| File name: | random.exe |
| Full analysis: | https://app.any.run/tasks/2193356e-7aed-4034-8663-a4f8e5f99a5a |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | March 16, 2025, 08:22:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | F0CAD0627E4B852E7CE633DF29855373 |
| SHA1: | 3187E3016D889FDCB5F3C38CC19C1DAC27163FE4 |
| SHA256: | E7B933849E850C1778C1378C7A5D07DF318D86F7B3EE6257885B768FA81F685C |
| SSDEEP: | 98304:gn2/2AvZ5PguaJjKQVCF4Jb9tJzTCtgdUxduWUYr3oPSgwleD/a9y8wSNHZA09Pq:I1ddm2uc |
MALICIOUS
AMADEY mutex has been found
- 1u87m9.exe (PID: 1660)
- rapes.exe (PID: 5364)
- TempBHPBVJ7N6OBJEASYUZWPJR76R9ZJEE6S.EXE (PID: 7352)
- Temp6KYGR25WAJYDGHNPSPT0SH5OHSIAGU6V.EXE (PID: 7420)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6584)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 2908)
- 2Q71SFVJ6FYFFM2WN.exe (PID: 5972)
- rapes.exe (PID: 8152)
- ZBXN87J24HMD6PBIQHQS0VLRTE2U.exe (PID: 8024)
- PDBw6sOKdW.exe (PID: 6476)
- rapes.exe (PID: 7600)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
AMADEY has been detected (SURICATA)
- rapes.exe (PID: 5364)
- Gxtuum.exe (PID: 7928)
StealC has been detected
- 3r19R.exe (PID: 4692)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
Connects to the CnC server
- 3r19R.exe (PID: 4692)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
STEALC has been detected (SURICATA)
- 3r19R.exe (PID: 4692)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
Actions looks like stealing of personal data
- 3r19R.exe (PID: 4692)
- MSBuild.exe (PID: 7456)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- 7608434c2a.exe (PID: 4880)
- 2d6f8edf24.exe (PID: 7644)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7488)
Run PowerShell with an invisible window
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
- powershell.exe (PID: 7260)
Changes the autorun value in the registry
- rapes.exe (PID: 5364)
AMADEY has been found (auto)
- rapes.exe (PID: 5364)
AMADEY has been detected (YARA)
- rapes.exe (PID: 5364)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
LUMMA mutex has been found
- MSBuild.exe (PID: 7456)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- 7608434c2a.exe (PID: 4880)
- 2d6f8edf24.exe (PID: 7644)
STEALC has been detected (YARA)
- 3r19R.exe (PID: 4692)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 7456)
- 3r19R.exe (PID: 4692)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- 7608434c2a.exe (PID: 4880)
GENERIC has been found (auto)
- 3r19R.exe (PID: 4692)
- rapes.exe (PID: 5364)
- HmngBpR.exe (PID: 4884)
- SplashWin.exe (PID: 6372)
- BitLockerToGo.exe (PID: 8044)
Possible tool for stealing has been detected
- cd34dbeb8a.exe (PID: 7264)
- firefox.exe (PID: 8108)
- cd34dbeb8a.exe (PID: 780)
- firefox.exe (PID: 4688)
- firefox.exe (PID: 7648)
- firefox.exe (PID: 7344)
- firefox.exe (PID: 2980)
- firefox.exe (PID: 4488)
- firefox.exe (PID: 6876)
- firefox.exe (PID: 7440)
- firefox.exe (PID: 6468)
- firefox.exe (PID: 3900)
- firefox.exe (PID: 8180)
- firefox.exe (PID: 6416)
- firefox.exe (PID: 3784)
- firefox.exe (PID: 3900)
- firefox.exe (PID: 7100)
- firefox.exe (PID: 7620)
- firefox.exe (PID: 5188)
- firefox.exe (PID: 6656)
- firefox.exe (PID: 7776)
- firefox.exe (PID: 5260)
Executing a file with an untrusted certificate
- 2d6f8edf24.exe (PID: 5796)
- 2d6f8edf24.exe (PID: 7644)
GCLEANER has been detected (SURICATA)
- BitLockerToGo.exe (PID: 8044)
Uses Task Scheduler to autorun other applications
- packed.exe (PID: 7448)
Changes the login/logoff helper path in the registry
- powershell.exe (PID: 6640)
SUSPICIOUS
Starts a Microsoft application from unusual location
- random.exe (PID: 5164)
- u0k28.exe (PID: 1188)
Executable content was dropped or overwritten
- random.exe (PID: 5164)
- u0k28.exe (PID: 1188)
- 1u87m9.exe (PID: 1660)
- rapes.exe (PID: 5364)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 7244)
- 3r19R.exe (PID: 4692)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- zY9sqWs.exe (PID: 7848)
- BitLockerToGo.exe (PID: 8044)
- yPO0L3ehRR.exe (PID: 4572)
- yPO0L3ehRR.tmp (PID: 2960)
- splitcattools.exe (PID: 7484)
- HmngBpR.exe (PID: 4884)
- SplashWin.exe (PID: 6372)
- packed.exe (PID: 7448)
- powershell.exe (PID: 7760)
- rsfff01fff.exe (PID: 7412)
- rsfff01fff.exe (PID: 7588)
- irestore.exe (PID: 1276)
Reads security settings of Internet Explorer
- 1u87m9.exe (PID: 1660)
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
- zY9sqWs.exe (PID: 7848)
- Gxtuum.exe (PID: 7928)
- BitLockerToGo.exe (PID: 8044)
- splitcattools.exe (PID: 7484)
- packed.exe (PID: 5556)
Reads the BIOS version
- 1u87m9.exe (PID: 1660)
- 2x8387.exe (PID: 5204)
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
- Temp6KYGR25WAJYDGHNPSPT0SH5OHSIAGU6V.EXE (PID: 7420)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6584)
- TempBHPBVJ7N6OBJEASYUZWPJR76R9ZJEE6S.EXE (PID: 7352)
- e0a692e7d3.exe (PID: 1568)
- 4a27ad871b.exe (PID: 7264)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 2908)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- rapes.exe (PID: 8152)
- 788a2fc0fb.exe (PID: 6592)
- 2Q71SFVJ6FYFFM2WN.exe (PID: 5972)
- 588ec43a33.exe (PID: 8100)
- ZBXN87J24HMD6PBIQHQS0VLRTE2U.exe (PID: 8024)
- 788a2fc0fb.exe (PID: 208)
- 7608434c2a.exe (PID: 4880)
- 588ec43a33.exe (PID: 7908)
- 8b9a560002.exe (PID: 4932)
- PDBw6sOKdW.exe (PID: 6476)
- rapes.exe (PID: 7600)
Starts itself from another location
- 1u87m9.exe (PID: 1660)
- zY9sqWs.exe (PID: 7848)
- SplashWin.exe (PID: 6372)
- rsfff01fff.exe (PID: 7412)
- irestore.exe (PID: 1276)
Process drops legitimate windows executable
- random.exe (PID: 5164)
- 3r19R.exe (PID: 4692)
- yPO0L3ehRR.tmp (PID: 2960)
- HmngBpR.exe (PID: 4884)
- SplashWin.exe (PID: 6372)
- rsfff01fff.exe (PID: 7588)
- irestore.exe (PID: 1276)
Contacting a server suspected of hosting an CnC
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
- Gxtuum.exe (PID: 7928)
Windows Defender mutex has been found
- 3r19R.exe (PID: 4692)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
Searches for installed software
- 3r19R.exe (PID: 4692)
- MSBuild.exe (PID: 7456)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- 7608434c2a.exe (PID: 4880)
- 2d6f8edf24.exe (PID: 7644)
Potential Corporate Privacy Violation
- 3r19R.exe (PID: 4692)
- rapes.exe (PID: 5364)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- BitLockerToGo.exe (PID: 8044)
Process requests binary or script from the Internet
- 3r19R.exe (PID: 4692)
- rapes.exe (PID: 5364)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
Connects to the server without a host name
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- Gxtuum.exe (PID: 7928)
- BitLockerToGo.exe (PID: 8044)
Probably download files using WebClient
- mshta.exe (PID: 7256)
- mshta.exe (PID: 7932)
- mshta.exe (PID: 4932)
- mshta.exe (PID: 7976)
Starts CMD.EXE for commands execution
- 96526116ec.exe (PID: 5360)
- 96526116ec.exe (PID: 7904)
- rapes.exe (PID: 5364)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7488)
- SplashWin.exe (PID: 5136)
- irestore.exe (PID: 5400)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7256)
- mshta.exe (PID: 7932)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 8132)
- mshta.exe (PID: 4932)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 8020)
- mshta.exe (PID: 7976)
- splitcattools.exe (PID: 7484)
- packed.exe (PID: 7448)
- ADFoyxP.exe (PID: 2516)
Starts process via Powershell
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
Manipulates environment variables
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
Found IP address in command line
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7504)
There is functionality for enable RDP (YARA)
- rapes.exe (PID: 5364)
Executing commands from ".cmd" file
- rapes.exe (PID: 5364)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7812)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 8020)
Application launched itself
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7488)
- 2d6f8edf24.exe (PID: 5796)
- packed.exe (PID: 5556)
Multiple wallet extension IDs have been found
- 3r19R.exe (PID: 4692)
- MSBuild.exe (PID: 7456)
The process drops C-runtime libraries
- 3r19R.exe (PID: 4692)
- yPO0L3ehRR.tmp (PID: 2960)
- SplashWin.exe (PID: 6372)
- HmngBpR.exe (PID: 4884)
- rsfff01fff.exe (PID: 7588)
- irestore.exe (PID: 1276)
The process drops Mozilla's DLL files
- 3r19R.exe (PID: 4692)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 7456)
The process executes via Task Scheduler
- rapes.exe (PID: 8152)
- rapes.exe (PID: 7600)
- Gxtuum.exe (PID: 7560)
Uses TASKKILL.EXE to kill Browsers
- cd34dbeb8a.exe (PID: 7264)
- cd34dbeb8a.exe (PID: 780)
Uses TASKKILL.EXE to kill process
- cd34dbeb8a.exe (PID: 7264)
- cd34dbeb8a.exe (PID: 780)
Reads the Windows owner or organization settings
- yPO0L3ehRR.tmp (PID: 2960)
Reads the date of Windows installation
- packed.exe (PID: 5556)
The process bypasses the loading of PowerShell profile settings
- packed.exe (PID: 7448)
Base64-obfuscated command line is found
- packed.exe (PID: 7448)
BASE64 encoded PowerShell command has been detected
- packed.exe (PID: 7448)
Downloads file from URI via Powershell
- powershell.exe (PID: 7760)
Connects to unusual port
- 0000026153.exe (PID: 2552)
Checks for external IP
- 0000026153.exe (PID: 2552)
- svchost.exe (PID: 2196)
INFO
Create files in a temporary directory
- random.exe (PID: 5164)
- u0k28.exe (PID: 1188)
- 1u87m9.exe (PID: 1660)
- rapes.exe (PID: 5364)
- 96526116ec.exe (PID: 5360)
- 96526116ec.exe (PID: 7904)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- zY9sqWs.exe (PID: 7848)
- yPO0L3ehRR.exe (PID: 4572)
- yPO0L3ehRR.tmp (PID: 2960)
- HmngBpR.exe (PID: 4884)
- SplashWin.exe (PID: 5136)
- BitLockerToGo.exe (PID: 8044)
- rsfff01fff.exe (PID: 7412)
- rsfff01fff.exe (PID: 7588)
- irestore.exe (PID: 5400)
Checks supported languages
- random.exe (PID: 5164)
- u0k28.exe (PID: 1188)
- 1u87m9.exe (PID: 1660)
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
- 2x8387.exe (PID: 5204)
- 96526116ec.exe (PID: 5360)
- 96526116ec.exe (PID: 7904)
- TempBHPBVJ7N6OBJEASYUZWPJR76R9ZJEE6S.EXE (PID: 7352)
- FnJ67k2.exe (PID: 7688)
- MSBuild.exe (PID: 7456)
- Temp6KYGR25WAJYDGHNPSPT0SH5OHSIAGU6V.EXE (PID: 7420)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6584)
- e0a692e7d3.exe (PID: 1568)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 2908)
- 4a27ad871b.exe (PID: 7264)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- rapes.exe (PID: 8152)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
- cd34dbeb8a.exe (PID: 7264)
- cd34dbeb8a.exe (PID: 780)
- 2Q71SFVJ6FYFFM2WN.exe (PID: 5972)
- 588ec43a33.exe (PID: 8100)
- ZBXN87J24HMD6PBIQHQS0VLRTE2U.exe (PID: 8024)
- 7608434c2a.exe (PID: 4880)
- 588ec43a33.exe (PID: 7908)
- 8b9a560002.exe (PID: 4932)
- 2d6f8edf24.exe (PID: 5796)
- 2d6f8edf24.exe (PID: 7644)
- zY9sqWs.exe (PID: 7848)
- Gxtuum.exe (PID: 7928)
- BitLockerToGo.exe (PID: 8044)
- yPO0L3ehRR.exe (PID: 4572)
- yPO0L3ehRR.tmp (PID: 2960)
- splitcattools.exe (PID: 7484)
- HmngBpR.exe (PID: 4884)
- SplashWin.exe (PID: 6372)
- SplashWin.exe (PID: 5136)
- PDBw6sOKdW.exe (PID: 6476)
- SplitcatTools.exe (PID: 8100)
- rapes.exe (PID: 7600)
- Gxtuum.exe (PID: 7560)
- packed.exe (PID: 5556)
- packed.exe (PID: 7448)
- ADFoyxP.exe (PID: 2516)
- 0000026153.exe (PID: 2552)
- rsfff01fff.exe (PID: 7412)
- irestore.exe (PID: 1276)
- rsfff01fff.exe (PID: 7588)
- irestore.exe (PID: 5400)
Reads the computer name
- 1u87m9.exe (PID: 1660)
- 2x8387.exe (PID: 5204)
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
- 96526116ec.exe (PID: 5360)
- 96526116ec.exe (PID: 7904)
- MSBuild.exe (PID: 7456)
- e0a692e7d3.exe (PID: 1568)
- 4a27ad871b.exe (PID: 7264)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- 788a2fc0fb.exe (PID: 208)
- cd34dbeb8a.exe (PID: 7264)
- 788a2fc0fb.exe (PID: 6592)
- cd34dbeb8a.exe (PID: 780)
- 588ec43a33.exe (PID: 8100)
- 588ec43a33.exe (PID: 7908)
- 7608434c2a.exe (PID: 4880)
- 2d6f8edf24.exe (PID: 7644)
- zY9sqWs.exe (PID: 7848)
- Gxtuum.exe (PID: 7928)
- BitLockerToGo.exe (PID: 8044)
- yPO0L3ehRR.tmp (PID: 2960)
- splitcattools.exe (PID: 7484)
- HmngBpR.exe (PID: 4884)
- SplashWin.exe (PID: 6372)
- SplashWin.exe (PID: 5136)
- SplitcatTools.exe (PID: 8100)
- packed.exe (PID: 5556)
- ADFoyxP.exe (PID: 2516)
- 0000026153.exe (PID: 2552)
- rsfff01fff.exe (PID: 7588)
Process checks computer location settings
- 1u87m9.exe (PID: 1660)
- rapes.exe (PID: 5364)
- zY9sqWs.exe (PID: 7848)
- splitcattools.exe (PID: 7484)
- packed.exe (PID: 5556)
The sample compiled with english language support
- random.exe (PID: 5164)
- 3r19R.exe (PID: 4692)
- yPO0L3ehRR.tmp (PID: 2960)
- splitcattools.exe (PID: 7484)
- SplashWin.exe (PID: 6372)
- HmngBpR.exe (PID: 4884)
- powershell.exe (PID: 7760)
- rsfff01fff.exe (PID: 7412)
- rsfff01fff.exe (PID: 7588)
- irestore.exe (PID: 1276)
Reads the software policy settings
- 2x8387.exe (PID: 5204)
- MSBuild.exe (PID: 7456)
- e0a692e7d3.exe (PID: 1568)
- 4a27ad871b.exe (PID: 7264)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- 7608434c2a.exe (PID: 4880)
- 2d6f8edf24.exe (PID: 7644)
- rapes.exe (PID: 5364)
- slui.exe (PID: 7840)
- 0000026153.exe (PID: 2552)
Checks proxy server information
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7552)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
- 788a2fc0fb.exe (PID: 208)
- 788a2fc0fb.exe (PID: 6592)
- Gxtuum.exe (PID: 7928)
- BitLockerToGo.exe (PID: 8044)
- slui.exe (PID: 7840)
- powershell.exe (PID: 7760)
Reads the machine GUID from the registry
- 2x8387.exe (PID: 5204)
- MSBuild.exe (PID: 7456)
- e0a692e7d3.exe (PID: 1568)
- 4a27ad871b.exe (PID: 7264)
- e29a9bc6d5.exe (PID: 6372)
- cb68442713.exe (PID: 5260)
- cb68442713.exe (PID: 7832)
- 7608434c2a.exe (PID: 4880)
- 2d6f8edf24.exe (PID: 7644)
- BitLockerToGo.exe (PID: 8044)
- rapes.exe (PID: 5364)
- 0000026153.exe (PID: 2552)
Creates files or folders in the user directory
- 3r19R.exe (PID: 4692)
- rapes.exe (PID: 5364)
- 788a2fc0fb.exe (PID: 6592)
- 788a2fc0fb.exe (PID: 208)
- BitLockerToGo.exe (PID: 8044)
- yPO0L3ehRR.tmp (PID: 2960)
- SplashWin.exe (PID: 6372)
- irestore.exe (PID: 1276)
Reads Environment values
- 3r19R.exe (PID: 4692)
Reads product name
- 3r19R.exe (PID: 4692)
Reads CPU info
- 3r19R.exe (PID: 4692)
Application launched itself
- chrome.exe (PID: 5244)
- msedge.exe (PID: 7900)
- firefox.exe (PID: 8108)
- firefox.exe (PID: 6656)
- firefox.exe (PID: 4688)
- firefox.exe (PID: 4880)
- firefox.exe (PID: 8016)
- firefox.exe (PID: 7344)
- firefox.exe (PID: 2980)
- firefox.exe (PID: 7452)
- firefox.exe (PID: 7100)
- firefox.exe (PID: 7760)
- firefox.exe (PID: 2268)
- firefox.exe (PID: 4488)
- firefox.exe (PID: 7176)
- firefox.exe (PID: 6876)
- firefox.exe (PID: 728)
- firefox.exe (PID: 6676)
- firefox.exe (PID: 7440)
- firefox.exe (PID: 6752)
- firefox.exe (PID: 6468)
- firefox.exe (PID: 7744)
- firefox.exe (PID: 7152)
- firefox.exe (PID: 3900)
- firefox.exe (PID: 6300)
- firefox.exe (PID: 6384)
- firefox.exe (PID: 7648)
- firefox.exe (PID: 8180)
- firefox.exe (PID: 6388)
- firefox.exe (PID: 4844)
- firefox.exe (PID: 6416)
- firefox.exe (PID: 7144)
- firefox.exe (PID: 6660)
- firefox.exe (PID: 5400)
- firefox.exe (PID: 3900)
- firefox.exe (PID: 6640)
- firefox.exe (PID: 6576)
- firefox.exe (PID: 5244)
- firefox.exe (PID: 1600)
- firefox.exe (PID: 7100)
- firefox.exe (PID: 1312)
- firefox.exe (PID: 7260)
- firefox.exe (PID: 3784)
- firefox.exe (PID: 7620)
- firefox.exe (PID: 4056)
- firefox.exe (PID: 7352)
- firefox.exe (PID: 7576)
- firefox.exe (PID: 5188)
- firefox.exe (PID: 6808)
- firefox.exe (PID: 6656)
- firefox.exe (PID: 7152)
- firefox.exe (PID: 2432)
- firefox.exe (PID: 7776)
- firefox.exe (PID: 7728)
- firefox.exe (PID: 856)
- firefox.exe (PID: 5260)
- firefox.exe (PID: 8128)
- firefox.exe (PID: 1348)
Reads mouse settings
- 96526116ec.exe (PID: 5360)
- 96526116ec.exe (PID: 7904)
- cd34dbeb8a.exe (PID: 7264)
- cd34dbeb8a.exe (PID: 780)
Reads Internet Explorer settings
- mshta.exe (PID: 7256)
- mshta.exe (PID: 7932)
- mshta.exe (PID: 4932)
- mshta.exe (PID: 7976)
Autorun file from Registry key
- rapes.exe (PID: 5364)
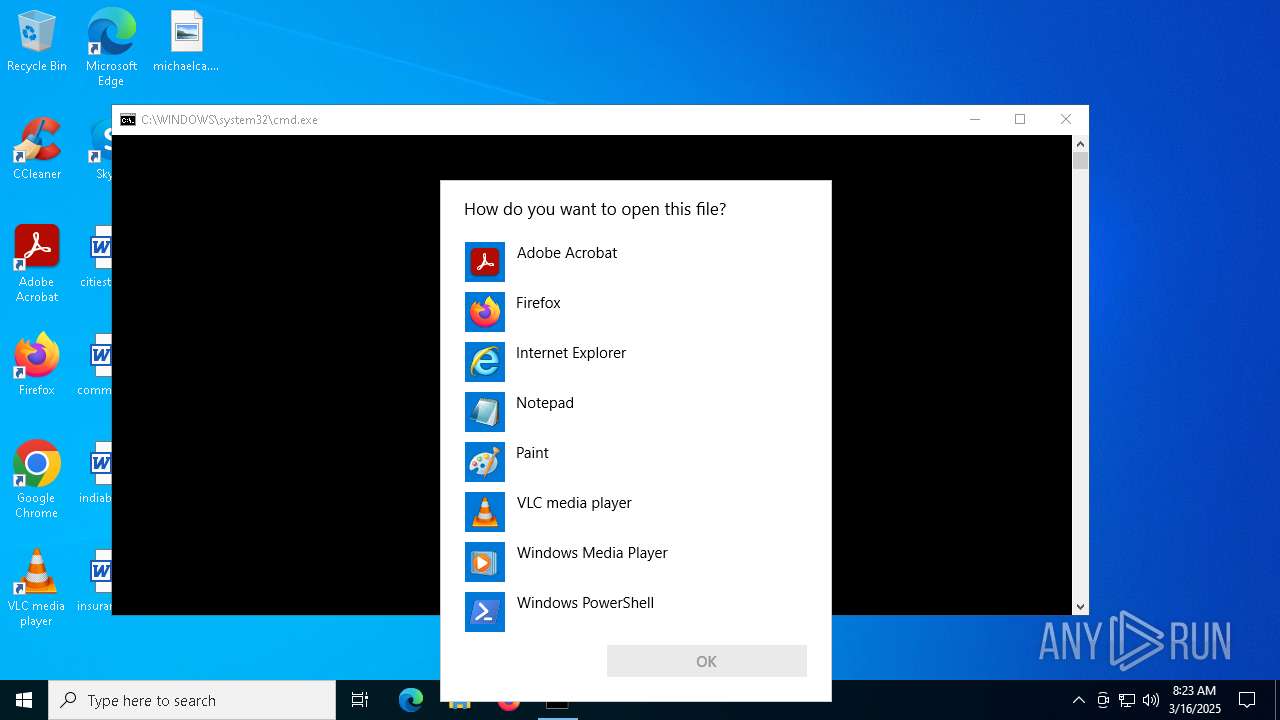
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7824)
- OpenWith.exe (PID: 7312)
- OpenWith.exe (PID: 516)
- OpenWith.exe (PID: 3240)
Manual execution by a user
- 96526116ec.exe (PID: 7904)
- OpenWith.exe (PID: 7824)
- OpenWith.exe (PID: 7312)
- cmd.exe (PID: 7488)
- OpenWith.exe (PID: 516)
- cb68442713.exe (PID: 7832)
- 788a2fc0fb.exe (PID: 6592)
- cd34dbeb8a.exe (PID: 780)
- 588ec43a33.exe (PID: 7908)
- SplitcatTools.exe (PID: 8100)
- OpenWith.exe (PID: 3240)
- OpenWith.exe (PID: 6872)
Autorun file from Task Scheduler
- cmd.exe (PID: 7924)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7488)
Themida protector has been detected
- rapes.exe (PID: 5364)
- 3r19R.exe (PID: 4692)
Creates files in the program directory
- 3r19R.exe (PID: 4692)
- splitcattools.exe (PID: 7484)
- packed.exe (PID: 7448)
Disables trace logs
- powershell.exe (PID: 7552)
- powershell.exe (PID: 8080)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8128)
- powershell.exe (PID: 7760)
The executable file from the user directory is run by the Powershell process
- TempBHPBVJ7N6OBJEASYUZWPJR76R9ZJEE6S.EXE (PID: 7352)
- Temp6KYGR25WAJYDGHNPSPT0SH5OHSIAGU6V.EXE (PID: 7420)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6584)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 2908)
Creates a software uninstall entry
- yPO0L3ehRR.tmp (PID: 2960)
Changes the registry key values via Powershell
- splitcattools.exe (PID: 7484)
- ADFoyxP.exe (PID: 2516)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7260)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7260)
The sample compiled with chinese language support
- rsfff01fff.exe (PID: 7588)
- irestore.exe (PID: 1276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(5364) rapes.exe
C2176.113.115.6
URLhttp://176.113.115.6/Ni9kiput/index.php
Version5.21
Options
Drop directorybb556cff4a
Drop namerapes.exe
Strings (125)360TotalSecurity
rundll32.exe
Doctor Web
ProductName
AVAST Software
ProgramData\
sd:
/Plugins/
?scr=1
bi:
2016
rundll32
/Ni9kiput/index.php
-executionpolicy remotesigned -File "
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
.jpg
+++
%USERPROFILE%
wb
os:
00000422
&unit=
&& Exit"
ar:
Main
Kaspersky Lab
"taskkill /f /im "
ESET
Programs
/k
CurrentBuild
"
Content-Type: application/octet-stream
Bitdefender
S-%lu-
SYSTEM\ControlSet001\Services\BasicDisplay\Video
------
Content-Type: application/x-www-form-urlencoded
https://
og:
SOFTWARE\Microsoft\Windows NT\CurrentVersion
" && timeout 1 && del
WinDefender
ps1
r=
GetNativeSystemInfo
Rem
<d>
Norton
shutdown -s -t 0
Avira
GET
Powershell.exe
pc:
#
cred.dll|clip.dll|
00000423
ComputerName
rapes.exe
clip.dll
0123456789
cred.dll
http://
AVG
Content-Disposition: form-data; name="data"; filename="
Comodo
msi
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
-unicode-
DefaultSettings.YResolution
un:
bb556cff4a
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
vs:
2022
176.113.115.6
abcdefghijklmnopqrstuvwxyz0123456789-_
--
:::
dm:
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
|
cmd
av:
00000419
e1
/quiet
0000043f
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
2019
\0000
5.21
&&
e3
zip
DefaultSettings.XResolution
=
<c>
d1
cmd /C RMDIR /s/q
exe
-%lu
VideoID
%-lu
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
shell32.dll
Panda Security
2025
------
Startup
POST
"
Content-Type: multipart/form-data; boundary=----
id:
" && ren
\
lv:
Keyboard Layout\Preload
dll
rb
st=s
Sophos
e2
random
\App
kernel32.dll
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:24 22:49:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 5815808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
584
Monitored processes
457
Malicious processes
50
Suspicious processes
33
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\AppData\Local\Temp\10232530101\788a2fc0fb.exe" | C:\Users\admin\AppData\Local\Temp\10232530101\788a2fc0fb.exe | rapes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 208 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2116 -parentBuildID 20240213221259 -prefsHandle 2108 -prefMapHandle 2104 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9248a0c9-9e5e-4a3a-af93-07d99929e06d} 6656 "\\.\pipe\gecko-crash-server-pipe.6656" 2ec4be81d10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 208 | taskkill /F /IM brave.exe /T | C:\Windows\SysWOW64\taskkill.exe | — | cd34dbeb8a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2080 -parentBuildID 20240213221259 -prefsHandle 2072 -prefMapHandle 2068 -prefsLen 31088 -prefMapSize 244635 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d8627bd1-1824-482d-8bbb-a1216a2d2b93} 7576 "\\.\pipe\gecko-crash-server-pipe.7576" 1d3eb881d10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 516 | powershell -command "-join ((48..57) + (65..90) + (97..122) | Get-Random -Count 5 | ForEach-Object {[char]$_})" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\WINDOWS\System32\OpenWith.exe" ""mshta \"" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2064 -parentBuildID 20240213221259 -prefsHandle 2056 -prefMapHandle 2052 -prefsLen 31088 -prefMapSize 244635 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b99a879a-737b-4827-8101-bd134837d648} 1600 "\\.\pipe\gecko-crash-server-pipe.1600" 21732383910 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
202 574
Read events
202 495
Write events
79
Delete events
0
Modification events
| (PID) Process: | (5364) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5364) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5364) rapes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4692) 3r19R.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4692) 3r19R.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4692) 3r19R.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
125
Suspicious files
957
Text files
171
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10f677.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10f687.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10f687.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10f687.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10f687.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10f687.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
187
TCP/UDP connections
130
DNS requests
124
Threats
155
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.73.234.102:443 | https://steamcommunity.com/profiles/76561199822375128 | NL | html | 25.9 Kb | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4692 | 3r19R.exe | POST | 200 | 45.93.20.28:80 | http://45.93.20.28/85a1cacf11314eb8.php | RU | text | 180 b | malicious |
4692 | 3r19R.exe | GET | 200 | 45.93.20.28:80 | http://45.93.20.28/ | RU | — | — | malicious |
4692 | 3r19R.exe | POST | 200 | 45.93.20.28:80 | http://45.93.20.28/85a1cacf11314eb8.php | RU | text | 6.95 Kb | malicious |
4692 | 3r19R.exe | POST | 200 | 45.93.20.28:80 | http://45.93.20.28/85a1cacf11314eb8.php | RU | text | 1.98 Kb | malicious |
4692 | 3r19R.exe | POST | 200 | 45.93.20.28:80 | http://45.93.20.28/85a1cacf11314eb8.php | RU | text | 108 b | malicious |
— | — | GET | 200 | 142.250.186.163:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=122 | US | compressed | 96.1 Kb | whitelisted |
4692 | 3r19R.exe | GET | 200 | 45.93.20.28:80 | http://45.93.20.28/c66c0eade263c9a8/sqlite3.dll | RU | executable | 1.06 Mb | malicious |
5364 | rapes.exe | POST | 200 | 176.113.115.6:80 | http://176.113.115.6/Ni9kiput/index.php | RU | text | 1.69 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5204 | 2x8387.exe | 104.73.234.102:443 | steamcommunity.com | AKAMAI-AS | DE | whitelisted |
5364 | rapes.exe | 176.113.115.6:80 | — | Red Bytes LLC | RU | malicious |
4692 | 3r19R.exe | 45.93.20.28:80 | — | Chang Way Technologies Co. Limited | RU | malicious |
5364 | rapes.exe | 176.113.115.7:80 | — | Red Bytes LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
citydisco.bet |
| malicious |
crosshairc.life |
| malicious |
mrodularmall.top |
| malicious |
jowinjoinery.icu |
| malicious |
legenassedk.top |
| malicious |
htardwarehu.icu |
| malicious |
cjlaspcorne.icu |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (jowinjoinery .icu) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (mrodularmall .top) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (bugildbett .top) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (htardwarehu .icu) |
5364 | rapes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 29 |
5364 | rapes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
4692 | 3r19R.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 4 |
4692 | 3r19R.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Stealc HTTP POST Request |