| File name: | f83fb9ce6a83da58b20685c1d7e1e546 |
| Full analysis: | https://app.any.run/tasks/f6409cf7-08e4-44f8-a9da-43a44b0e037f |
| Verdict: | Malicious activity |
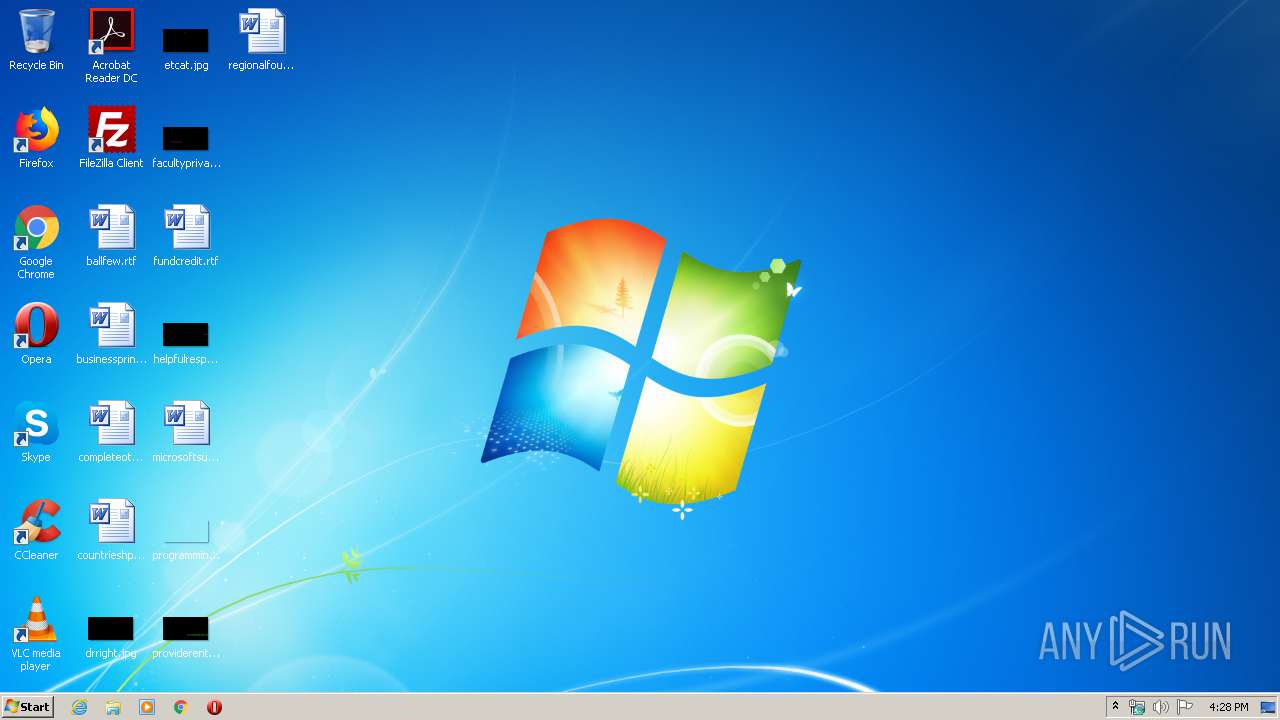
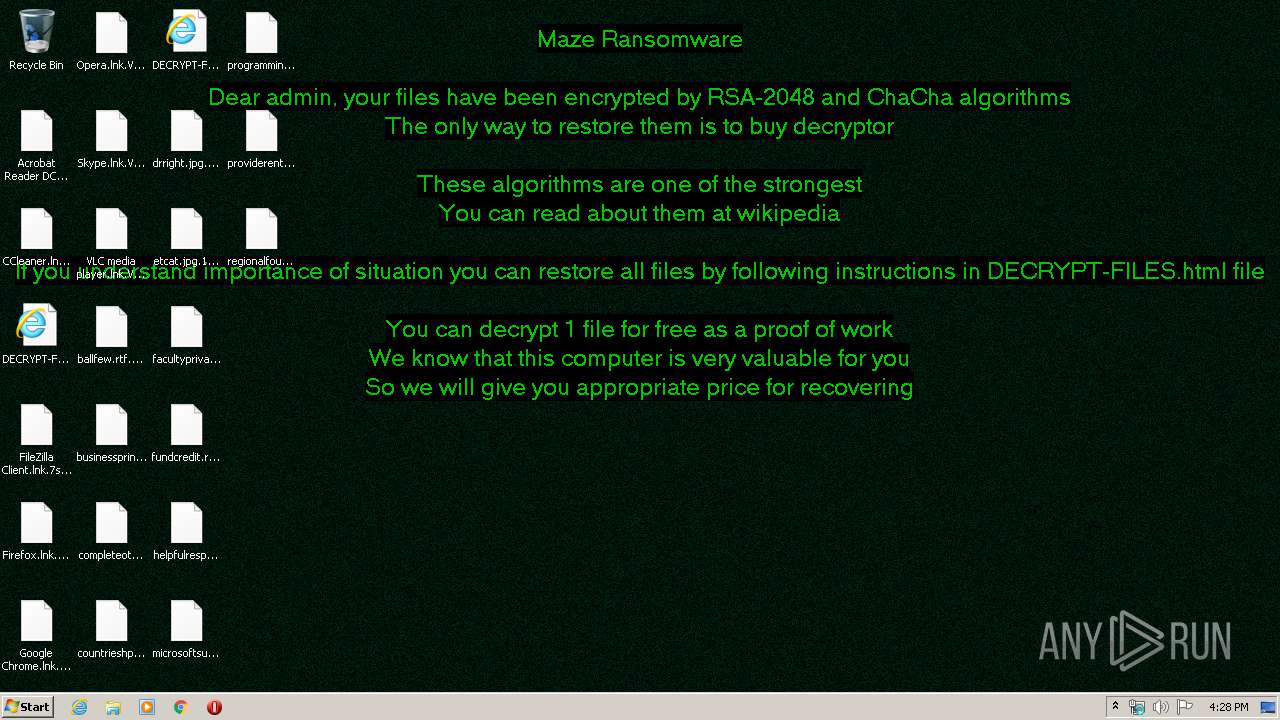
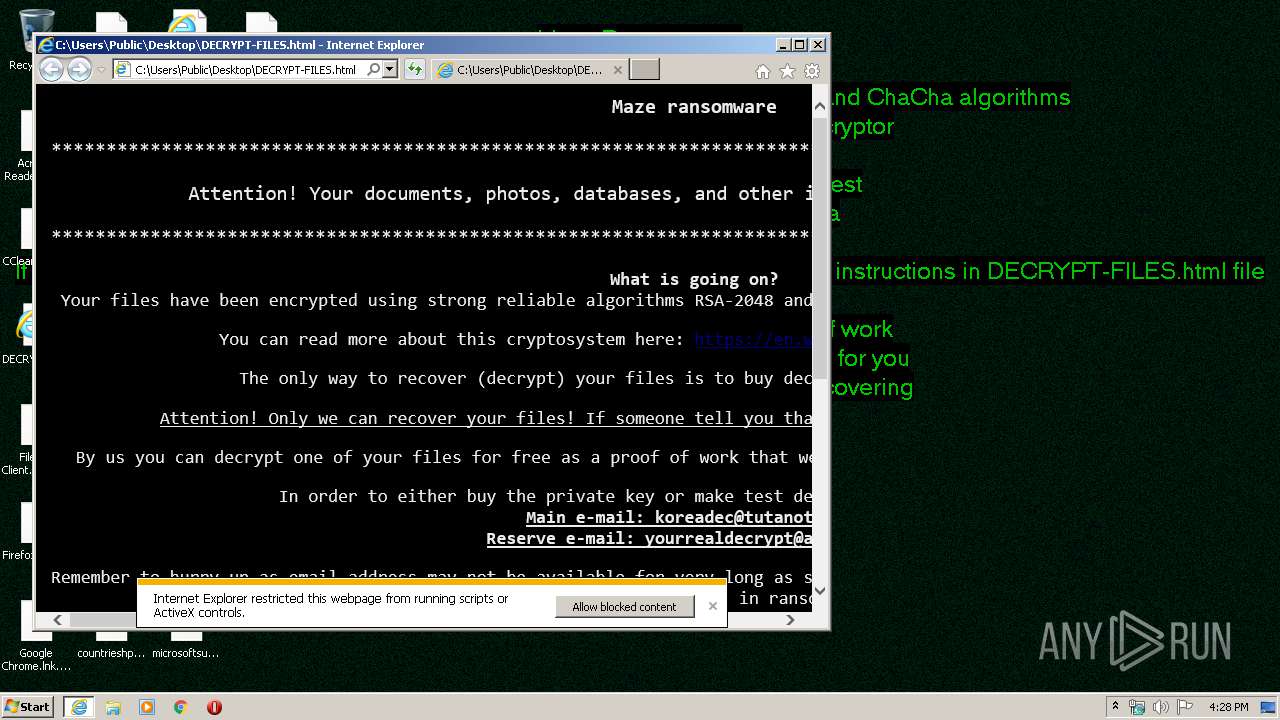
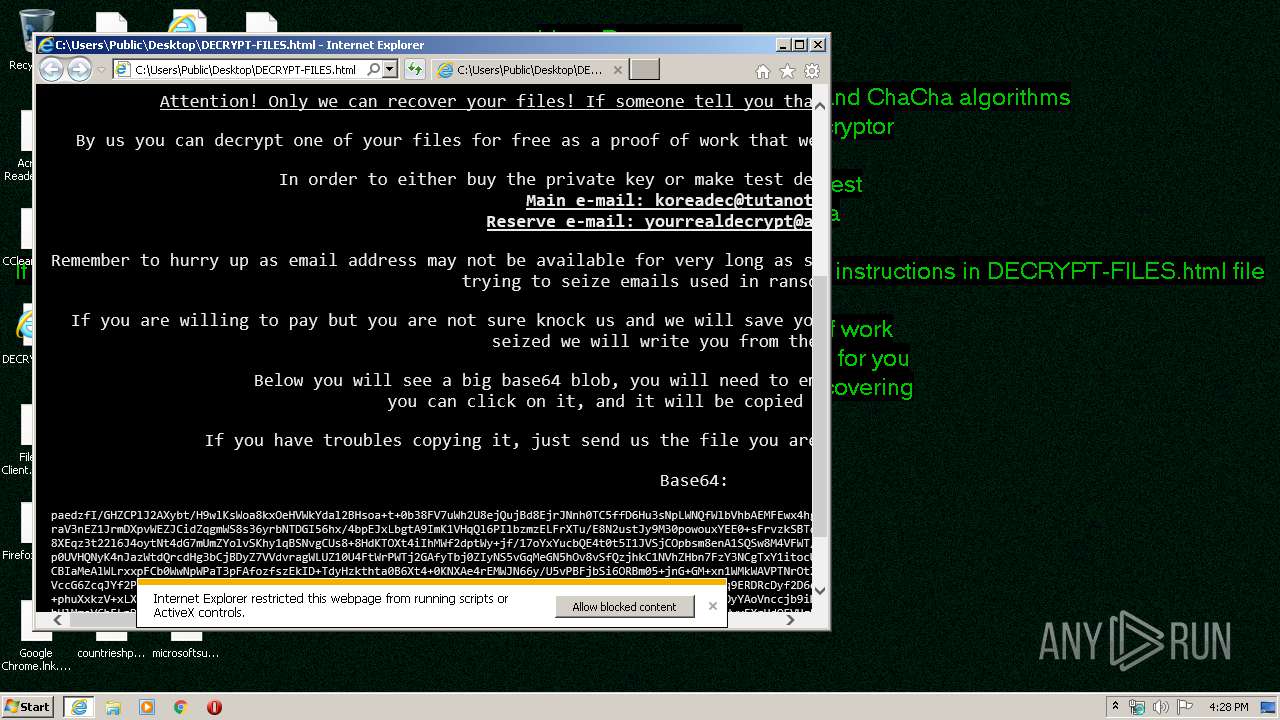
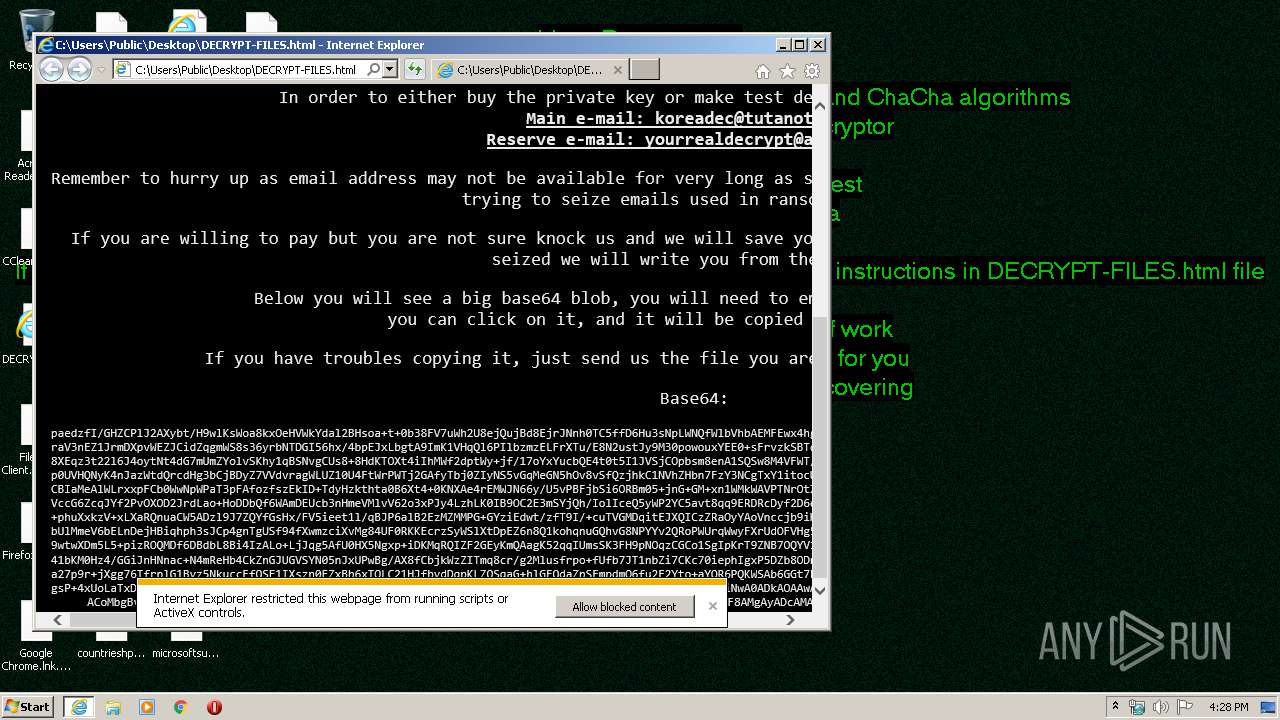
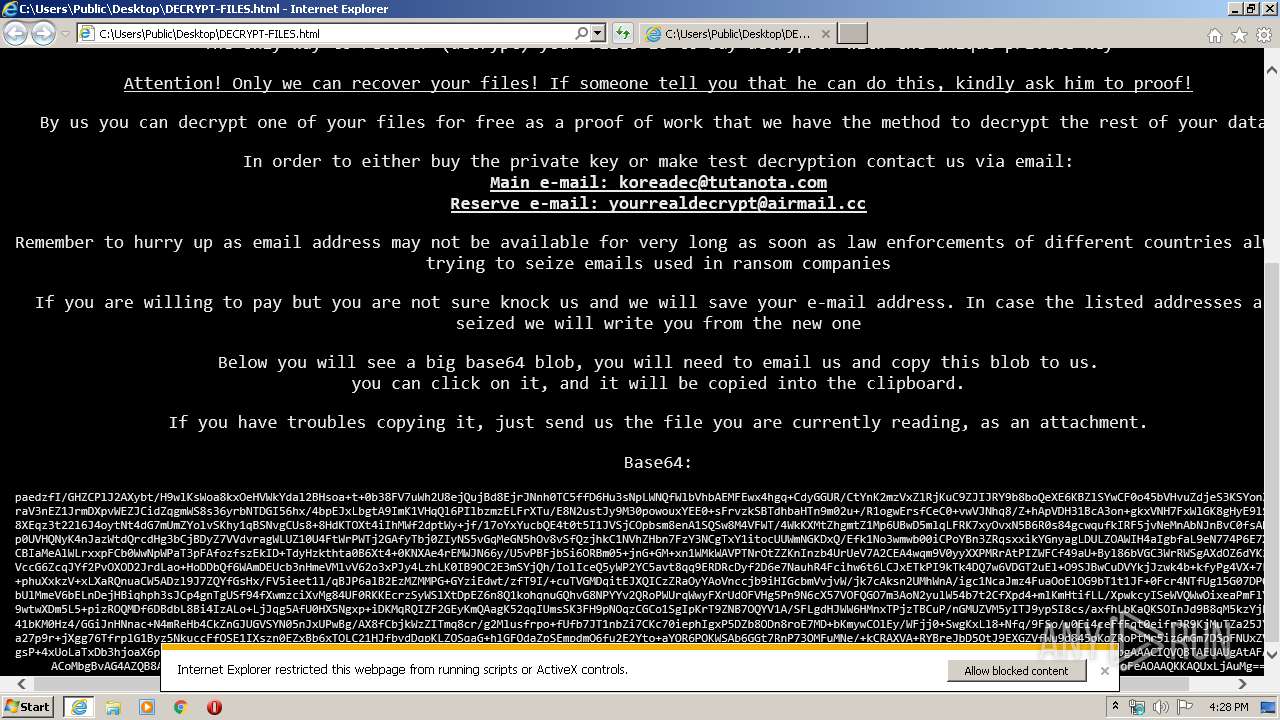
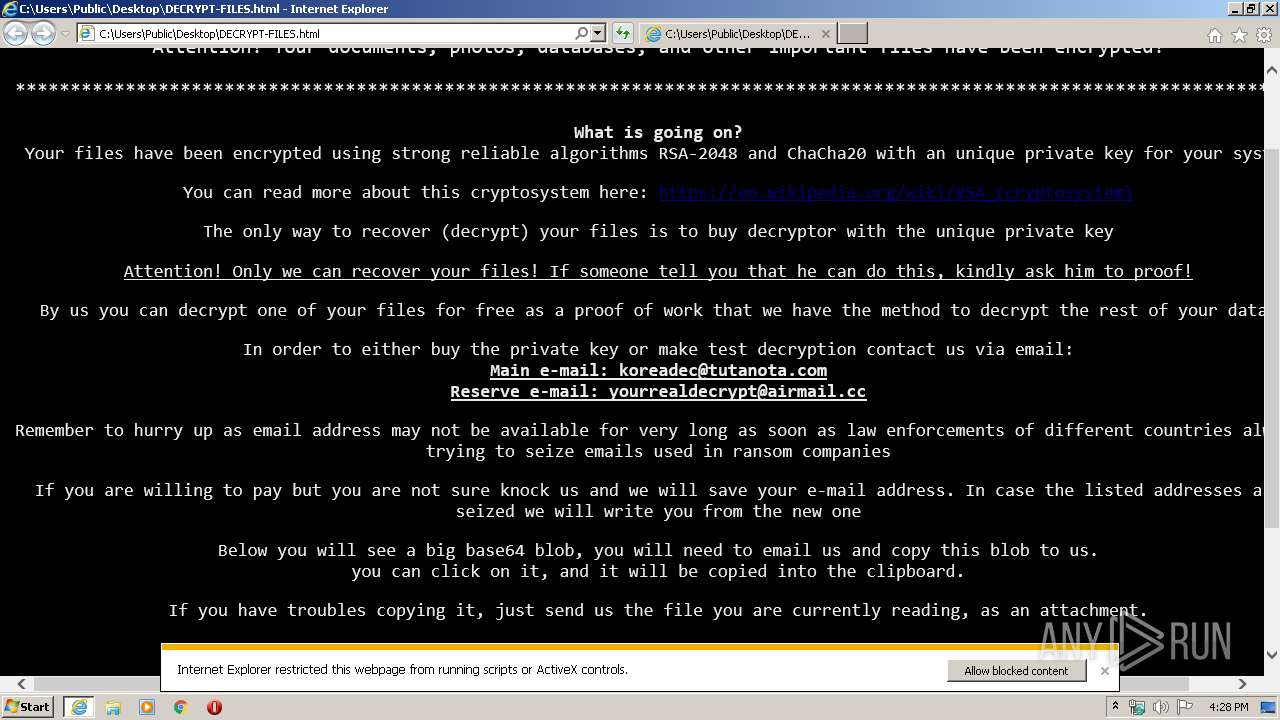
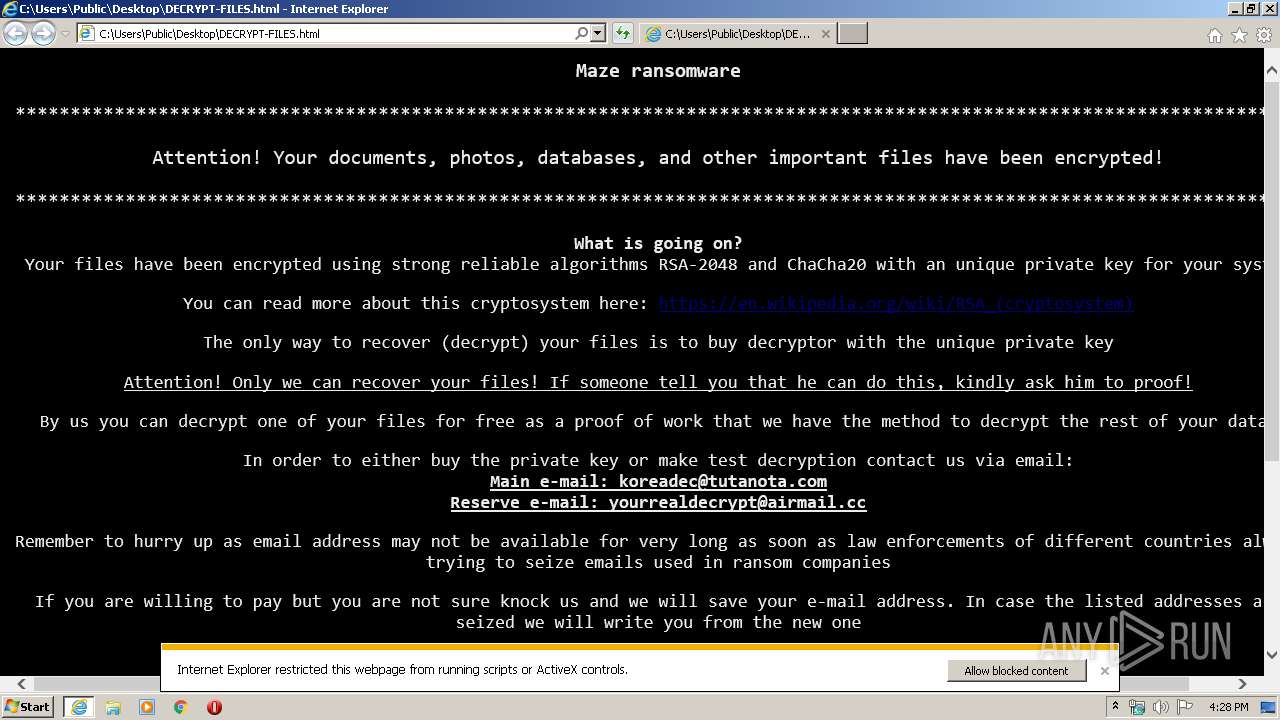
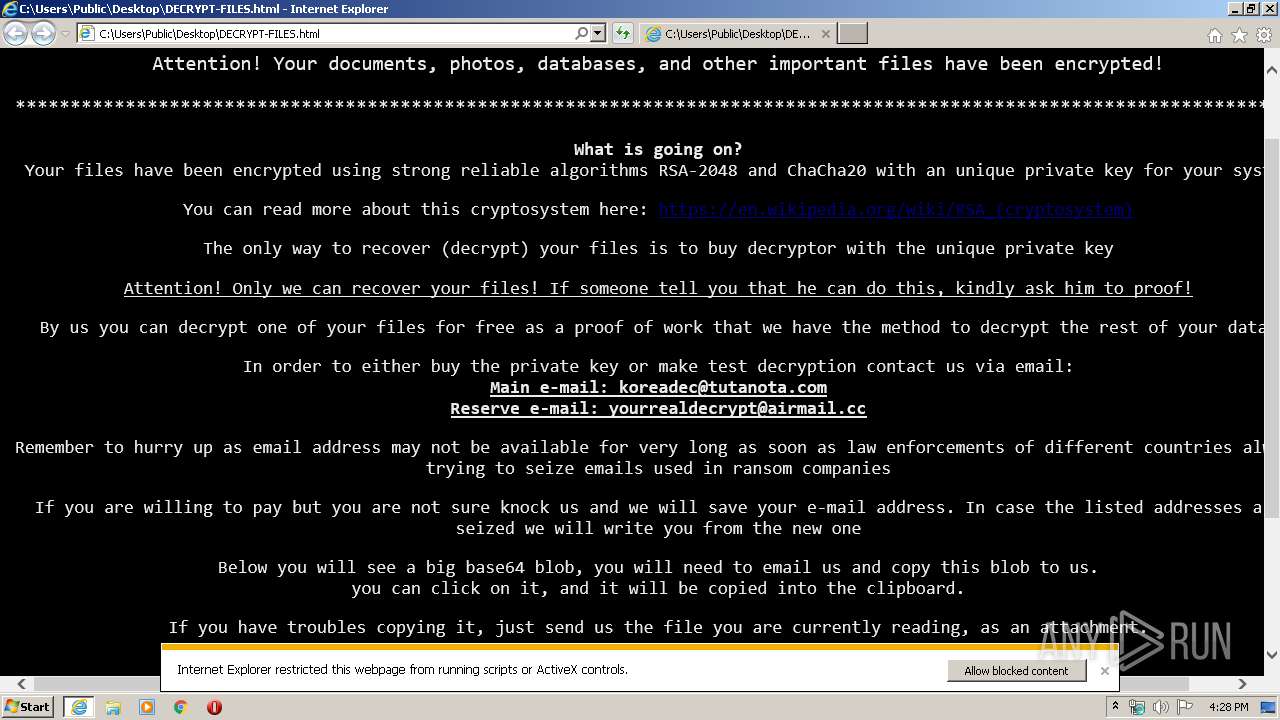
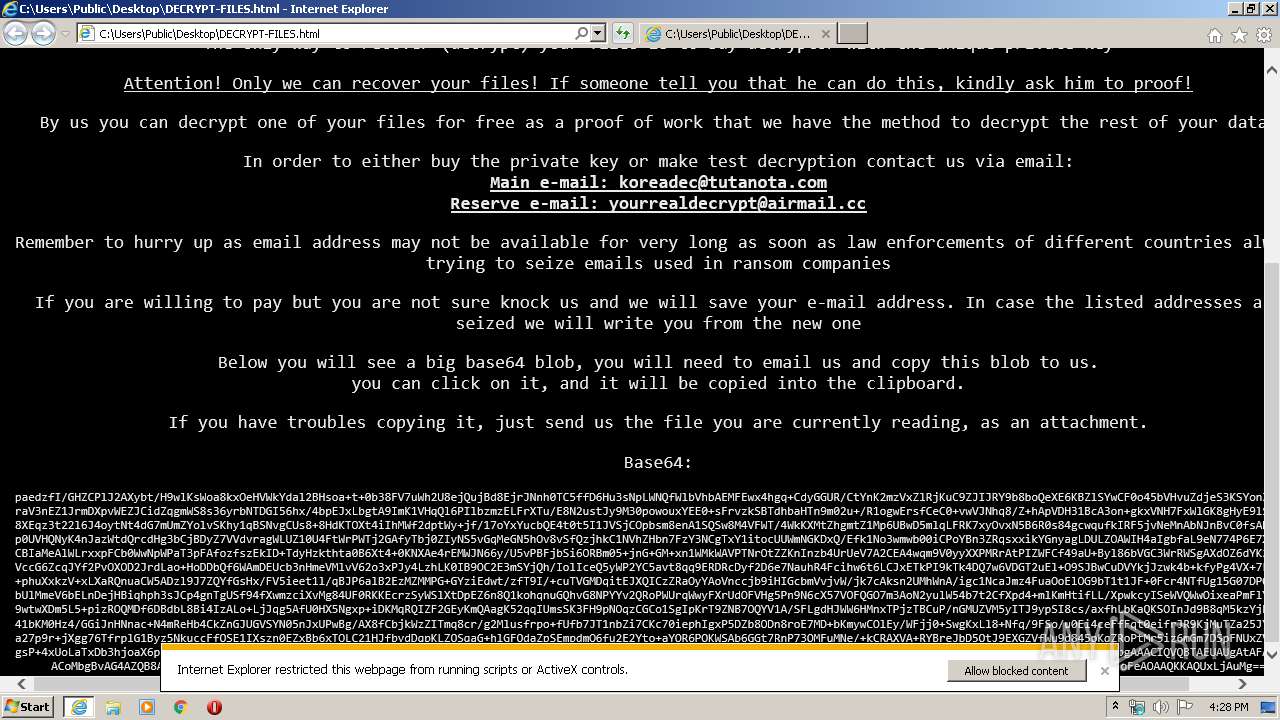
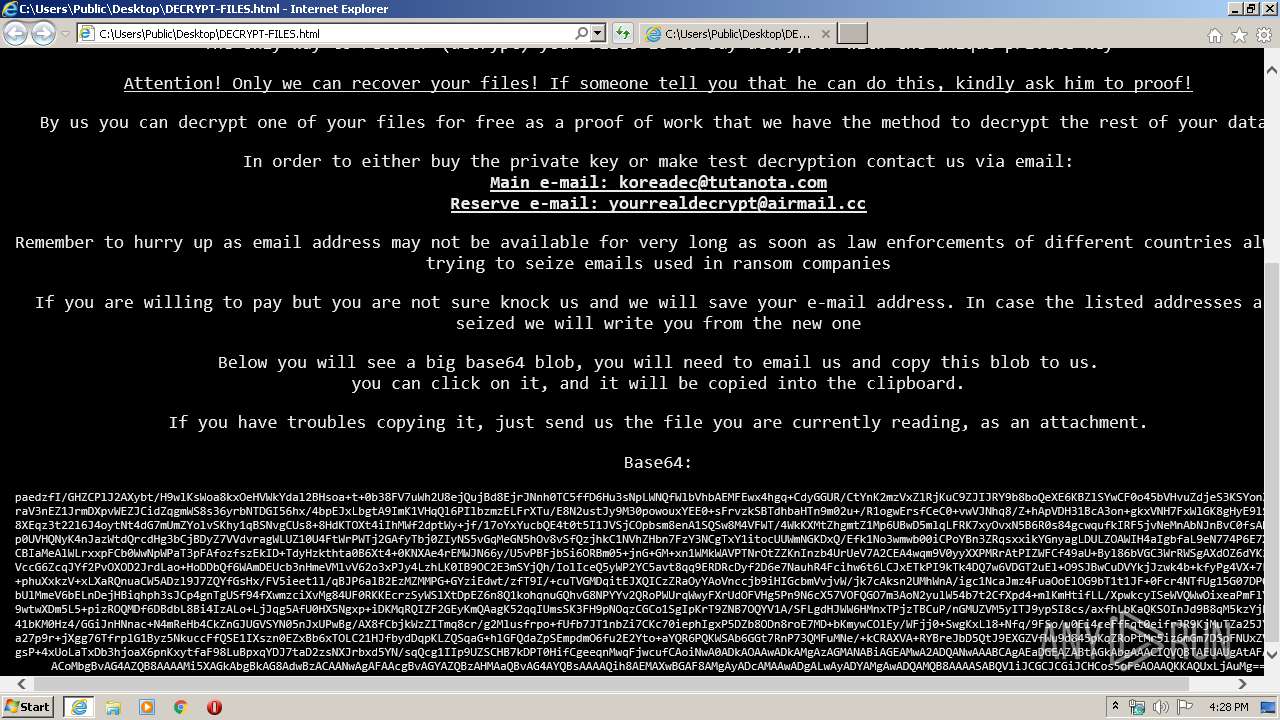
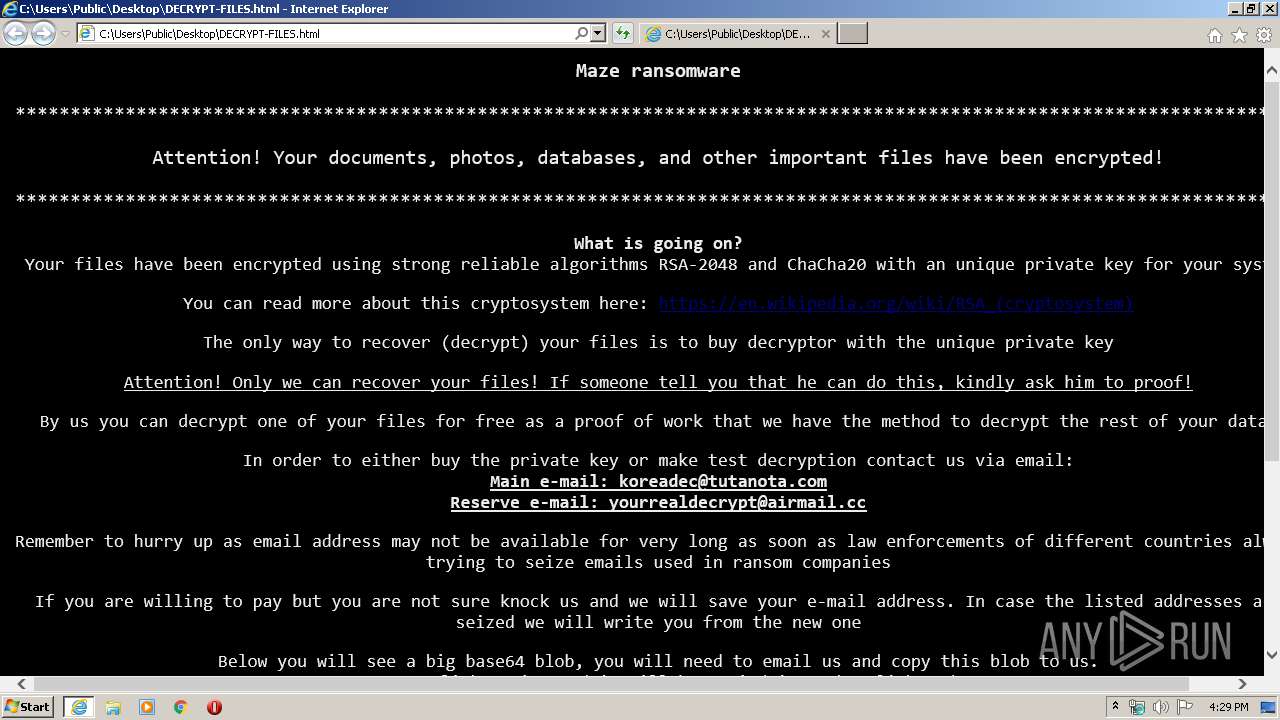
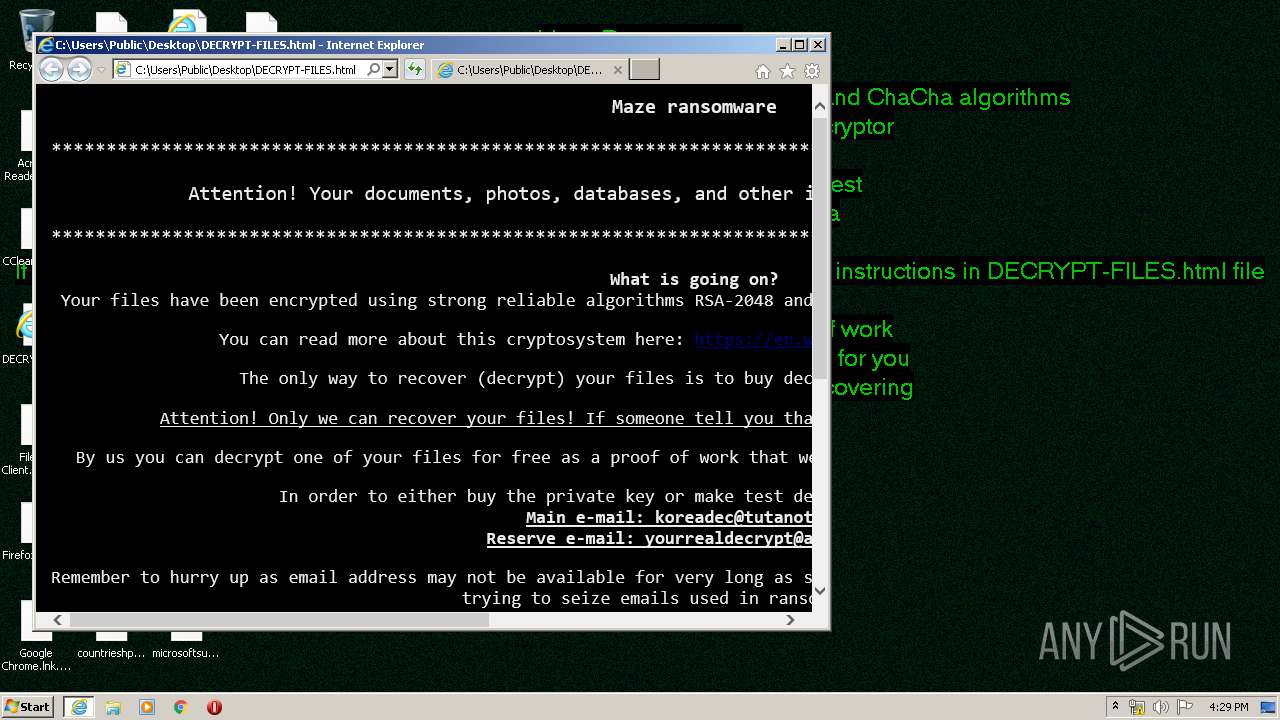
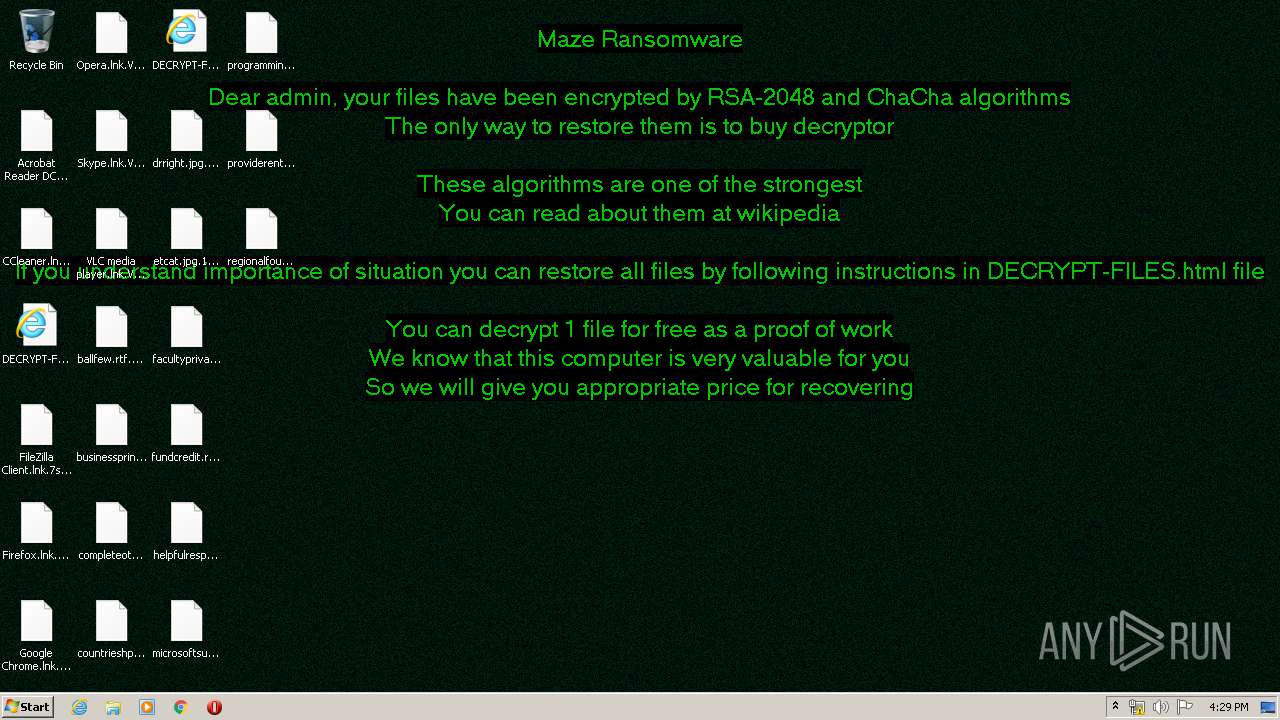
| Threats: | Maze is ransomware — a malware type that encrypts the victim’s files and restores the data in exchange for a ransom payment. One of the most distinguishable features of Maze is that it is one of the first malware of the kind to publicly release stolen data. |
| Analysis date: | March 30, 2020, 15:27:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F83FB9CE6A83DA58B20685C1D7E1E546 |
| SHA1: | 01C459B549C1C2A68208D38D4BA5E36D29212A4F |
| SHA256: | E8A091A84DD2EA7EE429135FF48E9F48F7787637CCB79F6C3EB42F34588BC684 |
| SSDEEP: | 12288:v6l/7FpnaeoQbRLBYdunMCayql4YcQD+AgJbAWgjbgpQ:CDna43YAKl4Yci+AggEpQ |
MALICIOUS
Deletes shadow copies
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Writes file to Word startup folder
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Actions looks like stealing of personal data
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Writes to a start menu file
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
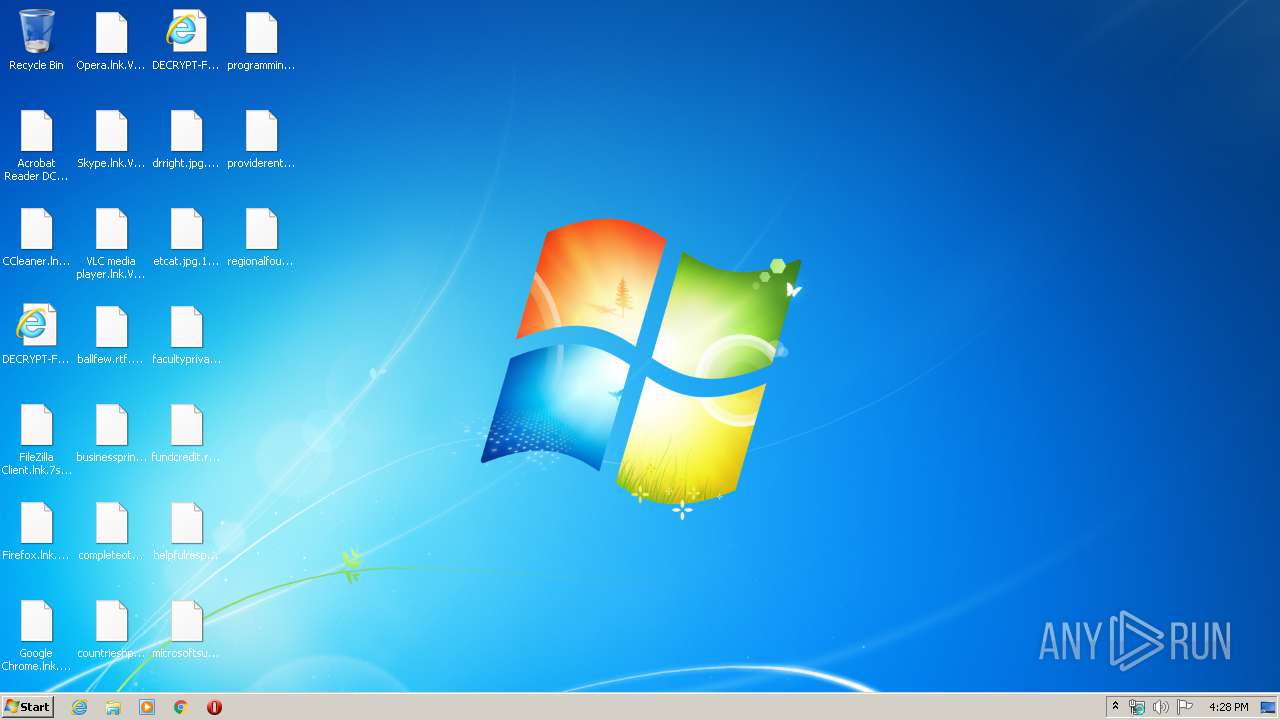
Renames files like Ransomware
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Modifies files in Chrome extension folder
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
SUSPICIOUS
Reads the cookies of Google Chrome
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Executed as Windows Service
- vssvc.exe (PID: 3036)
Creates files in the program directory
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Reads the cookies of Mozilla Firefox
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Connects to server without host name
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Creates files like Ransomware instruction
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
Creates files in the user directory
- f83fb9ce6a83da58b20685c1d7e1e546.exe (PID: 660)
INFO
Manual execution by user
- iexplore.exe (PID: 2448)
Reads Internet Cache Settings
- iexplore.exe (PID: 2448)
Changes internet zones settings
- iexplore.exe (PID: 2448)
Reads internet explorer settings
- iexplore.exe (PID: 3536)
Creates files in the user directory
- iexplore.exe (PID: 2448)
Reads settings of System Certificates
- iexplore.exe (PID: 2448)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2448)
Changes settings of System certificates
- iexplore.exe (PID: 2448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:27 22:03:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 82432 |
| InitializedDataSize: | 409088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9fa7 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-May-2019 20:03:22 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 27-May-2019 20:03:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014043 | 0x00014200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62596 |
.rdata | 0x00016000 | 0x000065BE | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.76406 |
.data | 0x0001D000 | 0x0005C240 | 0x0005A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99076 |
.reloc | 0x0007A000 | 0x00001214 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.22098 |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
45
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Users\admin\AppData\Local\Temp\f83fb9ce6a83da58b20685c1d7e1e546.exe" | C:\Users\admin\AppData\Local\Temp\f83fb9ce6a83da58b20685c1d7e1e546.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\Public\Desktop\DECRYPT-FILES.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2988 | "C:\knnwh\ofbx\nh\..\..\..\Windows\j\ikwx\fygv\..\..\..\system32\n\tfdv\..\..\wbem\mj\..\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | f83fb9ce6a83da58b20685c1d7e1e546.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3036 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3536 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2448 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3876 | "C:\loi\kqjq\..\..\Windows\b\x\xqln\..\..\..\system32\kxxds\..\wbem\crqrr\kdq\x\..\..\..\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | f83fb9ce6a83da58b20685c1d7e1e546.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 897
Read events
1 057
Write events
4 594
Delete events
2 246
Modification events
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\Voices |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech\Voices\Tokens\MS-Anna-1033-20-DSK | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | CLSID |
Value: {C9E37C15-DF92-4727-85D6-72E5EEB6995A} | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | |
Value: Current User Lexicon | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\CurrentUserLexicon\{C9E37C15-DF92-4727-85D6-72E5EEB6995A}\Files |
| Operation: | write | Name: | Datafile |
Value: %1a%\Microsoft\Speech\Files\UserLexicons\SP_733D9546B0914480836EAA96FAC036D1.dat | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | Generation |
Value: 0 | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\PhoneConverters |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech\PhoneConverters\Tokens\English | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | |
Value: Speakers (Realtek AC'97 Audio) | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | CLSID |
Value: {A8C680EB-3D32-11D2-9EE7-00C04F797396} | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | DeviceName |
Value: Speakers (Realtek AC'97 Audio) | |||
| (PID) Process: | (660) f83fb9ce6a83da58b20685c1d7e1e546.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | DeviceId |
Value: {0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} | |||
Executable files
0
Suspicious files
1 808
Text files
1 055
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\config.sys | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.I4ZfGrO | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{02b4b32f-3d9a-4f0c-90b3-b3f695ffdbdb}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{0e2a6214-ab14-4acd-9944-51dcd3caf902}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\DECRYPT-FILES.html | html | |
MD5:— | SHA256:— | |||
| 660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{14e6e058-39ee-43ce-ac15-7acb7d834dae}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
10
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | POST | — | 92.63.8.47:80 | http://92.63.8.47/signout/loiikqjq.shtml | TR | — | — | malicious |
660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | POST | — | 92.63.8.47:80 | http://92.63.8.47/view/private/j.aspx | TR | — | — | malicious |
2448 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2448 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2448 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2448 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
660 | f83fb9ce6a83da58b20685c1d7e1e546.exe | 92.63.8.47:80 | — | Nethouse Bilgi Islem Merkezi Ltd | TR | malicious |
2448 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2448 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2448 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |