| URL: | tr.ee/BceCca |
| Full analysis: | https://app.any.run/tasks/44e790c7-063f-4cc2-8fb2-c1c137ec53fa |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
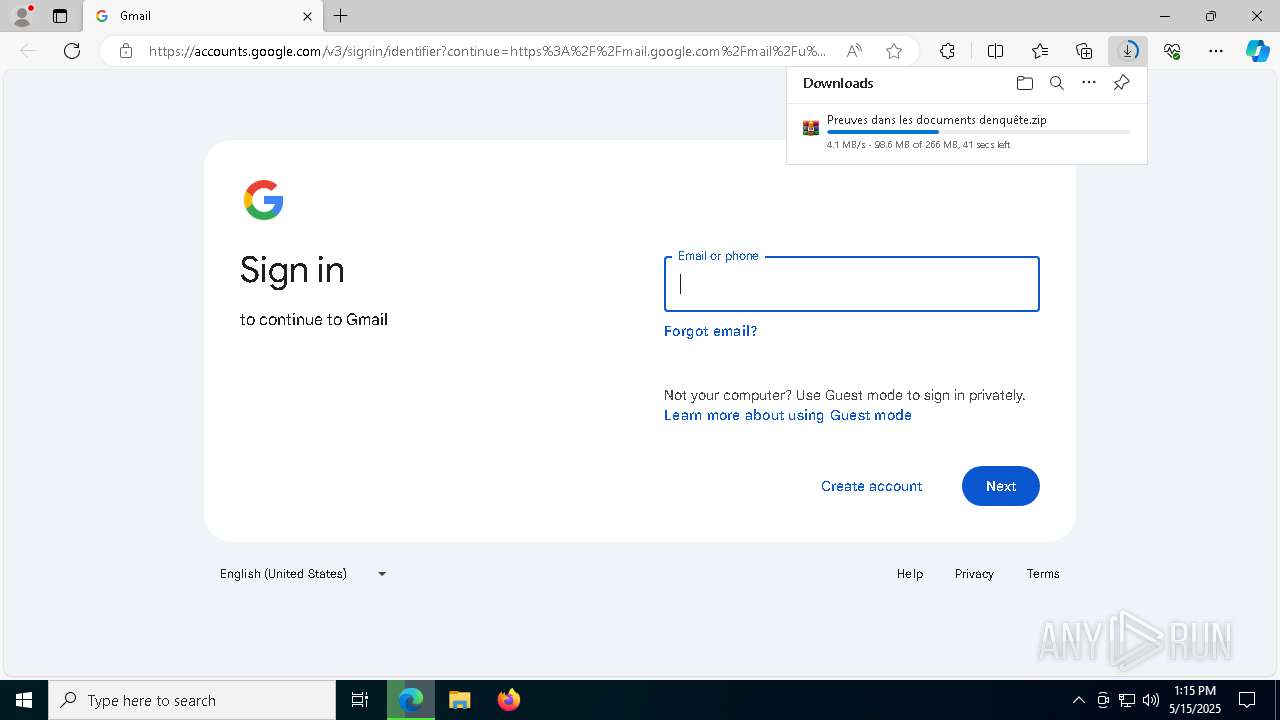
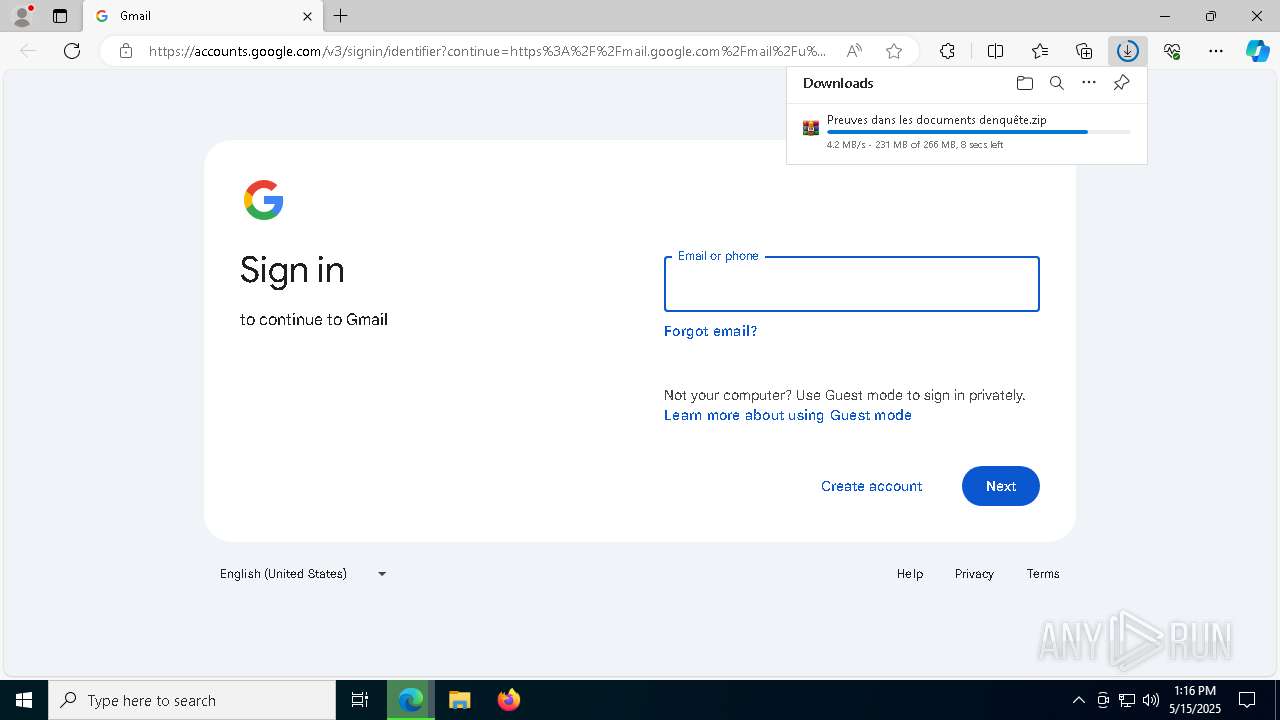
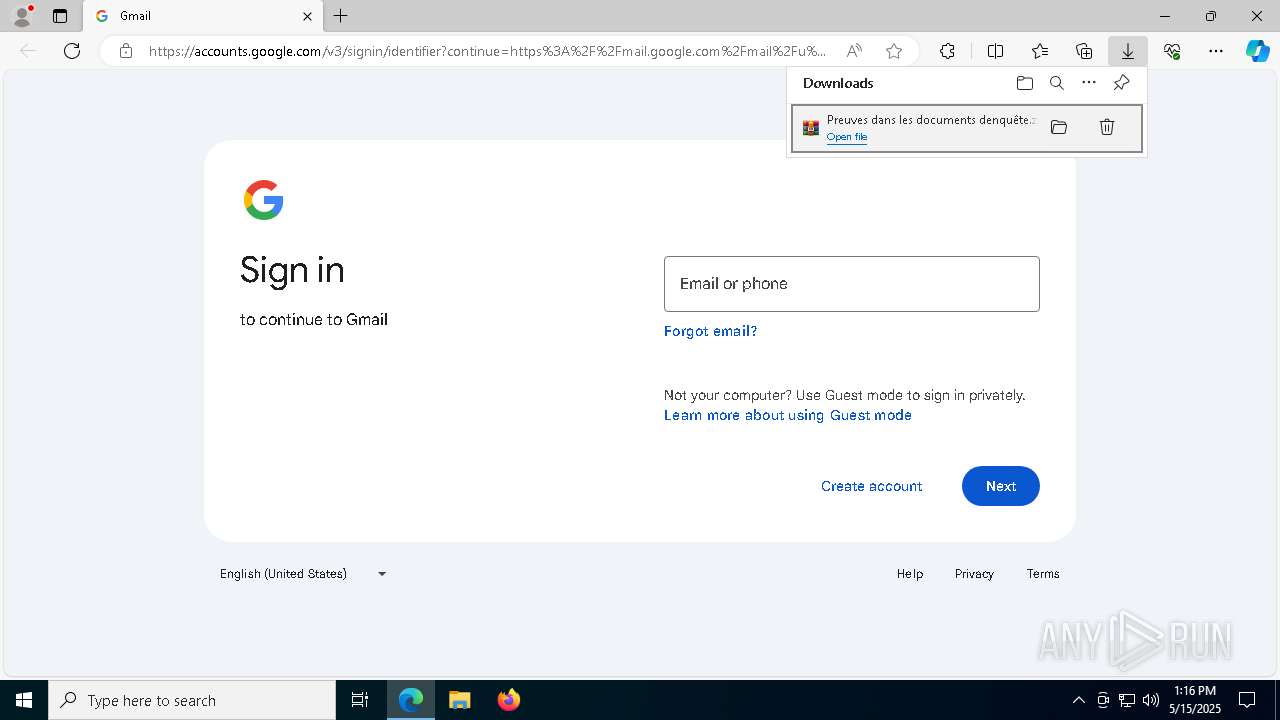
| Analysis date: | May 15, 2025, 13:15:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E57B322E83BDB9F35FB7EA98858C7ABF |
| SHA1: | 3BE8B318127693F62D174F02BD58FB9E0260BF57 |
| SHA256: | E7AE30A307C7DA180FA3E5B18211F27837AD9140F397F8EB328CF7B1E3E3C0EB |
| SSDEEP: | 3:NQS:T |
MALICIOUS
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 1128)
- svchost.exe (PID: 4304)
SUSPICIOUS
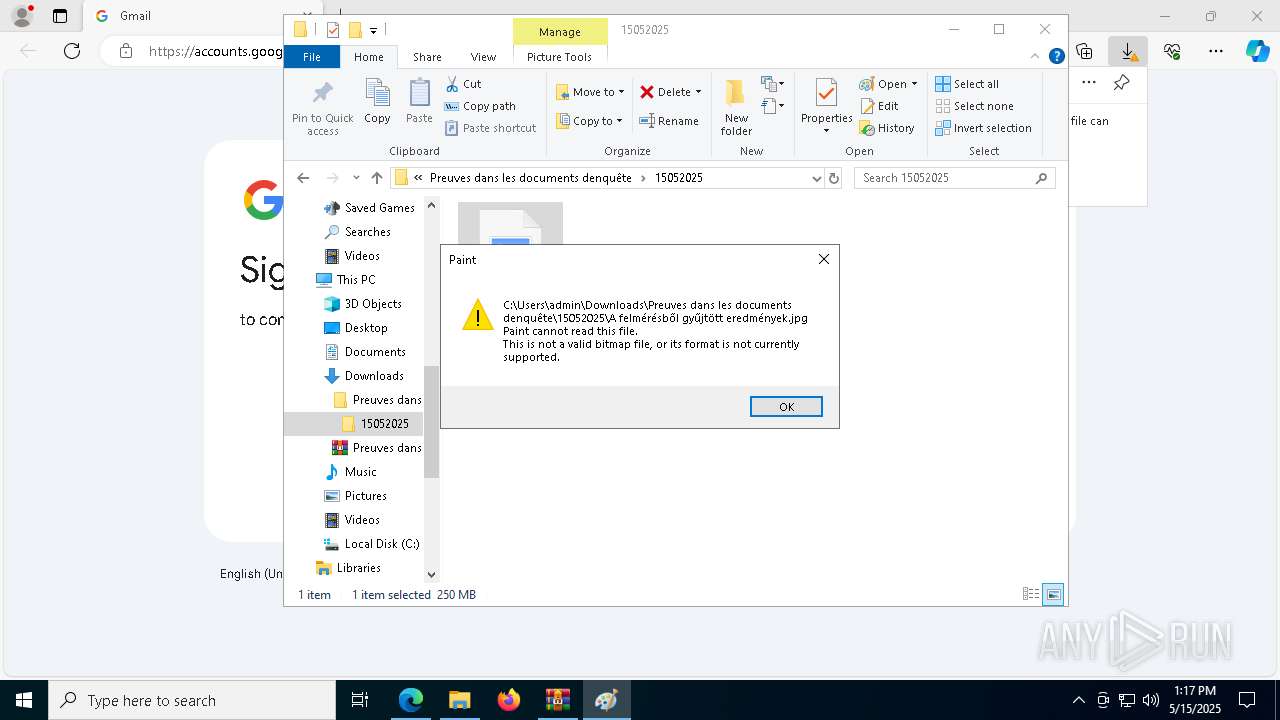
There is functionality for taking screenshot (YARA)
- Preuves dans les documents d'enquête.exe (PID: 6456)
- Preuves dans les documents d'enquête.exe (PID: 7724)
Application launched itself
- Preuves dans les documents d'enquête.exe (PID: 6456)
- Preuves dans les documents d'enquête.exe (PID: 7724)
Executes application which crashes
- Preuves dans les documents d'enquête.exe (PID: 8032)
- Preuves dans les documents d'enquête.exe (PID: 6816)
Connects to unusual port
- svchost.exe (PID: 5084)
- svchost.exe (PID: 1128)
- svchost.exe (PID: 4304)
- svchost.exe (PID: 5180)
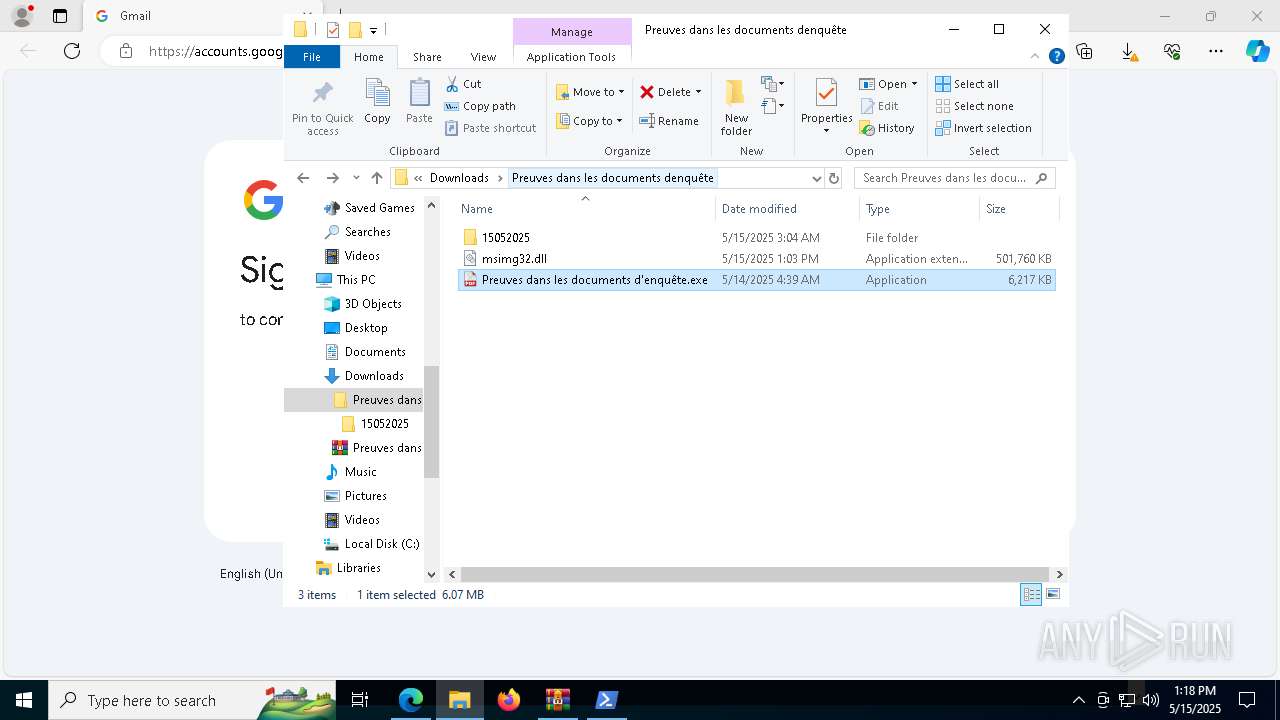
Executable content was dropped or overwritten
- wmpnscfg.exe (PID: 8516)
- svchost.exe (PID: 1128)
- svchost.exe (PID: 4304)
INFO
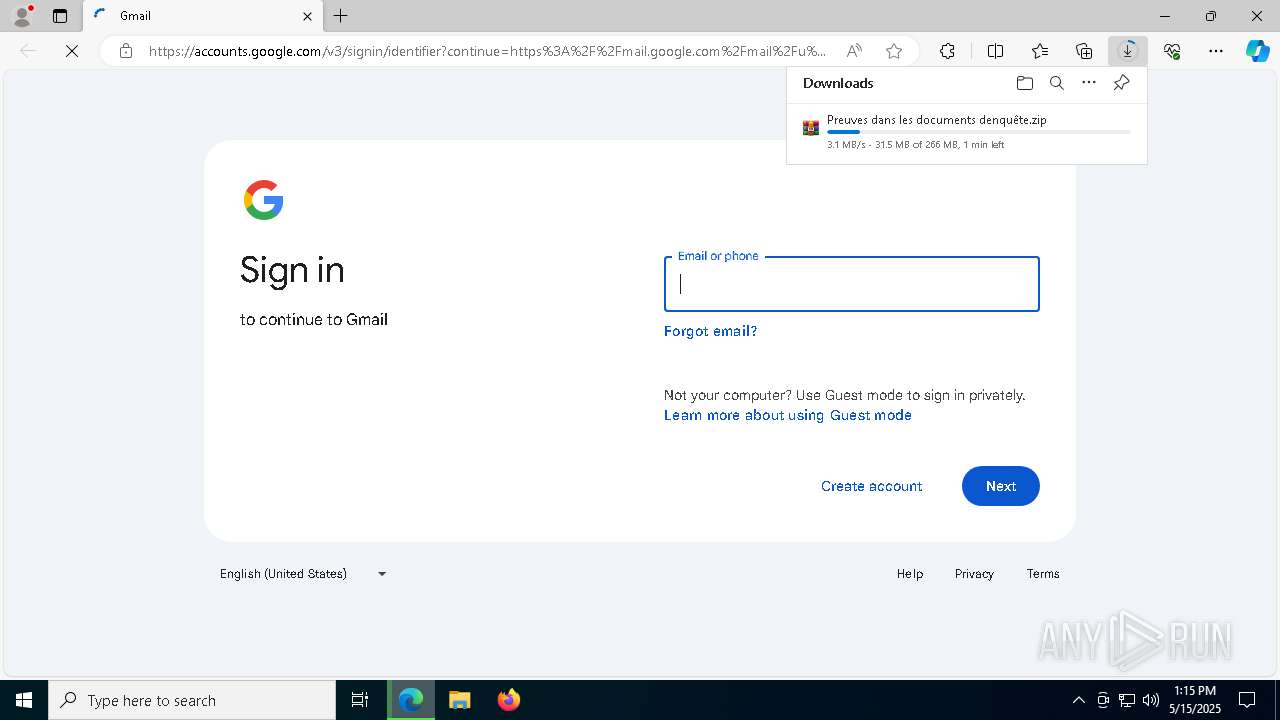
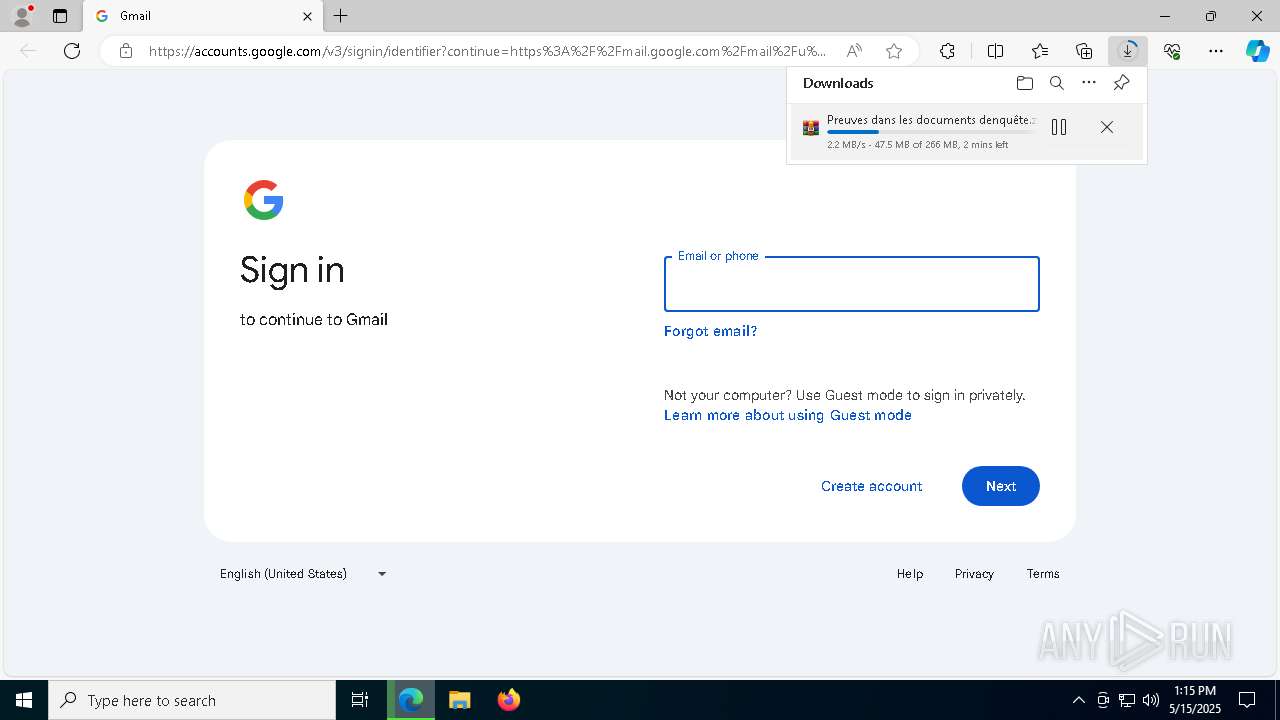
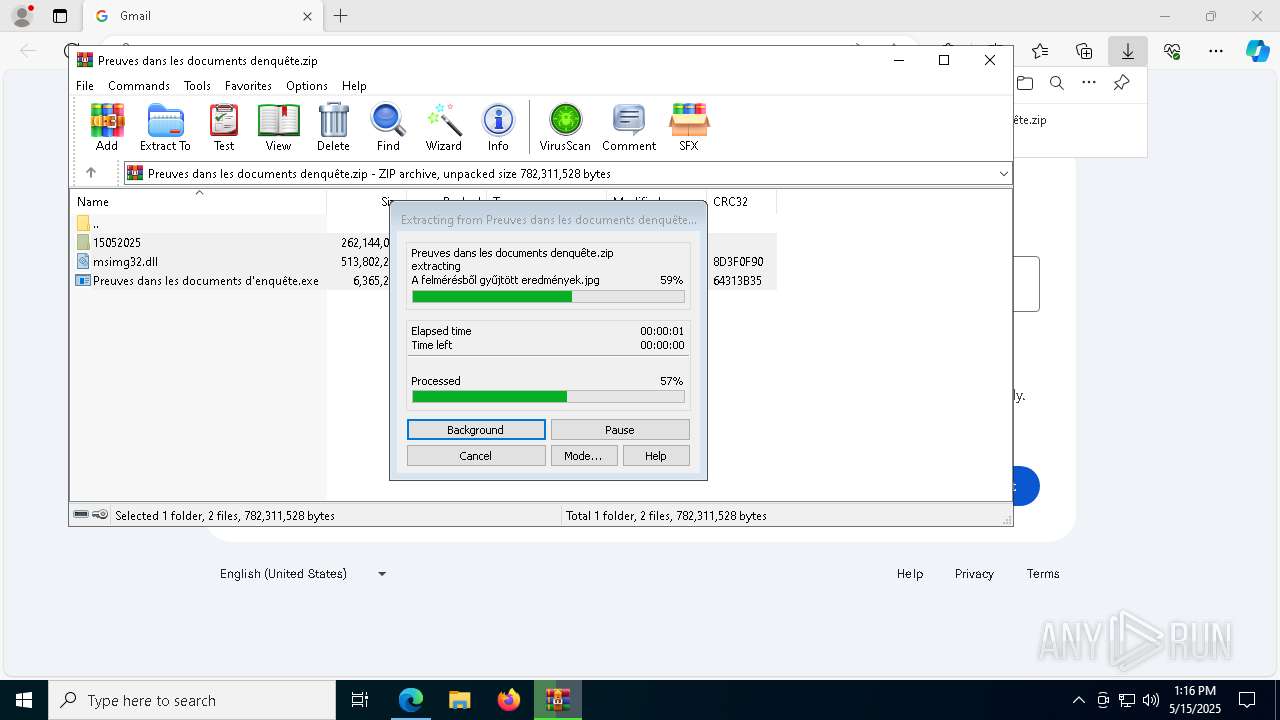
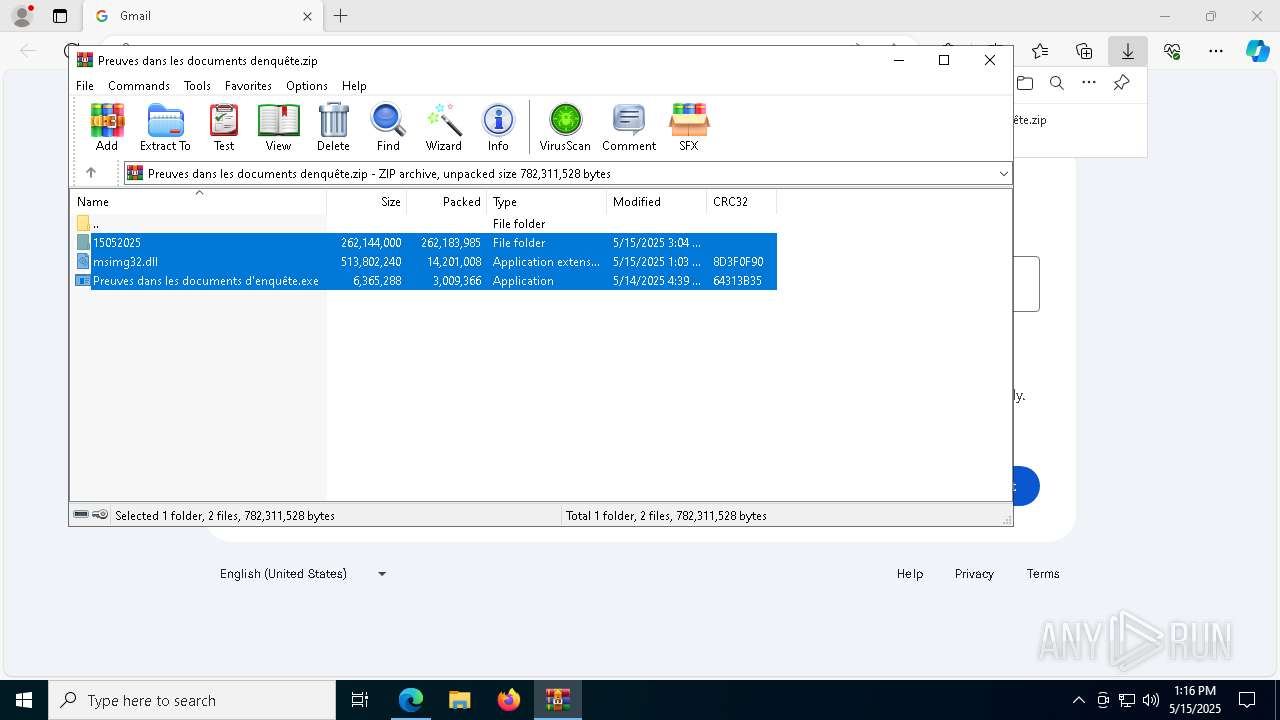
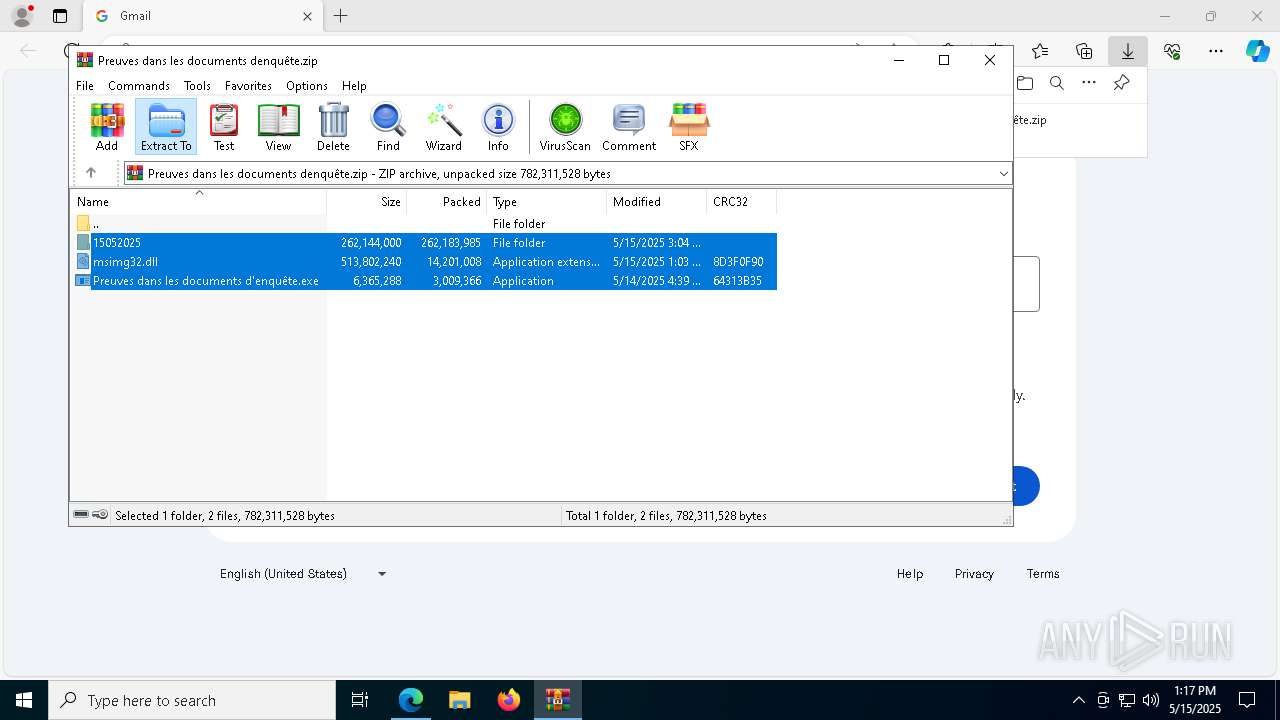
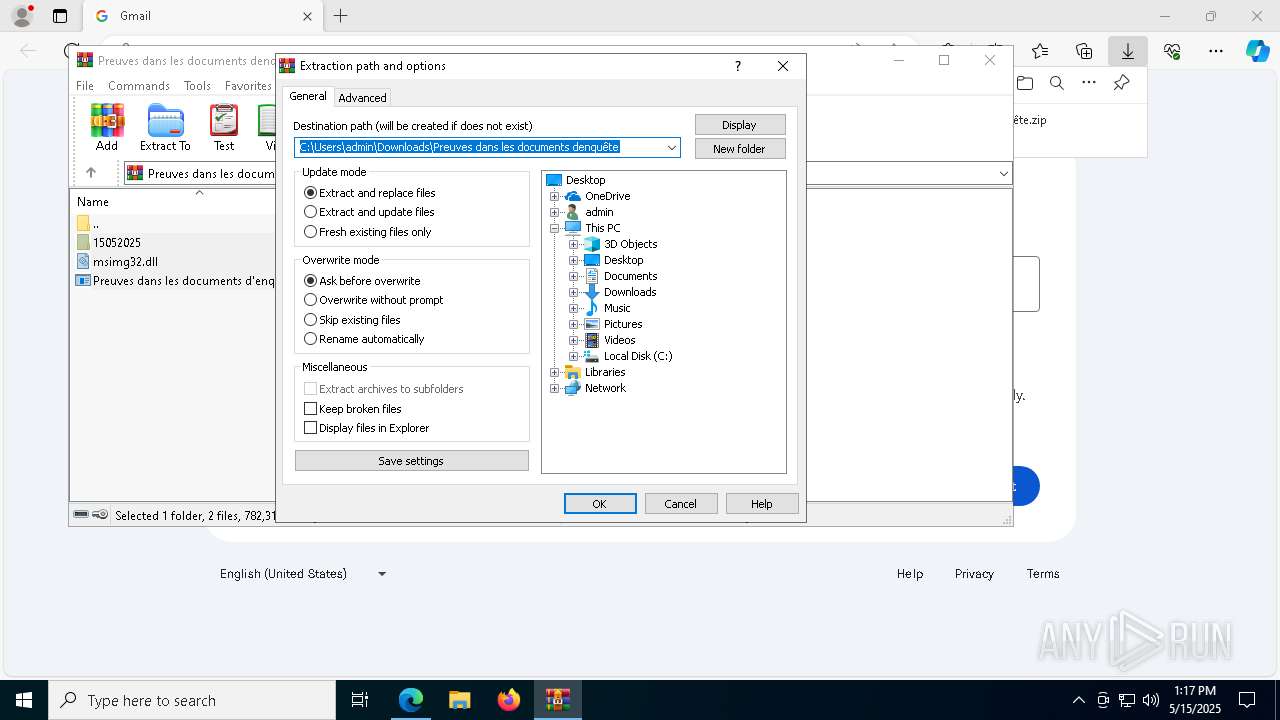
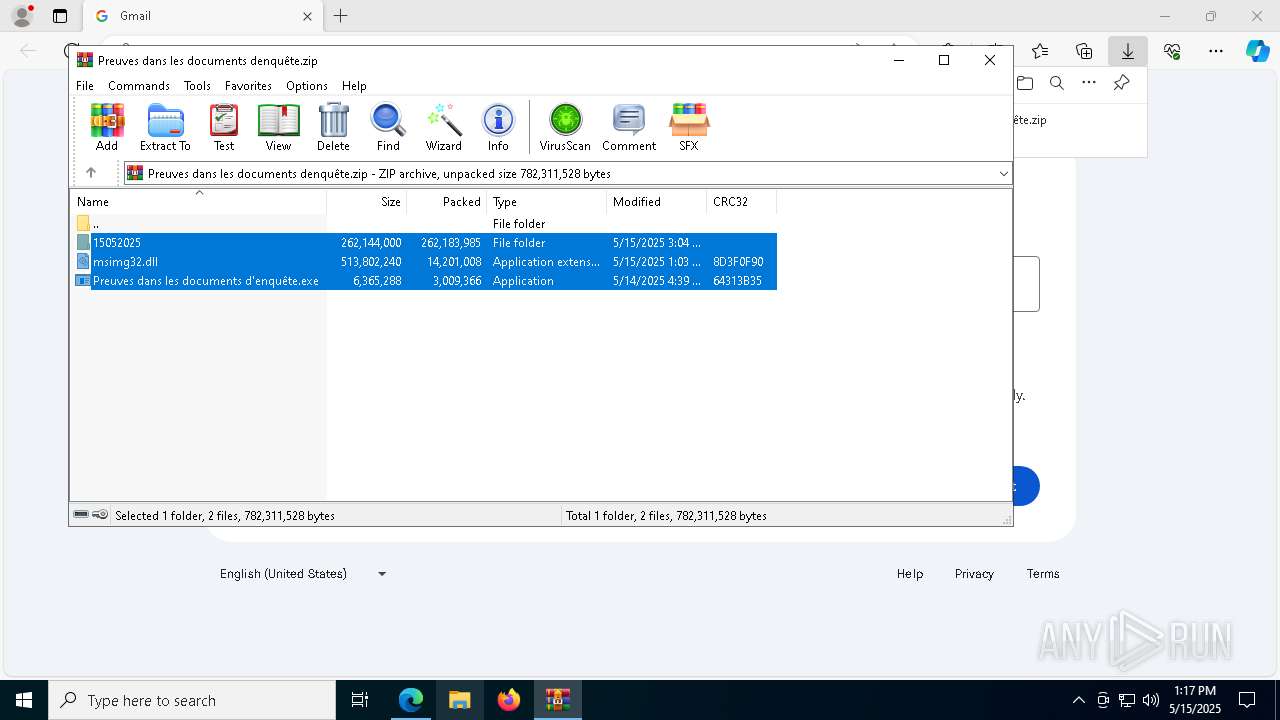
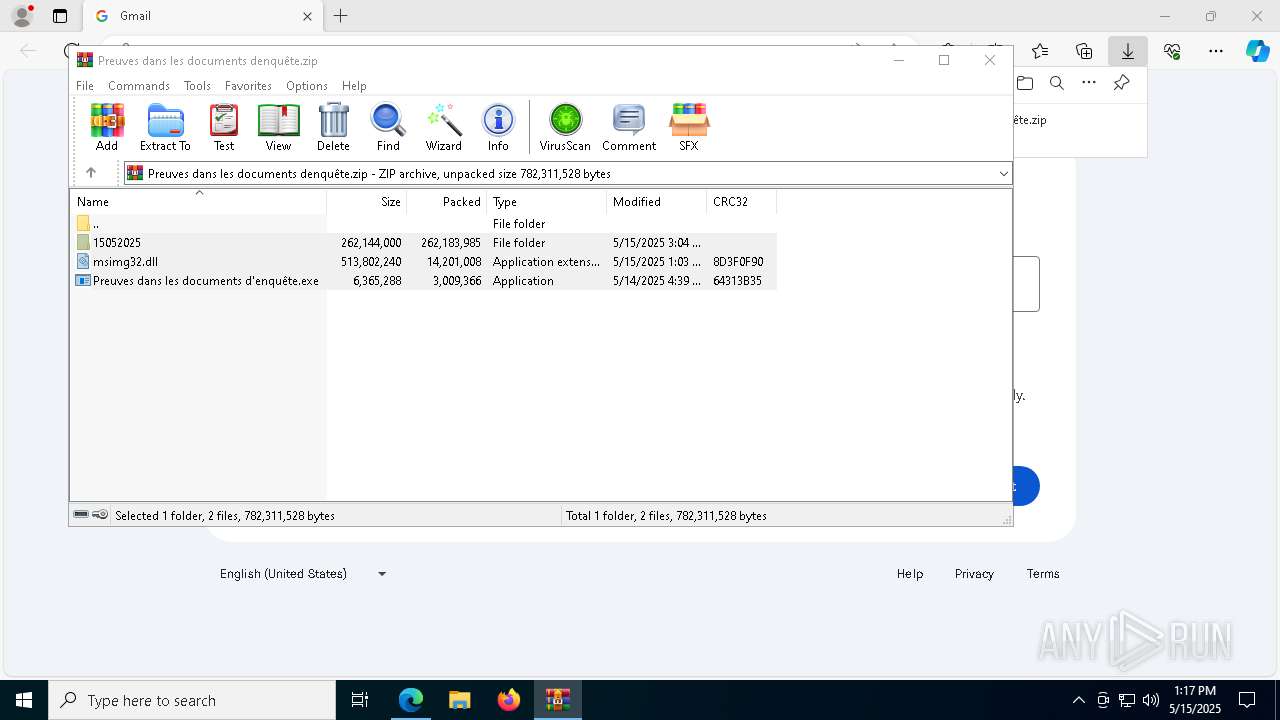
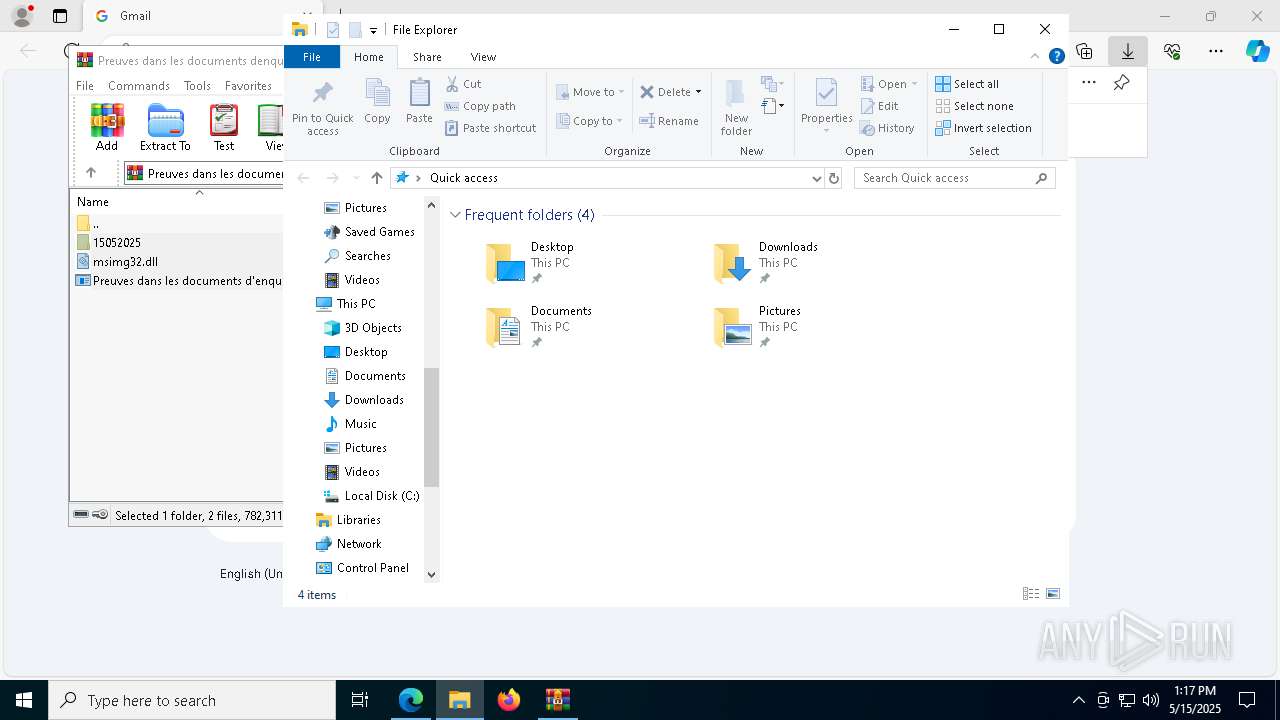
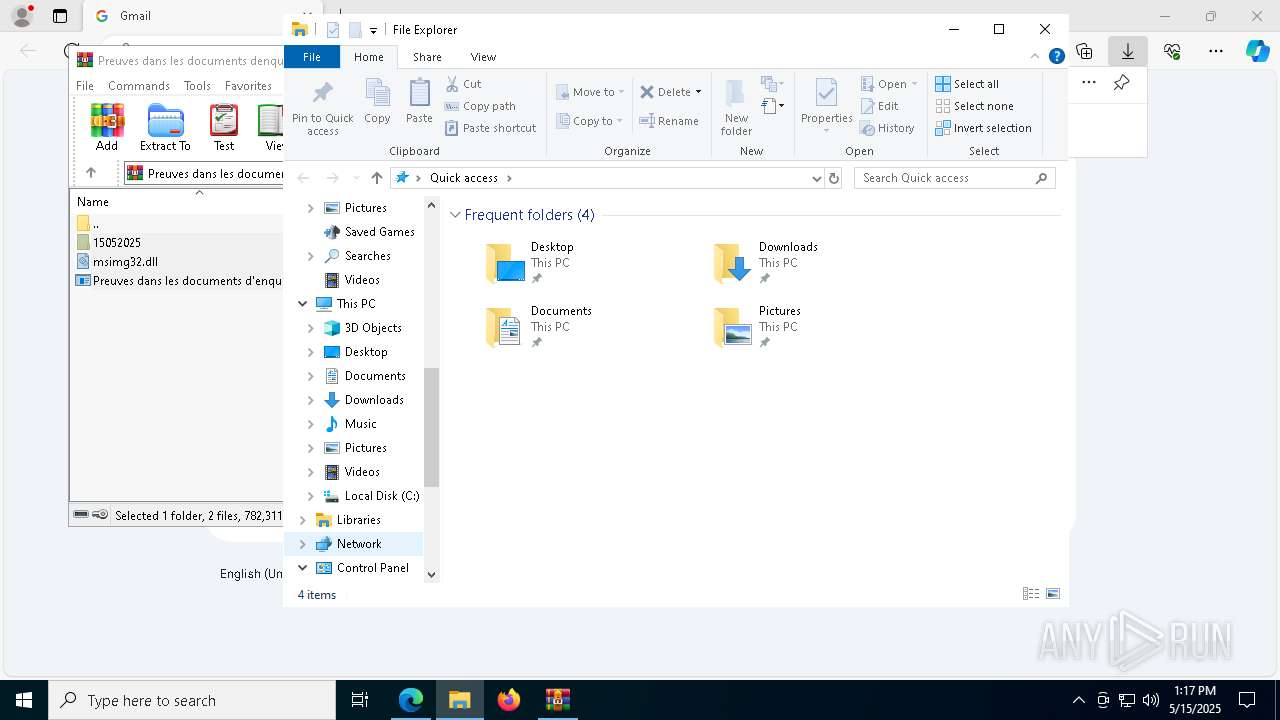
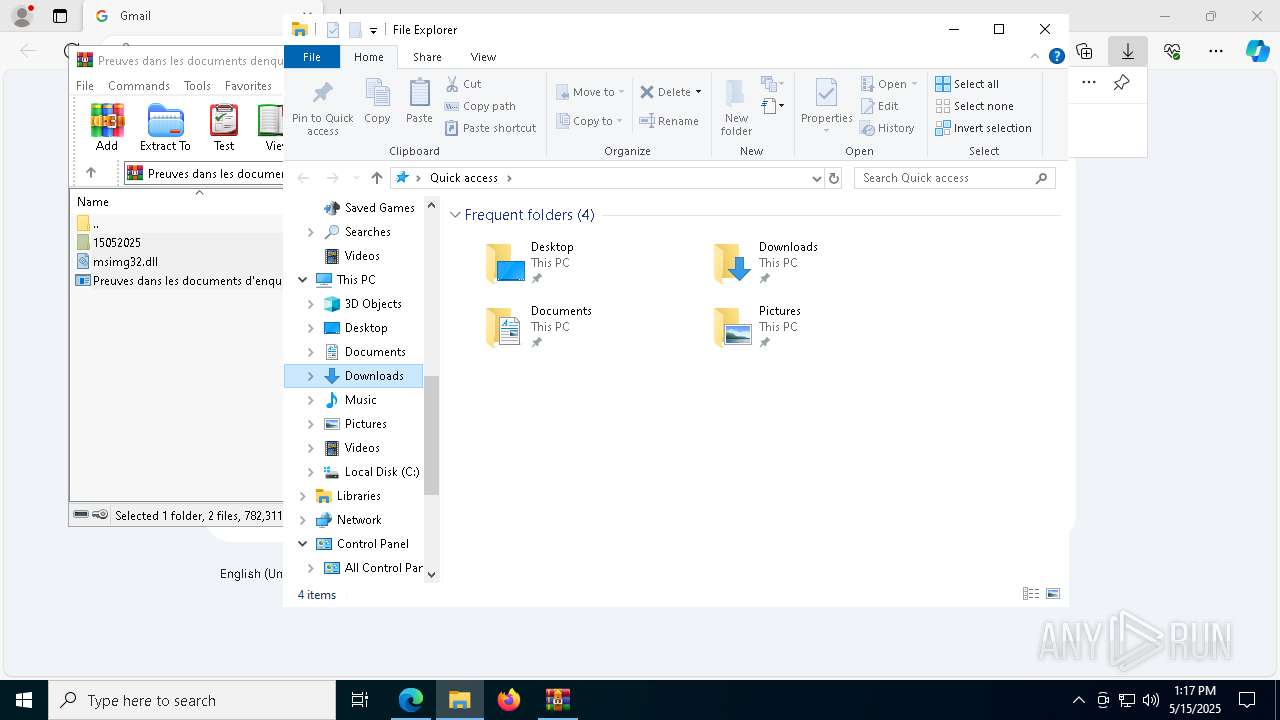
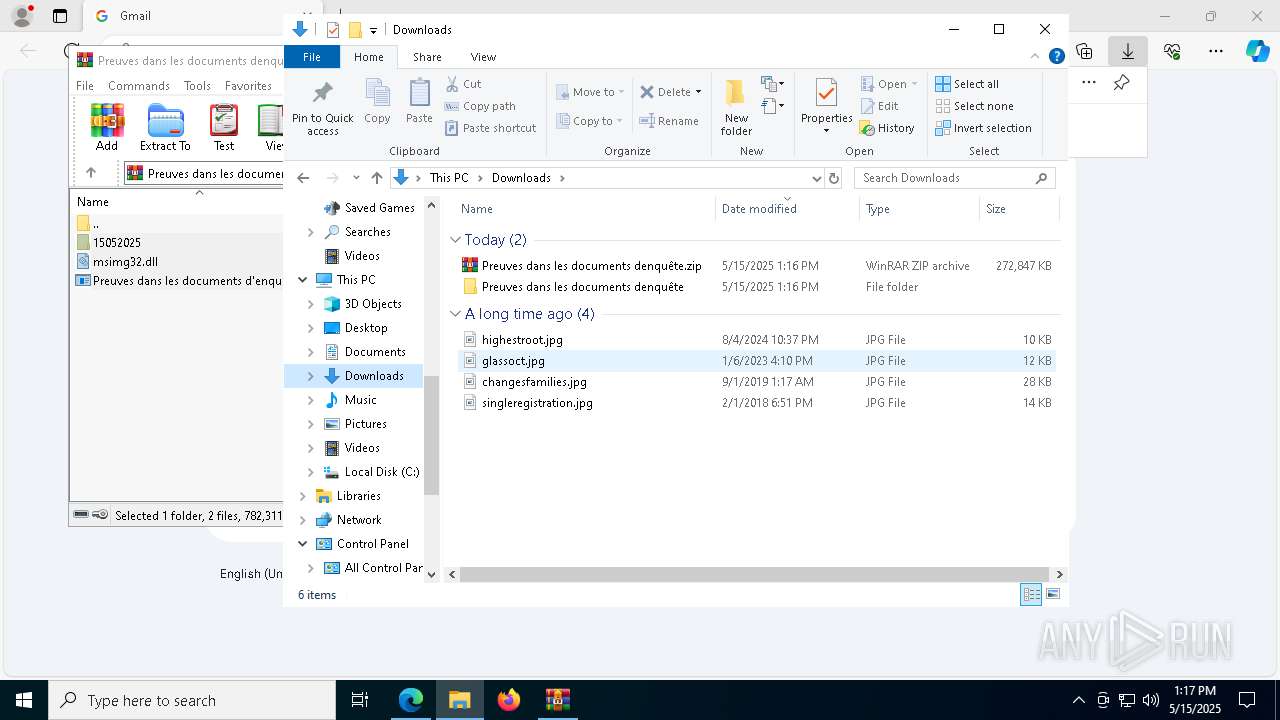
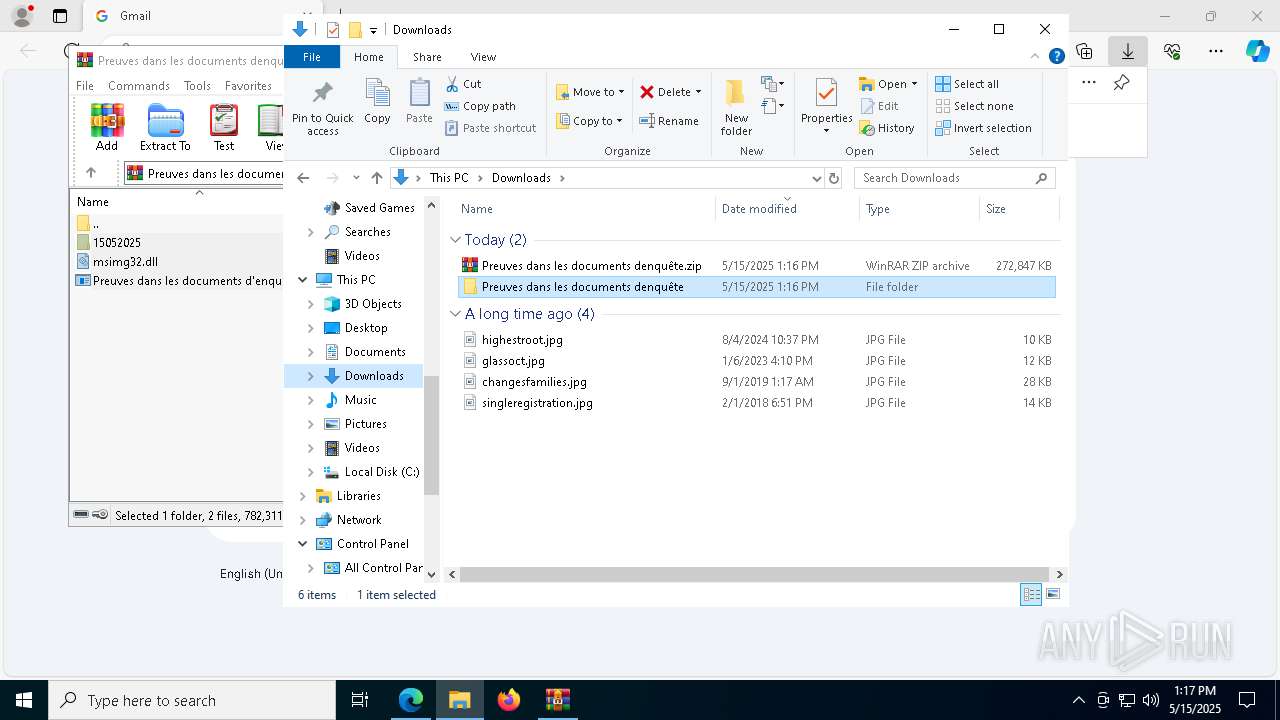
Executable content was dropped or overwritten
- WinRAR.exe (PID: 872)
- msedge.exe (PID: 8144)
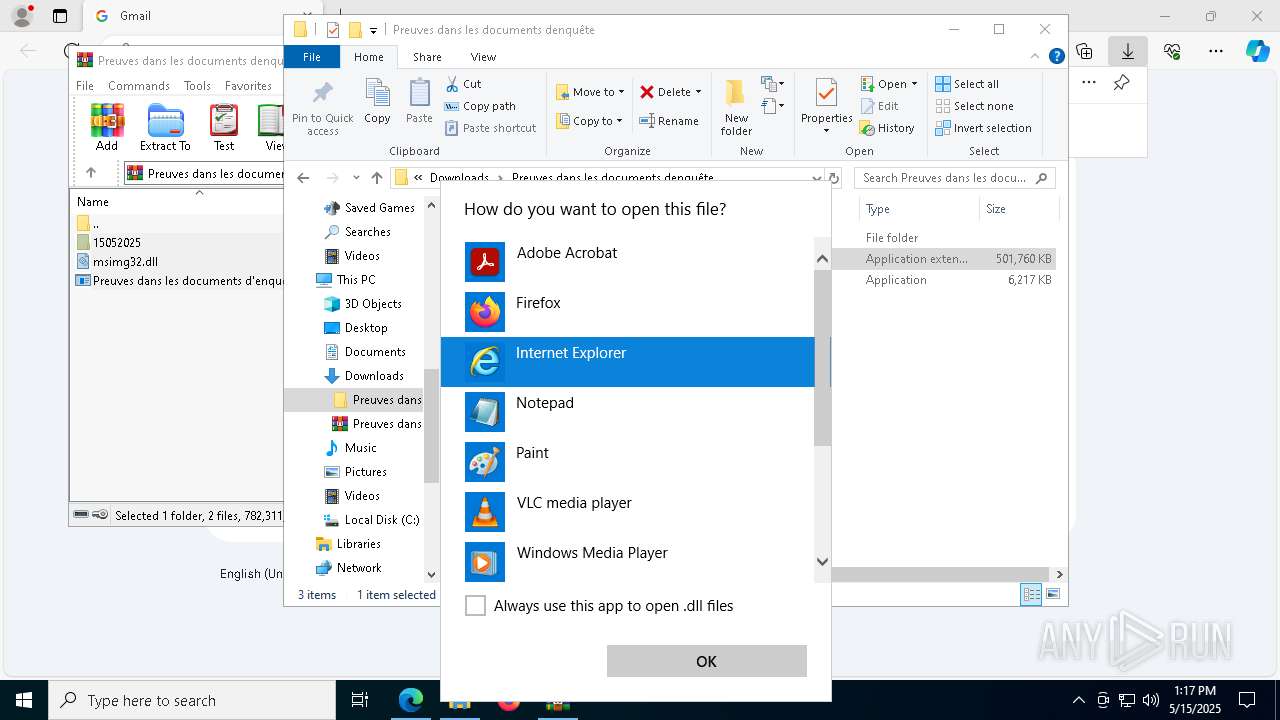
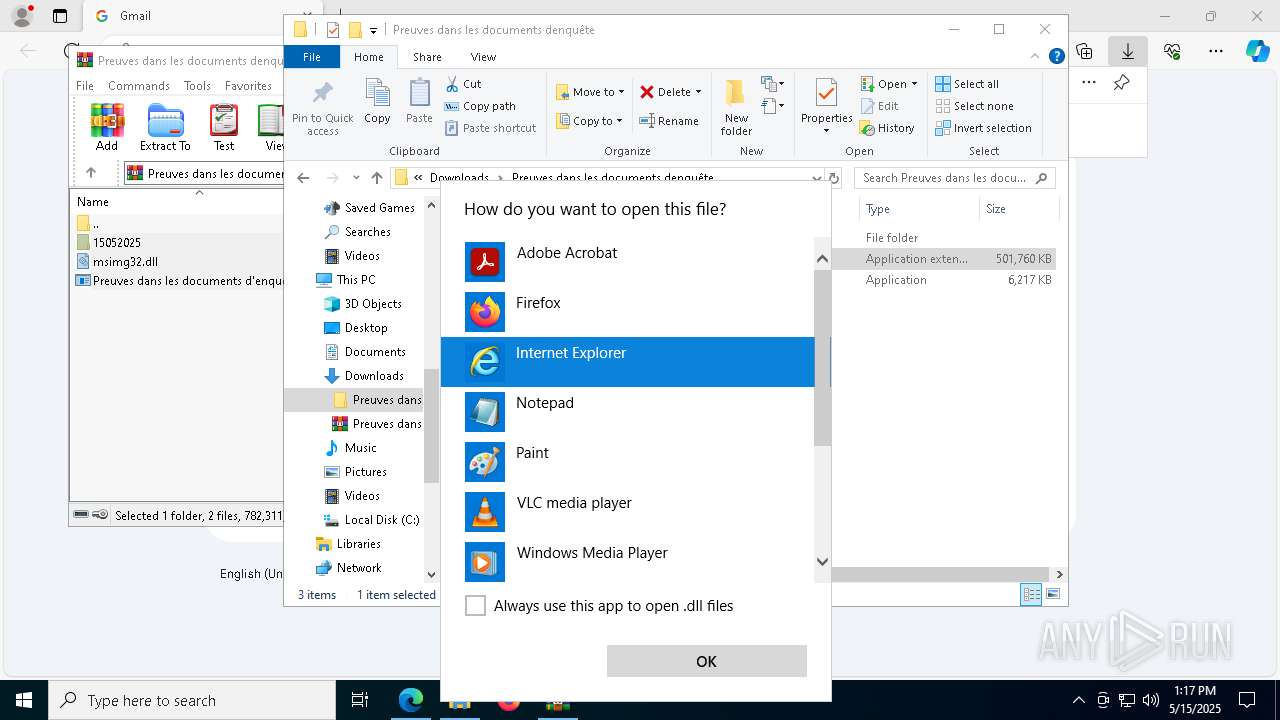
Reads Microsoft Office registry keys
- msedge.exe (PID: 1276)
- OpenWith.exe (PID: 8012)
Reads Environment values
- identity_helper.exe (PID: 7644)
Application launched itself
- msedge.exe (PID: 1276)
- msedge.exe (PID: 7800)
- chrome.exe (PID: 6972)
- msedge.exe (PID: 7208)
- chrome.exe (PID: 8860)
Reads the computer name
- identity_helper.exe (PID: 7644)
Checks supported languages
- identity_helper.exe (PID: 7644)
- Preuves dans les documents d'enquête.exe (PID: 6456)
Reads the software policy settings
- slui.exe (PID: 8040)
- slui.exe (PID: 6584)
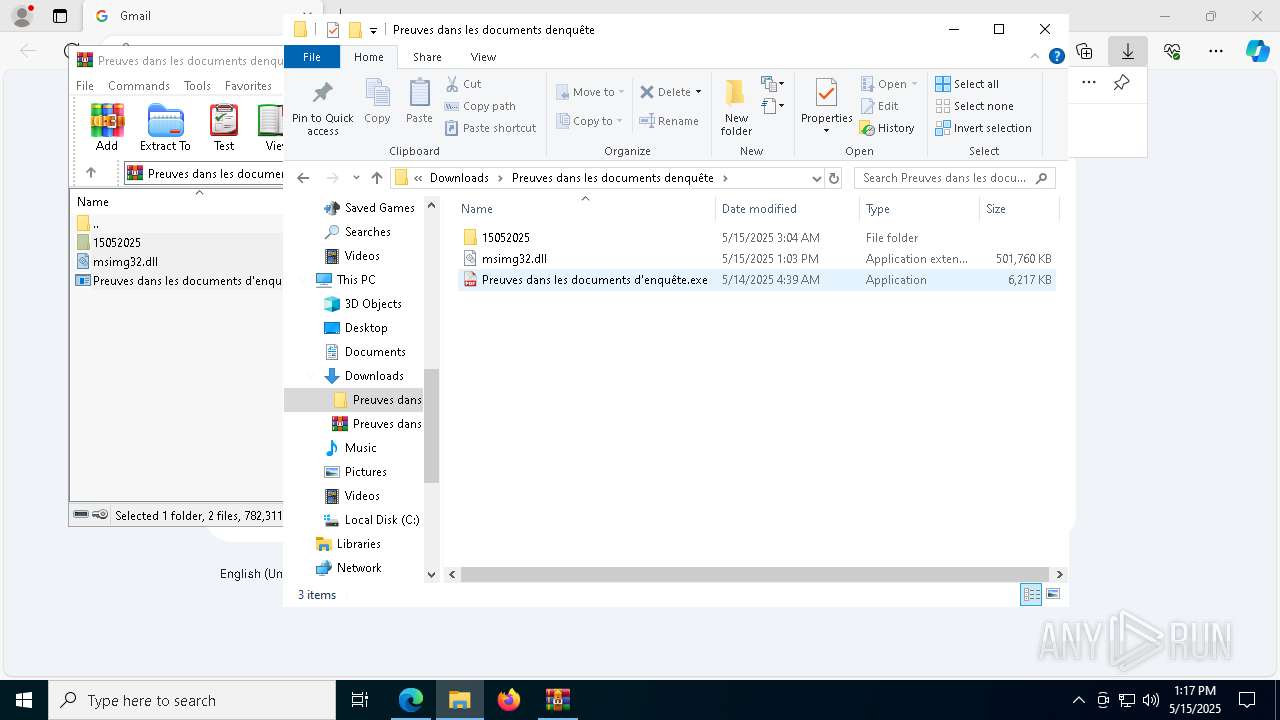
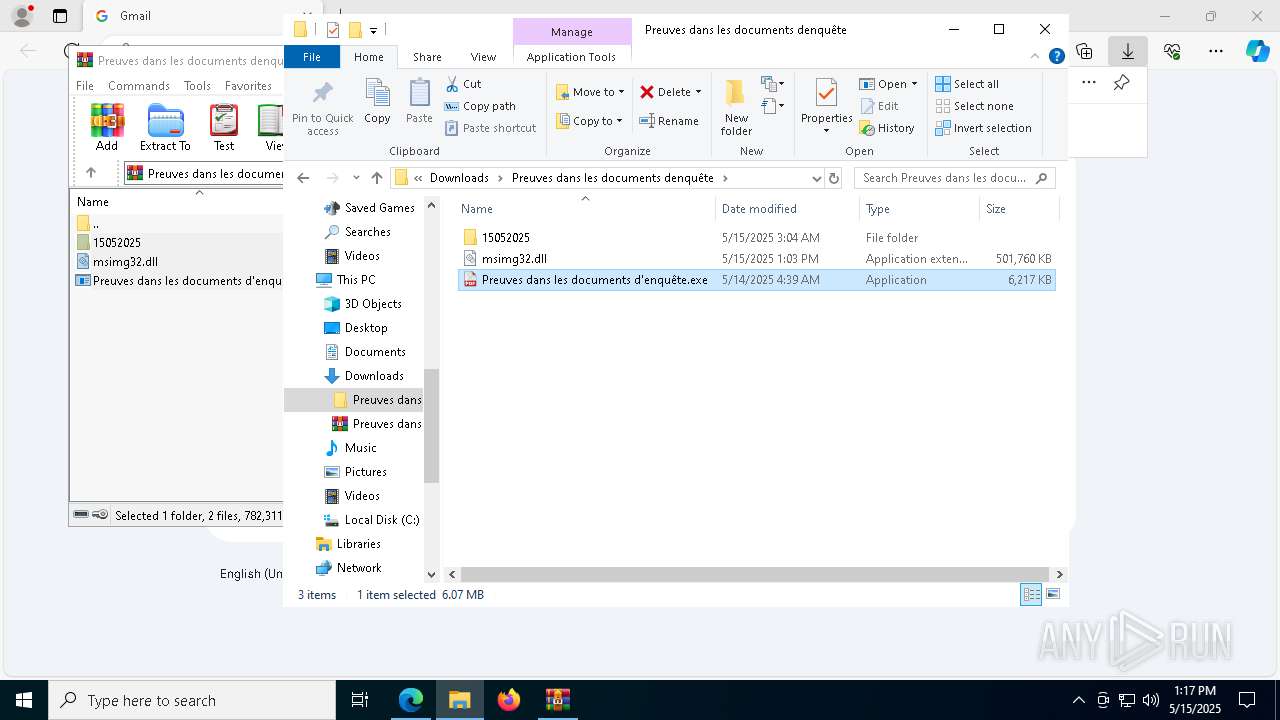
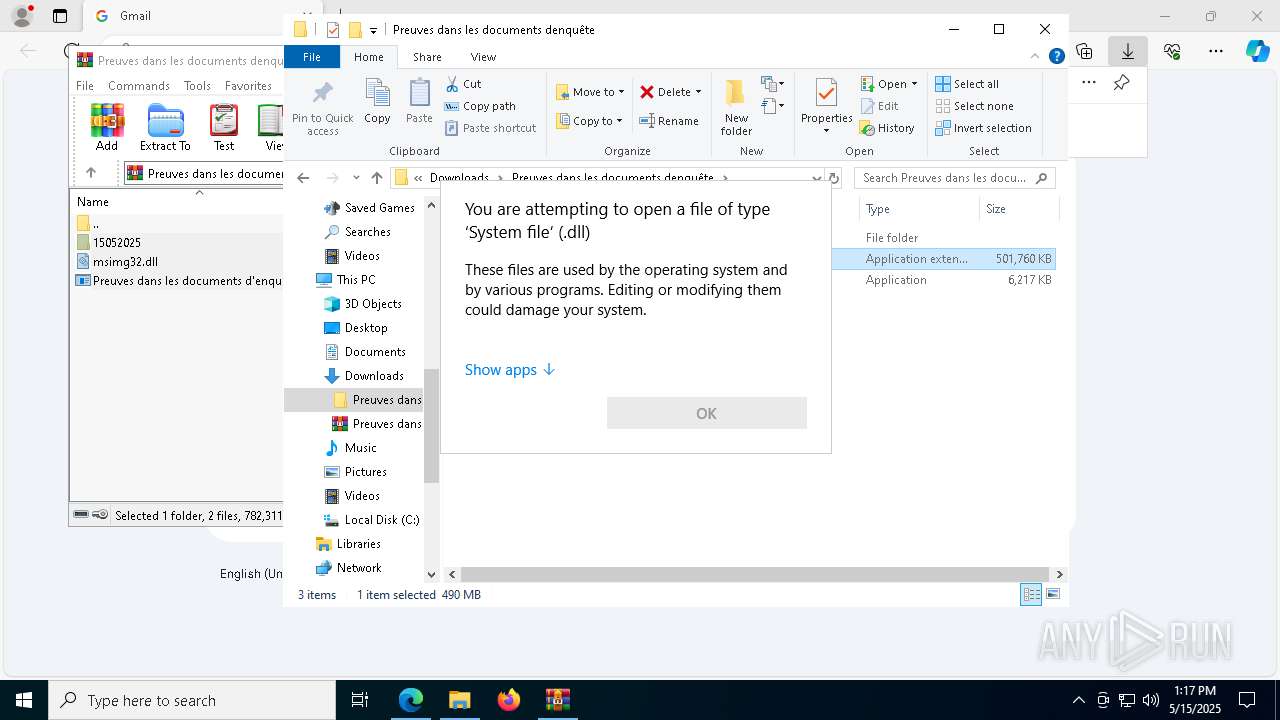
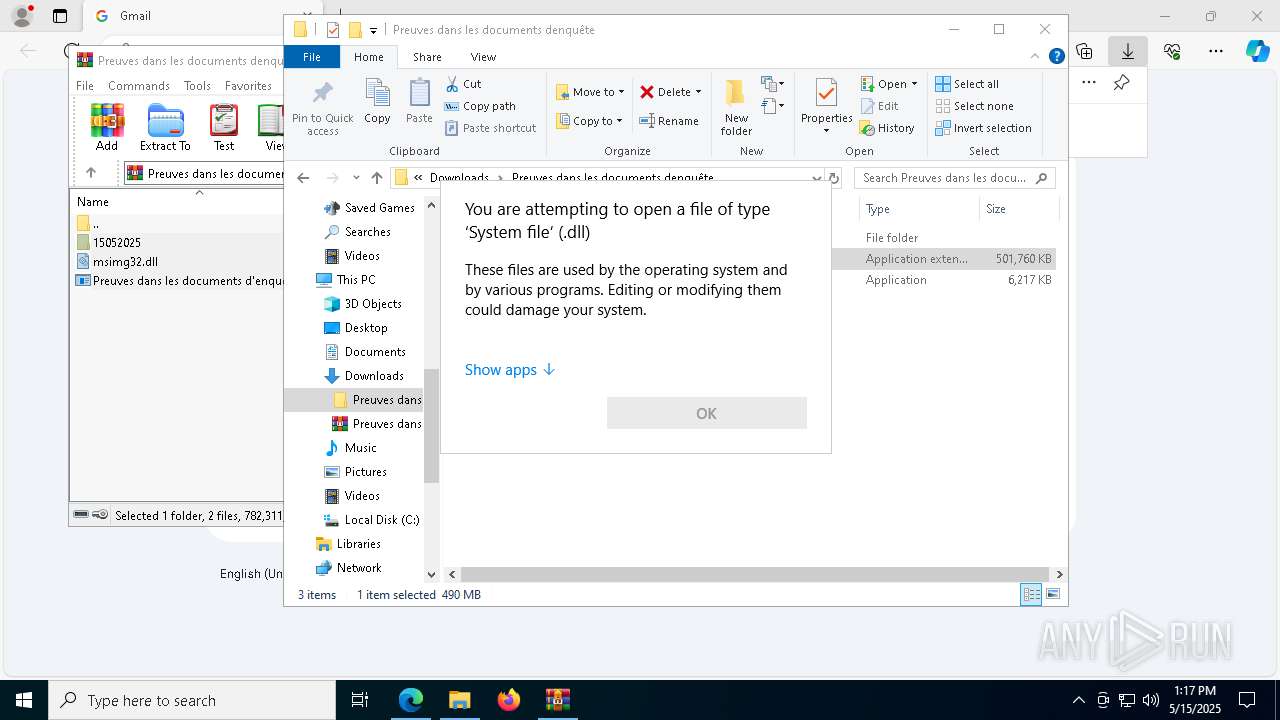
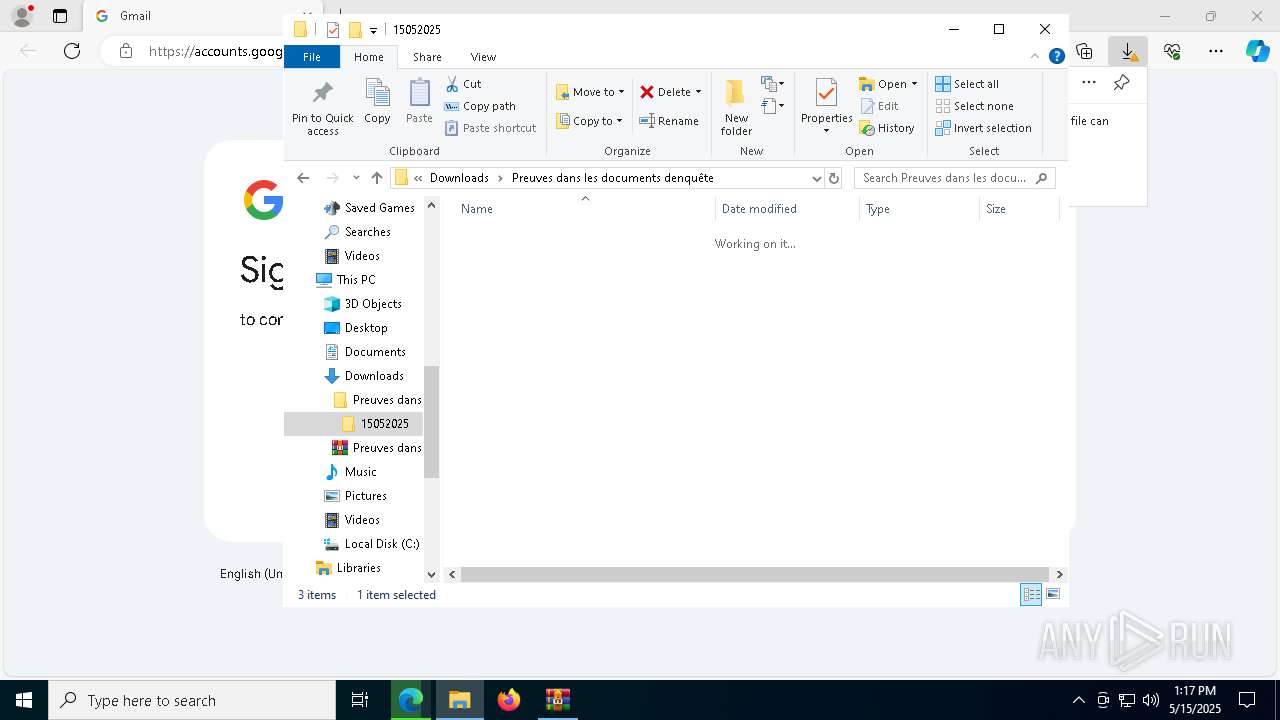
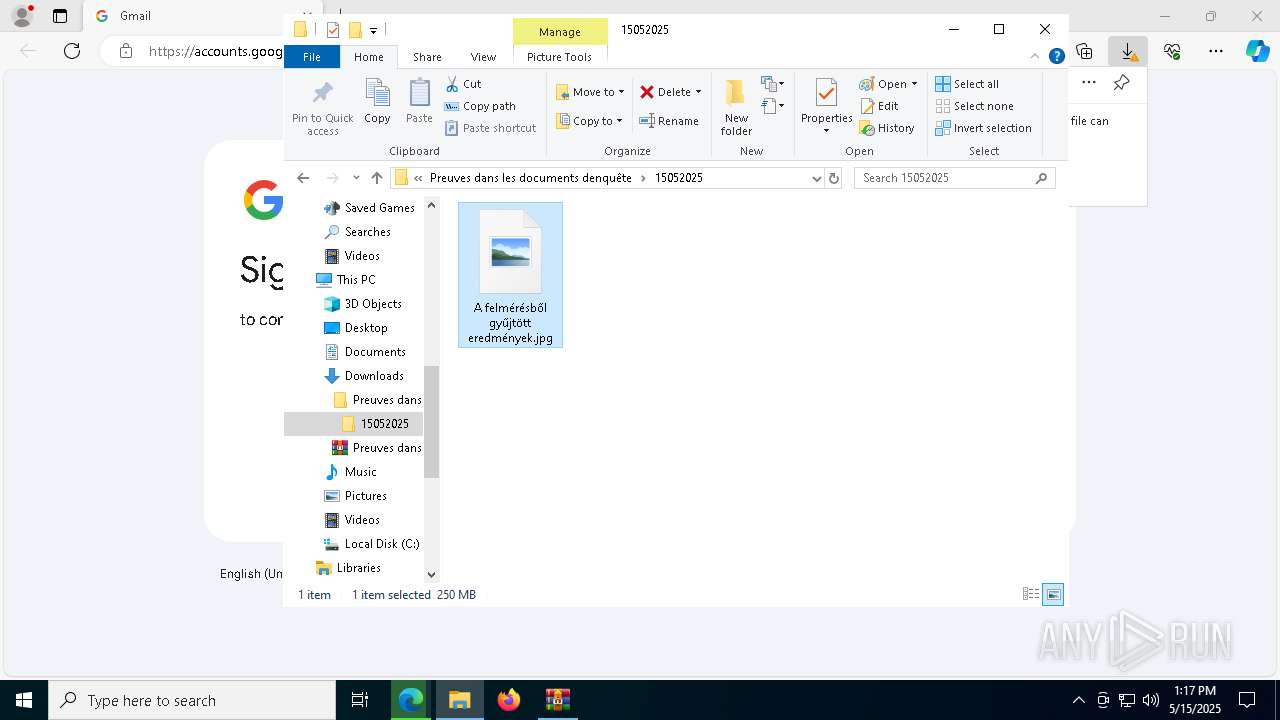
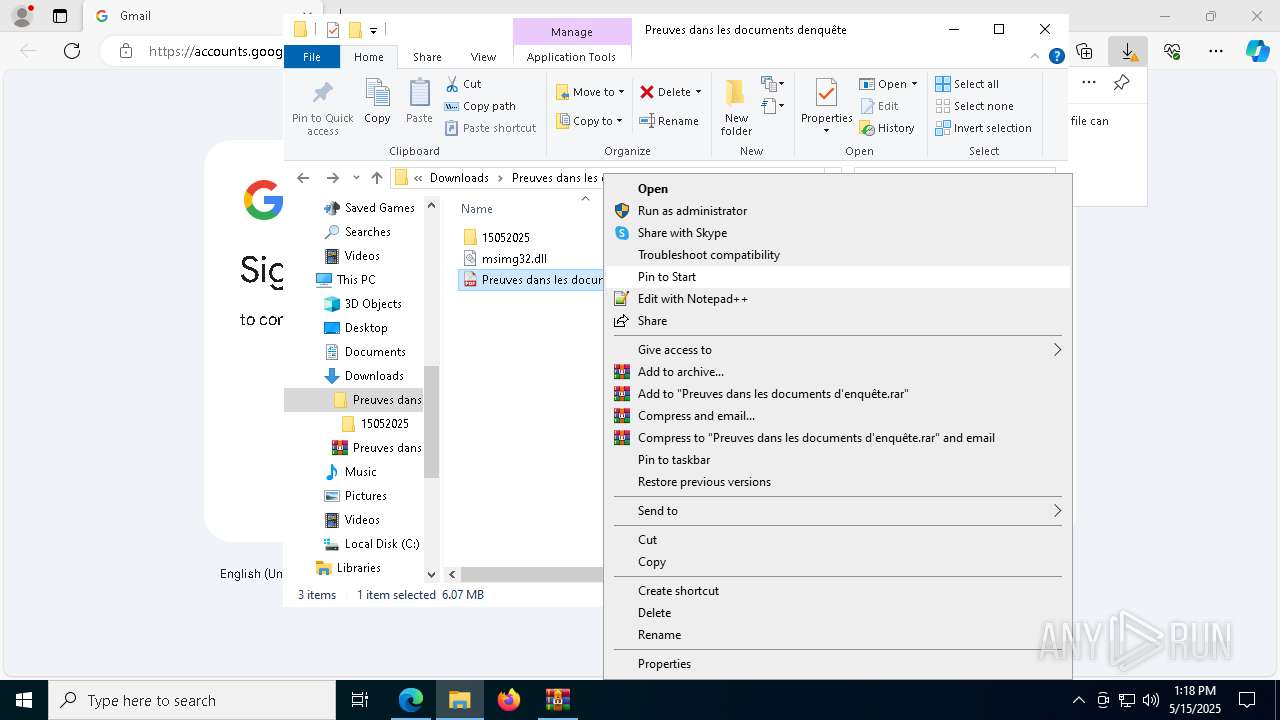
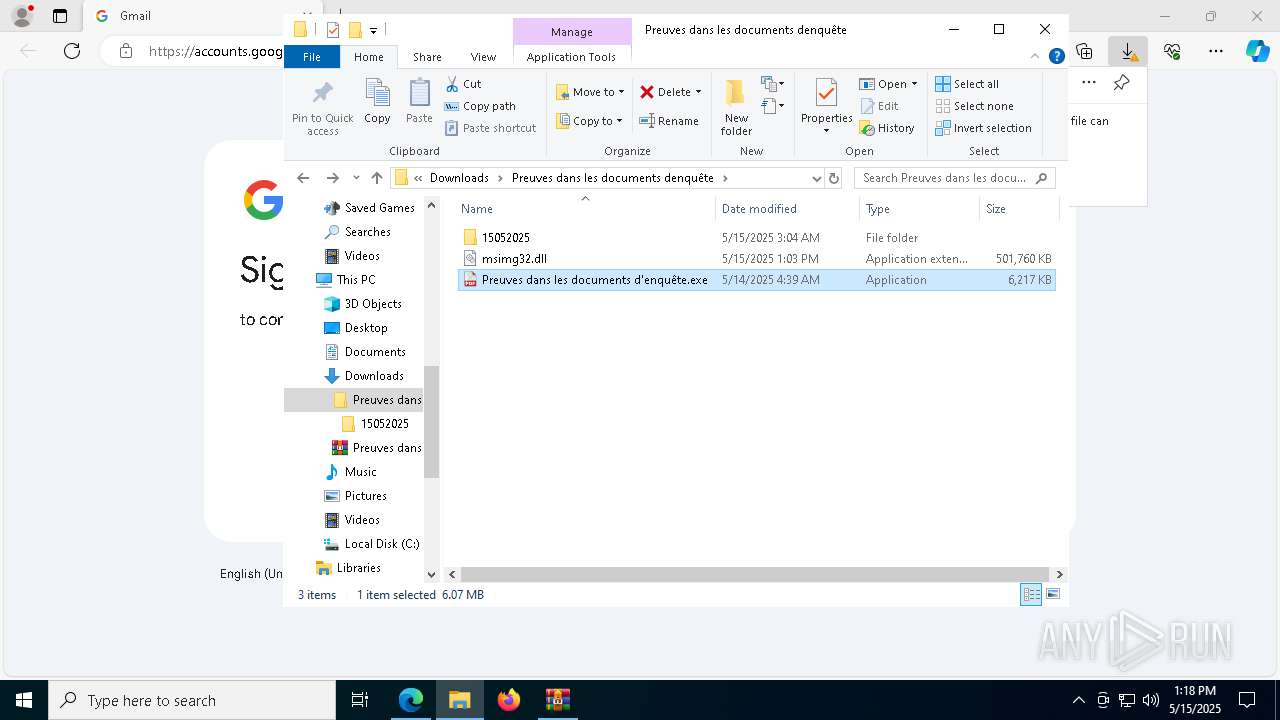
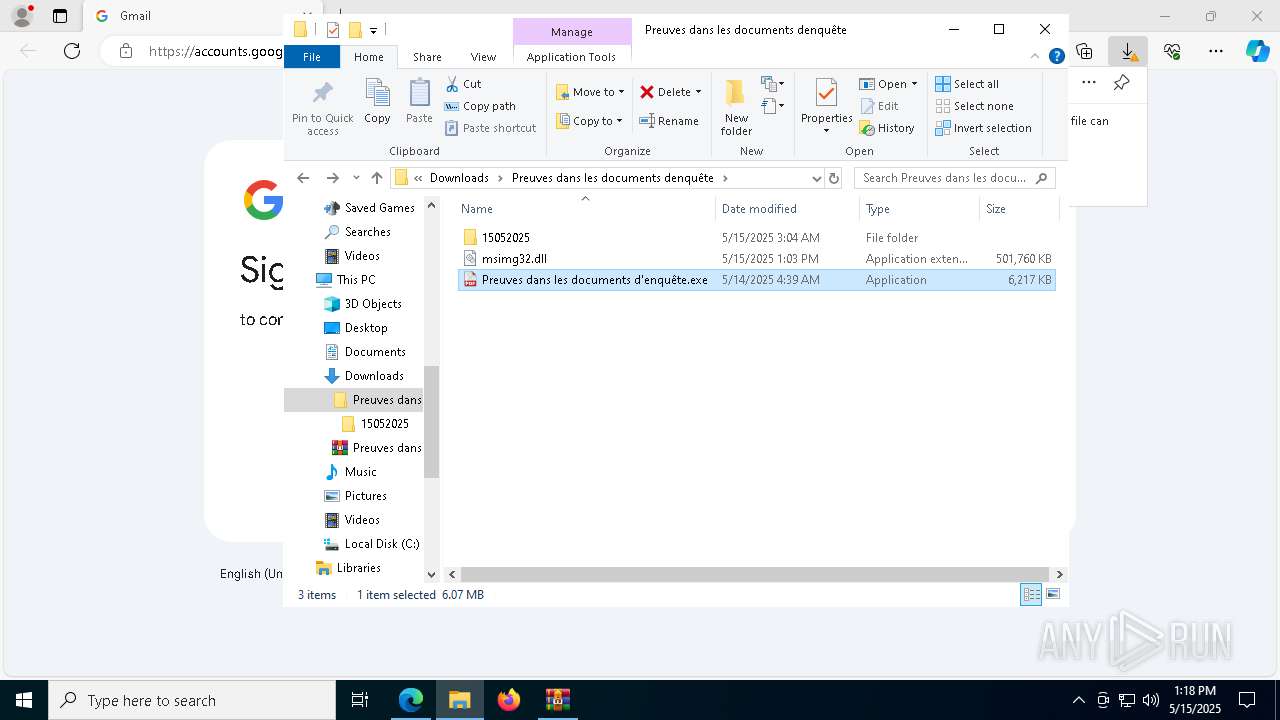
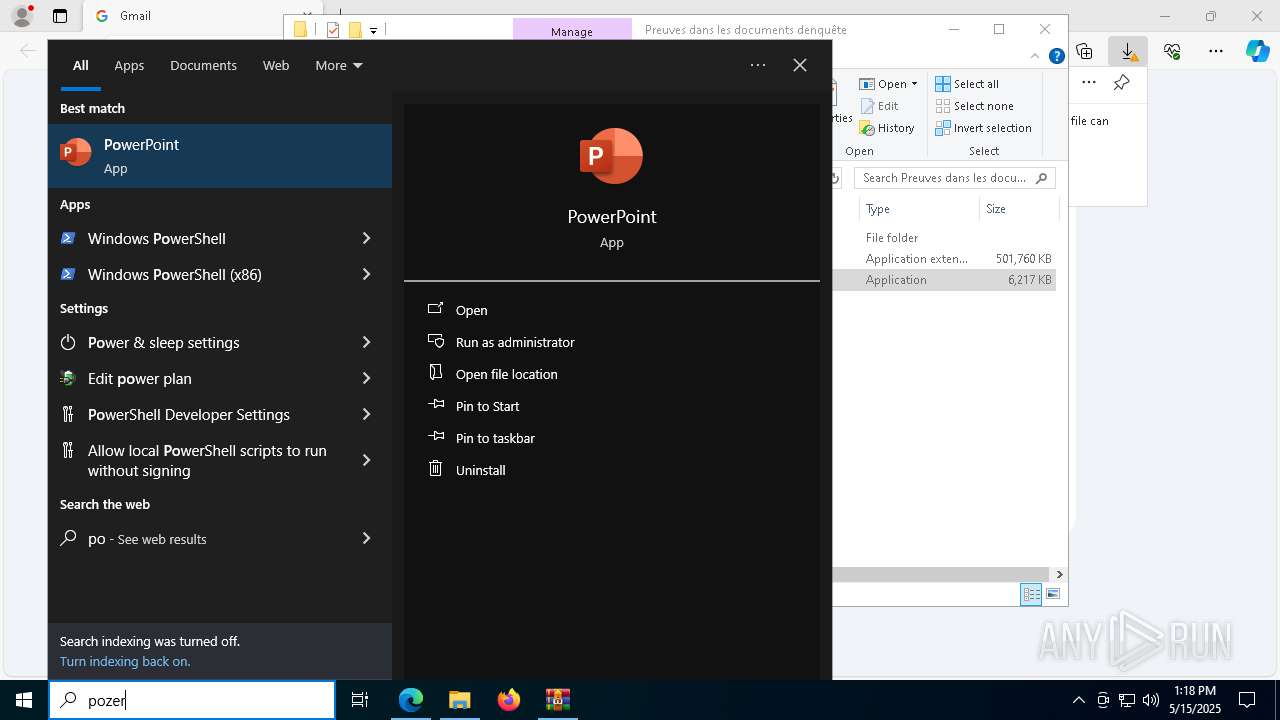
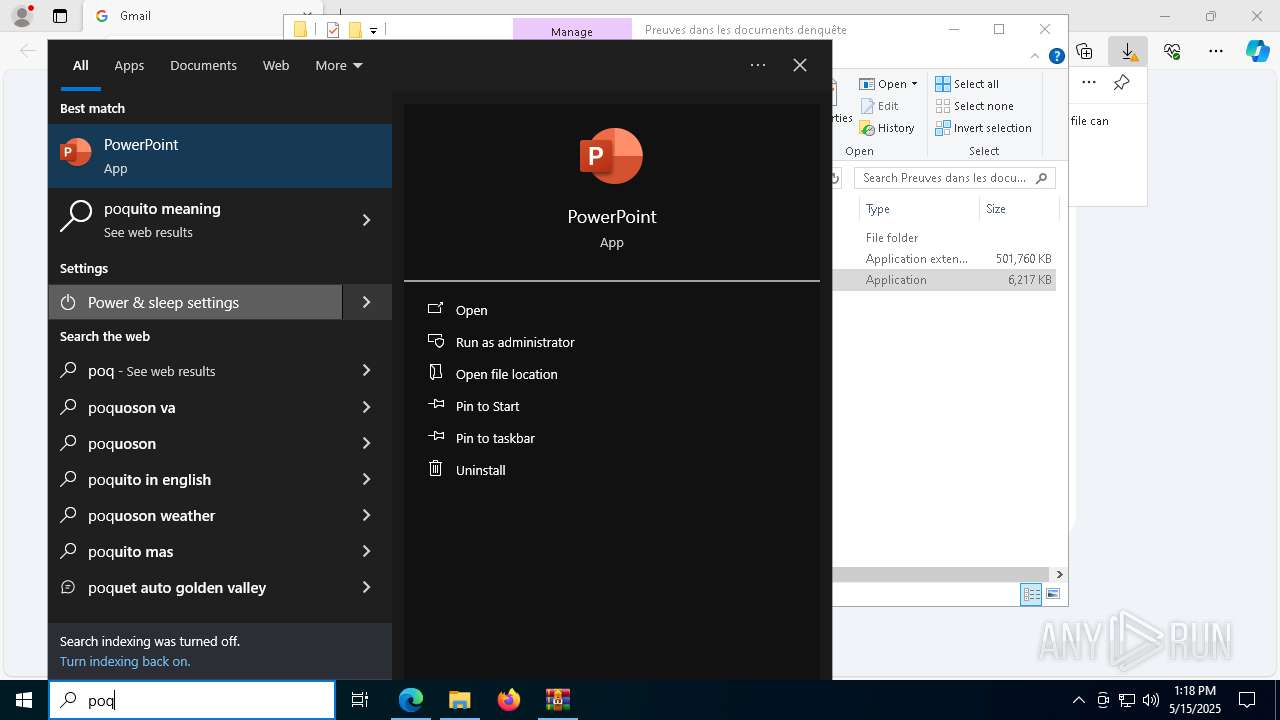
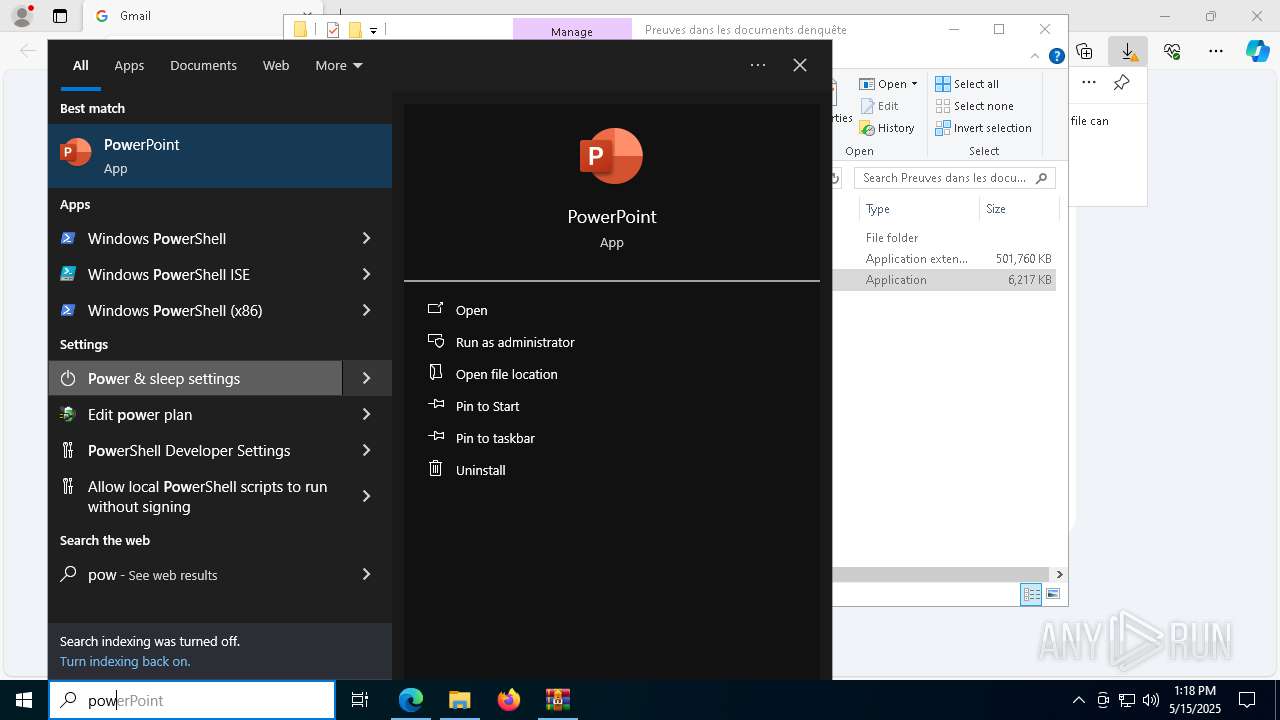
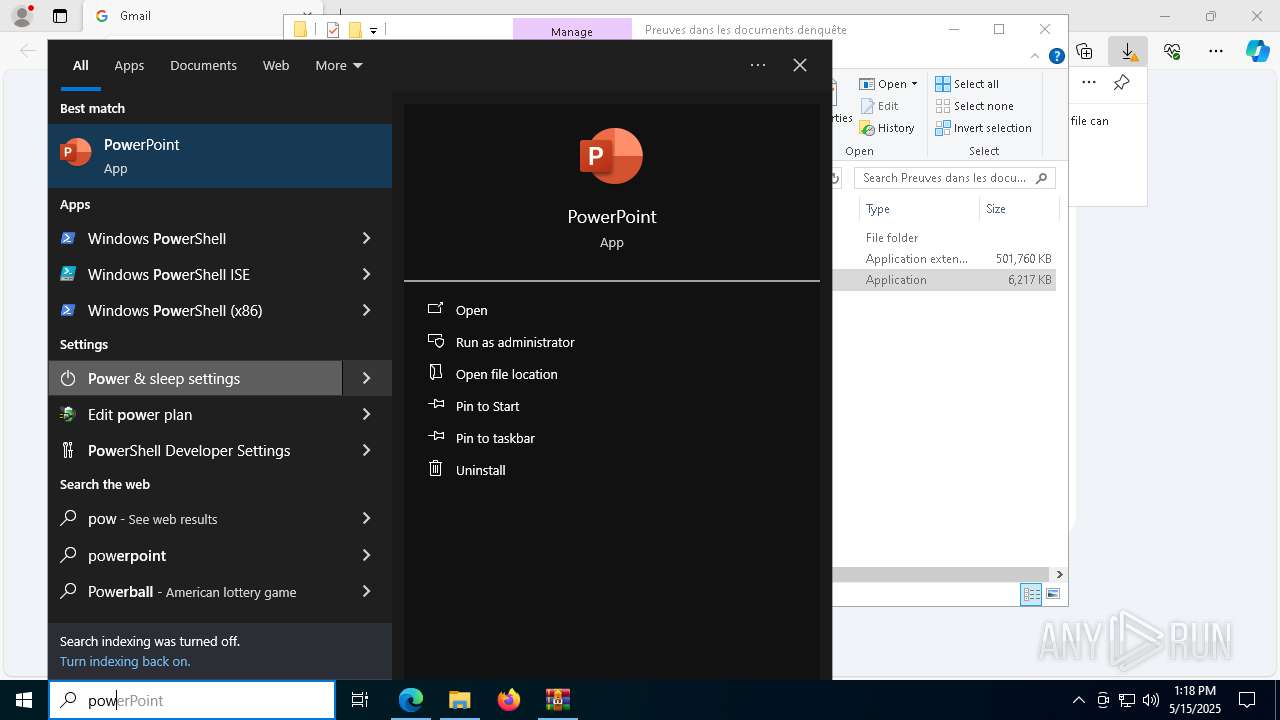
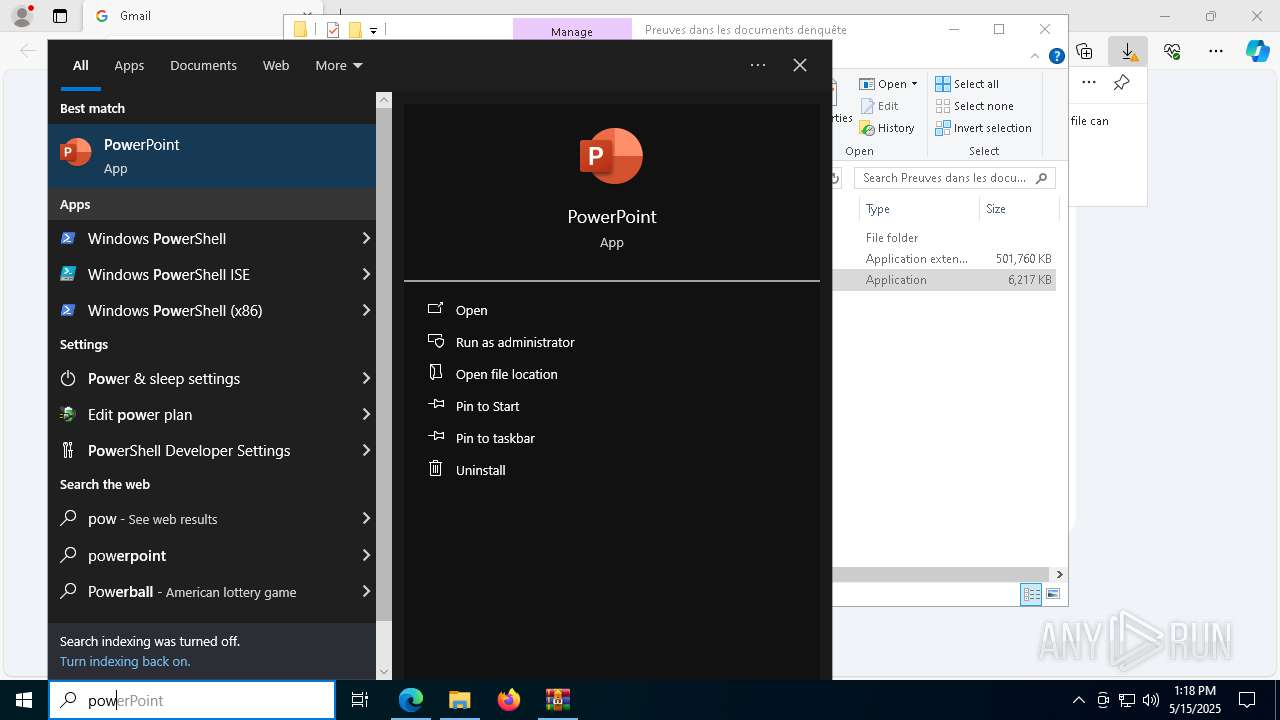
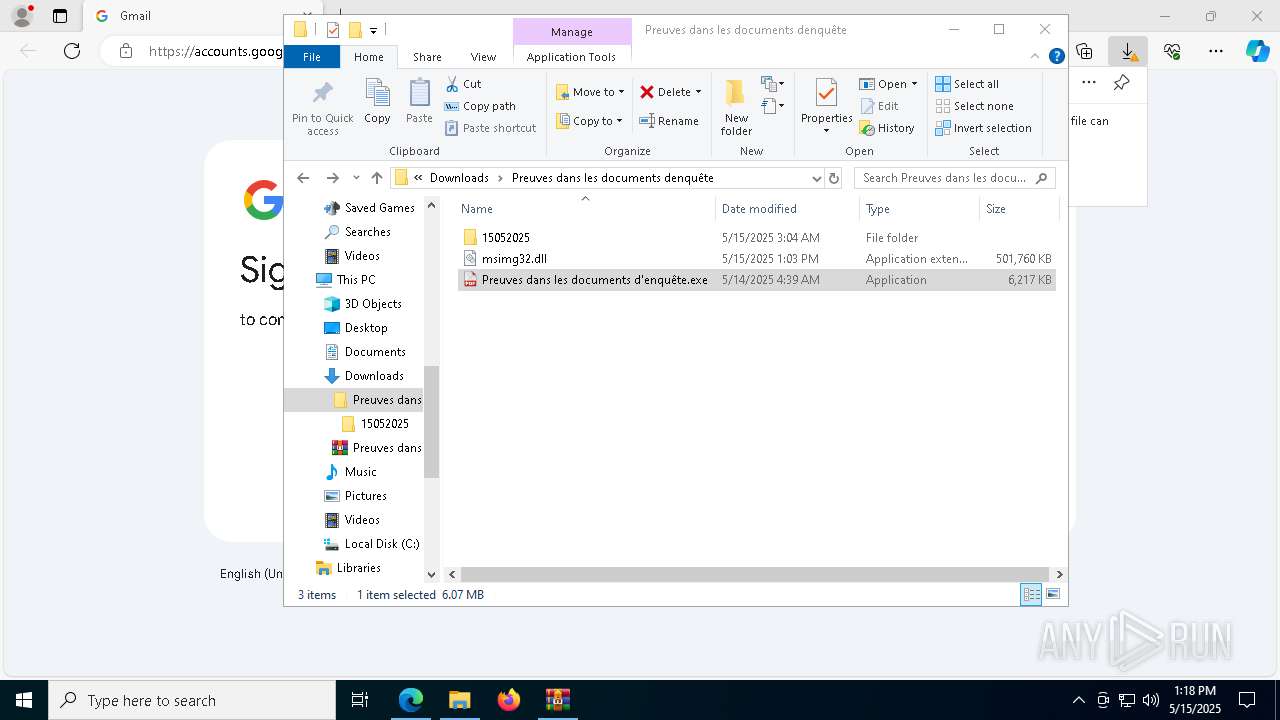
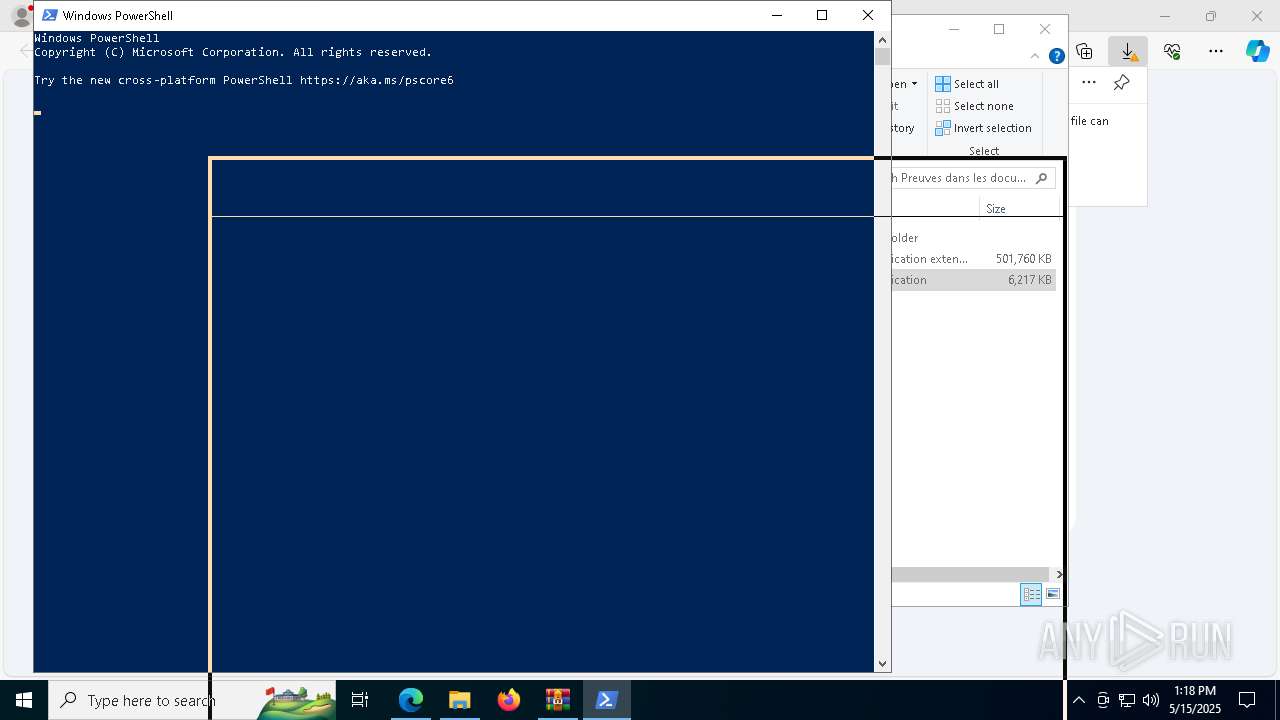
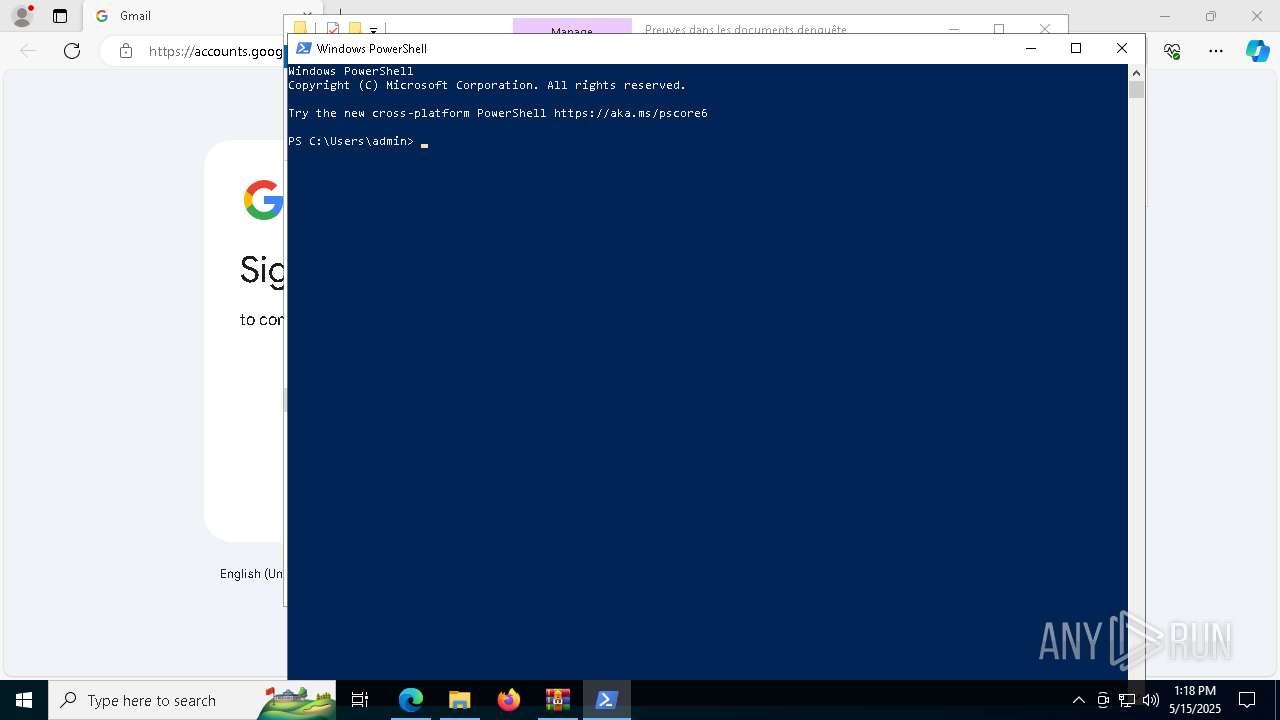
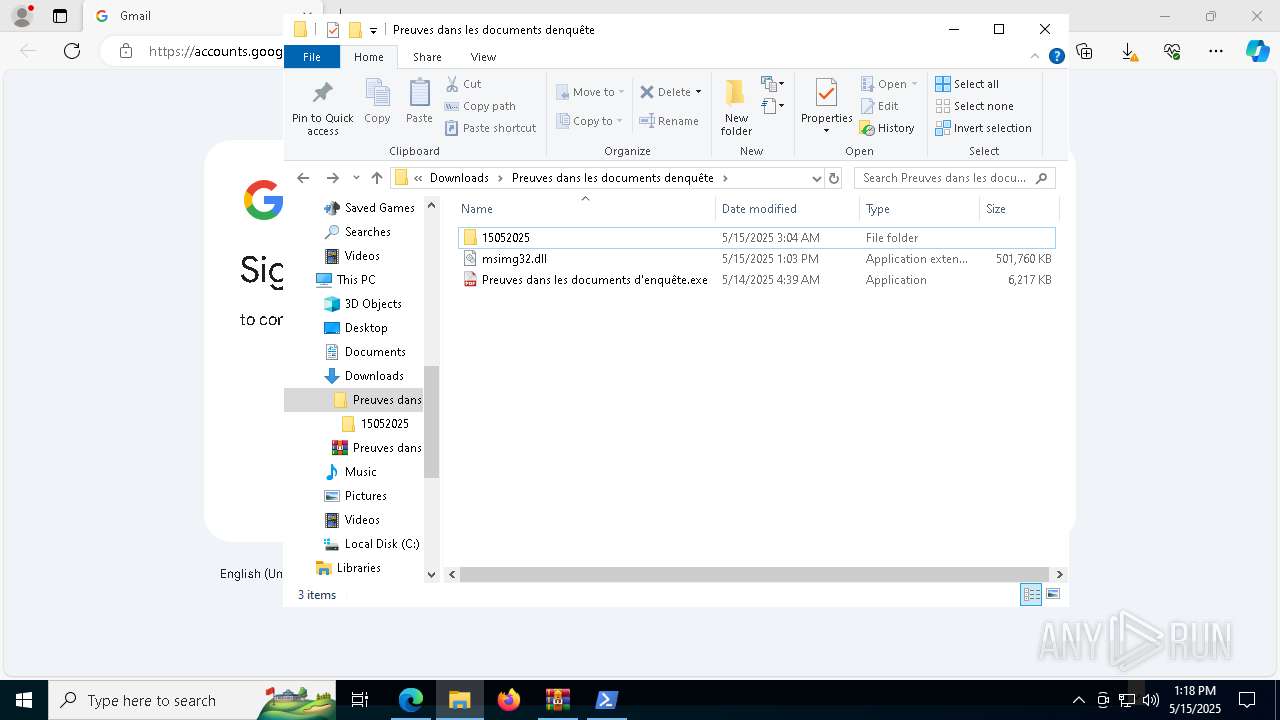
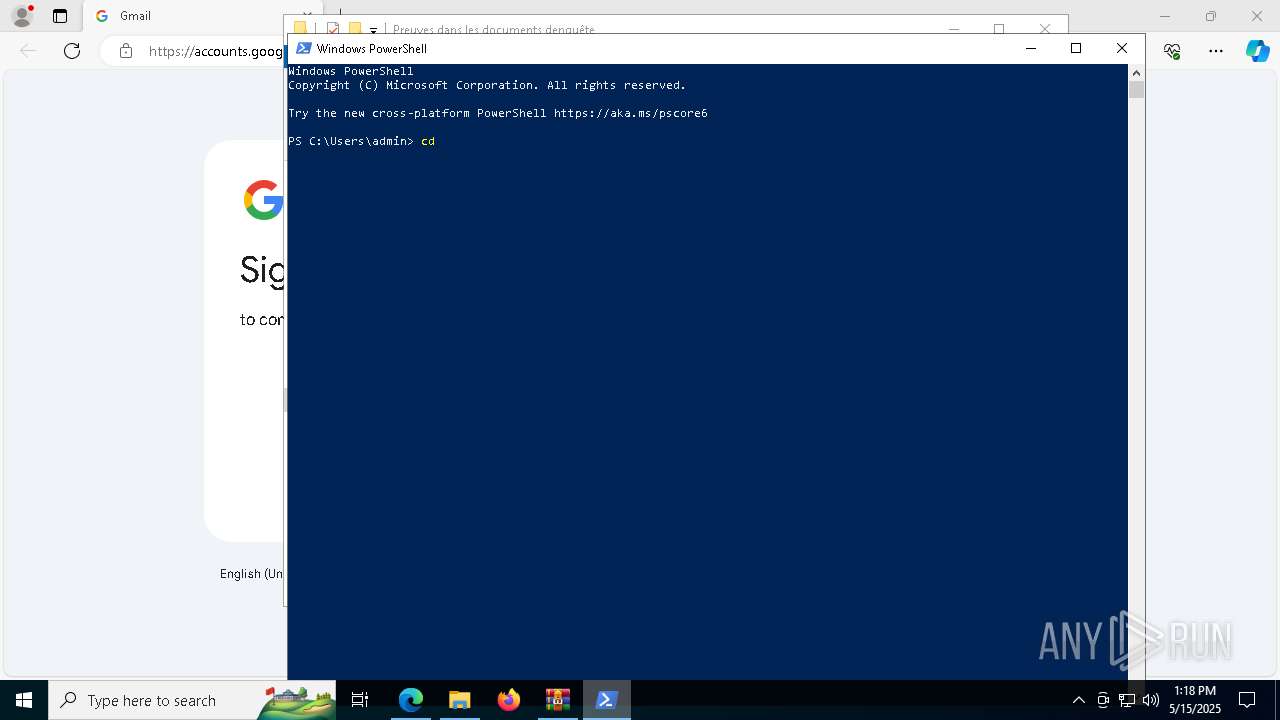
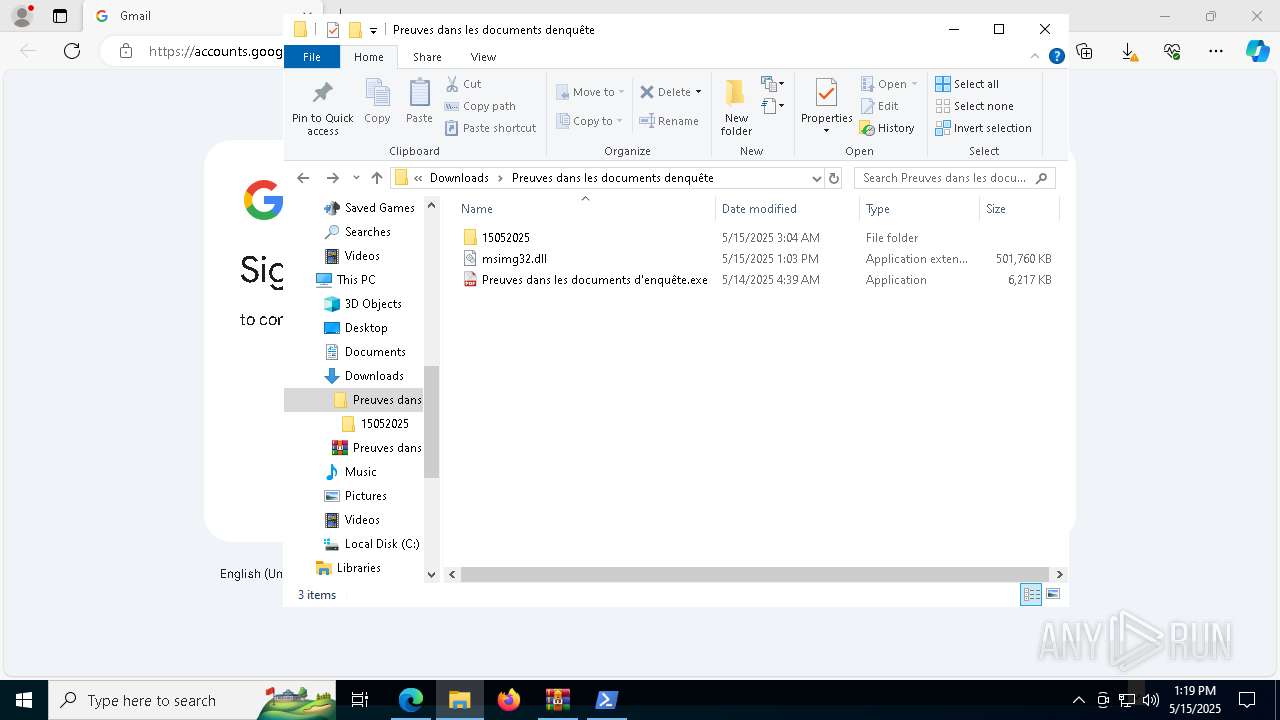
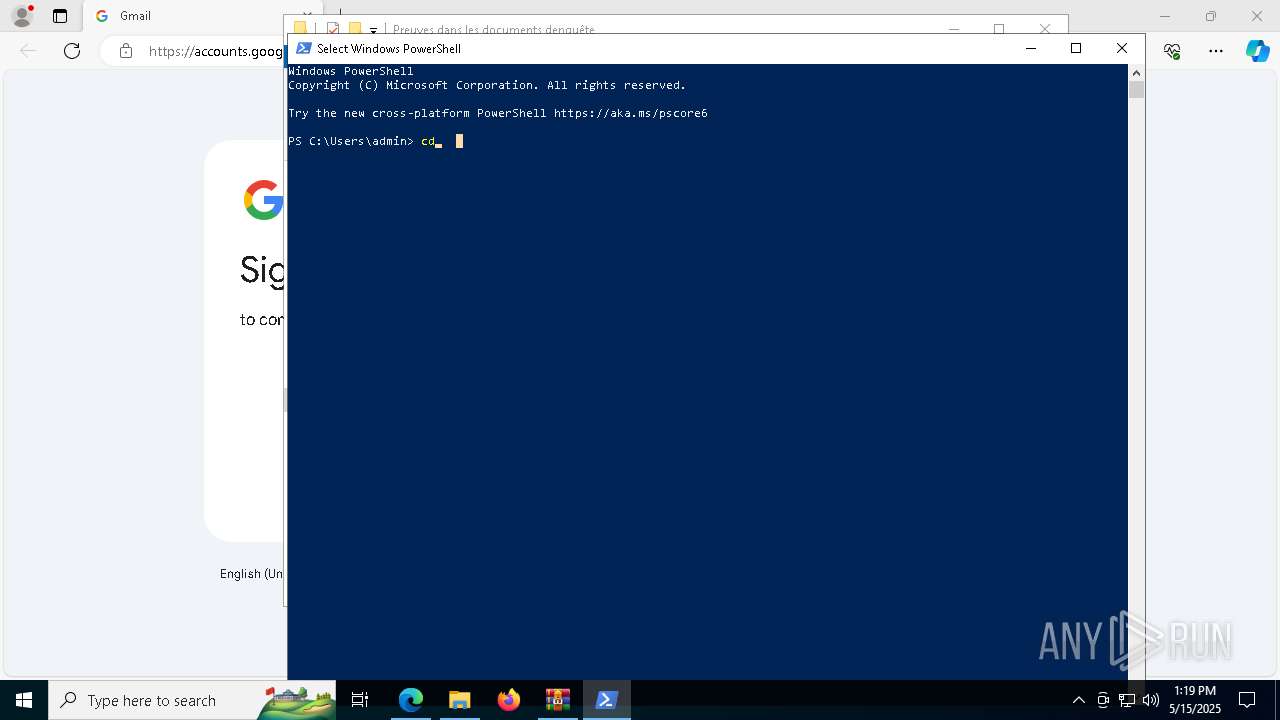
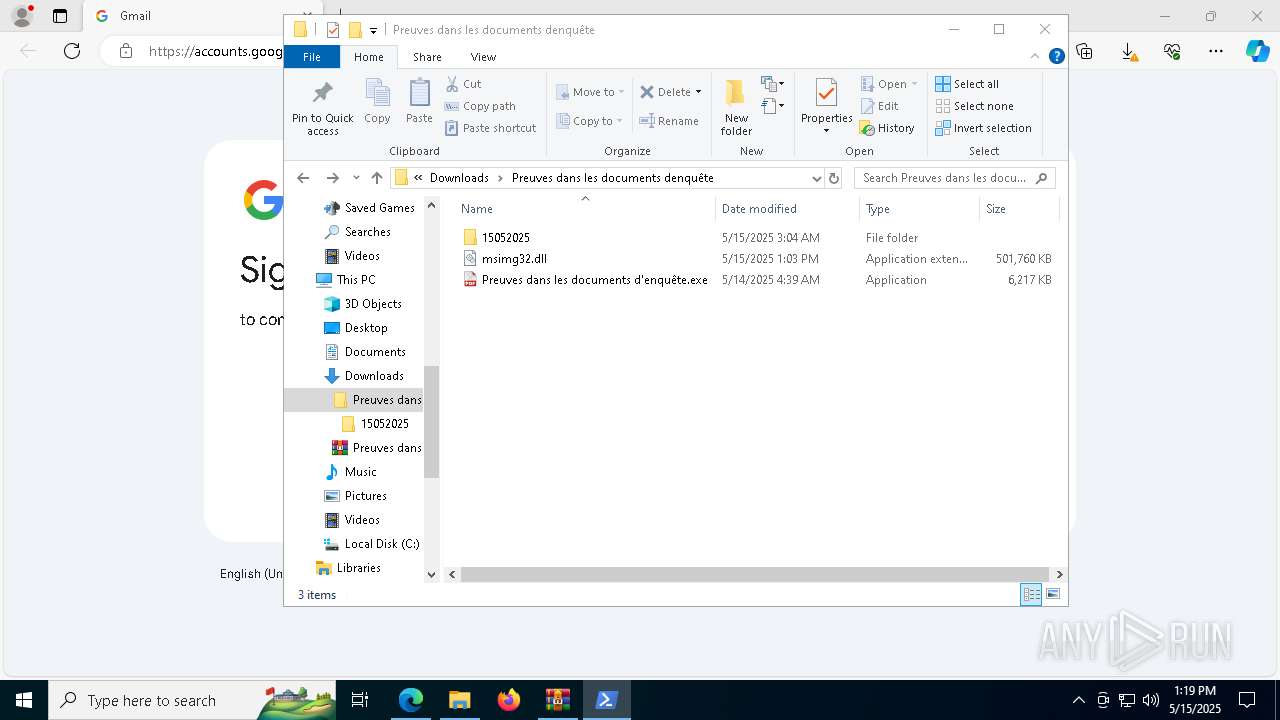
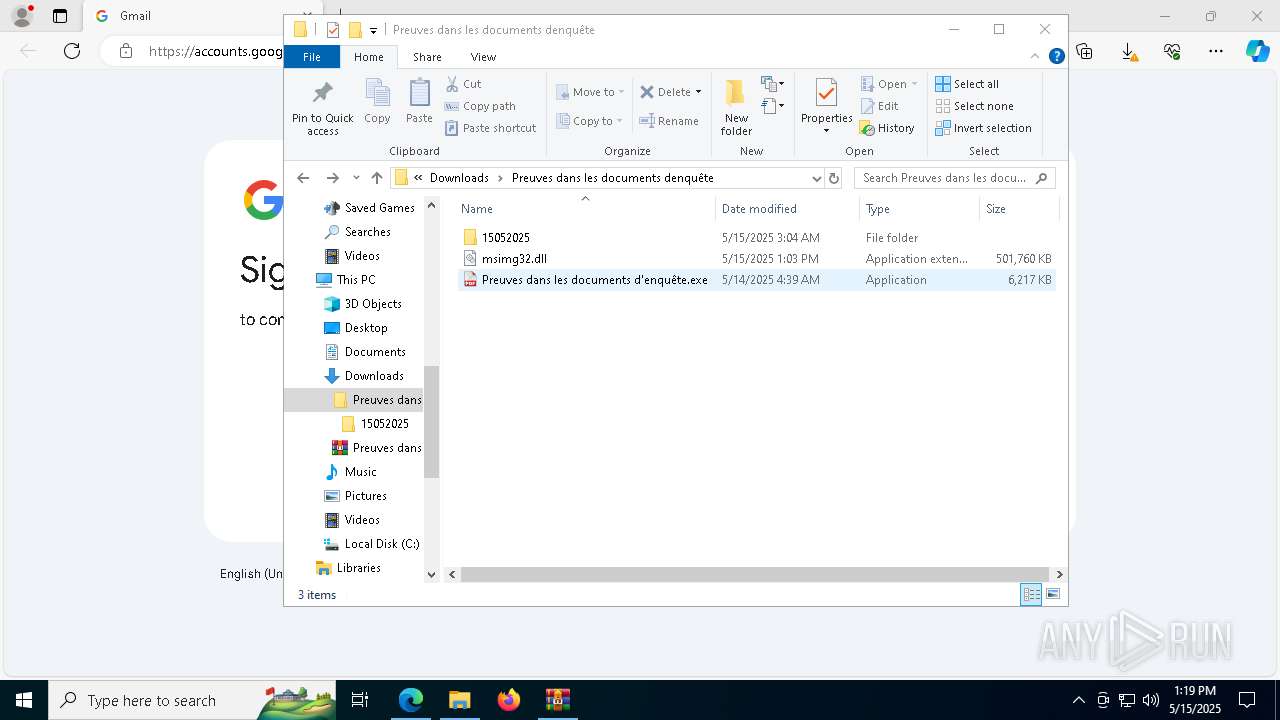
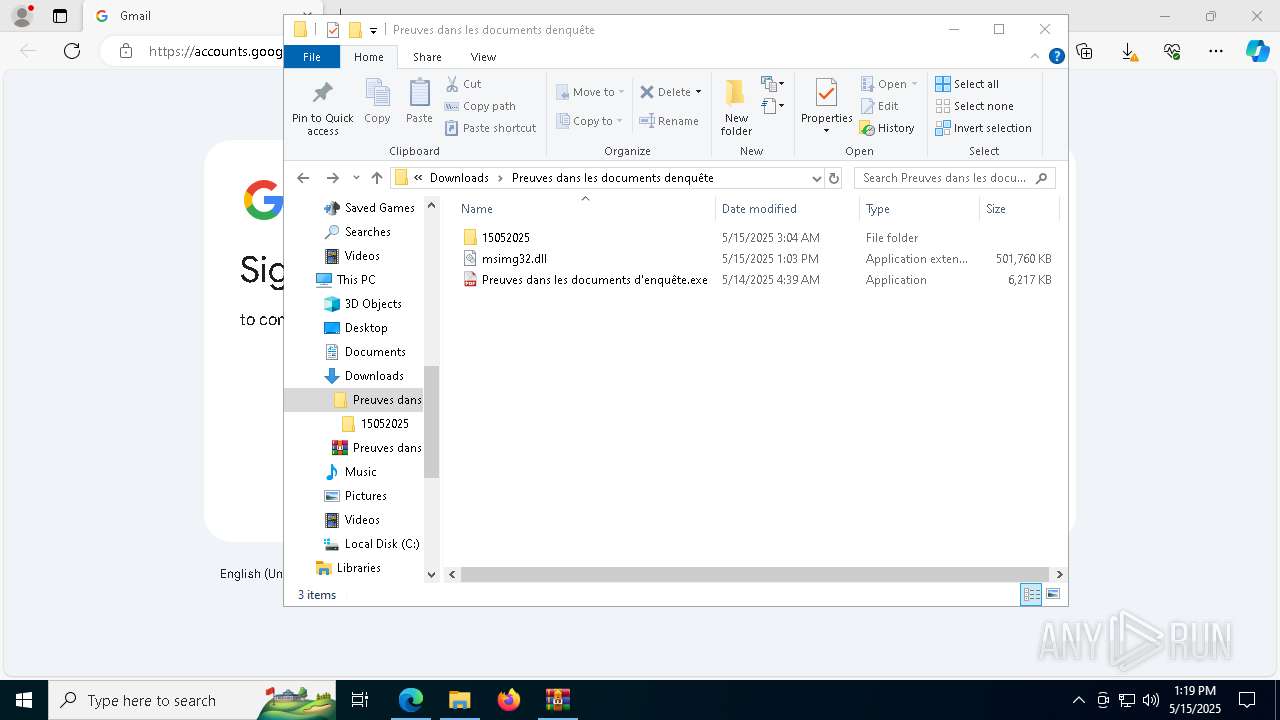
Manual execution by a user
- Preuves dans les documents d'enquête.exe (PID: 6456)
- mspaint.exe (PID: 5812)
- Preuves dans les documents d'enquête.exe (PID: 7724)
- svchost.exe (PID: 5084)
- powershell.exe (PID: 4756)
- svchost.exe (PID: 1128)
- msedge.exe (PID: 8668)
The sample compiled with english language support
- WinRAR.exe (PID: 872)
- msedge.exe (PID: 8144)
- svchost.exe (PID: 1128)
- wmpnscfg.exe (PID: 8516)
- svchost.exe (PID: 4304)
Checks proxy server information
- slui.exe (PID: 6584)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 8012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
280
Monitored processes
135
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2120 --field-trial-handle=2068,i,8820946356454172556,15361195951810019955,262144 --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 236 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 8032 -s 584 | C:\Windows\SysWOW64\WerFault.exe | — | Preuves dans les documents d'enquête.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2628 --field-trial-handle=2496,i,11678650362399173768,15443697254996415829,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
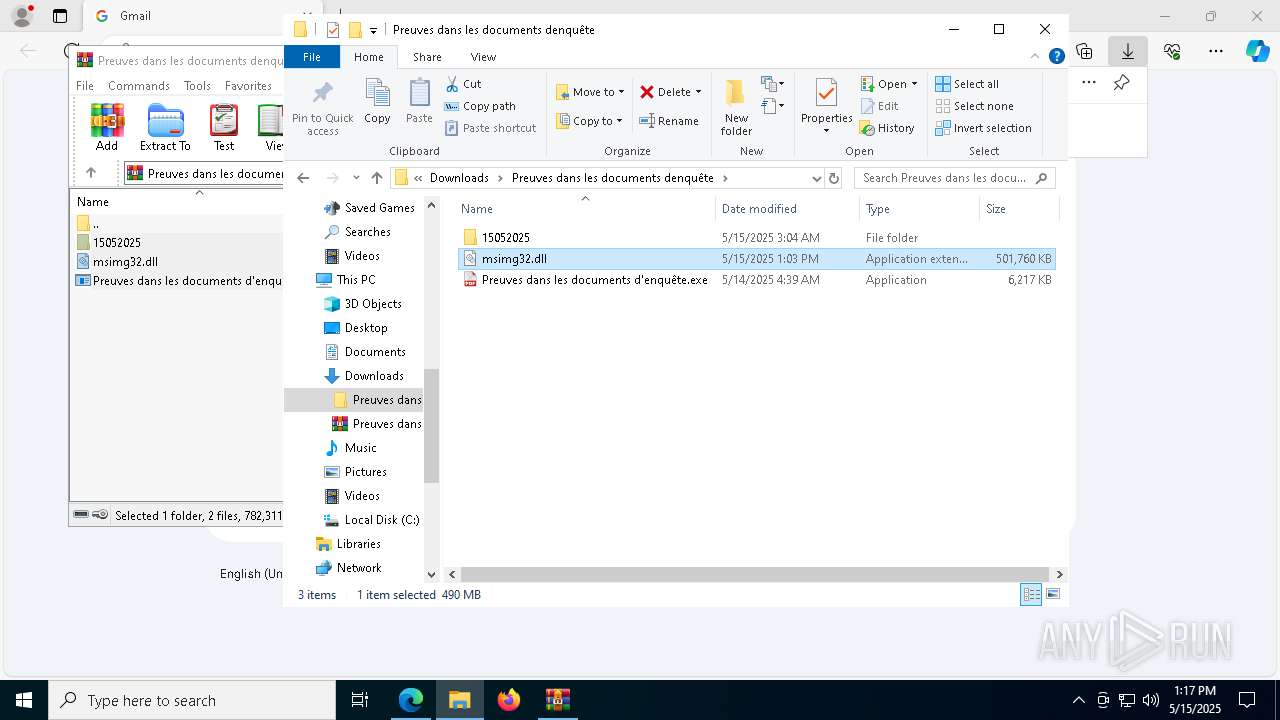
| 672 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" C:\Users\admin\Downloads\Preuves dans les documents denquête\msimg32.dll | C:\Program Files\Internet Explorer\iexplore.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5128 --field-trial-handle=2420,i,14707224083747438839,7322657320983201105,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
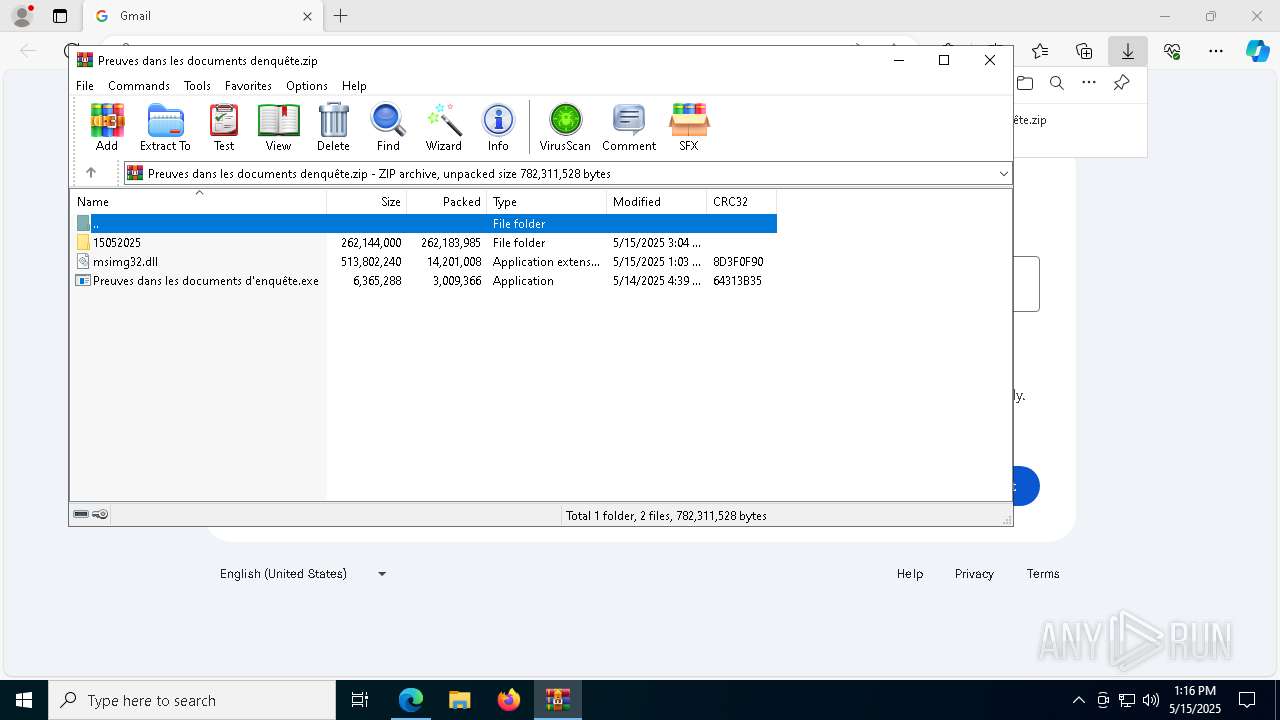
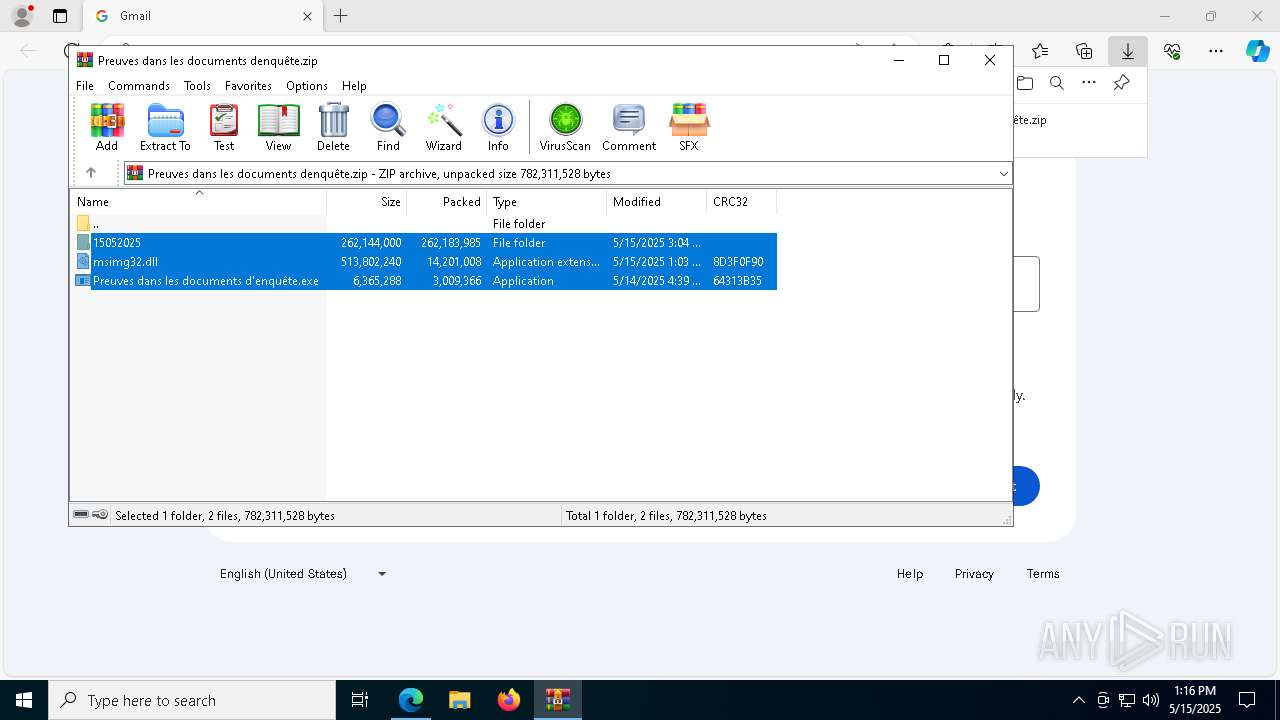
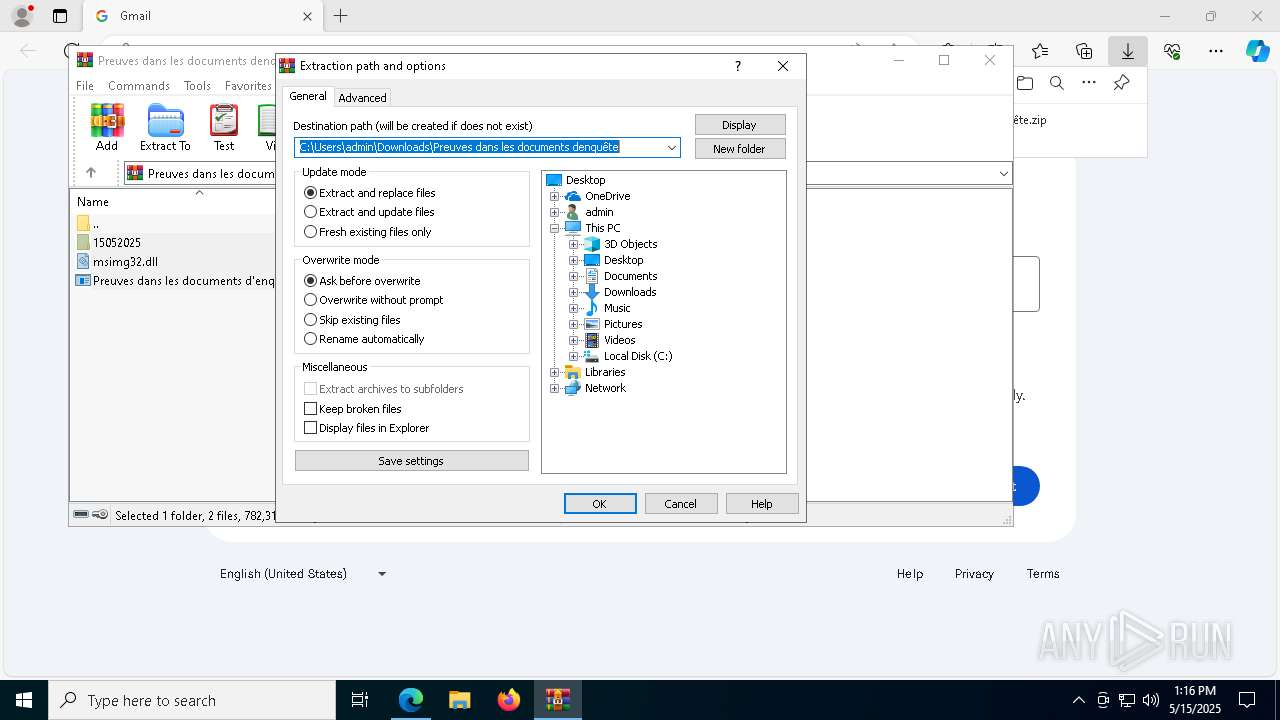
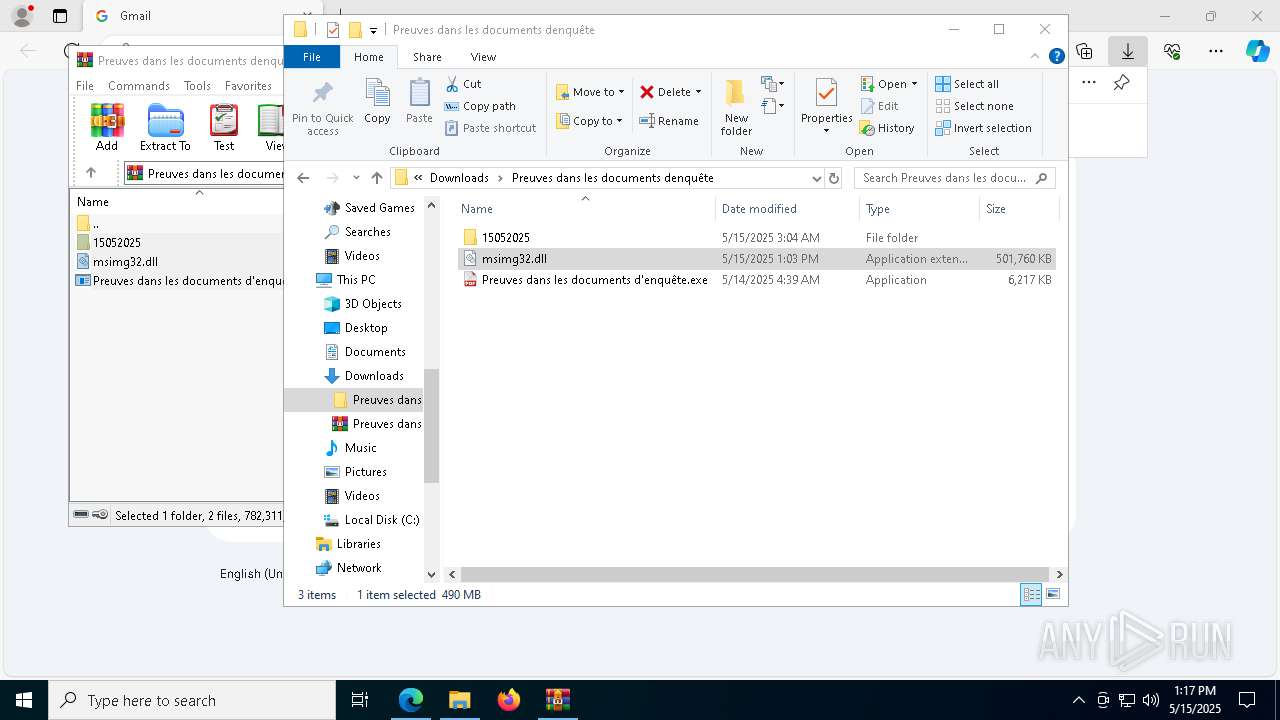
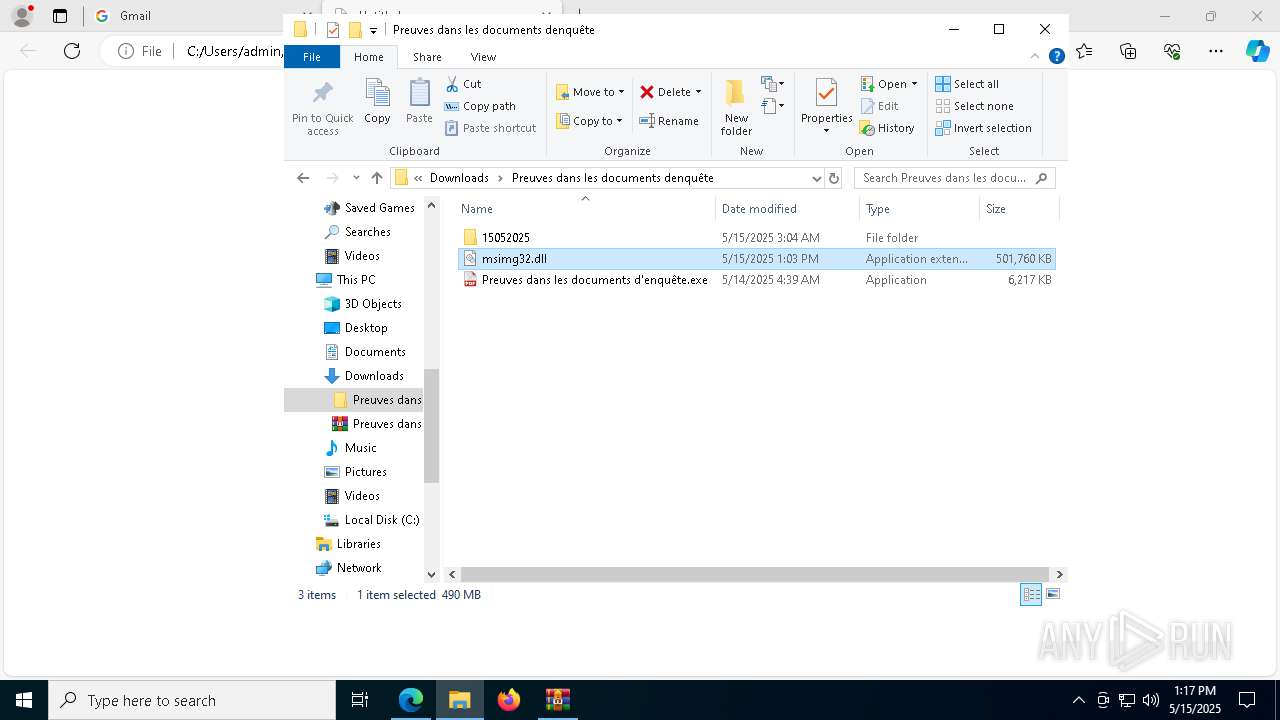
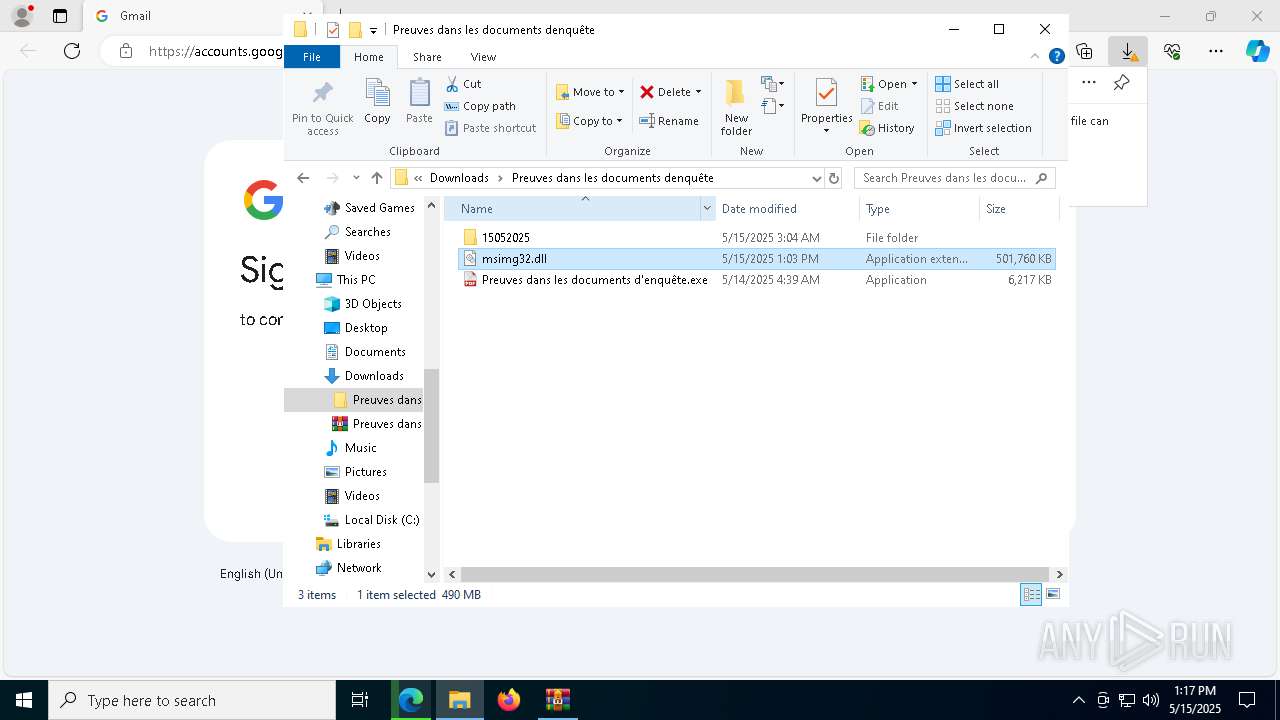
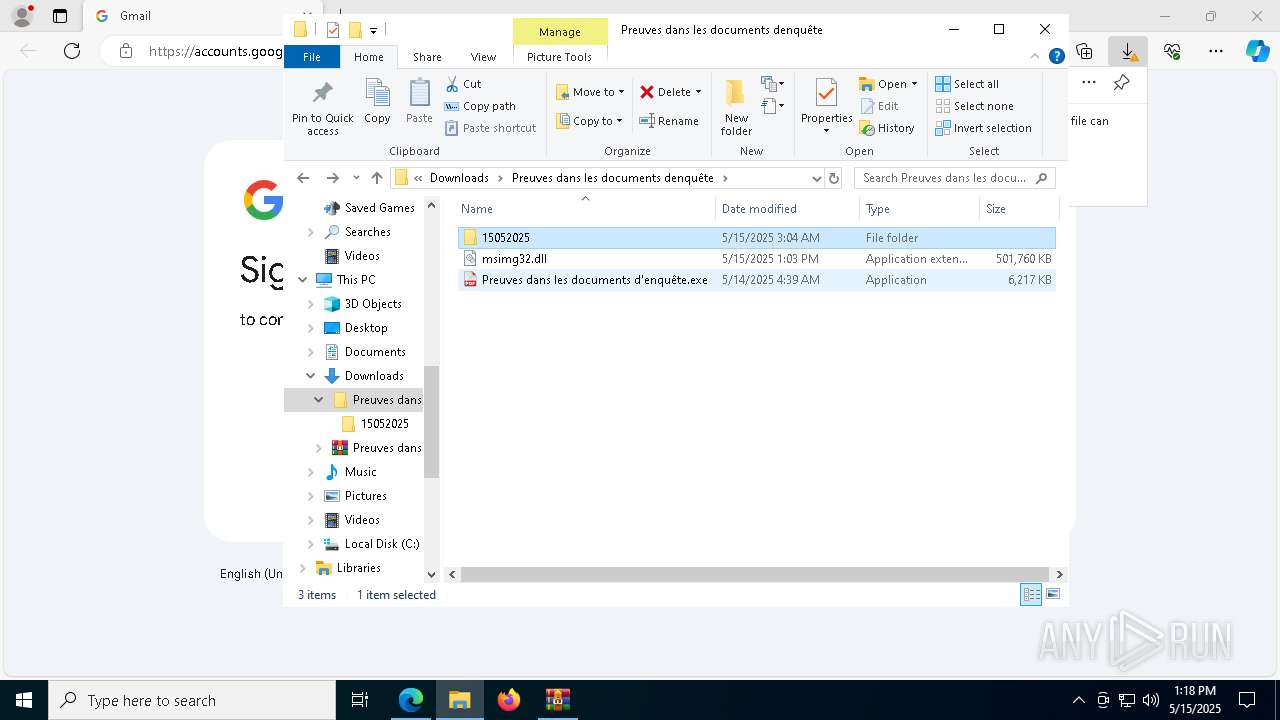
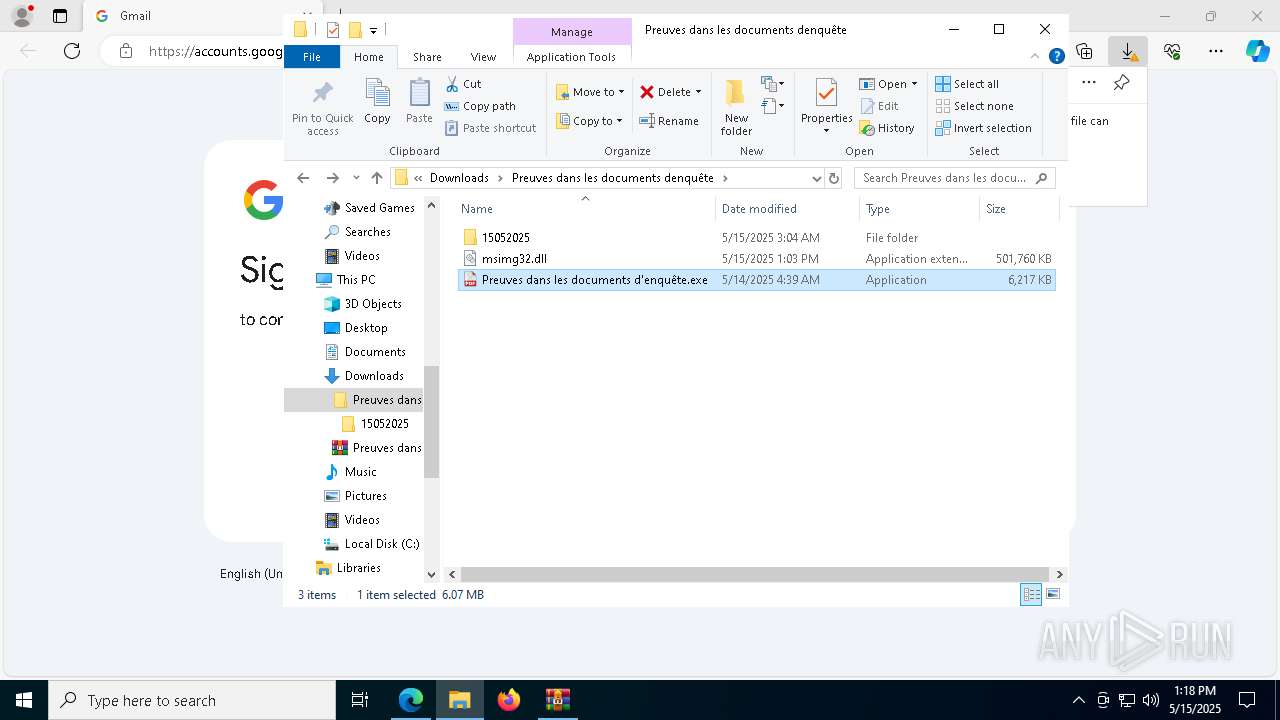
| 872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Preuves dans les documents denquête.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=2052 --field-trial-handle=2068,i,8820946356454172556,15361195951810019955,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1128 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | "C:\WINDOWS\system32\dllhost.exe" | C:\Windows\System32\dllhost.exe | wmpnscfg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --no-appcompat-clear --mojo-platform-channel-handle=7920 --field-trial-handle=2420,i,14707224083747438839,7322657320983201105,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
27 780
Read events
27 652
Write events
113
Delete events
15
Modification events
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 92F64EBDC2932F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F09A6EBDC2932F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6F555265-BE79-4949-BF4A-A353A53C9884} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5DB33757-1978-43A1-8399-79F0C7E245E4} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4355E283-7CB8-42A8-B7F8-F185FAAD80EE} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5220C1BDC2932F00 | |||
Executable files
48
Suspicious files
1 018
Text files
240
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c805.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c824.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c824.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c824.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c834.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
173
DNS requests
191
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4996 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/86605bd6-bfe9-473b-8c26-a52795ef3565?P1=1747702796&P2=404&P3=2&P4=nIXC3hnvkU7vLNYSMT3Pyj9hpuR9gFyjOvKDp8p6mlXhTZKMAv05RJ8A6R9337QywjjsNfIJM9rCWjeJp9IYwA%3d%3d | unknown | — | — | whitelisted |
4996 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/86605bd6-bfe9-473b-8c26-a52795ef3565?P1=1747702796&P2=404&P3=2&P4=nIXC3hnvkU7vLNYSMT3Pyj9hpuR9gFyjOvKDp8p6mlXhTZKMAv05RJ8A6R9337QywjjsNfIJM9rCWjeJp9IYwA%3d%3d | unknown | — | — | whitelisted |
4996 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/86605bd6-bfe9-473b-8c26-a52795ef3565?P1=1747702796&P2=404&P3=2&P4=nIXC3hnvkU7vLNYSMT3Pyj9hpuR9gFyjOvKDp8p6mlXhTZKMAv05RJ8A6R9337QywjjsNfIJM9rCWjeJp9IYwA%3d%3d | unknown | — | — | whitelisted |
4996 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/86605bd6-bfe9-473b-8c26-a52795ef3565?P1=1747702796&P2=404&P3=2&P4=nIXC3hnvkU7vLNYSMT3Pyj9hpuR9gFyjOvKDp8p6mlXhTZKMAv05RJ8A6R9337QywjjsNfIJM9rCWjeJp9IYwA%3d%3d | unknown | — | — | whitelisted |
4996 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/86605bd6-bfe9-473b-8c26-a52795ef3565?P1=1747702796&P2=404&P3=2&P4=nIXC3hnvkU7vLNYSMT3Pyj9hpuR9gFyjOvKDp8p6mlXhTZKMAv05RJ8A6R9337QywjjsNfIJM9rCWjeJp9IYwA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7320 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1276 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7320 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
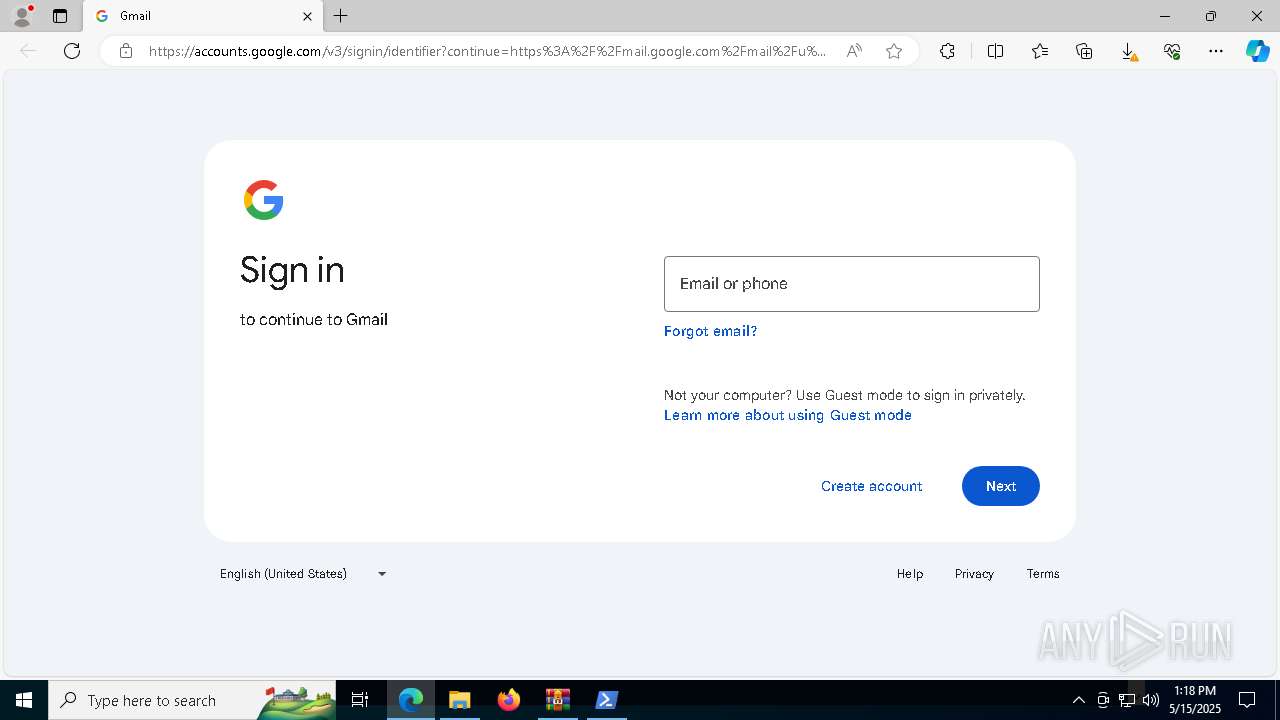
7320 | msedge.exe | 151.101.2.133:80 | tr.ee | FASTLY | US | malicious |
7320 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
tr.ee |
| malicious |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service (tr .ee) in DNS Lookup |
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (tr .ee) in TLS SNI |
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
7320 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
7320 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
7320 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |