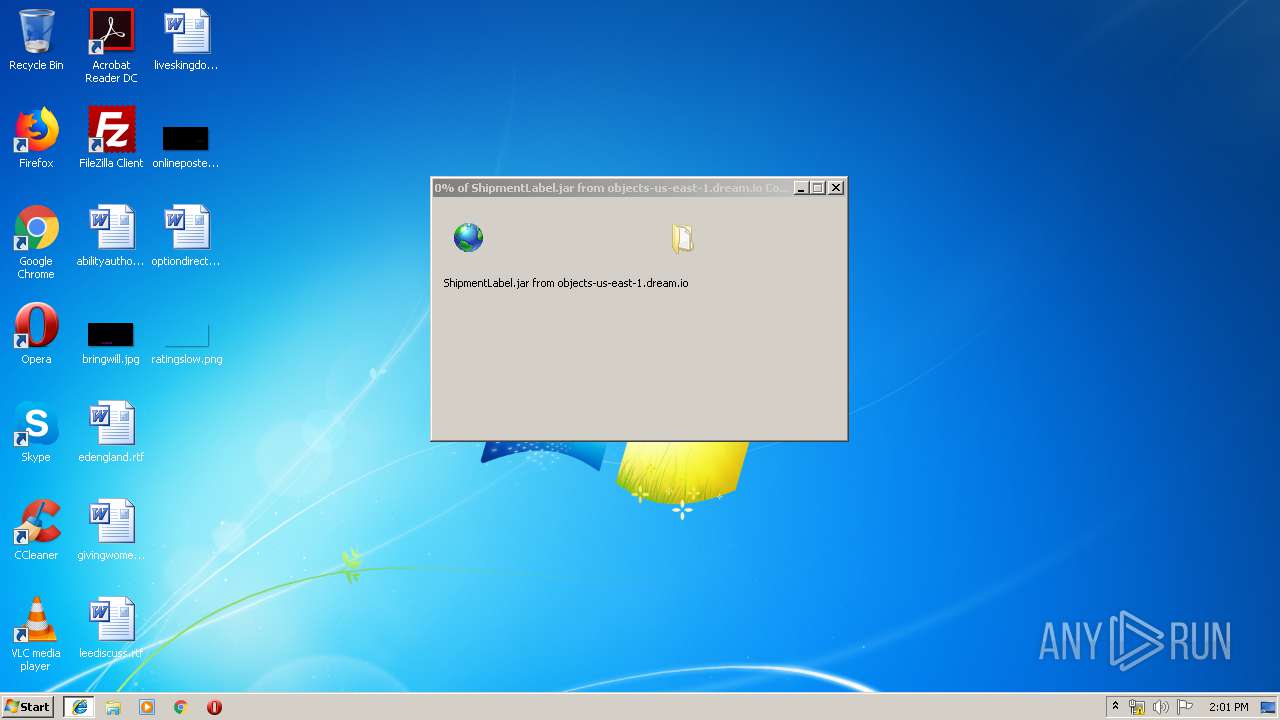
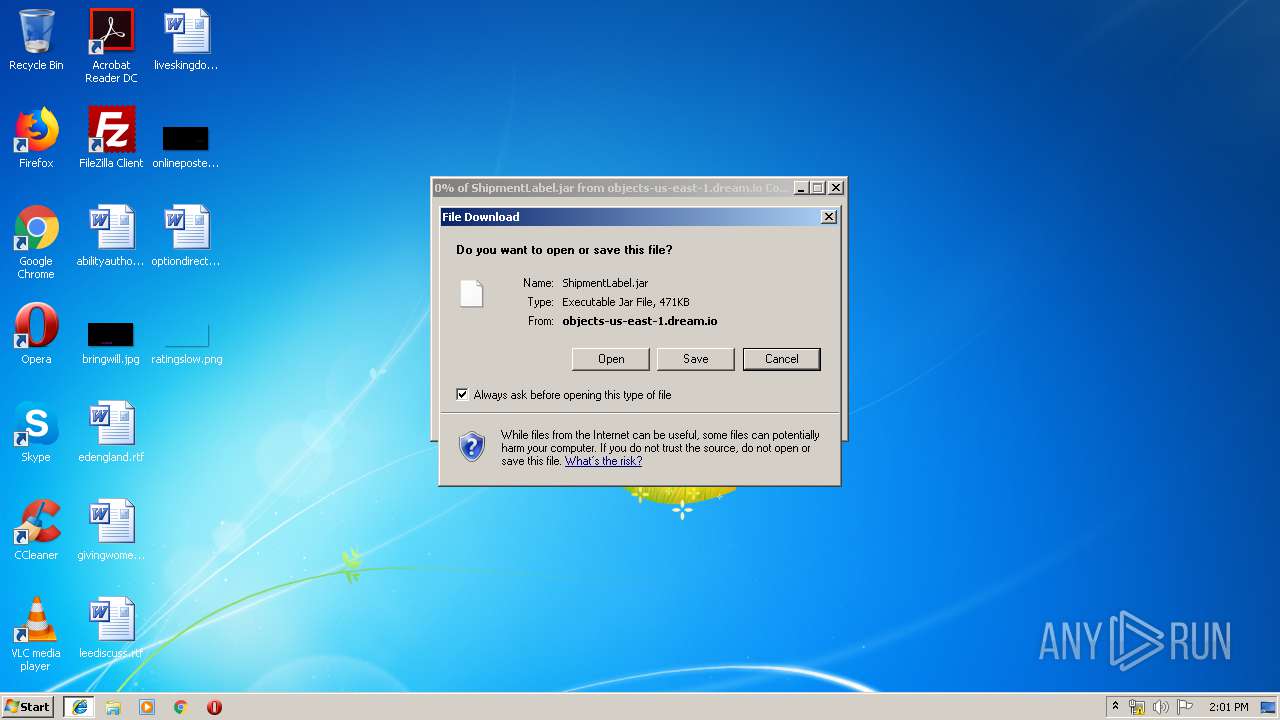
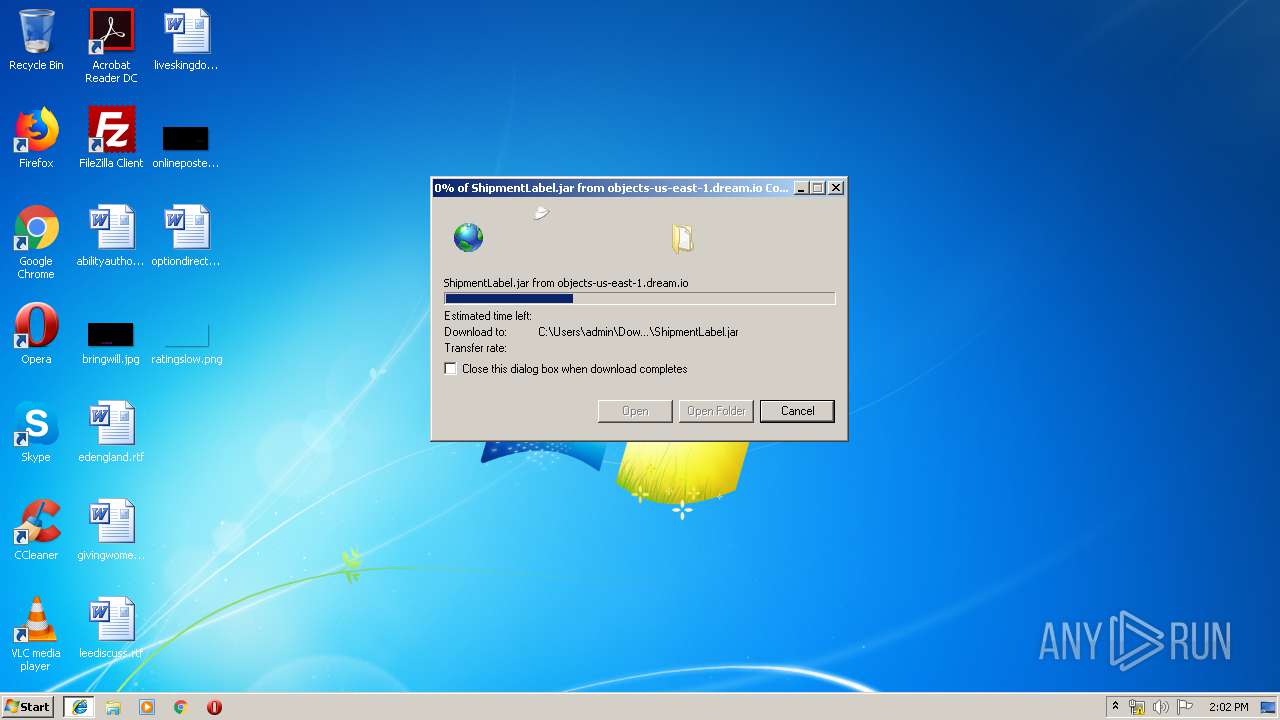
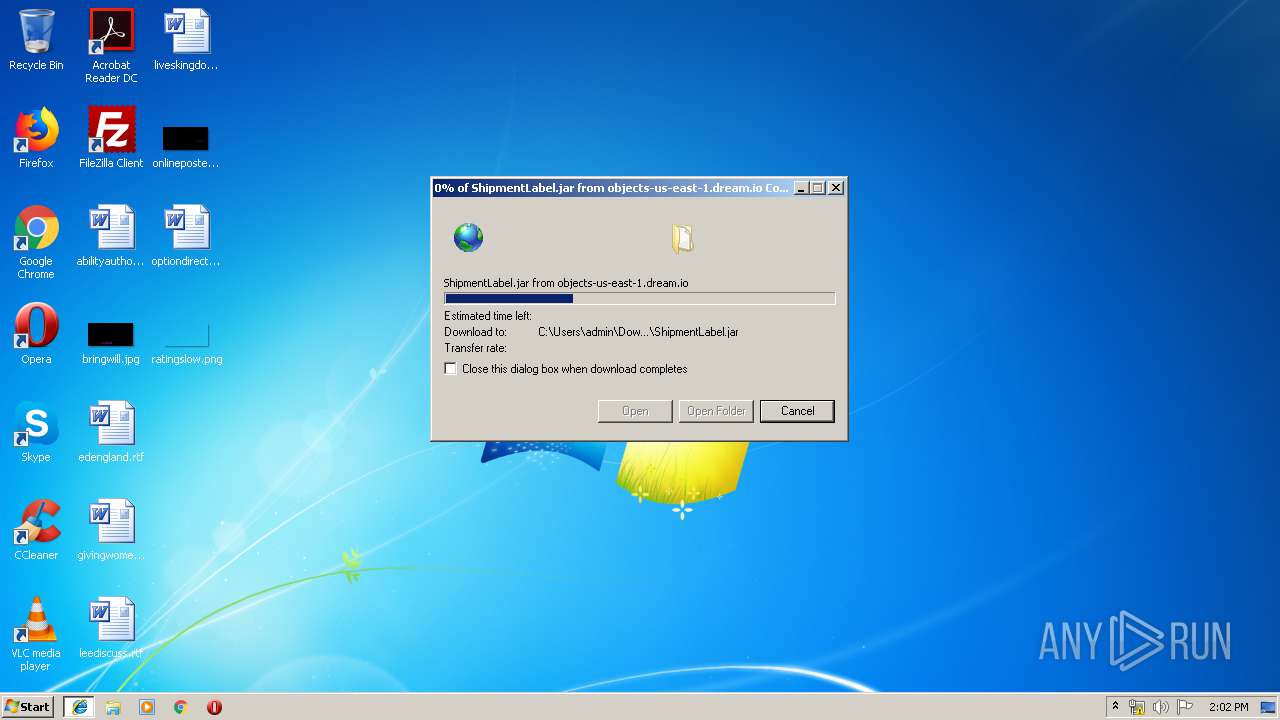
| URL: | https://objects-us-east-1.dream.io/fedex/ShipmentLabel.jar |
| Full analysis: | https://app.any.run/tasks/6ee28d9d-784a-448b-9350-ab546e472601 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | July 11, 2019, 13:01:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 53DF064A79F2680E06F20014A92A2B2F |
| SHA1: | 3CAFE4AE0B939A61410FE058287AF67BF00379FC |
| SHA256: | E97E49105940A10D11E4E66F2952DFA7B7C802CA05E2B6926C833E79FBC44544 |
| SSDEEP: | 3:N8OL99uS/5K2N8p7+:2OL9k4Kq8Y |
MALICIOUS
Loads dropped or rewritten executable
- javaw.exe (PID: 4056)
- java.exe (PID: 2160)
- iexplore.exe (PID: 3948)
- iexplore.exe (PID: 3312)
- javaw.exe (PID: 3696)
- java.exe (PID: 2232)
AdWind was detected
- java.exe (PID: 2160)
- java.exe (PID: 2232)
Application was dropped or rewritten from another process
- javaw.exe (PID: 3696)
- javaw.exe (PID: 4056)
- java.exe (PID: 2232)
- java.exe (PID: 2160)
Changes the autorun value in the registry
- reg.exe (PID: 3132)
ADWIND was detected
- javaw.exe (PID: 3696)
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 3432)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 1292)
- cmd.exe (PID: 1904)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 3052)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 3908)
Creates files in the user directory
- javaw.exe (PID: 4056)
- xcopy.exe (PID: 2736)
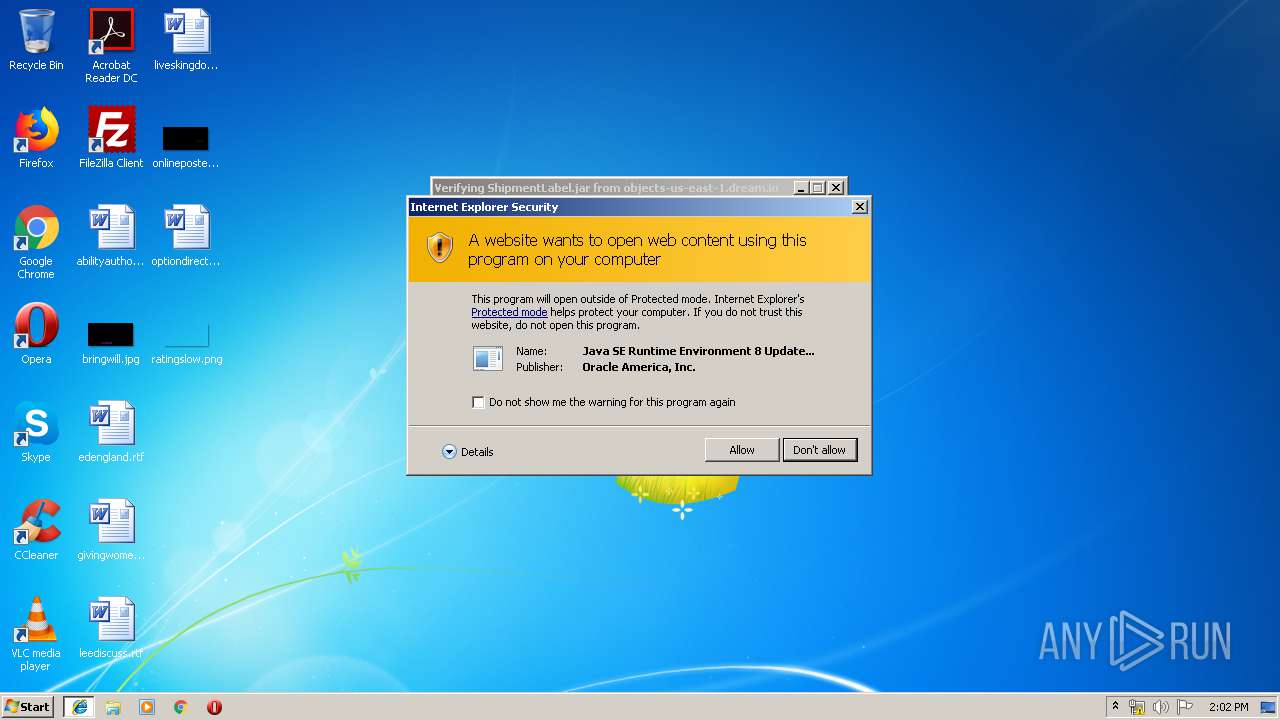
Executes JAVA applets
- iexplore.exe (PID: 3312)
- javaw.exe (PID: 4056)
Starts CMD.EXE for commands execution
- java.exe (PID: 2160)
- javaw.exe (PID: 4056)
- javaw.exe (PID: 3696)
- java.exe (PID: 2232)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 4056)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2736)
- javaw.exe (PID: 3696)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 4056)
Starts itself from another location
- javaw.exe (PID: 4056)
Uses WMIC.EXE to obtain a system information
- javaw.exe (PID: 3696)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3312)
- iexplore.exe (PID: 3948)
Changes internet zones settings
- iexplore.exe (PID: 3312)
Reads Internet Cache Settings
- iexplore.exe (PID: 3948)
- iexplore.exe (PID: 3312)
Reads settings of System Certificates
- iexplore.exe (PID: 3312)
Manual execution by user
- sidebar.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
28
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 500 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive6597014922513740302.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 860 | attrib +h "C:\Users\admin\DfSJGumiMVk\*.*" | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive5383608271206531289.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1292 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive8923587865553758821.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1904 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive4833830694418912478.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -jar C:\Users\admin\AppData\Local\Temp\_0.29118516681125443083537082860879476.class | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2232 | C:\Users\admin\AppData\Roaming\Oracle\bin\java.exe -jar C:\Users\admin\AppData\Local\Temp\_0.45238128129064973052636718263652606.class | C:\Users\admin\AppData\Roaming\Oracle\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2264 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive4279580050010456430.vbs | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2364 | WMIC /Node:localhost /Namespace:\\root\cimv2 Path Win32_PnpSignedDriver Get /Format:List | C:\Windows\System32\Wbem\WMIC.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Windows Sidebar\sidebar.exe" /showGadgets | C:\Program Files\Windows Sidebar\sidebar.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Desktop Gadgets Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 190
Read events
1 087
Write events
99
Delete events
4
Modification events
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000078000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {0D62E691-A3DC-11E9-95C0-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3312) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307070004000B000D0001003500A002 | |||
Executable files
112
Suspicious files
11
Text files
79
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3312 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF96B857FDD2ED3003.TMP | — | |
MD5:— | SHA256:— | |||
| 3312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{0D62E692-A3DC-11E9-95C0-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 3312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF52221244BDA341F3.TMP | — | |
MD5:— | SHA256:— | |||
| 3312 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{0D62E691-A3DC-11E9-95C0-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\8BW8CI0Y\ShipmentLabel[1].jar | java | |
MD5:— | SHA256:— | |||
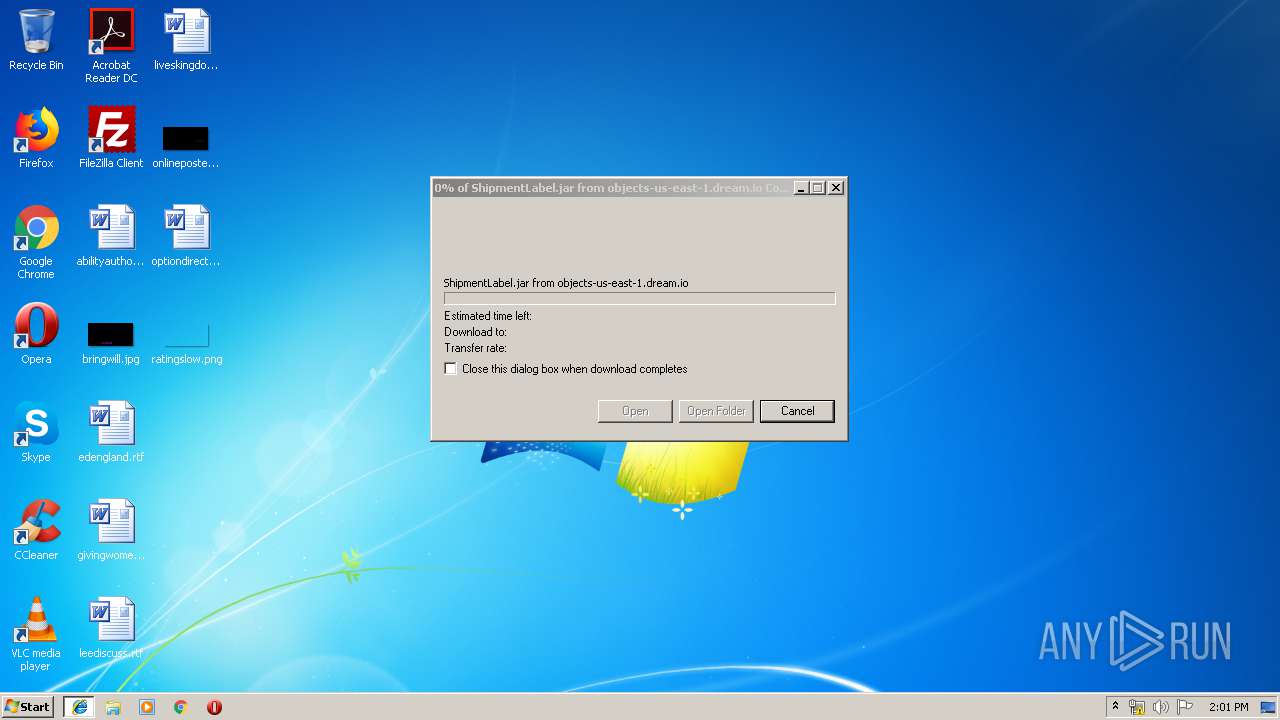
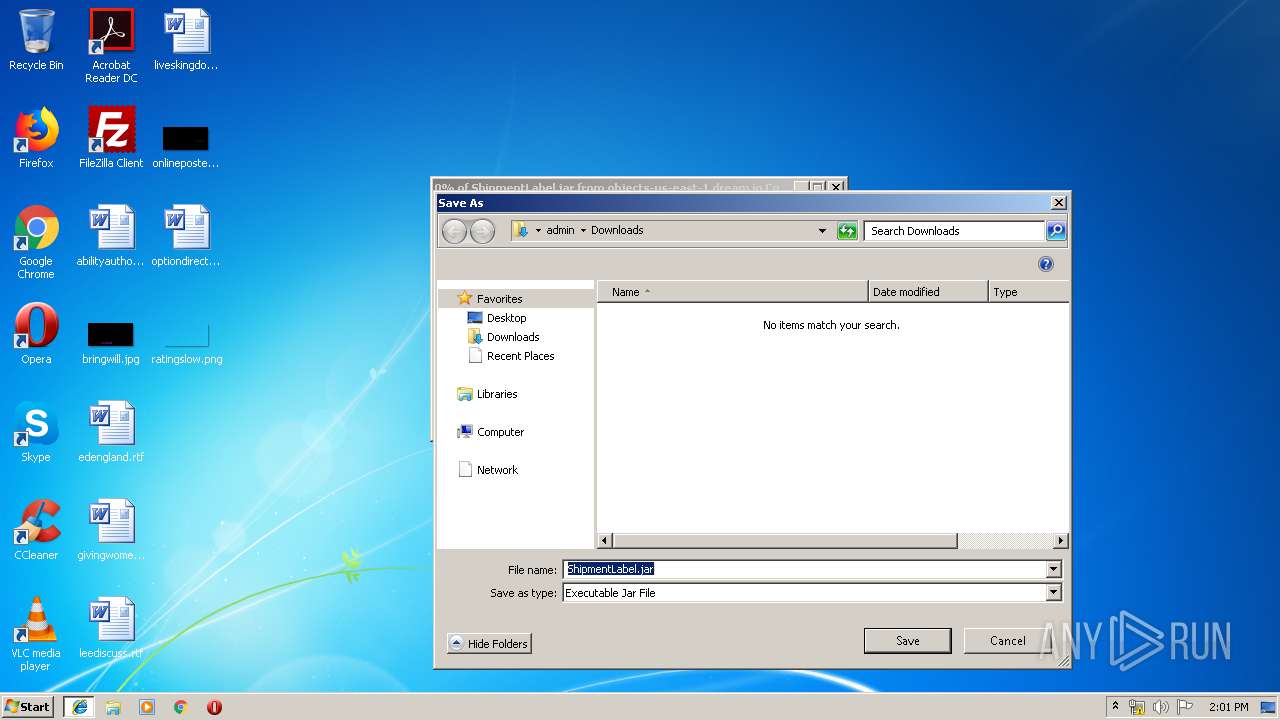
| 3312 | iexplore.exe | C:\Users\admin\Downloads\ShipmentLabel.jar | java | |
MD5:— | SHA256:— | |||
| 3948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019071120190712\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3312 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3696 | javaw.exe | 185.141.61.192:1507 | mrillo.ddns.net | — | — | malicious |
3948 | iexplore.exe | 208.113.201.33:443 | objects-us-east-1.dream.io | New Dream Network, LLC | US | unknown |
3312 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
objects-us-east-1.dream.io |
| suspicious |
www.bing.com |
| whitelisted |
mrillo.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3696 | javaw.exe | A Network Trojan was detected | ET TROJAN Possible Adwind SSL Cert (assylias.Inc) |
3696 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |
3696 | javaw.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Java.Adwind.cu |