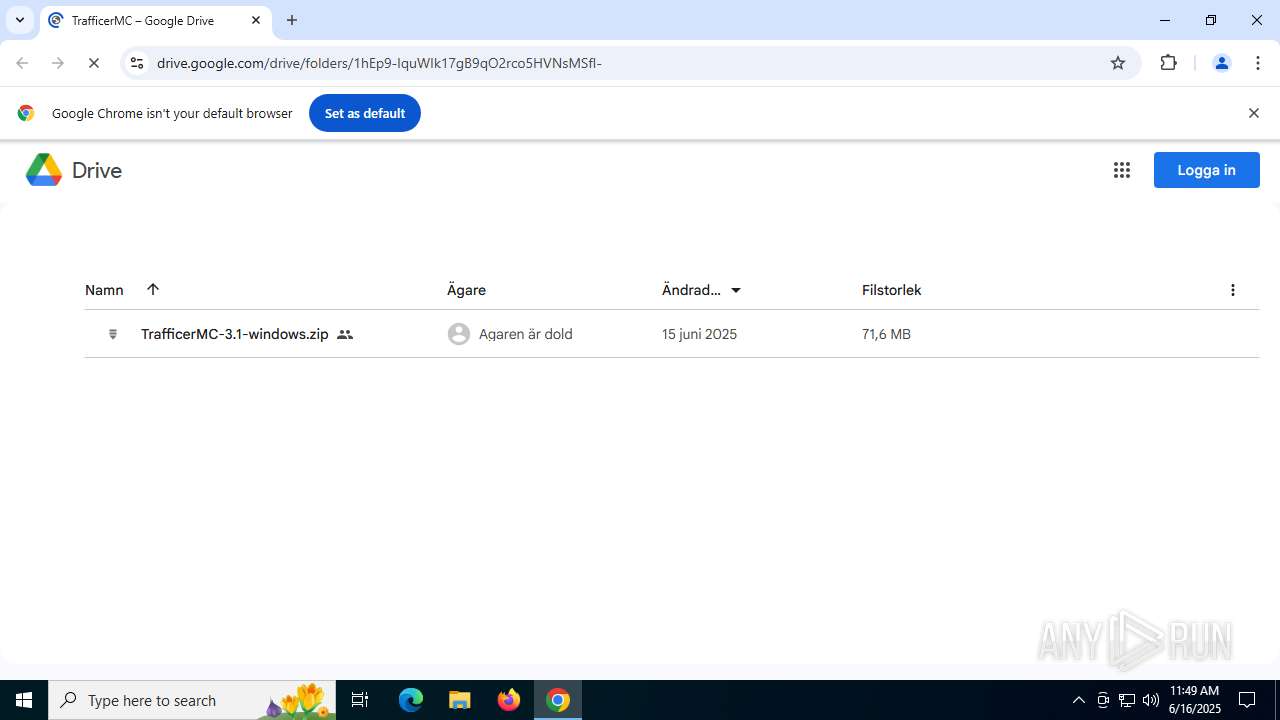
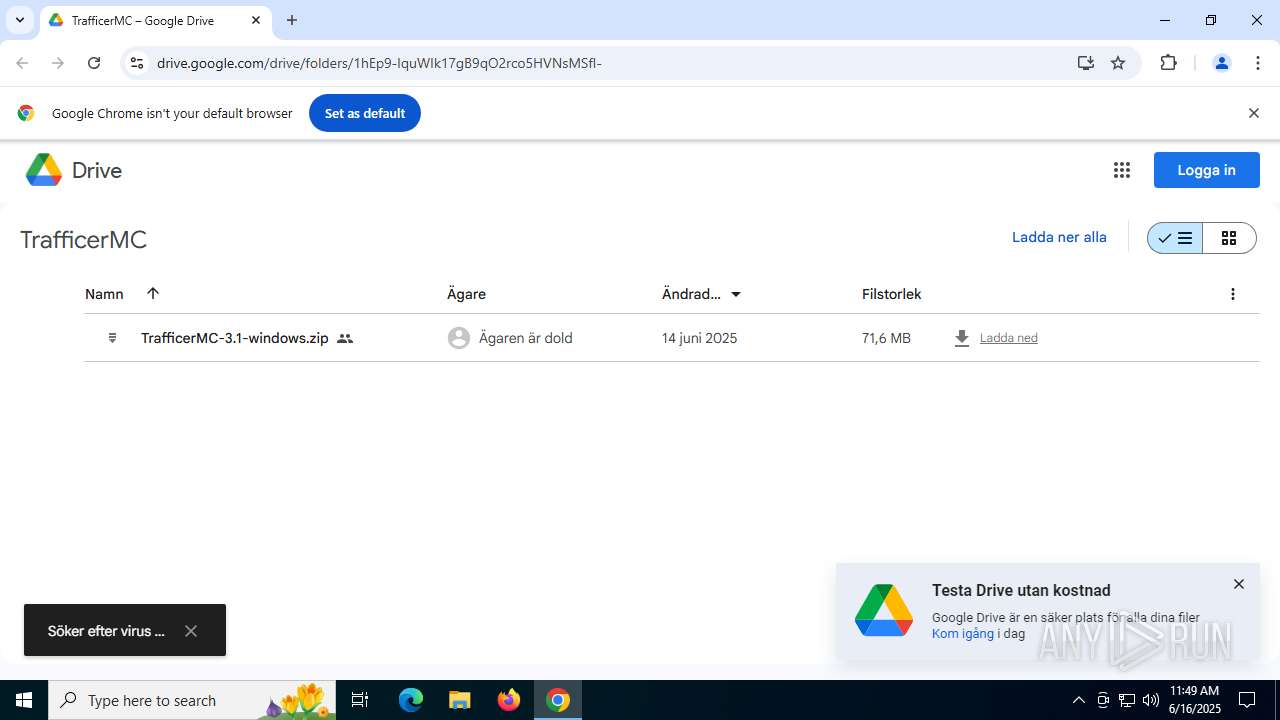
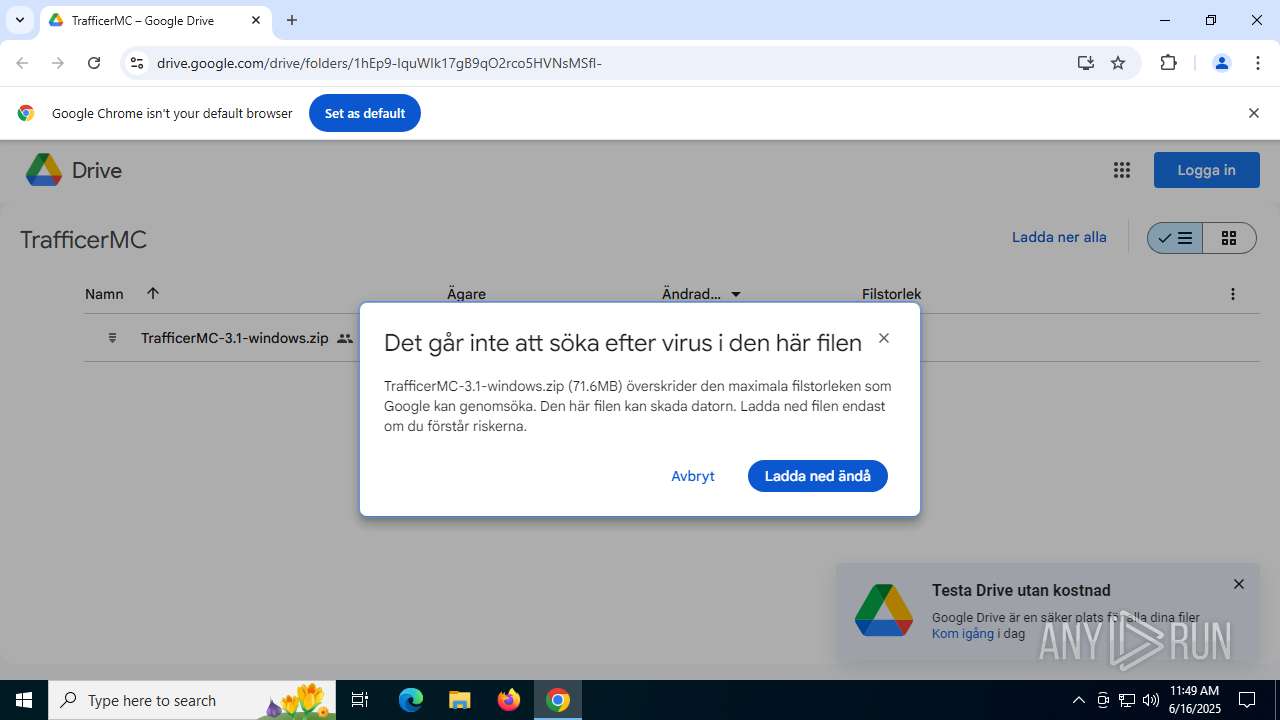
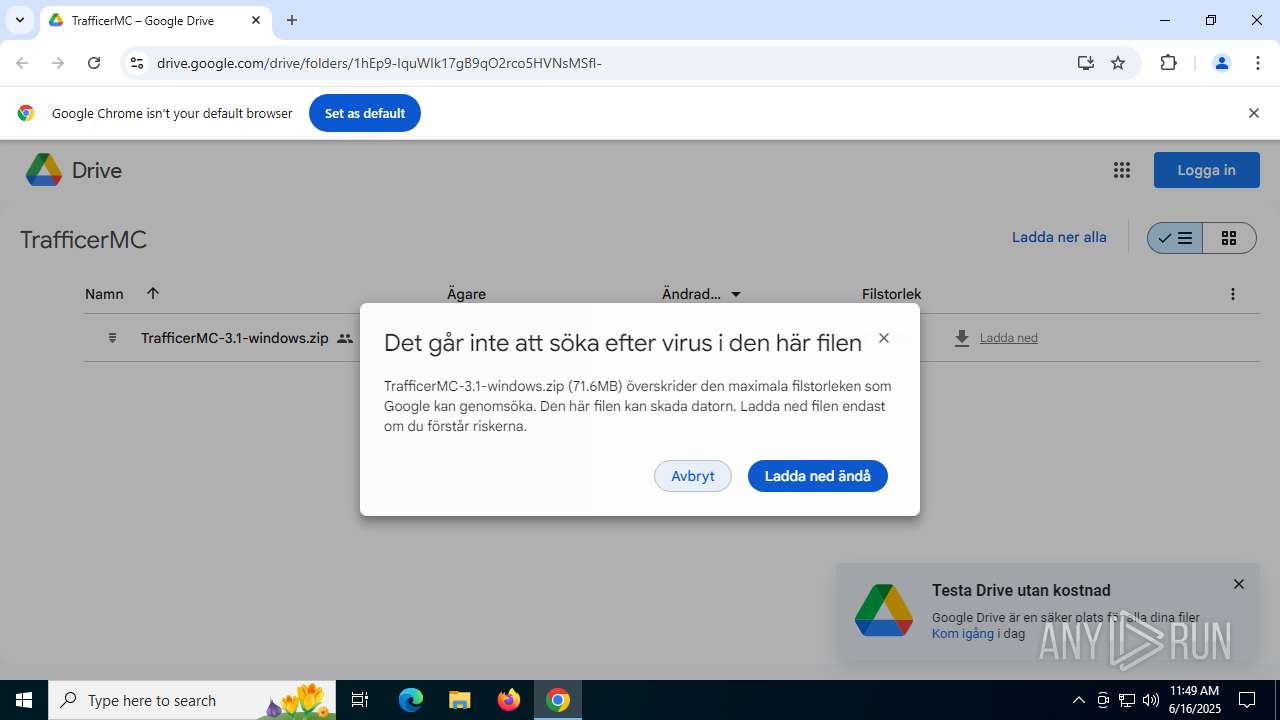
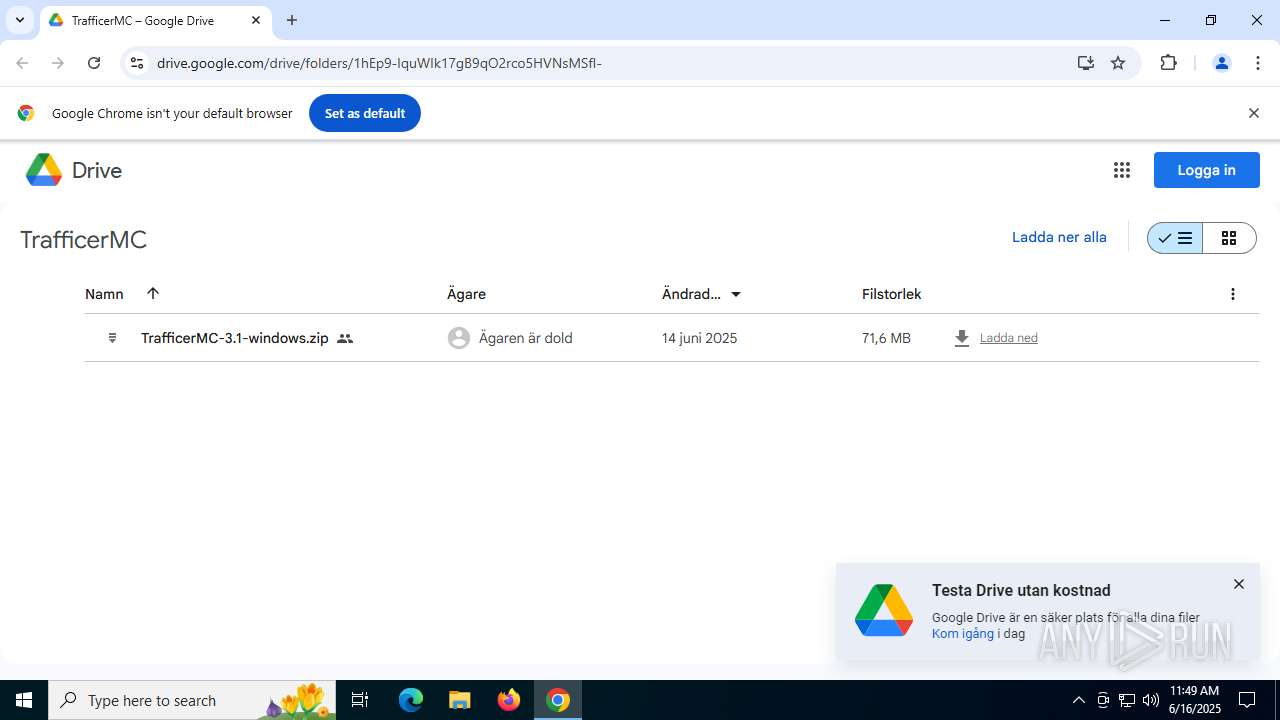
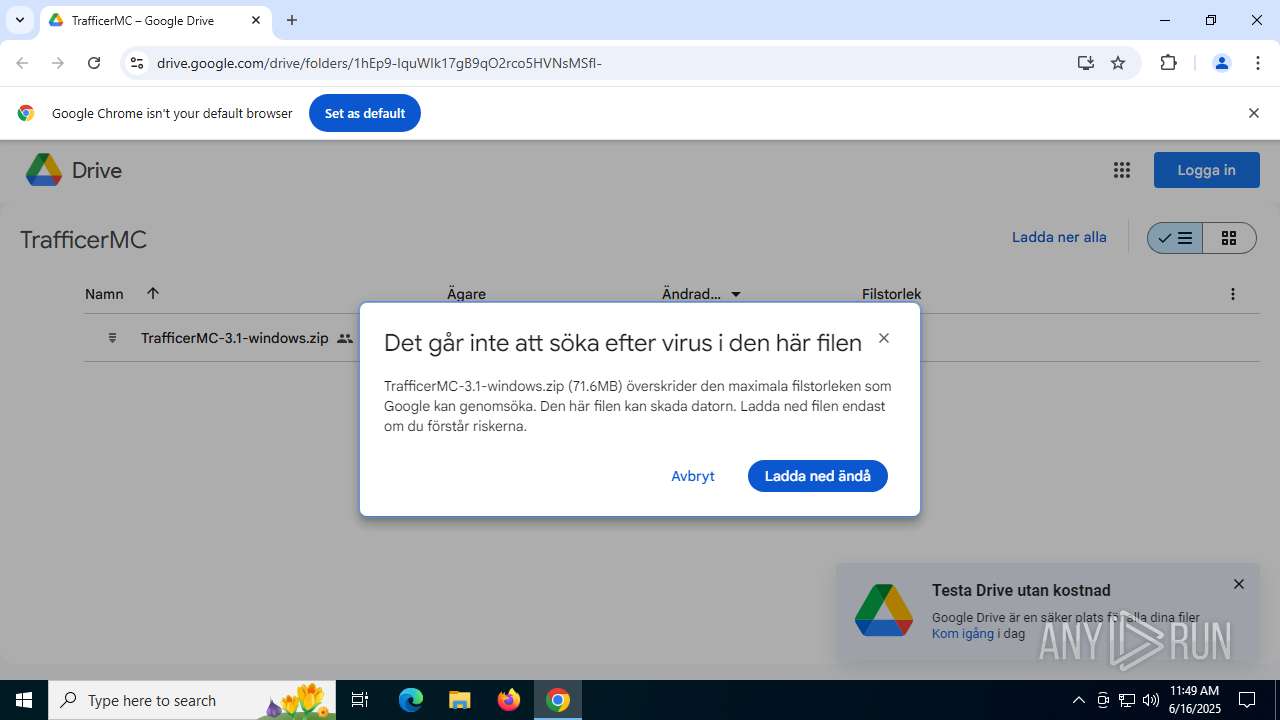
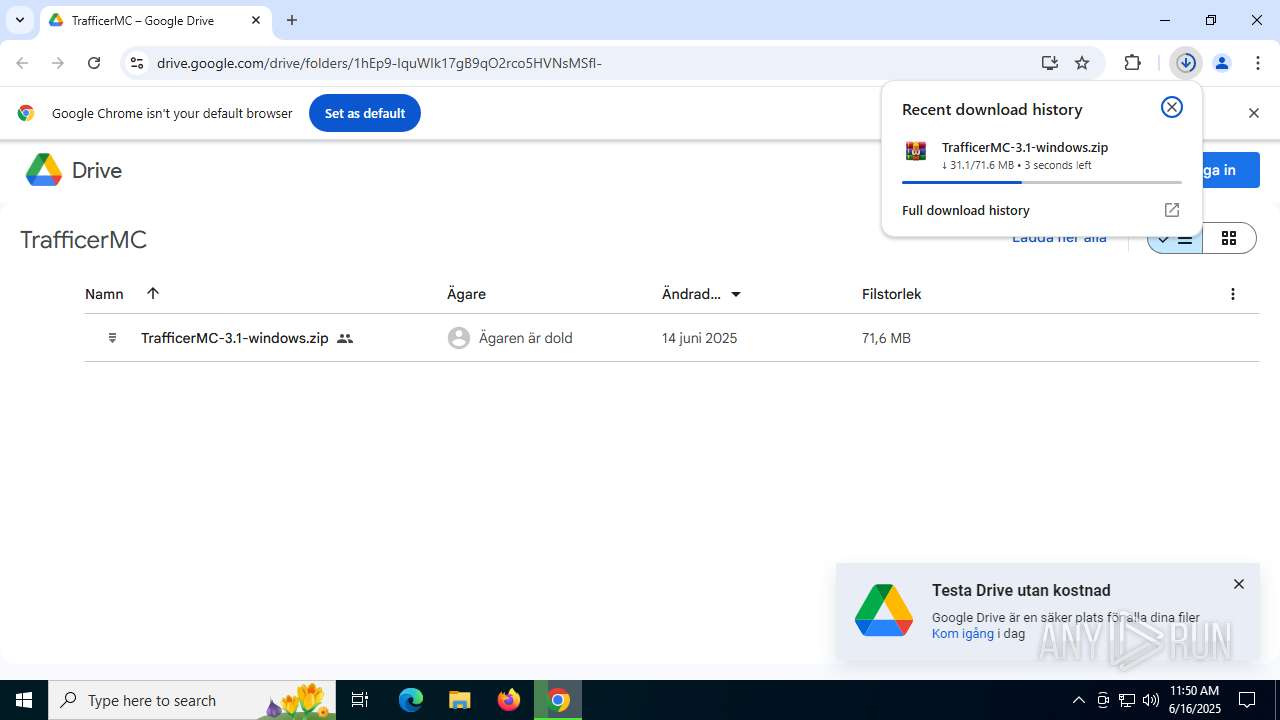
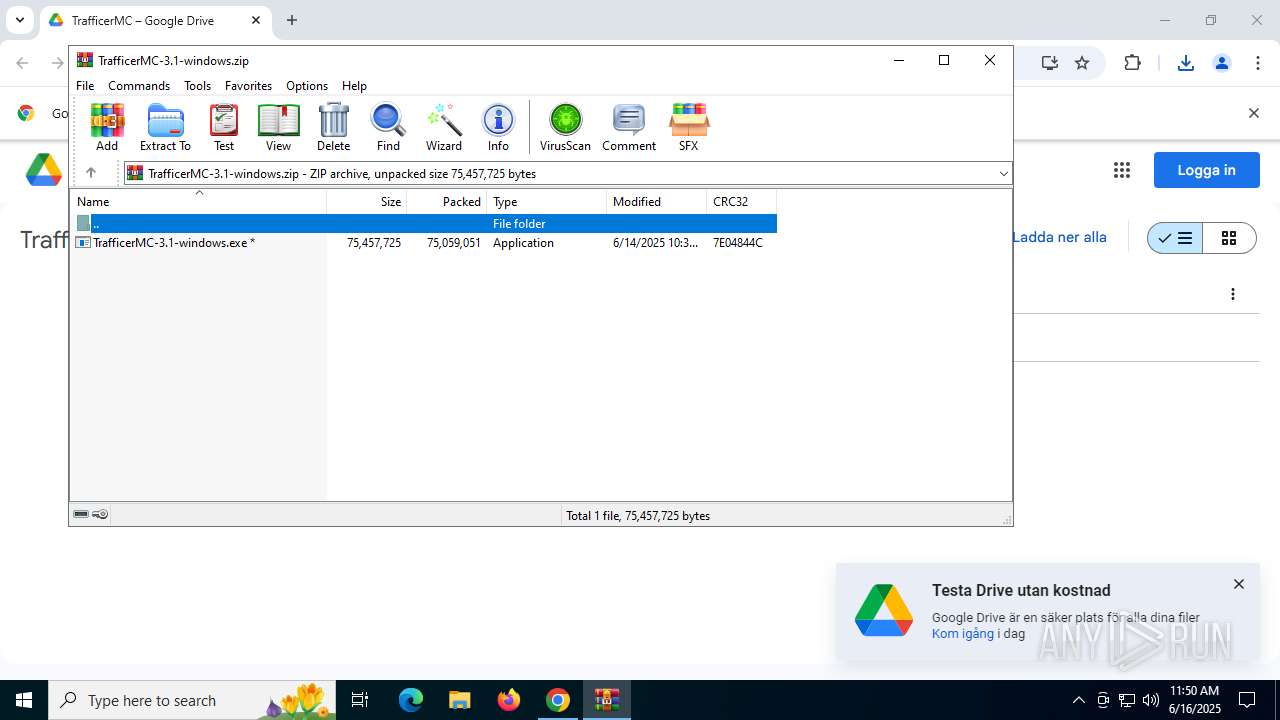
| URL: | https://drive.google.com/drive/folders/1hEp9-IquWIk17gB9qO2rco5HVNsMSfI- |
| Full analysis: | https://app.any.run/tasks/3269ffef-0f21-42a5-8aad-a752858eb84e |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 16, 2025, 11:49:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
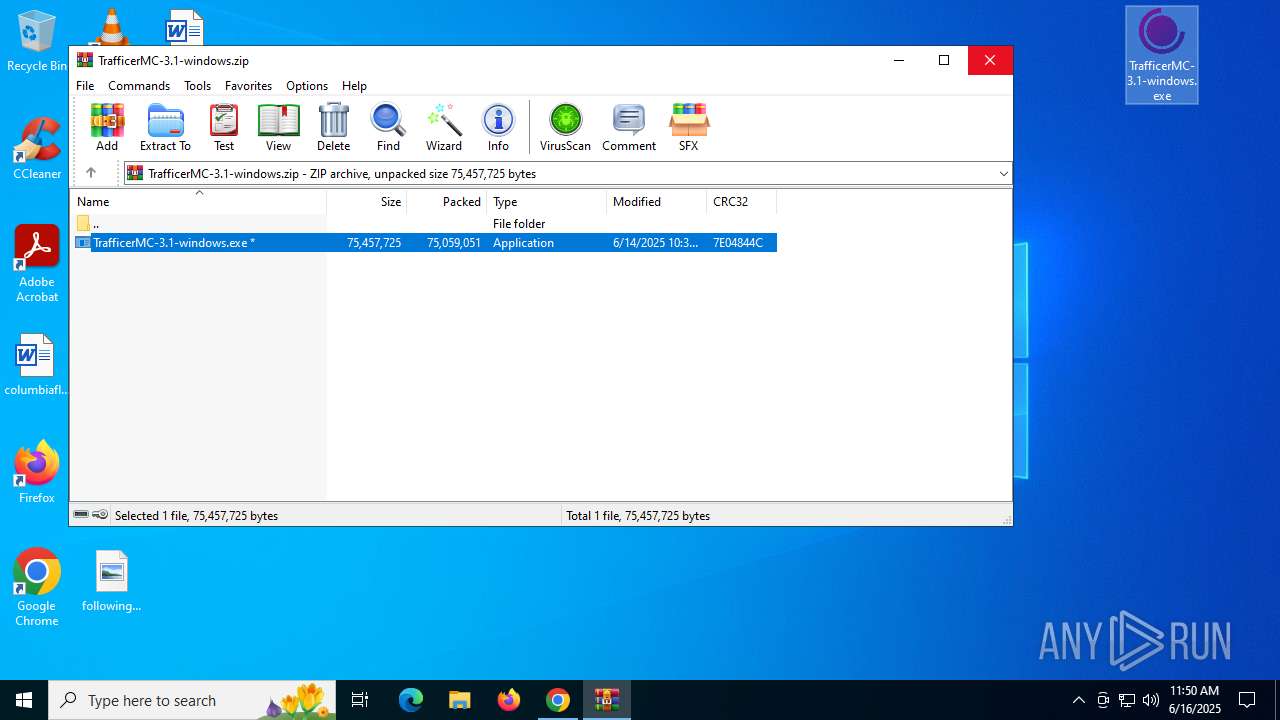
| MD5: | F2783EBCBF22DB6A6CA3A93BC0FF33CC |
| SHA1: | AA610C75624A25883C4449740693E501728B6DA3 |
| SHA256: | E990578A5D35DB1D337FB968C97E20C1B46870E2D847811F2B55822D580563F6 |
| SSDEEP: | 3:N8PMMtZJunXzJByBys2czXN4HWokpn:2ADPyBBzXNQS |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 6980)
- MSBuild.exe (PID: 2120)
Connects to the CnC server
- svchost.exe (PID: 2200)
LUMMA mutex has been found
- MSBuild.exe (PID: 6980)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 6980)
SUSPICIOUS
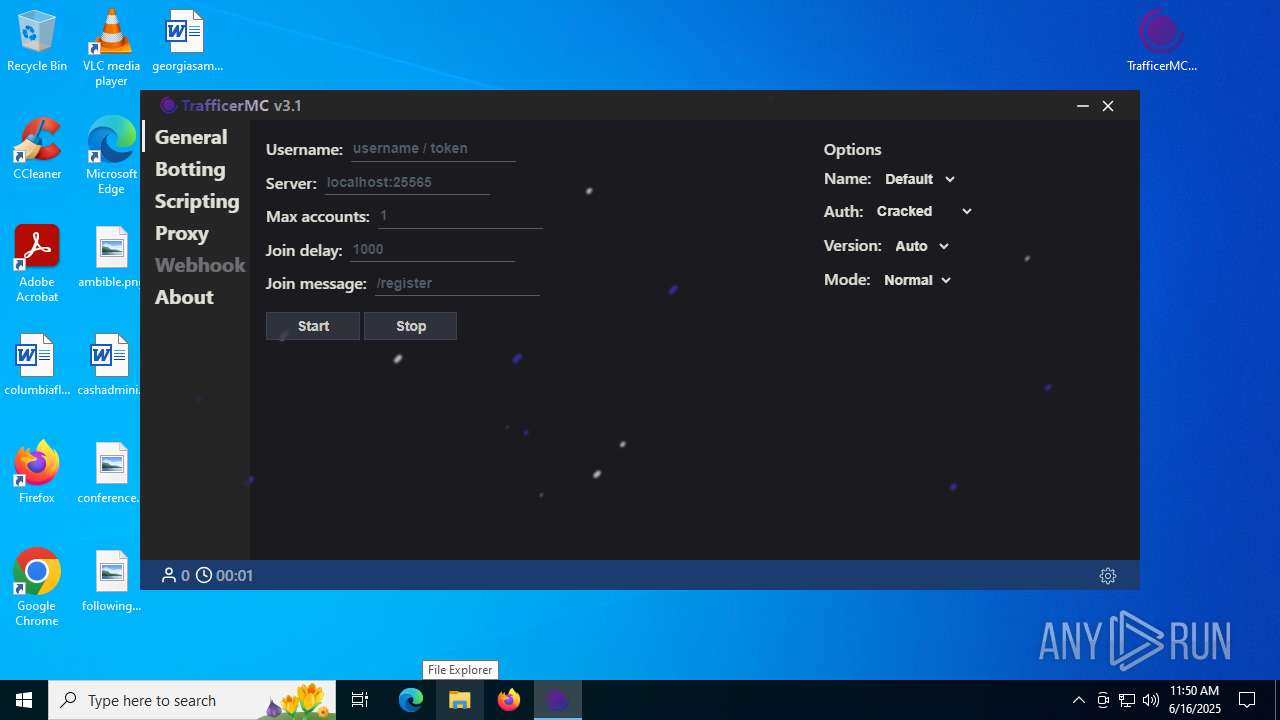
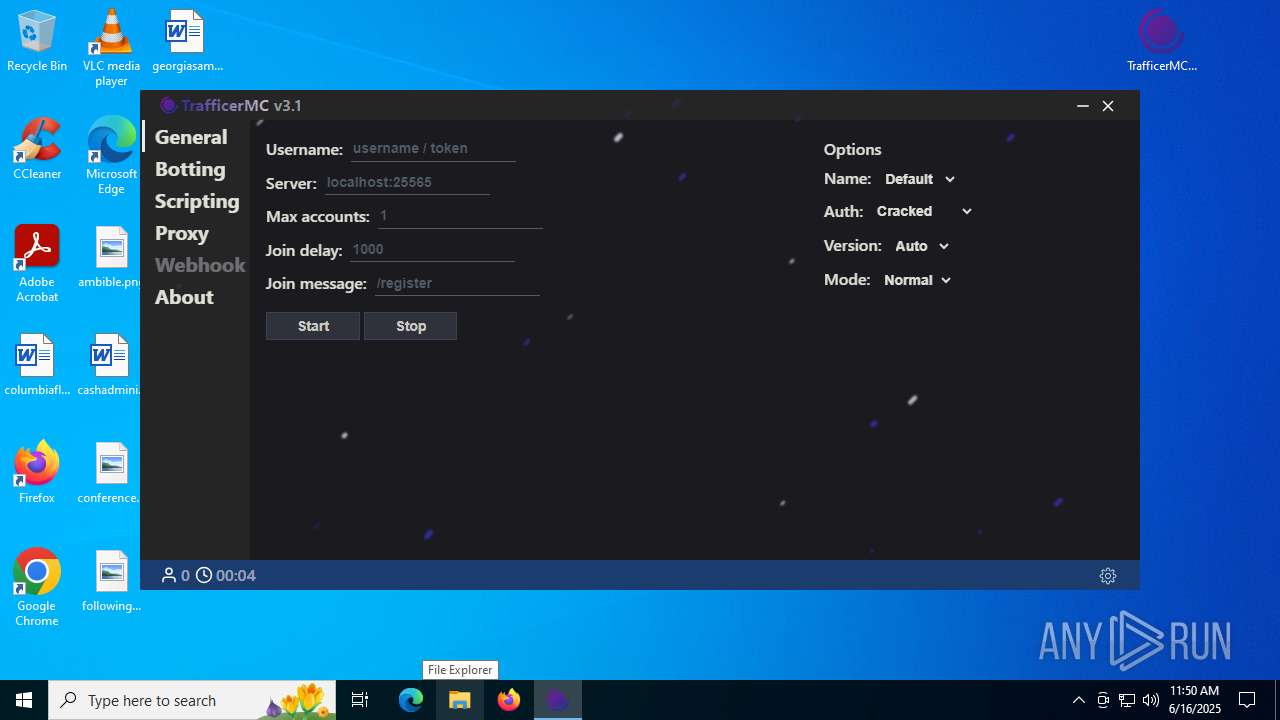
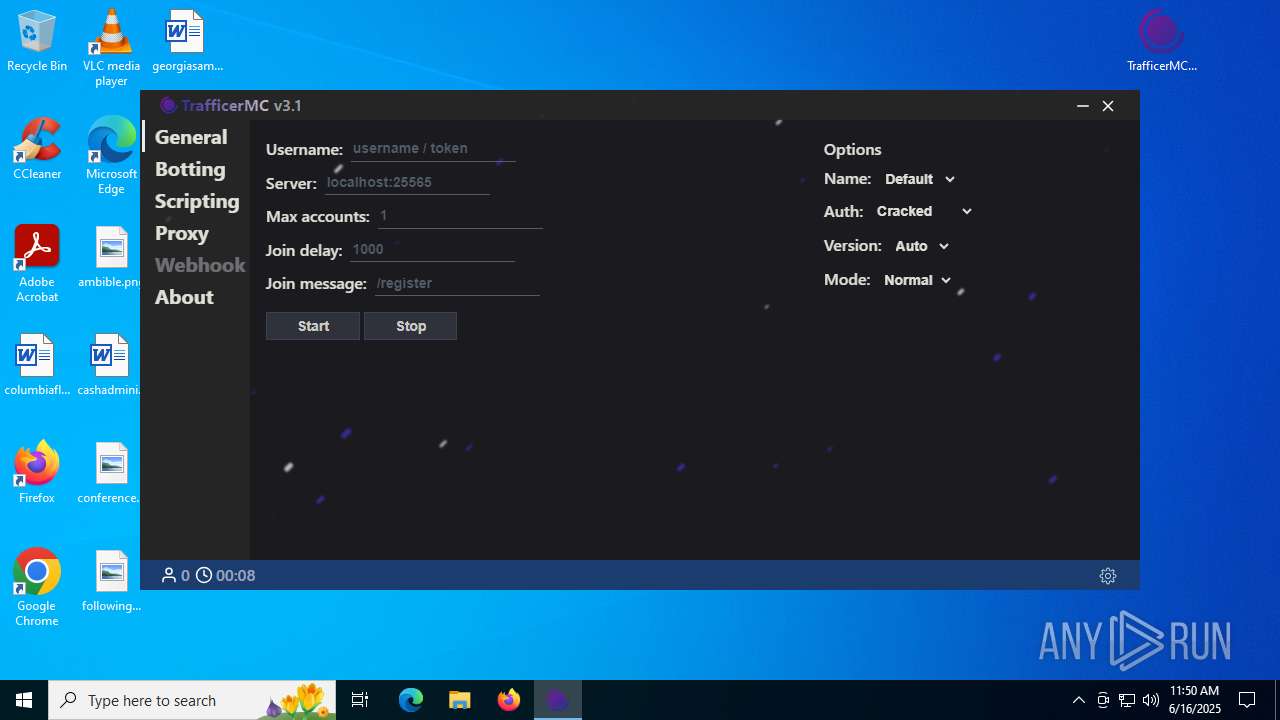
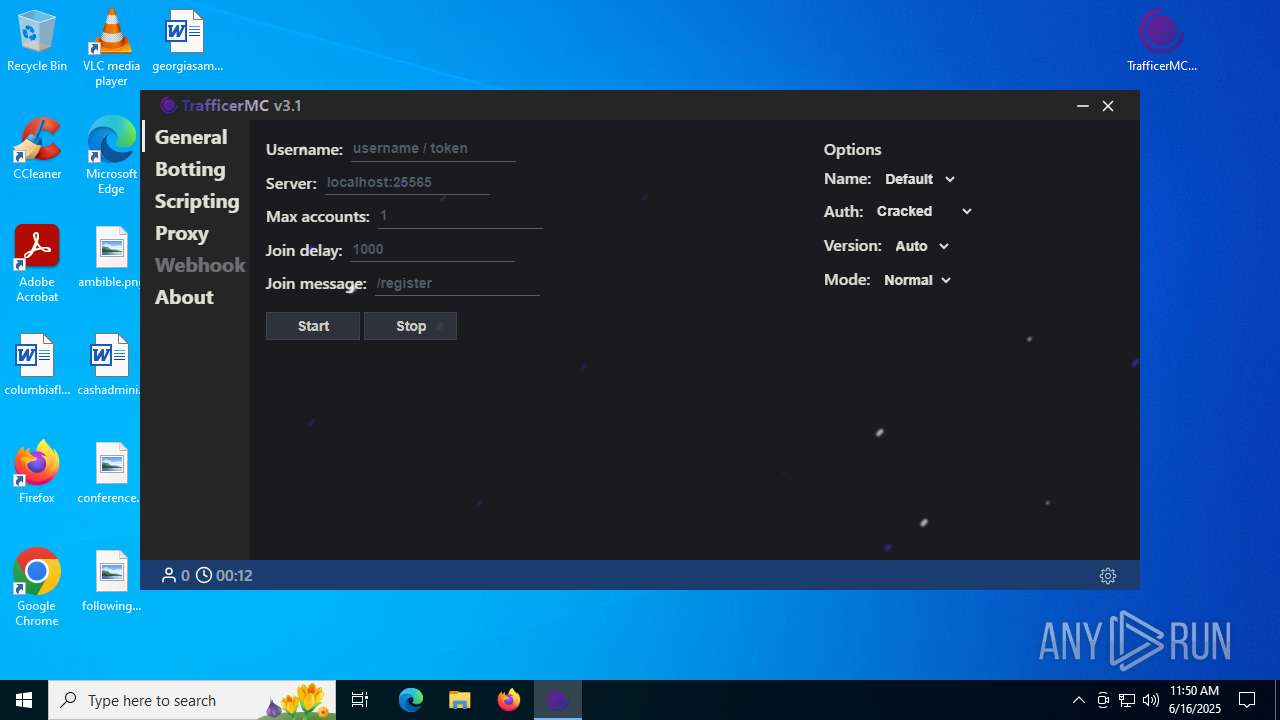
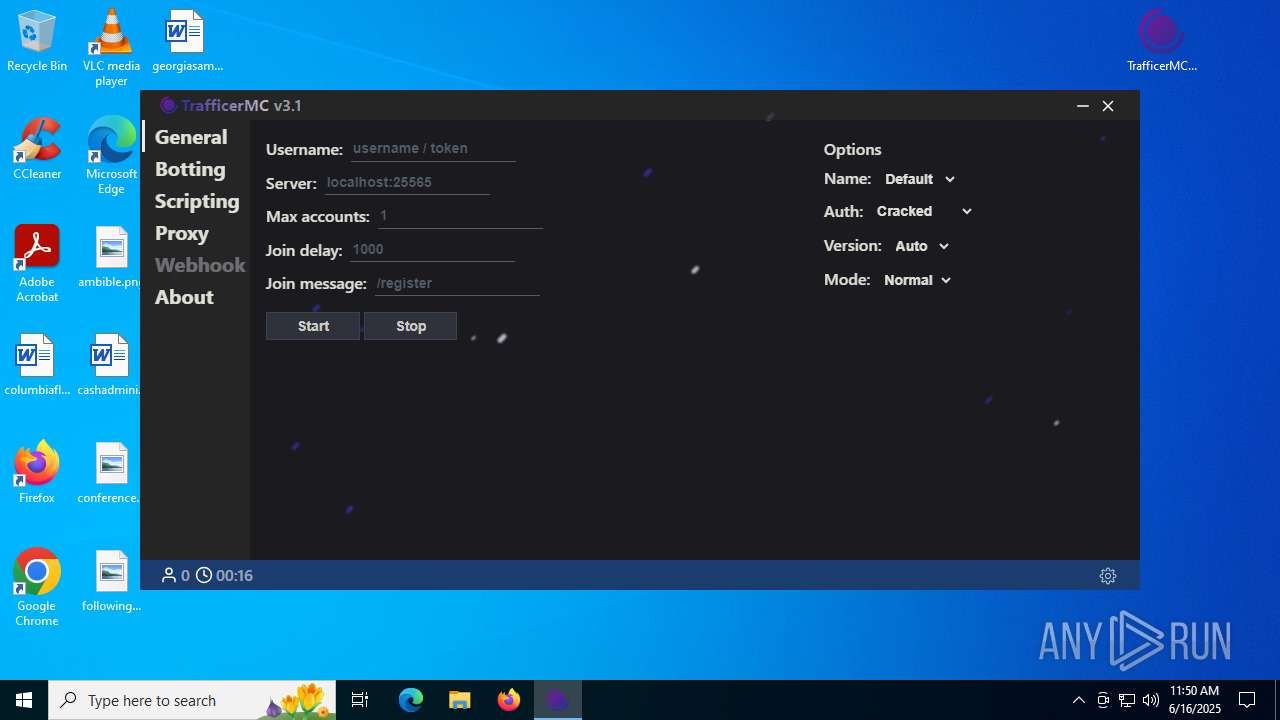
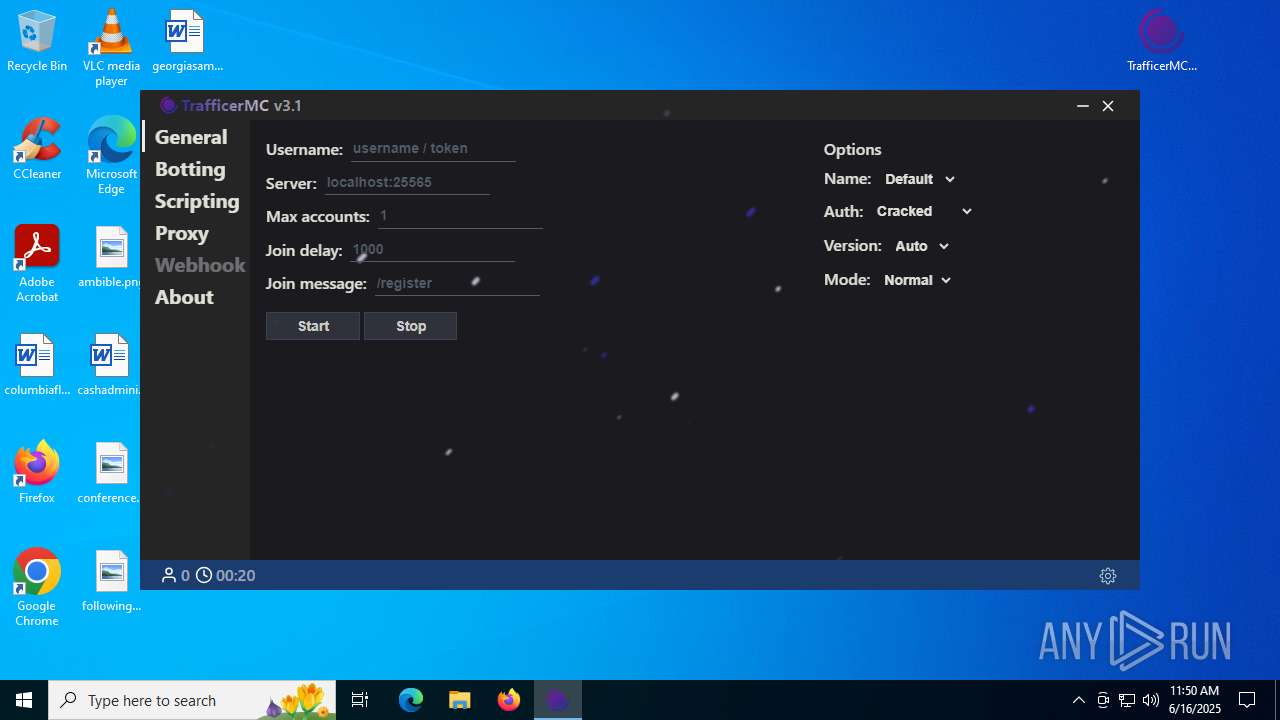
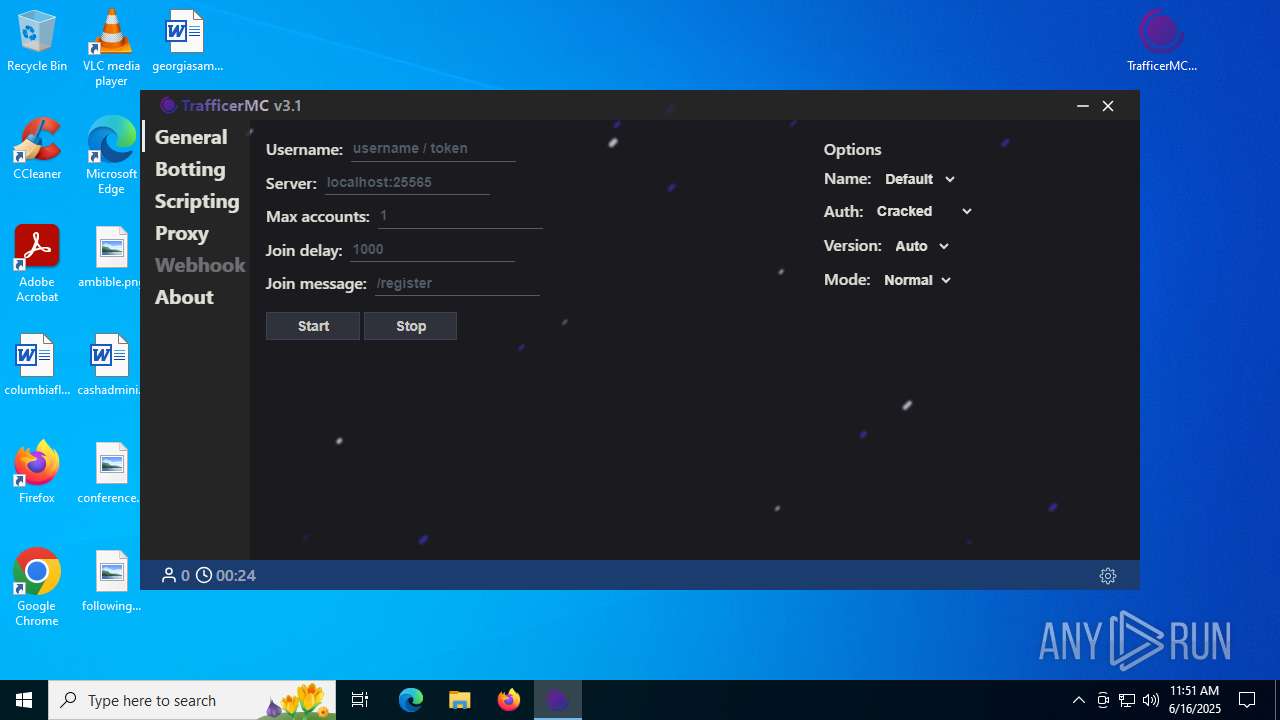
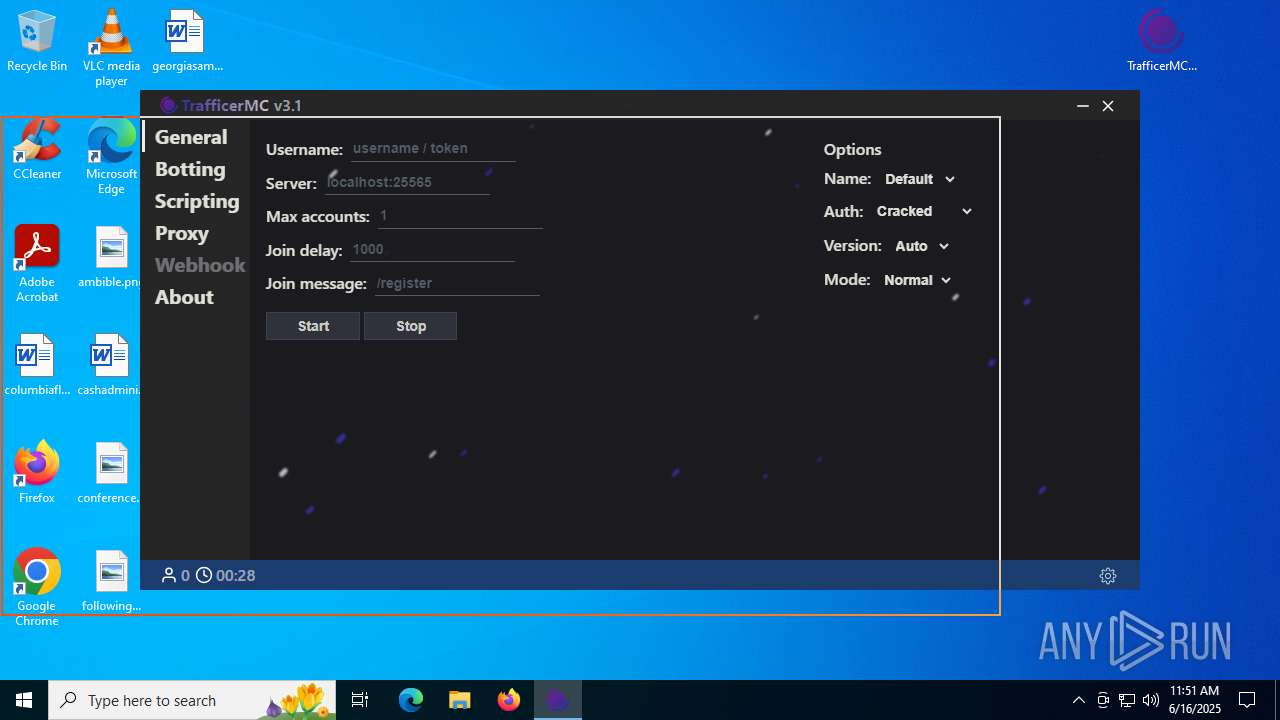
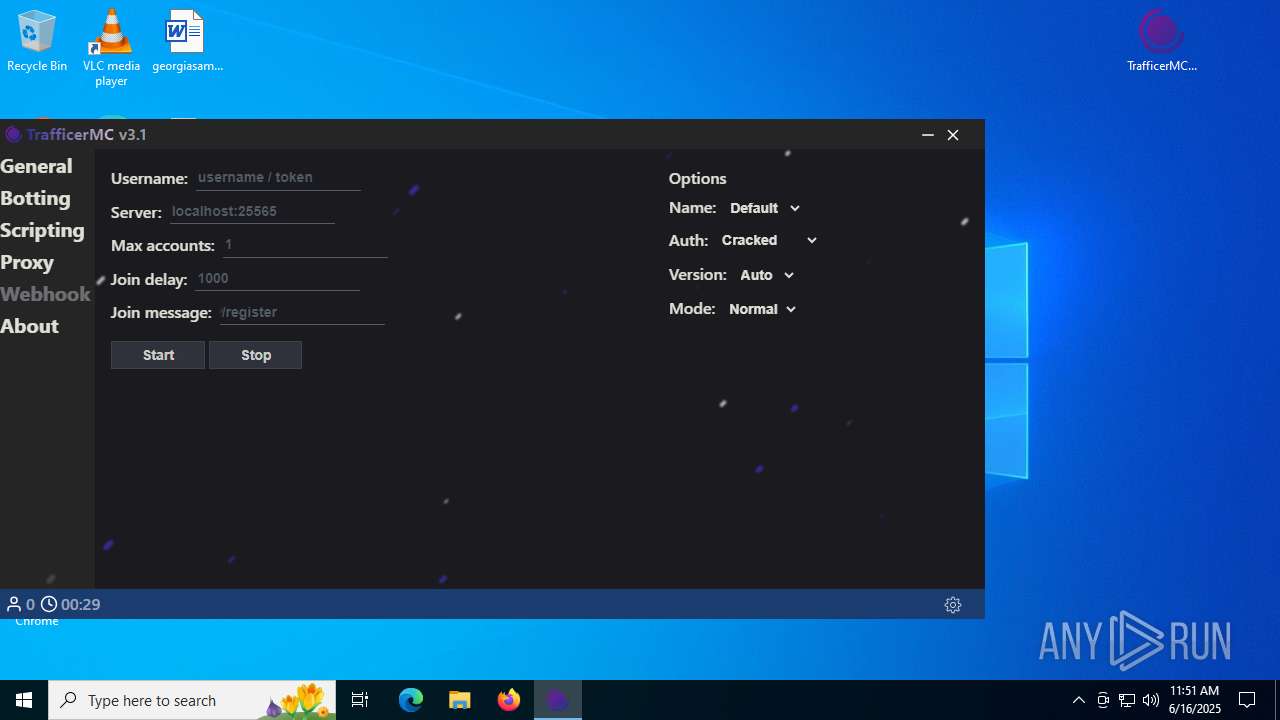
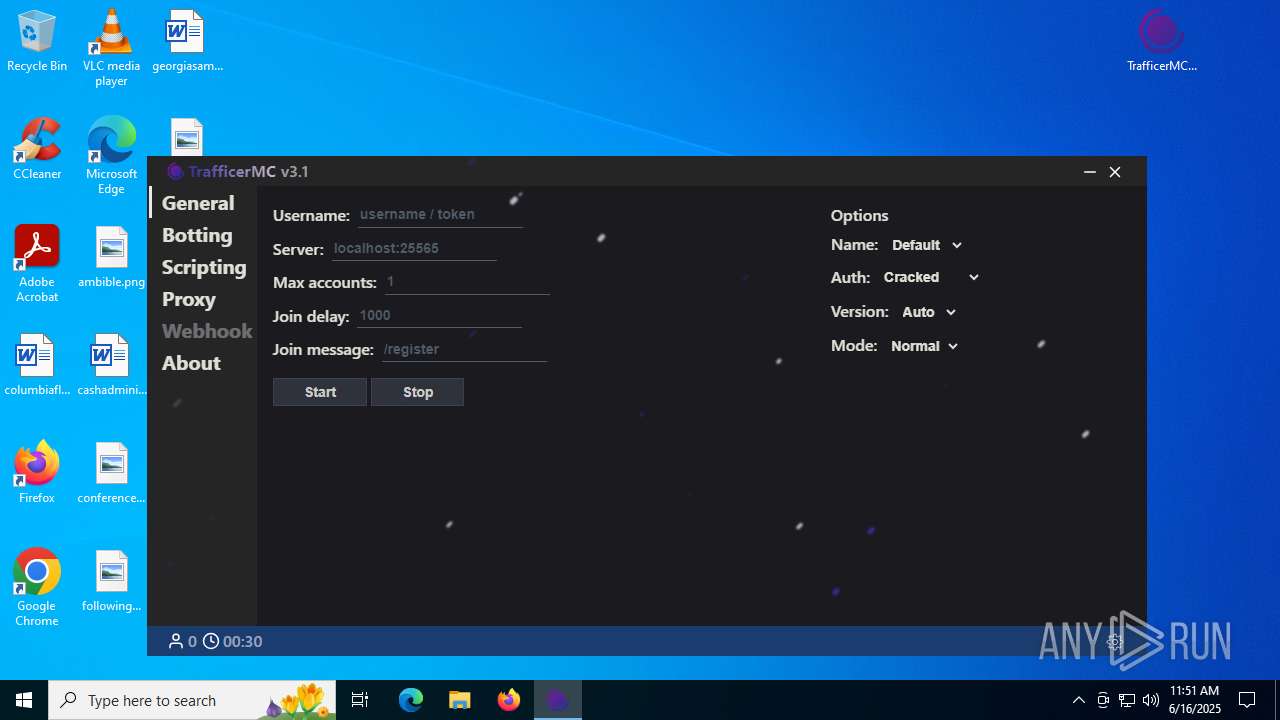
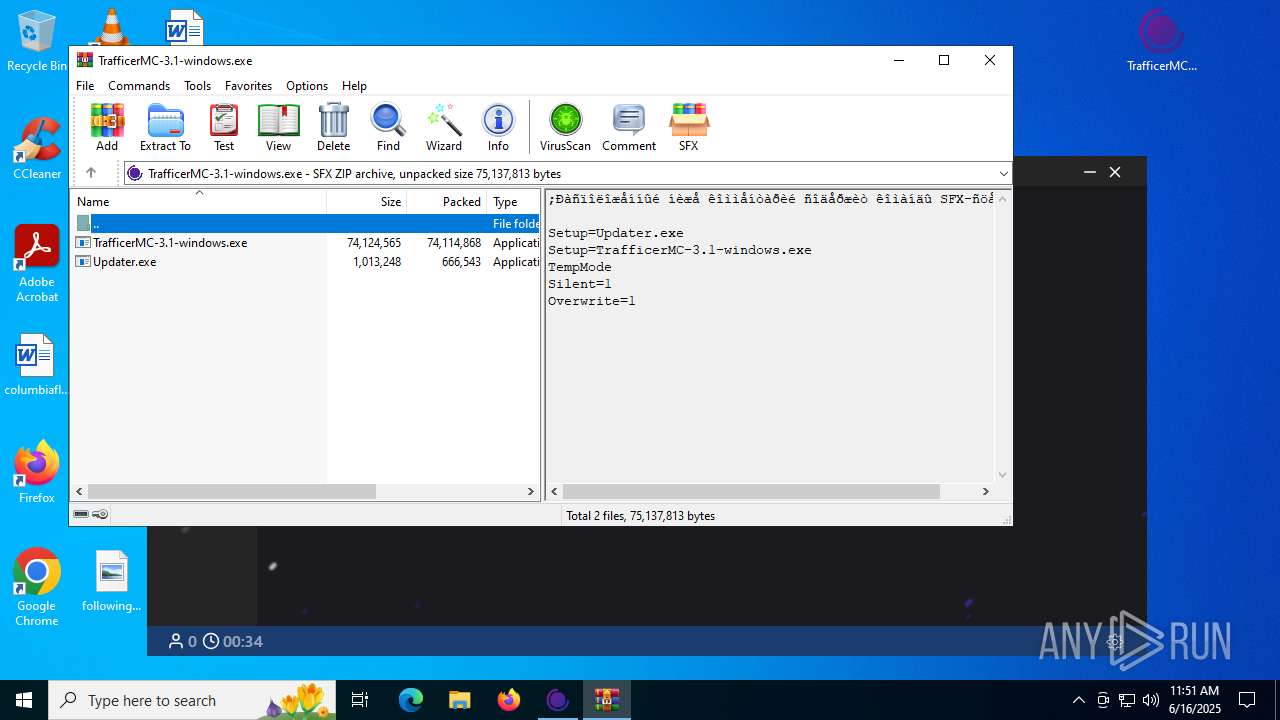
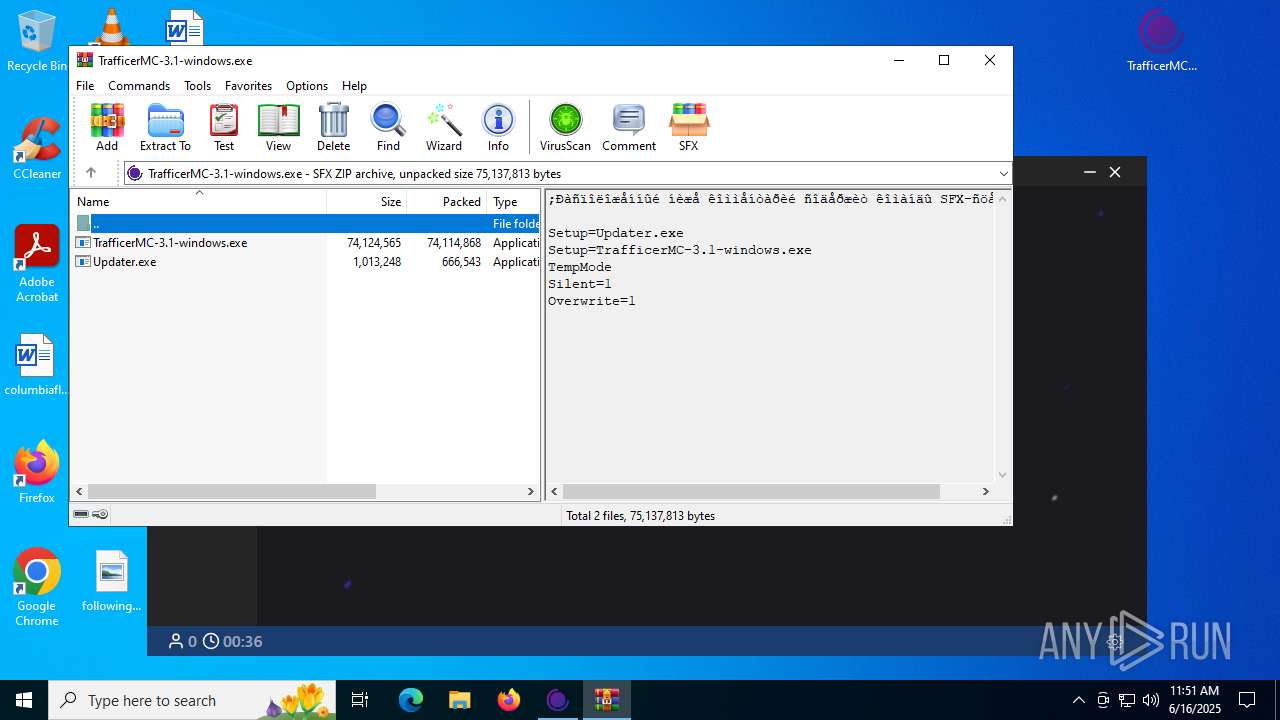
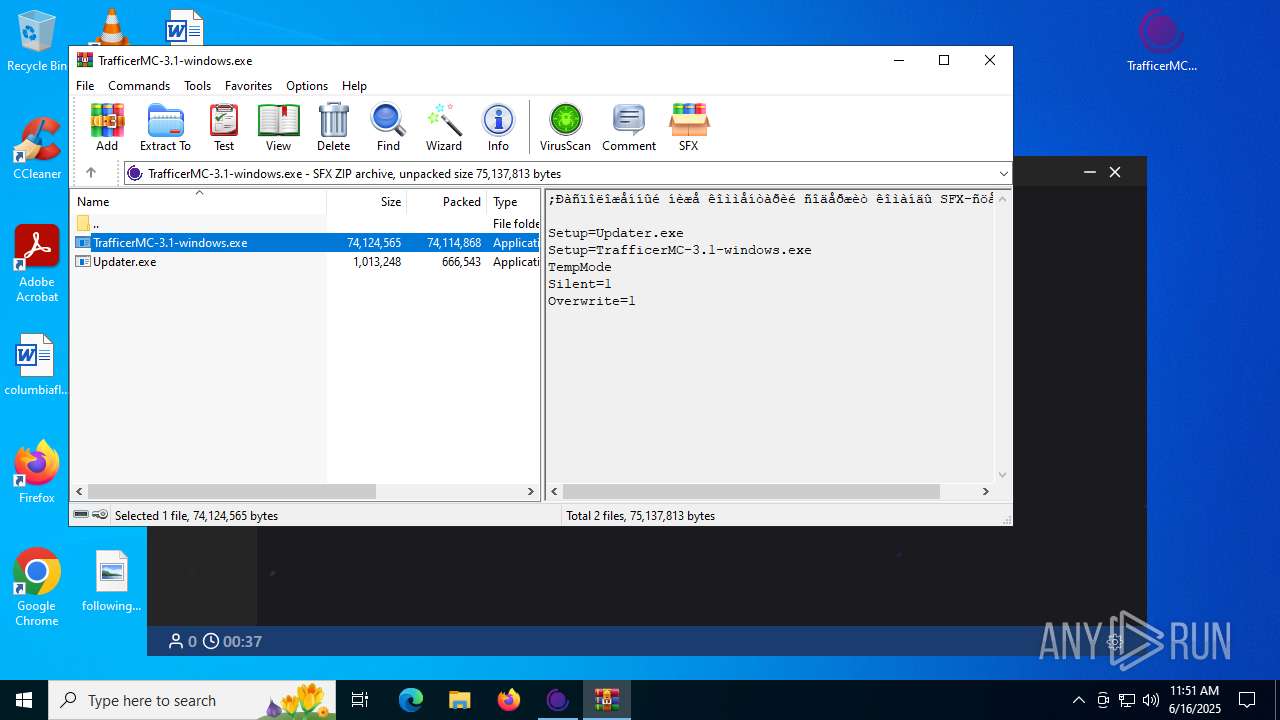
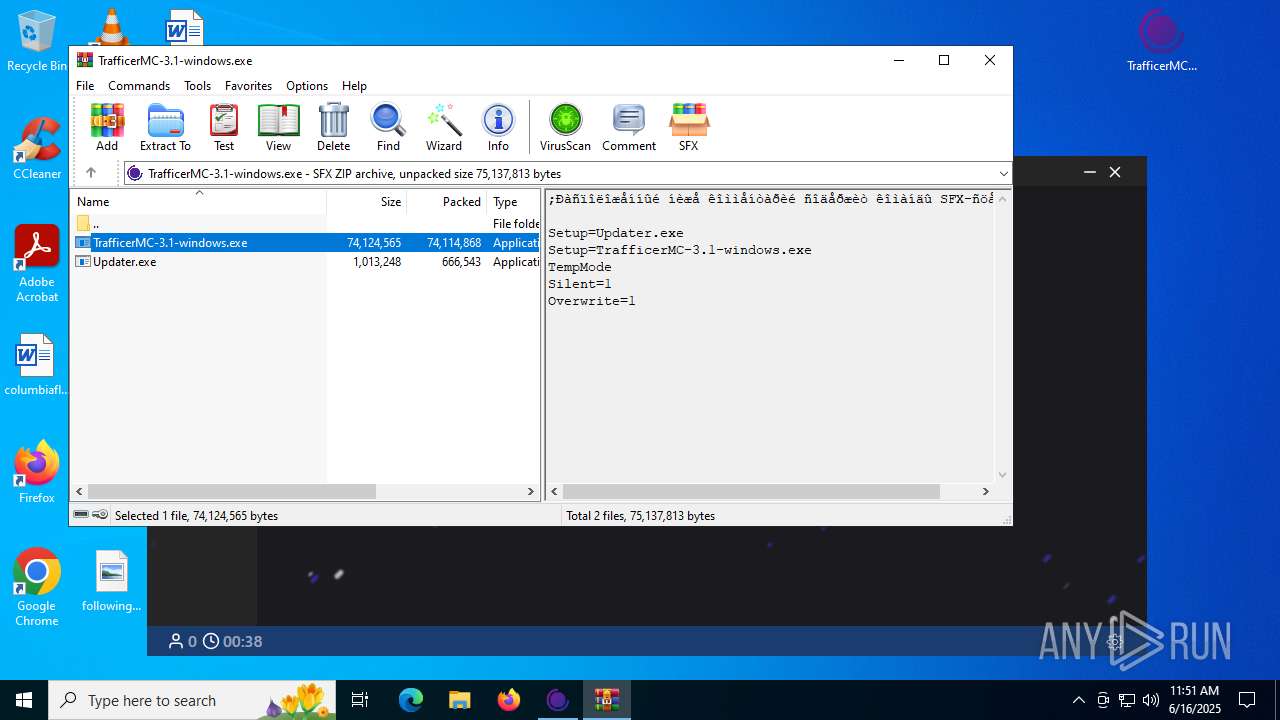
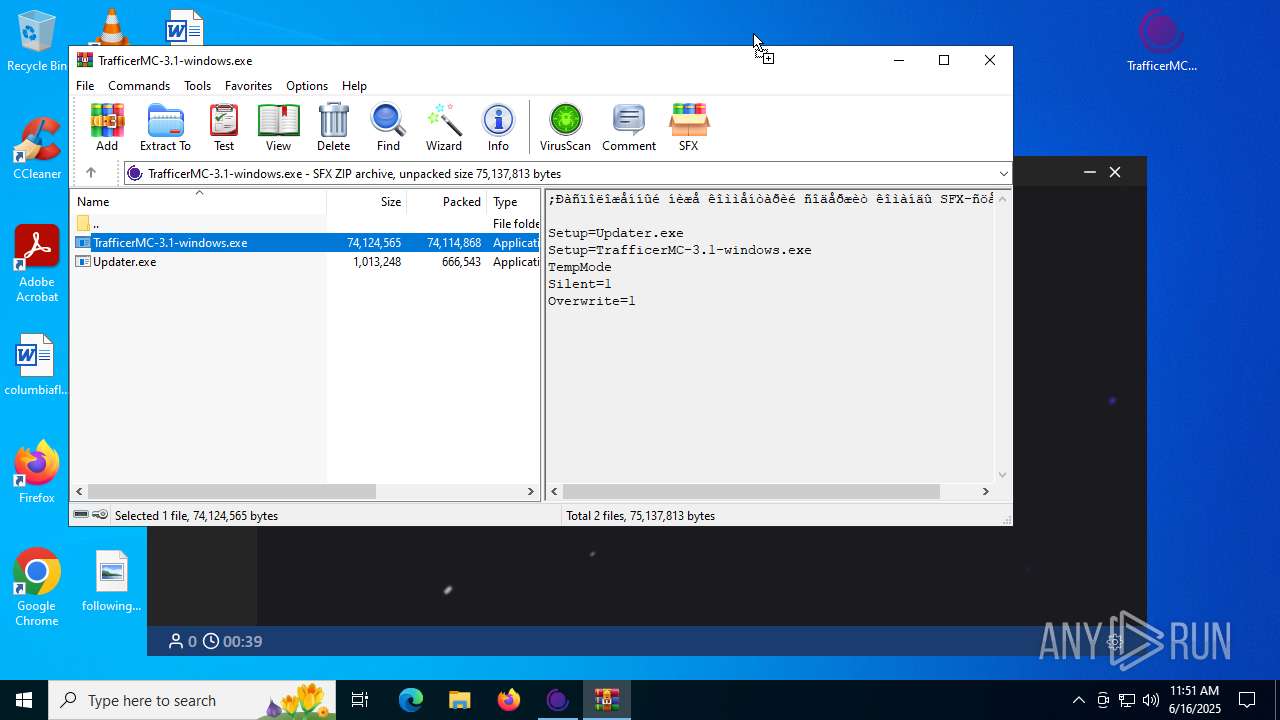
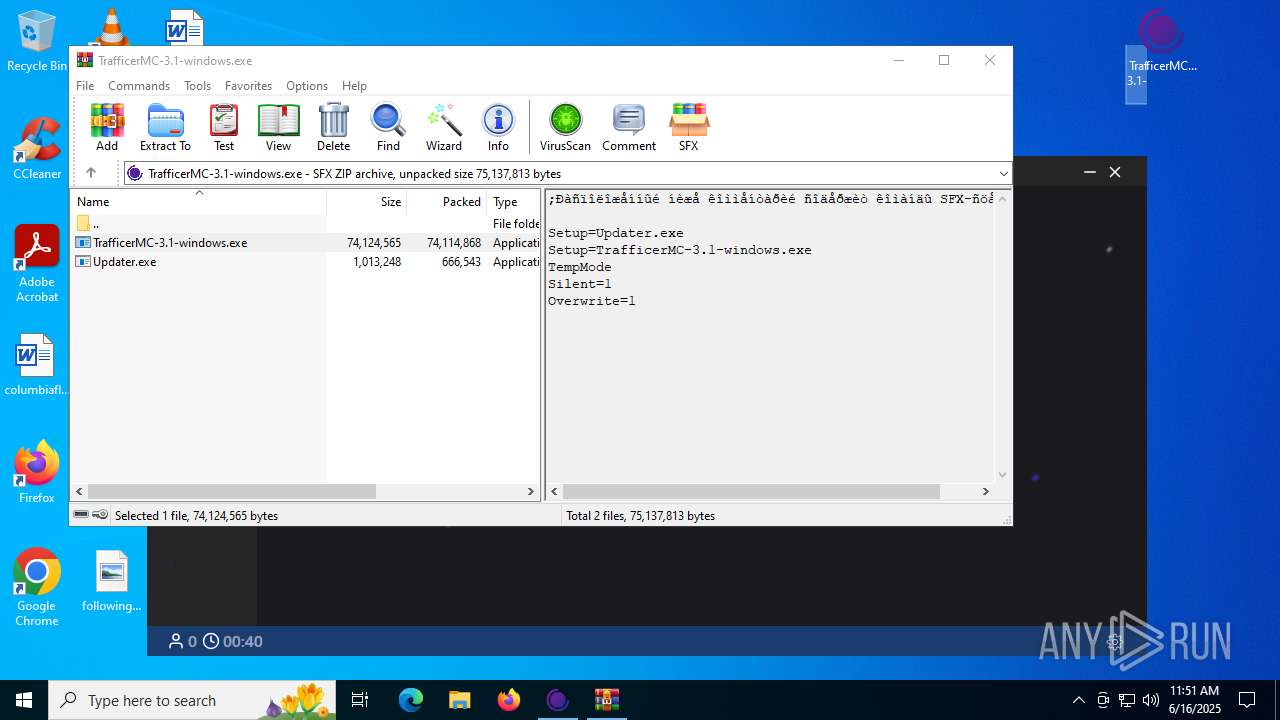
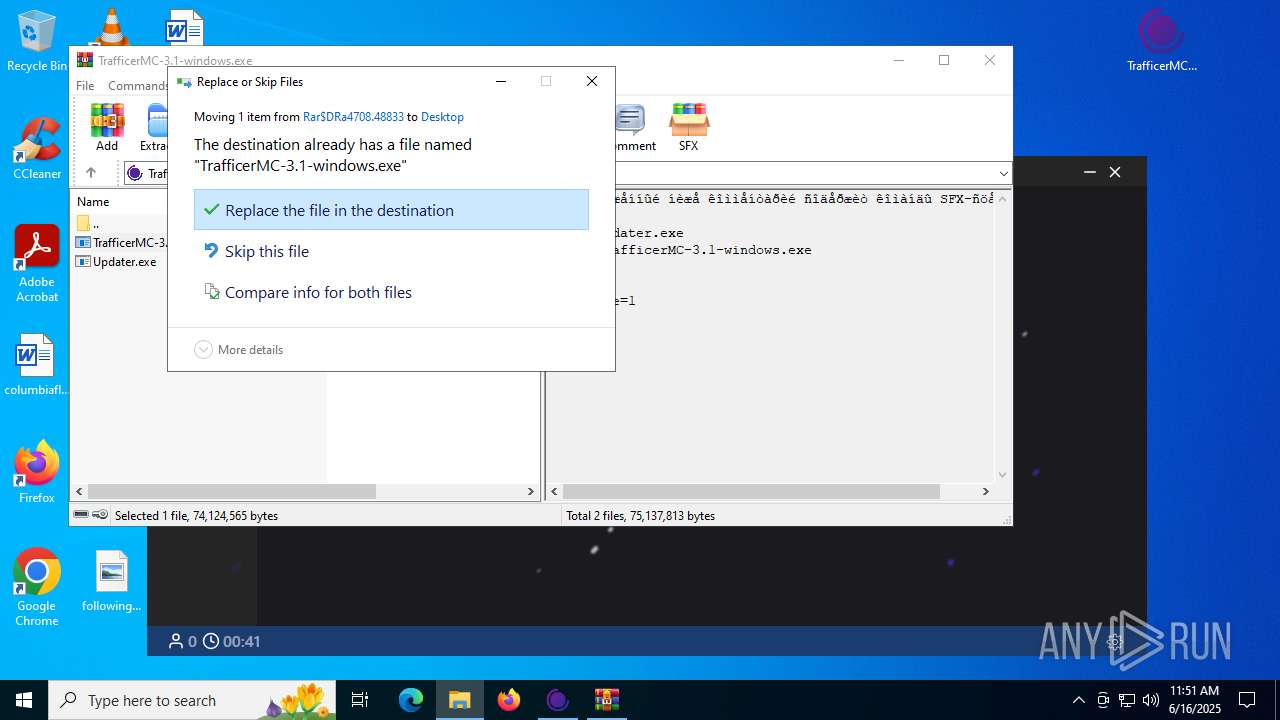
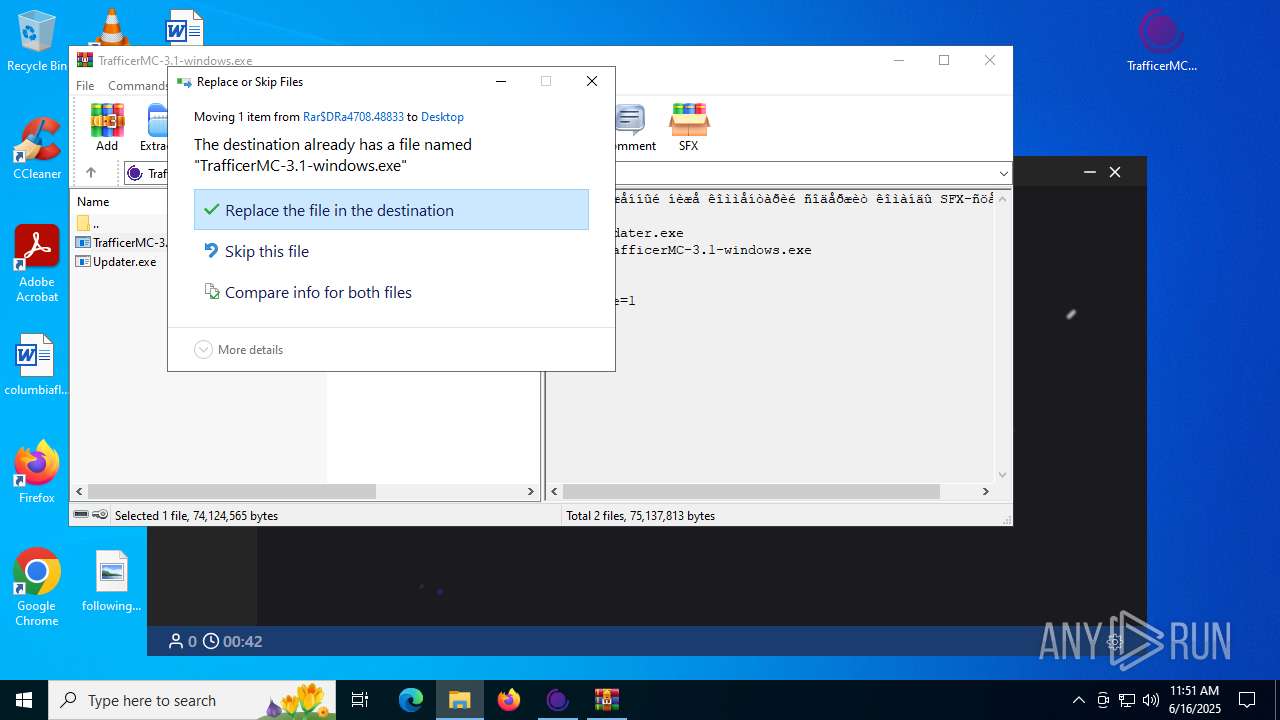
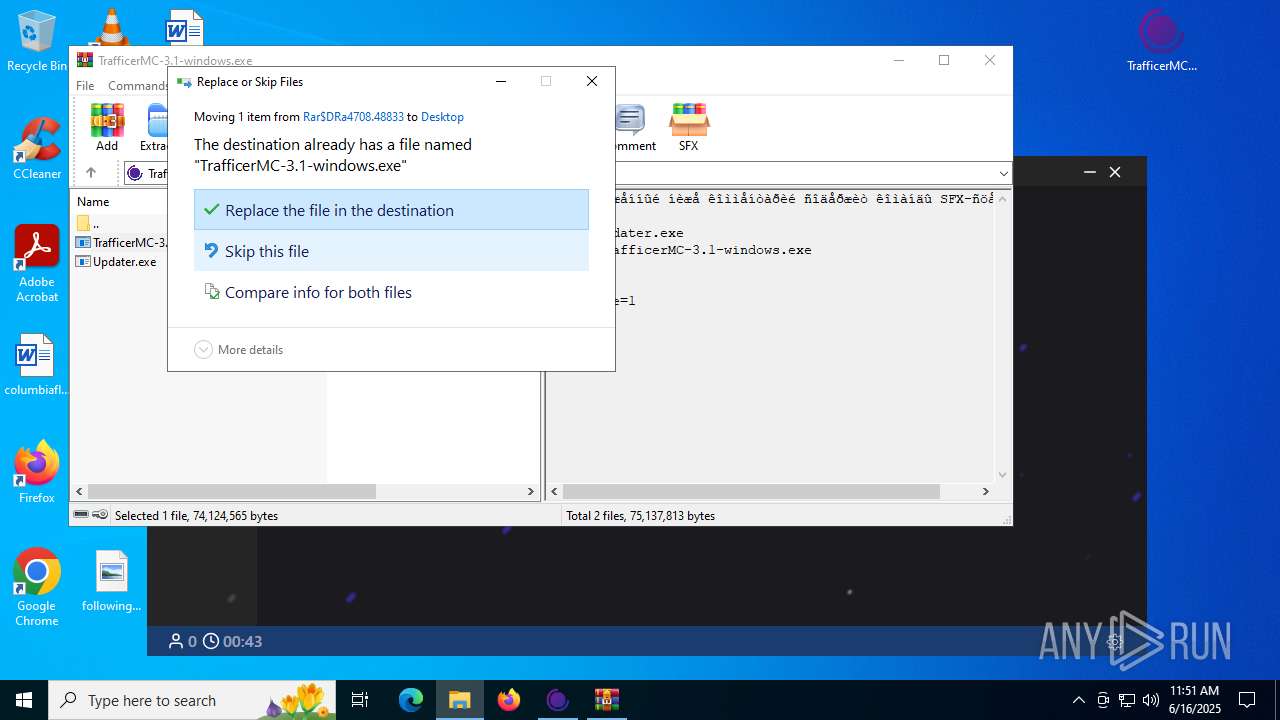
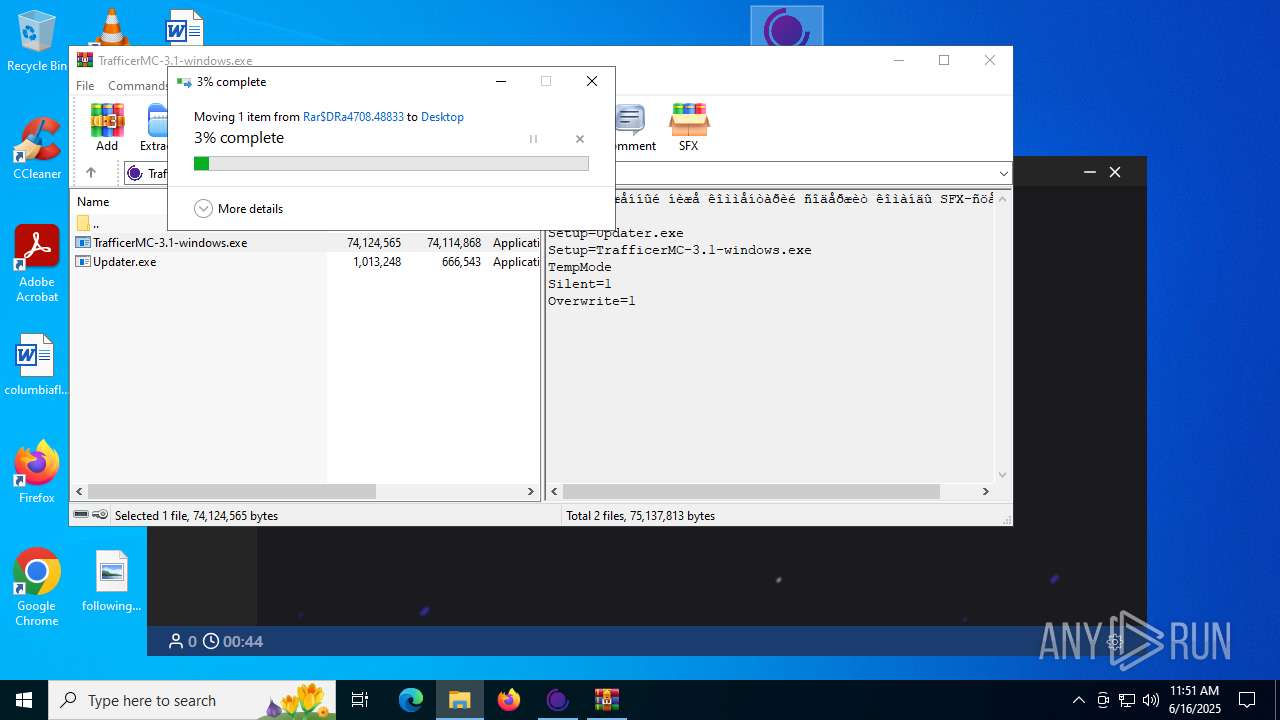
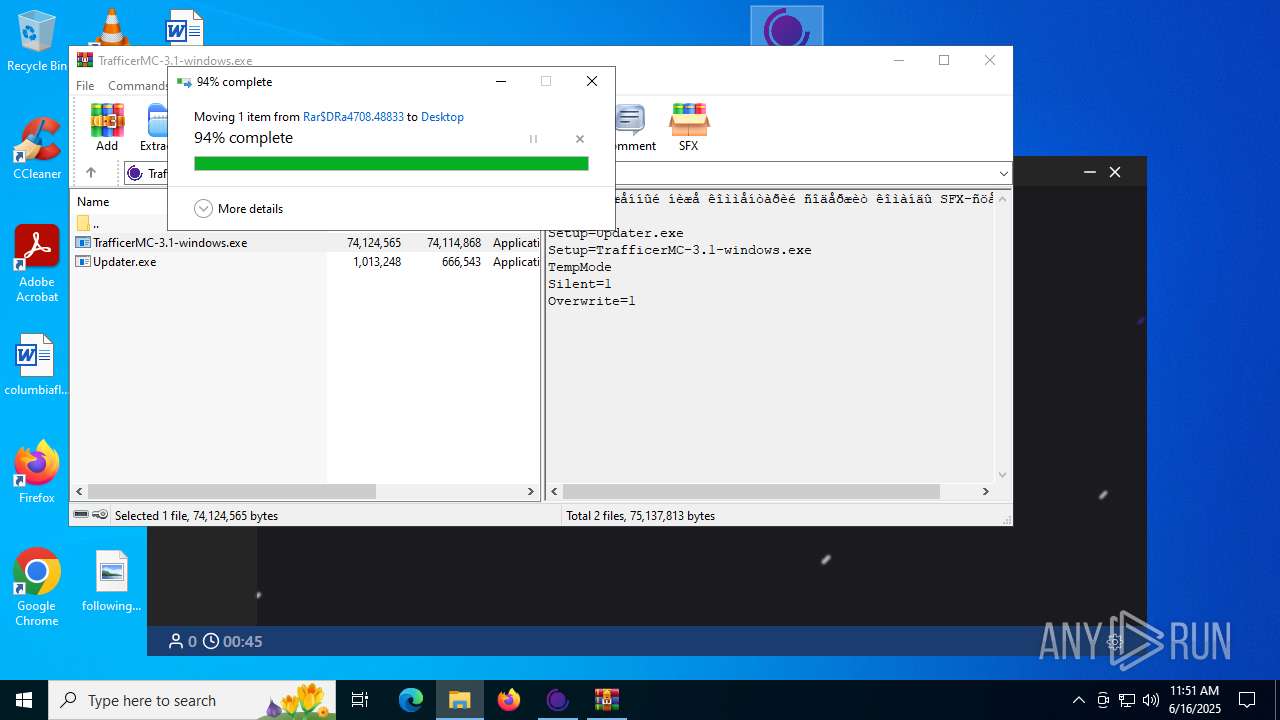
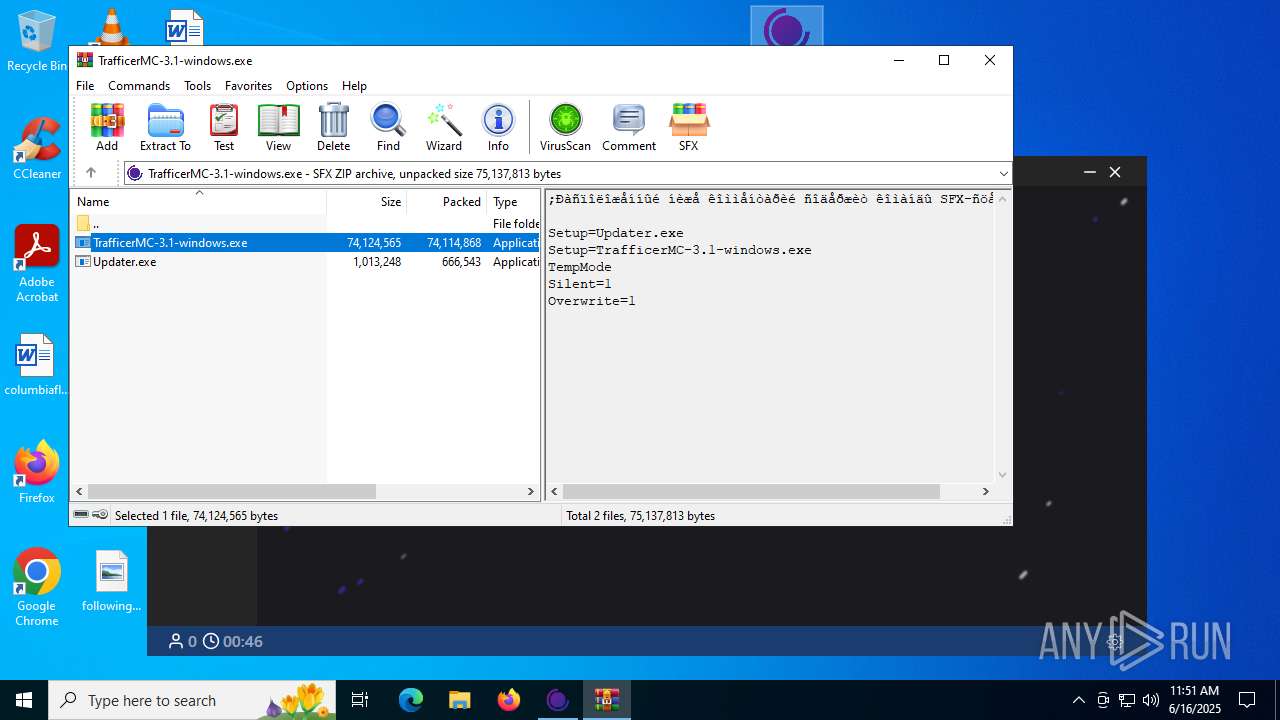
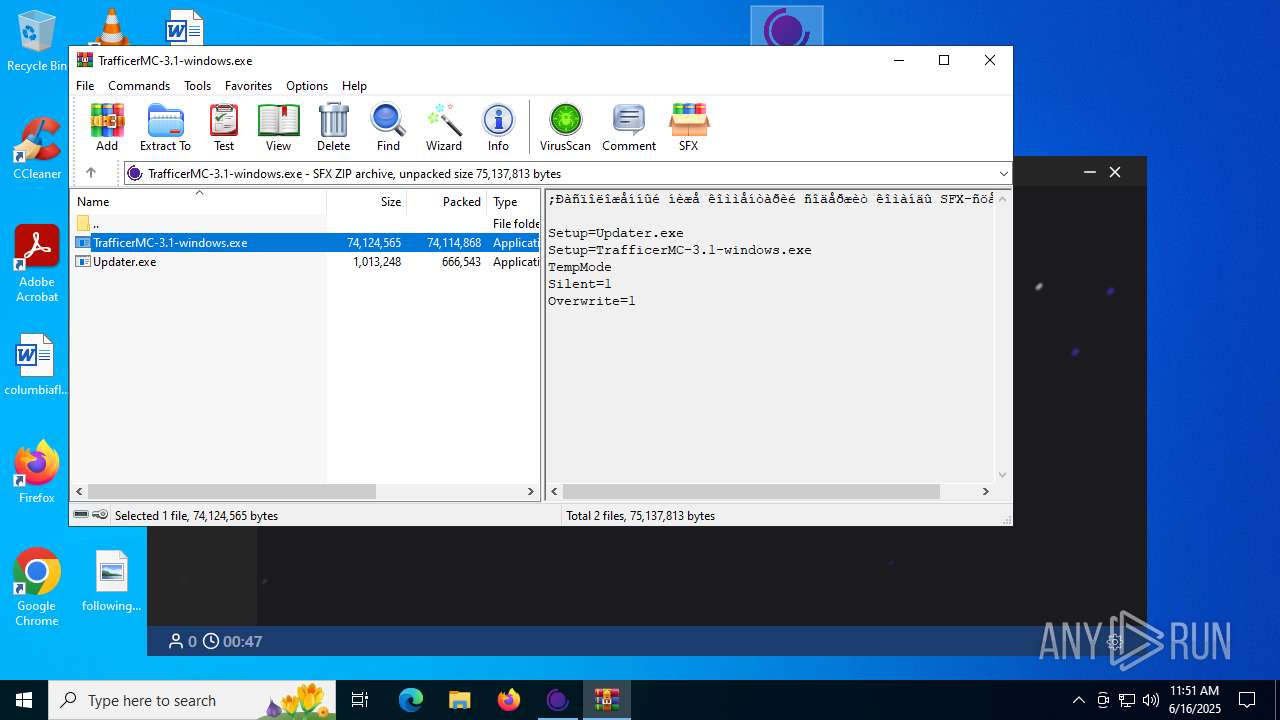
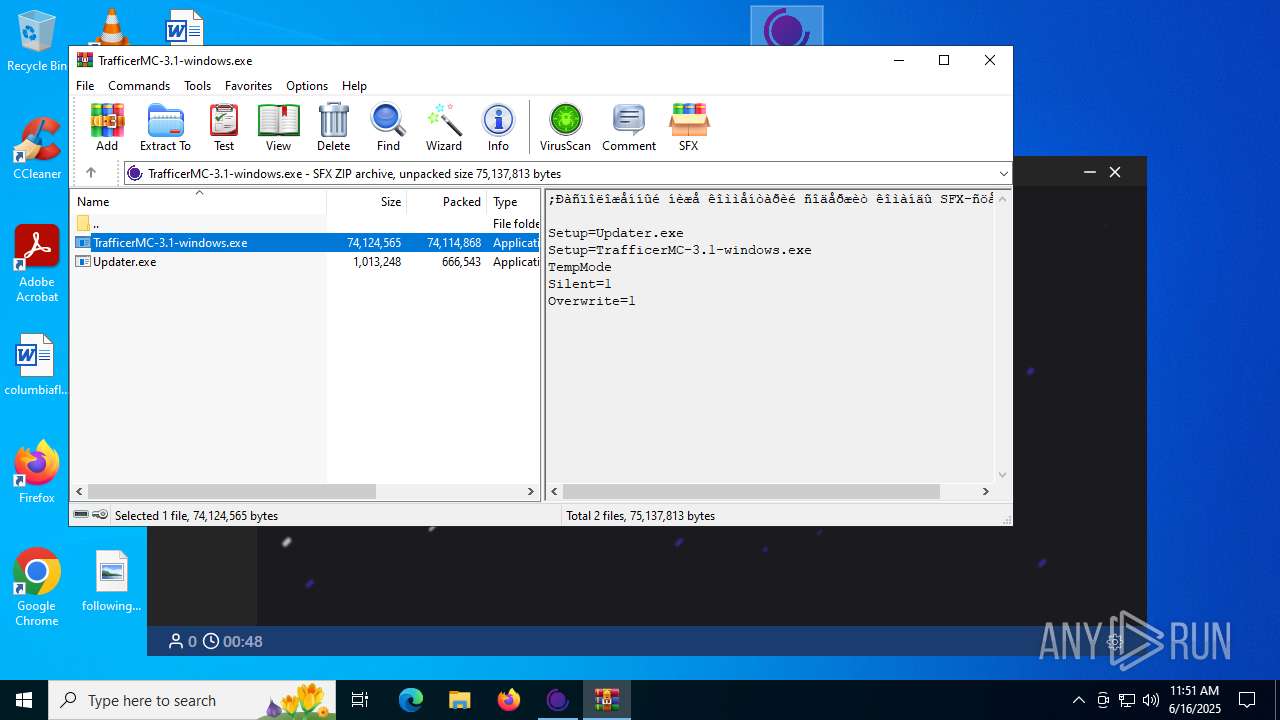
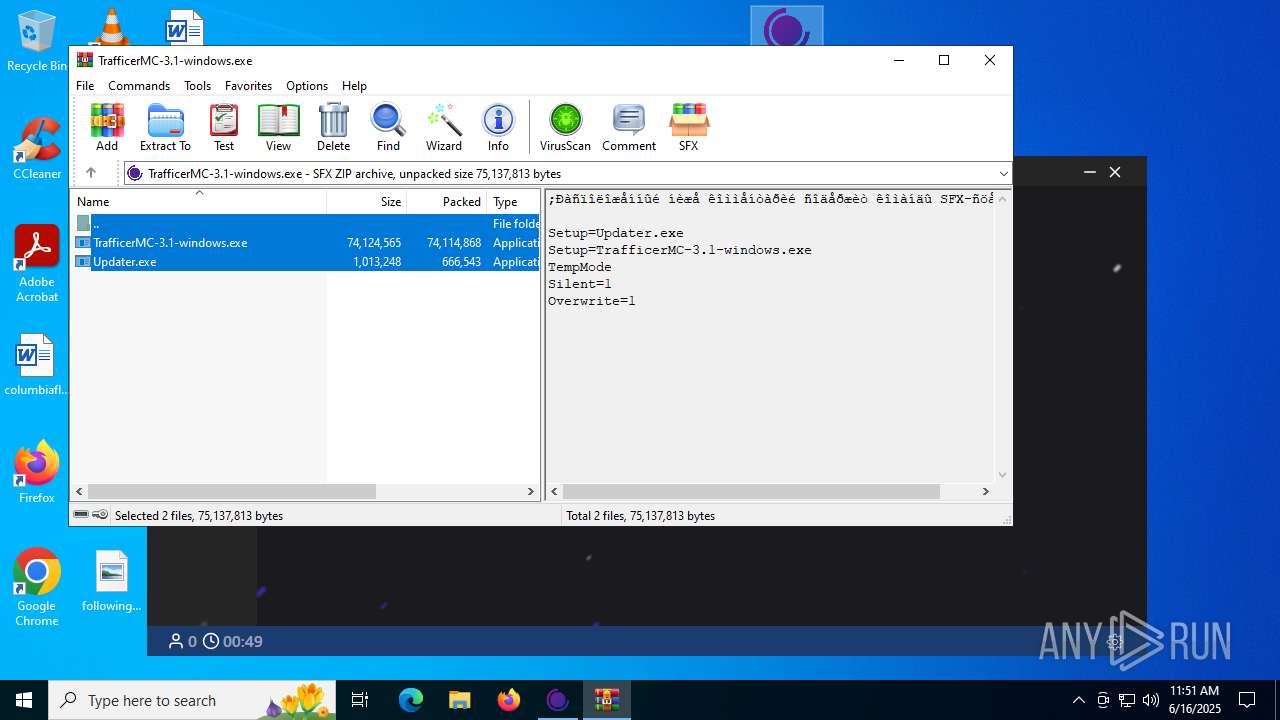
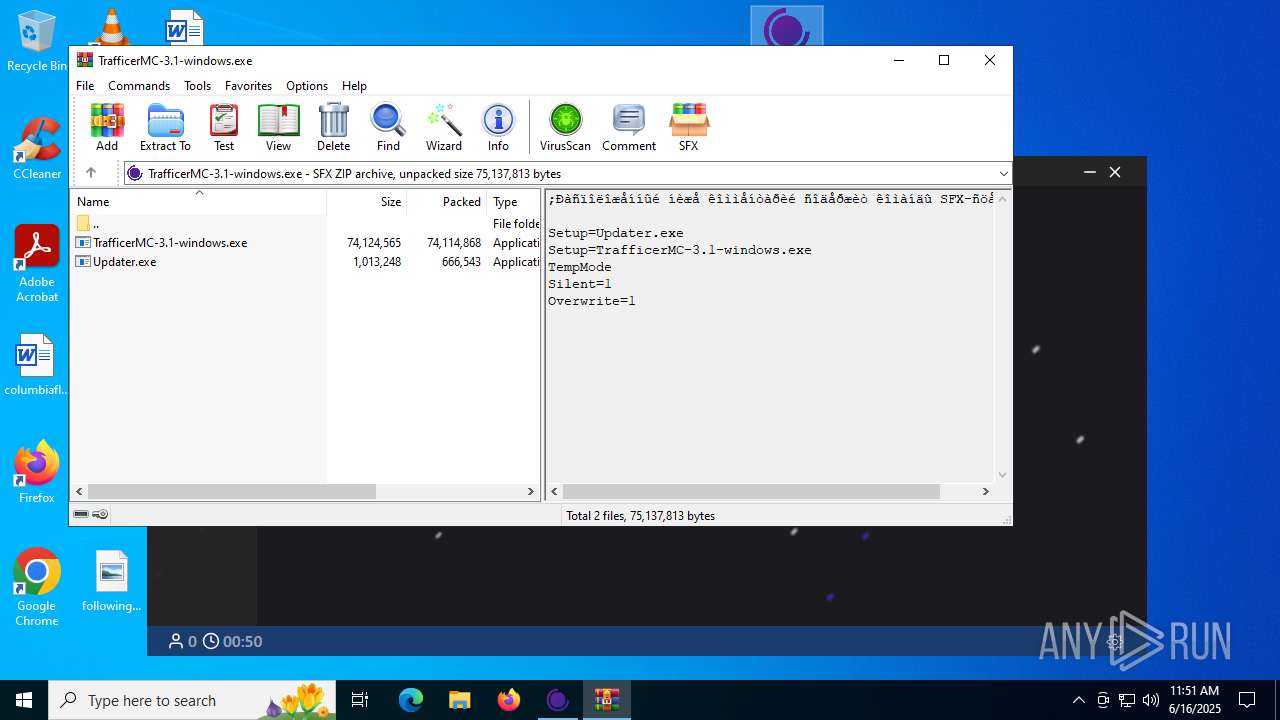
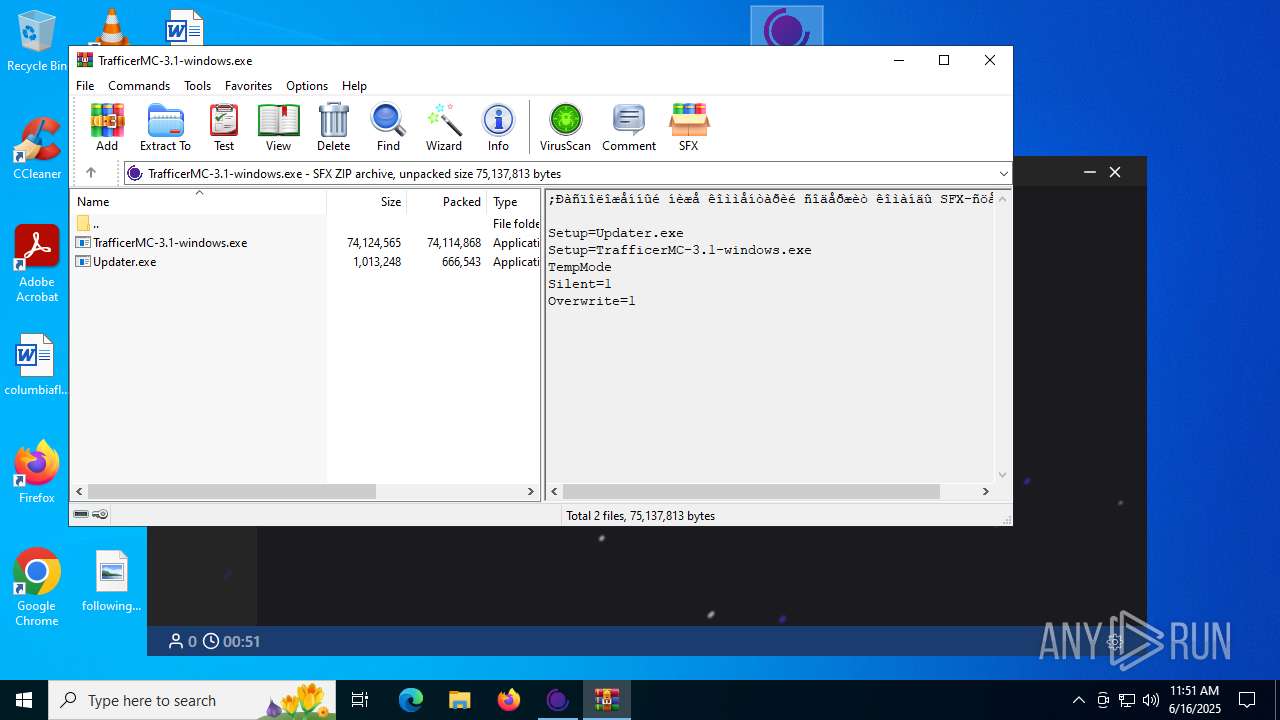
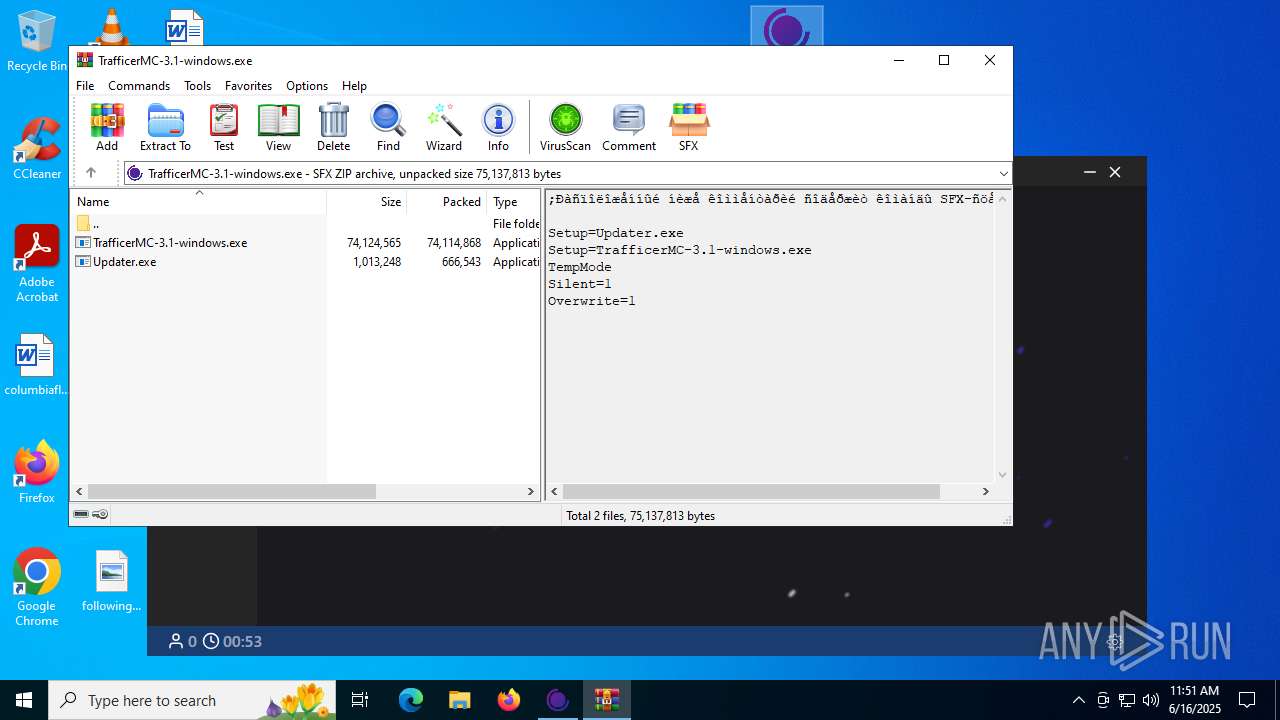
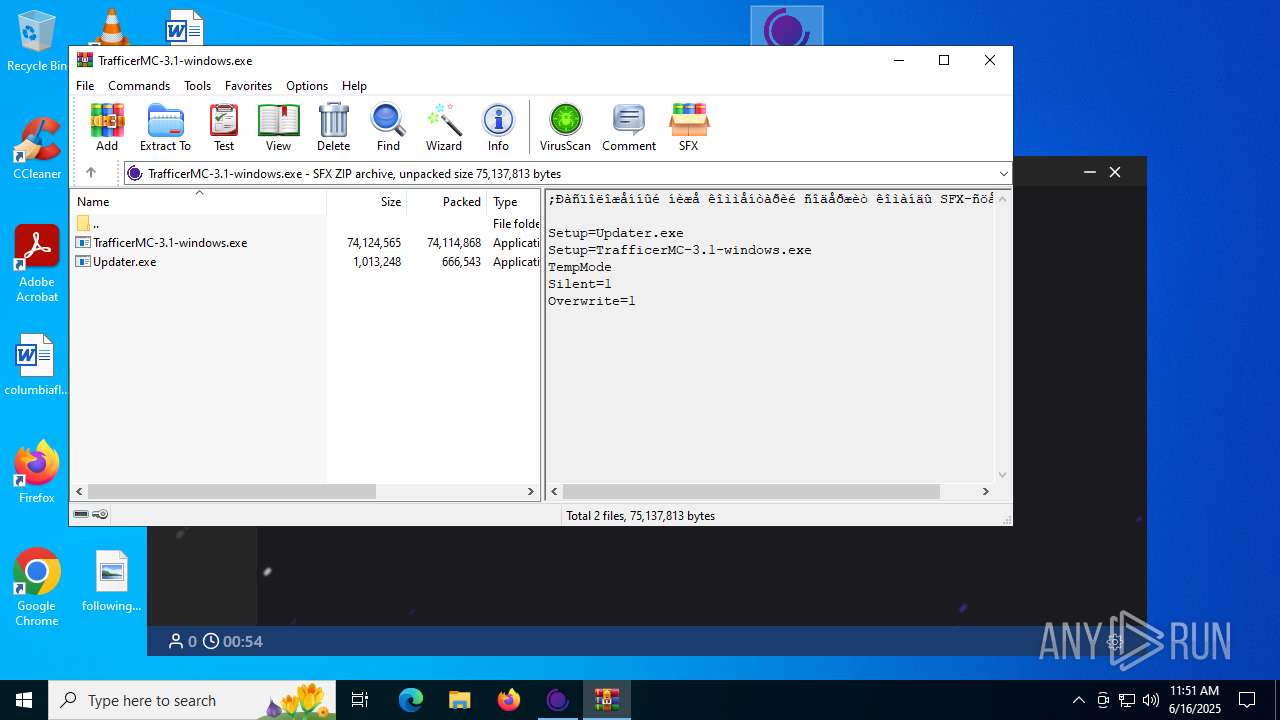
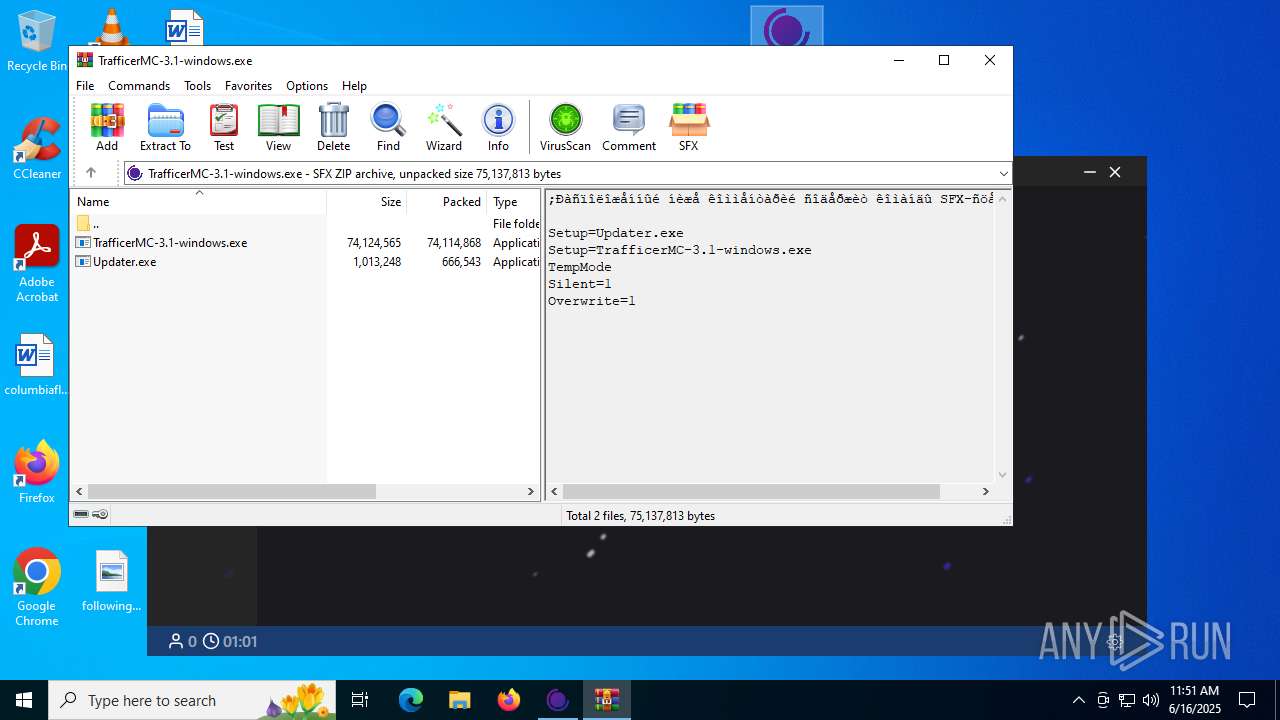
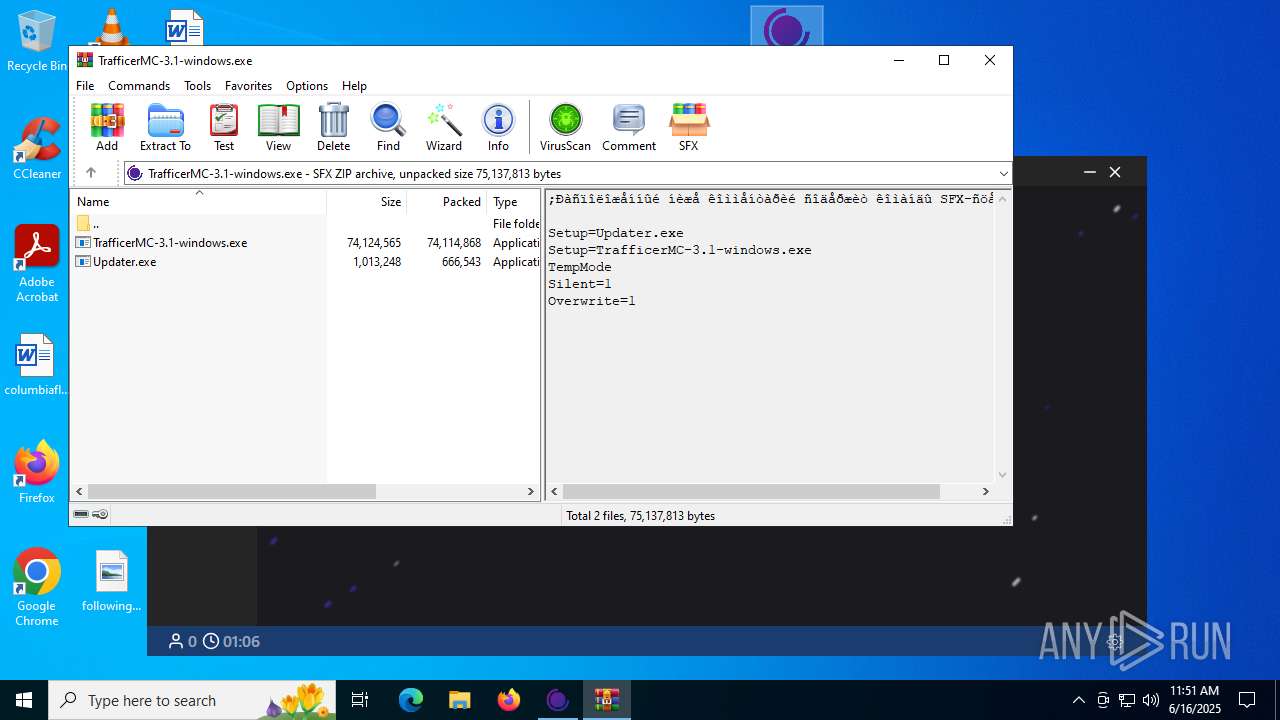
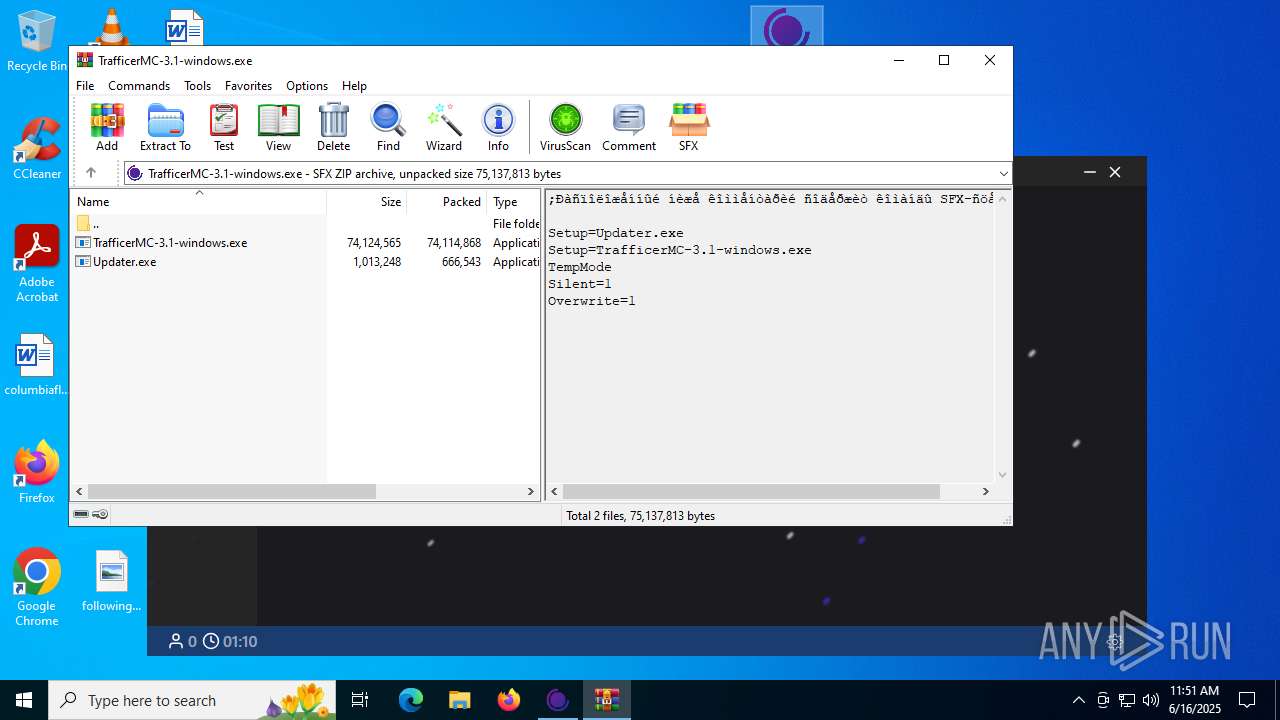
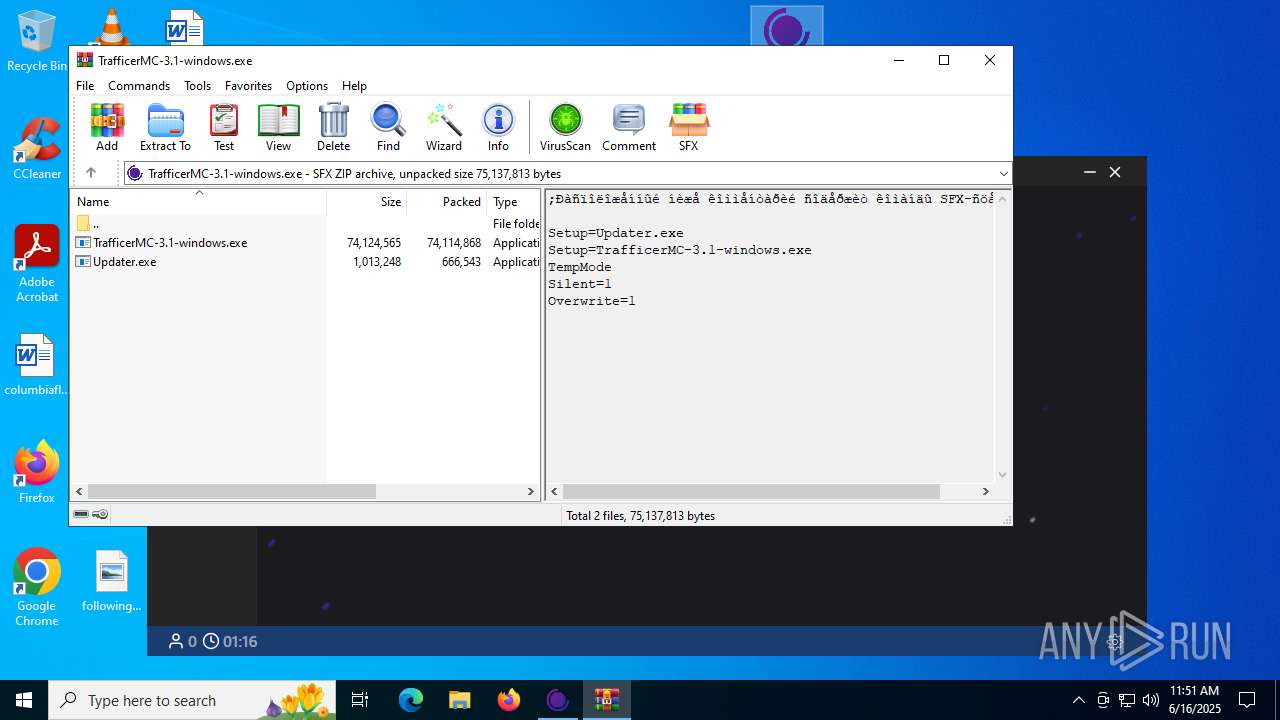
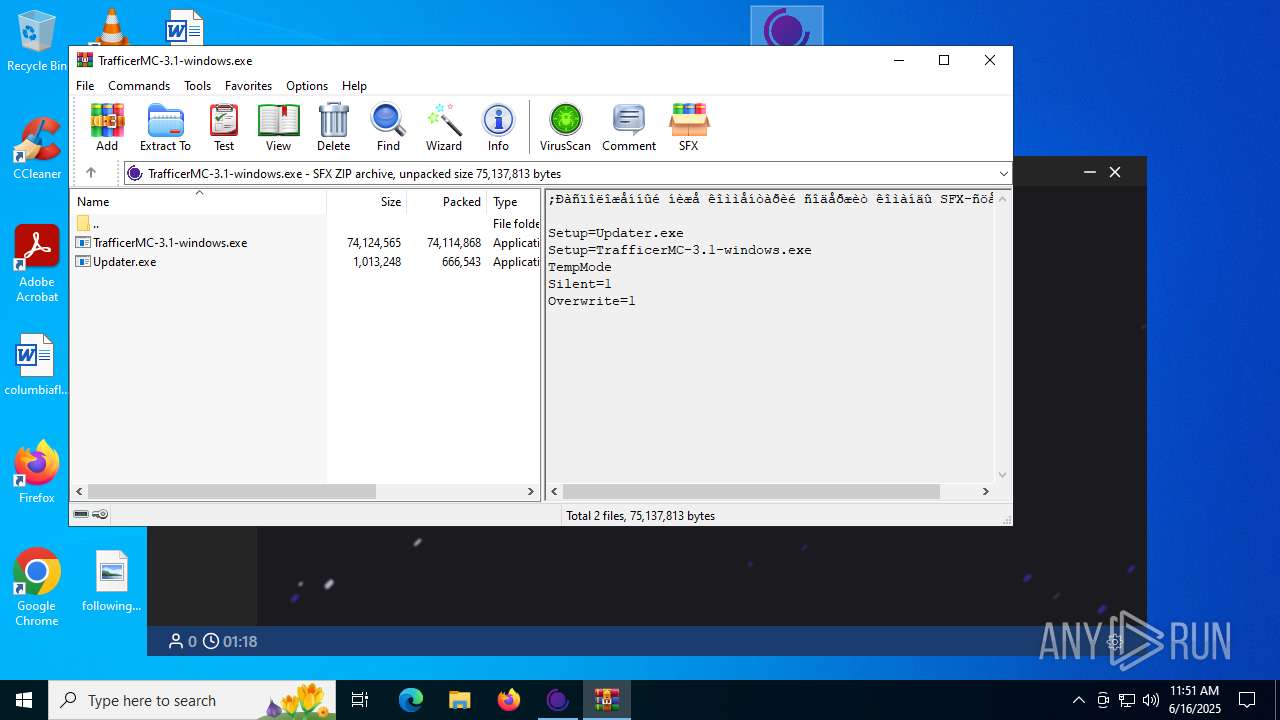
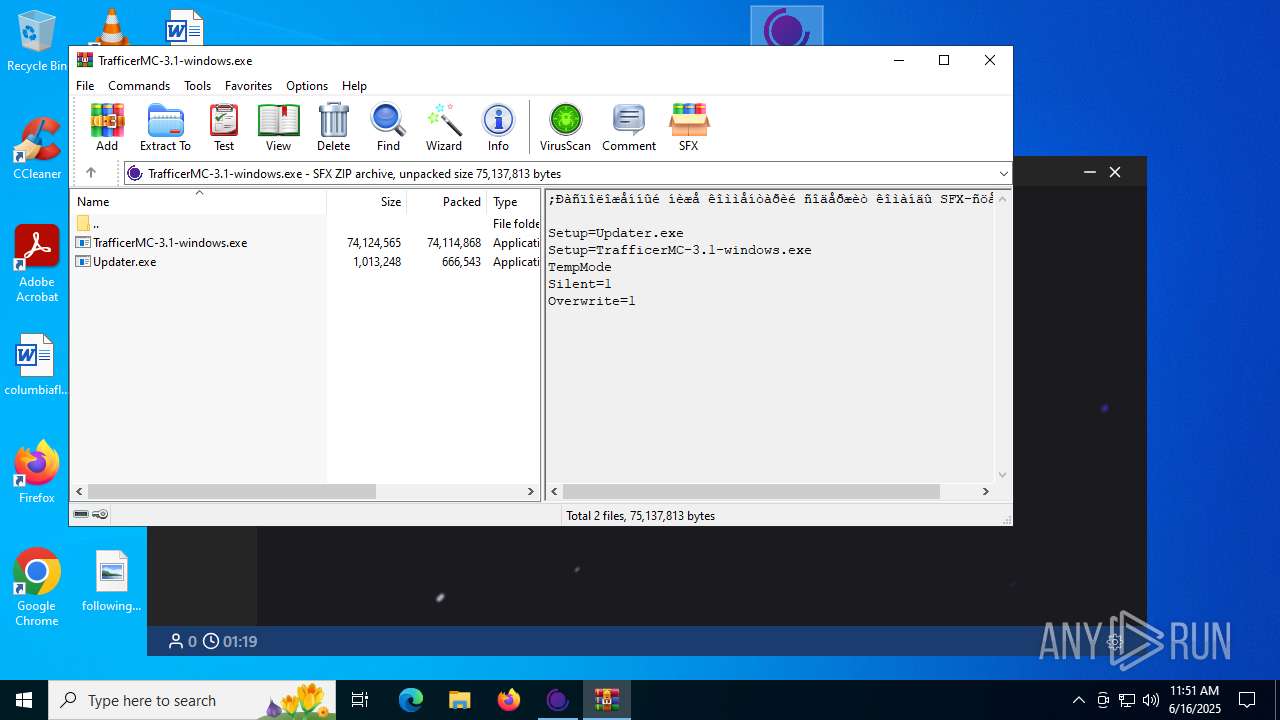
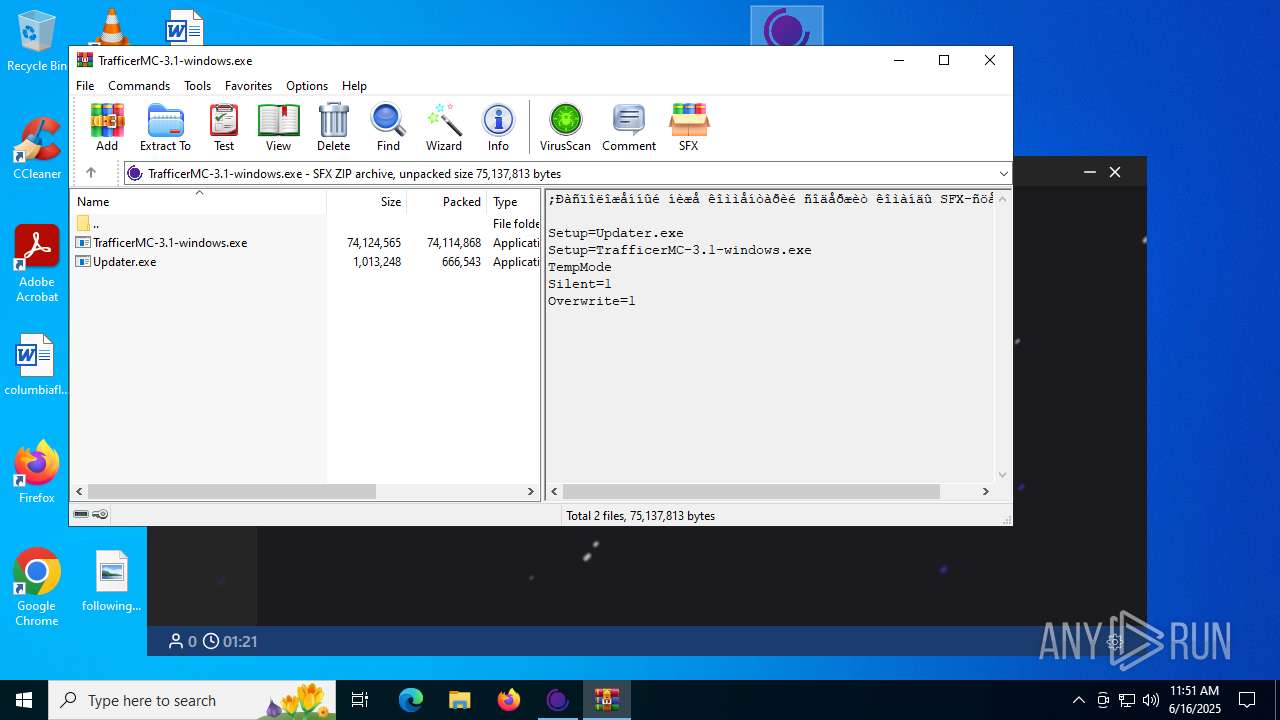
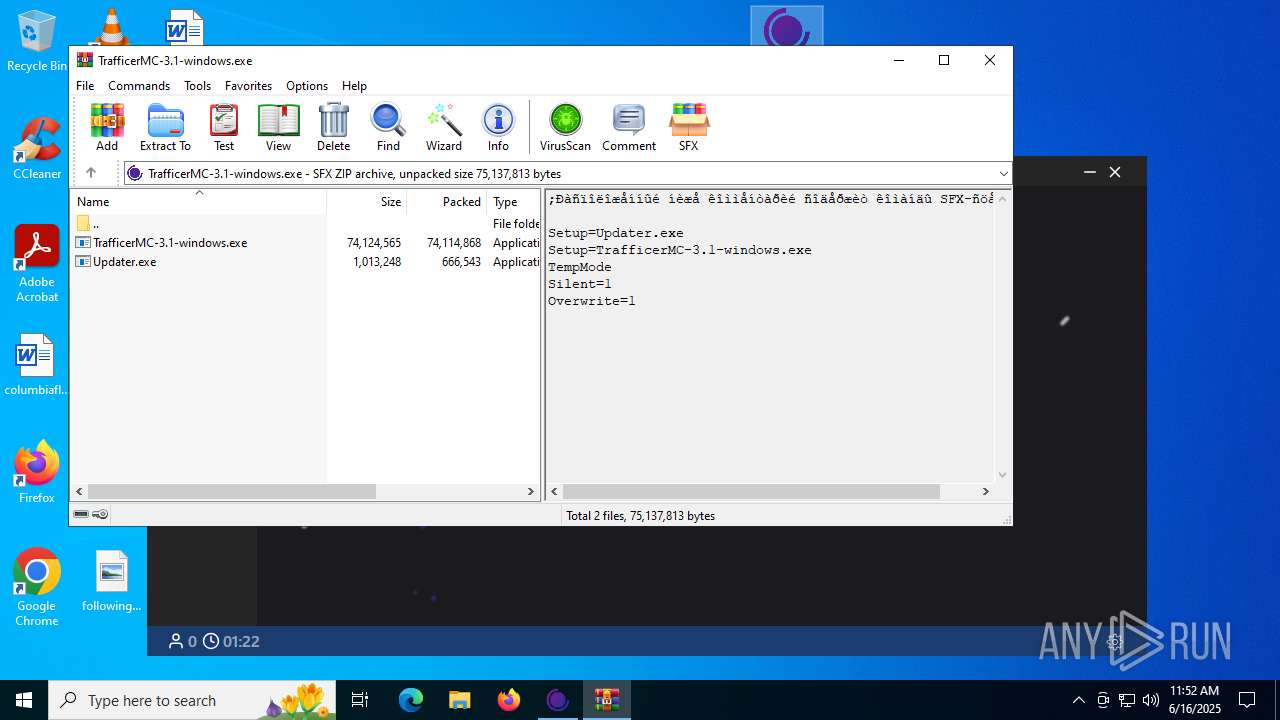
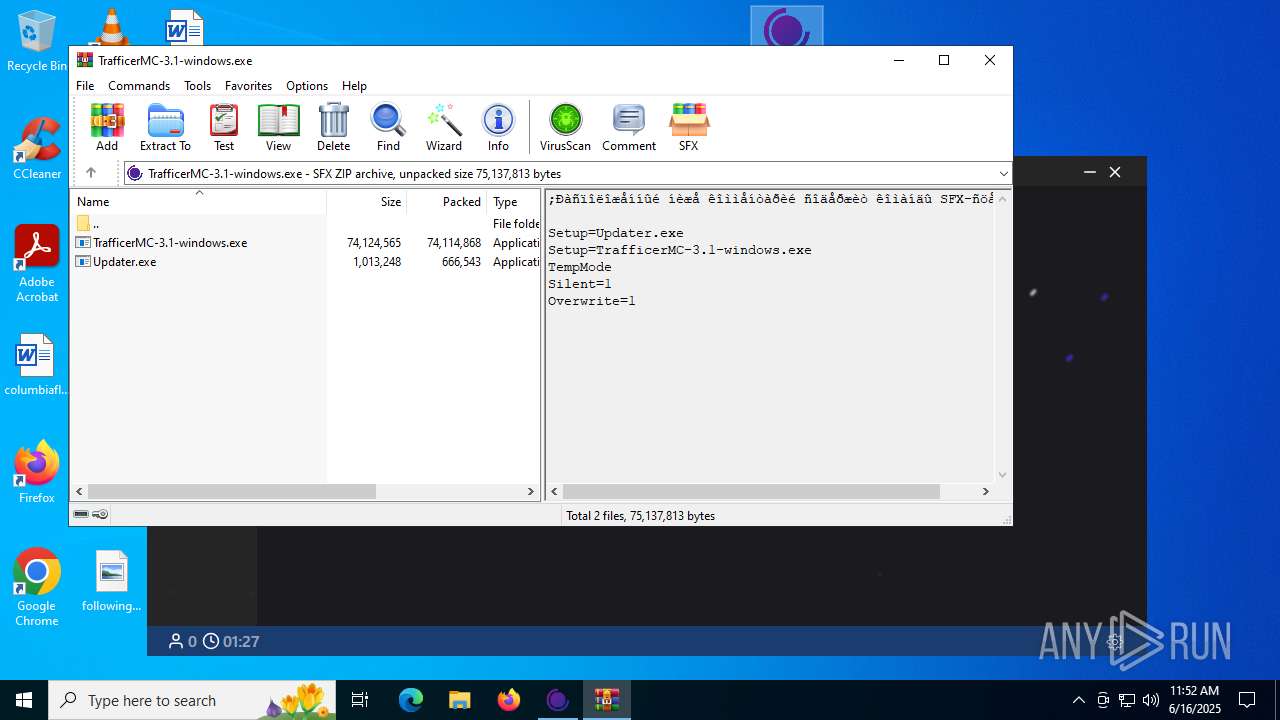
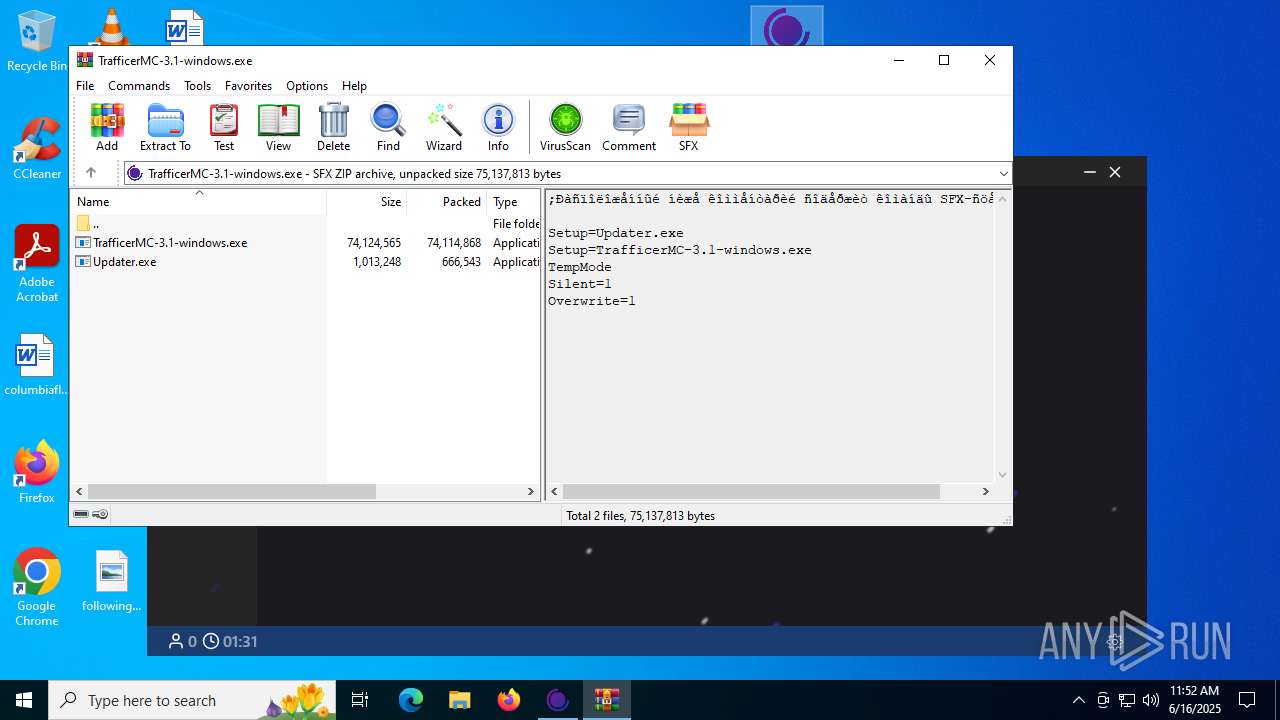
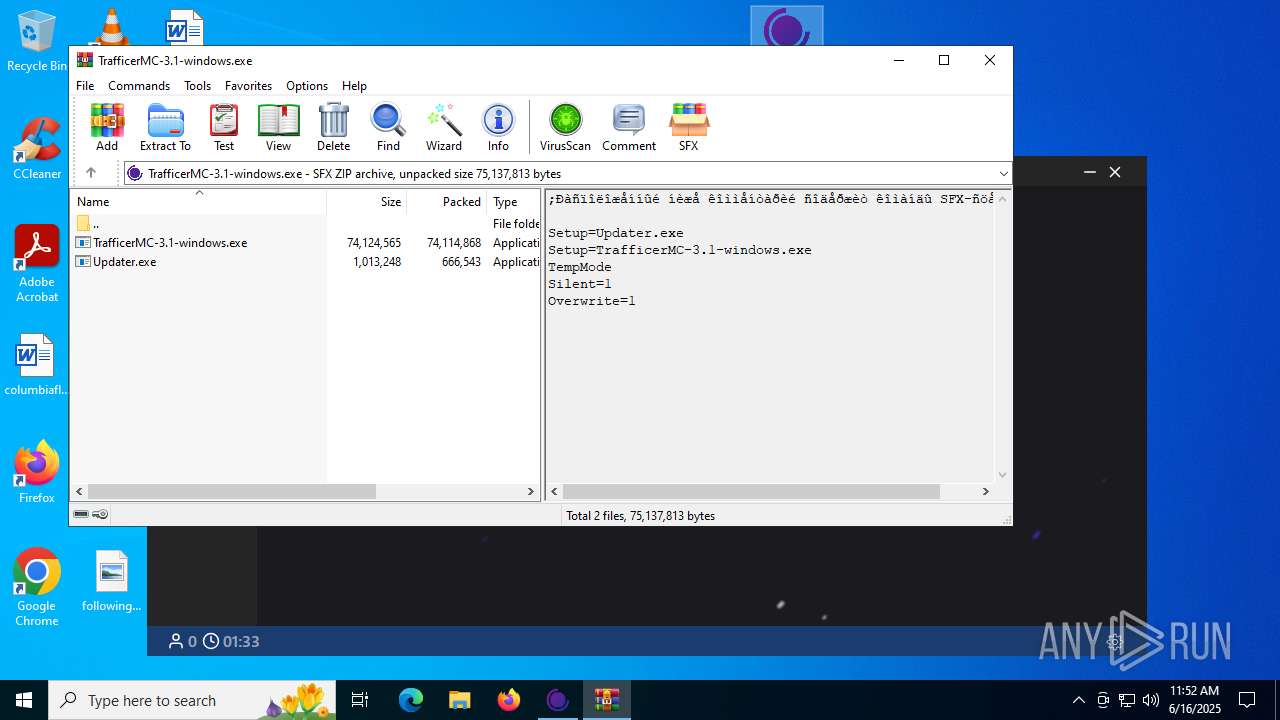
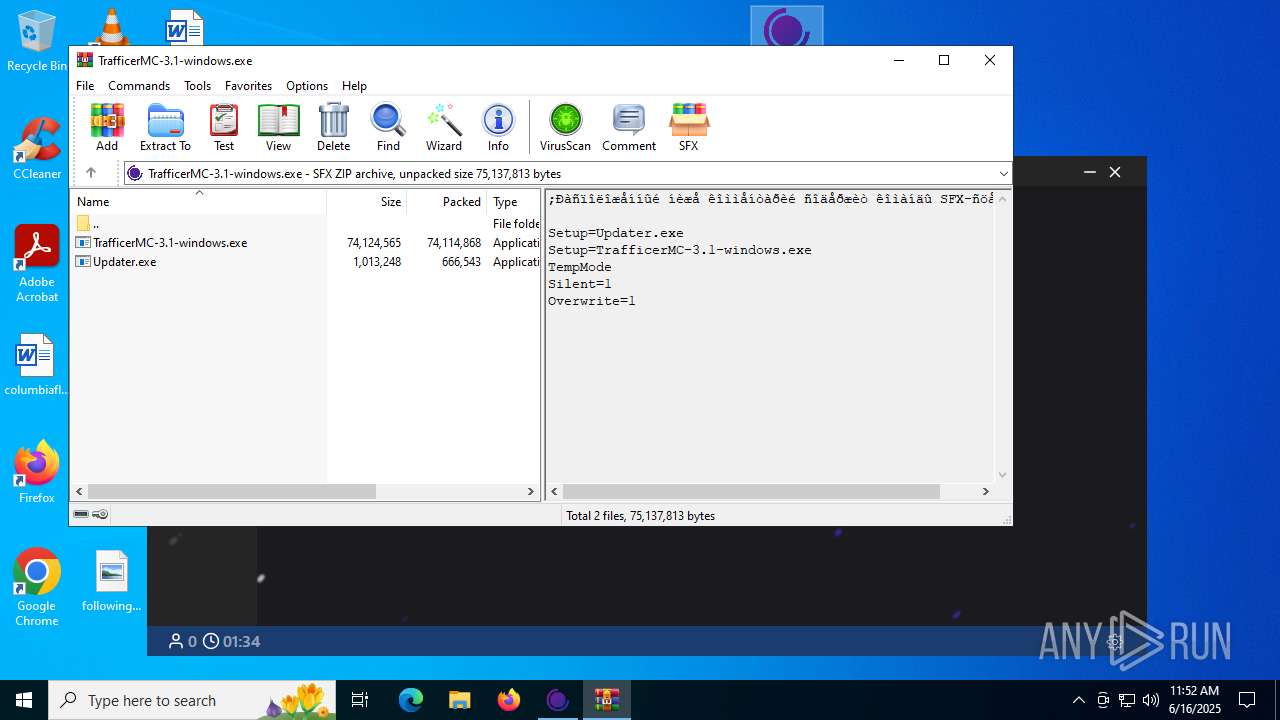
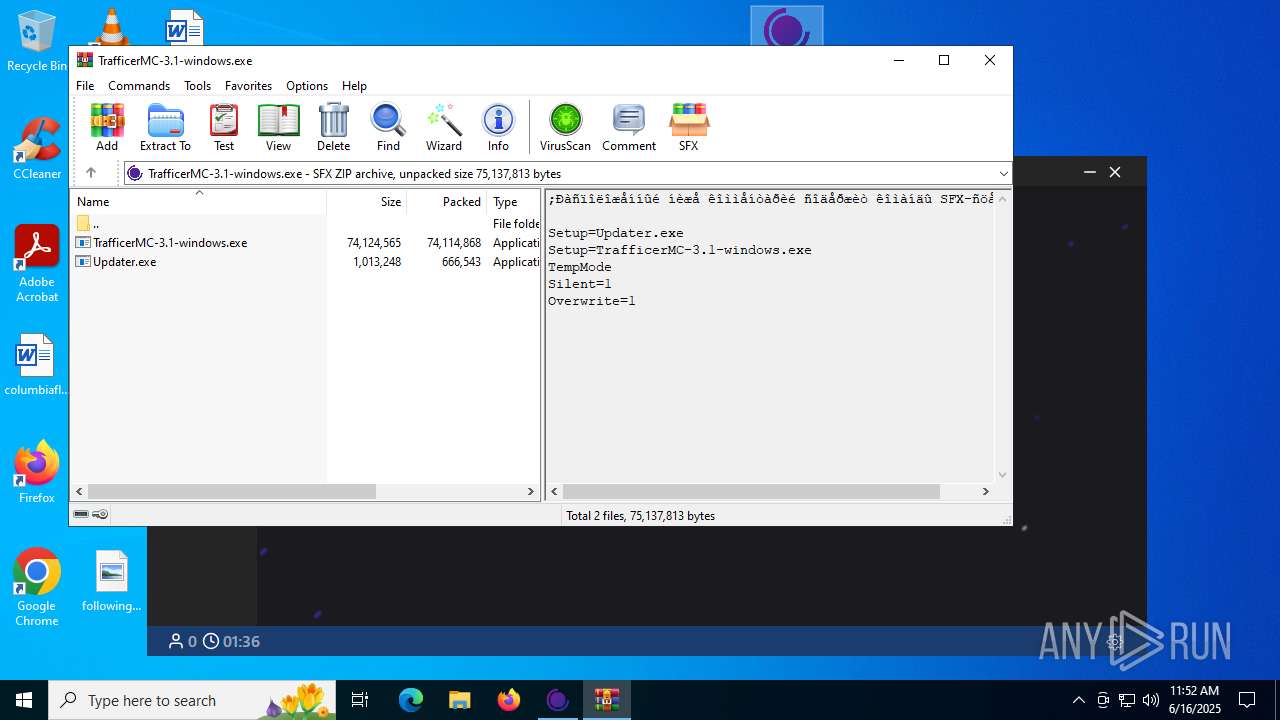
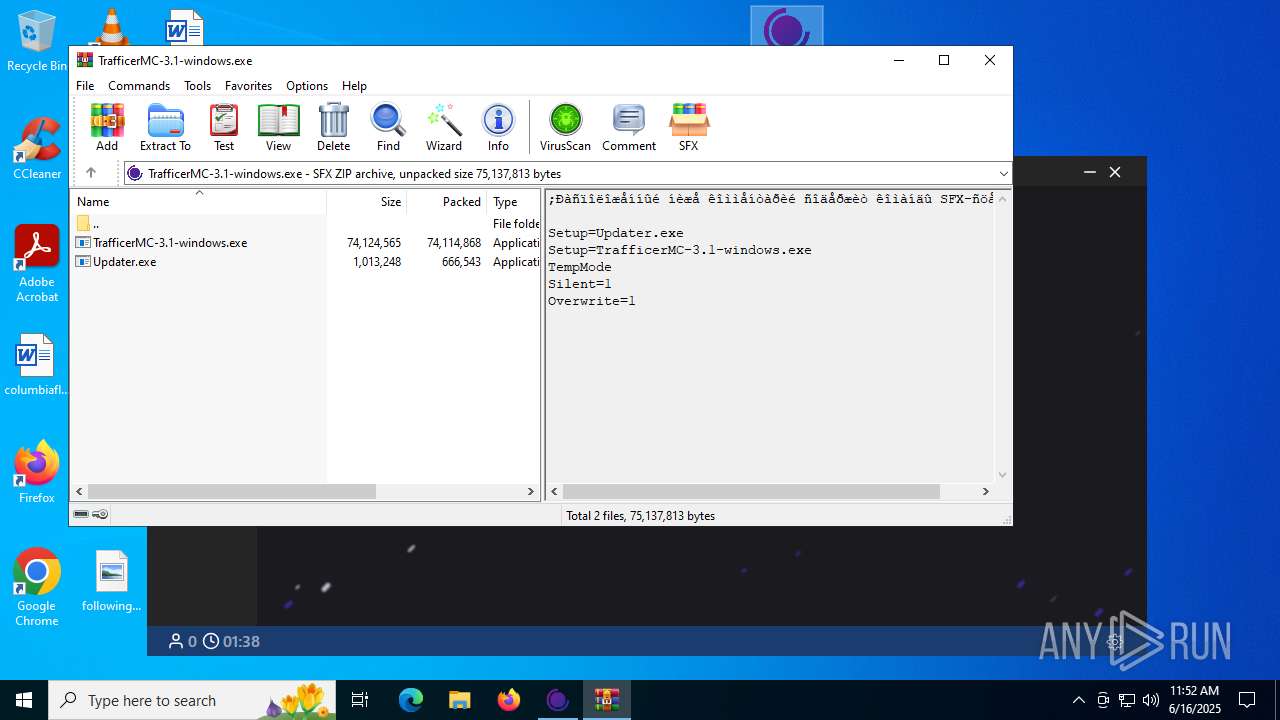
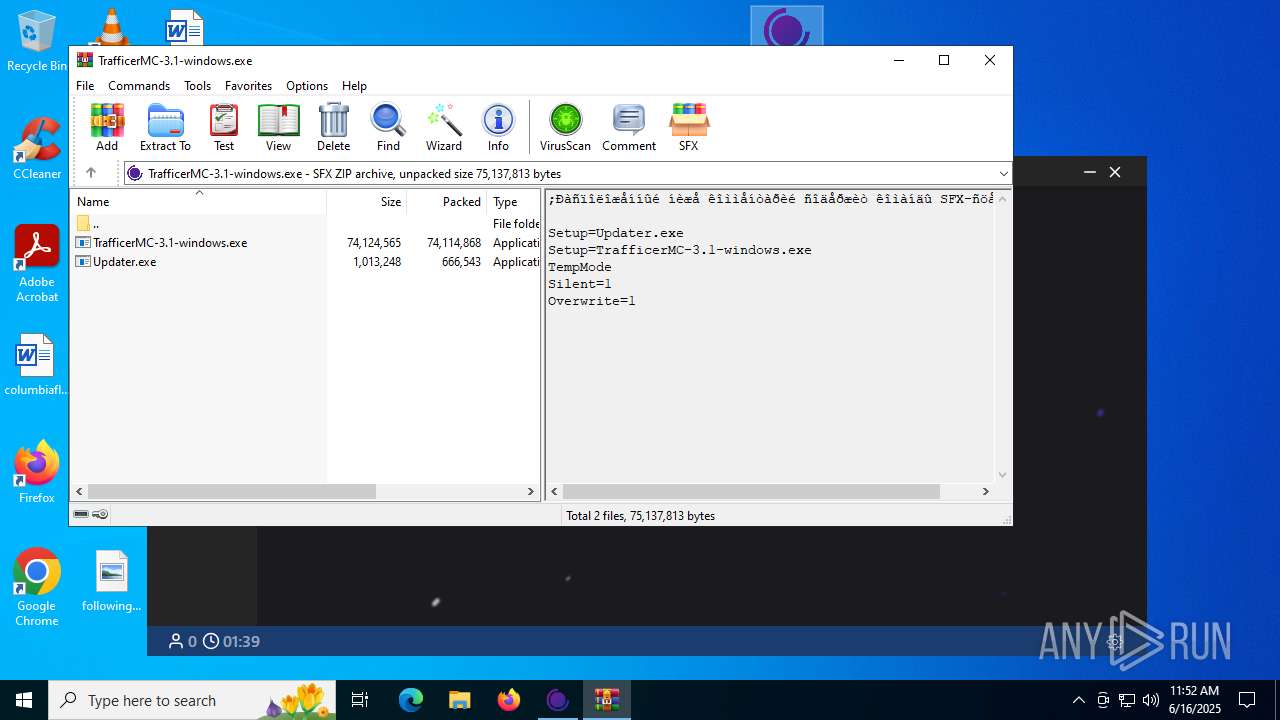
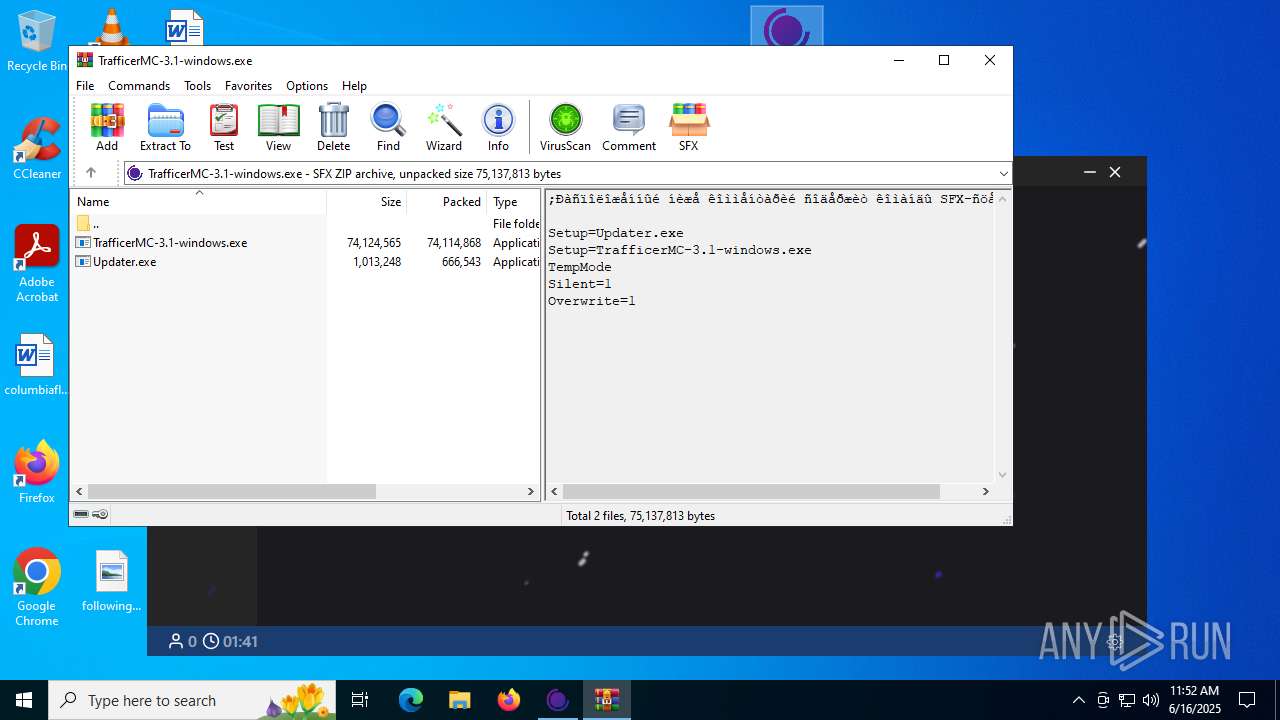
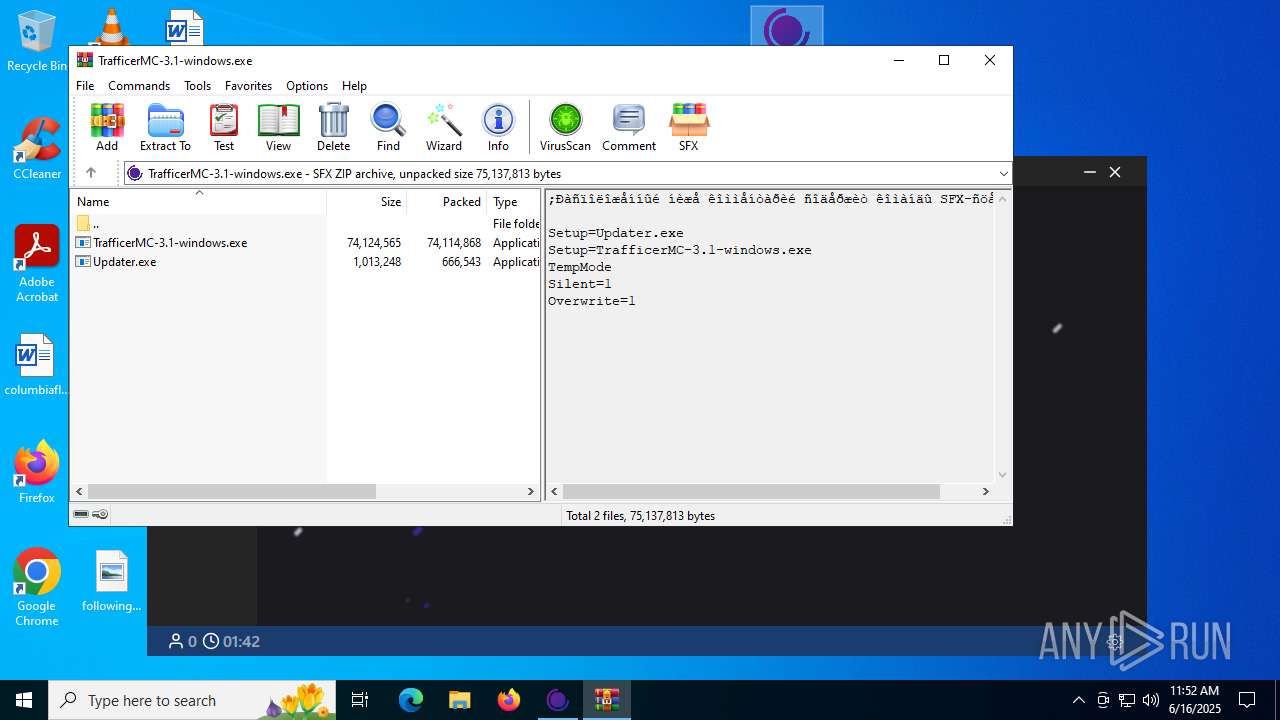
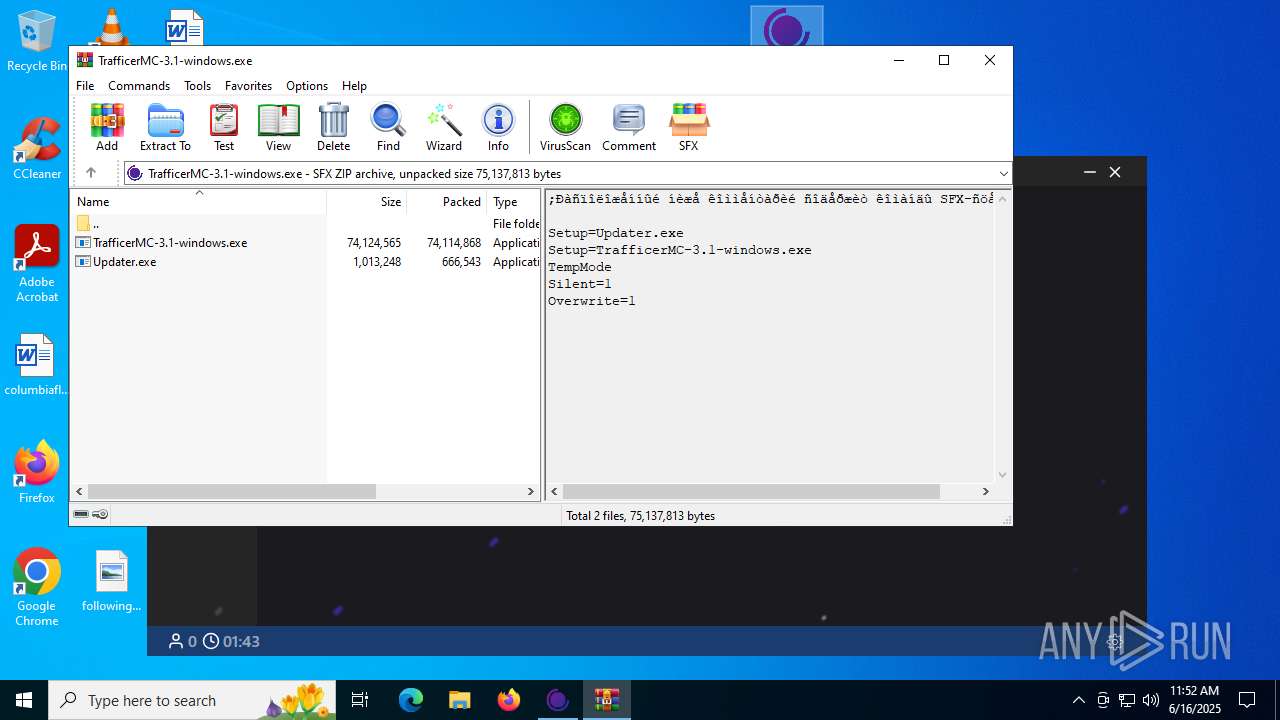
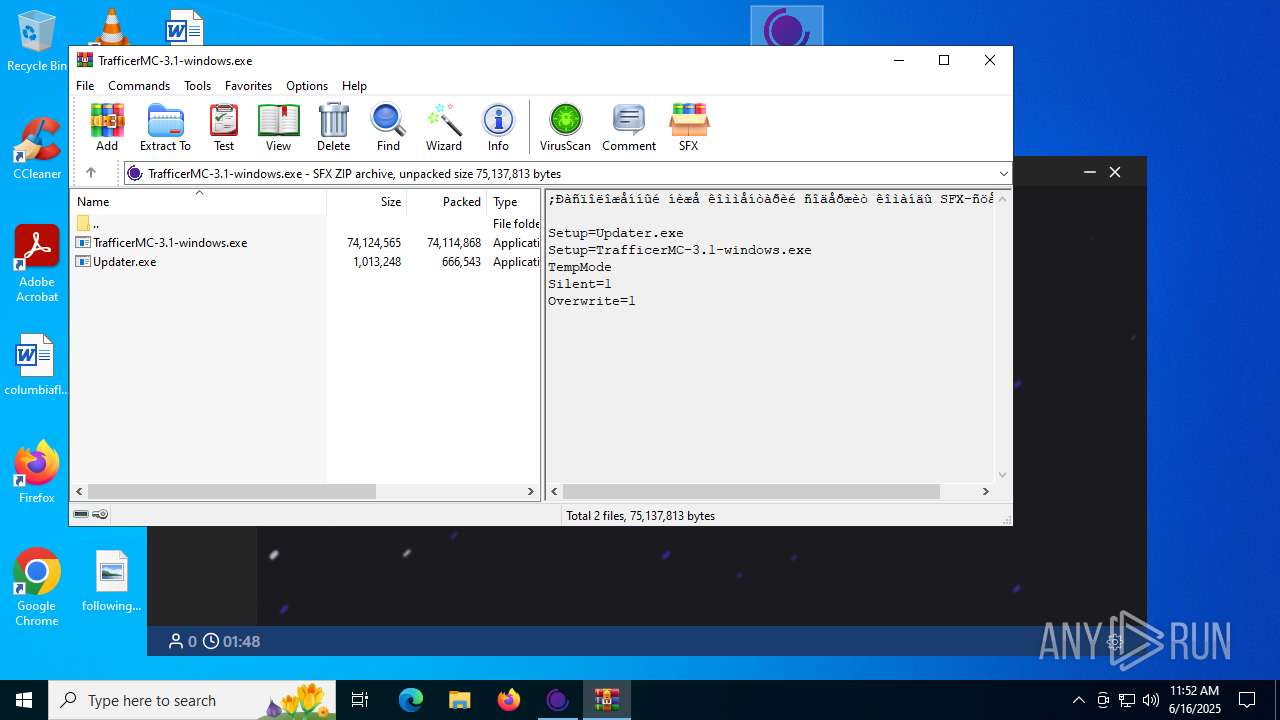
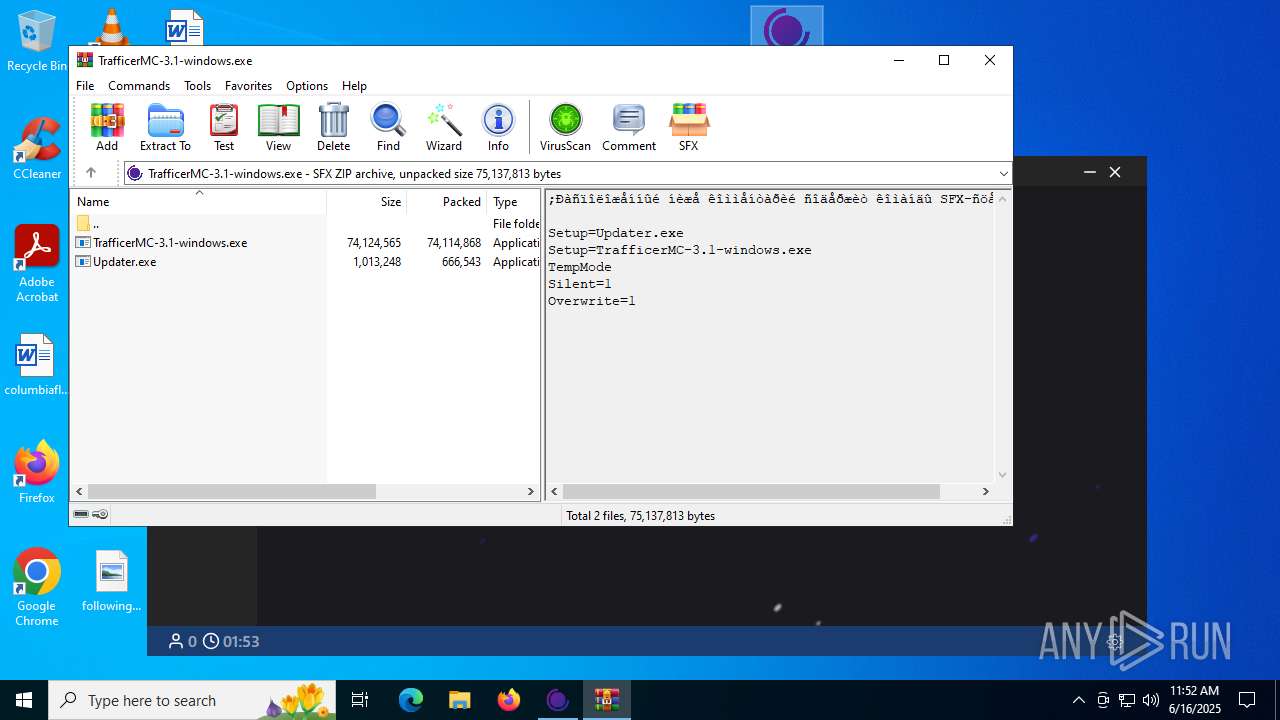
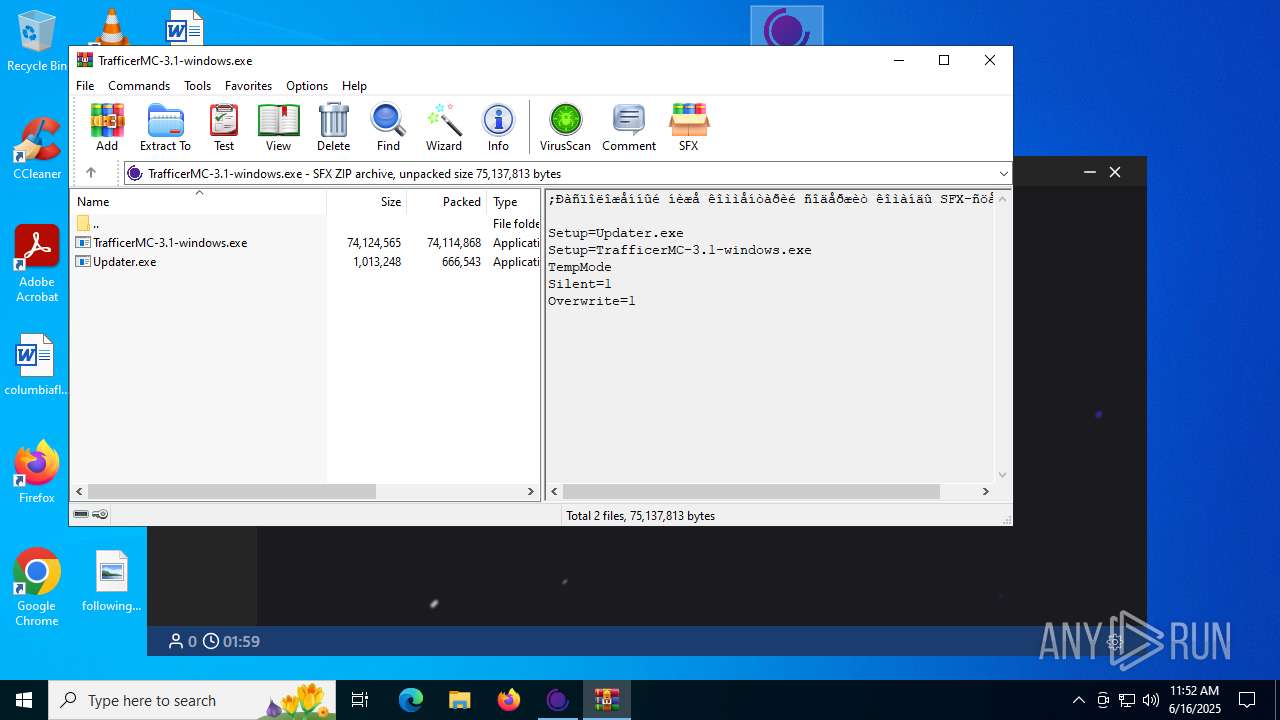
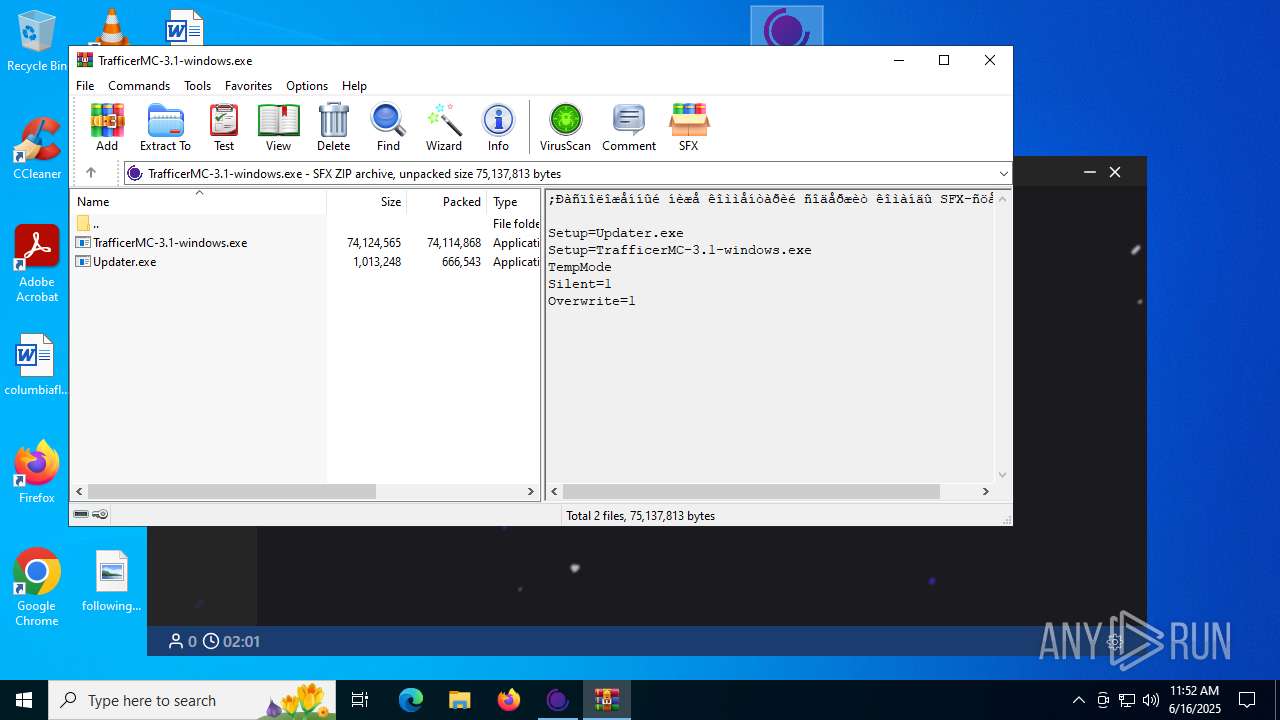
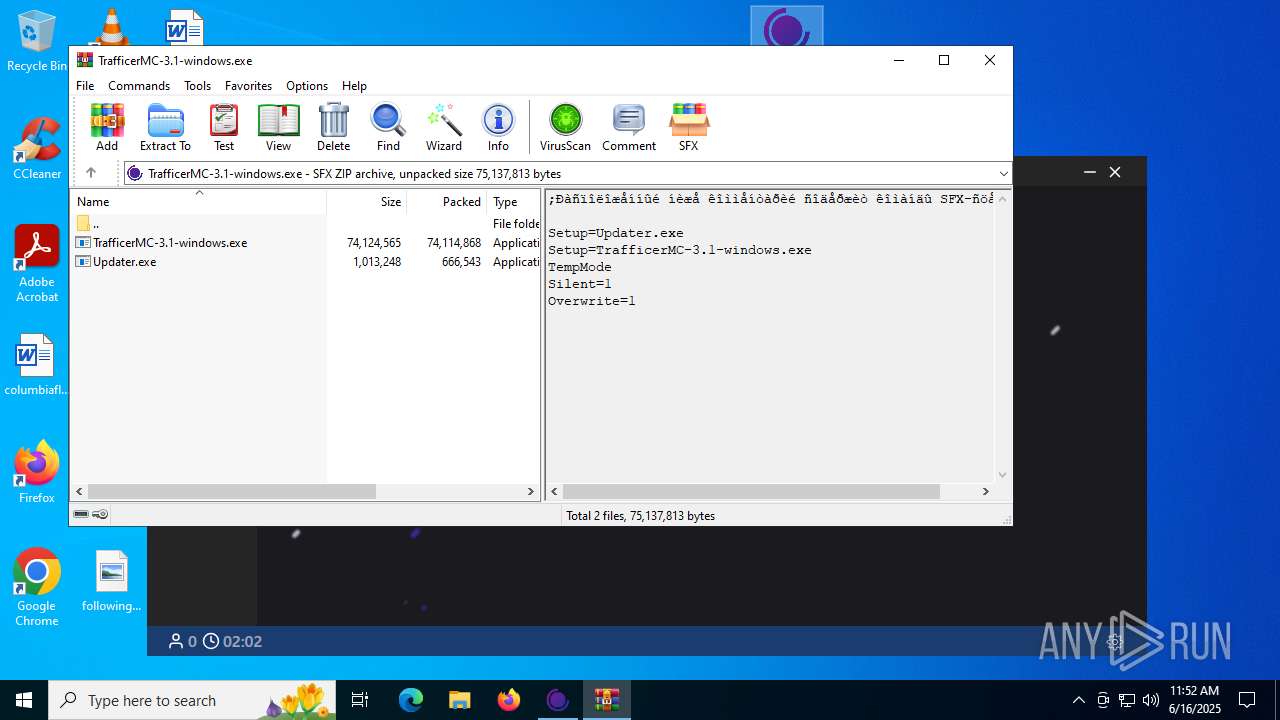
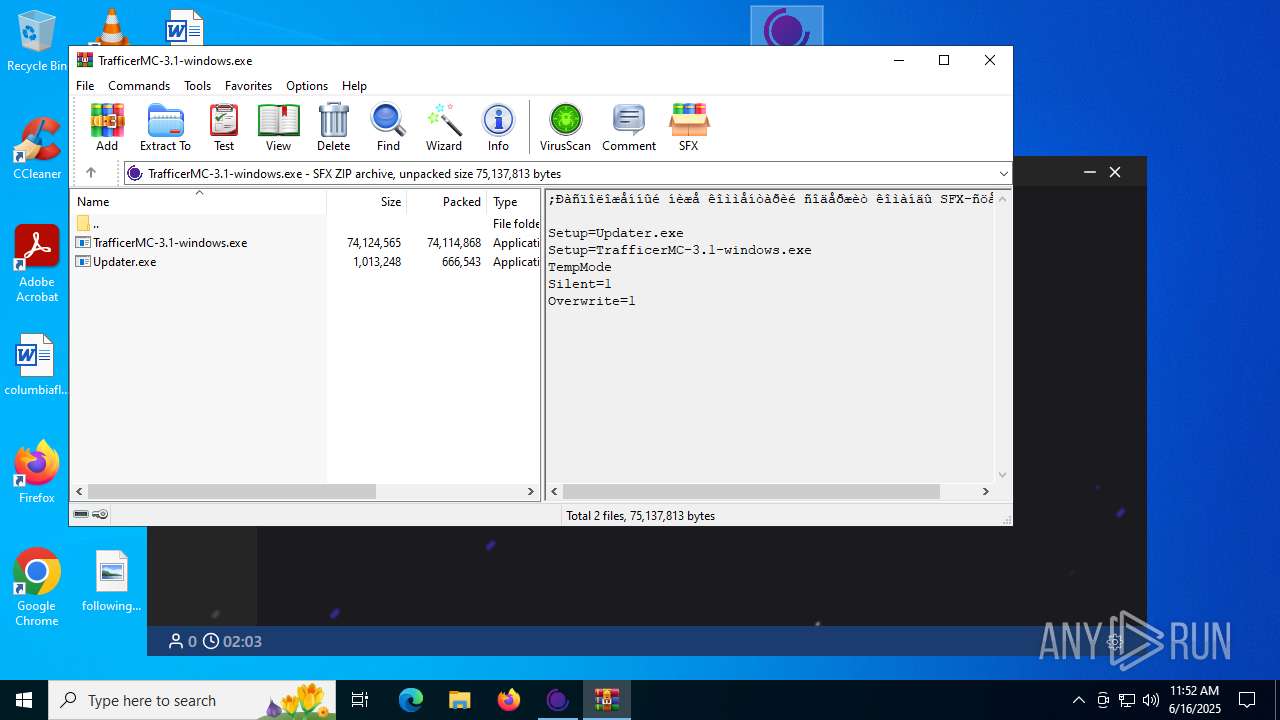
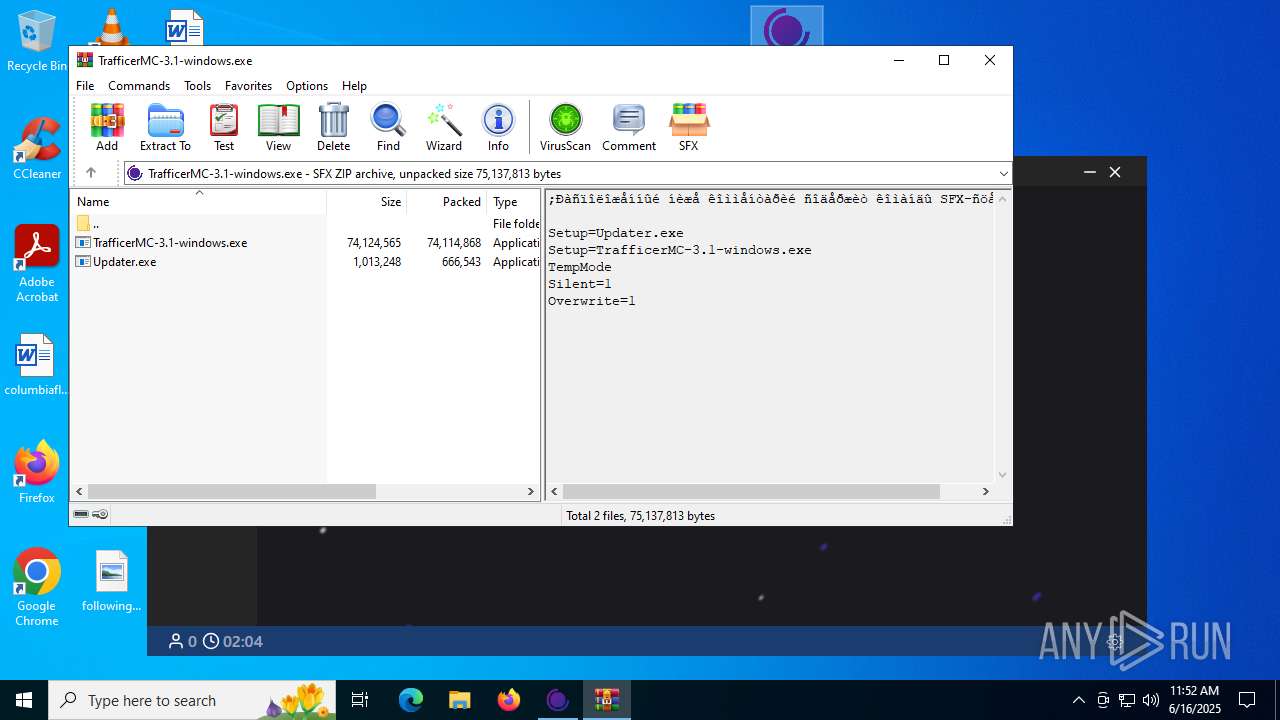
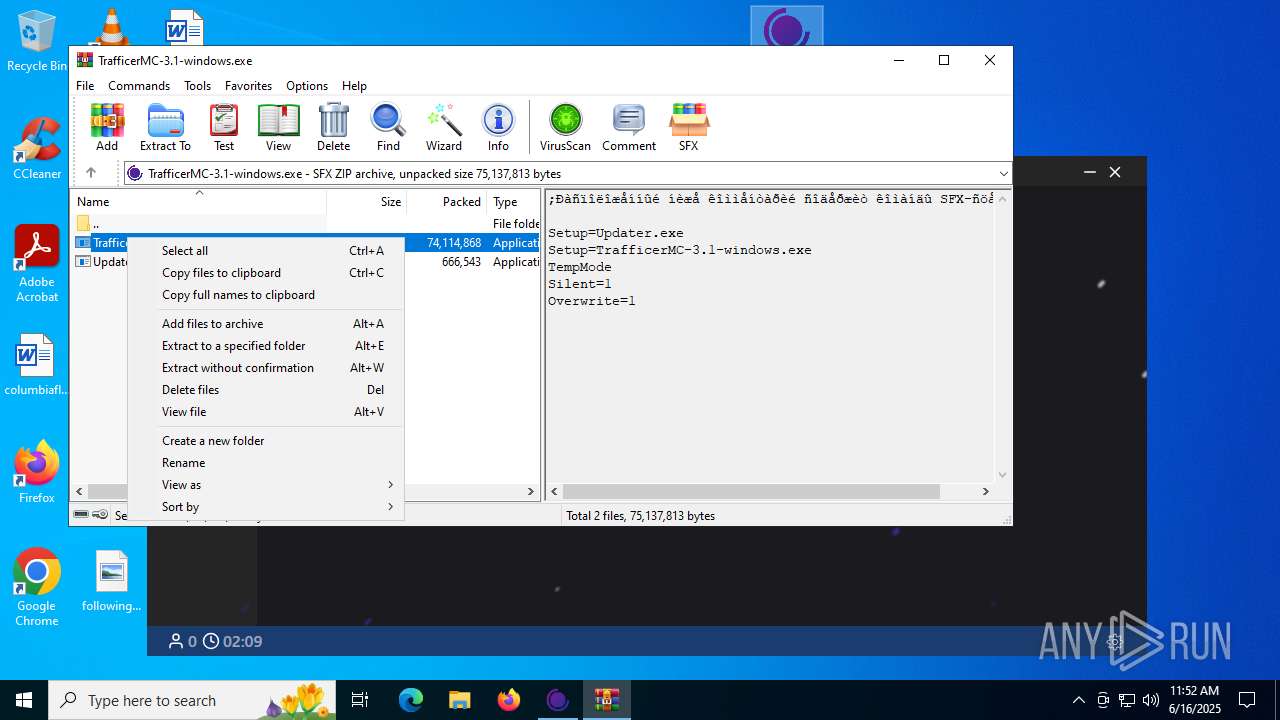
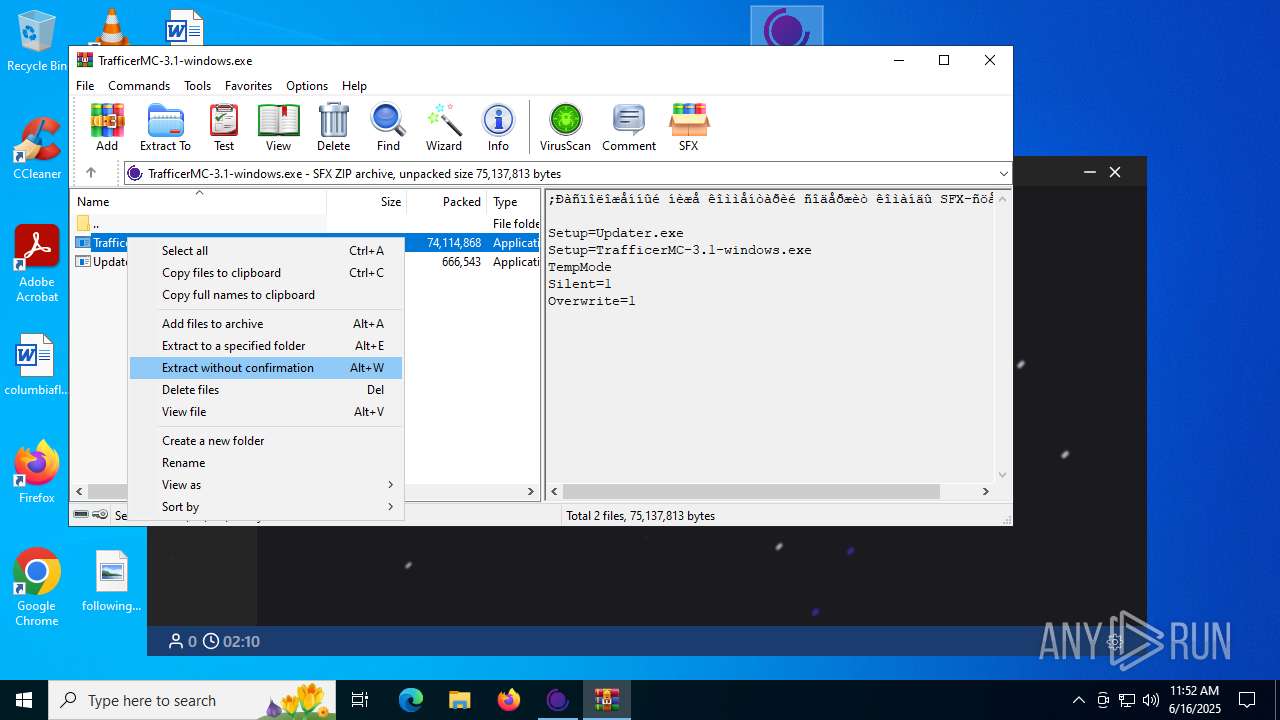
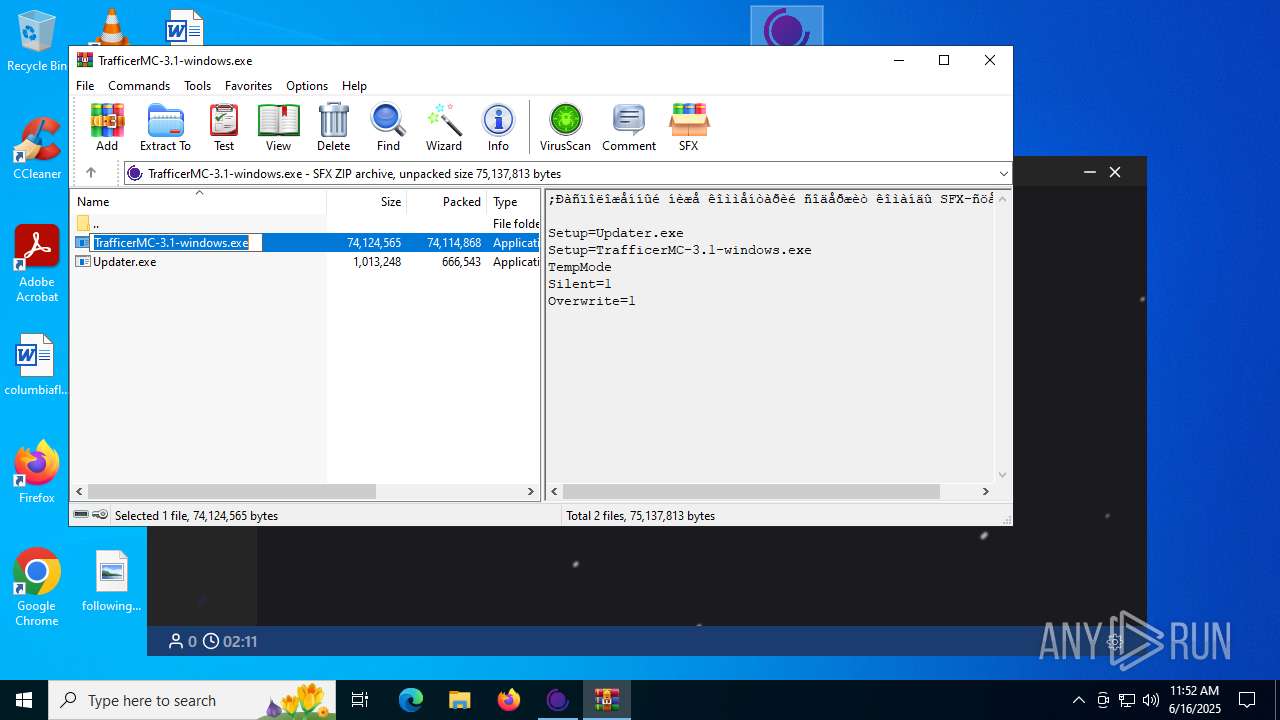
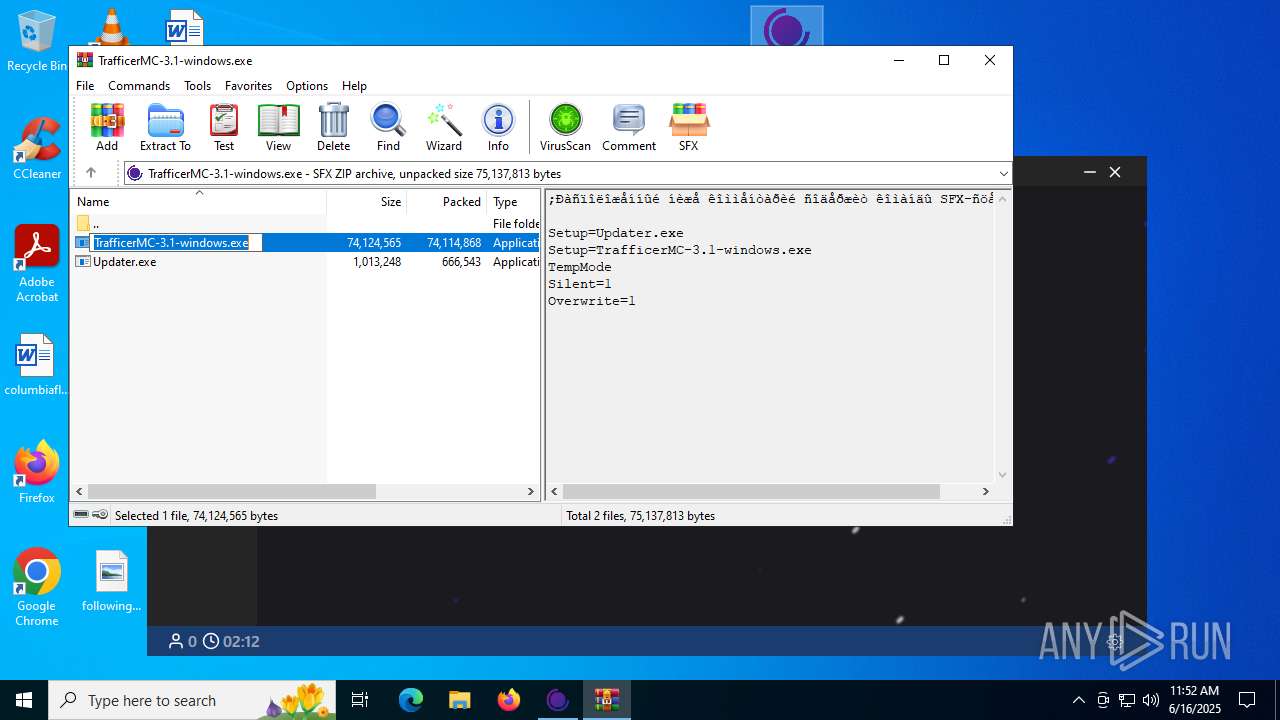
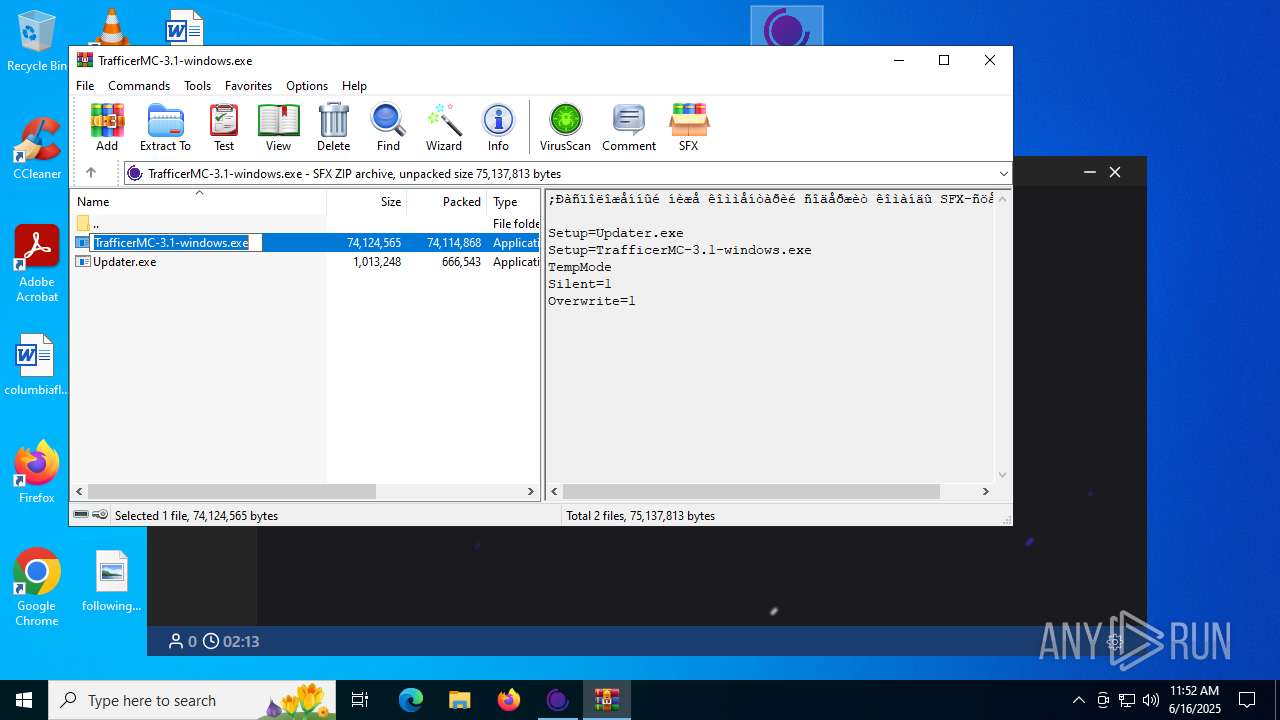
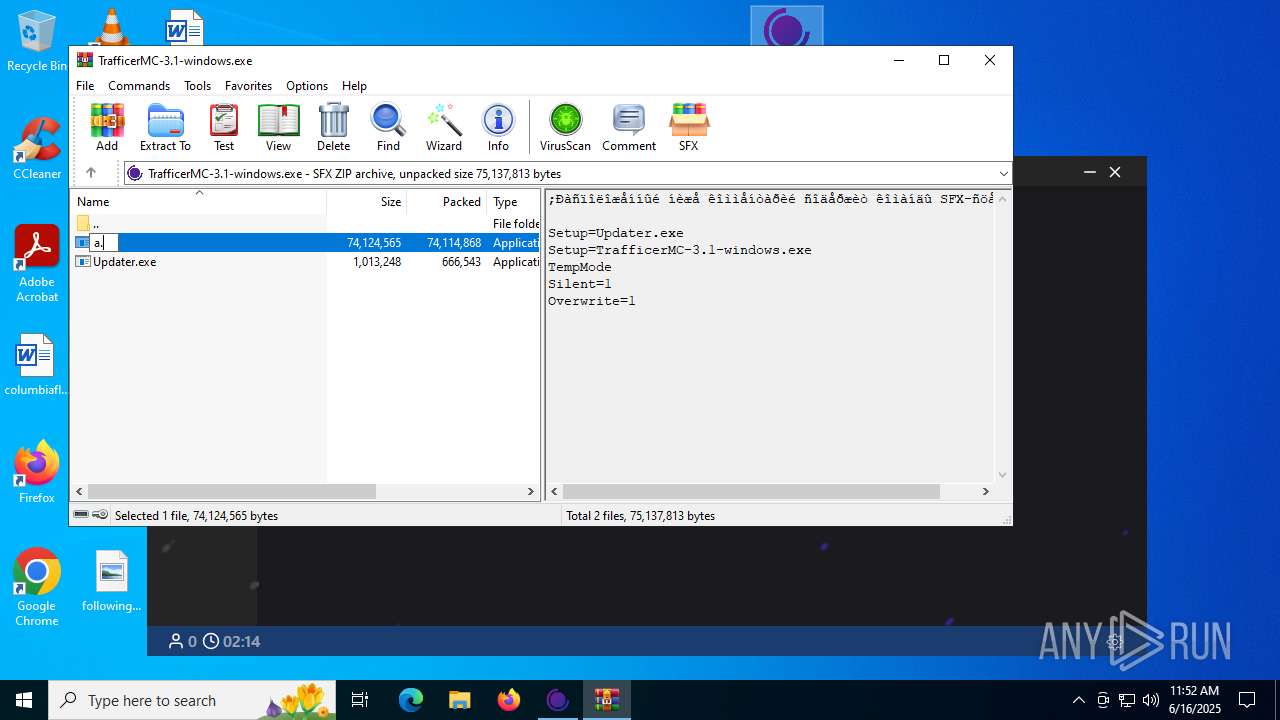
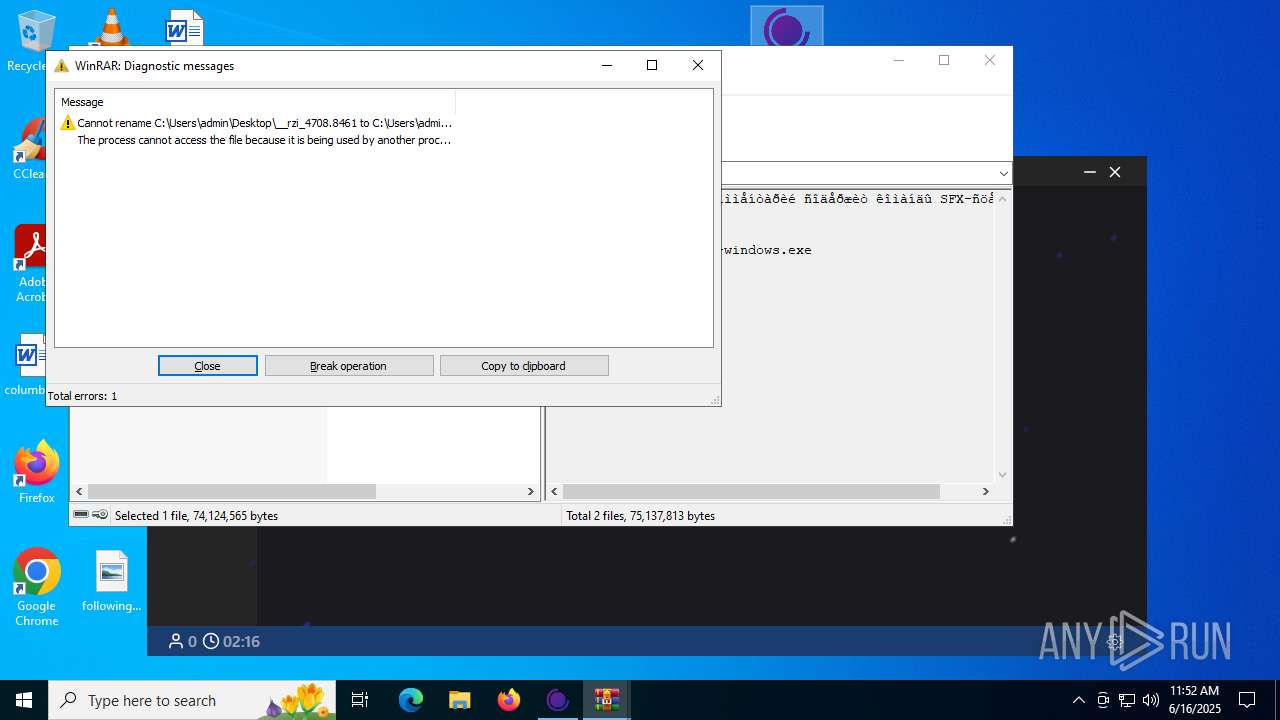
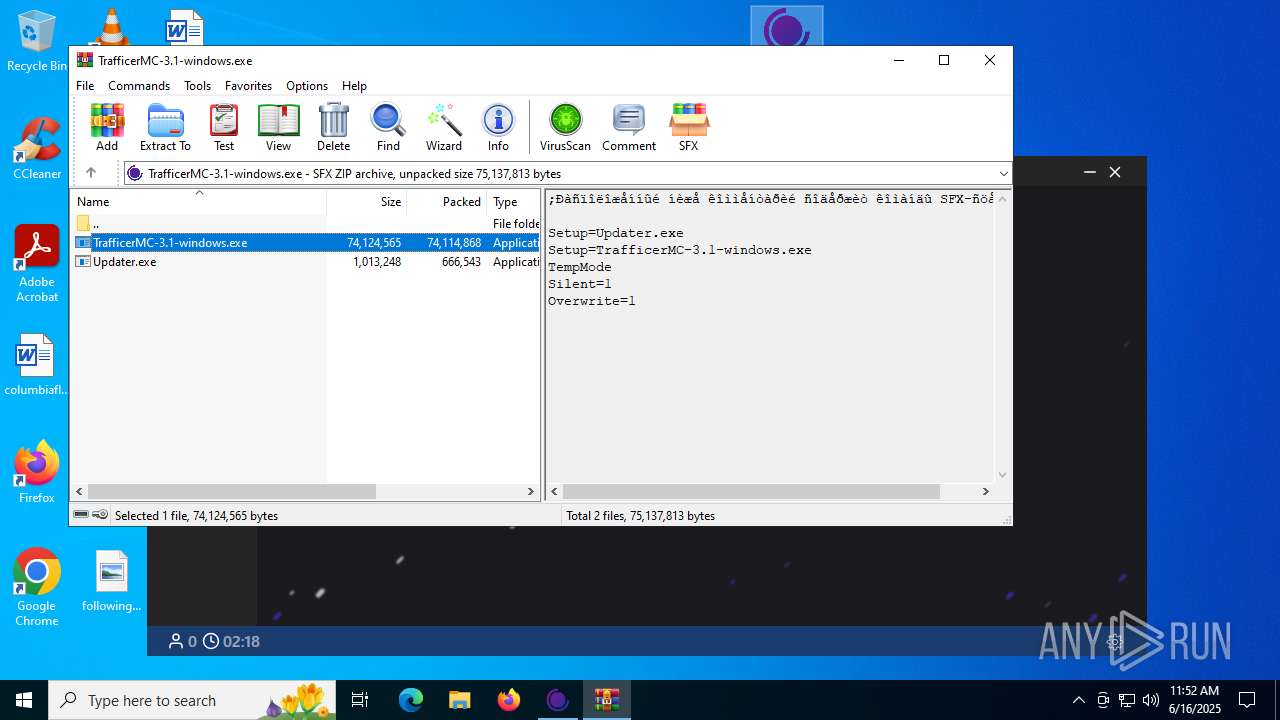
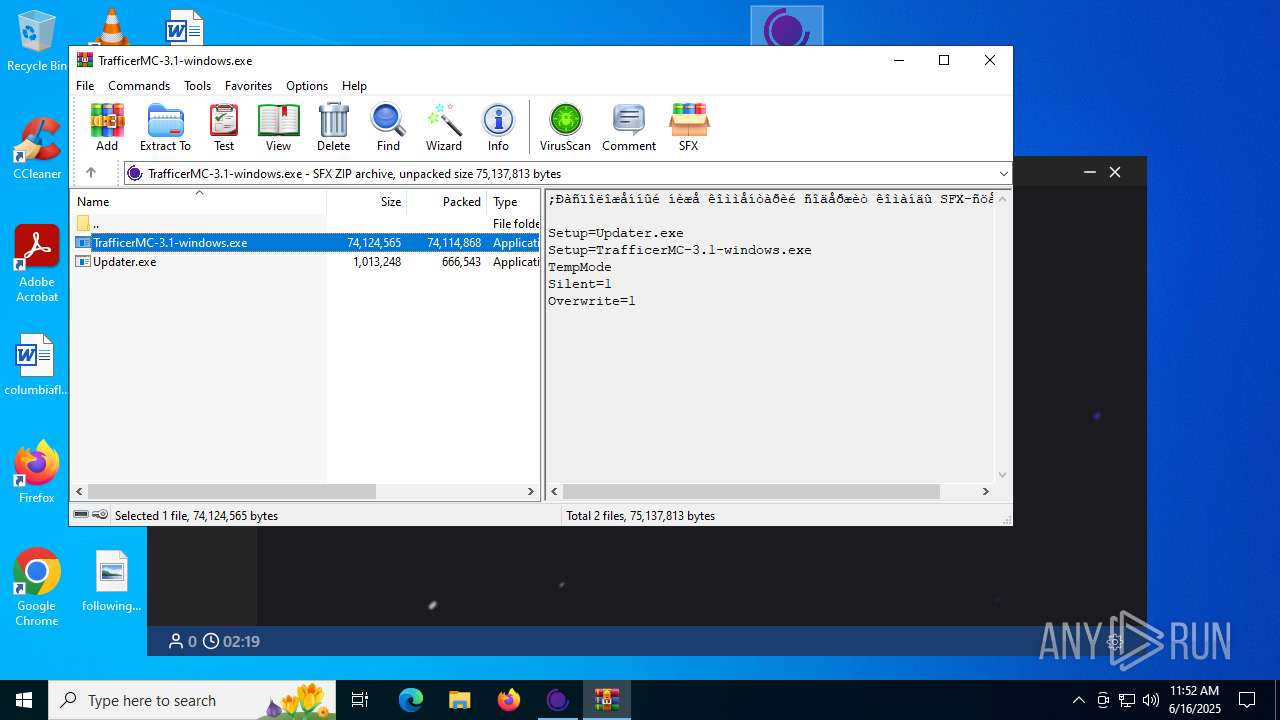
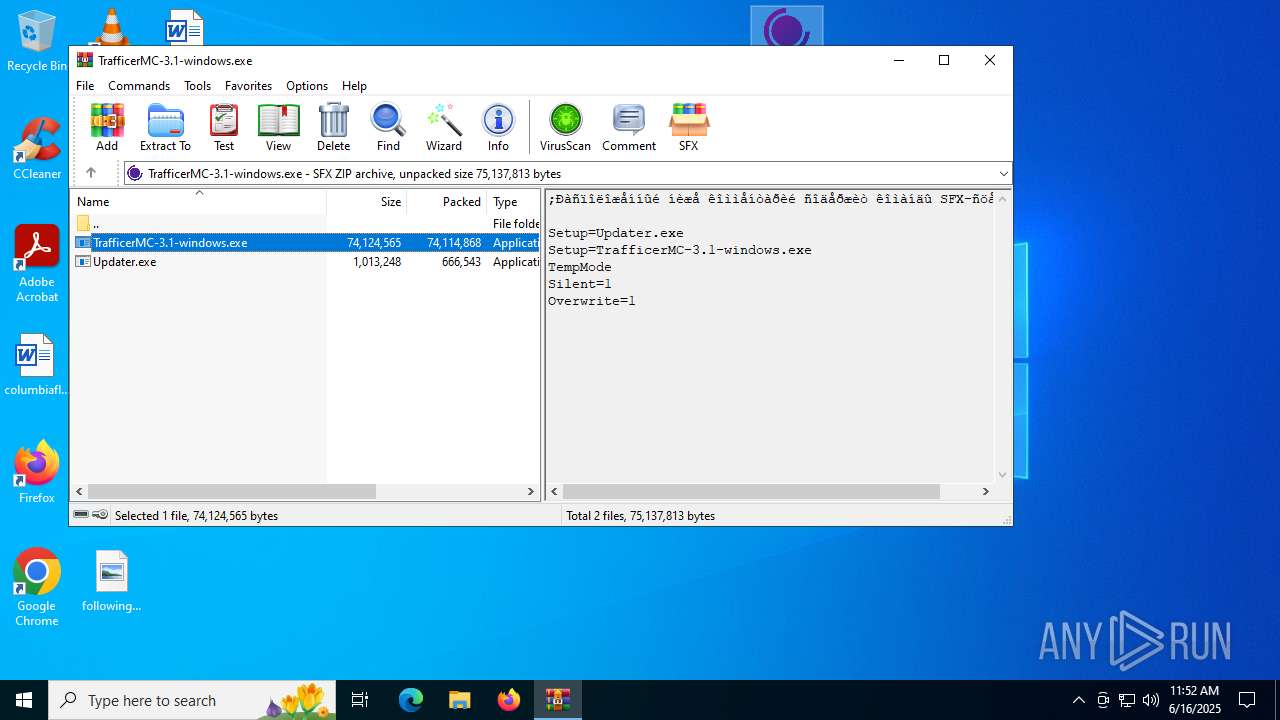
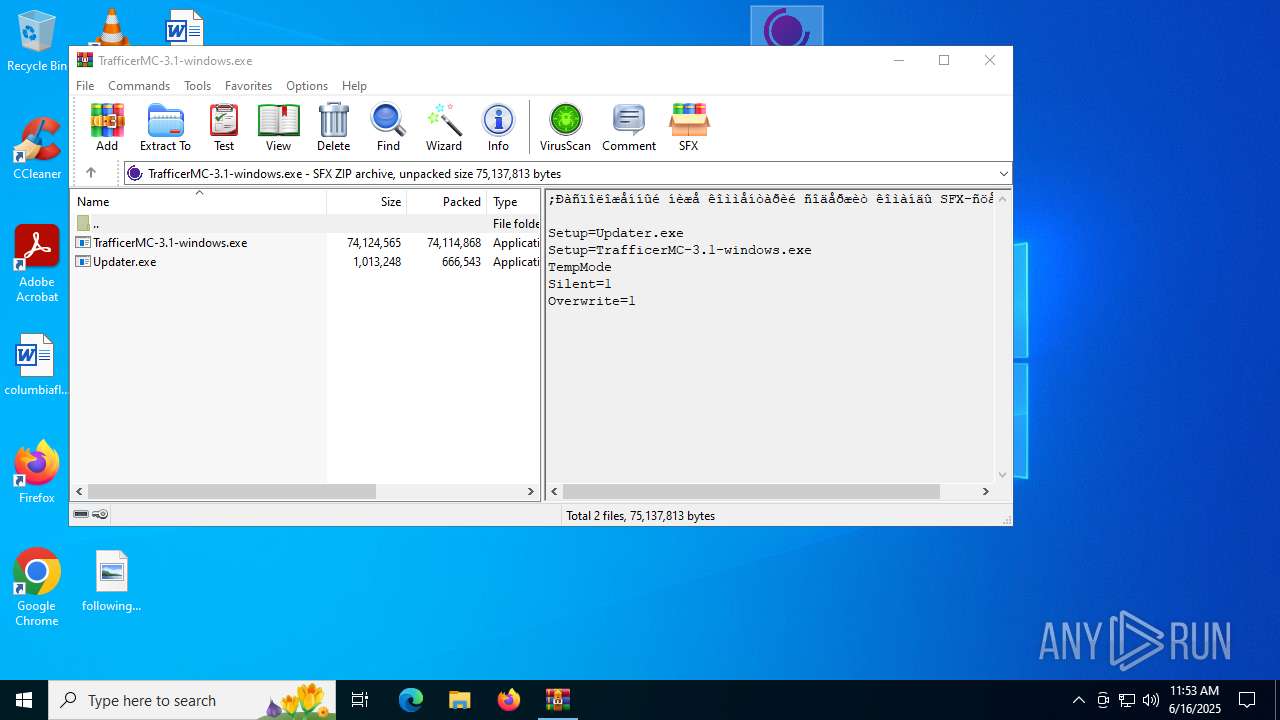
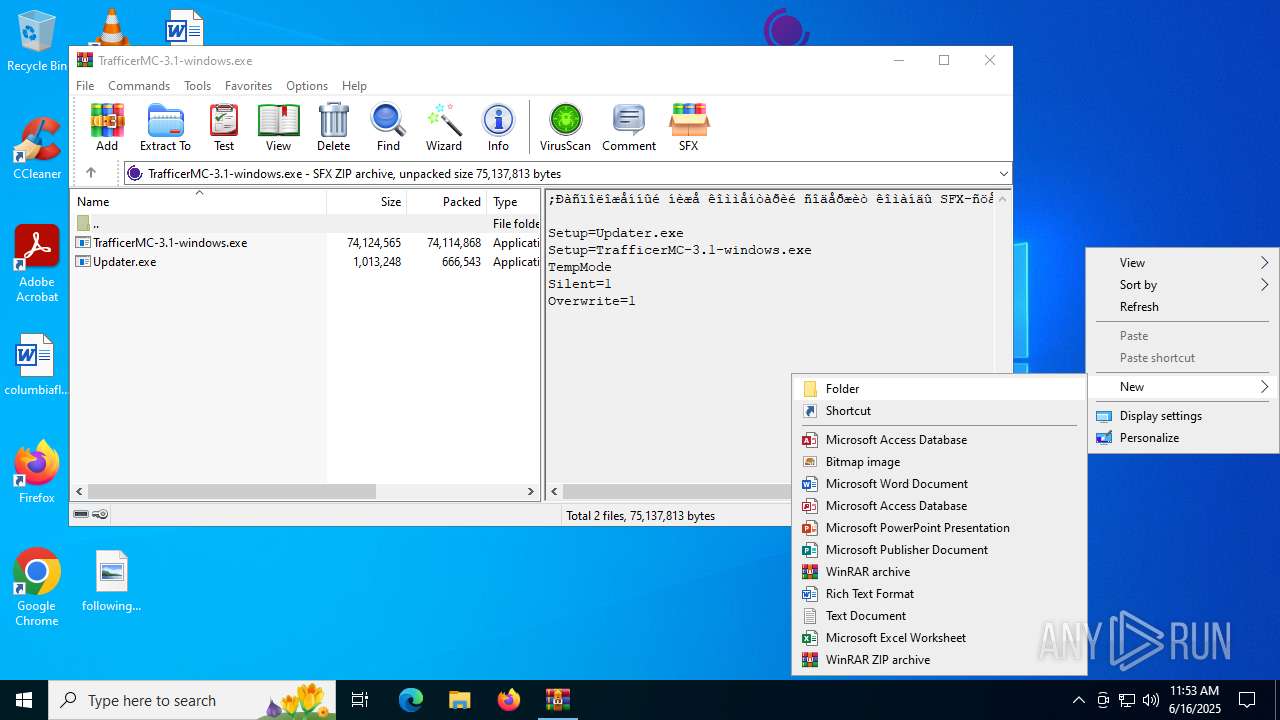
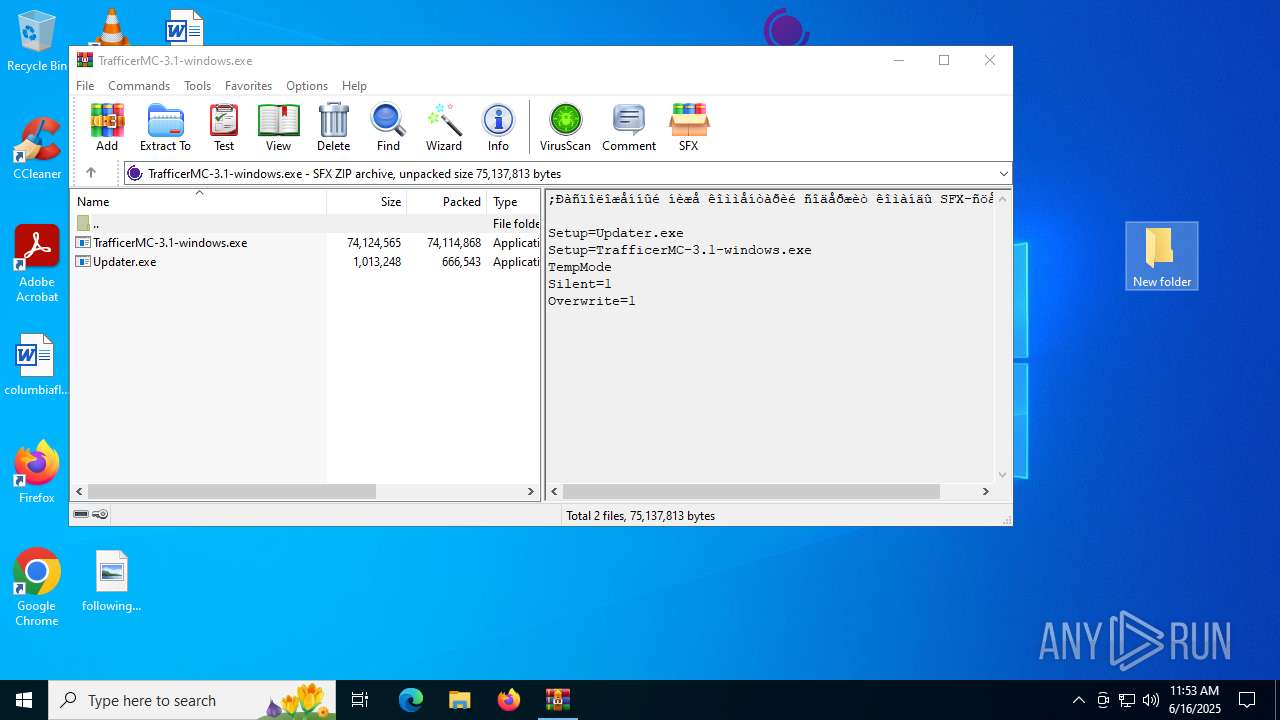
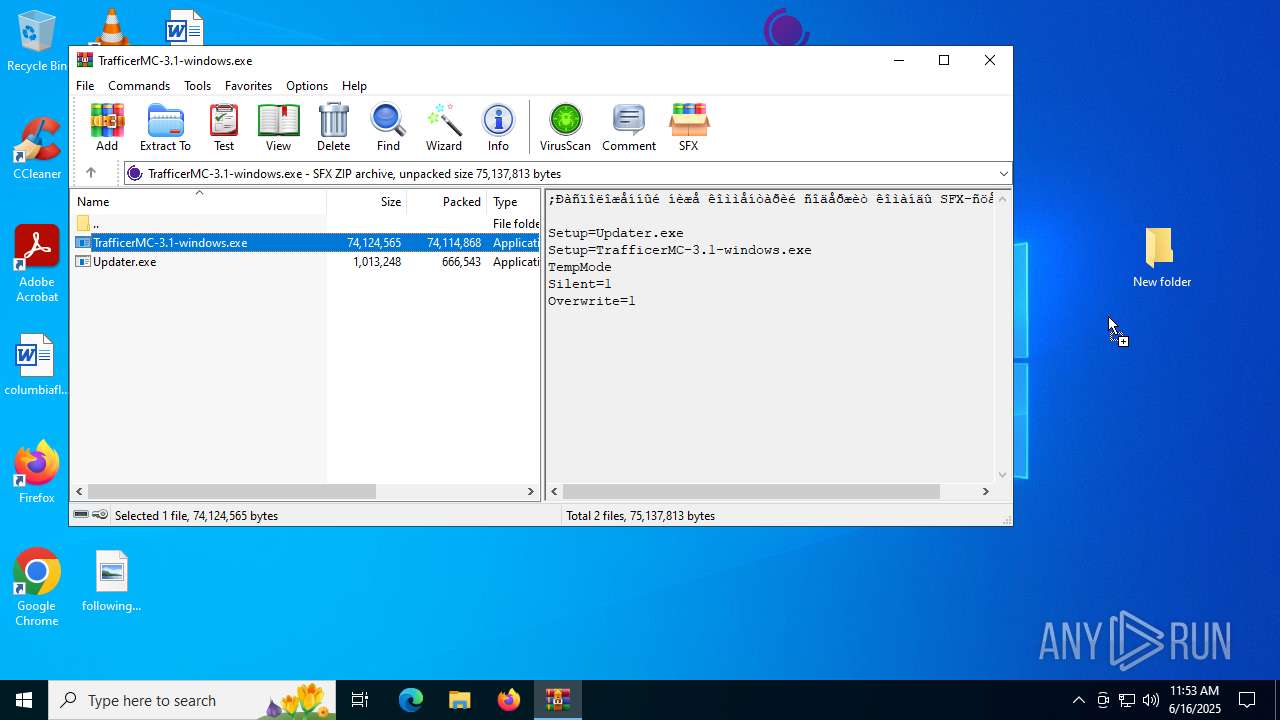
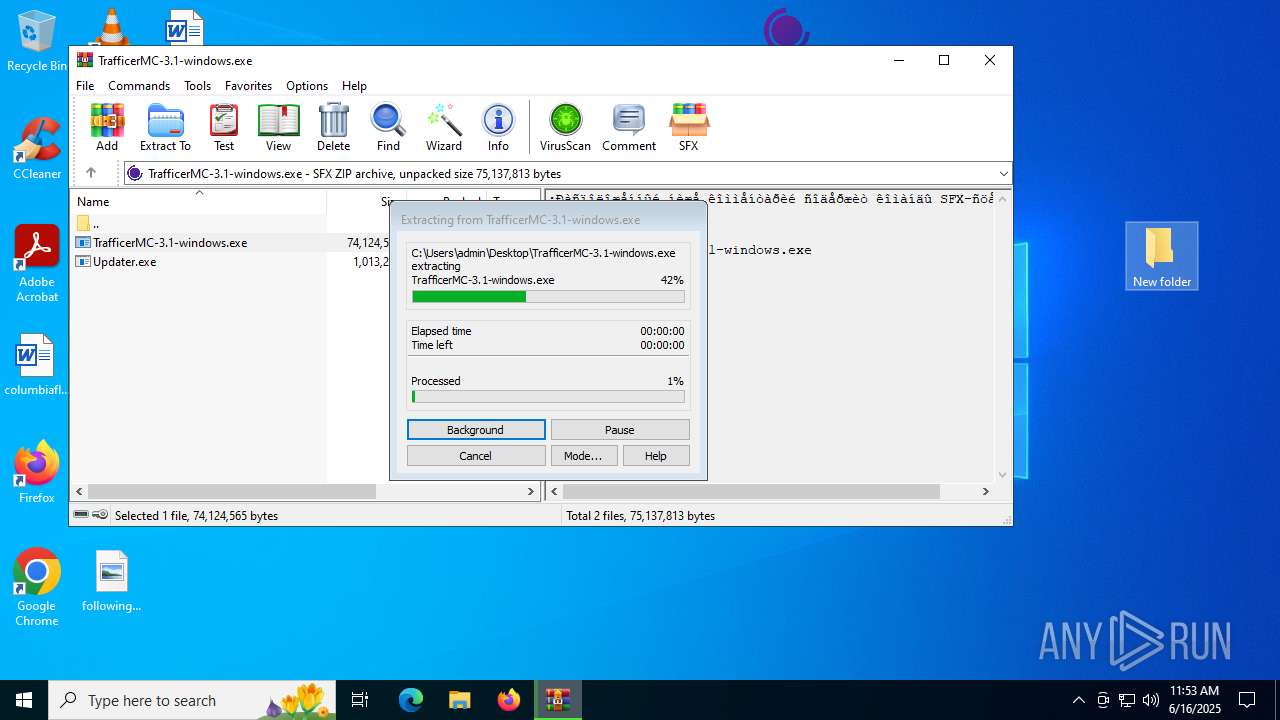
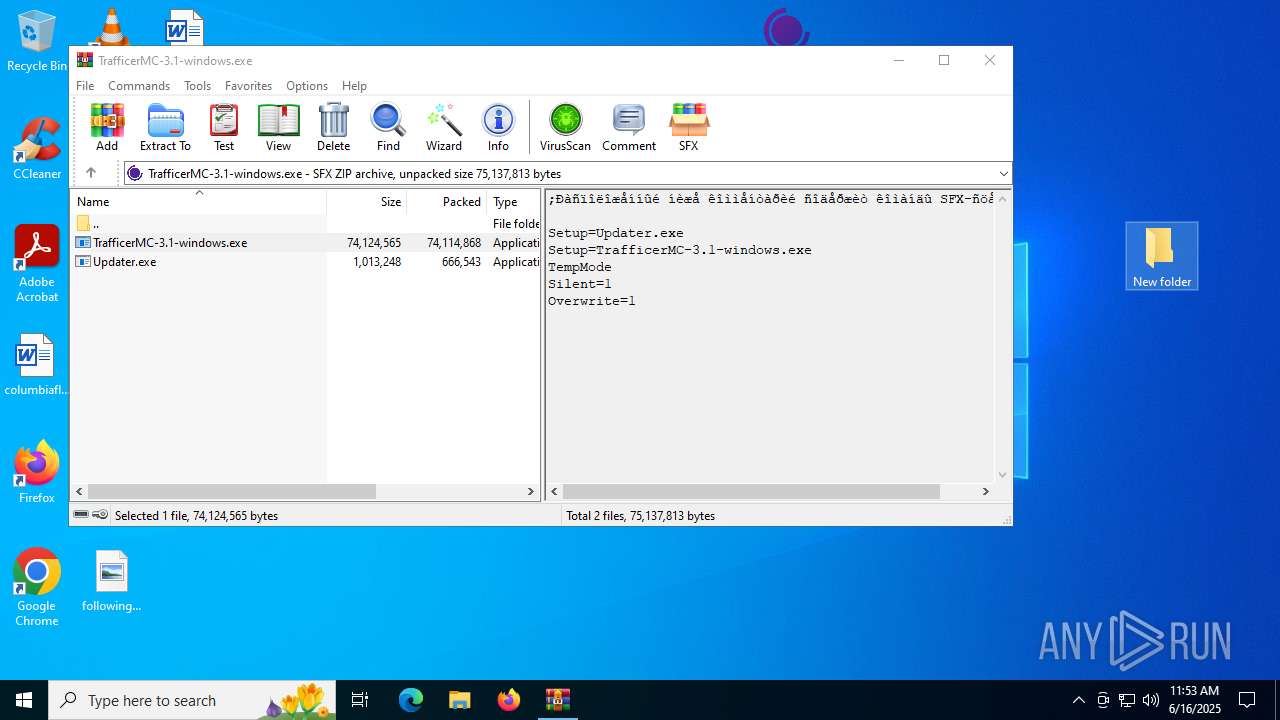
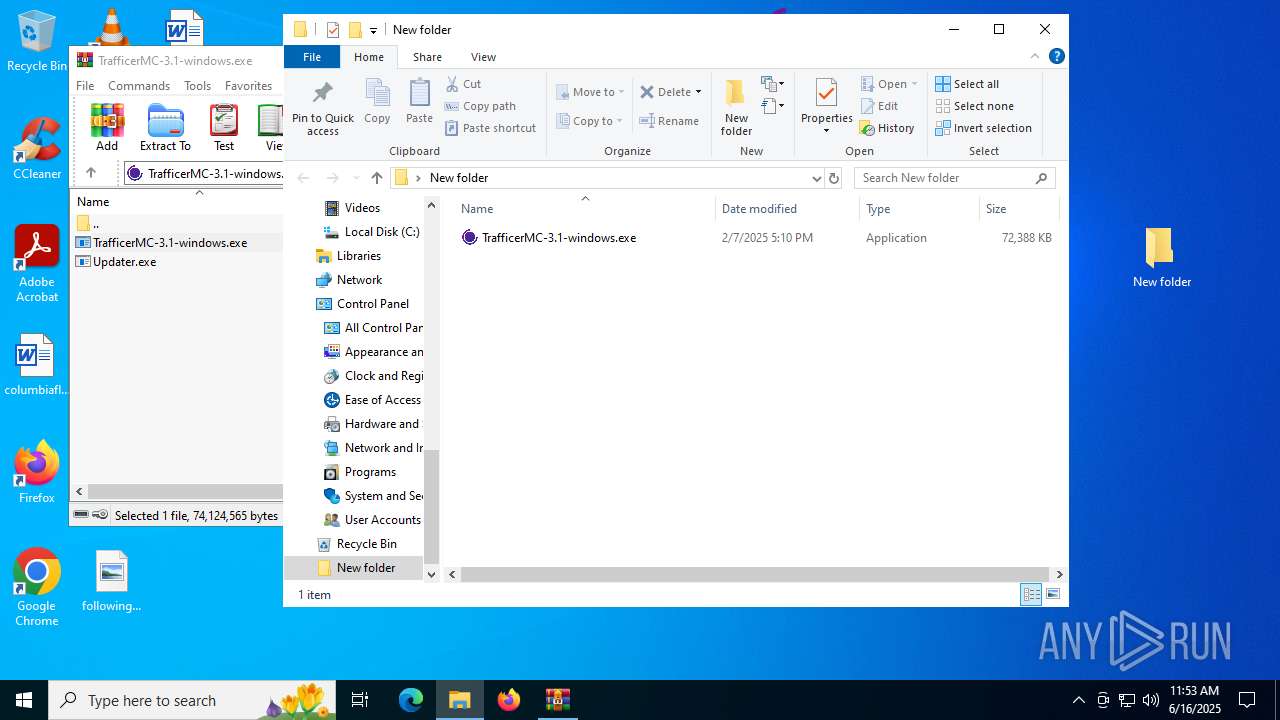
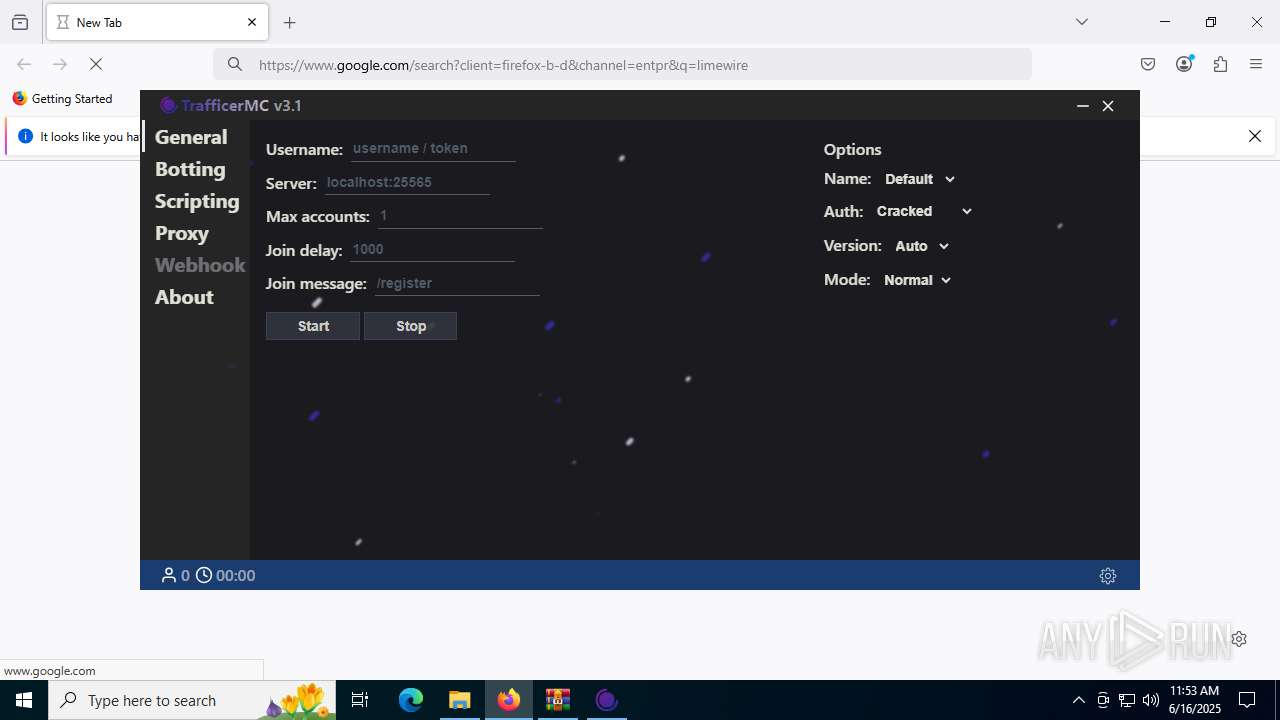
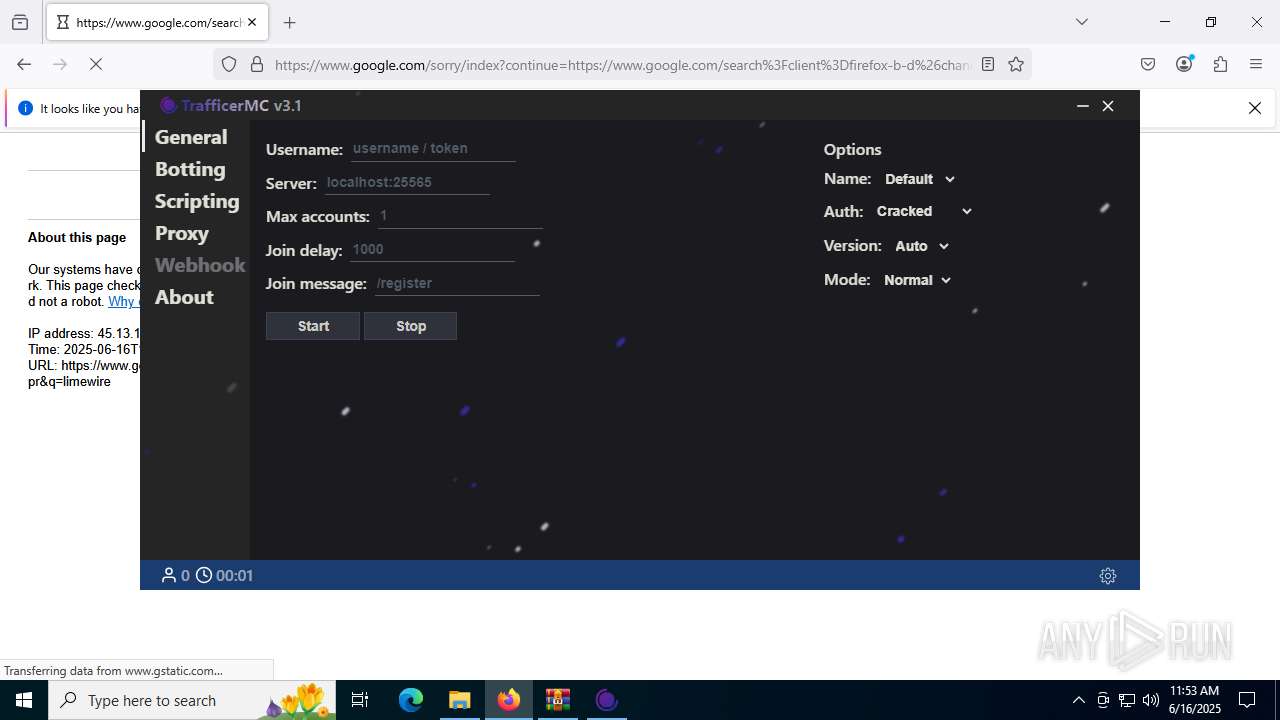
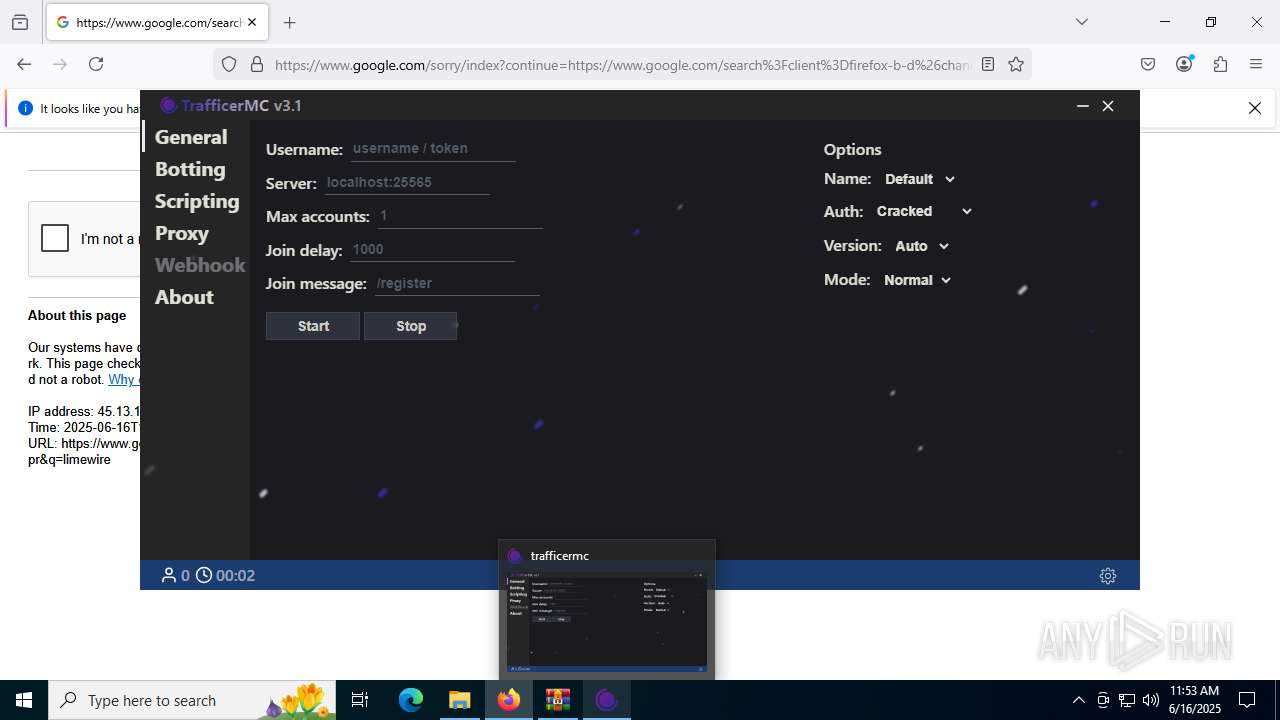
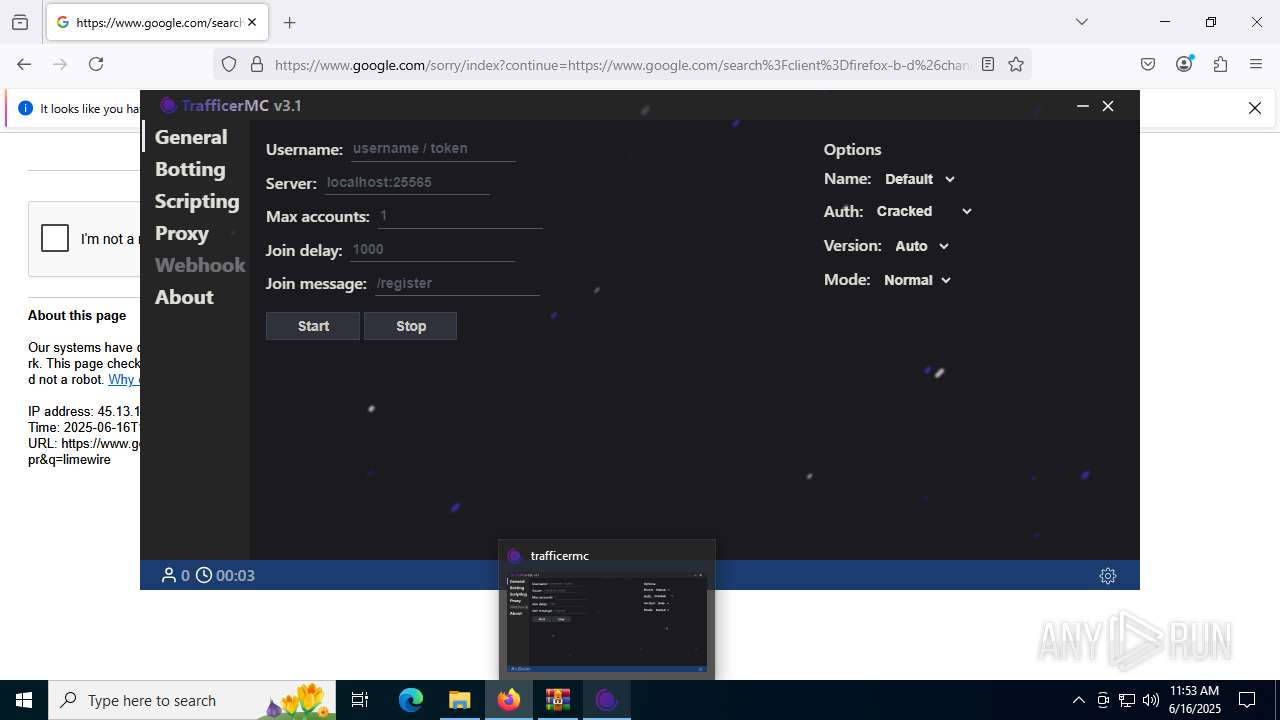
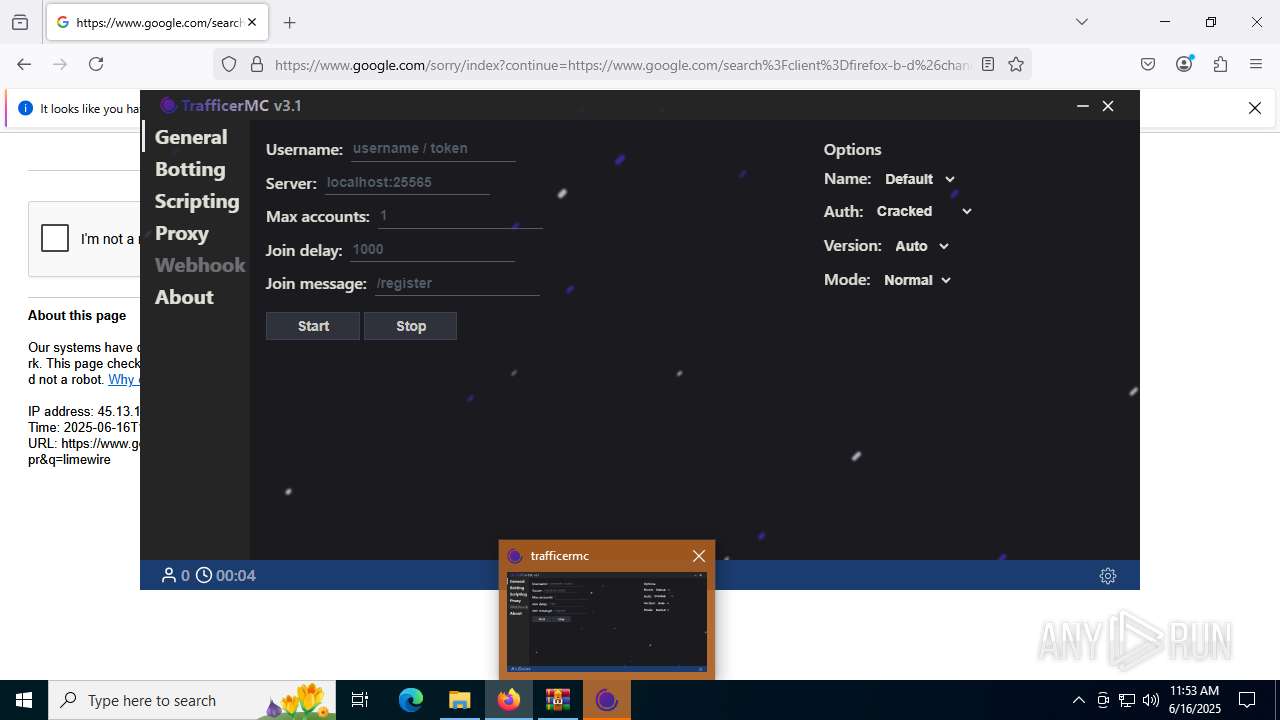
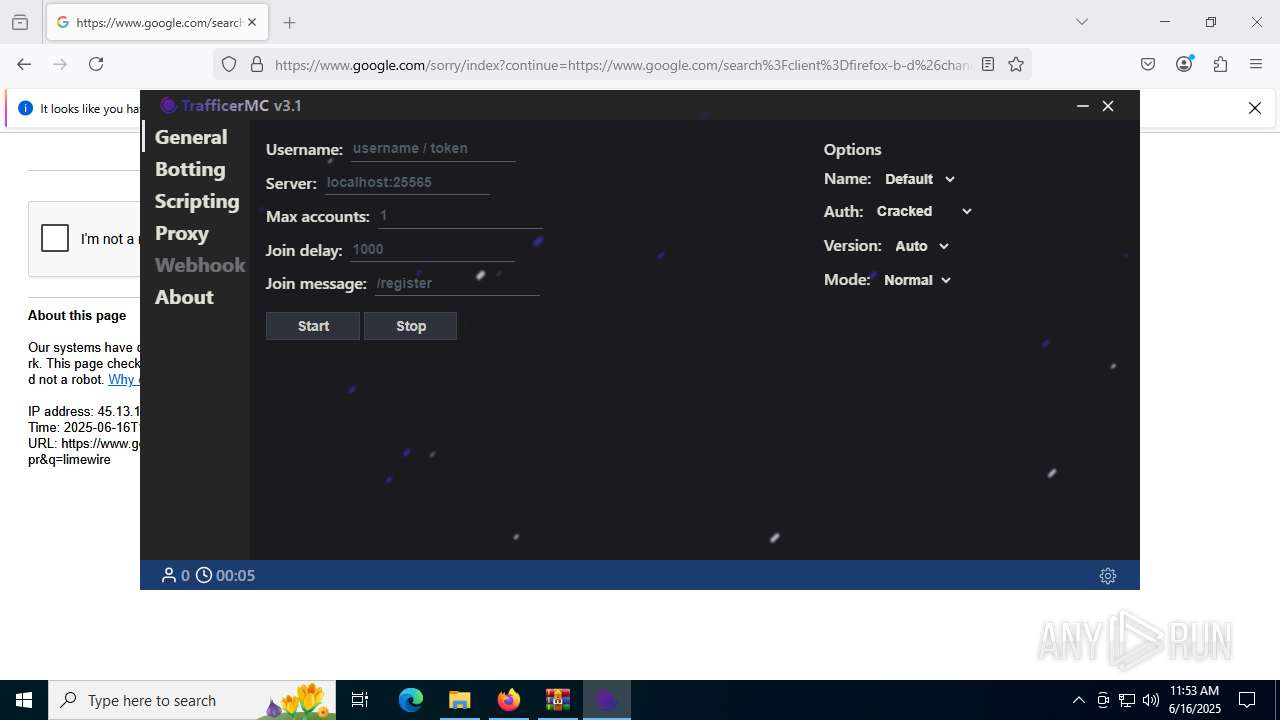
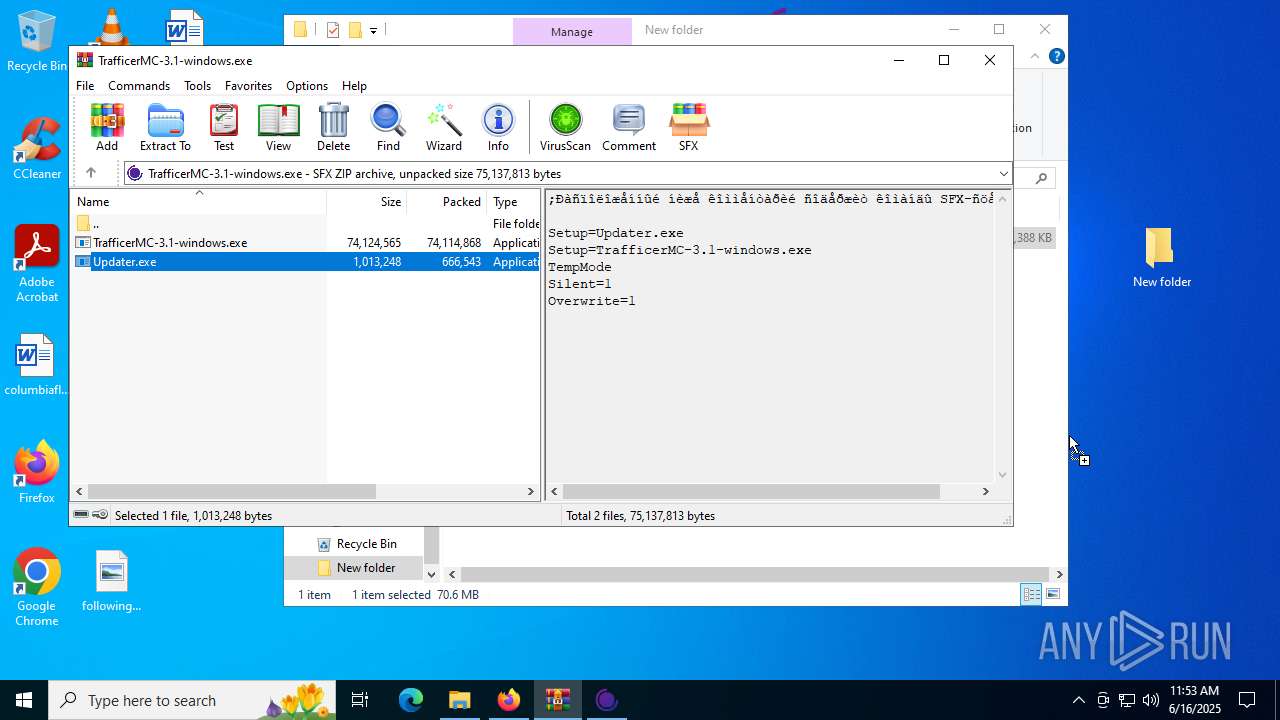
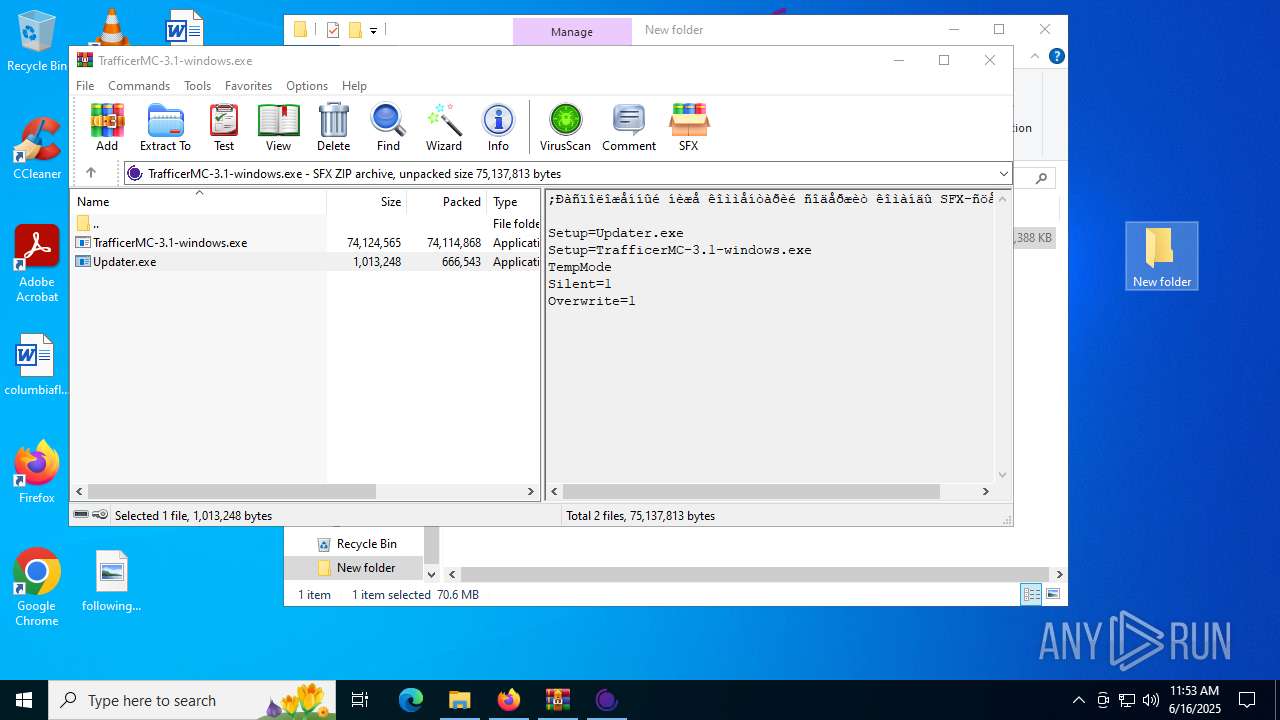
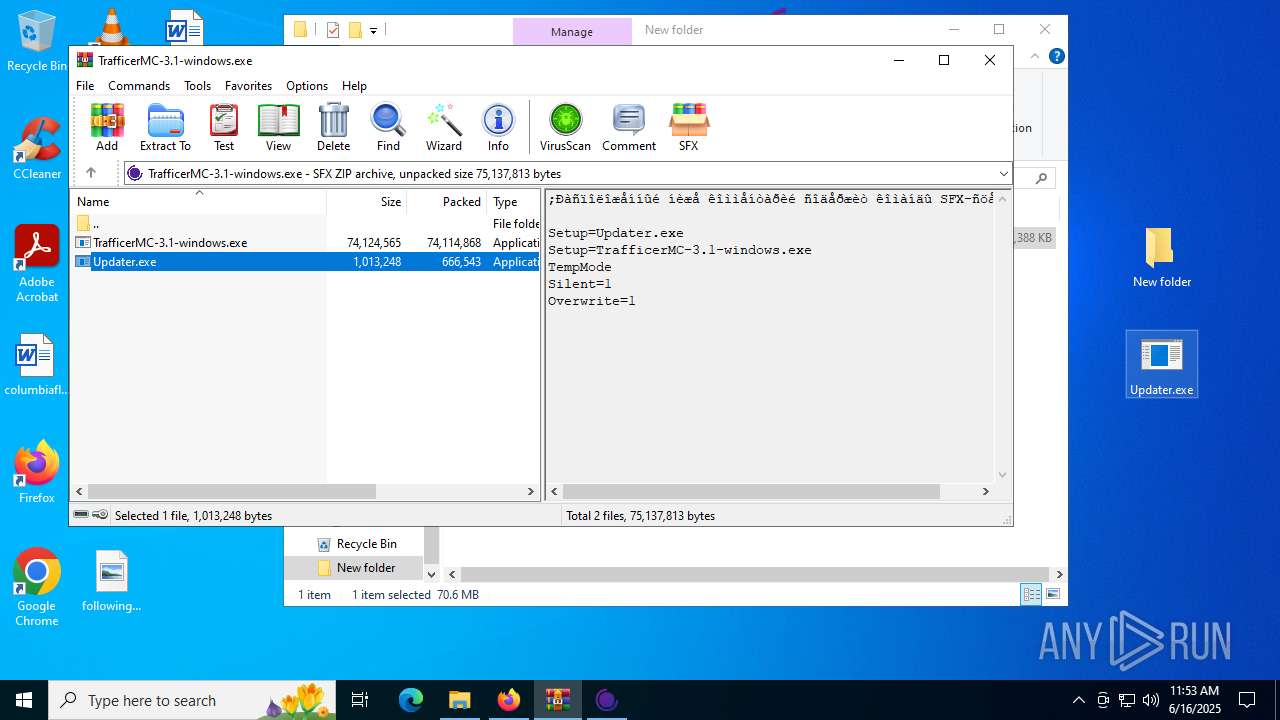
Process drops legitimate windows executable
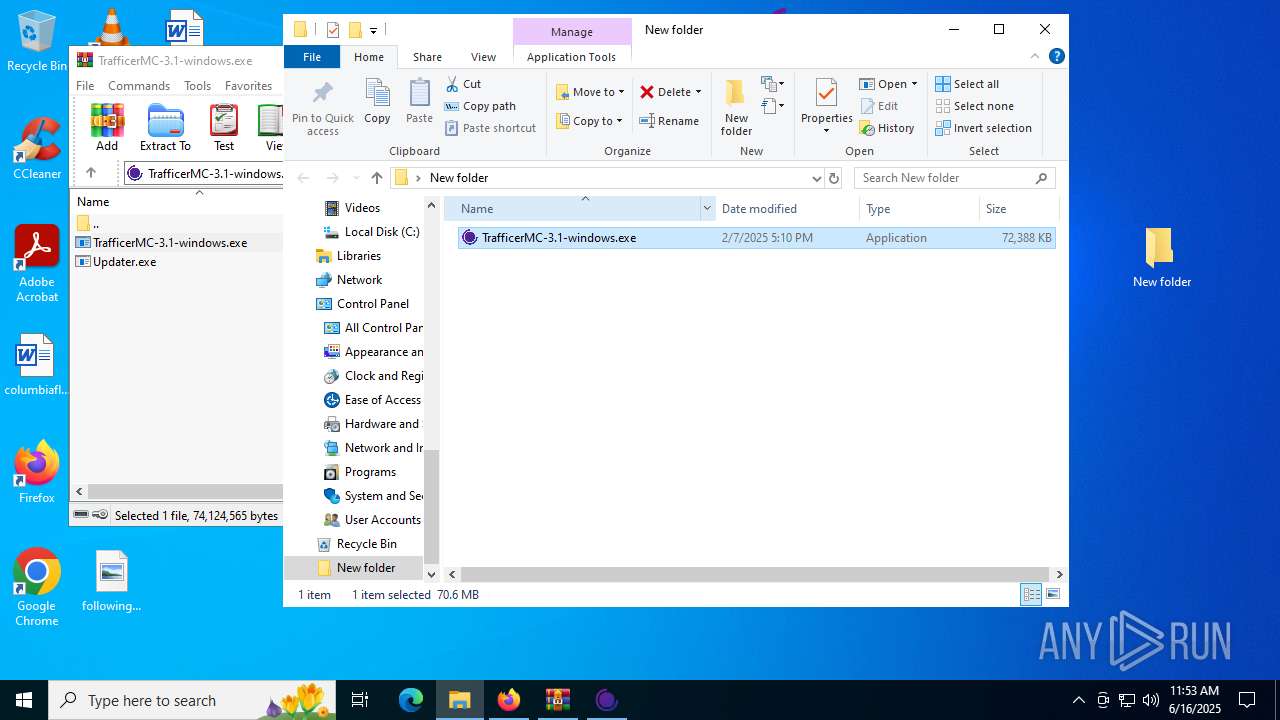
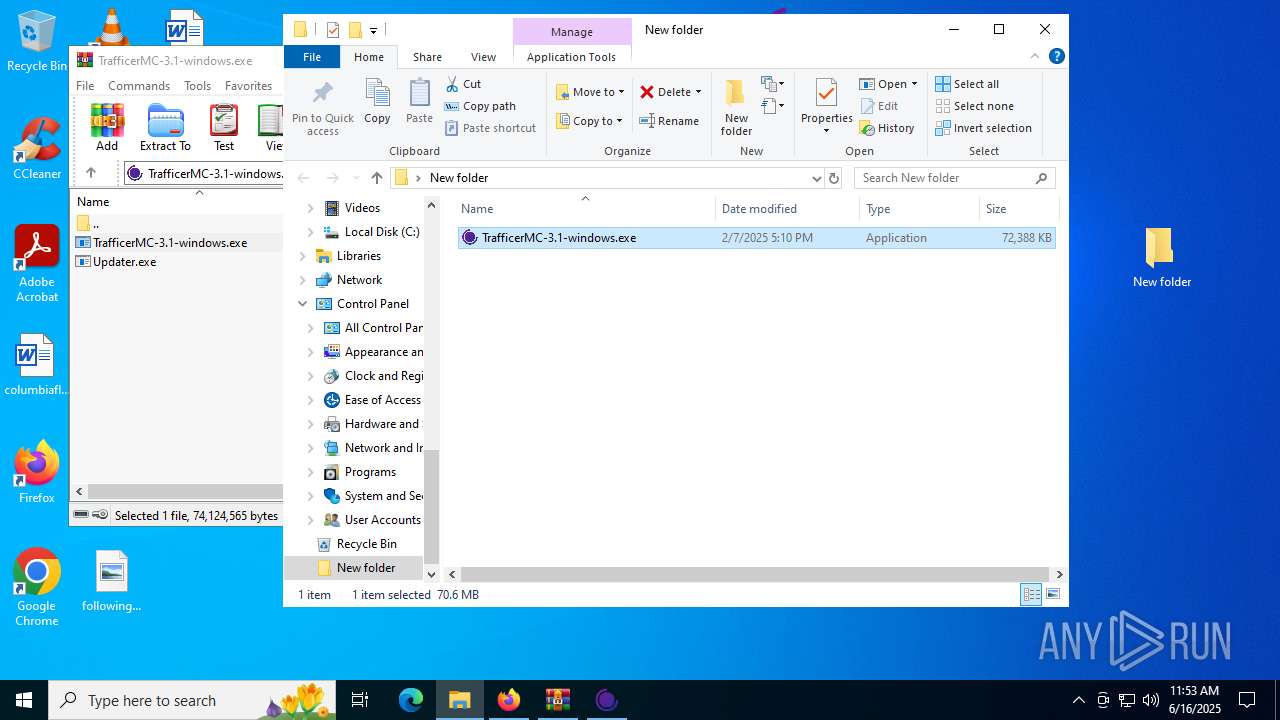
- TrafficerMC-3.1-windows.exe (PID: 4528)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC-3.1-windows.exe (PID: 8184)
- WinRAR.exe (PID: 4708)
Starts a Microsoft application from unusual location
- Updater.exe (PID: 2708)
- Updater.exe (PID: 6148)
Executable content was dropped or overwritten
- TrafficerMC-3.1-windows.exe (PID: 4528)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC-3.1-windows.exe (PID: 8184)
Reads security settings of Internet Explorer
- TrafficerMC-3.1-windows.exe (PID: 4528)
- TrafficerMC-3.1-windows.exe (PID: 4752)
Reads the date of Windows installation
- TrafficerMC-3.1-windows.exe (PID: 4528)
Malware-specific behavior (creating "System.dll" in Temp)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC-3.1-windows.exe (PID: 8184)
The process creates files with name similar to system file names
- TrafficerMC-3.1-windows.exe (PID: 4752)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 6980)
- MSBuild.exe (PID: 2120)
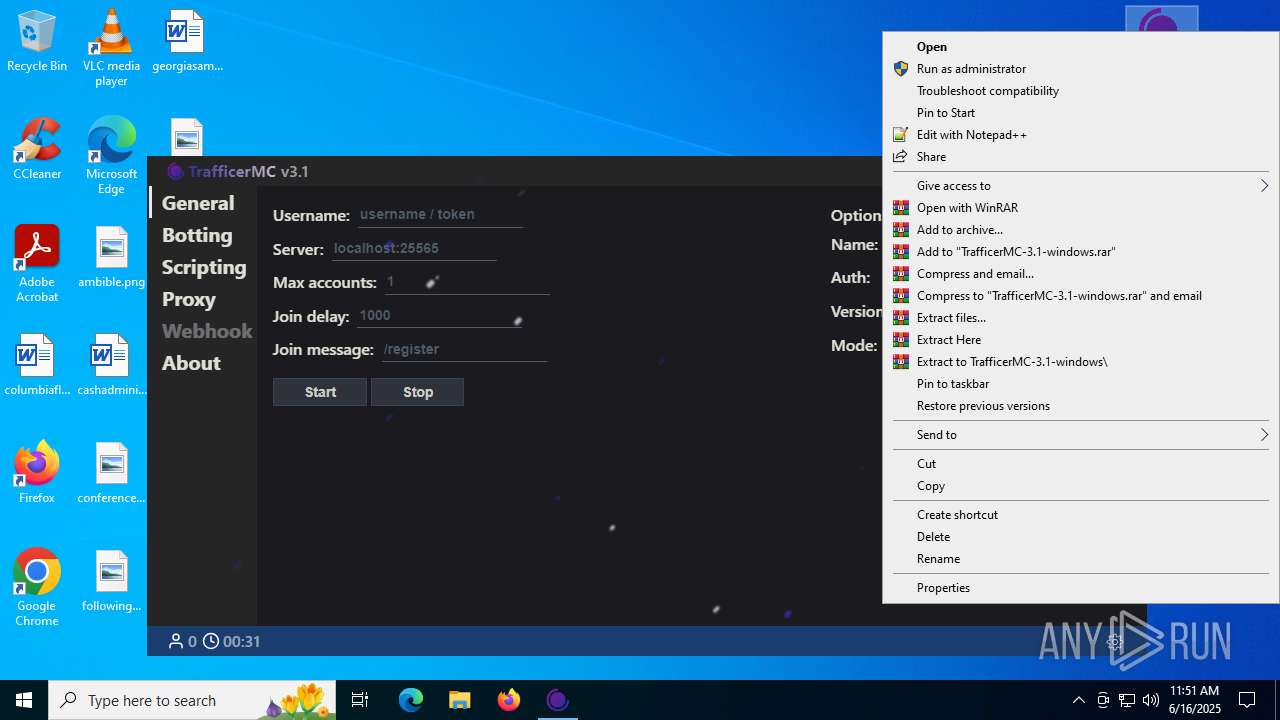
Drops 7-zip archiver for unpacking
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC-3.1-windows.exe (PID: 8184)
There is functionality for taking screenshot (YARA)
- TrafficerMC-3.1-windows.exe (PID: 4528)
- MSBuild.exe (PID: 6980)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC.exe (PID: 5600)
Application launched itself
- TrafficerMC.exe (PID: 2292)
- TrafficerMC.exe (PID: 6672)
INFO
Application launched itself
- chrome.exe (PID: 6536)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 6876)
- chrome.exe (PID: 1352)
- chrome.exe (PID: 7288)
- msedge.exe (PID: 8064)
- msedge.exe (PID: 8104)
- msedge.exe (PID: 8120)
- msedge.exe (PID: 6900)
- msedge.exe (PID: 7464)
- msedge.exe (PID: 7496)
- firefox.exe (PID: 7736)
- firefox.exe (PID: 7308)
- chrome.exe (PID: 8408)
- msedge.exe (PID: 8824)
- chrome.exe (PID: 1496)
- msedge.exe (PID: 8536)
- msedge.exe (PID: 8412)
- chrome.exe (PID: 1356)
- msedge.exe (PID: 7740)
- msedge.exe (PID: 7856)
- msedge.exe (PID: 8644)
- msedge.exe (PID: 1496)
- msedge.exe (PID: 8448)
- chrome.exe (PID: 3900)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6536)
Reads the computer name
- TrafficerMC-3.1-windows.exe (PID: 4528)
- MSBuild.exe (PID: 6980)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC.exe (PID: 2292)
- TrafficerMC.exe (PID: 5600)
- TrafficerMC.exe (PID: 2520)
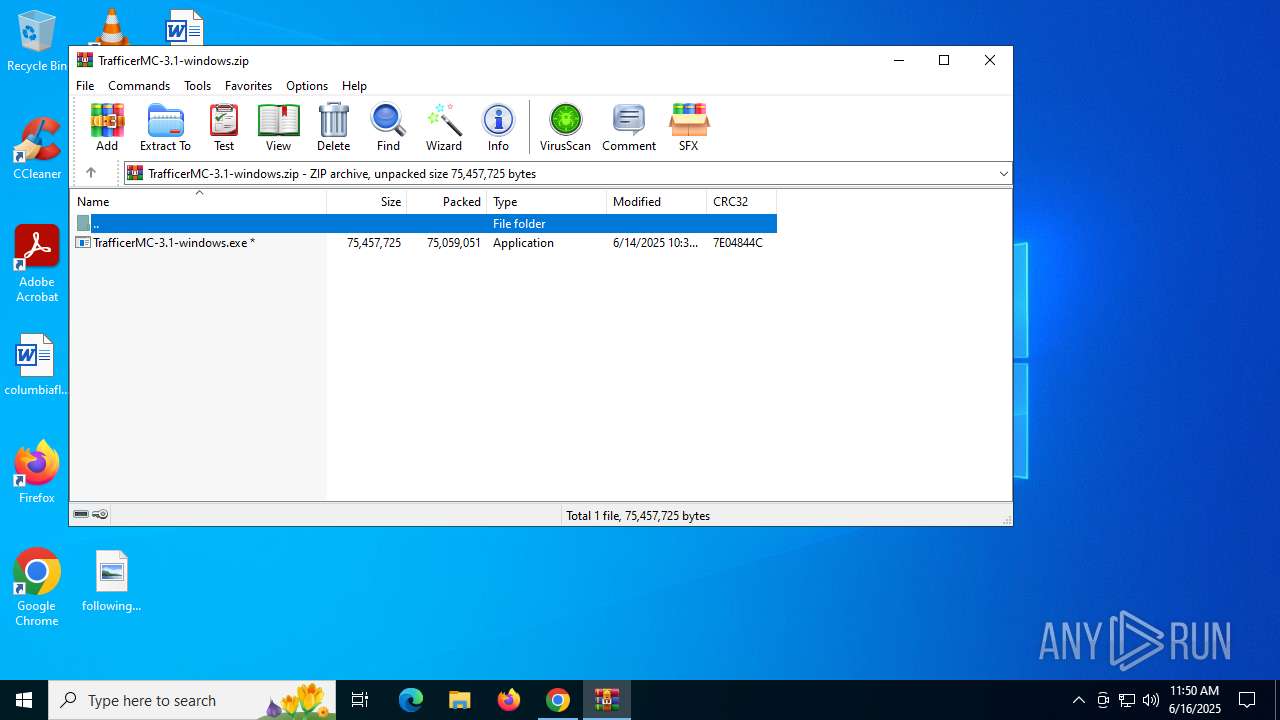
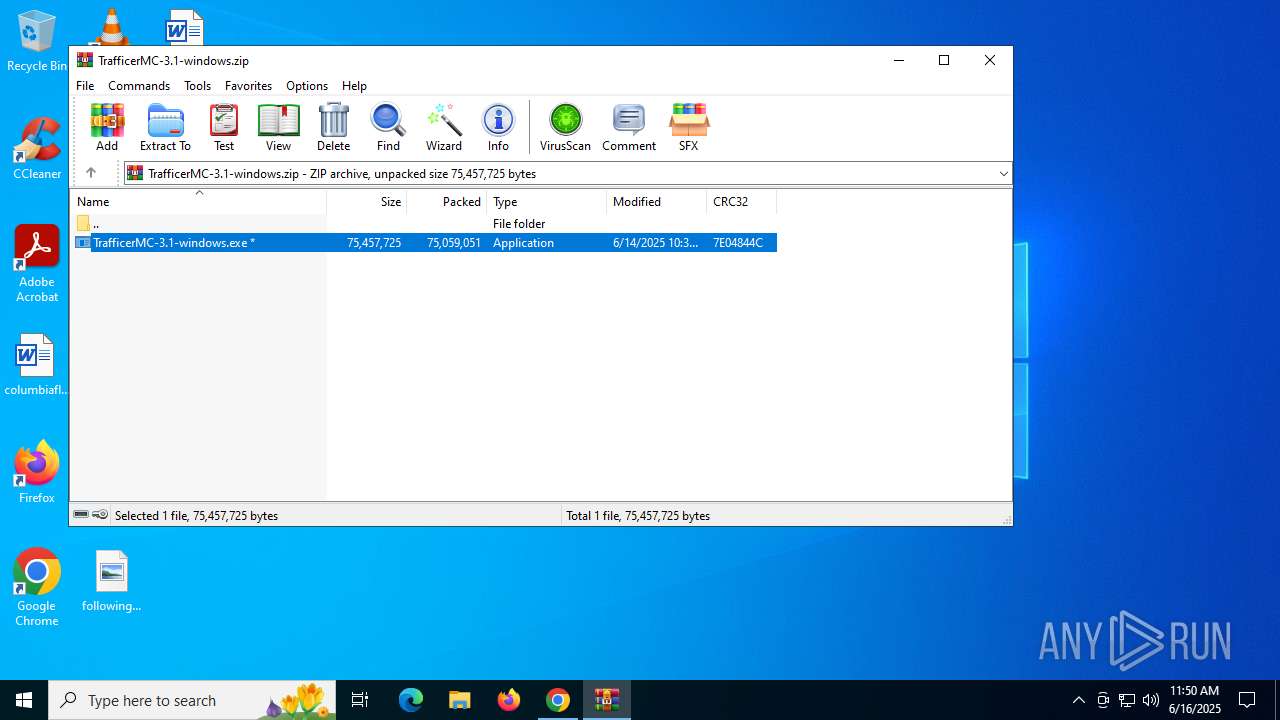
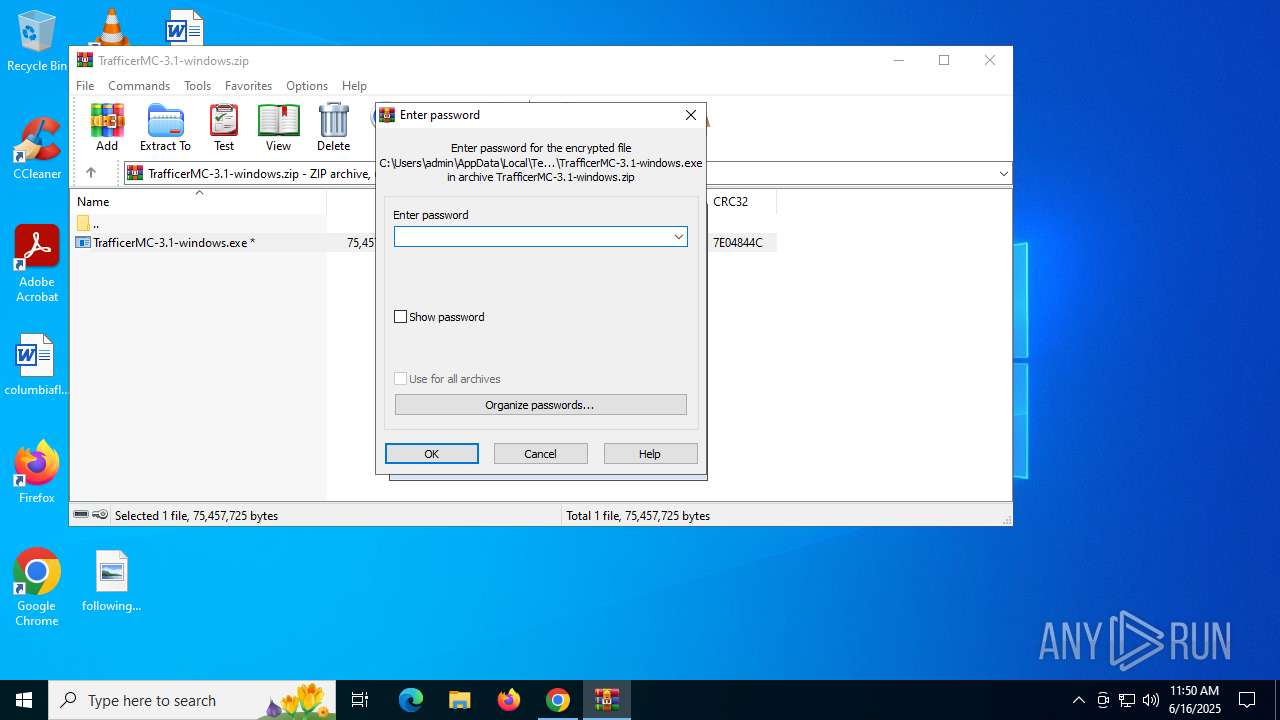
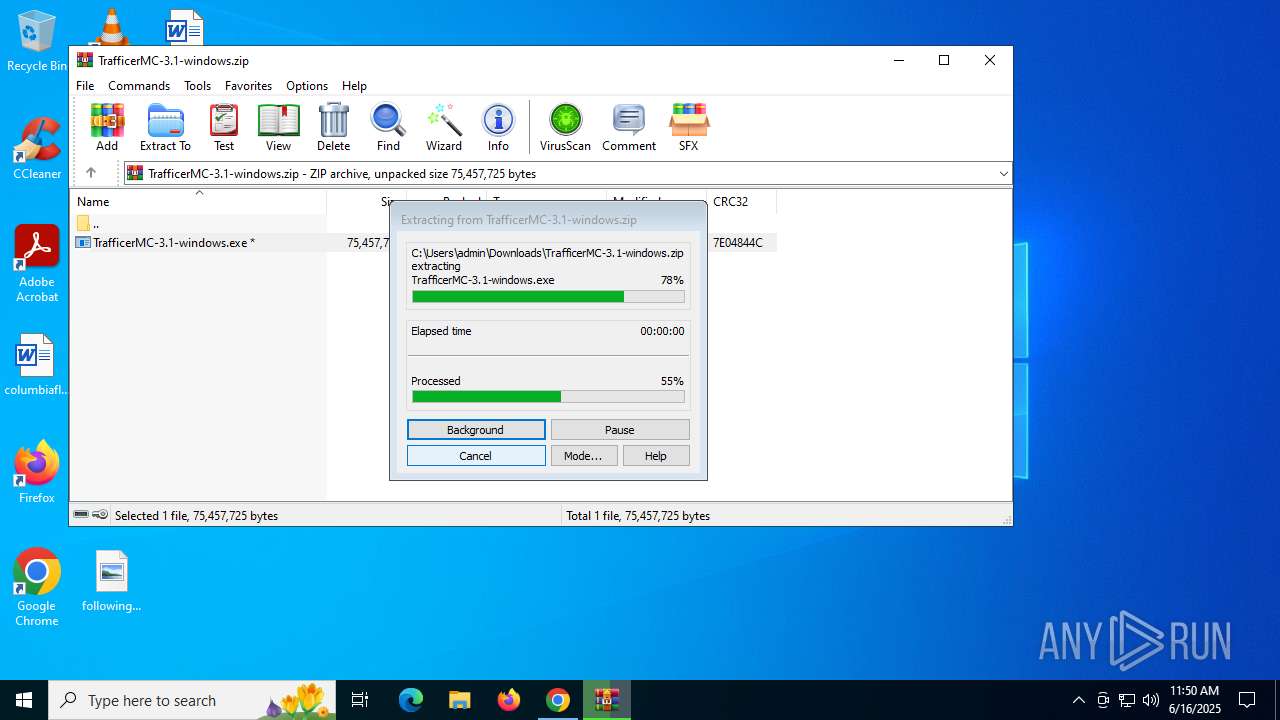
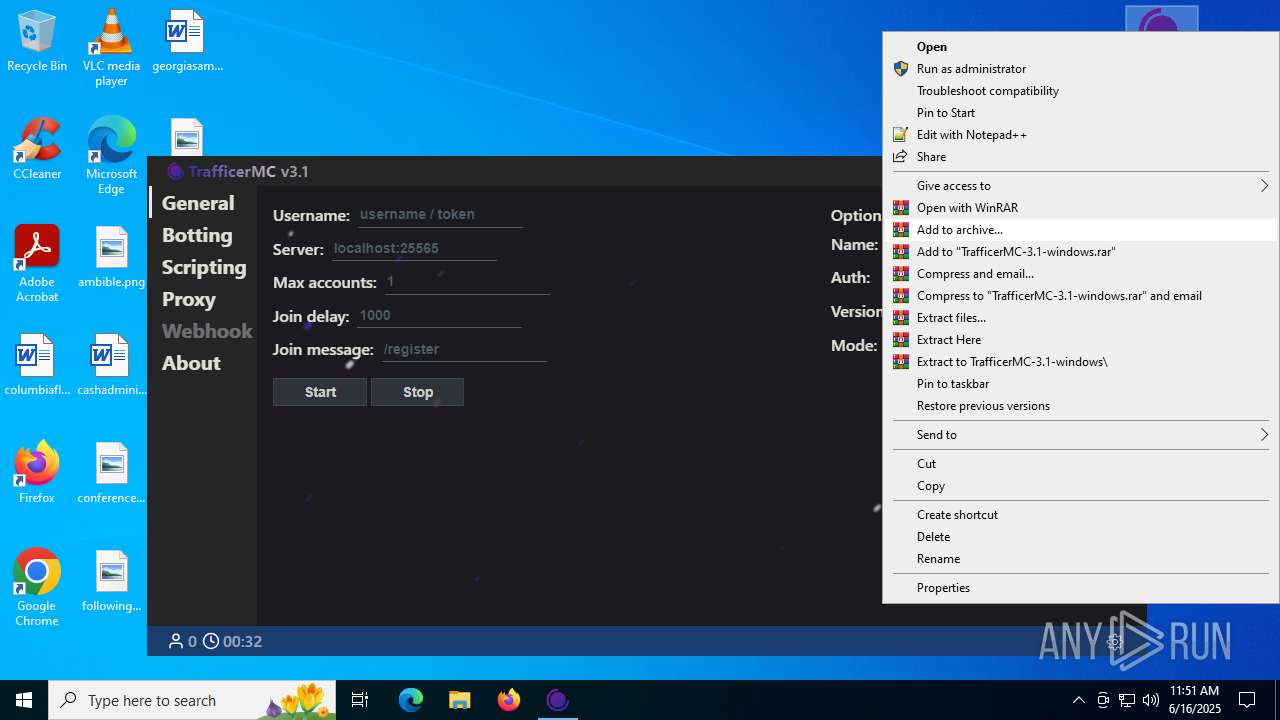
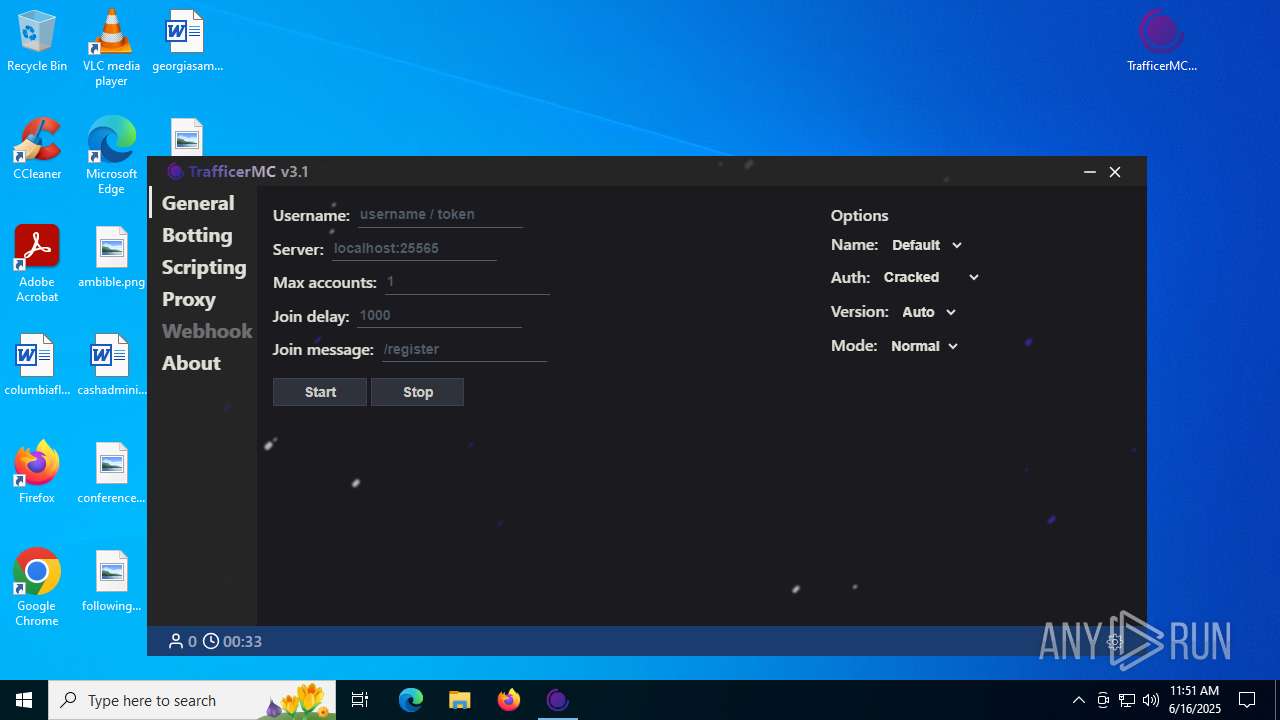
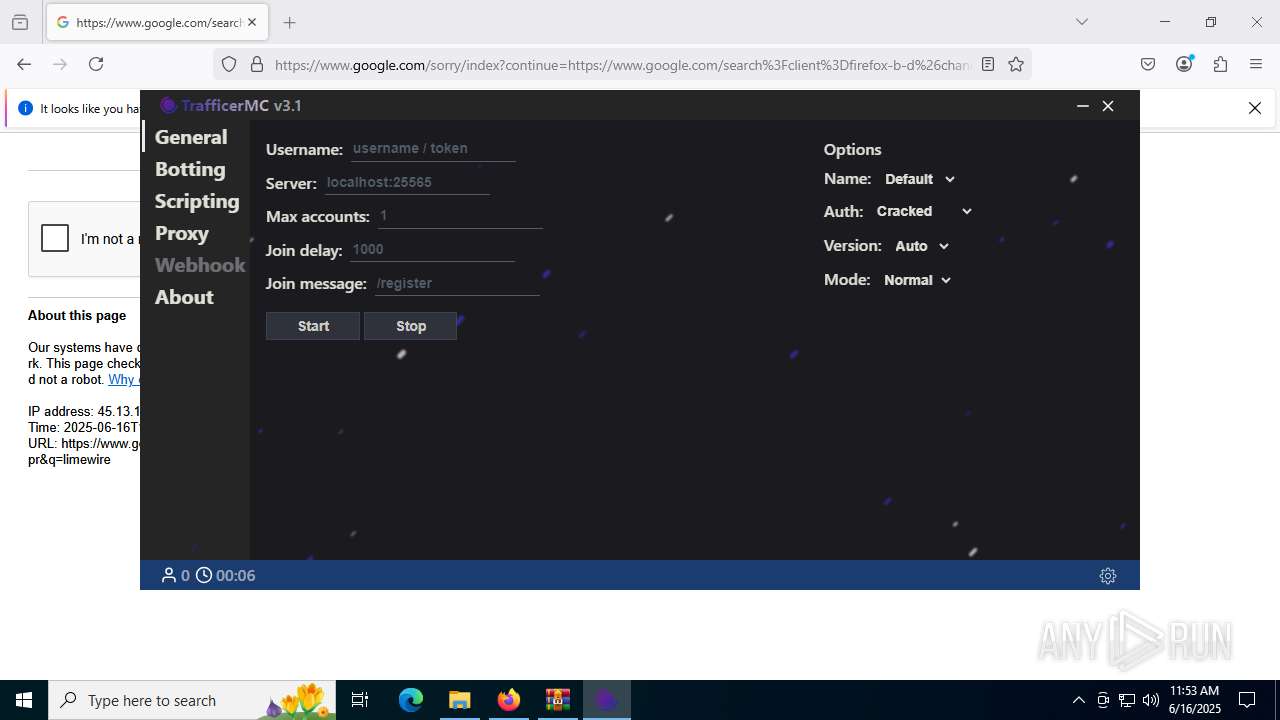
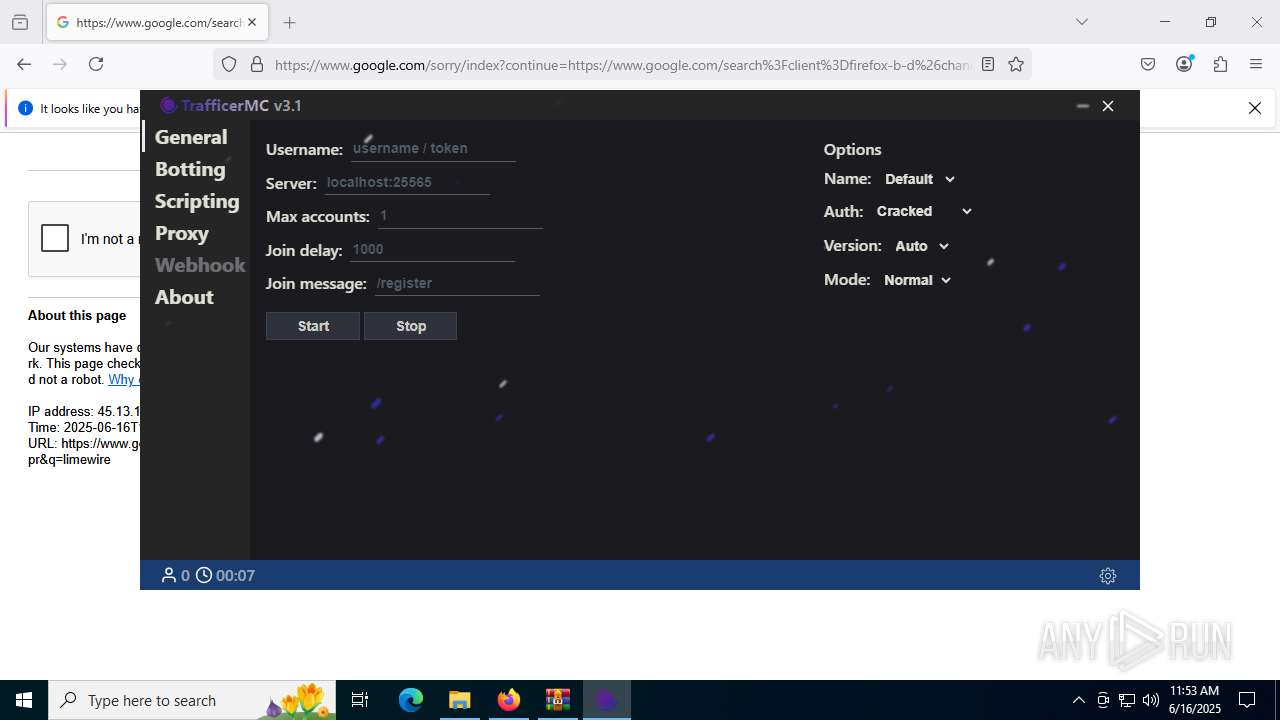
Manual execution by a user
- TrafficerMC-3.1-windows.exe (PID: 4528)
- WinRAR.exe (PID: 4708)
- TrafficerMC-3.1-windows.exe (PID: 8184)
- firefox.exe (PID: 7736)
- Updater.exe (PID: 6148)
Create files in a temporary directory
- TrafficerMC-3.1-windows.exe (PID: 4528)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC.exe (PID: 2292)
The sample compiled with english language support
- TrafficerMC-3.1-windows.exe (PID: 4528)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- TrafficerMC-3.1-windows.exe (PID: 8184)
- WinRAR.exe (PID: 4708)
- firefox.exe (PID: 7308)
Checks supported languages
- TrafficerMC-3.1-windows.exe (PID: 4528)
- Updater.exe (PID: 2708)
- TrafficerMC-3.1-windows.exe (PID: 4752)
- MSBuild.exe (PID: 6980)
- TrafficerMC.exe (PID: 2292)
- TrafficerMC.exe (PID: 5600)
- TrafficerMC.exe (PID: 2520)
- TrafficerMC.exe (PID: 6796)
Process checks computer location settings
- TrafficerMC-3.1-windows.exe (PID: 4528)
- TrafficerMC.exe (PID: 2292)
- TrafficerMC.exe (PID: 6796)
Reads product name
- TrafficerMC.exe (PID: 2292)
Reads Environment values
- TrafficerMC.exe (PID: 2292)
Reads the machine GUID from the registry
- TrafficerMC.exe (PID: 2292)
Creates files or folders in the user directory
- TrafficerMC.exe (PID: 2520)
- TrafficerMC.exe (PID: 2292)
Checks proxy server information
- TrafficerMC.exe (PID: 2292)
Node.js compiler has been detected
- TrafficerMC.exe (PID: 2292)
- TrafficerMC.exe (PID: 2520)
- TrafficerMC.exe (PID: 5600)
Executable content was dropped or overwritten
- firefox.exe (PID: 7308)
- WinRAR.exe (PID: 4708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
332
Monitored processes
181
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2168,i,1397157170168369947,15978007138923854033,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2160 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2056,i,9405751068332548661,12647836240282302663,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4828 -prefsLen 38963 -prefMapHandle 4832 -prefMapSize 272997 -jsInitHandle 4836 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4684 -initialChannelId {b6d01d11-a91b-4625-9cca-7ceaa3e043cb} -parentPid 7308 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7308" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Updater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4444,i,3550563881993506884,1031997602113832706,262144 --variations-seed-version --mojo-platform-channel-handle=4484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Local\Temp\2ippFodBfUEKs1Mexhf5rV5XTud\TrafficerMC.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\trafficermc" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1780 --field-trial-handle=1784,i,7192430332876412075,14927013778179034937,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2ippFodBfUEKs1Mexhf5rV5XTud\TrafficerMC.exe | — | TrafficerMC.exe | |||||||||||
User: admin Company: RattlesHyper Integrity Level: LOW Description: TrafficerMC Version: 3.1.0 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3260,i,265722258397853054,12524434053490299622,262144 --variations-seed-version --mojo-platform-channel-handle=3692 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2148,i,9405751068332548661,12647836240282302663,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2168 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4072 -prefsLen 44823 -prefMapHandle 4076 -prefMapSize 272997 -jsInitHandle 4080 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4088 -initialChannelId {820084fd-6f93-45a6-98bc-286855693484} -parentPid 7308 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7308" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | MSBuild.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
64 962
Read events
64 767
Write events
159
Delete events
36
Modification events
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 121 | |||
| (PID) Process: | (6536) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
Executable files
40
Suspicious files
541
Text files
534
Unknown types
412
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF176590.TMP | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF17659f.TMP | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1765bf.TMP | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1765bf.TMP | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1765bf.TMP | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6536 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
401
DNS requests
468
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6460 | chrome.exe | GET | 200 | 216.58.206.78:80 | http://clients2.google.com/time/1/current?cup2key=8:XU07K6DZNM82nf36y8xK6AtsbZAA_UF6fl-u-8QslKo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4888 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4888 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4800 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:VKJcp_73jbMLjpIZJQmF6ZorHsy15eNn7M5AC1T48DA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7704 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:cKXDbG_CT6mirkhNZm1u-G7lHOtepSA-goeMjps-eHI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7308 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6960 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6460 | chrome.exe | 216.58.206.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
6460 | chrome.exe | 142.250.185.142:443 | drive.google.com | GOOGLE | US | whitelisted |
6460 | chrome.exe | 142.250.184.234:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
6460 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6460 | chrome.exe | 142.250.185.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
drive.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
drive-thirdparty.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (battlefled .top) |
6980 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (battlefled .top) in TLS SNI |
6980 | MSBuild.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 42 |
2520 | TrafficerMC.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2520 | TrafficerMC.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6980 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (battlefled .top) in TLS SNI |
6980 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (battlefled .top) in TLS SNI |
6980 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (battlefled .top) in TLS SNI |
6980 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (battlefled .top) in TLS SNI |