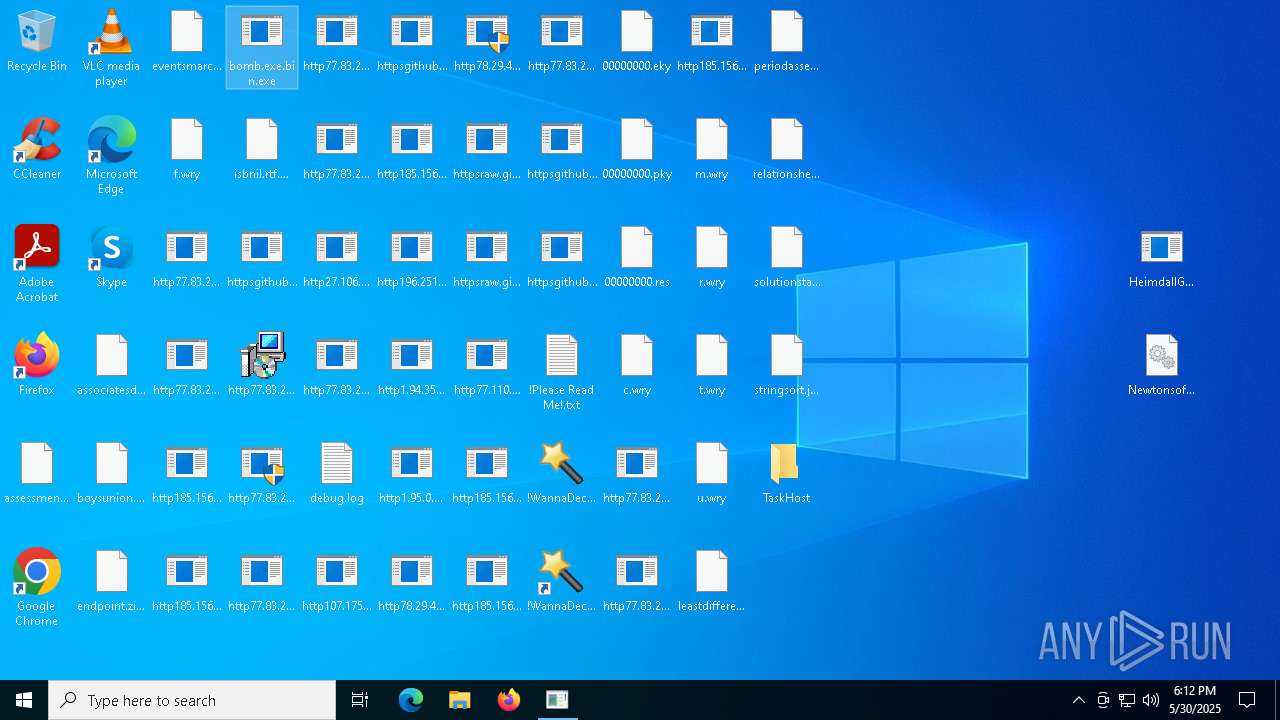
| File name: | bomb.exe.bin |
| Full analysis: | https://app.any.run/tasks/dfb356c0-f2a4-4e83-89ba-f314baabfe8f |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 30, 2025, 18:08:36 |
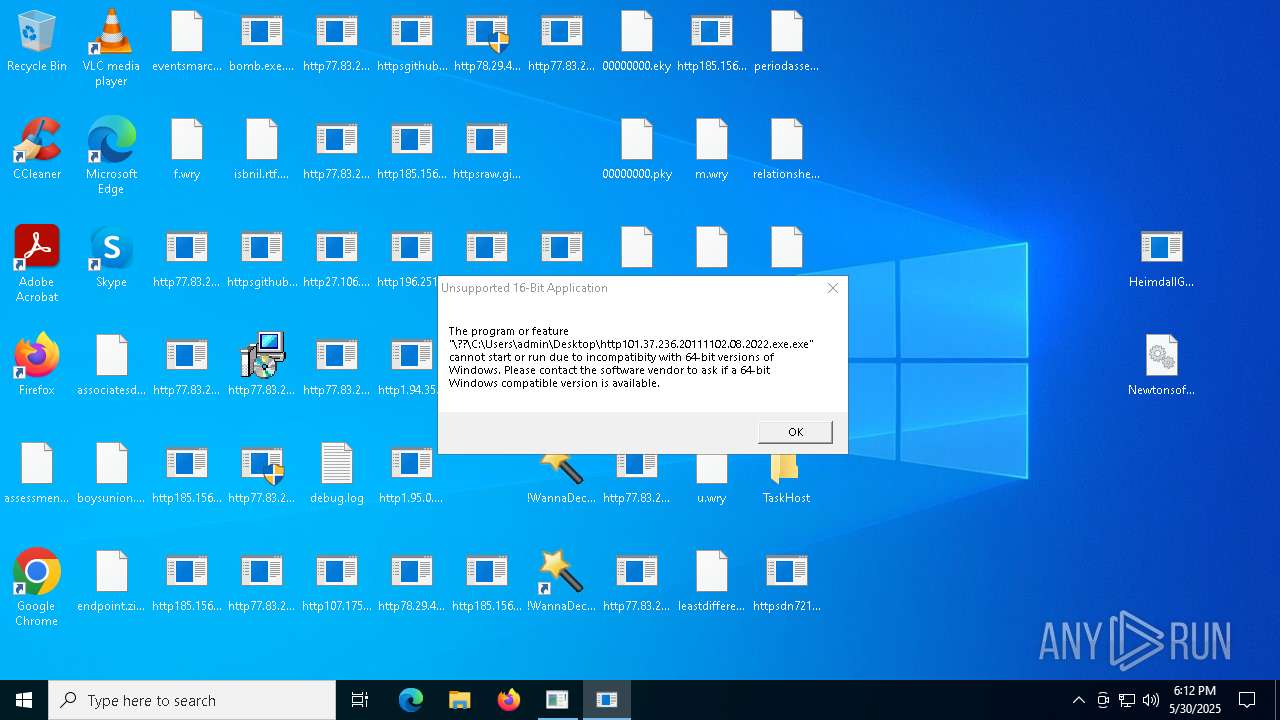
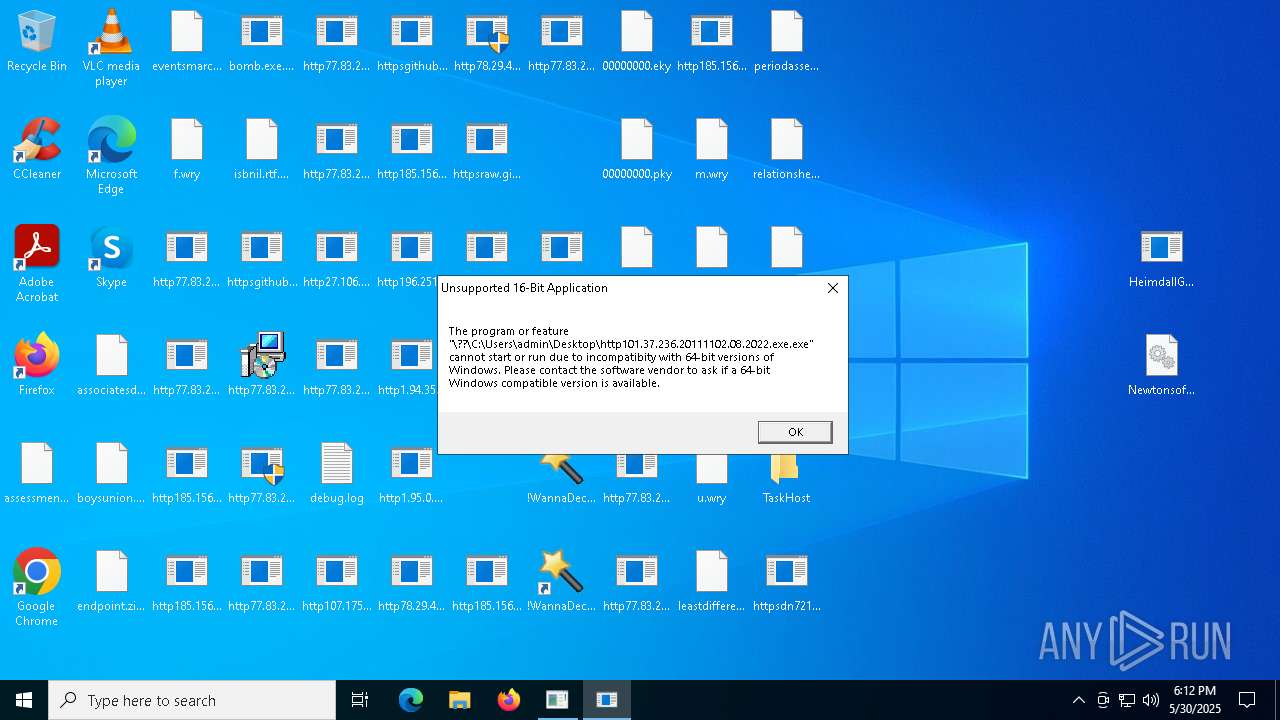
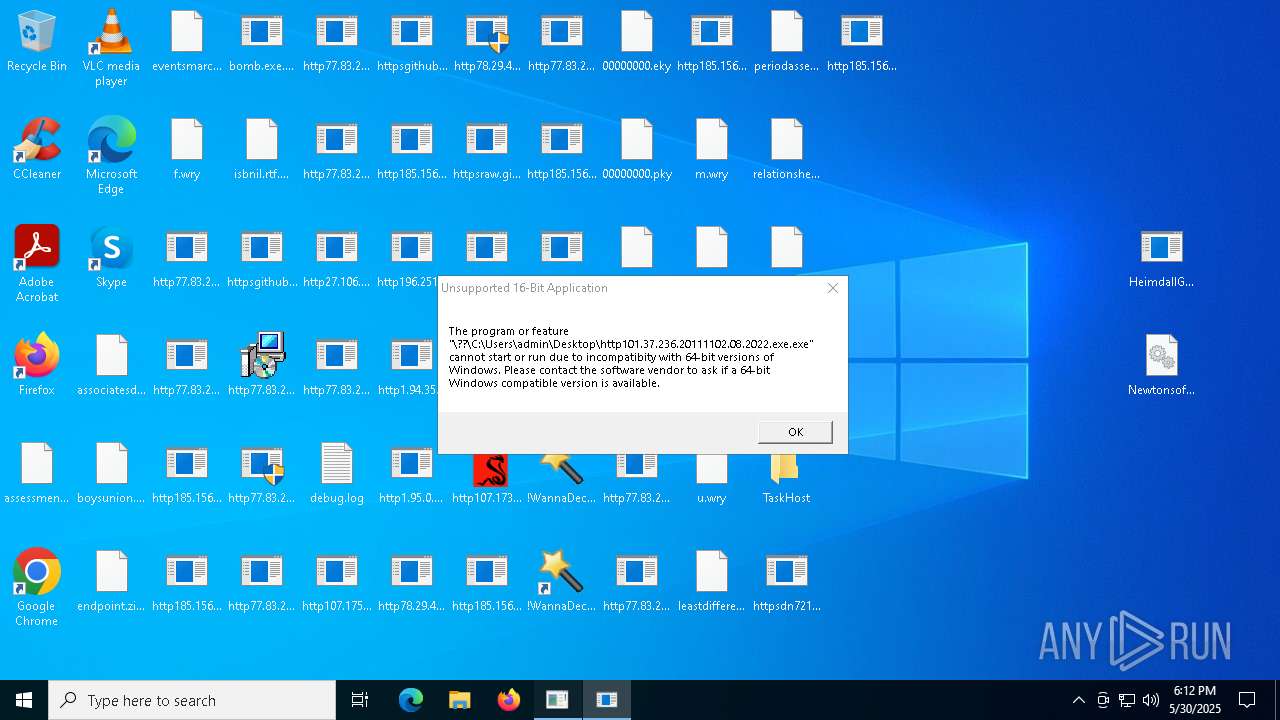
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
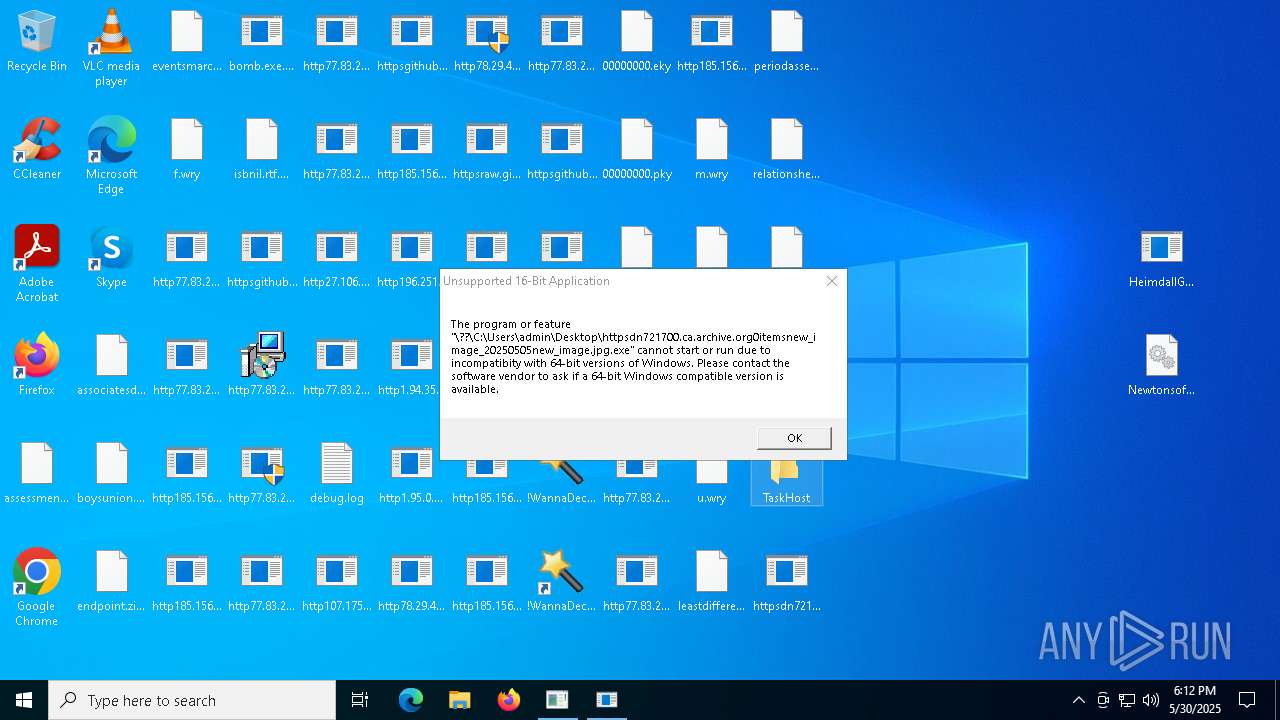
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 21D3C4B6869E61ACB836ECE73DD265DA |
| SHA1: | 4D3AC5EAA89B0ACF14EED249EA774D00CF5AA2C8 |
| SHA256: | E8582DA9A3FA365A425ED0225F7C6681E561061AA0B5285538BAE4B334B97F7C |
| SSDEEP: | 192:UnNv1XCiAzsBhl3y9+QHzdPbw7z1OLU87glpp/bI6J4j0rVIp:ANozz9+qzZYOLU870NJlVI |
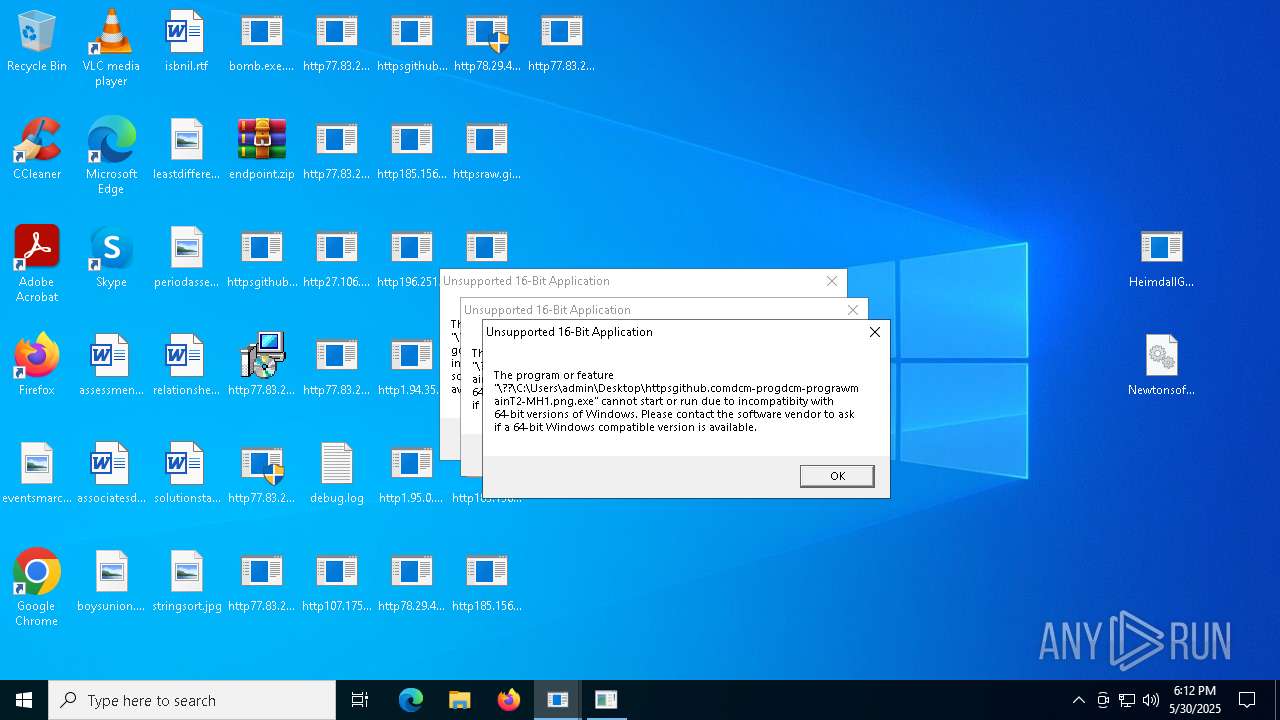
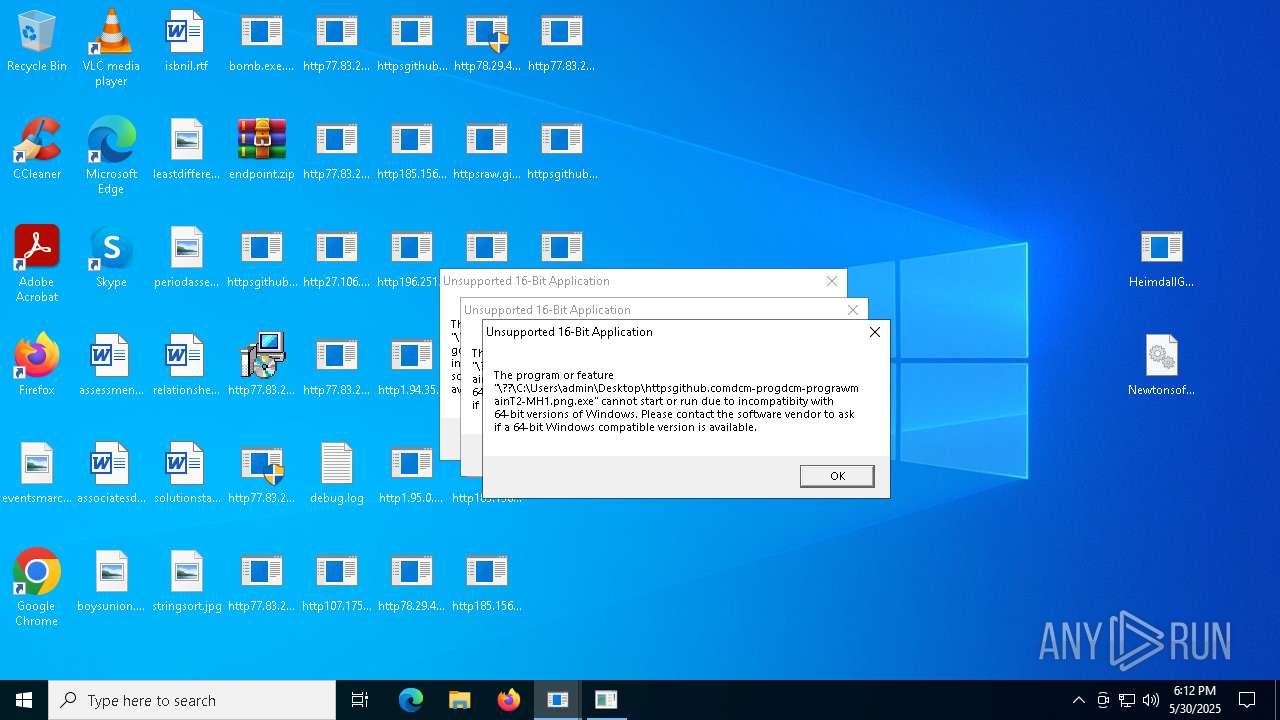
MALICIOUS
HAUSBOMBER has been detected (YARA)
- bomb.exe.bin.exe (PID: 5556)
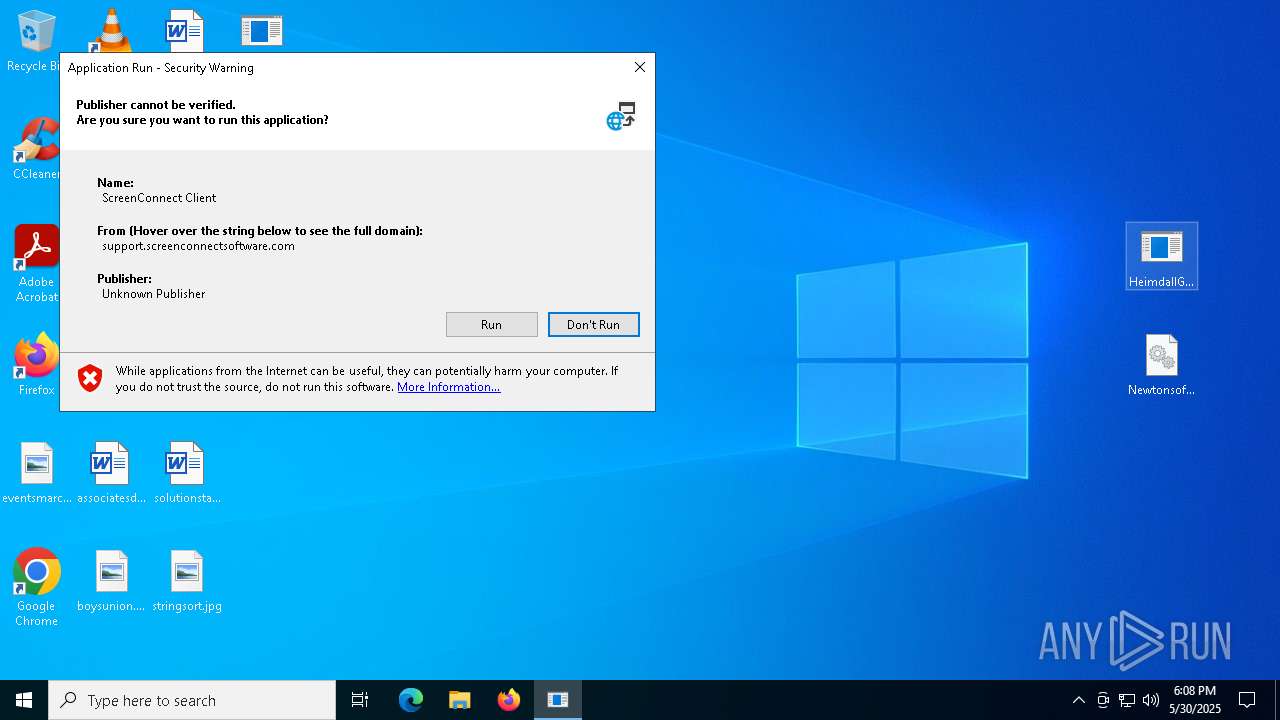
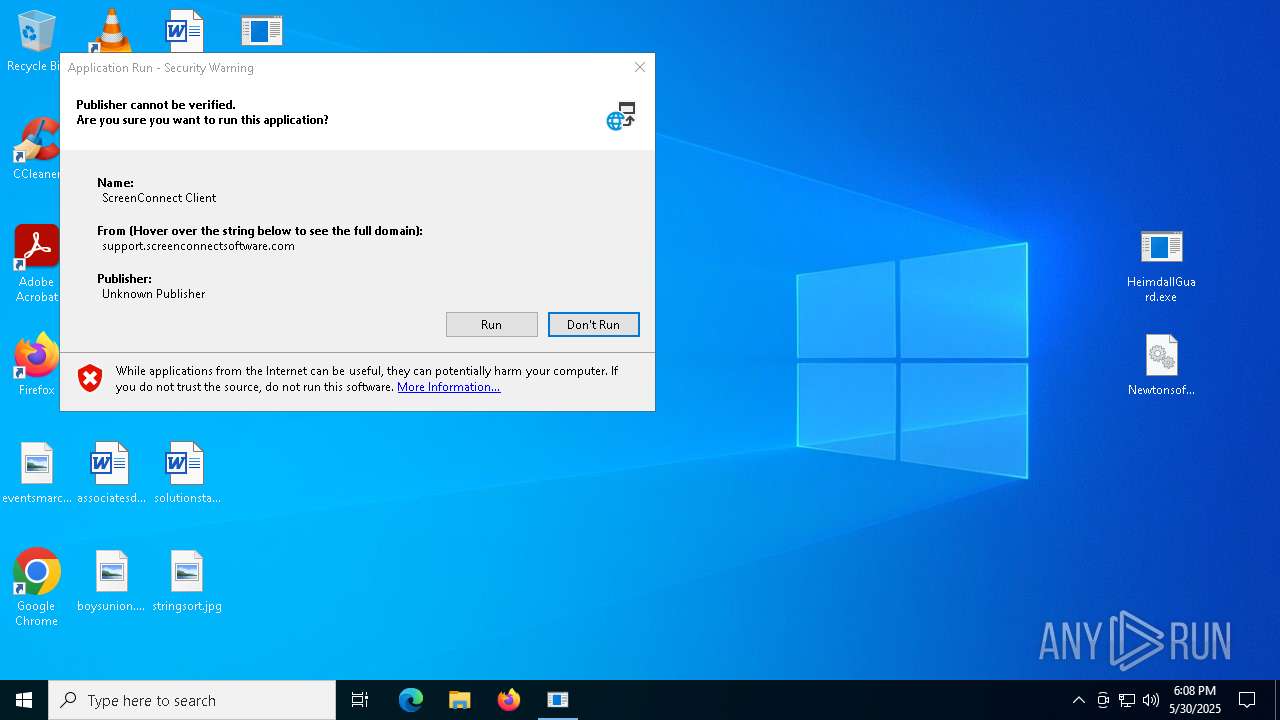
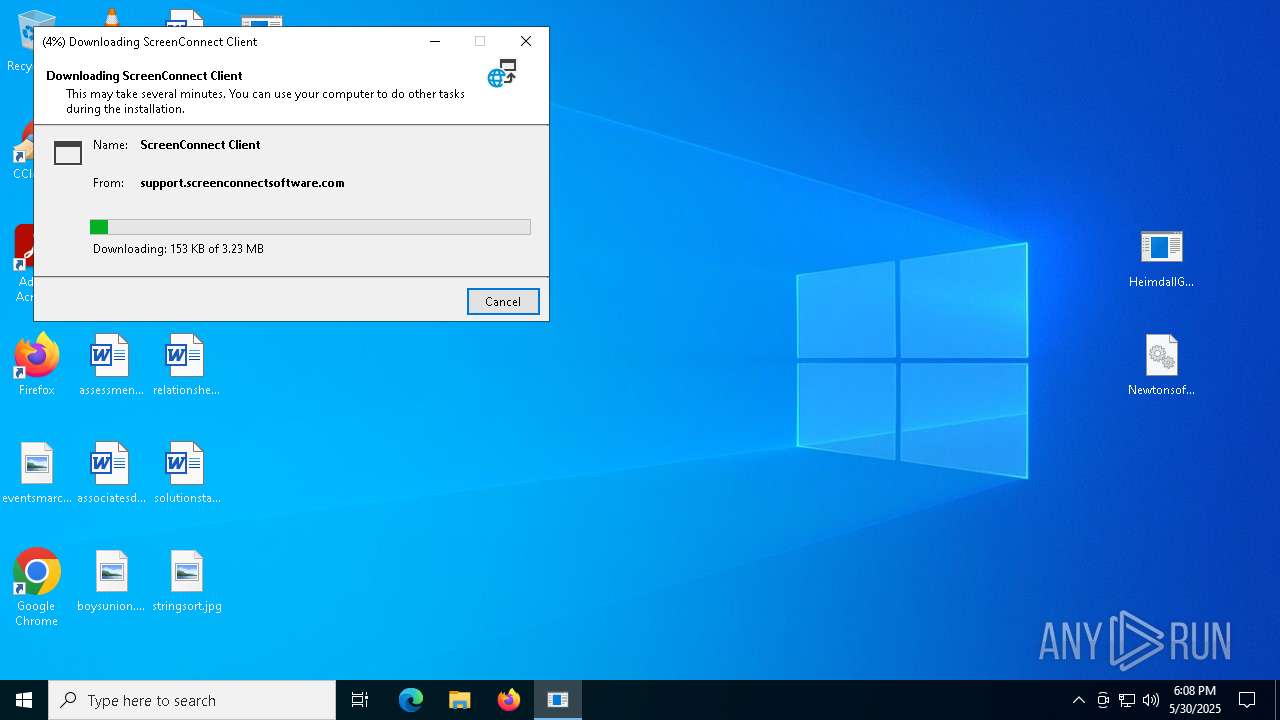
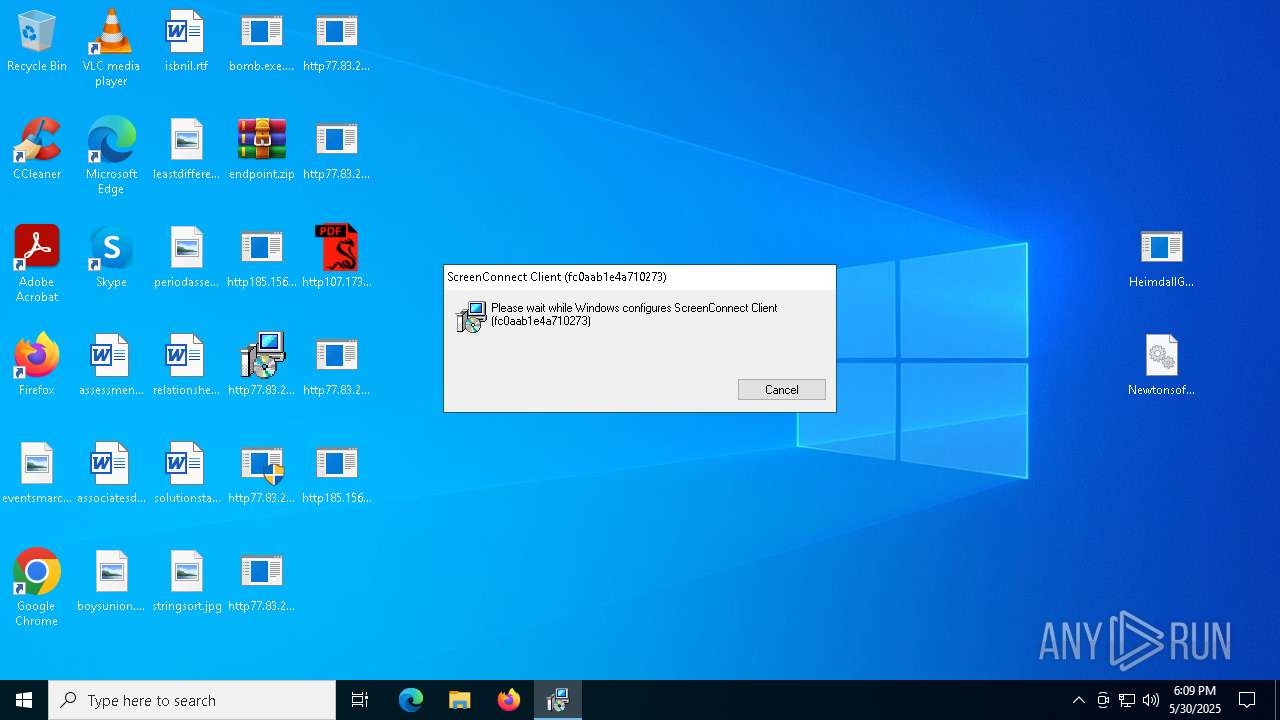
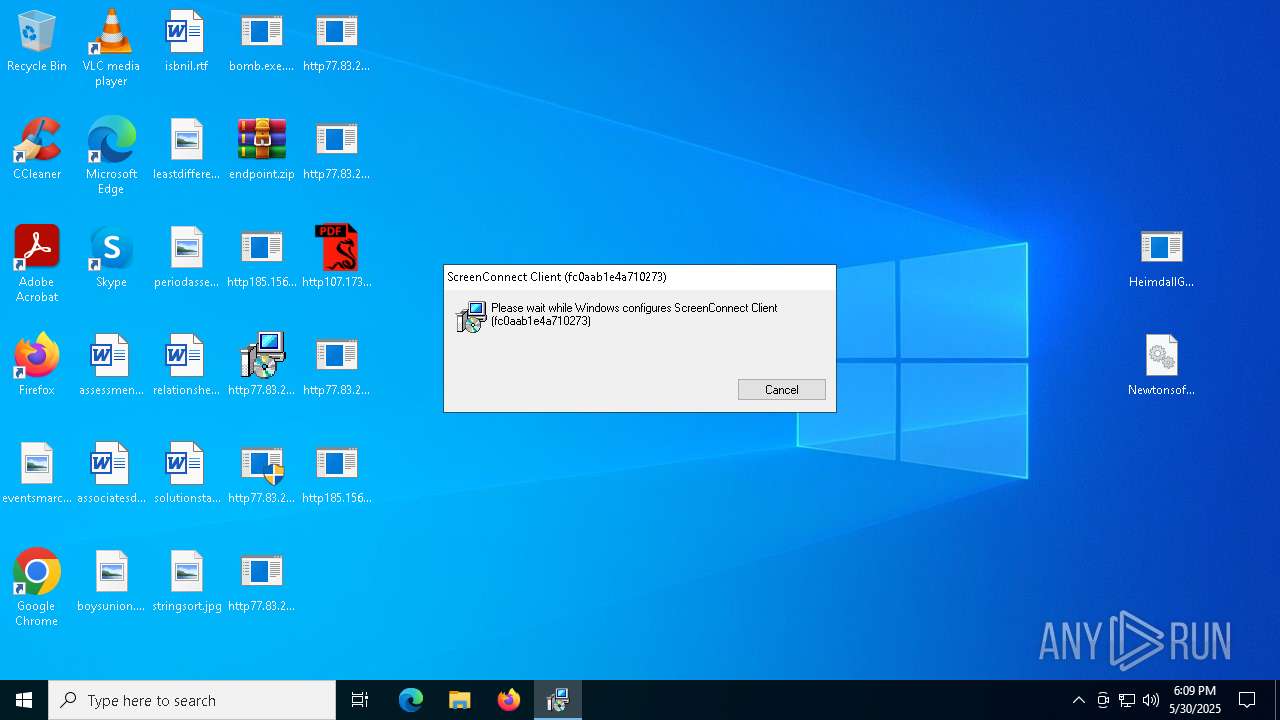
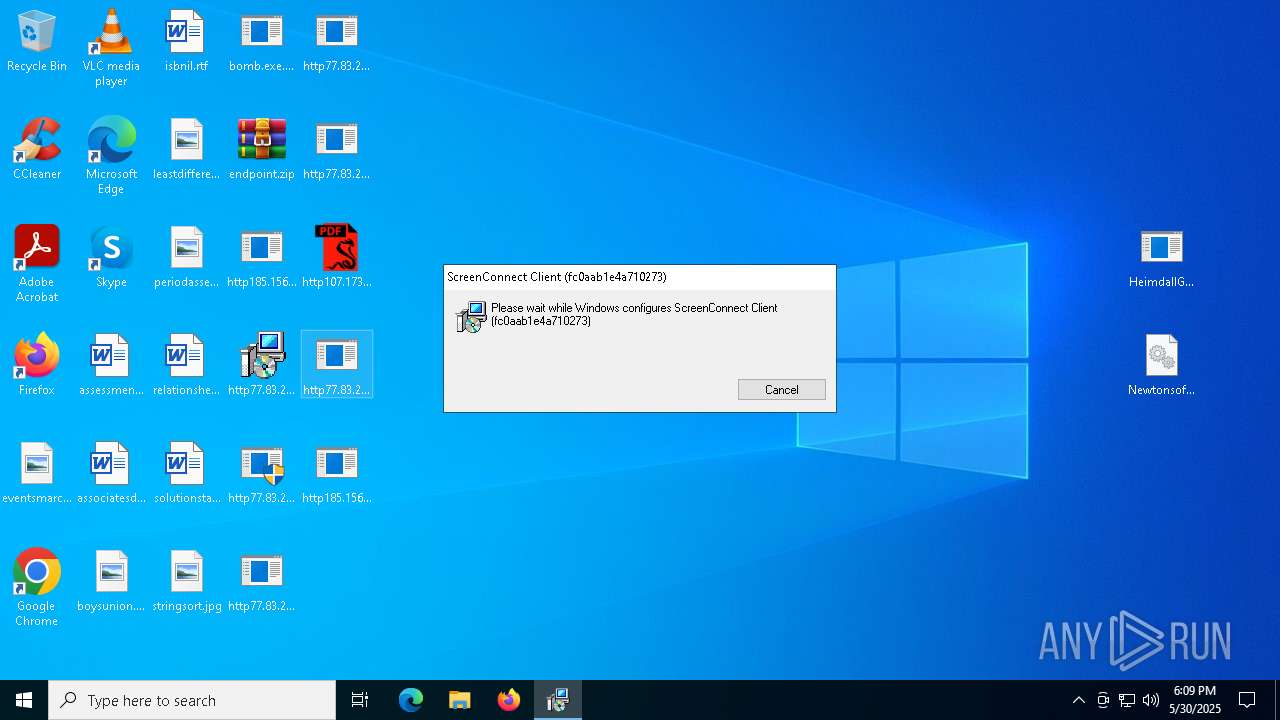
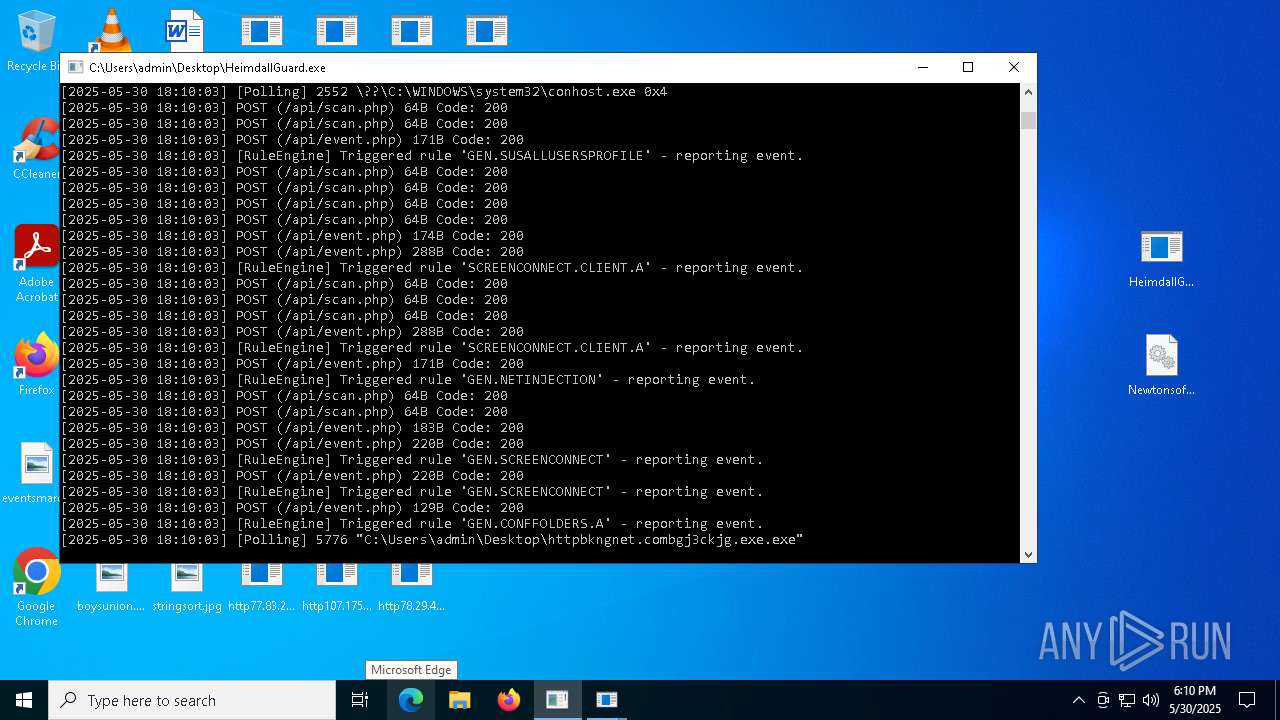
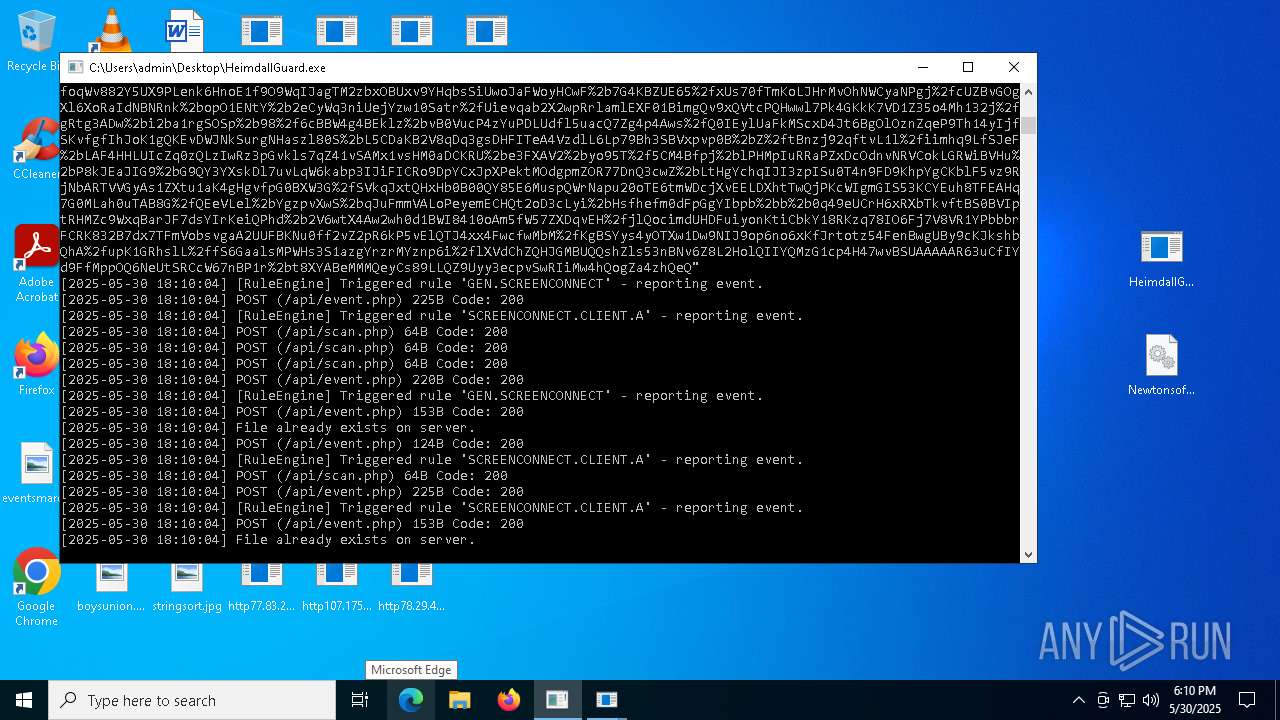
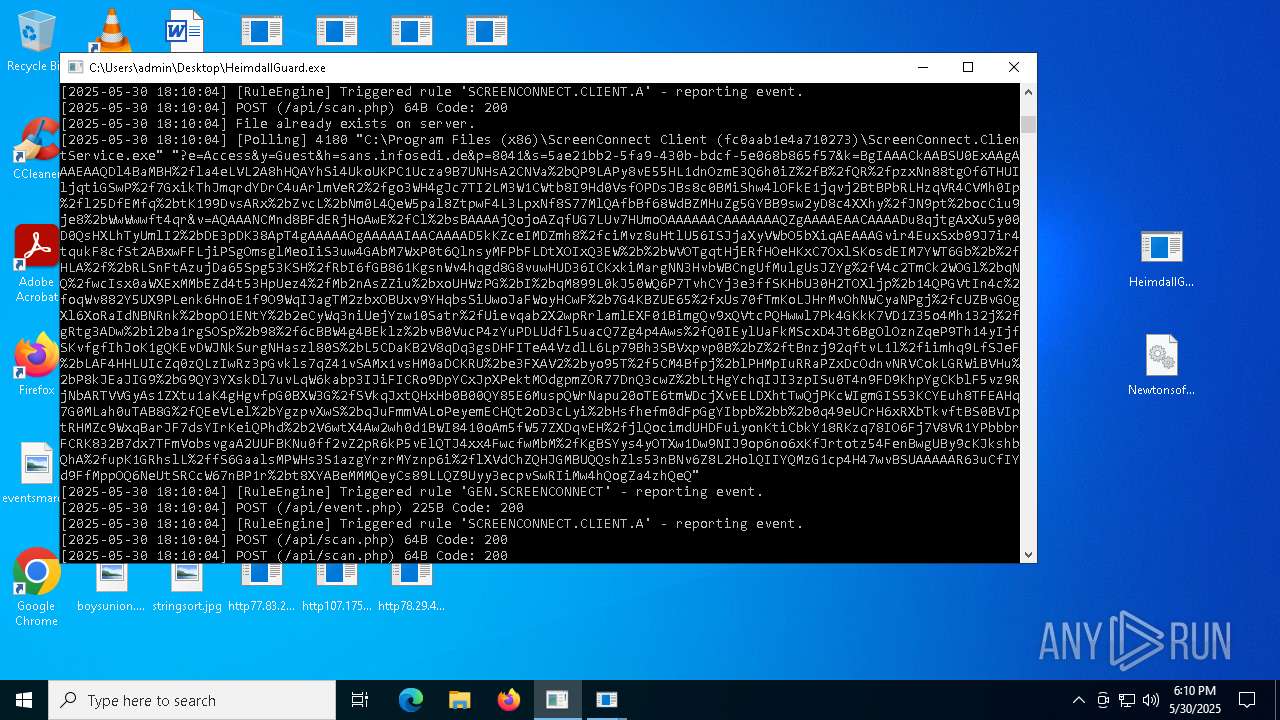
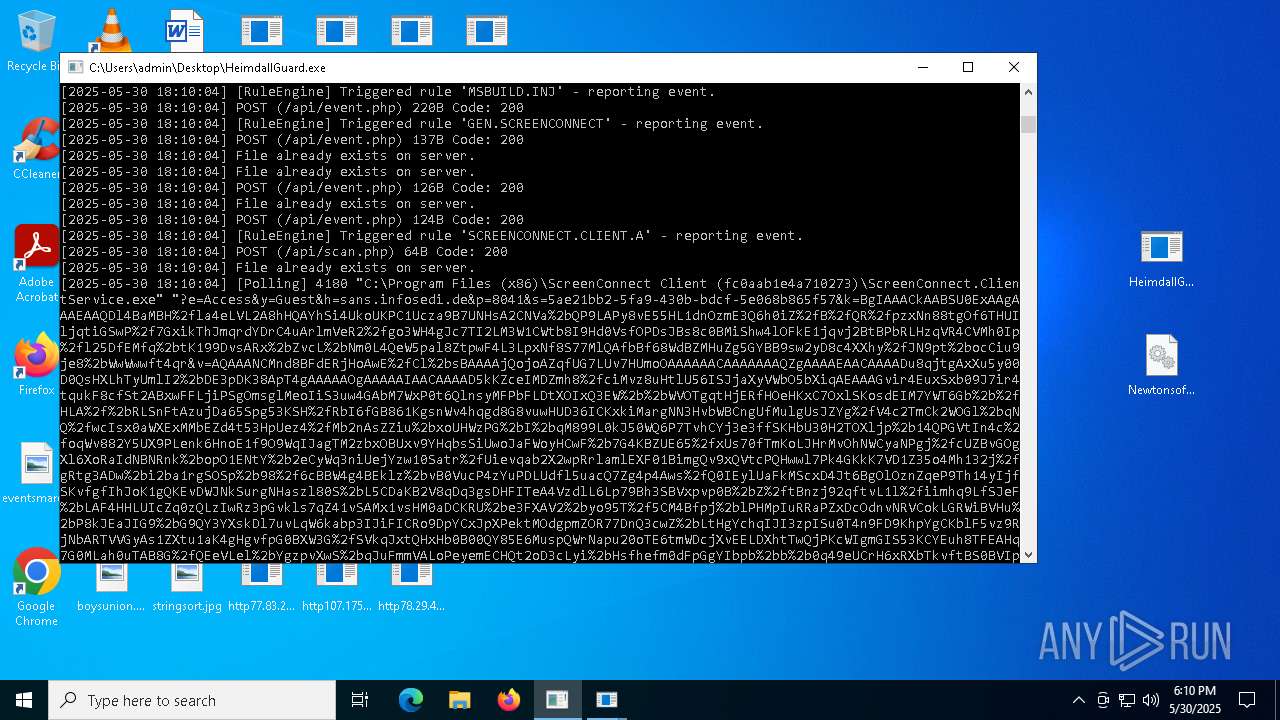
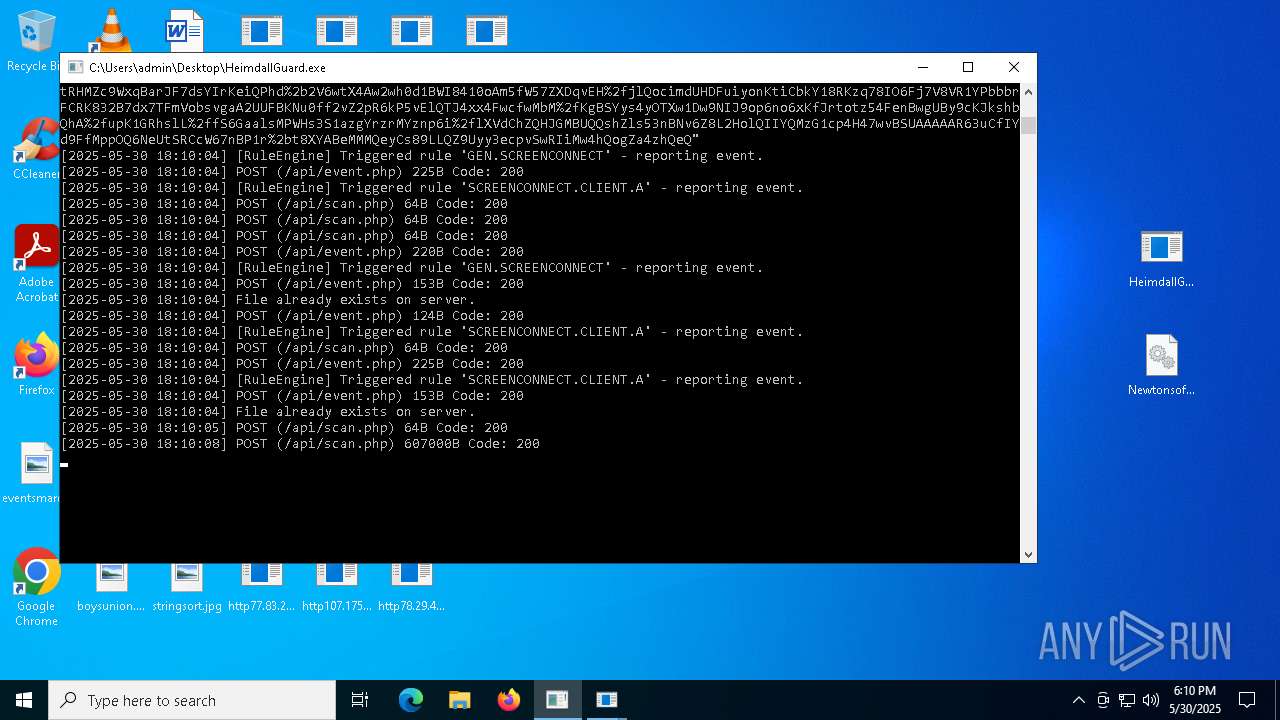
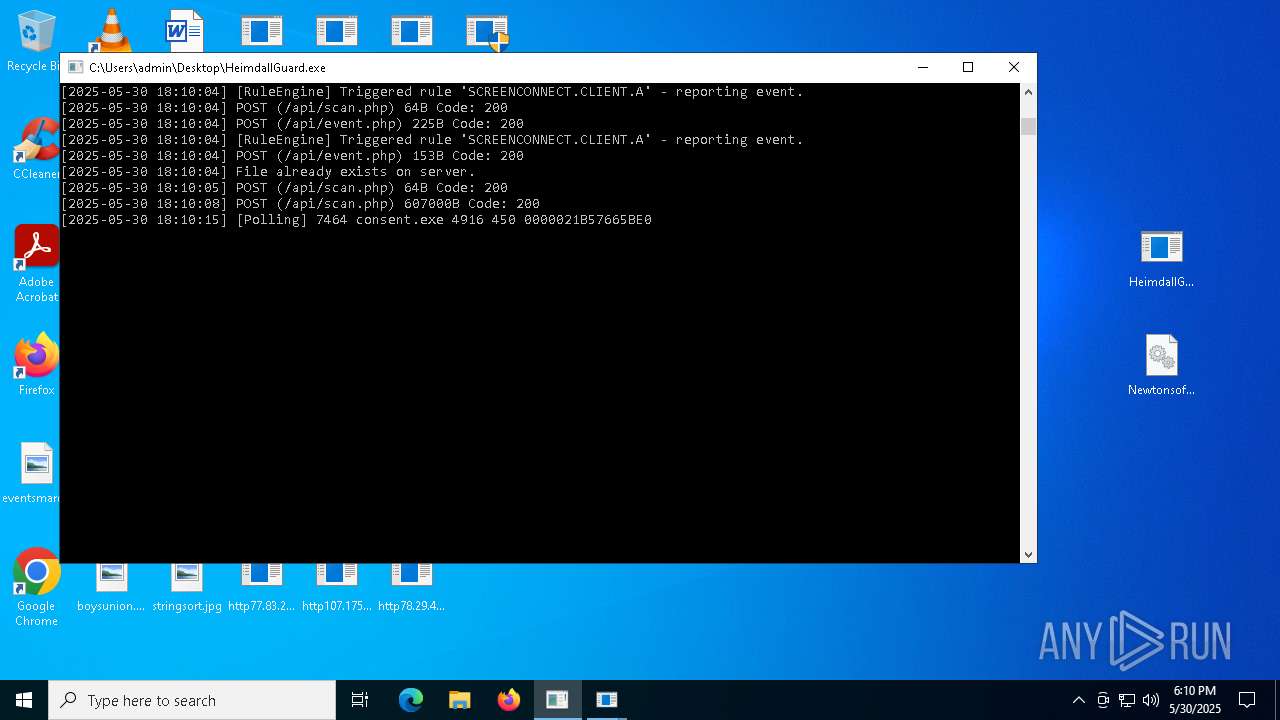
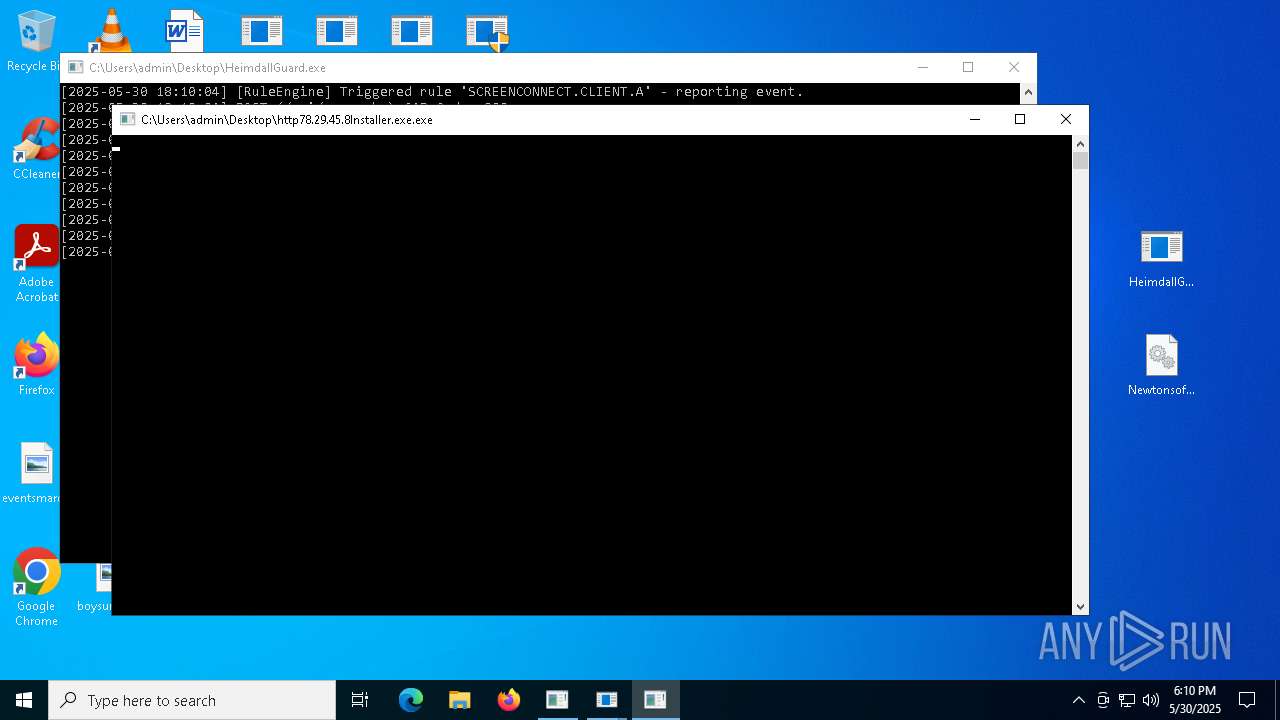
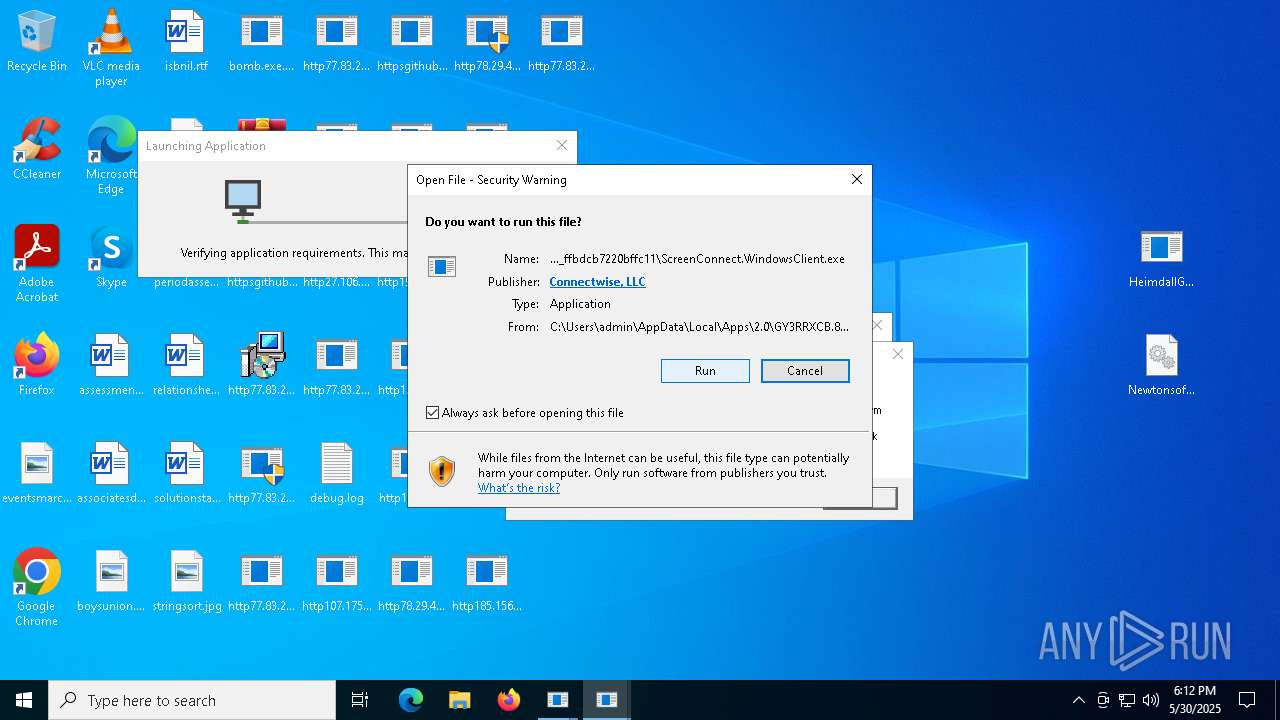
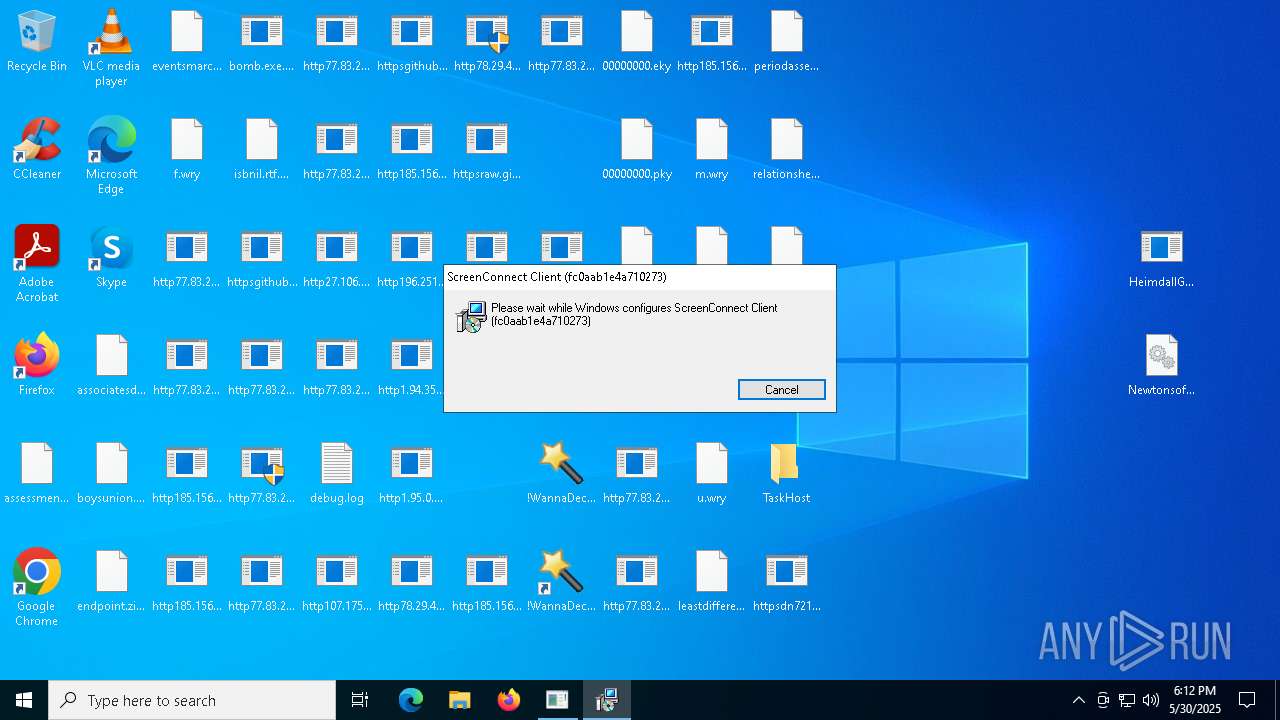
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.ClientService.exe (PID: 3304)
- ScreenConnect.ClientService.exe (PID: 6480)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
GENERIC has been found (auto)
- http107.173.47.141125dllhost.exe.exe (PID: 3032)
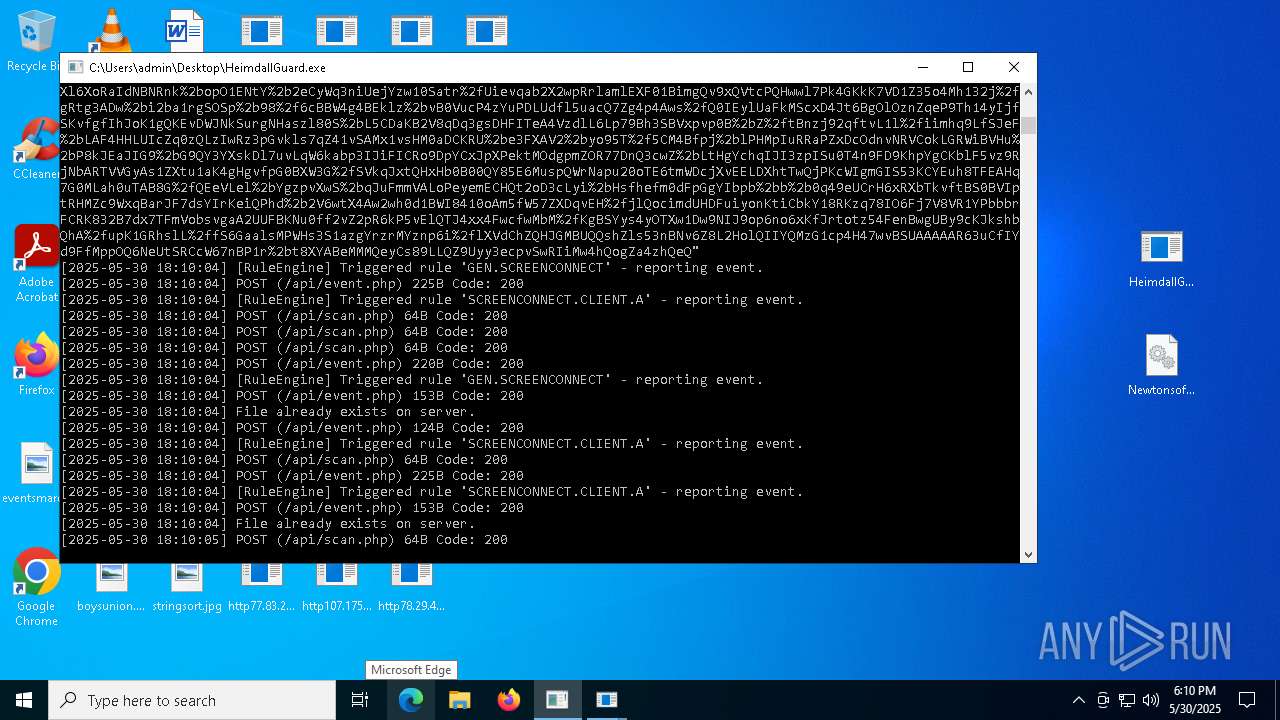
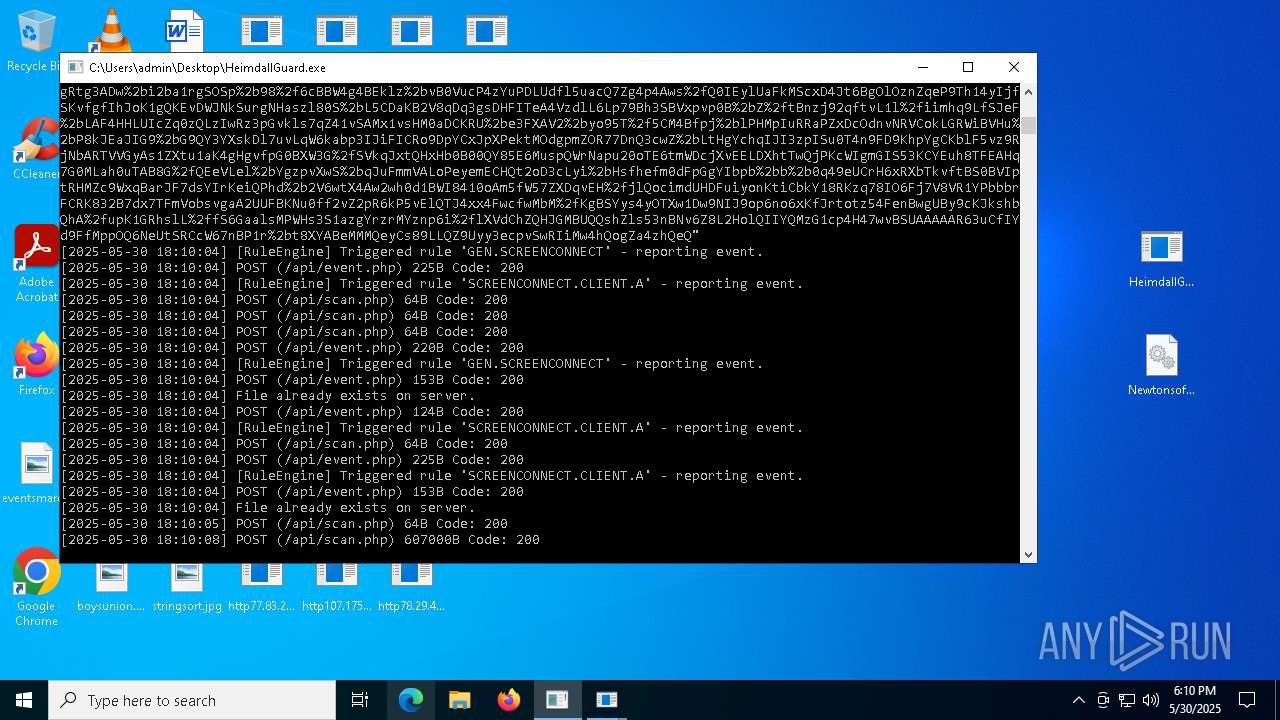
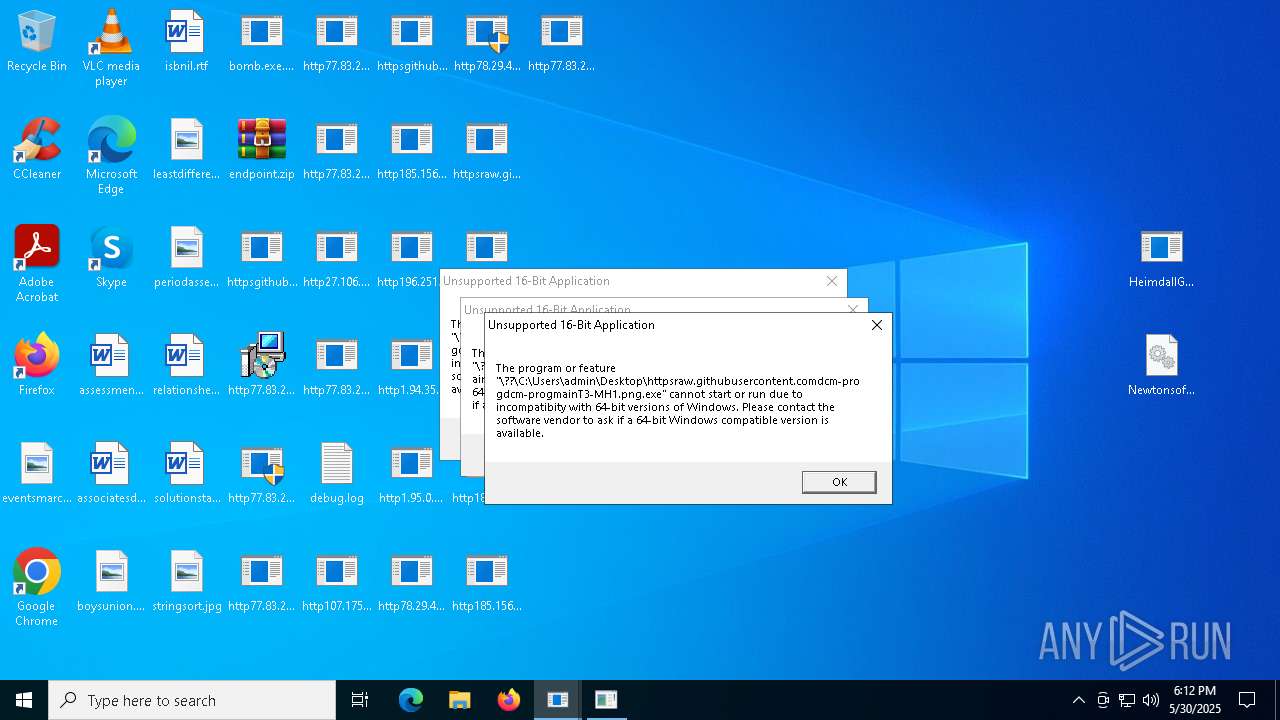
STEGOCAMPAIGN has been detected (SURICATA)
- bomb.exe.bin.exe (PID: 5556)
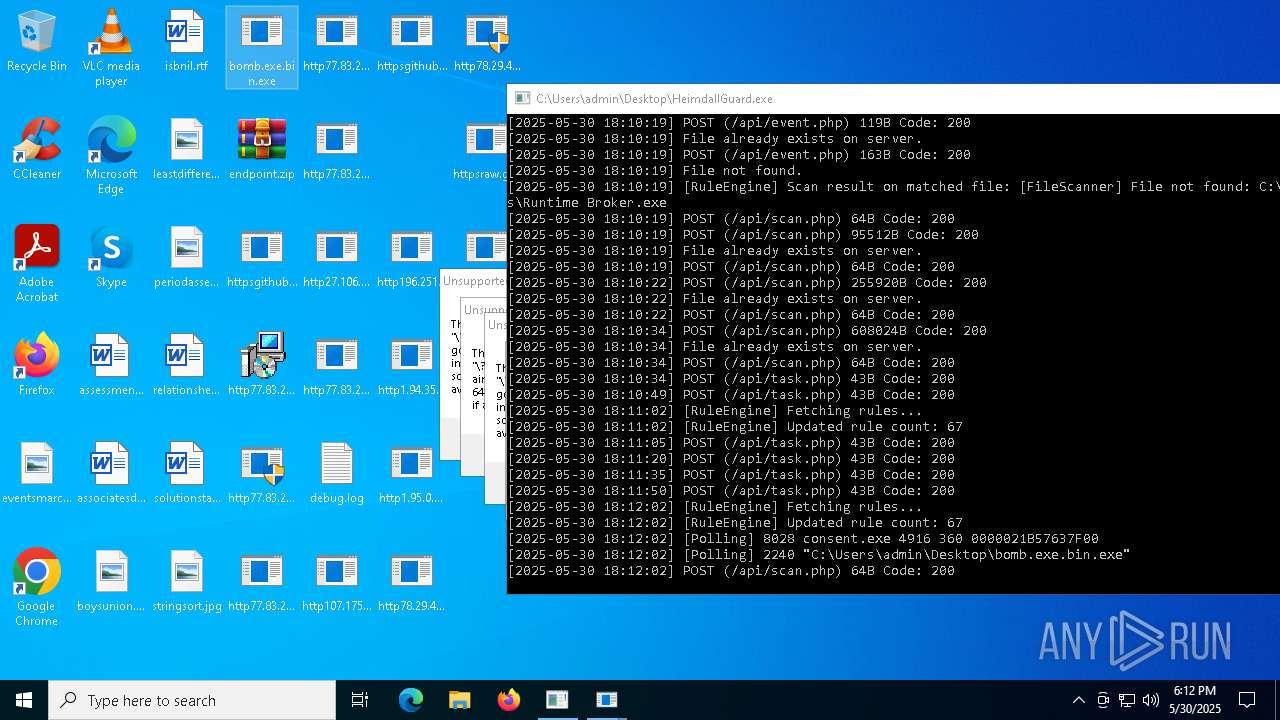
- bomb.exe.bin.exe (PID: 2240)
REVERSELOADER has been detected (SURICATA)
- bomb.exe.bin.exe (PID: 5556)
- bomb.exe.bin.exe (PID: 2240)
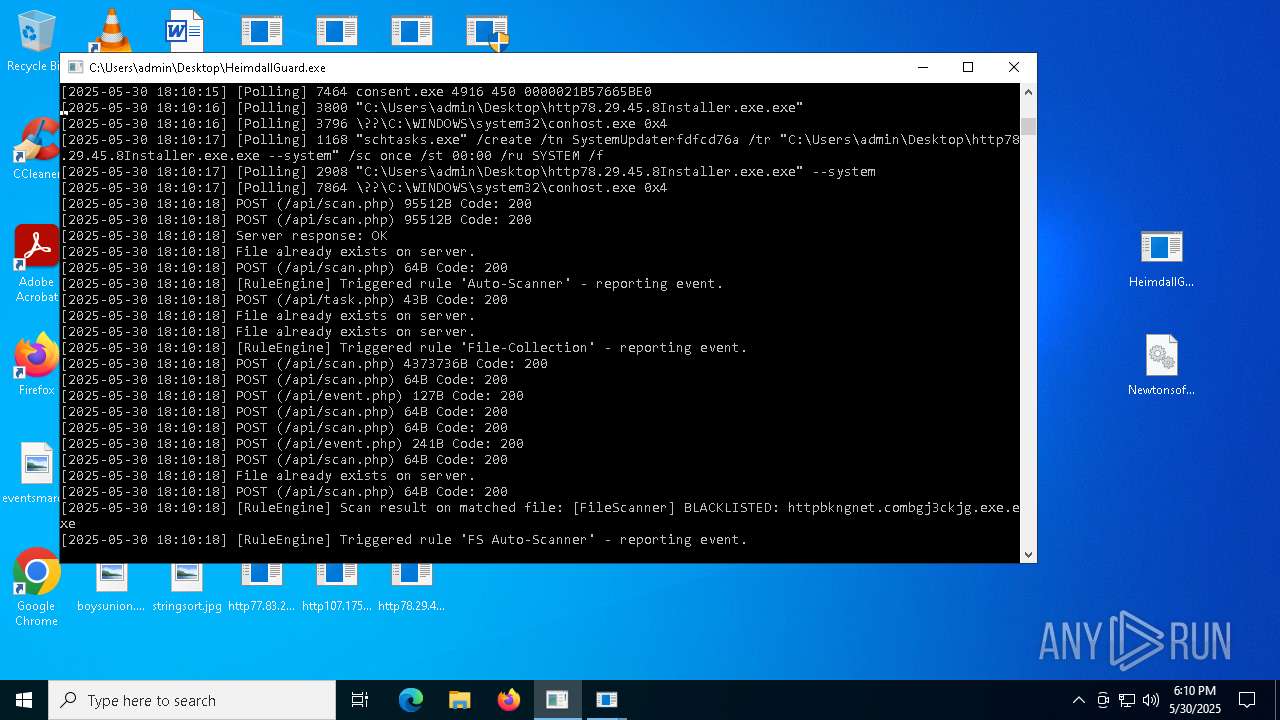
BRAODO has been found (auto)
- bomb.exe.bin.exe (PID: 5556)
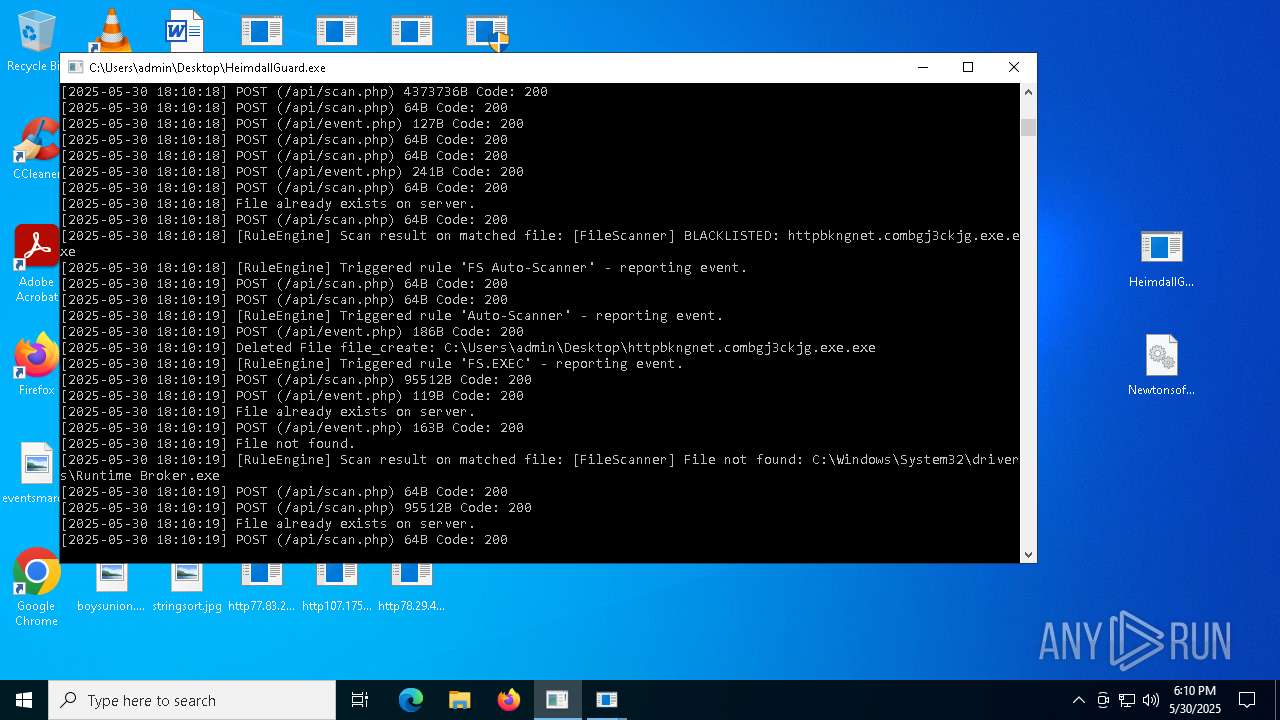
ASYNCRAT has been detected (SURICATA)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 5776)
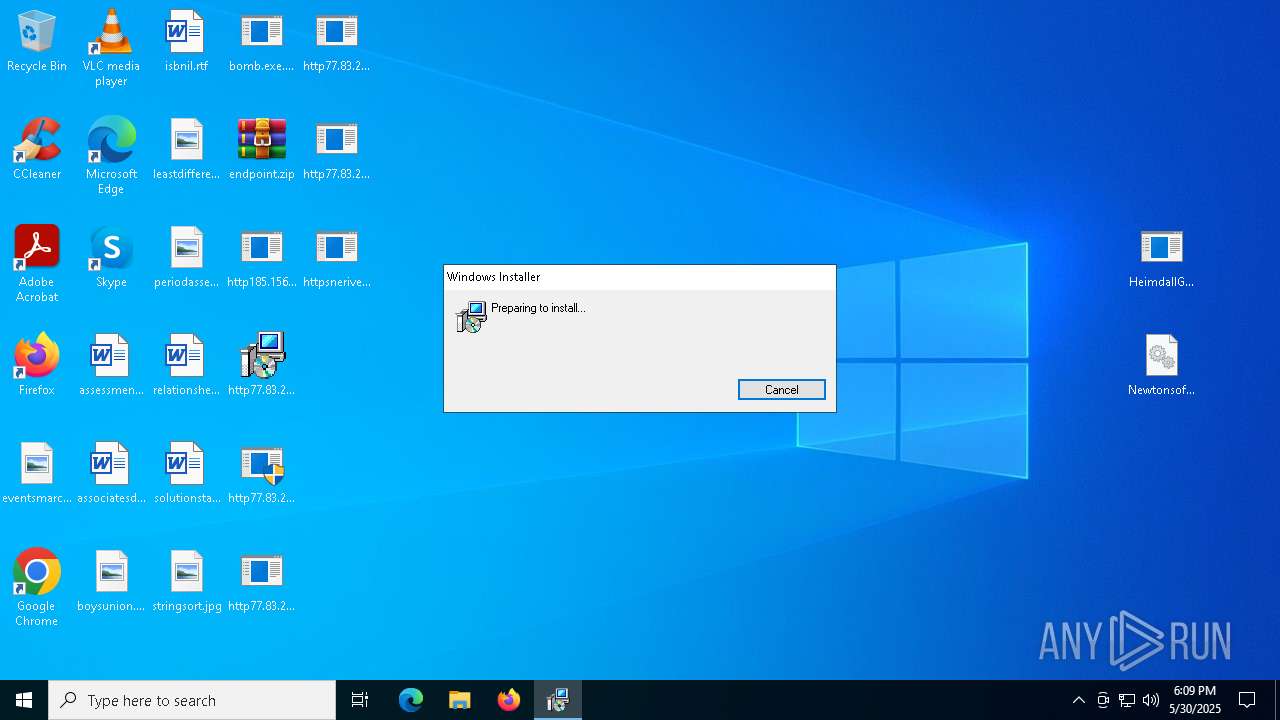
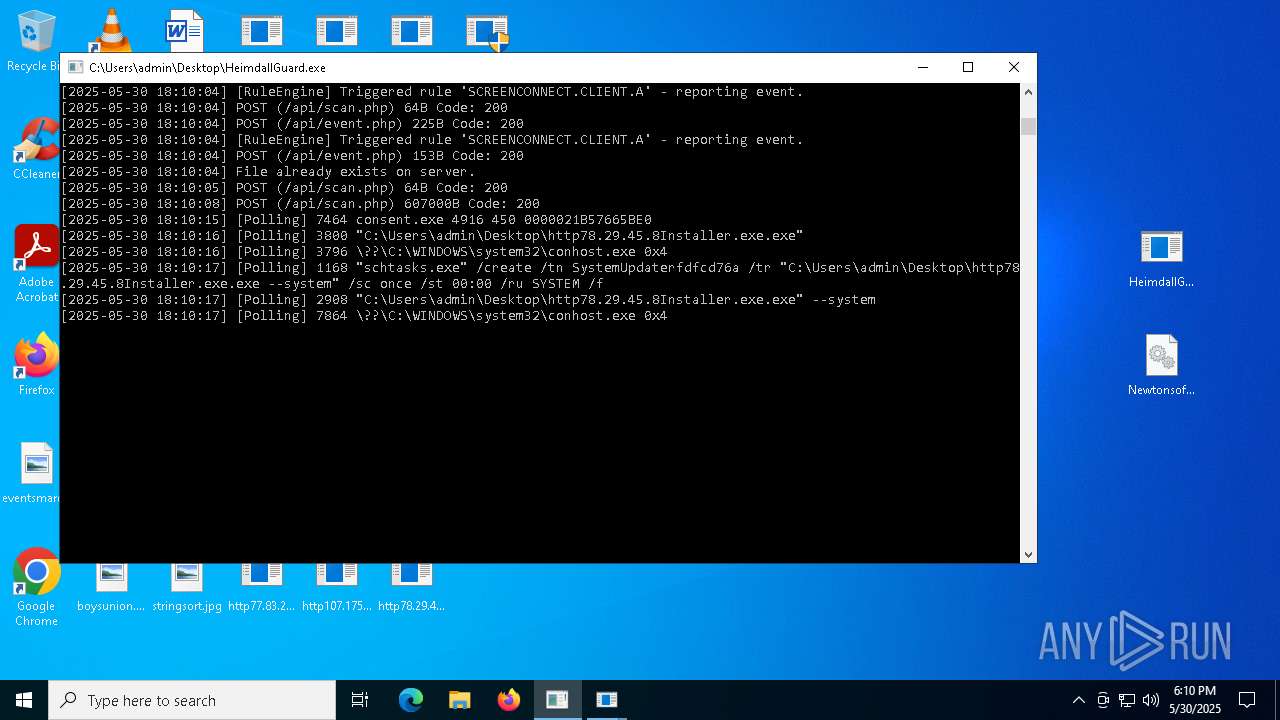
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7824)
- http78.29.45.8Installer.exe.exe (PID: 3800)
HIJACKLOADER has been detected (YARA)
- ModSolar.exe (PID: 4976)
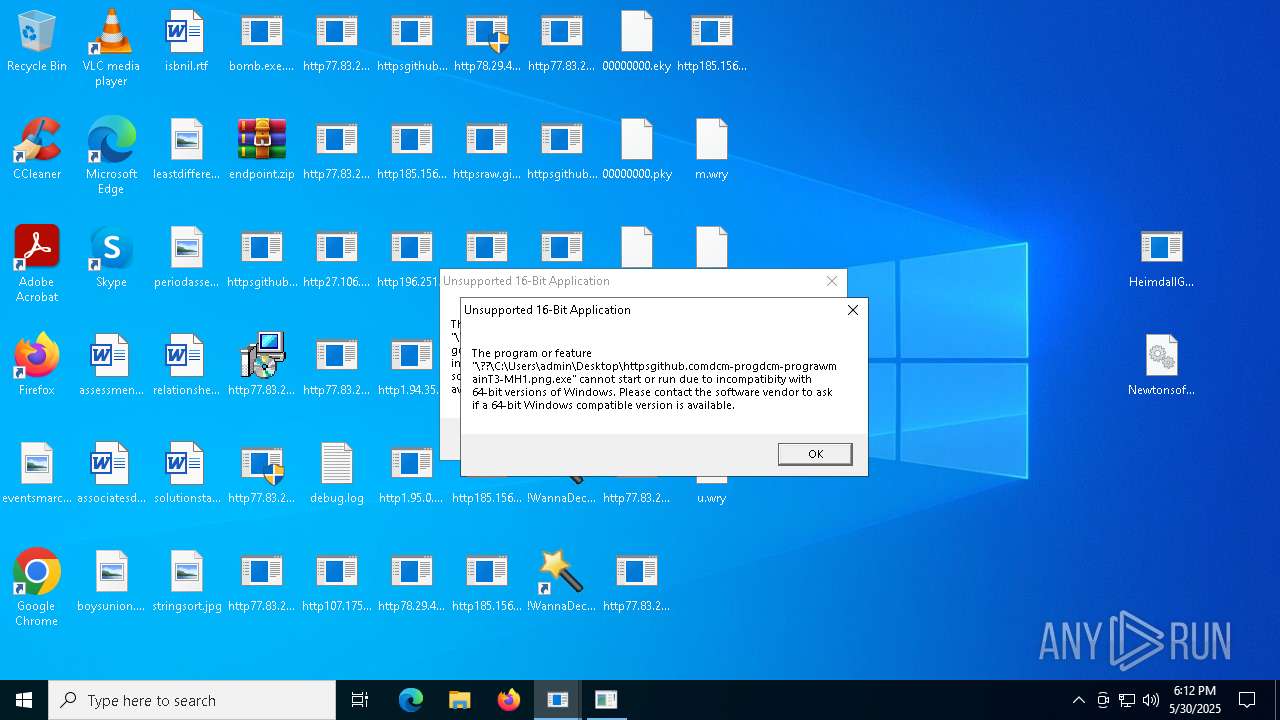
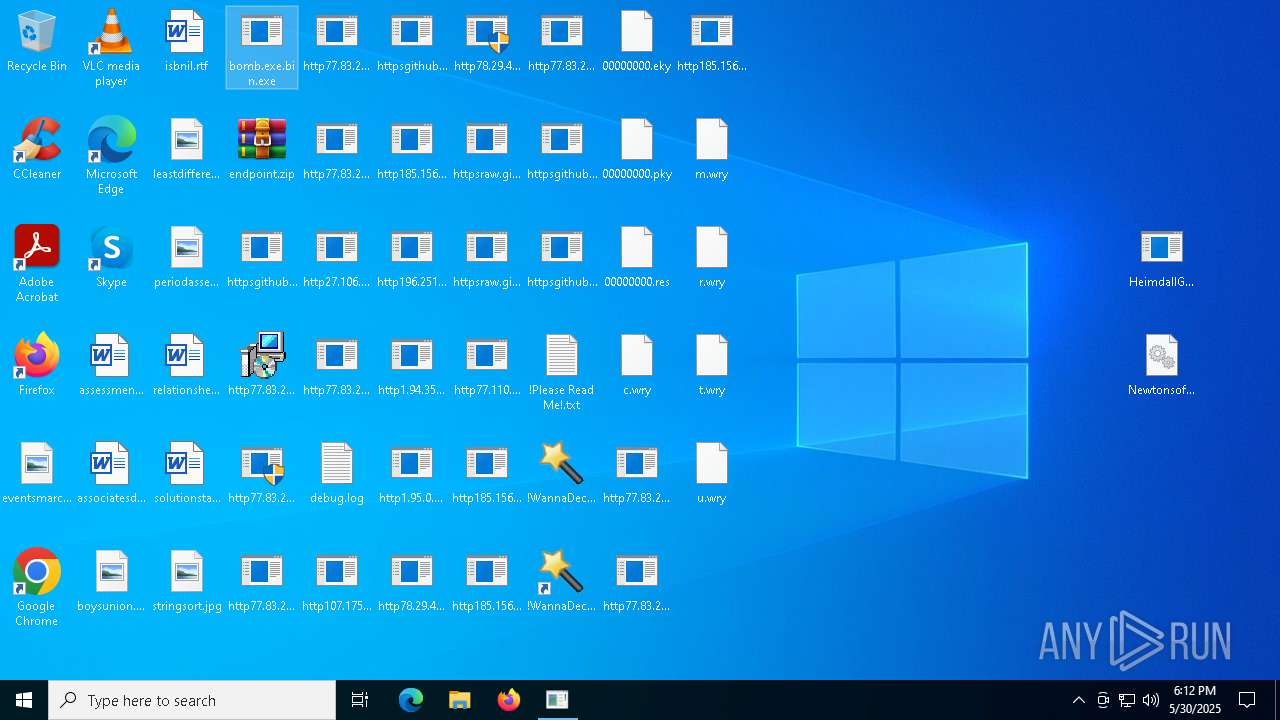
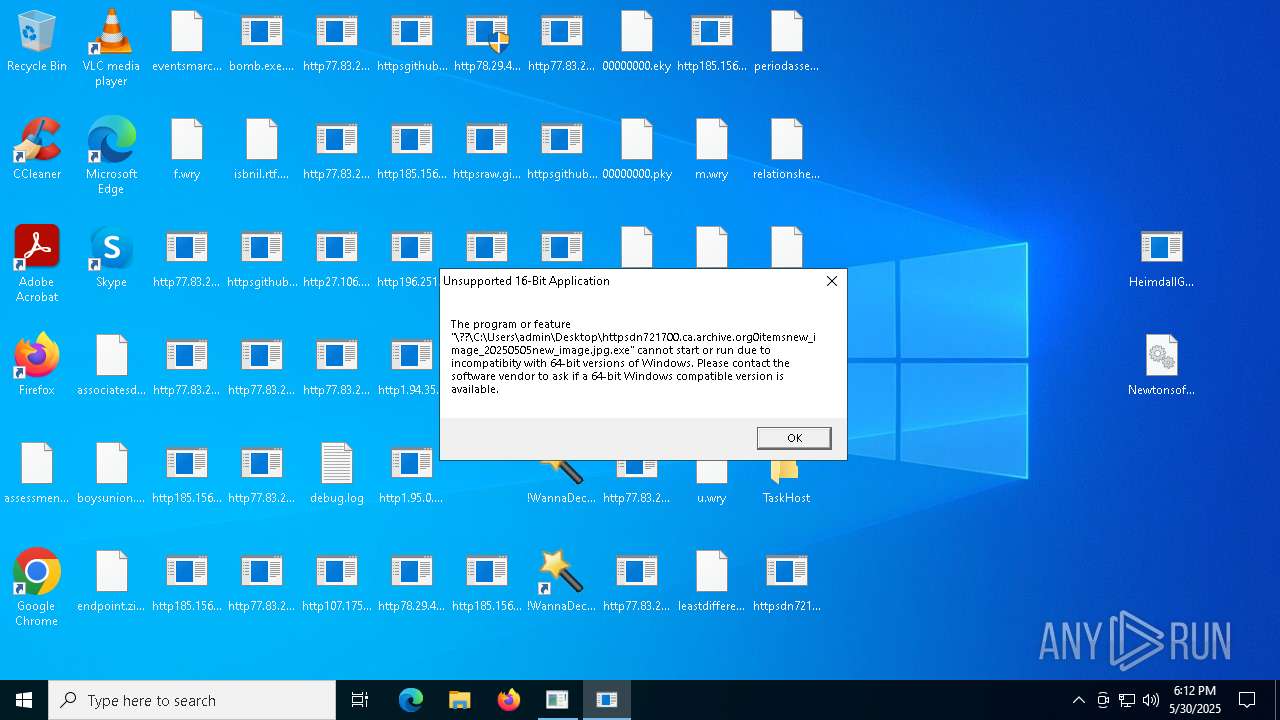
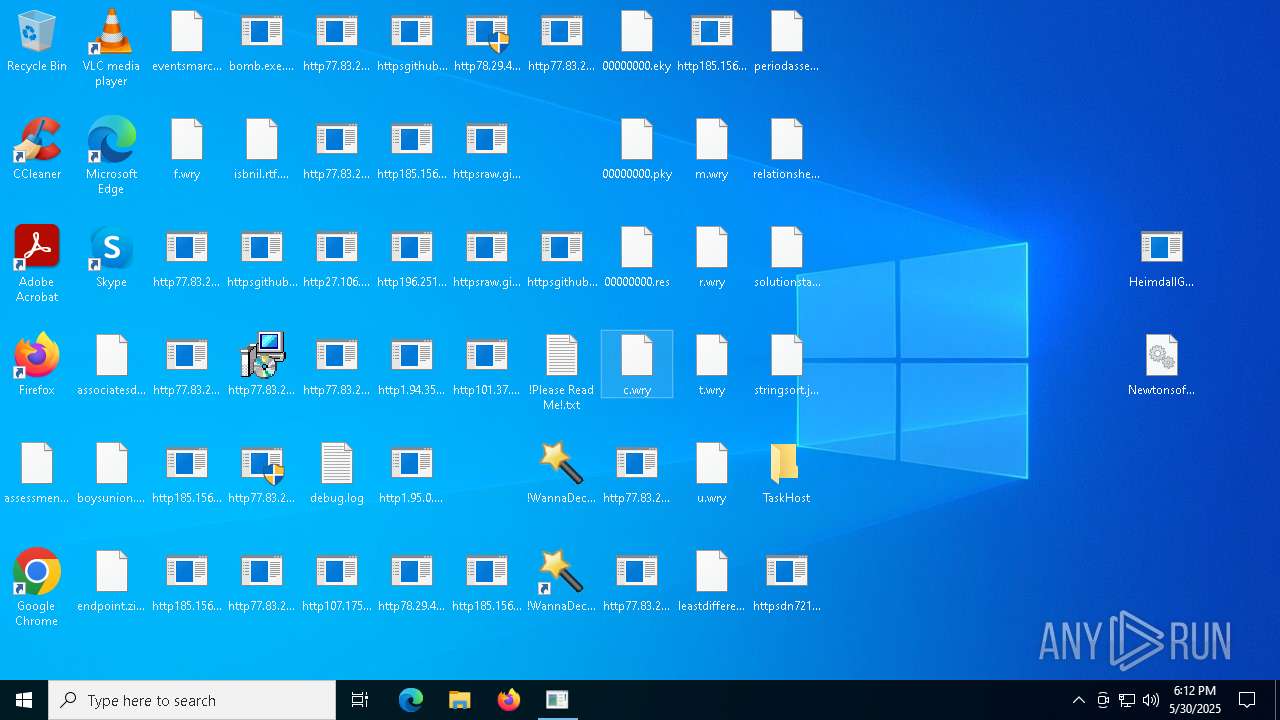
WannaCry Ransomware is detected
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
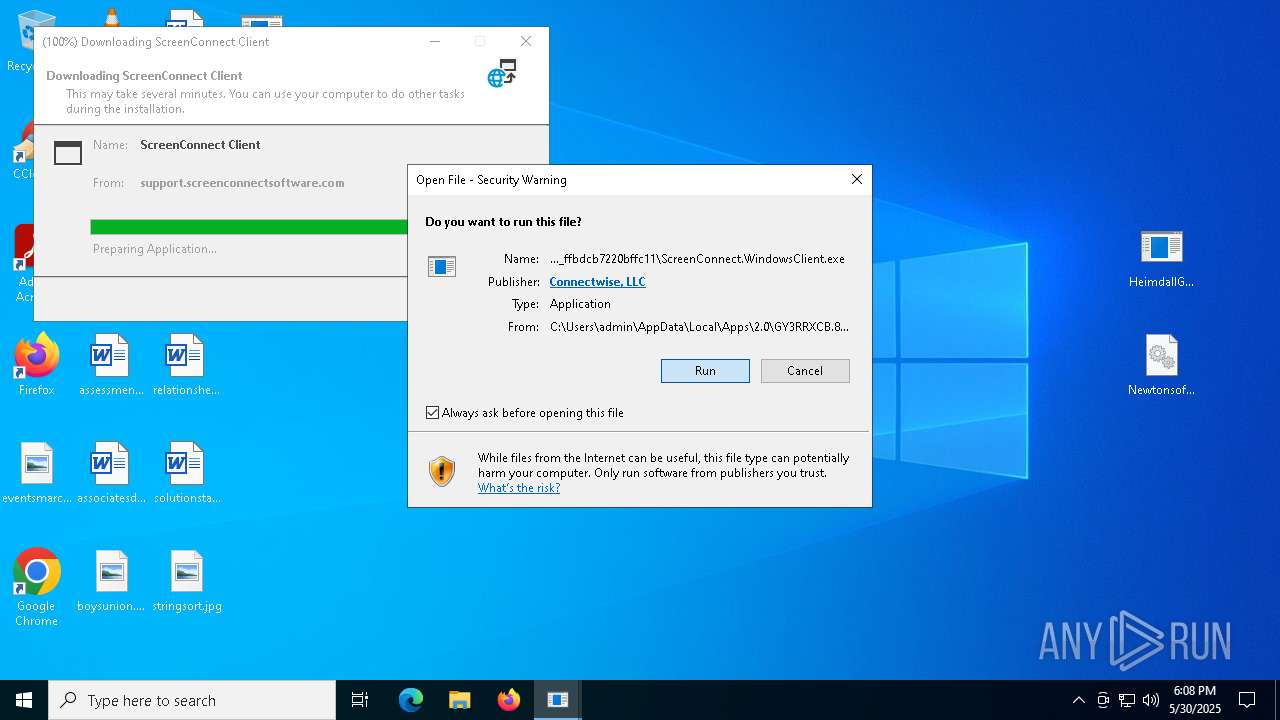
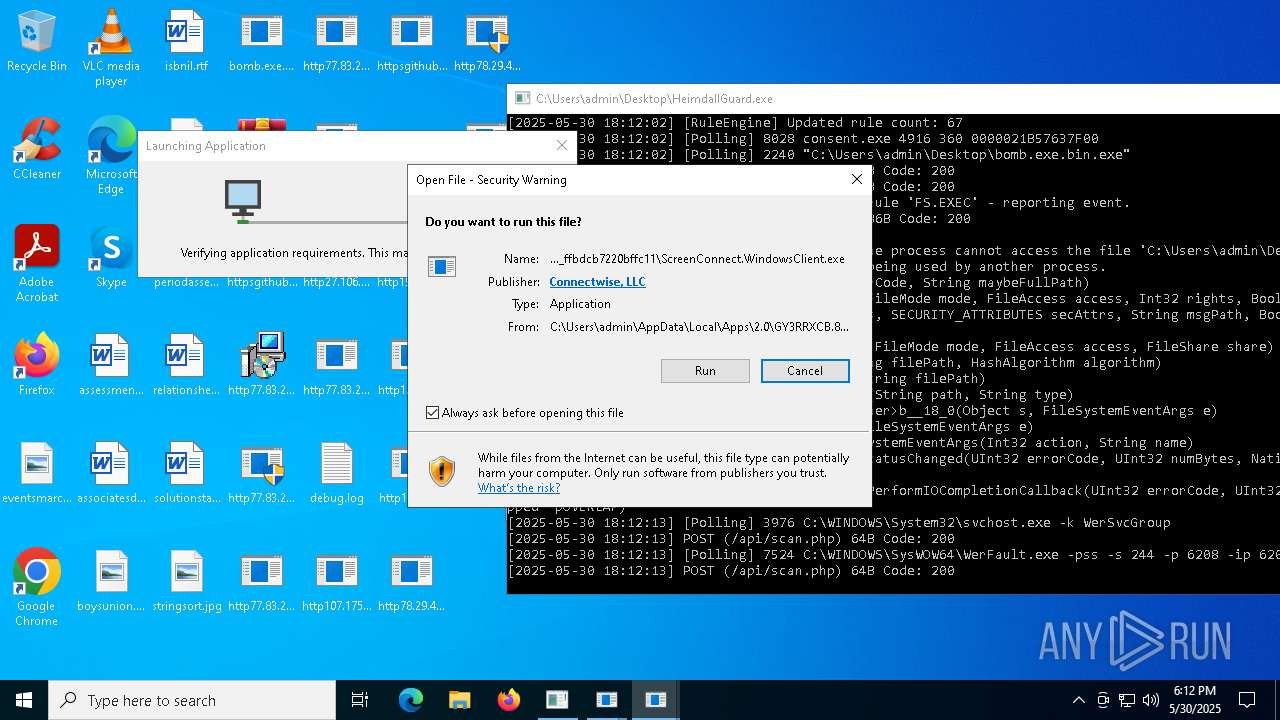
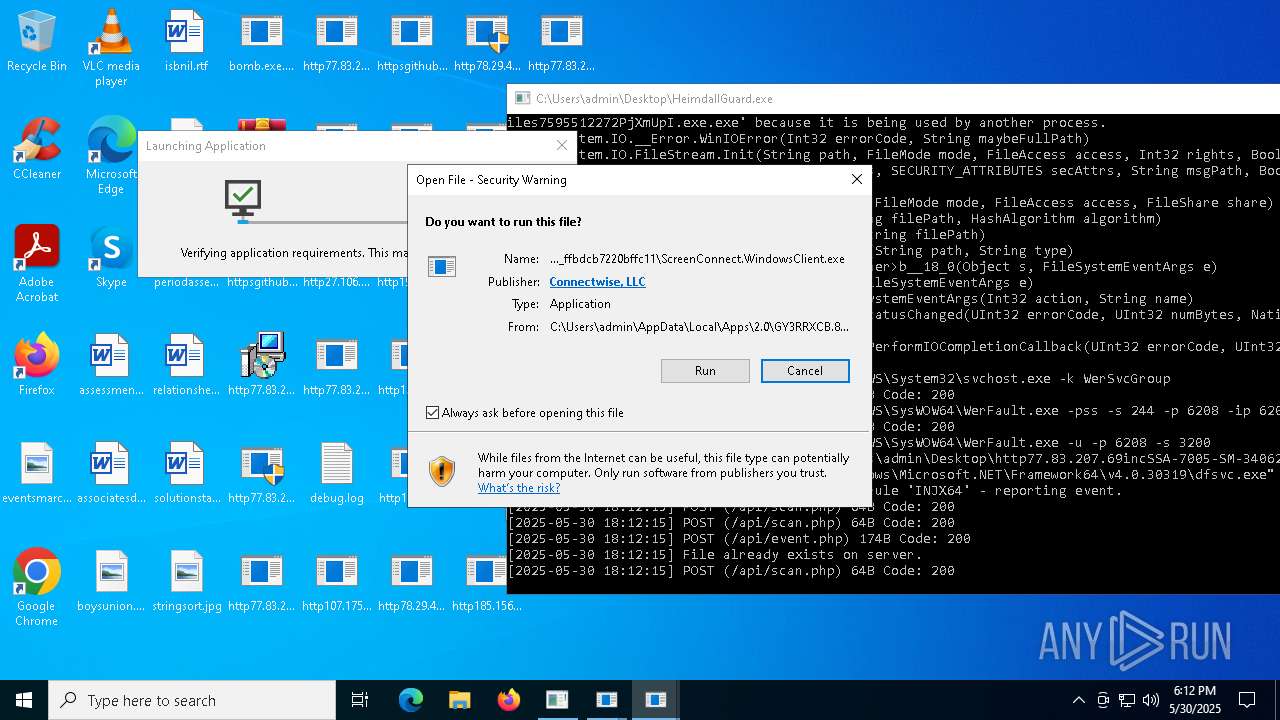
Executing a file with an untrusted certificate
- httpsbvu.oss-ap-southeast-6.aliyuncs.comDimension.exe.exe (PID: 668)
SUSPICIOUS
Reads the date of Windows installation
- bomb.exe.bin.exe (PID: 5556)
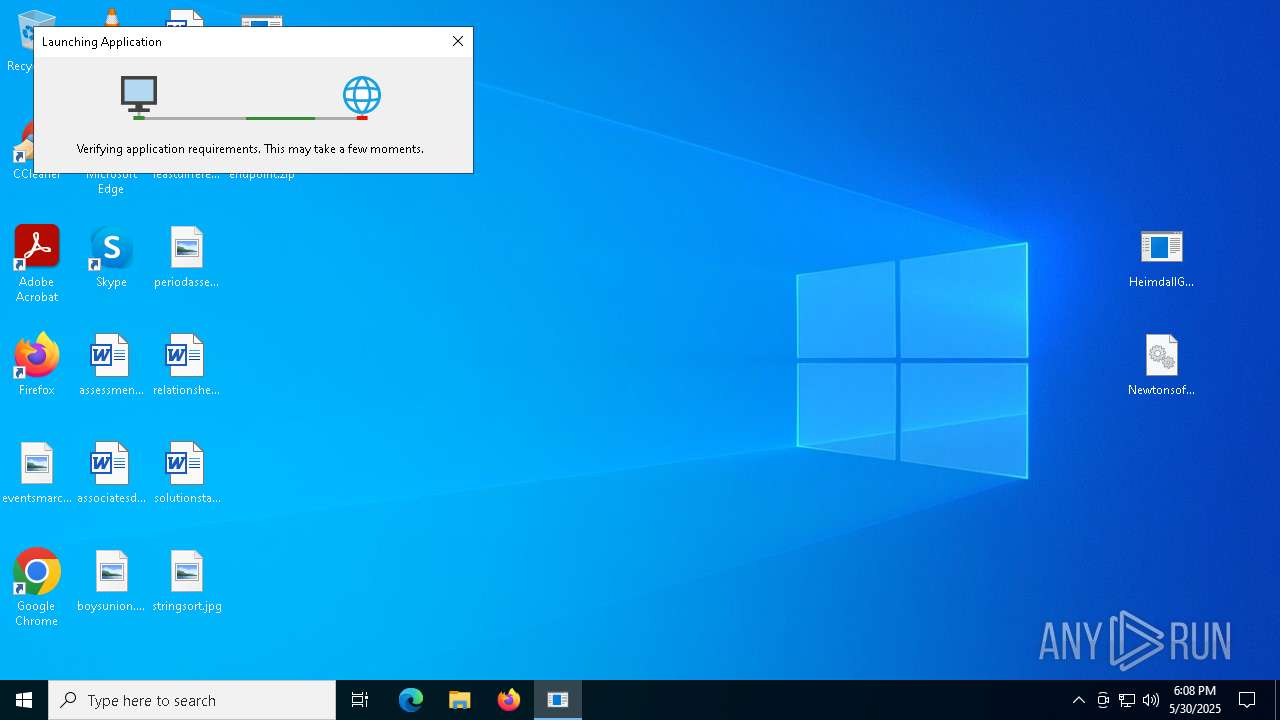
- dfsvc.exe (PID: 5528)
- ScreenConnect.WindowsClient.exe (PID: 7508)
Reads security settings of Internet Explorer
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
- ScreenConnect.ClientService.exe (PID: 7276)
- ScreenConnect.WindowsClient.exe (PID: 7508)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.WindowsClient.exe (PID: 8176)
- http77.83.207.69incClientSetup1.exe.exe (PID: 5596)
Process requests binary or script from the Internet
- bomb.exe.bin.exe (PID: 5556)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- bomb.exe.bin.exe (PID: 2240)
Executable content was dropped or overwritten
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7776)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 1168)
- ModSolar.exe (PID: 1804)
- ModSolar.exe (PID: 4976)
- rundll32.exe (PID: 6108)
- esentutl.exe (PID: 3364)
- http107.173.47.141125dllhost.exe.exe (PID: 3032)
- http78.29.45.8Installer.exe.exe (PID: 3800)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
- rundll32.exe (PID: 1804)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 3160)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 5996)
- bomb.exe.bin.exe (PID: 2240)
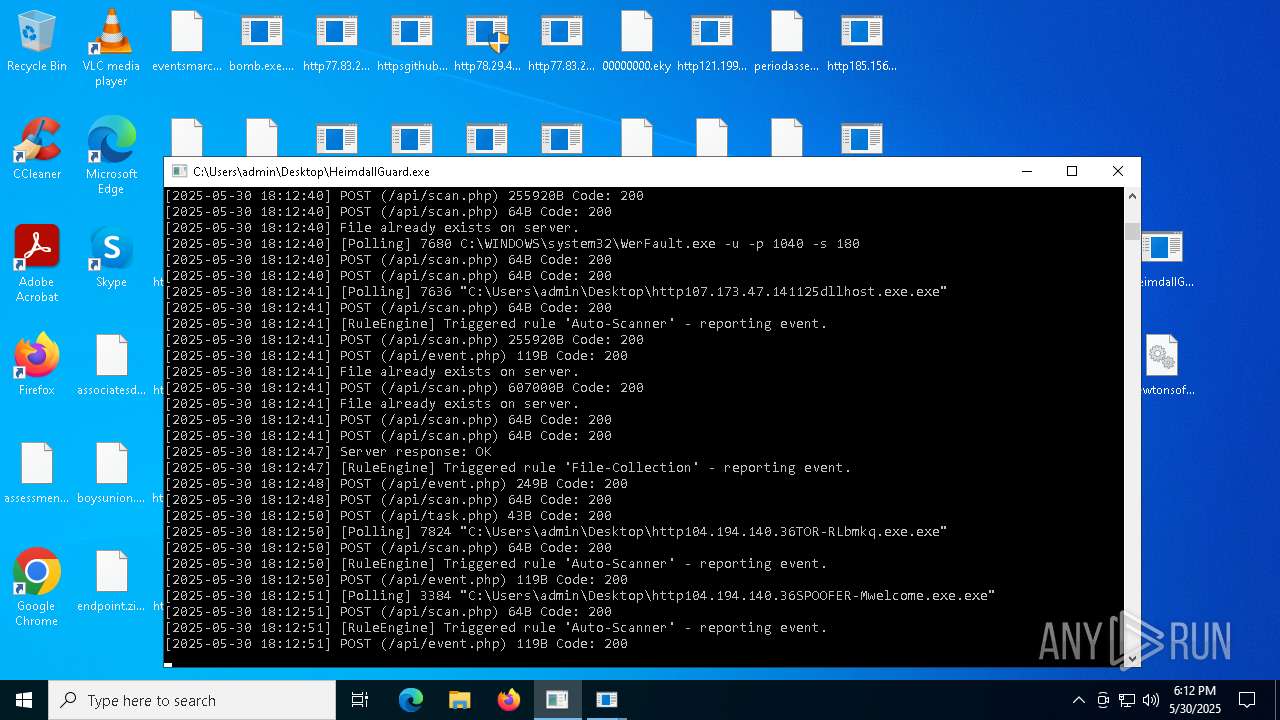
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 3384)
- ModSolar.exe (PID: 7216)
Adds/modifies Windows certificates
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 4988)
- dfsvc.exe (PID: 5528)
Connects to the server without a host name
- bomb.exe.bin.exe (PID: 5556)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- bomb.exe.bin.exe (PID: 2240)
Potential Corporate Privacy Violation
- bomb.exe.bin.exe (PID: 5556)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.ClientService.exe (PID: 3304)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- bomb.exe.bin.exe (PID: 2240)
- ScreenConnect.ClientService.exe (PID: 6480)
Connects to unusual port
- bomb.exe.bin.exe (PID: 5556)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.ClientService.exe (PID: 3304)
- SndVol.exe (PID: 7976)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 5776)
- bomb.exe.bin.exe (PID: 2240)
- ScreenConnect.ClientService.exe (PID: 6480)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 5528)
- bomb.exe.bin.exe (PID: 5556)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 5352)
- VSSVC.exe (PID: 8076)
- ScreenConnect.ClientService.exe (PID: 3304)
- ScreenConnect.ClientService.exe (PID: 1568)
- ScreenConnect.ClientService.exe (PID: 4180)
- ScreenConnect.ClientService.exe (PID: 6480)
Reads Internet Explorer settings
- dfsvc.exe (PID: 5528)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 5352)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 5352)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 5352)
Starts itself from another location
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7776)
- ModSolar.exe (PID: 1804)
- cmd.exe (PID: 7420)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 3160)
- ModSolar.exe (PID: 7216)
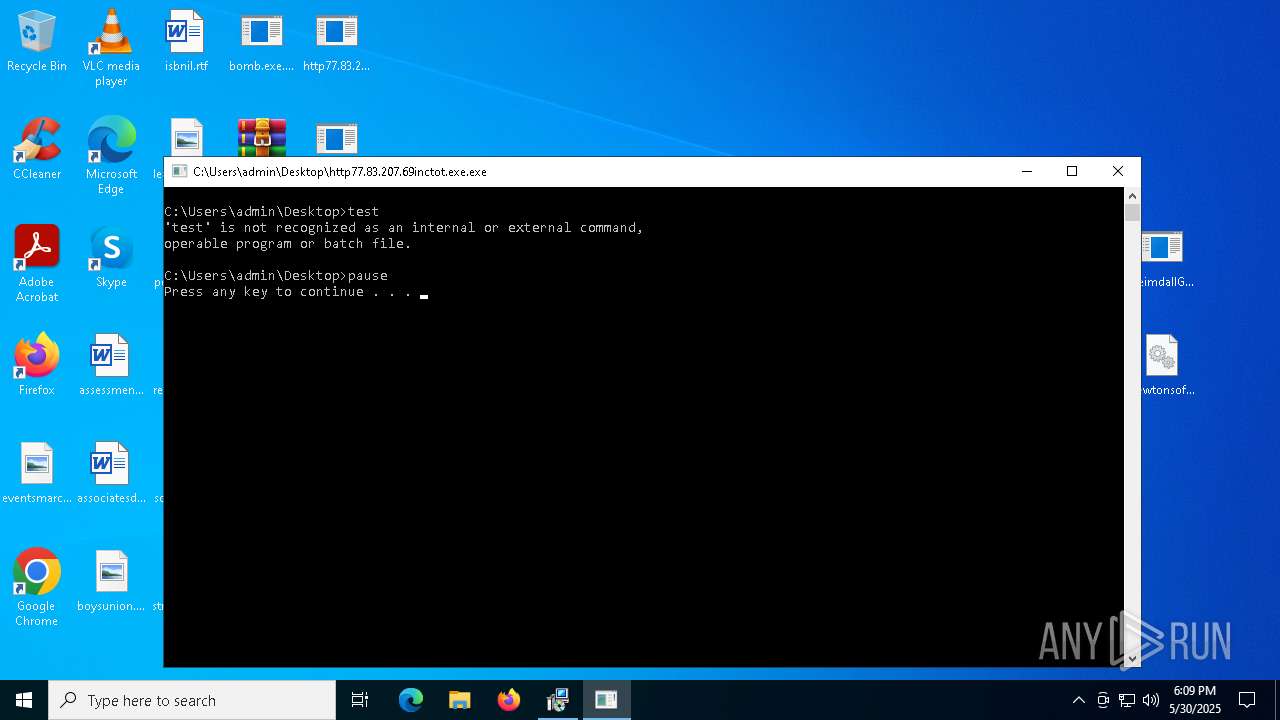
Starts CMD.EXE for commands execution
- http77.83.207.69inctot.exe.exe (PID: 7716)
- http107.173.47.141125dllhost.exe.exe (PID: 3032)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
Executing commands from a ".bat" file
- http77.83.207.69inctot.exe.exe (PID: 7716)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 5776)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 6656)
- MSBuild.exe (PID: 7912)
- MSBuild.exe (PID: 5980)
Starts application with an unusual extension
- cmd.exe (PID: 7420)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6300)
Executing commands from ".cmd" file
- http107.173.47.141125dllhost.exe.exe (PID: 3032)
Likely accesses (executes) a file from the Public directory
- esentutl.exe (PID: 3364)
- alpha.pif (PID: 8036)
- alpha.pif (PID: 7712)
Detects ScreenConnect RAT (YARA)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.WindowsClient.exe (PID: 8176)
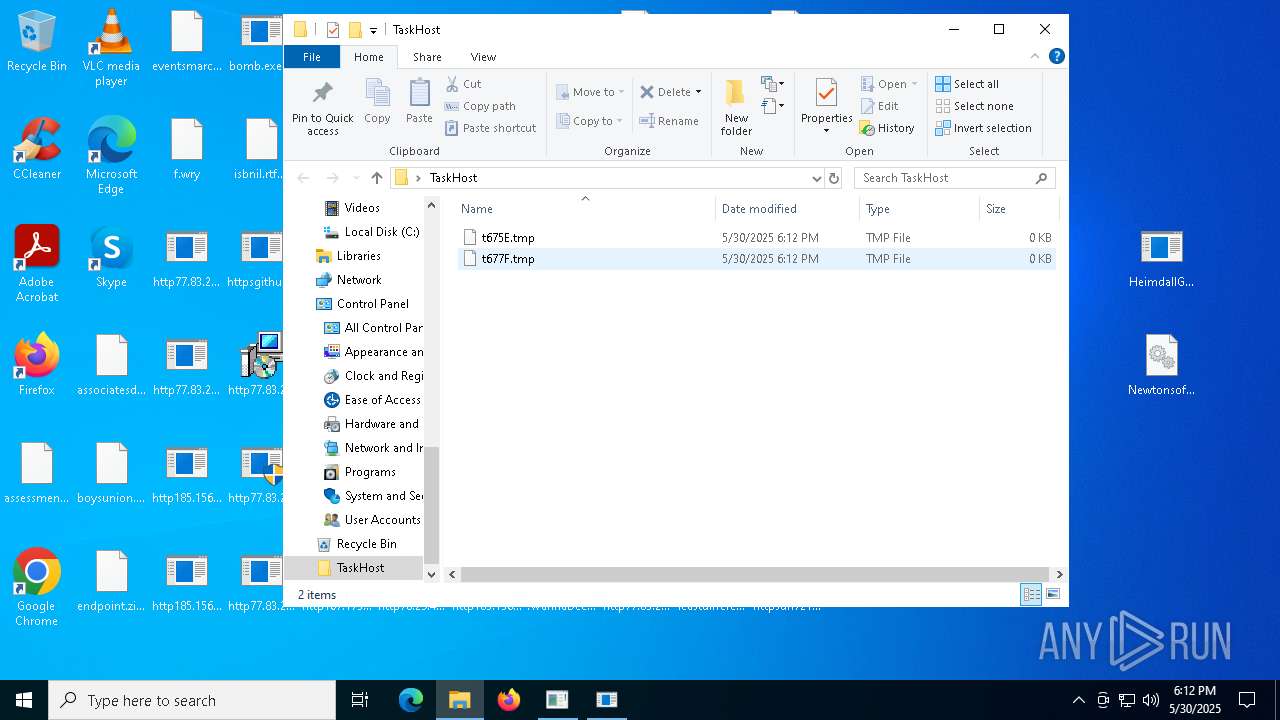
Created directory related to system
- alpha.pif (PID: 8036)
Starts a Microsoft application from unusual location
- alpha.pif (PID: 8036)
- alpha.pif (PID: 7712)
- http78.29.45.8Installer.exe.exe (PID: 7692)
- http78.29.45.8Installer.exe.exe (PID: 3800)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
- !WannaDecryptor!.exe (PID: 6180)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 6044)
There is functionality for taking screenshot (YARA)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.WindowsClient.exe (PID: 8176)
- ModSolar.exe (PID: 4976)
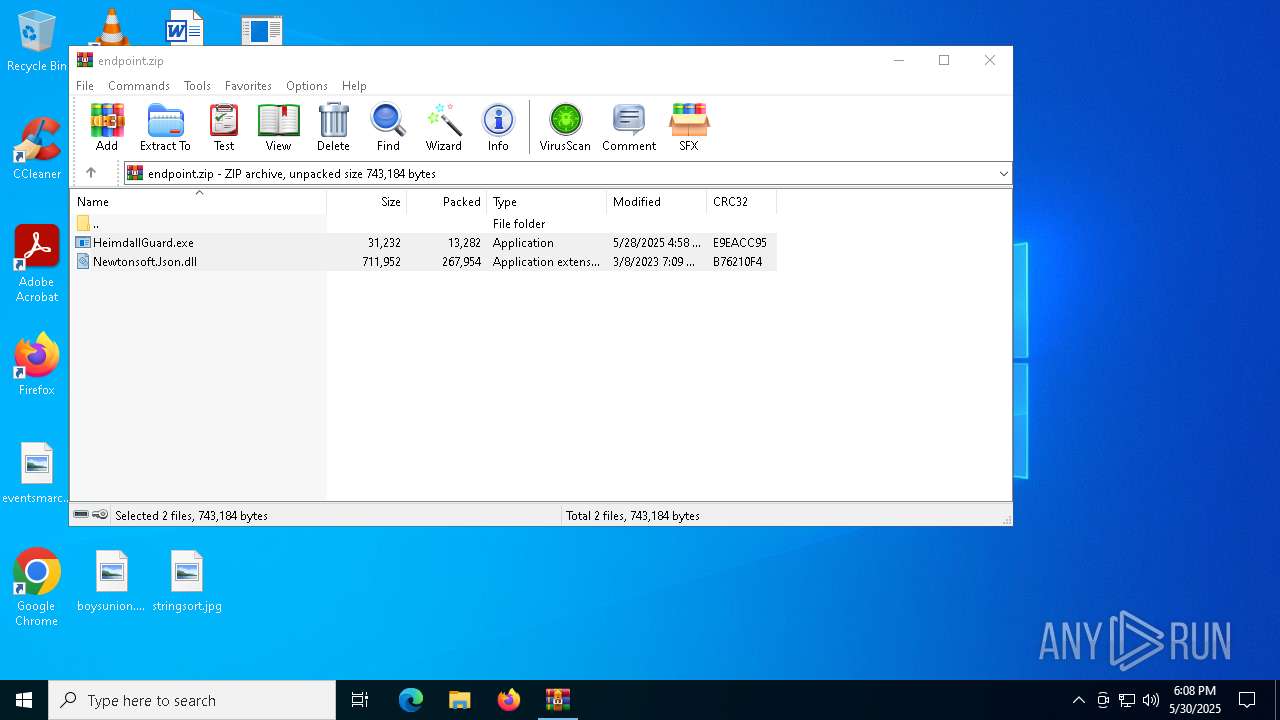
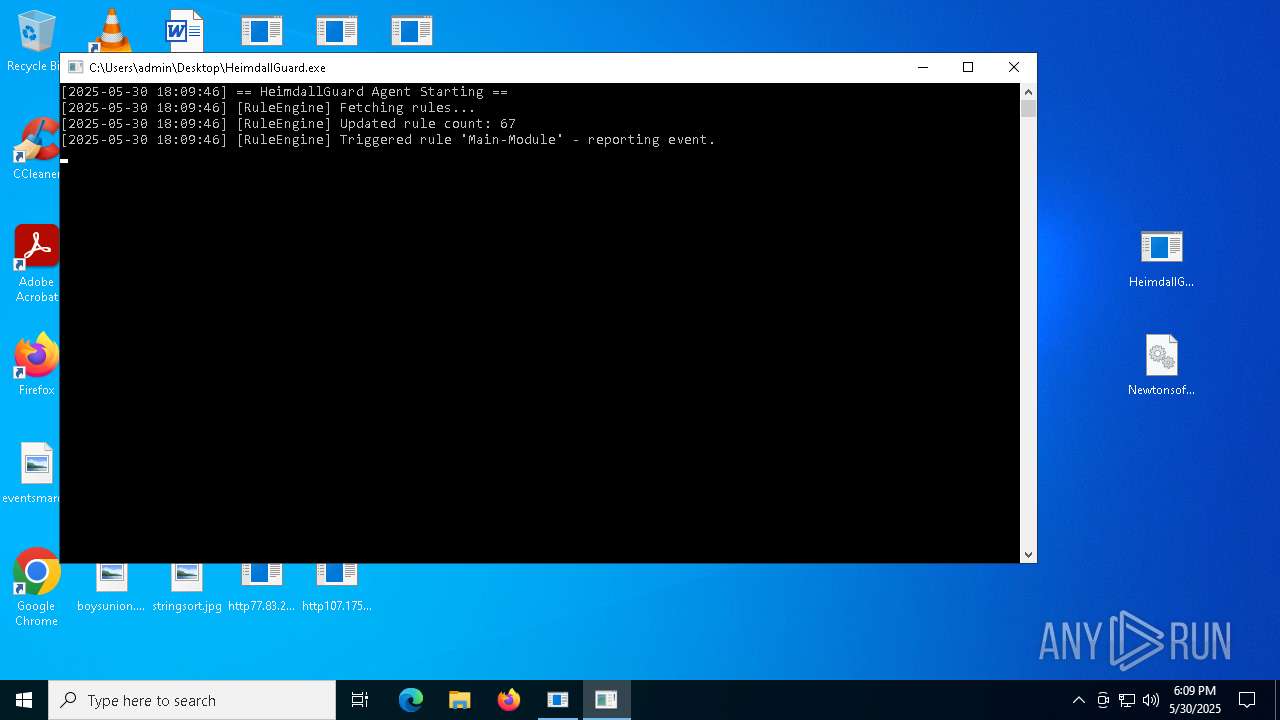
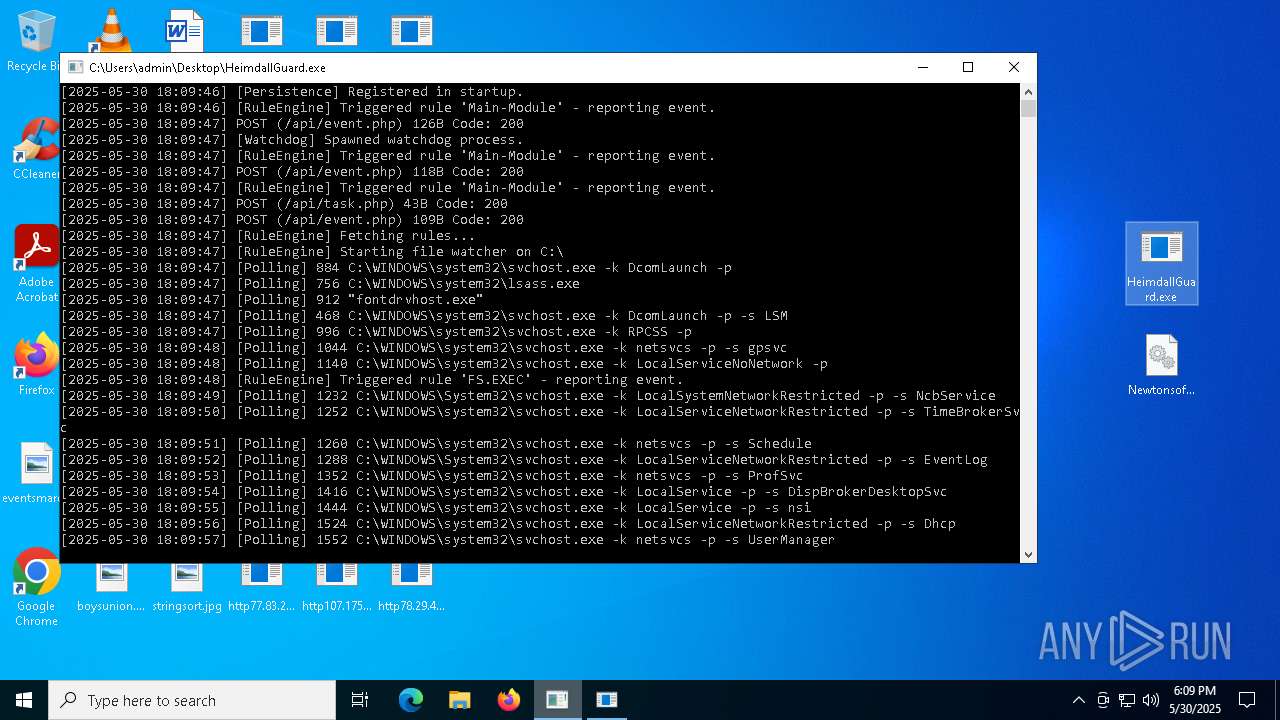
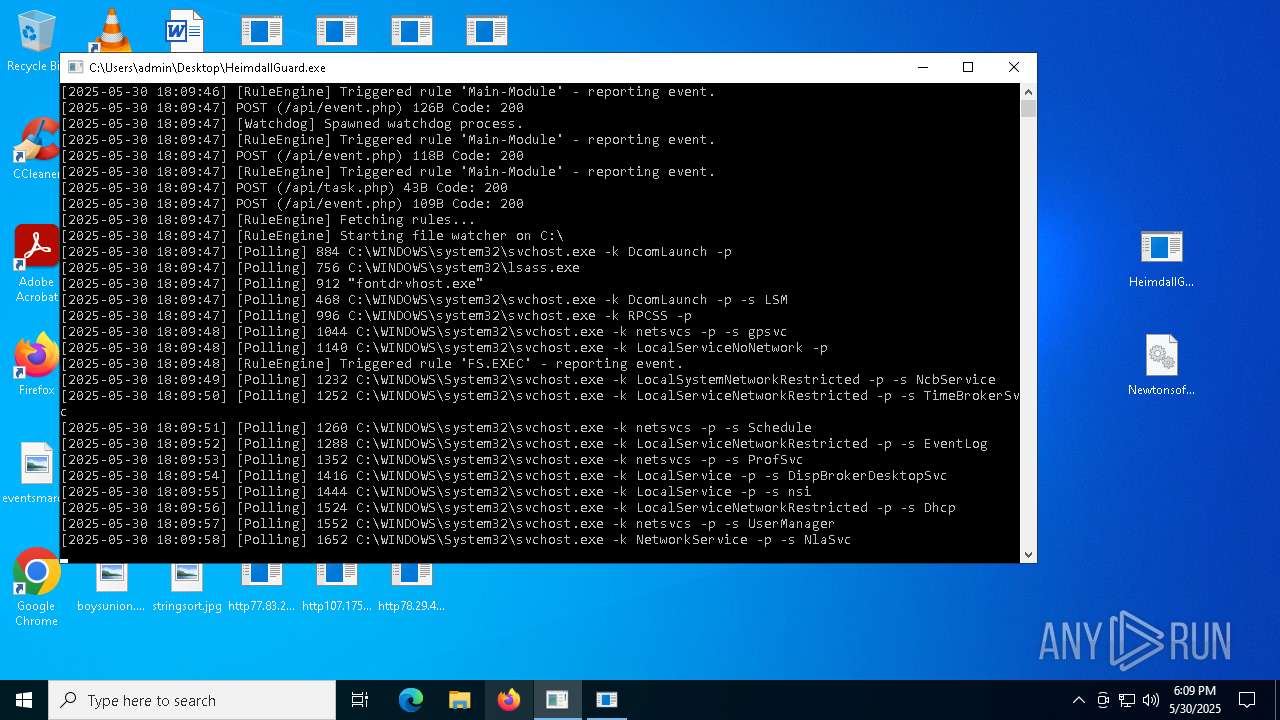
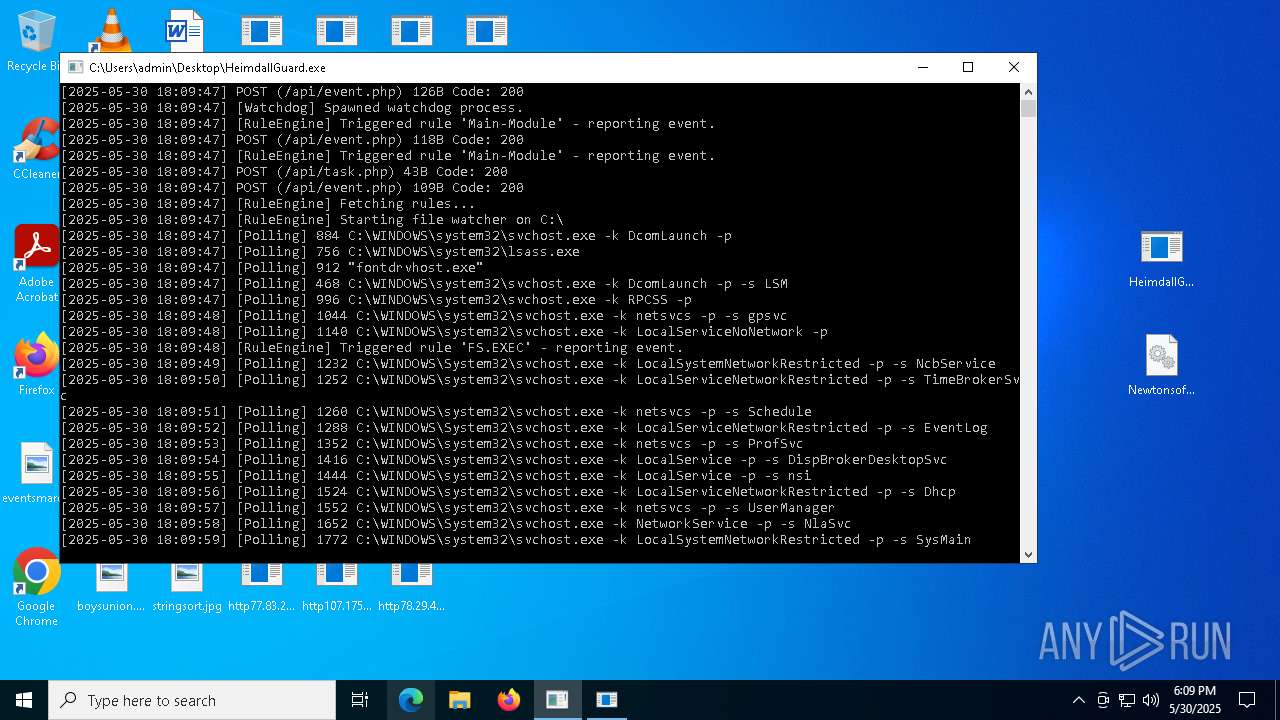
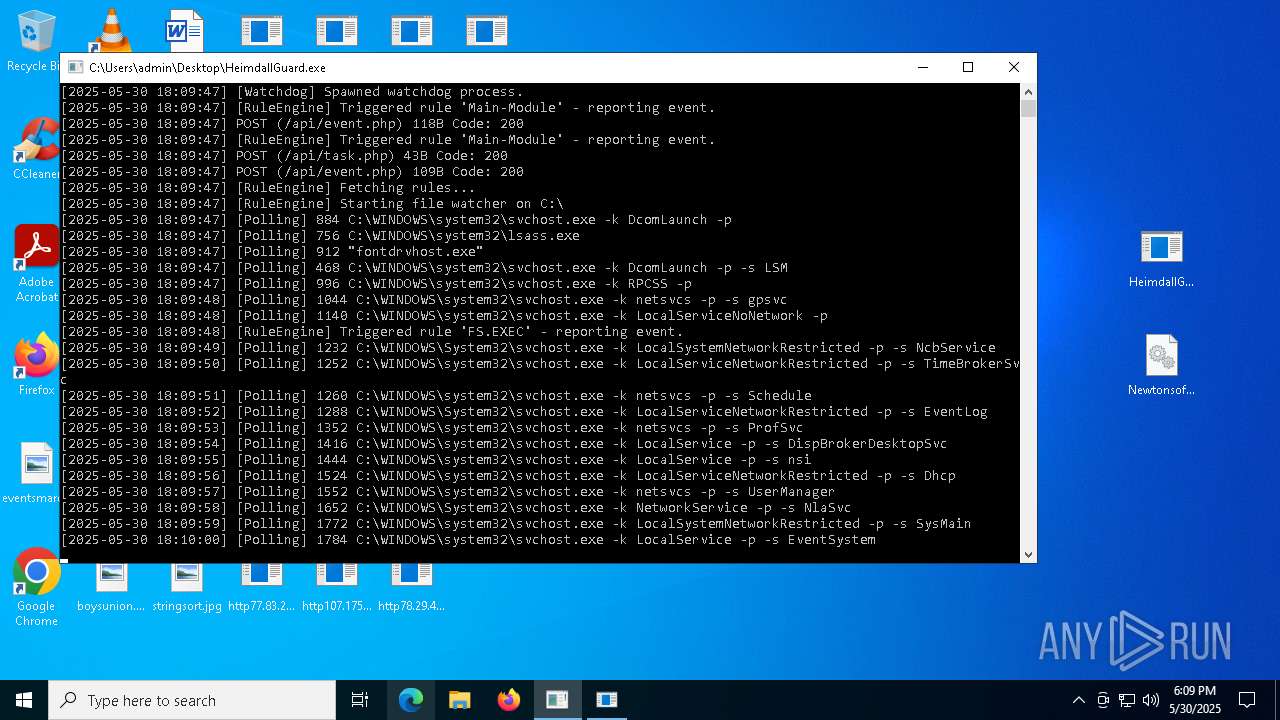
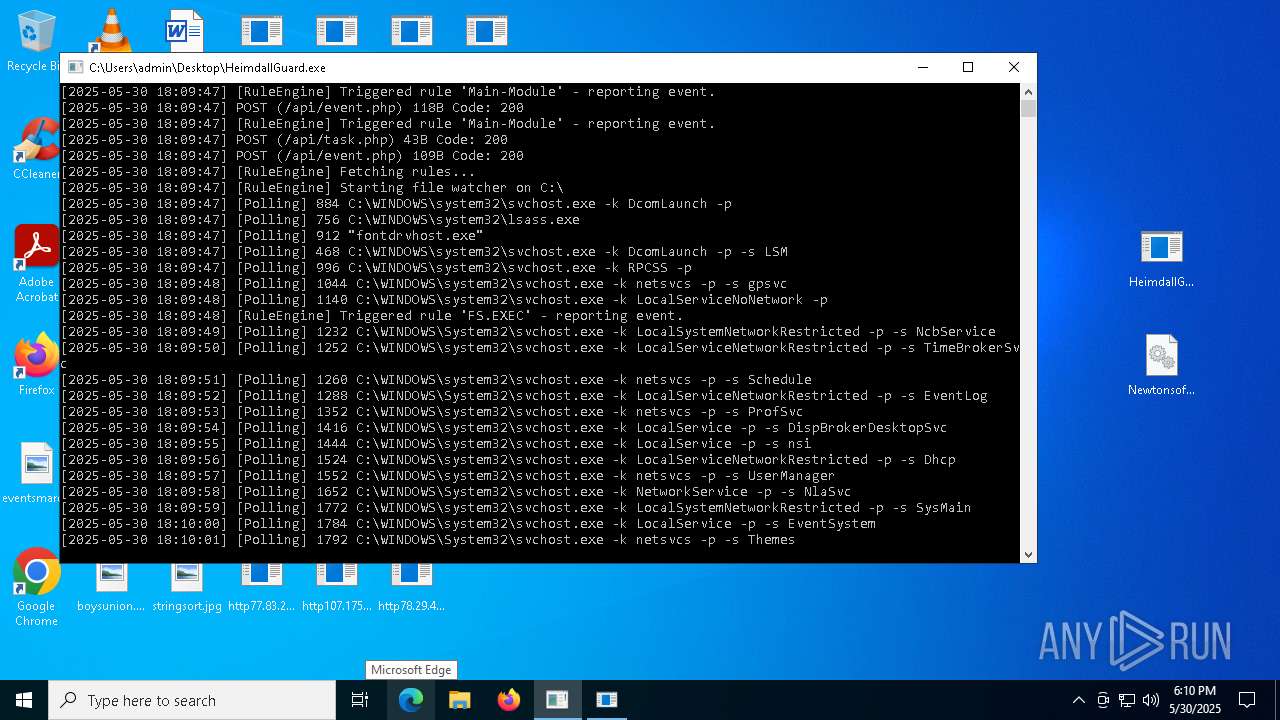
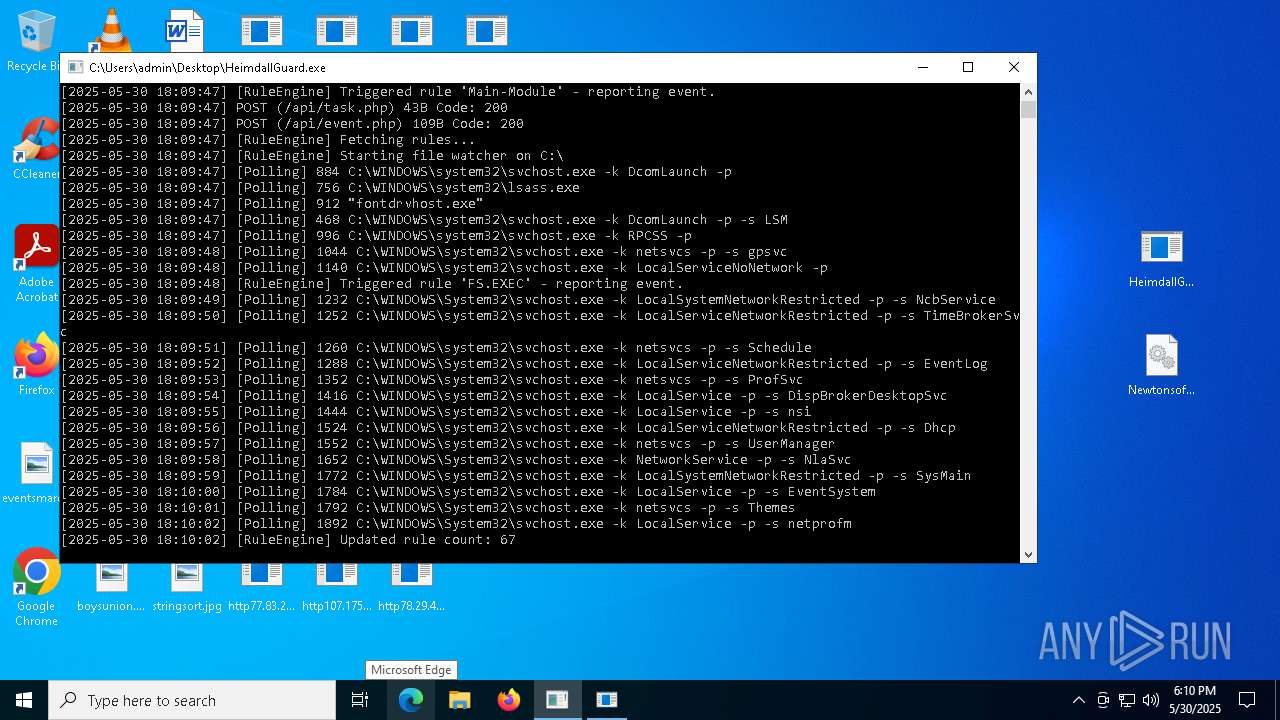
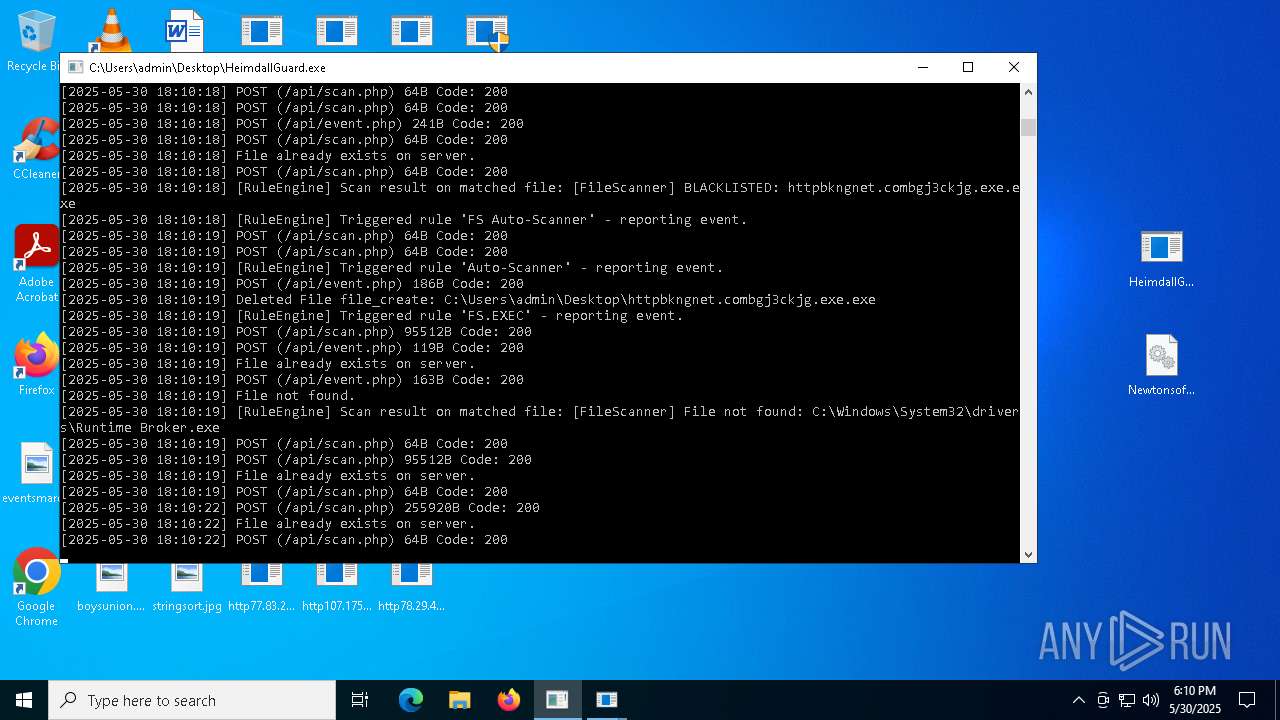
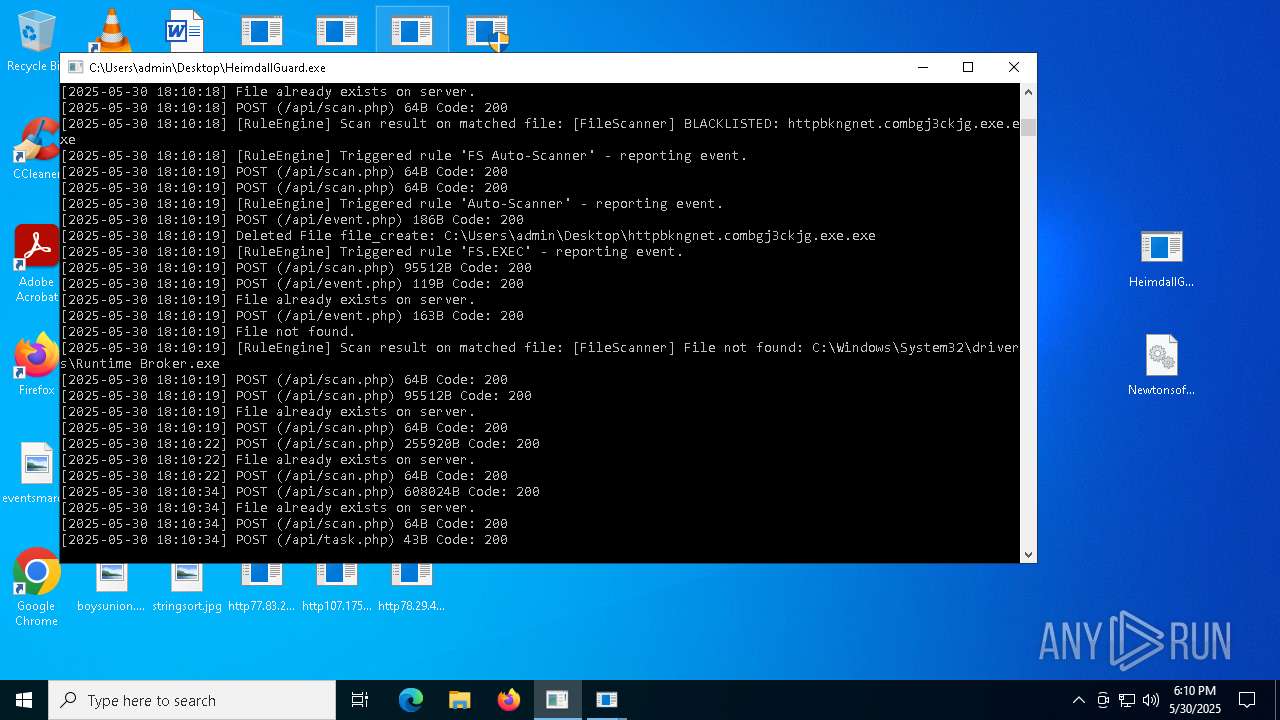
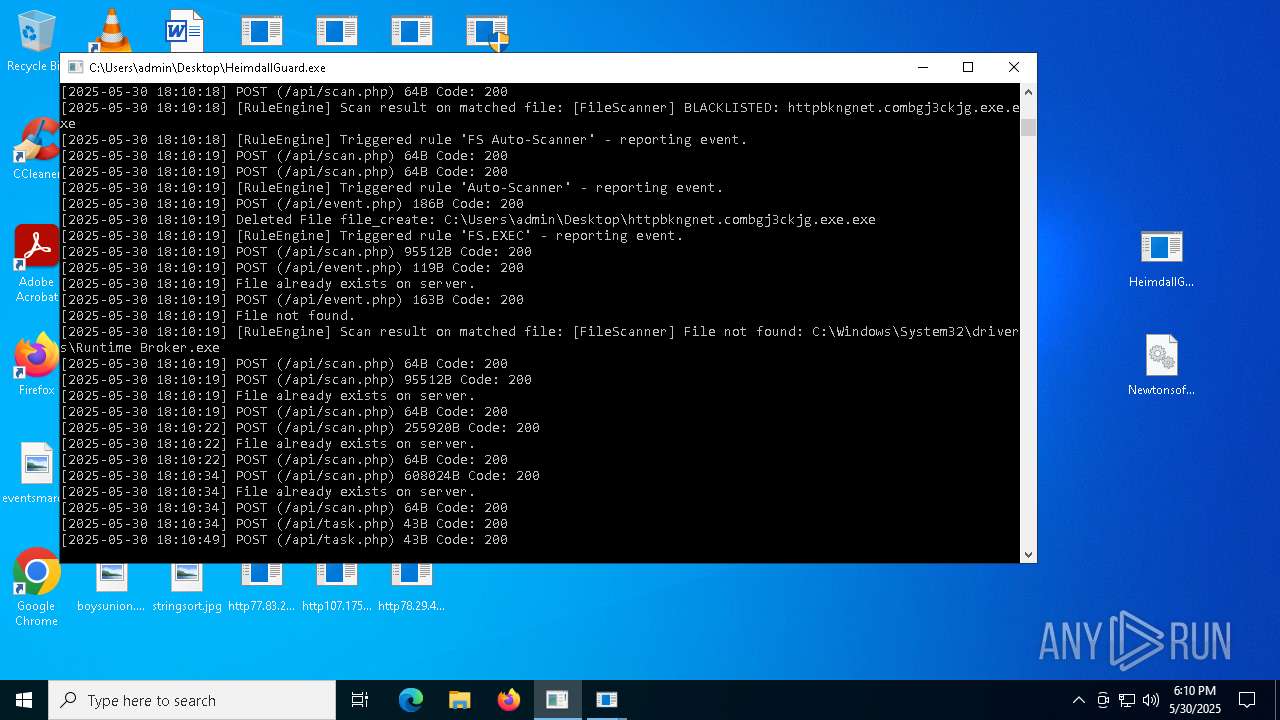
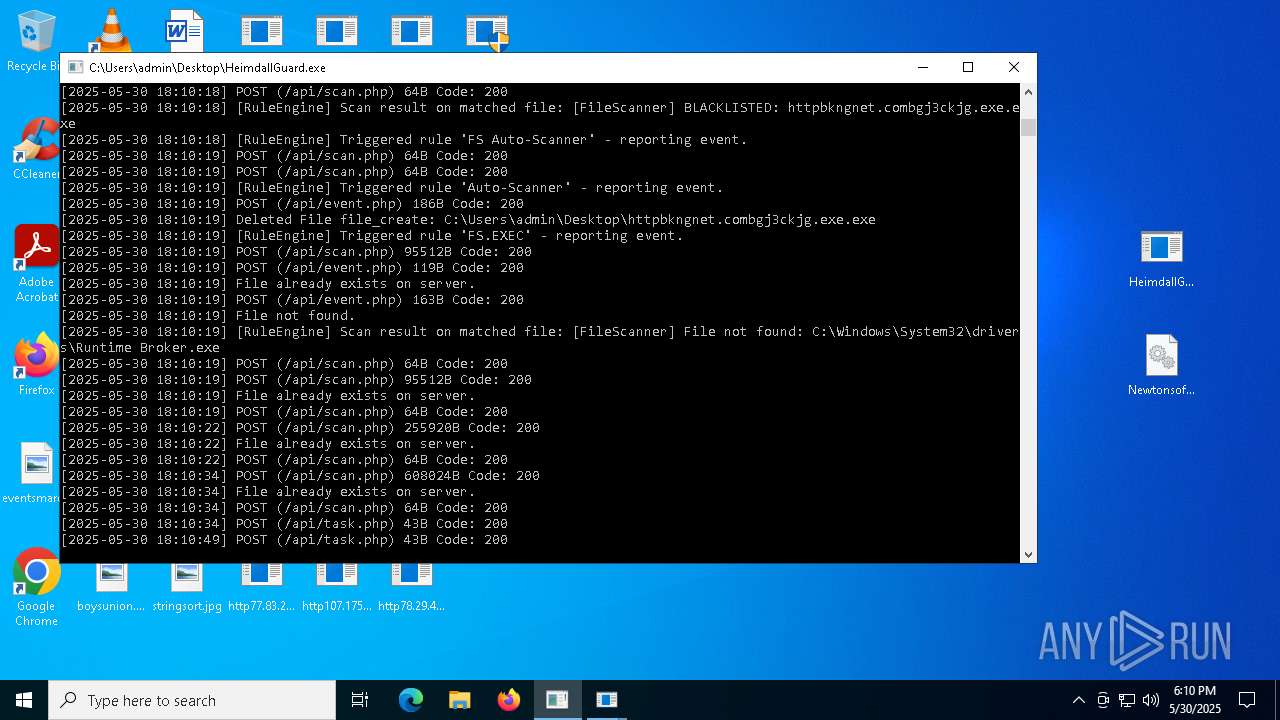
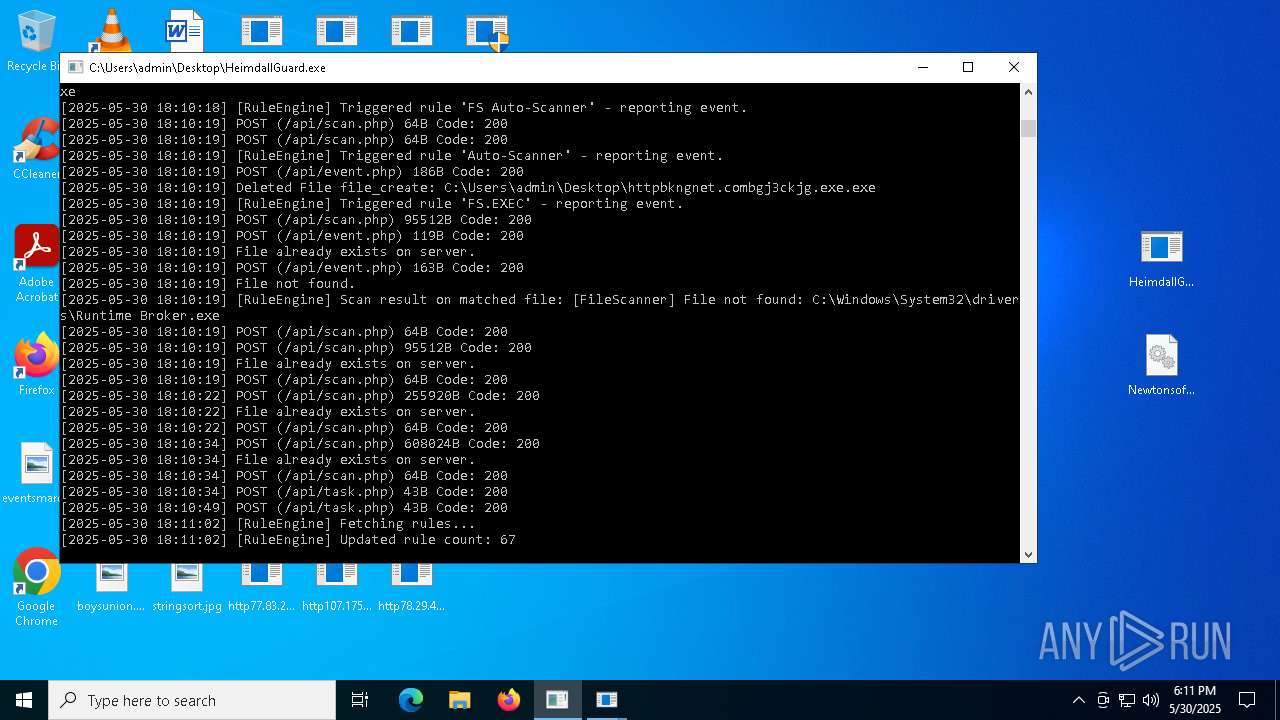
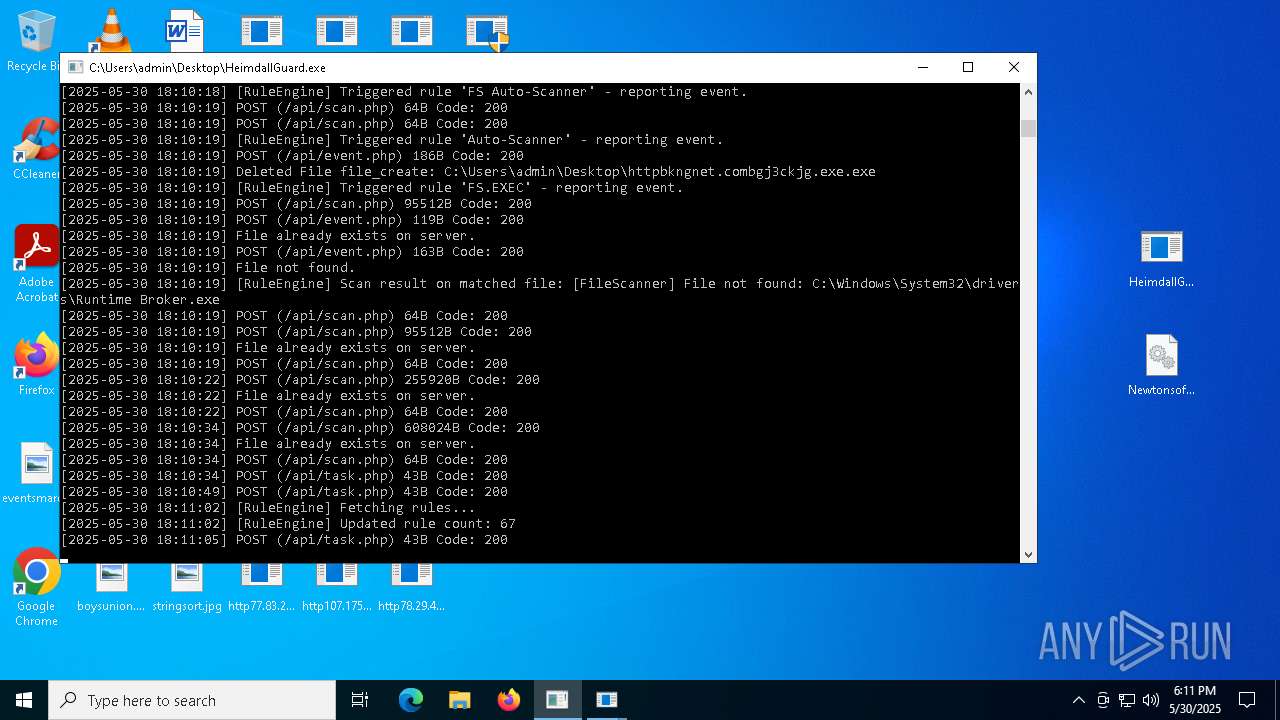
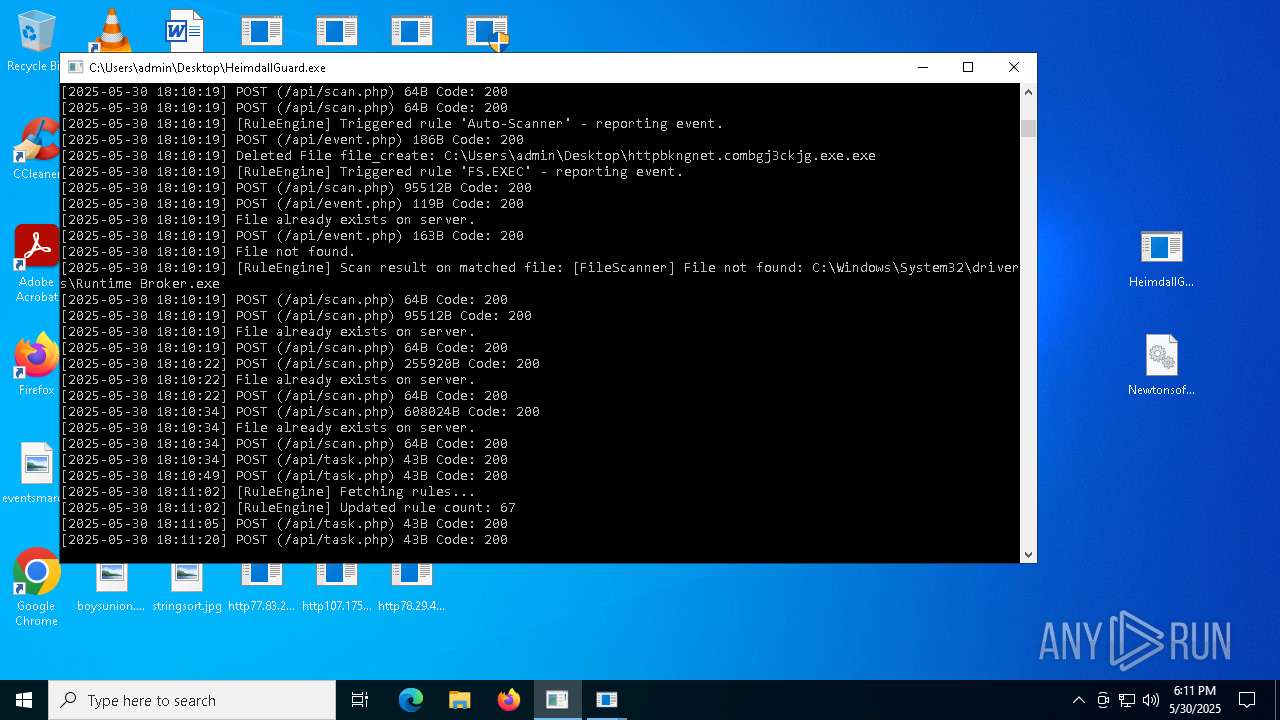
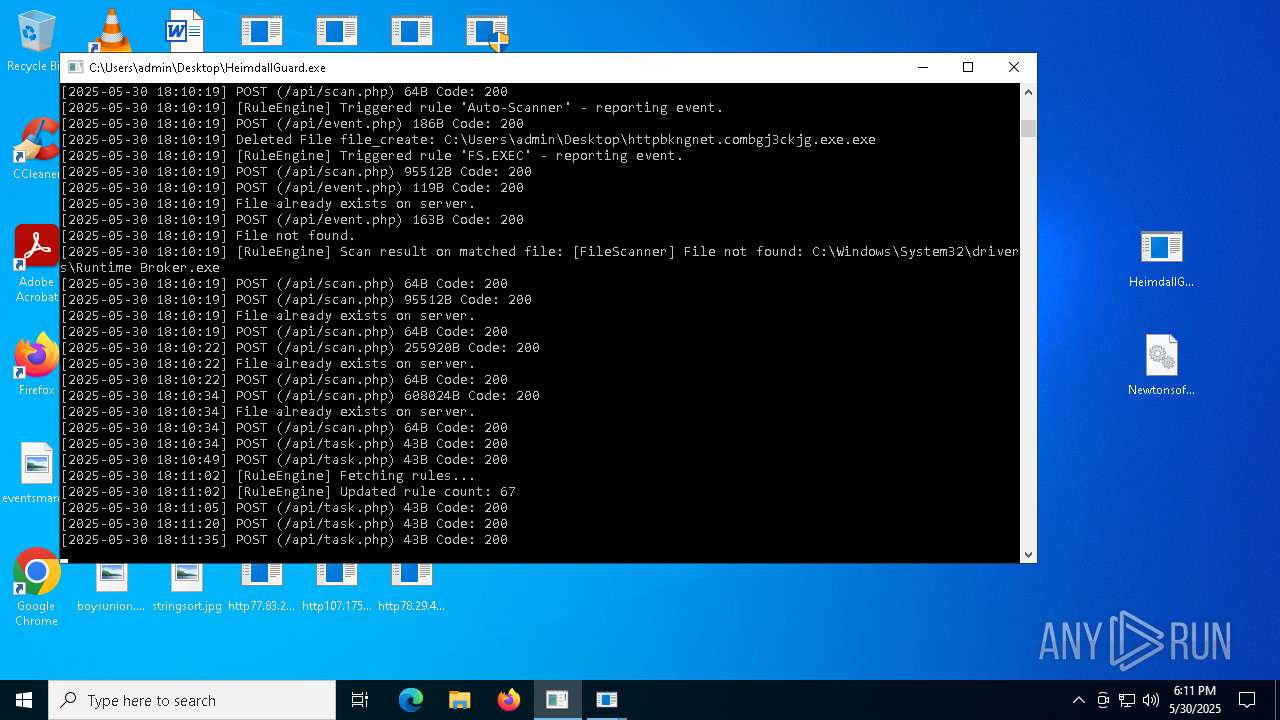
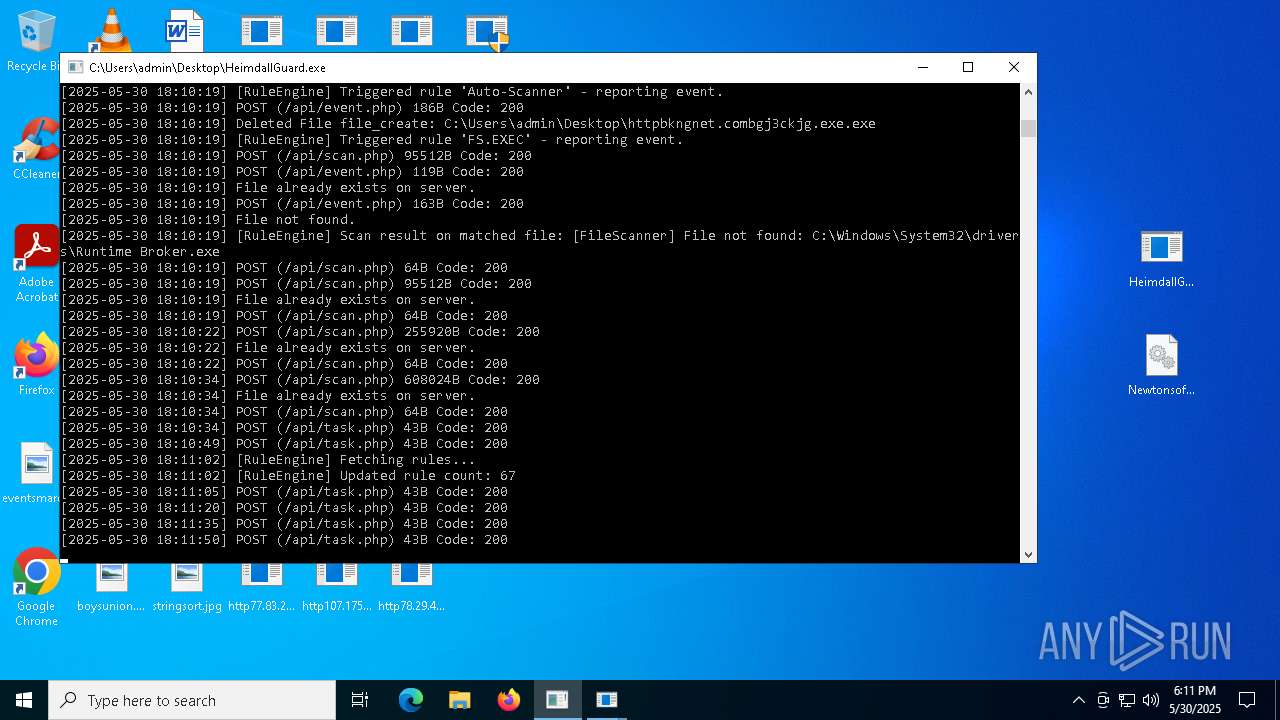
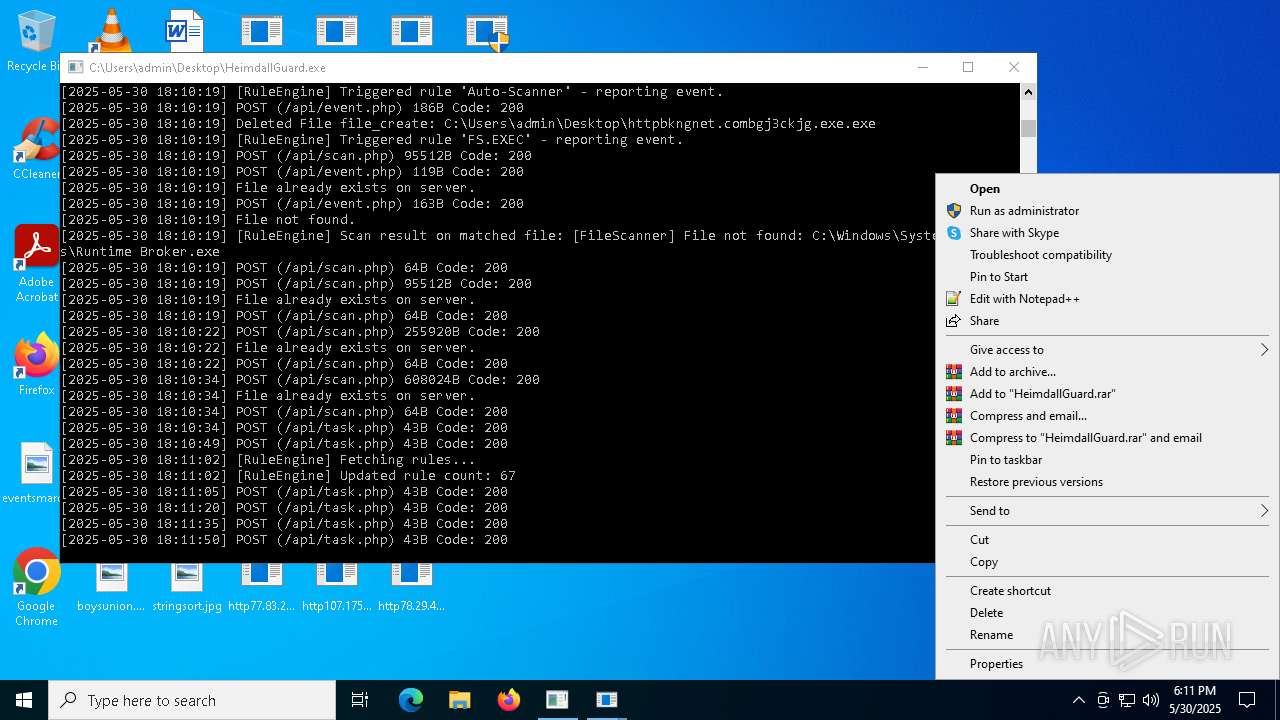
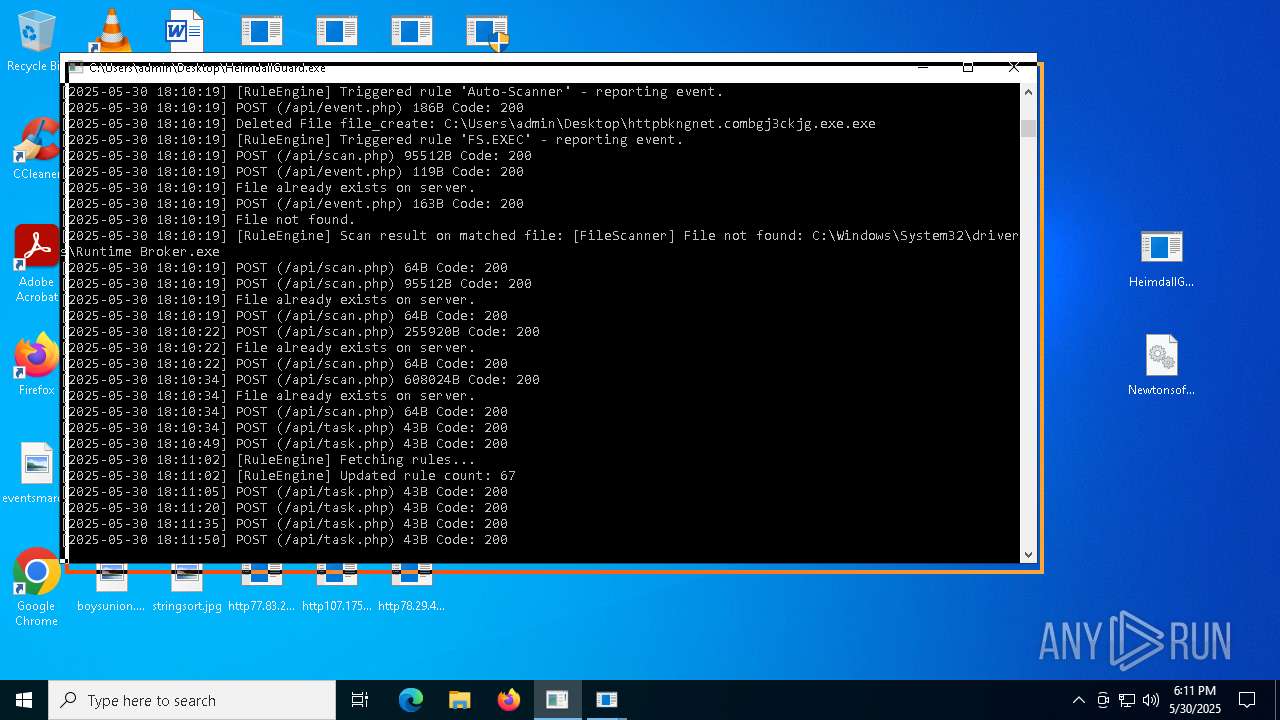
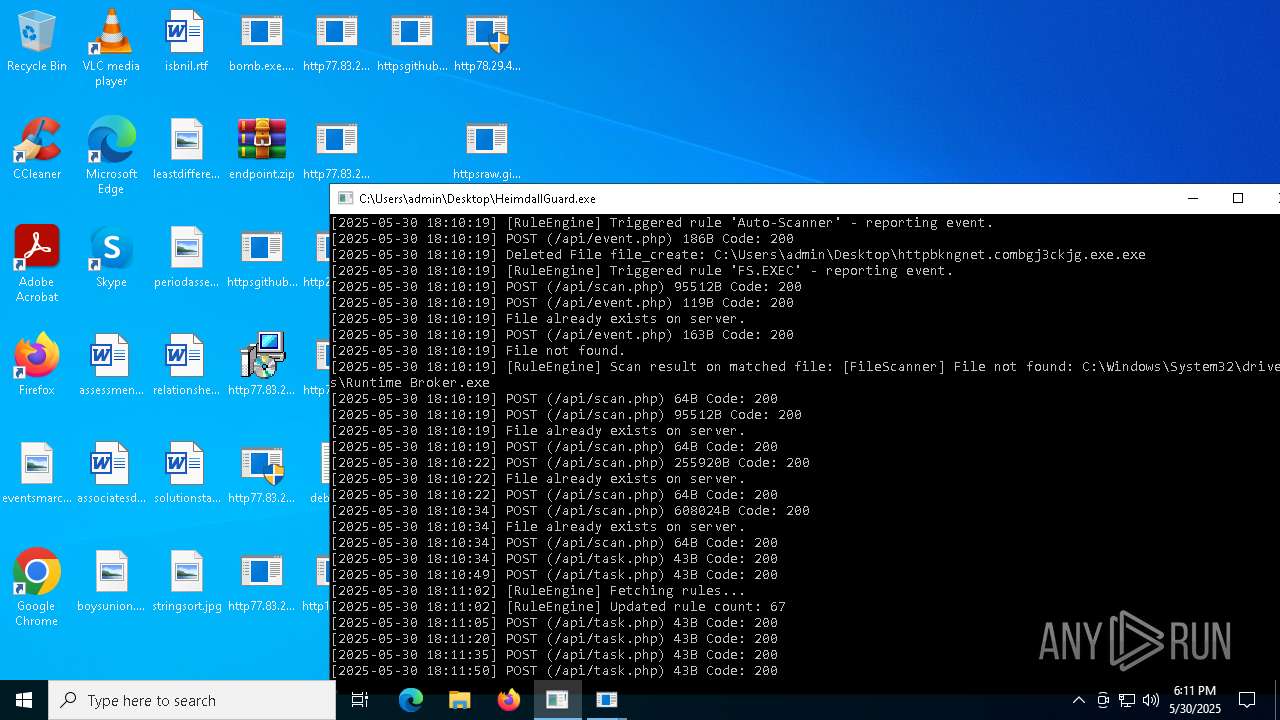
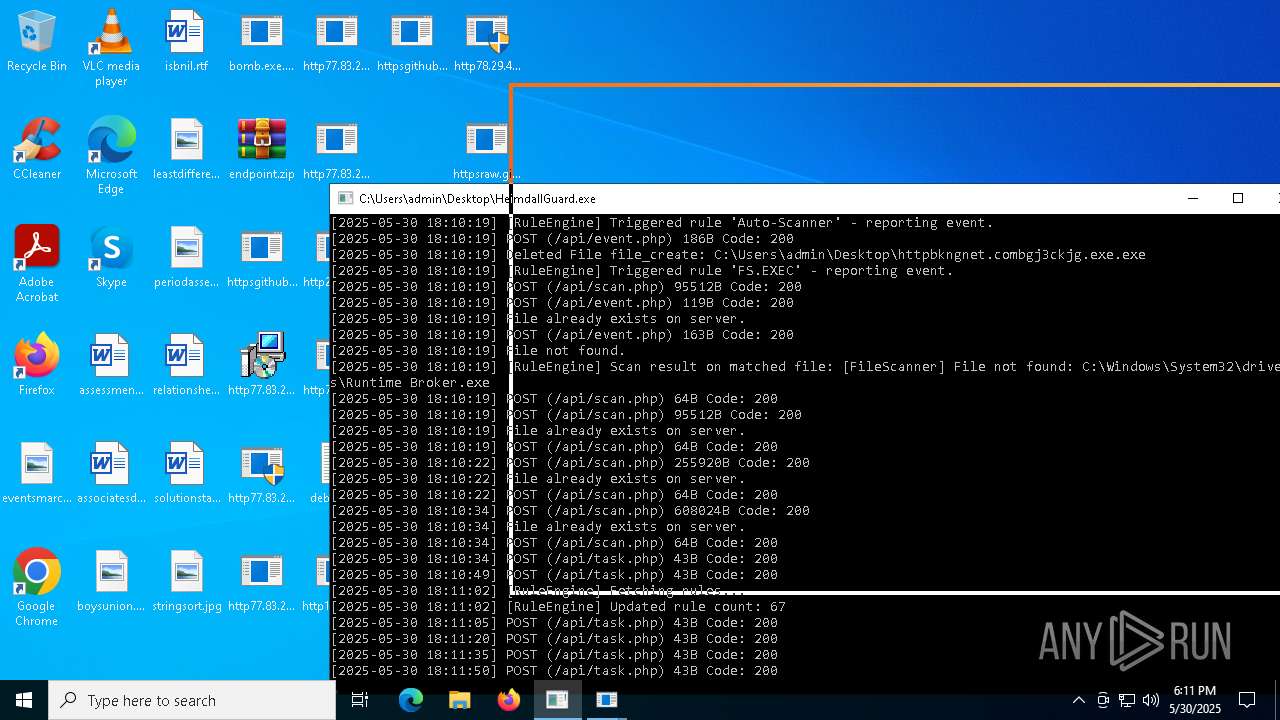
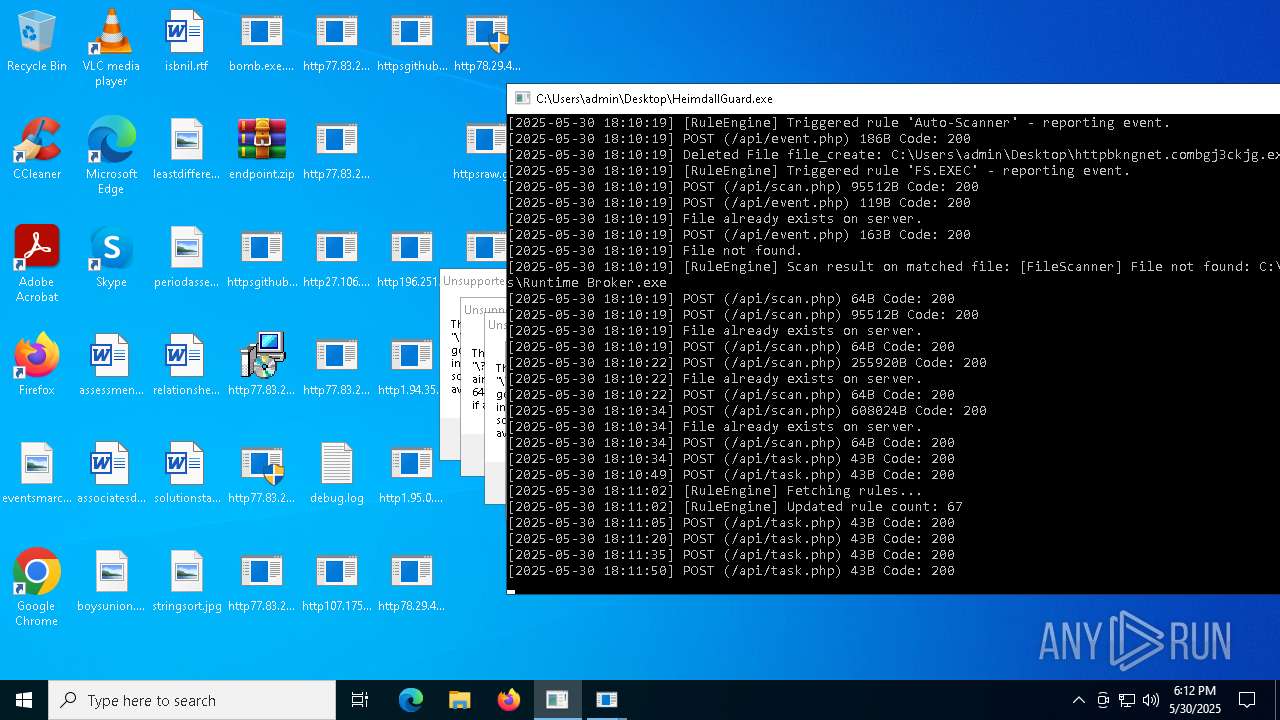
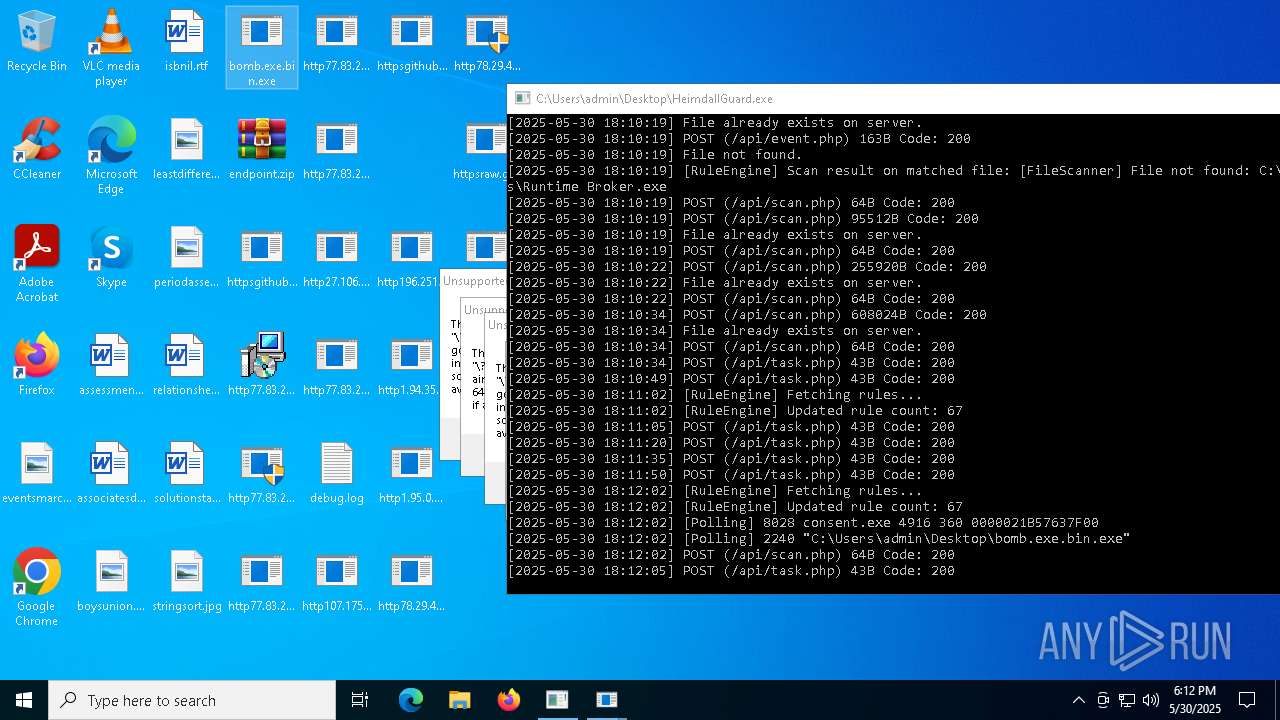
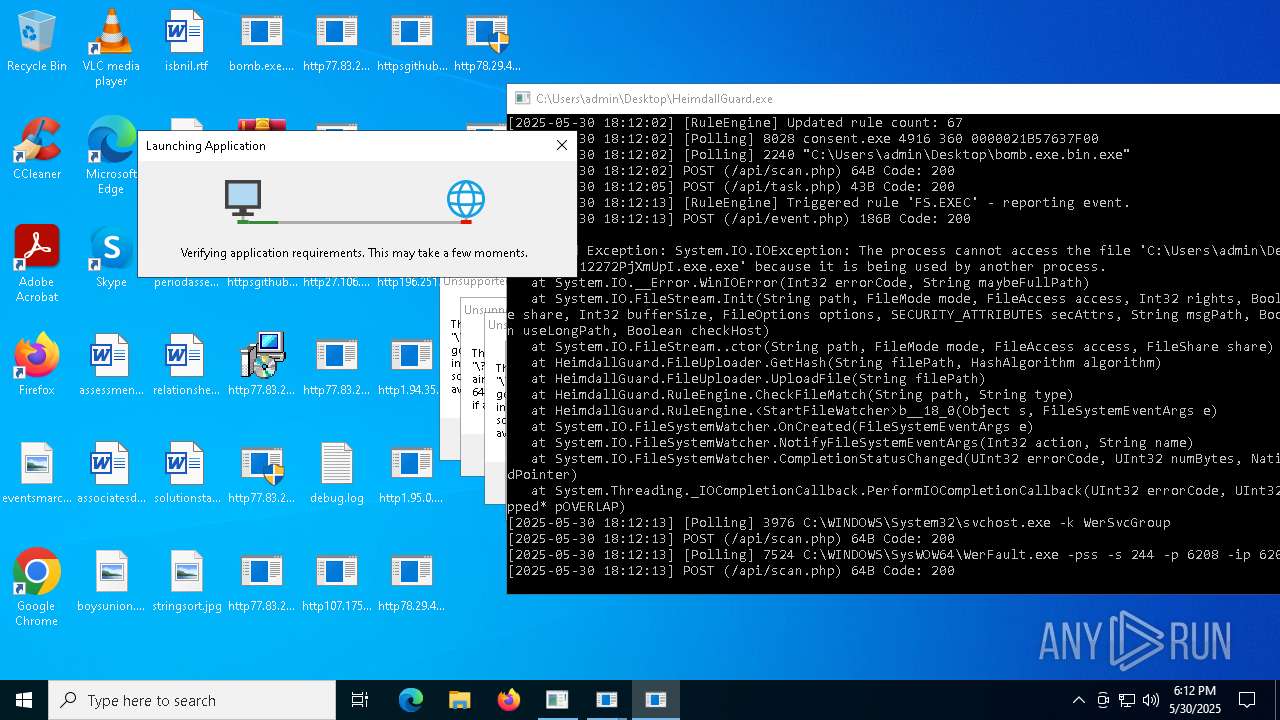
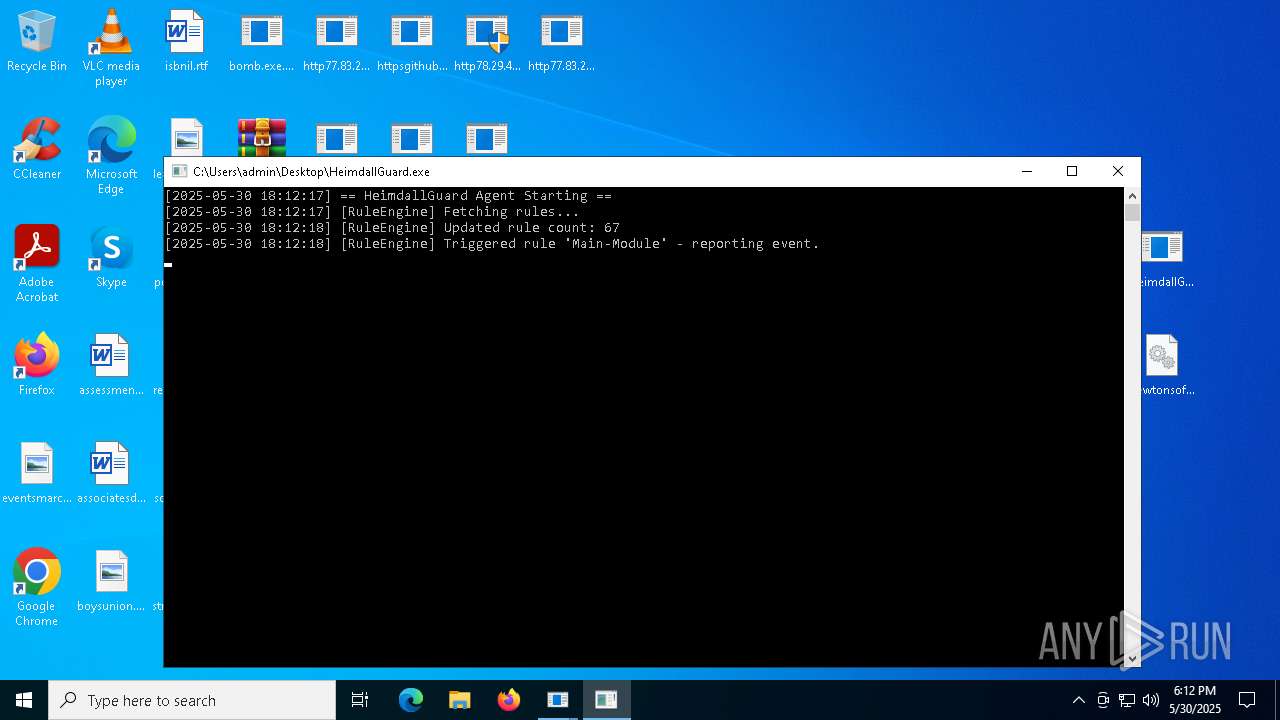
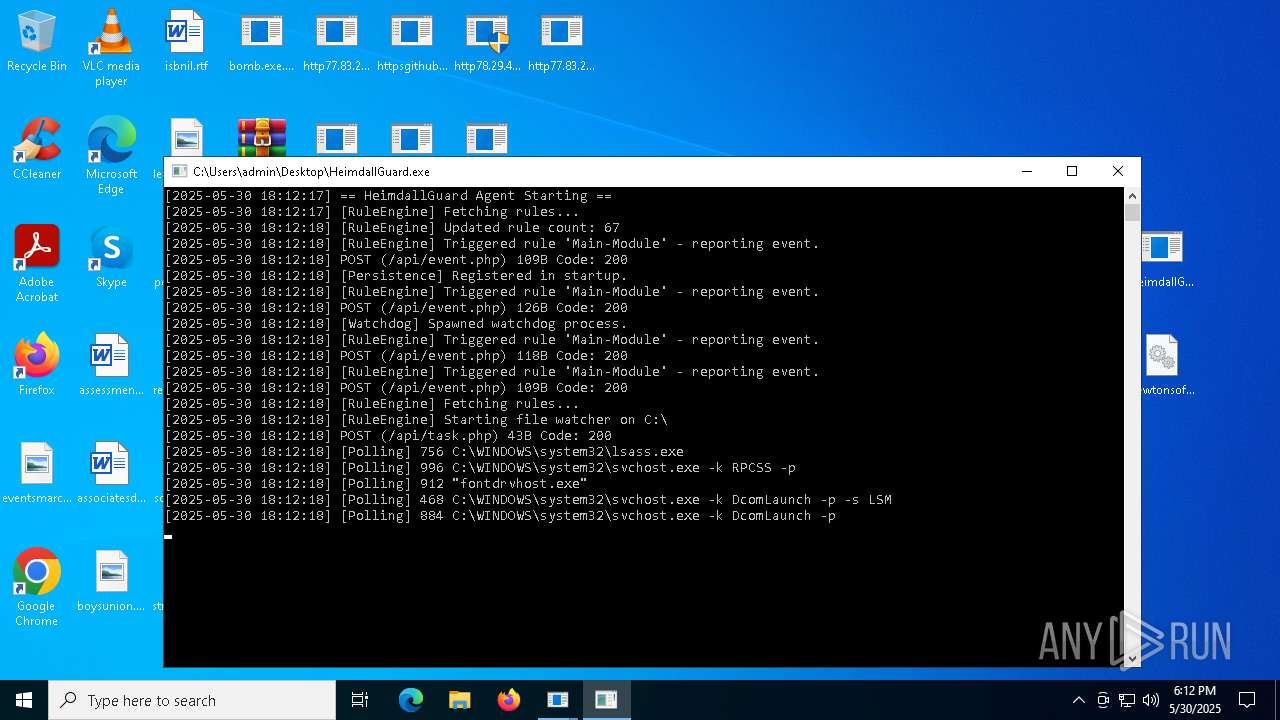
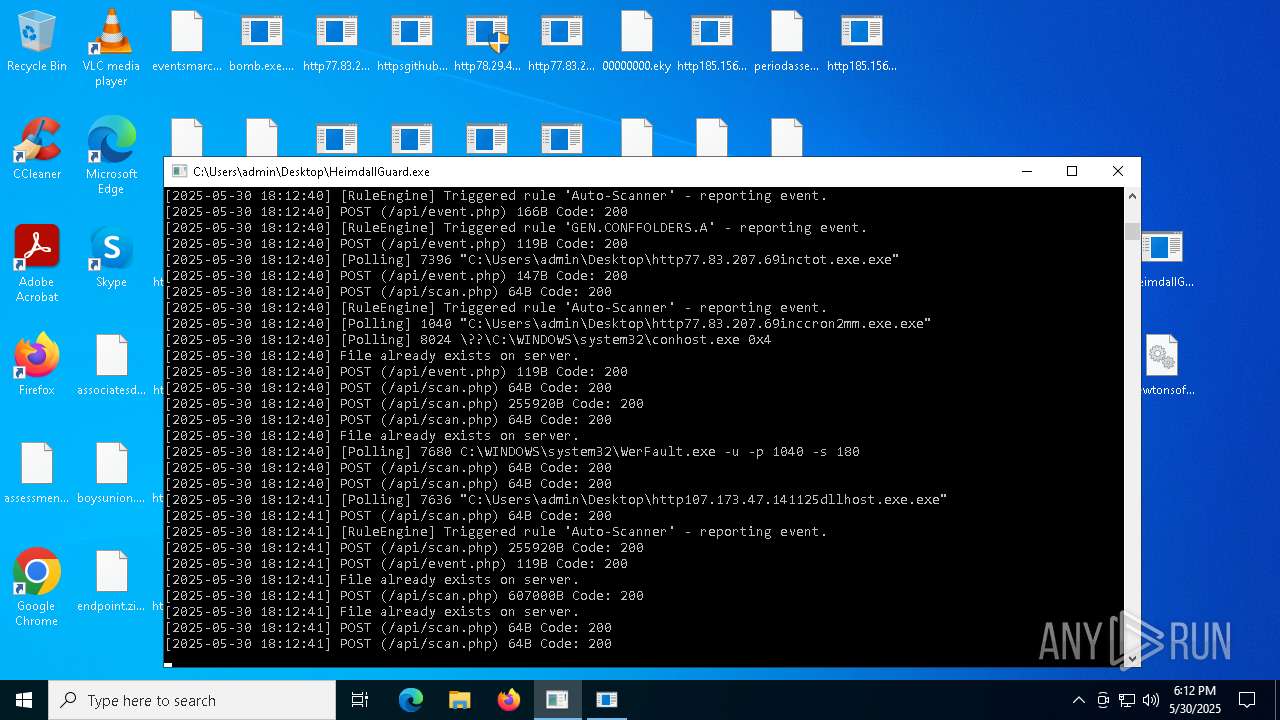
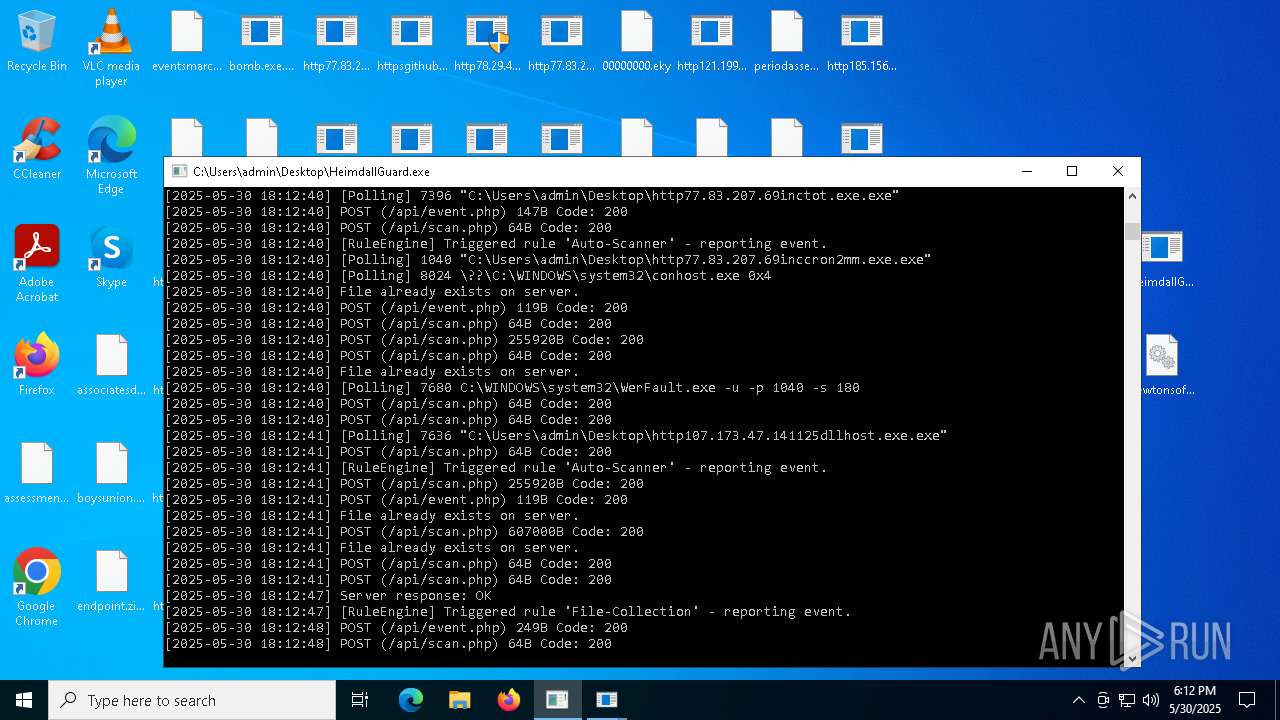
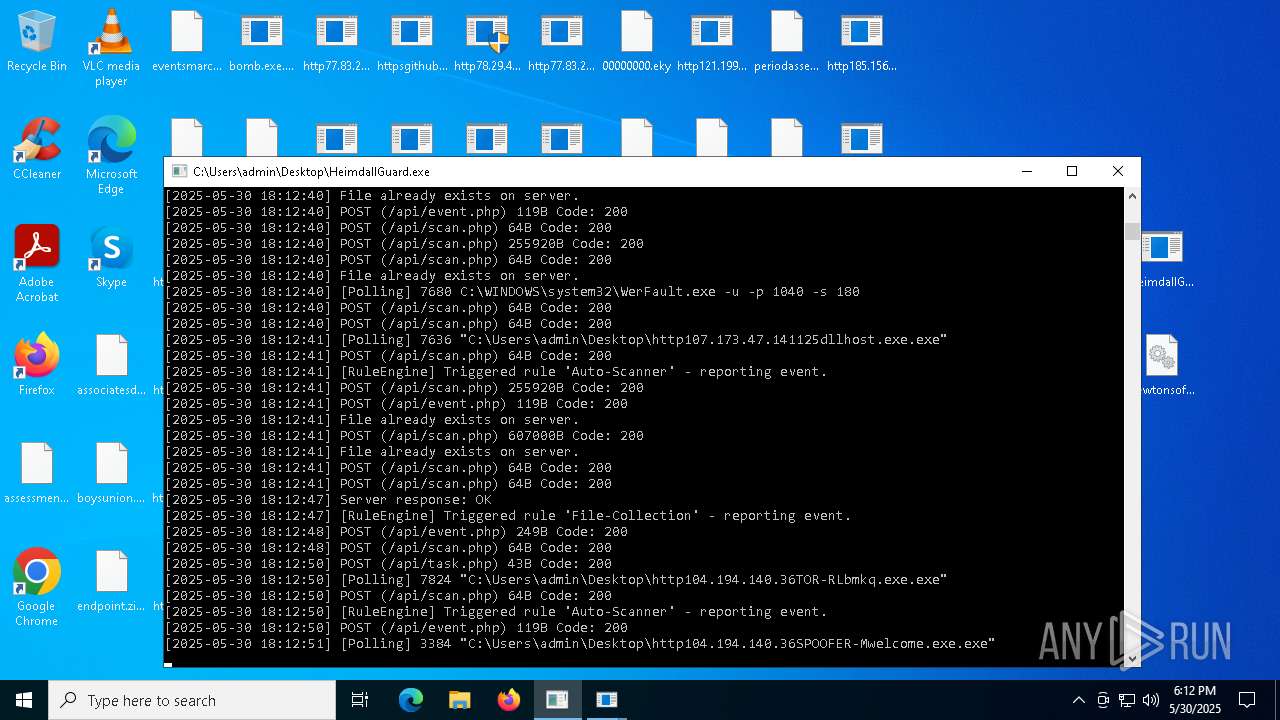
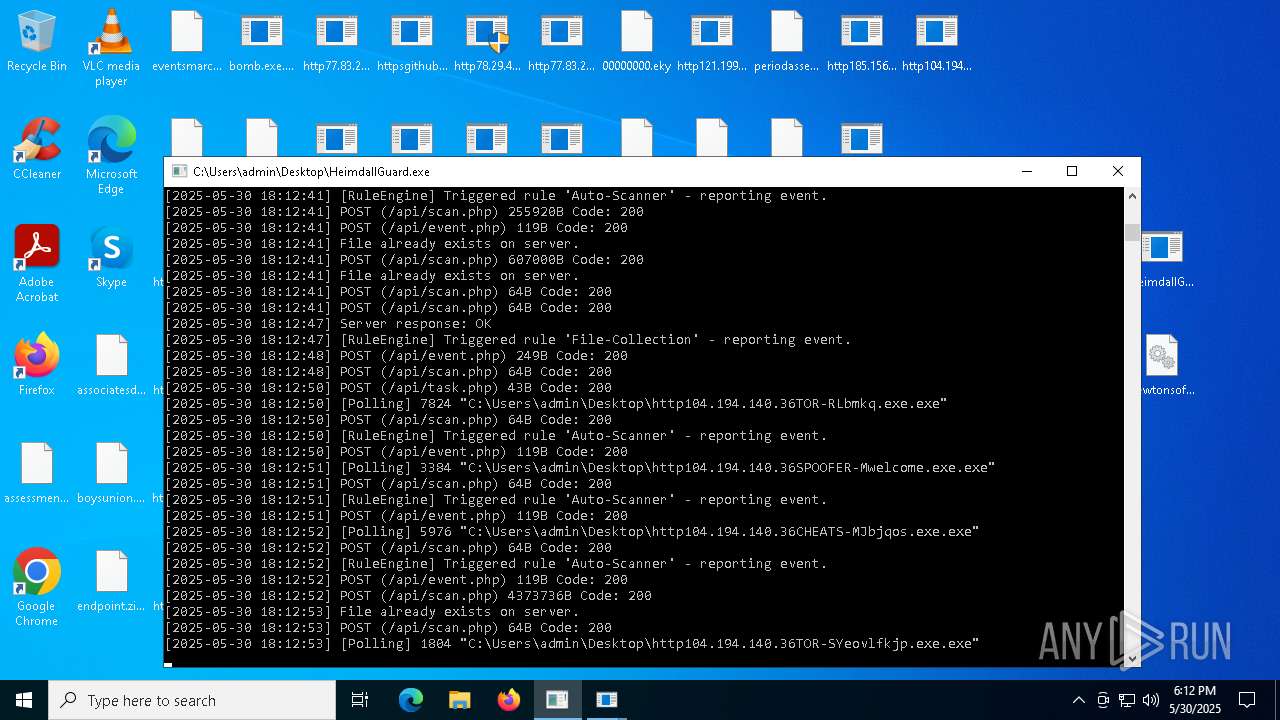
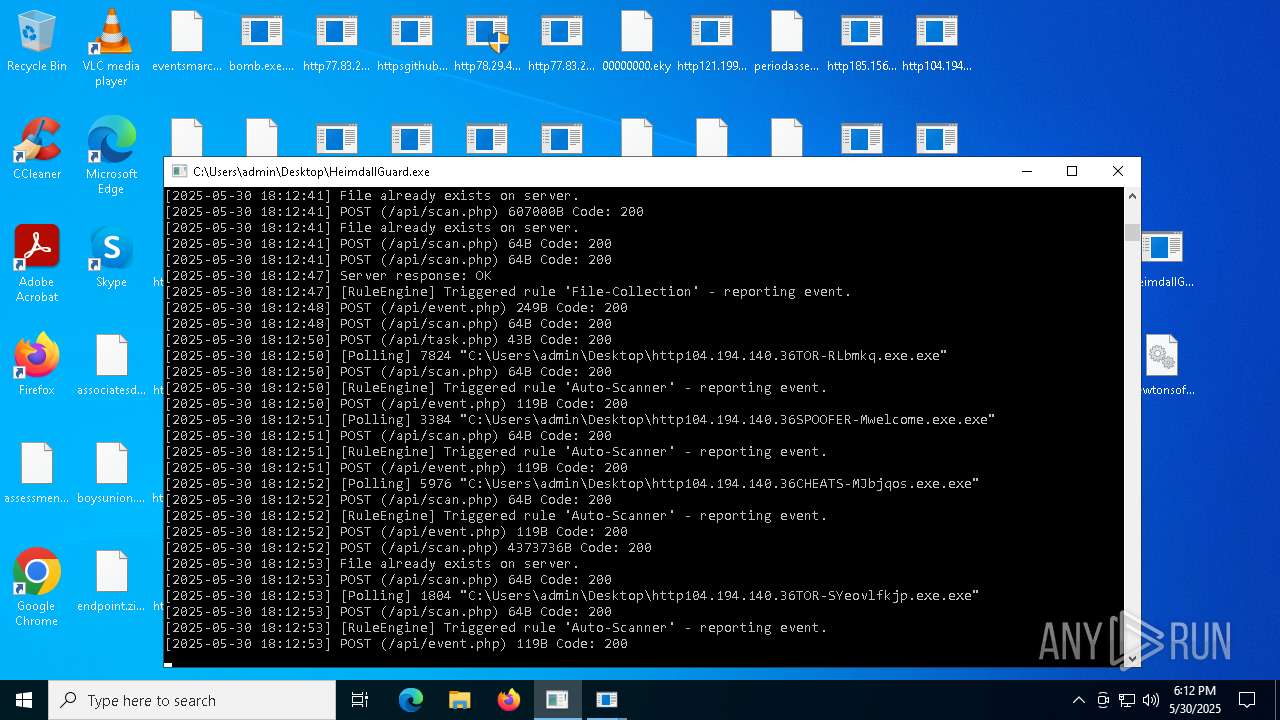
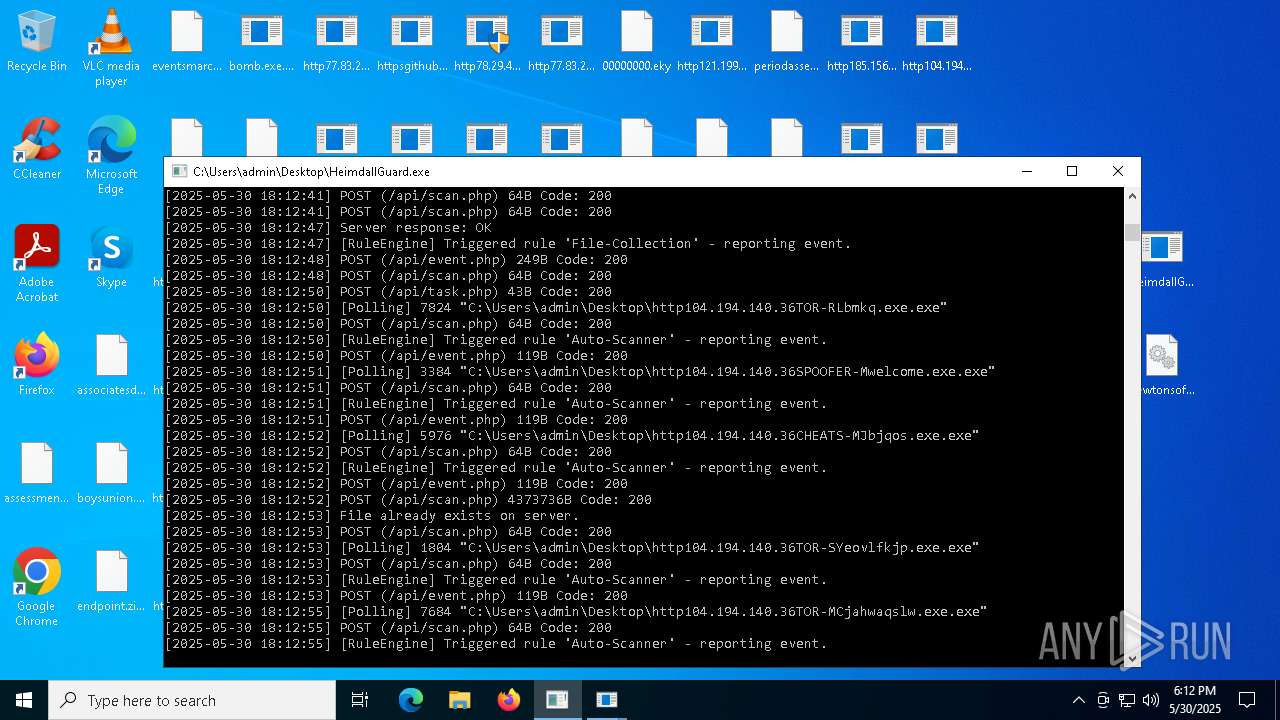
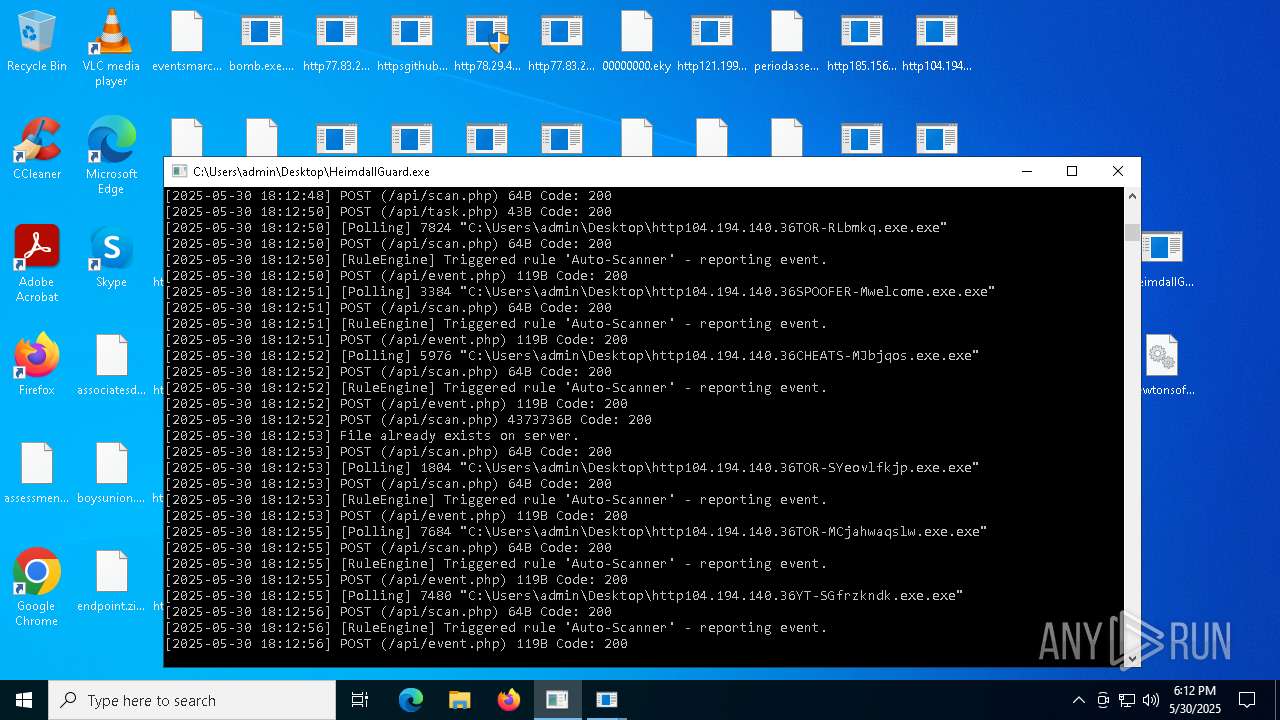
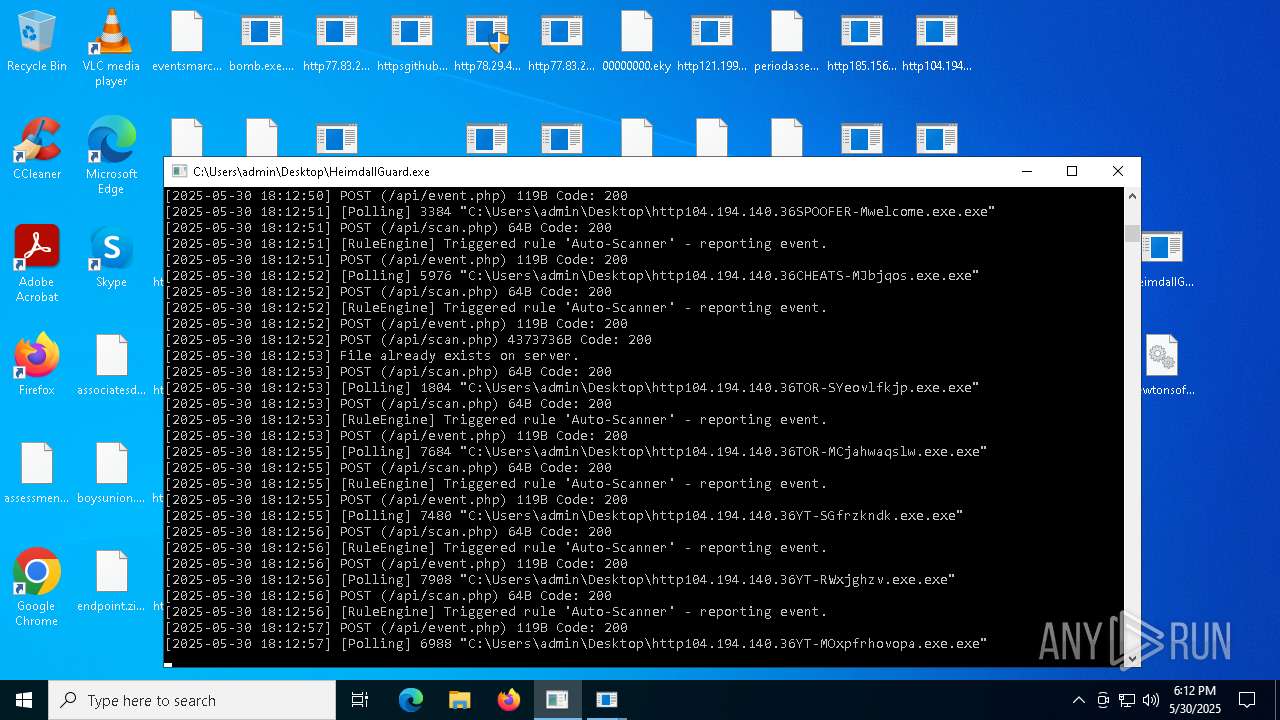
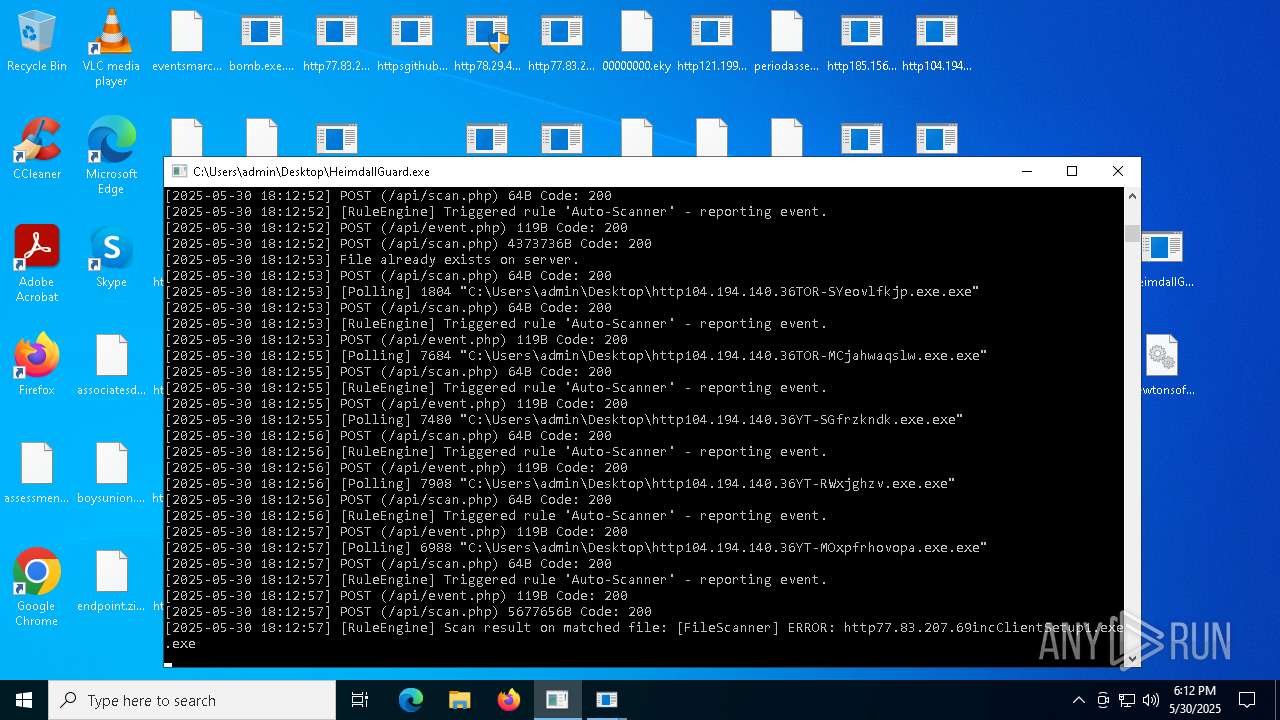
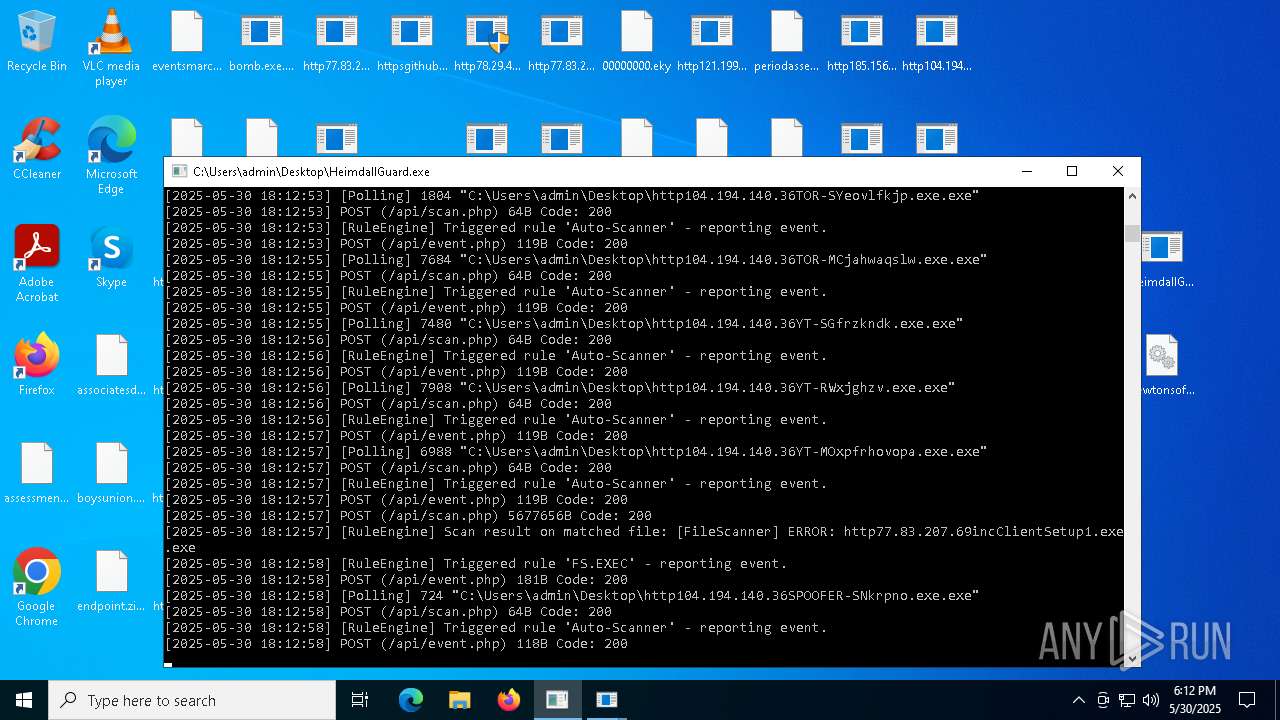
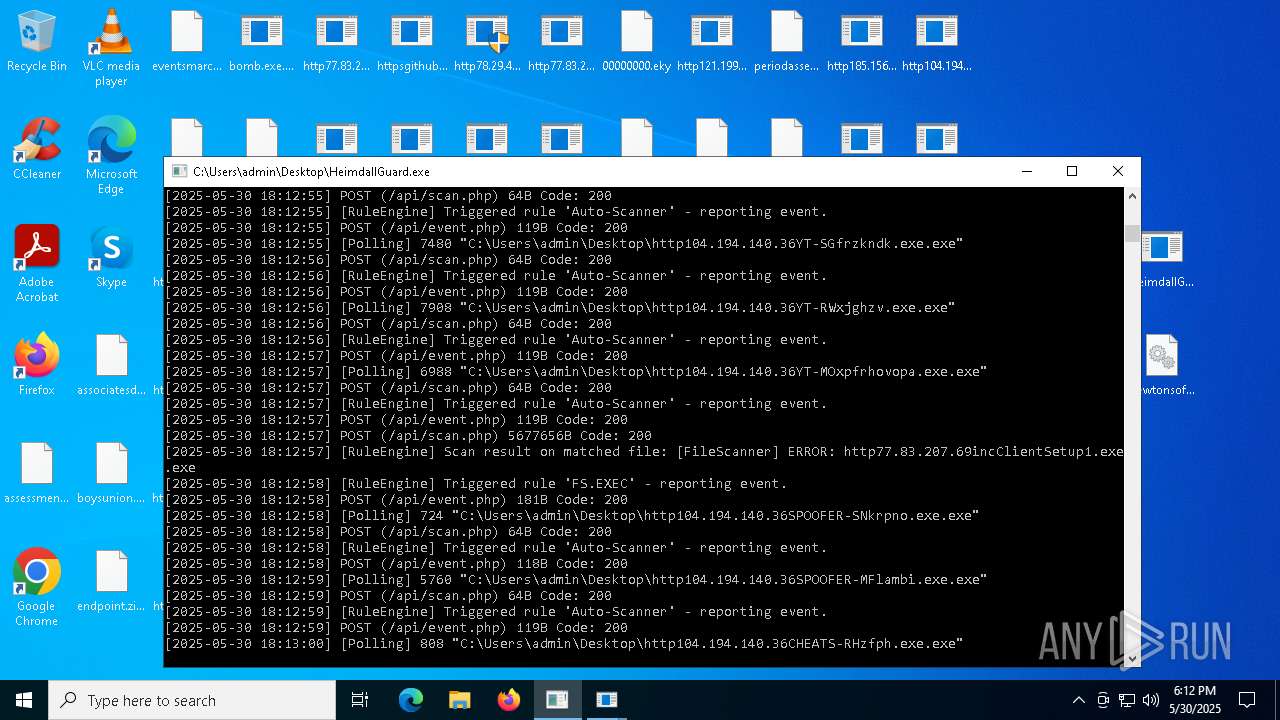
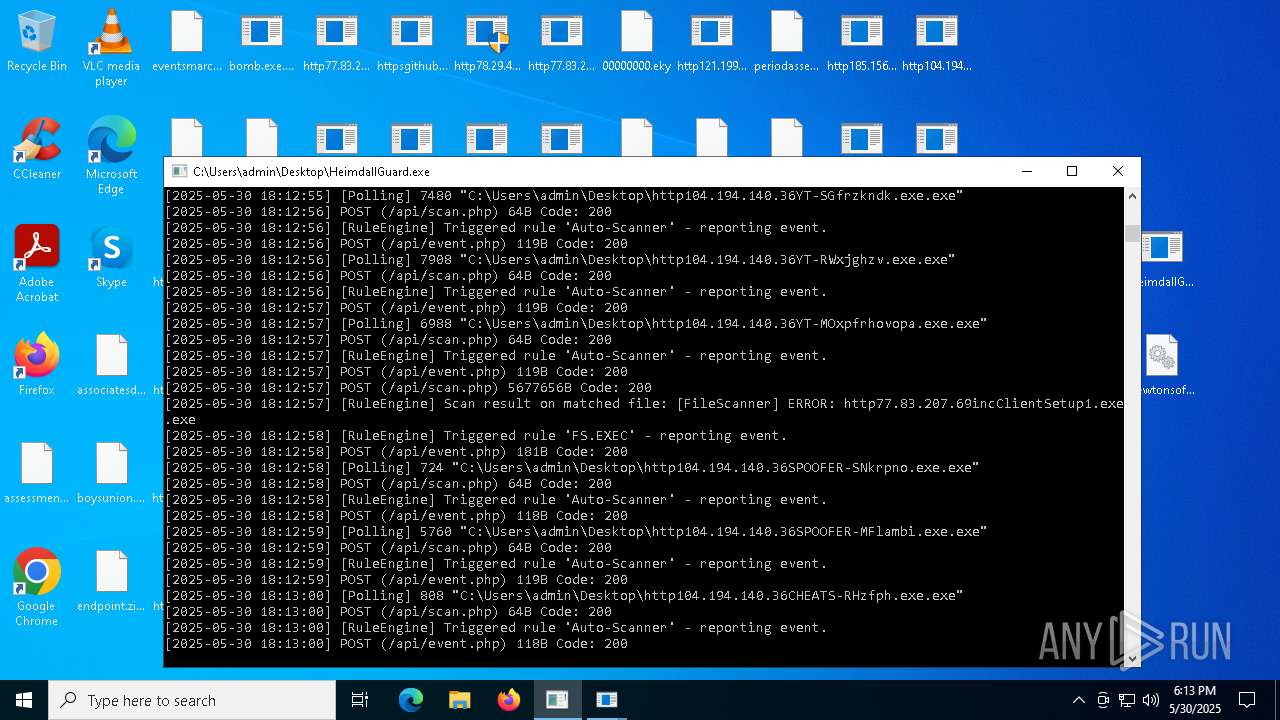
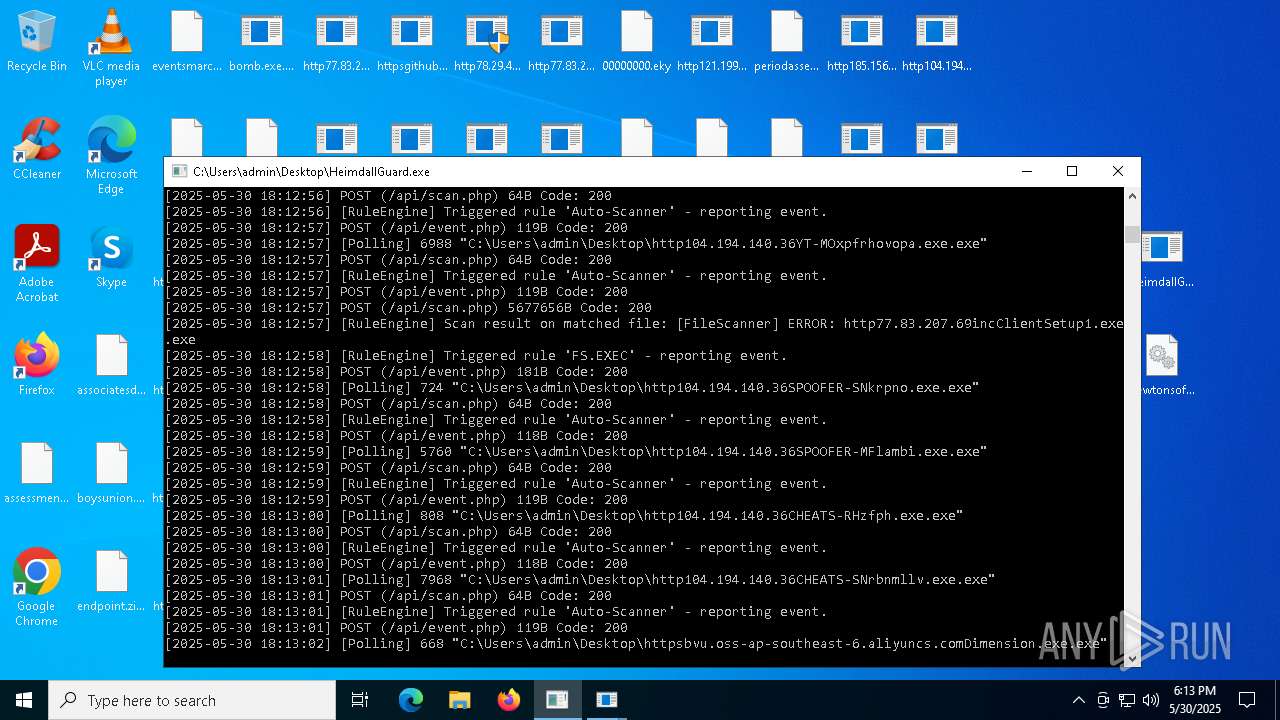
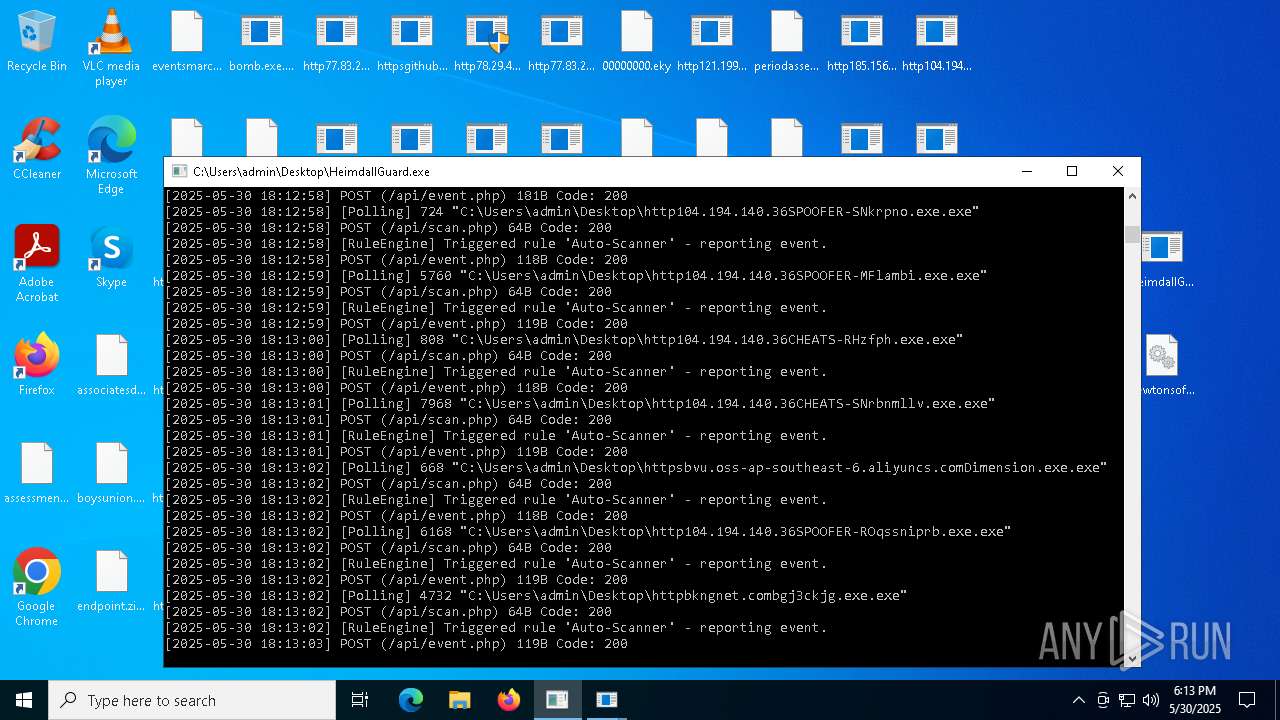
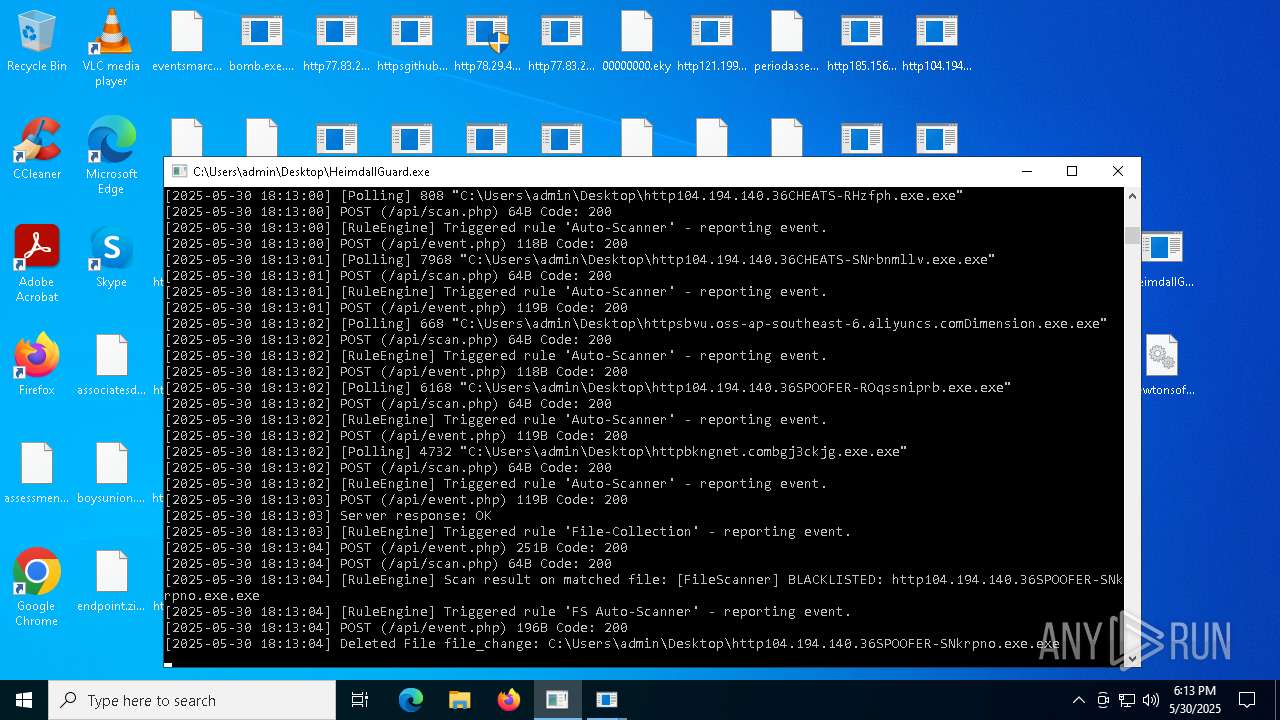
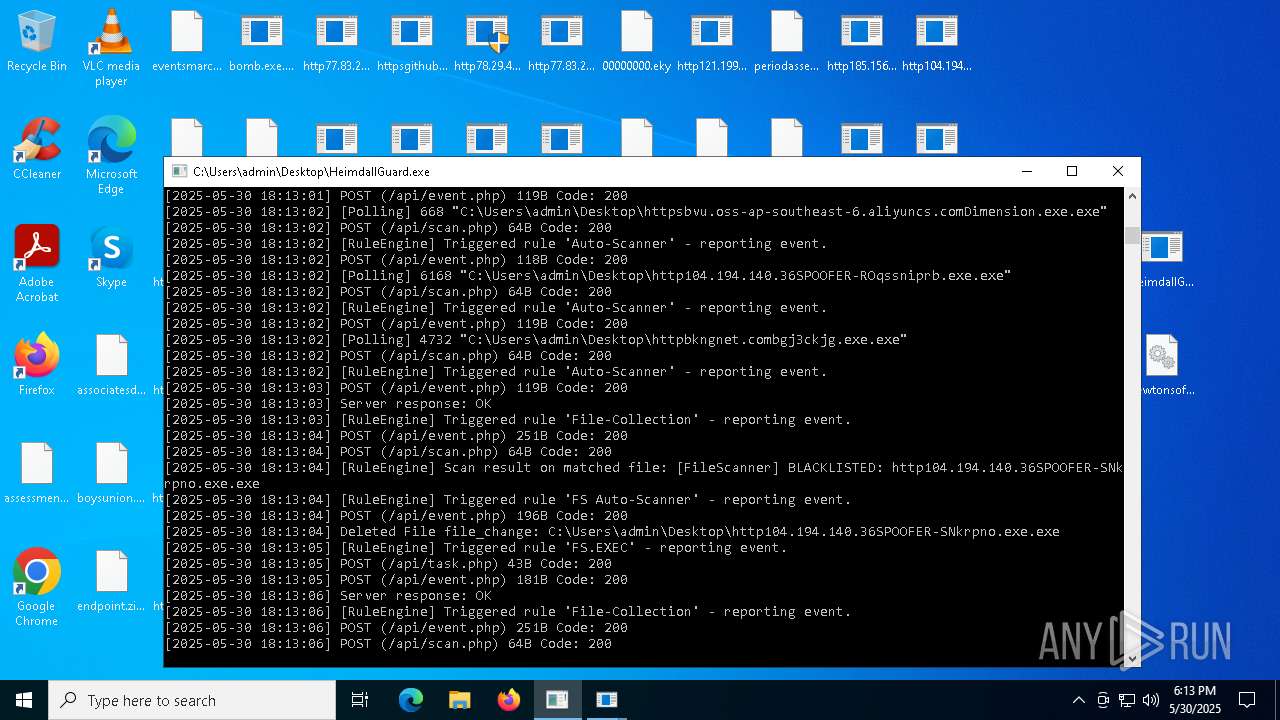
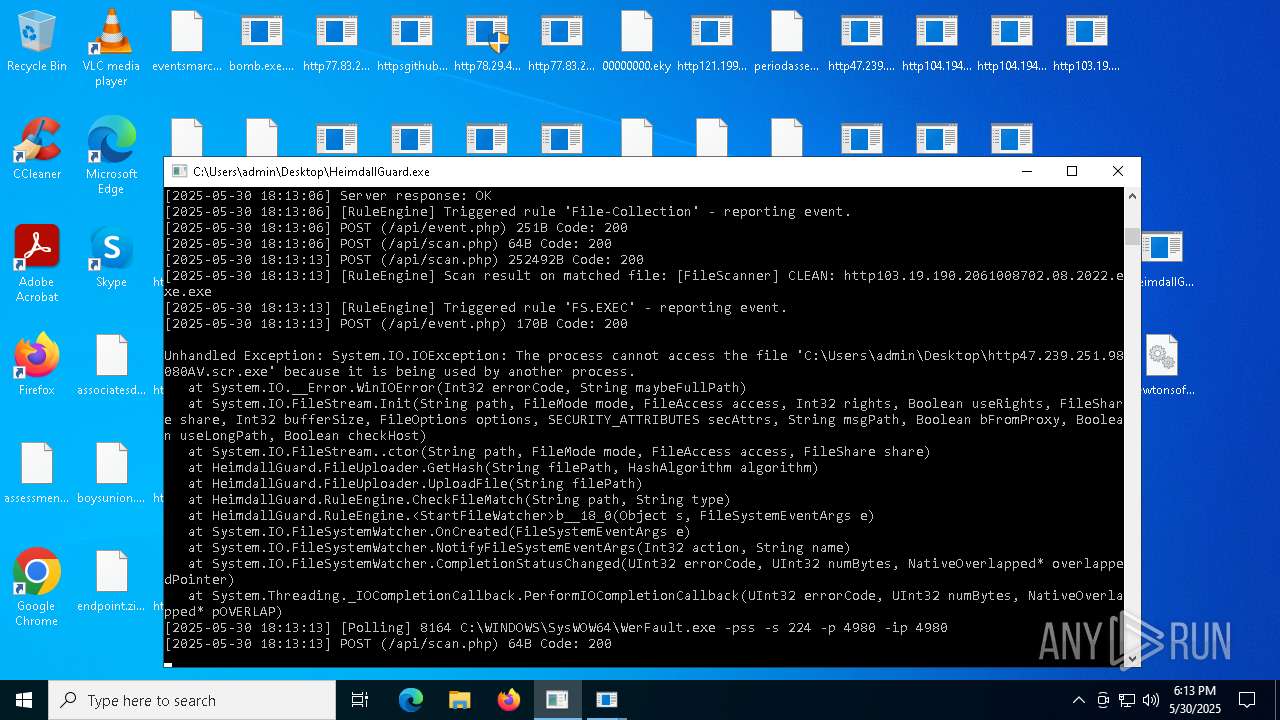
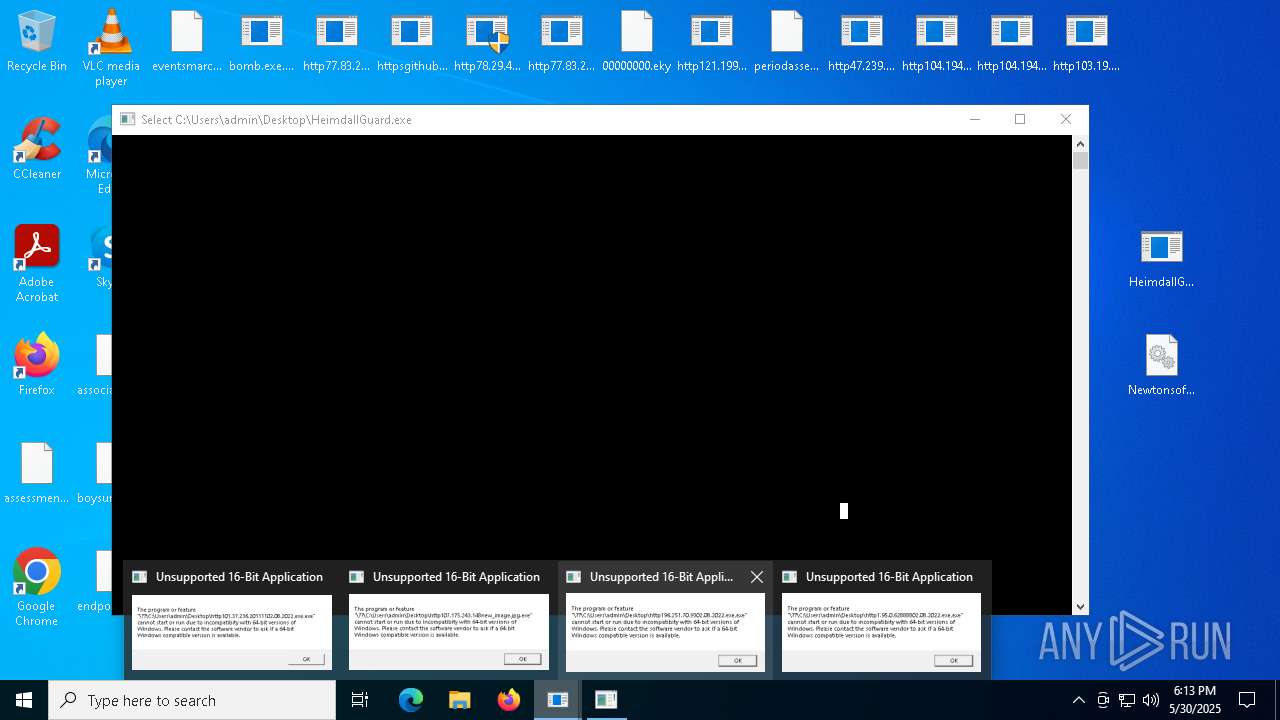
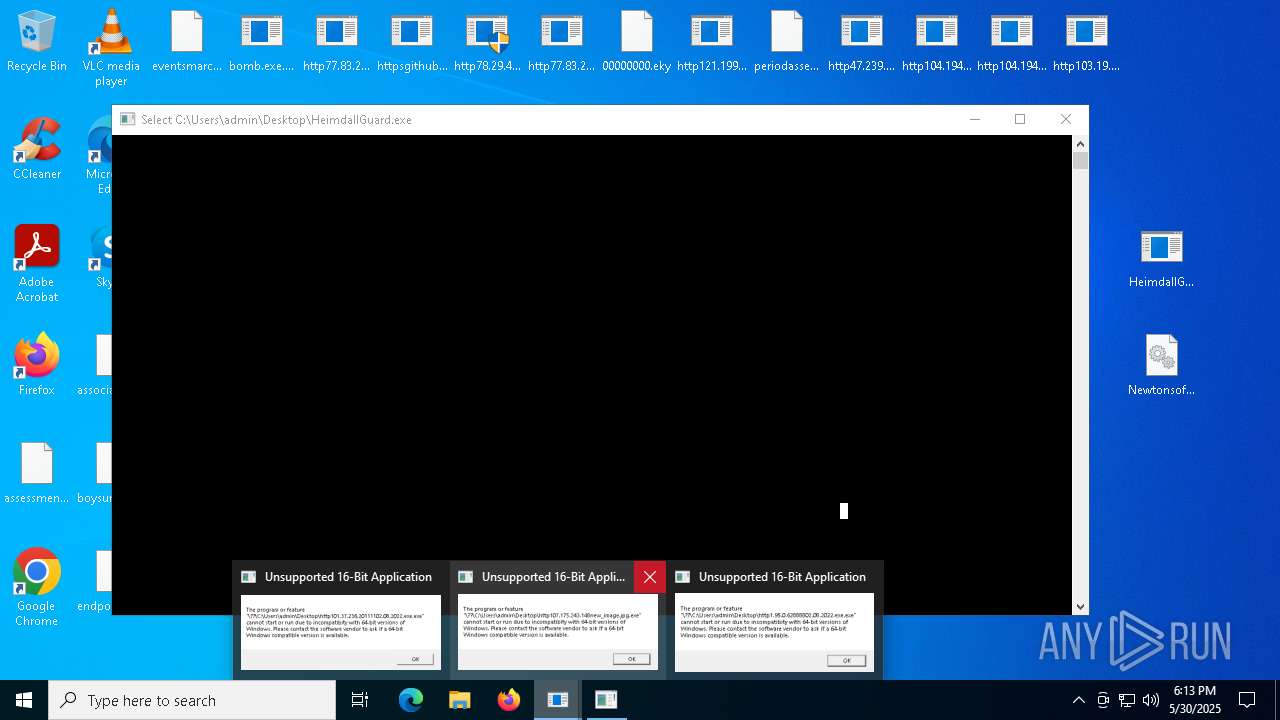
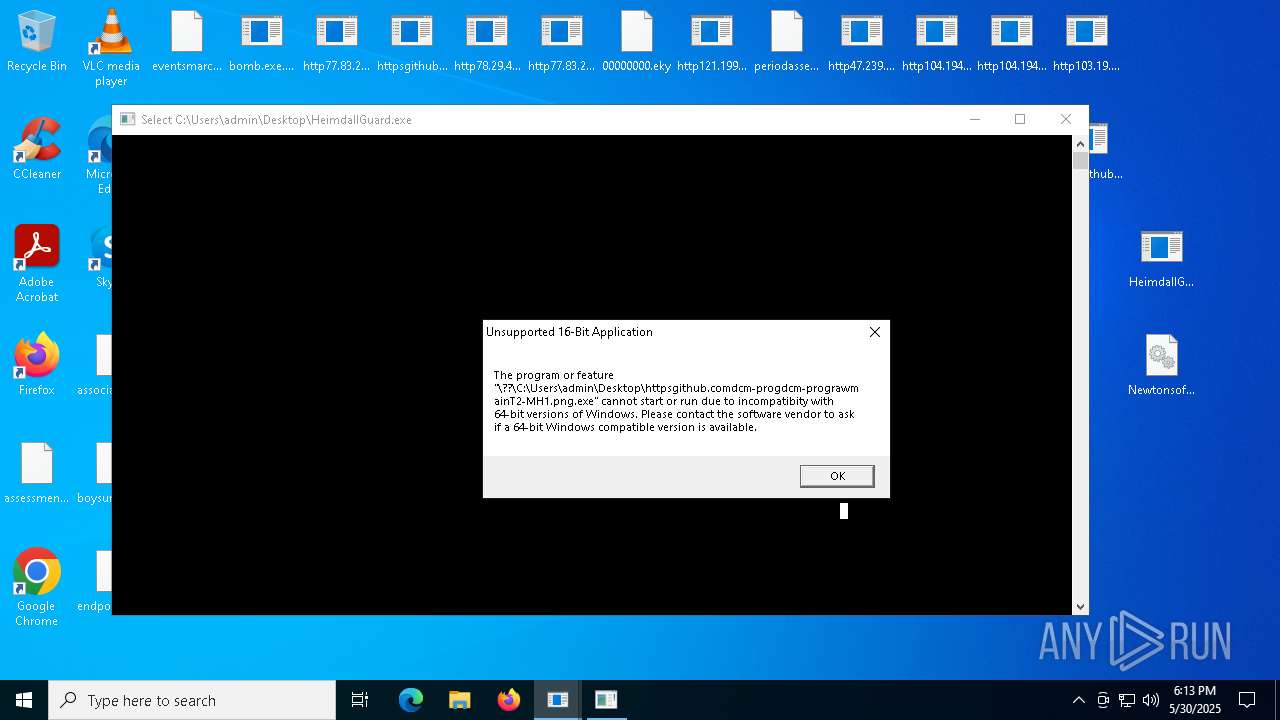
Application launched itself
- HeimdallGuard.exe (PID: 6208)
- HeimdallGuard.exe (PID: 7956)
- HeimdallGuard.exe (PID: 4980)
- HeimdallGuard.exe (PID: 7676)
The process drops C-runtime libraries
- http78.29.45.8Installer.exe.exe (PID: 3800)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 3384)
Process drops legitimate windows executable
- http78.29.45.8Installer.exe.exe (PID: 3800)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- bomb.exe.bin.exe (PID: 5556)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 3384)
- bomb.exe.bin.exe (PID: 2240)
Starts SC.EXE for service management
- http78.29.45.8Installer.exe.exe (PID: 3800)
- http78.29.45.8Installer.exe.exe (PID: 2908)
Windows service management via SC.EXE
- sc.exe (PID: 4272)
- sc.exe (PID: 7520)
The process executes via Task Scheduler
- http78.29.45.8Installer.exe.exe (PID: 2908)
Uses WMIC.EXE to obtain computer system information
- httpbkngnet.combgj3ckjg.exe.exe (PID: 5776)
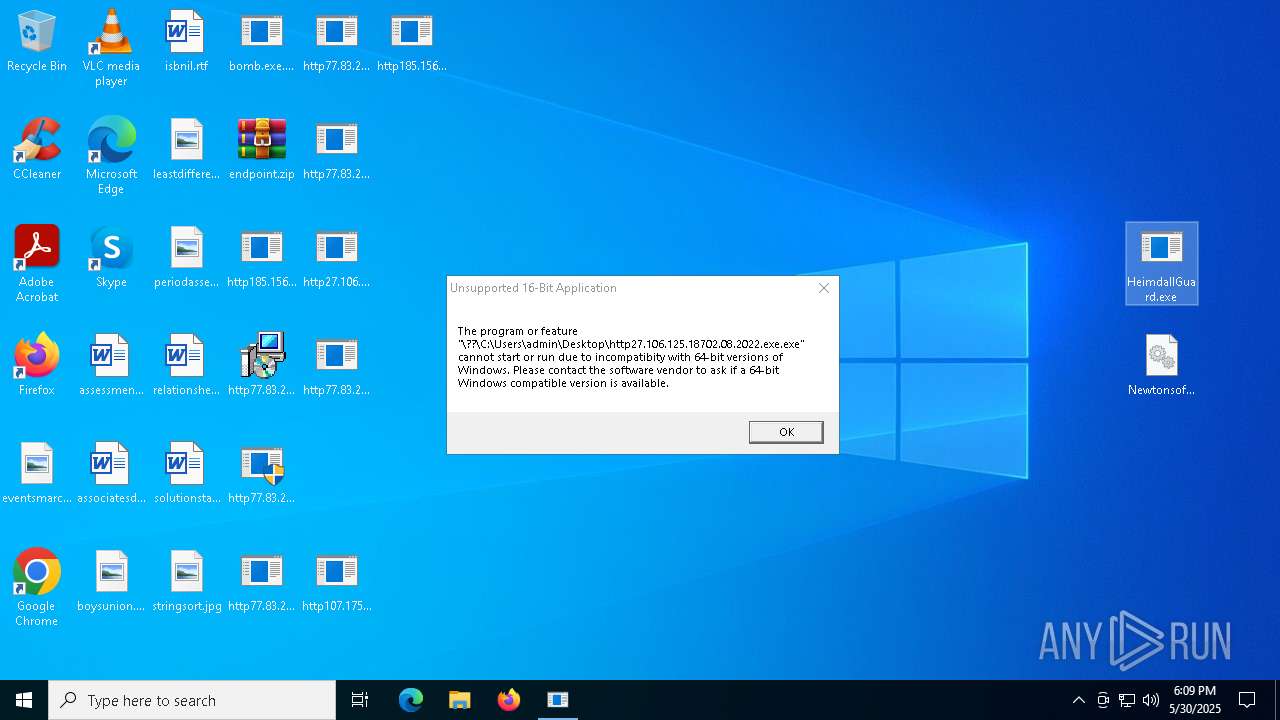
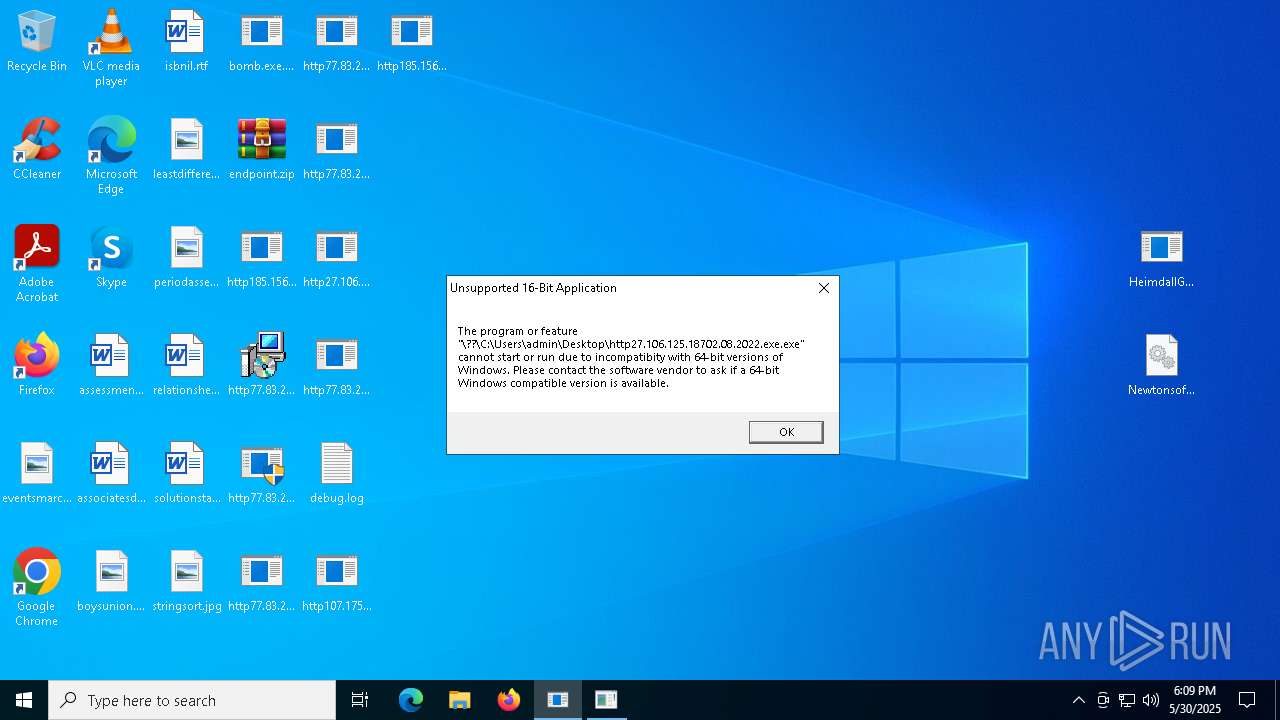
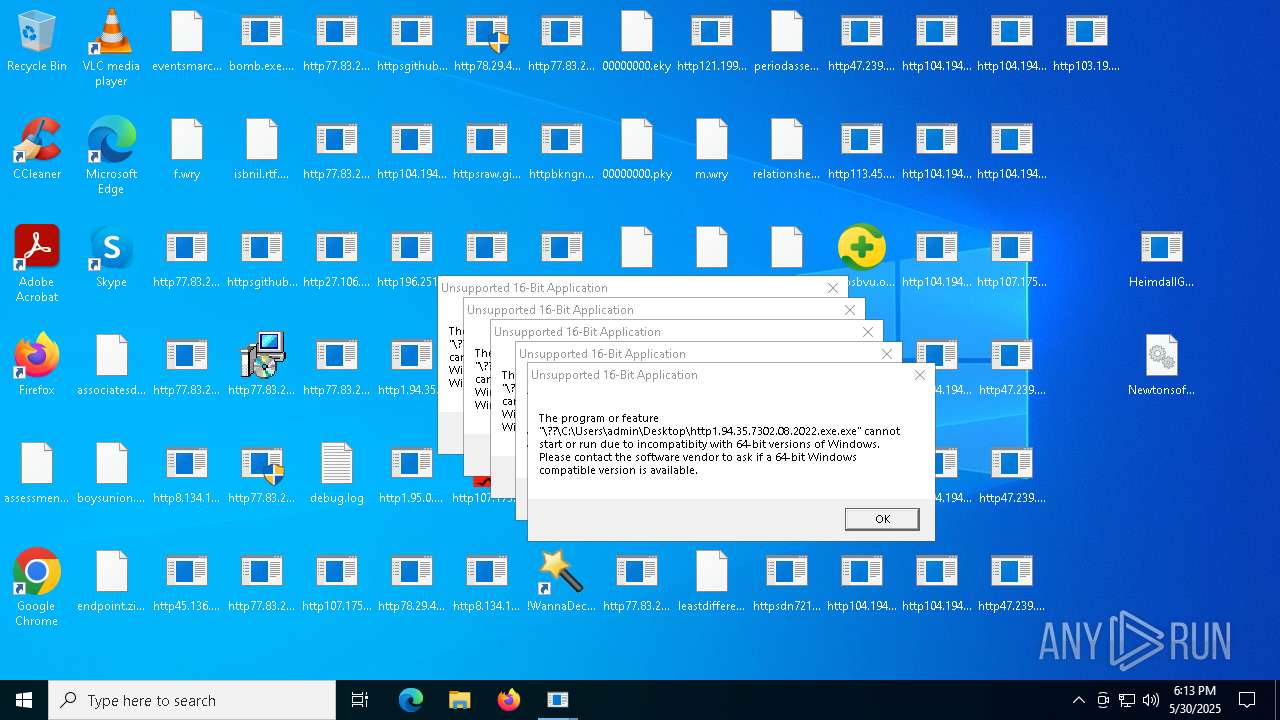
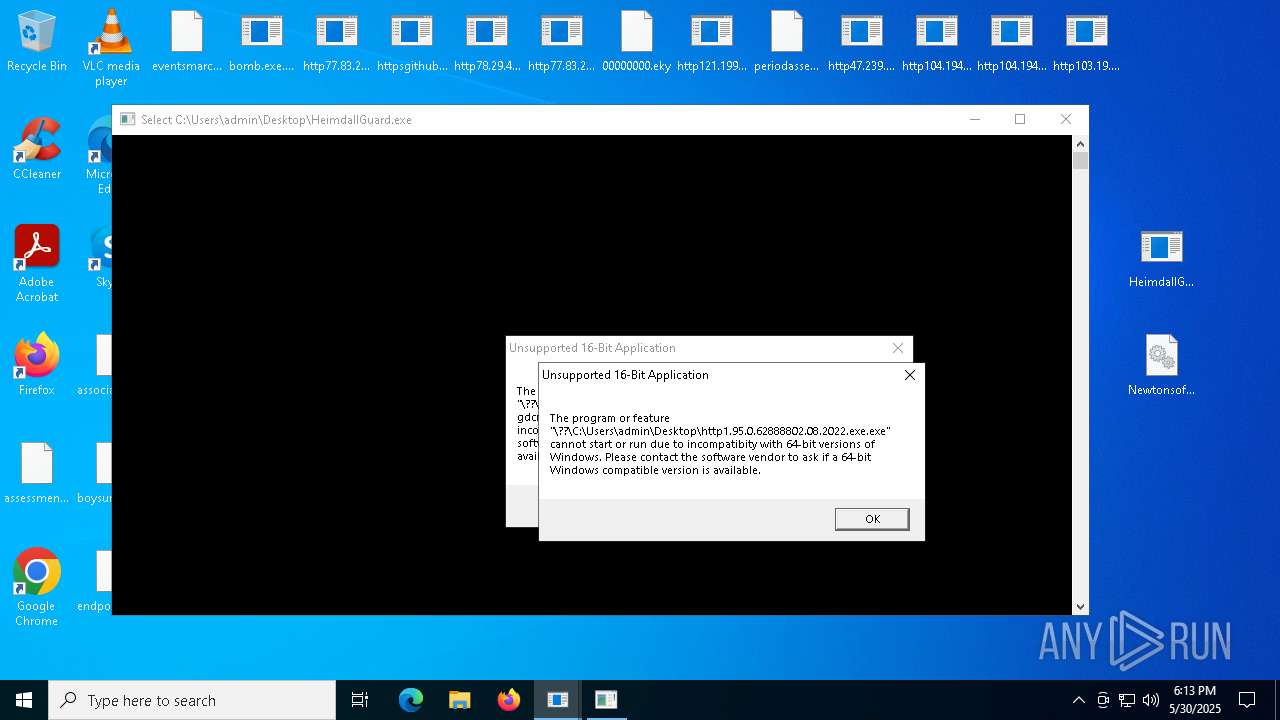
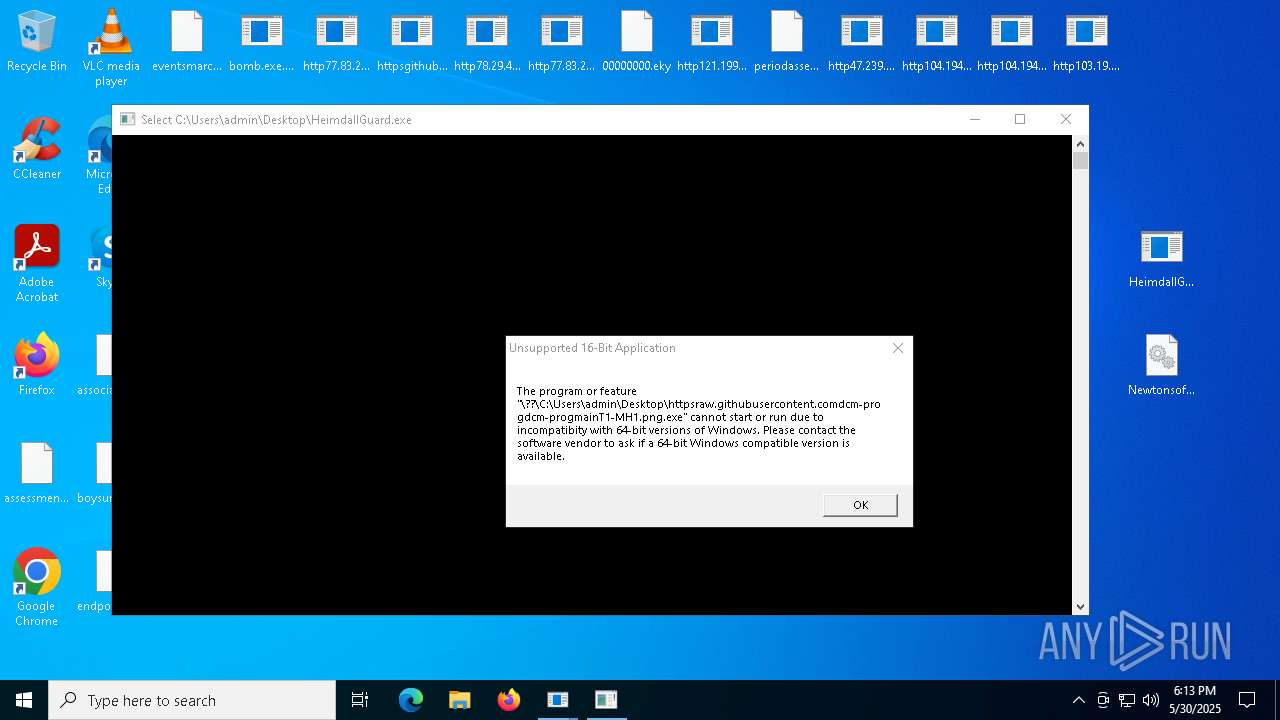
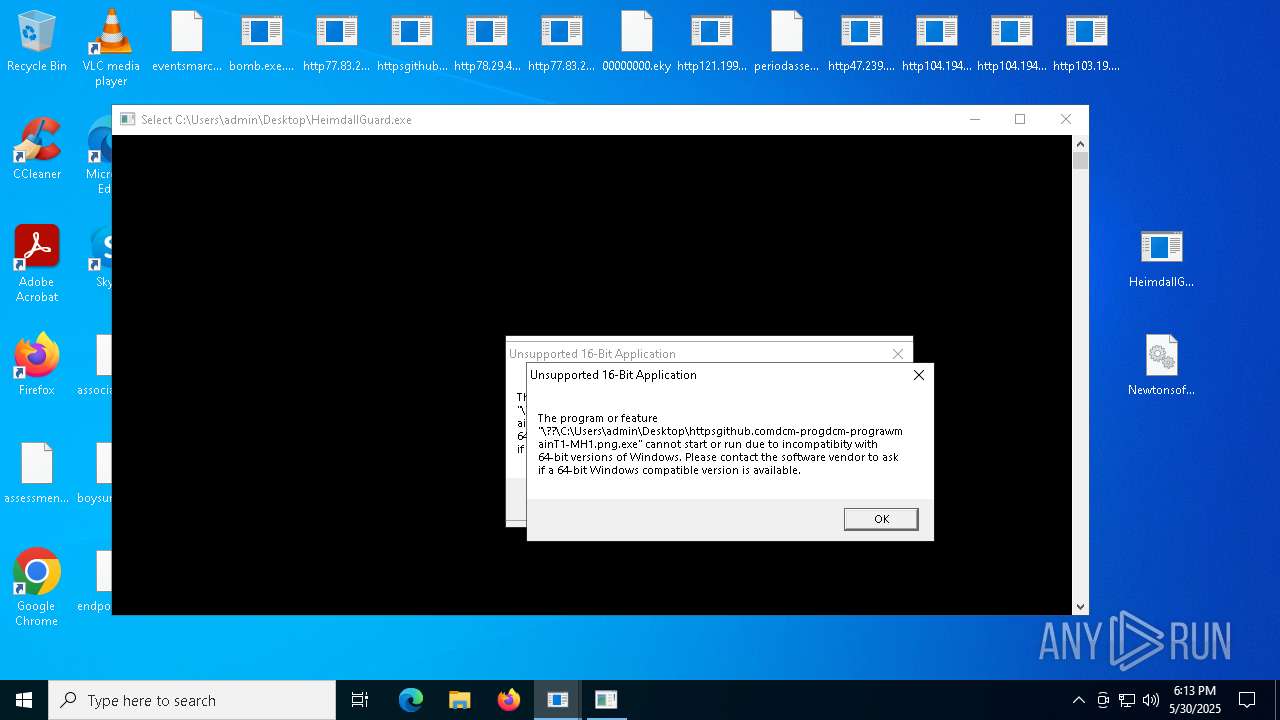
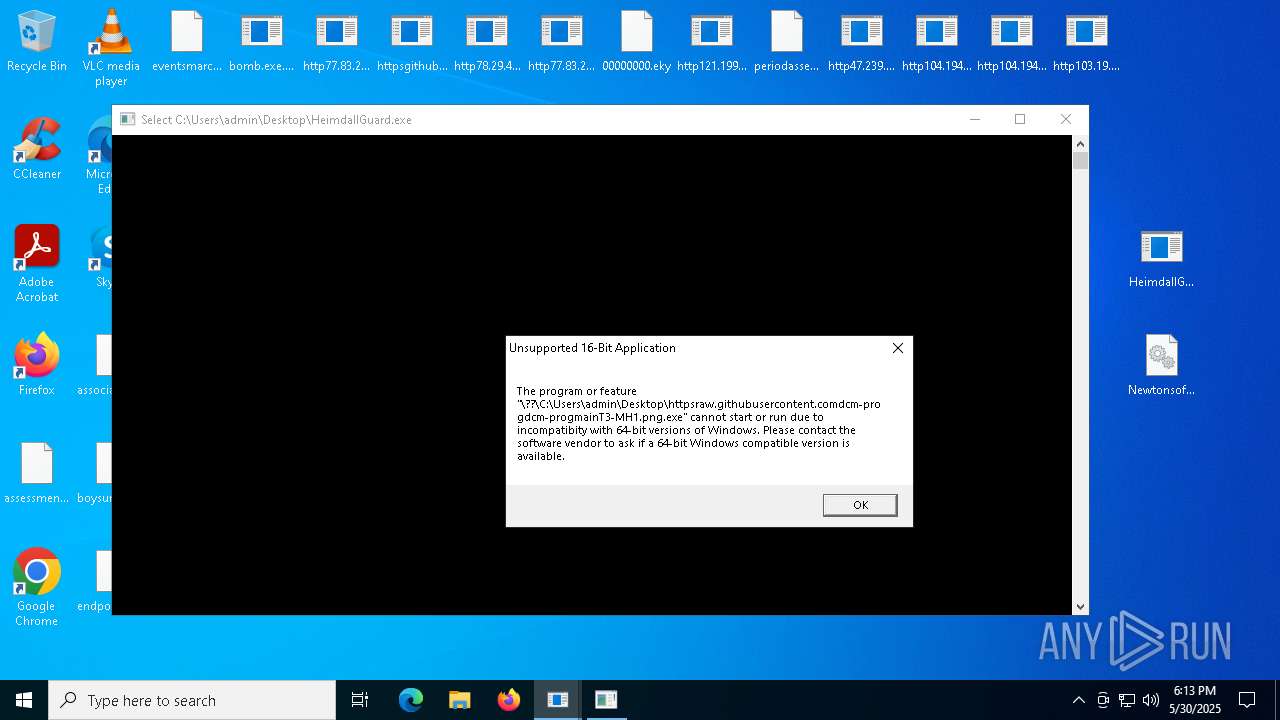
Executes application which crashes
- HeimdallGuard.exe (PID: 6208)
- http77.83.207.69inccron2mm.exe.exe (PID: 1040)
- HeimdallGuard.exe (PID: 4980)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 4452)
The process executes VB scripts
- cmd.exe (PID: 6656)
Uses TASKKILL.EXE to kill process
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 6044)
Process drops python dynamic module
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 3384)
INFO
Checks supported languages
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 4988)
- ScreenConnect.WindowsClient.exe (PID: 7508)
- ScreenConnect.ClientService.exe (PID: 7276)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.WindowsClient.exe (PID: 8176)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7776)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 1168)
- http77.83.207.69inccron1mm.exe.exe (PID: 4776)
- http77.83.207.69incClientSetup1.exe.exe (PID: 5596)
- ModSolar.exe (PID: 1804)
- http77.83.207.69incale11.exe.exe (PID: 5504)
- ModSolar.exe (PID: 4976)
- http77.83.207.69inccron2mm.exe.exe (PID: 7820)
- http77.83.207.69inctot.exe.exe (PID: 7716)
- msiexec.exe (PID: 1388)
- http107.173.47.141125dllhost.exe.exe (PID: 3032)
- msiexec.exe (PID: 6516)
- MSBuild.exe (PID: 7836)
- MSBuild.exe (PID: 6656)
Reads the computer name
- bomb.exe.bin.exe (PID: 5556)
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 4988)
- dfsvc.exe (PID: 5528)
- ScreenConnect.WindowsClient.exe (PID: 7508)
- ScreenConnect.ClientService.exe (PID: 7276)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.WindowsClient.exe (PID: 8176)
- http77.83.207.69incClientSetup1.exe.exe (PID: 5596)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 1168)
- ModSolar.exe (PID: 1804)
- ModSolar.exe (PID: 4976)
- msiexec.exe (PID: 1388)
- msiexec.exe (PID: 6516)
- MSBuild.exe (PID: 7836)
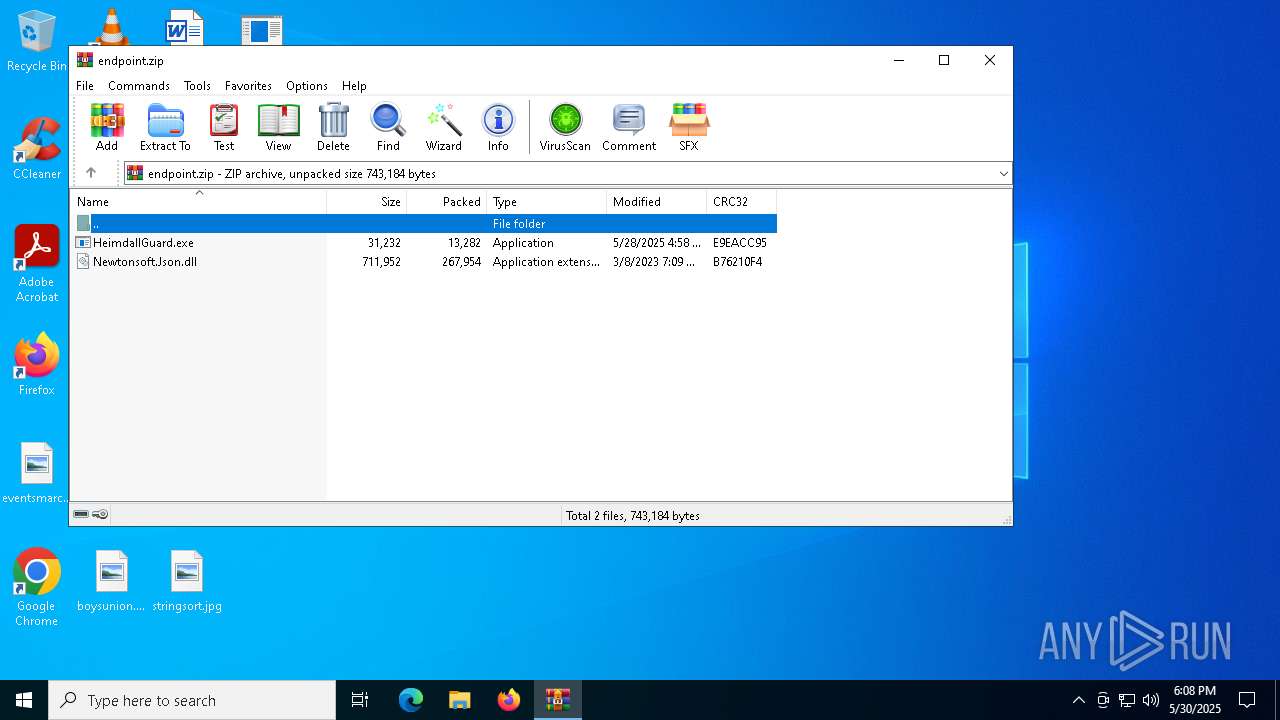
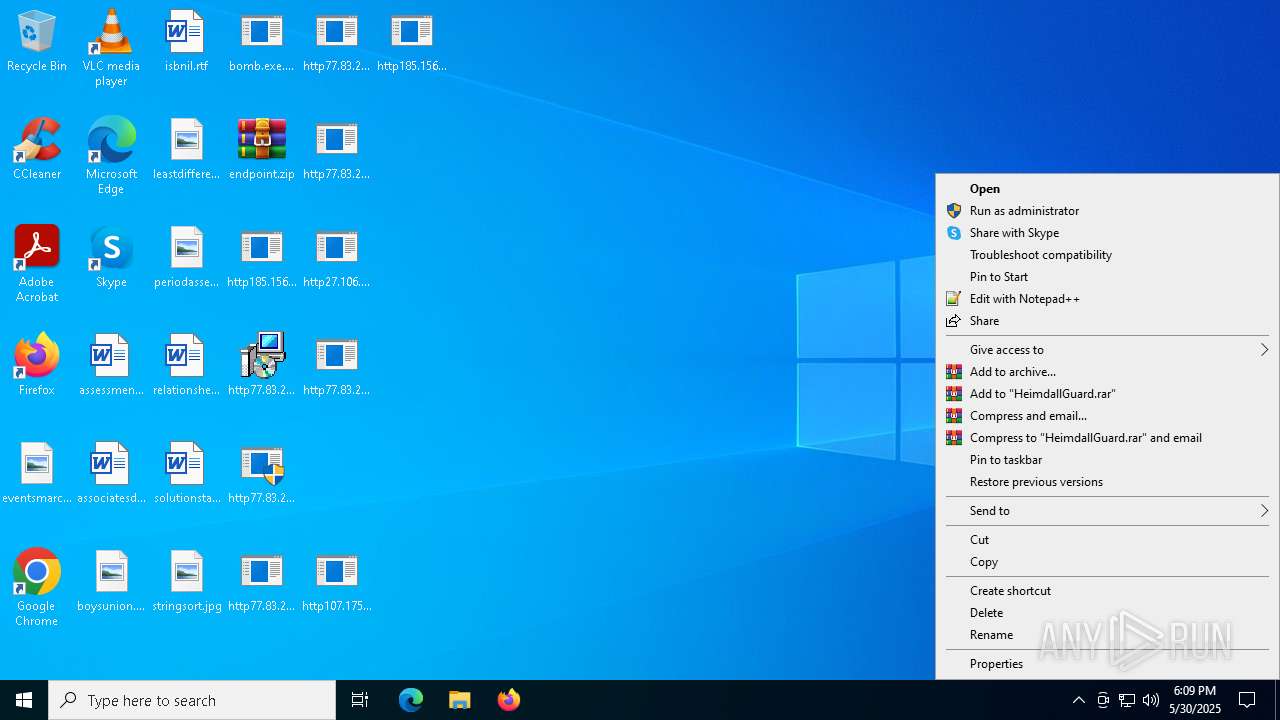
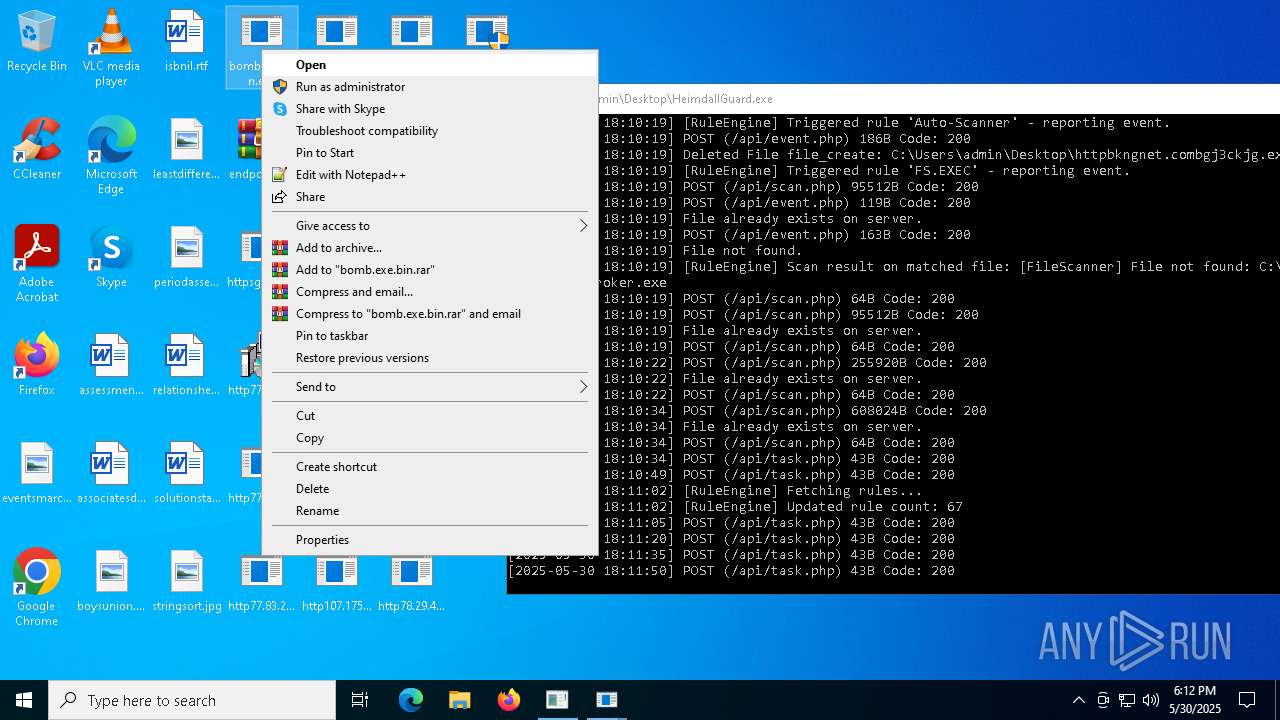
Manual execution by a user
- WinRAR.exe (PID: 1052)
- HeimdallGuard.exe (PID: 6208)
- bomb.exe.bin.exe (PID: 2240)
Reads the machine GUID from the registry
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 4988)
- ScreenConnect.WindowsClient.exe (PID: 7508)
- ScreenConnect.ClientService.exe (PID: 7276)
- ScreenConnect.ClientService.exe (PID: 5352)
- ScreenConnect.WindowsClient.exe (PID: 8176)
- http77.83.207.69incClientSetup1.exe.exe (PID: 5596)
Disables trace logs
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
Reads Environment values
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
Checks proxy server information
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
Reads the software policy settings
- bomb.exe.bin.exe (PID: 5556)
- dfsvc.exe (PID: 5528)
Creates files or folders in the user directory
- dfsvc.exe (PID: 5528)
- ScreenConnect.WindowsClient.exe (PID: 7508)
- ScreenConnect.ClientService.exe (PID: 5352)
- ModSolar.exe (PID: 4976)
Process checks computer location settings
- bomb.exe.bin.exe (PID: 5556)
- ScreenConnect.WindowsClient.exe (PID: 7508)
- dfsvc.exe (PID: 5528)
- http77.83.207.69incClientSetup1.exe.exe (PID: 5596)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1052)
- msiexec.exe (PID: 2616)
- msiexec.exe (PID: 1388)
- msiexec.exe (PID: 4948)
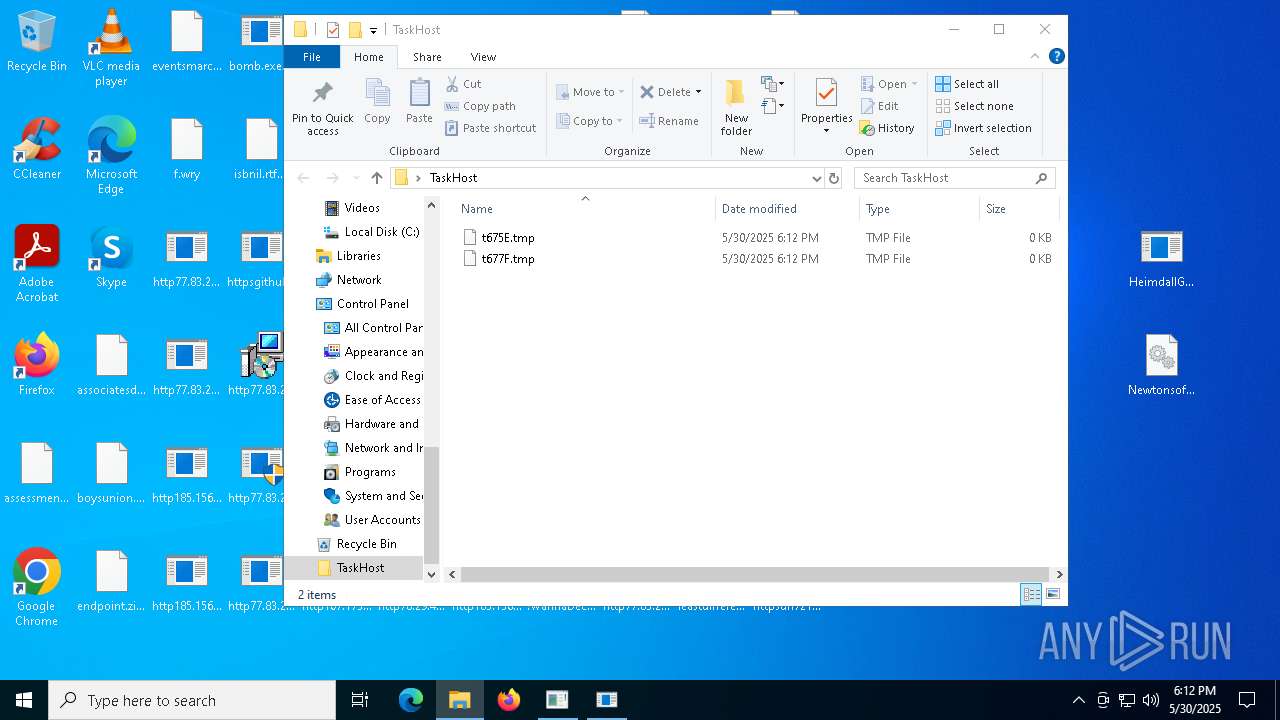
Create files in a temporary directory
- dfsvc.exe (PID: 5528)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7776)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 1168)
- http77.83.207.69incClientSetup1.exe.exe (PID: 5596)
- ModSolar.exe (PID: 4976)
- http77.83.207.69inctot.exe.exe (PID: 7716)
- rundll32.exe (PID: 6108)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 5528)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 5352)
The sample compiled with english language support
- bomb.exe.bin.exe (PID: 5556)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7776)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 1168)
- ModSolar.exe (PID: 1804)
- ModSolar.exe (PID: 4976)
- esentutl.exe (PID: 3364)
- http78.29.45.8Installer.exe.exe (PID: 3800)
- http78.29.45.8Installer.exe.exe (PID: 2908)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 7332)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 3160)
- bomb.exe.bin.exe (PID: 2240)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 5996)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 3384)
The sample compiled with chinese language support
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 1168)
- ModSolar.exe (PID: 1804)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 5996)
- ModSolar.exe (PID: 7216)
Creates files in the program directory
- ModSolar.exe (PID: 1804)
CONNECTWISE has been detected
- msiexec.exe (PID: 2616)
Reads security settings of Internet Explorer
- cmd.exe (PID: 680)
Application launched itself
- chrome.exe (PID: 7408)
Manages system restore points
- SrTasks.exe (PID: 4944)
Launch of the file from Task Scheduler
- cmd.exe (PID: 7824)
- http78.29.45.8Installer.exe.exe (PID: 3800)
Compiled with Borland Delphi (YARA)
- ModSolar.exe (PID: 4976)
Attempting to use instant messaging service
- MSBuild.exe (PID: 5980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2057:01:07 19:44:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 9216 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x431e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | bomb.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | bomb.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
325
Monitored processes
186
Malicious processes
19
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | C:\Windows\syswow64\MsiExec.exe -Embedding D8DABF211912EB532AFB6BFE3471E977 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Users\admin\Desktop\httpsbvu.oss-ap-southeast-6.aliyuncs.comDimension.exe.exe" | C:\Users\admin\Desktop\httpsbvu.oss-ap-southeast-6.aliyuncs.comDimension.exe.exe | — | bomb.exe.bin.exe | |||||||||||
User: admin Company: Qihoo 360 Technology Co. Ltd. Integrity Level: MEDIUM Description: CEF Utility Application Exit code: 1 Version: 1, 0, 0, 1047 Modules
| |||||||||||||||
| 680 | "C:\WINDOWS\sysnative\cmd" /c "C:\Users\admin\AppData\Local\Temp\99F6.tmp\99F7.tmp\99F8.bat C:\Users\admin\Desktop\http77.83.207.69inctot.exe.exe" | C:\Windows\System32\cmd.exe | — | http77.83.207.69inctot.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 724 | C:\ProgramData\beaconclient\ModSolar.exe | C:\ProgramData\beaconclient\ModSolar.exe | — | ModSolar.exe | |||||||||||
User: admin Company: Wondershare Software Integrity Level: HIGH Description: Wondershare DVD Creator Exit code: 1 Version: 6.6.0.1 Modules
| |||||||||||||||
| 724 | "C:\Users\admin\Desktop\http104.194.140.36SPOOFER-SNkrpno.exe.exe" | C:\Users\admin\Desktop\http104.194.140.36SPOOFER-SNkrpno.exe.exe | — | bomb.exe.bin.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Nkrpno Exit code: 1 Version: 1.0.5383.20133 Modules
| |||||||||||||||
| 772 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | http77.83.207.69inccron2.exe.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 1 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 808 | "C:\Users\admin\Desktop\http104.194.140.36CHEATS-RHzfph.exe.exe" | C:\Users\admin\Desktop\http104.194.140.36CHEATS-RHzfph.exe.exe | — | bomb.exe.bin.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Hzfph Exit code: 1 Version: 1.0.8930.15658 Modules
| |||||||||||||||
| 908 | taskkill /f /im MSExchange* | C:\Windows\SysWOW64\taskkill.exe | — | httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 980 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | http77.83.207.69incalex12321.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
72 742
Read events
72 053
Write events
587
Delete events
102
Modification events
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\endpoint.zip | |||
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1052) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5556) bomb.exe.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5556) bomb.exe.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
146
Suspicious files
1 078
Text files
249
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1052.34178\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 5528 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:26A3C07BAA46D30BBC8D971741FE6764 | SHA256:FA828C8B34AEBF7C187A583F30190604D5091818BE7DE273B59C77FAD7997734 | |||
| 5556 | bomb.exe.bin.exe | C:\Users\admin\Desktop\http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe | executable | |
MD5:B28AC406FC4D1596B24B25913CB976BB | SHA256:8501047B053255F04CF9D0402BB947CEB13532B8C9BD2FA052A4647B357524B8 | |||
| 5528 | dfsvc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\932a2db58c237abd381d22df4c63a04a_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:D2DED43CE07BFCE4D1C101DFCAA178C8 | SHA256:8EEE9284E733B9D4F2E5C43F71B81E27966F5CD8900183EB3BB77A1F1160D050 | |||
| 5528 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:3F2919800F413E1A157AB1AE97631C1C | SHA256:0CBC7B56B69001C3EB23BDDB1140C36F393B2A43C3A85F4E1AF2267C626DA8E1 | |||
| 1052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1052.34178\HeimdallGuard.exe | executable | |
MD5:72EDFF31DFF1490EAA9D0D8BA02C97C9 | SHA256:7B63E00DF0FDF76552FF27FAAEB8F73FD70CD27758FD49561A74A531A3986D50 | |||
| 5528 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\982EWJB1.E4Z\9QT2O84X.N5V\ScreenConnect.WindowsClient.exe.manifest | xml | |
MD5:5259D3B040AD978D0D23AC1E1698CBCD | SHA256:92DDF8B23746703A24F5E1FB6B9F087E98E68116AEC5DE9174D2662E53C1505E | |||
| 5528 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\06NZW5OV.QM6\HT0B63WN.DDT.application | xml | |
MD5:A6D87EA7D3B83528560724CC58155152 | SHA256:8D9F670912B080E8B06647FB49029DCEF895CE59615BDD285BB6F1CE47DA366E | |||
| 5528 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_BE4413523710330F97BEE5D4A544C42B | binary | |
MD5:988D1EB85065983219EF389F5230F012 | SHA256:214E80CD3519E274C113D9C988080D1FB7A00D43B83C86186AD52CE5034B8469 | |||
| 5528 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_BE4413523710330F97BEE5D4A544C42B | binary | |
MD5:4C96FC7E6410BD55C317280B3E193780 | SHA256:181343455167770D0CE49A737304C05C4C3E607924CE4F5CF84F249A3868A13A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
1 053
DNS requests
61
Threats
171
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5556 | bomb.exe.bin.exe | GET | 200 | 77.83.207.69:80 | http://77.83.207.69/inc/tot.exe | unknown | — | — | malicious |
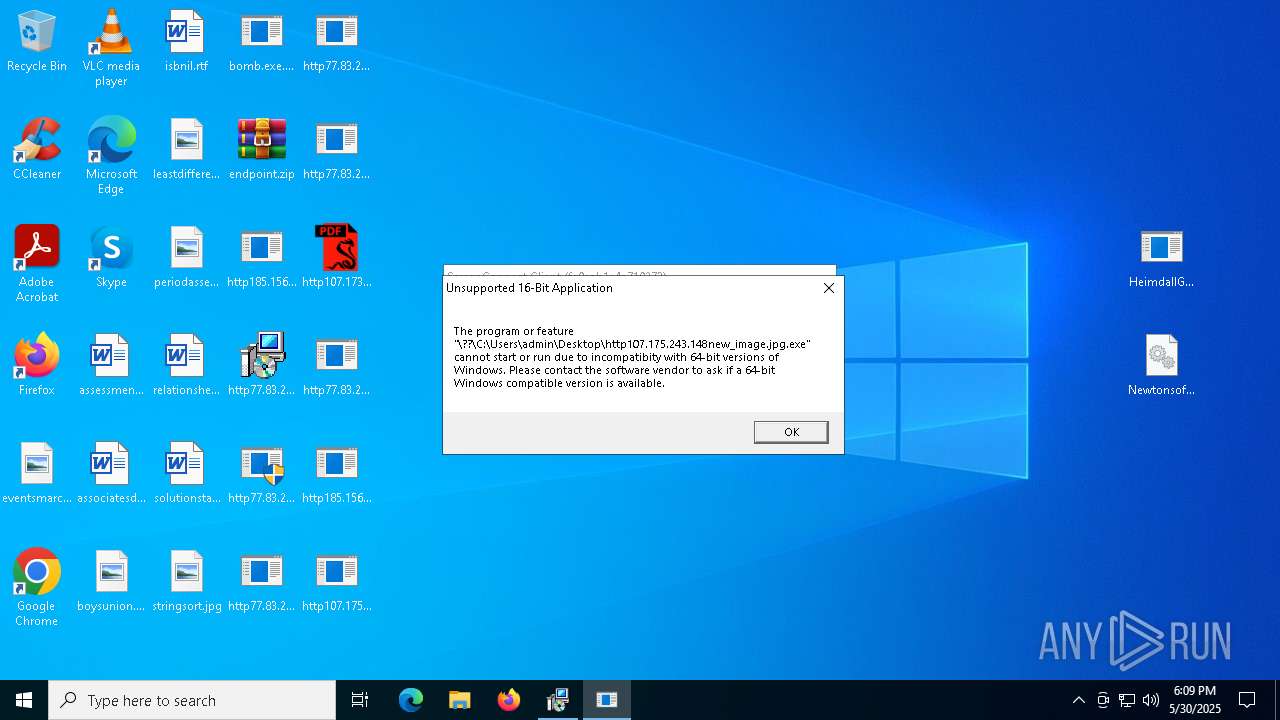
5556 | bomb.exe.bin.exe | GET | — | 107.175.243.148:80 | http://107.175.243.148/new_image.jpg | unknown | — | — | unknown |
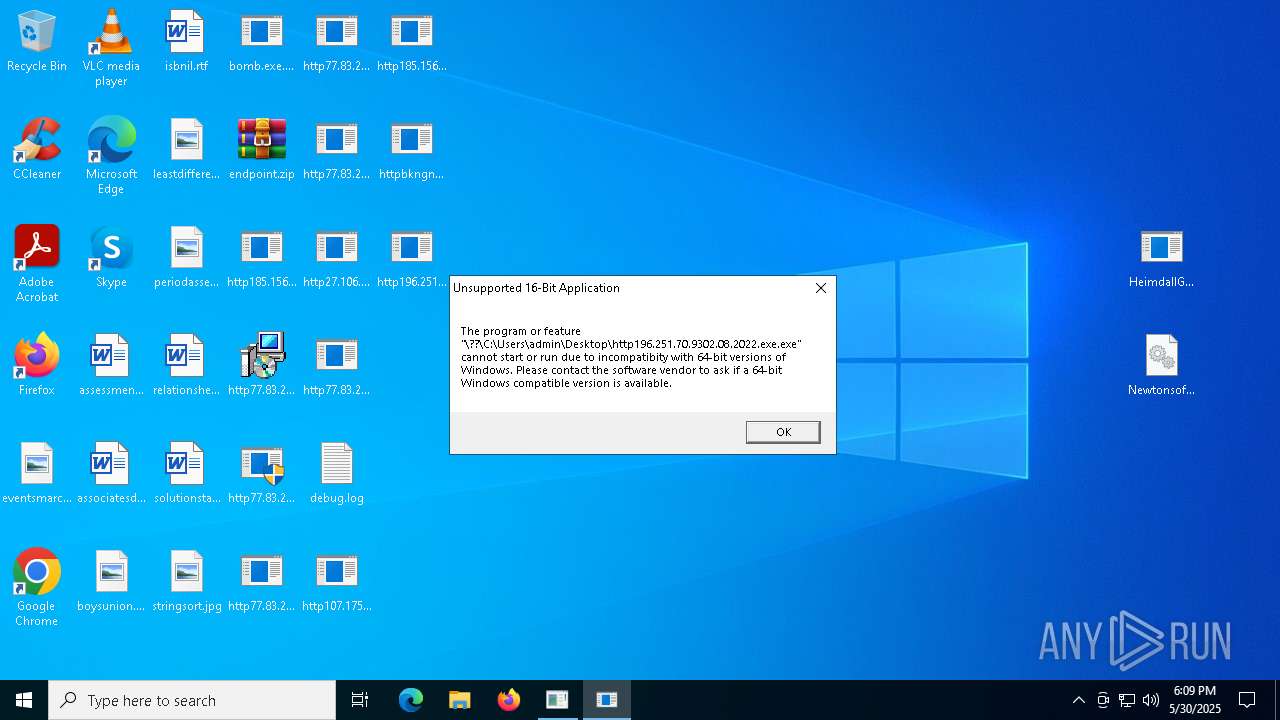
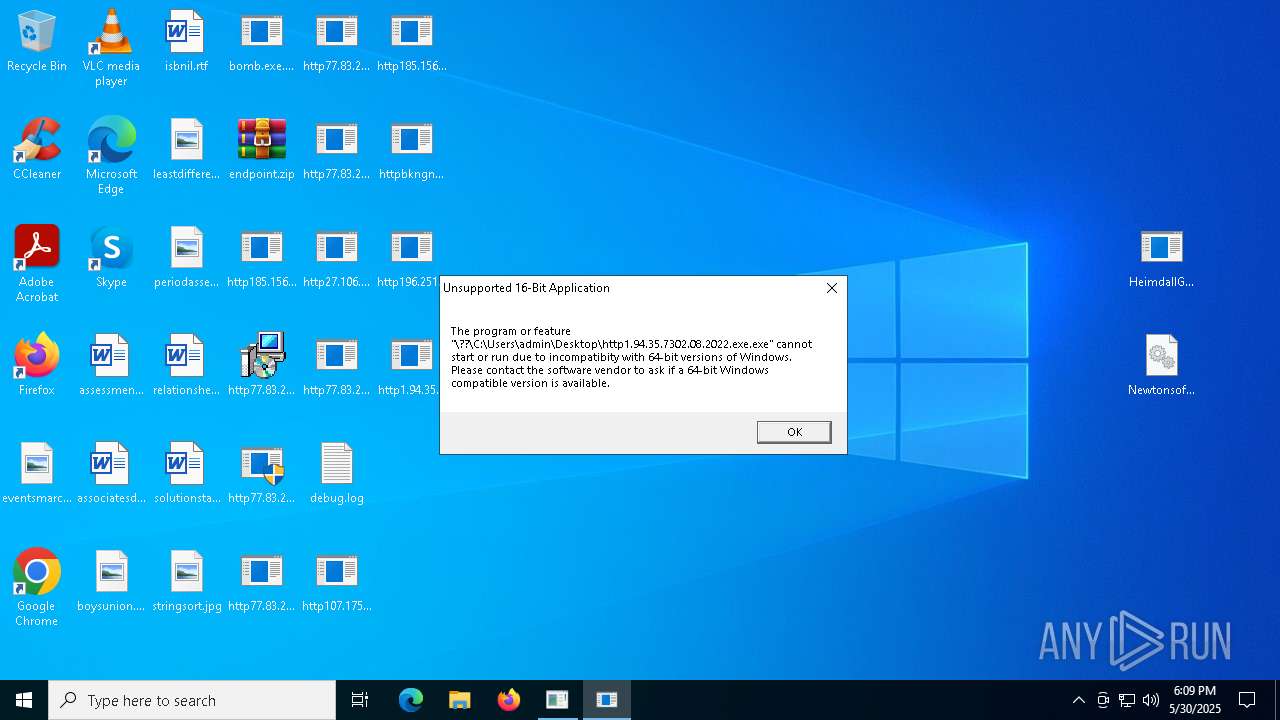
5556 | bomb.exe.bin.exe | GET | 200 | 27.106.125.187:80 | http://27.106.125.187/02.08.2022.exe | unknown | — | — | malicious |
5556 | bomb.exe.bin.exe | GET | 200 | 196.251.70.93:80 | http://196.251.70.93/02.08.2022.exe | unknown | — | — | malicious |
5556 | bomb.exe.bin.exe | GET | 200 | 77.83.207.69:80 | http://77.83.207.69/inc/SSA-7005-SM-34062529.pdf.exe | unknown | — | — | malicious |
7560 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5528 | dfsvc.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuTYAUbzPZmQpmJmNW6l84%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7212 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
7560 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7560 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5556 | bomb.exe.bin.exe | 151.101.2.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
5556 | bomb.exe.bin.exe | 185.156.72.2:80 | — | Tov Vaiz Partner | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
support.screenconnectsoftware.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5556 | bomb.exe.bin.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS *.pdf.exe in HTTP URL |
5556 | bomb.exe.bin.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5556 | bomb.exe.bin.exe | Misc activity | ET INFO Packed Executable Download |
5556 | bomb.exe.bin.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5556 | bomb.exe.bin.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5556 | bomb.exe.bin.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5352 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
5556 | bomb.exe.bin.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5556 | bomb.exe.bin.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5556 | bomb.exe.bin.exe | Misc activity | ET INFO Packed Executable Download |