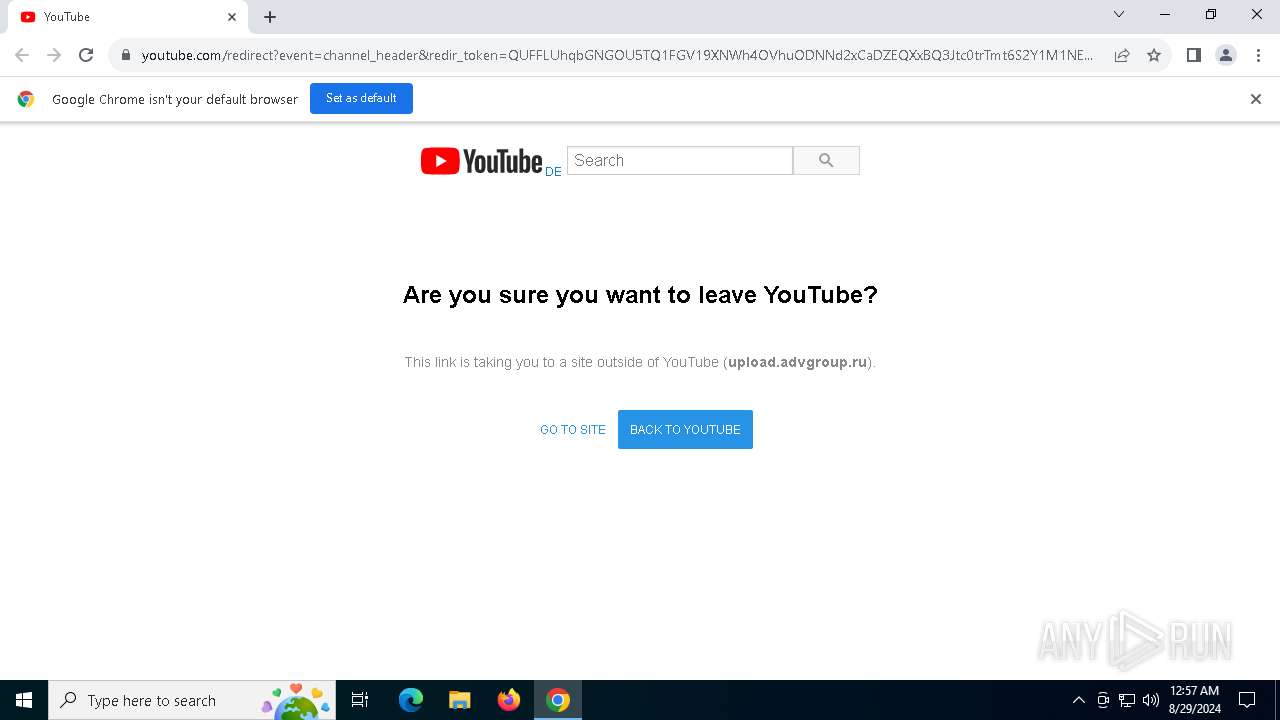
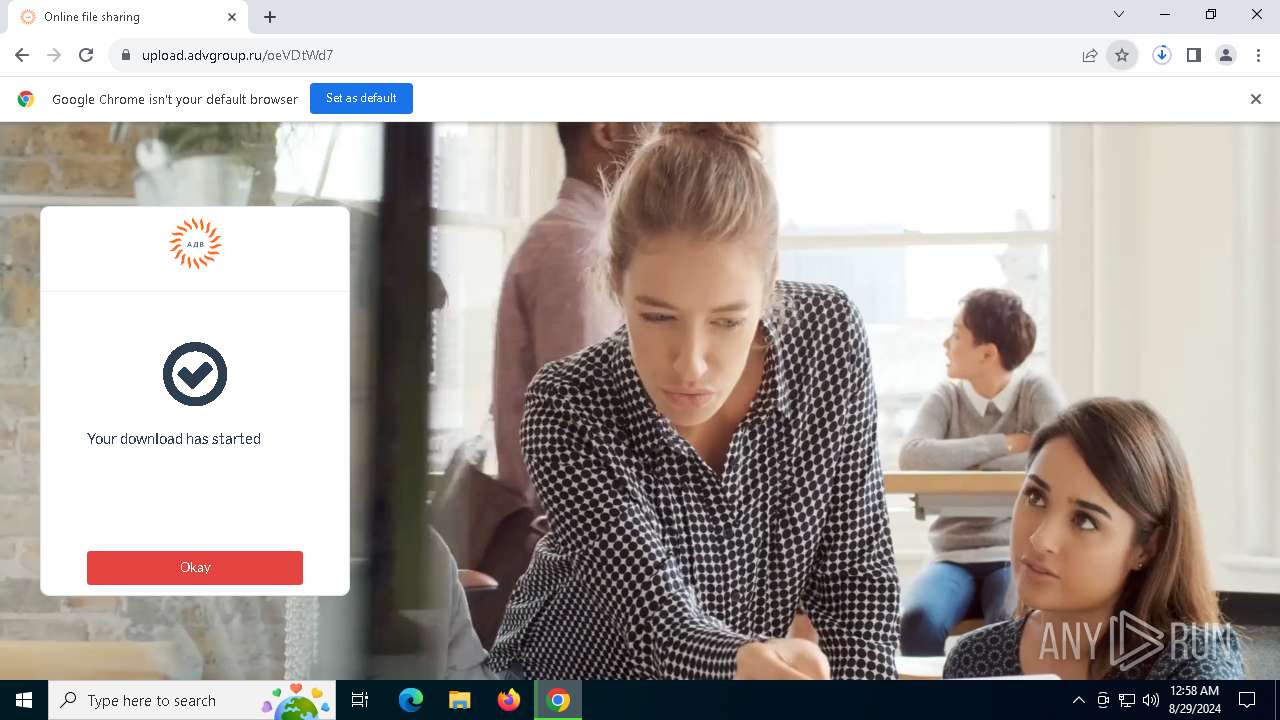
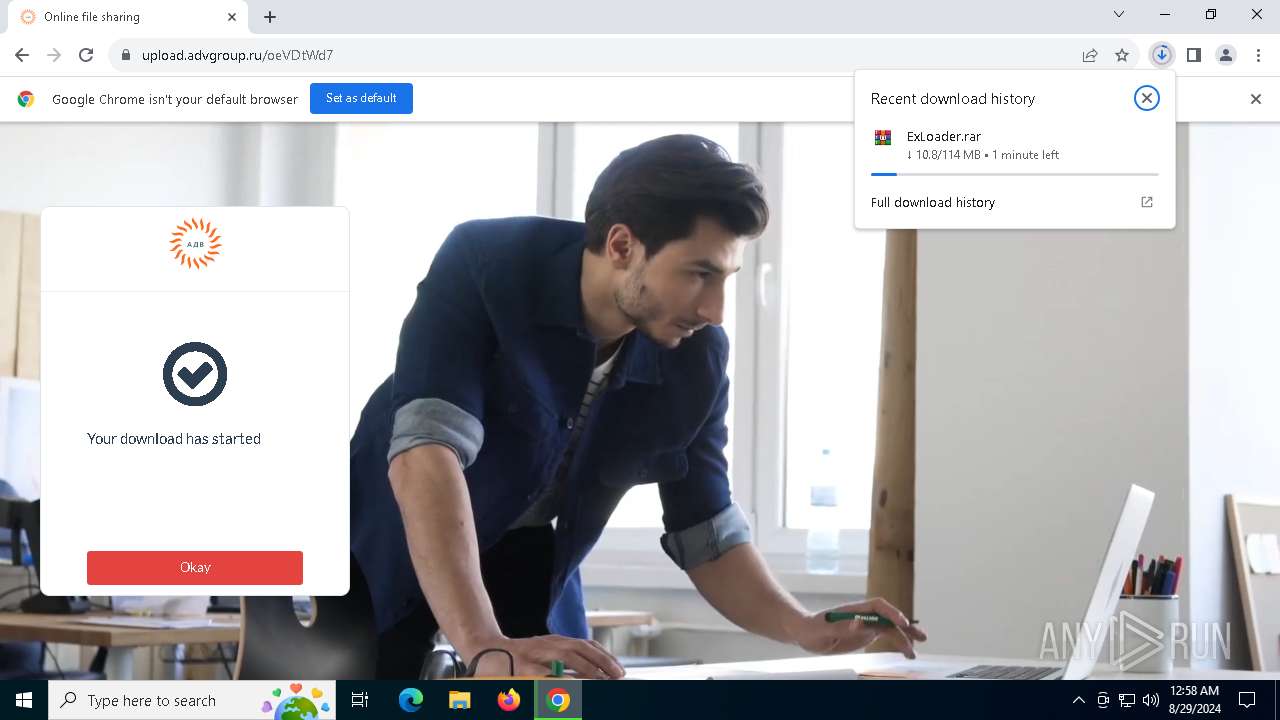
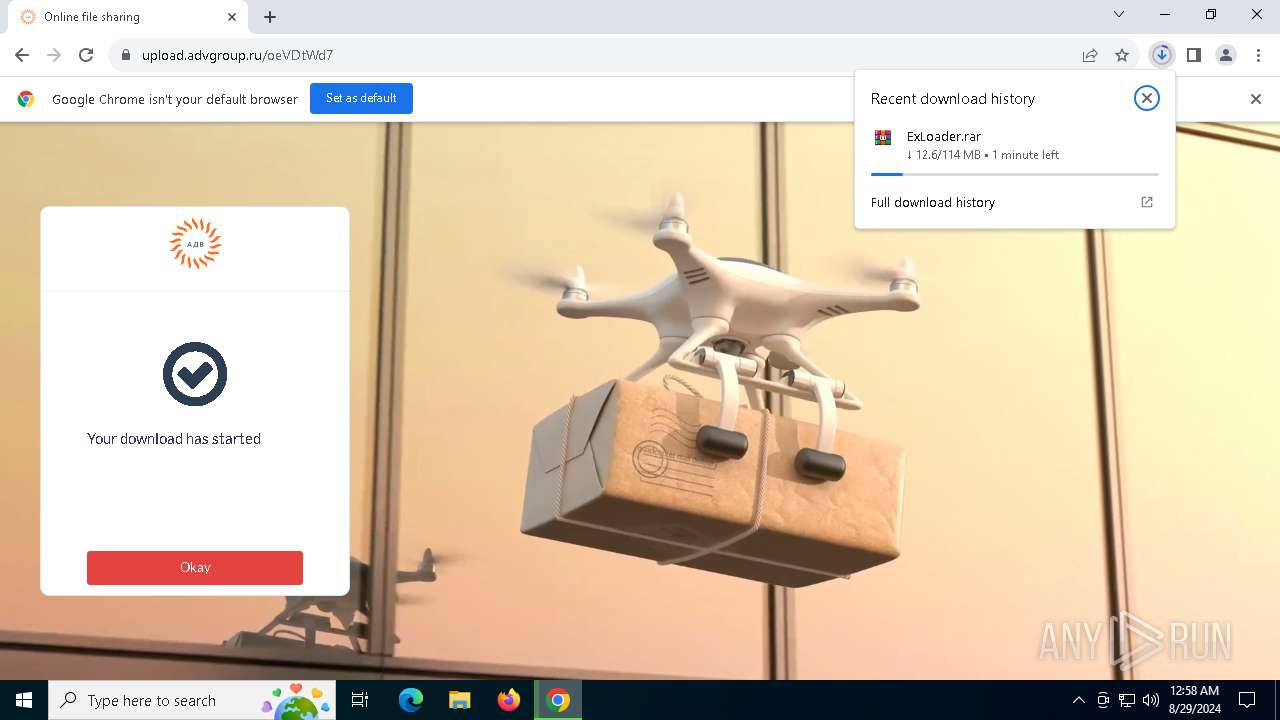
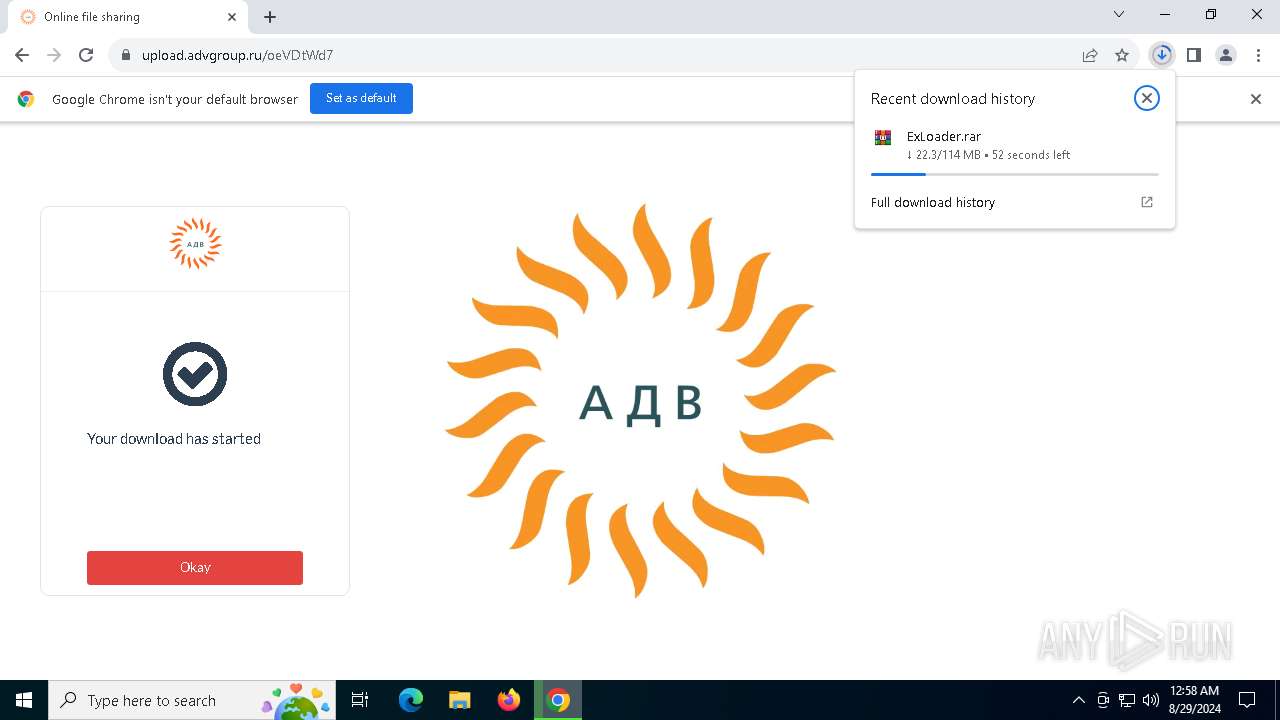
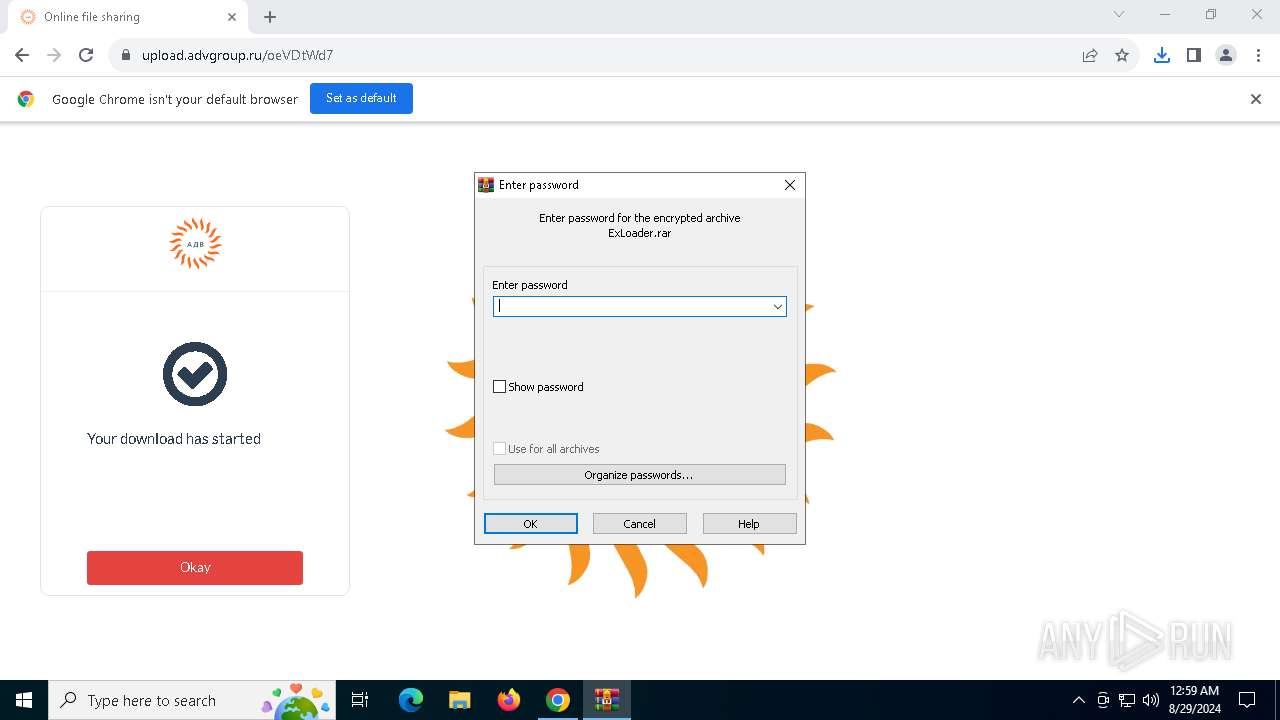
| URL: | https://www.youtube.com/redirect?event=channel_header&redir_token=QUFFLUhqbGNGOU5TQ1FGV19XNWh4OVhuODNNd2xCaDZEQXxBQ3Jtc0trTmt6S2Y1M1NEWG9zYlB3c29RN3pSVFJtNUVlcDk4bkVnUWh6UlpJZmo4UkphQmhWUjE1VzF0RTNFSDd4bWE0TDVyWnNGSGlEUzhGRmkzQWtLV0lkNHBhaENkSWMzZEdJYWc3c2ZjdUxLaUhBUGdWSQ&q=upload.advgroup.ru%2FoeVDtWd7 |
| Full analysis: | https://app.any.run/tasks/84602682-79ed-4fb4-83c6-c0f72b0ec604 |
| Verdict: | Malicious activity |
| Threats: | MetaStealer is an info-stealing malware primarily targeting sensitive data like login credentials, payment details, and browser history. It typically infects systems via phishing emails or malicious downloads and can exfiltrate data to a command and control (C2) server. MetaStealer is known for its stealthy techniques, including evasion and persistence mechanisms, which make it difficult to detect. This malware has been actively used in various cyberattacks, particularly for financial theft and credential harvesting from individuals and organizations. |
| Analysis date: | August 29, 2024, 00:57:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0E00B6B99B76C436B2BC9A59D7BE9AF1 |
| SHA1: | 2CC0AD72221E2DC51AD107136DB738B29EB4F06F |
| SHA256: | E843167410A695FC198ABB3A2A14E5D51DAA6125072C2A0B822CE39A9F2C1E9D |
| SSDEEP: | 6:2OLUxGKmToATYZCwhV5mD5DzLSYqV3QhZrHVJOrVaogf09Gh:2jGR8pCwhreczurDOrBH9Gh |
MALICIOUS
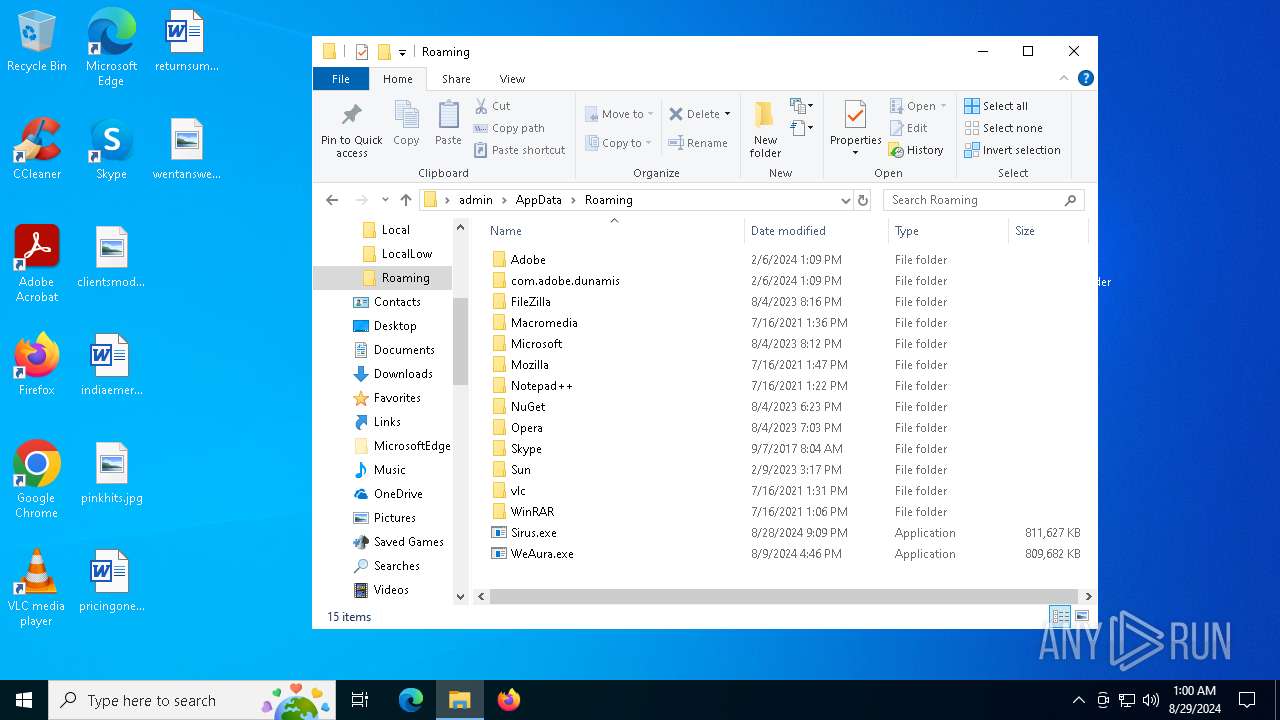
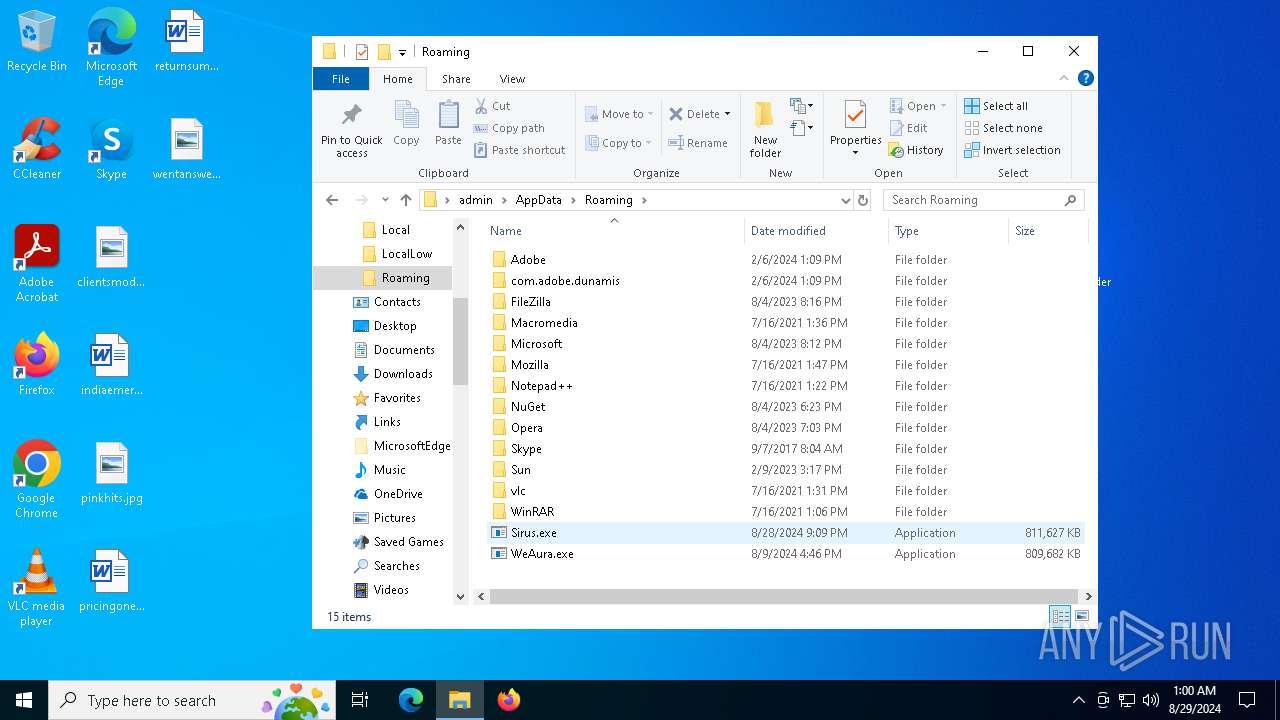
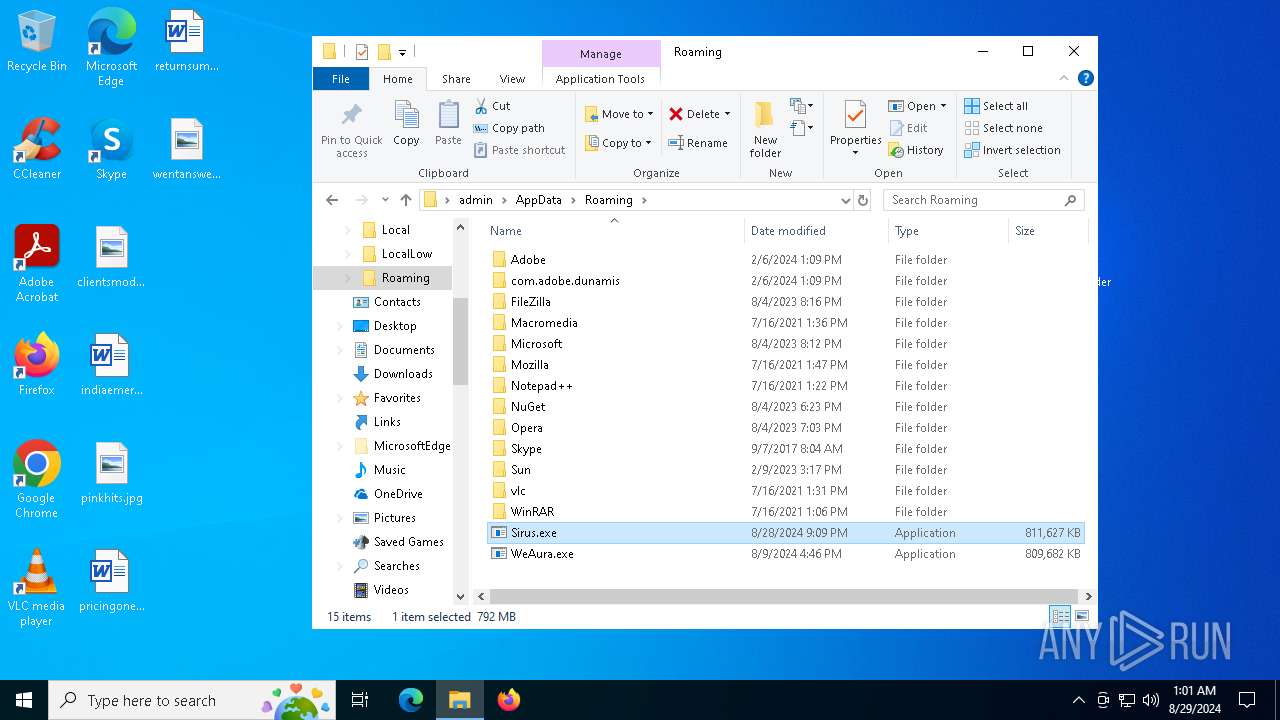
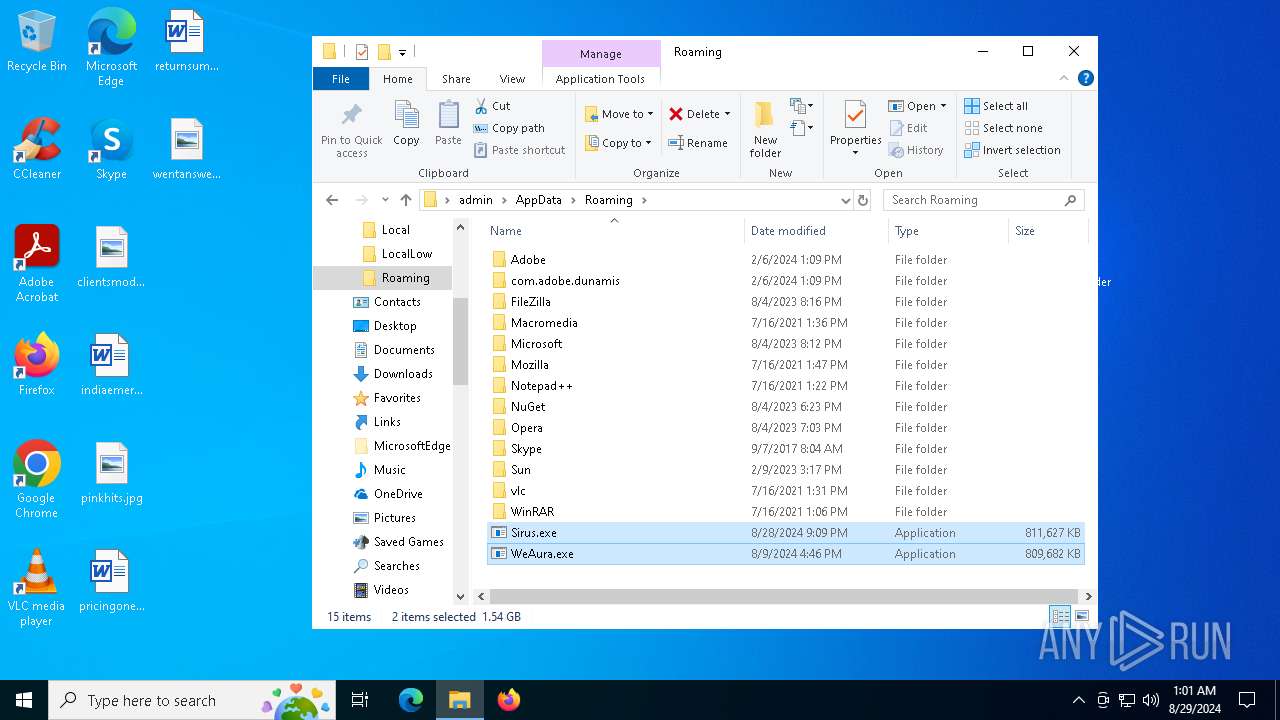
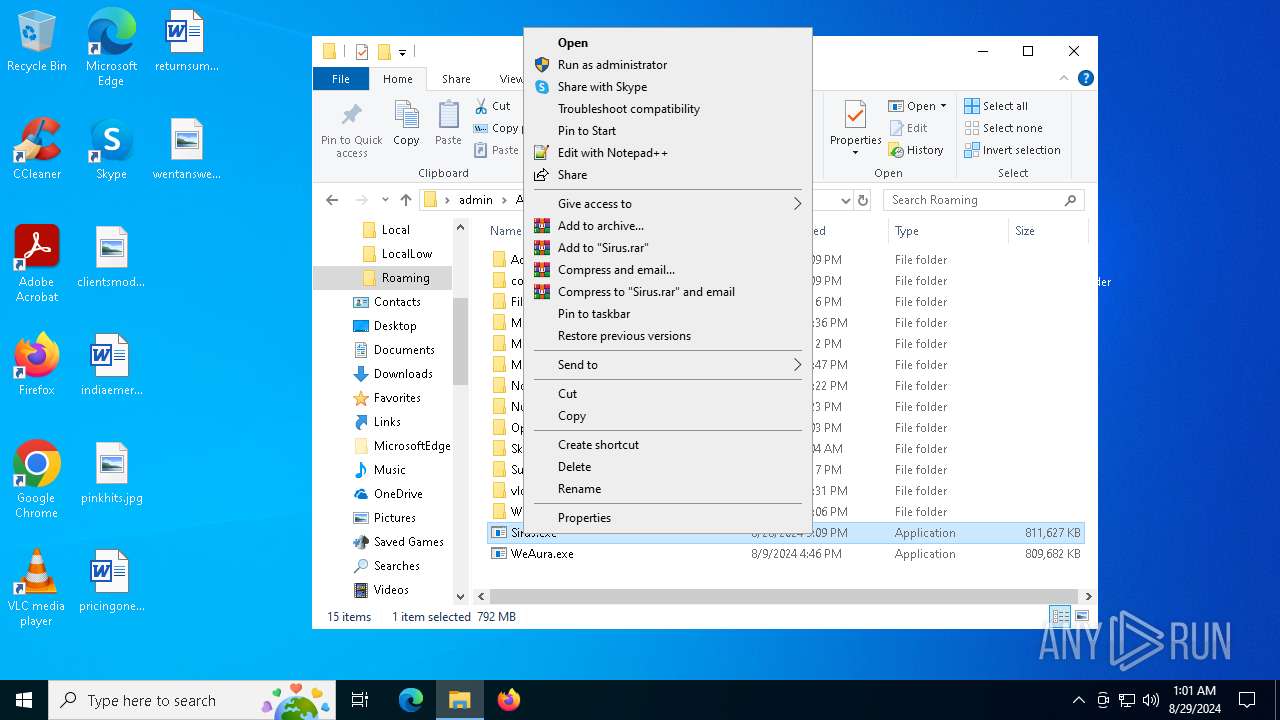
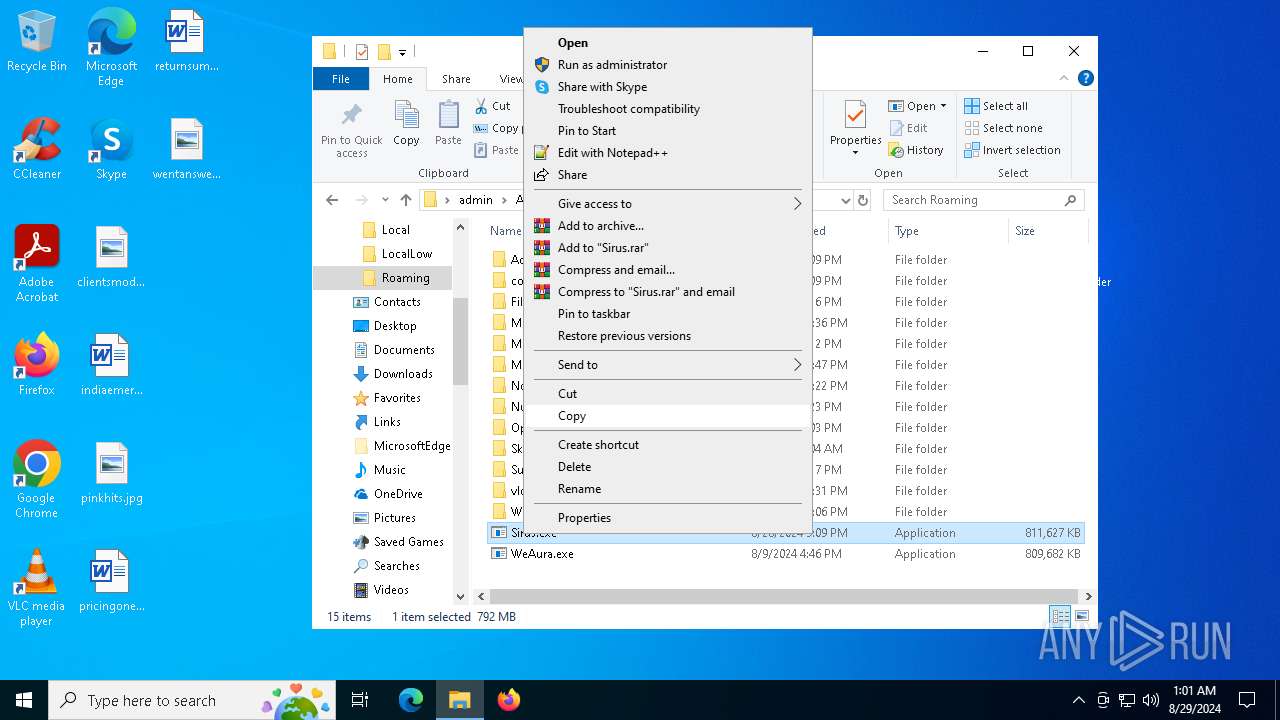
Adds extension to the Windows Defender exclusion list
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Stealers network behavior
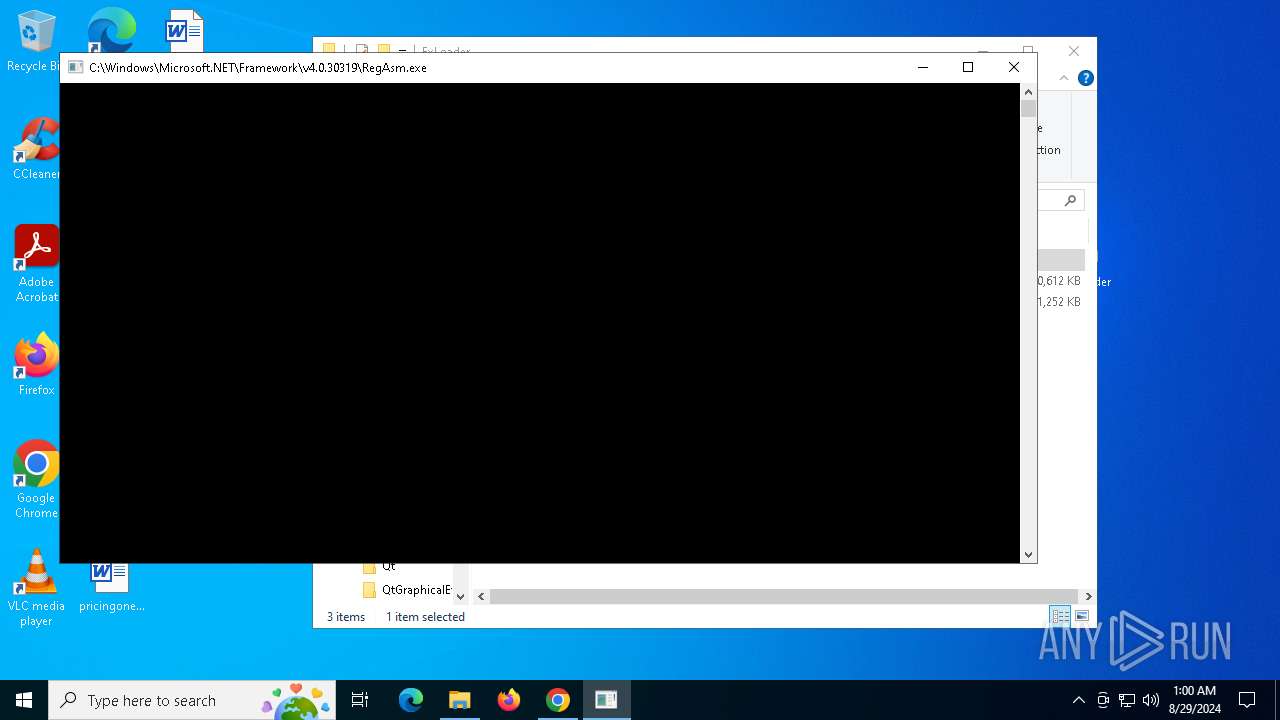
- RegAsm.exe (PID: 6504)
METASTEALER has been detected (SURICATA)
- RegAsm.exe (PID: 6504)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 6504)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 6504)
MINER has been detected (SURICATA)
- explorer.exe (PID: 5116)
XORed URL has been found (YARA)
- explorer.exe (PID: 5116)
SUSPICIOUS
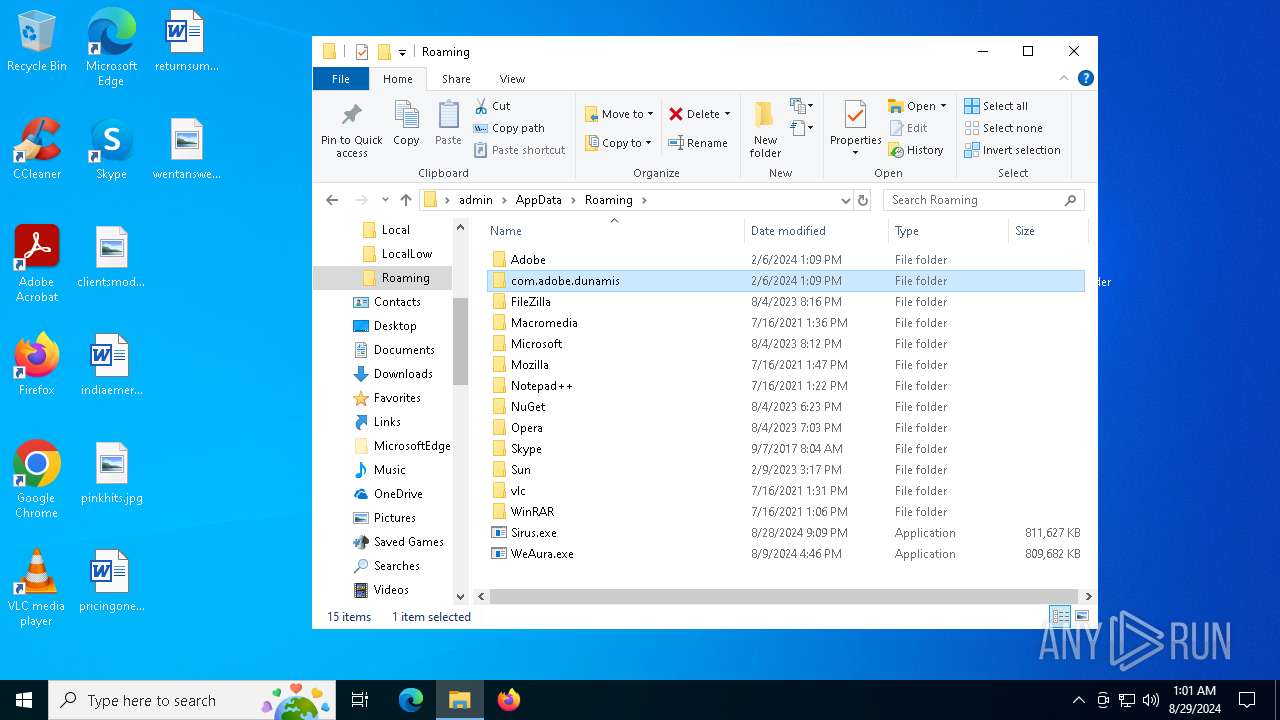
Reads the BIOS version
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Starts POWERSHELL.EXE for commands execution
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Script adds exclusion path to Windows Defender
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Script adds exclusion extension to Windows Defender
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Contacting a server suspected of hosting an CnC
- RegAsm.exe (PID: 6504)
Connects to unusual port
- RegAsm.exe (PID: 6504)
- explorer.exe (PID: 5116)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6880)
Searches for installed software
- RegAsm.exe (PID: 6504)
Process uninstalls Windows update
- wusa.exe (PID: 6892)
- wusa.exe (PID: 6172)
Uses powercfg.exe to modify the power settings
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Starts SC.EXE for service management
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Starts CMD.EXE for commands execution
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Executes as Windows Service
- valrjyxscerz.exe (PID: 6292)
Drops a system driver (possible attempt to evade defenses)
- valrjyxscerz.exe (PID: 6292)
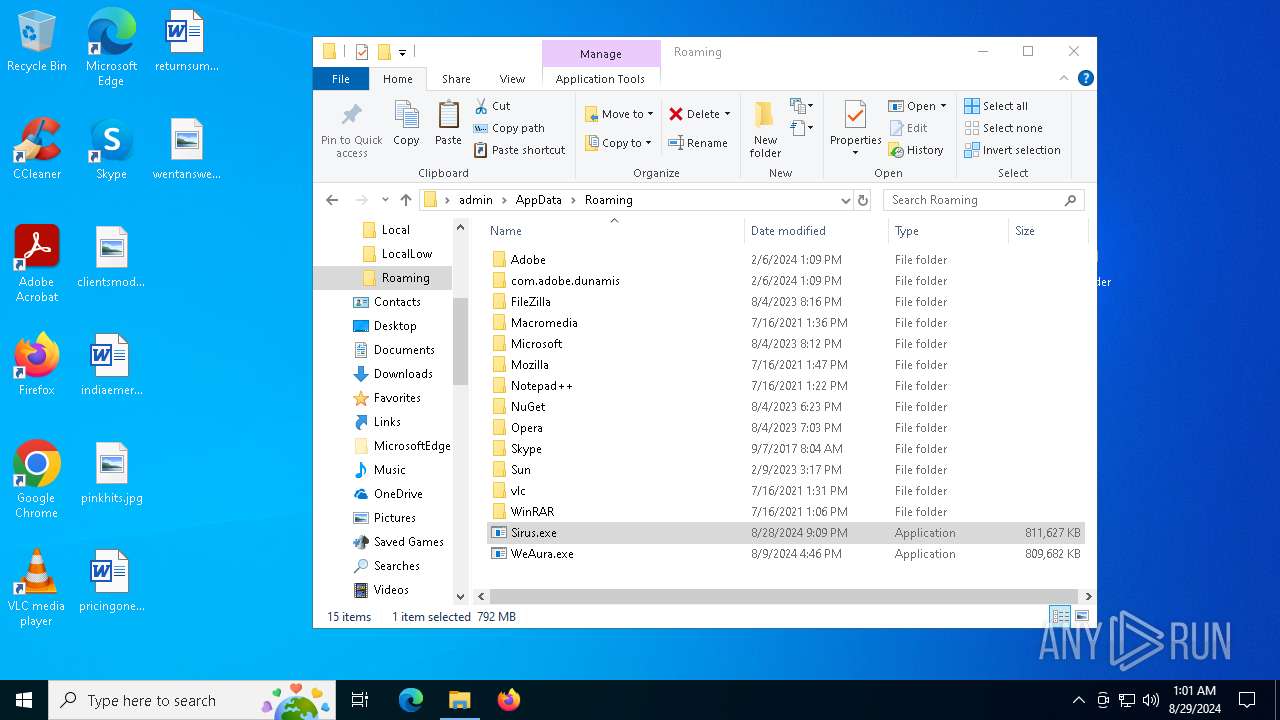
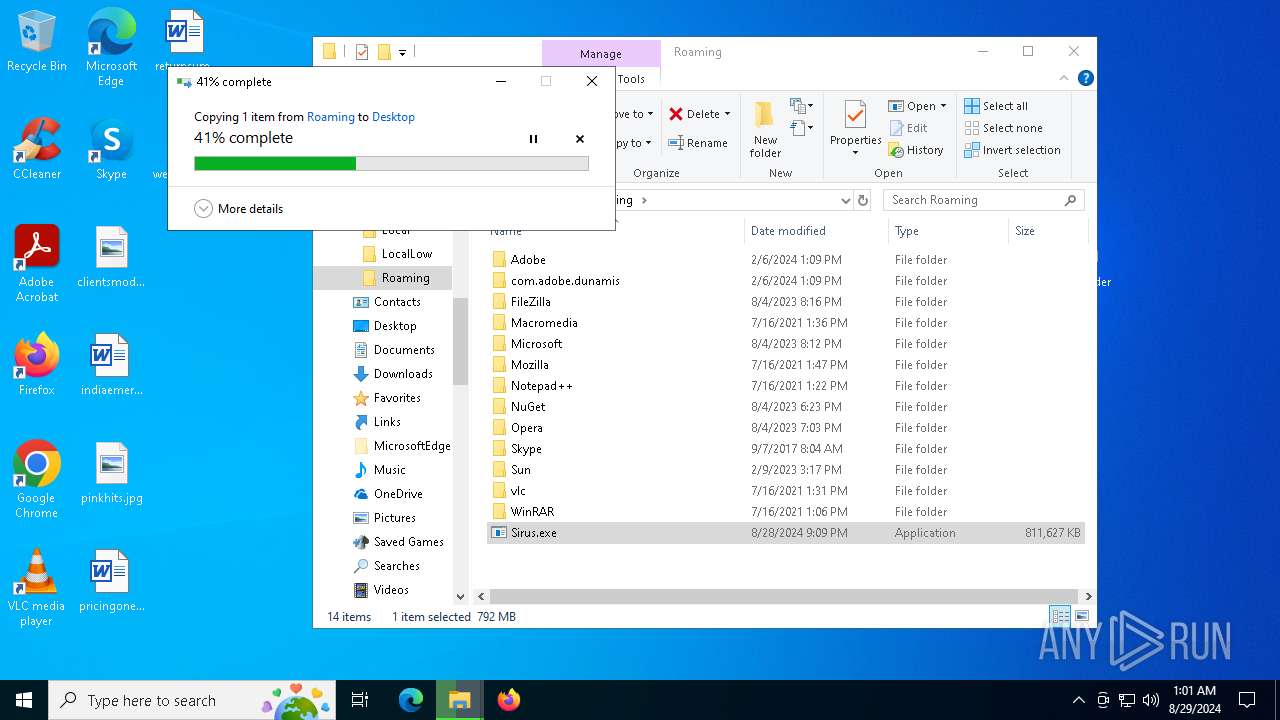
Drops the executable file immediately after the start
- valrjyxscerz.exe (PID: 6292)
Executable content was dropped or overwritten
- valrjyxscerz.exe (PID: 6292)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2256)
Potential Corporate Privacy Violation
- explorer.exe (PID: 5116)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 5920)
- firefox.exe (PID: 2568)
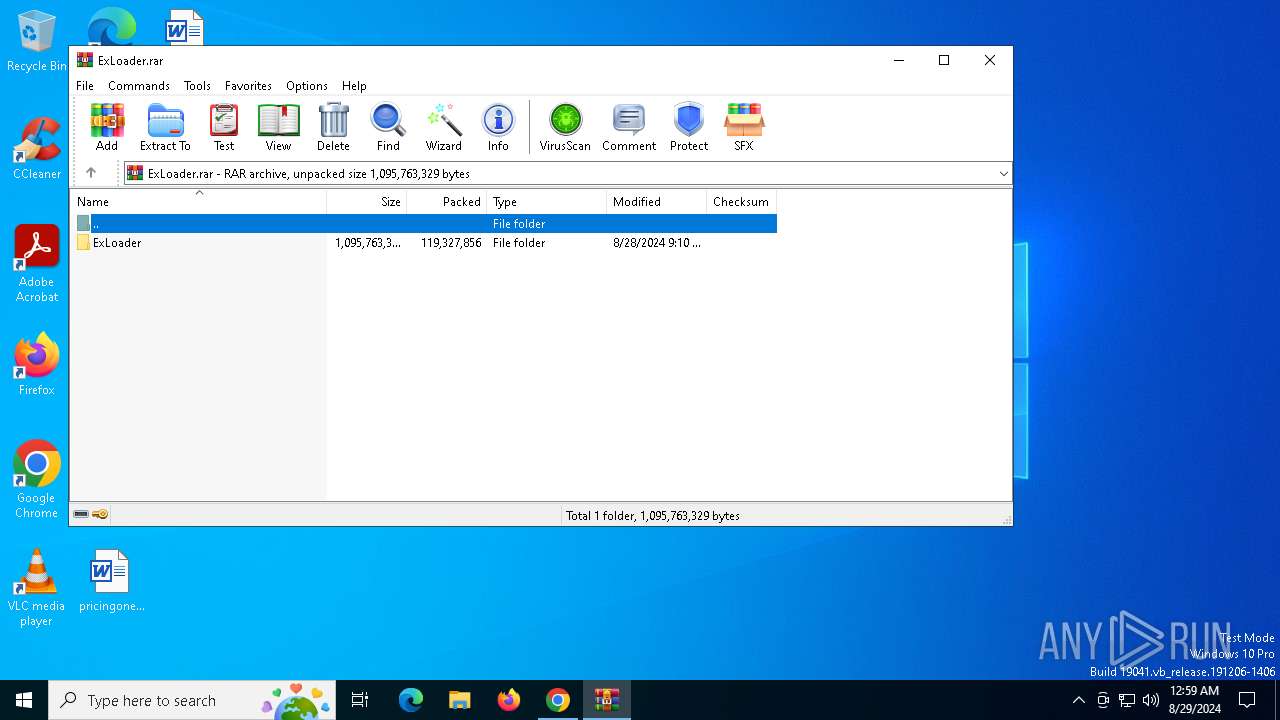
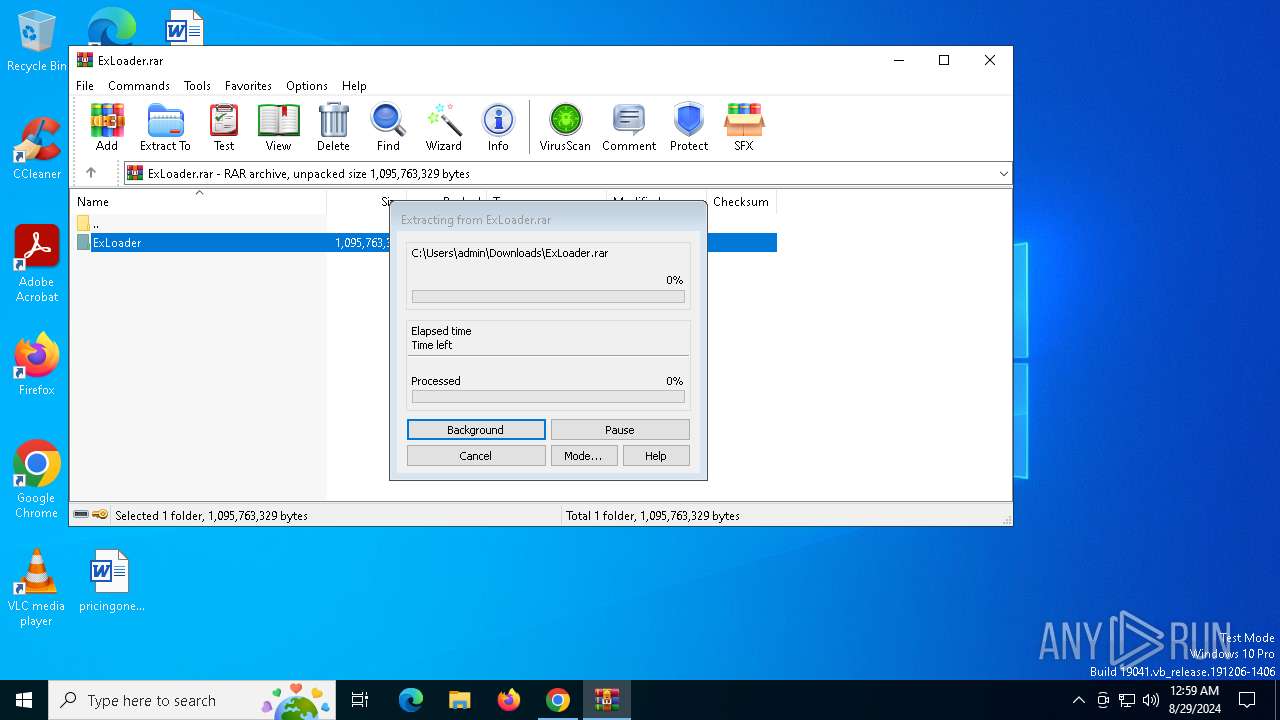
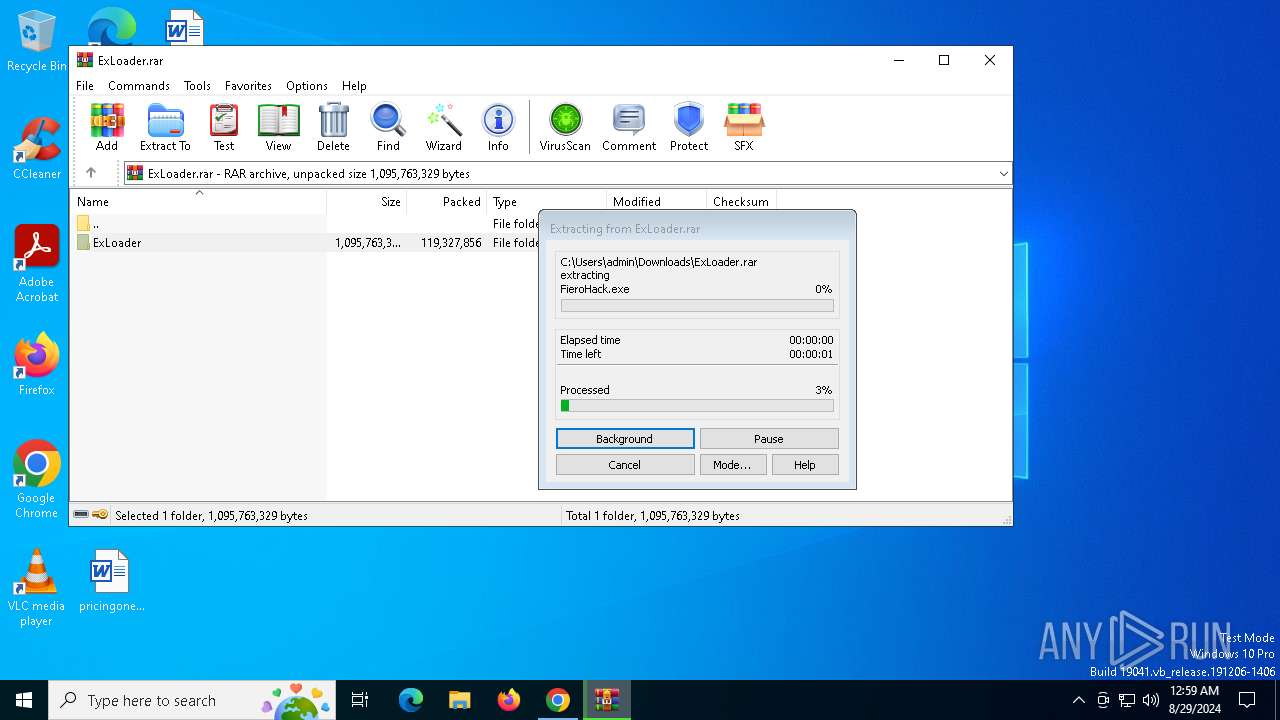
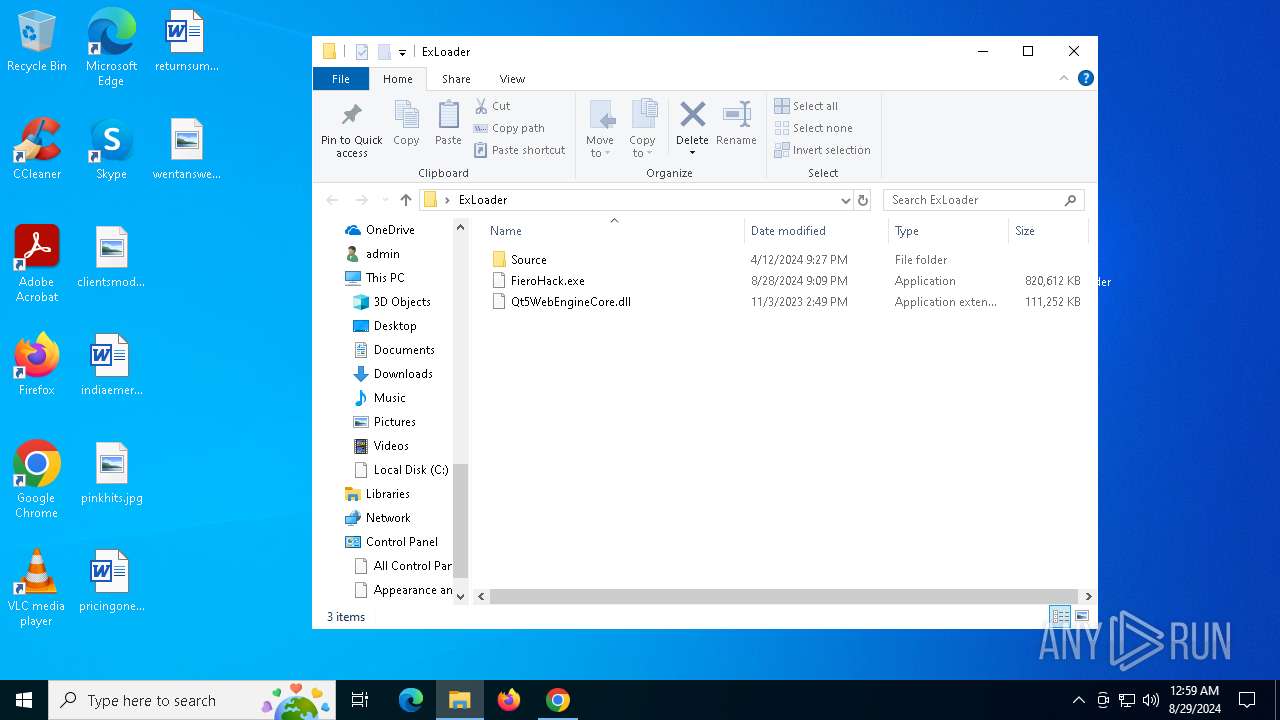
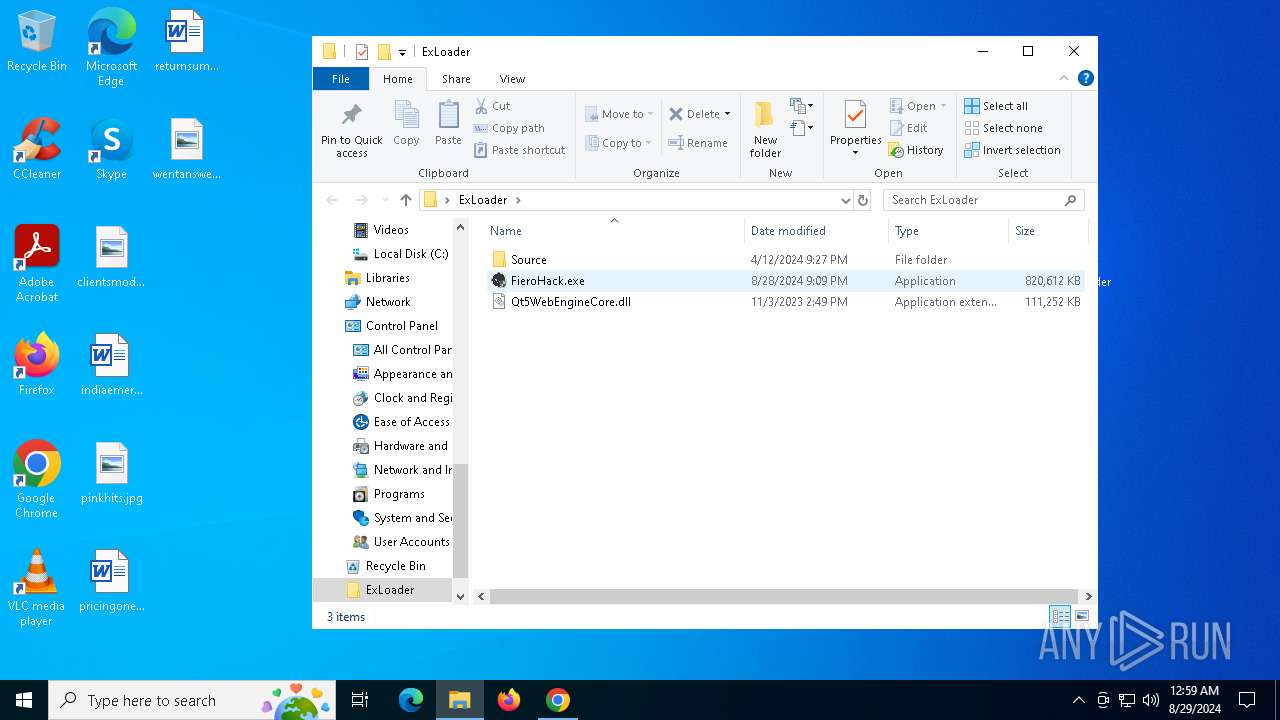
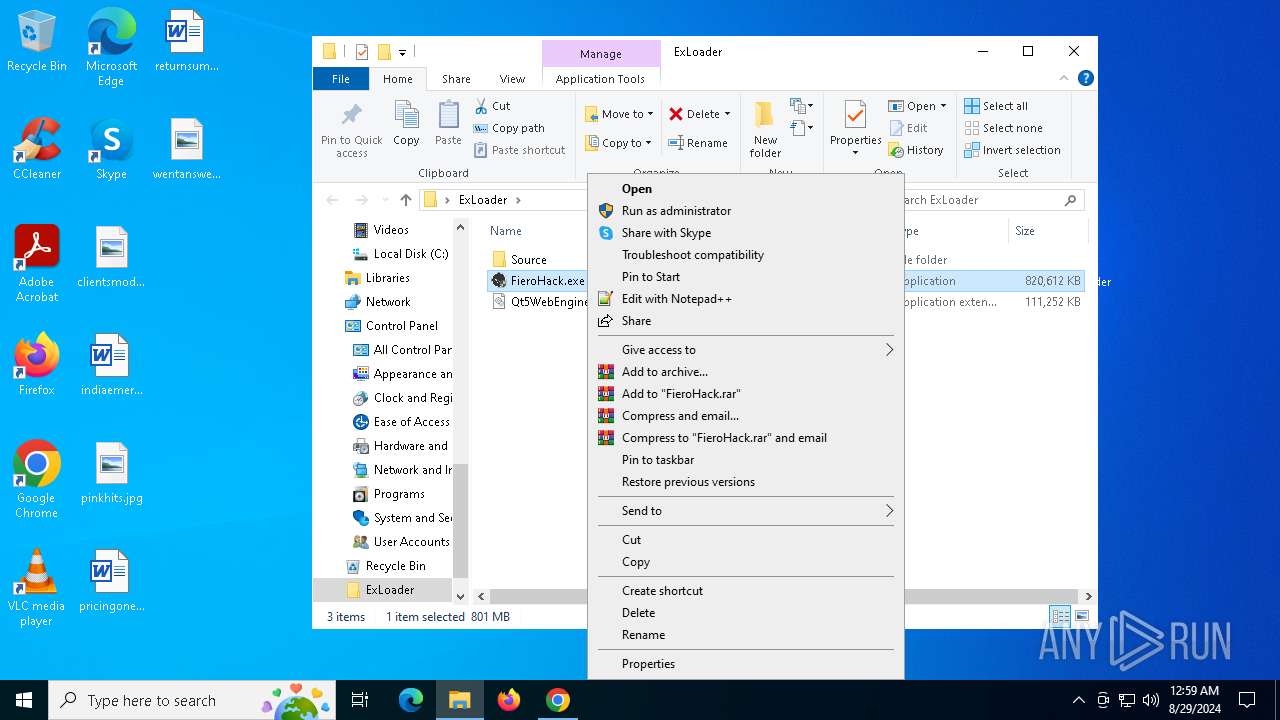
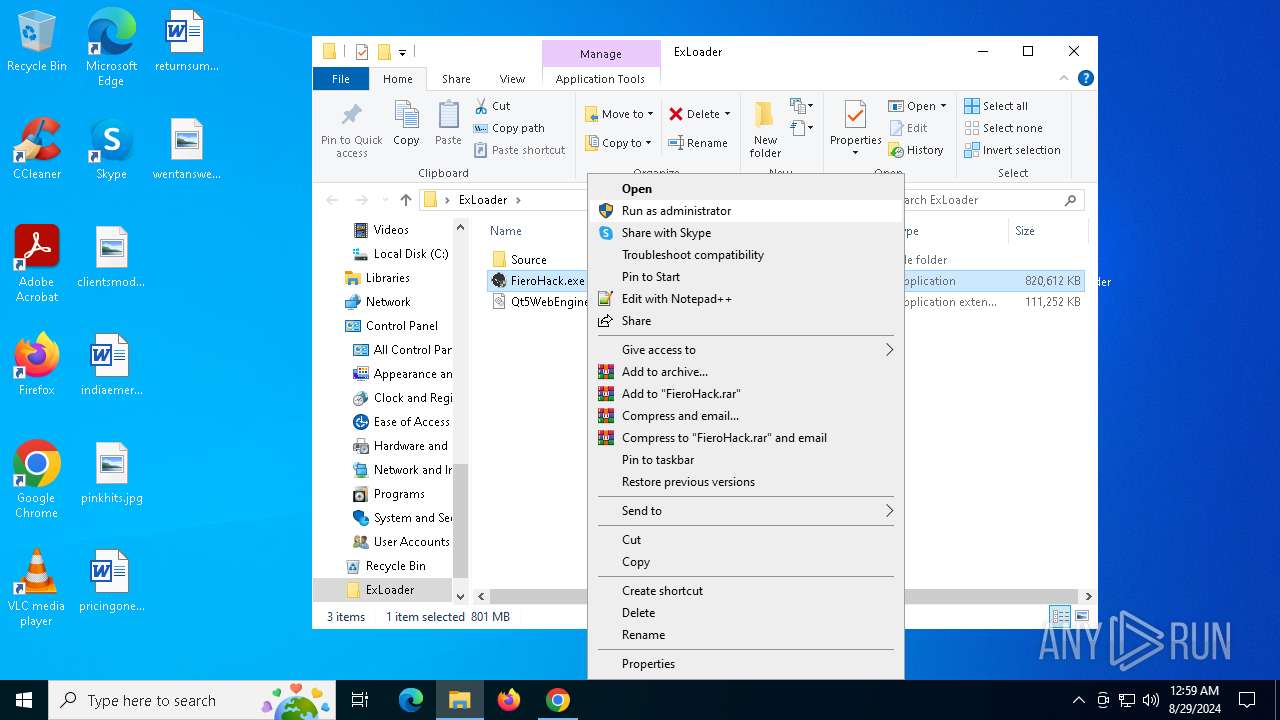
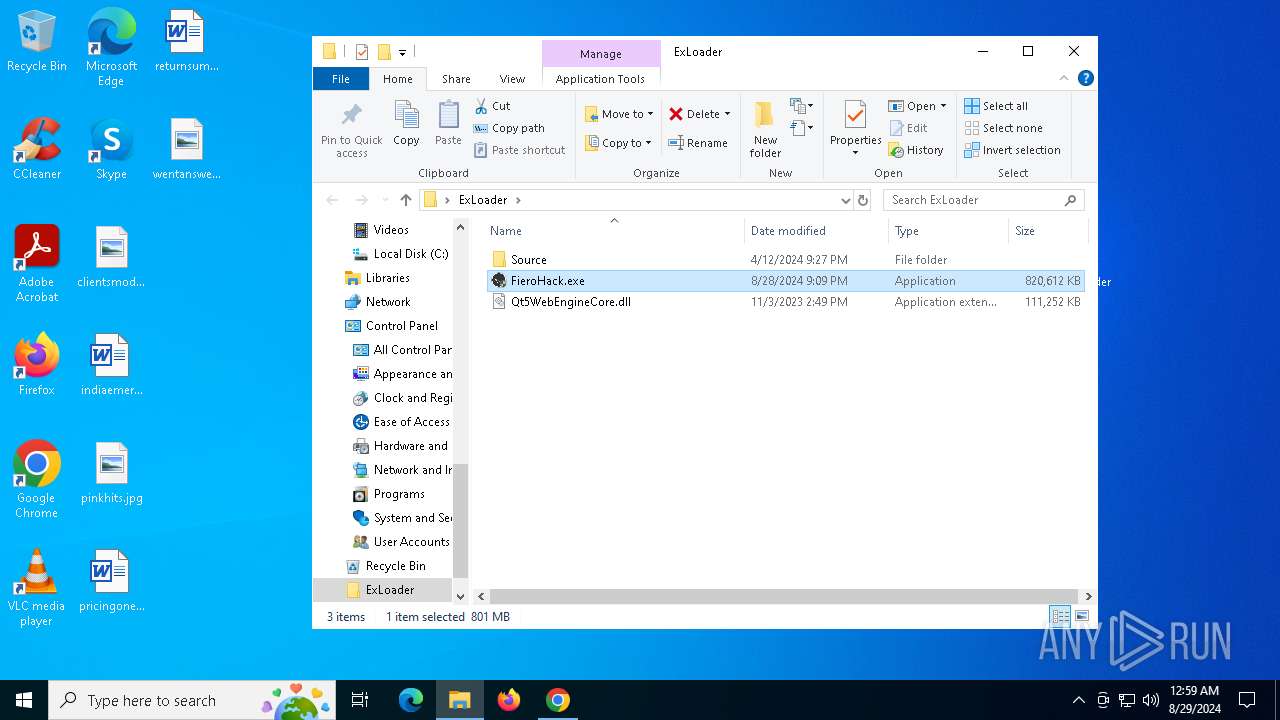
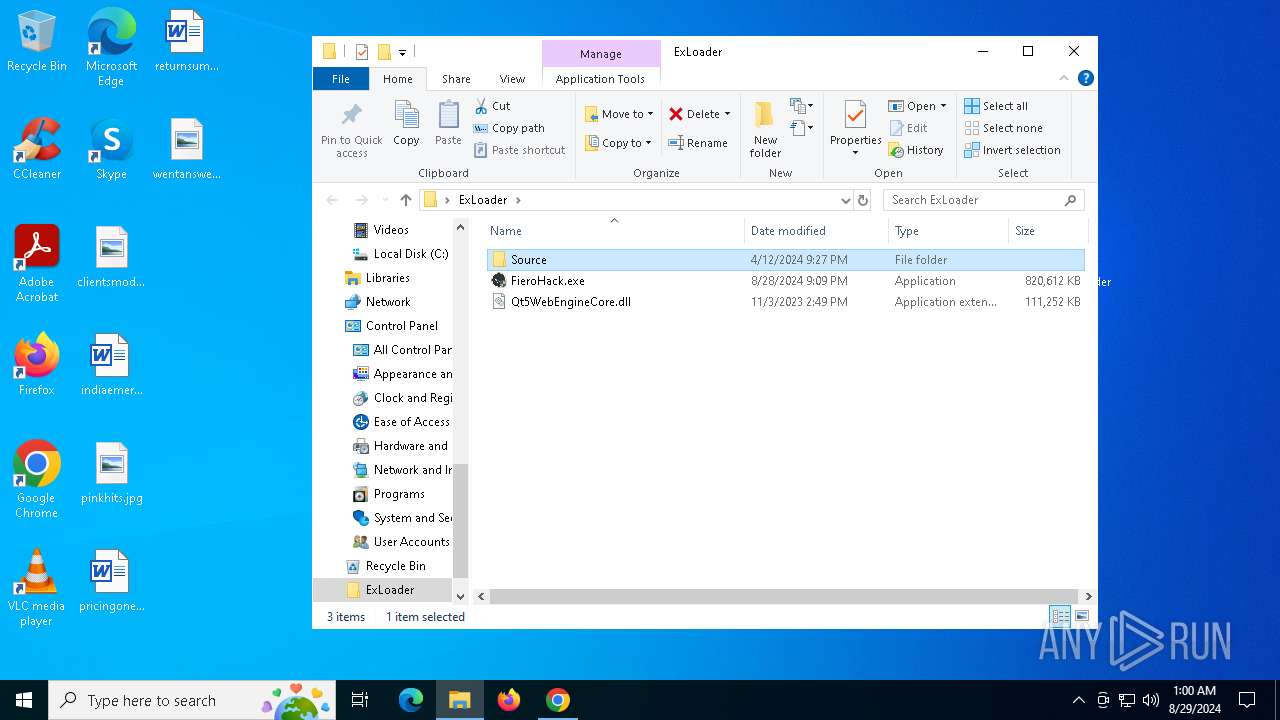
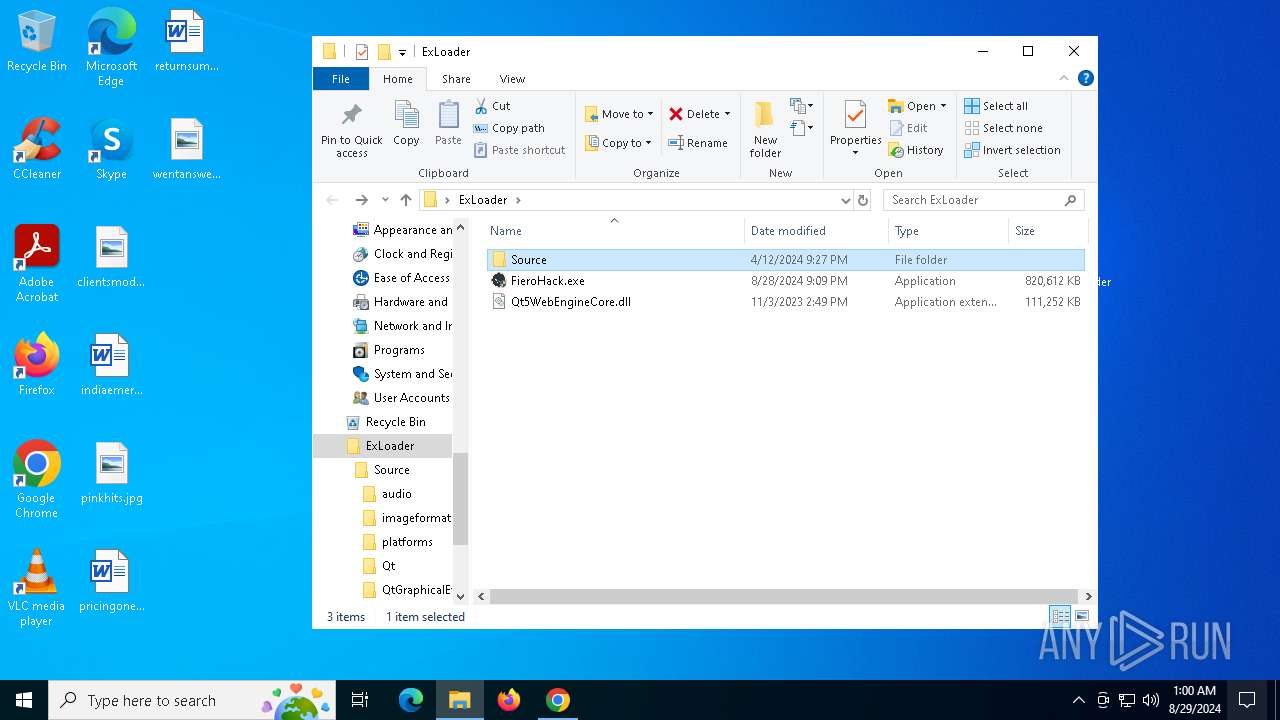
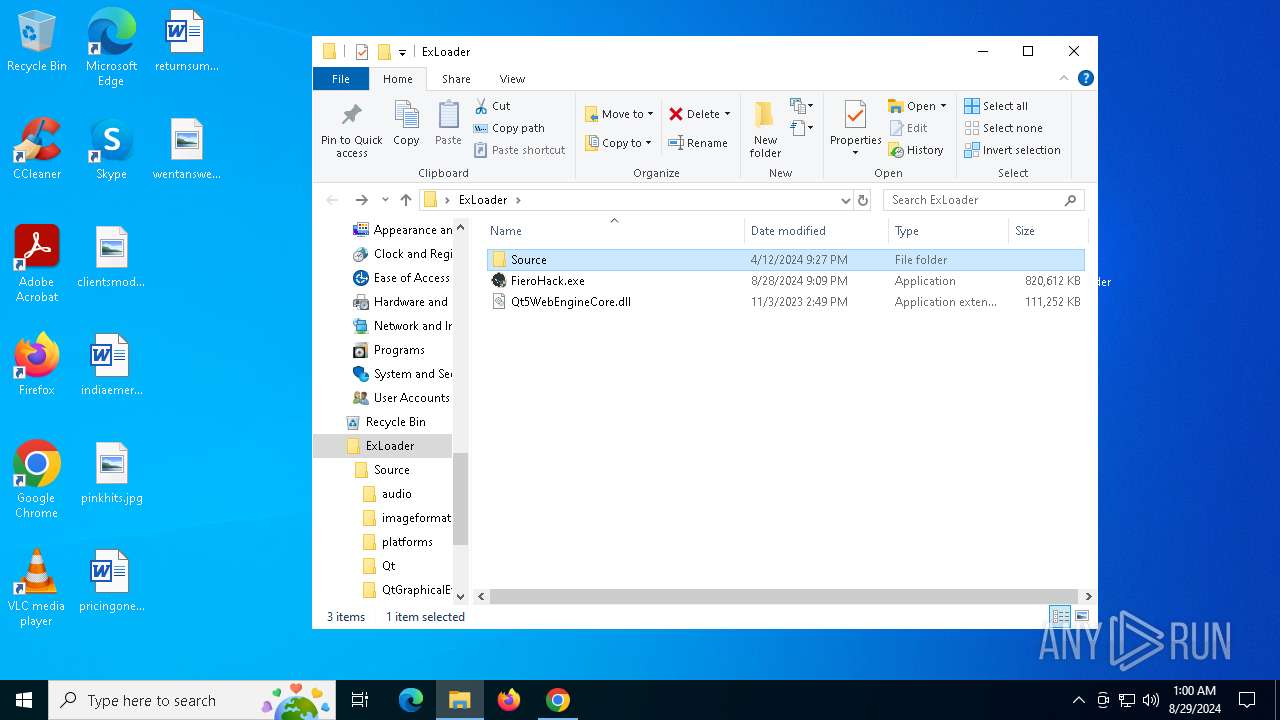
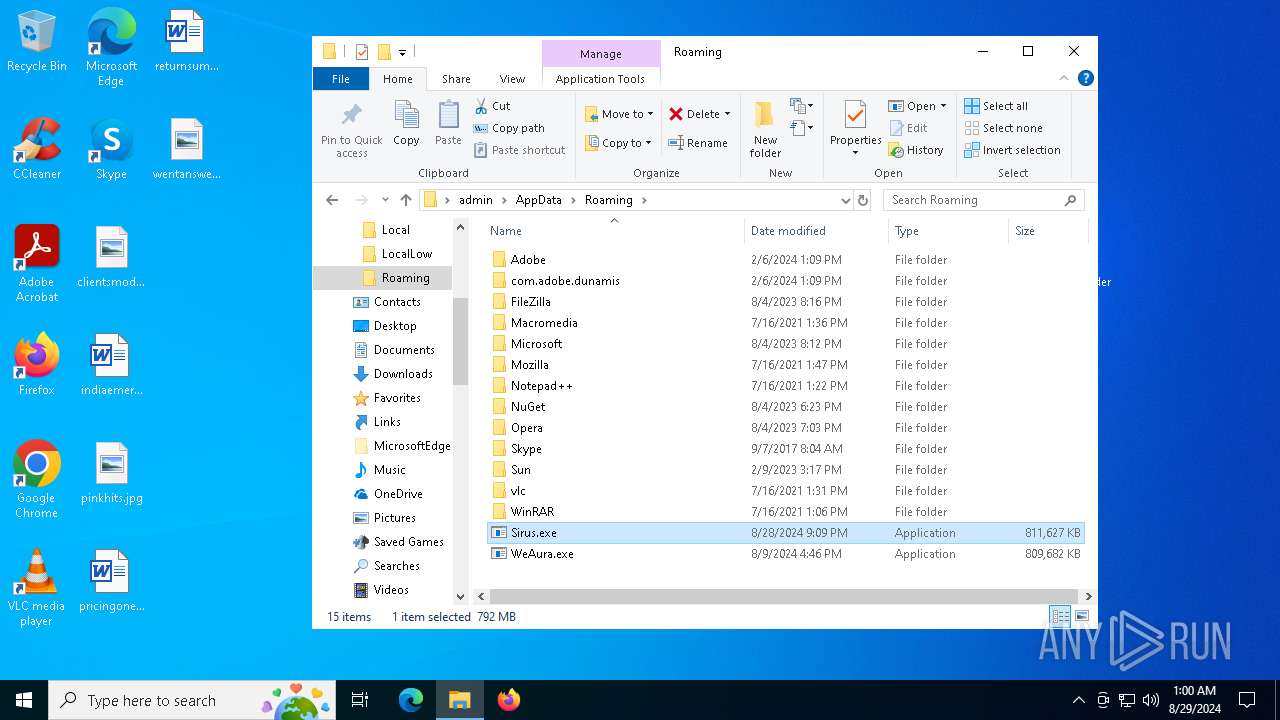
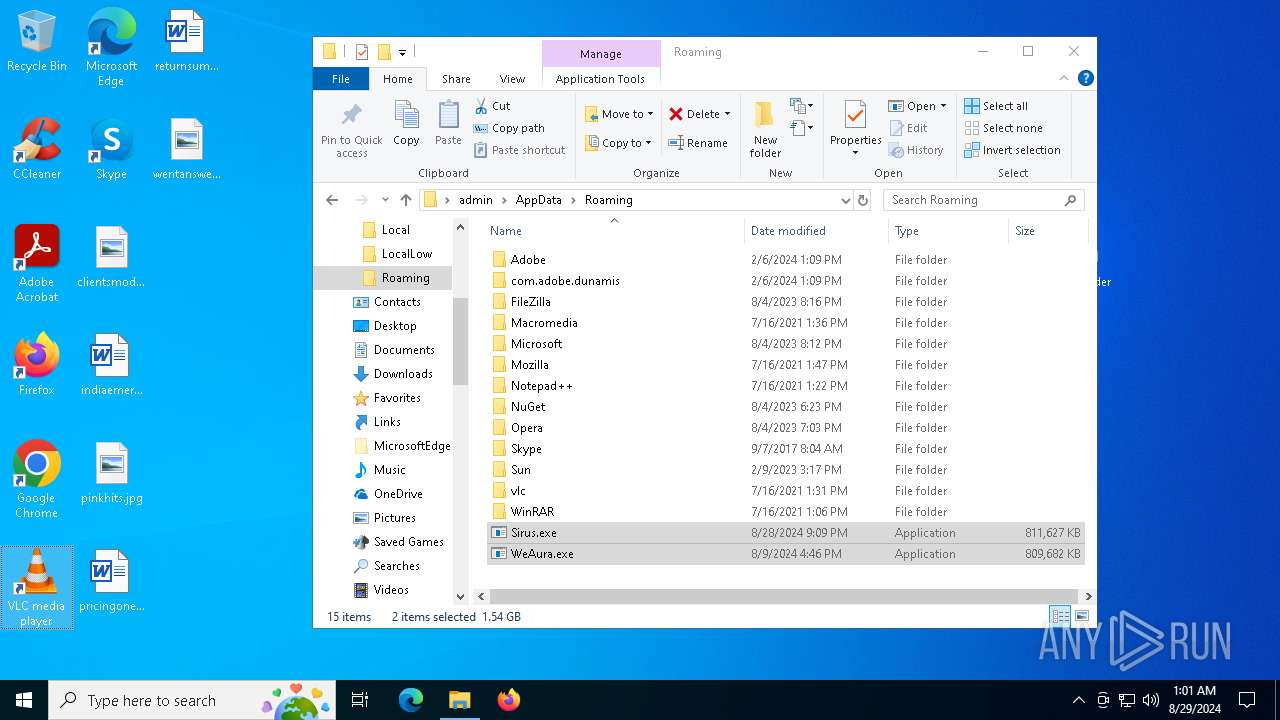
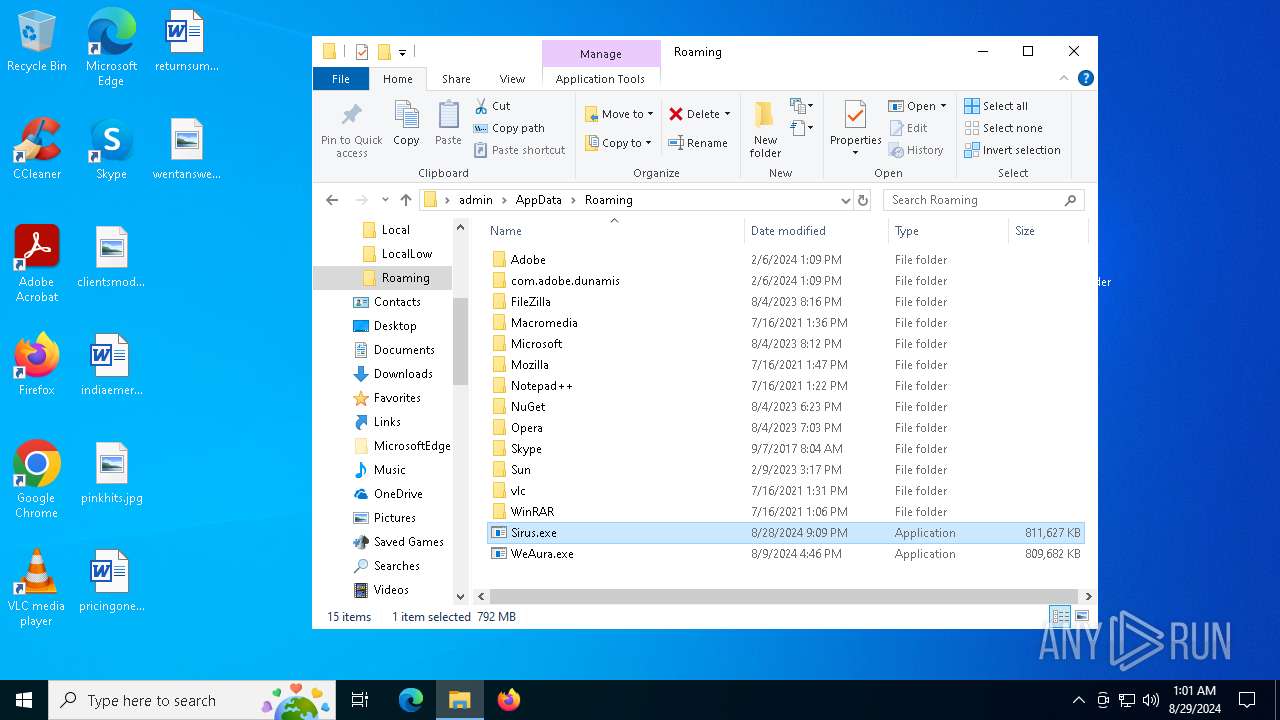
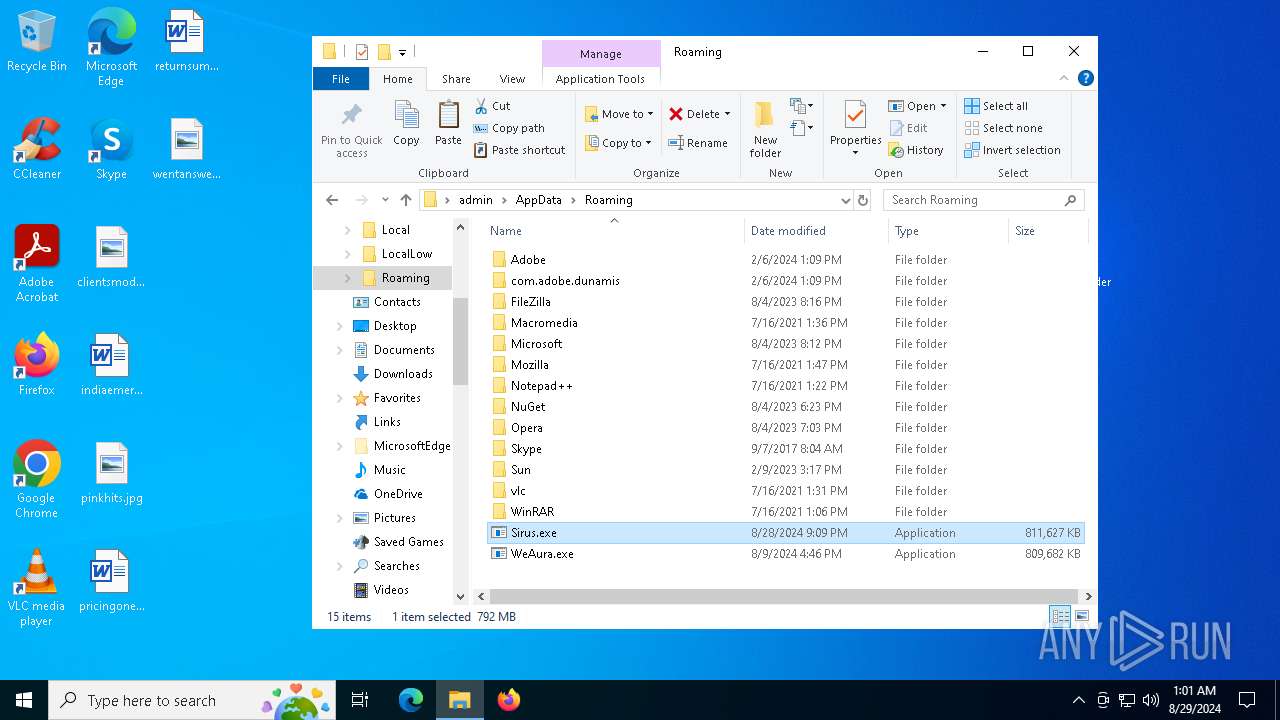
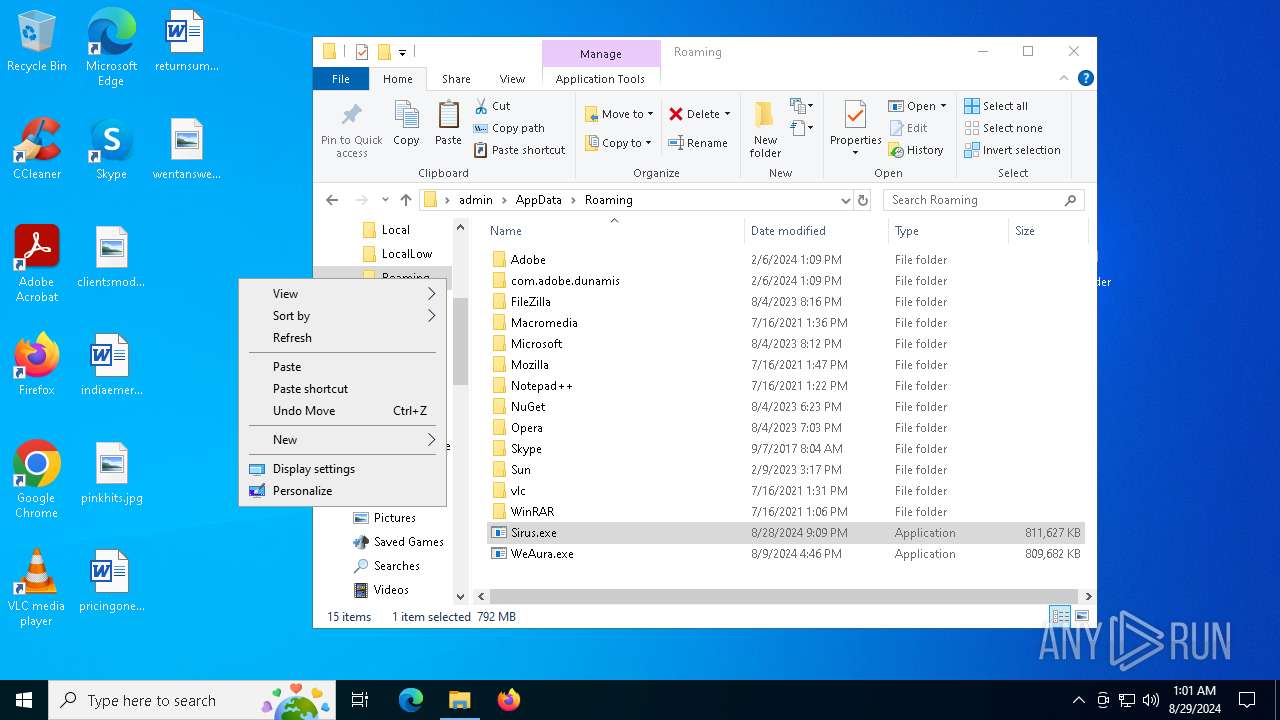
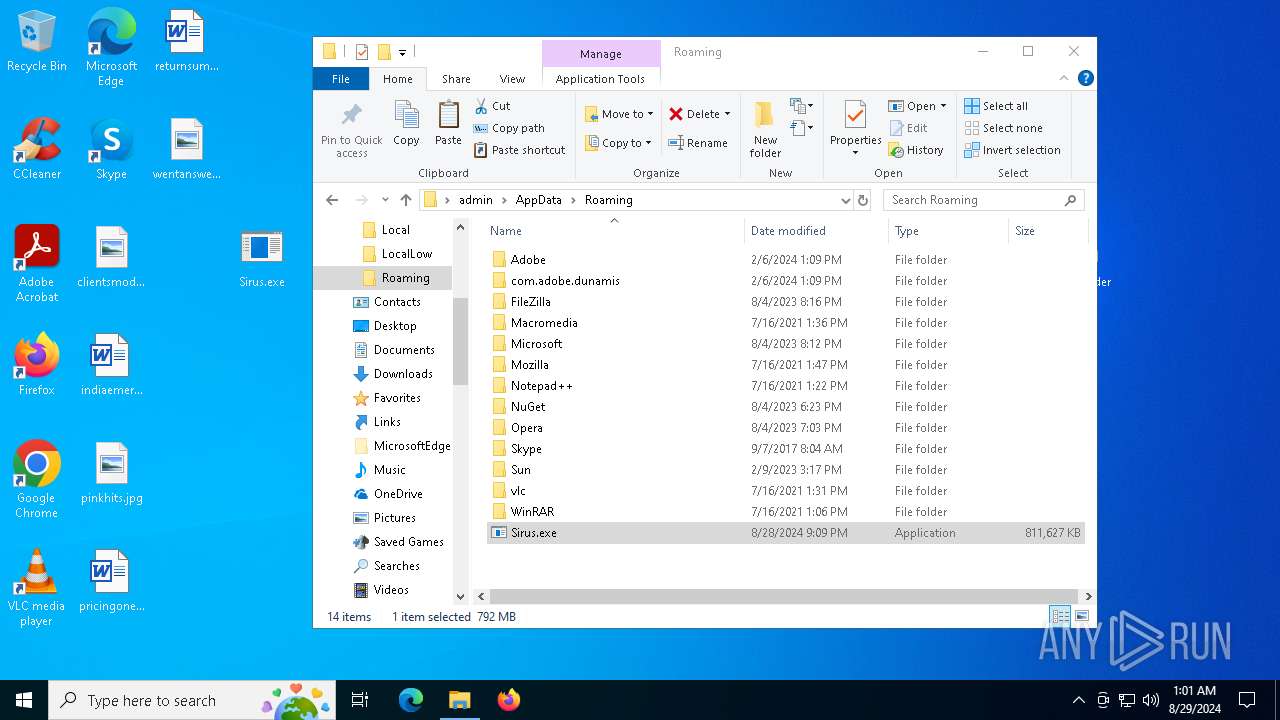
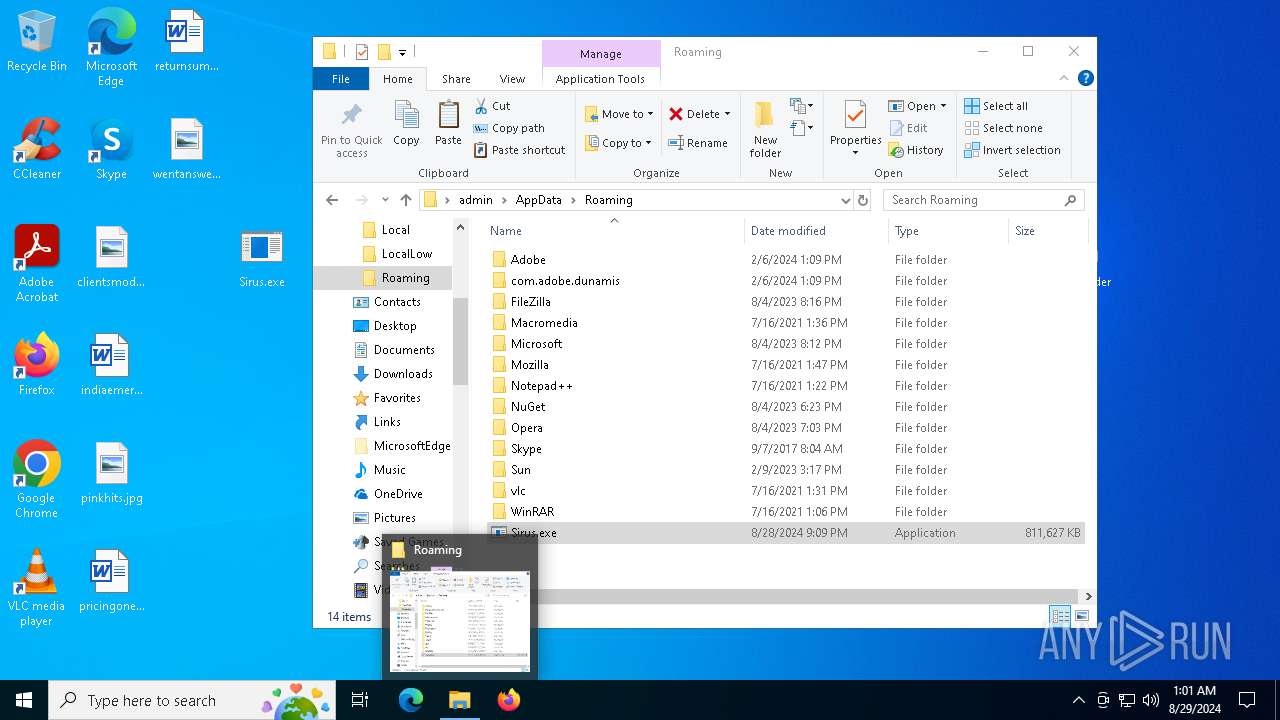
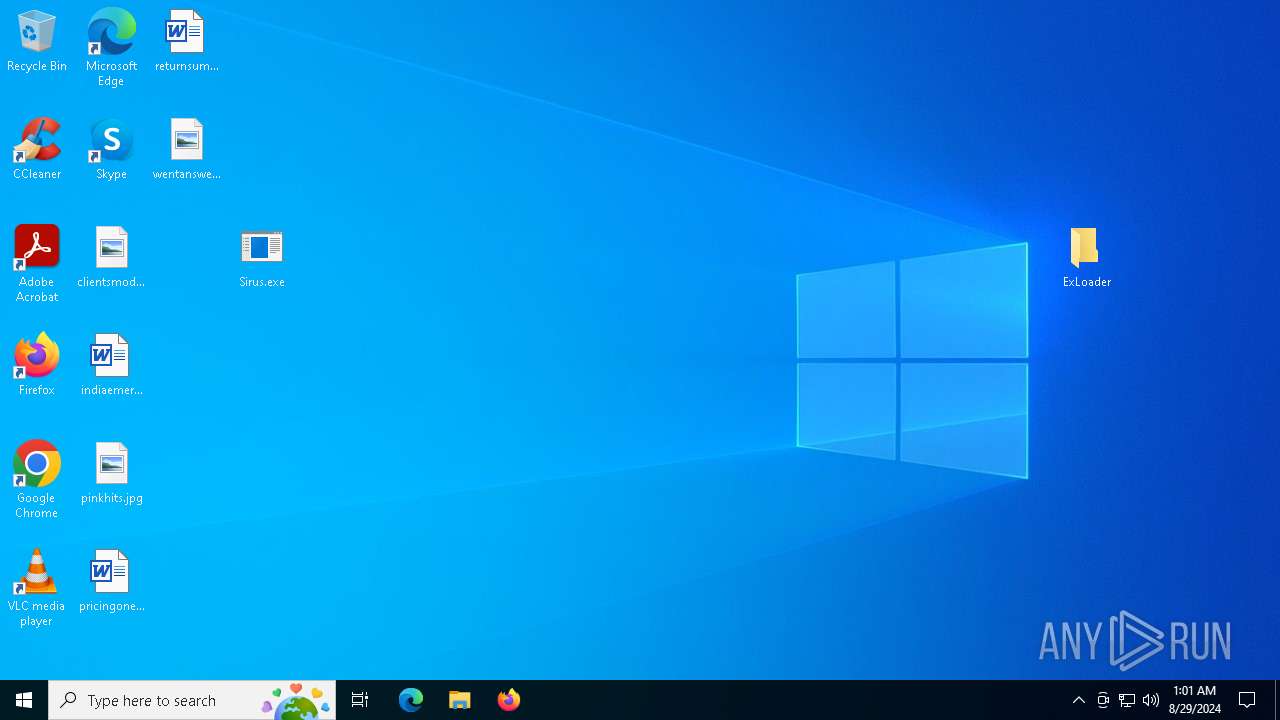
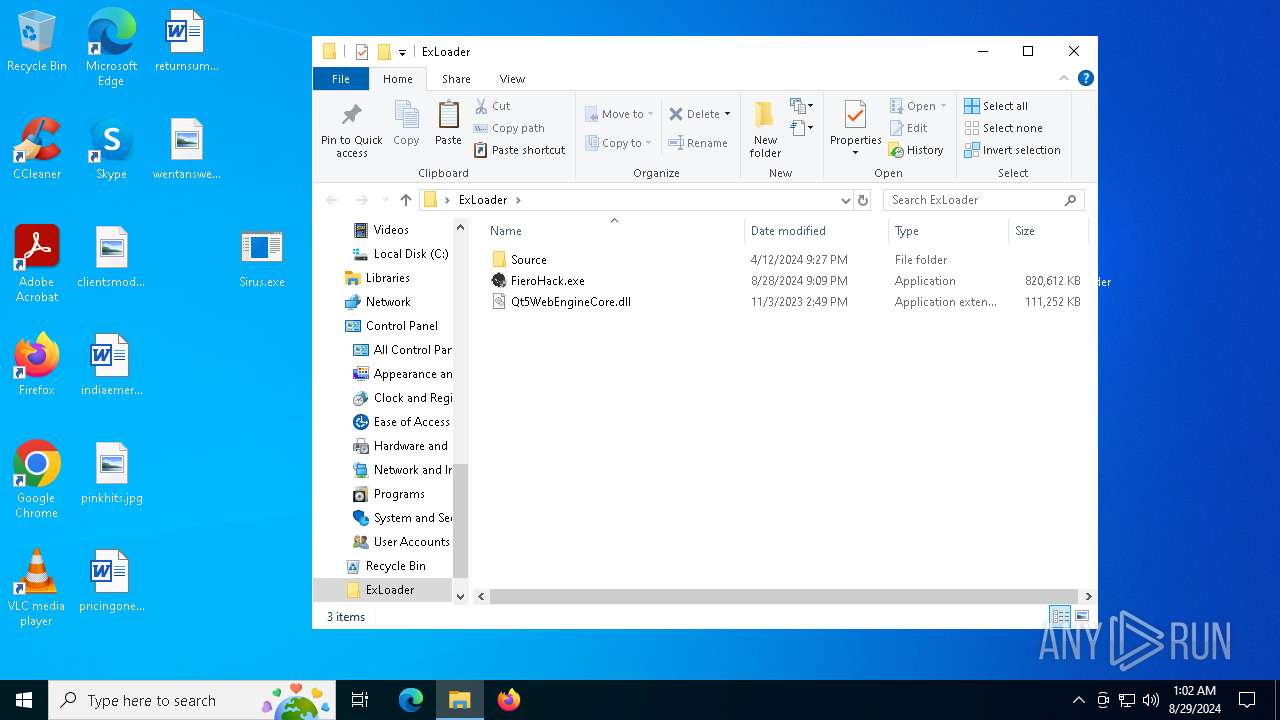
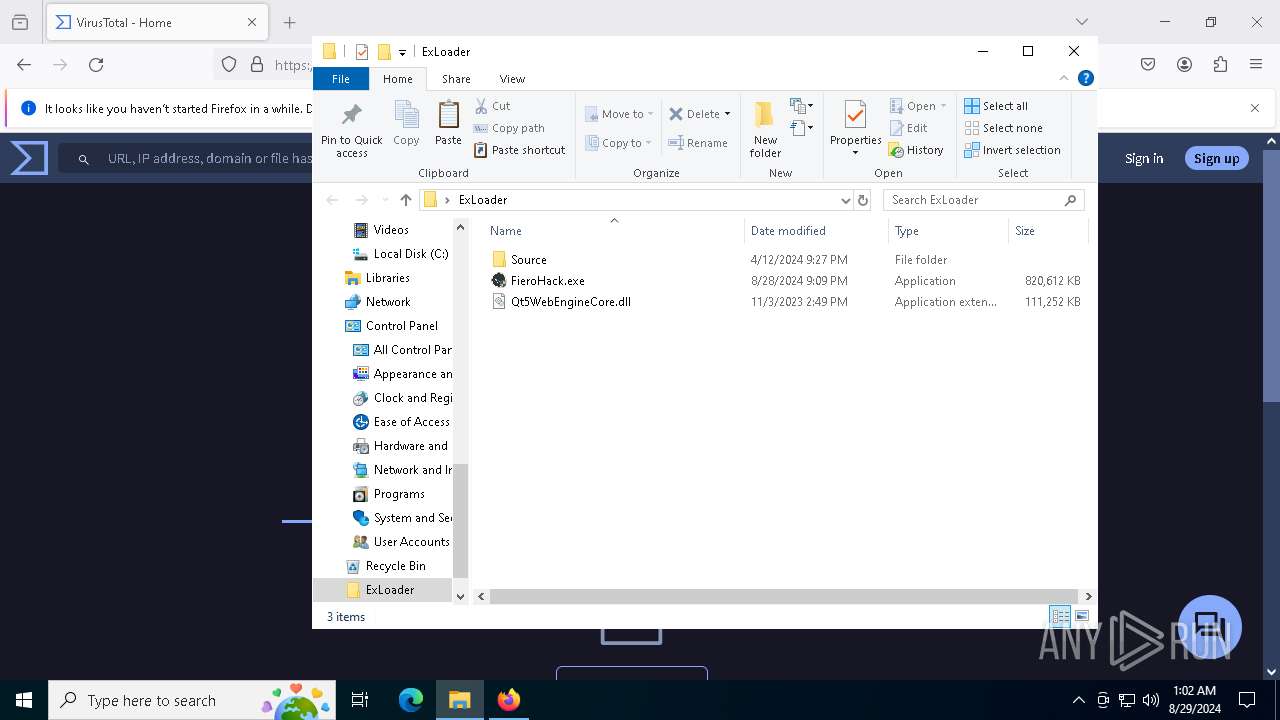
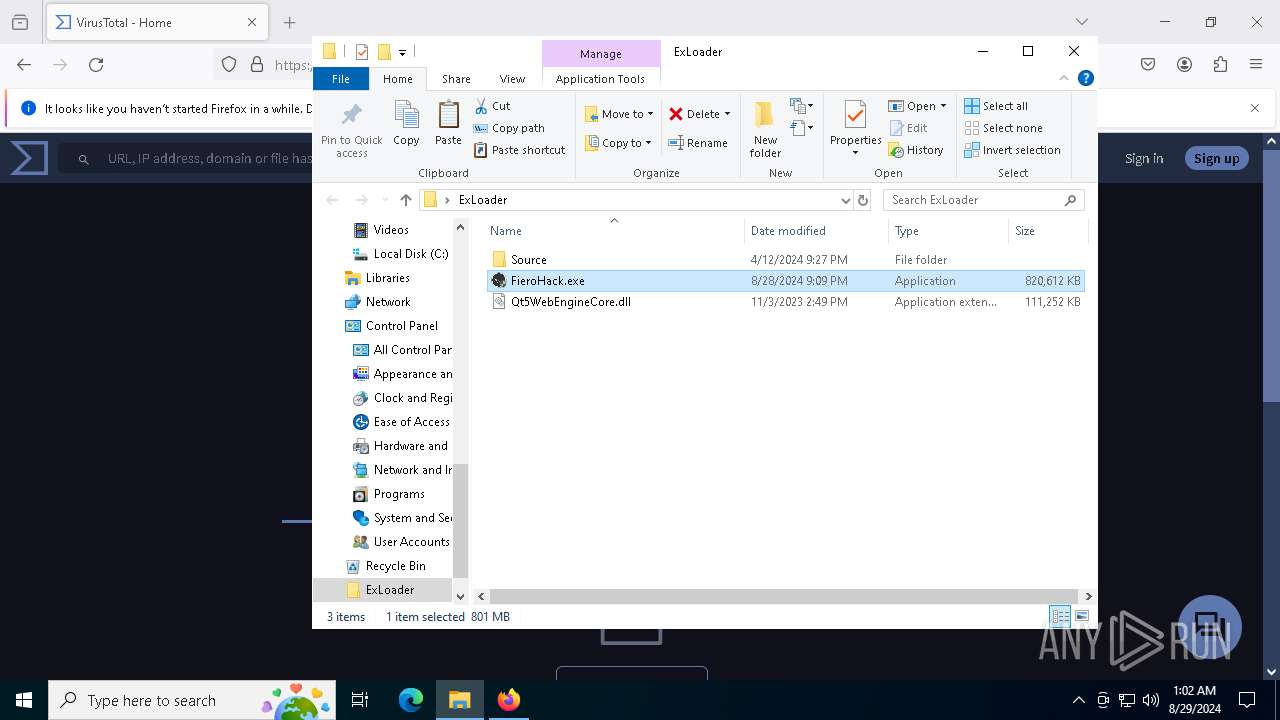
Manual execution by a user
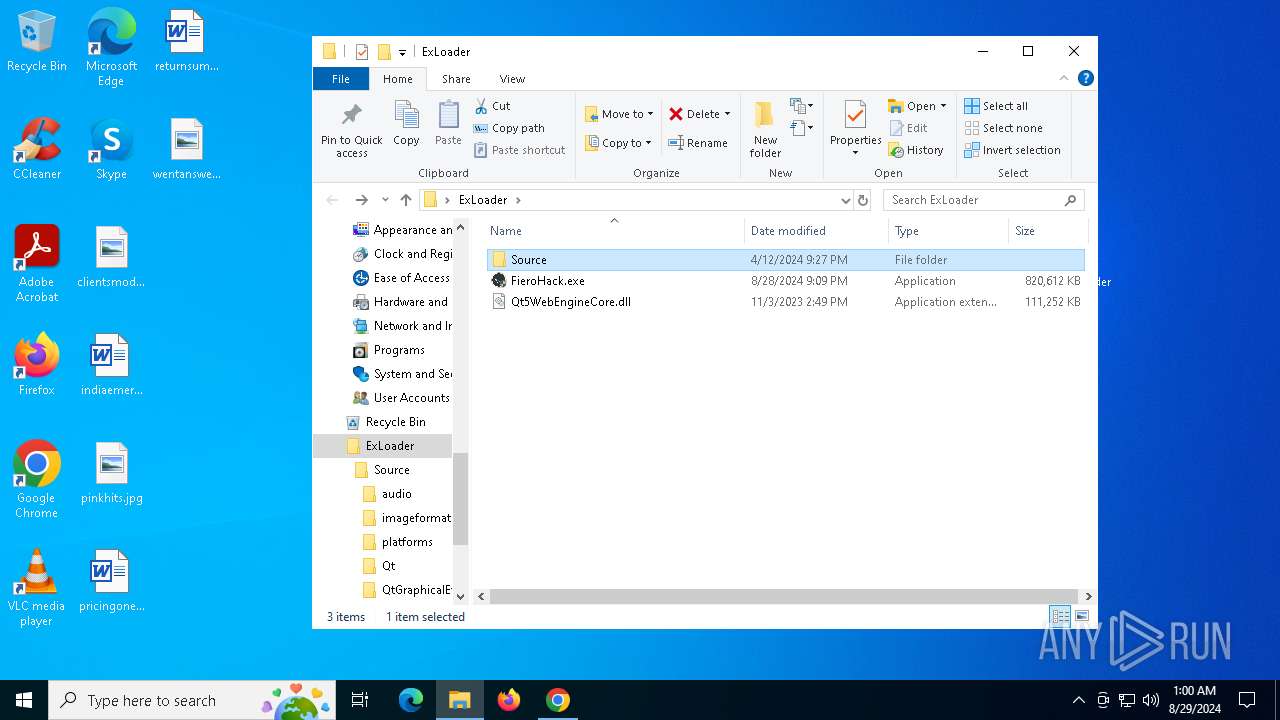
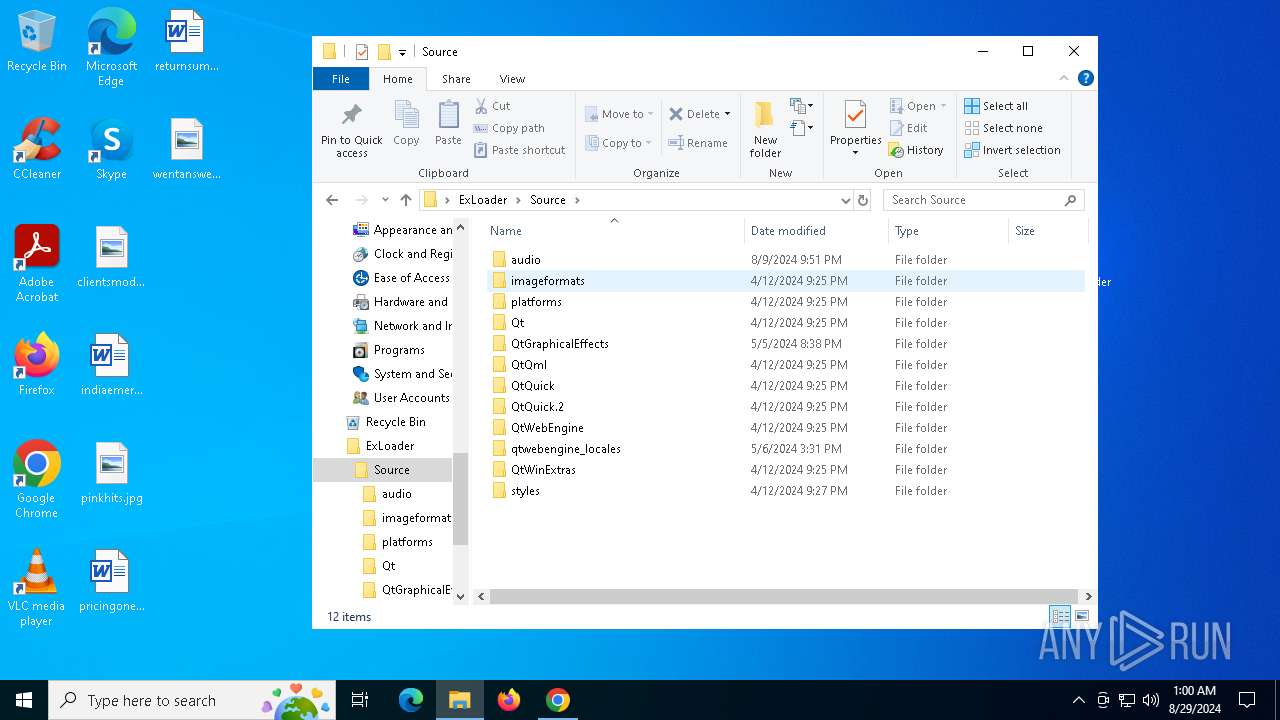
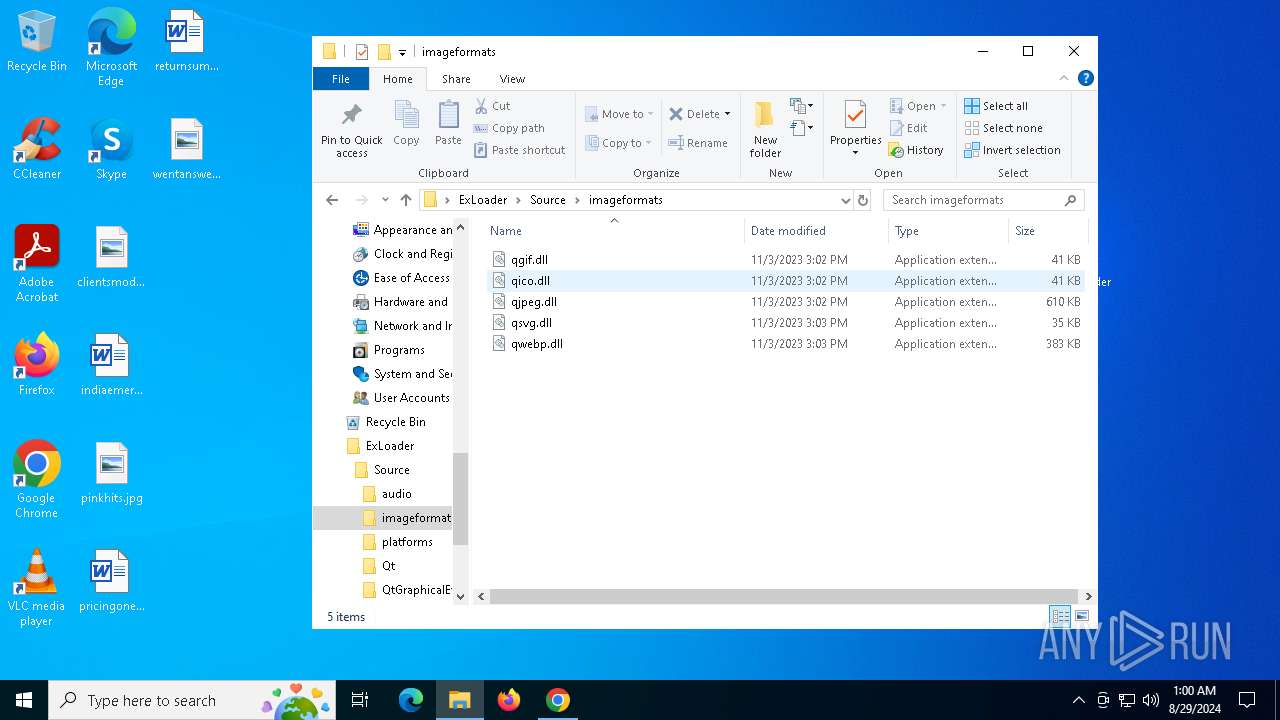
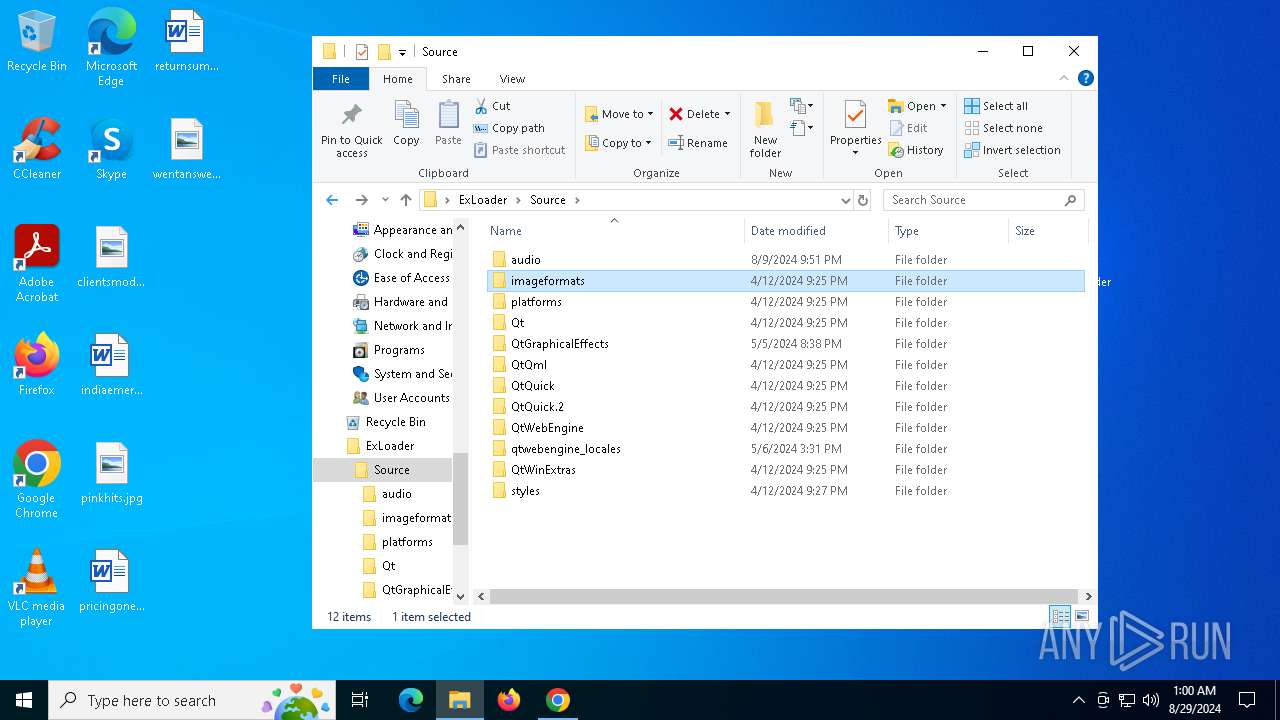
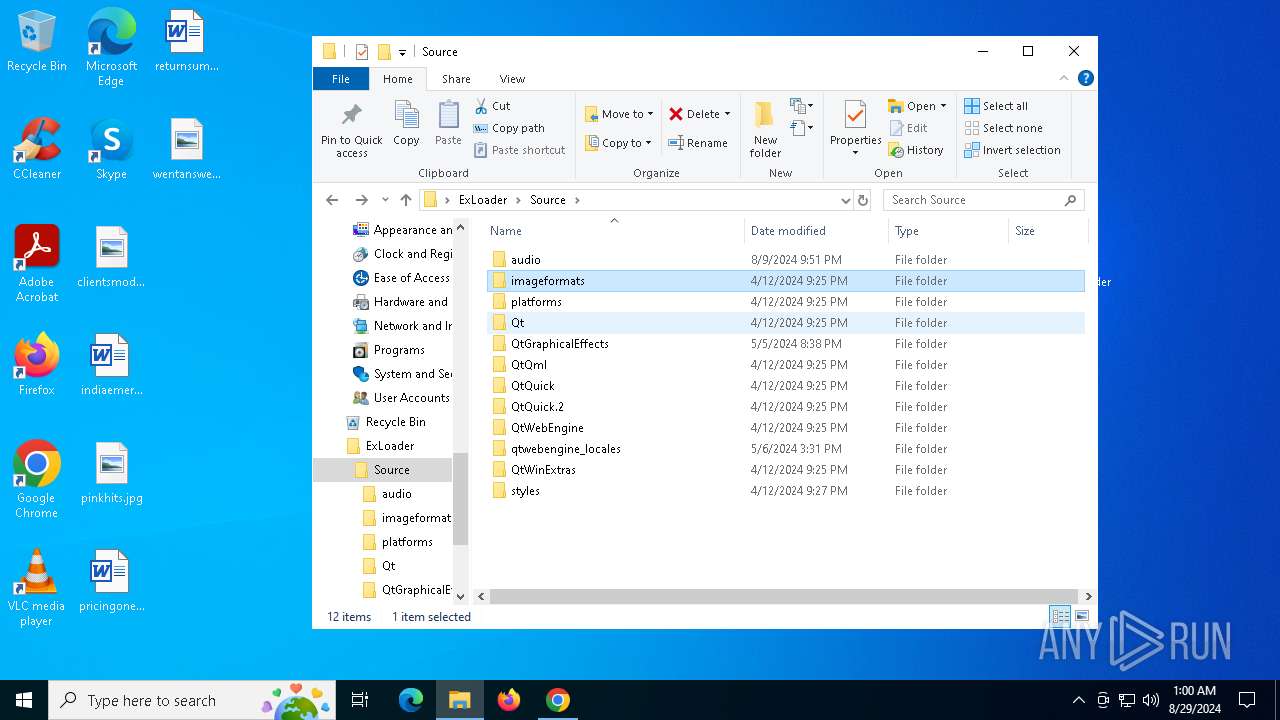
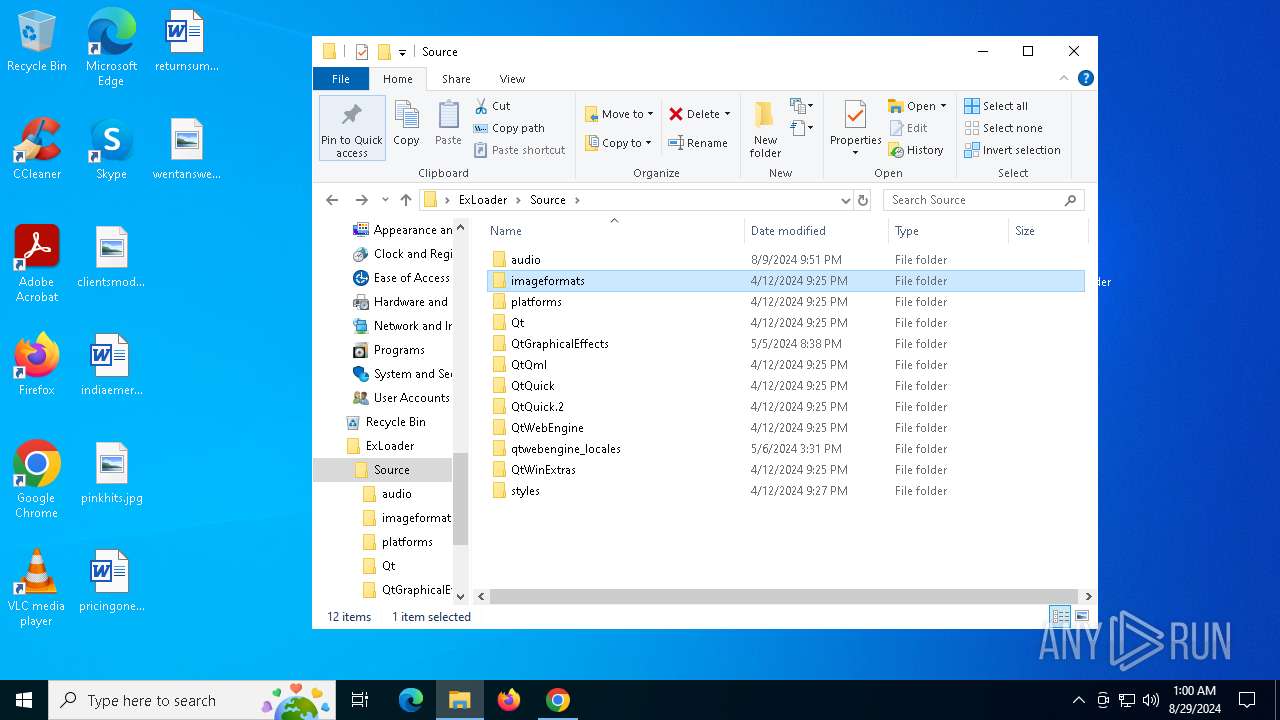
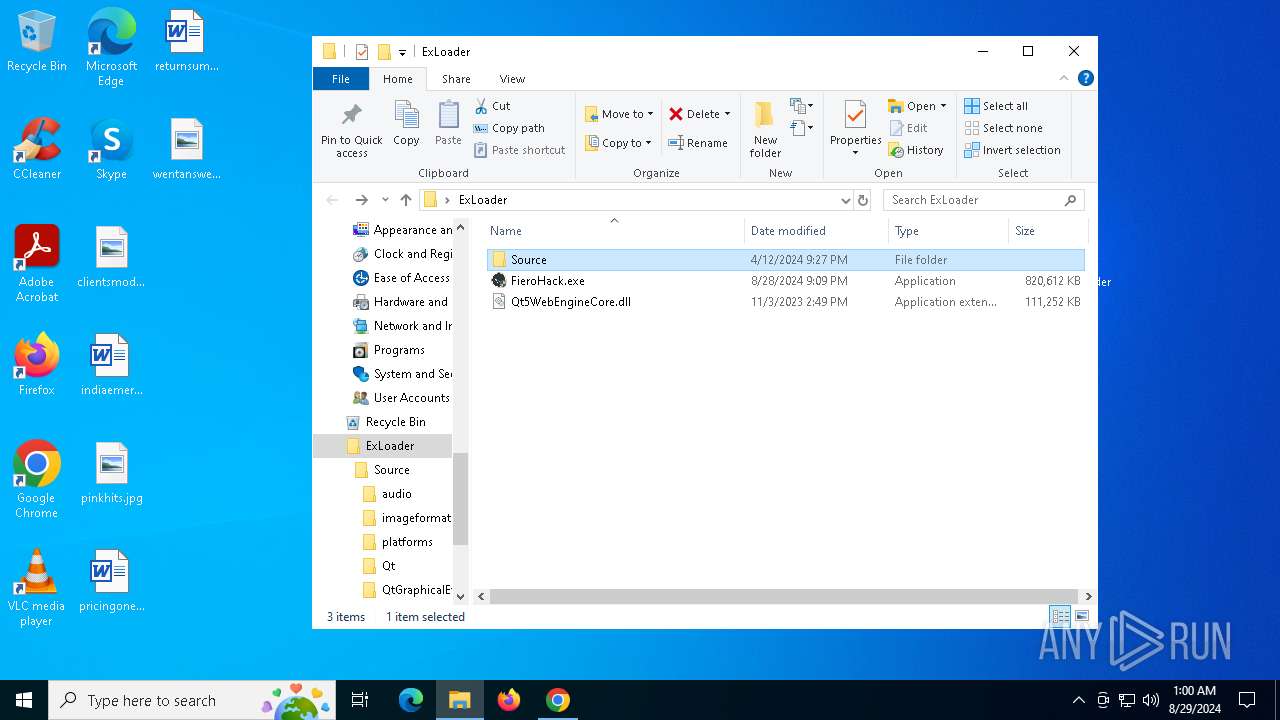
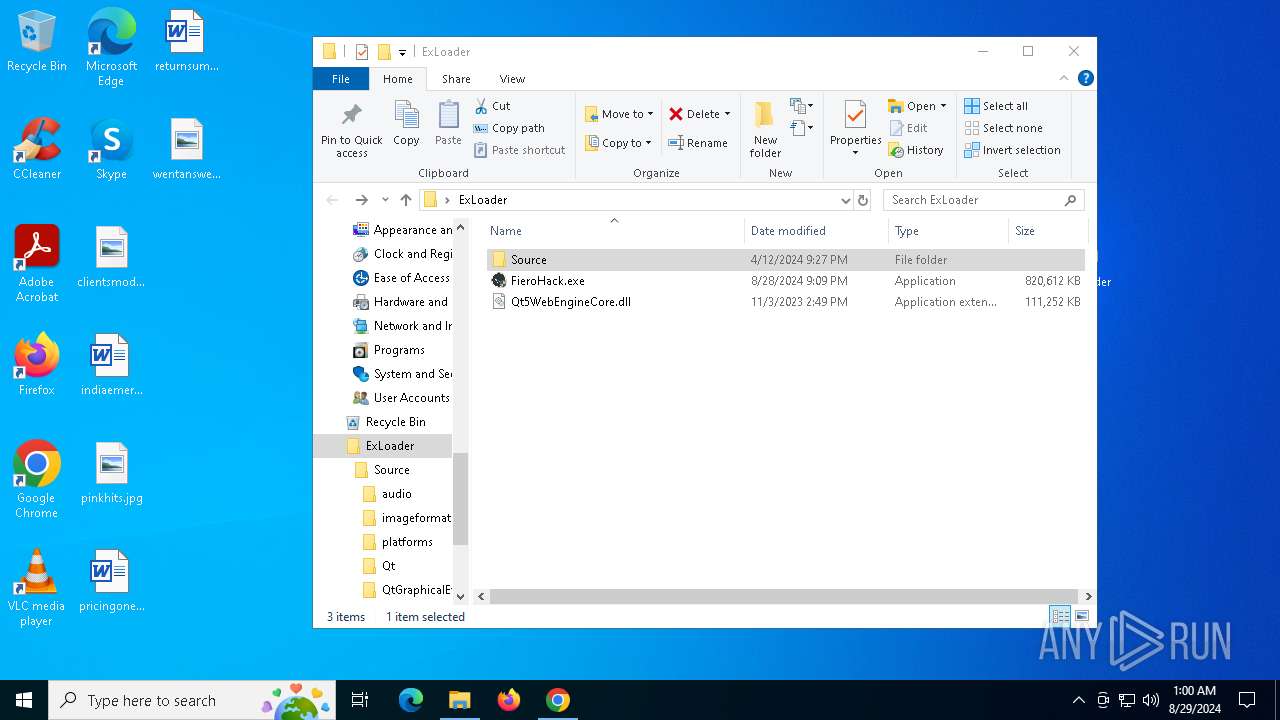
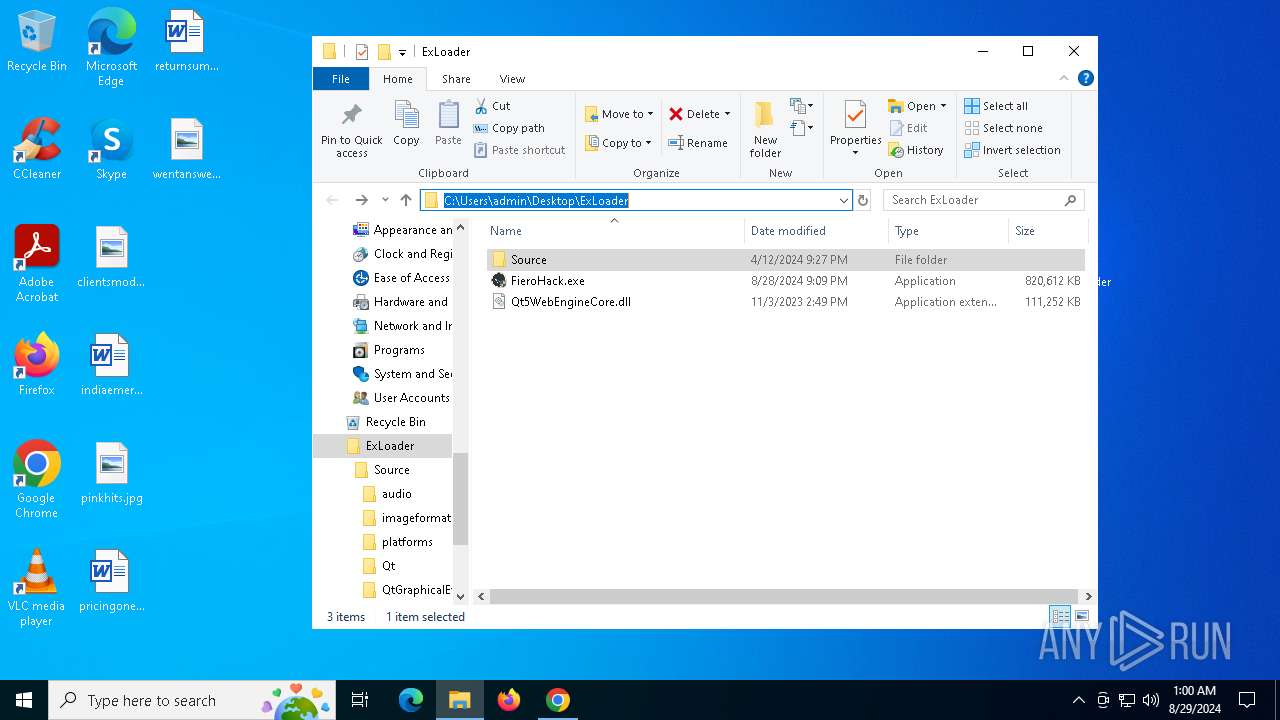
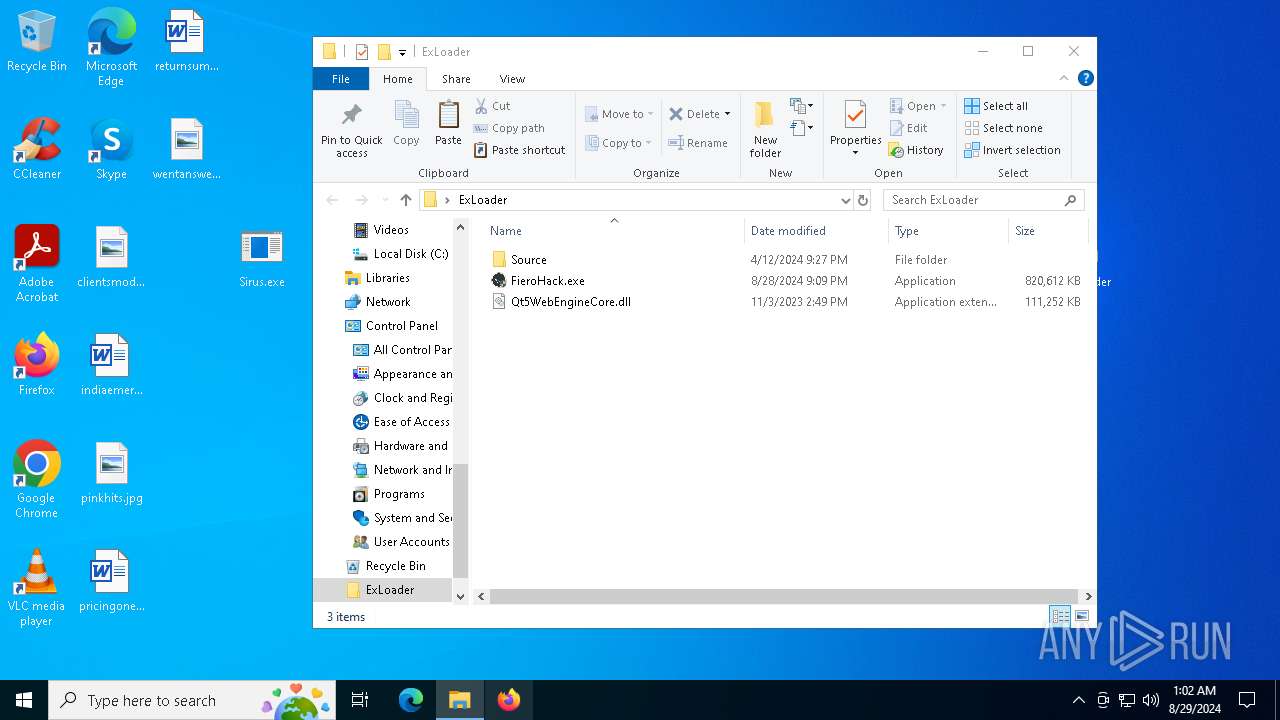
- FieroHack.exe (PID: 6040)
- firefox.exe (PID: 400)
Reads the software policy settings
- slui.exe (PID: 376)
- slui.exe (PID: 6712)
- RegAsm.exe (PID: 6504)
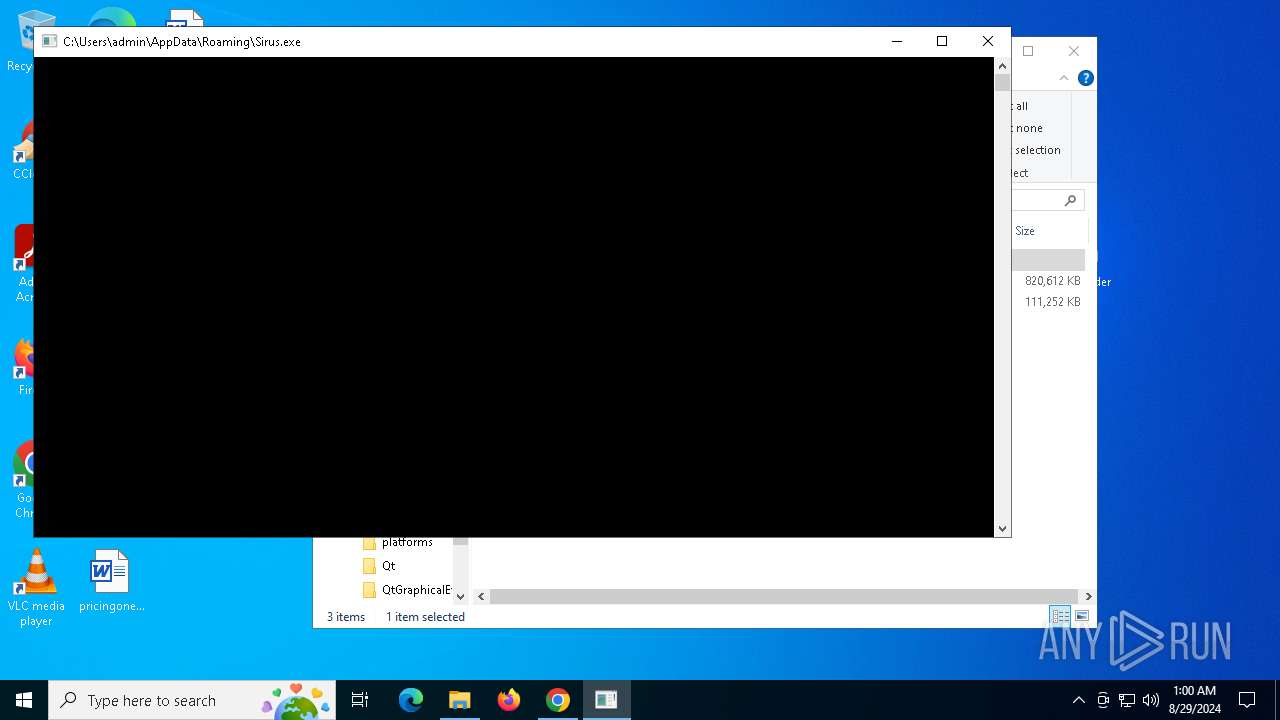
Checks supported languages
- FieroHack.exe (PID: 6040)
- WeAura.exe (PID: 6996)
- RegAsm.exe (PID: 6504)
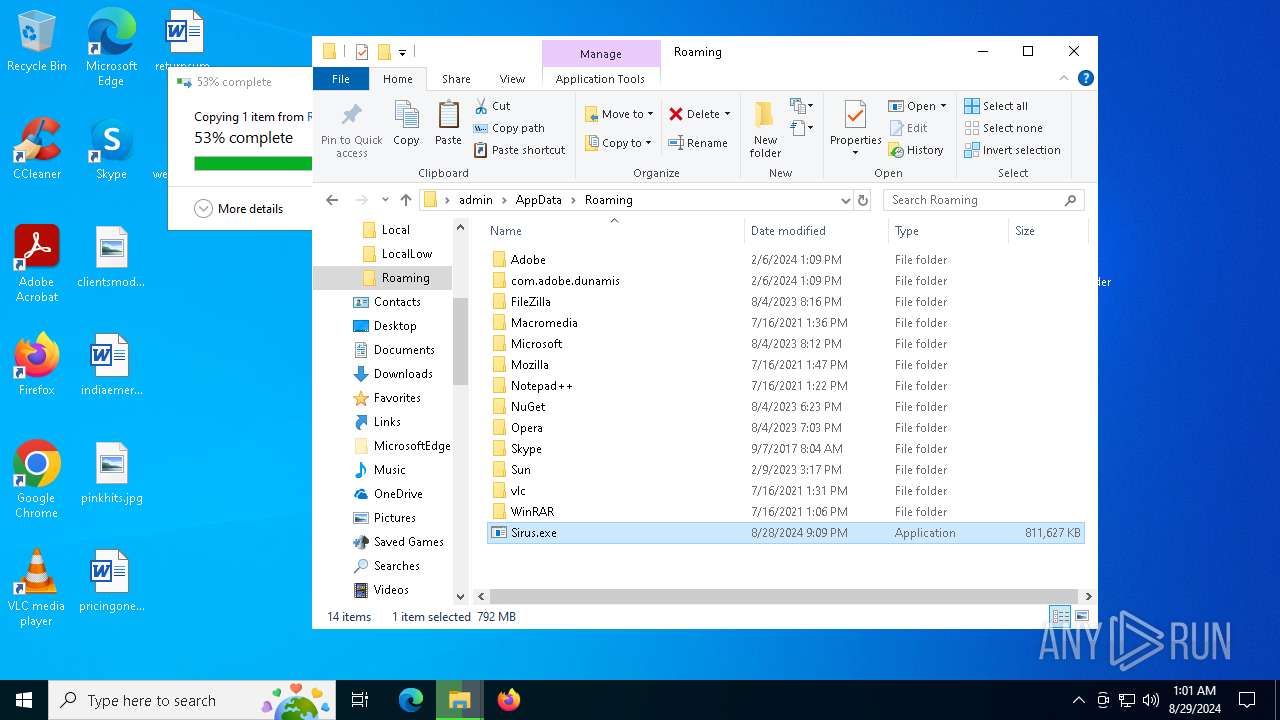
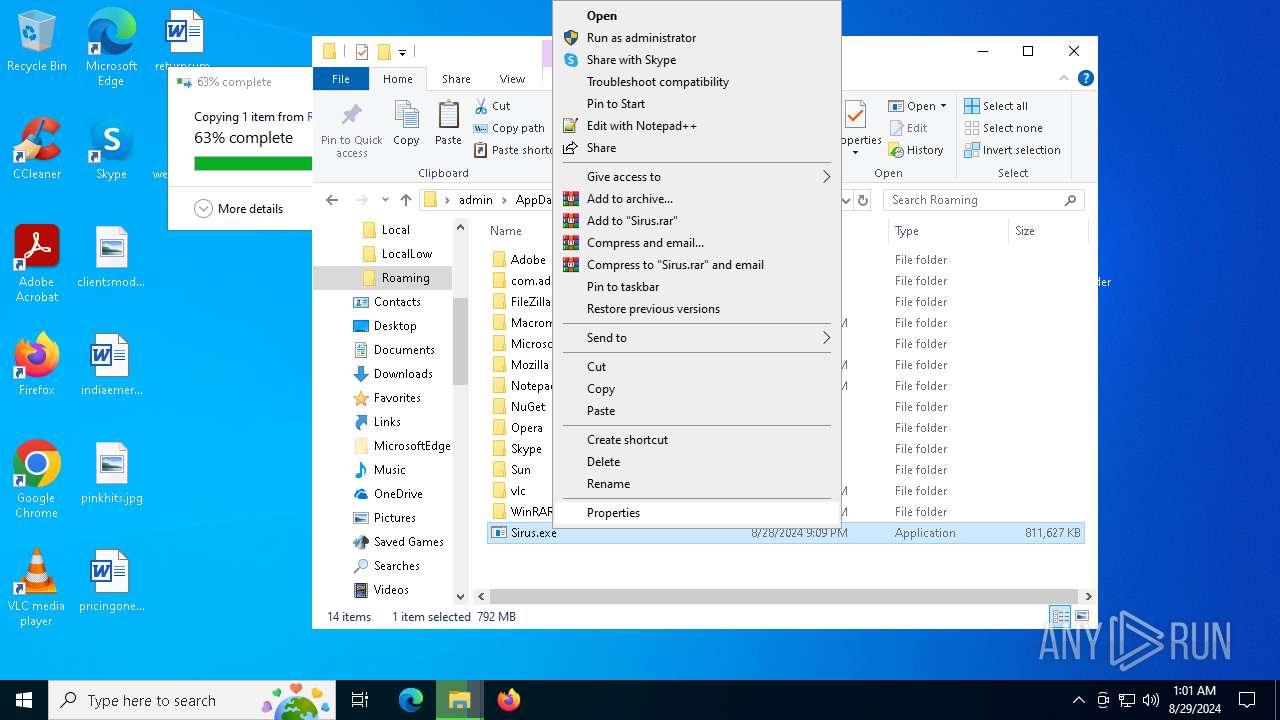
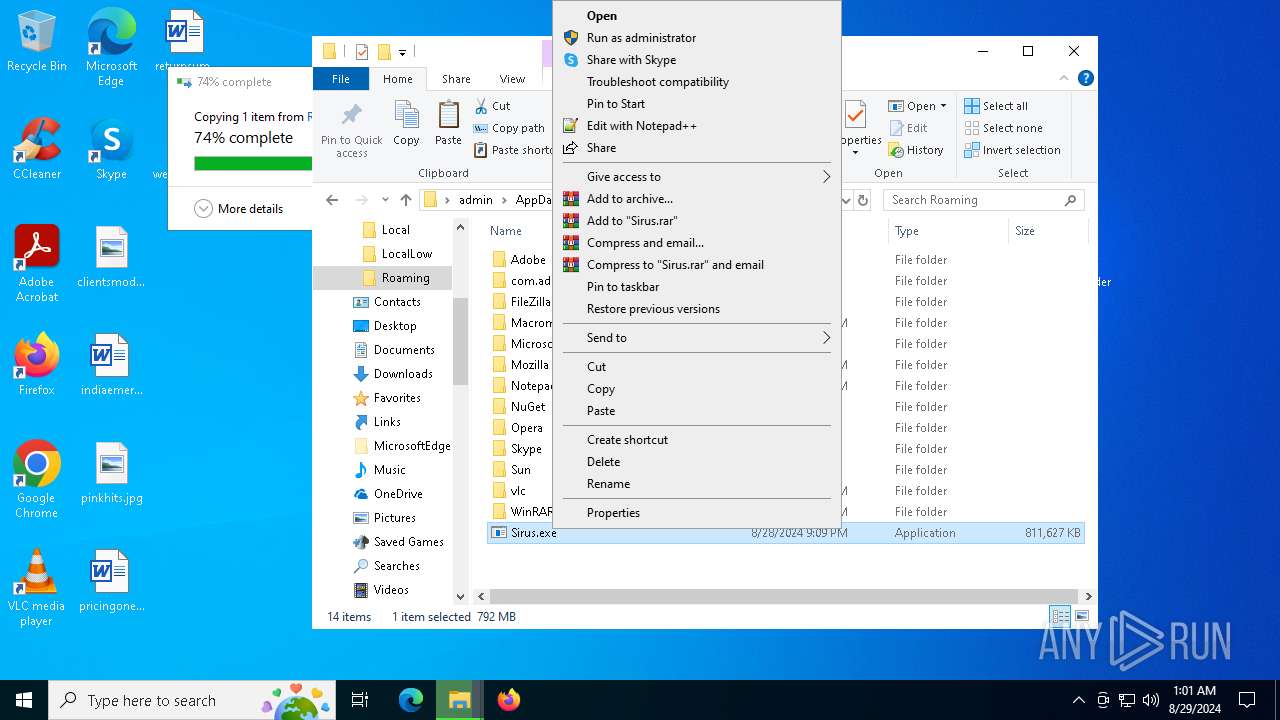
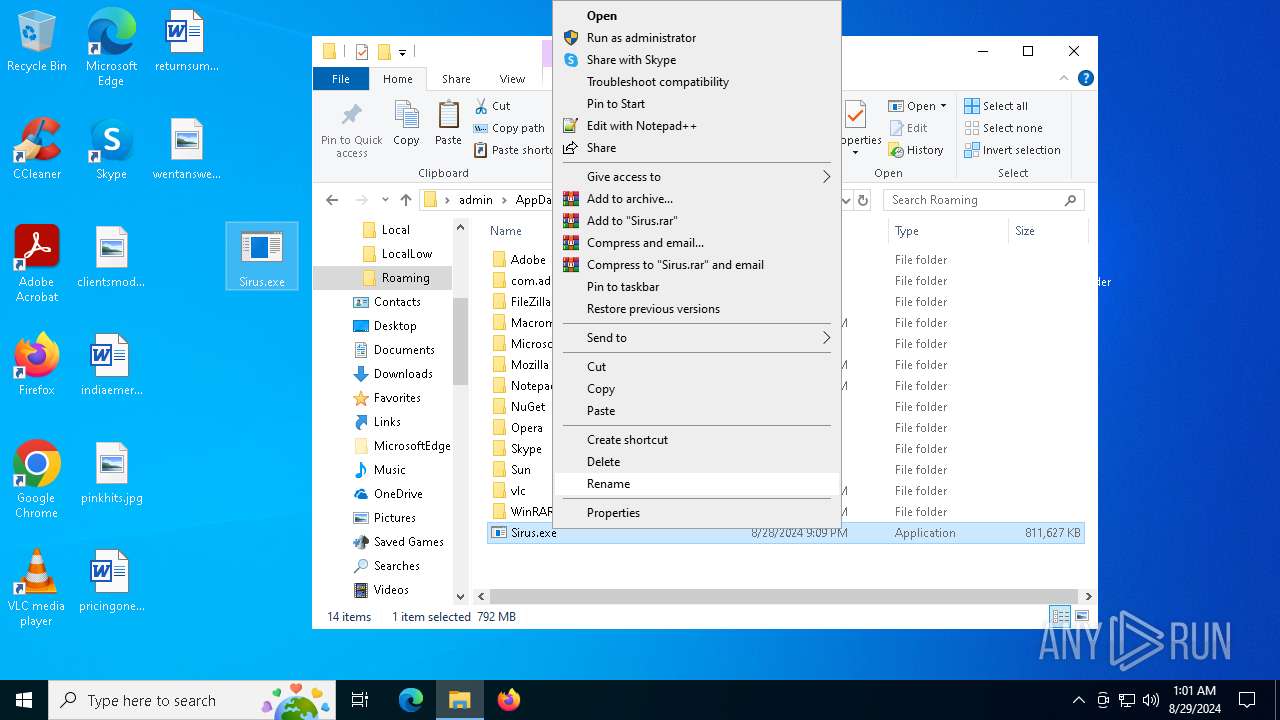
- Sirus.exe (PID: 1932)
- valrjyxscerz.exe (PID: 6292)
Application launched itself
- chrome.exe (PID: 5920)
- firefox.exe (PID: 2568)
- firefox.exe (PID: 400)
Creates files or folders in the user directory
- FieroHack.exe (PID: 6040)
Themida protector has been detected
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Process checks whether UAC notifications are on
- WeAura.exe (PID: 6996)
- valrjyxscerz.exe (PID: 6292)
Checks proxy server information
- slui.exe (PID: 6712)
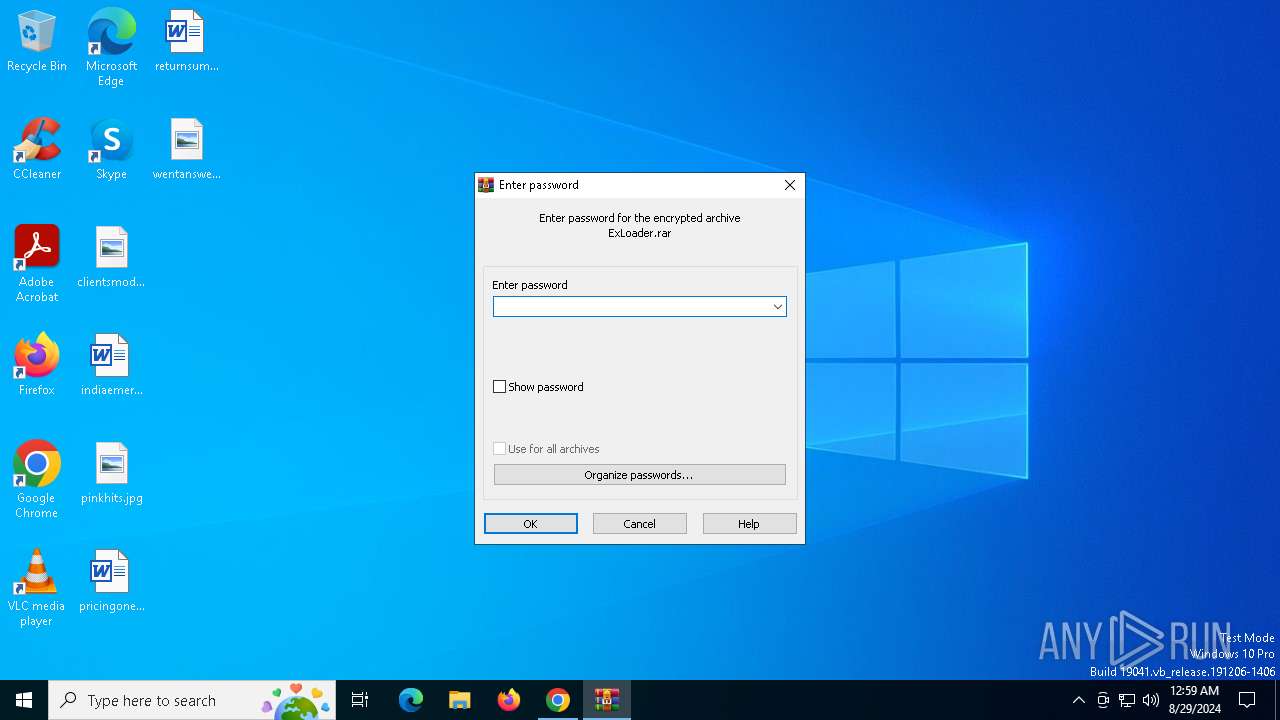
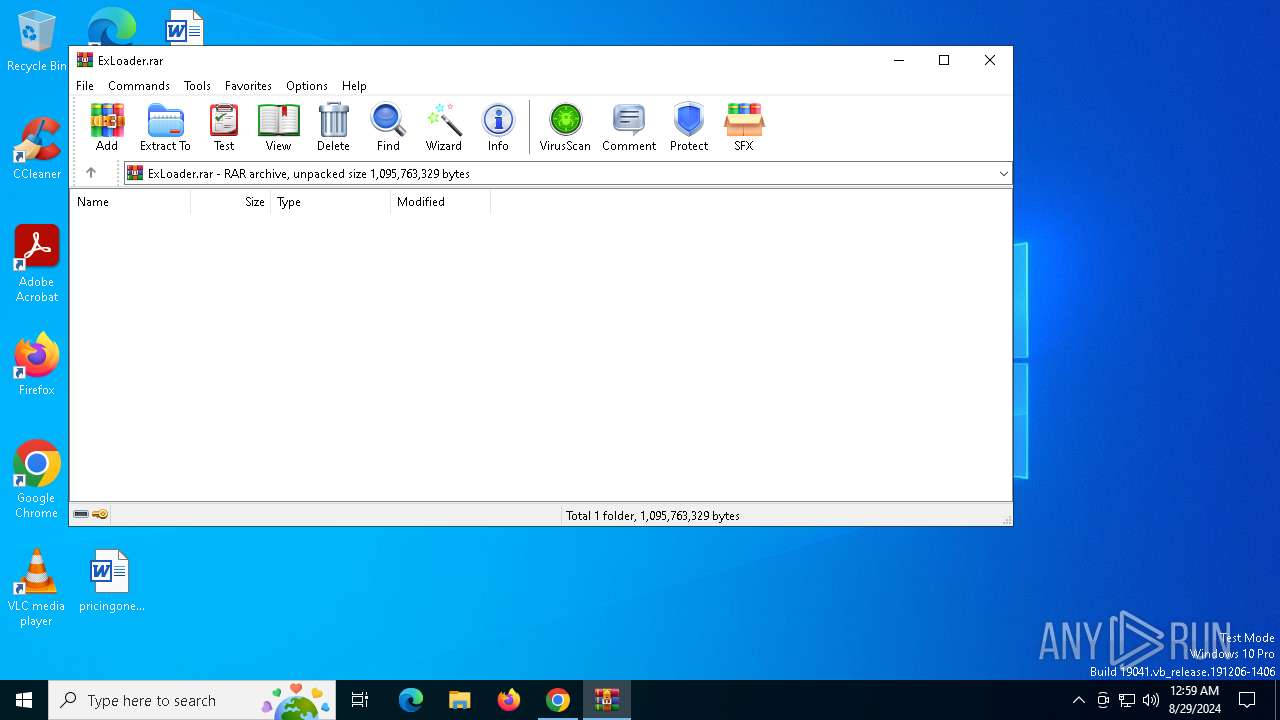
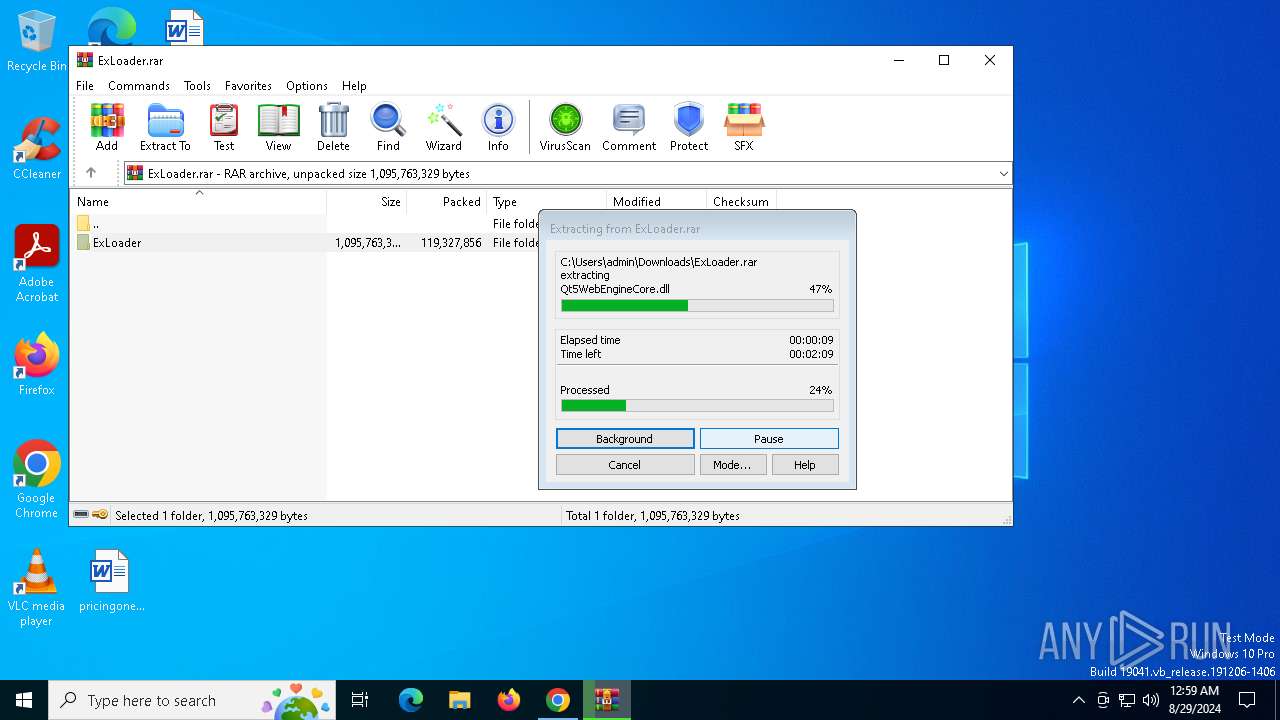
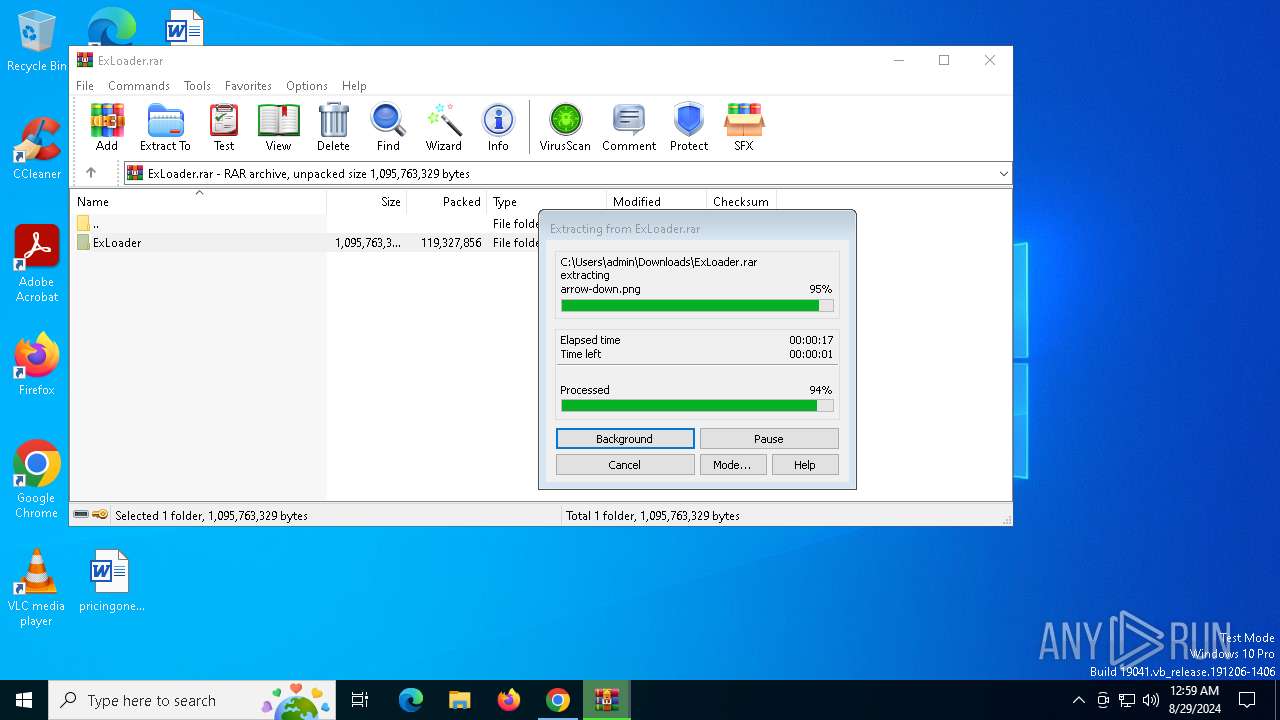
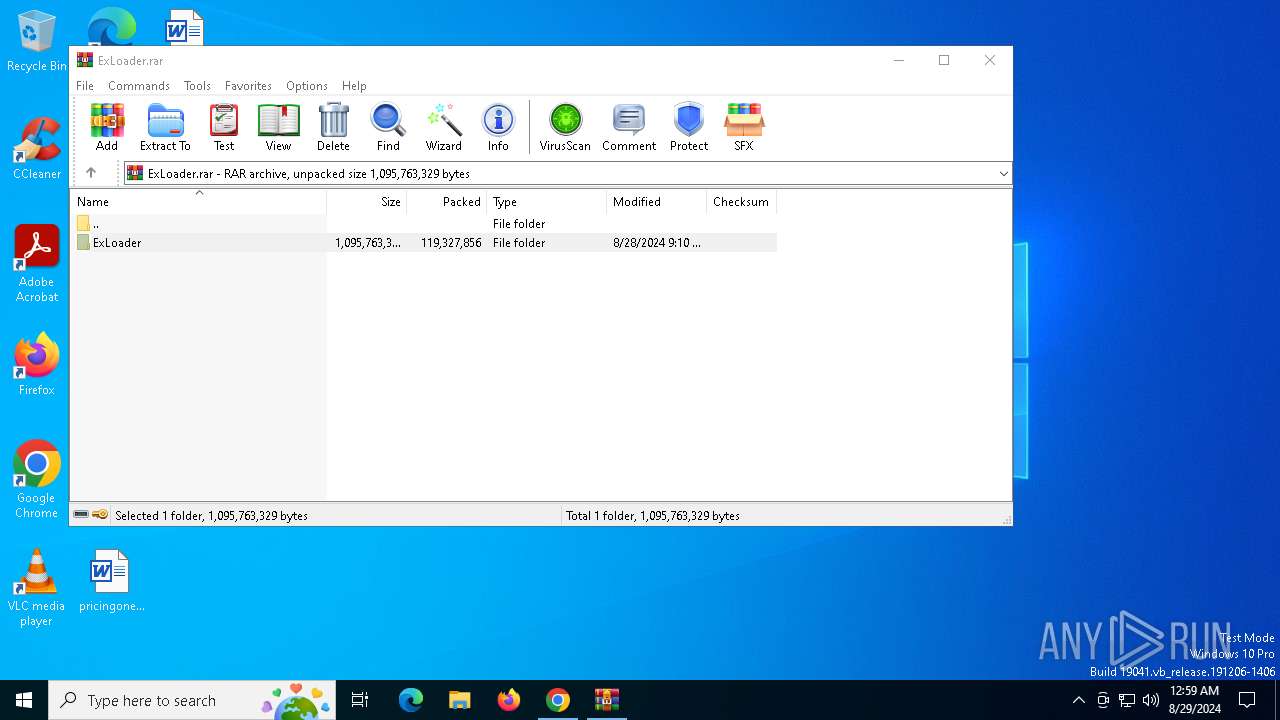
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4528)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 6504)
Reads the computer name
- Sirus.exe (PID: 1932)
- RegAsm.exe (PID: 6504)
Reads Environment values
- RegAsm.exe (PID: 6504)
.NET Reactor protector has been detected
- RegAsm.exe (PID: 6504)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 5088)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6880)
- powershell.exe (PID: 5088)
Creates files in the program directory
- WeAura.exe (PID: 6996)
UPX packer has been detected
- explorer.exe (PID: 5116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(5116) explorer.exe
Decrypted-URLs (1)https://206.12
Total processes
241
Monitored processes
104
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | valrjyxscerz.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | C:\WINDOWS\system32\powercfg.exe /x -hibernate-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | WeAura.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4244 --field-trial-handle=1896,i,17023781920181891652,13151195629988141500,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | valrjyxscerz.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
54 420
Read events
54 293
Write events
118
Delete events
9
Modification events
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5920) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
27
Suspicious files
345
Text files
366
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12b6e4.TMP | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12b6e4.TMP | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF12b89a.TMP | text | |
MD5:602C51DB8380F8CD0A961D9A46AF1186 | SHA256:84F716E38017F52138A76222524A3152DB8D3A7FBE30E94067458568B14DC36D | |||
| 5920 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:19D1A06251A8678F85D8DE5BFAB83807 | SHA256:AA6E55DCF84CDAF0BD3F913E7B837F65500E9B71A5A7AA773D02FFBC18C7FF01 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
126
DNS requests
161
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
740 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6268 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6268 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6816 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6816 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7080 | svchost.exe | 40.119.249.228:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.119.249.228:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6056 | RUXIMICS.exe | 40.119.249.228:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5920 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4688 | chrome.exe | 142.250.185.110:443 | www.youtube.com | GOOGLE | US | whitelisted |
4688 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4688 | chrome.exe | 142.250.185.227:443 | www.gstatic.com | GOOGLE | US | whitelisted |
4688 | chrome.exe | 142.250.185.74:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.youtube.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
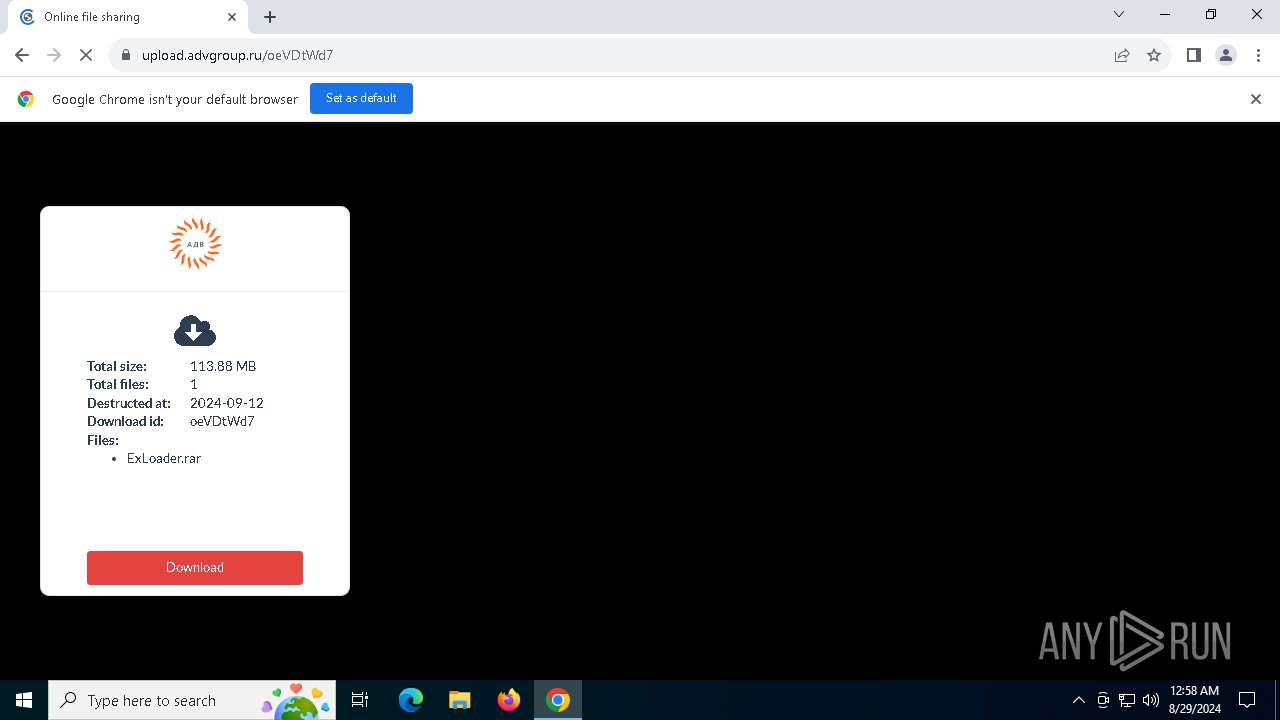
upload.advgroup.ru |
| unknown |
www.google.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4688 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4688 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6504 | RegAsm.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 13 |
6504 | RegAsm.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] MetaStealer v.5 TLS Certificate |
6504 | RegAsm.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] MetaStealer v.5 TLS Connection |
6504 | RegAsm.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] MetaStealer v.5 (MC-NMF TLS Server Certificate) |
2256 | svchost.exe | Crypto Currency Mining Activity Detected | ET MALWARE CoinMiner Domain in DNS Lookup (pool .supportxmr .com) |
1 ETPRO signatures available at the full report