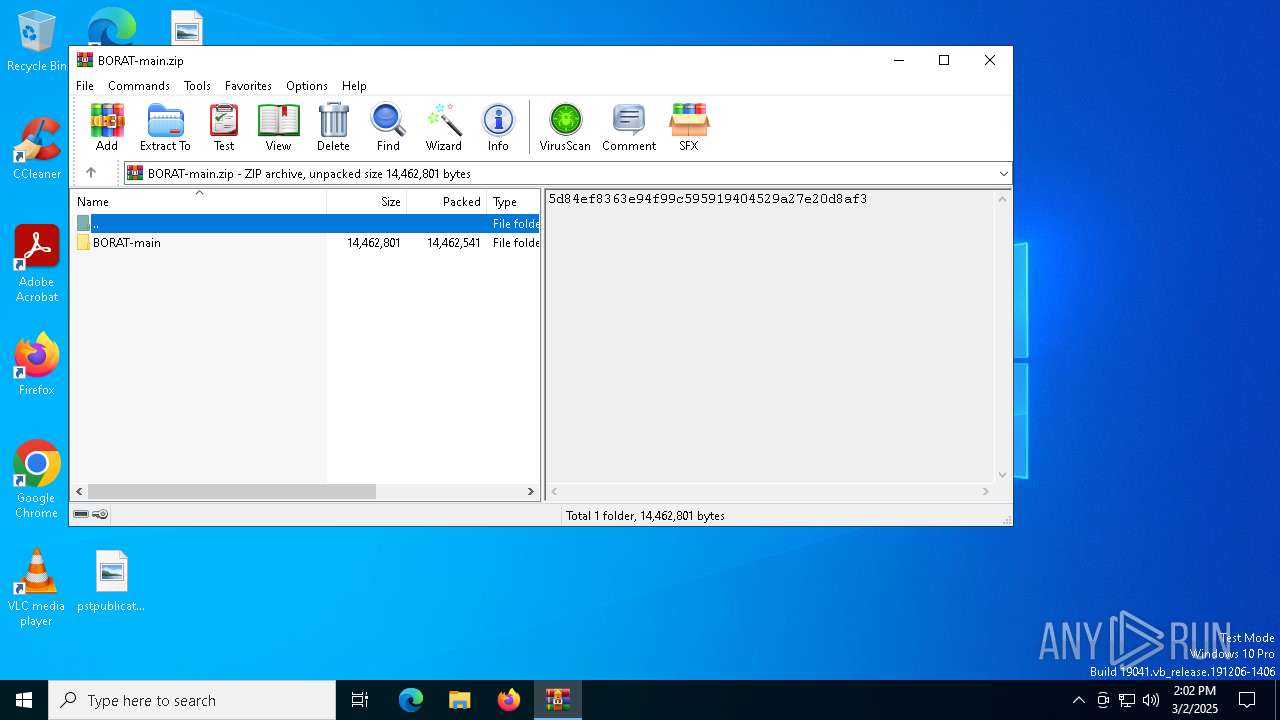
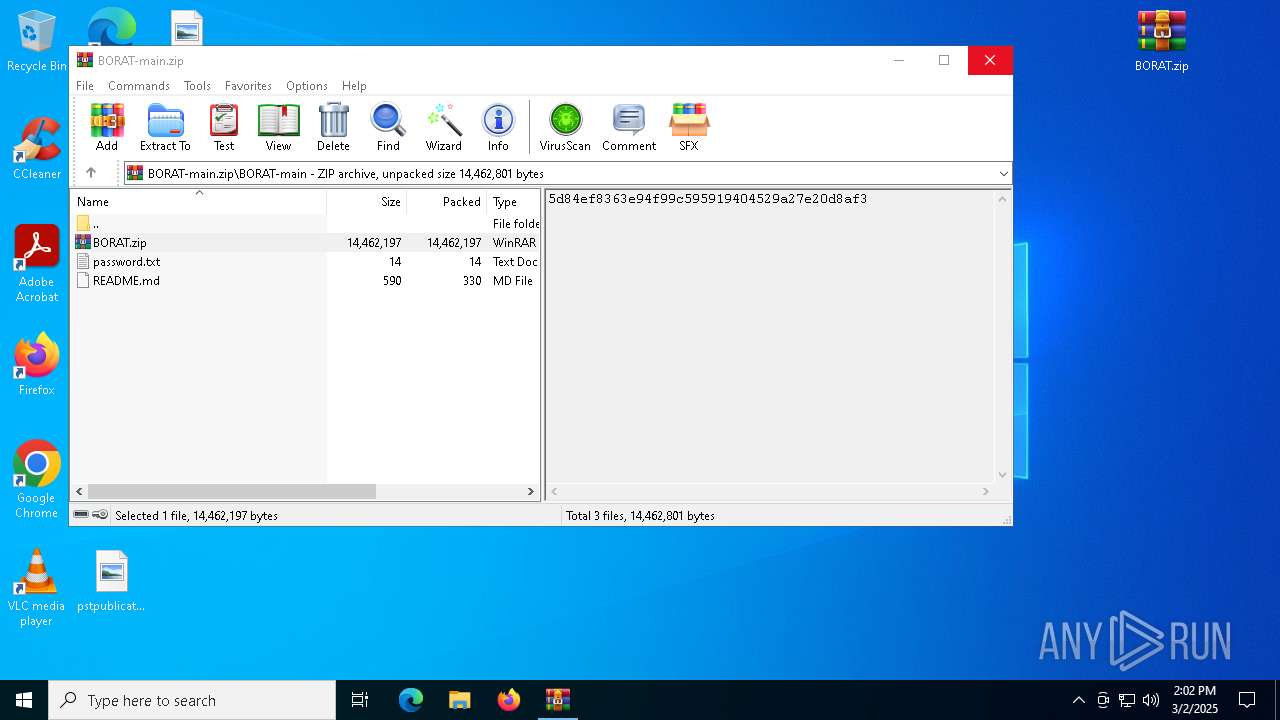
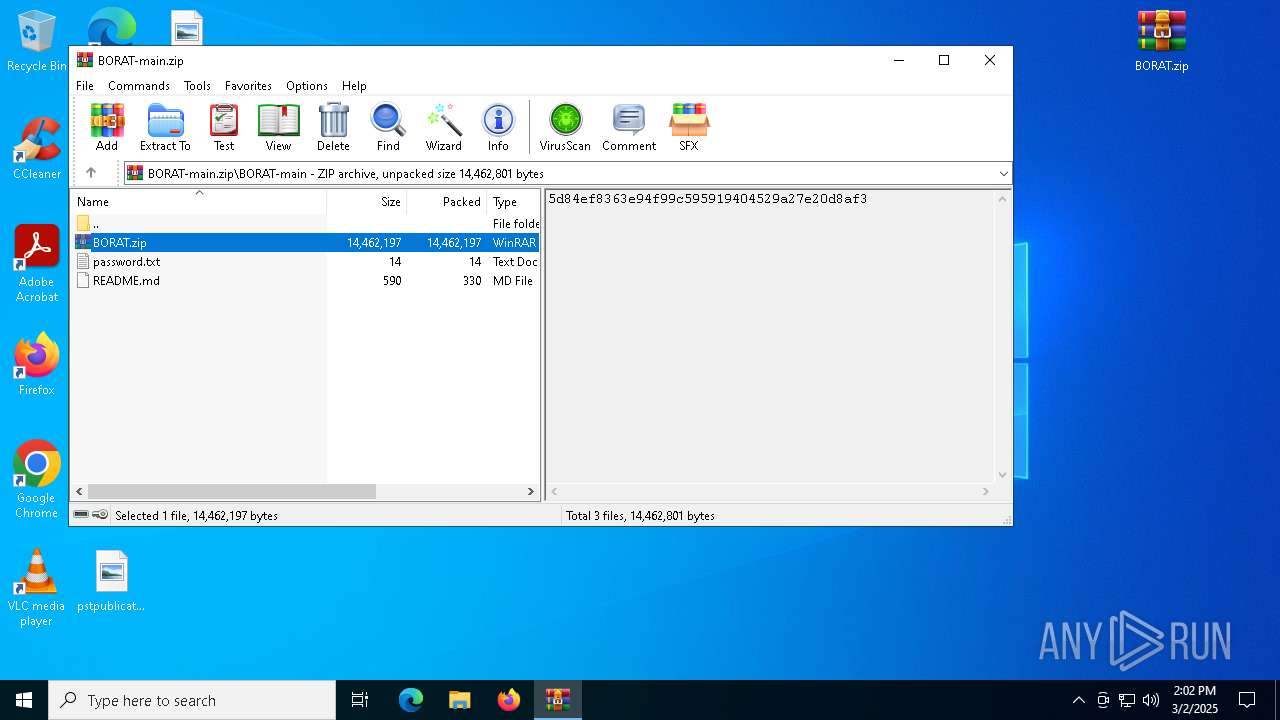
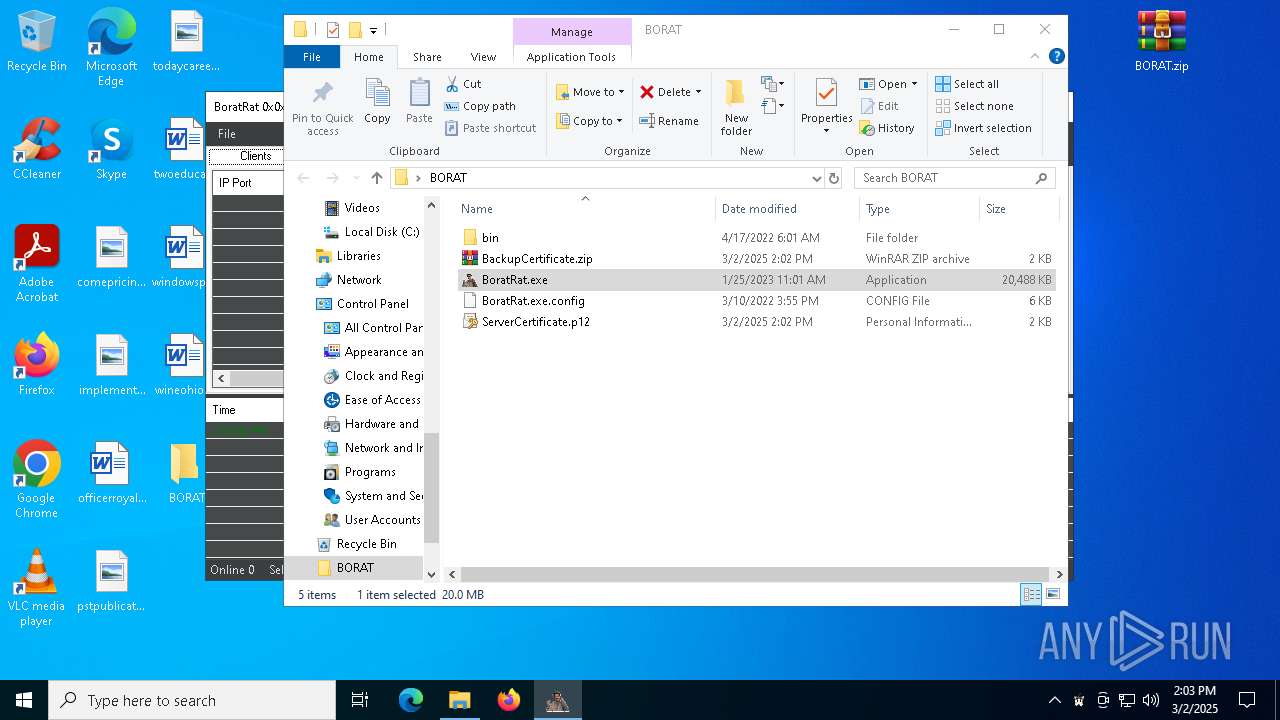
| File name: | BORAT-main.zip |
| Full analysis: | https://app.any.run/tasks/bb9d7151-3d5e-4731-96b7-4ea54f4d9bec |
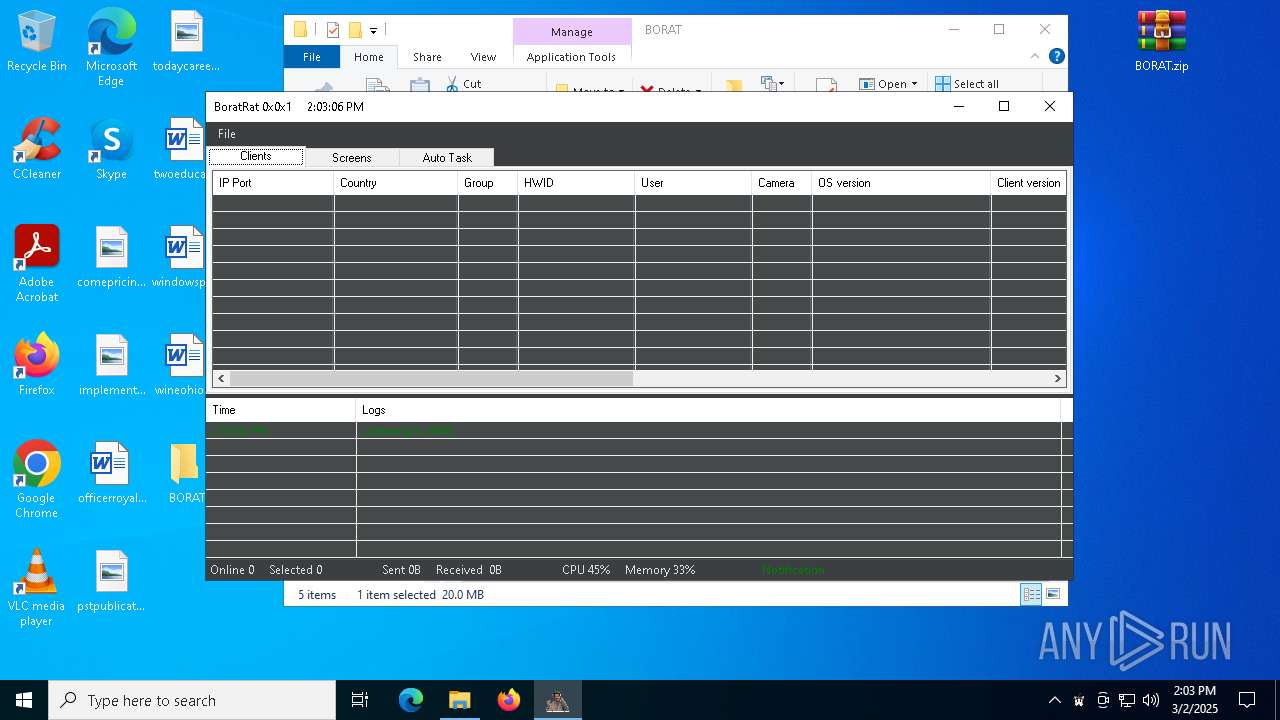
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 02, 2025, 14:02:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 3B9307E06439FEBE3E03944137D080D0 |
| SHA1: | 47B2616AE3FE2354829891A92742749BBCF913C0 |
| SHA256: | E9937032474F980B76234AD658D7F7DCBDBFC7104FA33FAD4ACC2E159F5E3E5B |
| SSDEEP: | 196608:sCIVHR3oKYepwGro3yg5TlhBfPlPIT+LX9RsY:sCIVHR3oKRpwx3ygRlvfPqyX9/ |
MALICIOUS
ASYNCRAT has been detected (YARA)
- BoratRat.exe (PID: 3268)
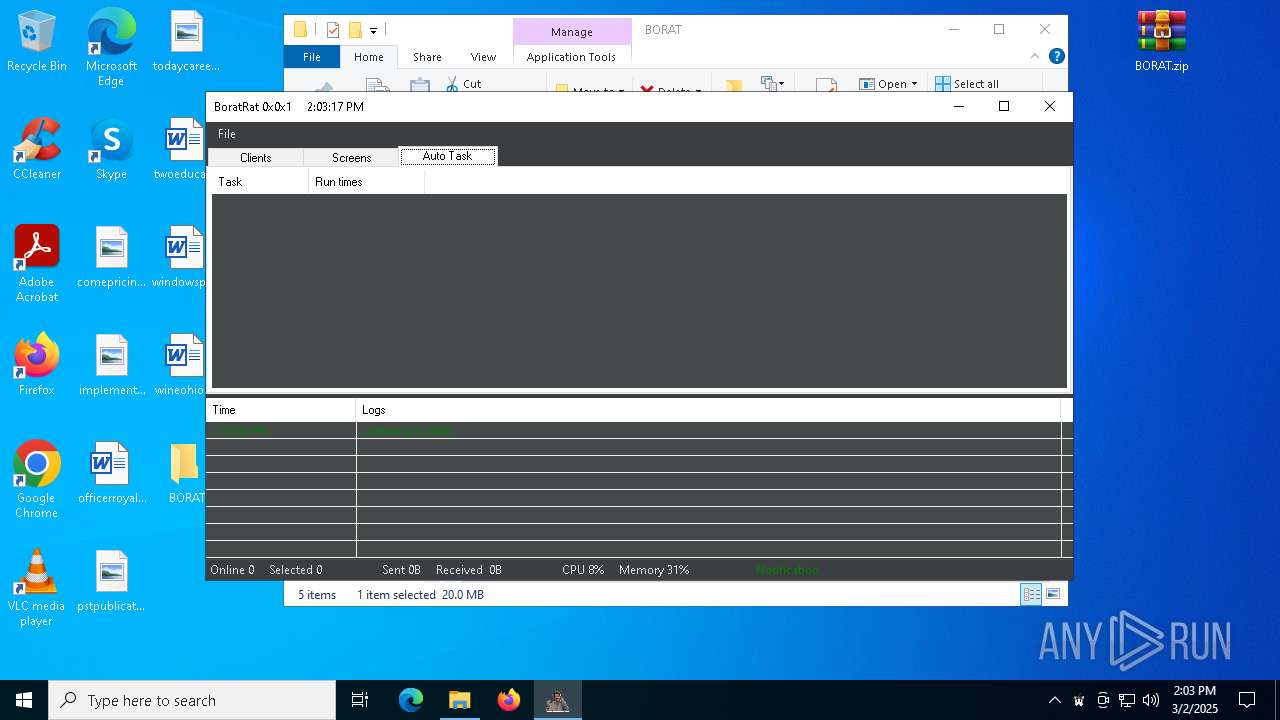
Bypass execution policy to execute commands
- powershell.exe (PID: 5116)
Changes the autorun value in the registry
- reg.exe (PID: 6576)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 5640)
SUSPICIOUS
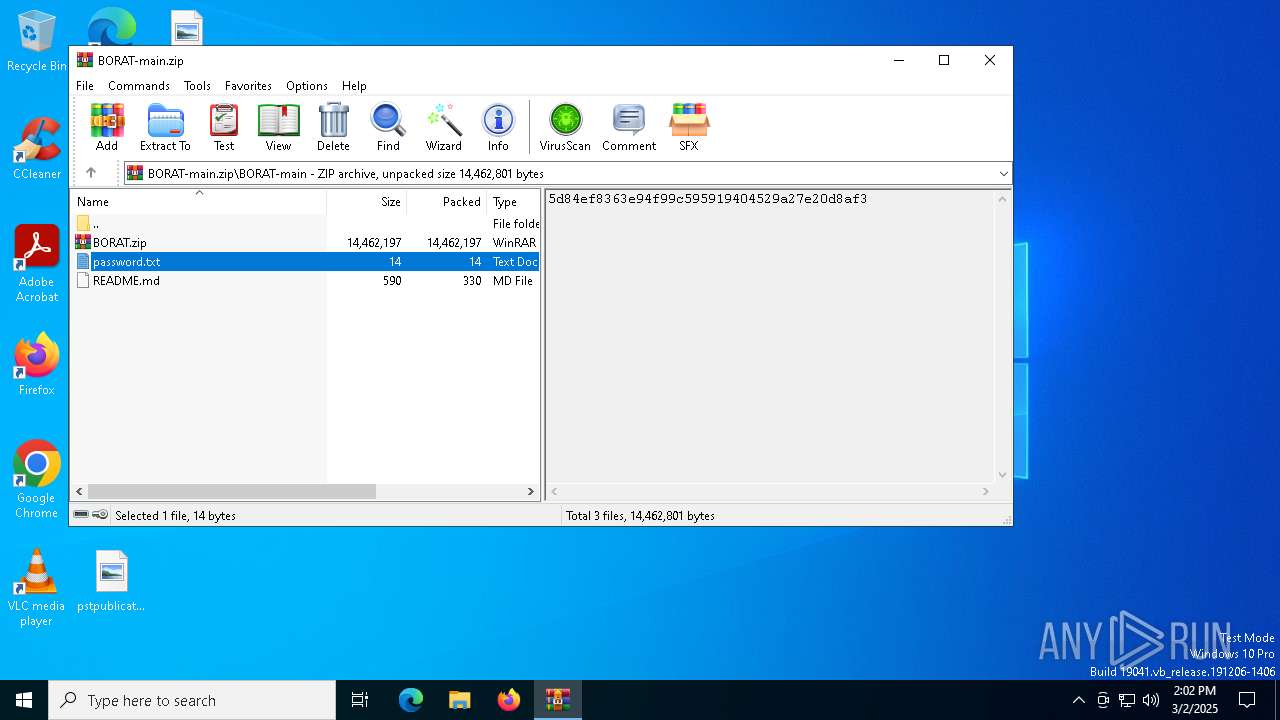
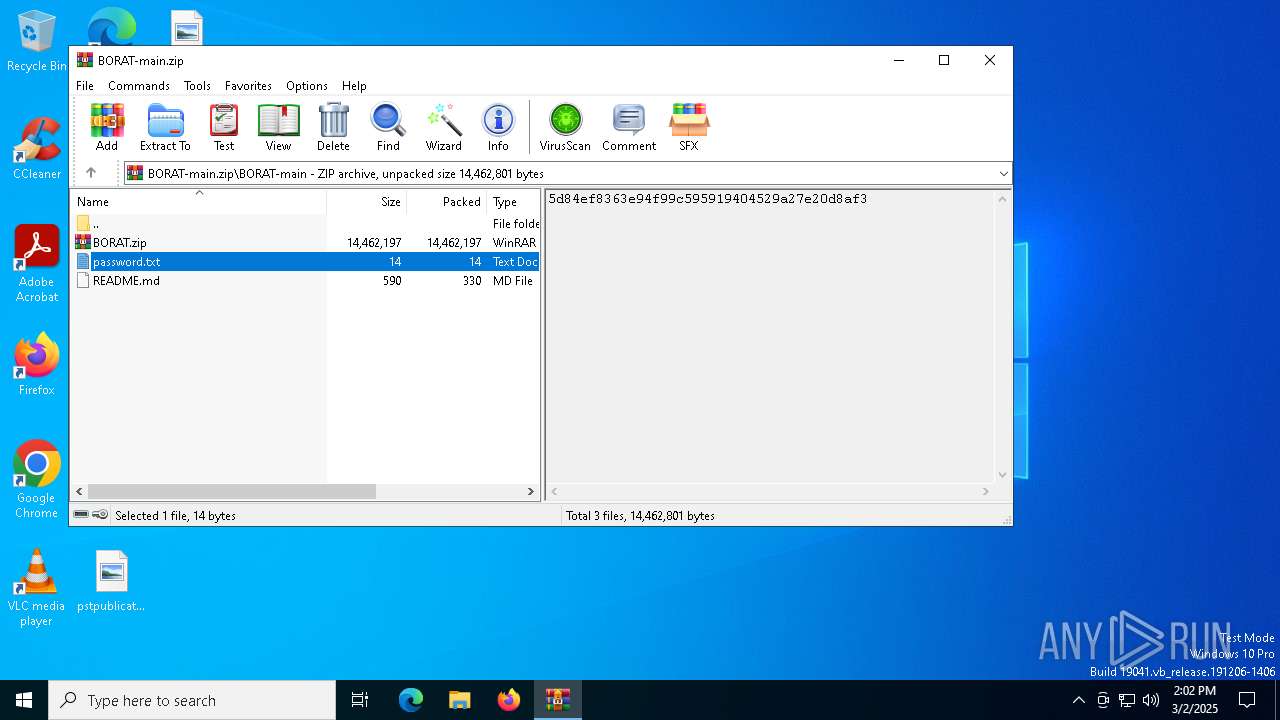
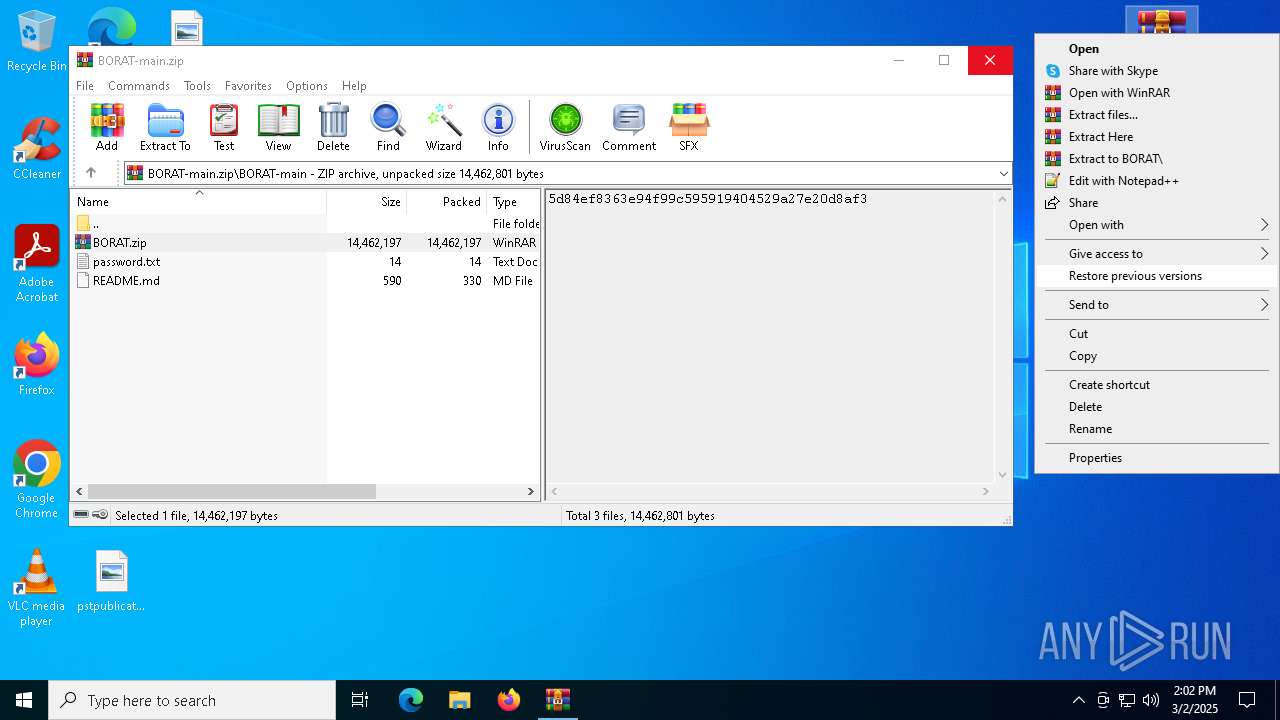
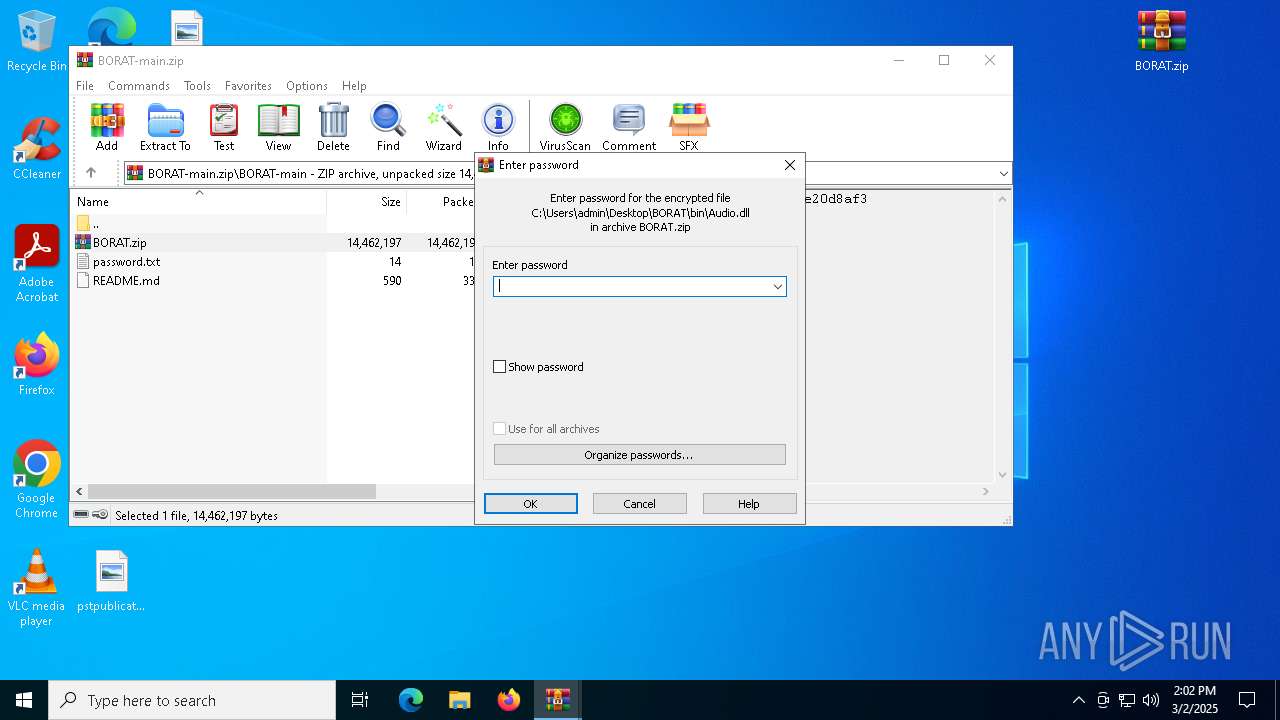
Generic archive extractor
- WinRAR.exe (PID: 3888)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3888)
- BoratRat.exe (PID: 3268)
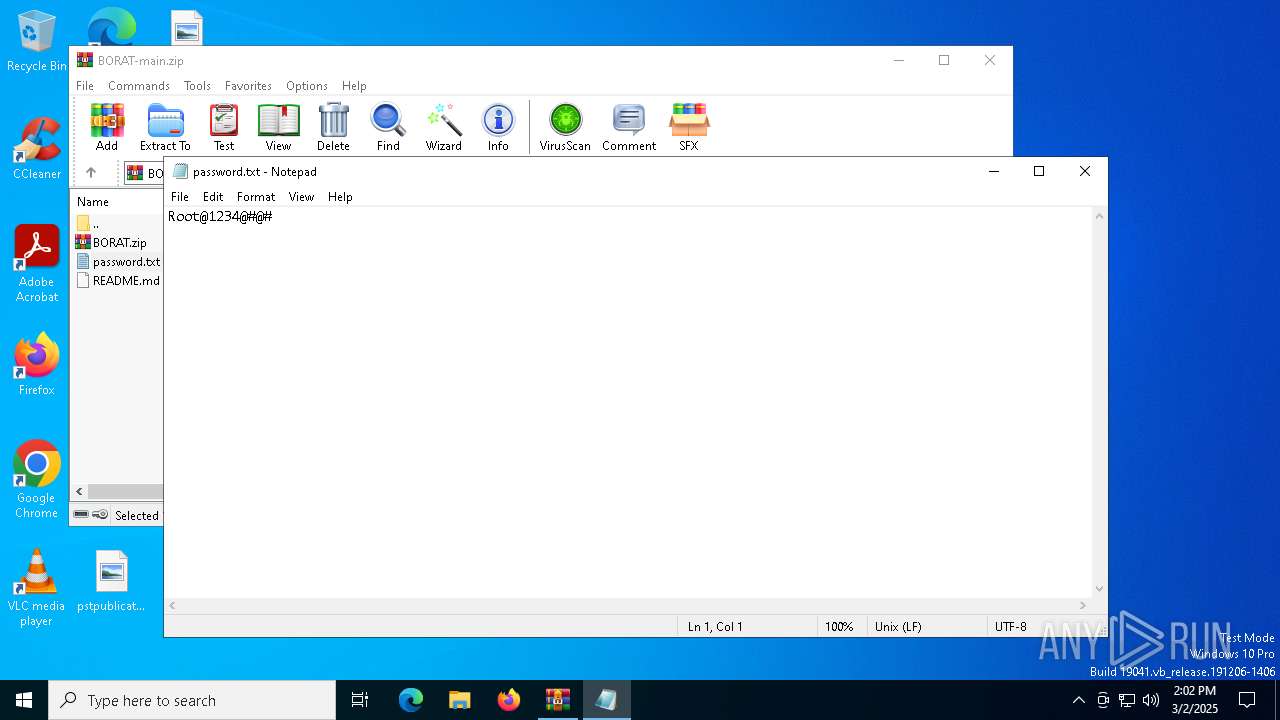
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 3888)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 208)
The process checks if it is being run in the virtual environment
- BoratRat.exe (PID: 3268)
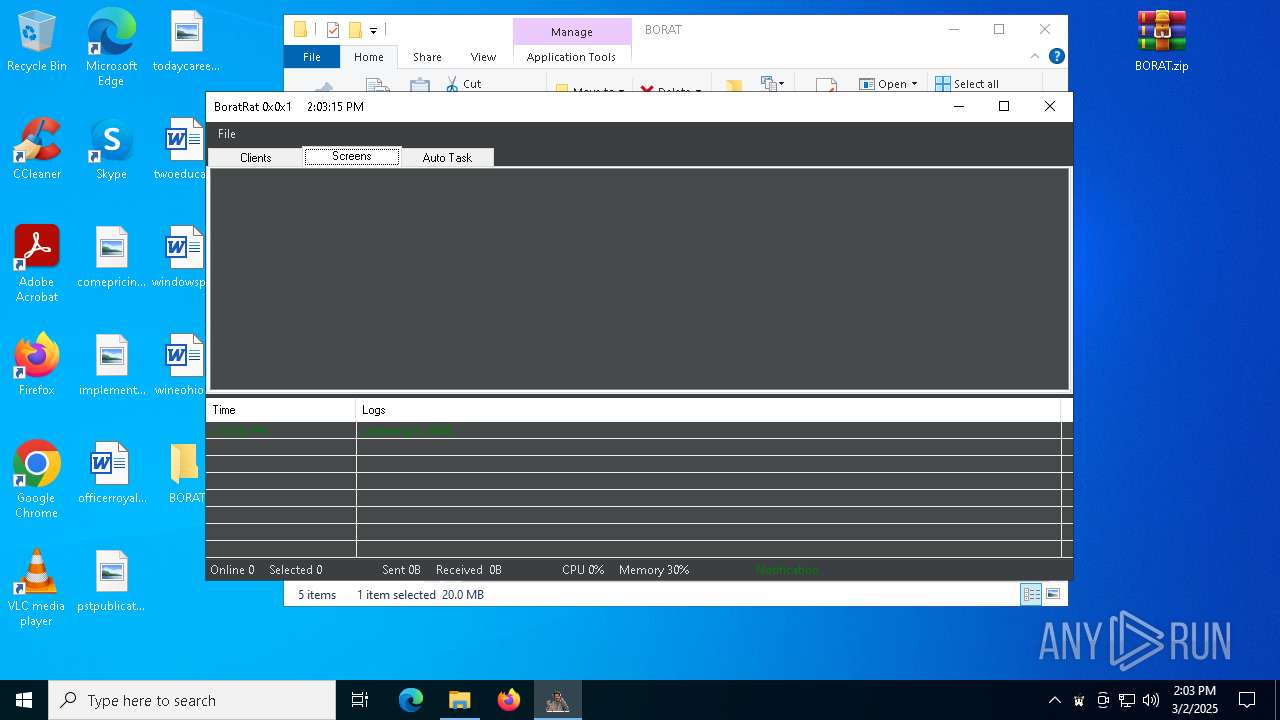
There is functionality for taking screenshot (YARA)
- BoratRat.exe (PID: 3268)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5640)
Reads the date of Windows installation
- BoratRat.exe (PID: 3268)
Likely accesses (executes) a file from the Public directory
- wscript.exe (PID: 5640)
- attrib.exe (PID: 4008)
- attrib.exe (PID: 4448)
- reg.exe (PID: 6576)
- cmd.exe (PID: 4228)
The process executes VB scripts
- BoratRat.exe (PID: 3268)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5640)
Uses ATTRIB.EXE to modify file attributes
- powershell.exe (PID: 5116)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 5116)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 5116)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5116)
Base64-obfuscated command line is found
- wscript.exe (PID: 5640)
BASE64 encoded PowerShell command has been detected
- wscript.exe (PID: 5640)
INFO
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 4628)
- BoratRat.exe (PID: 3268)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 4628)
- powershell.exe (PID: 5116)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 4628)
- BackgroundTransferHost.exe (PID: 4164)
- BackgroundTransferHost.exe (PID: 4024)
- BackgroundTransferHost.exe (PID: 744)
- notepad.exe (PID: 2236)
- BackgroundTransferHost.exe (PID: 4068)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4628)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 3888)
- BoratRat.exe (PID: 3268)
Manual execution by a user
- WinRAR.exe (PID: 208)
- BoratRat.exe (PID: 3268)
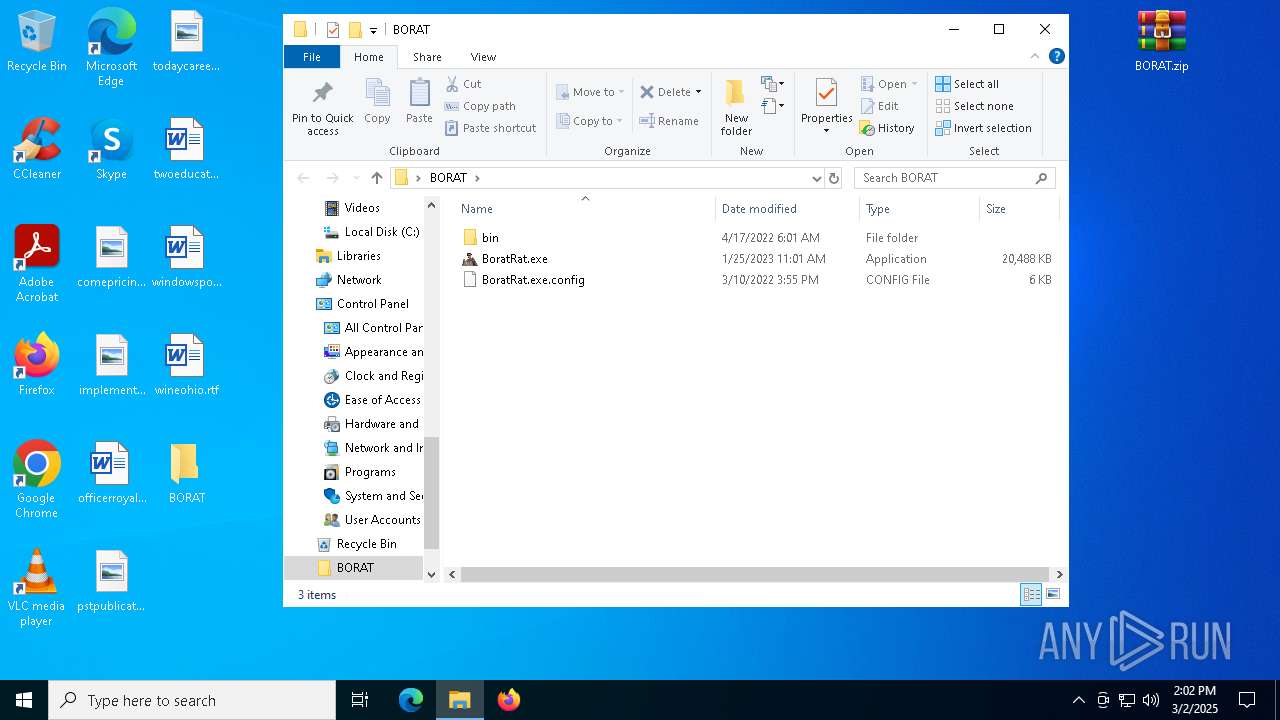
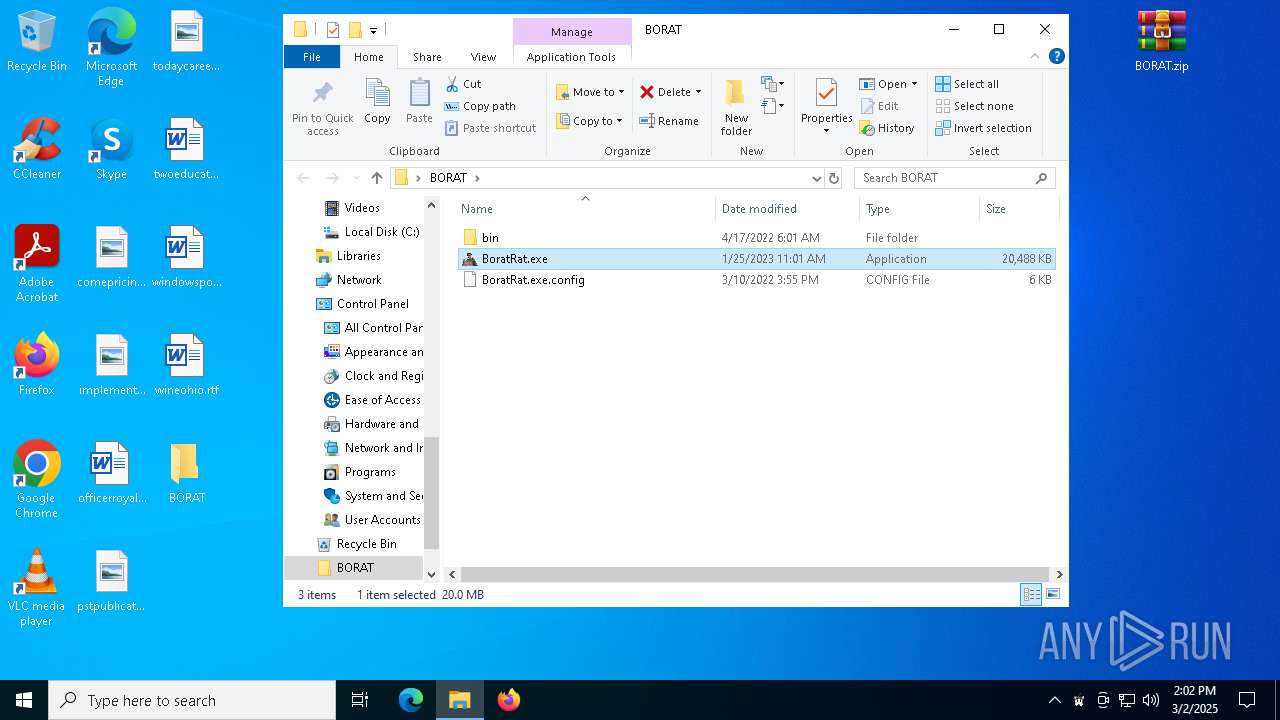
Executable content was dropped or overwritten
- WinRAR.exe (PID: 208)
Checks supported languages
- BoratRat.exe (PID: 3268)
Reads the computer name
- BoratRat.exe (PID: 3268)
Reads the machine GUID from the registry
- BoratRat.exe (PID: 3268)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- BoratRat.exe (PID: 3268)
Found Base64 encoded network access via PowerShell (YARA)
- BoratRat.exe (PID: 3268)
Process checks computer location settings
- BoratRat.exe (PID: 3268)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5116)
Reads Internet Explorer settings
- powershell.exe (PID: 5116)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5116)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5116)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5116)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 5116)
Disables trace logs
- powershell.exe (PID: 5116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:01:25 03:05:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | BORAT-main/ |
Total processes
142
Monitored processes
18
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\BORAT.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 744 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3888.45622\password.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
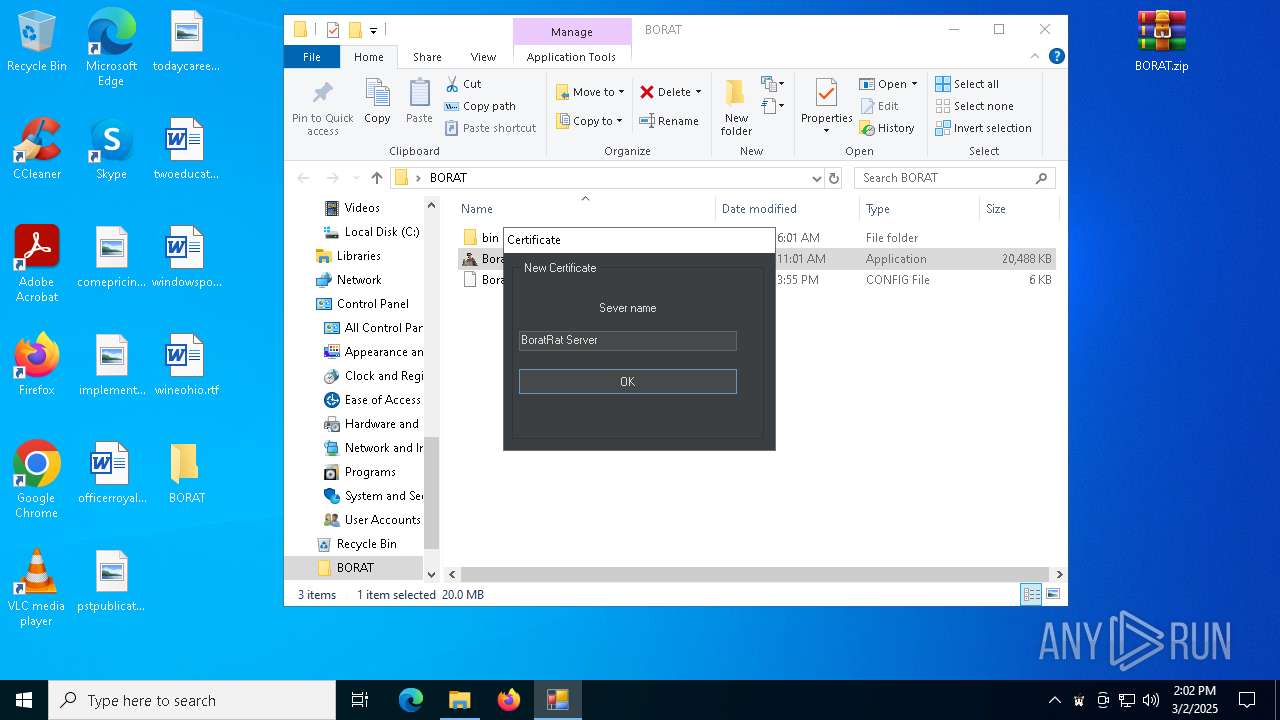
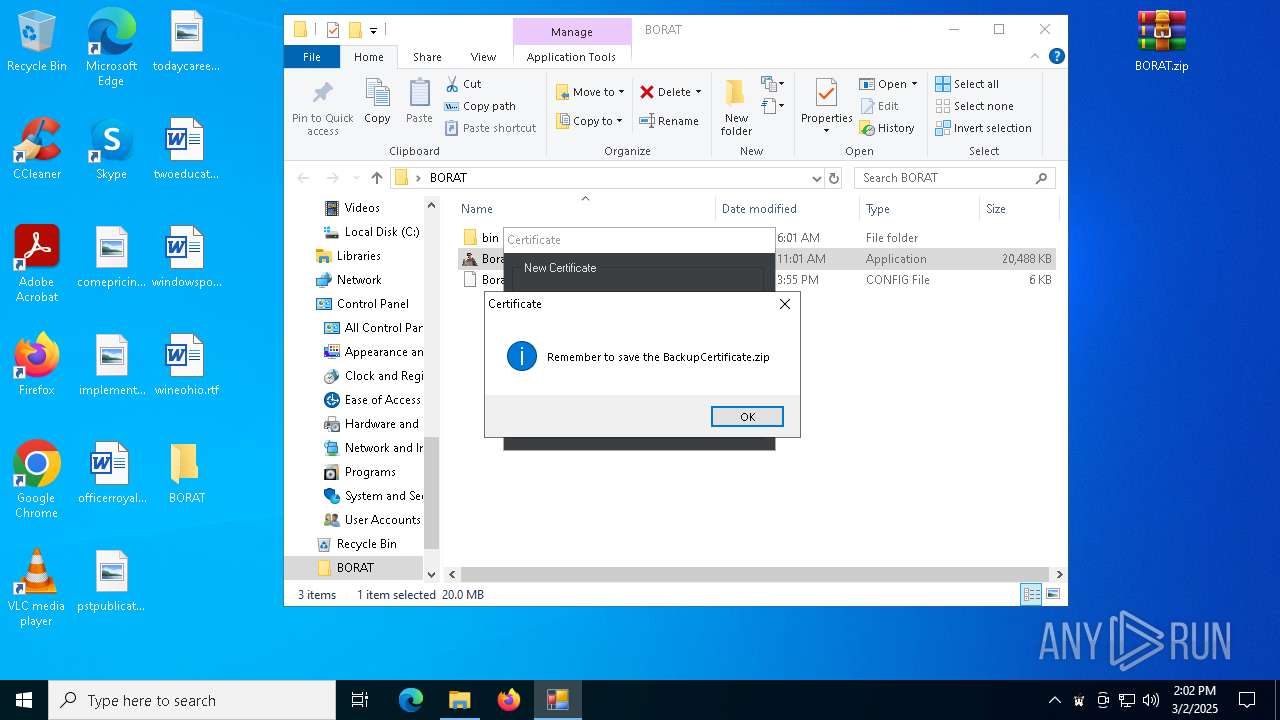
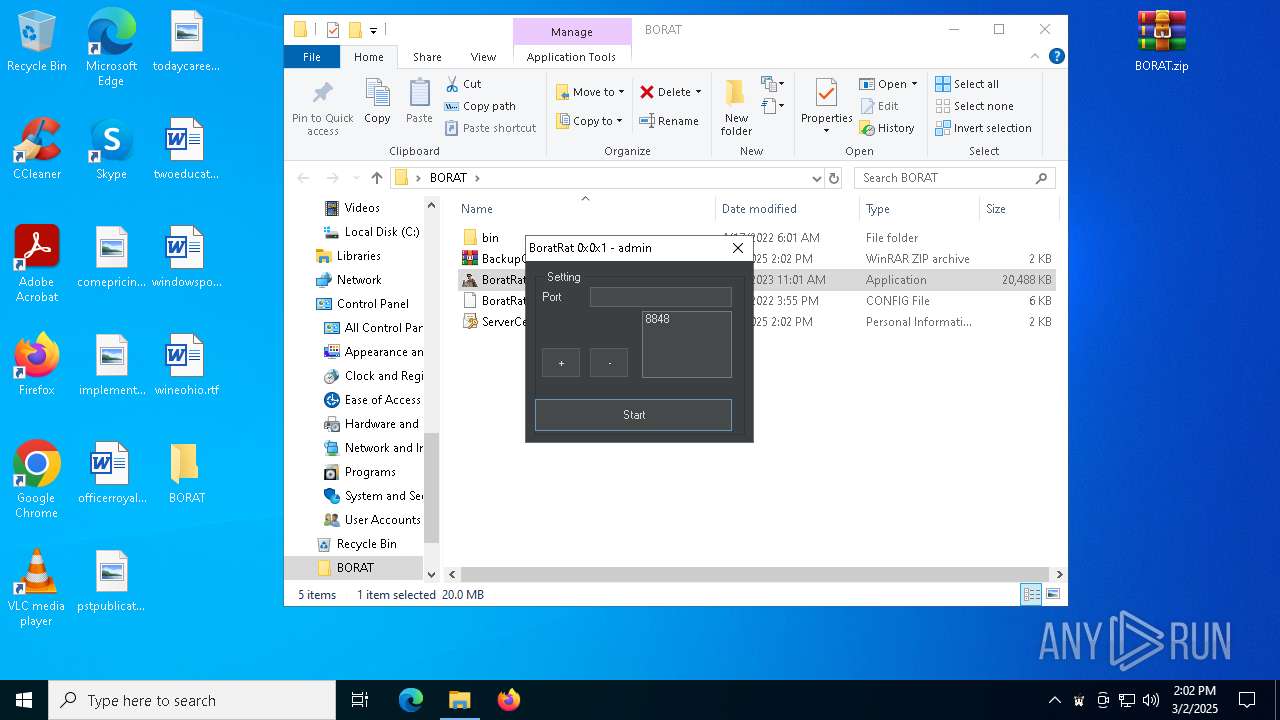
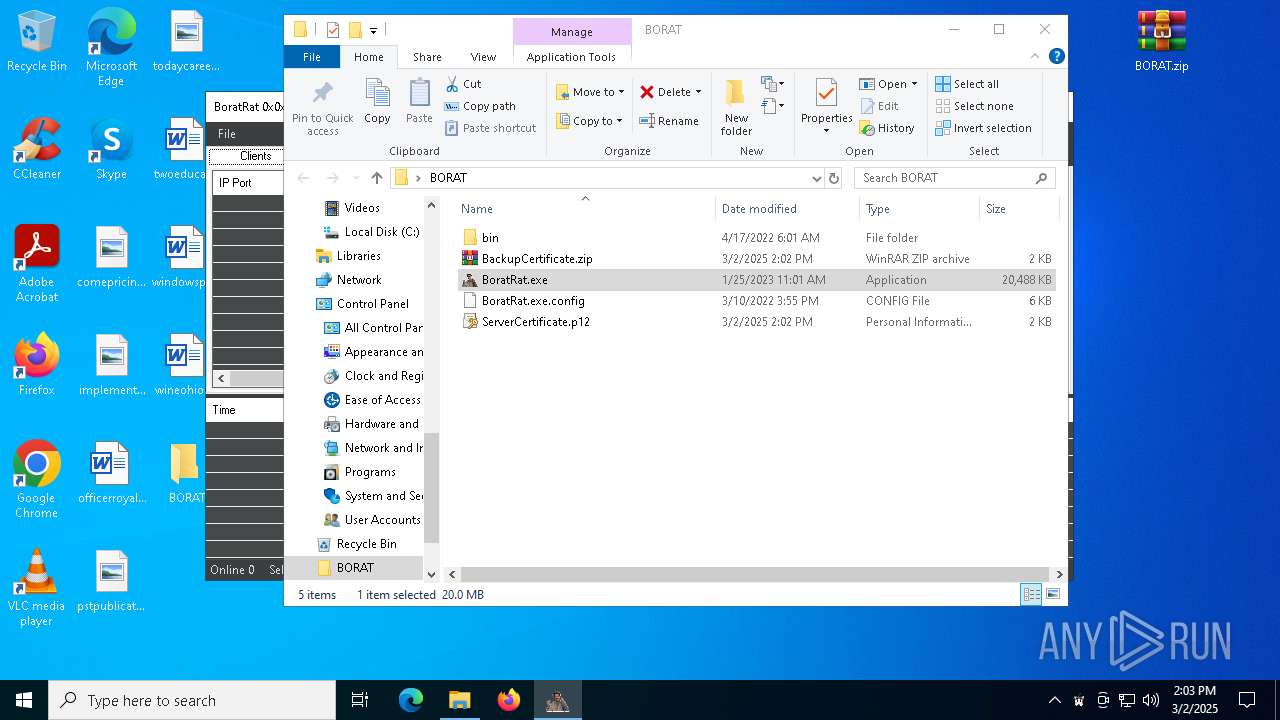
| 3268 | "C:\Users\admin\Desktop\BORAT\BoratRat.exe" | C:\Users\admin\Desktop\BORAT\BoratRat.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BoratRat Version: 1.0.7.0 Modules
| |||||||||||||||
| 3888 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\BORAT-main.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4008 | "C:\WINDOWS\system32\attrib.exe" +h C:\Users\Public\.MicrosoftCorporation\windowupdate.exe | C:\Windows\System32\attrib.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 601
Read events
14 556
Write events
45
Delete events
0
Modification events
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\BORAT-main.zip | |||
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3888) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4164) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4164) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
23
Suspicious files
16
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4628 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\27c01d37-96ce-4e80-b94e-e45f57f139b3.down_data | — | |
MD5:— | SHA256:— | |||
| 208 | WinRAR.exe | C:\Users\admin\Desktop\BORAT\bin\ip2region.db | — | |
MD5:— | SHA256:— | |||
| 4628 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:DC854D138DE7265C8AD76ECC2D10E0C0 | SHA256:CC8DB3E87A2BE481AB87C1E20802F592309745F2DC51B36AB7A8BDDB855B8E88 | |||
| 208 | WinRAR.exe | C:\Users\admin\Desktop\BORAT\bin\Discord.dll | executable | |
MD5:7EE673594BBB20F65448AAB05F1361D0 | SHA256:8FA7634B7DCA1A451CF8940429BE6AD2440821ED04D5D70B6E727E5968E0B5F6 | |||
| 3888 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3888.46455\BORAT-main\BORAT.zip | compressed | |
MD5:61C21E5ABE7107192E4513CA3C4680E0 | SHA256:8E6DA4E62F23E694B6E26FBC7F8AA990D3BD69D2E0025C7B6C837974E31CC227 | |||
| 208 | WinRAR.exe | C:\Users\admin\Desktop\BORAT\bin\MessagePackLib.dll | executable | |
MD5:590B00C87D5FF2FFE09079F0406EB2CD | SHA256:ADB00DEE751B4BA620D3B0E002F5B6D8B89CF63B062F74EC65BBA72294D553D1 | |||
| 208 | WinRAR.exe | C:\Users\admin\Desktop\BORAT\bin\Extra.dll | executable | |
MD5:62C231BAFA469AB04F090FCB4475D360 | SHA256:6A4F32B0228092CE68E8448C6F4B74B4C654F40FB2D462C1D6BBD4B4EF09053D | |||
| 208 | WinRAR.exe | C:\Users\admin\Desktop\BORAT\bin\Fun.dll | executable | |
MD5:499FC6AC30B3B342833C79523BE4A60C | SHA256:DCAC599B1BAB37E1A388AC469E6CC5DE1F35EB02BEAA6778F07A1C090CE3EA04 | |||
| 208 | WinRAR.exe | C:\Users\admin\Desktop\BORAT\bin\Information.dll | executable | |
MD5:87651B12453131DAFD3E91F60D8AEF5A | SHA256:A15D72D990686D06D89D7E11DF2B16BCD5719A40298C19D046FA22C40D56AF44 | |||
| 208 | WinRAR.exe | C:\Users\admin\Desktop\BORAT\bin\FileSearcher.dll | executable | |
MD5:0B7C33C5739903BA4F4B78C446773528 | SHA256:2D9625F41793F62BFE32C10B2D5E05668E321BCAF8B73414B3C31EF677B9BFF4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
27
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4628 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1660 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1660 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5116 | powershell.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAqrPaxeNOdsATKKidSdcMo%3D | unknown | — | — | whitelisted |
5116 | powershell.exe | GET | 200 | 18.66.145.213:80 | http://ocsp.rootca3.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRkNawYMzz%2BjKSfYbTyFR0AXuhs6QQUq7bb1waeN6wwhgeRcMecxBmxeMACEwdzEm3iwvr9LEetiLFWbgGCBG0%3D | unknown | — | — | whitelisted |
5116 | powershell.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5608 | backgroundTaskHost.exe | 20.86.201.138:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4628 | BackgroundTransferHost.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4628 | BackgroundTransferHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1660 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1660 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5116 | powershell.exe | Misc activity | ET INFO DropBox User Content Domain (dl .dropboxusercontent .com in TLS SNI) |