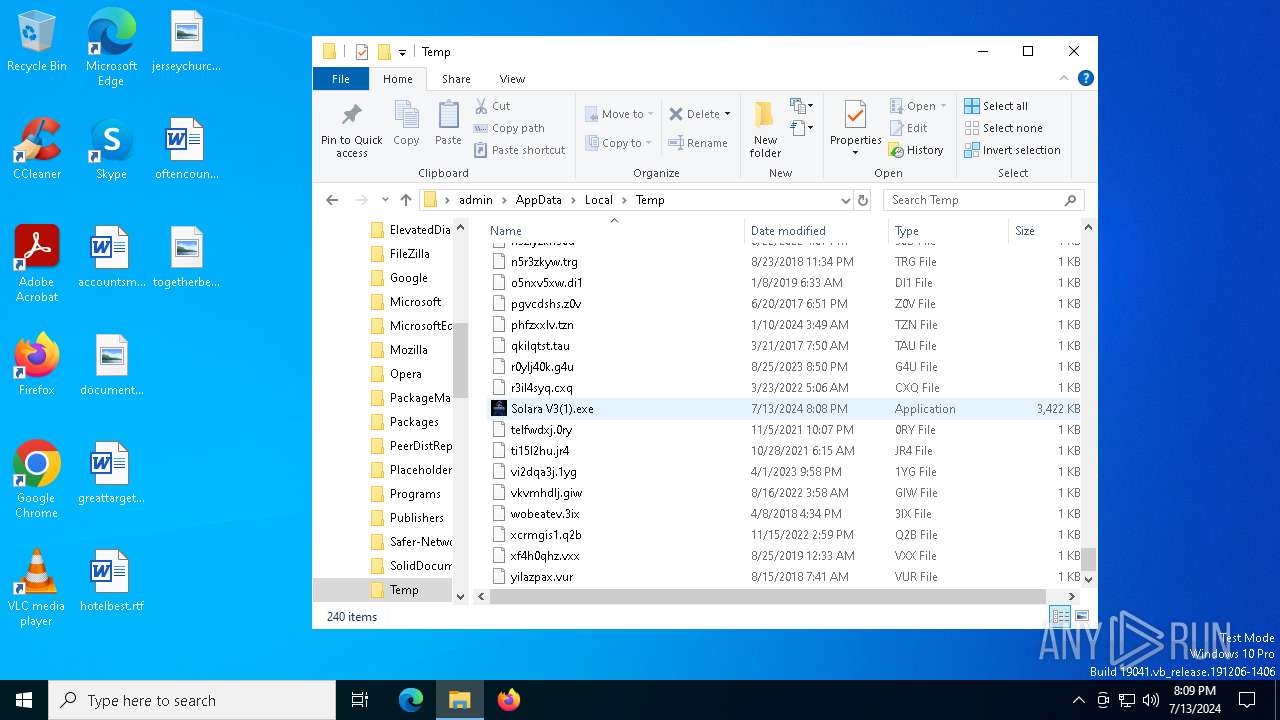
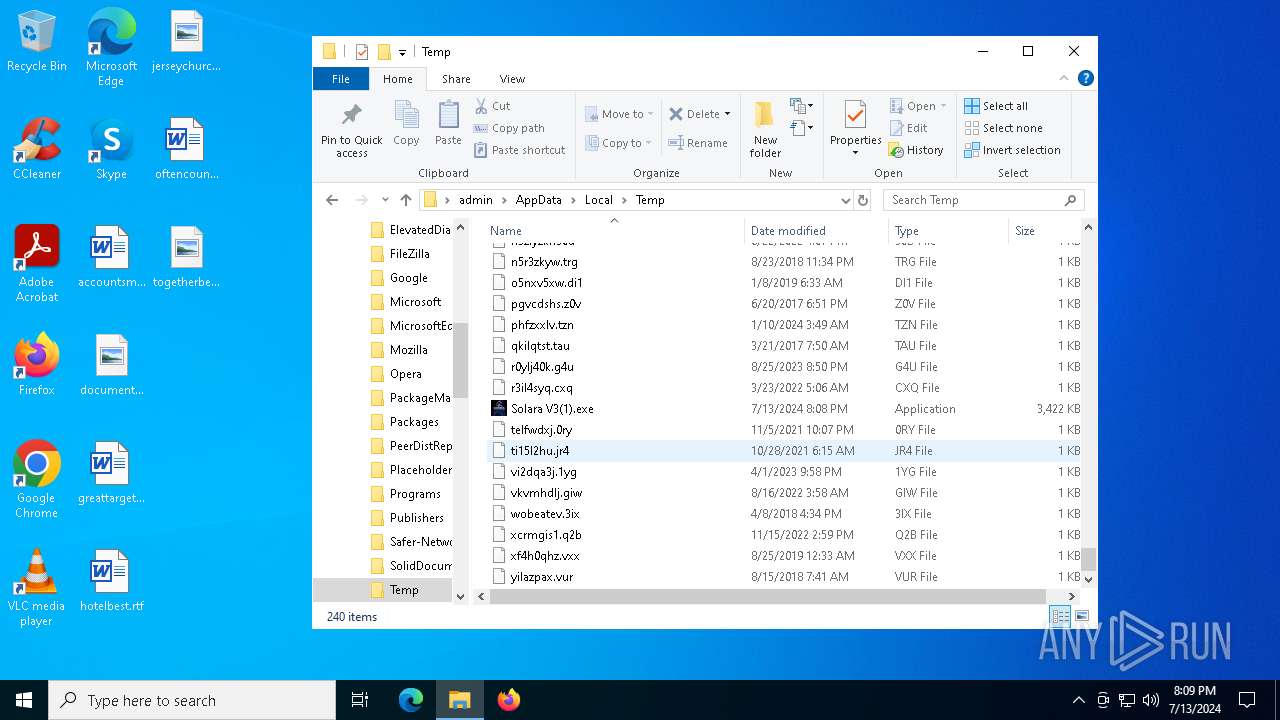
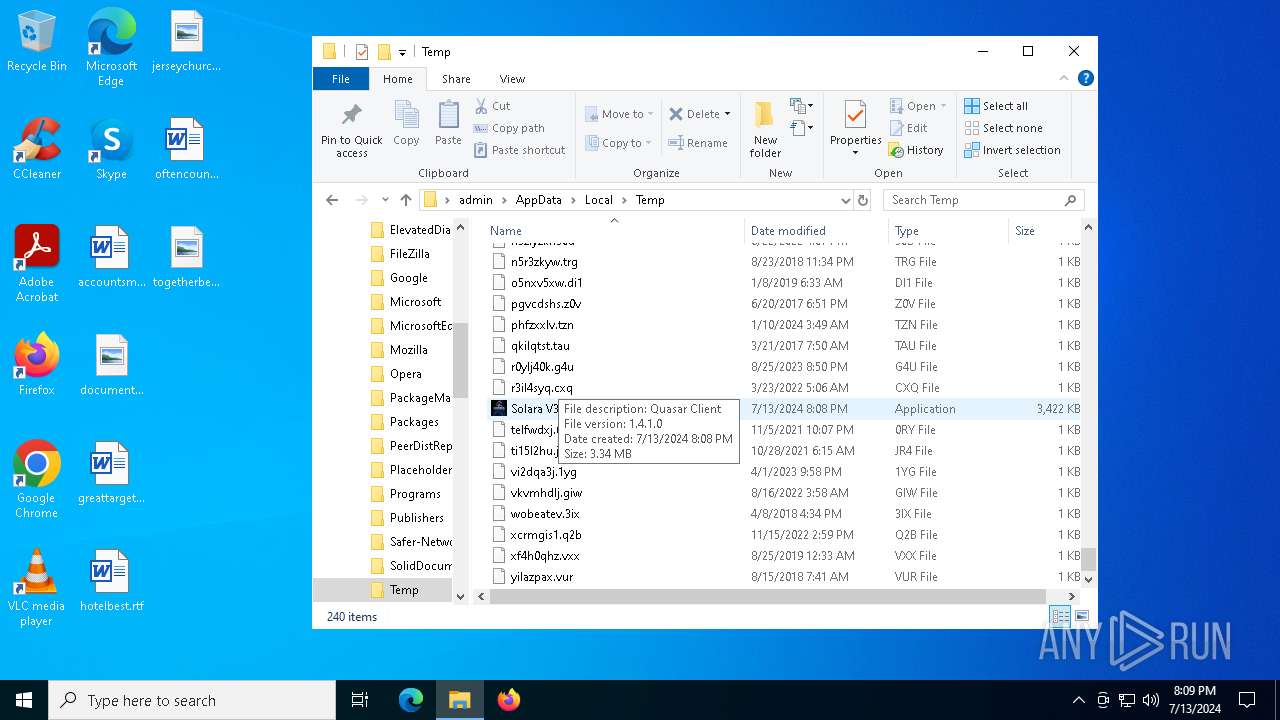
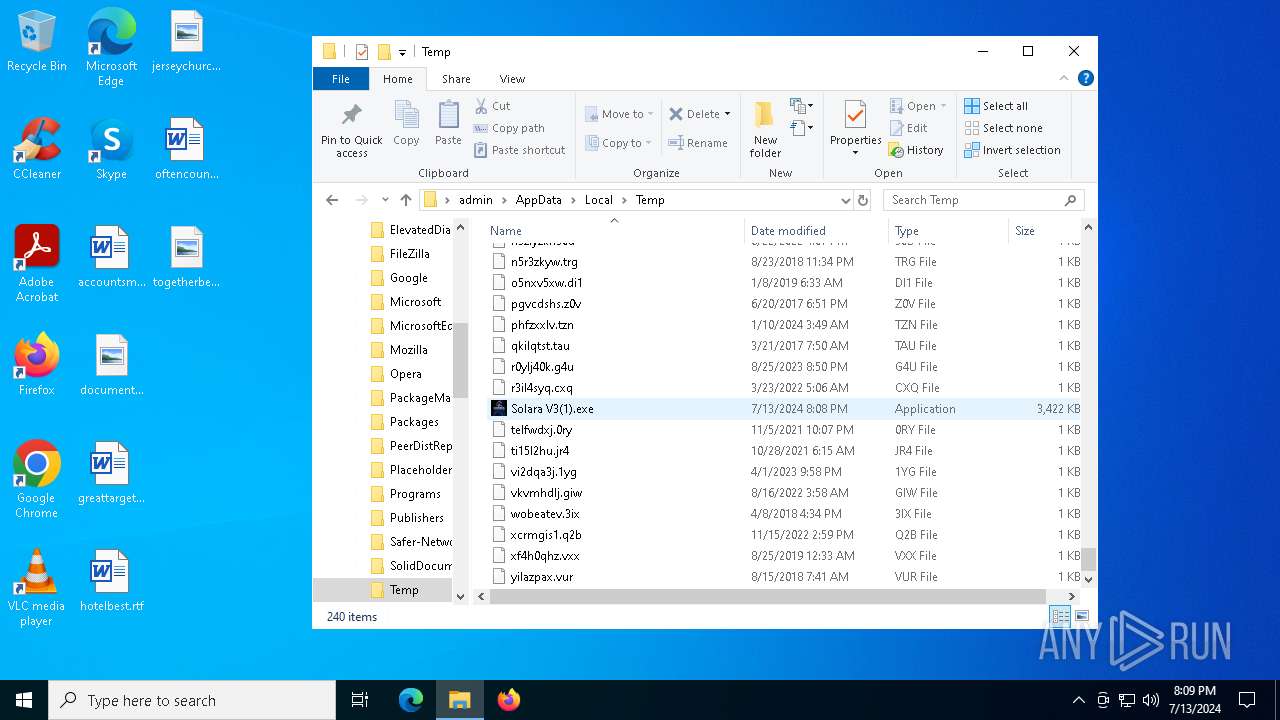
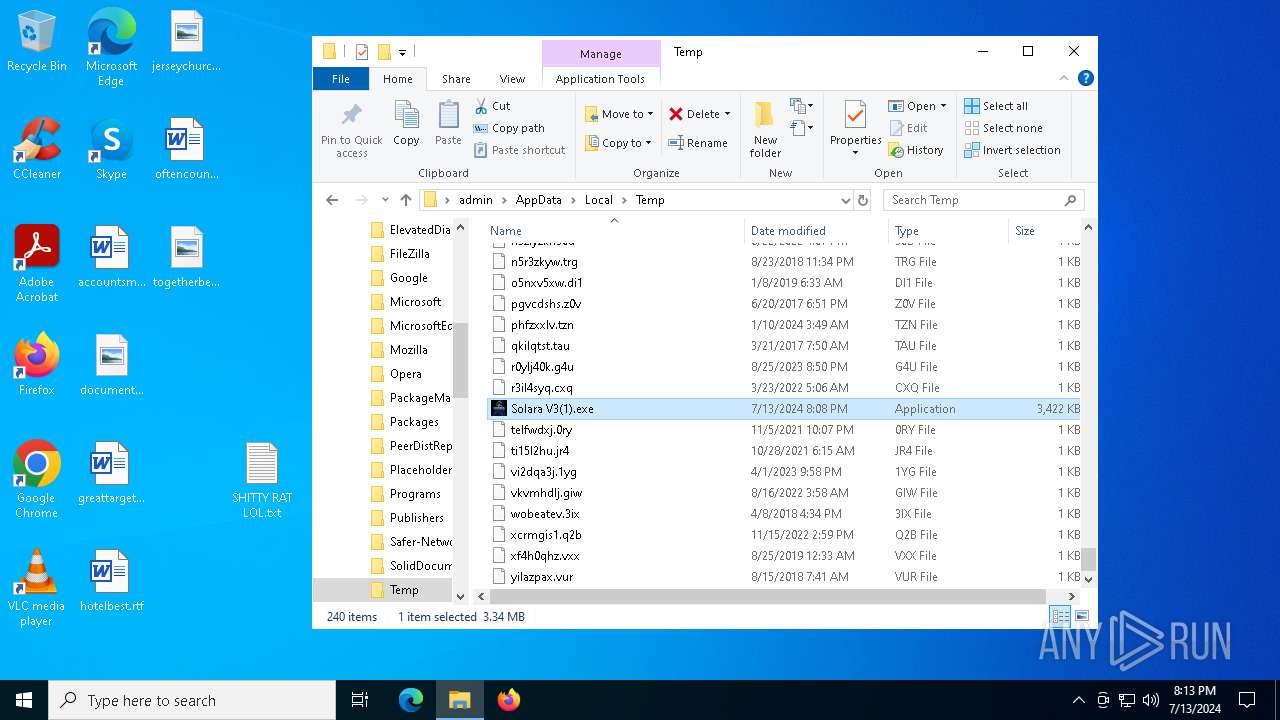
| File name: | Solara V3(1).exe |
| Full analysis: | https://app.any.run/tasks/0665d0b7-e07d-4b9b-ba27-ea44302efd85 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | July 13, 2024, 20:08:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 8D584617F5A696152BBB7A2AF535807E |
| SHA1: | 3B3F560107168496BE19FBE63C3E8BCDC067D7F6 |
| SHA256: | EA12C9150D0D869D3038A9EB72D561FC568AD4F24867FA4E5B2360545F6B61F7 |
| SSDEEP: | 98304:s2NkKCmRf7uY1+DVlYZ+hHaIDg0WFVrb0bj+iG0o:qXgP |
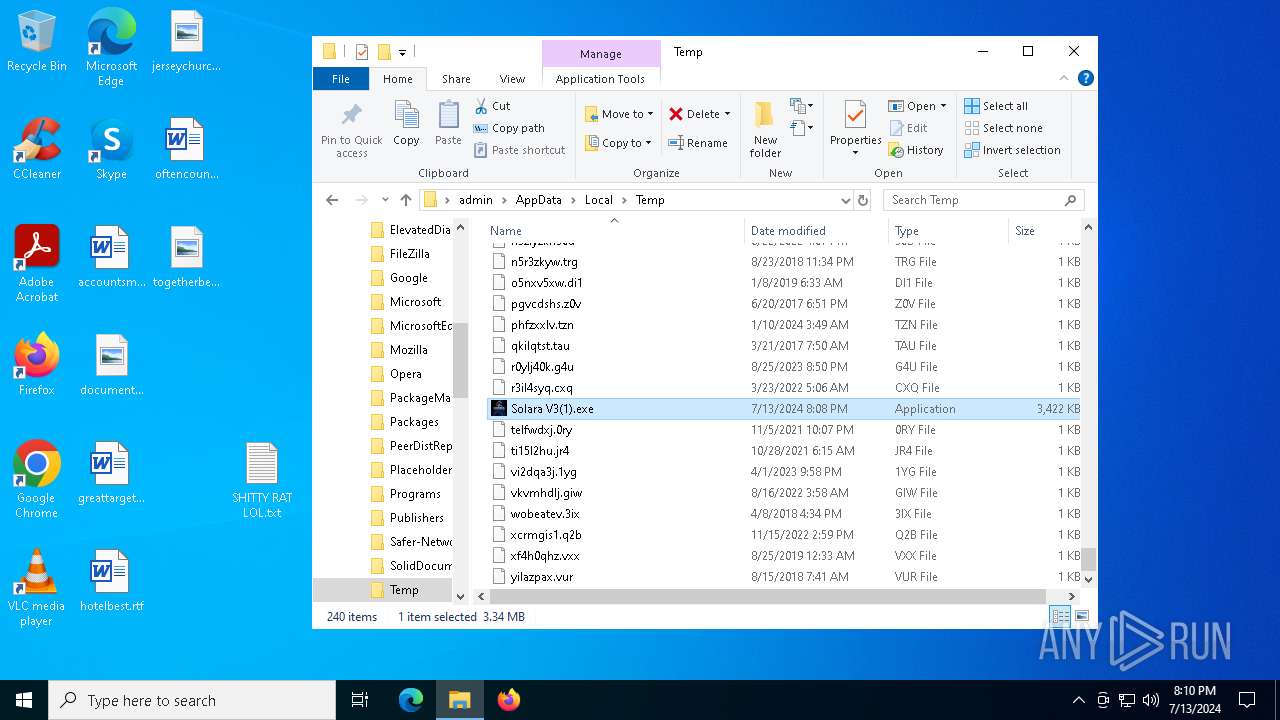
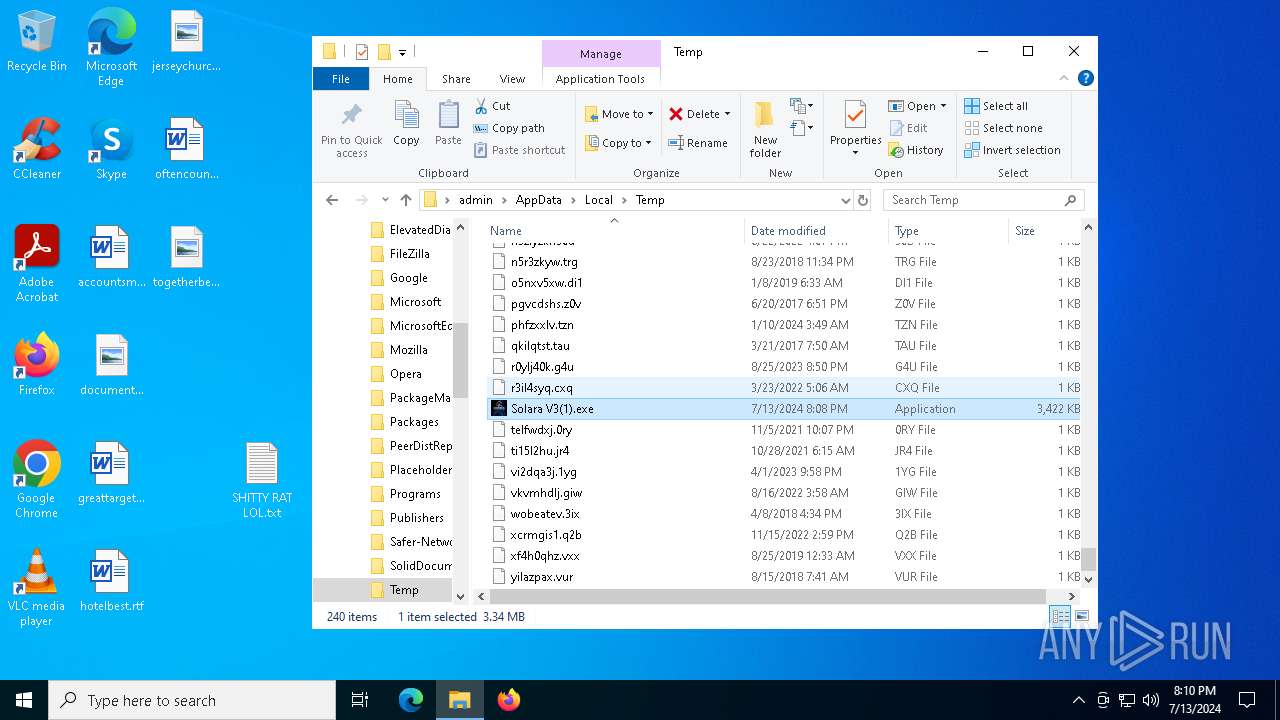
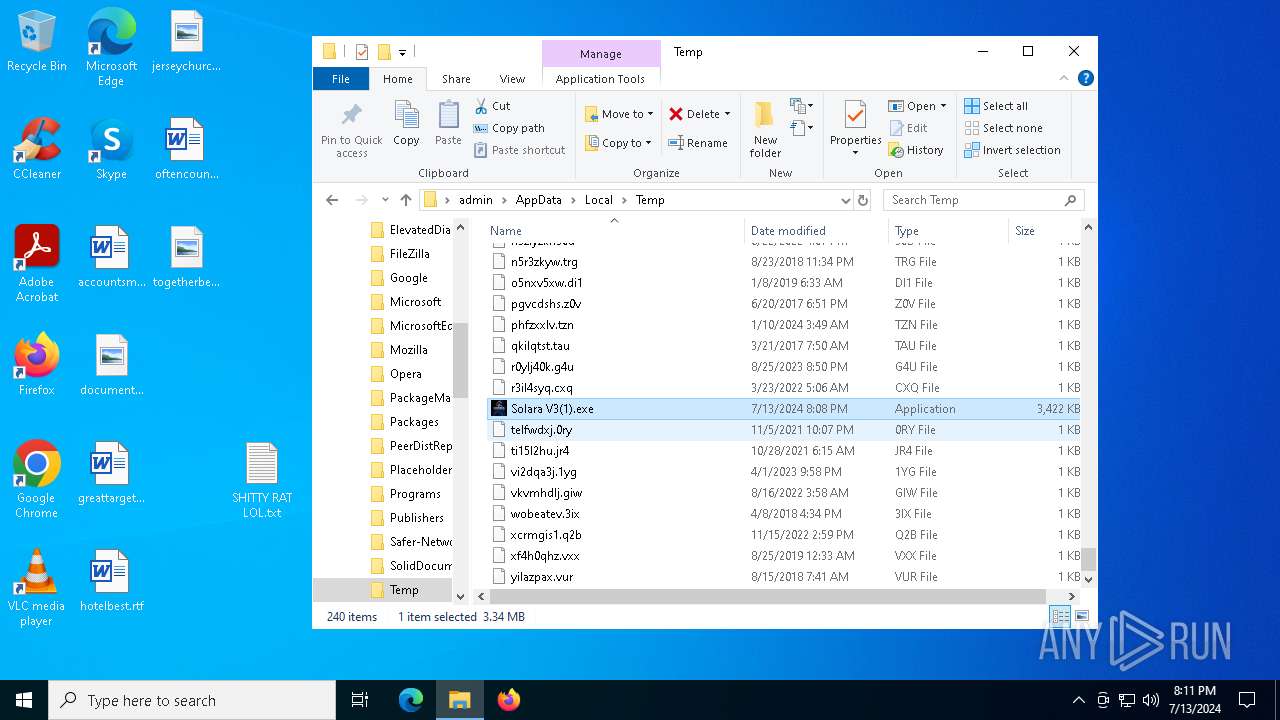
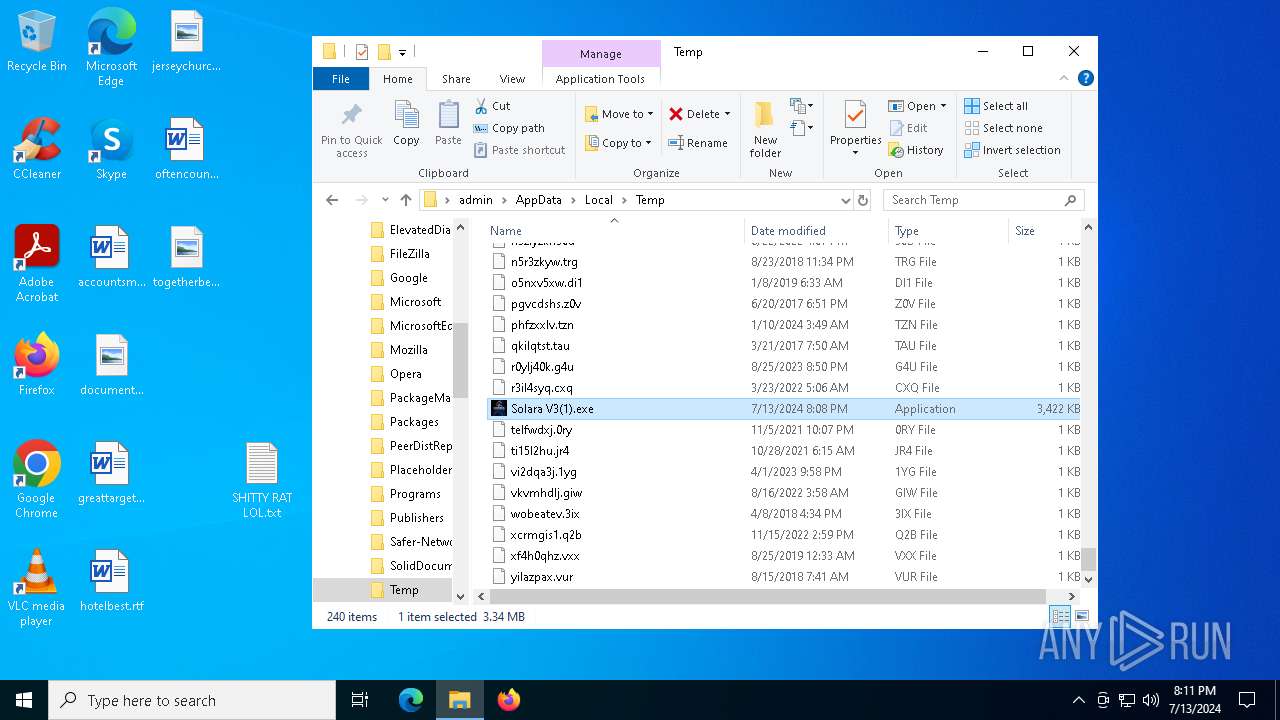
MALICIOUS
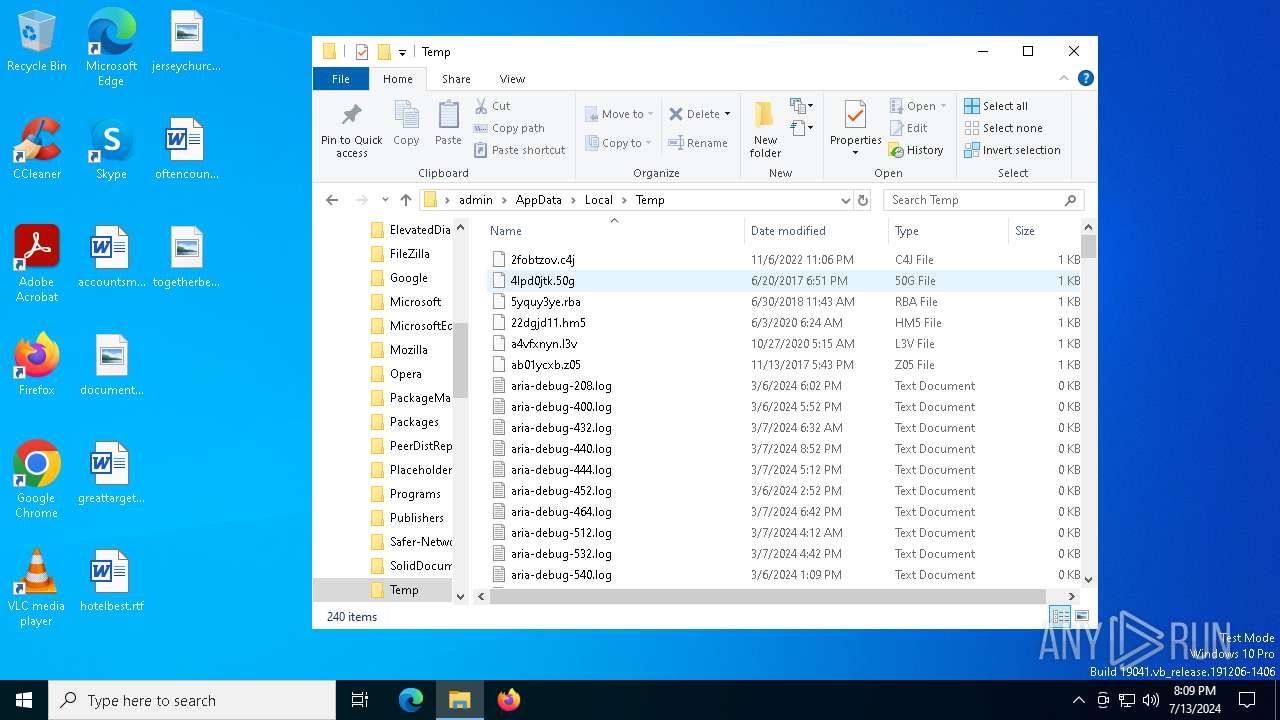
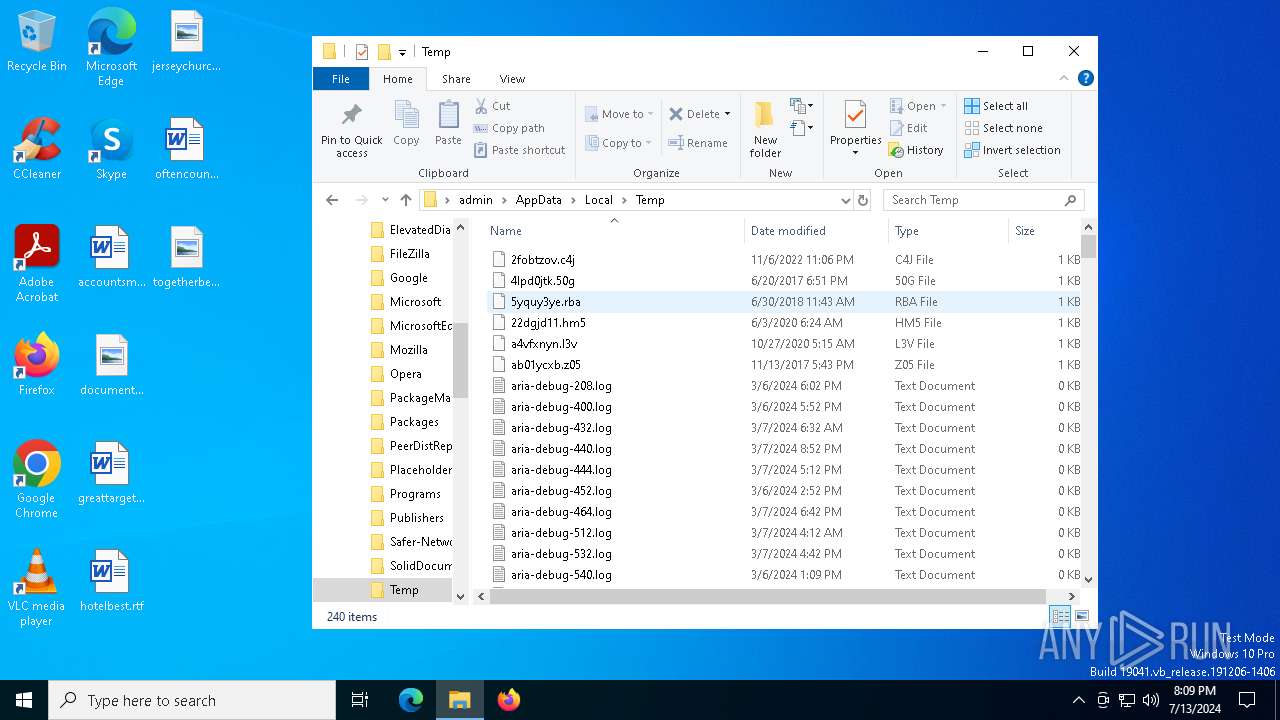
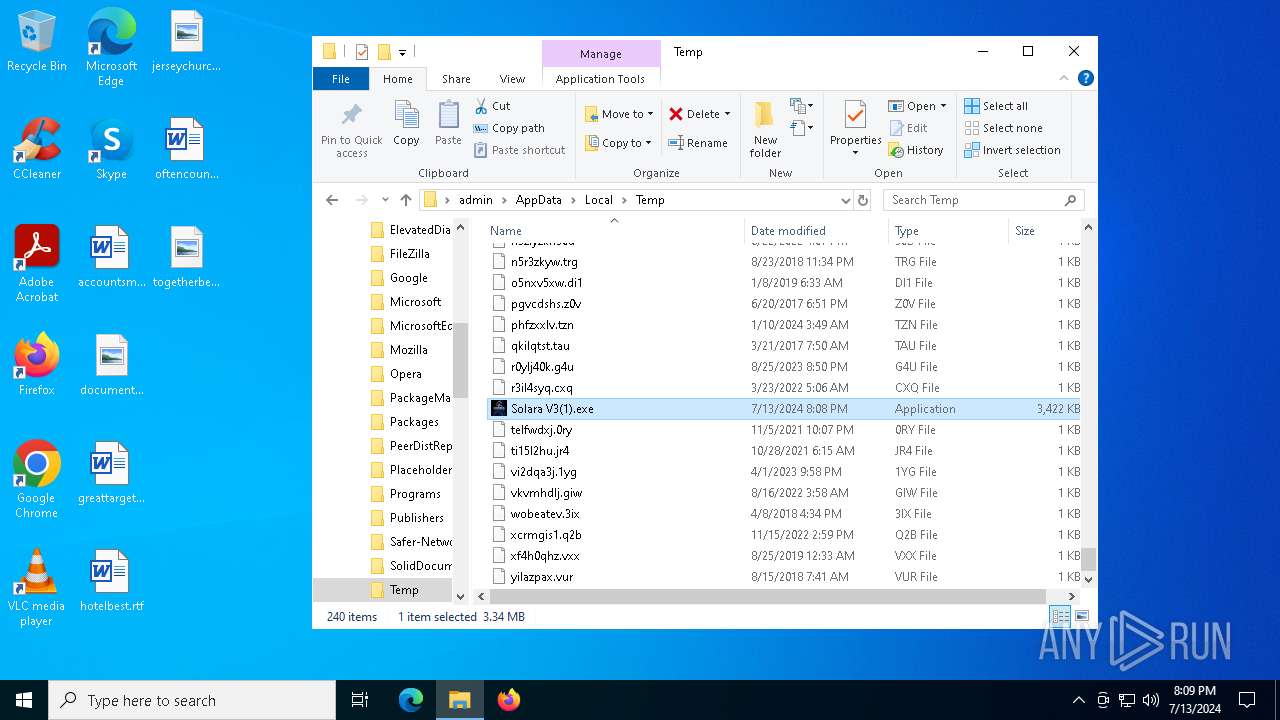
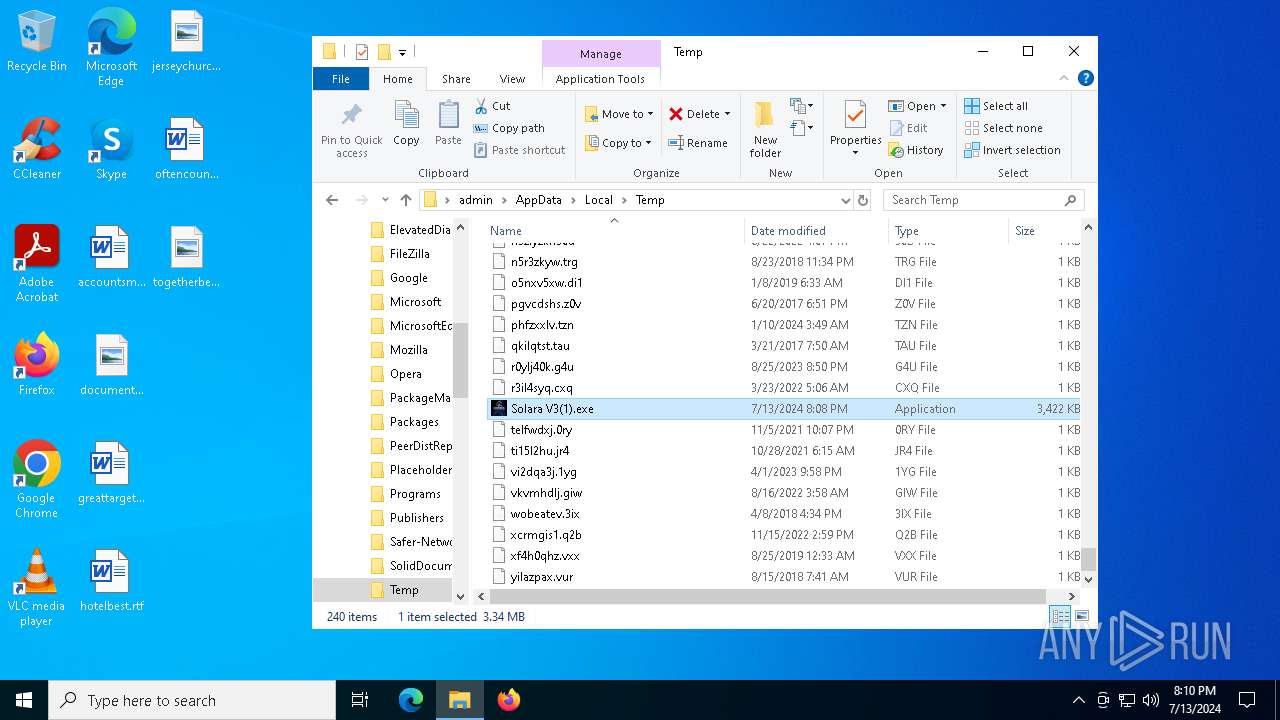
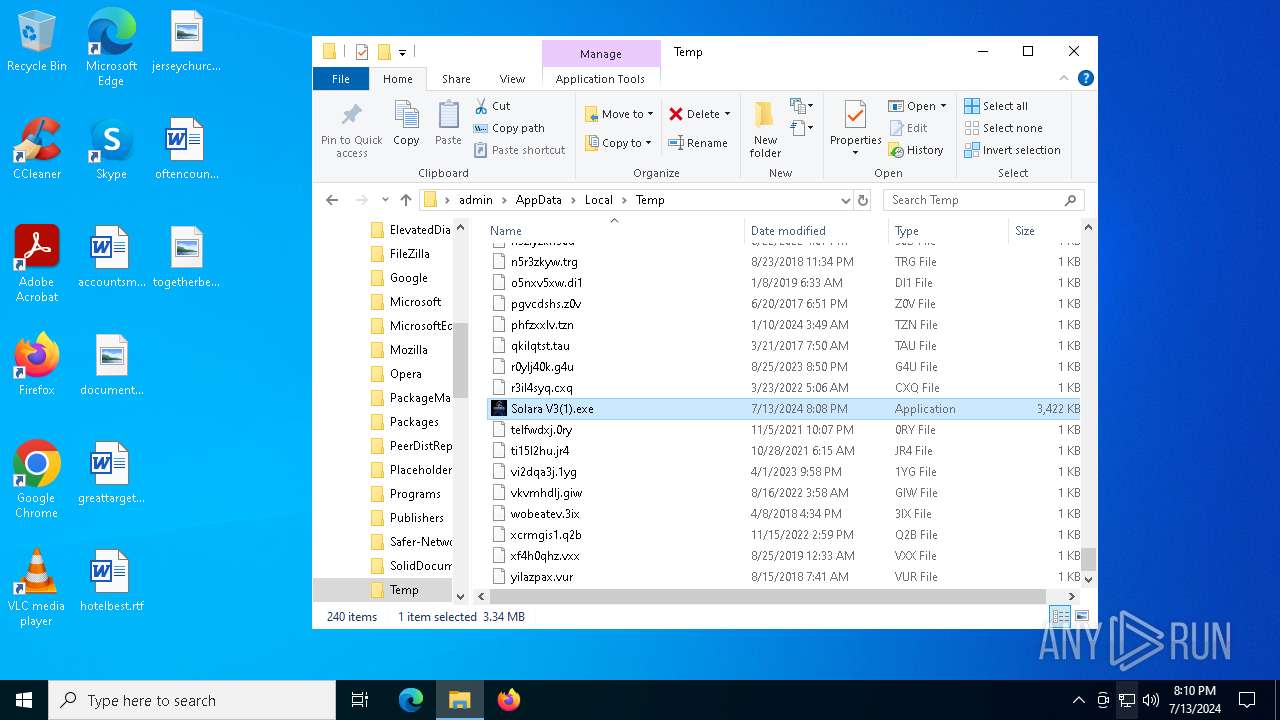
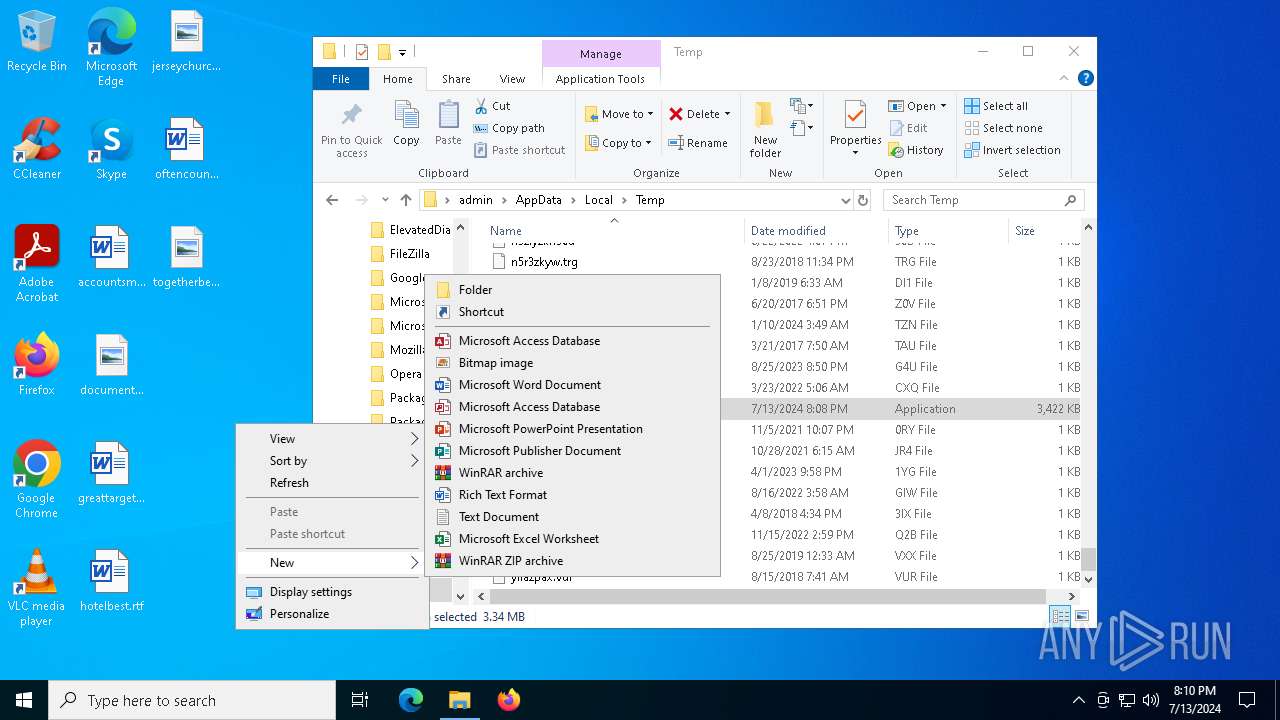
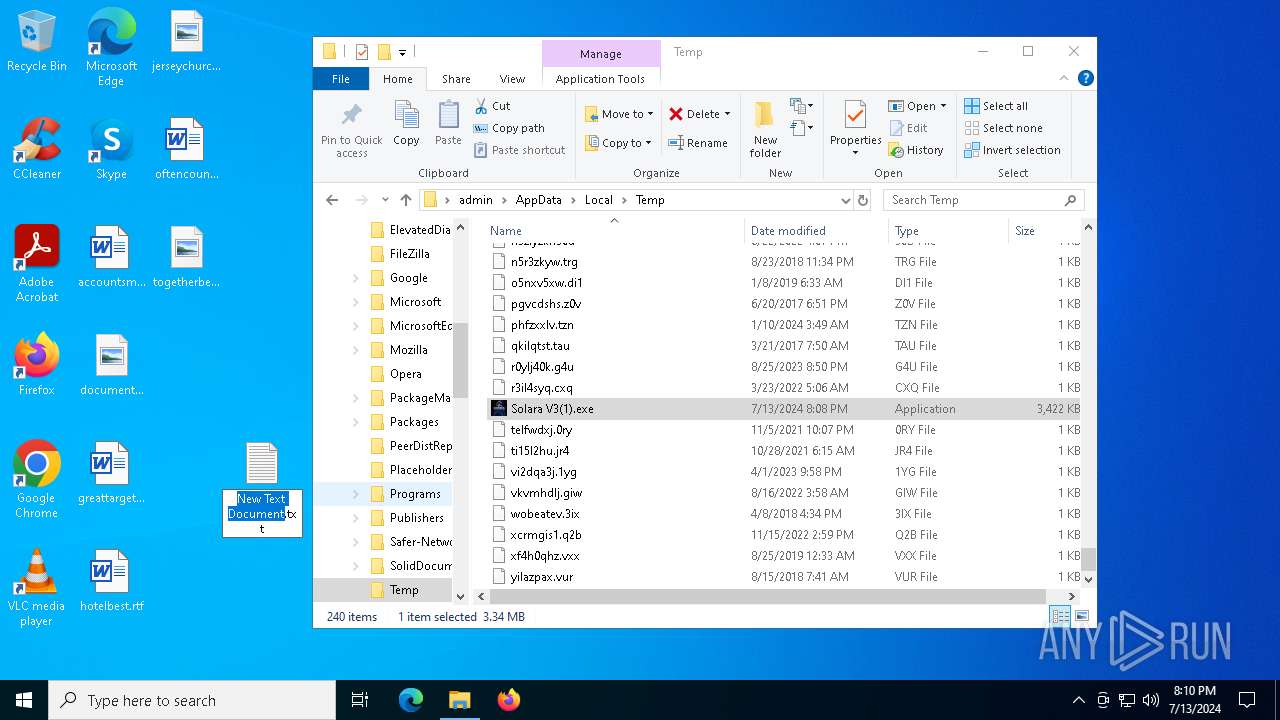
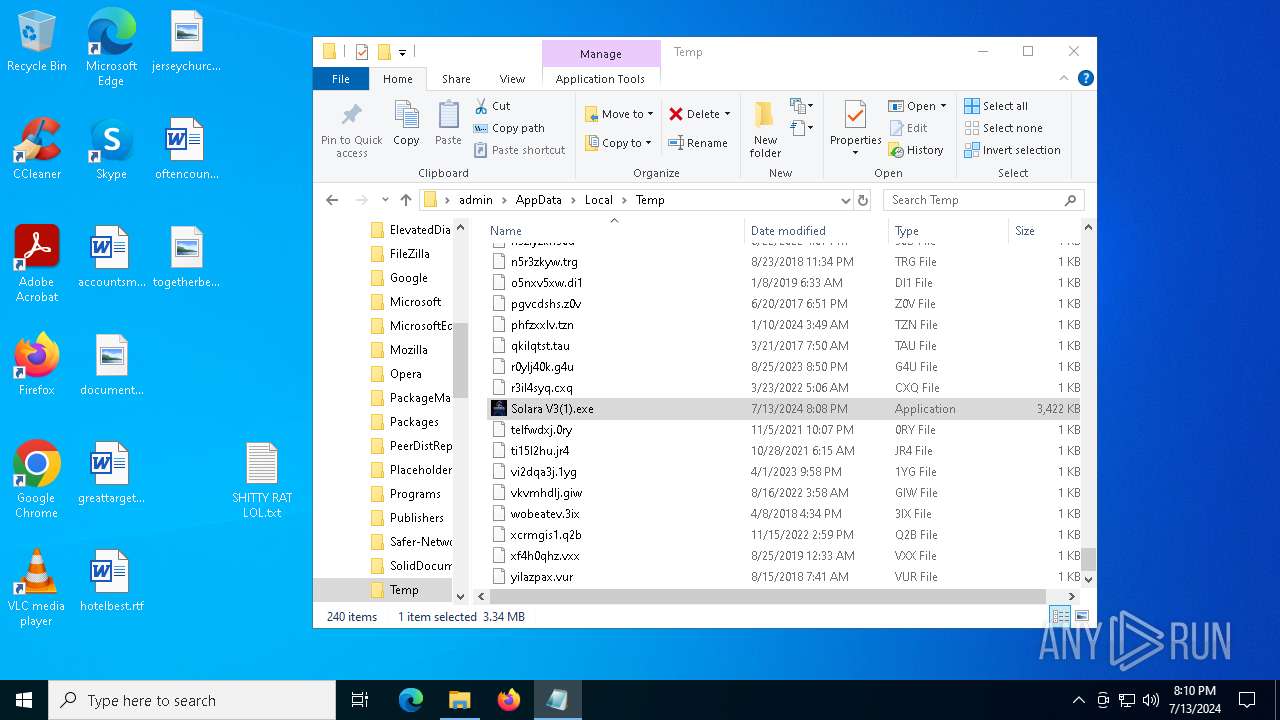
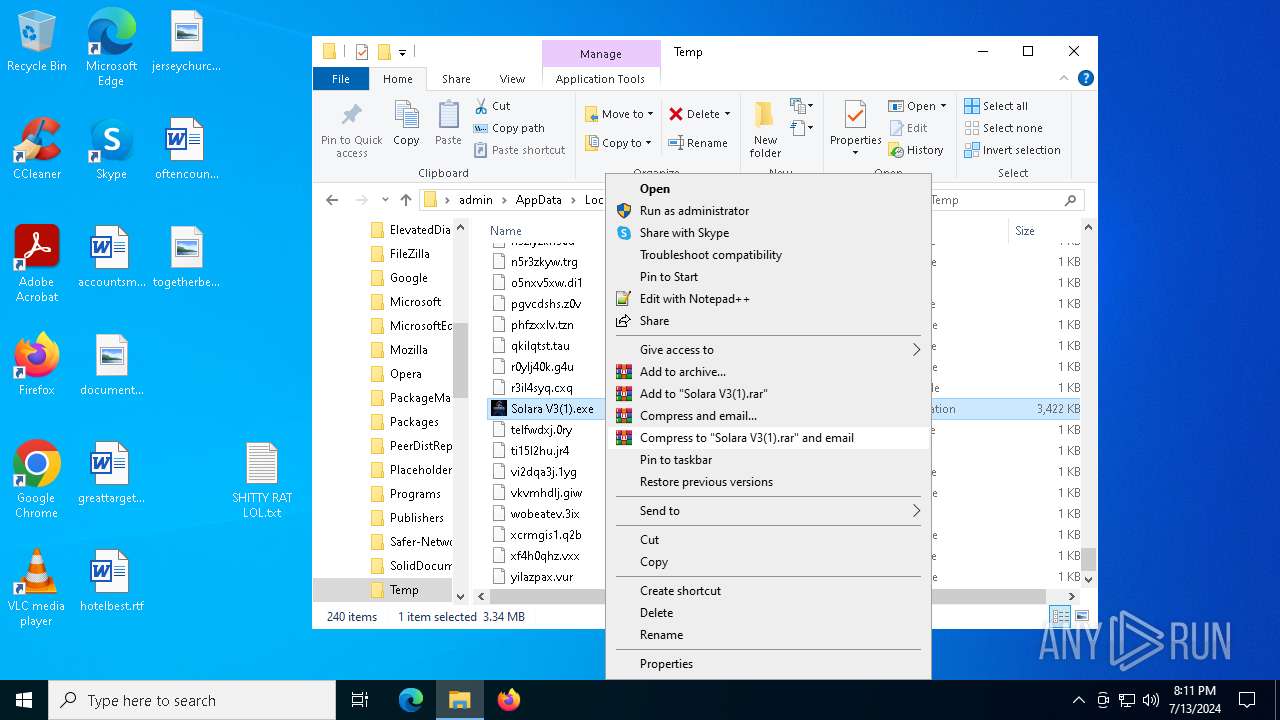
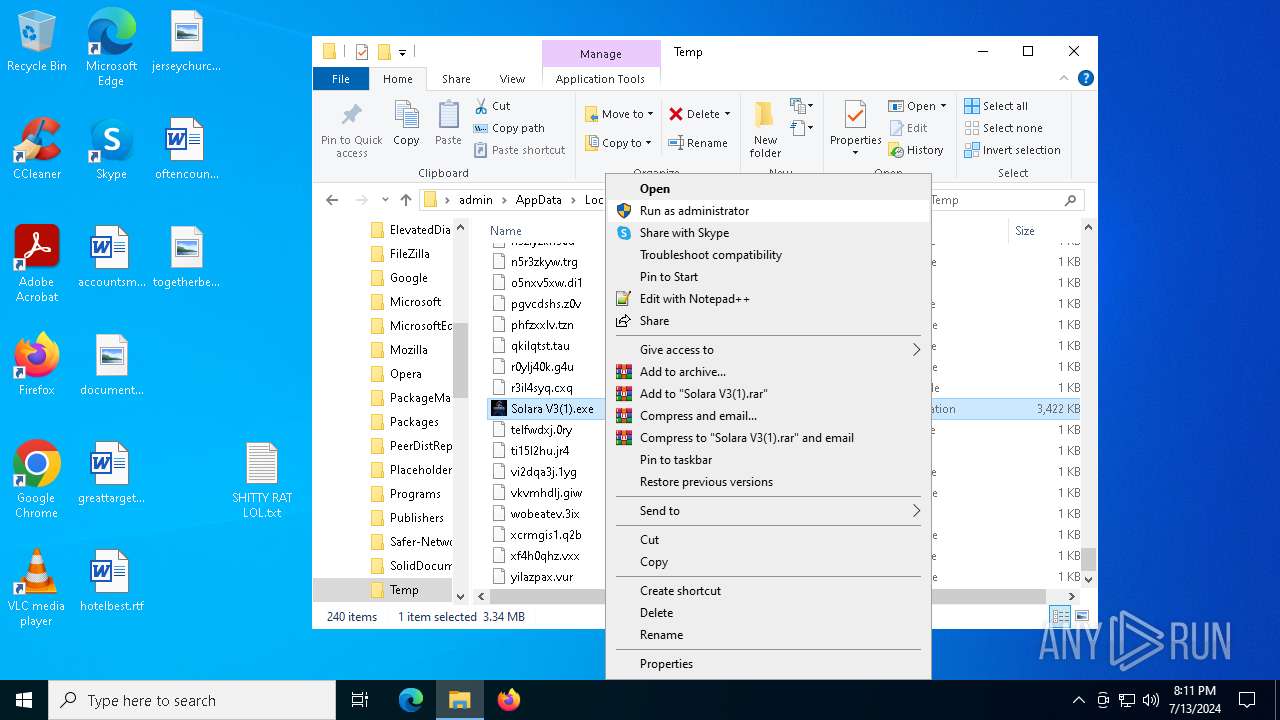
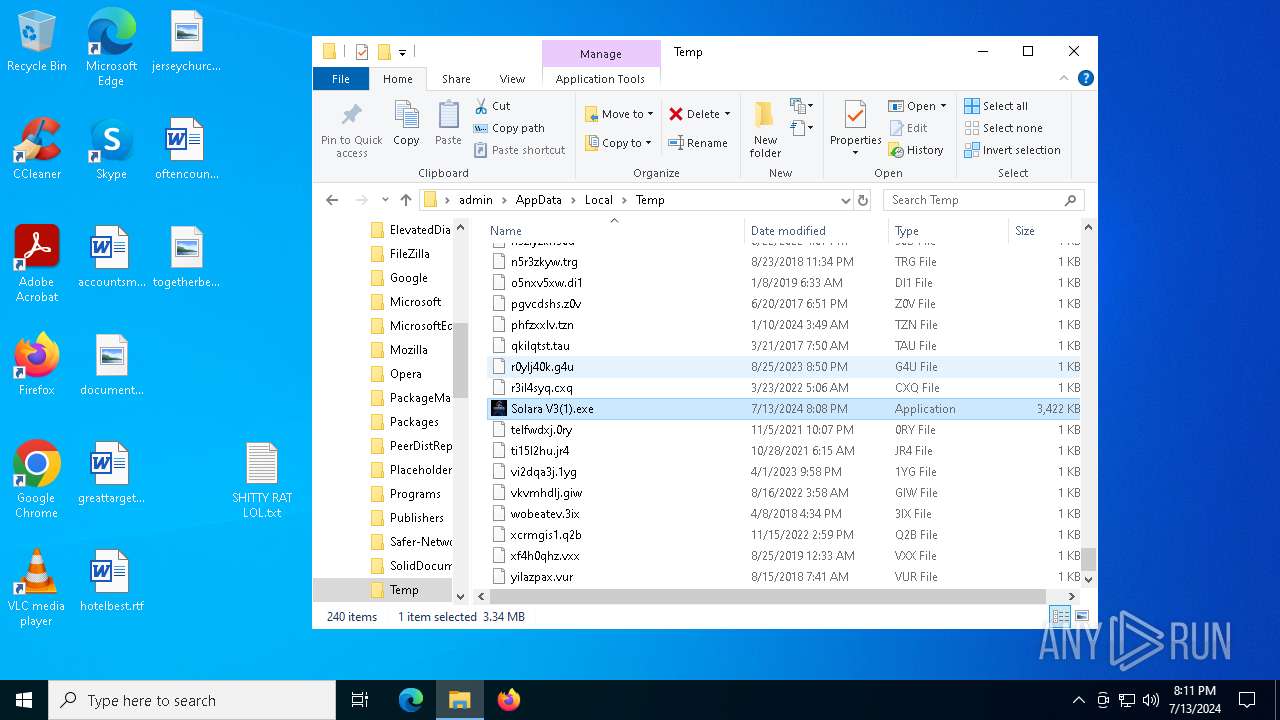
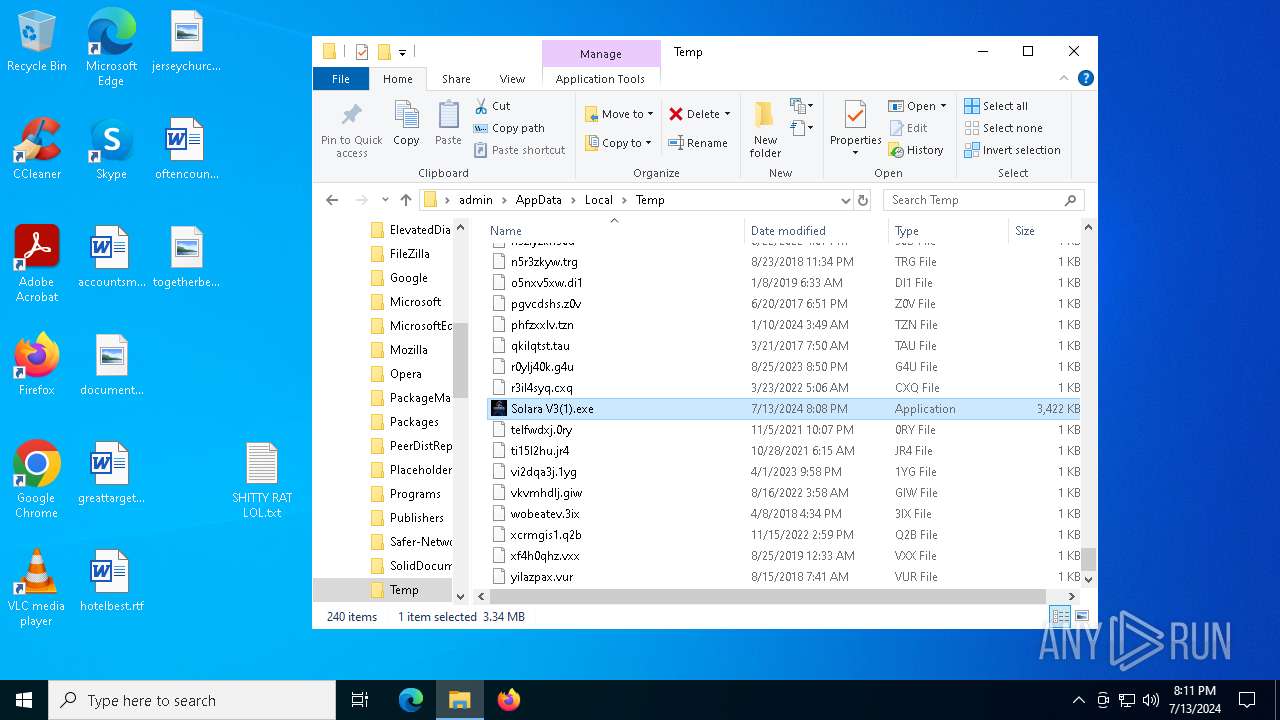
Drops the executable file immediately after the start
- Solara V3(1).exe (PID: 4452)
Changes the autorun value in the registry
- Solara V3.exe (PID: 2968)
- Solara V3(1).exe (PID: 4452)
QUASAR has been detected (YARA)
- Solara V3.exe (PID: 2968)
SUSPICIOUS
Starts itself from another location
- Solara V3(1).exe (PID: 4452)
Executable content was dropped or overwritten
- Solara V3(1).exe (PID: 4452)
Connects to unusual port
- Solara V3.exe (PID: 2968)
INFO
Checks supported languages
- Solara V3.exe (PID: 2968)
- Solara V3(1).exe (PID: 4452)
- Solara V3(1).exe (PID: 6264)
- Solara V3(1).exe (PID: 6224)
- Solara V3(1).exe (PID: 6348)
- Solara V3(1).exe (PID: 4772)
- Solara V3(1).exe (PID: 3660)
- Solara V3(1).exe (PID: 8)
- Solara V3(1).exe (PID: 6740)
- Solara V3(1).exe (PID: 6672)
- Solara V3(1).exe (PID: 6368)
- Solara V3(1).exe (PID: 6420)
- Solara V3(1).exe (PID: 6072)
- Solara V3(1).exe (PID: 6888)
- Solara V3(1).exe (PID: 4152)
Reads the machine GUID from the registry
- Solara V3(1).exe (PID: 4452)
- Solara V3.exe (PID: 2968)
- Solara V3(1).exe (PID: 6264)
- Solara V3(1).exe (PID: 6224)
- Solara V3(1).exe (PID: 6348)
- Solara V3(1).exe (PID: 3660)
- Solara V3(1).exe (PID: 6740)
- Solara V3(1).exe (PID: 4772)
- Solara V3(1).exe (PID: 6072)
- Solara V3(1).exe (PID: 6368)
- Solara V3(1).exe (PID: 8)
- Solara V3(1).exe (PID: 6672)
- Solara V3(1).exe (PID: 6420)
- Solara V3(1).exe (PID: 6888)
- Solara V3(1).exe (PID: 4152)
Reads the computer name
- Solara V3.exe (PID: 2968)
- Solara V3(1).exe (PID: 4452)
- Solara V3(1).exe (PID: 6264)
- Solara V3(1).exe (PID: 6224)
- Solara V3(1).exe (PID: 6348)
- Solara V3(1).exe (PID: 3660)
- Solara V3(1).exe (PID: 6740)
- Solara V3(1).exe (PID: 8)
- Solara V3(1).exe (PID: 4772)
- Solara V3(1).exe (PID: 6072)
- Solara V3(1).exe (PID: 6672)
- Solara V3(1).exe (PID: 6368)
- Solara V3(1).exe (PID: 6888)
- Solara V3(1).exe (PID: 6420)
- Solara V3(1).exe (PID: 4152)
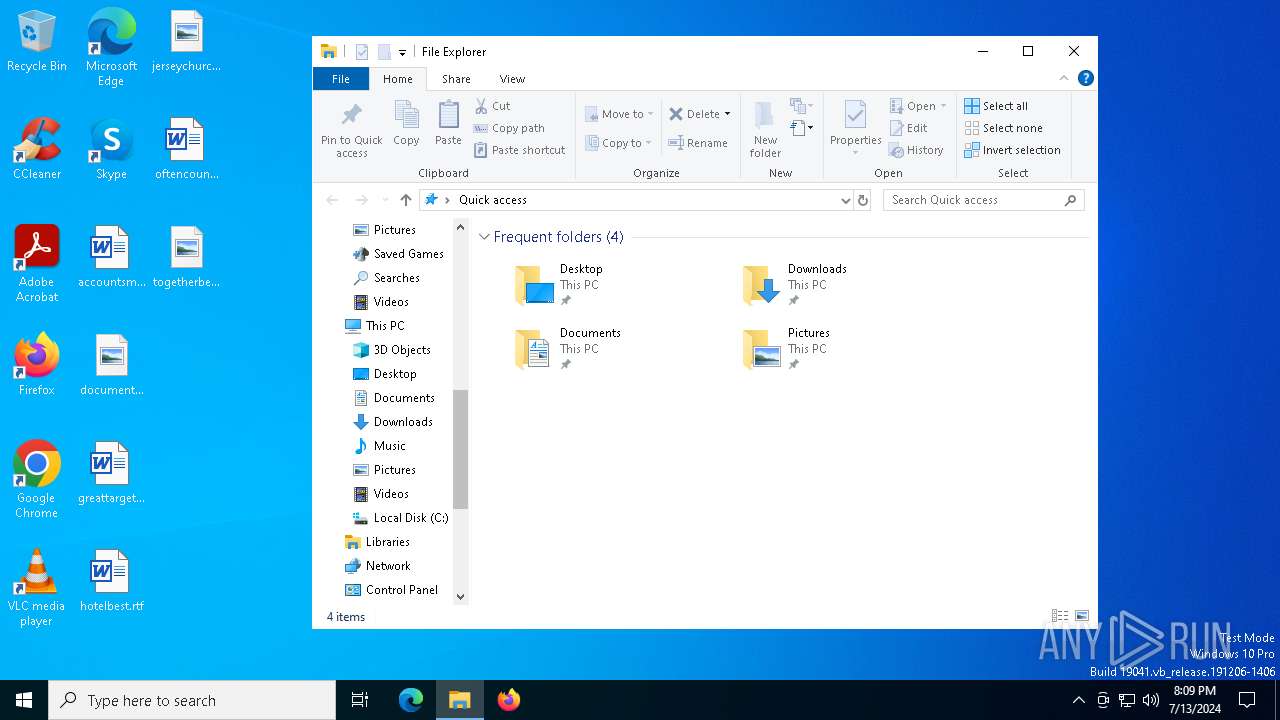
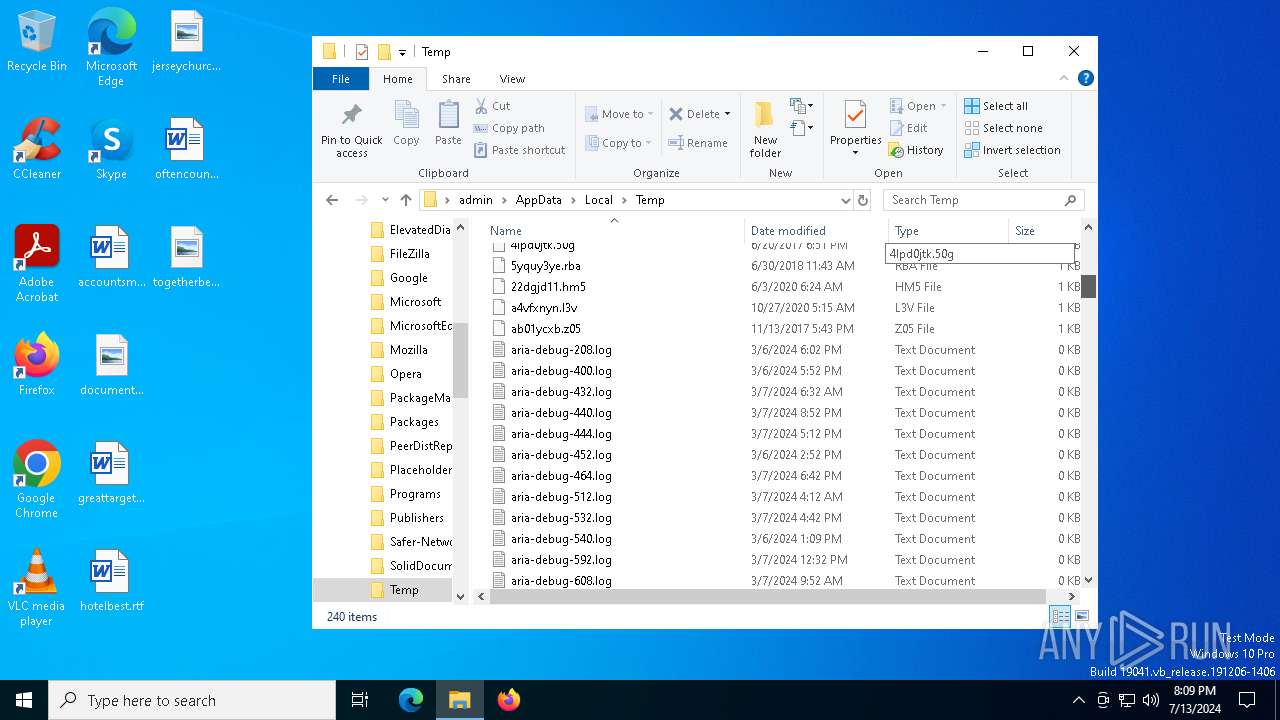
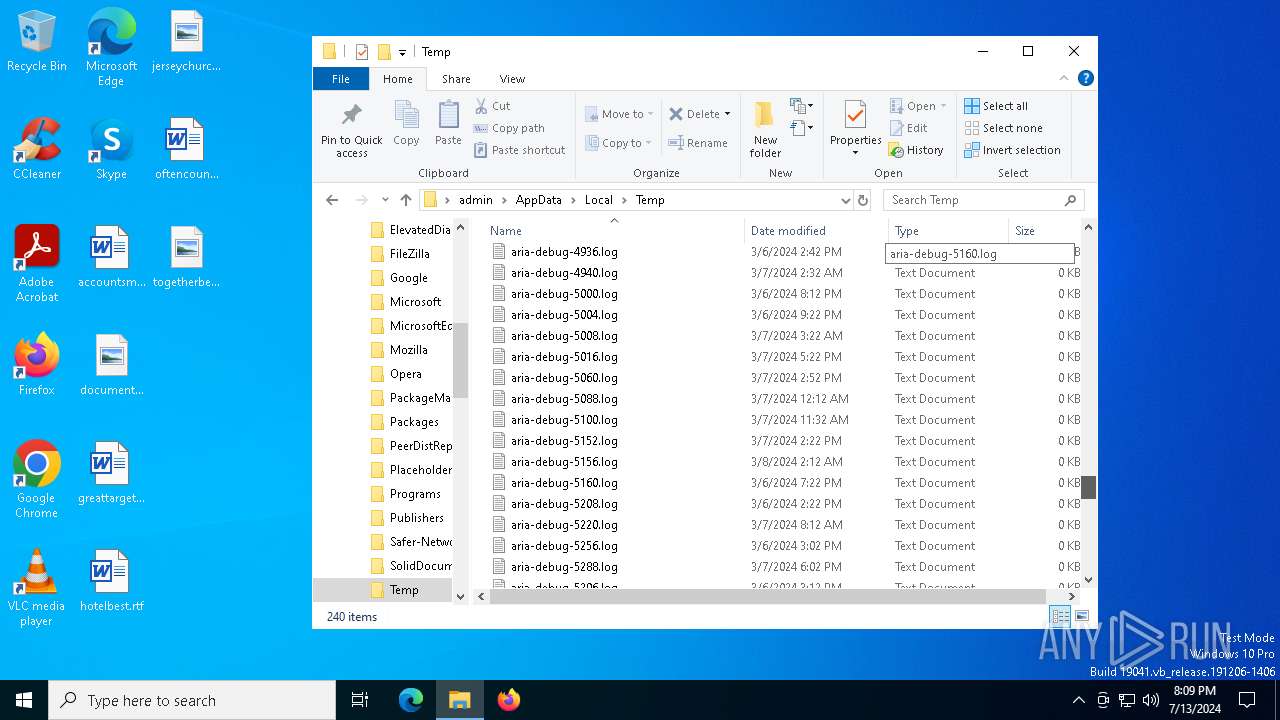
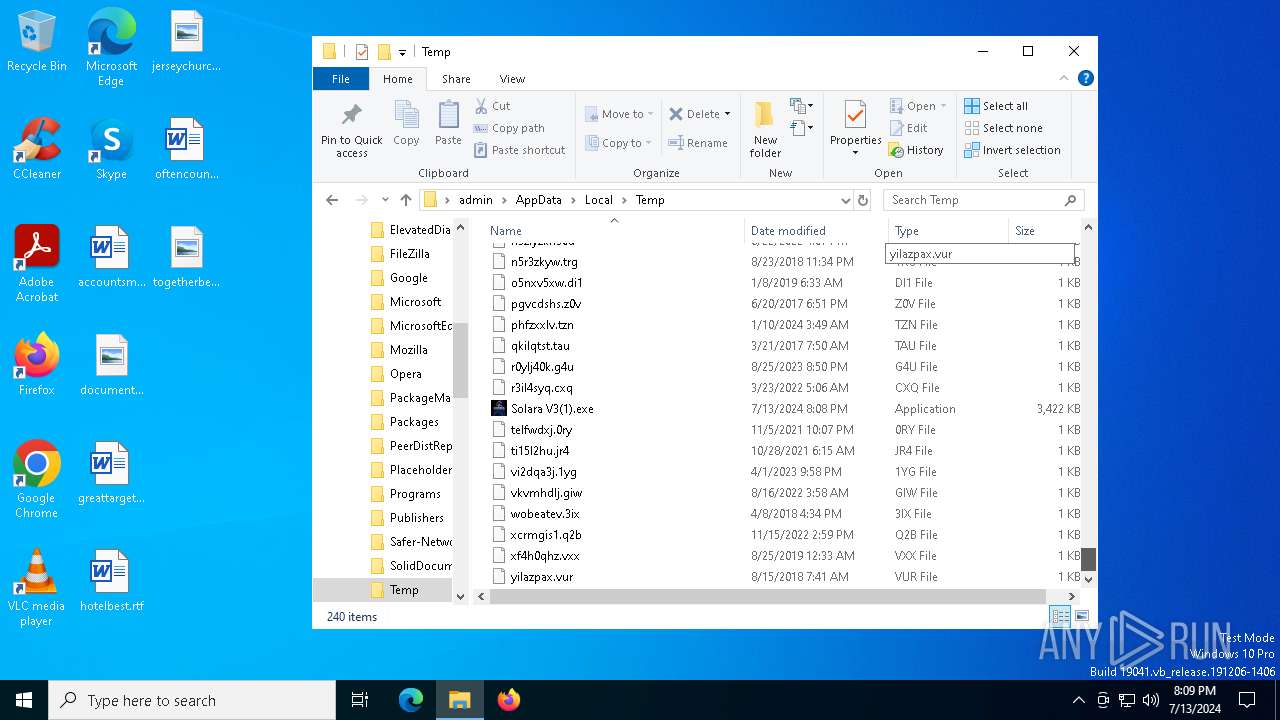
Creates files or folders in the user directory
- Solara V3(1).exe (PID: 4452)
- Solara V3.exe (PID: 2968)
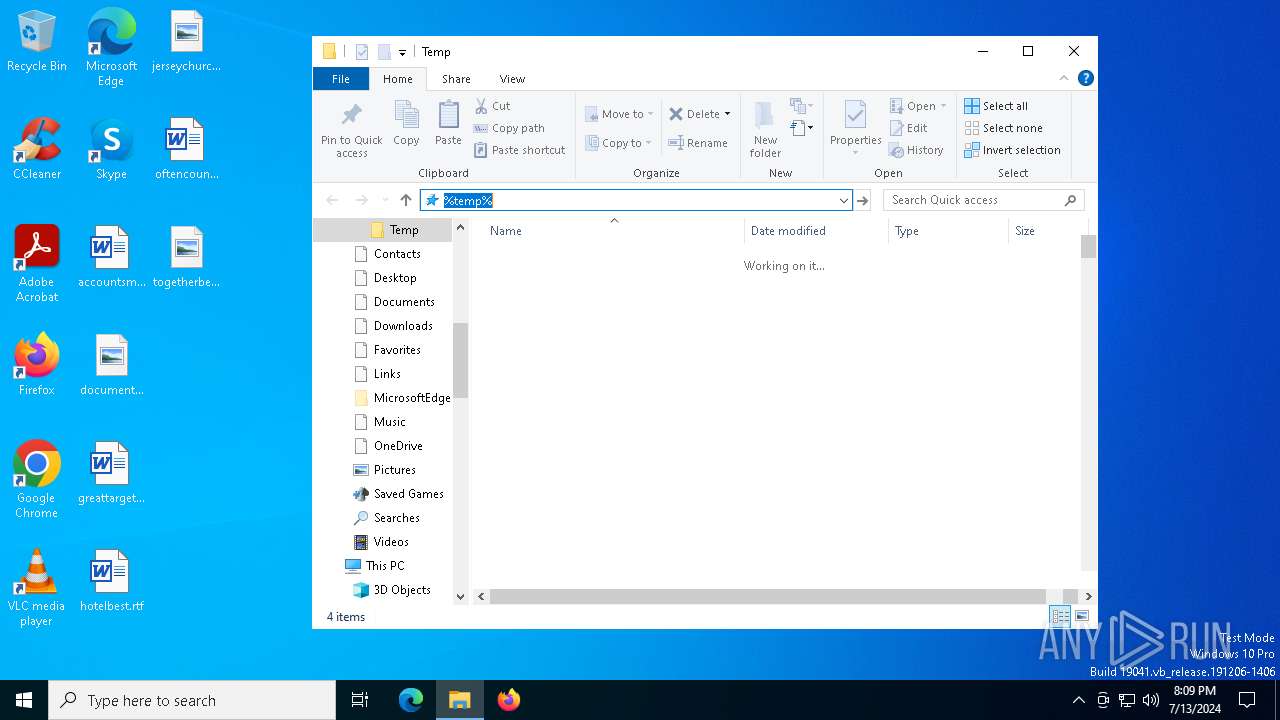
Reads Environment values
- Solara V3(1).exe (PID: 4452)
- Solara V3.exe (PID: 2968)
- Solara V3(1).exe (PID: 6264)
- Solara V3(1).exe (PID: 6348)
- Solara V3(1).exe (PID: 6224)
- Solara V3(1).exe (PID: 3660)
- Solara V3(1).exe (PID: 6740)
- Solara V3(1).exe (PID: 8)
- Solara V3(1).exe (PID: 4772)
- Solara V3(1).exe (PID: 6072)
- Solara V3(1).exe (PID: 6672)
- Solara V3(1).exe (PID: 6368)
- Solara V3(1).exe (PID: 6420)
- Solara V3(1).exe (PID: 6888)
- Solara V3(1).exe (PID: 4152)
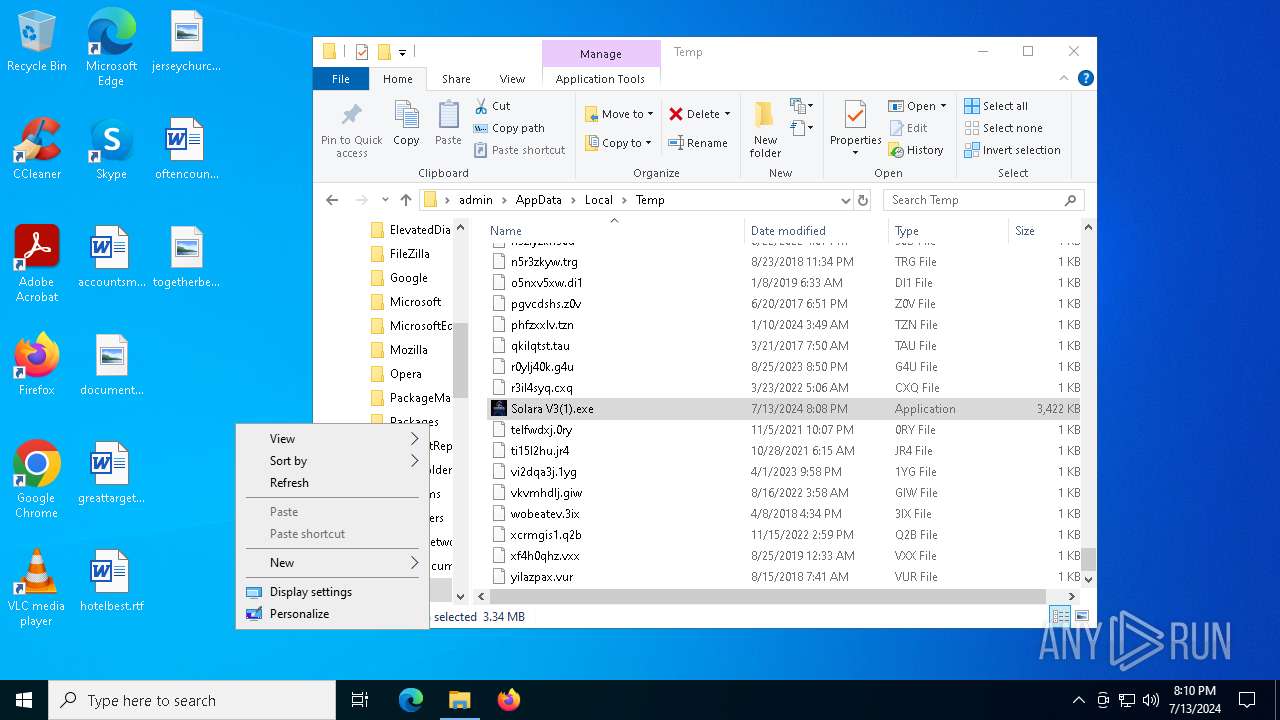
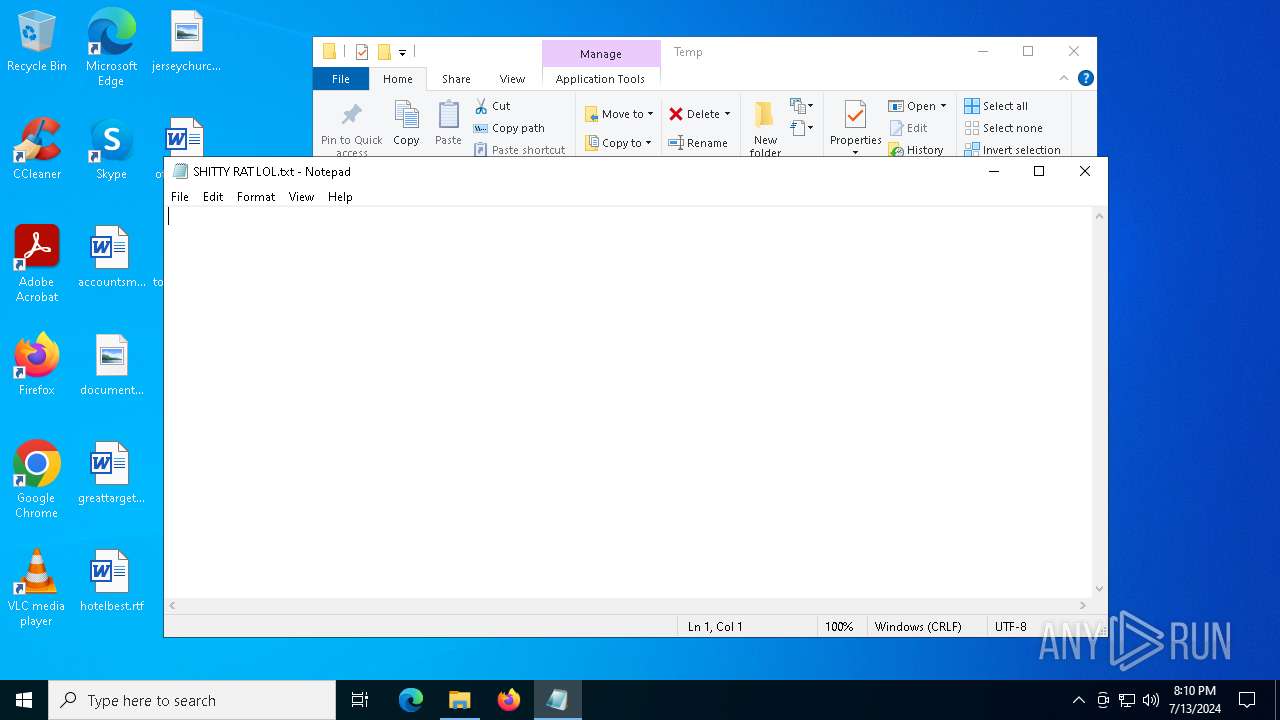
Manual execution by a user
- Solara V3(1).exe (PID: 6264)
- Solara V3(1).exe (PID: 6224)
- Solara V3(1).exe (PID: 6348)
- Solara V3(1).exe (PID: 4772)
- notepad.exe (PID: 5608)
- Solara V3(1).exe (PID: 6740)
- Solara V3(1).exe (PID: 3660)
- Solara V3(1).exe (PID: 8)
- Solara V3(1).exe (PID: 6672)
- Solara V3(1).exe (PID: 6072)
- Solara V3(1).exe (PID: 6420)
- Solara V3(1).exe (PID: 6888)
- Solara V3(1).exe (PID: 4152)
- Solara V3(1).exe (PID: 6368)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(2968) Solara V3.exe
Version1.4.1
C2 (2)thssdxf6y74-54495.portmap.host:54495
Sub_DirSubDir
Install_NameSolara V3.exe
Mutexb5404b50-f626-49b9-8b08-b7ac4b28d57b
StartupJava Updater
TagSolara
LogDirLogs
SignatureAv30iSH3J2ZgGzKE3ZvGfvtalcEUNyJT6Hrqn0mr7xxnz9QYryu3CtAEuJyBefTDqvjb7df7KzehytNW7SF/9Q6DmrHtbr7gIot2f3d7qPv+q3EeQFbGY49okO3ZZ7C4Uf+DaKj8TVSE4uVj1o4s7ftM8XE93JH/vEdzdhETx31sbQ8jCjPQF+AYCDotcTcNKTsxdL6wP/Z3gA7YOay30j6H8Su/WladqchMjm57e7eRYH2xuseYBbKML0joKqKJZ2KpwNYpG0i4+VtM4jDPVEfWTRuNiN+qQF9eQaBitNgl...
CertificateMIIE9DCCAtygAwIBAgIQANYw69ByThfmqNxppDSuyTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDcxMTEzMTA1OVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAwFp01JT4SGsHyUtU6cdyfN6TYy5R8zJ1r0JXDFblftiGKm+167g0Gy7JFznAUT5K9XDfwZ2U...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 16:16:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261440 |
| InitializedDataSize: | 241664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e3ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Quasar Client |
| FileVersion: | 1.4.1 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © MaxXor 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Quasar |
| ProductVersion: | 1.4.1 |
| AssemblyVersion: | 1.4.1.0 |
Total processes
146
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Roaming\SubDir\Solara V3.exe" | C:\Users\admin\AppData\Roaming\SubDir\Solara V3.exe | Solara V3(1).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Version: 1.4.1 Modules
Quasar(PID) Process(2968) Solara V3.exe Version1.4.1 C2 (2)thssdxf6y74-54495.portmap.host:54495 Sub_DirSubDir Install_NameSolara V3.exe Mutexb5404b50-f626-49b9-8b08-b7ac4b28d57b StartupJava Updater TagSolara LogDirLogs SignatureAv30iSH3J2ZgGzKE3ZvGfvtalcEUNyJT6Hrqn0mr7xxnz9QYryu3CtAEuJyBefTDqvjb7df7KzehytNW7SF/9Q6DmrHtbr7gIot2f3d7qPv+q3EeQFbGY49okO3ZZ7C4Uf+DaKj8TVSE4uVj1o4s7ftM8XE93JH/vEdzdhETx31sbQ8jCjPQF+AYCDotcTcNKTsxdL6wP/Z3gA7YOay30j6H8Su/WladqchMjm57e7eRYH2xuseYBbKML0joKqKJZ2KpwNYpG0i4+VtM4jDPVEfWTRuNiN+qQF9eQaBitNgl... CertificateMIIE9DCCAtygAwIBAgIQANYw69ByThfmqNxppDSuyTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDcxMTEzMTA1OVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAwFp01JT4SGsHyUtU6cdyfN6TYy5R8zJ1r0JXDFblftiGKm+167g0Gy7JFznAUT5K9XDfwZ2U... | |||||||||||||||
| 3660 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 4152 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 4452 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 3 Version: 1.4.1 Modules
| |||||||||||||||
| 4772 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 5608 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\SHITTY RAT LOL.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6072 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 6224 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 6264 | "C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe" | C:\Users\admin\AppData\Local\Temp\Solara V3(1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
Total events
5 504
Read events
5 502
Write events
2
Delete events
0
Modification events
| (PID) Process: | (4452) Solara V3(1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Java Updater |
Value: "C:\Users\admin\AppData\Roaming\SubDir\Solara V3.exe" | |||
| (PID) Process: | (2968) Solara V3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Java Updater |
Value: "C:\Users\admin\AppData\Roaming\SubDir\Solara V3.exe" | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4452 | Solara V3(1).exe | C:\Users\admin\AppData\Roaming\SubDir\Solara V3.exe | executable | |
MD5:8D584617F5A696152BBB7A2AF535807E | SHA256:EA12C9150D0D869D3038A9EB72D561FC568AD4F24867FA4E5B2360545F6B61F7 | |||
| 2968 | Solara V3.exe | C:\Users\admin\AppData\Roaming\Logs\2024-07-13 | binary | |
MD5:B49D1484F5C2804EE5BB5AE7C25F5B78 | SHA256:F6CA8FC0E74B08A0CCE56C1B2B4FB6616D2466E8F823965715C49FC61988F393 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
336
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4392 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4392 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2808 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3832 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1796 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6628 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6628 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2088 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1968 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4392 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4392 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4656 | SearchApp.exe | 104.126.37.129:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2808 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2808 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
thssdxf6y74-54495.portmap.host |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |
2168 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |