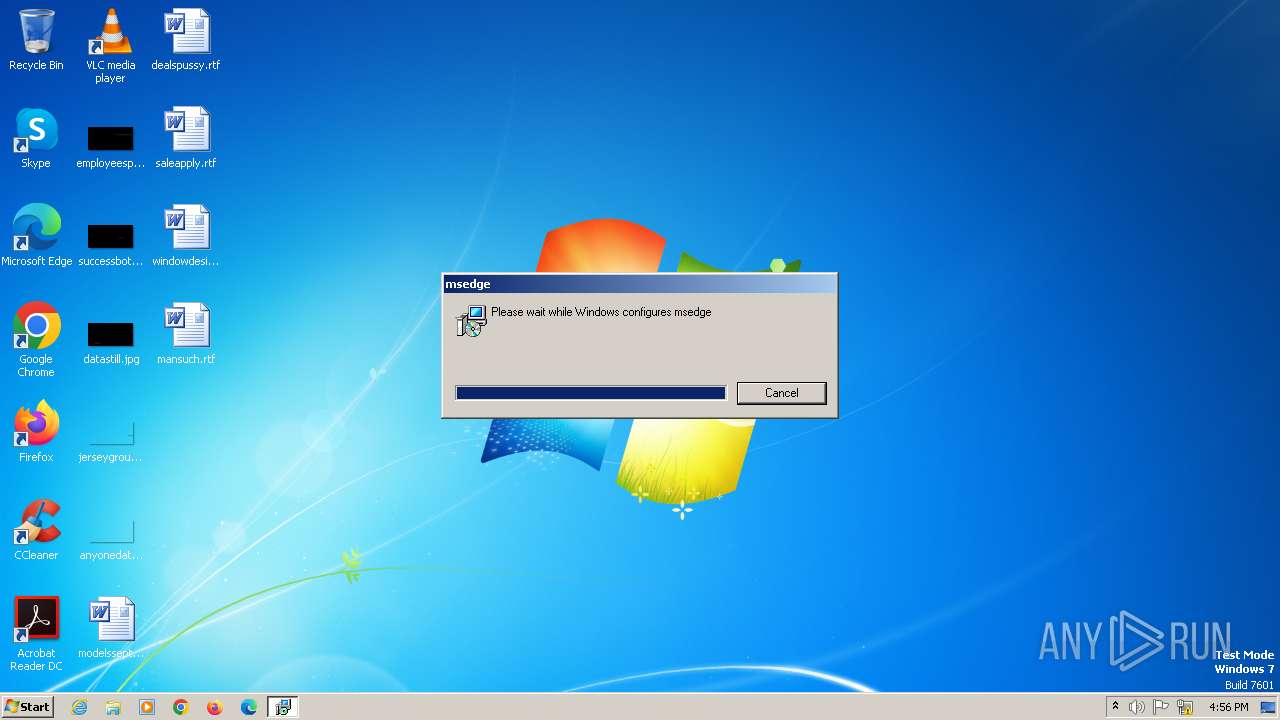
| File name: | N-.428270.msi |
| Full analysis: | https://app.any.run/tasks/43eaa667-14c0-45a2-83b6-7c90087c47fc |
| Verdict: | Malicious activity |
| Threats: | Danabot is an advanced banking Trojan malware that was designed to steal financial information from victims. Out of the Trojans in the wild, this is one of the most advanced thanks to the modular design and a complex delivery method. |
| Analysis date: | December 11, 2023, 16:55:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Title: Installation Database, Keywords: Installer, MSI, Database, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Number of Pages: 200, Security: 0, Code page: 1252, Revision Number: {40484CC9-6F70-4035-AC8C-C3866325D025}, Number of Words: 10, Subject: msedge, Author: msedge, Name of Creating Application: Advanced Installer 12.3 build 64631, Template: ;1033, Comments: This installer database contains the logic and data required to install msedge. |
| MD5: | C9C6DB0BF85A6E3B3021F7F86C32F0AC |
| SHA1: | 90797382CA79EE40ABDEAC09D4A334BB1326DEB7 |
| SHA256: | E7D5D59A61EC599175866BD863CAB56233C722E4B6637901CC0108CB52B419C5 |
| SSDEEP: | 98304:pMvn40ykSxzwBWCs6GUo/eS5l7EskJbNJkh3j2hMRi1sOlNE0OvdPVnPdND4v+ij:HR3 |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 1828)
- identity_helper.exe (PID: 2868)
Create files in the Startup directory
- msiexec.exe (PID: 1828)
Connects to the CnC server
- identity_helper.exe (PID: 2868)
DANABOT has been detected (YARA)
- identity_helper.exe (PID: 2868)
METAMORFO has been detected (YARA)
- c4u2-CDrex.exe (PID: 2852)
SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 1828)
Connects to unusual port
- identity_helper.exe (PID: 2868)
Reads the Internet Settings
- identity_helper.exe (PID: 2868)
Connects to the server without a host name
- c4u2-CDrex.exe (PID: 2852)
INFO
Reads the machine GUID from the registry
- msiexec.exe (PID: 1828)
- msiexec.exe (PID: 392)
Reads the computer name
- msiexec.exe (PID: 1828)
- msiexec.exe (PID: 392)
- identity_helper.exe (PID: 2868)
Create files in a temporary directory
- msiexec.exe (PID: 2932)
- msiexec.exe (PID: 1828)
Checks supported languages
- msiexec.exe (PID: 1828)
- msiexec.exe (PID: 392)
- identity_helper.exe (PID: 2868)
- c4u2-CDrex.exe (PID: 2852)
Creates files or folders in the user directory
- msiexec.exe (PID: 1828)
- identity_helper.exe (PID: 2868)
- c4u2-CDrex.exe (PID: 2852)
Reads Environment values
- c4u2-CDrex.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Title: | Installation Database |
|---|---|
| Keywords: | Installer, MSI, Database |
| LastPrinted: | 2009:12:11 11:47:44 |
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Pages: | 200 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {40484CC9-6F70-4035-AC8C-C3866325D025} |
| Words: | 10 |
| Subject: | msedge |
| Author: | msedge |
| LastModifiedBy: | - |
| Software: | Advanced Installer 12.3 build 64631 |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install msedge. |
Total processes
36
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\syswow64\MsiExec.exe -Embedding 38A32403523415D05B5C29711259BB51 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1828 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Roaming\CDrex\E8B5488BF90A4B94A2AADB597A00375A\c4u2-CDrex.exe" | C:\Users\admin\AppData\Roaming\CDrex\E8B5488BF90A4B94A2AADB597A00375A\c4u2-CDrex.exe | identity_helper.exe | ||||||||||||
User: admin Company: The CDex Project - http://cdex.mu/ Integrity Level: MEDIUM Description: CDex - Open Source Digital Audio CD Extractor Exit code: 0 Version: 2.05 Modules
| |||||||||||||||
| 2868 | "C:\Users\admin\Documents\identity_helper.exe" | C:\Users\admin\Documents\identity_helper.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 105.0.1343.50 Modules
| |||||||||||||||
| 2932 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\N-.428270.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 295
Read events
3 286
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2868) identity_helper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2868) identity_helper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2868) identity_helper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2868) identity_helper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2852) c4u2-CDrex.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Skype.exe | |||
Executable files
10
Suspicious files
4
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | identity_helper.exe | C:\Users\admin\AppData\Roaming\CDrex\E8B5488BF90A4B94A2AADB597A00375A\wnaspi32.dll | — | |
MD5:— | SHA256:— | |||
| 1828 | msiexec.exe | C:\Windows\Installer\MSIBAC0.tmp | executable | |
MD5:5C5BEF05B6F3806106F8F3CE13401CC1 | SHA256:F2F3AE8CA06F5CF320CA1D234A623BF55CF2B84C1D6DEA3D85D5392E29AAF437 | |||
| 2852 | c4u2-CDrex.exe | C:\Users\admin\AppData\Roaming\CDrex\E8B5488BF90A4B94A2AADB597A00375A\.pdf | — | |
MD5:— | SHA256:— | |||
| 1828 | msiexec.exe | C:\Windows\Installer\MSIBA80.tmp | executable | |
MD5:5C5BEF05B6F3806106F8F3CE13401CC1 | SHA256:F2F3AE8CA06F5CF320CA1D234A623BF55CF2B84C1D6DEA3D85D5392E29AAF437 | |||
| 1828 | msiexec.exe | C:\Windows\Installer\MSIBB3E.tmp | binary | |
MD5:F096F28326785A75D7E6A8E67E5B5149 | SHA256:A95D4271EC631AE55EF3BE62E75DCD06477F5B0922567813A20900100AE948E1 | |||
| 1828 | msiexec.exe | C:\Users\admin\Documents\msedge_elf.dll | executable | |
MD5:84DF8D4579B6FAFFFFD44B840448C341 | SHA256:C8A5573952F3D16D1681FBC8F4FEEA946F99B7209C70D3A0B22D43563EB173D8 | |||
| 1828 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF2FEFFFF414BE4E03.TMP | binary | |
MD5:665D53E7ACFB31C9F9668E857C29BB92 | SHA256:A036AEA50ECC80E6349937D37437EC6498A6EF07EADE80AF4E086C6B410FEB06 | |||
| 1828 | msiexec.exe | C:\Windows\Installer\22ba34.ipi | binary | |
MD5:2F757D31CB9C59008D1E5E079CDAE6E1 | SHA256:2E702A26A145B98F6D9E88DCE5C767BACD9AF62F5B0080CD607B83DFBF85E390 | |||
| 1828 | msiexec.exe | C:\Users\admin\Pictures\download (1).jfif | image | |
MD5:8F1C3C676DED12086617FDA43DCFAC76 | SHA256:AF4861D752A31E2B21F80D6D0446B7CD30094E680855E0F6793A6C12FD751871 | |||
| 1828 | msiexec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\identity_helper.cmd | text | |
MD5:5B3405F3063C8B1822D6A9959F44B419 | SHA256:5F5F31F0D8E364521765D5C2D65DEA208270C9140DE8379208B1693D68A62437 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
0
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2852 | c4u2-CDrex.exe | POST | 200 | 69.10.43.175:80 | http://69.10.43.175/1/zip.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2868 | identity_helper.exe | 216.238.118.19:48082 | — | AS-CHOOPA | BR | unknown |
2852 | c4u2-CDrex.exe | 69.10.43.175:80 | — | IS-AS-1 | US | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2868 | identity_helper.exe | Malware Command and Control Activity Detected | ET MALWARE [eSentire] Win32/Spy.Banker CnC Command (DOWNLOAD) |