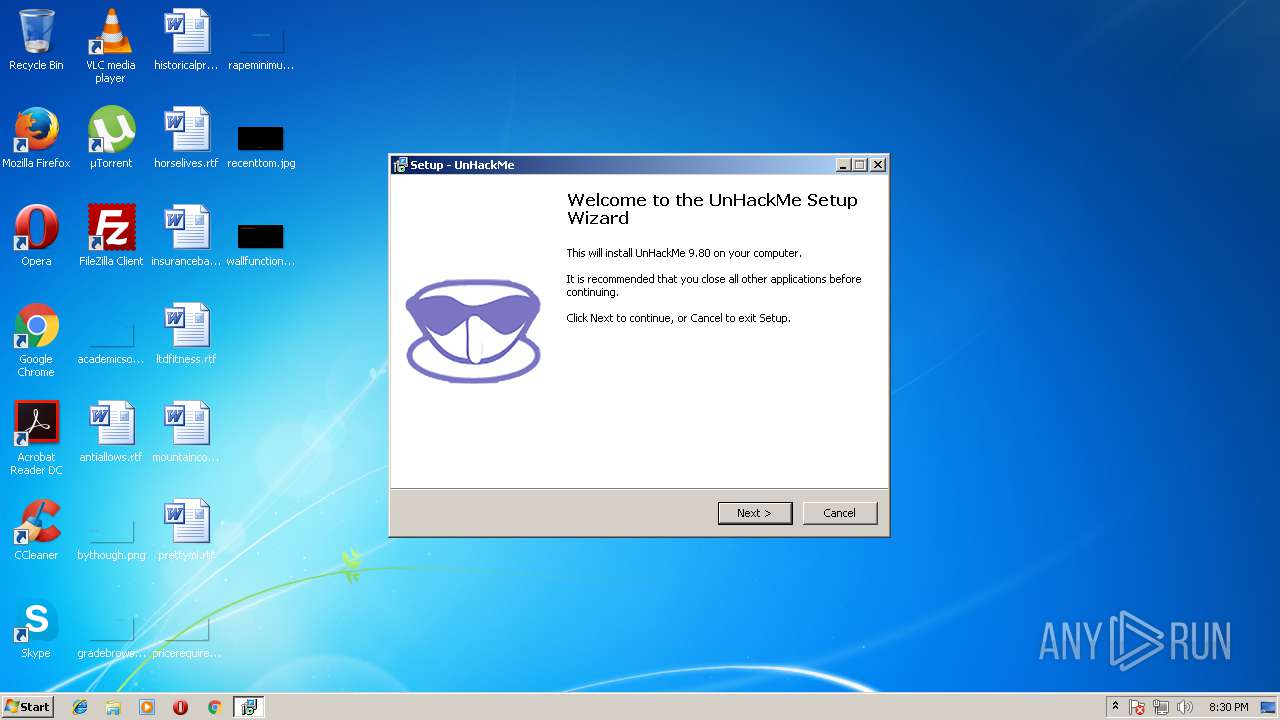
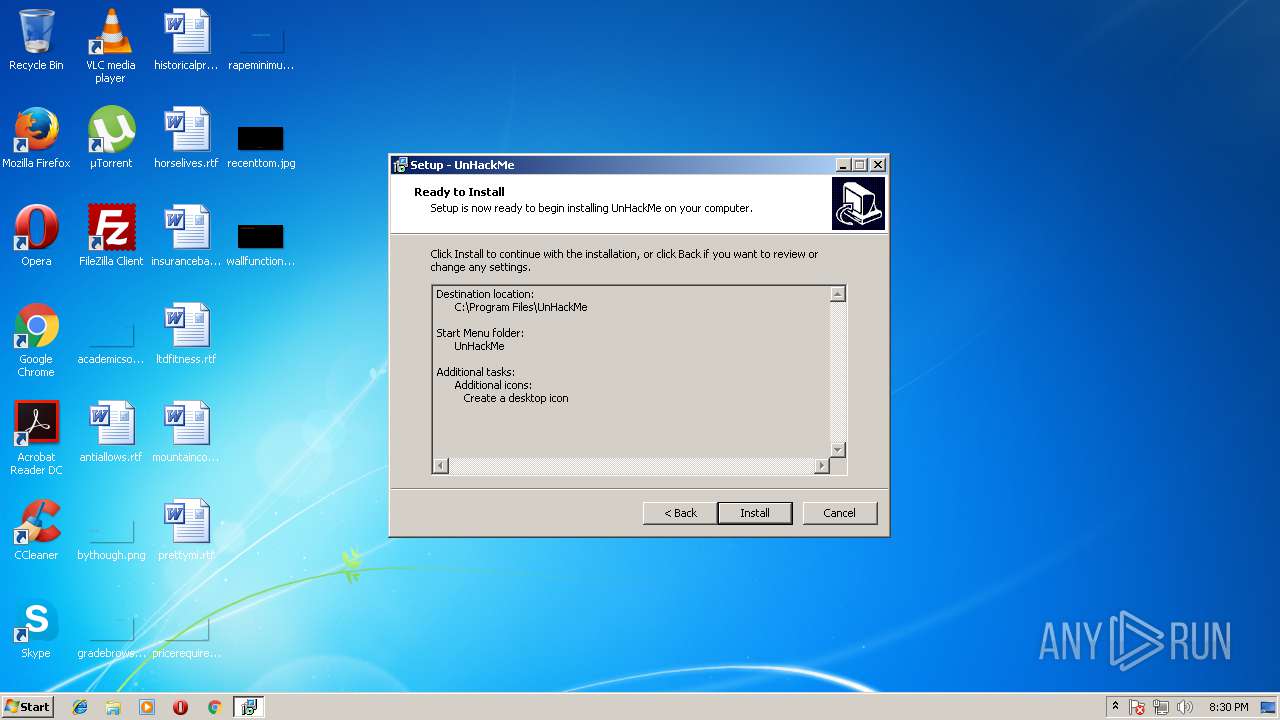
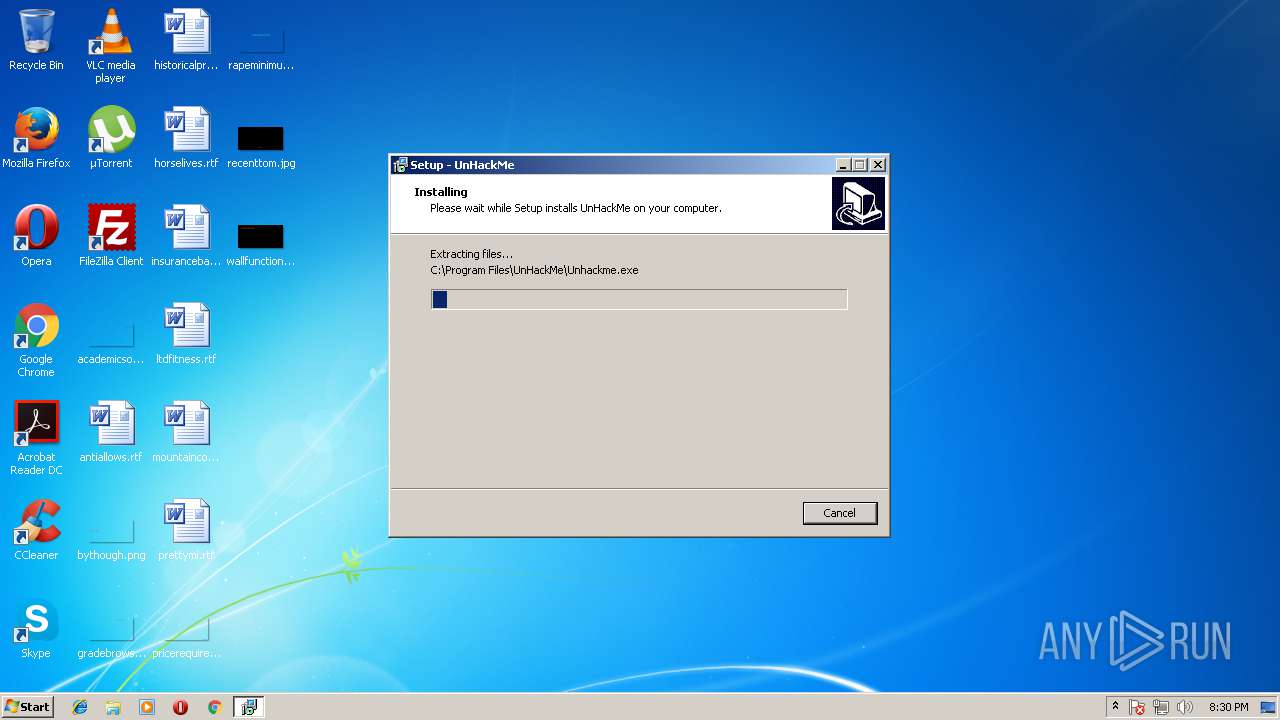
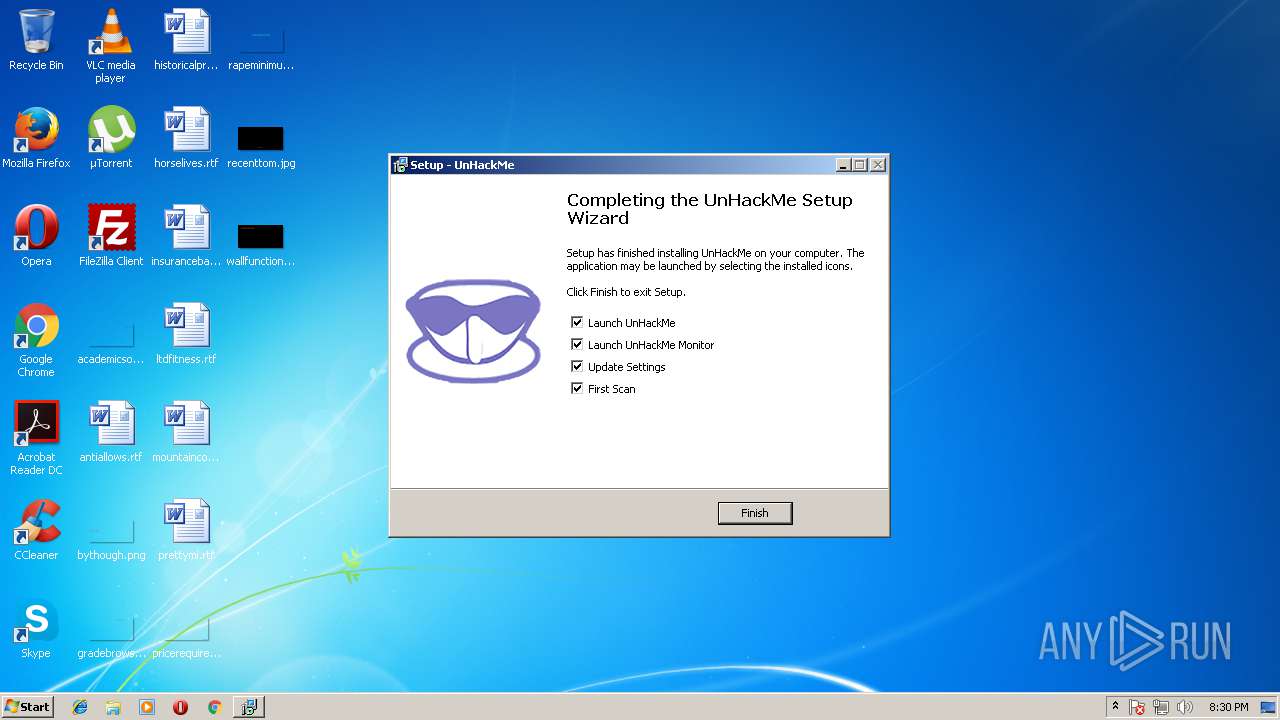
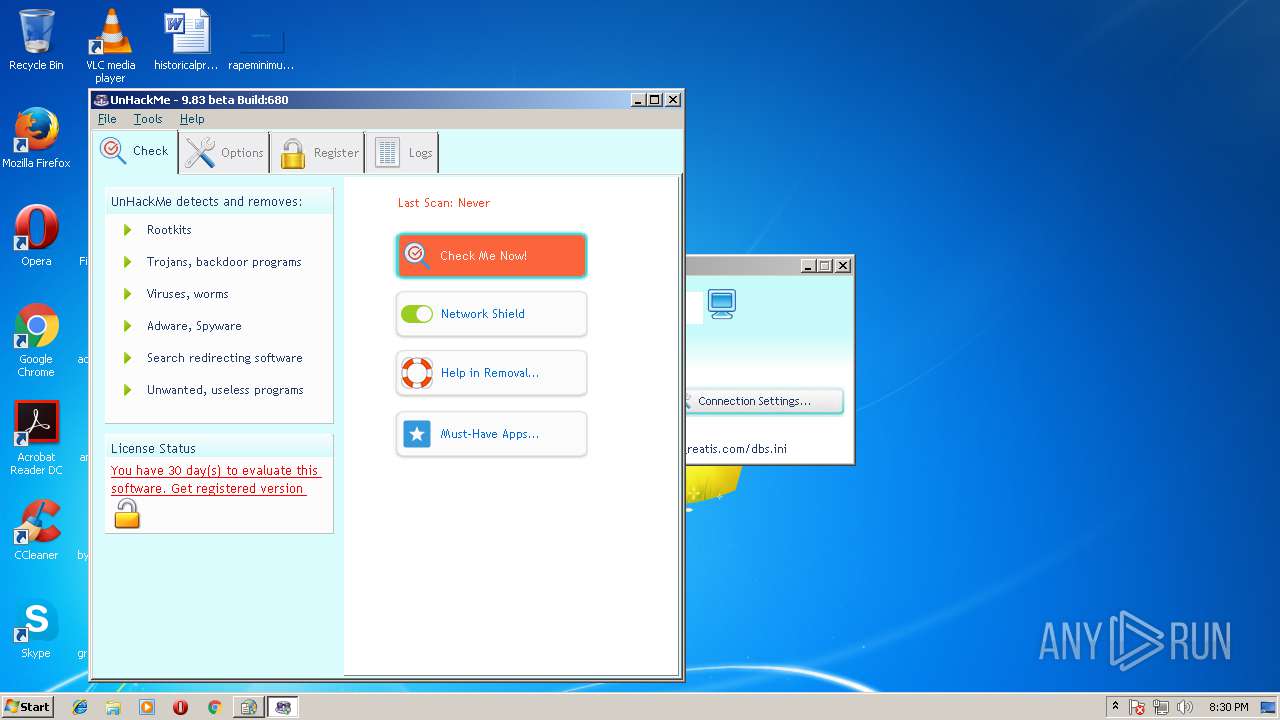
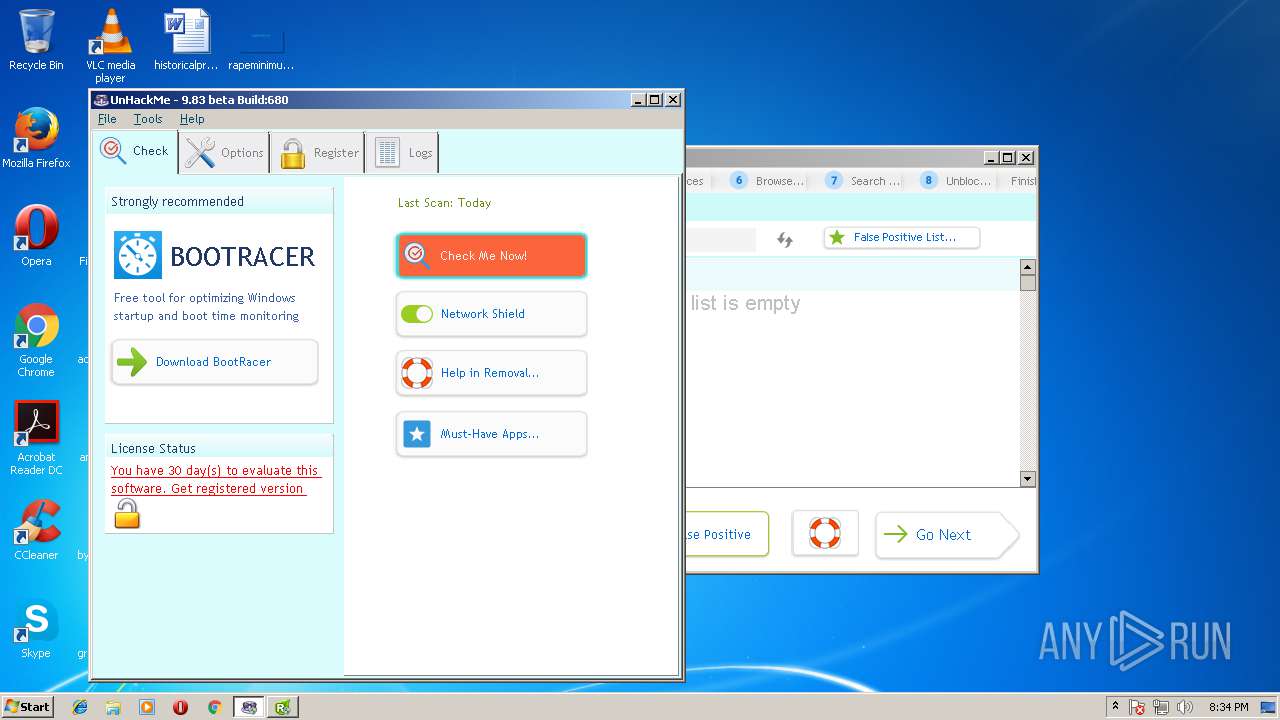
| download: | unhackme_setup.exe |
| Full analysis: | https://app.any.run/tasks/1f9b7fa5-d7fa-4faf-ae12-8d077c8d8ee1 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | May 11, 2018, 19:29:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4BC27A49A448FBBF04A466D4F0BD5114 |
| SHA1: | C521A434D1CFBEC70DD1A83B1A19917D591D1168 |
| SHA256: | E86D6D2FBBD246A746AAD93F1920648016A60A073198E87513BB5BAD9C6F40E9 |
| SSDEEP: | 393216:stmdMuX4n/gmOQGlT4SFSrm8ZpAnWMYQt+WDzCy:ddMuX4n/mQ64wcRTpMgWyy |
MALICIOUS
Loads the Task Scheduler COM API
- unhackmeschedule.exe (PID: 3104)
- reanimator.exe (PID: 3008)
Application was dropped or rewritten from another process
- reanimator.exe (PID: 1224)
- regruninfo.exe (PID: 3356)
- unhackmeschedule.exe (PID: 3104)
- ShowTrayIcon.exe (PID: 2604)
- Unhackme.exe (PID: 1596)
- reanimator.exe (PID: 3008)
- wu.exe (PID: 2360)
- mozlz4d.exe (PID: 3916)
- regruninfo.exe (PID: 3208)
Application loaded dropped or rewritten executable
- reanimator.exe (PID: 1224)
- reanimator.exe (PID: 3008)
Changes settings of System certificates
- regruninfo.exe (PID: 3356)
- reanimator.exe (PID: 3008)
- regruninfo.exe (PID: 3208)
Actions looks like stealing of personal data
- reanimator.exe (PID: 3008)
Loads the Task Scheduler DLL interface
- reanimator.exe (PID: 3008)
SUSPICIOUS
Executable content was dropped or overwritten
- unhackme_setup.exe (PID: 2624)
- unhackme_setup.tmp (PID: 3876)
- unhackme_setup.exe (PID: 3504)
Dropped object may contain URLs of mainers pools
- unhackme_setup.tmp (PID: 3876)
Modifies the open verb of a shell class
- unhackme_setup.tmp (PID: 3876)
Creates files in the Windows directory
- unhackme_setup.tmp (PID: 3876)
- Unhackme.exe (PID: 1596)
Creates files in the driver directory
- unhackme_setup.tmp (PID: 3876)
- Unhackme.exe (PID: 1596)
Uses NETSH.EXE for network configuration
- unhackme_setup.tmp (PID: 3876)
Creates or modifies windows services
- unhackme_setup.tmp (PID: 3876)
- reanimator.exe (PID: 3008)
Creates files in the program directory
- reanimator.exe (PID: 1224)
- wu.exe (PID: 2360)
- reanimator.exe (PID: 3008)
Creates COM task schedule object
- Unhackme.exe (PID: 1596)
Adds / modifies Windows certificates
- regruninfo.exe (PID: 3356)
- regruninfo.exe (PID: 3208)
- reanimator.exe (PID: 3008)
Low-level read access rights to disk partition
- reanimator.exe (PID: 3008)
Creates files in the user directory
- regruninfo.exe (PID: 3208)
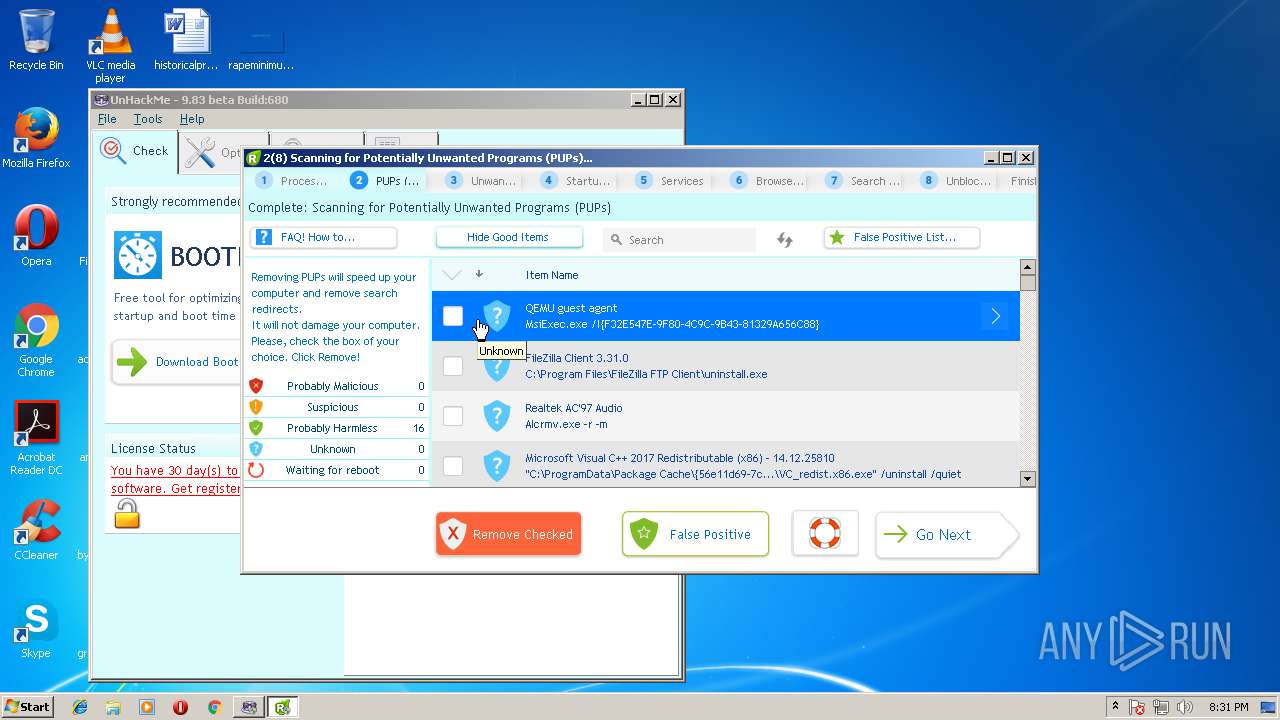
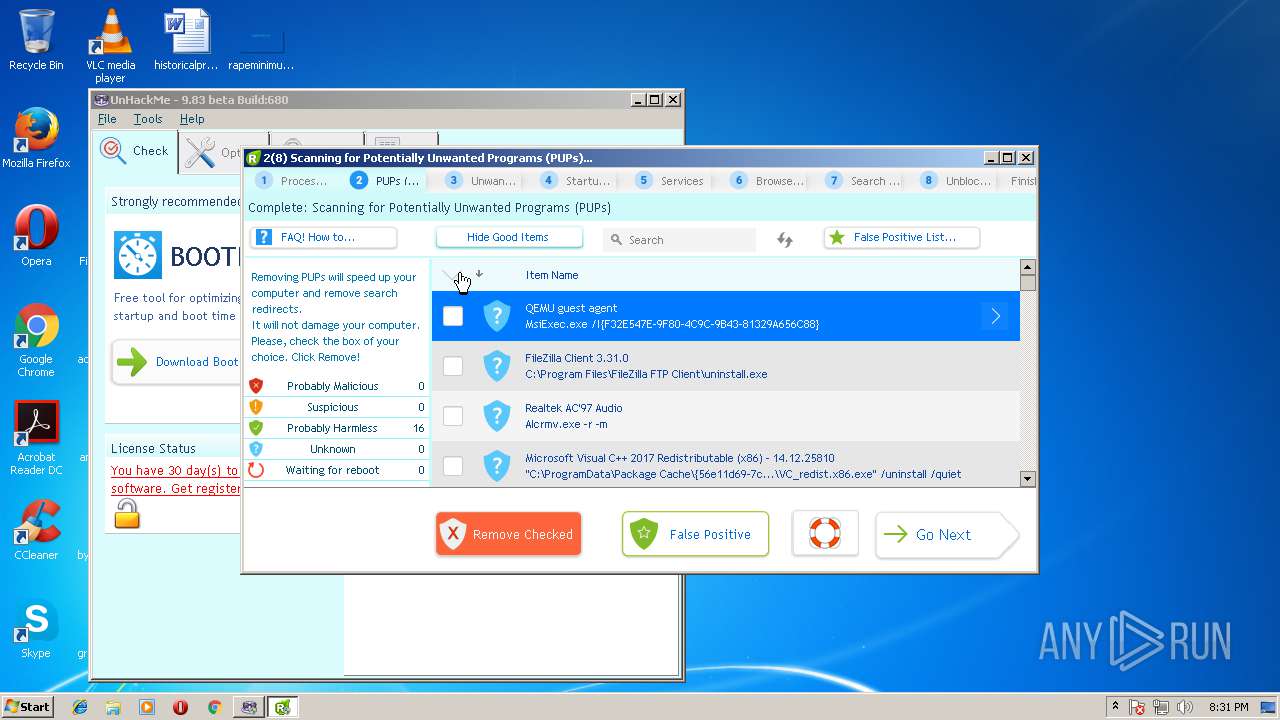
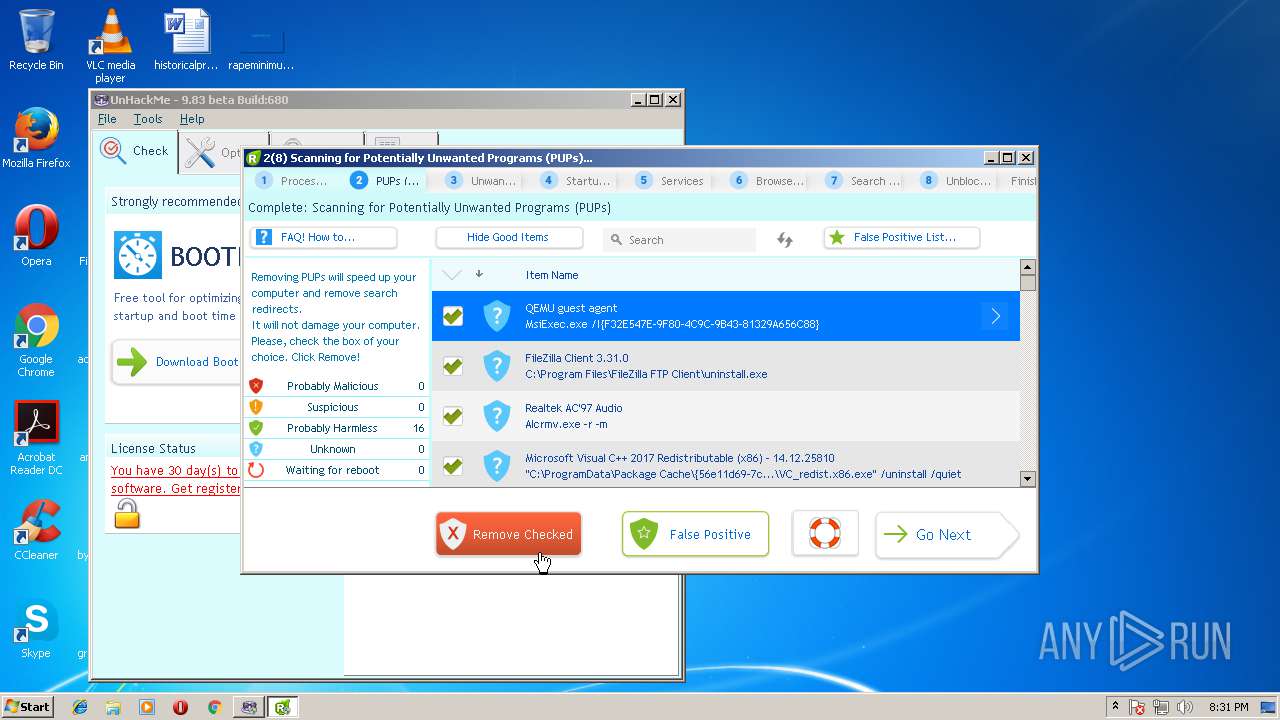
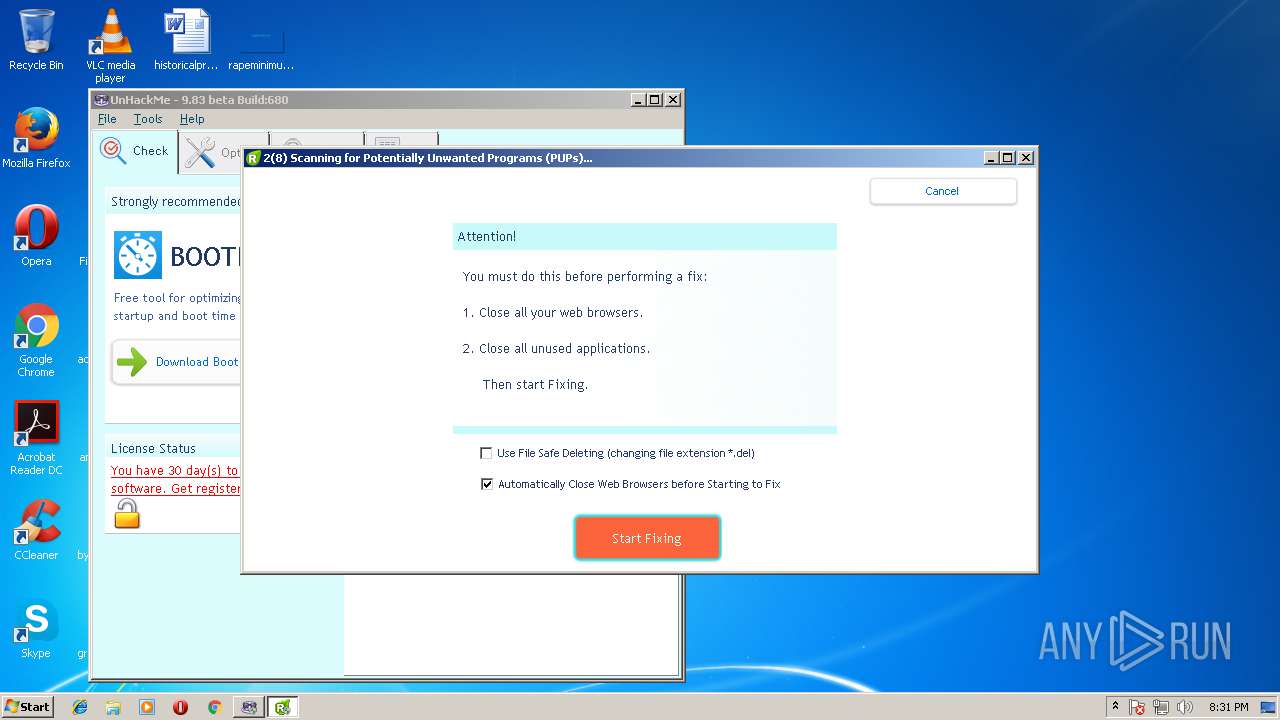
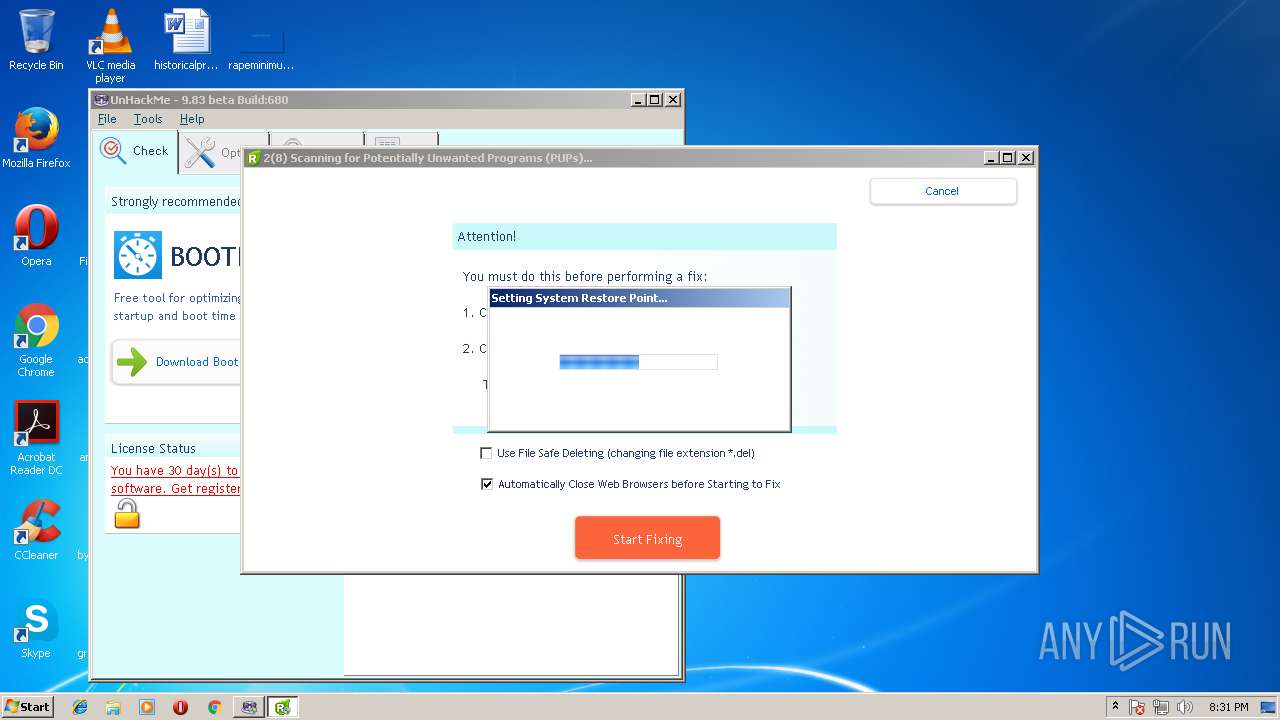
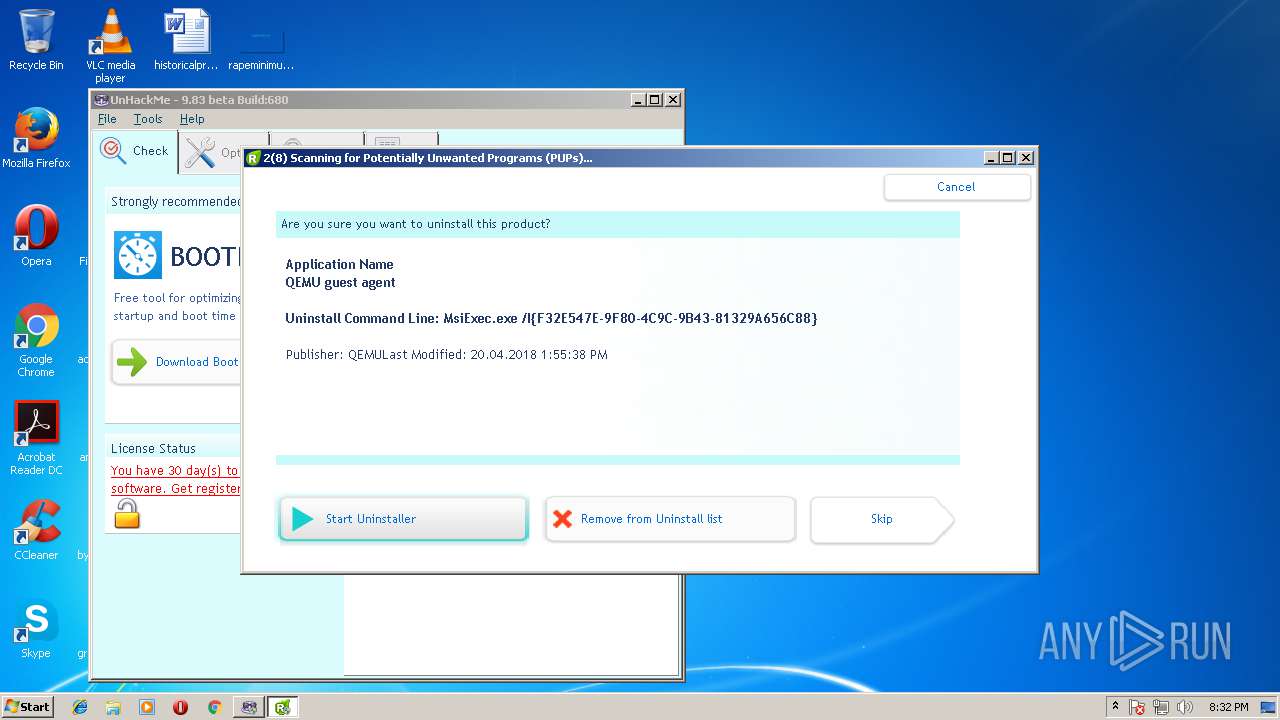
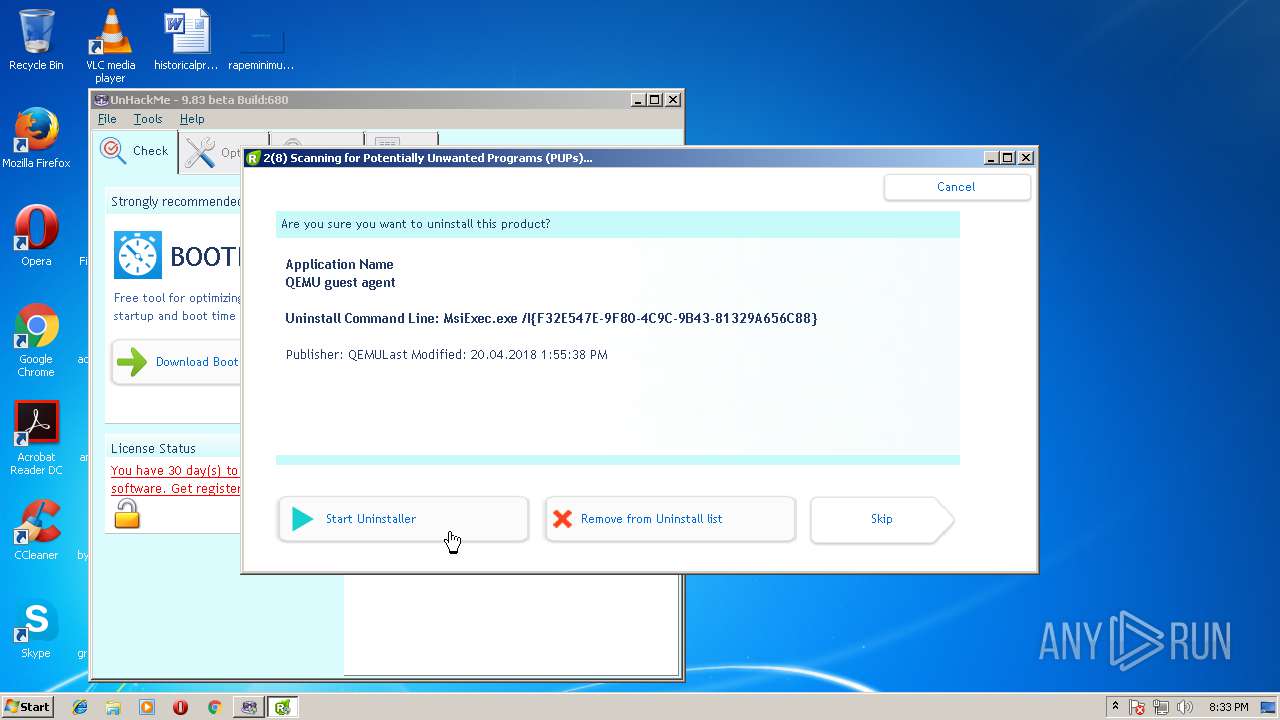
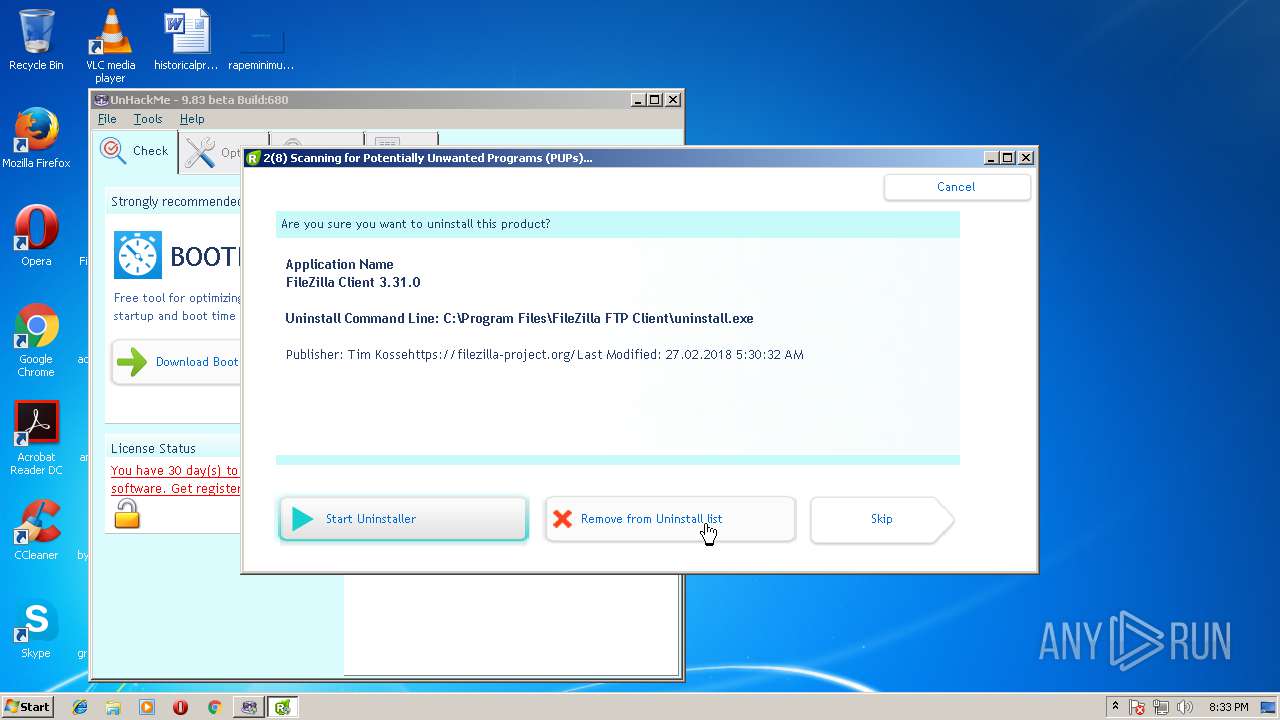
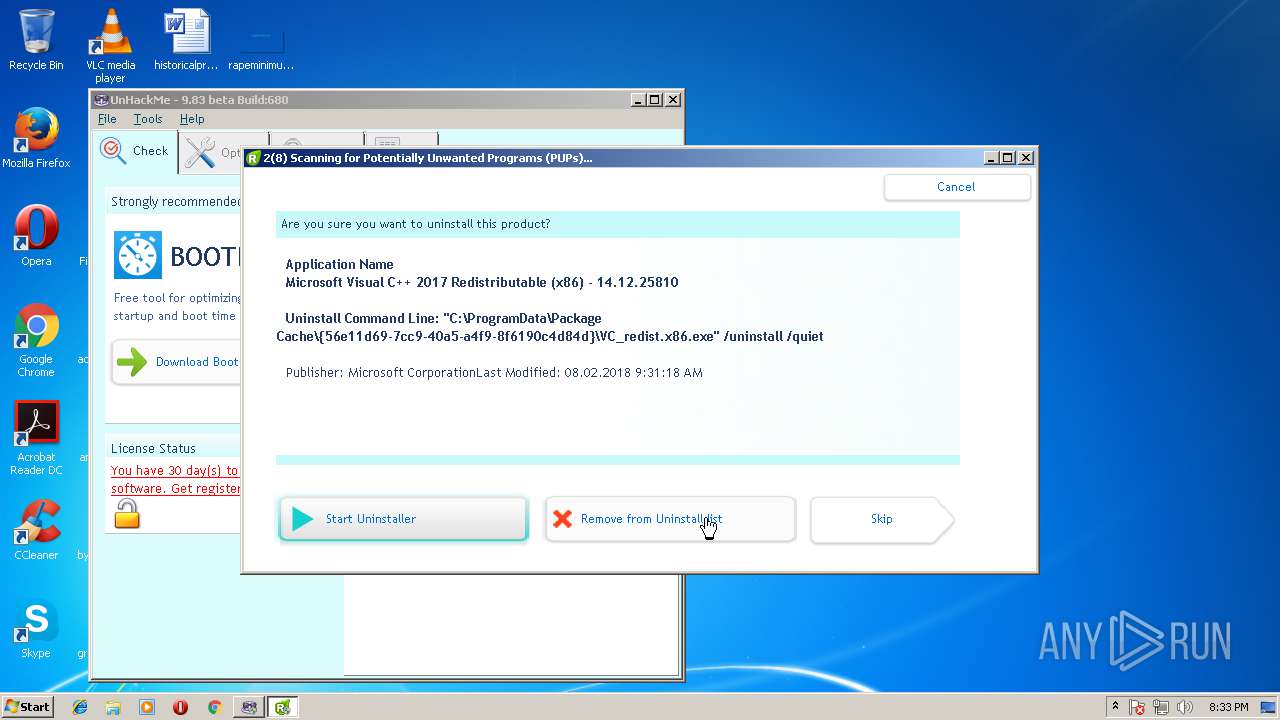
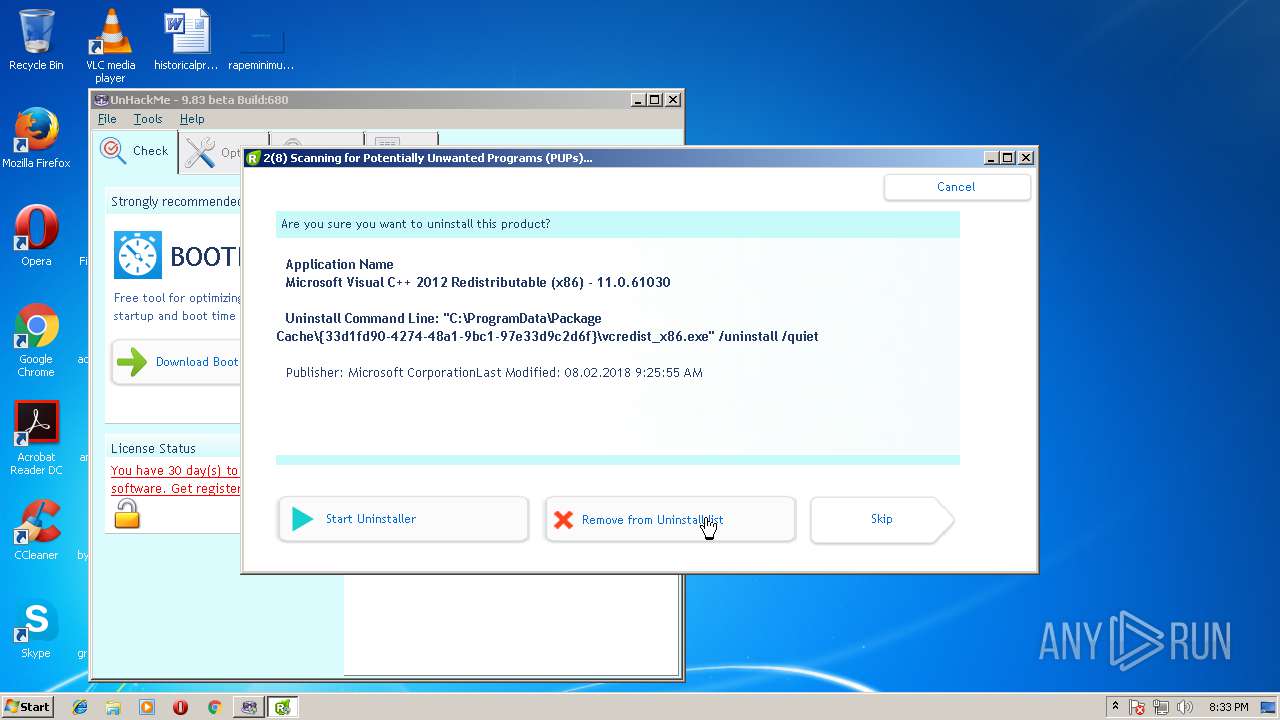
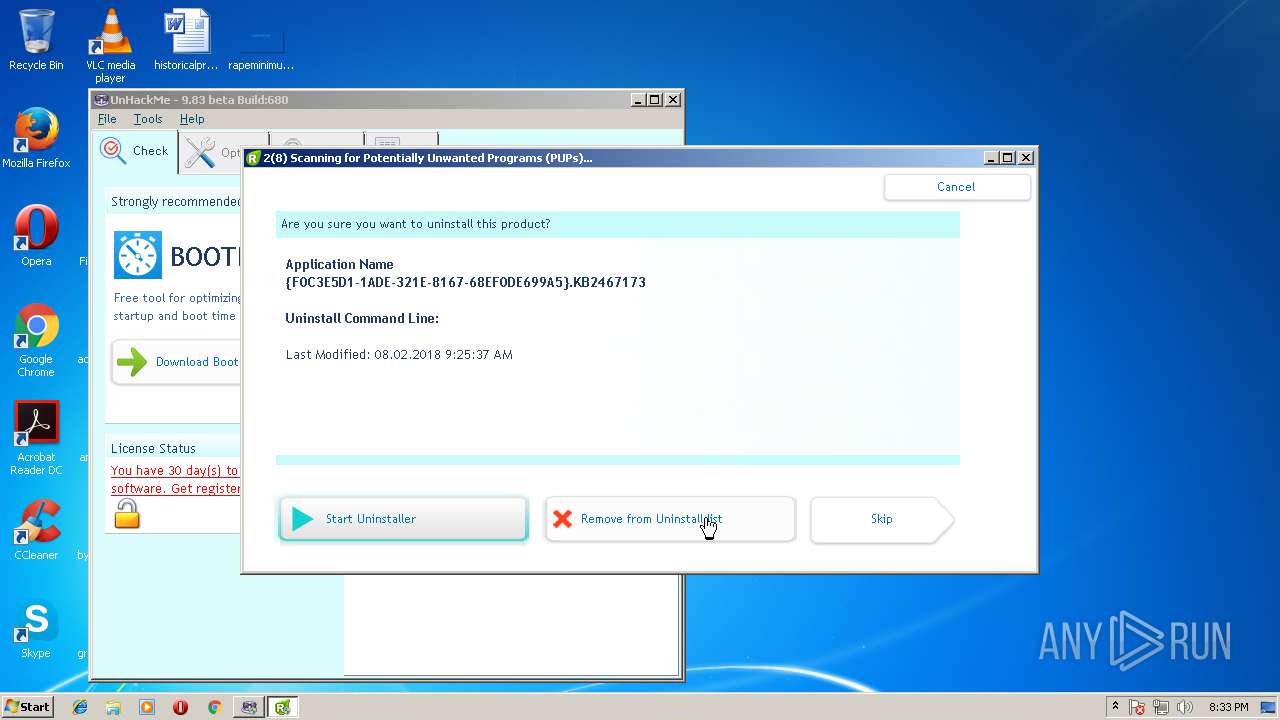
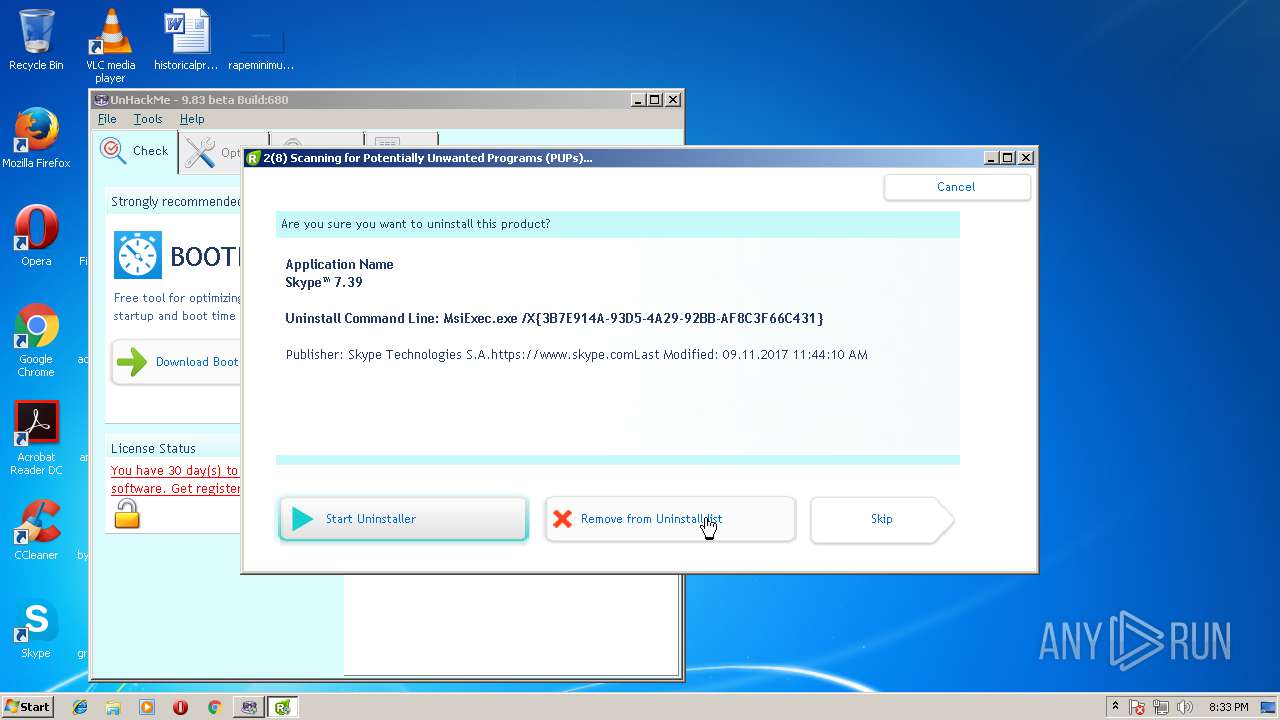
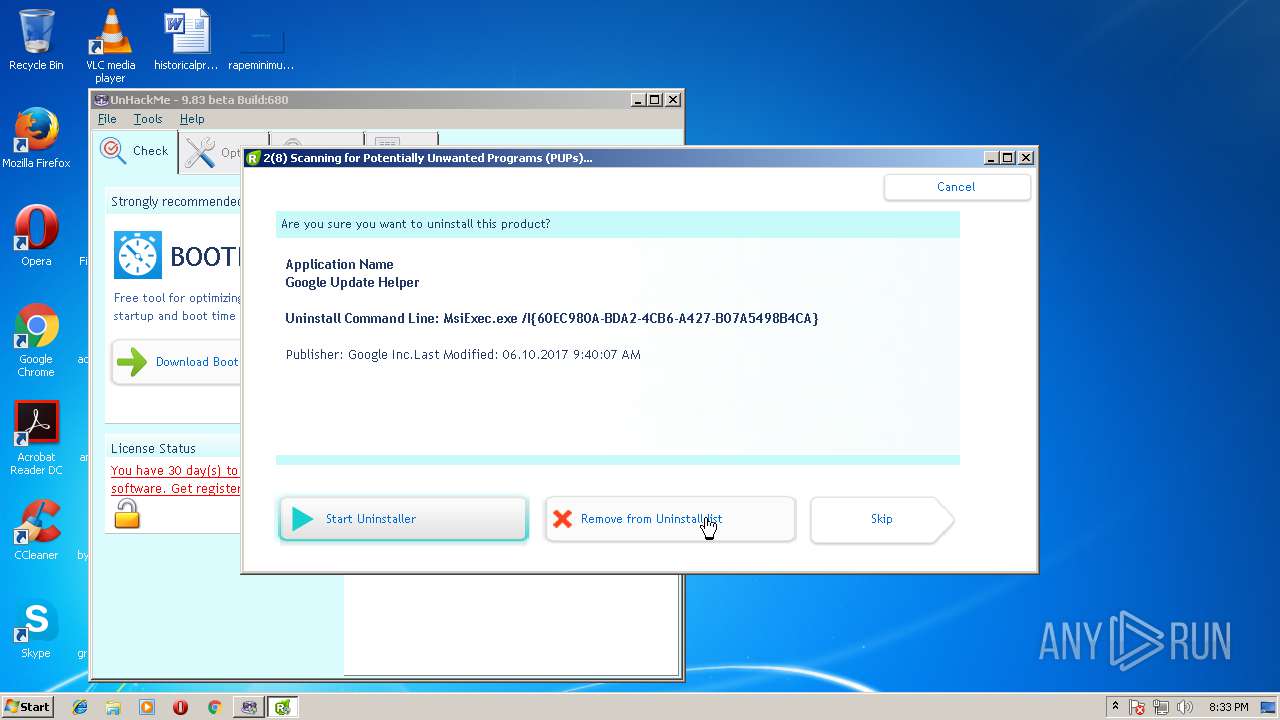
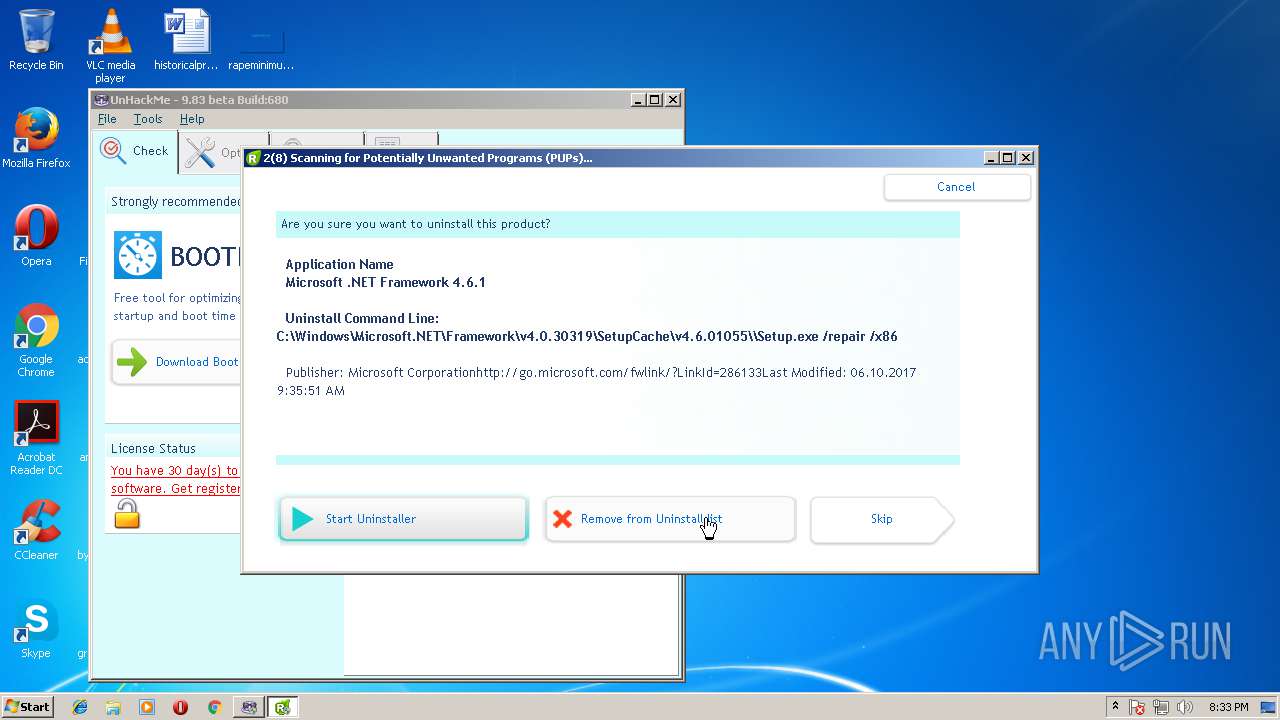
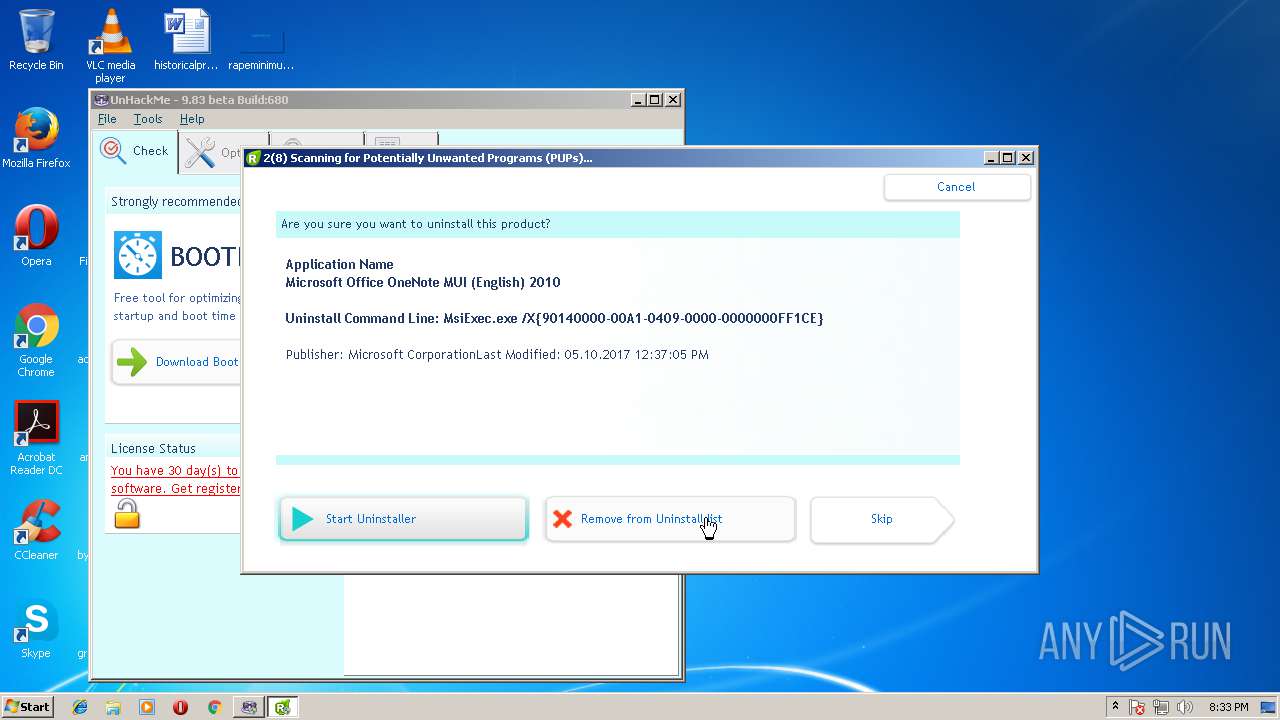
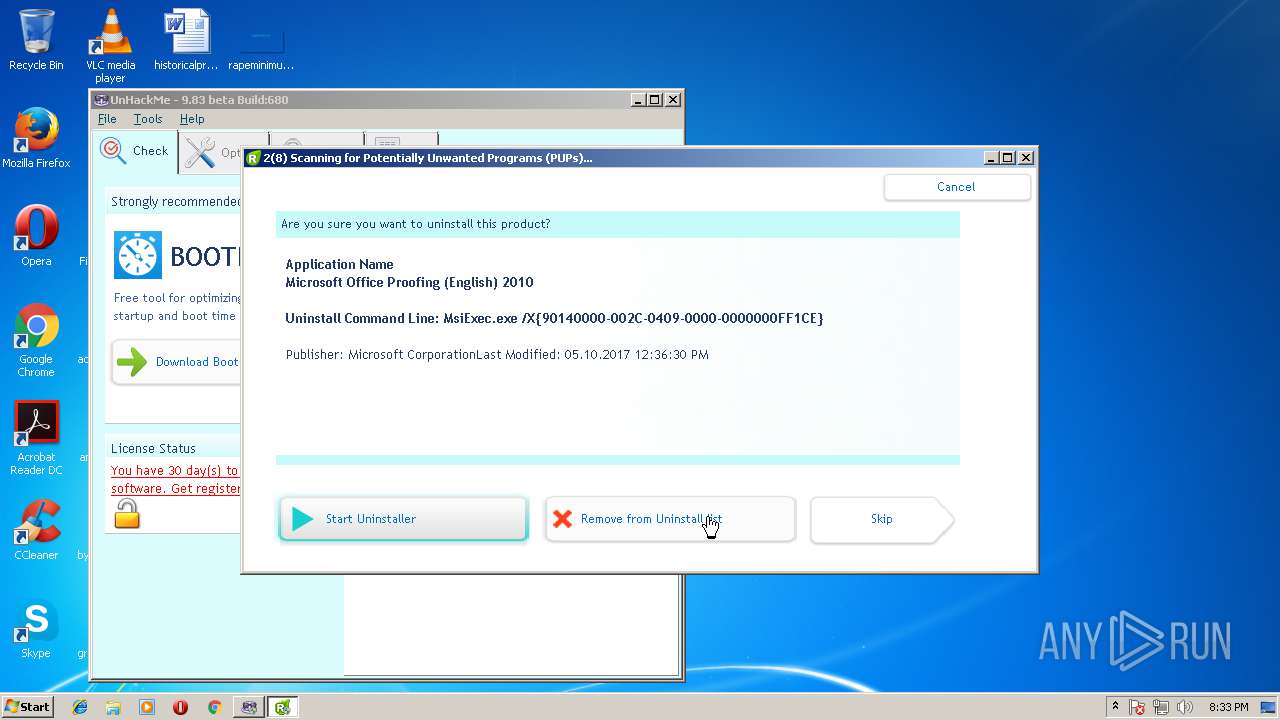
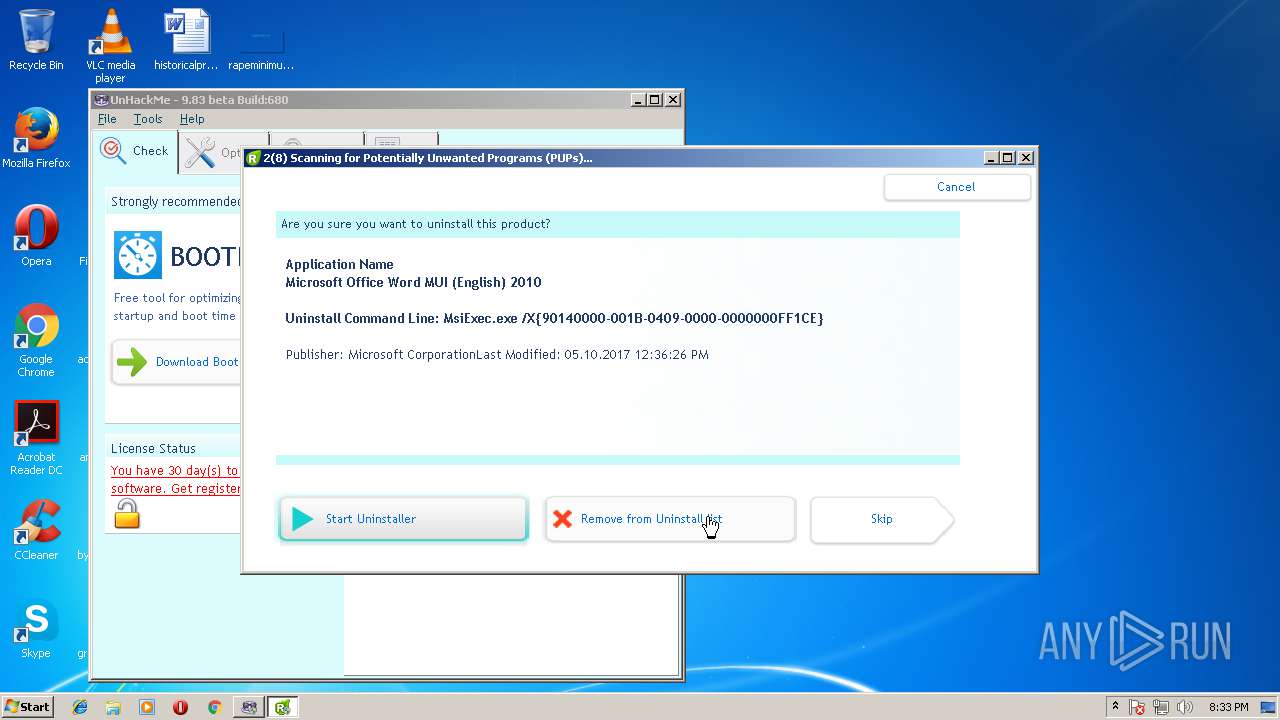
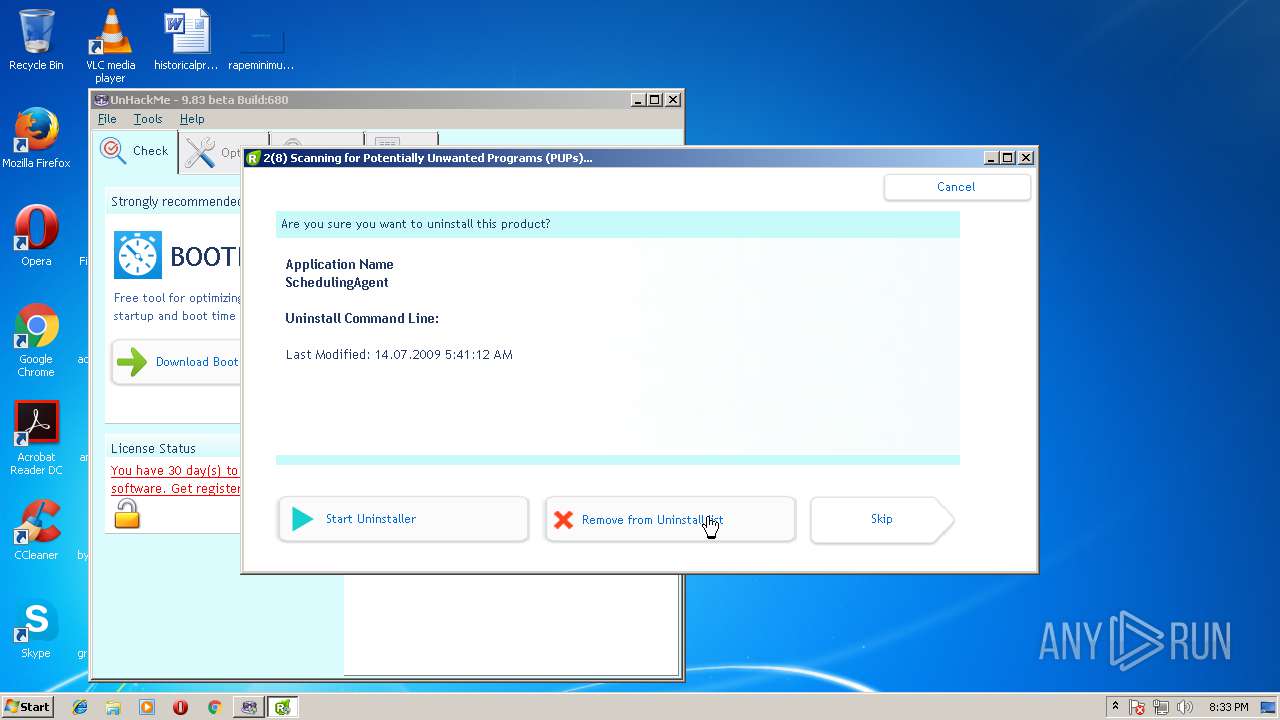
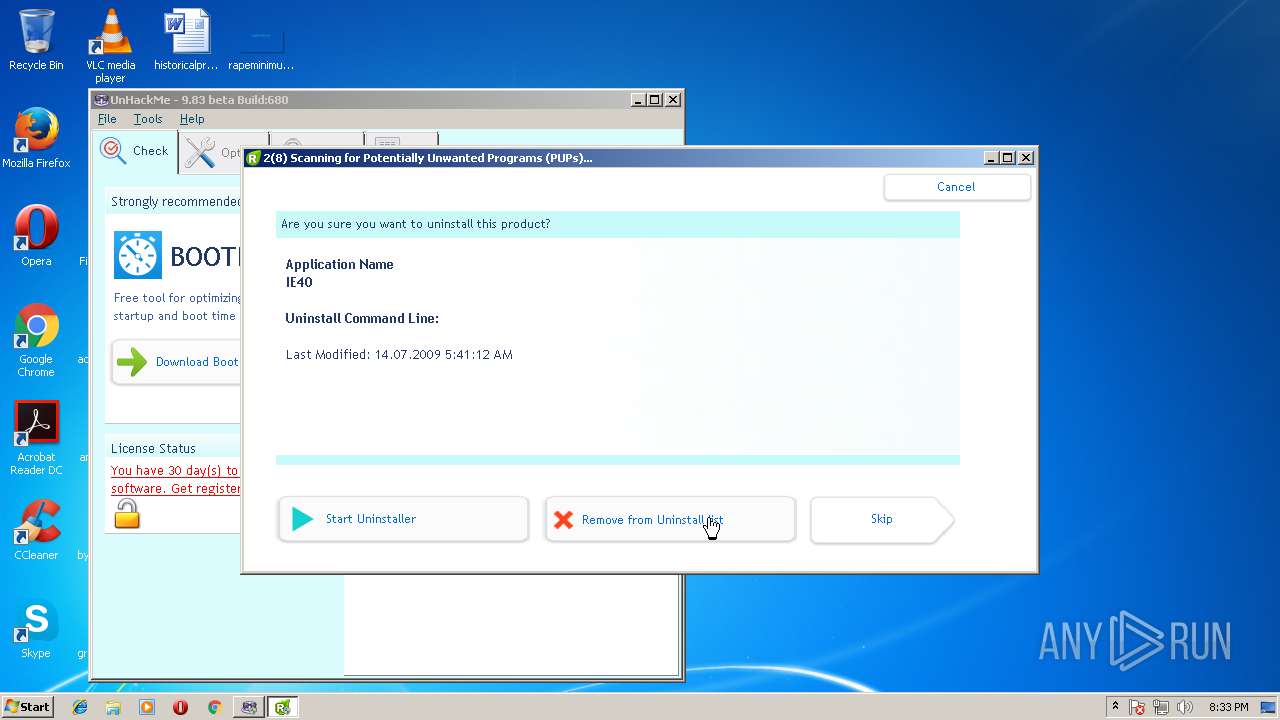
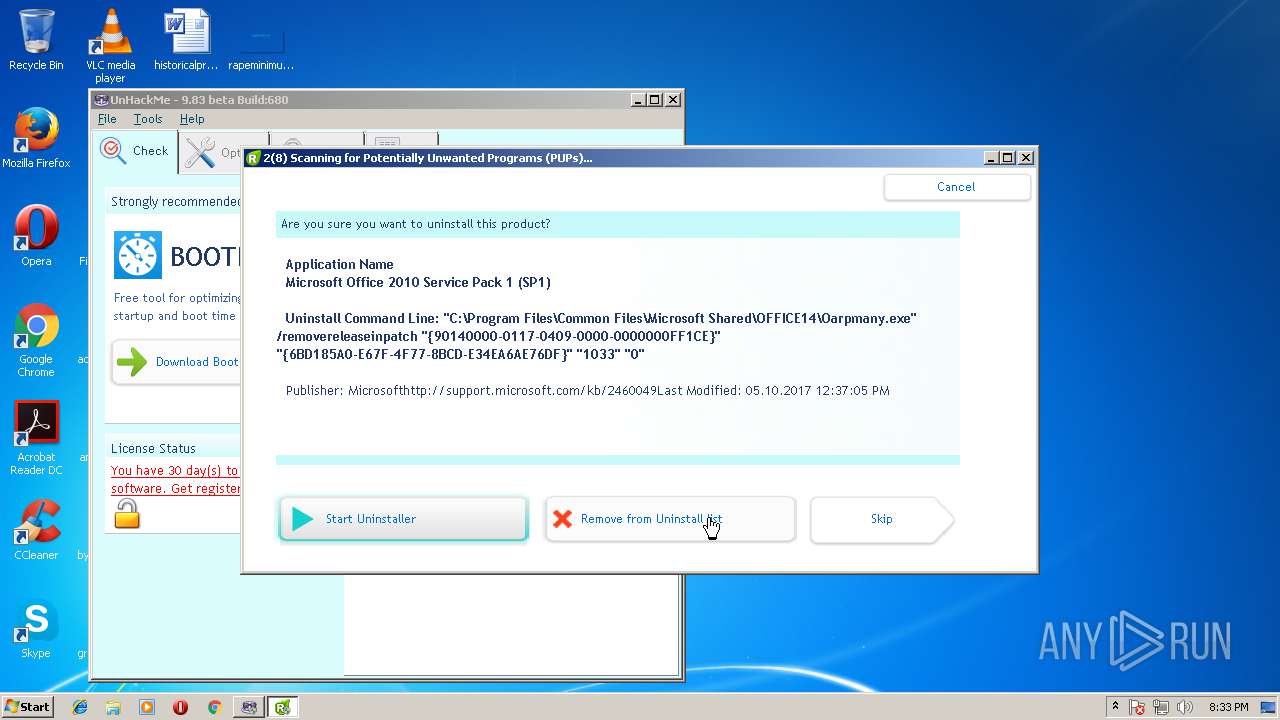
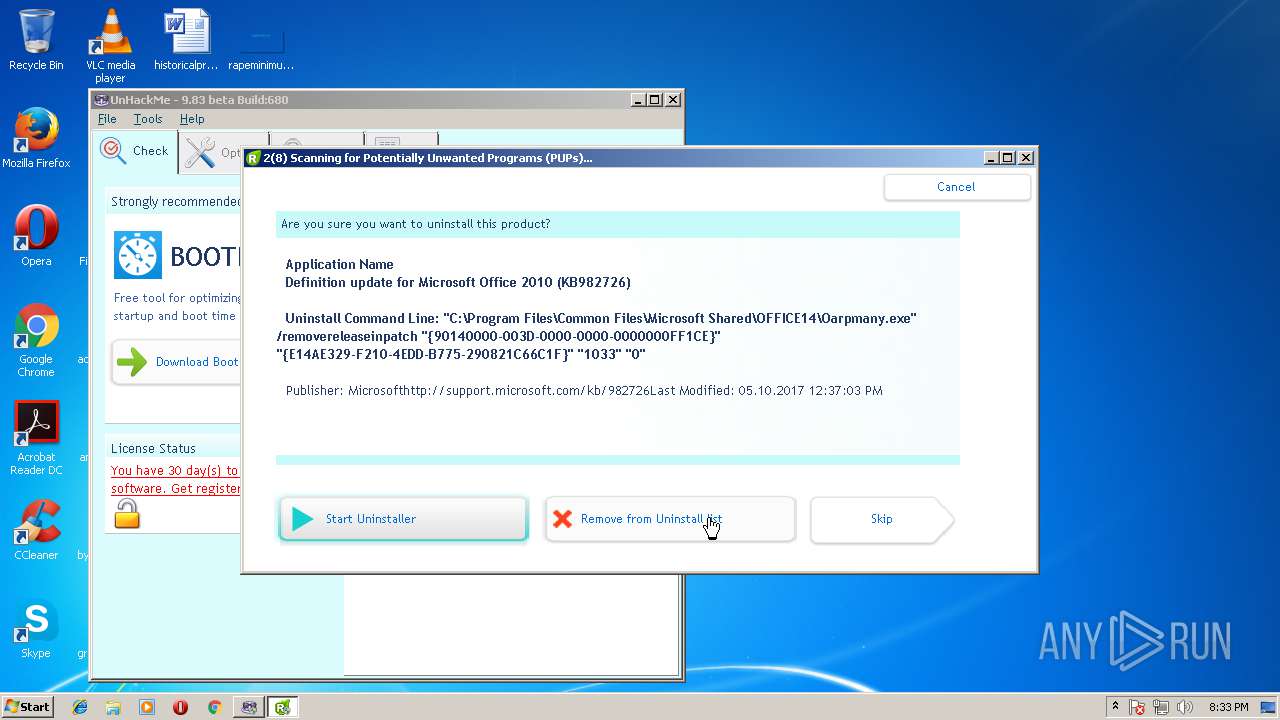
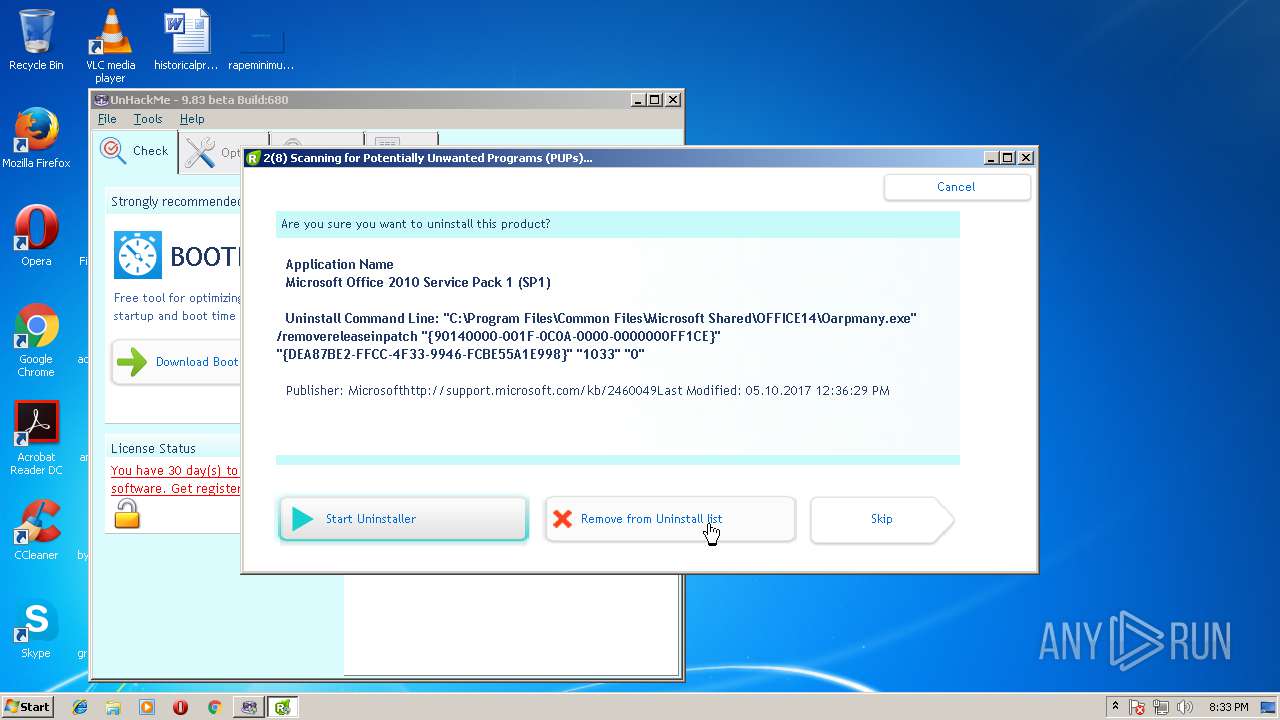
Searches for installed software
- reanimator.exe (PID: 3008)
INFO
Dropped object may contain URL's
- unhackme_setup.exe (PID: 2624)
- unhackme_setup.exe (PID: 3504)
- unhackme_setup.tmp (PID: 3876)
- wu.exe (PID: 2360)
- reanimator.exe (PID: 3008)
- regruninfo.exe (PID: 3356)
- regruninfo.exe (PID: 3208)
Application was dropped or rewritten from another process
- unhackme_setup.tmp (PID: 3740)
- unhackme_setup.tmp (PID: 3876)
Creates files in the program directory
- unhackme_setup.tmp (PID: 3876)
Dropped object may contain Bitcoin addresses
- unhackme_setup.tmp (PID: 3876)
- reanimator.exe (PID: 3008)
- regruninfo.exe (PID: 3208)
Creates a software uninstall entry
- unhackme_setup.tmp (PID: 3876)
Dropped object may contain TOR URL's
- unhackme_setup.tmp (PID: 3876)
- Unhackme.exe (PID: 1596)
- reanimator.exe (PID: 3008)
Application loaded dropped or rewritten executable
- unhackme_setup.tmp (PID: 3876)
Reads settings of System Certificates
- reanimator.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (91.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (3.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.80.0.680 |
| ProductVersionNumber: | 9.80.0.680 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Greatis Software, LLC. |
| FileDescription: | UnHackMe Setup |
| FileVersion: | 9.80.0.680 |
| LegalCopyright: | |
| ProductName: | UnHackMe |
| ProductVersion: | 9.80.0.680 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Greatis Software, LLC. |
| FileDescription: | UnHackMe Setup |
| FileVersion: | 9.80.0.680 |
| LegalCopyright: | - |
| ProductName: | UnHackMe |
| ProductVersion: | 9.80.0.680 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63177 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75182 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.56123 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11919 | 1512 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
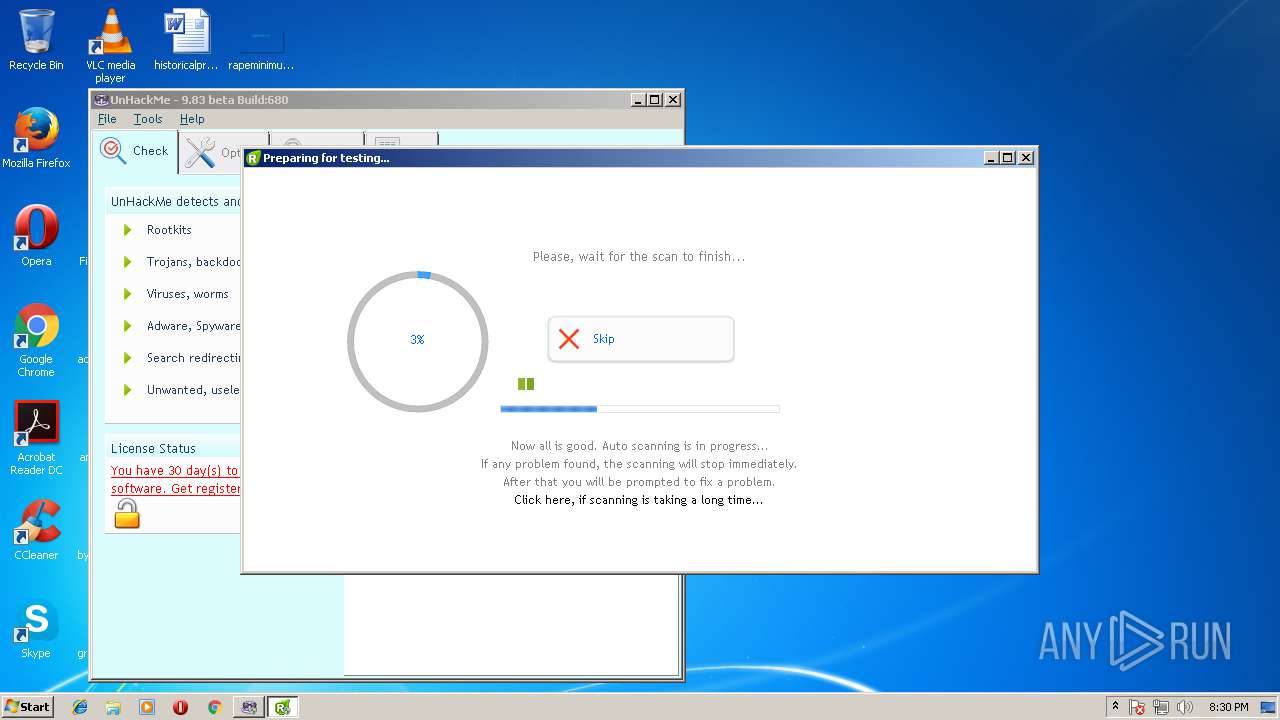
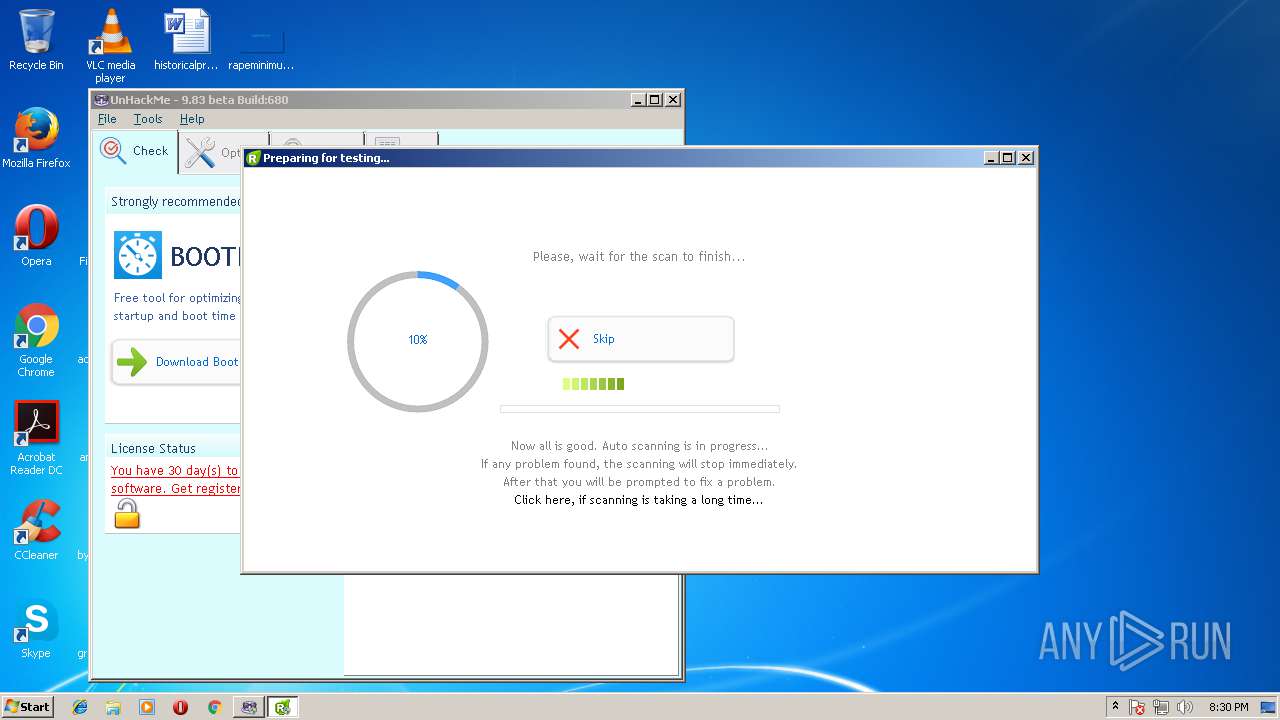
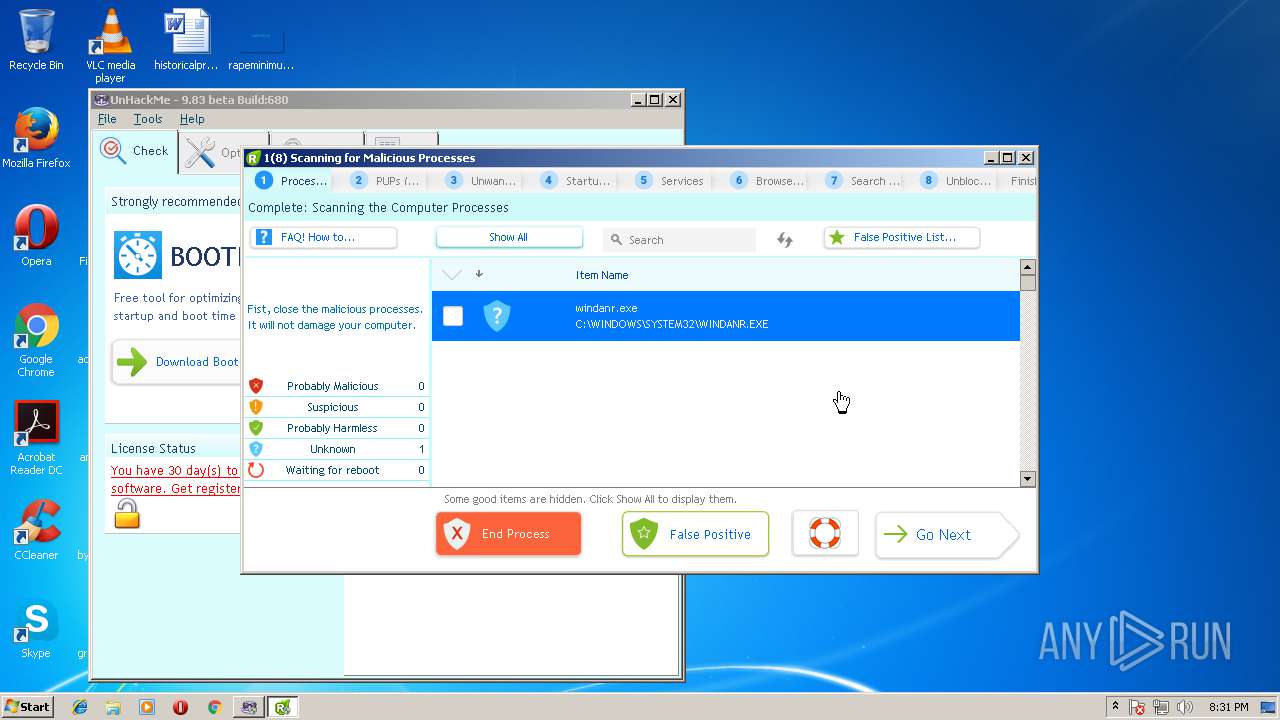
Total processes
62
Monitored processes
16
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1224 | "C:\Program Files\UnHackMe\reanimator.exe" /c | C:\Program Files\UnHackMe\reanimator.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: RegRun Start Control Exit code: 0 Version: 9.80.0.680 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\UnHackMe\Unhackme.exe" | C:\Program Files\UnHackMe\Unhackme.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: Detects and removes rootkits Exit code: 0 Version: 9.80.0.680 Modules
| |||||||||||||||
| 2136 | "netsh.exe" firewall add allowedprogram program="C:\Program Files\UnHackMe\regruninfo.exe" name="UnHackMe Info" mode=ENABLE profile=CURRENT | C:\Windows\system32\netsh.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Program Files\UnHackMe\wu.exe" http://greatis.com/dbs.ini /r /i | C:\Program Files\UnHackMe\wu.exe | reanimator.exe | ||||||||||||
User: admin Company: Greais Software Integrity Level: HIGH Description: Web Update component Exit code: 0 Version: 9.40.0.2018 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\UnHackMe\ShowTrayIcon.exe" | C:\Program Files\UnHackMe\ShowTrayIcon.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: MEDIUM Description: Always display UnHackMe tray icon Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2624 | "C:\Users\admin\AppData\Local\Temp\unhackme_setup.exe" | C:\Users\admin\AppData\Local\Temp\unhackme_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Greatis Software, LLC. Integrity Level: MEDIUM Description: UnHackMe Setup Exit code: 0 Version: 9.80.0.680 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\UnHackMe\reanimator.exe" /wiz /full /malw | C:\Program Files\UnHackMe\reanimator.exe | unhackme_setup.tmp | ||||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: RegRun Start Control Exit code: 0 Version: 9.80.0.680 Modules
| |||||||||||||||
| 3104 | "C:\Program Files\UnHackMe\unhackmeschedule.exe" | C:\Program Files\UnHackMe\unhackmeschedule.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: UnHackMe Schedule Creator Exit code: 0 Version: 5, 0, 9, 9 Modules
| |||||||||||||||
| 3208 | "C:\Program Files\UnHackMe\regruninfo.exe" C:\Users\admin\DOCUME~1\RegRun2\regrunlog.txt /hid: "2018-05-11-20:30:41 On-line Multi-Antivirus Scanning...." /mal: C:\Users\admin\DOCUME~1\RegRun2\ | C:\Program Files\UnHackMe\regruninfo.exe | reanimator.exe | ||||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: Module for retrieving file info from Internet Exit code: 0 Version: 9.70.0.670 Modules
| |||||||||||||||
| 3356 | "C:\Program Files\UnHackMe\regruninfo.exe" /postins | C:\Program Files\UnHackMe\regruninfo.exe | unhackme_setup.tmp | ||||||||||||
User: admin Company: Greatis Software Integrity Level: HIGH Description: Module for retrieving file info from Internet Exit code: 0 Version: 9.70.0.670 Modules
| |||||||||||||||
Total events
2 520
Read events
1 291
Write events
1 132
Delete events
97
Modification events
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 240F00007054C0765EE9D301 | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 50CA2902107ABDB5B72EFB2E03568428B72418CCC617526F111709CAE4FEC506 | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\UnHackMe\Unhackme.exe | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: C99C1A12992AADCA0C7A5CE3A75D3E10442A8F770C780D1C04EA40ACF8D4262B | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Greatis\Unhackme |
| Operation: | write | Name: | @Name |
Value: UnHackMe | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Greatis\Unhackme |
| Operation: | write | Name: | @Version |
Value: 9.80.0.680 | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Greatis\Reanimator |
| Operation: | write | Name: | @Version |
Value: 9.80.0.680 | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Greatis\Reanimator |
| Operation: | write | Name: | @Name |
Value: Reanimator | |||
| (PID) Process: | (3876) unhackme_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Greatis\Unhackme |
| Operation: | write | Name: | AutoStart |
Value: 1 | |||
Executable files
21
Suspicious files
84
Text files
222
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-NUSFT.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-LLK49.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-90T5B.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-5SGIT.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-L6OVV.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-1CFFI.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-QR64P.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\greatis.rdb | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-AEUJ4.tmp | — | |
MD5:— | SHA256:— | |||
| 3876 | unhackme_setup.tmp | C:\Program Files\UnHackMe\is-PH4G0.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
22
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3356 | regruninfo.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.4 Kb | whitelisted |
2360 | wu.exe | GET | 200 | 208.76.245.34:80 | http://greatis.com/dbs.ini | US | text | 386 b | whitelisted |
3208 | regruninfo.exe | GET | 200 | 23.37.43.27:80 | http://g2.symcb.com/MEQwQjBAMD4wPDAJBgUrDgMCGgUABBSxtDkXkBa3l3lQEfFgudSiPNvt7gQUAPkqw0GRtsnCuD5V8sCXEROgByACAwI6cQ%3D%3D | NL | der | 1.35 Kb | whitelisted |
3008 | reanimator.exe | GET | 200 | 23.37.43.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | NL | der | 1.71 Kb | whitelisted |
3008 | reanimator.exe | GET | 200 | 23.37.43.27:80 | http://sf.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSqZMG5M8TA9rdzkbCnNwuMAd5VgQUz5mp6nsm9EvJjo%2FX8AUm7%2BPSp50CEFbG0met4H9y7rRgO7%2BEzqU%3D | NL | der | 1.62 Kb | whitelisted |
3208 | regruninfo.exe | GET | 200 | 23.37.43.27:80 | http://gp.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRH4mIoBb%2Bhjdi7K%2FE2J4ZS9L%2FZgAQUl8InUJ7CyewMiDLIfK3ipgFP2m8CEDOGzcWpUIGpwl%2FBX90neyE%3D | NL | der | 1.38 Kb | whitelisted |
3356 | regruninfo.exe | GET | 200 | 52.85.177.41:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3356 | regruninfo.exe | GET | 200 | 52.85.177.18:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3008 | reanimator.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | der | 530 b | whitelisted |
3356 | regruninfo.exe | GET | 200 | 52.85.177.22:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3356 | regruninfo.exe | 52.71.97.206:443 | api.gameanalytics.com | Amazon.com, Inc. | US | unknown |
3356 | regruninfo.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
3356 | regruninfo.exe | 52.85.177.41:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
2360 | wu.exe | 208.76.245.34:80 | greatis.com | Crucial Paradigm | US | malicious |
3356 | regruninfo.exe | 52.85.177.35:80 | ocsp.sca1b.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3356 | regruninfo.exe | 52.85.177.18:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
3008 | reanimator.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3008 | reanimator.exe | 23.37.43.27:80 | ocsp.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
3208 | regruninfo.exe | 23.37.43.27:80 | ocsp.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
3208 | regruninfo.exe | 74.125.34.46:443 | www.virustotal.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.gameanalytics.com |
| suspicious |
greatis.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.verisign.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2360 | wu.exe | A Network Trojan was detected | ET TROJAN Suspicious Malformed Double Accept Header |
2360 | wu.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User-Agent Mozilla/3.0 |