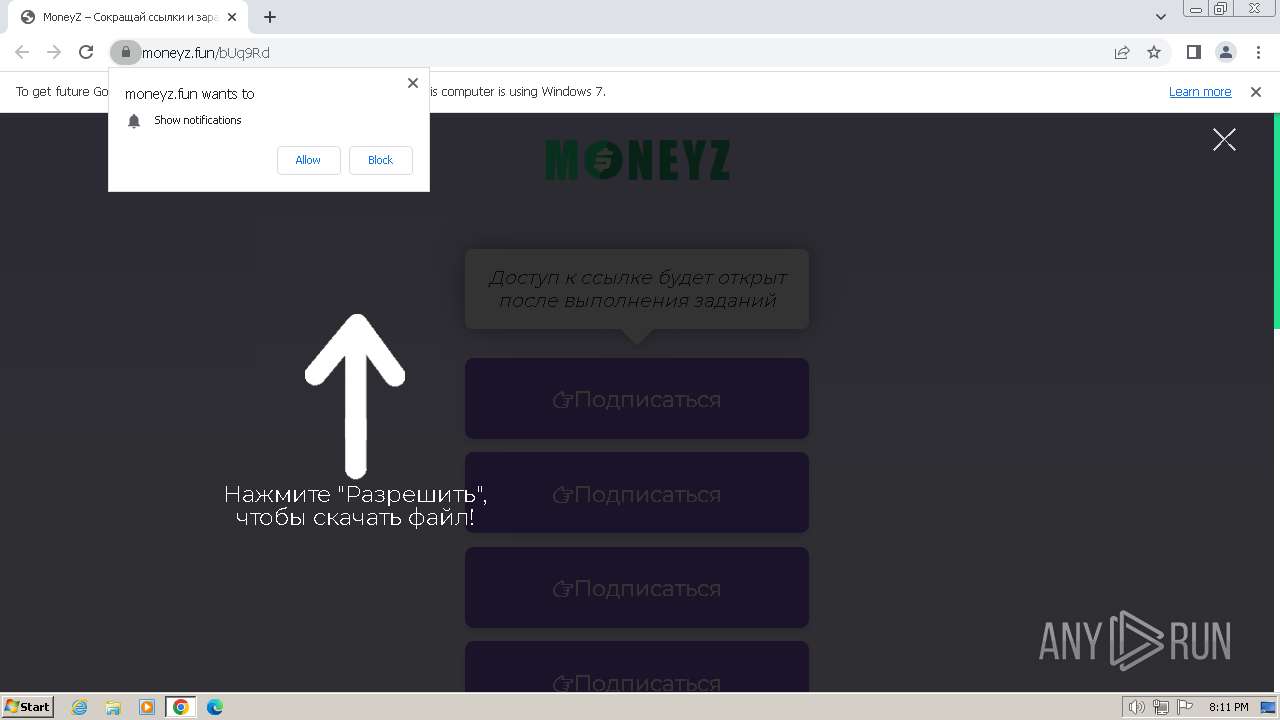
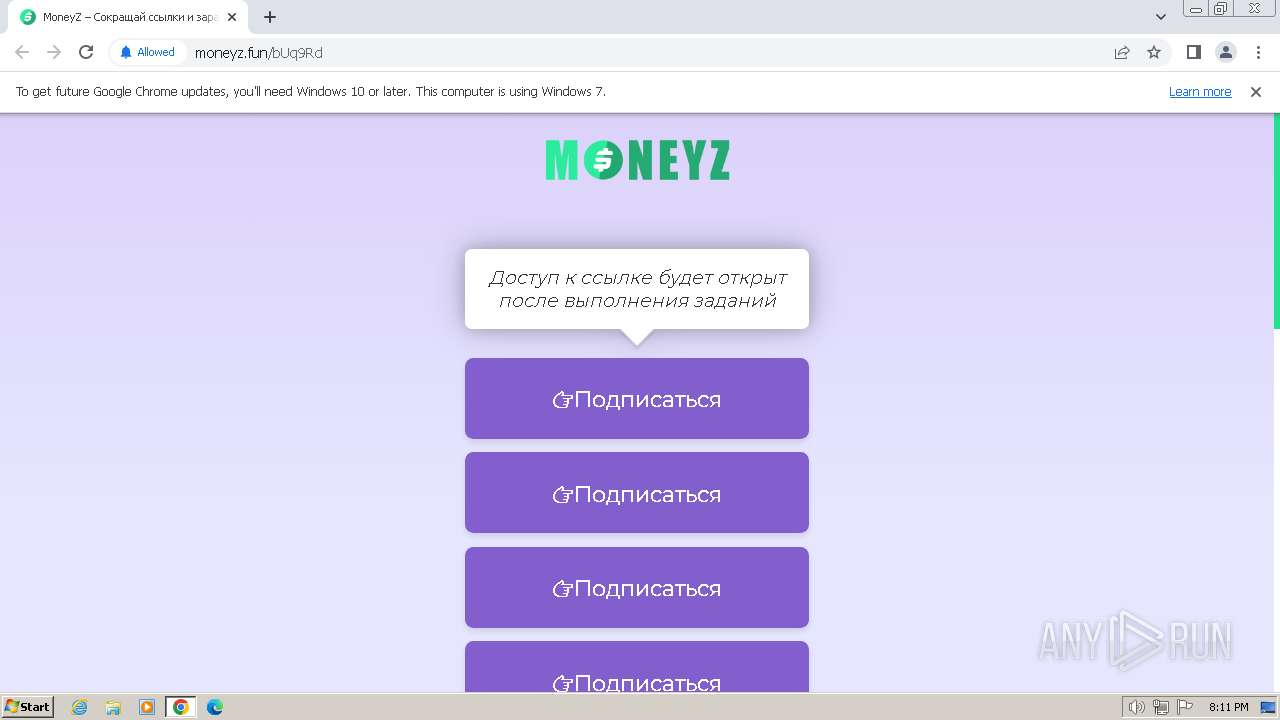
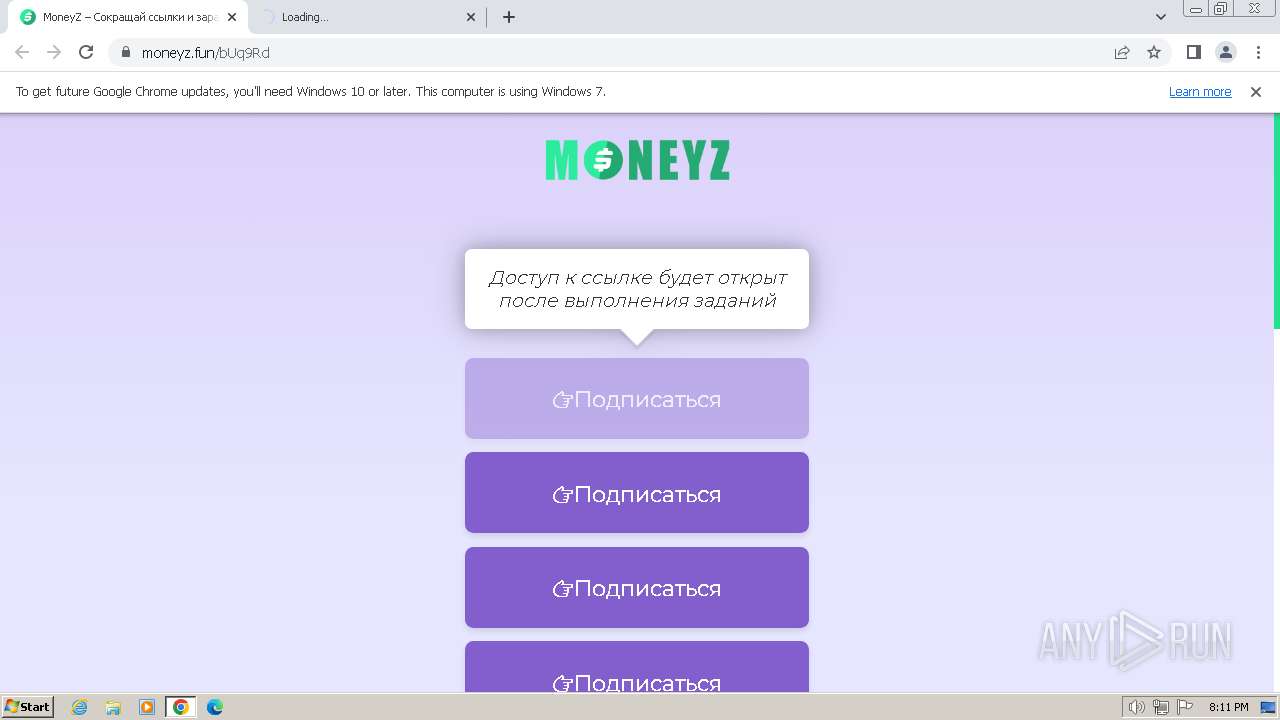
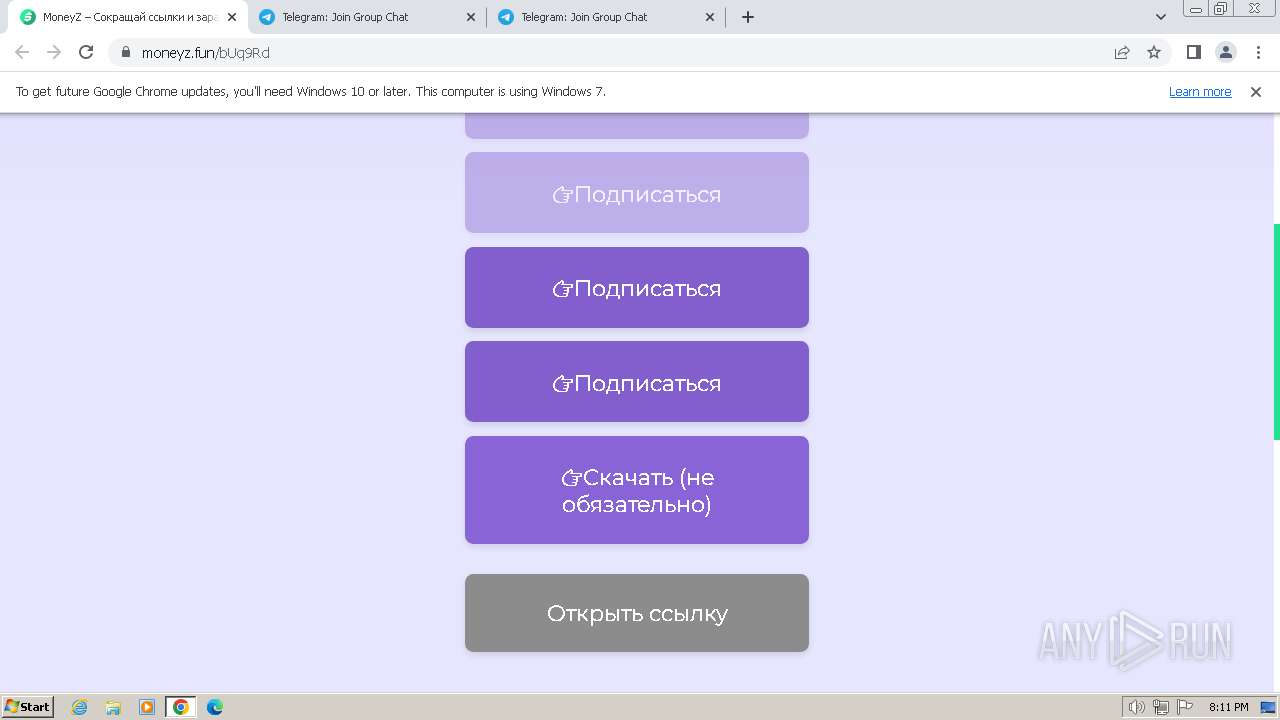
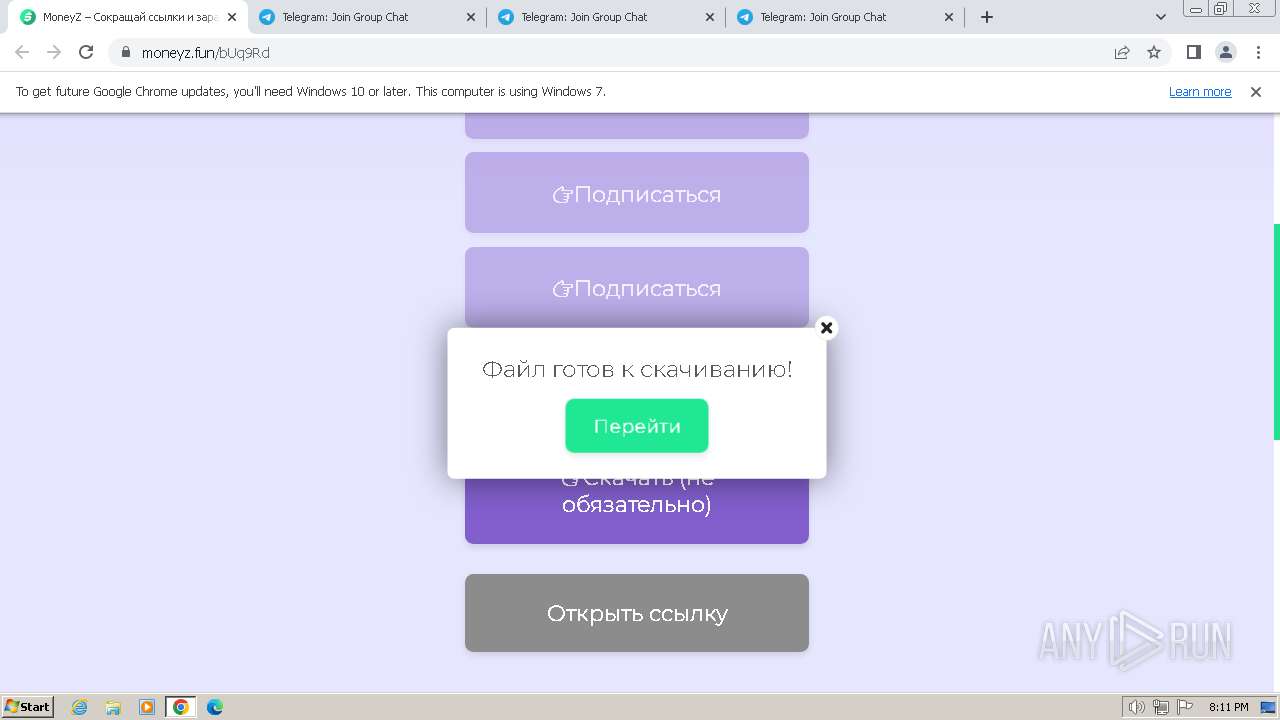
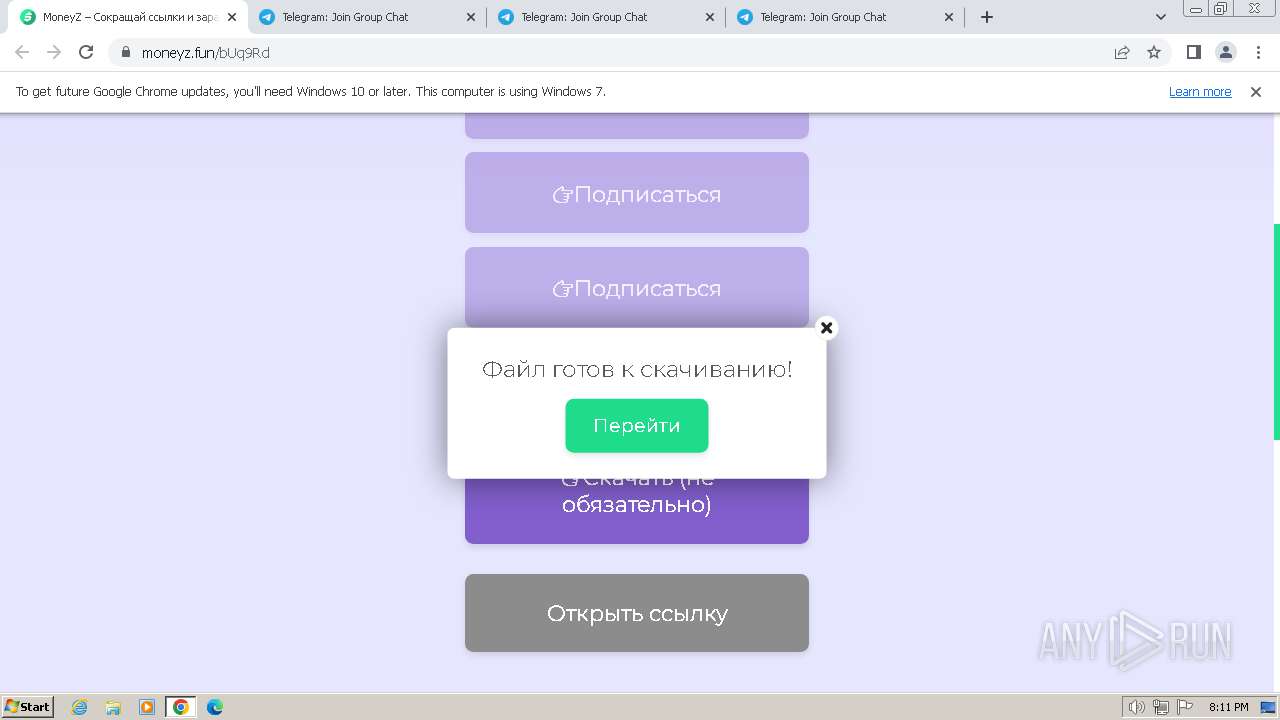
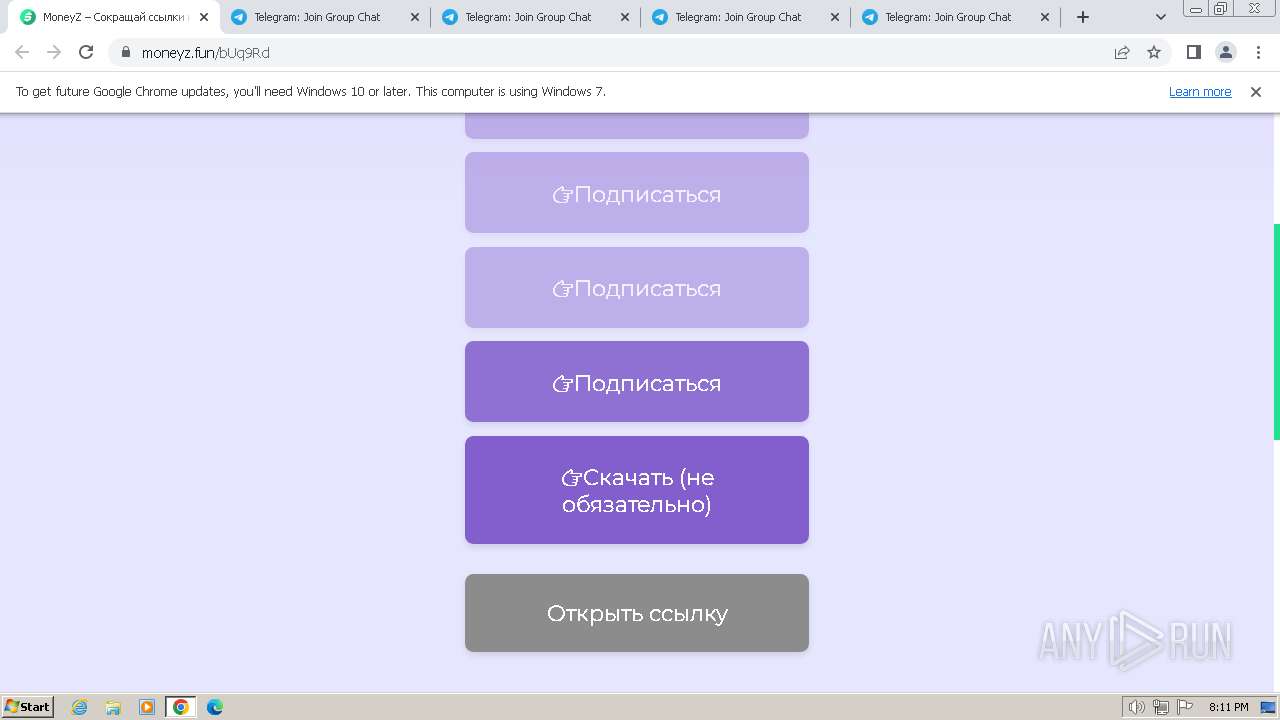
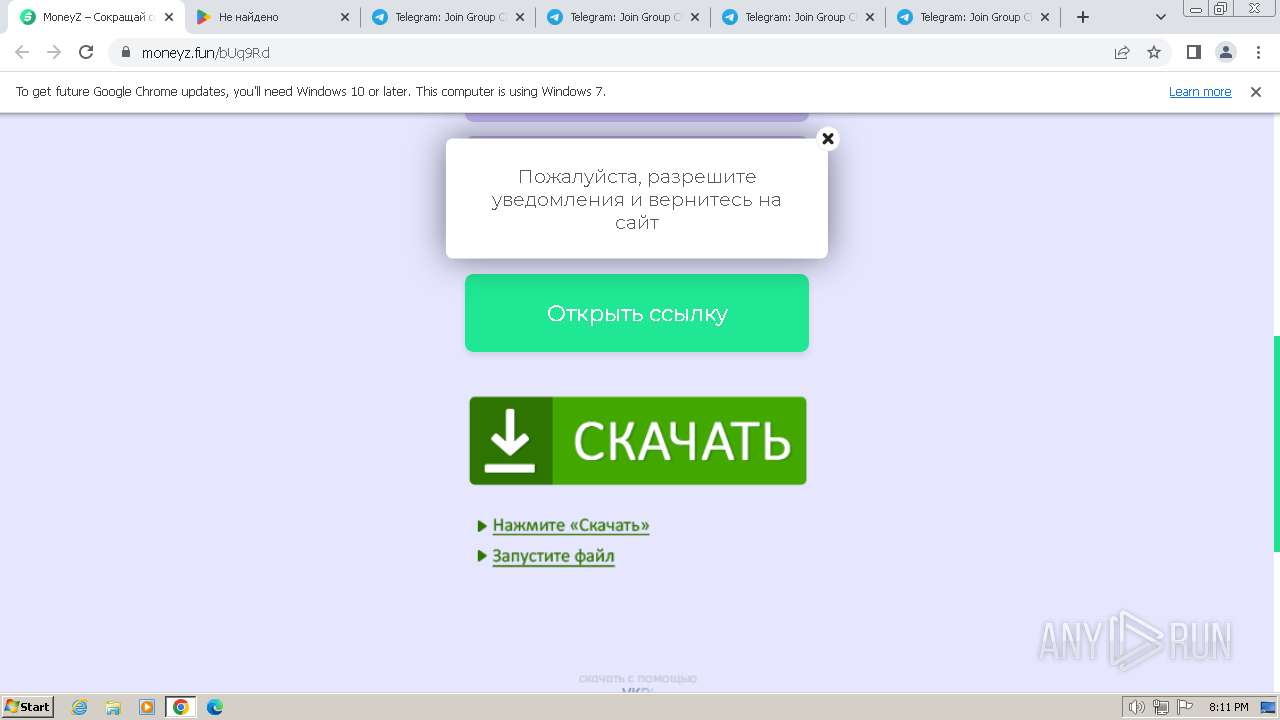
| URL: | https://moneyz.fun/bUq9Rd |
| Full analysis: | https://app.any.run/tasks/58f16c8f-2694-407a-bf24-fcf1658dfa20 |
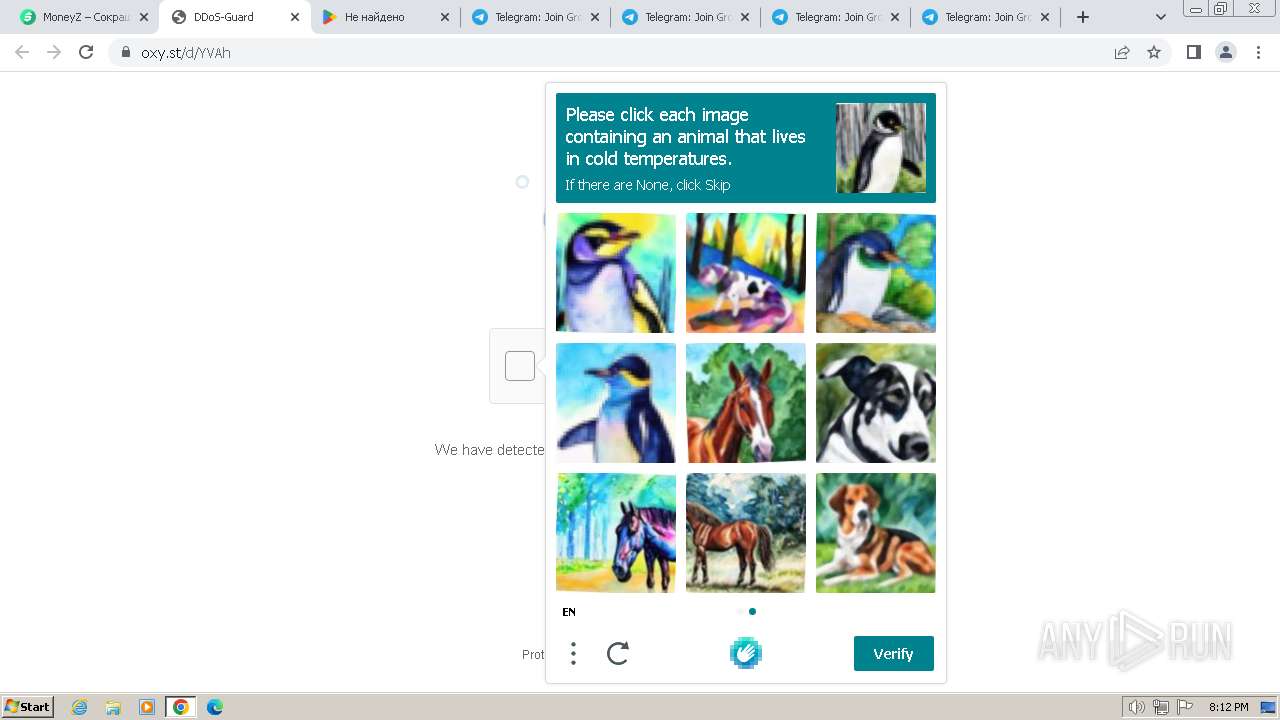
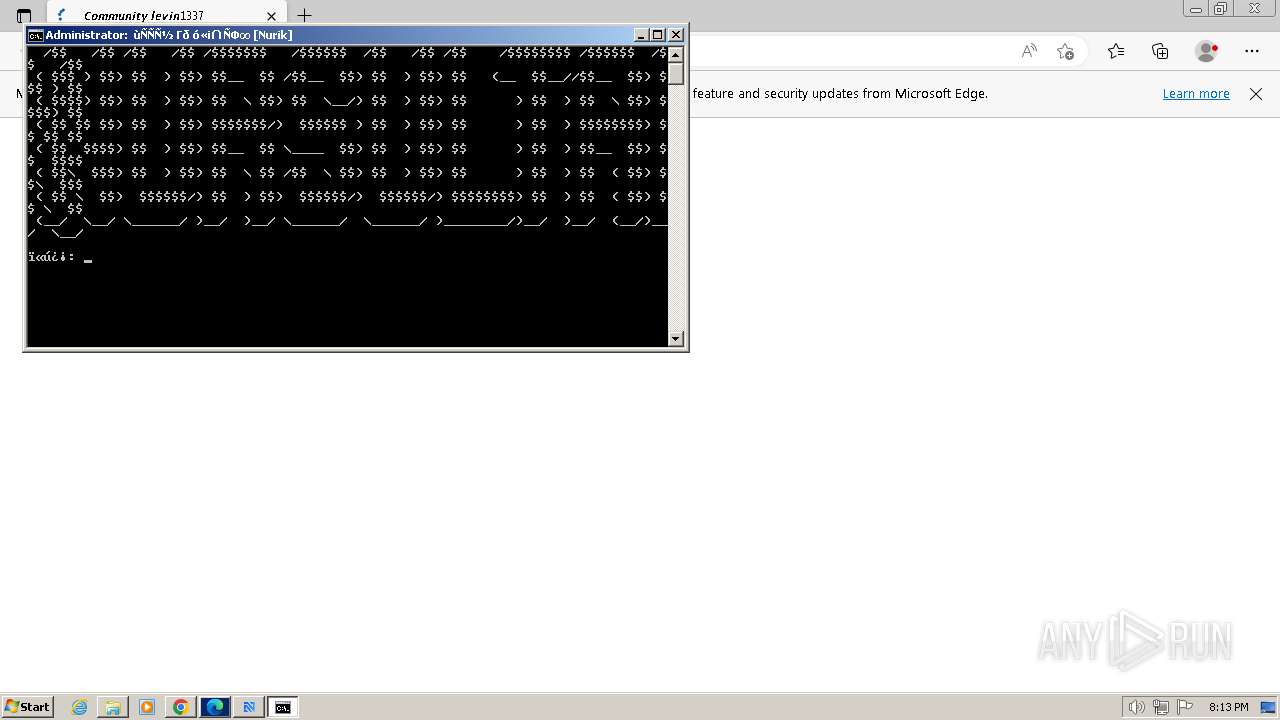
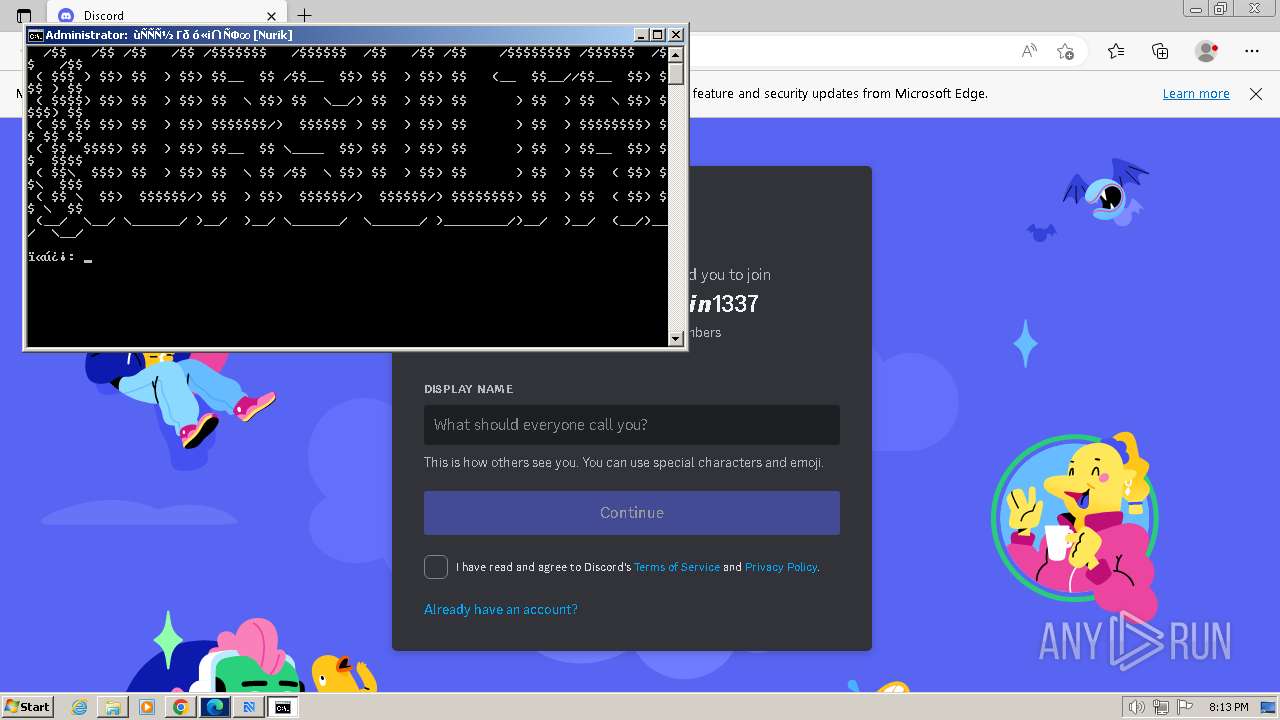
| Verdict: | Malicious activity |
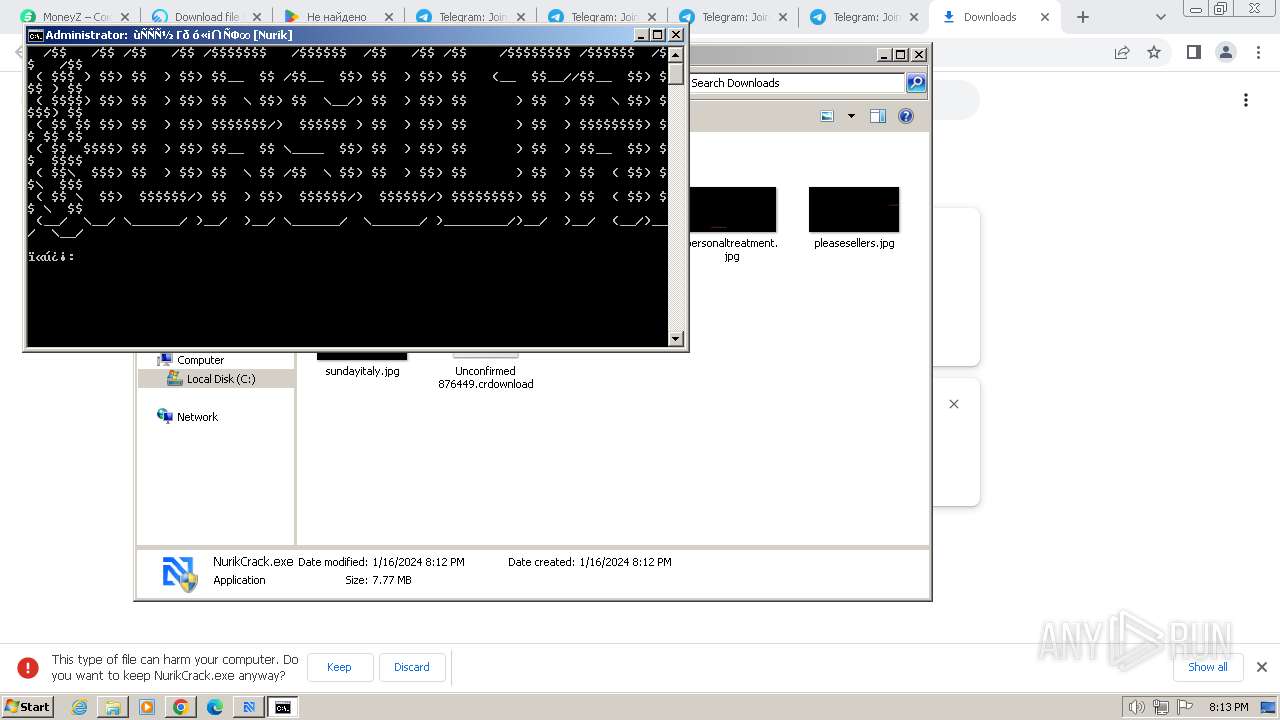
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | January 16, 2024, 20:11:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1928A96FE5DD7A53DD9974EB82B2AE58 |
| SHA1: | 920D6A91BE305DFEE6D17CEB594A1D5D5F3B02E8 |
| SHA256: | E9B6F9B6B7F14BB126B5436EE1DD9883606275B767DD36DED7613E22EBB4ED64 |
| SSDEEP: | 3:N8pGLKqxn:2xAn |
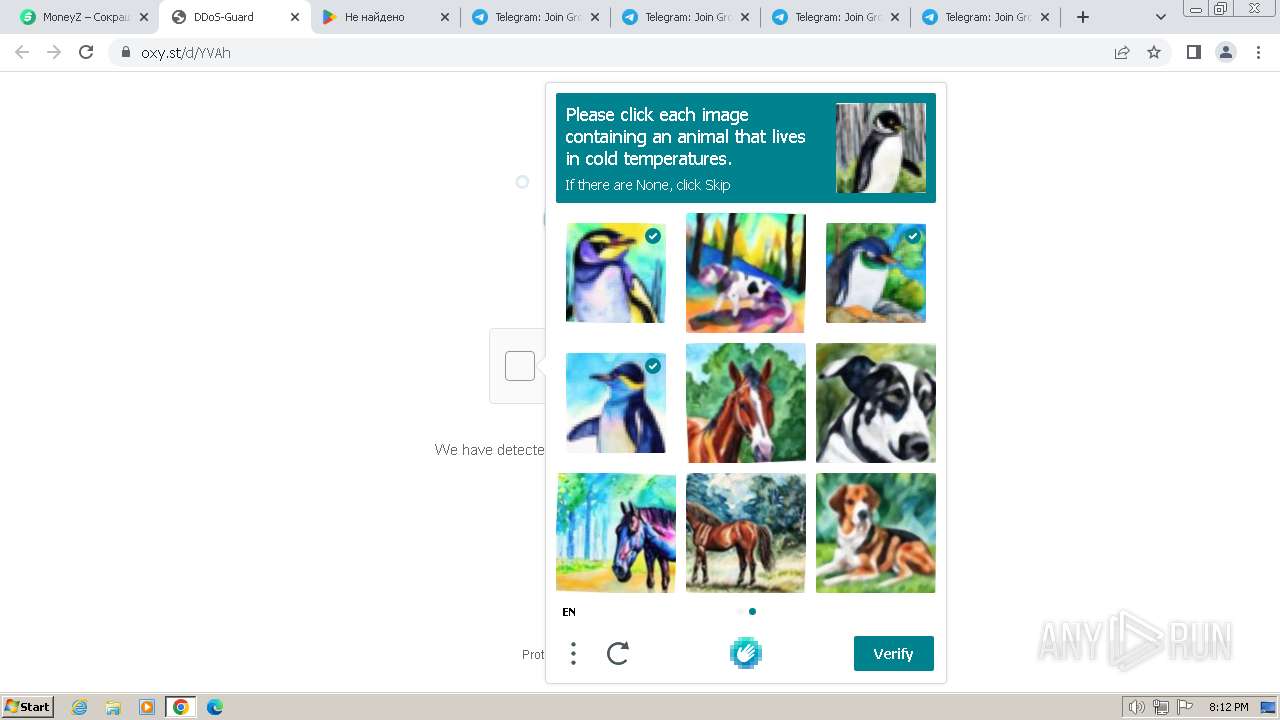
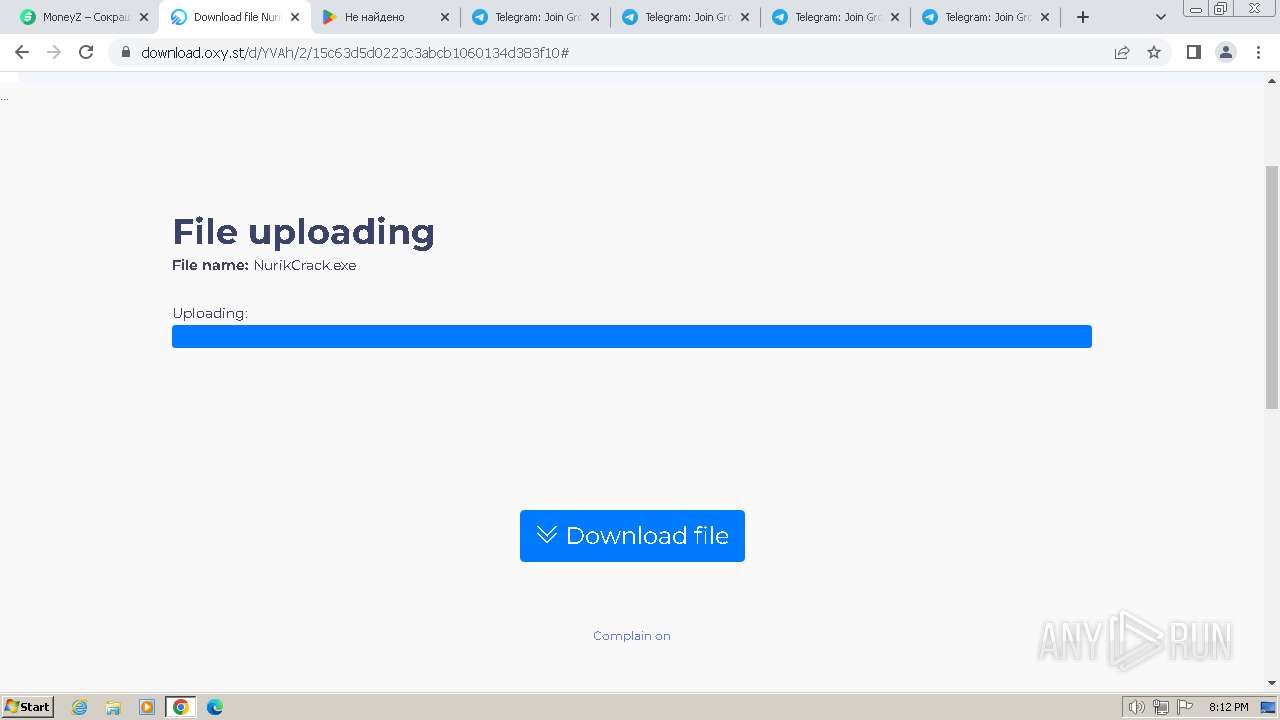
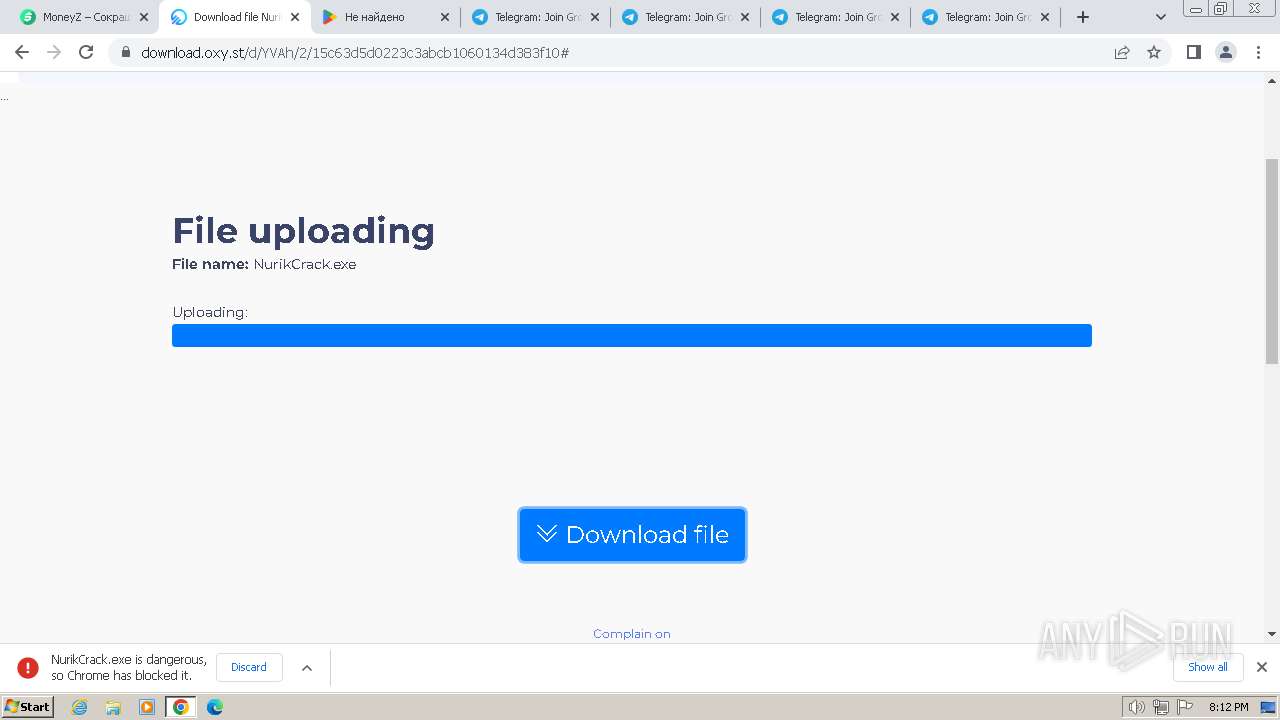
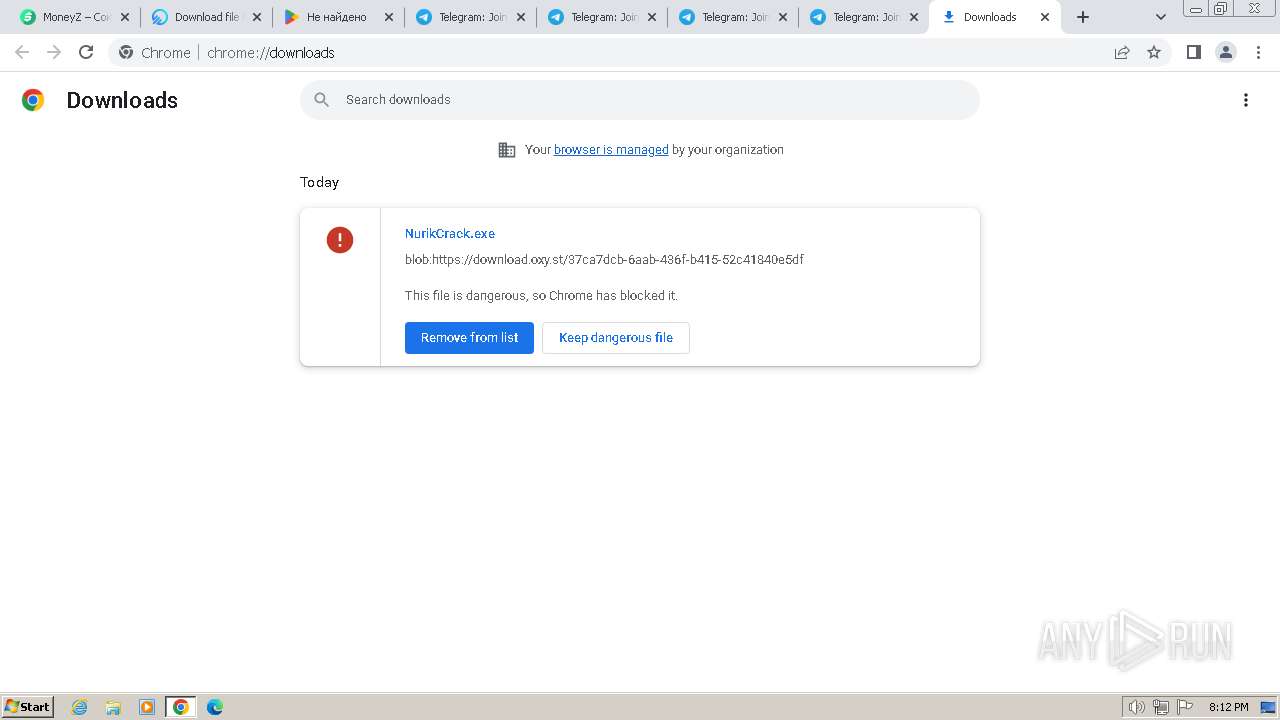
MALICIOUS
Actions looks like stealing of personal data
- cmd.exe (PID: 2792)
- Minecraft.exe (PID: 552)
- SearchIndexer.exe (PID: 3876)
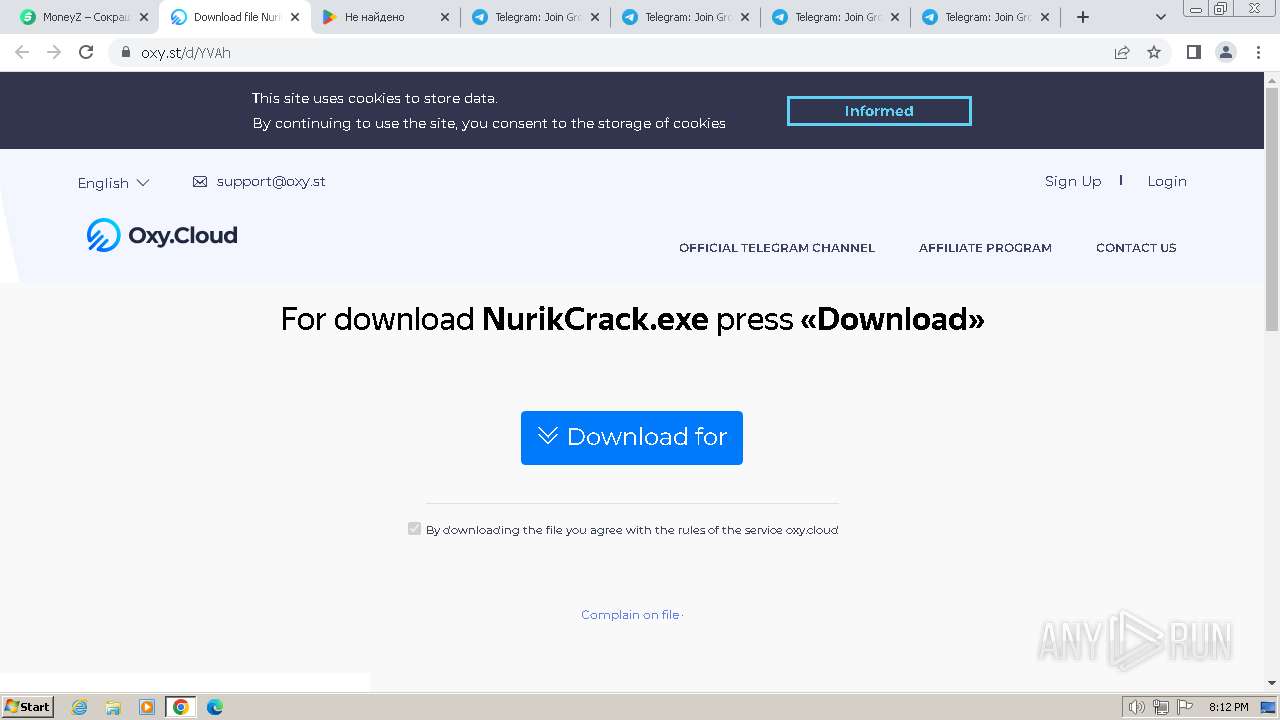
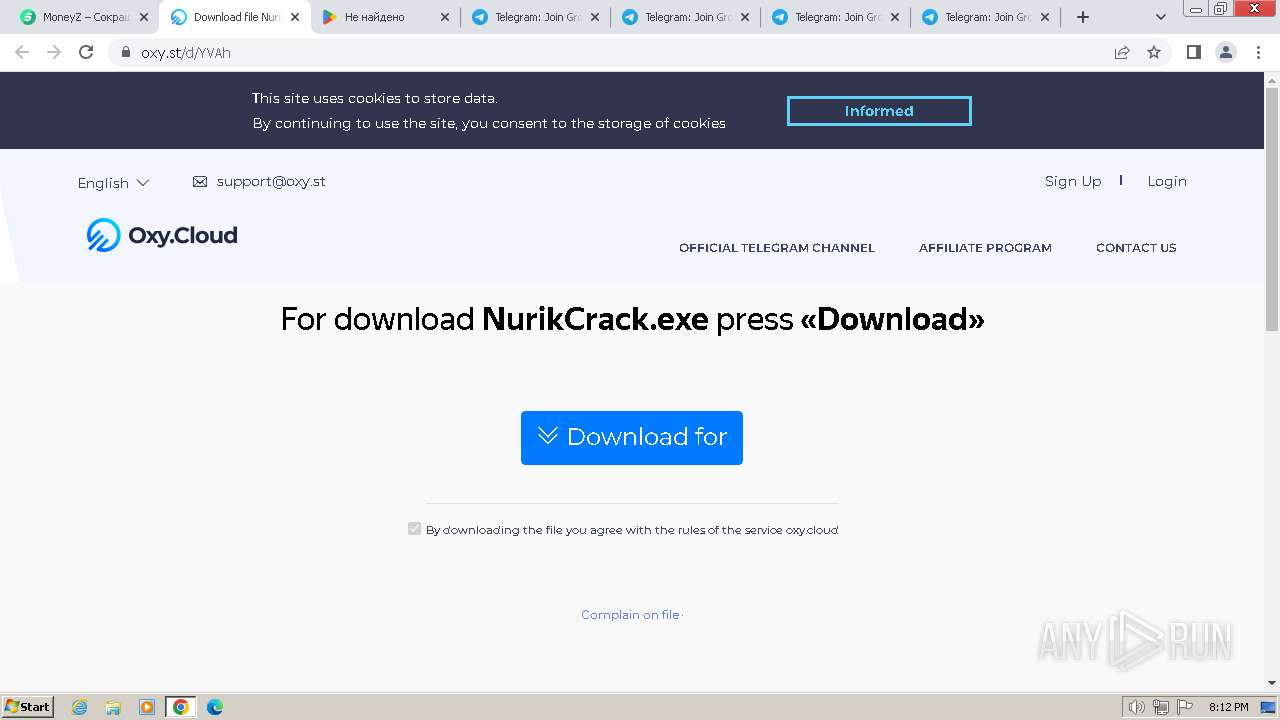
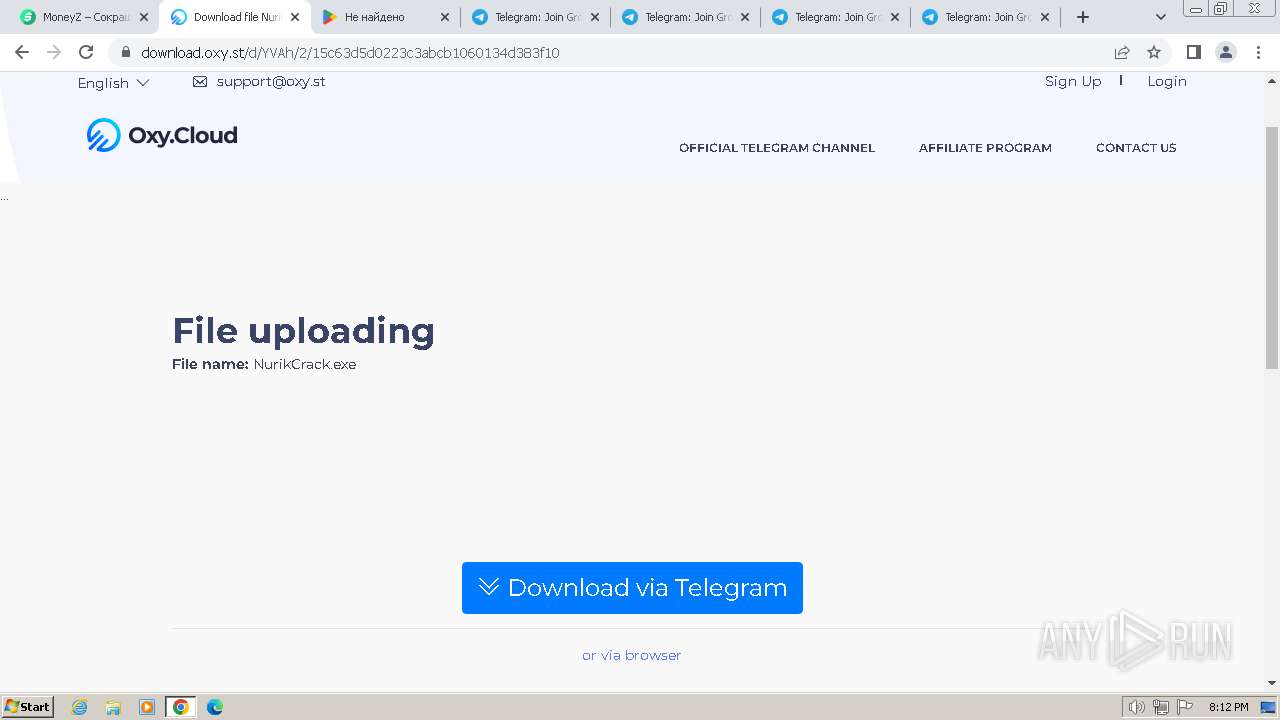
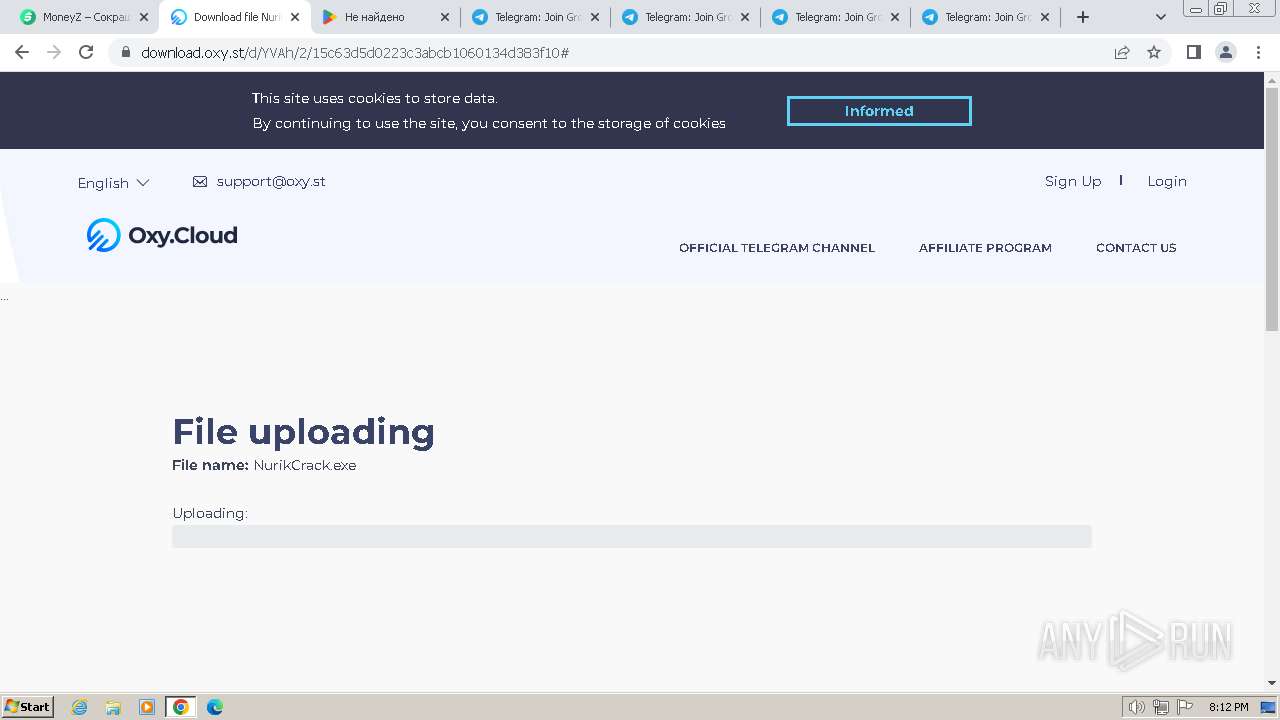
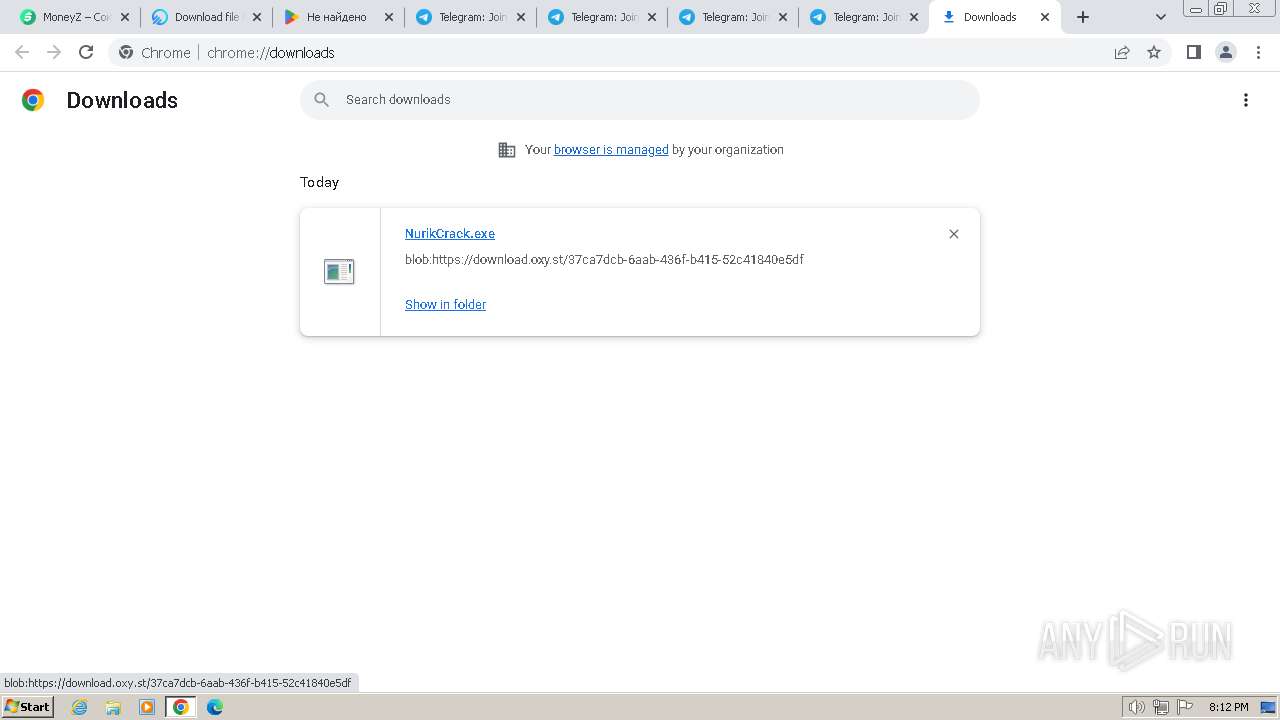
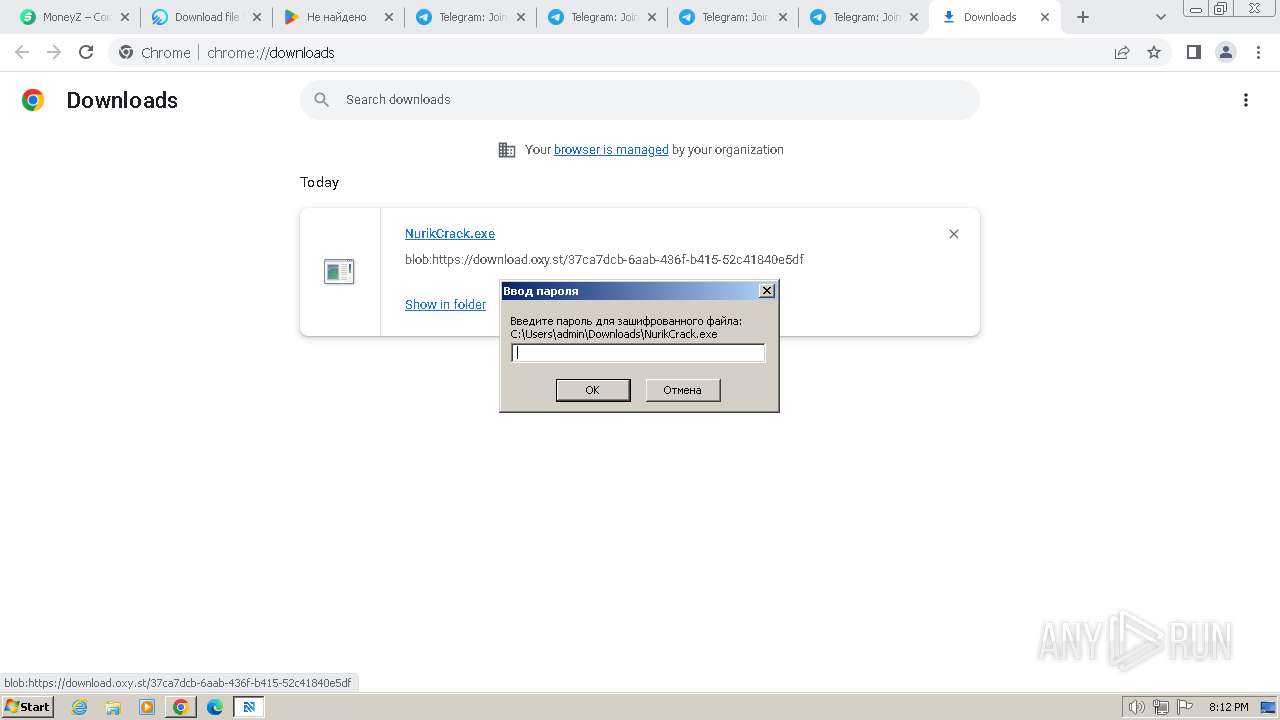
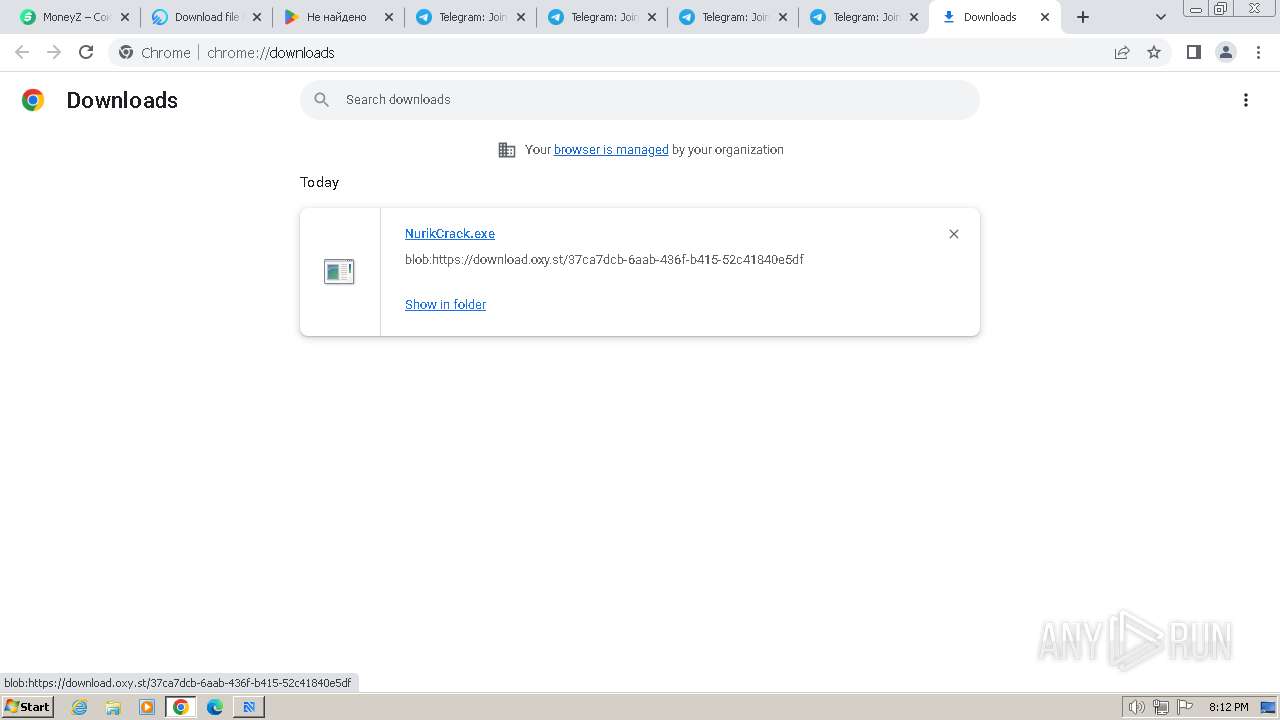
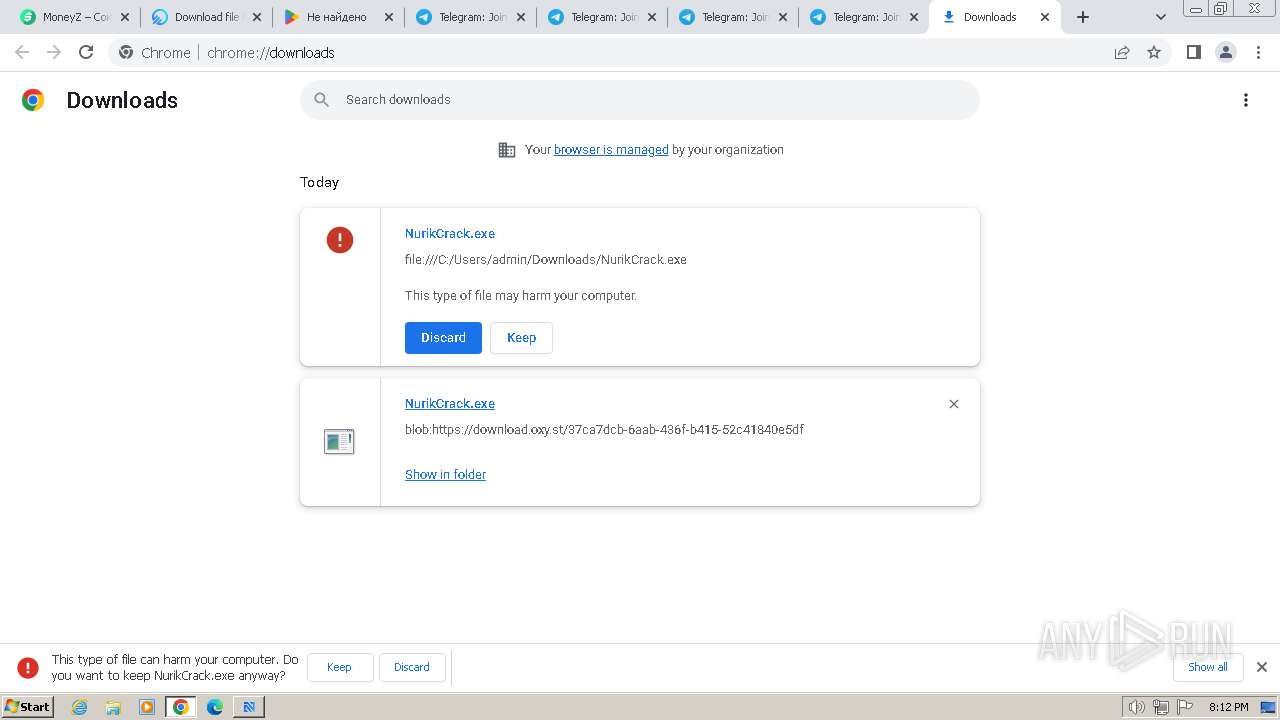
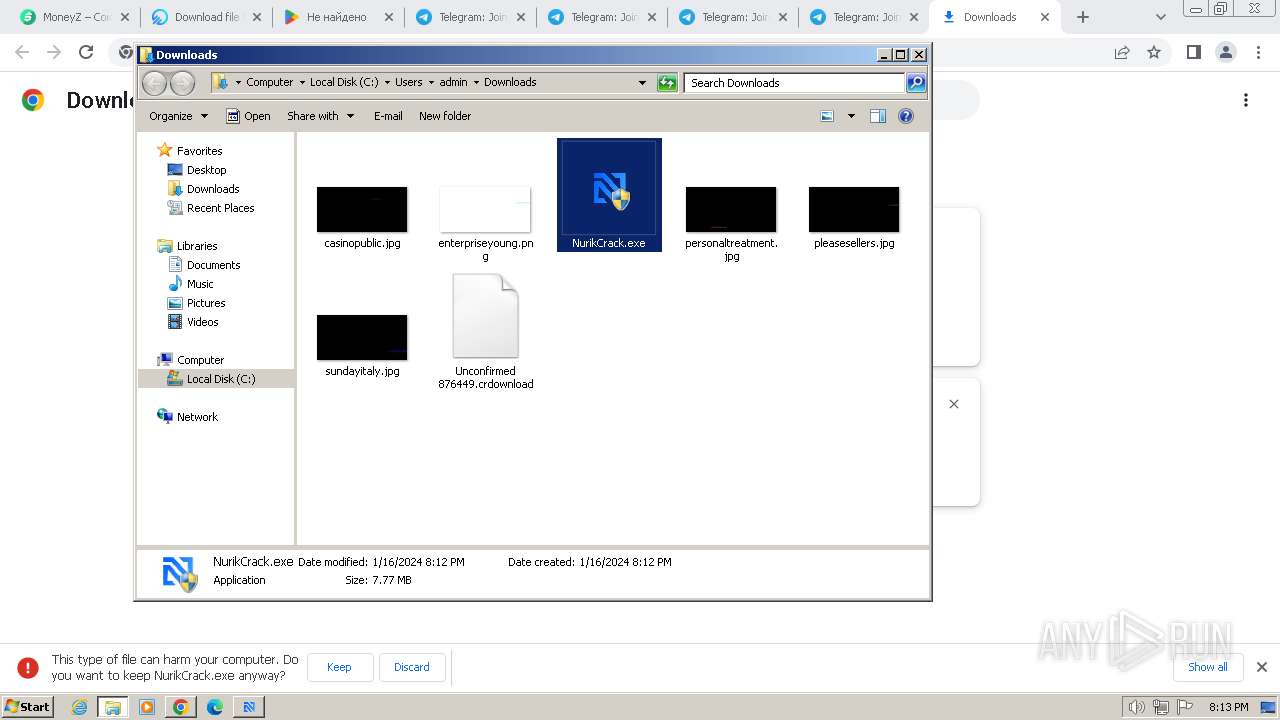
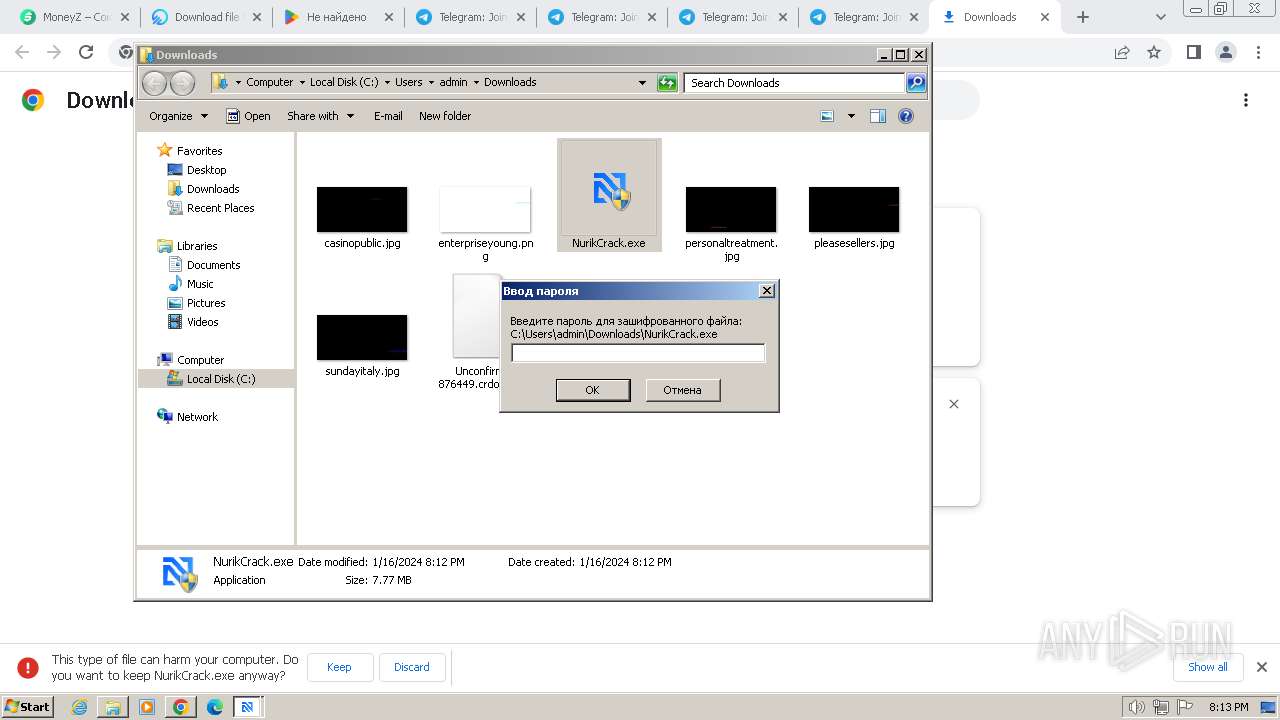
Drops the executable file immediately after the start
- NurikCrack.exe (PID: 3776)
- update.exe (PID: 3064)
- hyperfont.exe (PID: 2368)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 1000)
REDLINE has been detected (SURICATA)
- Minecraft.exe (PID: 552)
Steals credentials from Web Browsers
- Minecraft.exe (PID: 552)
- SearchIndexer.exe (PID: 3876)
DCRAT has been detected (SURICATA)
- SearchIndexer.exe (PID: 3876)
Connects to the CnC server
- SearchIndexer.exe (PID: 3876)
Steals credentials
- SearchIndexer.exe (PID: 3876)
DCRAT has been detected (YARA)
- SearchIndexer.exe (PID: 3876)
SUSPICIOUS
Executing commands from a ".bat" file
- NurikCrack.exe (PID: 3776)
- wscript.exe (PID: 1000)
- hyperfont.exe (PID: 2368)
Starts CMD.EXE for commands execution
- NurikCrack.exe (PID: 3776)
- wscript.exe (PID: 1000)
- hyperfont.exe (PID: 2368)
Reads the Internet Settings
- cmd.exe (PID: 2792)
- update.exe (PID: 3064)
- wscript.exe (PID: 1000)
- NurikCrack.exe (PID: 3776)
- Minecraft.exe (PID: 552)
- hyperfont.exe (PID: 2368)
- SearchIndexer.exe (PID: 3876)
Executable content was dropped or overwritten
- NurikCrack.exe (PID: 3776)
- update.exe (PID: 3064)
- hyperfont.exe (PID: 2368)
The executable file from the user directory is run by the CMD process
- Minecraft.exe (PID: 552)
- update.exe (PID: 3064)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1000)
The process creates files with name similar to system file names
- hyperfont.exe (PID: 2368)
Executed via WMI
- schtasks.exe (PID: 3500)
- schtasks.exe (PID: 4024)
- schtasks.exe (PID: 3960)
- schtasks.exe (PID: 3520)
- schtasks.exe (PID: 3016)
- schtasks.exe (PID: 3956)
- schtasks.exe (PID: 3948)
- schtasks.exe (PID: 3884)
- schtasks.exe (PID: 3700)
- schtasks.exe (PID: 876)
- schtasks.exe (PID: 3824)
- schtasks.exe (PID: 1196)
- schtasks.exe (PID: 2436)
- schtasks.exe (PID: 3508)
- schtasks.exe (PID: 764)
- schtasks.exe (PID: 3480)
- schtasks.exe (PID: 2752)
- schtasks.exe (PID: 3104)
- schtasks.exe (PID: 2880)
- schtasks.exe (PID: 880)
- schtasks.exe (PID: 2556)
- schtasks.exe (PID: 2816)
- schtasks.exe (PID: 3876)
- schtasks.exe (PID: 2892)
- schtasks.exe (PID: 3920)
- schtasks.exe (PID: 3852)
- schtasks.exe (PID: 3680)
- schtasks.exe (PID: 3892)
- schtasks.exe (PID: 2500)
- schtasks.exe (PID: 2584)
- schtasks.exe (PID: 3872)
- schtasks.exe (PID: 2548)
- schtasks.exe (PID: 1384)
- schtasks.exe (PID: 2672)
- schtasks.exe (PID: 3152)
- schtasks.exe (PID: 2192)
Reads settings of System Certificates
- Minecraft.exe (PID: 552)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 2960)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2488)
Searches for installed software
- Minecraft.exe (PID: 552)
Reads browser cookies
- Minecraft.exe (PID: 552)
Loads DLL from Mozilla Firefox
- SearchIndexer.exe (PID: 3876)
INFO
Application launched itself
- chrome.exe (PID: 2044)
- msedge.exe (PID: 2560)
- msedge.exe (PID: 920)
Connects to unusual port
- chrome.exe (PID: 532)
Drops the executable file immediately after the start
- chrome.exe (PID: 2044)
Executable content was dropped or overwritten
- chrome.exe (PID: 2044)
The process uses the downloaded file
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2044)
Checks supported languages
- NurikCrack.exe (PID: 992)
- NurikCrack.exe (PID: 3776)
- Minecraft.exe (PID: 552)
- update.exe (PID: 3064)
- hyperfont.exe (PID: 2368)
- SearchIndexer.exe (PID: 3876)
Manual execution by a user
- NurikCrack.exe (PID: 3776)
- NurikCrack.exe (PID: 3452)
- msedge.exe (PID: 920)
Reads the computer name
- NurikCrack.exe (PID: 992)
- NurikCrack.exe (PID: 3776)
- update.exe (PID: 3064)
- hyperfont.exe (PID: 2368)
- Minecraft.exe (PID: 552)
- SearchIndexer.exe (PID: 3876)
Create files in a temporary directory
- NurikCrack.exe (PID: 3776)
- hyperfont.exe (PID: 2368)
- SearchIndexer.exe (PID: 3876)
Reads the machine GUID from the registry
- Minecraft.exe (PID: 552)
- hyperfont.exe (PID: 2368)
- SearchIndexer.exe (PID: 3876)
Reads Environment values
- hyperfont.exe (PID: 2368)
- Minecraft.exe (PID: 552)
- SearchIndexer.exe (PID: 3876)
Reads product name
- hyperfont.exe (PID: 2368)
- Minecraft.exe (PID: 552)
- SearchIndexer.exe (PID: 3876)
Creates files in the program directory
- hyperfont.exe (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
168
Monitored processes
120
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4160 --field-trial-handle=1120,i,15788987607783941533,9688265571250195688,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3428 --field-trial-handle=1120,i,15788987607783941533,9688265571250195688,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1520 --field-trial-handle=1120,i,15788987607783941533,9688265571250195688,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1300 --field-trial-handle=1120,i,15788987607783941533,9688265571250195688,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1148 --field-trial-handle=1120,i,15788987607783941533,9688265571250195688,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 552 | Minecraft.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Minecraft.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1196 --field-trial-handle=1180,i,13334204412017981961,12866959273924598948,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 764 | schtasks.exe /create /tn "chromec" /sc MINUTE /mo 7 /tr "'C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\chrome.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | schtasks.exe /create /tn "chrome" /sc ONLOGON /tr "'C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\chrome.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | schtasks.exe /create /tn "conhostc" /sc MINUTE /mo 12 /tr "'C:\Program Files\Windows Photo Viewer\conhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 795
Read events
15 561
Write events
232
Delete events
2
Modification events
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
23
Suspicious files
640
Text files
90
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdf8a9.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFdfa6e.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFdfa9d.TMP | text | |
MD5:F5B58F0B08202C8D6DE12514994A84BF | SHA256:F5BA8809B6A3920A11CF31E7F6A1DEC46EF4F4339D6158967CCB1405409D1241 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFdffcd.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 2044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
117
DNS requests
156
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.53 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.82 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 8.67 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 17.8 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 49.6 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 49.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | binary | 339 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 43.6 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 8.67 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/py5dqeczg3bmfxj4vm3bvsxb6y_3013/jflookgnkcckhobaglndicnbbgbonegd_3013_all_adgpehxzxriaky3auope65o5vw7q.crx3 | unknown | binary | 345 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2044 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
532 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
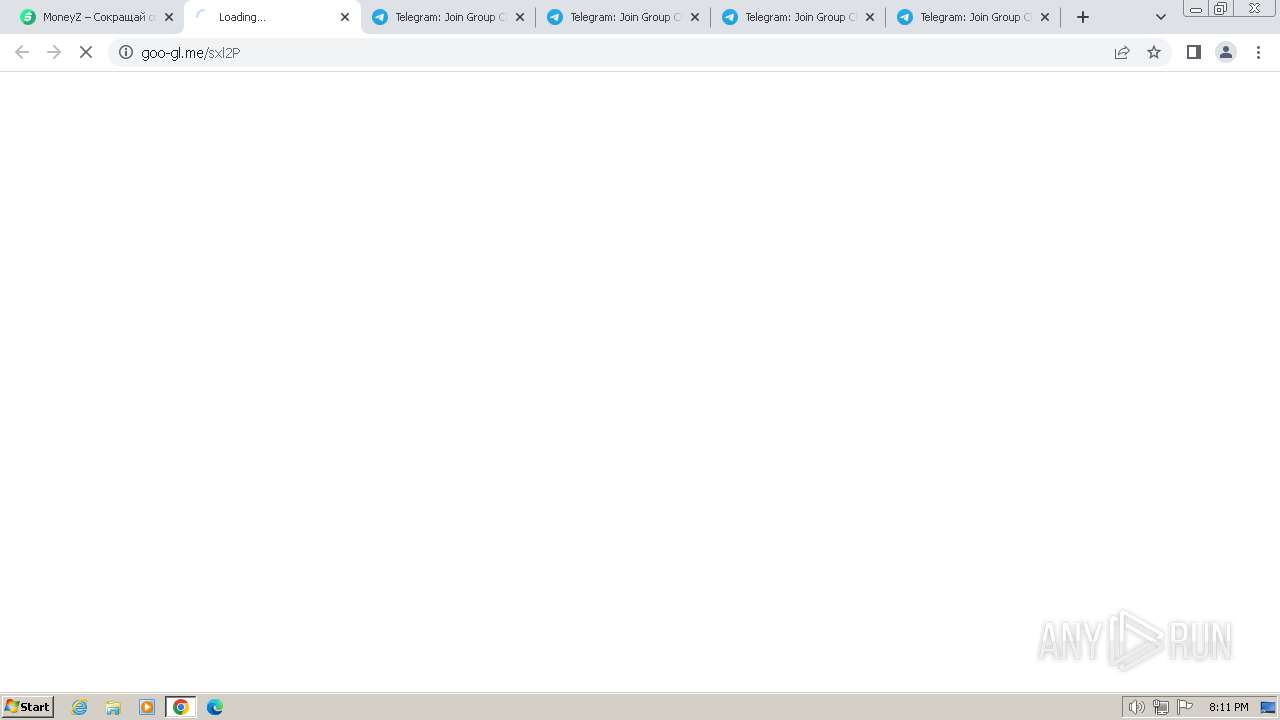
532 | chrome.exe | 188.114.96.3:443 | moneyz.fun | CLOUDFLARENET | NL | unknown |
532 | chrome.exe | 95.163.118.168:443 | ulogin.ru | LLC Digital Network | RU | unknown |
532 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
532 | chrome.exe | 142.250.186.74:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
moneyz.fun |
| unknown |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ulogin.ru |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
pushadv.biz |
| unknown |
mc.yandex.ru |
| whitelisted |
counter.yadro.ru |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
532 | chrome.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
532 | chrome.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
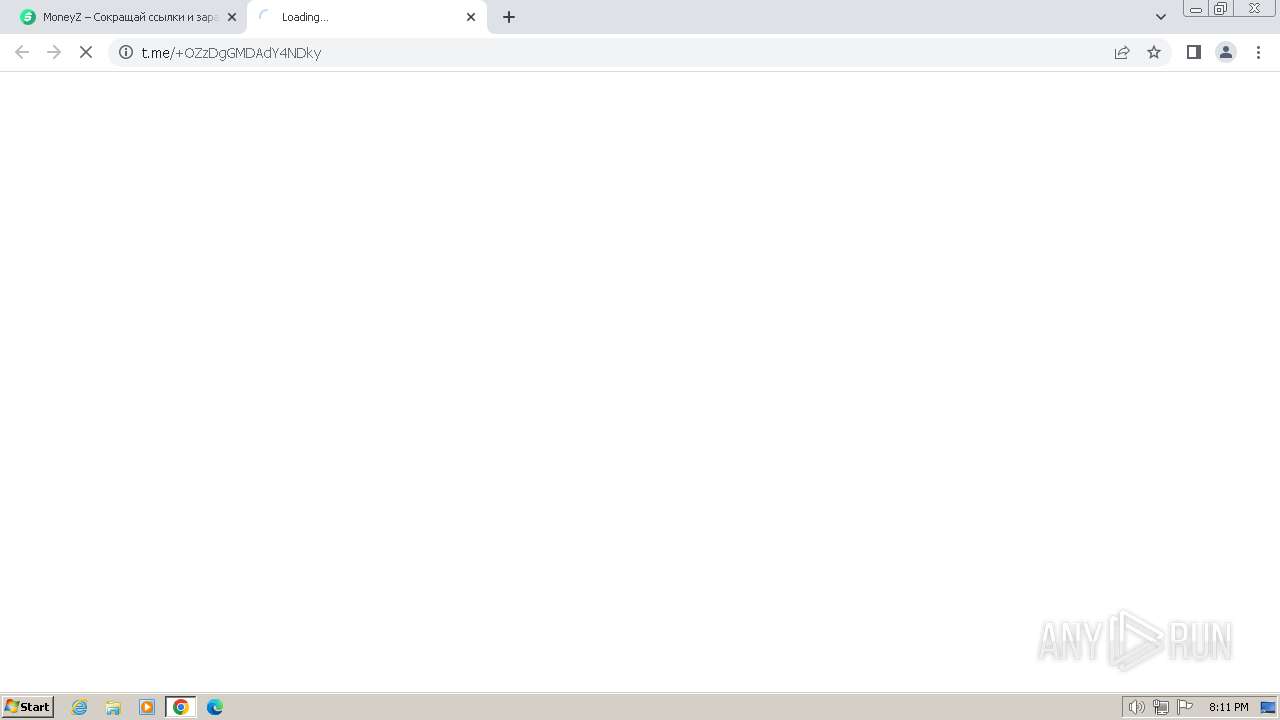
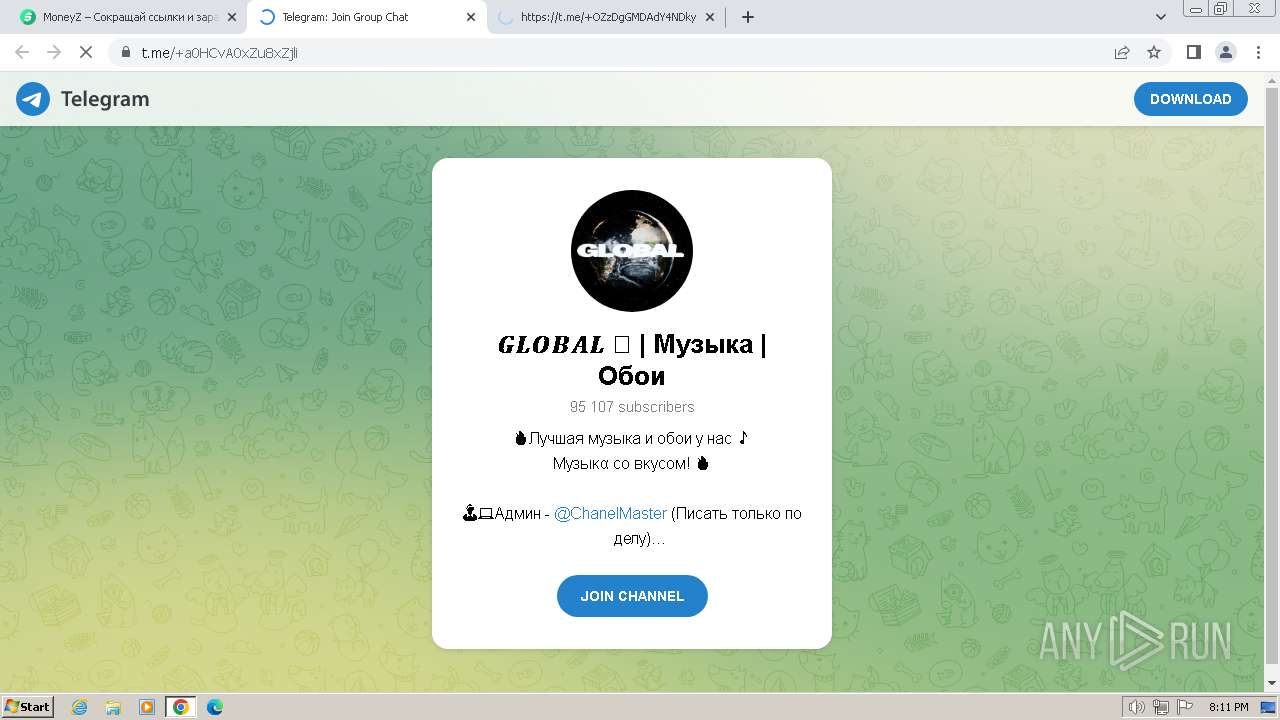
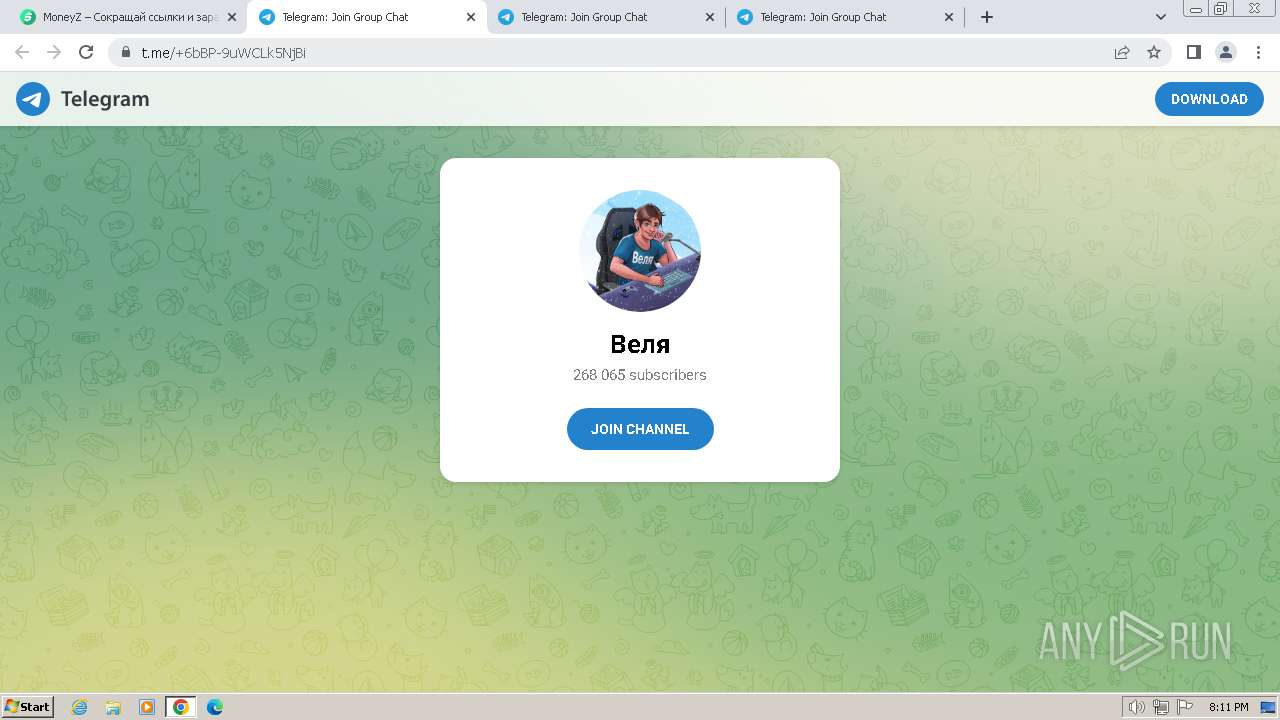
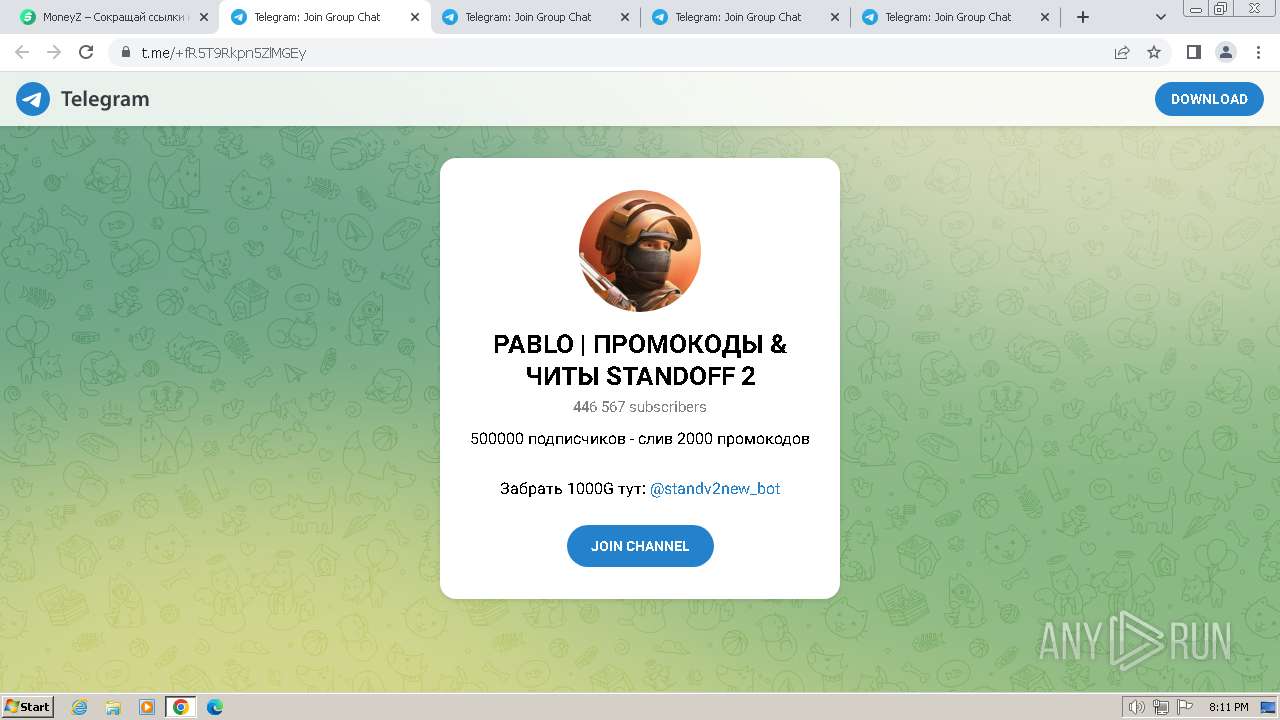
532 | chrome.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
532 | chrome.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
532 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
532 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
532 | chrome.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
532 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
532 | chrome.exe | Potentially Bad Traffic | ET HUNTING Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |
532 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
3 ETPRO signatures available at the full report