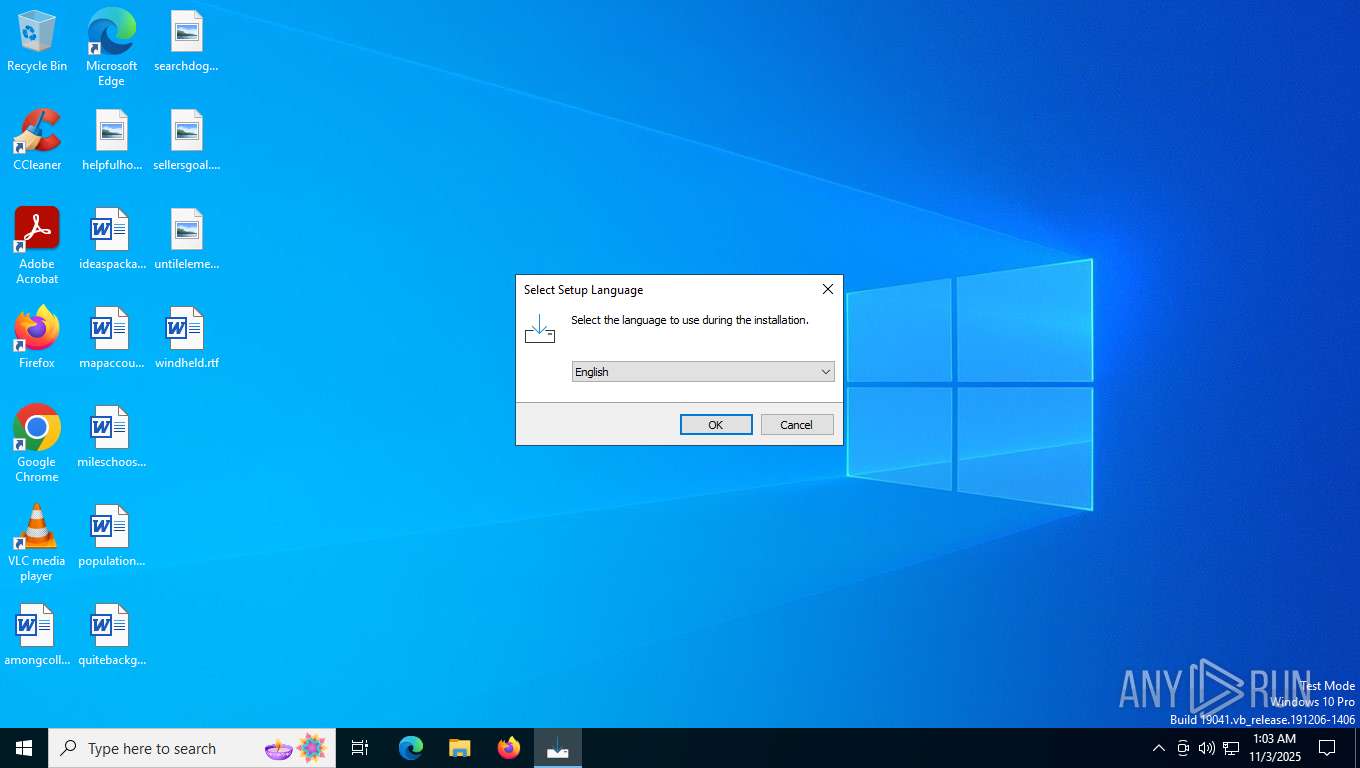
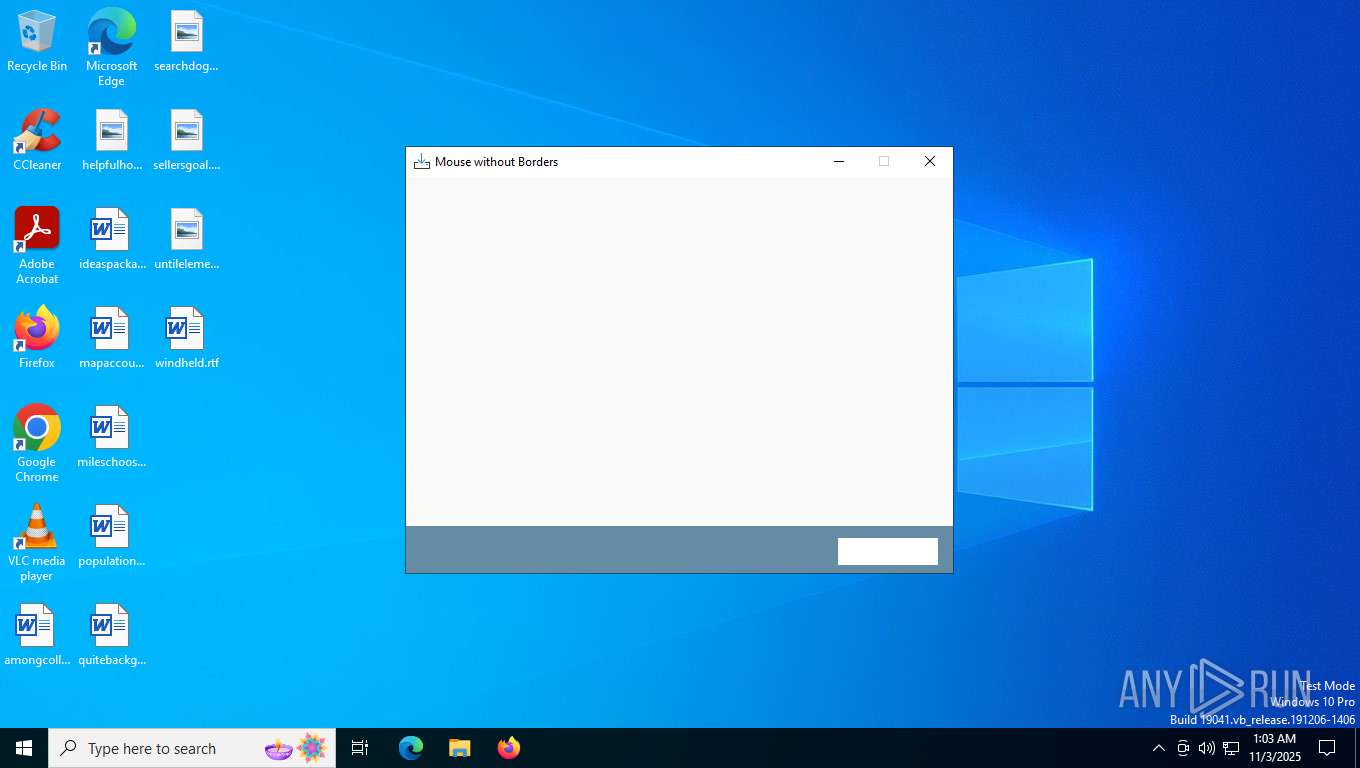
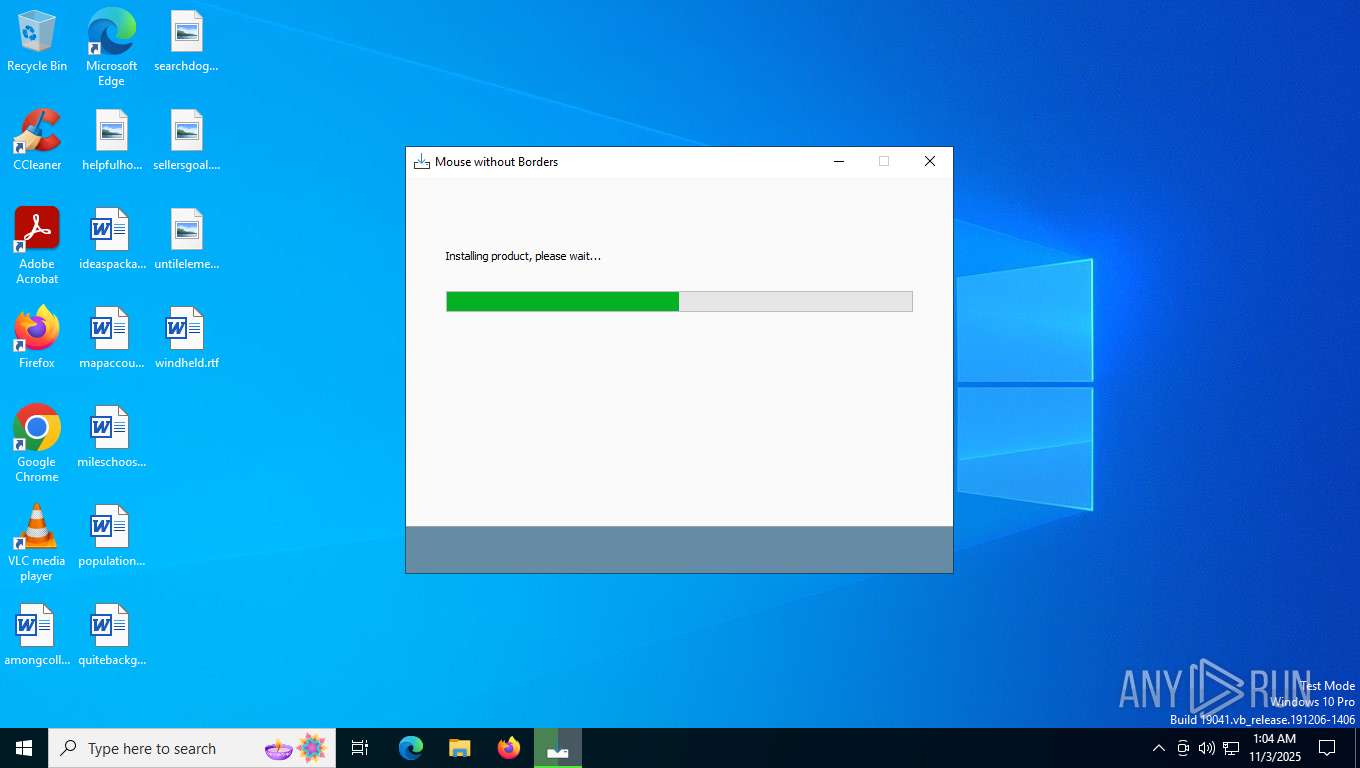
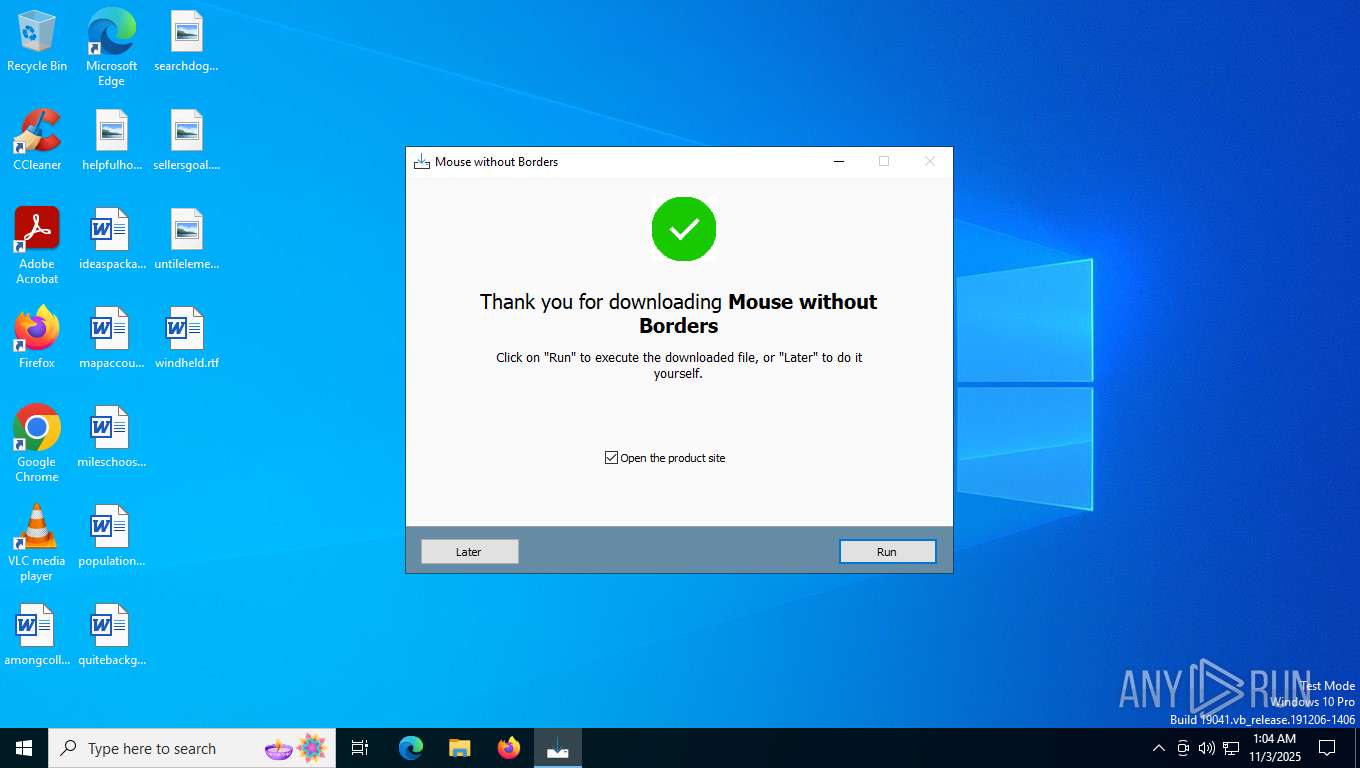
| File name: | mouse-without-borders_iqqX0-1.exe |
| Full analysis: | https://app.any.run/tasks/2faa7e72-49e6-4151-b803-9fddc3f11aa7 |
| Verdict: | Malicious activity |
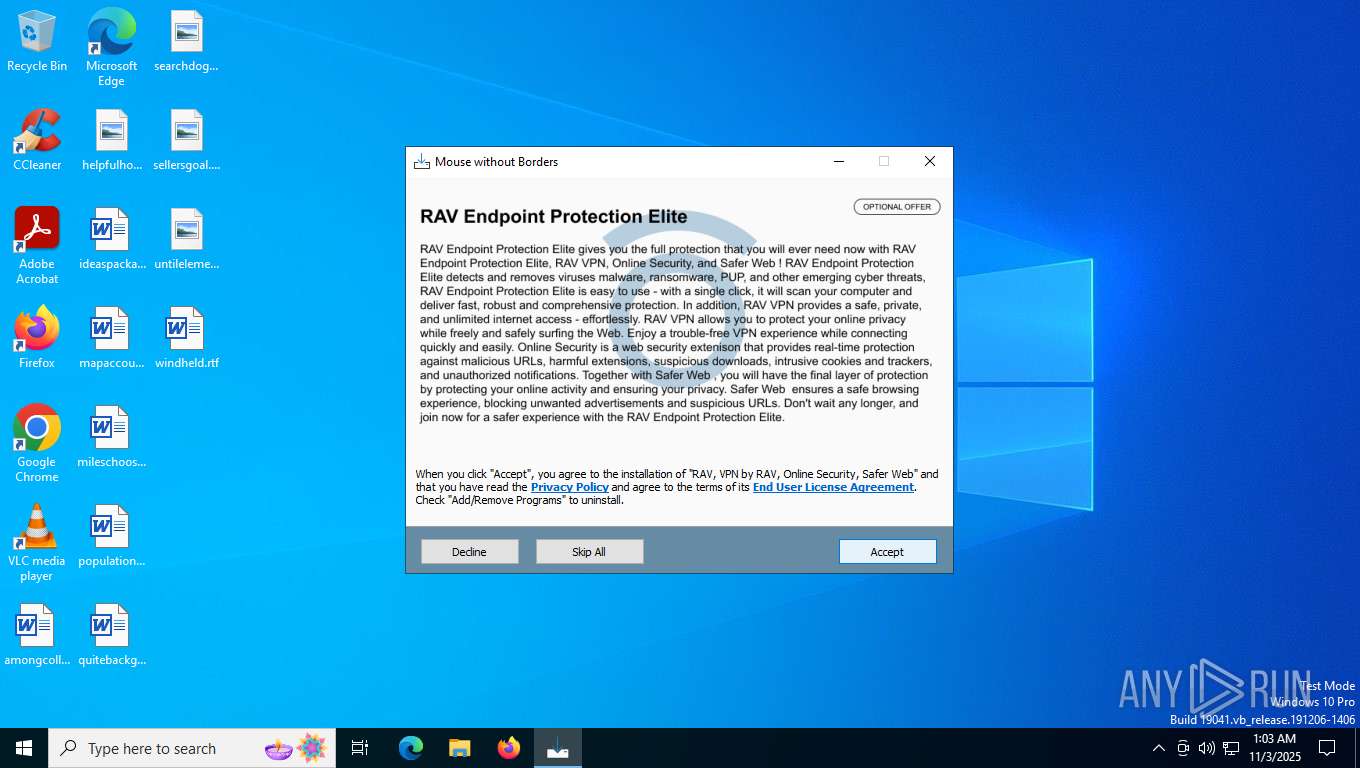
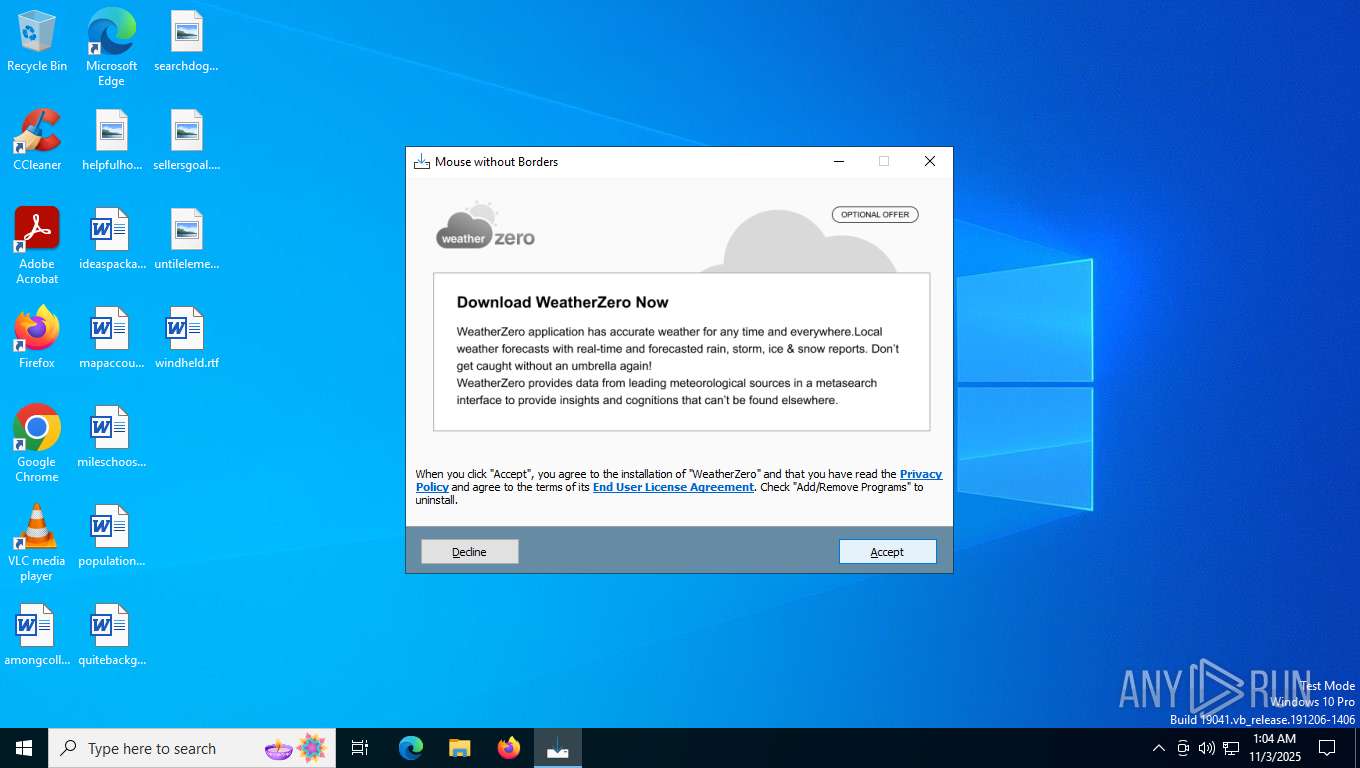
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | November 03, 2025, 01:03:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | A446F67ED6C5417AAACE3A6E805F3128 |
| SHA1: | 010B7BD1932F87B4E03B03FBB6F1693ADCA40952 |
| SHA256: | E6A4CD894A831087112E29FD774283772C4ACA6A0522E5FBFE0B086E8A253353 |
| SSDEEP: | 98304:5LVIF8P3n1BLHxtD59KEKjSvDhLI7VTZgtT160NZbXQc98CyhWtAh8GLRokZWtKG:rTYr3t/m7qoEJ+13P |
MALICIOUS
Bundleinstaller mutex has been found
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
INNOSETUP has been detected (SURICATA)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
Changes settings of System certificates
- UnifiedStub-installer.exe (PID: 5308)
- rsWSC.exe (PID: 5580)
- rsEngineSvc.exe (PID: 5336)
Starts Visual C# compiler
- WeatherZero.exe (PID: 5772)
Changes the autorun value in the registry
- rundll32.exe (PID: 7856)
SUSPICIOUS
Reads security settings of Internet Explorer
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- WZSetup.exe (PID: 7252)
- UnifiedStub-installer.exe (PID: 5308)
- rsWSC.exe (PID: 5580)
- WeatherZero.exe (PID: 5772)
- rsEngineSvc.exe (PID: 6368)
- rsEDRSvc.exe (PID: 3356)
- rsVPNSvc.exe (PID: 8736)
- rsDNSSvc.exe (PID: 8928)
- rsDNSSvc.exe (PID: 5448)
Executable content was dropped or overwritten
- mouse-without-borders_iqqX0-1.exe (PID: 7576)
- mouse-without-borders_iqqX0-1.exe (PID: 7784)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- xclwscmn.exe (PID: 2120)
- WZSetup.exe (PID: 7252)
- UnifiedStub-installer.exe (PID: 5308)
- csc.exe (PID: 6764)
Reads the date of Windows installation
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
- prod0.exe (PID: 1572)
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 8060)
Reads the Windows owner or organization settings
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
Access to an unwanted program domain was detected
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
There is functionality for taking screenshot (YARA)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
Process drops legitimate windows executable
- xclwscmn.exe (PID: 2120)
- UnifiedStub-installer.exe (PID: 5308)
Searches for installed software
- UnifiedStub-installer.exe (PID: 5308)
- WZSetup.exe (PID: 7252)
- rsVPNSvc.exe (PID: 8812)
- rsDNSSvc.exe (PID: 5448)
Non windows owned service launched
- rsSyncSvc.exe (PID: 7228)
- WeatherZeroService.exe (PID: 7888)
- rsWSC.exe (PID: 5724)
- rsClientSvc.exe (PID: 5648)
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 8060)
- rsVPNClientSvc.exe (PID: 8700)
- rsVPNSvc.exe (PID: 8812)
- rsDNSClientSvc.exe (PID: 2396)
- rsDNSResolver.exe (PID: 2720)
- rsDNSSvc.exe (PID: 5448)
Executes as Windows Service
- rsSyncSvc.exe (PID: 7228)
- WeatherZeroService.exe (PID: 7888)
- rsWSC.exe (PID: 5724)
- rsClientSvc.exe (PID: 5648)
- rsEngineSvc.exe (PID: 5336)
- PresentationFontCache.exe (PID: 6168)
- rsEDRSvc.exe (PID: 8060)
- rsVPNClientSvc.exe (PID: 8700)
- rsVPNSvc.exe (PID: 8812)
- WmiApSrv.exe (PID: 8304)
- rsDNSResolver.exe (PID: 2720)
- rsDNSClientSvc.exe (PID: 2396)
- rsDNSSvc.exe (PID: 5448)
The process creates files with name similar to system file names
- UnifiedStub-installer.exe (PID: 5308)
The process drops C-runtime libraries
- UnifiedStub-installer.exe (PID: 5308)
Drops 7-zip archiver for unpacking
- UnifiedStub-installer.exe (PID: 5308)
Drops a system driver (possible attempt to evade defenses)
- UnifiedStub-installer.exe (PID: 5308)
Adds/modifies Windows certificates
- rsWSC.exe (PID: 5580)
- UnifiedStub-installer.exe (PID: 5308)
- rsEngineSvc.exe (PID: 5336)
Creates or modifies Windows services
- UnifiedStub-installer.exe (PID: 5308)
Creates files in the driver directory
- UnifiedStub-installer.exe (PID: 5308)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- UnifiedStub-installer.exe (PID: 5308)
Uses .NET C# to load dll
- WeatherZero.exe (PID: 5772)
Checks for external IP
- svchost.exe (PID: 2276)
Reads the BIOS version
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 8060)
Process checks is Powershell's Script Block Logging on
- rsEDRSvc.exe (PID: 8060)
Application launched itself
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 8956)
- rsAppUI.exe (PID: 2764)
Uses RUNDLL32.EXE to load library
- UnifiedStub-installer.exe (PID: 5308)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 1312)
Starts CMD.EXE for commands execution
- rsDNSSvc.exe (PID: 5448)
INFO
Reads Environment values
- mouse-without-borders_iqqX0-1.exe (PID: 7576)
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
- mouse-without-borders_iqqX0-1.exe (PID: 7784)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- UnifiedStub-installer.exe (PID: 5308)
- rsEngineSvc.exe (PID: 5336)
- rsAppUI.exe (PID: 2816)
- rsEDRSvc.exe (PID: 8060)
- rsVPNSvc.exe (PID: 8812)
- rsAppUI.exe (PID: 8956)
- rsDNSSvc.exe (PID: 5448)
Reads the computer name
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
- mouse-without-borders_iqqX0-1.exe (PID: 7784)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- UnifiedStub-installer.exe (PID: 5308)
- WZSetup.exe (PID: 7252)
- rsSyncSvc.exe (PID: 2160)
- rsSyncSvc.exe (PID: 7228)
- WeatherZeroService.exe (PID: 4452)
- WeatherZeroService.exe (PID: 7916)
- WeatherZeroService.exe (PID: 7888)
- rsWSC.exe (PID: 5580)
- rsWSC.exe (PID: 5724)
- rsClientSvc.exe (PID: 5488)
- rsClientSvc.exe (PID: 5648)
- rsEngineSvc.exe (PID: 6368)
- rsEngineSvc.exe (PID: 5336)
- WeatherZero.exe (PID: 5772)
- PresentationFontCache.exe (PID: 6168)
- rsEDRSvc.exe (PID: 3356)
- rsEDRSvc.exe (PID: 8060)
- rsHelper.exe (PID: 7520)
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 7880)
- rsAppUI.exe (PID: 5604)
- rsVPNClientSvc.exe (PID: 8644)
- rsVPNClientSvc.exe (PID: 8700)
- rsVPNSvc.exe (PID: 8736)
- rsVPNSvc.exe (PID: 8812)
- rsAppUI.exe (PID: 8956)
- rsAppUI.exe (PID: 5048)
- rsAppUI.exe (PID: 864)
- rsDNSClientSvc.exe (PID: 9164)
- rsDNSClientSvc.exe (PID: 2396)
- rsDNSResolver.exe (PID: 8772)
- rsDNSSvc.exe (PID: 8928)
- rsDNSResolver.exe (PID: 2720)
- rsDNSSvc.exe (PID: 5448)
- rsAppUI.exe (PID: 2764)
- rsAppUI.exe (PID: 476)
- rsAppUI.exe (PID: 2032)
Checks supported languages
- mouse-without-borders_iqqX0-1.exe (PID: 7576)
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
- mouse-without-borders_iqqX0-1.exe (PID: 7784)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- WZSetup.exe (PID: 7252)
- xclwscmn.exe (PID: 2120)
- UnifiedStub-installer.exe (PID: 5308)
- rsSyncSvc.exe (PID: 2160)
- rsSyncSvc.exe (PID: 7228)
- WeatherZeroService.exe (PID: 4452)
- WeatherZeroService.exe (PID: 7916)
- WeatherZeroService.exe (PID: 7888)
- rsWSC.exe (PID: 5580)
- rsClientSvc.exe (PID: 5488)
- rsEngineSvc.exe (PID: 6368)
- rsClientSvc.exe (PID: 5648)
- rsWSC.exe (PID: 5724)
- rsEngineSvc.exe (PID: 5336)
- WeatherZero.exe (PID: 5772)
- csc.exe (PID: 6764)
- cvtres.exe (PID: 7180)
- PresentationFontCache.exe (PID: 6168)
- rsEDRSvc.exe (PID: 3356)
- rsEDRSvc.exe (PID: 8060)
- rsHelper.exe (PID: 7520)
- rsLitmus.A.exe (PID: 5036)
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 7880)
- EPP.exe (PID: 8136)
- rsVPNClientSvc.exe (PID: 8700)
- rsAppUI.exe (PID: 5604)
- rsAppUI.exe (PID: 7620)
- rsVPNClientSvc.exe (PID: 8644)
- rsVPNSvc.exe (PID: 8736)
- rsVPNSvc.exe (PID: 8812)
- VPN.exe (PID: 8936)
- rsAppUI.exe (PID: 8956)
- rsAppUI.exe (PID: 5048)
- rsAppUI.exe (PID: 5696)
- rsAppUI.exe (PID: 864)
- rsAppUI.exe (PID: 7552)
- rsDNSClientSvc.exe (PID: 9164)
- rsDNSResolver.exe (PID: 8772)
- rsDNSClientSvc.exe (PID: 2396)
- rsDNSSvc.exe (PID: 8928)
- rsDNSResolver.exe (PID: 2720)
- rsDNSSvc.exe (PID: 5448)
- rsAppUI.exe (PID: 2764)
- rsAppUI.exe (PID: 476)
- rsAppUI.exe (PID: 2032)
- DNS.exe (PID: 7852)
- rsAppUI.exe (PID: 1060)
Process checks computer location settings
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 7620)
- rsVPNSvc.exe (PID: 8812)
- rsAppUI.exe (PID: 8956)
- rsAppUI.exe (PID: 7552)
- rsAppUI.exe (PID: 5696)
- rsAppUI.exe (PID: 2764)
- rsAppUI.exe (PID: 1060)
Create files in a temporary directory
- mouse-without-borders_iqqX0-1.exe (PID: 7576)
- mouse-without-borders_iqqX0-1.exe (PID: 7784)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- WZSetup.exe (PID: 7252)
- xclwscmn.exe (PID: 2120)
- UnifiedStub-installer.exe (PID: 5308)
- WeatherZero.exe (PID: 5772)
- cvtres.exe (PID: 7180)
- csc.exe (PID: 6764)
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 8956)
- rsAppUI.exe (PID: 2764)
The sample compiled with english language support
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- xclwscmn.exe (PID: 2120)
- WZSetup.exe (PID: 7252)
- UnifiedStub-installer.exe (PID: 5308)
Detects InnoSetup installer (YARA)
- mouse-without-borders_iqqX0-1.exe (PID: 7576)
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
- mouse-without-borders_iqqX0-1.exe (PID: 7784)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
Compiled with Borland Delphi (YARA)
- mouse-without-borders_iqqX0-1.exe (PID: 7784)
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- mouse-without-borders_iqqX0-1.exe (PID: 7576)
- mouse-without-borders_iqqX0-1.tmp (PID: 7600)
Reads the software policy settings
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- WZSetup.exe (PID: 7252)
- UnifiedStub-installer.exe (PID: 5308)
- rsWSC.exe (PID: 5580)
- WeatherZero.exe (PID: 5772)
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 3356)
- rsWSC.exe (PID: 5724)
- rsEDRSvc.exe (PID: 8060)
- rsVPNSvc.exe (PID: 8736)
- rsVPNSvc.exe (PID: 8812)
- rsDNSSvc.exe (PID: 8928)
- slui.exe (PID: 5232)
- rsDNSSvc.exe (PID: 5448)
Reads the machine GUID from the registry
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- WZSetup.exe (PID: 7252)
- UnifiedStub-installer.exe (PID: 5308)
- WeatherZeroService.exe (PID: 7916)
- WeatherZeroService.exe (PID: 7888)
- rsWSC.exe (PID: 5580)
- rsWSC.exe (PID: 5724)
- rsEngineSvc.exe (PID: 6368)
- rsEngineSvc.exe (PID: 5336)
- WeatherZero.exe (PID: 5772)
- csc.exe (PID: 6764)
- cvtres.exe (PID: 7180)
- PresentationFontCache.exe (PID: 6168)
- rsEDRSvc.exe (PID: 3356)
- rsHelper.exe (PID: 7520)
- rsEDRSvc.exe (PID: 8060)
- rsAppUI.exe (PID: 2816)
- rsVPNSvc.exe (PID: 8812)
- rsVPNSvc.exe (PID: 8736)
- rsAppUI.exe (PID: 8956)
- rsDNSSvc.exe (PID: 8928)
- rsDNSSvc.exe (PID: 5448)
- rsAppUI.exe (PID: 2764)
Checks proxy server information
- mouse-without-borders_iqqX0-1.tmp (PID: 7824)
- prod0.exe (PID: 1572)
- WZSetup.exe (PID: 7252)
- UnifiedStub-installer.exe (PID: 5308)
- rsWSC.exe (PID: 5580)
- WeatherZero.exe (PID: 5772)
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 8956)
- slui.exe (PID: 5232)
- rsAppUI.exe (PID: 2764)
- rsDNSSvc.exe (PID: 5448)
Disables trace logs
- prod0.exe (PID: 1572)
- UnifiedStub-installer.exe (PID: 5308)
- WeatherZero.exe (PID: 5772)
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 8060)
- rsVPNSvc.exe (PID: 8812)
- rsDNSSvc.exe (PID: 5448)
Creates files or folders in the user directory
- WZSetup.exe (PID: 7252)
- UnifiedStub-installer.exe (PID: 5308)
- rsWSC.exe (PID: 5580)
- WeatherZero.exe (PID: 5772)
- rsEngineSvc.exe (PID: 5336)
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 5604)
- rsVPNSvc.exe (PID: 8812)
- rsAppUI.exe (PID: 8956)
- rsAppUI.exe (PID: 5048)
- rsDNSSvc.exe (PID: 5448)
- rsAppUI.exe (PID: 2764)
- rsAppUI.exe (PID: 2032)
Creates files in the program directory
- UnifiedStub-installer.exe (PID: 5308)
- WZSetup.exe (PID: 7252)
- rsWSC.exe (PID: 5580)
- rsEngineSvc.exe (PID: 6368)
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 3356)
- rsEDRSvc.exe (PID: 8060)
- rsVPNSvc.exe (PID: 8812)
- rsVPNSvc.exe (PID: 8736)
- rsDNSResolver.exe (PID: 8772)
- rsDNSSvc.exe (PID: 8928)
- rsDNSSvc.exe (PID: 5448)
- rsDNSResolver.exe (PID: 2720)
Creates a software uninstall entry
- UnifiedStub-installer.exe (PID: 5308)
- WZSetup.exe (PID: 7252)
SQLite executable
- UnifiedStub-installer.exe (PID: 5308)
.NET Reactor protector has been detected
- UnifiedStub-installer.exe (PID: 5308)
Reads CPU info
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 8060)
- rsVPNSvc.exe (PID: 8812)
Reads the time zone
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 8060)
- rsVPNSvc.exe (PID: 8812)
- runonce.exe (PID: 480)
Reads product name
- rsEngineSvc.exe (PID: 5336)
- rsEDRSvc.exe (PID: 8060)
- rsAppUI.exe (PID: 2816)
- rsAppUI.exe (PID: 8956)
Launching a file from a Registry key
- rundll32.exe (PID: 7856)
Reads security settings of Internet Explorer
- runonce.exe (PID: 480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:03 14:45:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 704512 |
| InitializedDataSize: | 162304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xacfe0 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.0.9298 |
| ProductVersionNumber: | 2.4.0.9298 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Portale delle applicazioni |
| FileVersion: | 2.4.0.9298 |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Applicazioni Windows |
| ProductVersion: | 2.4.0.9298 |
Total processes
225
Monitored processes
73
Malicious processes
9
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\ReasonLabs\DNS" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAEAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --field-trial-handle=1716,i,3010657919324195353,16054995563478897228,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=1724 /prefetch:2 | C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe | — | rsAppUI.exe | |||||||||||
User: admin Company: Reason Cybersecurity Ltd. Integrity Level: LOW Description: ReasonLabs Application Version: 1.6.0 Modules
| |||||||||||||||
| 480 | "C:\WINDOWS\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\ReasonLabs\VPN" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAEAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --field-trial-handle=2252,i,14703727140371633449,16617646648978282408,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2244 /prefetch:2 | C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe | — | rsAppUI.exe | |||||||||||
User: admin Company: Reason Cybersecurity Ltd. Integrity Level: LOW Description: ReasonLabs Application Version: 1.6.0 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\ReasonLabs\DNS" --app-user-model-id=com.reasonlabs.dns --app-path="C:\Program Files\ReasonLabs\Common\Client\v1.6.0\resources\app.asar" --enable-sandbox --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=2404,i,3010657919324195353,16054995563478897228,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2400 /prefetch:1 | C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe | — | rsAppUI.exe | |||||||||||
User: admin Company: Reason Cybersecurity Ltd. Integrity Level: LOW Description: ReasonLabs Application Version: 1.6.0 Modules
| |||||||||||||||
| 1312 | "cmd.exe" /C ipconfig /flushdns | C:\Windows\System32\cmd.exe | — | rsDNSSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1572 | "C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\prod0.exe" -ip:"dui=bb926e54-e3ca-40fd-ae90-2764341e7792&dit=20251103010352&is_silent=true&oc=ZB_RAV_Cross_Tri_NCB&p=f4cc&a=100&b=ch" -vp:"dui=bb926e54-e3ca-40fd-ae90-2764341e7792&dit=20251103010352&oc=ZB_RAV_Cross_Tri_NCB&p=f4cc&a=100&oip=26&ptl=7&dta=true" -dp:"dui=bb926e54-e3ca-40fd-ae90-2764341e7792&dit=20251103010352&oc=ZB_RAV_Cross_Tri_NCB&p=f4cc&a=100" -i -v -d | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\prod0.exe | mouse-without-borders_iqqX0-1.tmp | ||||||||||||
User: admin Company: Reason Software Company Inc. Integrity Level: HIGH Description: rsStubActivator Exit code: 0 Version: 1.6.1.0 Modules
| |||||||||||||||
| 1836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rsDNSResolver.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | "C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\ReasonLabs\DNS" --field-trial-handle=2096,i,3010657919324195353,16054995563478897228,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2092 /prefetch:3 | C:\Program Files\ReasonLabs\Common\Client\v1.6.0\rsAppUI.exe | rsAppUI.exe | ||||||||||||
User: admin Company: Reason Cybersecurity Ltd. Integrity Level: MEDIUM Description: ReasonLabs Application Version: 1.6.0 Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Local\Temp\xclwscmn.exe" /silent | C:\Users\admin\AppData\Local\Temp\xclwscmn.exe | prod0.exe | ||||||||||||
User: admin Company: ReasonLabs Integrity Level: HIGH Description: ReasonLabs-setup-wizard.exe Exit code: 0 Version: 6.3.2 Modules
| |||||||||||||||
Total events
88 373
Read events
87 841
Write events
333
Delete events
199
Modification events
| (PID) Process: | (7824) mouse-without-borders_iqqX0-1.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E9070B00010003000100040010004E01010000001E768127E028094199FEB9D127C57AFE | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1572) prod0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\prod0_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
867
Suspicious files
319
Text files
88
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\is-TEC6U.tmp | image | |
MD5:CD09F361286D1AD2622BA8A57B7613BD | SHA256:B92A31D4853D1B2C4E5B9D9624F40B439856D0C6A517E100978CBDE8D3C47DC8 | |||
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\loader.gif | image | |
MD5:12D7FD91A06CEE2D0E76ABE0485036EE | SHA256:A6192B9A3FA5DB9917AEF72D651B7AD8FD8CCB9B53F3AD99D7C46701D00C78CB | |||
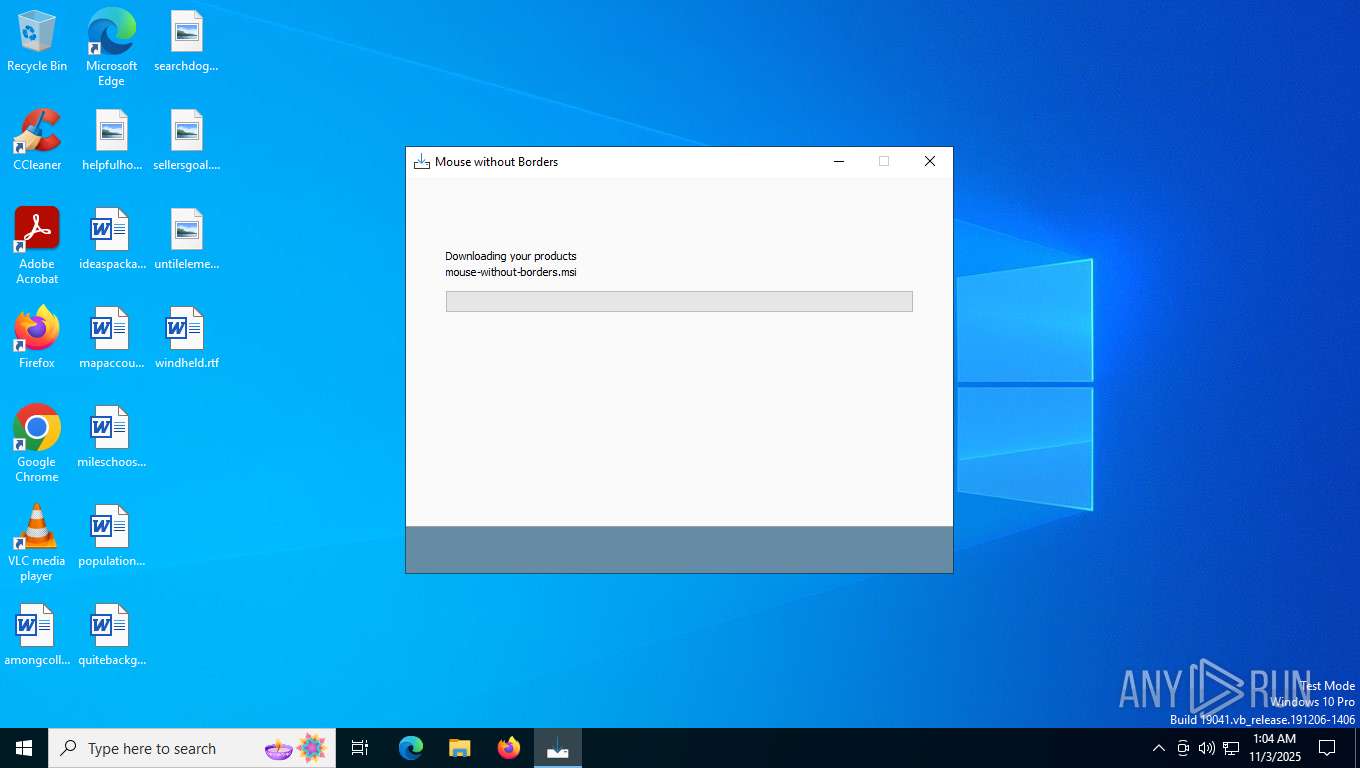
| 7784 | mouse-without-borders_iqqX0-1.exe | C:\Users\admin\AppData\Local\Temp\is-N0LCT.tmp\mouse-without-borders_iqqX0-1.tmp | executable | |
MD5:60C6EAA0CEEFDB49F7F667EE815D39DC | SHA256:0DEB82B58C4A2A54492CC612F17783A5B6C16F6EDA0F9B3DF093F9ABE88DA03E | |||
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\finish.png | image | |
MD5:FC70780968D3724313DABACDC3E43FCE | SHA256:CD84EF0D866E5D0969D1E6BCCE97C4408F9268C657D24BE578CB65FF056F0A14 | |||
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\mainlogo.png | image | |
MD5:FC89AF14F854B49725B6B136B5F86018 | SHA256:1836E1FD93897647B8F667017162993D9BBE5F9E3ED255E6DAD4BB99B1A55AB8 | |||
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\WeatherZero.png | image | |
MD5:9AC6287111CB2B272561781786C46CDD | SHA256:AB99CDB7D798CB7B7D8517584D546AA4ED54ECA1B808DE6D076710C8A400C8C4 | |||
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\is-L8IQL.tmp | image | |
MD5:9AC6287111CB2B272561781786C46CDD | SHA256:AB99CDB7D798CB7B7D8517584D546AA4ED54ECA1B808DE6D076710C8A400C8C4 | |||
| 7576 | mouse-without-borders_iqqX0-1.exe | C:\Users\admin\AppData\Local\Temp\is-6QTT8.tmp\mouse-without-borders_iqqX0-1.tmp | executable | |
MD5:60C6EAA0CEEFDB49F7F667EE815D39DC | SHA256:0DEB82B58C4A2A54492CC612F17783A5B6C16F6EDA0F9B3DF093F9ABE88DA03E | |||
| 7824 | mouse-without-borders_iqqX0-1.tmp | C:\Users\admin\AppData\Local\Temp\is-DBDUA.tmp\RAV_Cross.png | image | |
MD5:CD09F361286D1AD2622BA8A57B7613BD | SHA256:B92A31D4853D1B2C4E5B9D9624F40B439856D0C6A517E100978CBDE8D3C47DC8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
158
DNS requests
50
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7252 | WZSetup.exe | GET | 200 | 142.250.185.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
5308 | UnifiedStub-installer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTDHsfuqfubd3pihvq4mgQVWgHWNwQUyH7SaoUqG8oZmAQHJ89QEE9oqKICEzMAAAAHh6M0o3uljhwAAAAAAAc%3D | unknown | — | — | whitelisted |
5308 | UnifiedStub-installer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRBq81UG1MnDOVNKqff0SSEz6JuZwQU6IPEM9fcnwycdpoKptTfh6ZeWO4CEzMABSdpHv5L0ZWBpxUAAAAFJ2k%3D | unknown | — | — | whitelisted |
5308 | UnifiedStub-installer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTOQYLFSE5GO%2FpaRVfYu7d9gZEbQAQU2UEpsA8PY2zvadf1zSmepEhqMOYCEzMAAAAHN4xbodlbjNQAAAAAAAc%3D | unknown | — | — | whitelisted |
5308 | UnifiedStub-installer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRBq81UG1MnDOVNKqff0SSEz6JuZwQU6IPEM9fcnwycdpoKptTfh6ZeWO4CEzMABSdpHv5L0ZWBpxUAAAAFJ2k%3D | unknown | — | — | whitelisted |
5308 | UnifiedStub-installer.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ID%20Verified%20CS%20AOC%20CA%2001.crl | unknown | — | — | whitelisted |
5308 | UnifiedStub-installer.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Identity%20Verification%20Root%20Certificate%20Authority%202020.crl | unknown | — | — | whitelisted |
5580 | rsWSC.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQCeArDpSs6yEJyh6YNr4MLb | unknown | — | — | whitelisted |
5308 | UnifiedStub-installer.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Public%20RSA%20Timestamping%20CA%202020.crl | unknown | — | — | whitelisted |
5772 | WeatherZero.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2316 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6264 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7088 | SearchApp.exe | 92.123.104.38:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2316 | svchost.exe | 23.55.48.8:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
7824 | mouse-without-borders_iqqX0-1.tmp | 18.64.16.46:443 | djloiq2ki6v9p.cloudfront.net | — | US | malicious |
7824 | mouse-without-borders_iqqX0-1.tmp | 104.20.29.174:443 | static.download.it | CLOUDFLARENET | — | whitelisted |
5460 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
djloiq2ki6v9p.cloudfront.net |
| malicious |
static.download.it |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | A Network Trojan was detected | ET ADWARE_PUP Win32/OfferCore Checkin M1 |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | A Network Trojan was detected | ET ADWARE_PUP Win32/OfferCore Checkin M2 |
— | — | Possibly Unwanted Program Detected | ADWARE [ANY.RUN] InnoSetup Installer |
— | — | Possibly Unwanted Program Detected | ADWARE [ANY.RUN] InnoSetup Installer |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | A Network Trojan was detected | ET ADWARE_PUP Win32/OfferCore Checkin M2 |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | A Network Trojan was detected | ET ADWARE_PUP Win32/OfferCore Checkin M2 |
Process | Message |
|---|---|
rsEngineSvc.exe | [rsExceptionFilter] [InstallExceptionFilter] Installed Exception Filter |
rsEngineSvc.exe | [rsExceptionFilter] [InstallExceptionFilter] Installed Exception Filter |
rsEngineSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\ReasonLabs\EPP\x64\SQLite.Interop.dll"...
|
WeatherZero.exe | Load config error: System.InvalidOperationException: There is an error in XML document (0, 0). ---> System.Xml.XmlException: Root element is missing.
at System.Xml.XmlTextReaderImpl.Throw(Exception e)
at System.Xml.XmlTextReaderImpl.ThrowWithoutLineInfo(String res)
at System.Xml.XmlTextReaderImpl.ParseDocumentContent()
at System.Xml.XmlTextReaderImpl.Read()
at System.Xml.XmlTextReader.Read()
at System.Xml.XmlReader.MoveToContent()
at Microsoft.Xml.Serialization.GeneratedAssembly.XmlSerializationReaderWFSettings.Read5_WFSettings()
--- End of inner exception stack trace ---
at System.Xml.Serialization.XmlSerializer.Deserialize(XmlReader xmlReader, String encodingStyle, XmlDeserializationEvents events)
at System.Xml.Serialization.XmlSerializer.Deserialize(TextReader textReader)
at WeatherZero.Config`1.Load()
|
WeatherZero.exe | Load config error: System.InvalidOperationException: There is an error in XML document (0, 0). ---> System.Xml.XmlException: Root element is missing.
at System.Xml.XmlTextReaderImpl.Throw(Exception e)
at System.Xml.XmlTextReaderImpl.ThrowWithoutLineInfo(String res)
at System.Xml.XmlTextReaderImpl.ParseDocumentContent()
at System.Xml.XmlTextReaderImpl.Read()
at System.Xml.XmlTextReader.Read()
at System.Xml.XmlReader.MoveToContent()
at Microsoft.Xml.Serialization.GeneratedAssembly.XmlSerializationReaderWFSettings.Read5_WFSettings()
--- End of inner exception stack trace ---
at System.Xml.Serialization.XmlSerializer.Deserialize(XmlReader xmlReader, String encodingStyle, XmlDeserializationEvents events)
at System.Xml.Serialization.XmlSerializer.Deserialize(TextReader textReader)
at WeatherZero.Config`1.Load()
|
WeatherZero.exe | Get weather thread started
|
WeatherZero.exe | ter)
at System.Windows.Threading.ExceptionWrapper.TryCatchWhen(Object source, Delegate callback, Object args, Boolean isSingleParameter, Delegate catchHandler)
WRN: Assembly binding logging is turned OFF.
To enable assembly bind failure logging, set the registry value [HKLM\Software\Microsoft\Fusion!EnableLog] (DWORD) to 1.
Note: There is some performance penalty associated with assembly bind failure logging.
To turn this feature off, remove the registry value [HKLM\Software\Microsoft\Fusion!EnableLog].
|
WeatherZero.exe | Unhandled exception
System.IO.FileLoadException: Could not load file or assembly 'WeatherZero, Culture=neutral' or one of its dependencies. The located assembly's manifest definition does not match the assembly reference. (Exception from HRESULT: 0x80131040)
File name: 'WeatherZero, Culture=neutral'
at System.Reflection.Assembly._nLoad(AssemblyName fileName, String codeBase, Evidence assemblySecurity, Assembly locationHint, StackCrawlMark& stackMark, Boolean throwOnFileNotFound, Boolean forIntrospection)
at System.Reflection.Assembly.nLoad(AssemblyName fileName, String codeBase, Evidence assemblySecurity, Assembly locationHint, StackCrawlMark& stackMark, Boolean throwOnFileNotFound, Boolean forIntrospection)
at System.Reflection.Assembly.InternalLoad(AssemblyName assemblyRef, Evidence assemblySecurity, StackCrawlMark& stackMark, Boolean forIntrospection)
at System.Reflection.Assembly.Load(AssemblyName assemblyRef)
at System.Windows.Navigation.BaseUriHelper.GetLoadedAssembly(String assemblyName, String assemblyVersion, String assemblyKey)
at MS.Internal.AppModel.ResourceContainer.GetResourceManagerWrapper(Uri uri, String& partName, Boolean& isContentFile)
at MS.Internal.AppModel.ResourceContainer.GetPartCore(Uri uri)
at System.IO.Packaging.Package.GetPartHelper(Uri partUri)
at System.IO.Packaging.Package.GetPart(Uri partUri)
at System.IO.Packaging.PackWebResponse.CachedResponse.GetResponseStream()
at System.IO.Packaging.PackWebResponse.GetResponseStream()
at System.IO.Packaging.PackWebResponse.get_ContentType()
at System.Windows.Media.Imaging.BitmapDecoder.SetupDecoderFromUriOrStream(Uri uri, Stream stream, BitmapCacheOption cacheOption, Guid& clsId, Boolean& isOriginalWritable, Stream& uriStream, UnmanagedMemoryStream& unmanagedMemoryStream, SafeFileHandle& safeFilehandle)
at System.Windows.Media.Imaging.BitmapDecoder.CreateFromUriOrStream(Uri baseUri, Uri uri, Stream stream, BitmapCreateOptions createOptions, BitmapCacheOption cacheOption, RequestCachePolicy uriCachePolicy, Boolean insertInDecoderCache)
at System.Windows.Media.Imaging.BitmapImage.FinalizeCreation()
at System.Windows.Media.Imaging.BitmapImage.EndInit()
at System.Windows.Media.Imaging.BitmapImage..ctor(Uri uriSource, RequestCachePolicy uriCachePolicy)
at System.Windows.Media.Imaging.BitmapImage..ctor(Uri uriSource)
at WeatherZero.MainWindow.OnWindowLoaded(Object sender, RoutedEventArgs e)
at System.Windows.RoutedEventHandlerInfo.InvokeHandler(Object target, RoutedEventArgs routedEventArgs)
at System.Windows.EventRoute.InvokeHandlersImpl(Object source, RoutedEventArgs args, Boolean reRaised)
at System.Windows.UIElement.RaiseEventImpl(DependencyObject sender, RoutedEventArgs args)
at System.Windows.UIElement.RaiseEvent(RoutedEventArgs e)
at System.Windows.BroadcastEventHelper.BroadcastEvent(DependencyObject root, RoutedEvent routedEvent)
at System.Windows.BroadcastEventHelper.BroadcastLoadedEvent(Object root)
at MS.Internal.LoadedOrUnloadedOperation.DoWork()
at System.Windows.Media.MediaContext.FireLoadedPendingCallbacks()
at System.Windows.Media.MediaContext.FireInvokeOnRenderCallbacks()
at System.Windows.Media.MediaContext.RenderMessageHandlerCore(Object resizedCompositionTarget)
at System.Windows.Media.MediaContext.RenderMessageHandler(Object resizedCompositionTarget)
at System.Windows.Media.MediaContext.Resize(ICompositionTarget resizedCompositionTarget)
at System.Windows.Interop.HwndTarget.OnResize()
at System.Windows.Interop.HwndTarget.HandleMessage(Int32 msg, IntPtr wparam, IntPtr lparam)
at System.Windows.Interop.HwndSource.HwndTargetFilterMessage(IntPtr hwnd, Int32 msg, IntPtr wParam, IntPtr lParam, Boolean& handled)
at MS.Win32.HwndWrapper.WndProc(IntPtr hwnd, Int32 msg, IntPtr wParam, IntPtr lParam, Boolean& handled)
at MS.Win32.HwndSubclass.DispatcherCallbackOperation(Object o)
at System.Windows.Threading.ExceptionWrapper.InternalRealCall(Delegate callback, Object args, Boolean isSingleParame |
WeatherZero.exe | http://api.openweathermap.org/data/2.5/weather?zip=0031,no&units=imperial&appid=70297443c6fd8391e3fc4b7b0d344ae5
|
WeatherZero.exe | {"coord":{"lon":10.7461,"lat":59.9127},"weather":[{"id":804,"main":"Clouds","description":"overcast clouds","icon":"04n"}],"base":"stations","main":{"temp":43.25,"feels_like":41.25,"temp_min":43.25,"temp_max":43.25,"pressure":1005,"humidity":96,"sea_level":1005,"grnd_level":980},"visibility":10000,"wind":{"speed":3.8,"deg":199,"gust":11.81},"clouds":{"all":100},"dt":1762131747,"sys":{"type":2,"id":237284,"country":"NO","sunrise":1762152235,"sunset":1762183030},"timezone":3600,"id":0,"name":"Oslo","cod":200}
|