| URL: | https://linkprotect.cudasvc.com/url?a=https%3a%2f%2fmmm.byteoversea.com%2fapps%2fgcrm_overseas%2fbackend%2faccess%2fthird-party%2femail%2fexternal-link%2fclick%3femailId%3dLBQVAWL2LBEHMQ3XMZKVUWKRNRHGQL2KKFXDS5TTPB4WM22LGFEVG5DJIN4G2U3DJQYHANDZIVRHKT2VKAVWU53VLJXW23LUGYYFAUSDKNYFOZTLOBQUETCCOVZHMLZZ%26originUrl%3dhttps%3a%2f%2fabrcorporateservices.com%2fo%2f%3fc3Y9bzM2NV8xX25vbSZtPWhRJnVpZD1VU0VSMDEwNzIwMjVVMzUwNzAxNTQmdD1CYg%3d%3dN0123Ncporter%40stpetebeach.org&c=E,1,DiEtwJIpAZL_RBG-yZfB3NVZmlW3OAITOgFmvK8Z2_ygc2SxDrUMs55_rMZd2AZHRsmWUEXiB3xgT1ouwIyUiy1pR5zjddrbi9h9tjlzzNv0&typo=1 |
| Full analysis: | https://app.any.run/tasks/e9c777ba-32c1-4d8f-a0df-8c7bb1bc7388 |
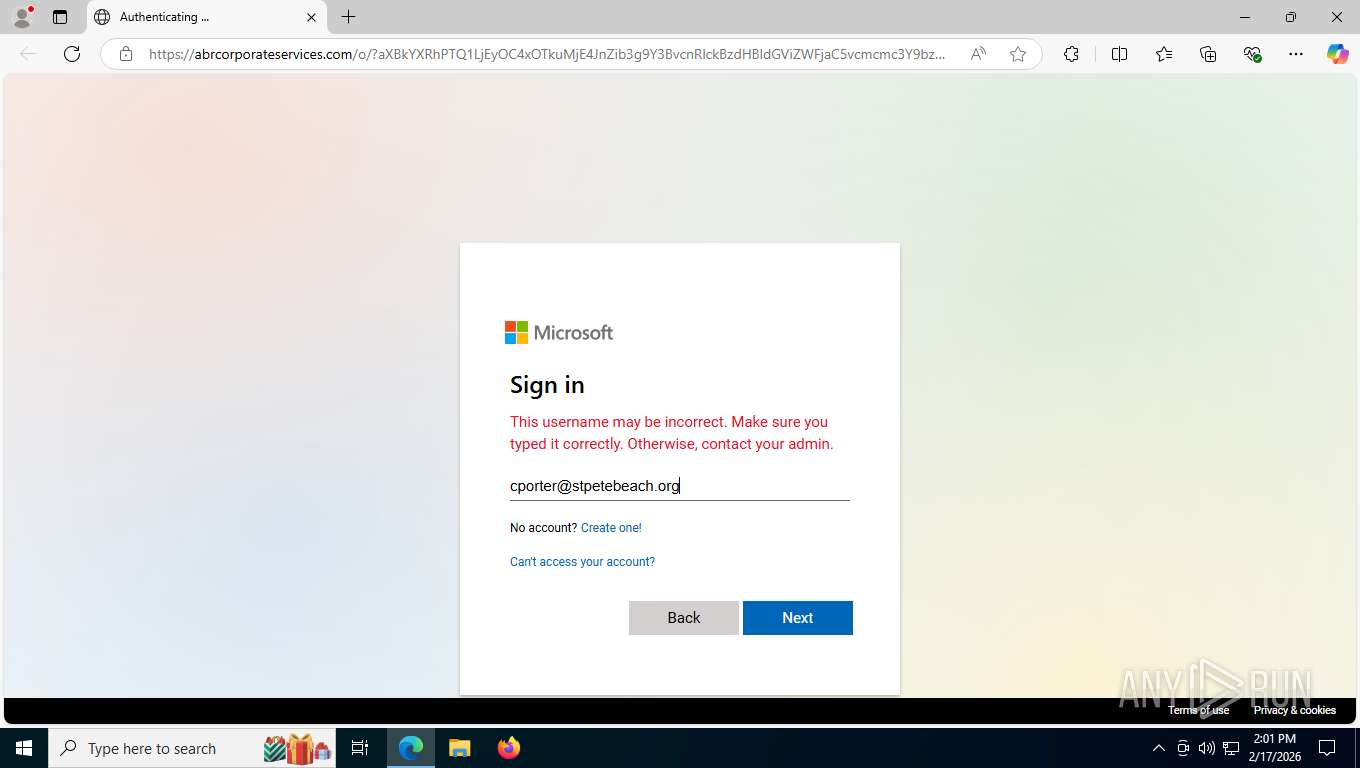
| Verdict: | Malicious activity |
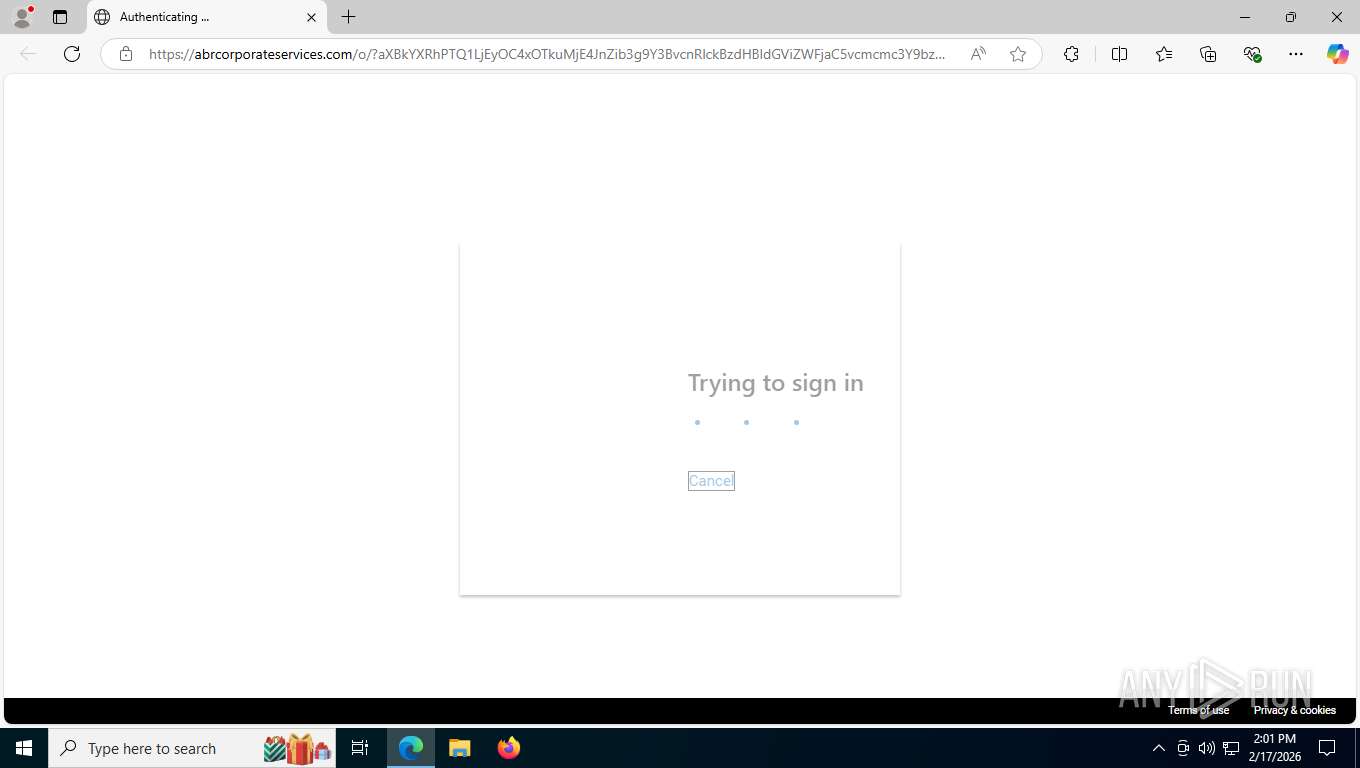
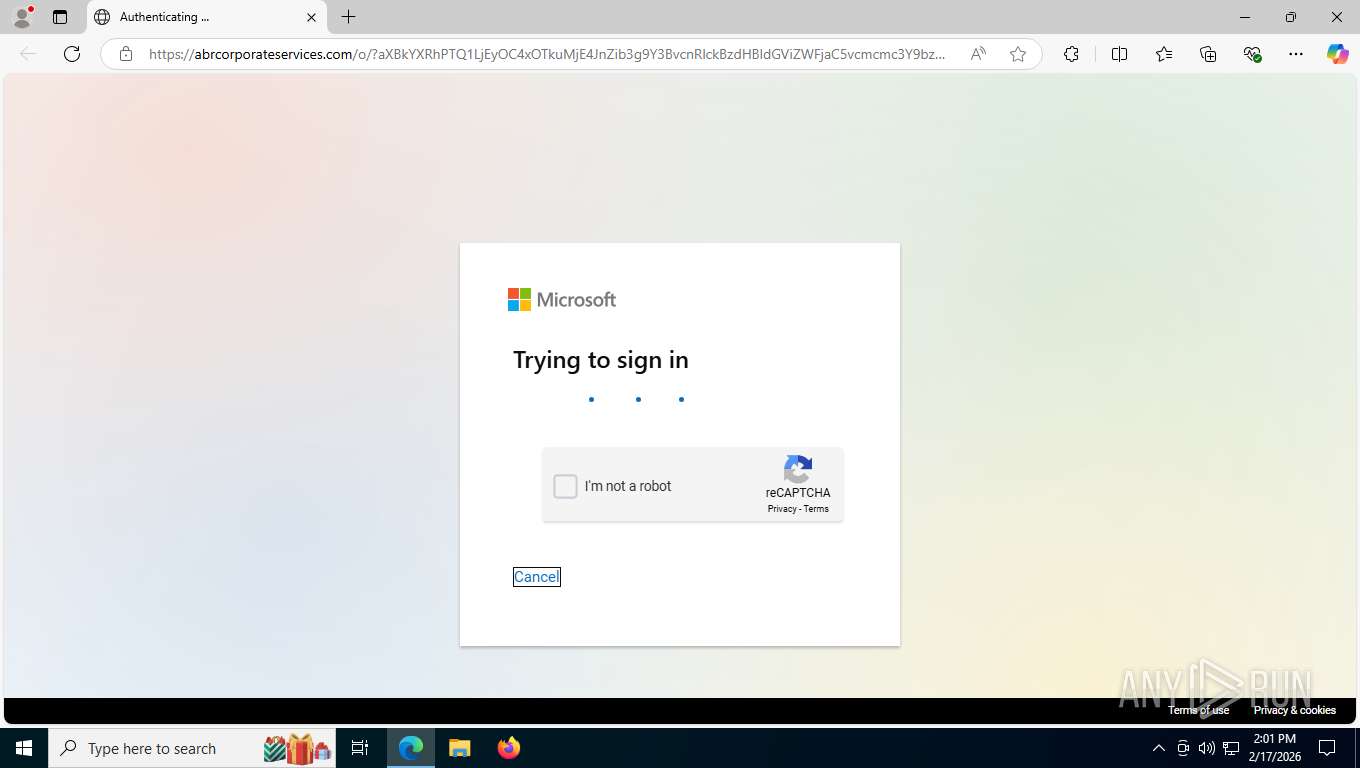
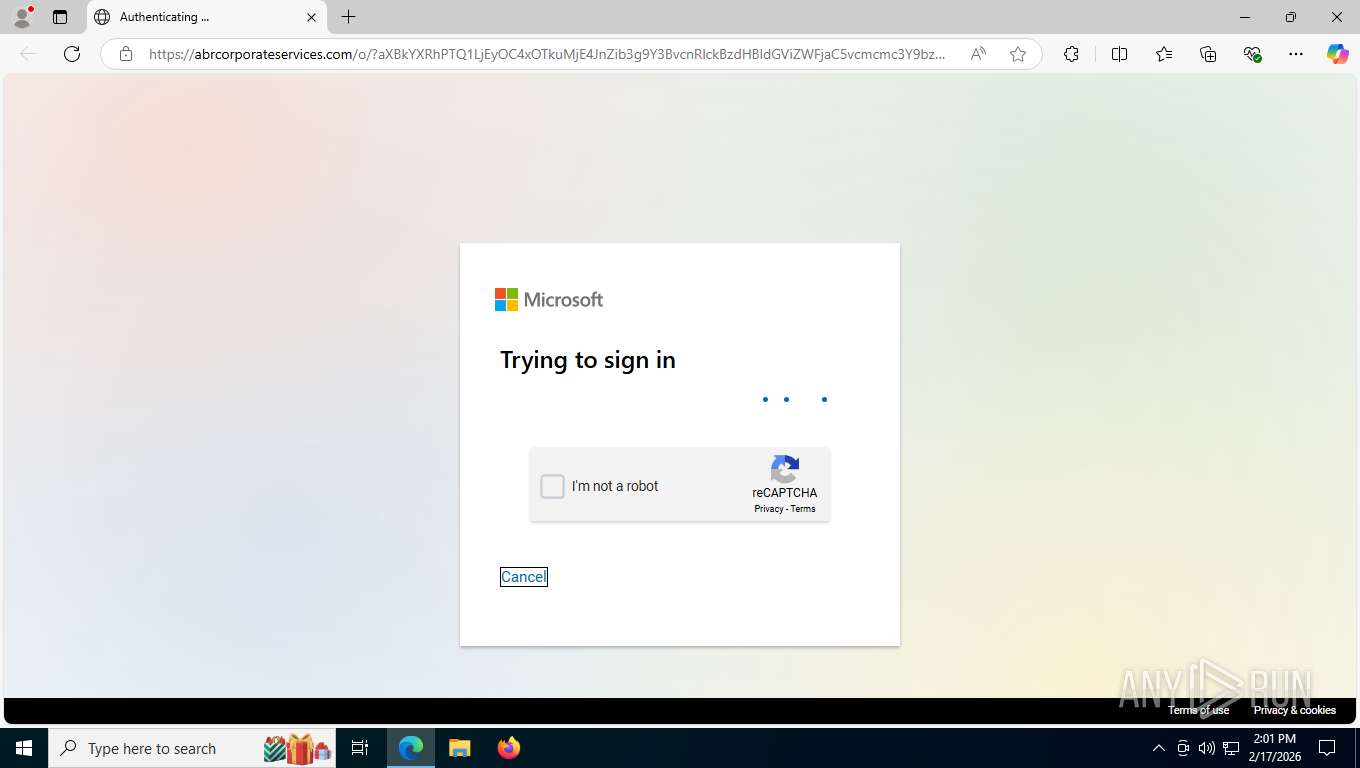
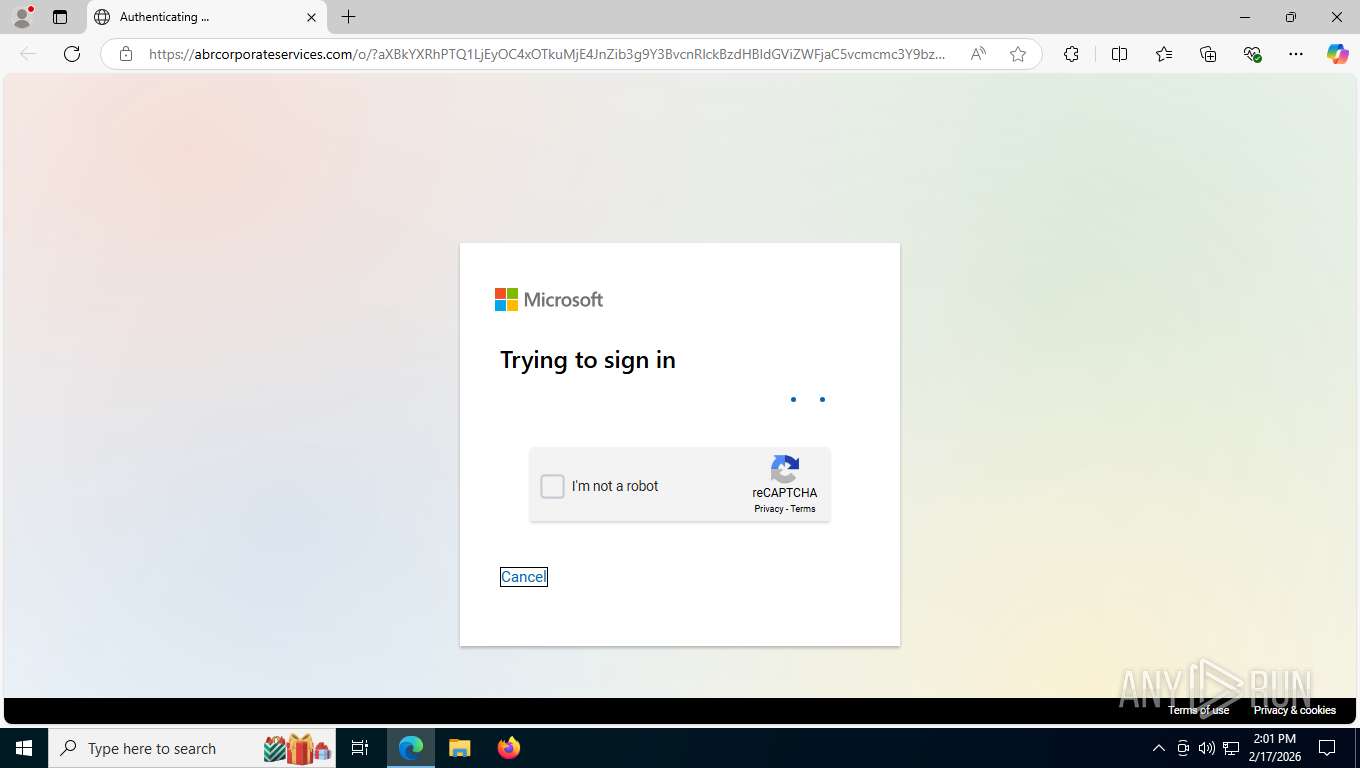
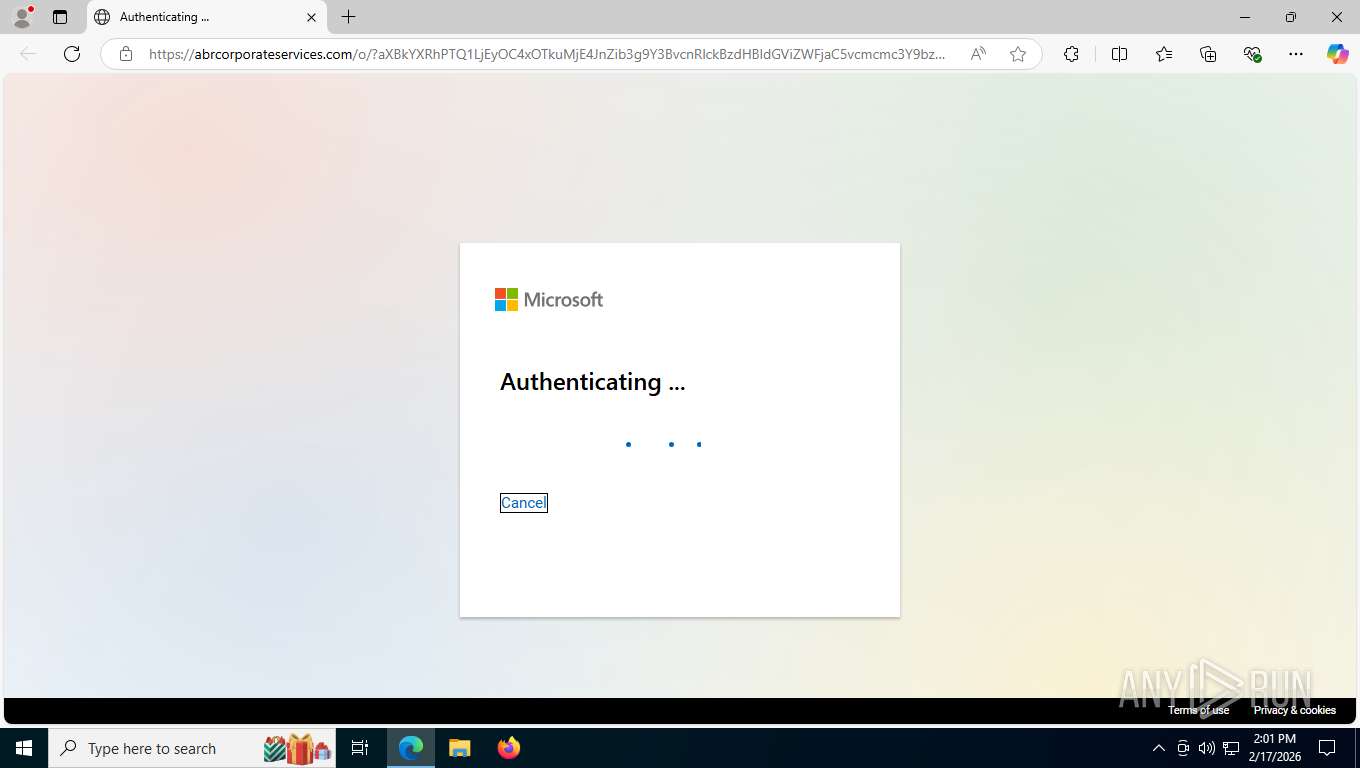
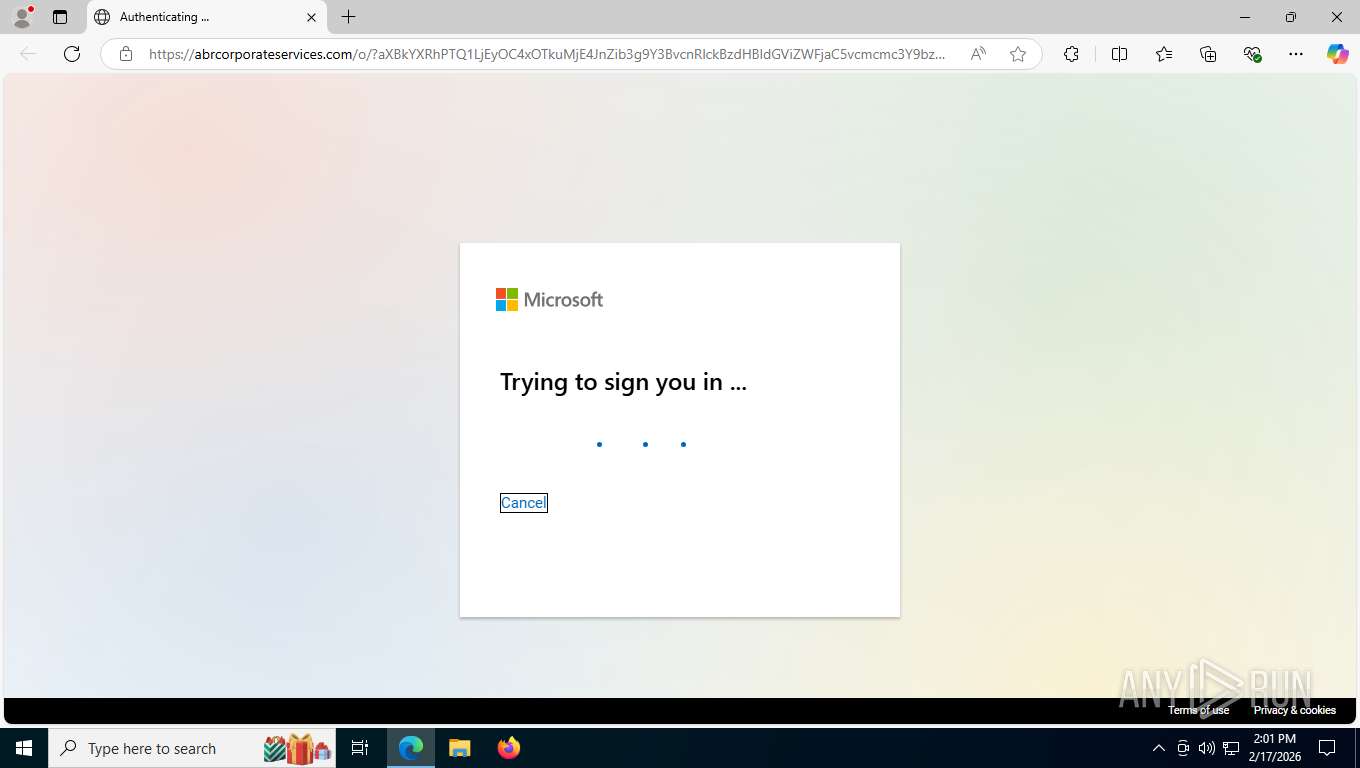
| Threats: | Mamba 2FA is an advanced phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) and target Microsoft 365 accounts. It focuses on intercepting authentication flows in real-time and enables threat actors to hijack user sessions and access sensitive systems even when additional security measures are in place. |
| Analysis date: | February 17, 2026, 19:01:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 47DD70823ECD1D18213AF7636AD5235F |
| SHA1: | DE0F2863F32324E4C4FCD22E70CCDAEA78E4BCE9 |
| SHA256: | E9227095D82459579FF914CE5BCCBBE93F62FA128F6F1948DA4A3D2944B936F9 |
| SSDEEP: | 12:2MtMeEcLFbaXwF1uUSBRU0rMsvQ9RgMYzhyq0KQ/zwM5aAo+3:2kjhIwF1uUSnMsI9RyzkJz1o+3 |
MALICIOUS
Mamba 2FA phishing kit has been detected
- msedge.exe (PID: 8004)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6852)
PHISHING has been detected (ML)
- msedge.exe (PID: 8004)
Fake Microsoft Authentication Page has been detected
- msedge.exe (PID: 8004)
SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- identity_helper.exe (PID: 5728)
Reads Environment values
- identity_helper.exe (PID: 5728)
Drops script file
- msedge.exe (PID: 8004)
Checks supported languages
- identity_helper.exe (PID: 5728)
Application launched itself
- msedge.exe (PID: 8004)
Page contains obfuscated JavaScript
- msedge.exe (PID: 8004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
170
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6428,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6488 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2260 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5452,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6912 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2376 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4240,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4260 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5616,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5608 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5780,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5660 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6080,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6124 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2836,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2804 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5460 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5852,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5992 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5728 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6496,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6660 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5848,i,9904170912351367562,12469089343297452609,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5876 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
583
Read events
583
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
4
Text files
12
Unknown types
109
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e51c7.TMP | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e51d7.TMP | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e51f6.TMP | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e5206.TMP | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5206.TMP | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8004 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
95
TCP/UDP connections
73
DNS requests
78
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6852 | msedge.exe | GET | 302 | 184.86.103.214:443 | https://mmm.byteoversea.com/apps/gcrm_overseas/backend/access/third-party/email/external-link/click?emailId=LBQVAWL2LBEHMQ3XMZKVUWKRNRHGQL2KKFXDS5TTPB4WM22LGFEVG5DJIN4G2U3DJQYHANDZIVRHKT2VKAVWU53VLJXW23LUGYYFAUSDKNYFOZTLOBQUETCCOVZHMLZZ&originUrl=https://abrcorporateservices.com/o/?c3Y9bzM2NV8xX25vbSZtPWhRJnVpZD1VU0VSMDEwNzIwMjVVMzUwNzAxNTQmdD1CYg==N0123Ncporter@stpetebeach.org | unknown | — | — | unknown |
6852 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:i3t3RbadfbKuyuzZ4J_58A6PPh4ae0LzrXrlyU5EFiY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6852 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | — | 4.30 Kb | whitelisted |
6852 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | — | 446 b | whitelisted |
6852 | msedge.exe | GET | 302 | 3.79.172.146:443 | https://linkprotect.cudasvc.com/url?a=https%3a%2f%2fmmm.byteoversea.com%2fapps%2fgcrm_overseas%2fbackend%2faccess%2fthird-party%2femail%2fexternal-link%2fclick%3femailId%3dLBQVAWL2LBEHMQ3XMZKVUWKRNRHGQL2KKFXDS5TTPB4WM22LGFEVG5DJIN4G2U3DJQYHANDZIVRHKT2VKAVWU53VLJXW23LUGYYFAUSDKNYFOZTLOBQUETCCOVZHMLZZ%26originUrl%3dhttps%3a%2f%2fabrcorporateservices.com%2fo%2f%3fc3Y9bzM2NV8xX25vbSZtPWhRJnVpZD1VU0VSMDEwNzIwMjVVMzUwNzAxNTQmdD1CYg%3d%3dN0123Ncporter%40stpetebeach.org&c=E,1,DiEtwJIpAZL_RBG-yZfB3NVZmlW3OAITOgFmvK8Z2_ygc2SxDrUMs55_rMZd2AZHRsmWUEXiB3xgT1ouwIyUiy1pR5zjddrbi9h9tjlzzNv0&typo=1 | unknown | — | 138 b | malicious |
6852 | msedge.exe | GET | 200 | 13.107.246.45:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | — | 82 b | whitelisted |
6852 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | — | 25 b | whitelisted |
6852 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1771354875&lafgdate=0 | unknown | — | 41.4 Kb | whitelisted |
6852 | msedge.exe | GET | 200 | 216.106.180.52:443 | https://abrcorporateservices.com/o/?c3Y9bzM2NV8xX25vbSZtPWhRJnVpZD1VU0VSMDEwNzIwMjVVMzUwNzAxNTQmdD1CYg==N0123Ncporter@stpetebeach.org | unknown | — | 2.81 Kb | unknown |
6852 | msedge.exe | GET | 404 | 216.106.180.52:443 | https://abrcorporateservices.com/files/images/Logo.png | unknown | — | 1.22 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5516 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7428 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6852 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6852 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6852 | msedge.exe | 3.79.172.146:443 | linkprotect.cudasvc.com | AMAZON-02 | US | whitelisted |
6852 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6852 | msedge.exe | 13.107.246.45:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
linkprotect.cudasvc.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
mmm.byteoversea.com |
| whitelisted |
abrcorporateservices.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6852 | msedge.exe | Generic Protocol Command Decode | SURICATA HTTP invalid response field folding |
6852 | msedge.exe | Generic Protocol Command Decode | SURICATA HTTP response header invalid |
6852 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Mamba2FA HTTP URL Observed (sv= b64-encoded) |
6852 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Mamba2FA HTTP URL Observed (sv= b64-encoded) |
6852 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing URL |
6852 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Mamba2FA HTTP URL Observed (sv= b64-encoded) |
6852 | msedge.exe | Attempted Information Leak | PHISHING [ANY.RUN] Browser Fingerprinting related to Phishing Kits observed |
6852 | msedge.exe | Possible Social Engineering Attempted | ET PHISHING Javascript Browser Fingerprinting POST Request |
6852 | msedge.exe | Information Leak | SUSPICIOUS [ANY.RUN] FingerprintJS Collected Data observed in HTTP POST request |
6852 | msedge.exe | Misc activity | ET HUNTING [TW] Likely Javascript-Obfuscator Usage Observed M1 |