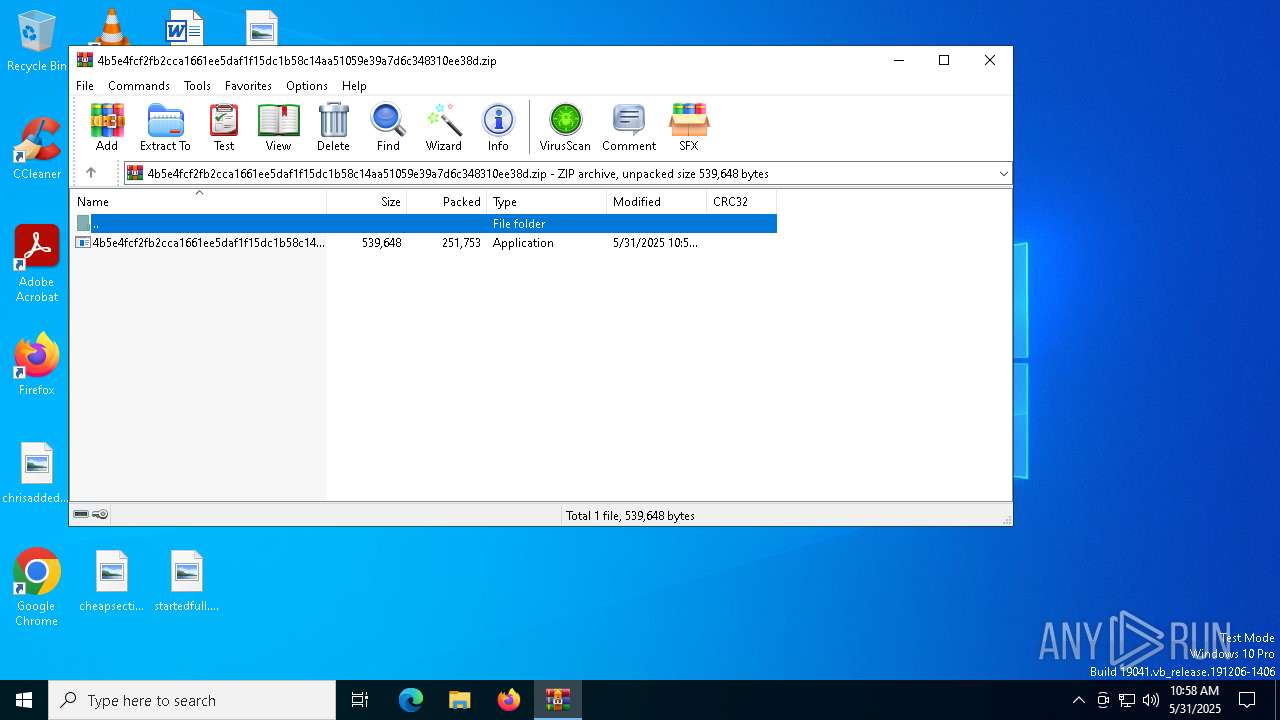
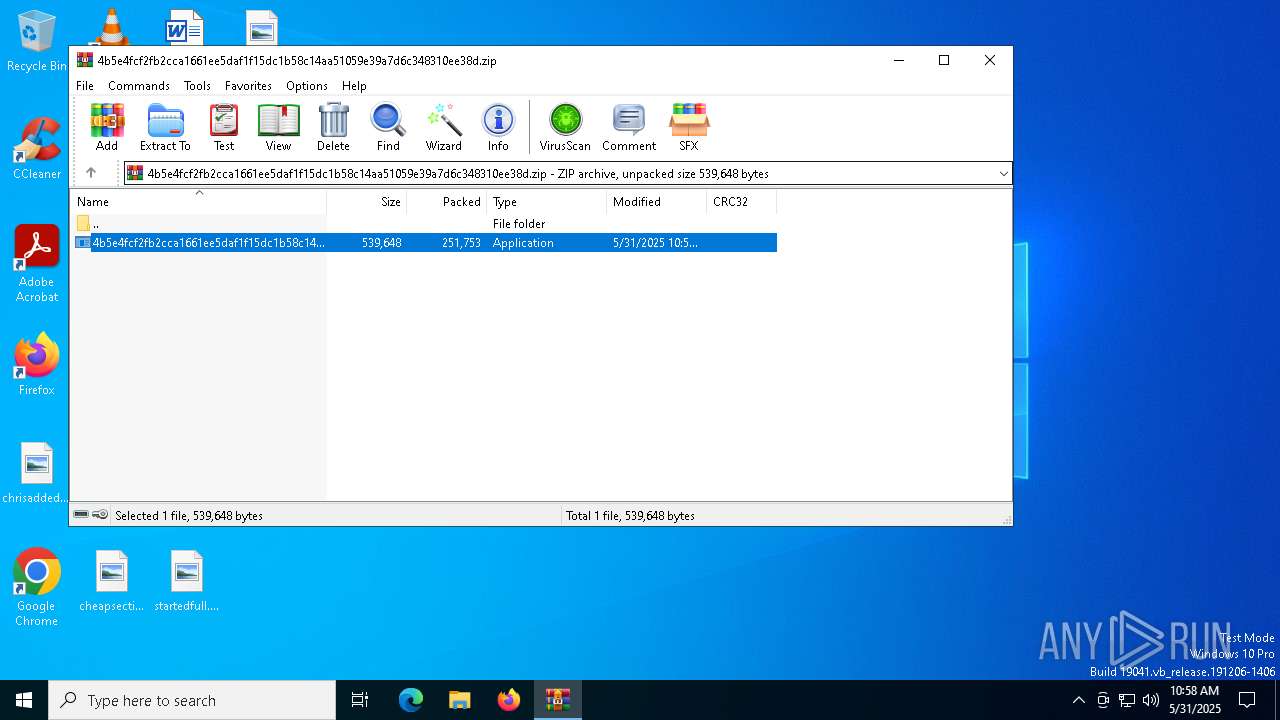
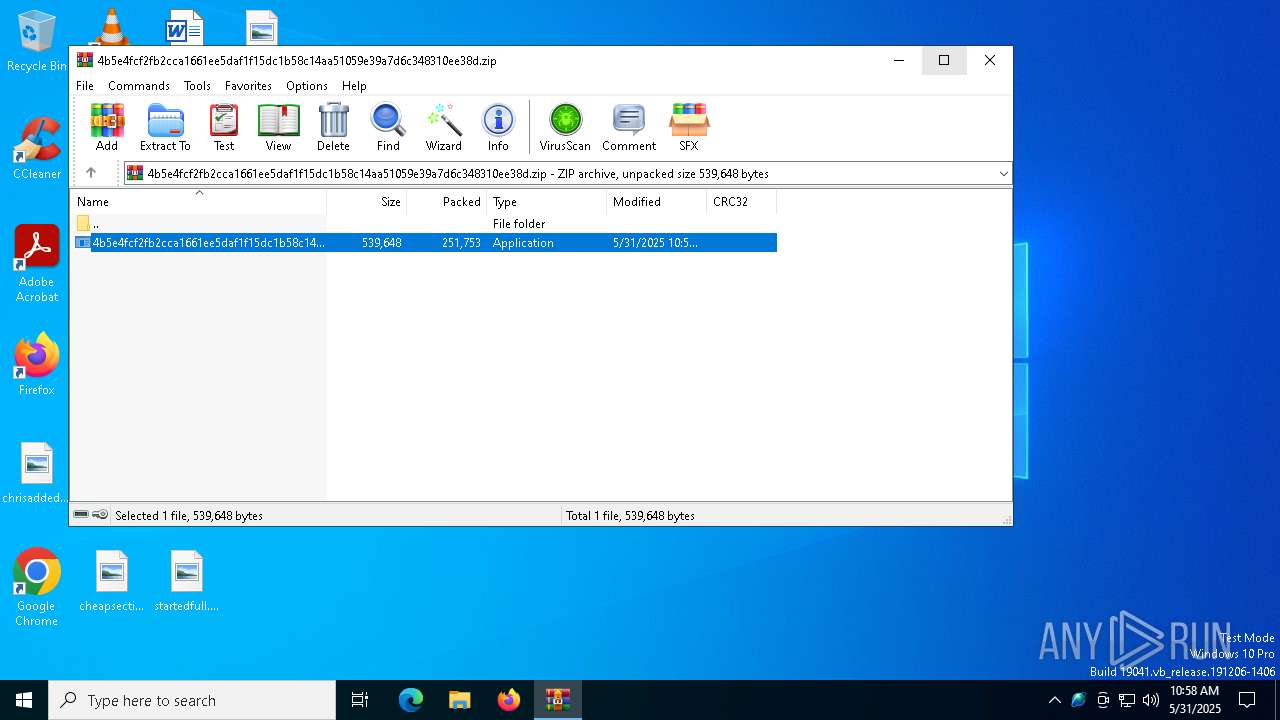
| File name: | 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.zip |
| Full analysis: | https://app.any.run/tasks/0af37333-467b-4965-8d3c-bfbe96650de4 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | May 31, 2025, 10:58:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
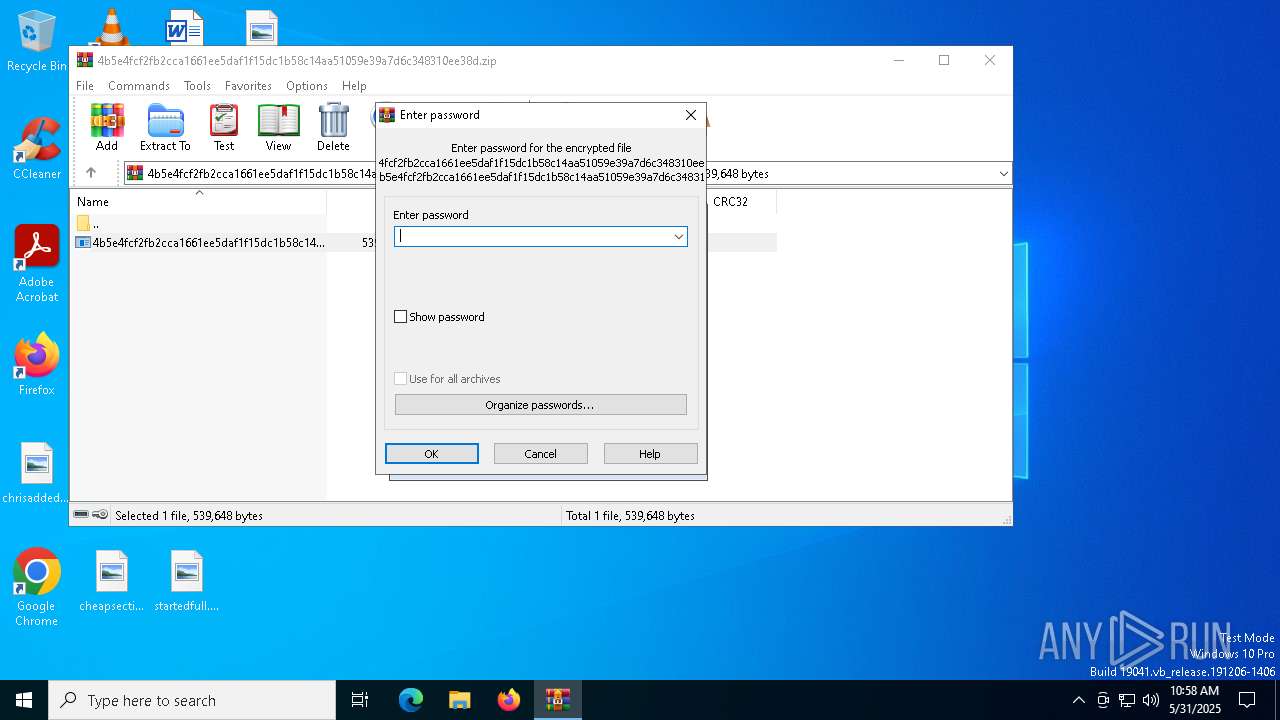
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 957799C0699C8EF89394268EF6B60E0B |
| SHA1: | 8A4F7A0ED9D9CA5E60C93AA5FD86EAA33669B854 |
| SHA256: | E65EA1159C06ACE37E1F0DDA84FF248E68E80718D414A2D9E1113FAABF362788 |
| SSDEEP: | 12288:C9JKqXL8z6I6NaOePPMmqJBDlPe91oI9er:CiqXL8z6hNaOAMmqJNlPe96I9er |
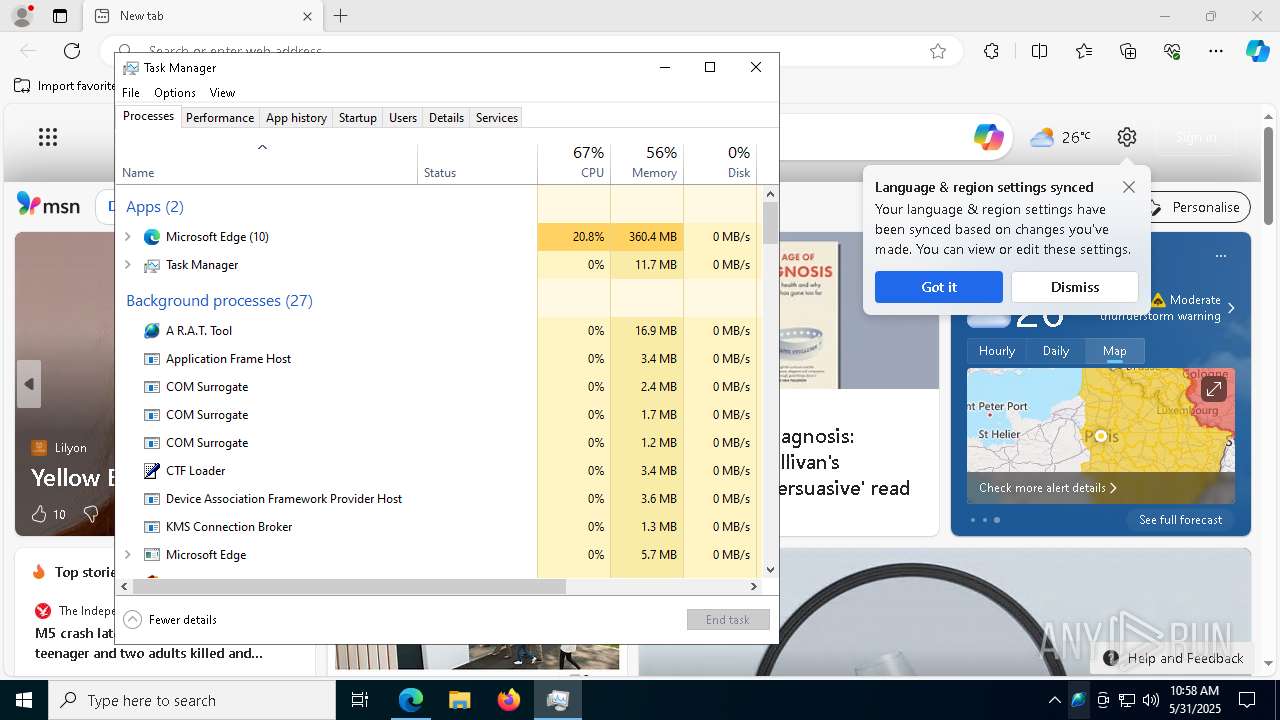
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6940)
Changes the autorun value in the registry
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
- Java.exe (PID: 4784)
QUASAR has been detected (YARA)
- Java.exe (PID: 4784)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6940)
Executable content was dropped or overwritten
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
Starts itself from another location
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
There is functionality for taking screenshot (YARA)
- Java.exe (PID: 4784)
INFO
Reads the machine GUID from the registry
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
- Java.exe (PID: 4784)
Reads the computer name
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
- identity_helper.exe (PID: 4404)
- Java.exe (PID: 4784)
Creates files or folders in the user directory
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
Checks supported languages
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
- identity_helper.exe (PID: 4404)
- Java.exe (PID: 4784)
Reads Environment values
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
- identity_helper.exe (PID: 4404)
- Java.exe (PID: 4784)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6940)
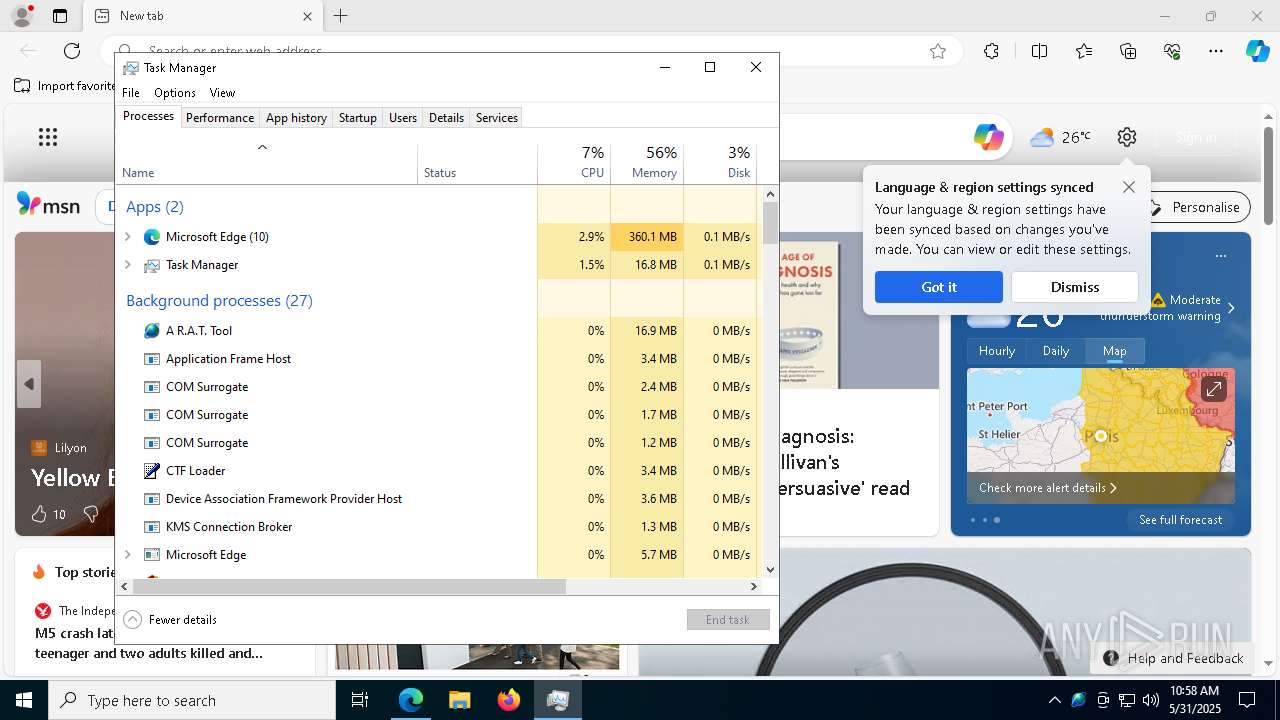
Launch of the file from Registry key
- 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe (PID: 3124)
- Java.exe (PID: 4784)
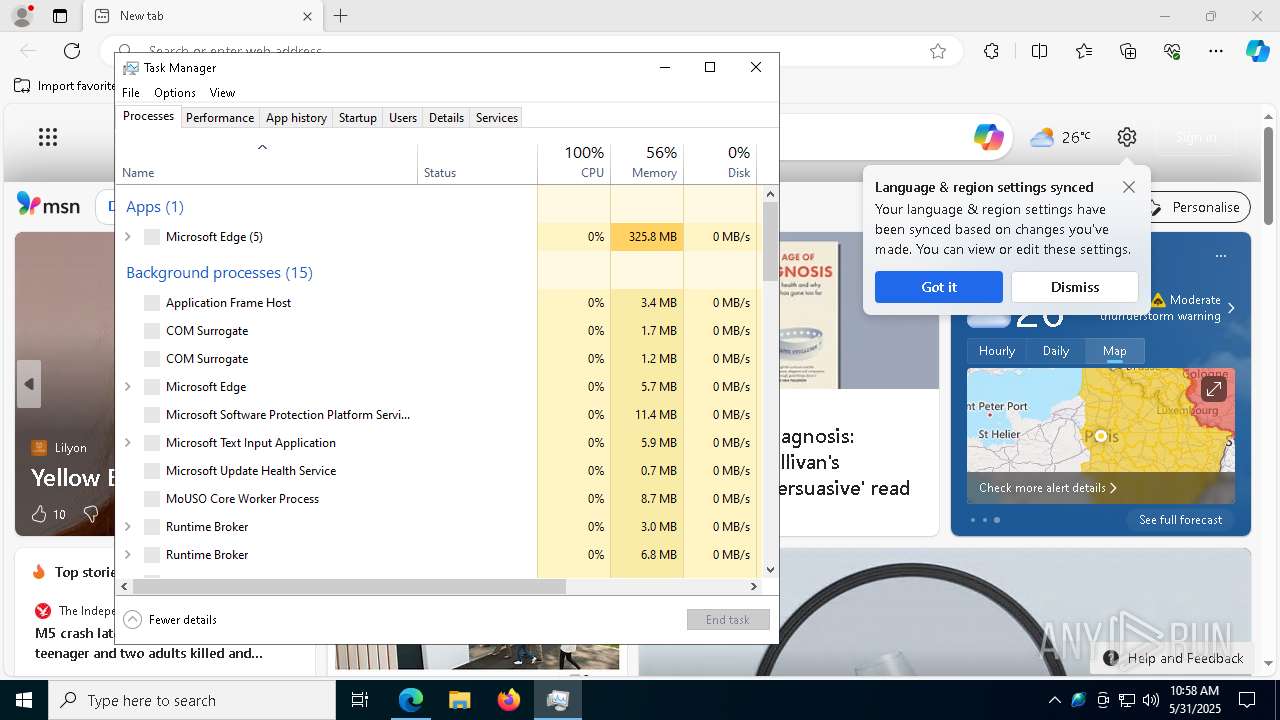
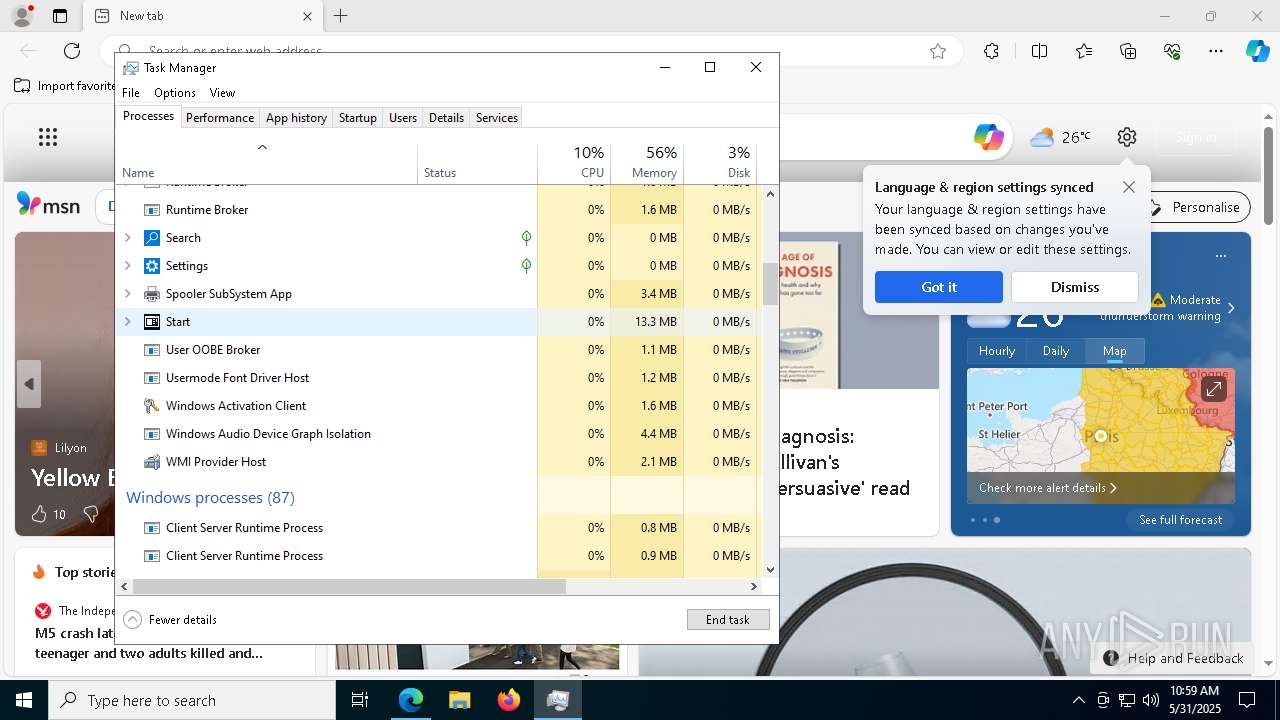
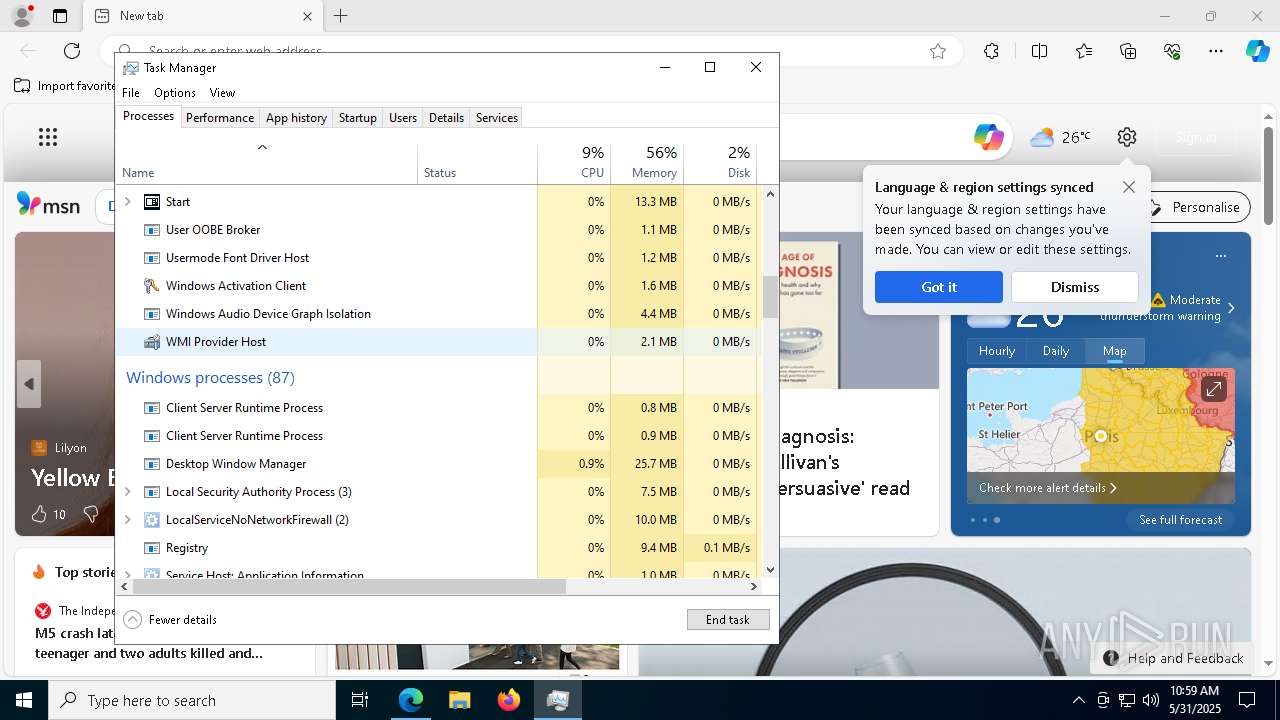
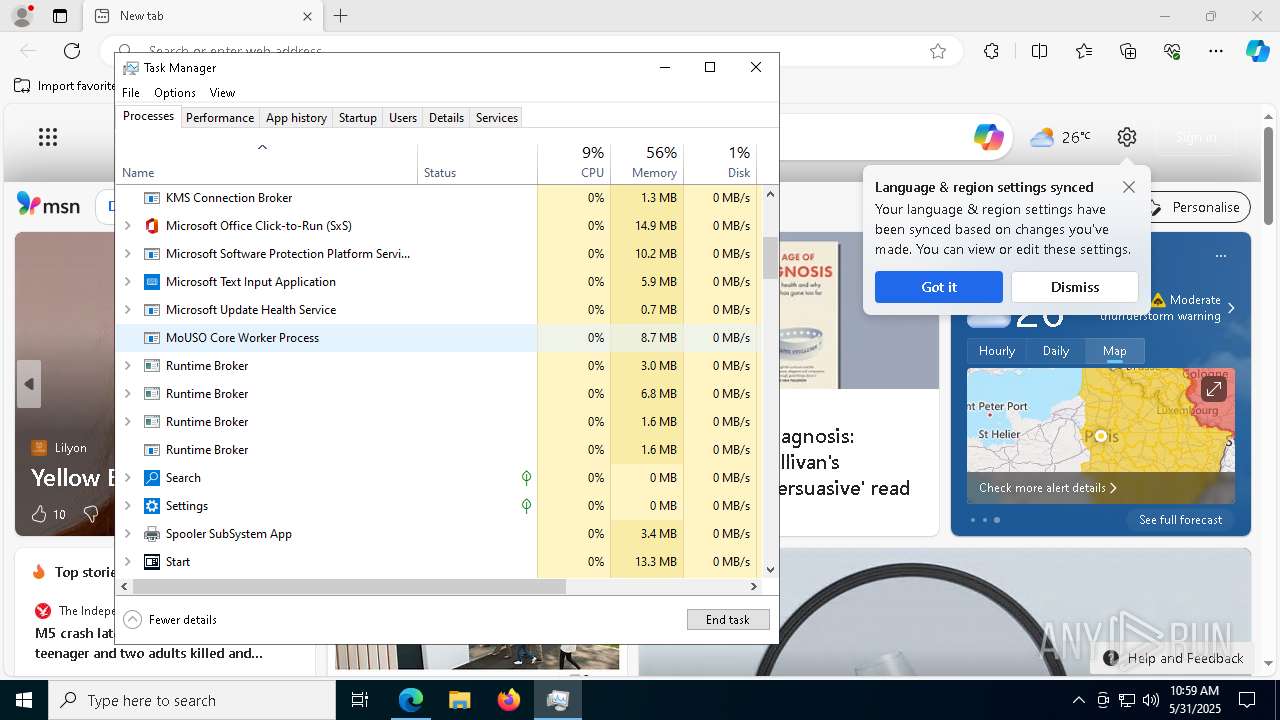
Manual execution by a user
- msedge.exe (PID: 4756)
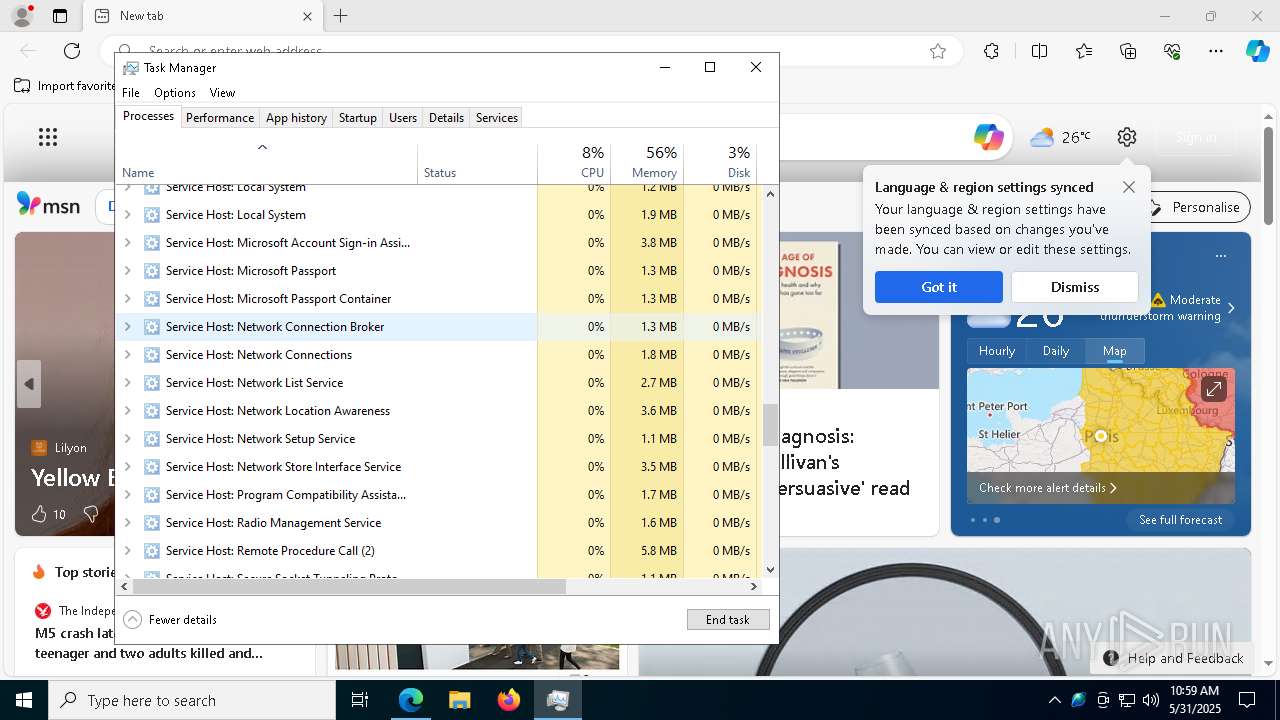
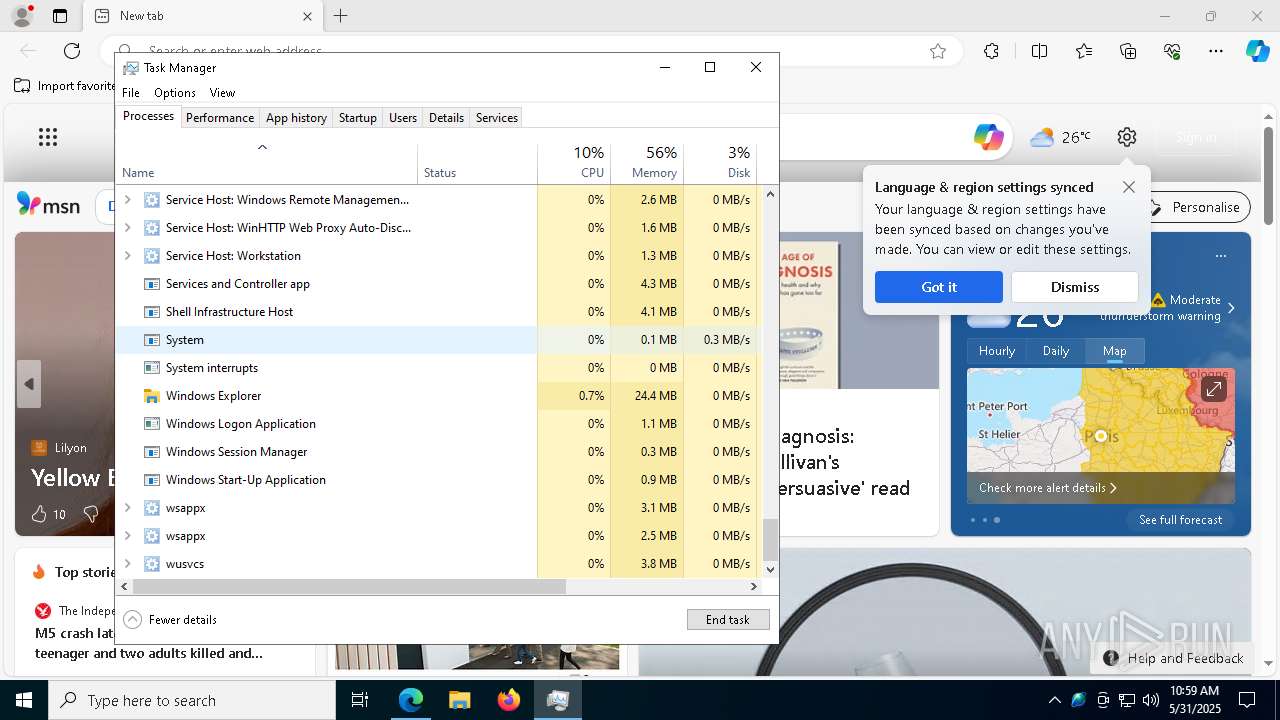
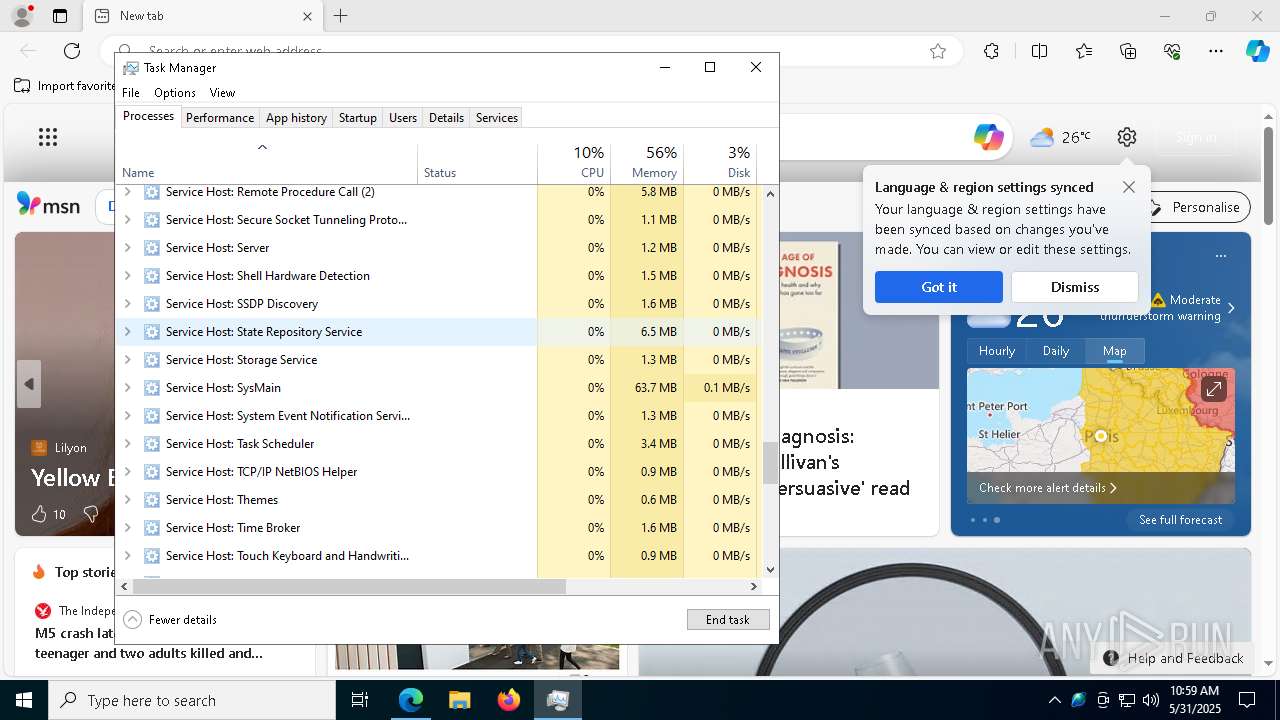
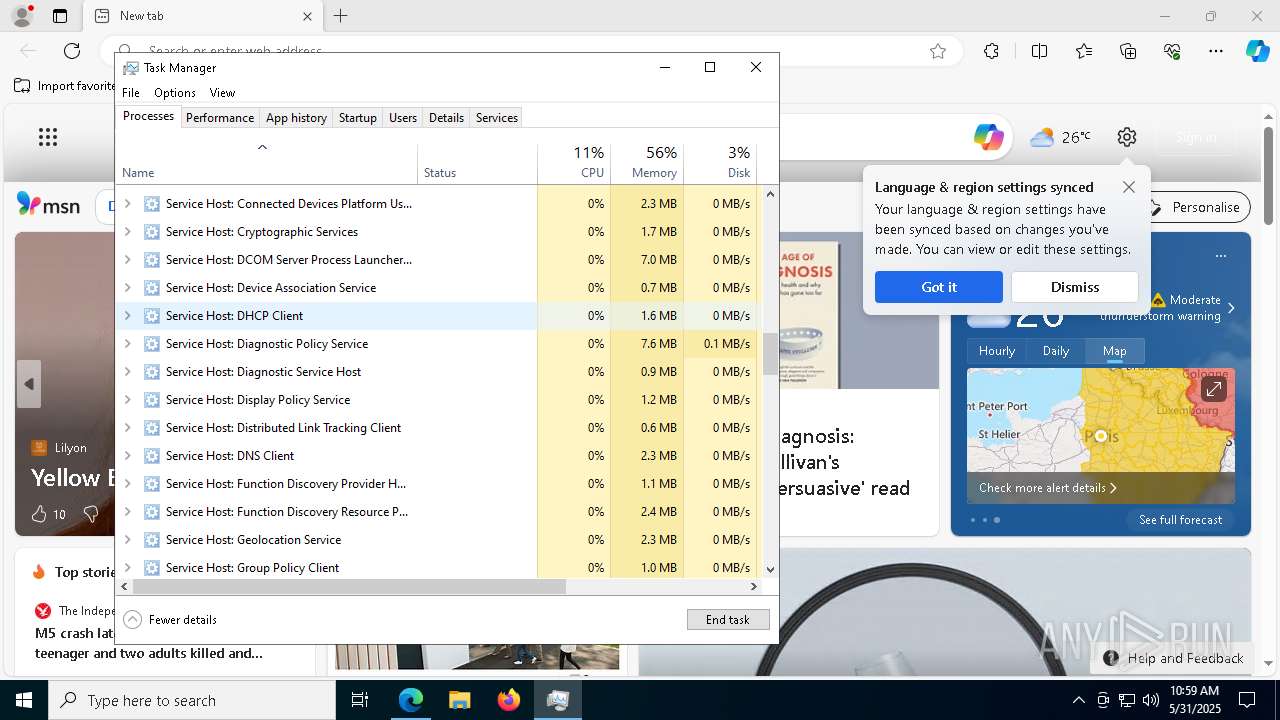
- Taskmgr.exe (PID: 5020)
- Taskmgr.exe (PID: 660)
Application launched itself
- msedge.exe (PID: 4756)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(4784) Java.exe
Version1.4.0
C2 (2)192.168.1.107:4782
Sub_DirJava Update
Install_NameJava.exe
Mutex1f44a168-88fa-4928-8143-ef11a89bed82
StartupJava Updater
TagOffice04
LogDirLogs
SignatureLvMaNN8tXGcFdkNgQiU5eNnFabtcl9eIrilWGjueAmyEkZXoR6svgAaU77PtriAe2itjyDv+f0RudBwemN7CV1t1i4FU+qzpb8ZBlUxOKxLwbyHPfaBERwRb5q/VTB5ini783G0mVy9c8ec8Tcfo6M+rp99zFhK7MSb+WGSC64psC25fsGTvbSov0p7gRF/xHoc5A/OCfPikqFEUX1mtHjfCBaJ2LTaXUkwXbrIGGyHCefYv905+P88w6niTgBxz+DprSWzhvzHgDc5FDJwixlBMLhNMqieC4ru9p2lVjiPl...
CertificateMIIE9DCCAtygAwIBAgIQAIyAcfB6CKnagJ11QSb2XTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIyMDcwODE5NTUwMloYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA2yzamvihkmUHtgaezdA8J08LSbx56WMspPiPedLP4s+j/MozYa0NGi/jv4SDPP8TCmnx278L...
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:31 10:55:28 |
| ZipCRC: | 0x6eeaa8c3 |
| ZipCompressedSize: | 251753 |
| ZipUncompressedSize: | 539648 |
| ZipFileName: | 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe |
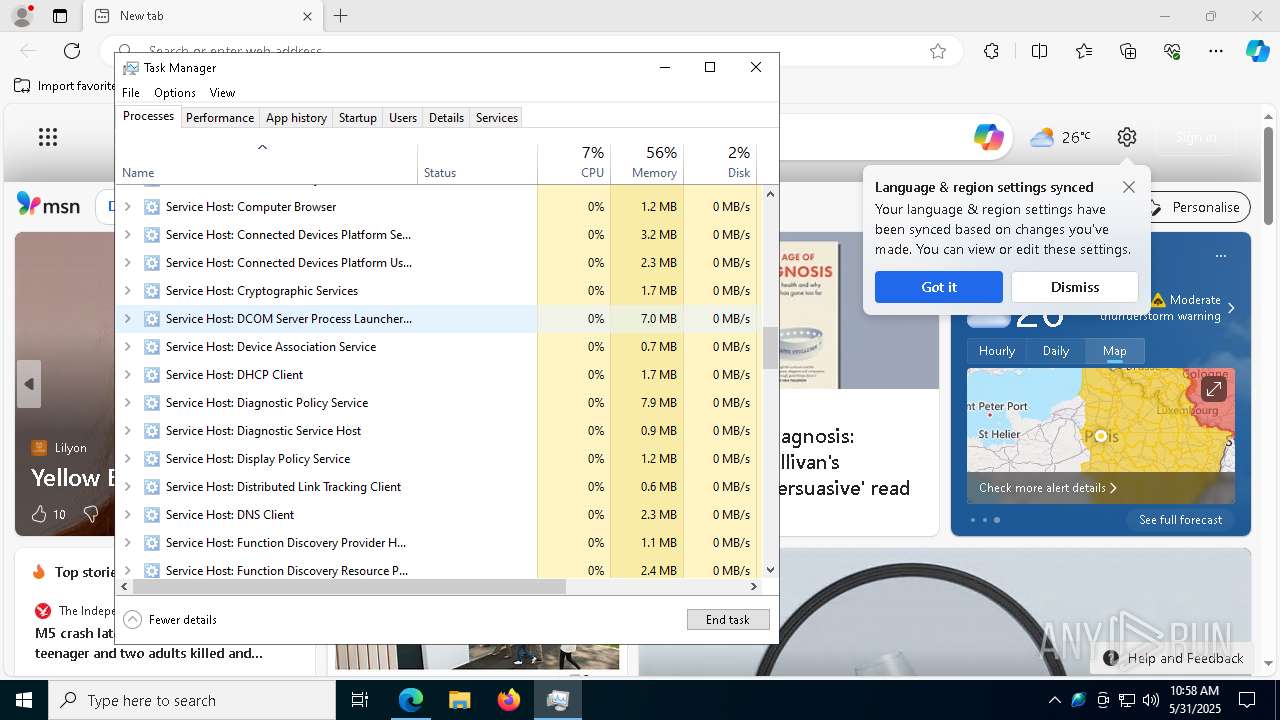
Total processes
159
Monitored processes
29
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4012 --field-trial-handle=2412,i,13033384749864613475,17069160080197631236,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6836 --field-trial-handle=2412,i,13033384749864613475,17069160080197631236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 656 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1608 --field-trial-handle=2412,i,13033384749864613475,17069160080197631236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5932 --field-trial-handle=2412,i,13033384749864613475,17069160080197631236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5204 --field-trial-handle=2412,i,13033384749864613475,17069160080197631236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6940.40143\4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6940.40143\4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe | WinRAR.exe | ||||||||||||
User: admin Company: Sercost Integrity Level: MEDIUM Description: A R.A.T. Tool Exit code: 0 Version: 1.2.6.0 Modules
| |||||||||||||||
| 3884 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4404 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6508 --field-trial-handle=2412,i,13033384749864613475,17069160080197631236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
7 896
Read events
7 853
Write events
42
Delete events
1
Modification events
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.zip | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6940) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3124) 4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Java Updater |
Value: "C:\Users\admin\AppData\Local\Temp\Rar$EXb6940.40143\4b5e4fcf2fb2cca1661ee5daf1f15dc1b58c14aa51059e39a7d6c348310ee38d.exe" | |||
Executable files
29
Suspicious files
423
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF125fac.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF125fdb.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF125fdb.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF125fdb.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF125fdb.TMP | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4756 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF125feb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
57
DNS requests
64
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4616 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4616 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8144 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3176 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4616 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
4616 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4616 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.168.100.7:49772 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |