| File name: | Vidar Binary |
| Full analysis: | https://app.any.run/tasks/b3eac3fa-4de0-44e5-a966-bc38cec08e66 |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
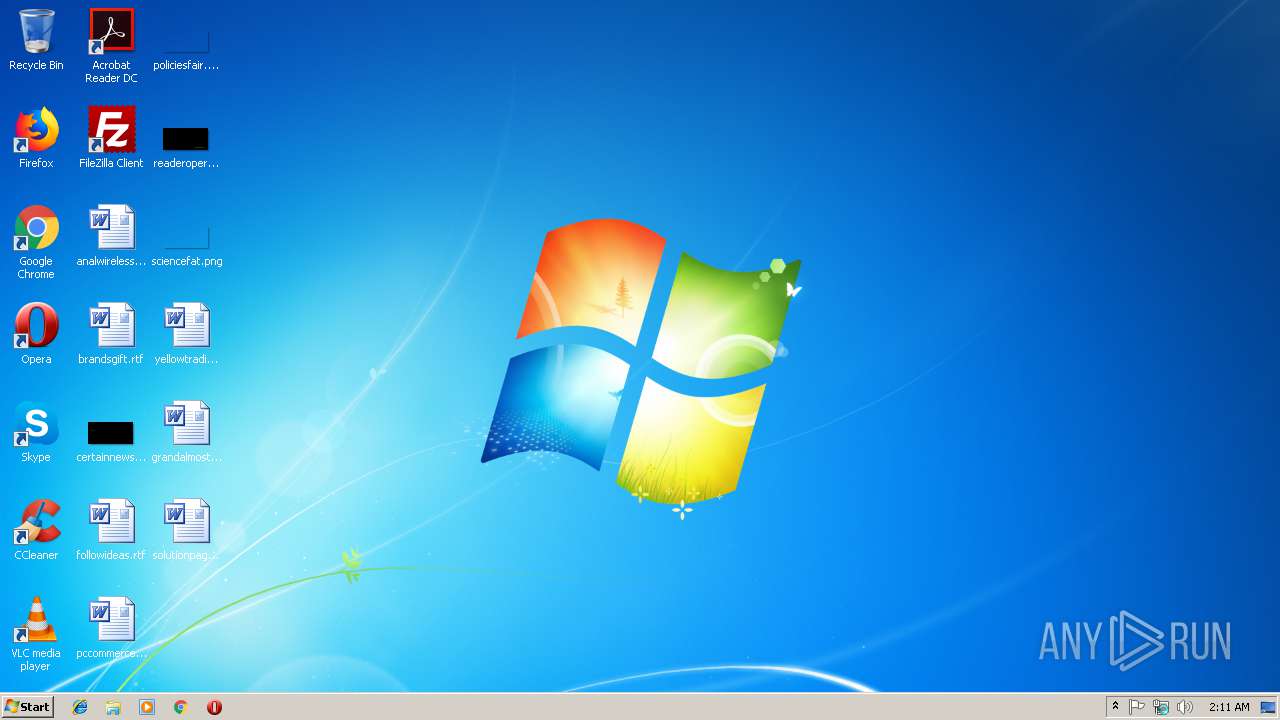
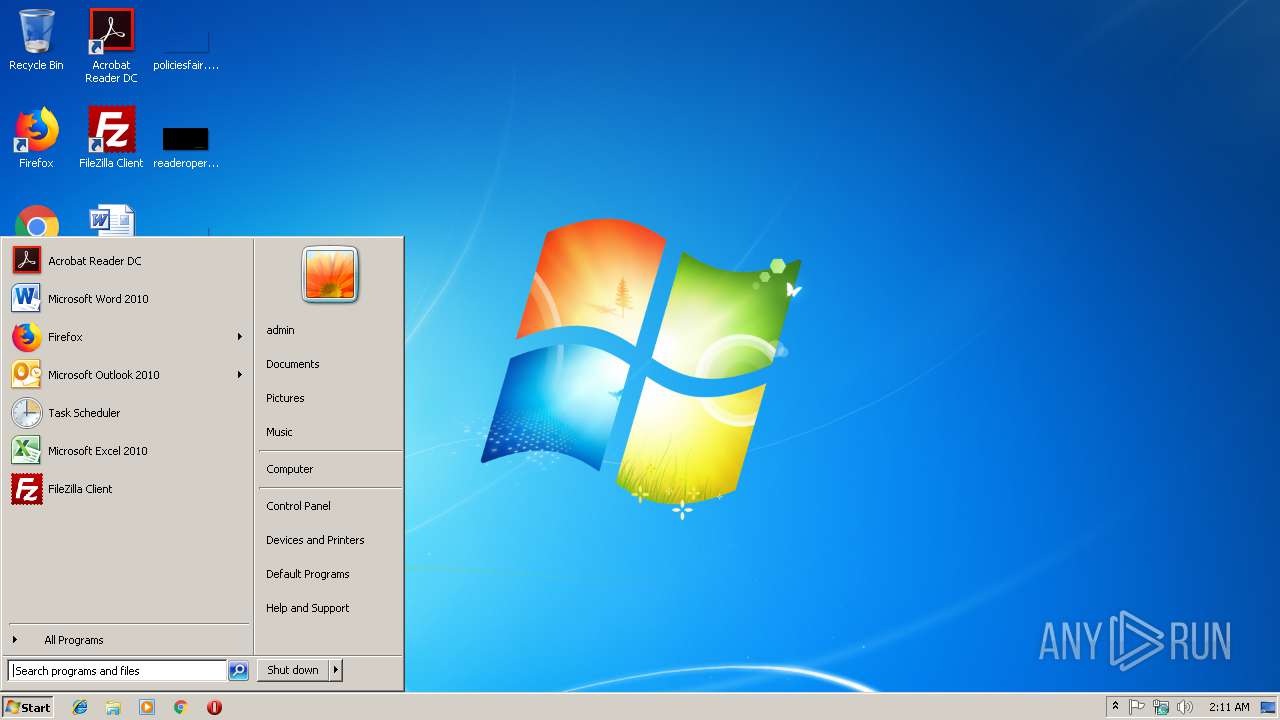
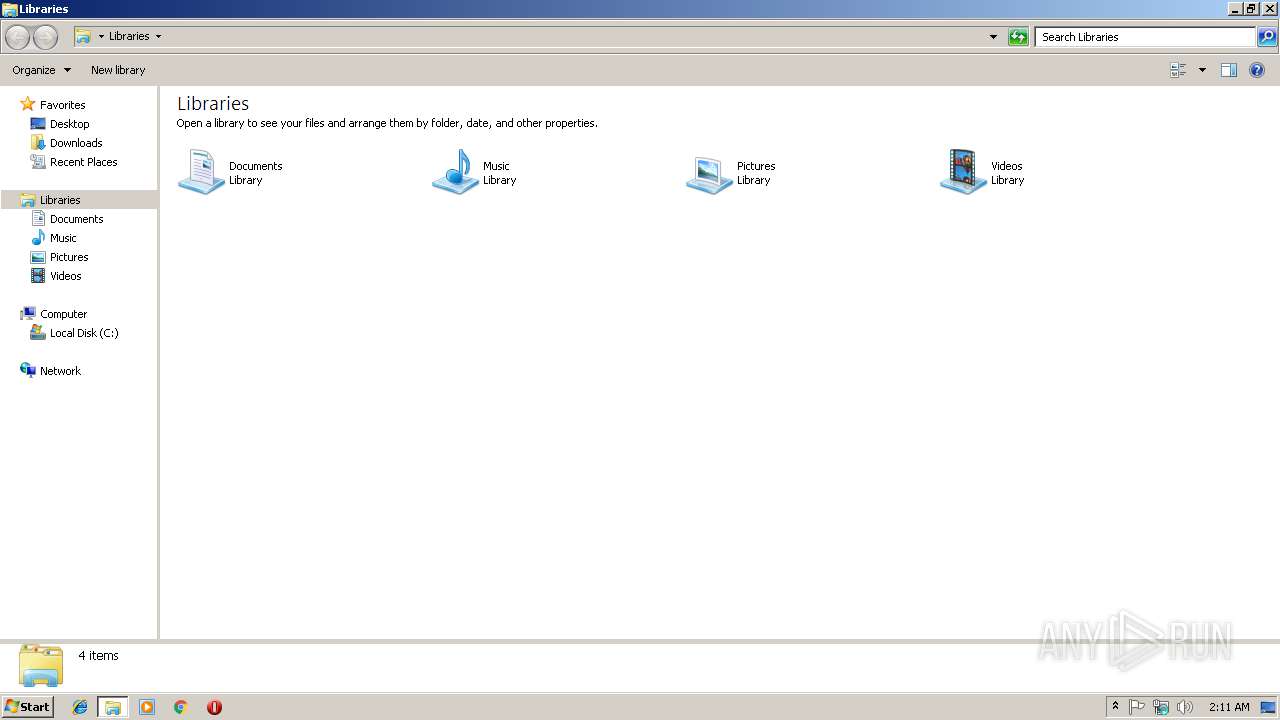
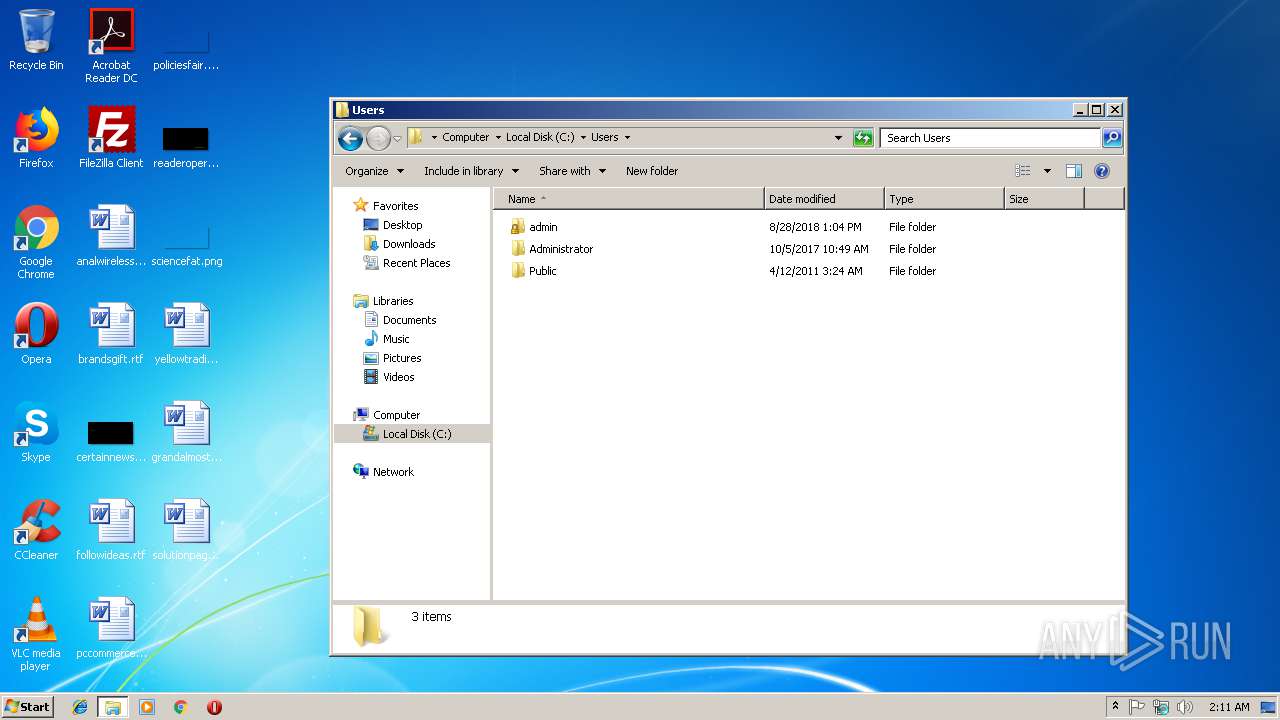
| Analysis date: | January 23, 2019, 02:11:07 |
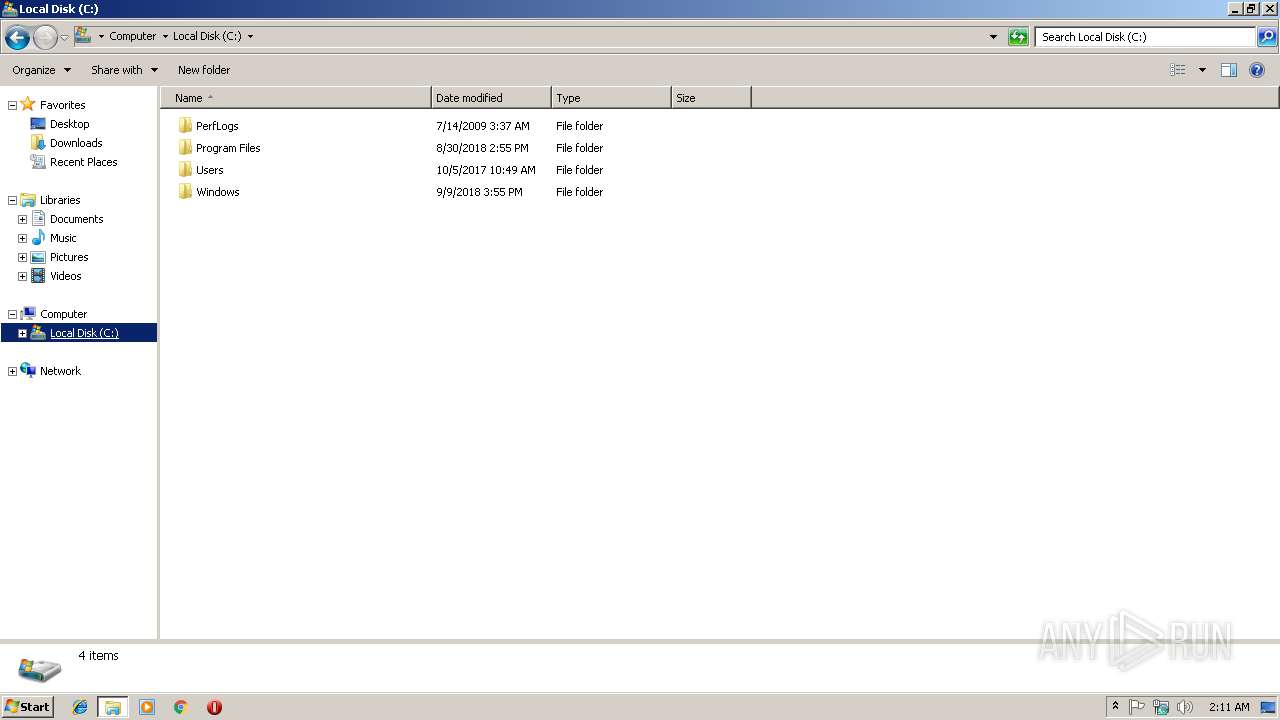
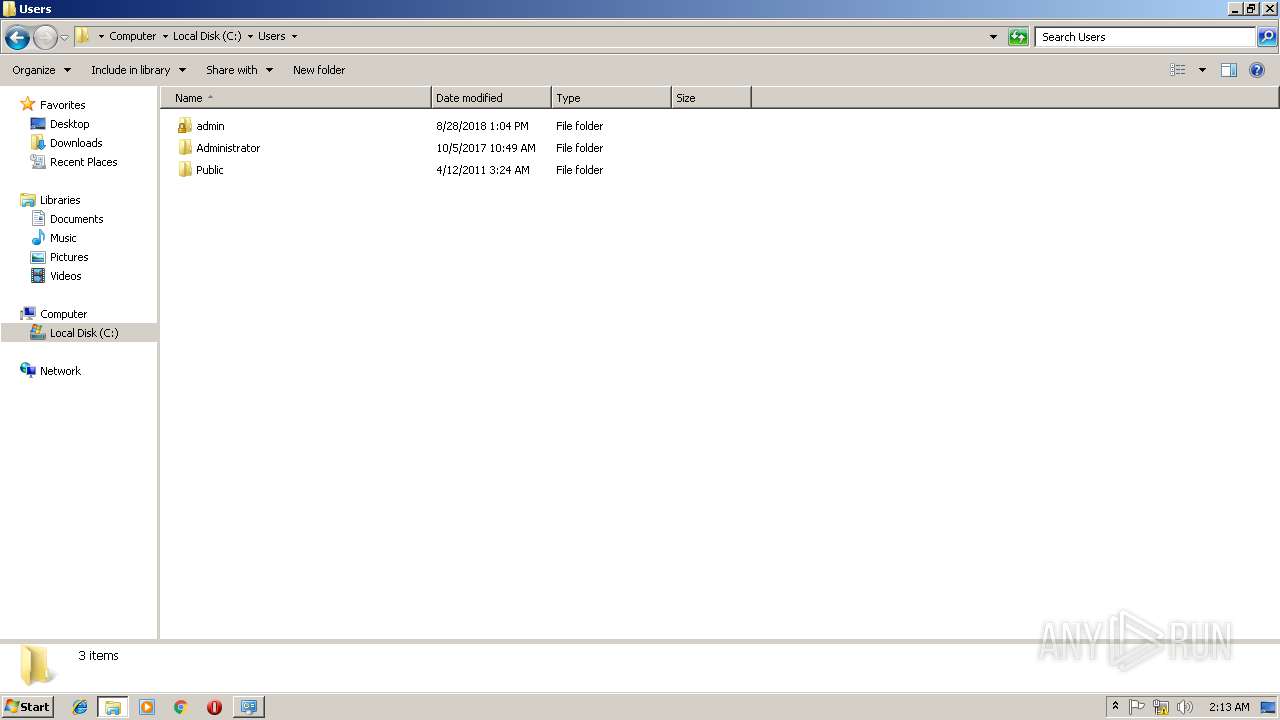
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2279E17D60F5530259F2A7579A40318D |
| SHA1: | 4423ACFD7062260B22CF0D8ED15F8A91AC735EA2 |
| SHA256: | E99DAF10E6CB98E93F82DBE344E6D6B483B9073E80B128C163034F68DE63BE33 |
| SSDEEP: | 12288:fkXIUl7ZCjz1LYyd17QLmSEjZG6EuP3XSB9tpxg:f7Ul7ZCH2wpfP06Eu/8I |
MALICIOUS
Actions looks like stealing of personal data
- Vidar Binary.exe (PID: 3480)
Stealing of credential data
- Vidar Binary.exe (PID: 3480)
ARKEI was detected
- Vidar Binary.exe (PID: 3480)
SUSPICIOUS
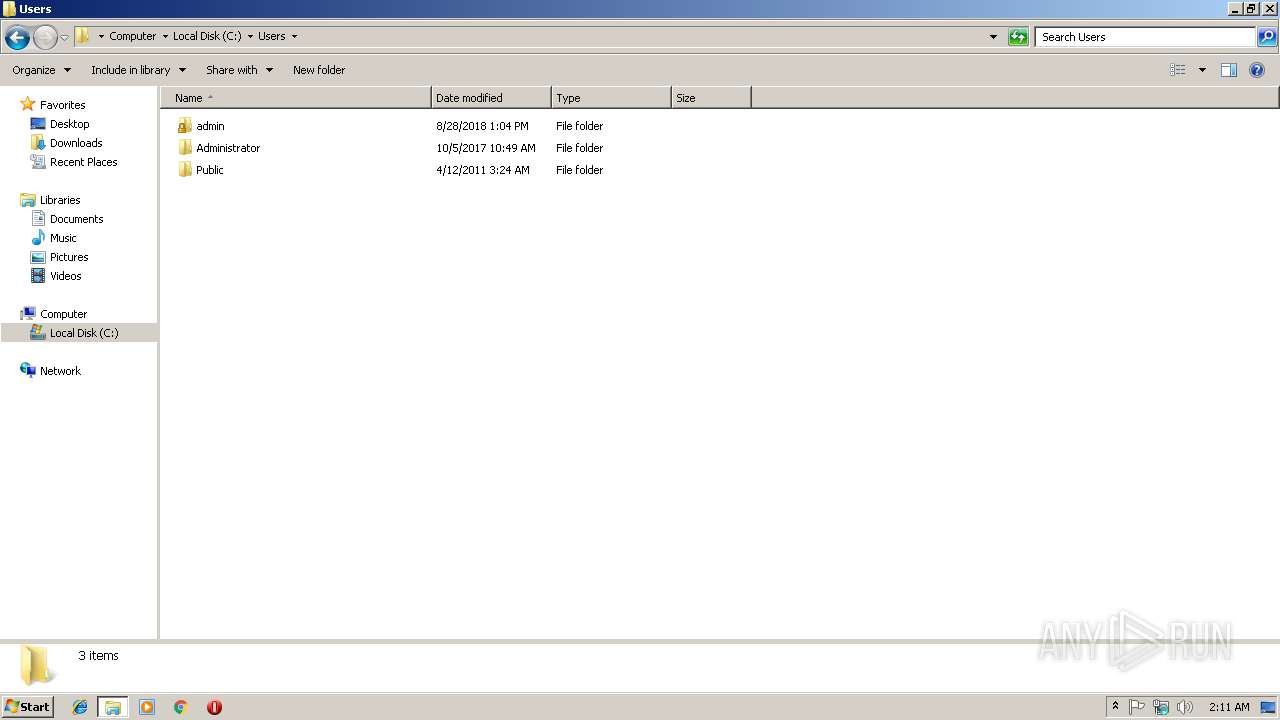
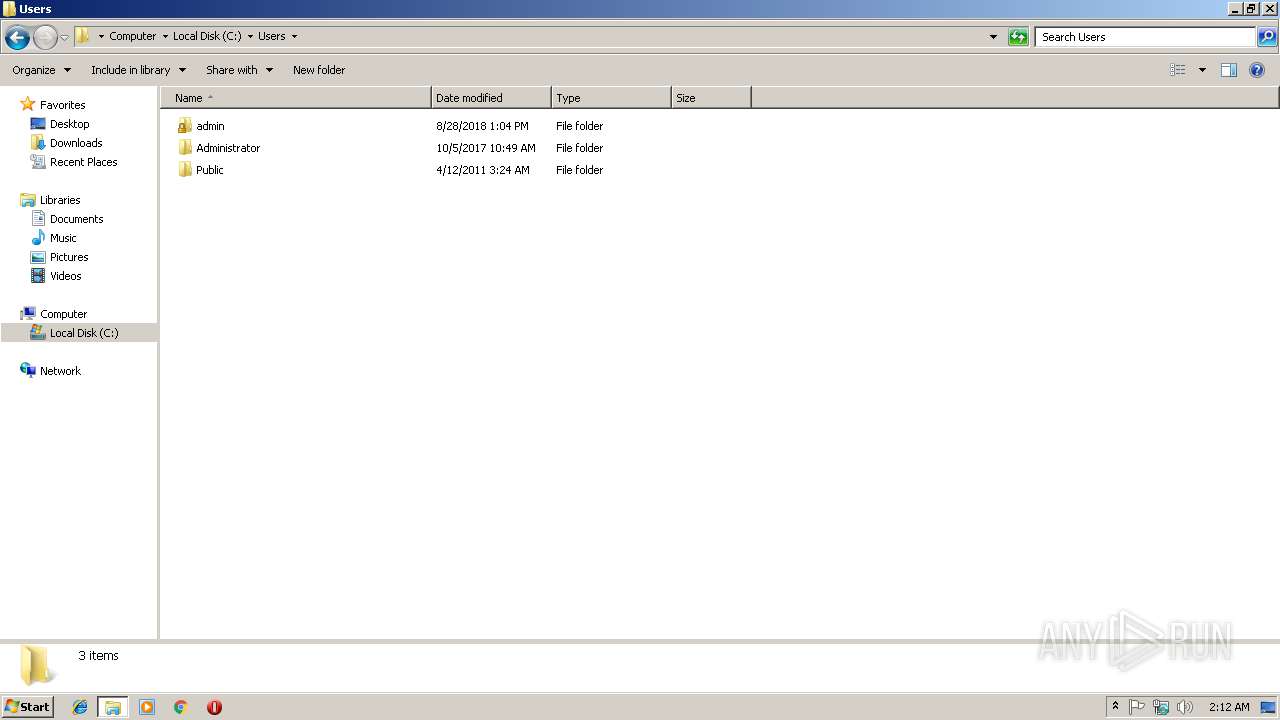
Creates files in the user directory
- Vidar Binary.exe (PID: 3480)
Creates files in the program directory
- Vidar Binary.exe (PID: 3480)
Checks for external IP
- Vidar Binary.exe (PID: 3480)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:28 18:29:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 147456 |
| InitializedDataSize: | 516096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13272 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.70.3 |
| ProductVersionNumber: | 3.5.70.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Delighters Simulations Retrieve |
| PrivateBuild: | 3.5.70.3 |
| LegalCopyright: | Copyright ©Spencer Kimball, Peter Mattis and the GIMP Development Team 2000 - 2014 KG and its Licensors |
| InternalName: | Transfrmed |
| FileDescription: | Delighters Simulations Retrieve |
| ProductName: | Transfrmed |
| CompanyName: | Spencer Kimball, Peter Mattis and the GIMP Development Team |
| ProductVersion: | 3.5.70.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Dec-2018 17:29:49 |
| Detected languages: |
|
| Comments: | Delighters Simulations Retrieve |
| PrivateBuild: | 3.5.70.3 |
| LegalCopyright: | Copyright ©Spencer Kimball, Peter Mattis and the GIMP Development Team 2000 - 2014 KG and its Licensors |
| InternalName: | Transfrmed |
| FileDescription: | Delighters Simulations Retrieve |
| ProductName: | Transfrmed |
| CompanyName: | Spencer Kimball, Peter Mattis and the GIMP Development Team |
| ProductVersion: | 3.5.70.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-Dec-2018 17:29:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00023FD0 | 0x00024000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62797 |
.rdata | 0x00025000 | 0x00008A88 | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.00543 |
.data | 0x0002E000 | 0x00005304 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.25124 |
.rsrc | 0x00034000 | 0x0006E430 | 0x0006E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.71956 |
.reloc | 0x000A3000 | 0x00003850 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.84628 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2454 | 1233 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.26897 | 19496 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.44447 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.07236 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.17761 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.90866 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.00288 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 0.545897 | 36 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 3.32378 | 238 | Latin 1 / Western European | English - United States | RT_DIALOG |
101 | 2.76249 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSVFW32.dll |
NETAPI32.dll |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
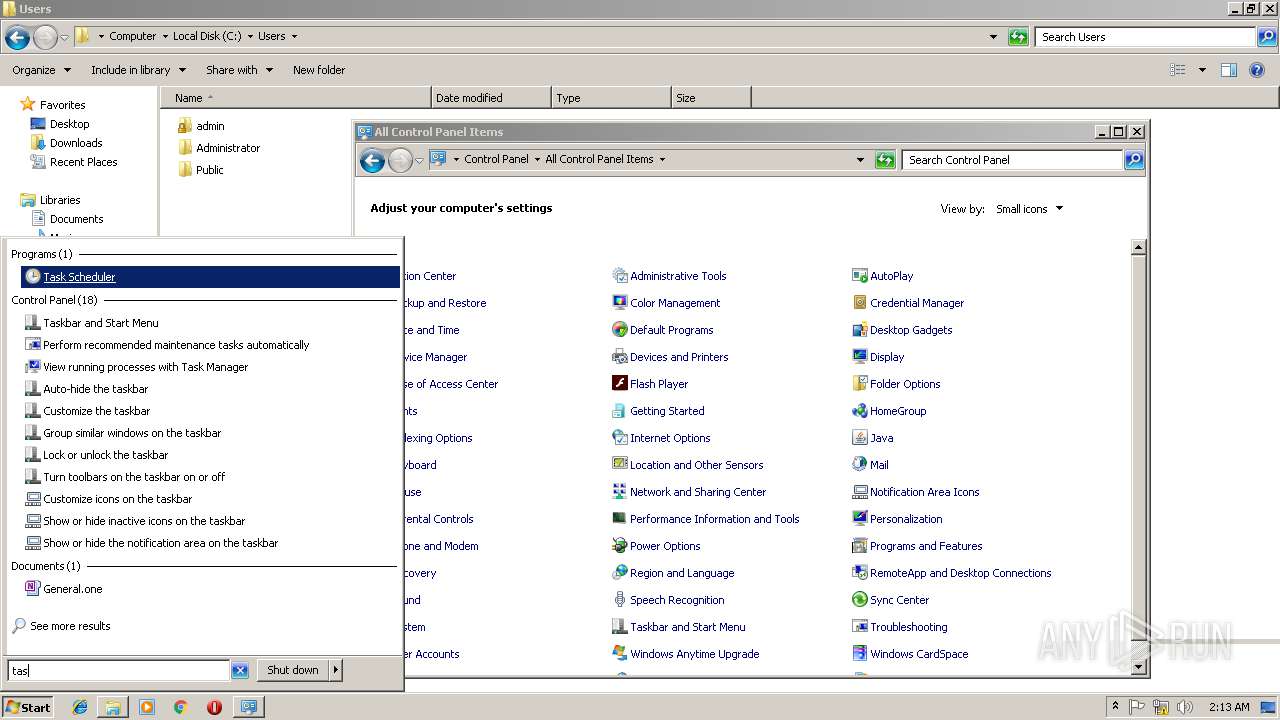
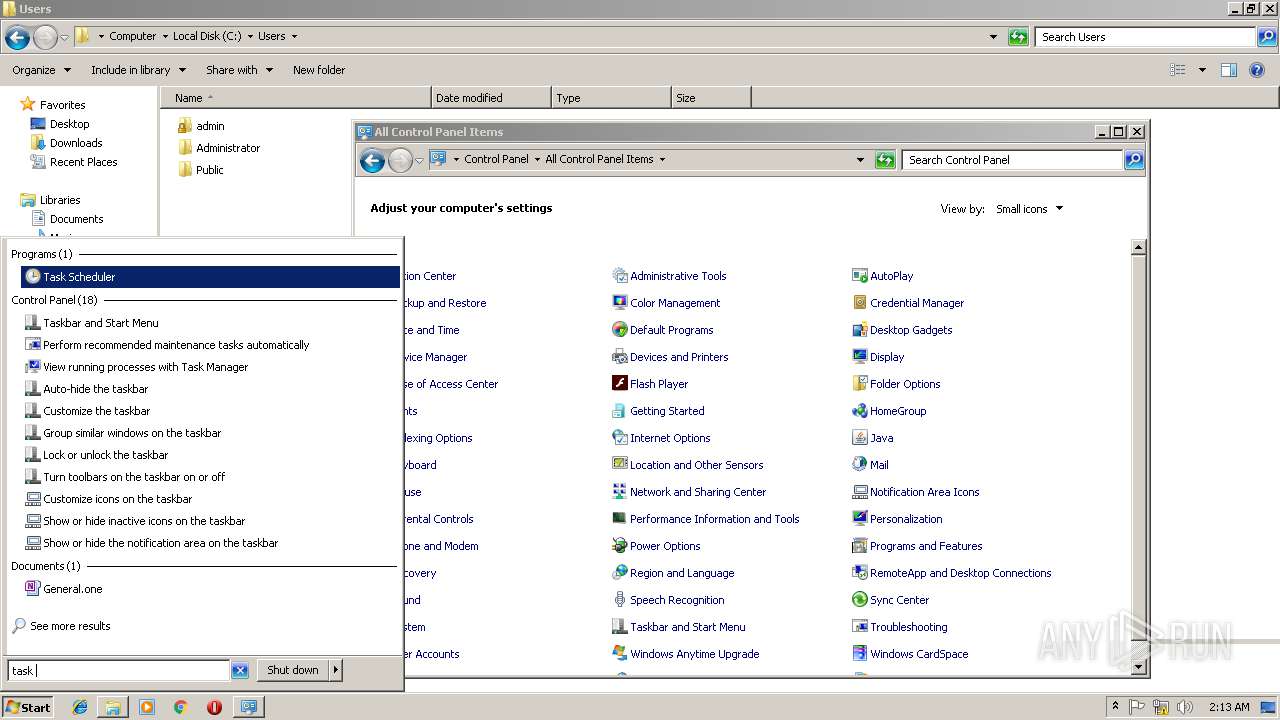
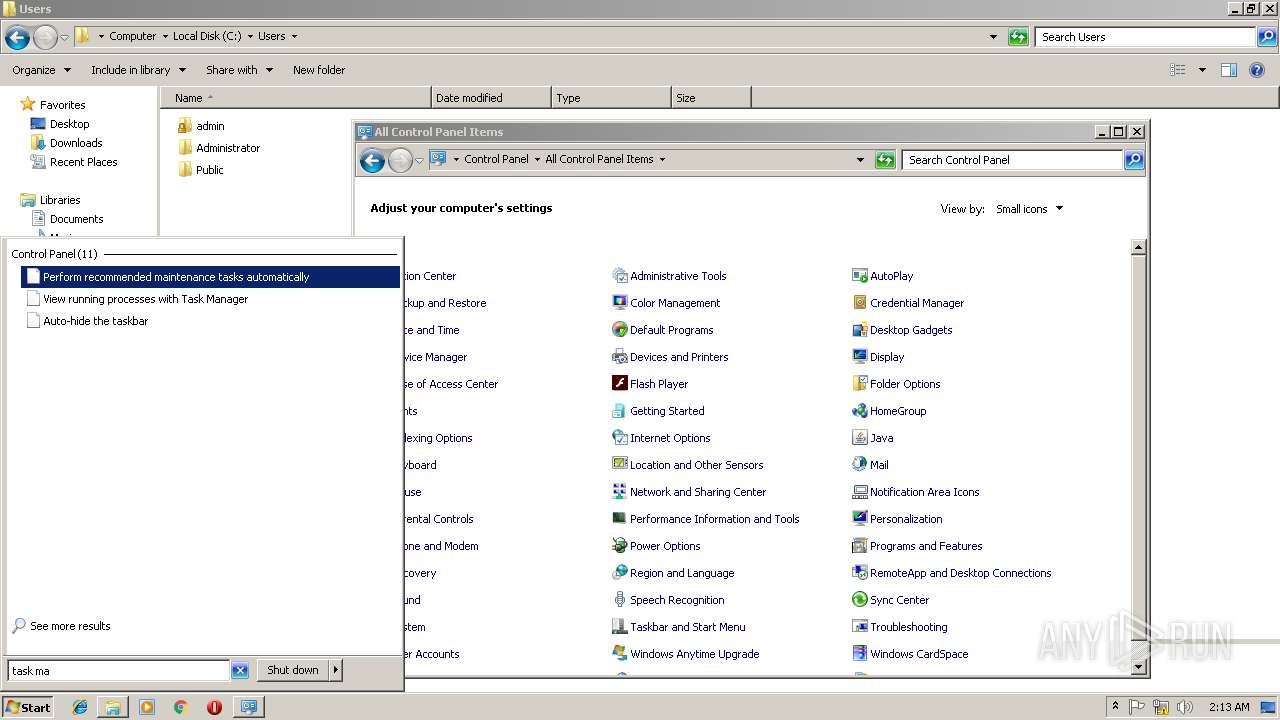
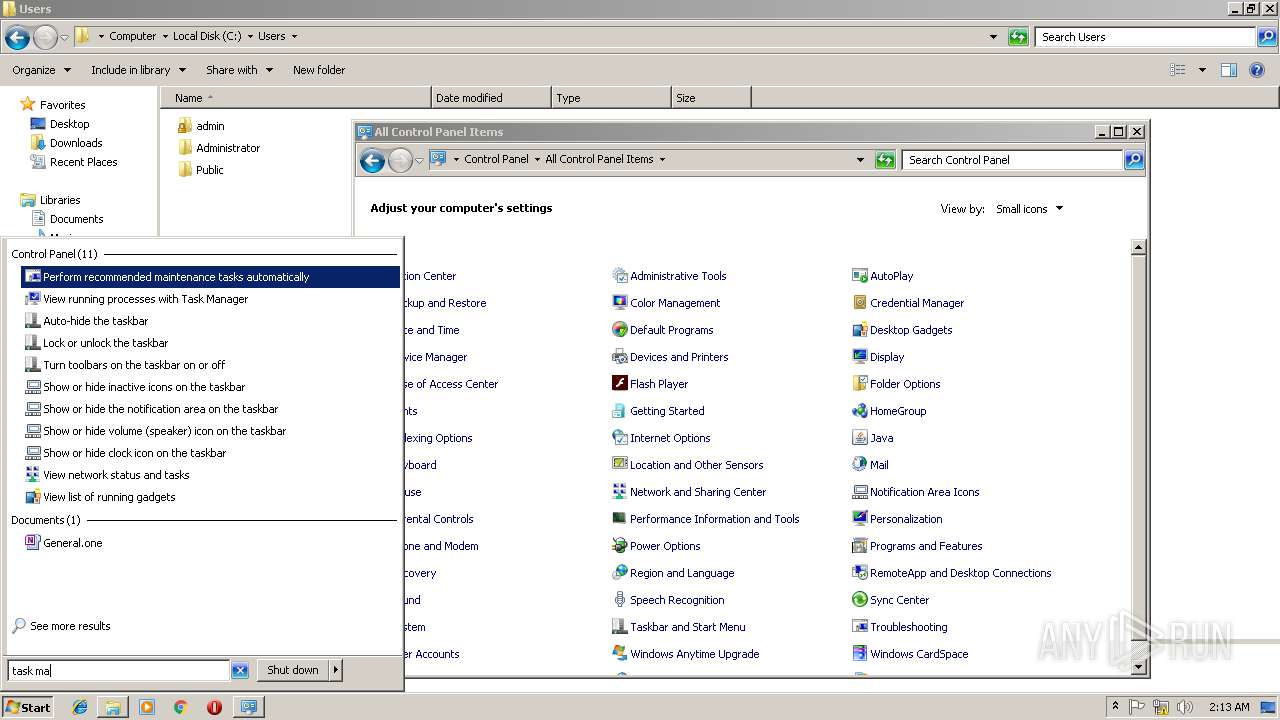
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
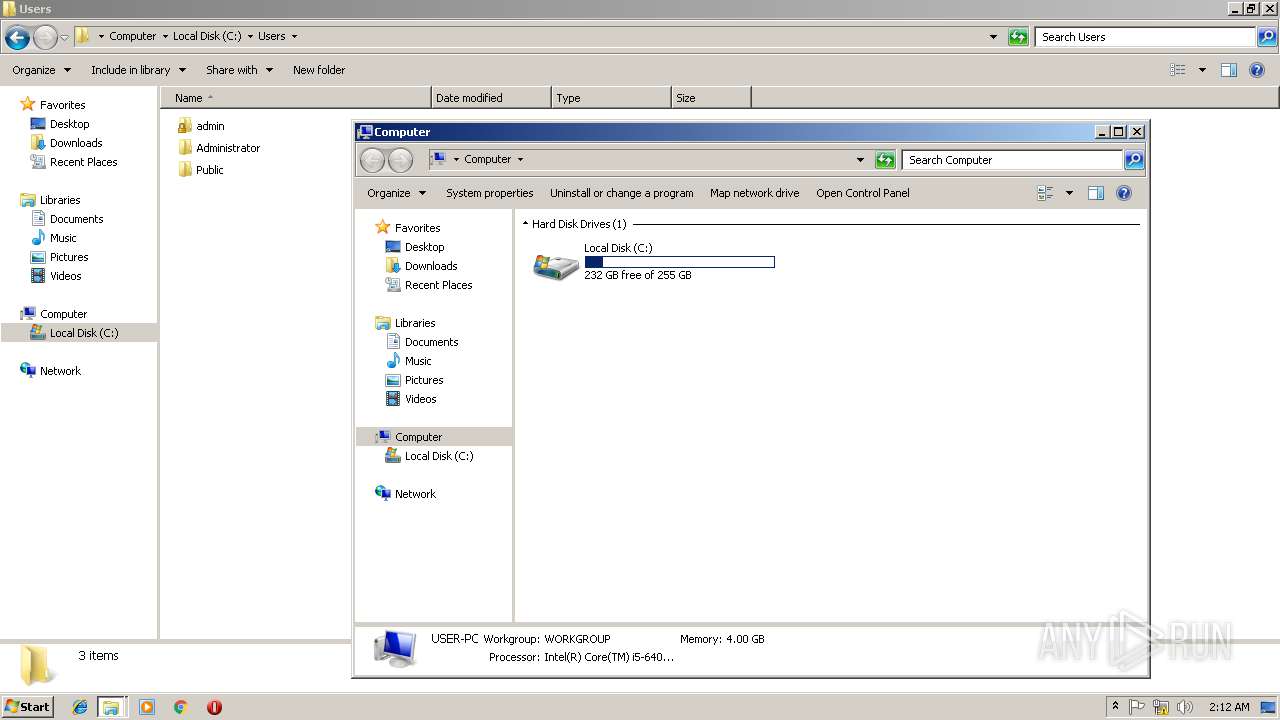
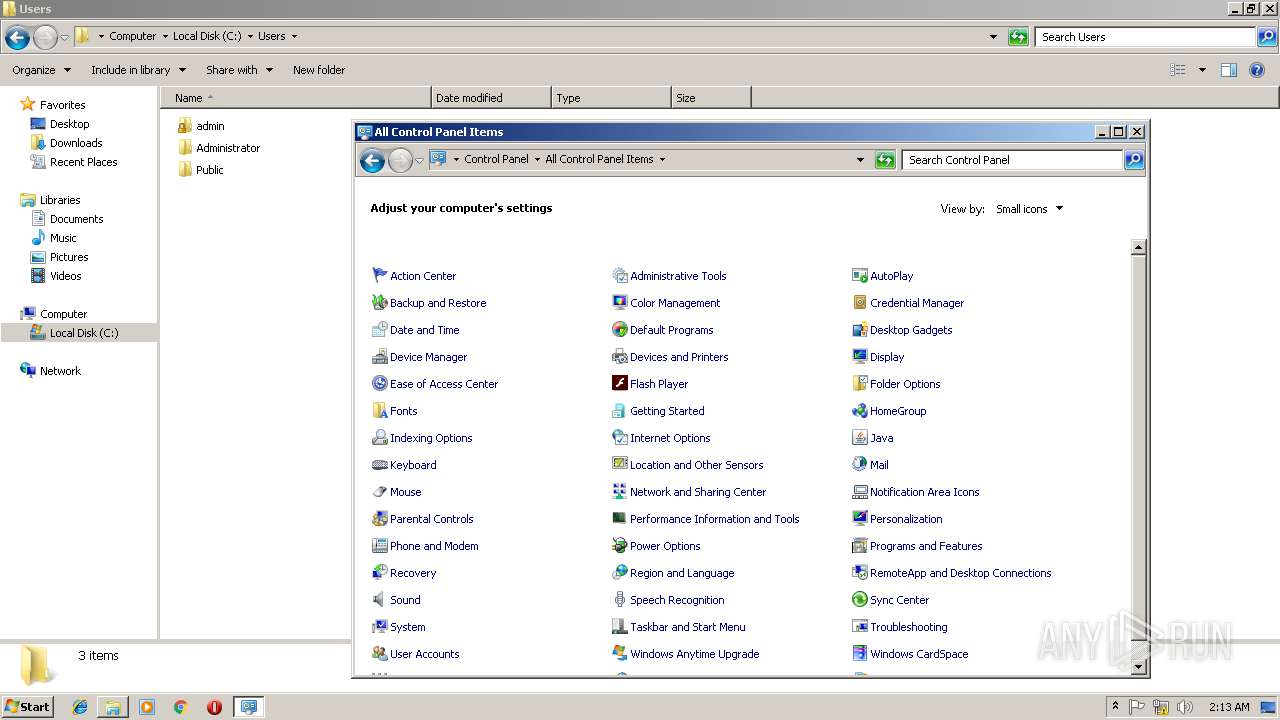
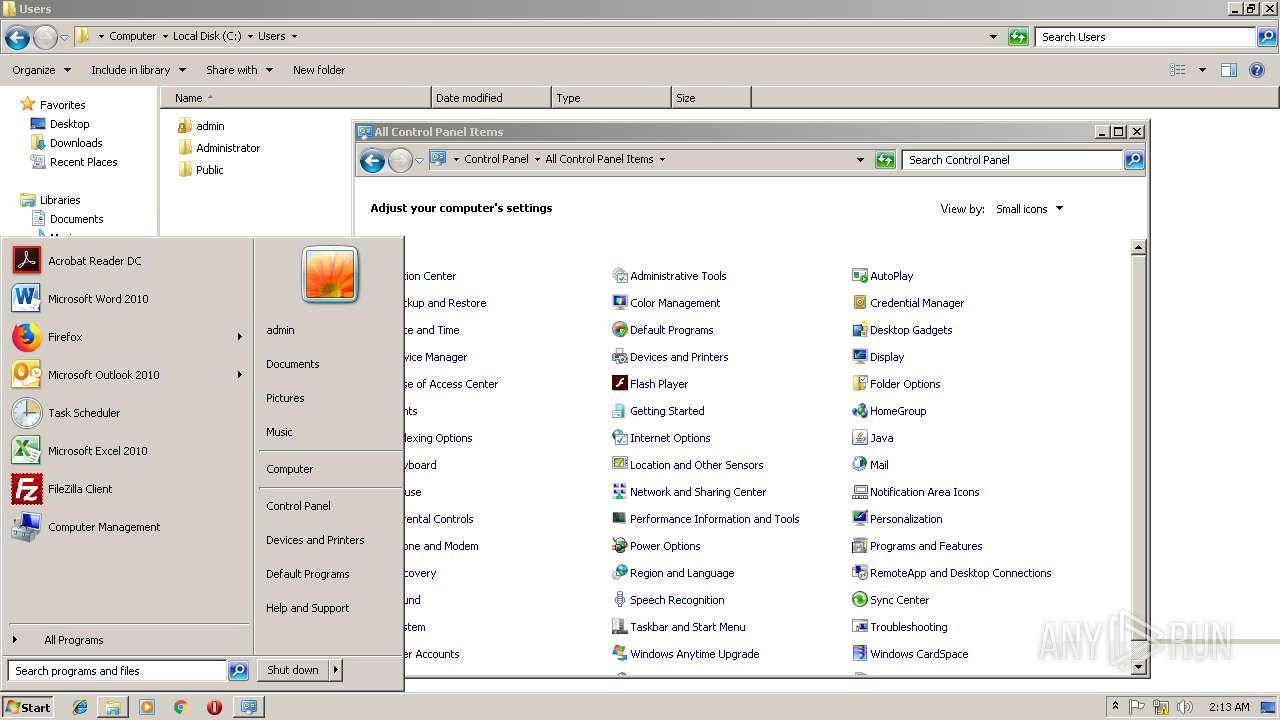
| 928 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
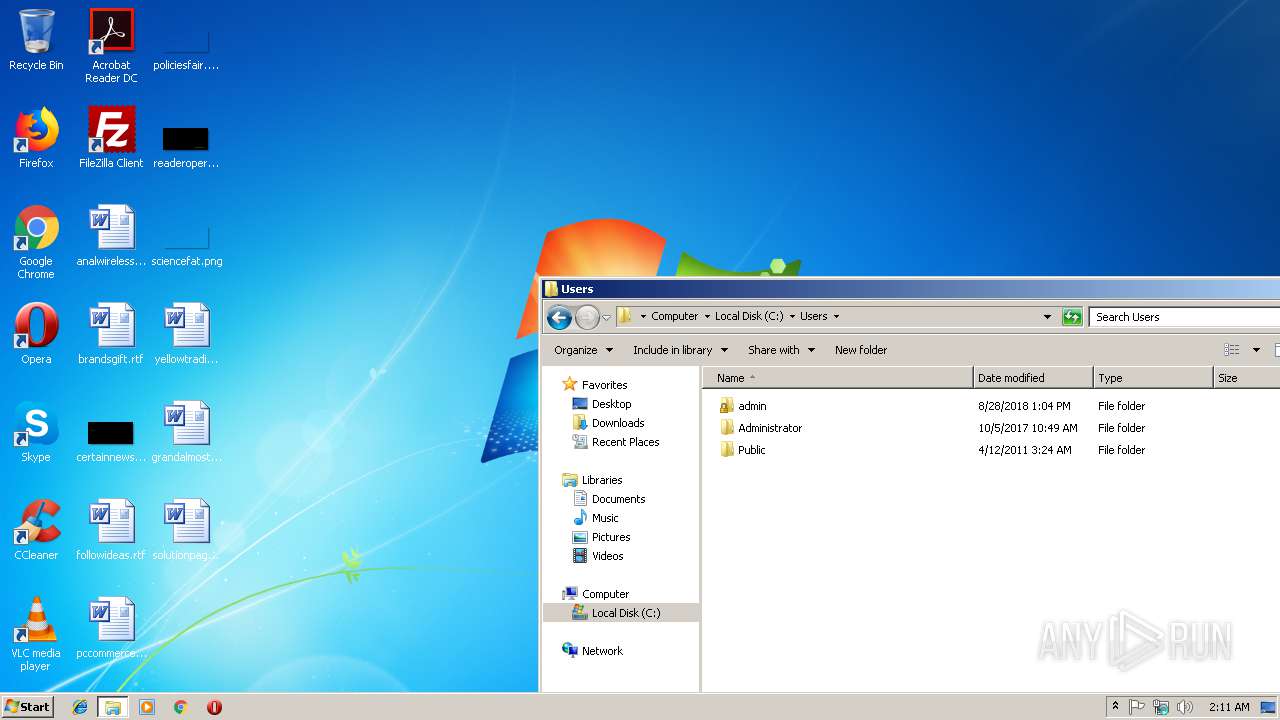
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
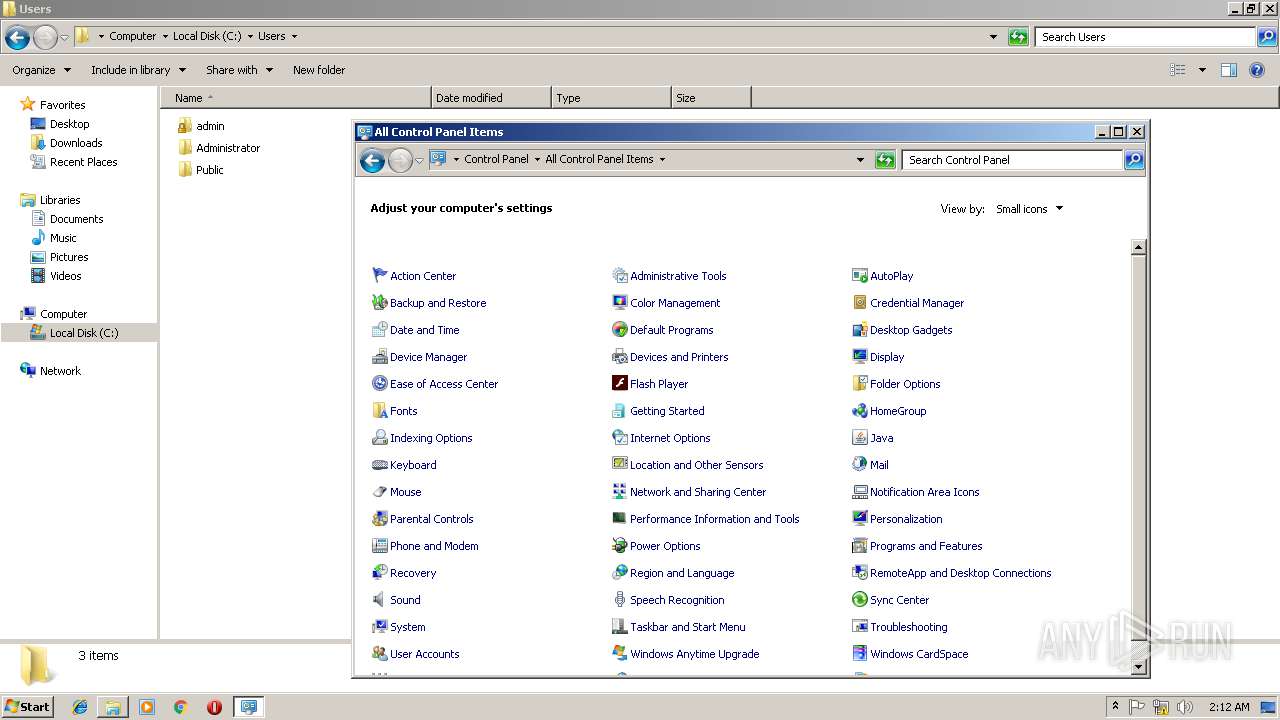
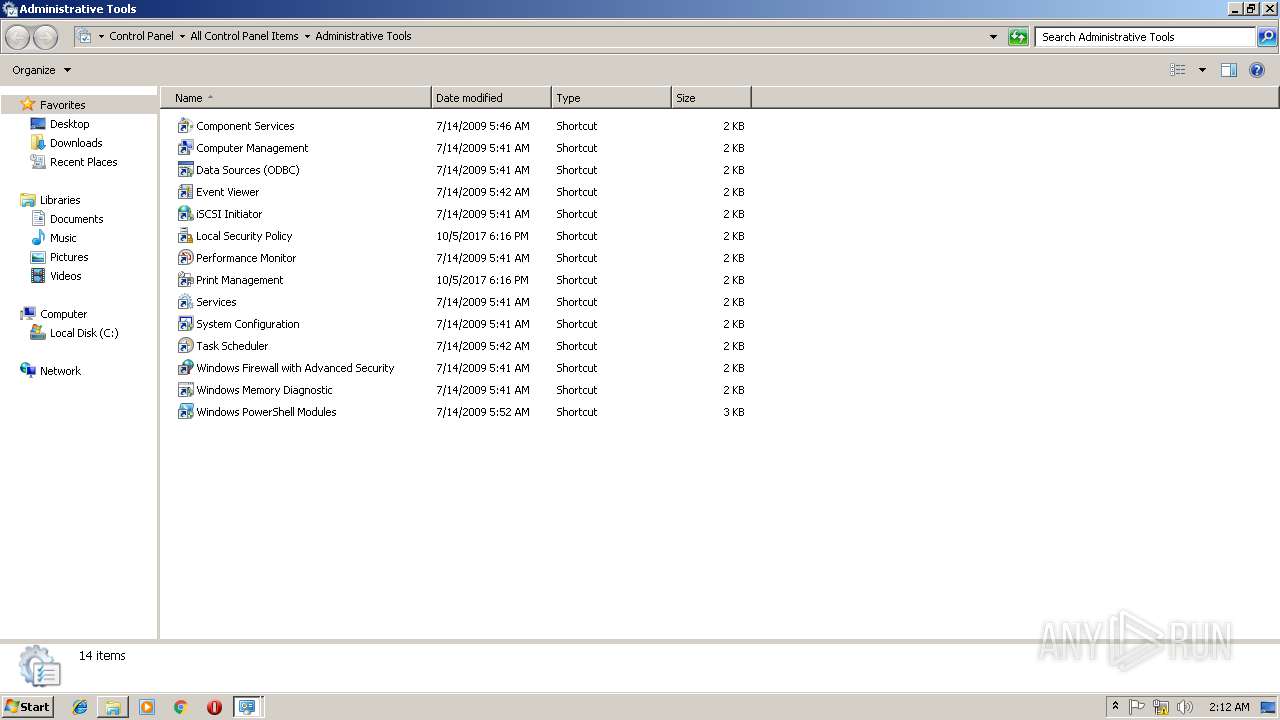
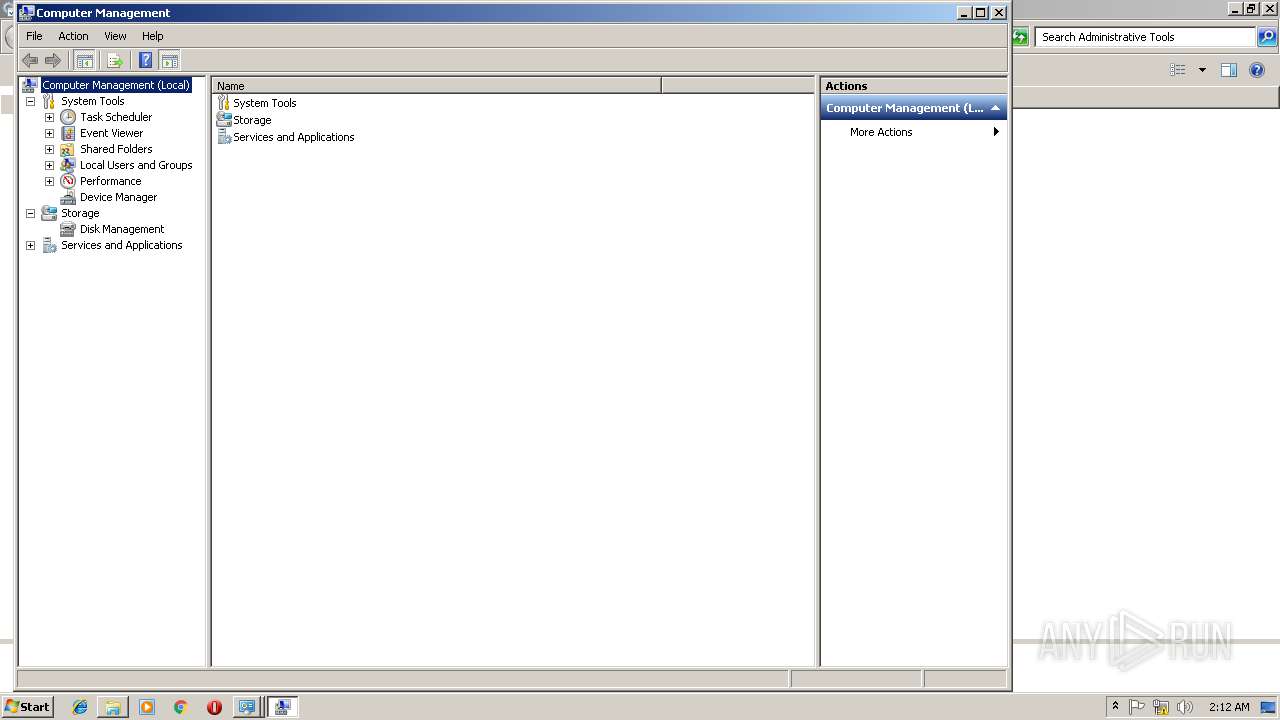
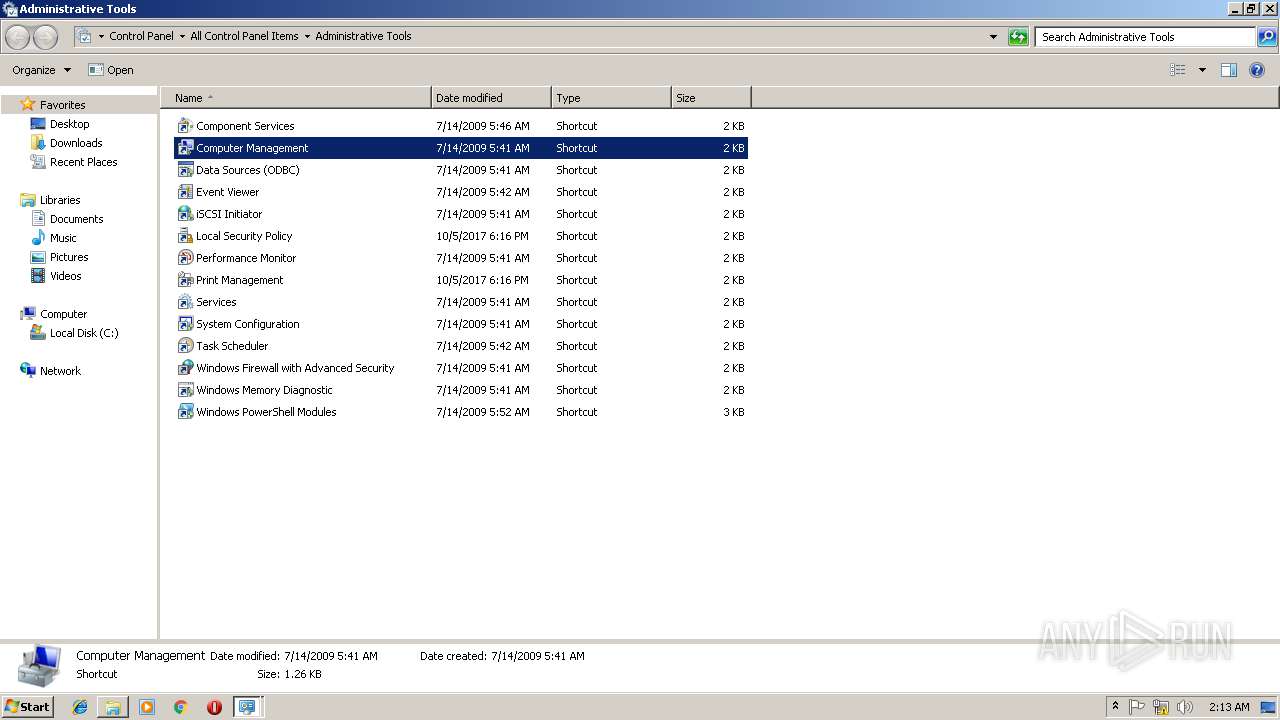
| 1940 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\compmgmt.msc" /s | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3480 | "C:\Users\admin\AppData\Local\Temp\Vidar Binary.exe" | C:\Users\admin\AppData\Local\Temp\Vidar Binary.exe | explorer.exe | ||||||||||||
User: admin Company: Spencer Kimball, Peter Mattis and the GIMP Development Team Integrity Level: MEDIUM Description: Delighters Simulations Retrieve Exit code: 0 Modules
| |||||||||||||||
| 3640 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\compmgmt.msc" /s | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
172
Read events
143
Write events
28
Delete events
1
Modification events
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3480) Vidar Binary.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Vidar Binary_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3480 | Vidar Binary.exe | C:\ProgramData\WJAUQKSZG87YG1ZX6Y7R\files\outlook.txt | text | |
MD5:— | SHA256:— | |||
| 3480 | Vidar Binary.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\line[1].txt | text | |
MD5:— | SHA256:— | |||
| 3480 | Vidar Binary.exe | C:\ProgramData\WJAUQKSZG87YG1ZX6Y7R\files\information.txt | text | |
MD5:— | SHA256:— | |||
| 3480 | Vidar Binary.exe | C:\ProgramData\WJAUQKSZG87YG1ZX6Y7R\ld | sqlite | |
MD5:— | SHA256:— | |||
| 3480 | Vidar Binary.exe | C:\ProgramData\WJAUQKSZG87YG1ZX6Y7R\NL_90059c37-1320-41a4-b58d-2b75a9850d2f6392352522.zip | compressed | |
MD5:— | SHA256:— | |||
| 3480 | Vidar Binary.exe | C:\ProgramData\WJAUQKSZG87YG1ZX6Y7R\files\passwords.txt | text | |
MD5:E0EE1892004A327AE8878494352A35E6 | SHA256:E1B782EB670A6D8ED01FEB9CD9DDEF9AE20569B72A1E33E078906D07627F7850 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3480 | Vidar Binary.exe | POST | 200 | 185.194.141.58:80 | http://ip-api.com/line/ | DE | text | 171 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | Vidar Binary.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kolobkoproms.ug |
| malicious |
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3480 | Vidar Binary.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3480 | Vidar Binary.exe | A Network Trojan was detected | MALWARE [PTsecurity] Generic.PWS.Arkei Stealers Header (Vidar) |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
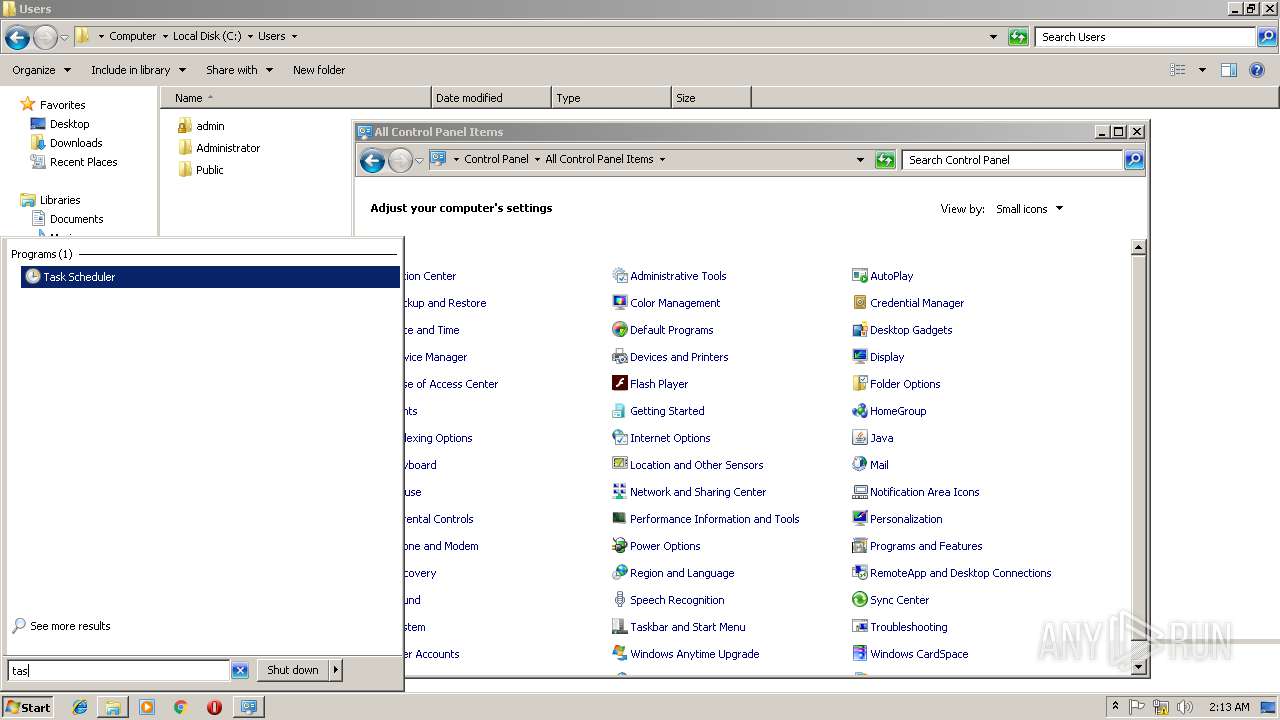
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerExtension
|