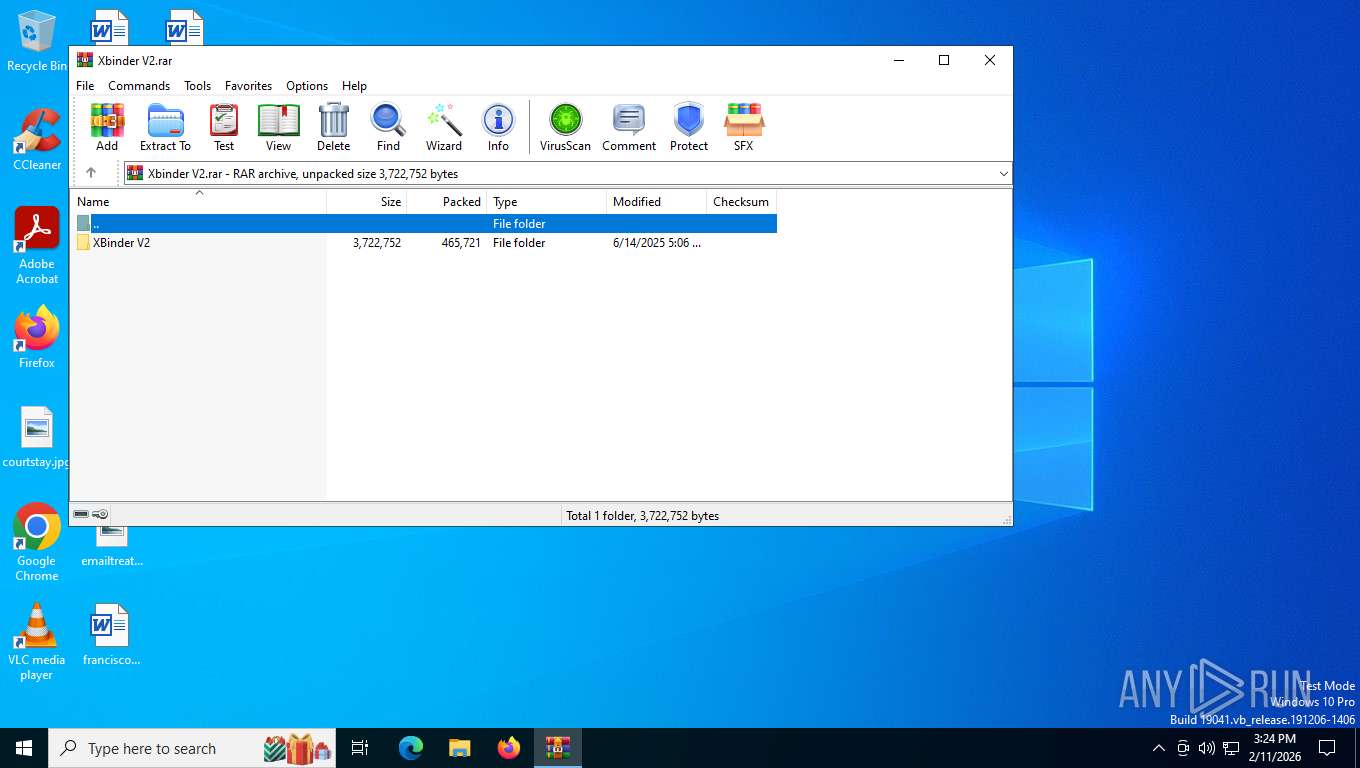
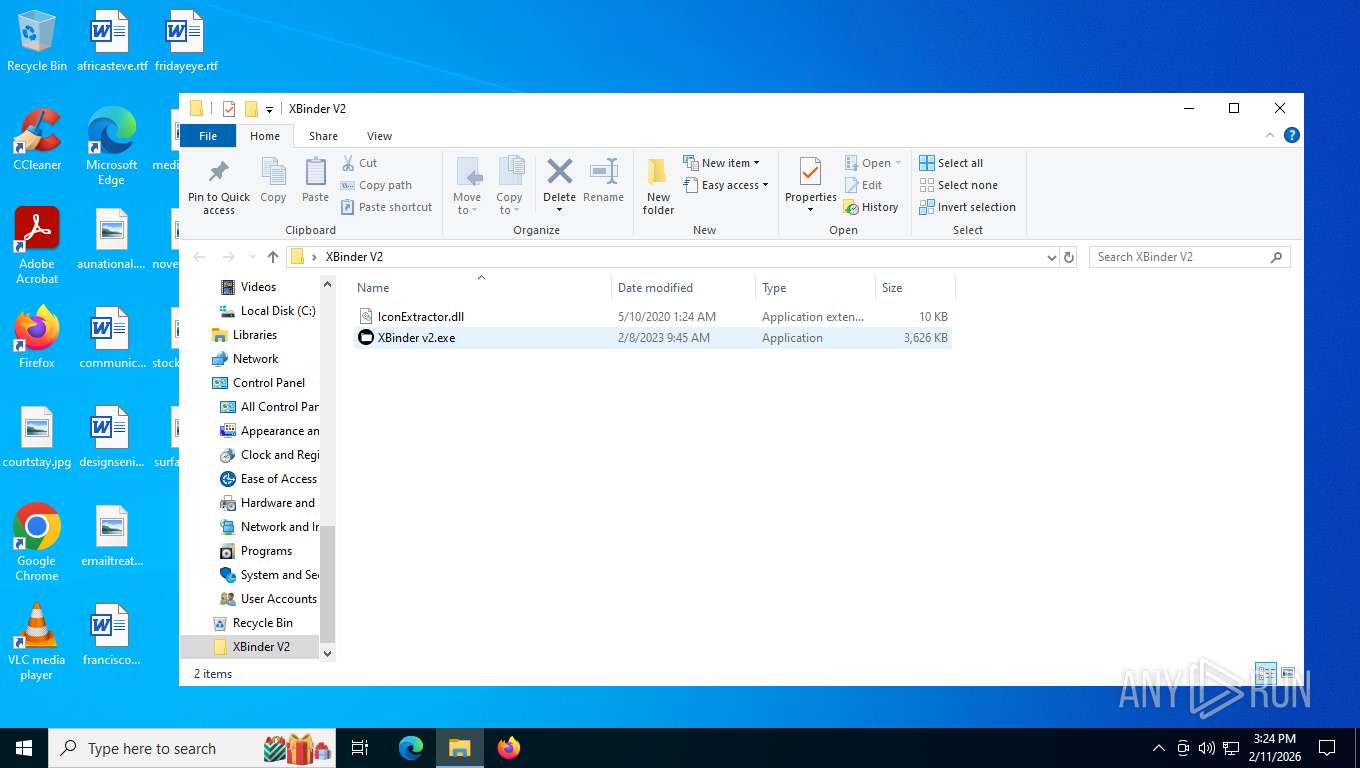
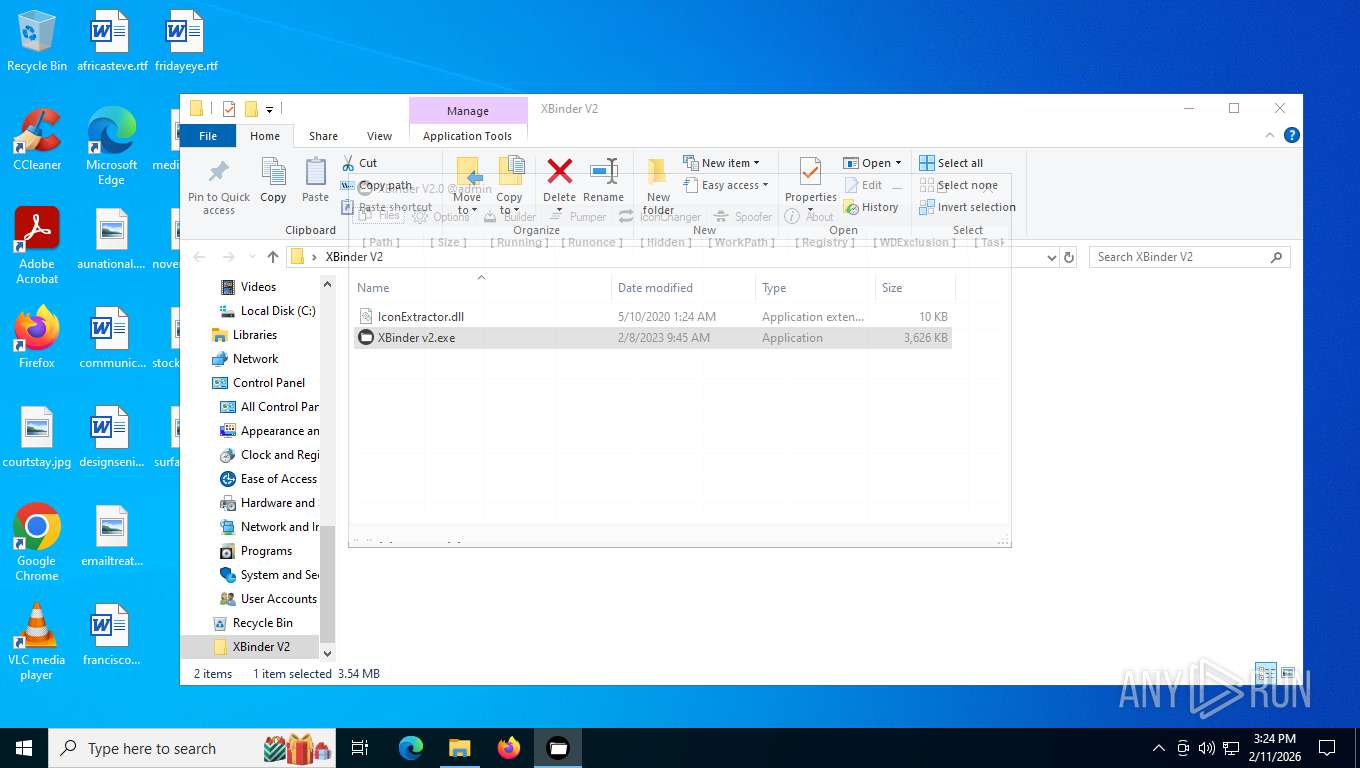
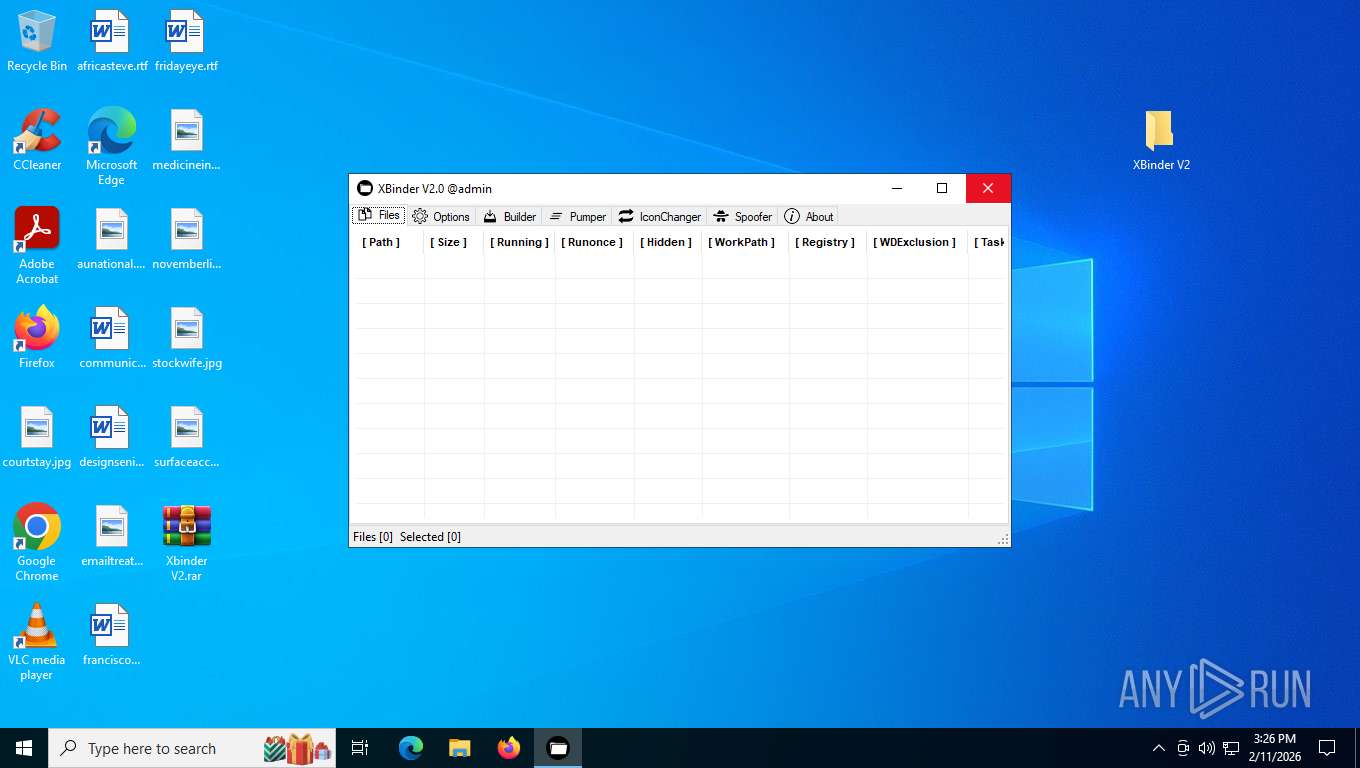
| File name: | Xbinder V2.rar |
| Full analysis: | https://app.any.run/tasks/8c9f0b0b-94e7-4a62-a1a5-baf9eaab9939 |
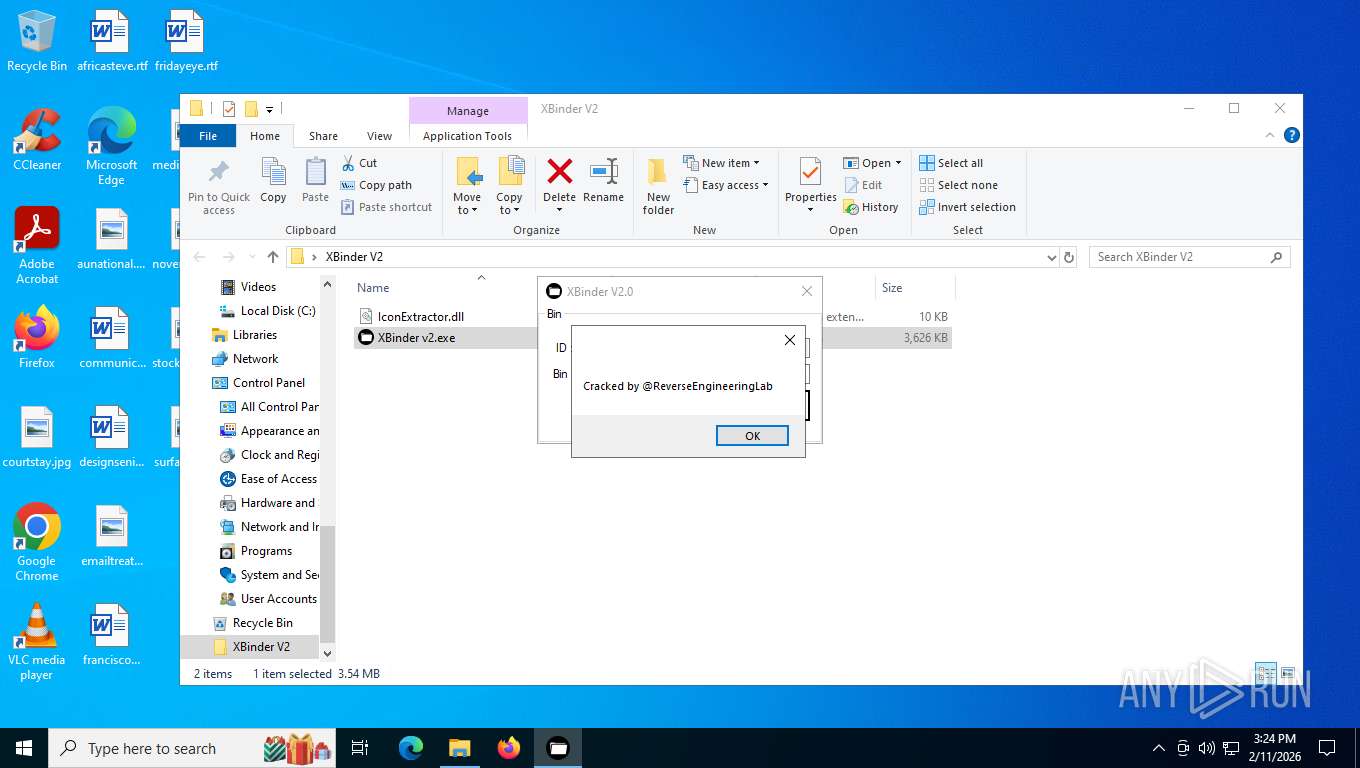
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | February 11, 2026, 20:24:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 50D85FD0A1896127D0A7767FFDF5C639 |
| SHA1: | 85BC2F1EFAF277EA8AF58E8CF4DF60B5FB114BAC |
| SHA256: | E85287F90748AF709544219B15349DB4082C1BEDD45782A9318CC8F4E0652765 |
| SSDEEP: | 24576:n8XO79y3iMDKG/QAsIhMfHovua7rjpA8Su9mvHYCRUBoNaAJHUFUL:n8XO79y3iMDKG/QAsIyfIvua7rjpjSu0 |
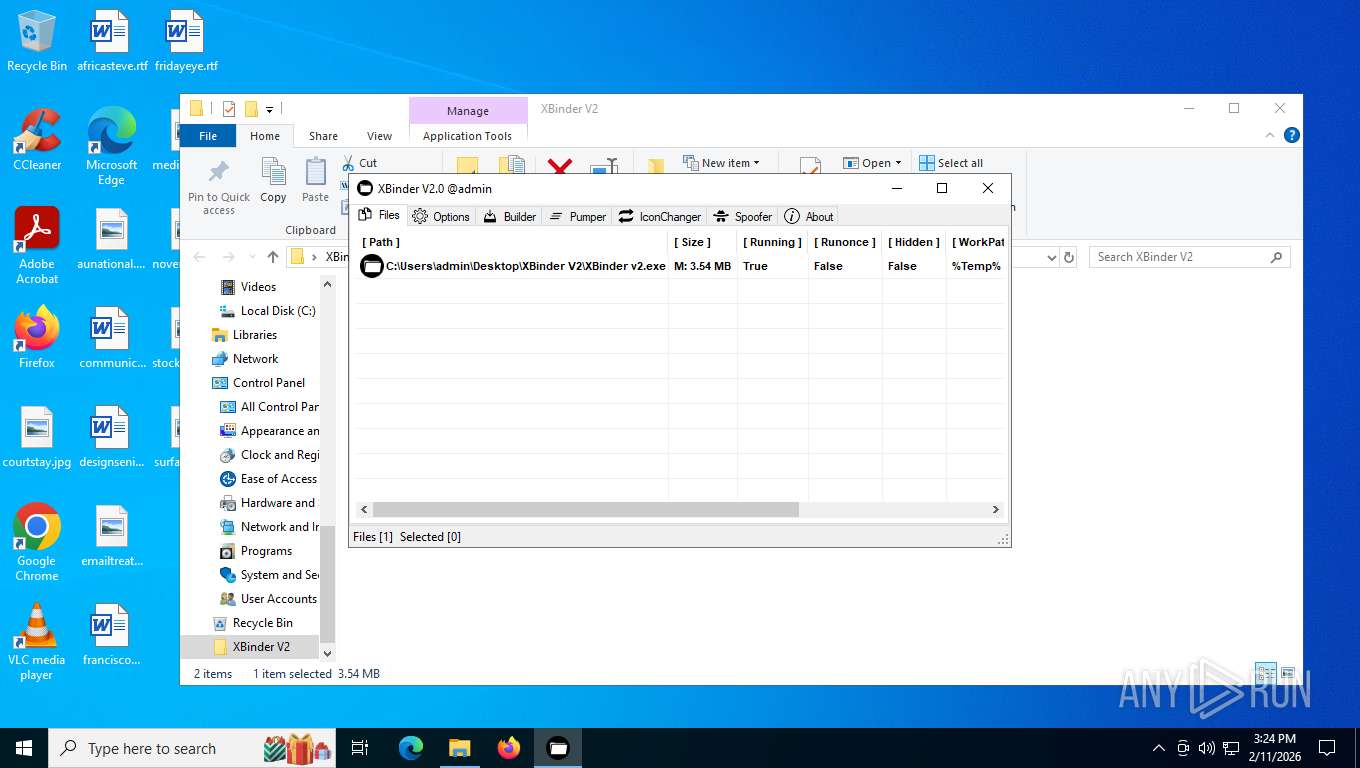
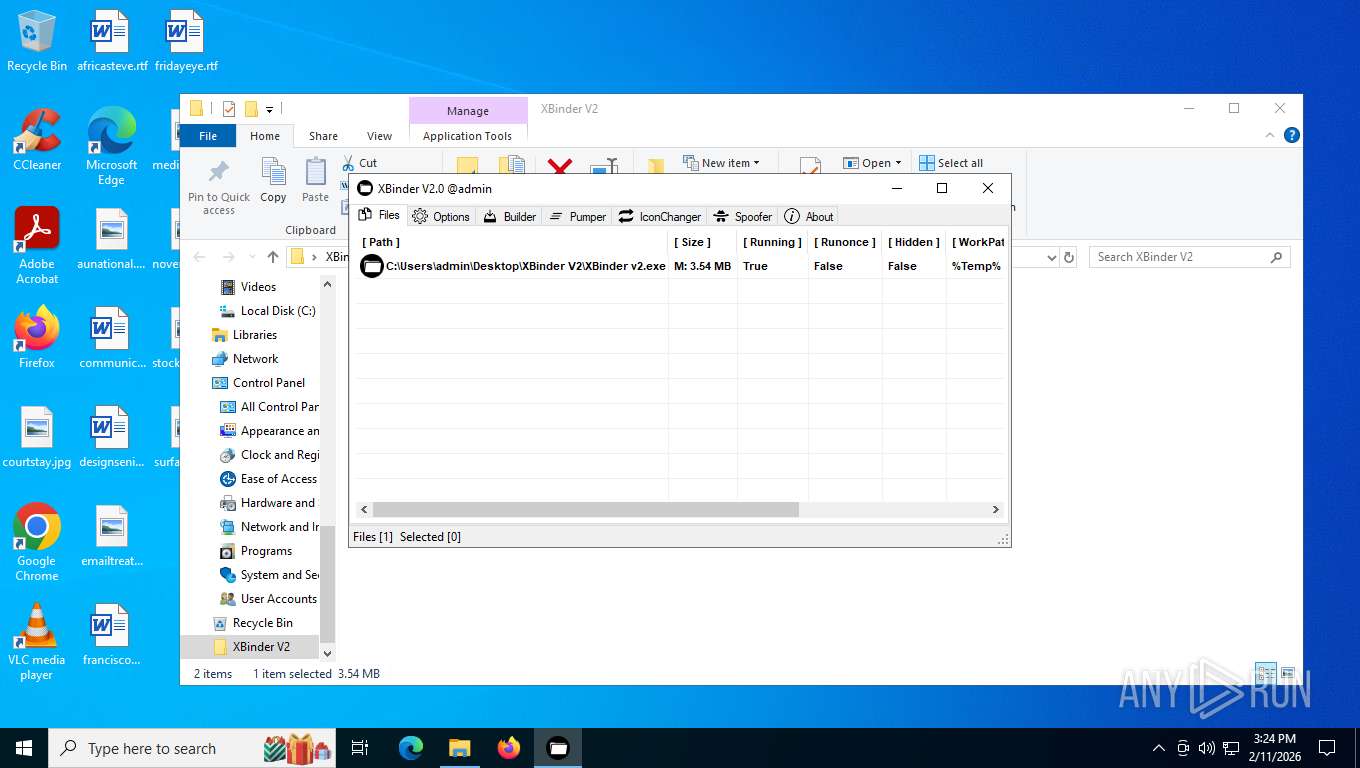
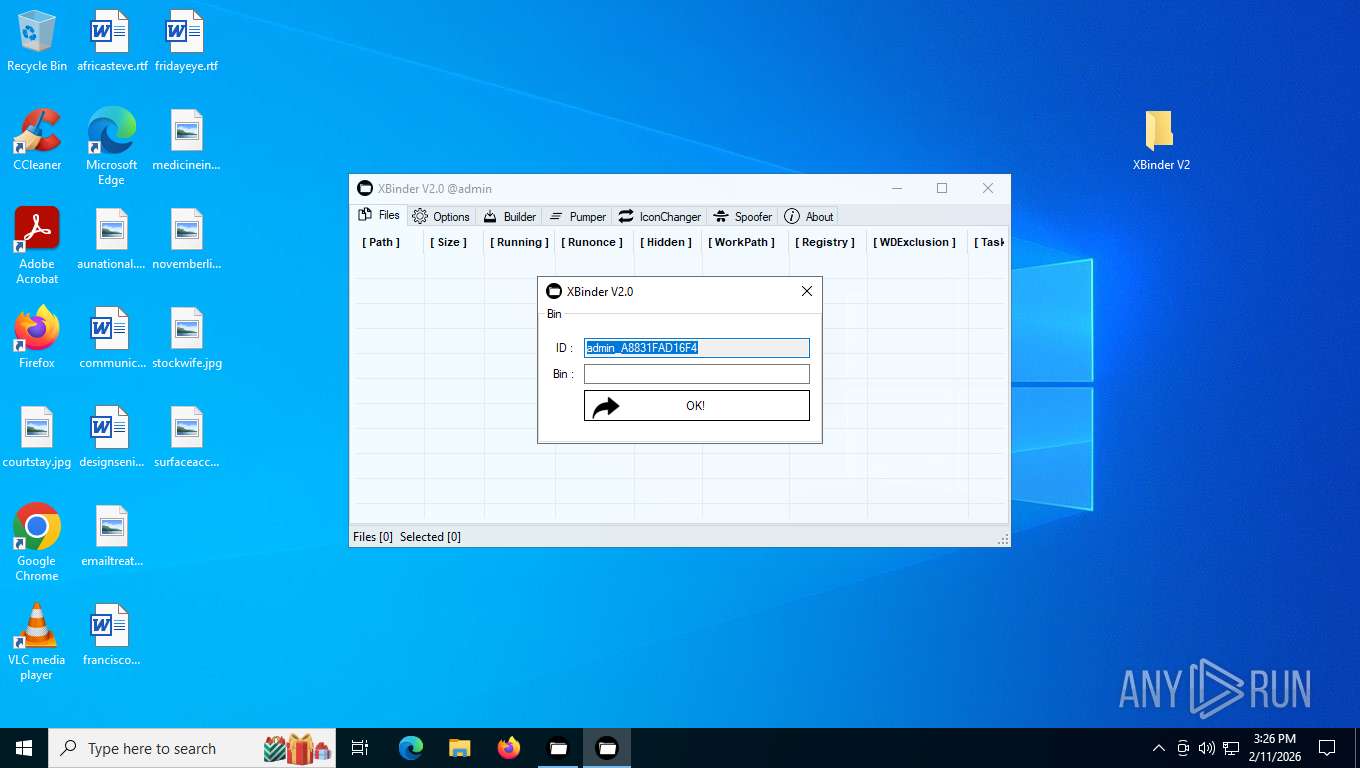
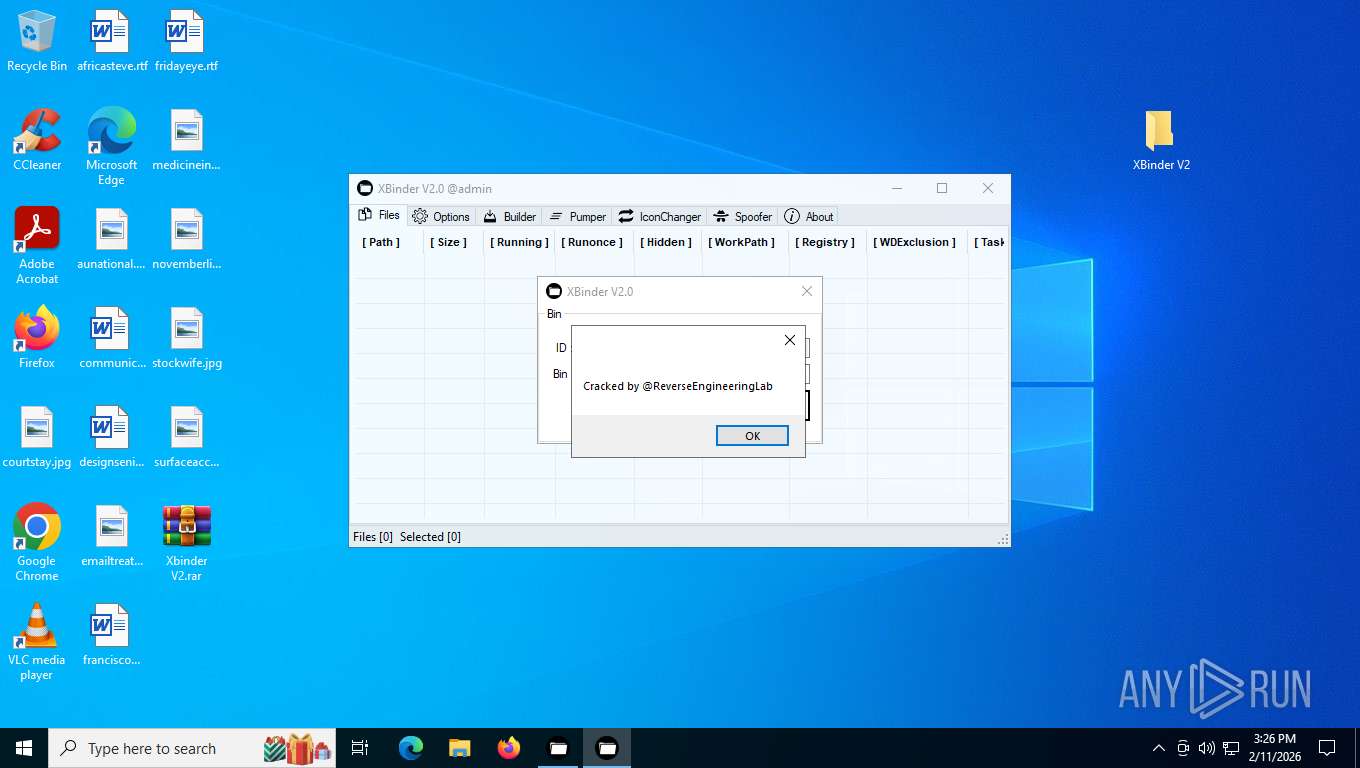
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 8108)
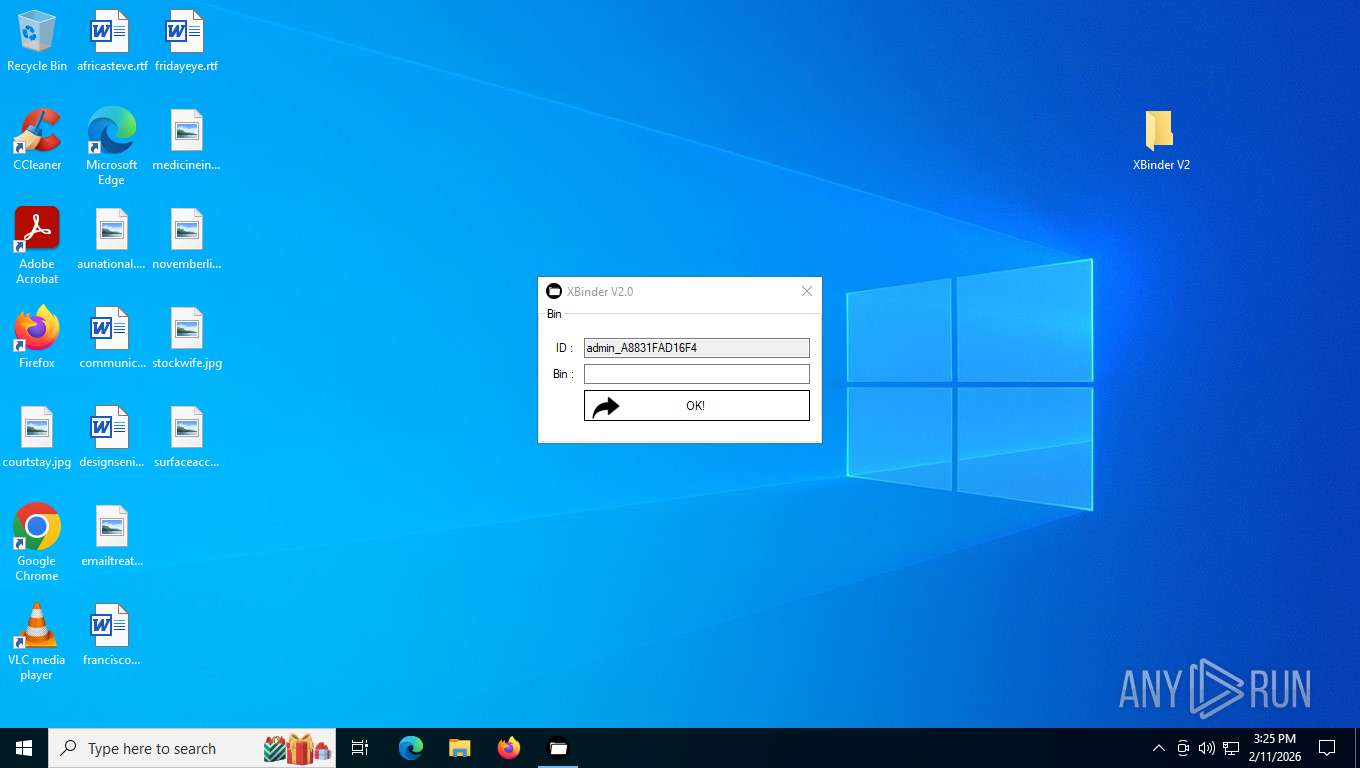
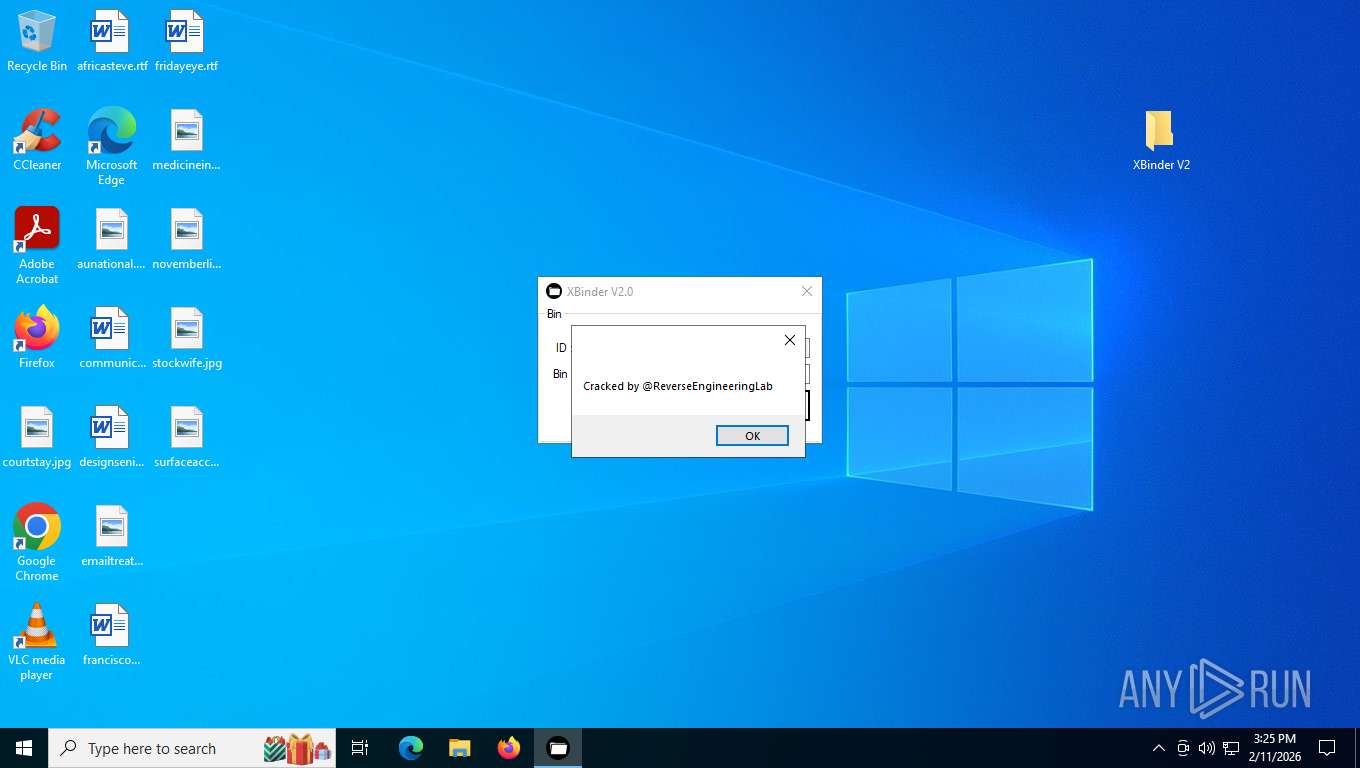
XORed URL has been found (YARA)
- XBinder v2.exe (PID: 7644)
- XBinder v2.exe (PID: 6172)
- XBinder v2.exe (PID: 6516)
AGENTTESLA has been detected
- XBinder v2.exe (PID: 7644)
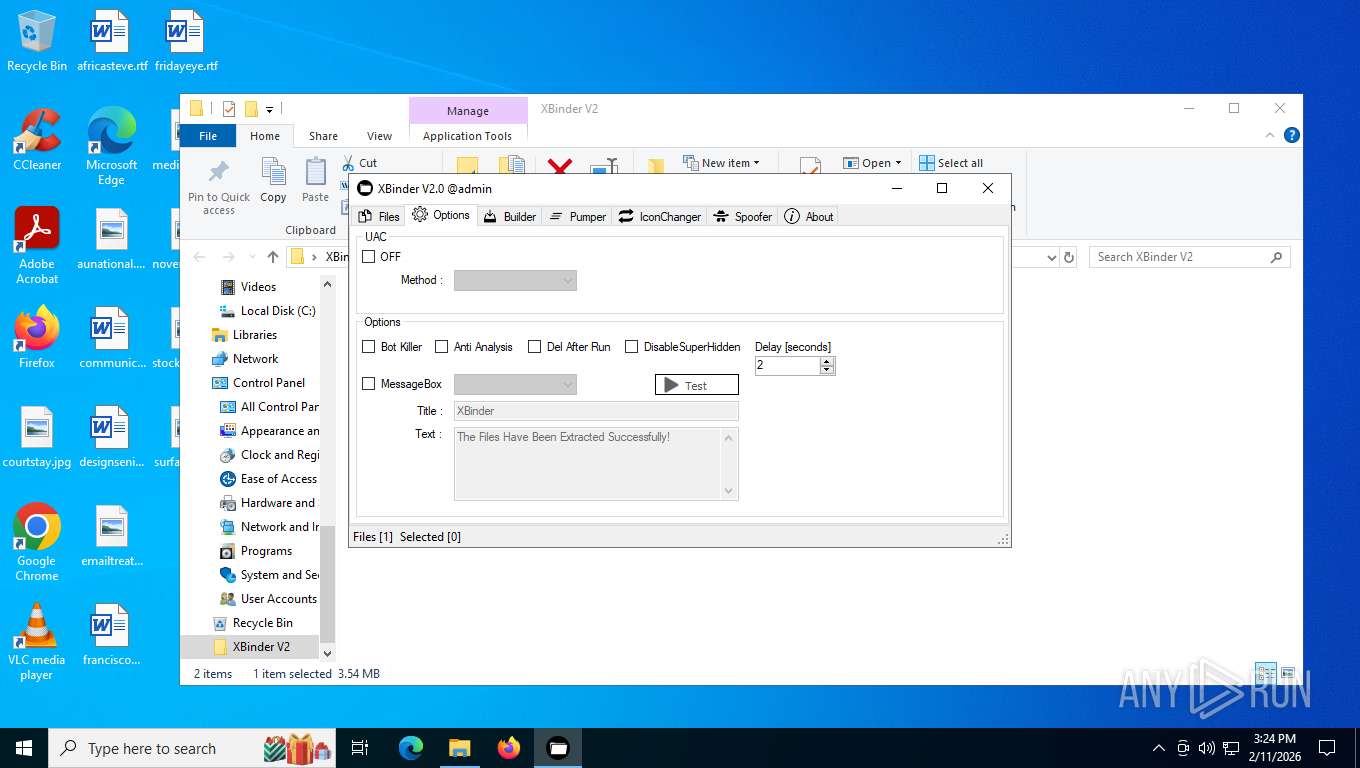
SUSPICIOUS
There is functionality for capture public ip (YARA)
- XBinder v2.exe (PID: 7644)
- XBinder v2.exe (PID: 6172)
- XBinder v2.exe (PID: 6516)
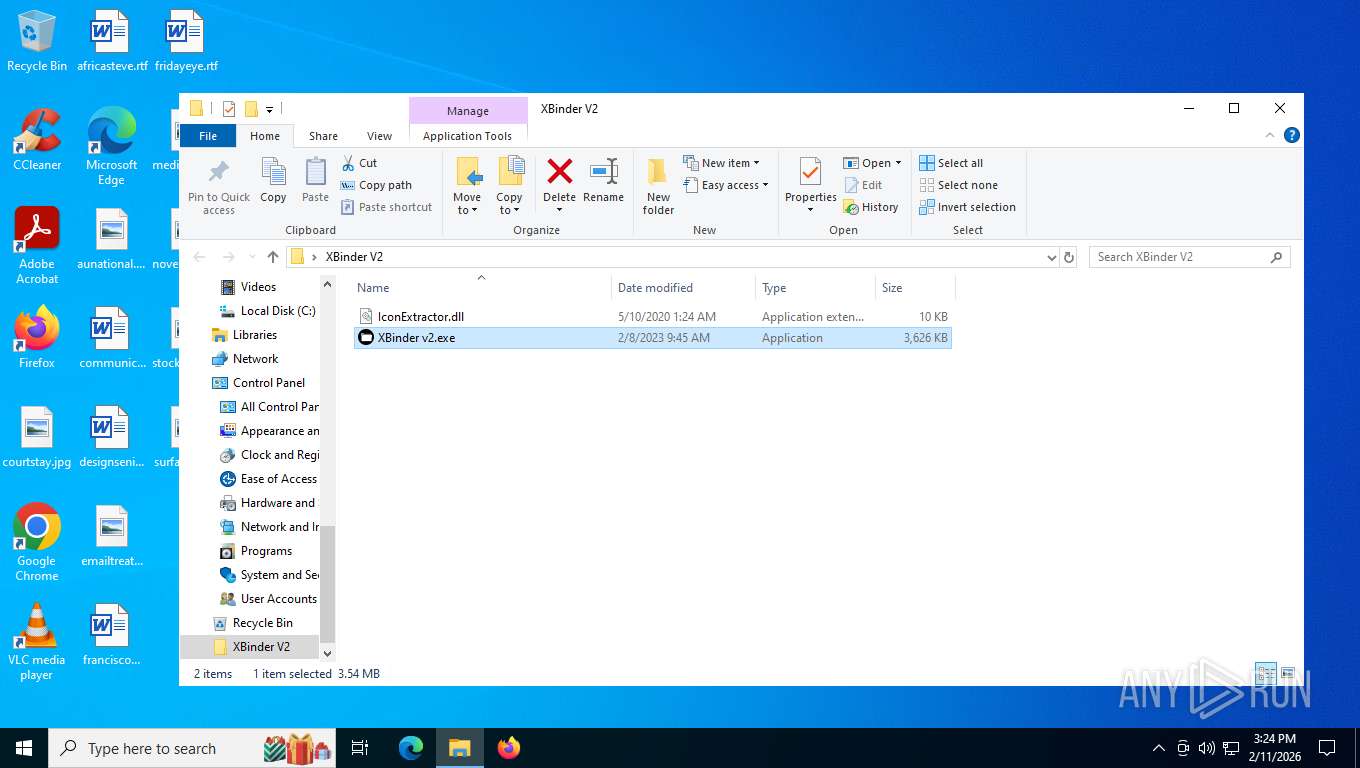
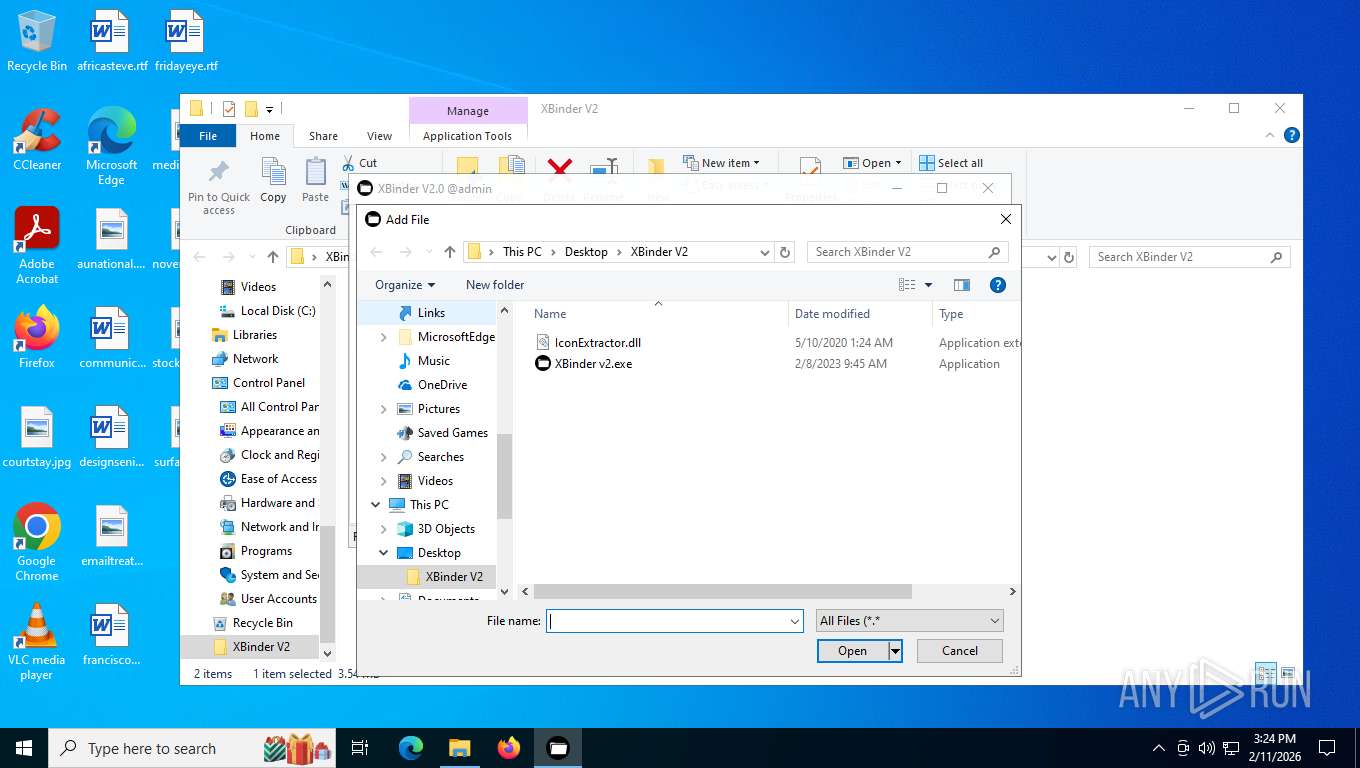
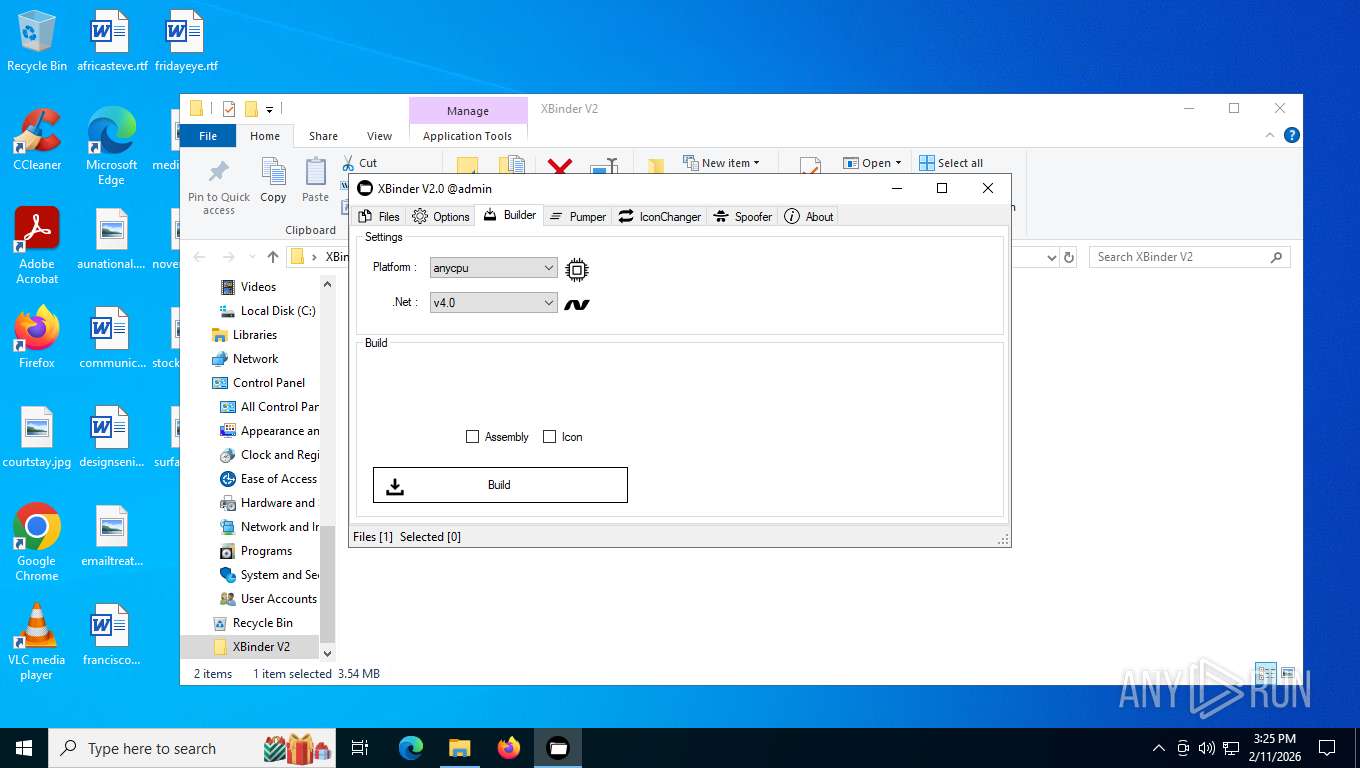
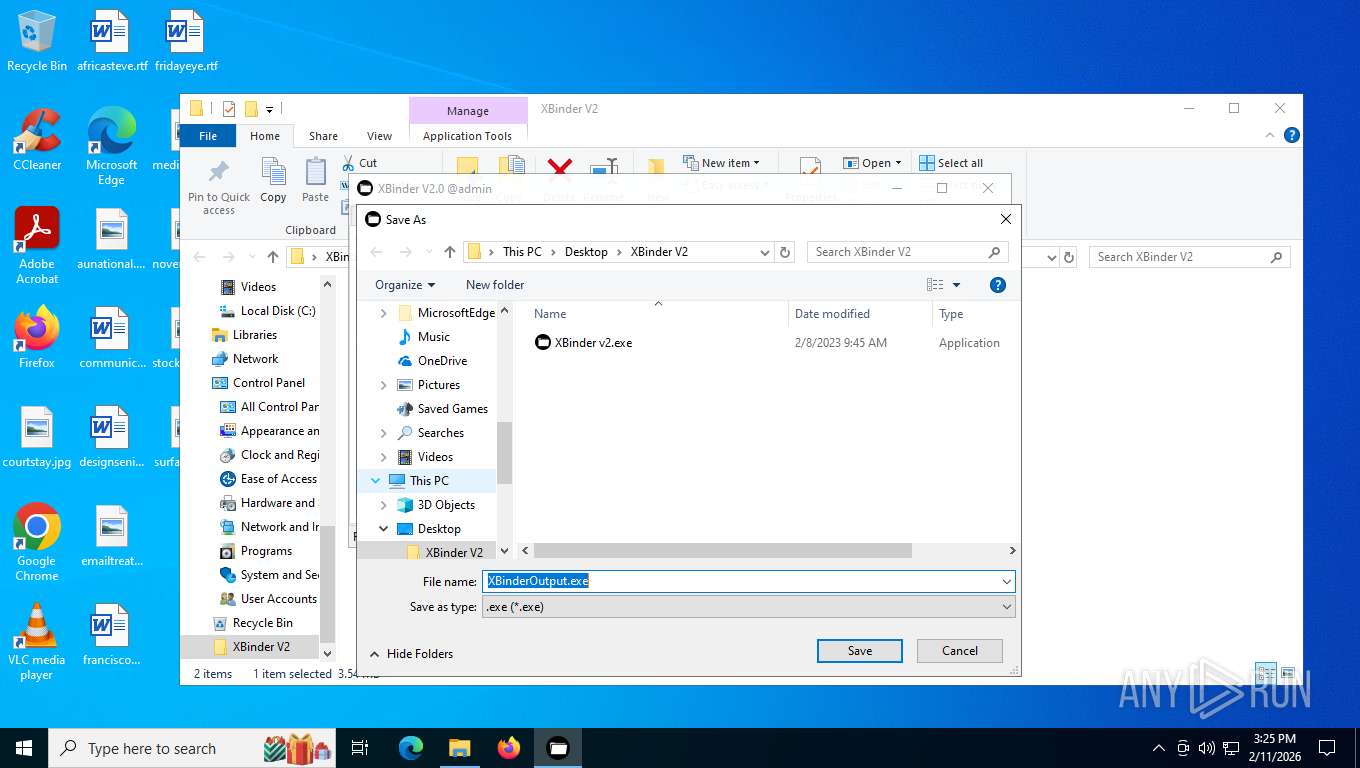
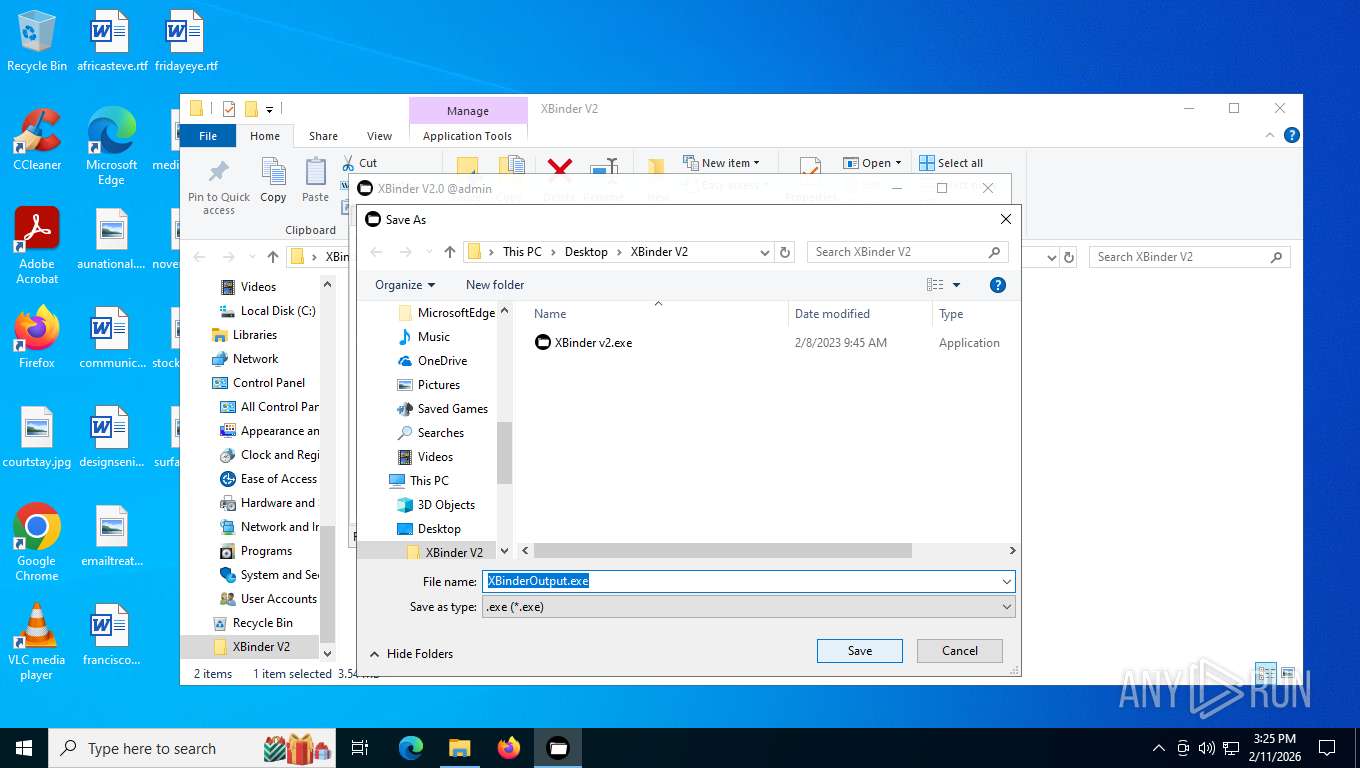
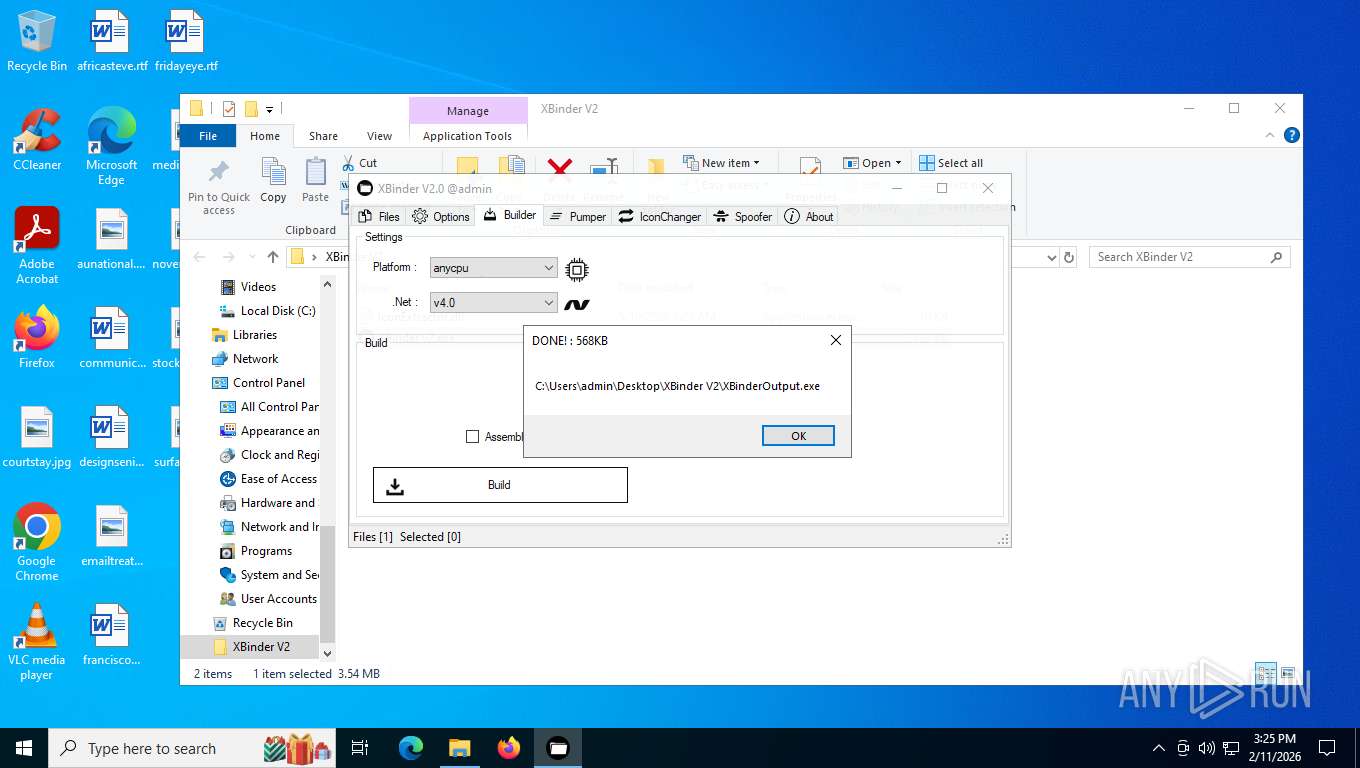
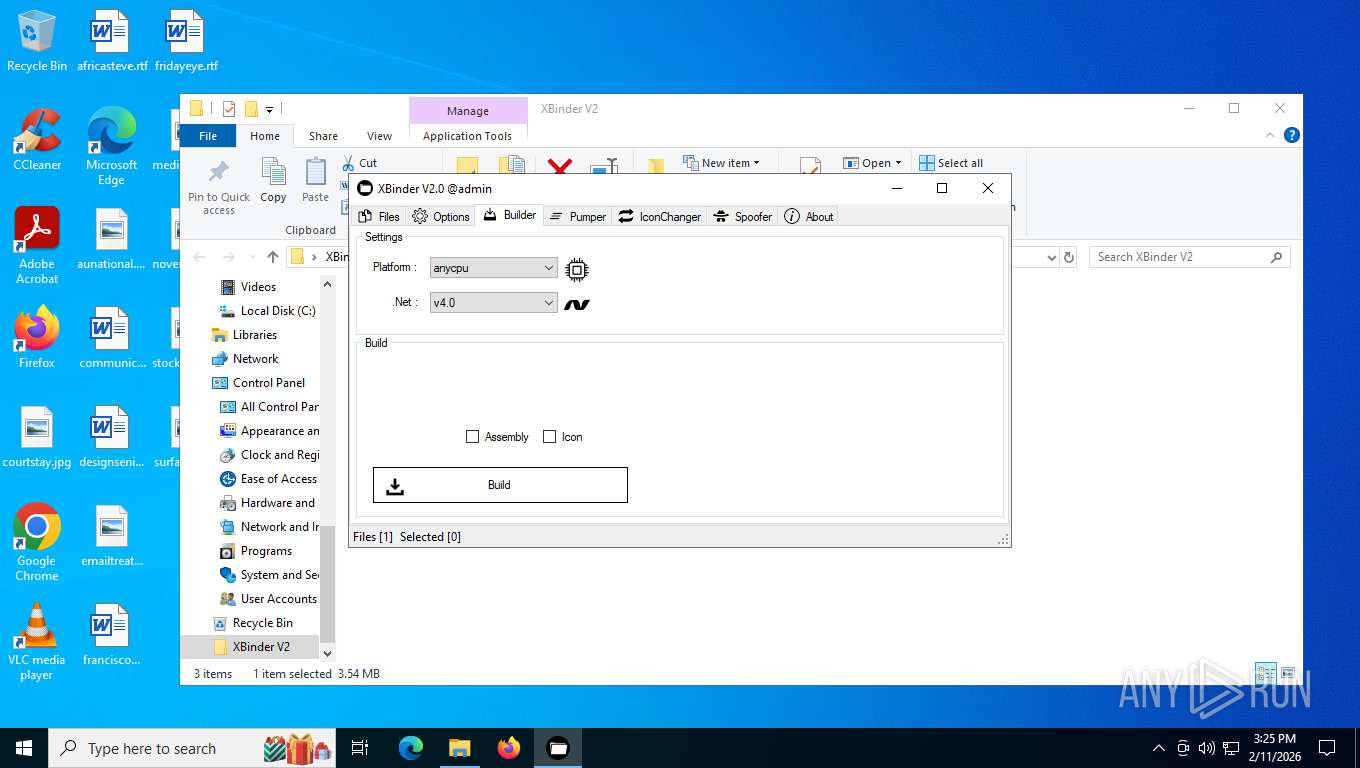
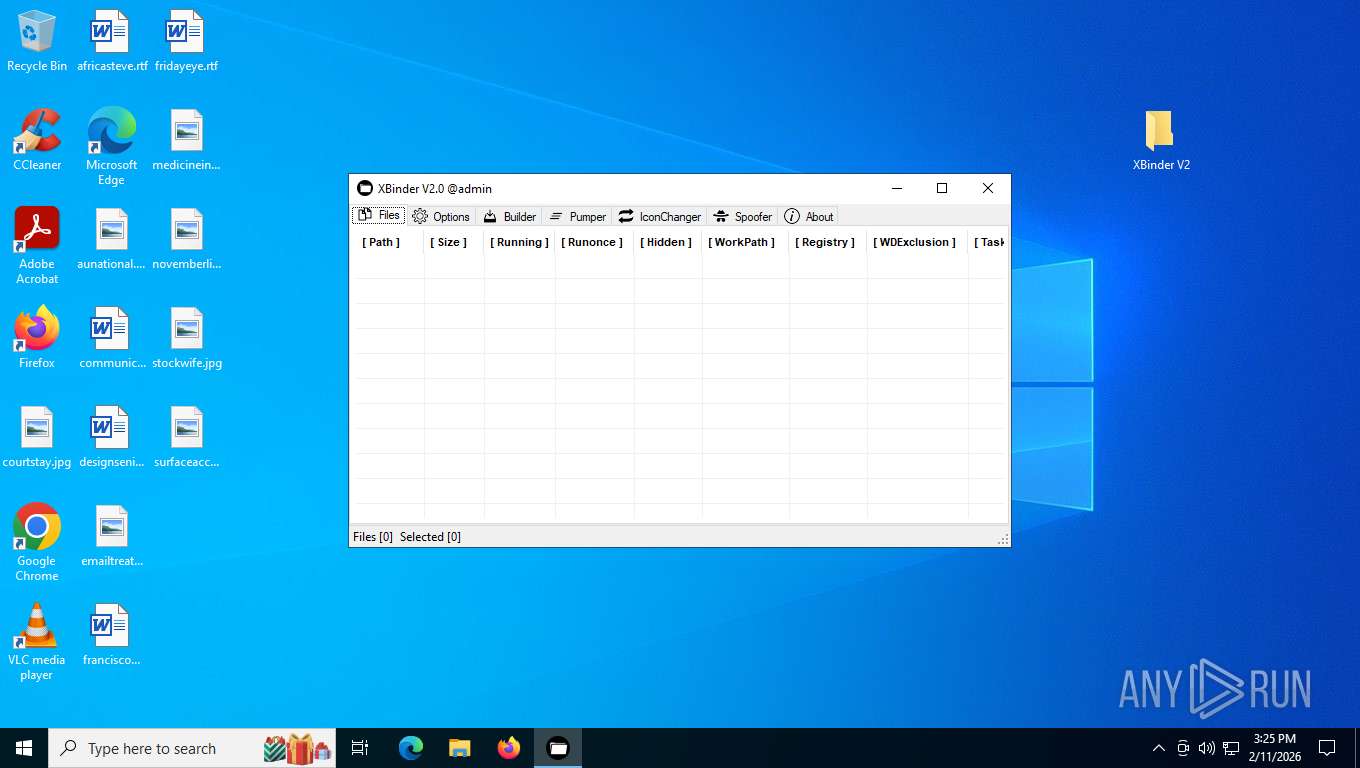
Executable content was dropped or overwritten
- vbc.exe (PID: 7280)
- XBinderOutput.exe (PID: 3916)
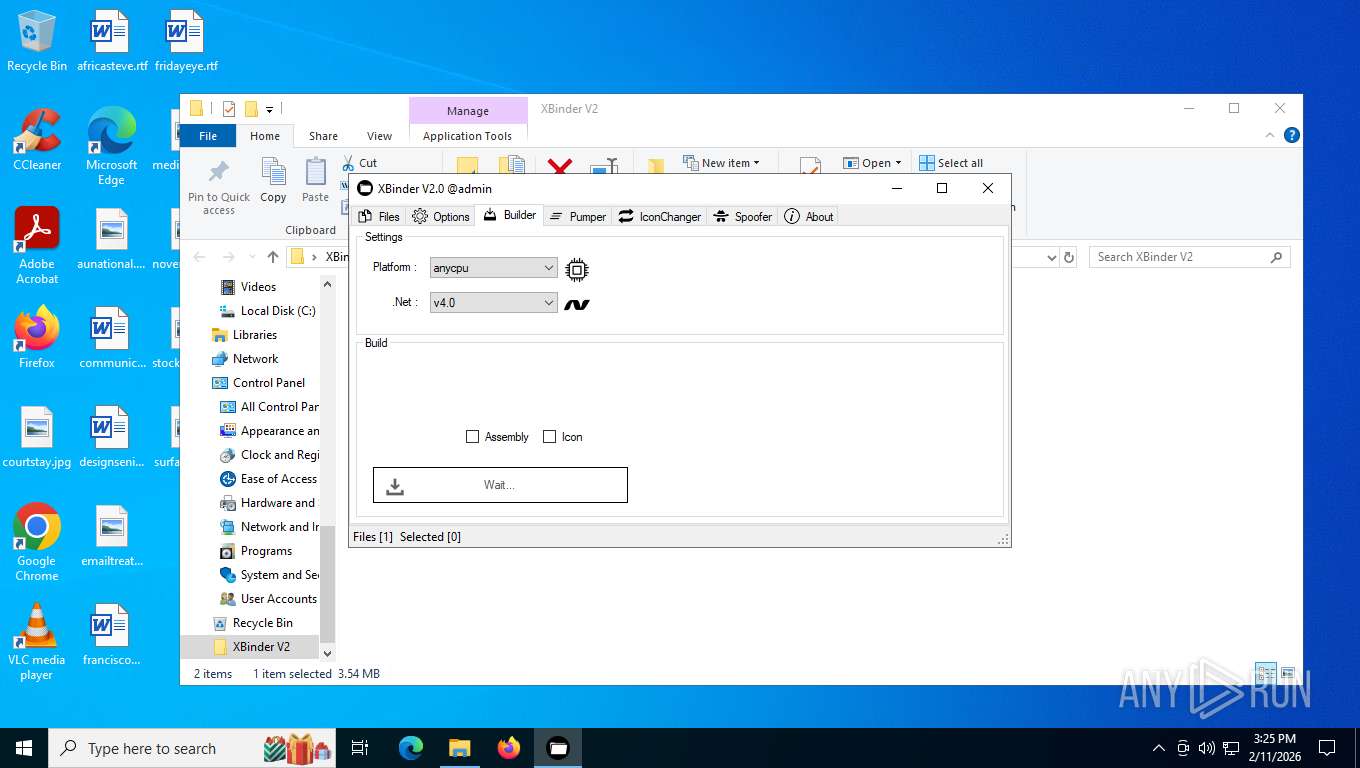
Application launched itself
- XBinderOutput.exe (PID: 5460)
Reads the date of Windows installation
- XBinderOutput.exe (PID: 5460)
- XBinderOutput.exe (PID: 3916)
INFO
Reads the computer name
- XBinder v2.exe (PID: 7644)
- XBinderOutput.exe (PID: 3916)
- XBinder v2.exe (PID: 6172)
- XBinderOutput.exe (PID: 5460)
- XBinder v2.exe (PID: 6516)
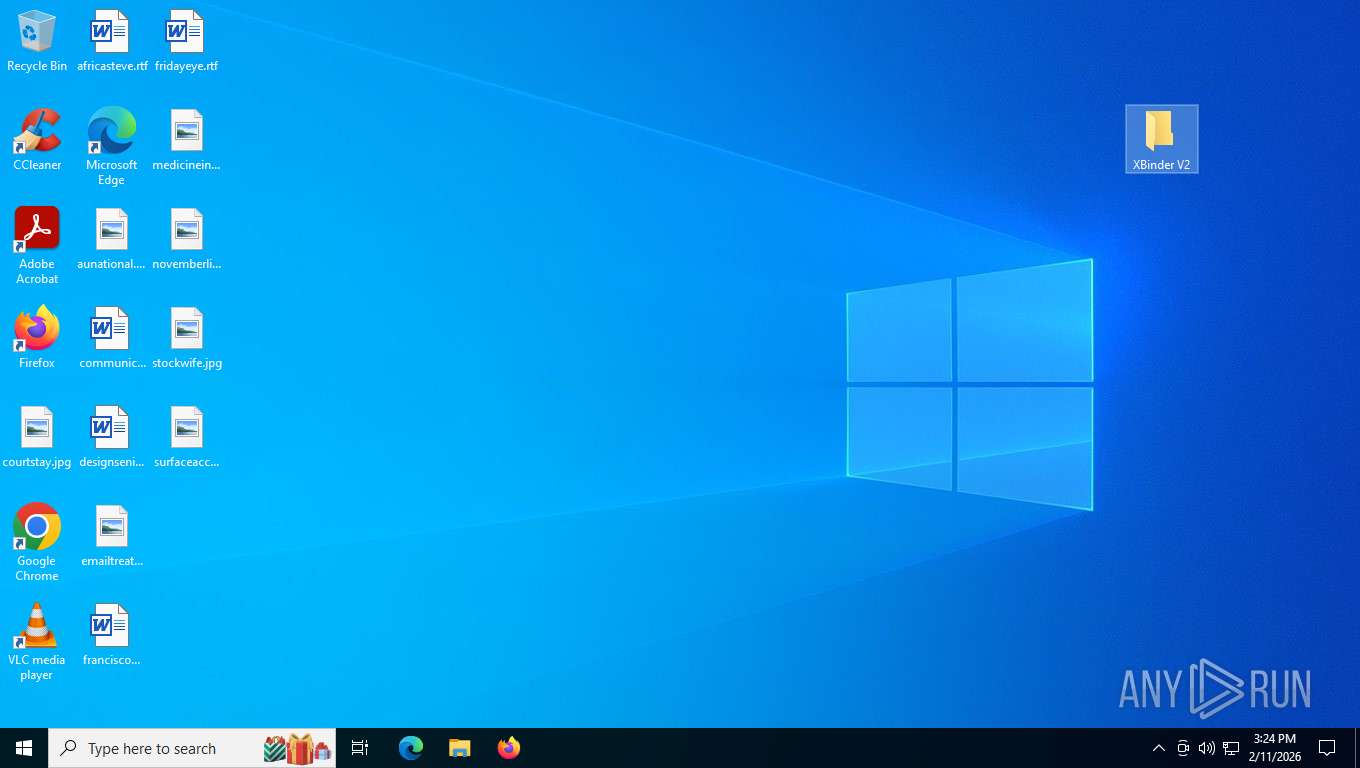
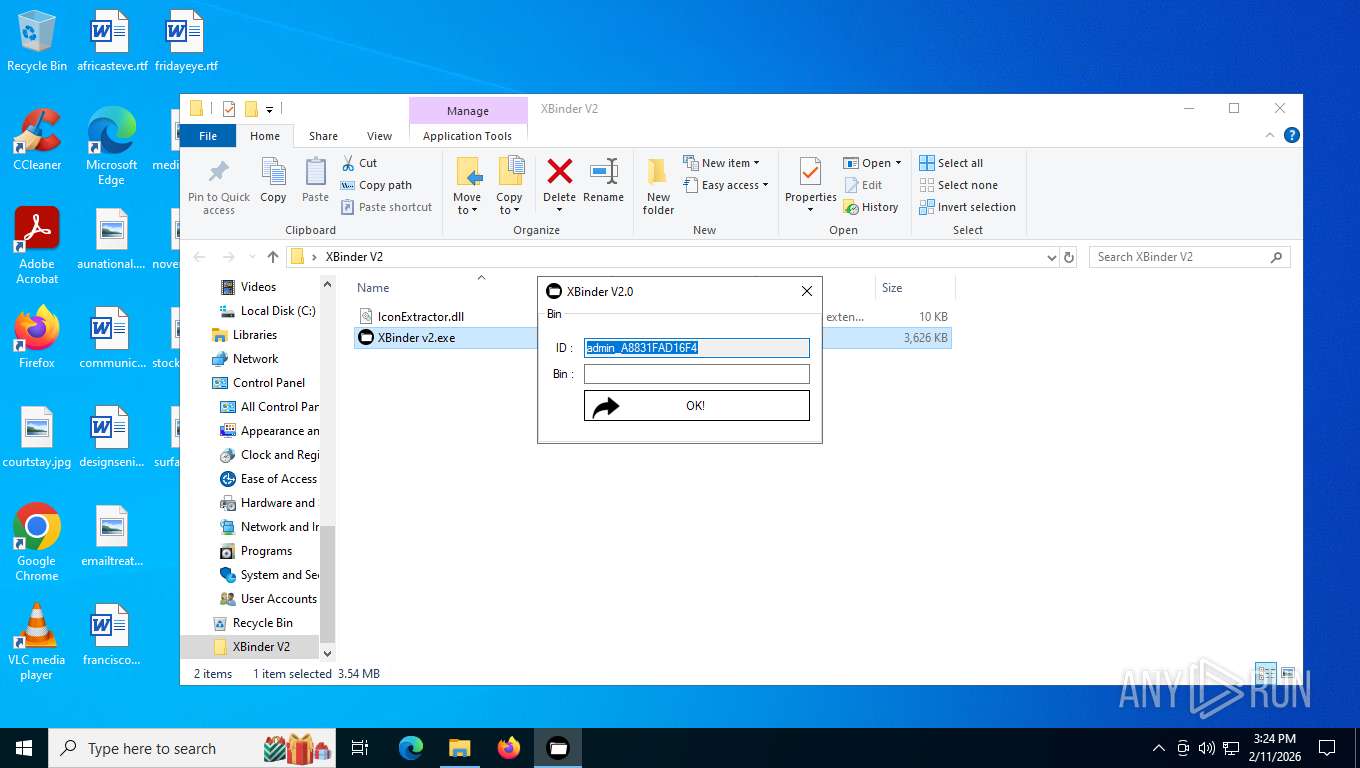
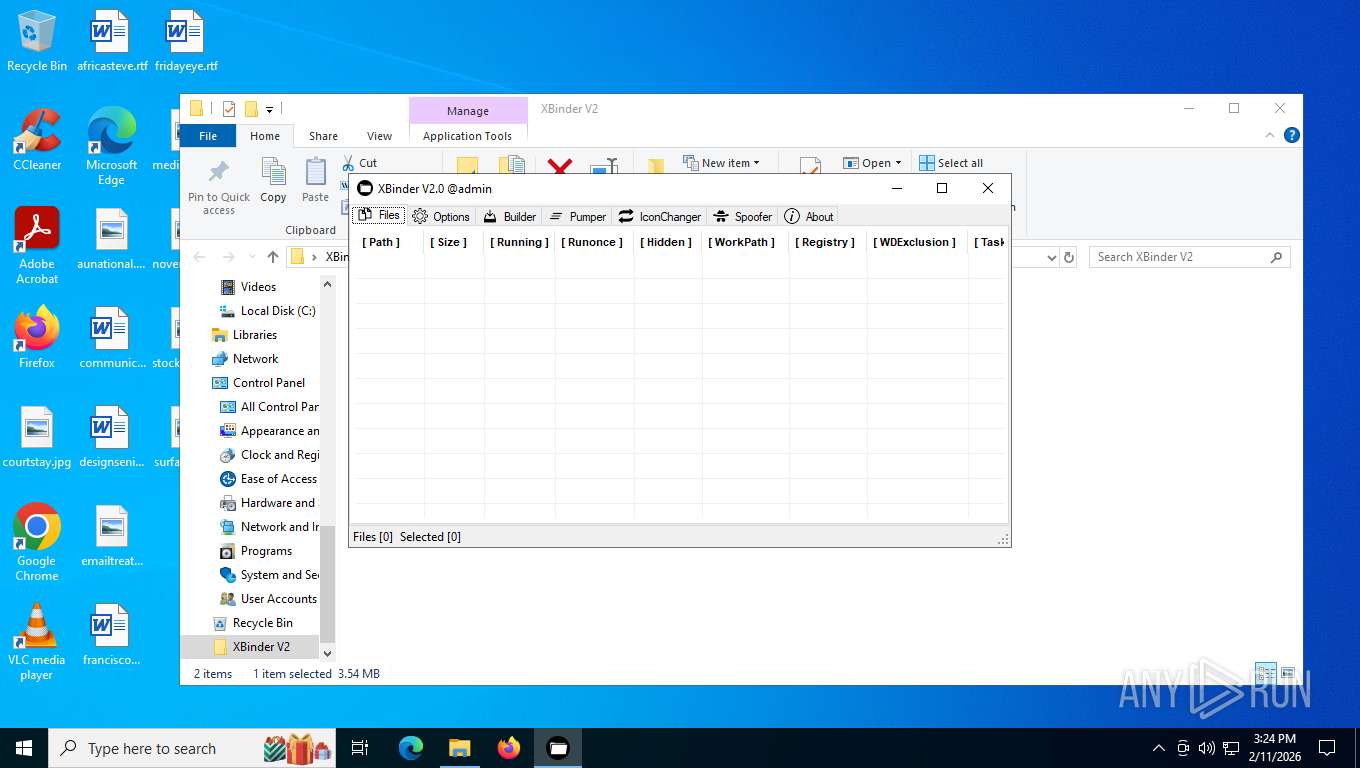
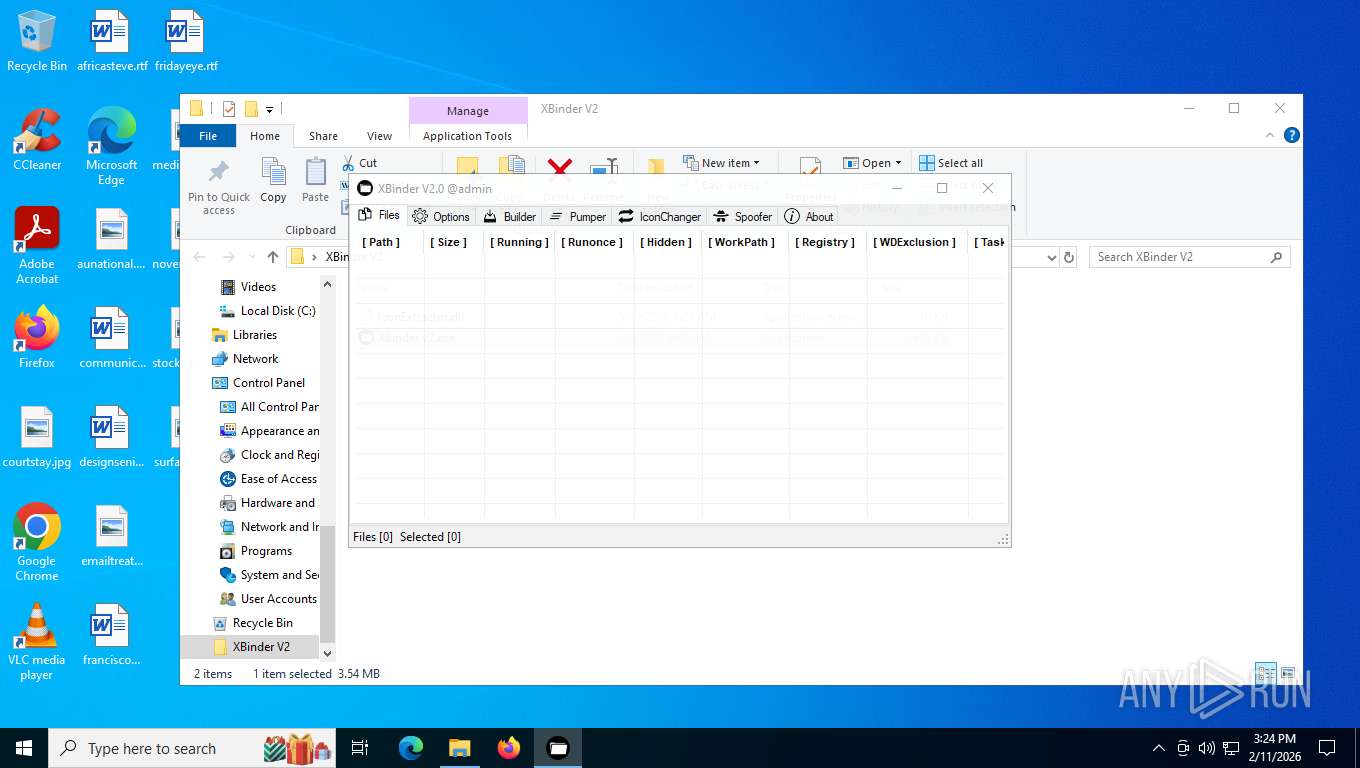
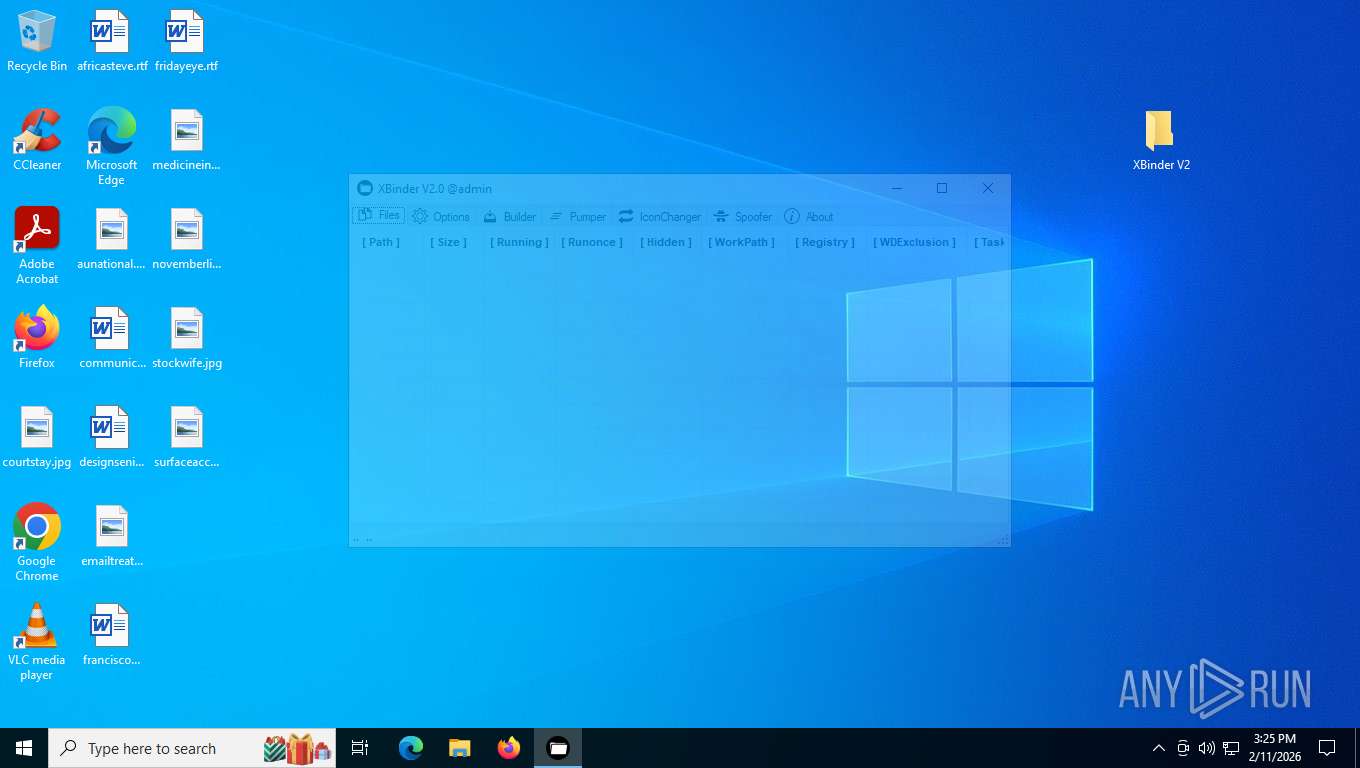
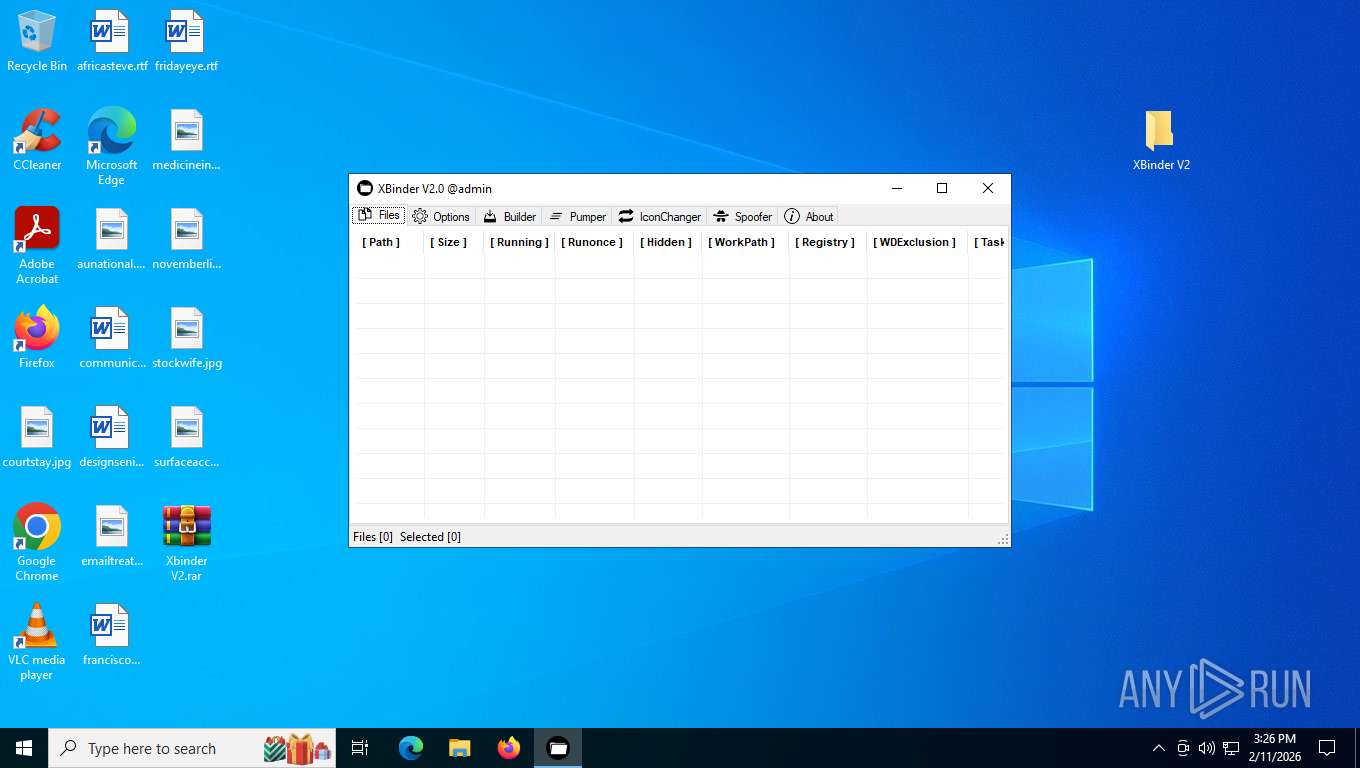
Manual execution by a user
- XBinder v2.exe (PID: 7644)
- XBinderOutput.exe (PID: 5460)
- XBinder v2.exe (PID: 6516)
Checks supported languages
- XBinder v2.exe (PID: 7644)
- vbc.exe (PID: 7280)
- cvtres.exe (PID: 552)
- XBinderOutput.exe (PID: 3916)
- XBinder v2.exe (PID: 6172)
- XBinderOutput.exe (PID: 5460)
- XBinder v2.exe (PID: 6516)
Reads the machine GUID from the registry
- XBinder v2.exe (PID: 7644)
- vbc.exe (PID: 7280)
- XBinderOutput.exe (PID: 3916)
- XBinder v2.exe (PID: 6172)
- XBinder v2.exe (PID: 6516)
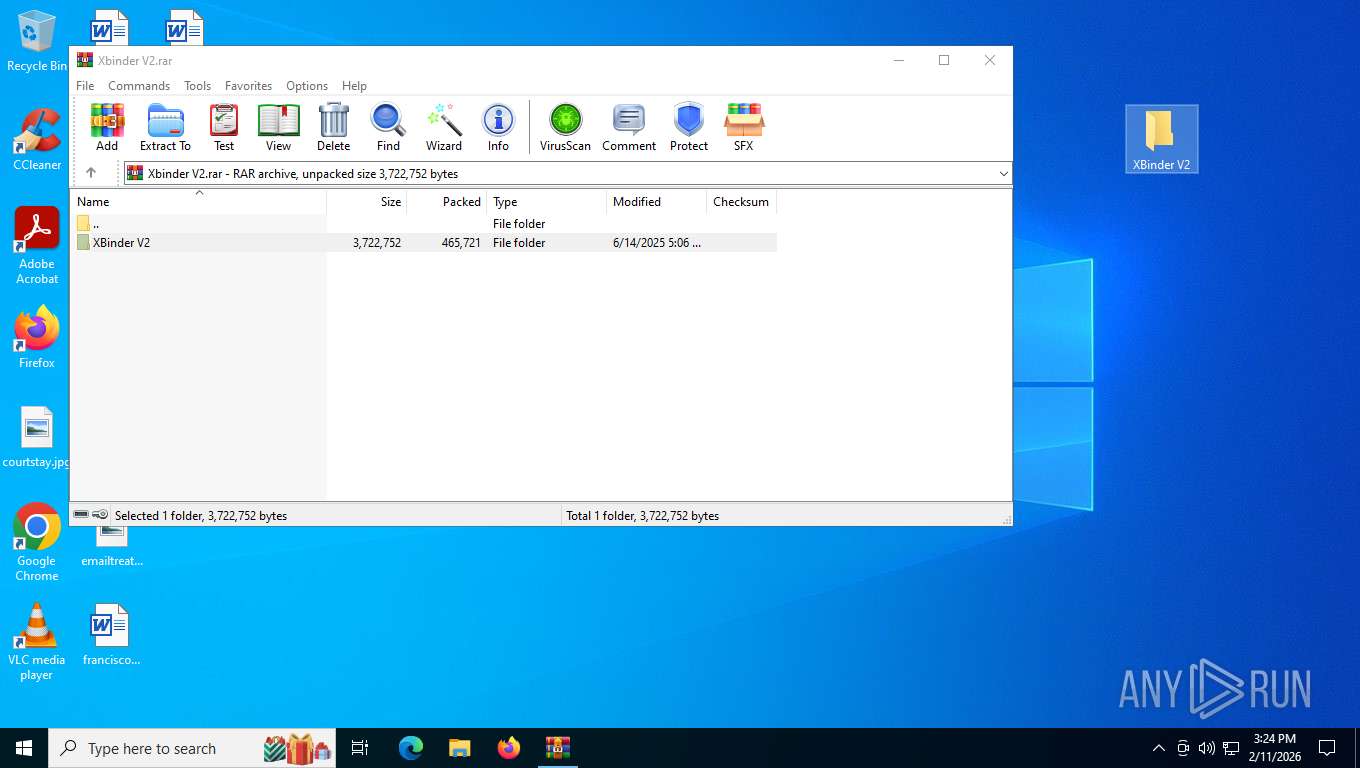
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8108)
Create files in a temporary directory
- XBinder v2.exe (PID: 7644)
- vbc.exe (PID: 7280)
- cvtres.exe (PID: 552)
- XBinderOutput.exe (PID: 3916)
Detects Babel protector (YARA)
- XBinder v2.exe (PID: 7644)
- XBinder v2.exe (PID: 6172)
- XBinder v2.exe (PID: 6516)
Detects Yano protector (YARA)
- XBinder v2.exe (PID: 7644)
- XBinder v2.exe (PID: 6172)
- XBinder v2.exe (PID: 6516)
Reads security settings of Internet Explorer
- XBinder v2.exe (PID: 7644)
- XBinderOutput.exe (PID: 3916)
- XBinderOutput.exe (PID: 5460)
Process checks computer location settings
- XBinderOutput.exe (PID: 5460)
- XBinderOutput.exe (PID: 3916)
Checks proxy server information
- slui.exe (PID: 5772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 4735 |
| UncompressedSize: | 10240 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | XBinder V2/IconExtractor.dll |
Total processes
157
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4CB2.tmp" "C:\Users\admin\AppData\Local\Temp\vbc35D3D386CF224A7393EA5D9DEE45D78A.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | vbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | vbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
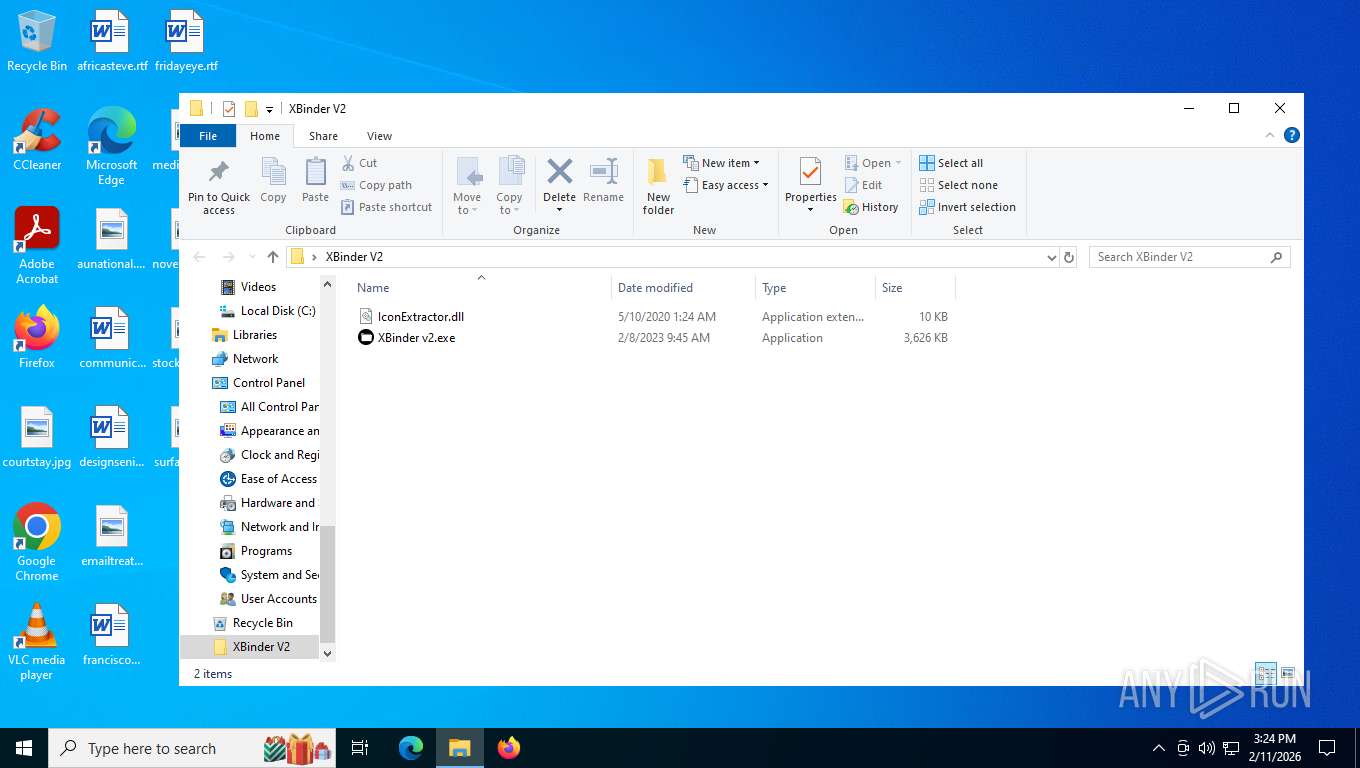
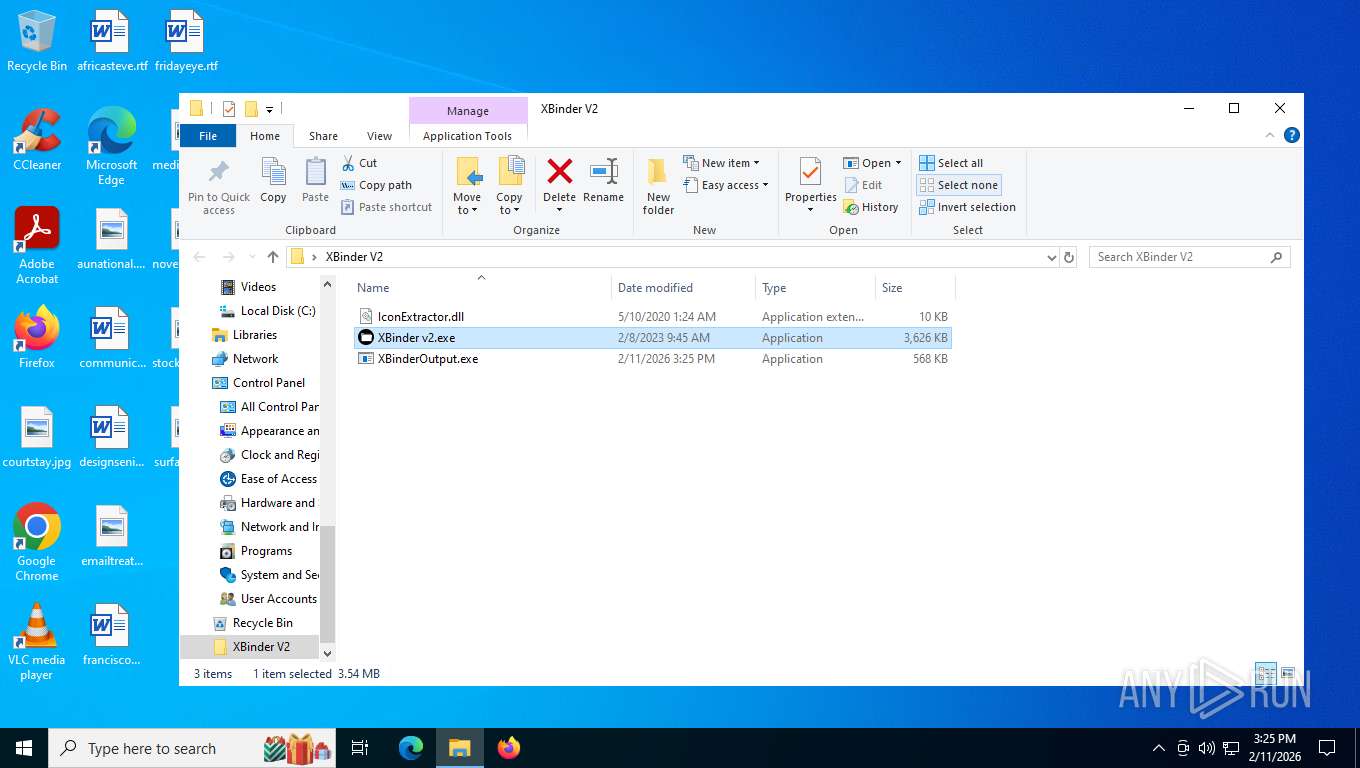
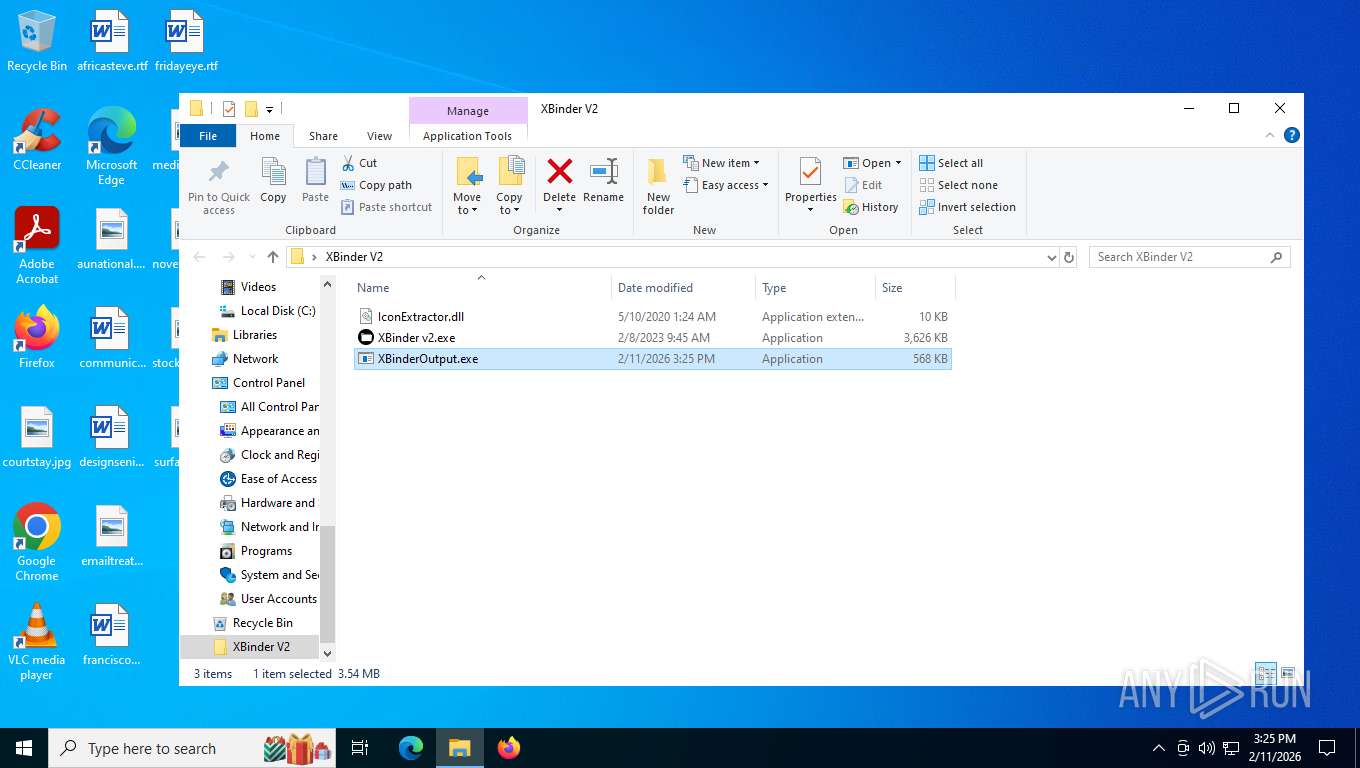
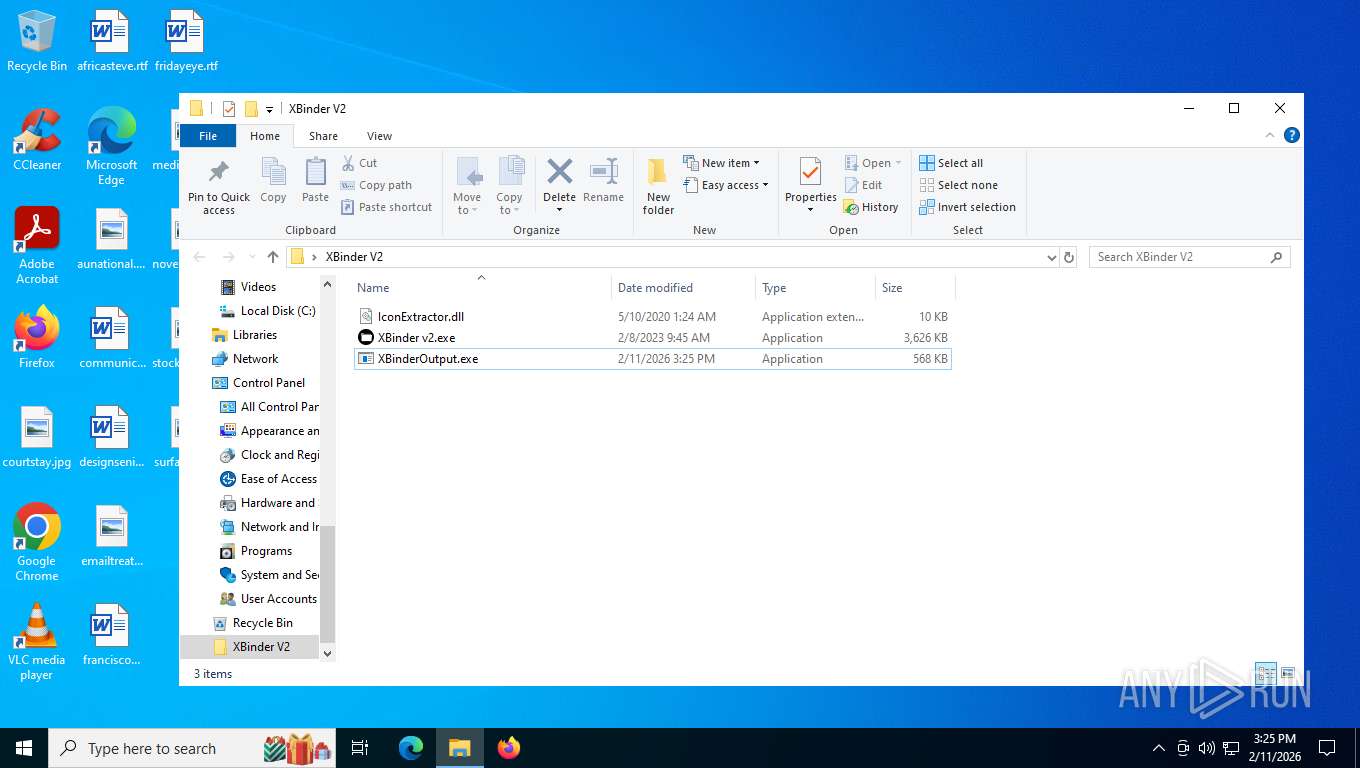
| 3916 | "C:\Users\admin\Desktop\XBinder V2\XBinderOutput.exe" | C:\Users\admin\Desktop\XBinder V2\XBinderOutput.exe | XBinderOutput.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5460 | "C:\Users\admin\Desktop\XBinder V2\XBinderOutput.exe" | C:\Users\admin\Desktop\XBinder V2\XBinderOutput.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5772 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6172 | "C:\Users\admin\AppData\Local\Temp\XBinder v2.exe" | C:\Users\admin\AppData\Local\Temp\XBinder v2.exe | XBinderOutput.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: XBinder Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 6516 | "C:\Users\admin\Desktop\XBinder V2\XBinder v2.exe" | C:\Users\admin\Desktop\XBinder V2\XBinder v2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: XBinder Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 7280 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\vbc.exe" /noconfig @"C:\Users\admin\AppData\Local\Temp\dutlx1kx.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\vbc.exe | XBinder v2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.8.9037.0 Modules
| |||||||||||||||
| 7644 | "C:\Users\admin\Desktop\XBinder V2\XBinder v2.exe" | C:\Users\admin\Desktop\XBinder V2\XBinder v2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: XBinder Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 8108 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Xbinder V2.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
33 424
Read events
33 330
Write events
91
Delete events
3
Modification events
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Xbinder V2.rar | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (8108) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7644 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\dutlx1kx.cmdline | text | |
MD5:95E28209C1D10D56AC381A09780D540C | SHA256:22804C3C7DE80694F373F5DA866BACDFEAB9745C487942148672CF5781072F81 | |||
| 7644 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\bbkgtpwmhqblxv.Resources | binary | |
MD5:EE7A5B5B73F3E601CAA3A5E7D82D7192 | SHA256:D0FD4810670E60EF5FA969E9C35ACCCA7BCBD4A1BA3ACACDA121D2668B3D9C53 | |||
| 8108 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8108.9925\XBinder V2\IconExtractor.dll | executable | |
MD5:640D8FFA779C6DD5252A262E440C66C0 | SHA256:440912D85D2F98BB4F508AB82847067C18E1E15BE0D8ECDCFF0CC19327527FC2 | |||
| 8108 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8108.9925\XBinder V2\XBinder v2.exe | executable | |
MD5:A98358EB7F4953AA6D60015CCD8506CE | SHA256:21E0CC9EF715CC2147B9EC481B3FB876DBAE8A4491367B478513128D7F7B8555 | |||
| 7644 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\tmp4B98.tmp | binary | |
MD5:CAD3BAC031DCA335687B7FA21EAFAF82 | SHA256:0FC452E907D88F4B83C058135800F0317EEE22544D897939E633852597CFA33E | |||
| 7280 | vbc.exe | C:\Users\admin\AppData\Local\Temp\vbc35D3D386CF224A7393EA5D9DEE45D78A.TMP | binary | |
MD5:CE7EE761D5F0A9CCC4E37A527ACE11D6 | SHA256:D8DB9A7547590C3AFDB024EA67EC9026F367DC18C4D944F4980397628036108E | |||
| 7644 | XBinder v2.exe | C:\Users\admin\AppData\Local\Temp\dutlx1kx.0.vb | text | |
MD5:7E608D4C9AF857E074B351643FAD71D4 | SHA256:4FFABF6B63BAB531CE8C6C33E45F9176ABE97021B9C95231D67D6DD86F806E15 | |||
| 7280 | vbc.exe | C:\Users\admin\AppData\Local\Temp\vbcC95BF488C33D4D8186C99F33CB41D0E.TMP | binary | |
MD5:A3FD405DB9CEA79A2EA95E96A0E75558 | SHA256:0FF2BF47078D8ABAA3BD36CA9BBA95D112732555ABC968CF5B4957A493D0DF8E | |||
| 7280 | vbc.exe | C:\Users\admin\AppData\Local\Temp\dutlx1kx.out | text | |
MD5:CB3D0054859284E7977751B6F27646F1 | SHA256:F8A99FE9B1FC56FEA5A6C02C09B1EB8244D85584A1D9D2C29365FCFD652532D8 | |||
| 7280 | vbc.exe | C:\Users\admin\Desktop\XBinder V2\XBinderOutput.exe | executable | |
MD5:D0119FDC505B3444F70A67567B7D2021 | SHA256:B3A740878F7B7647F61FDA866095D95EAC111D5613CA69F151E734739EA1CE6F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
30
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
492 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 304 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 200 | 20.165.94.63:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
7624 | SIHClient.exe | GET | 304 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 960 b | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.160.132:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
492 | svchost.exe | GET | 200 | 184.24.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
492 | svchost.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
492 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8568 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.207:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
356 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
492 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |