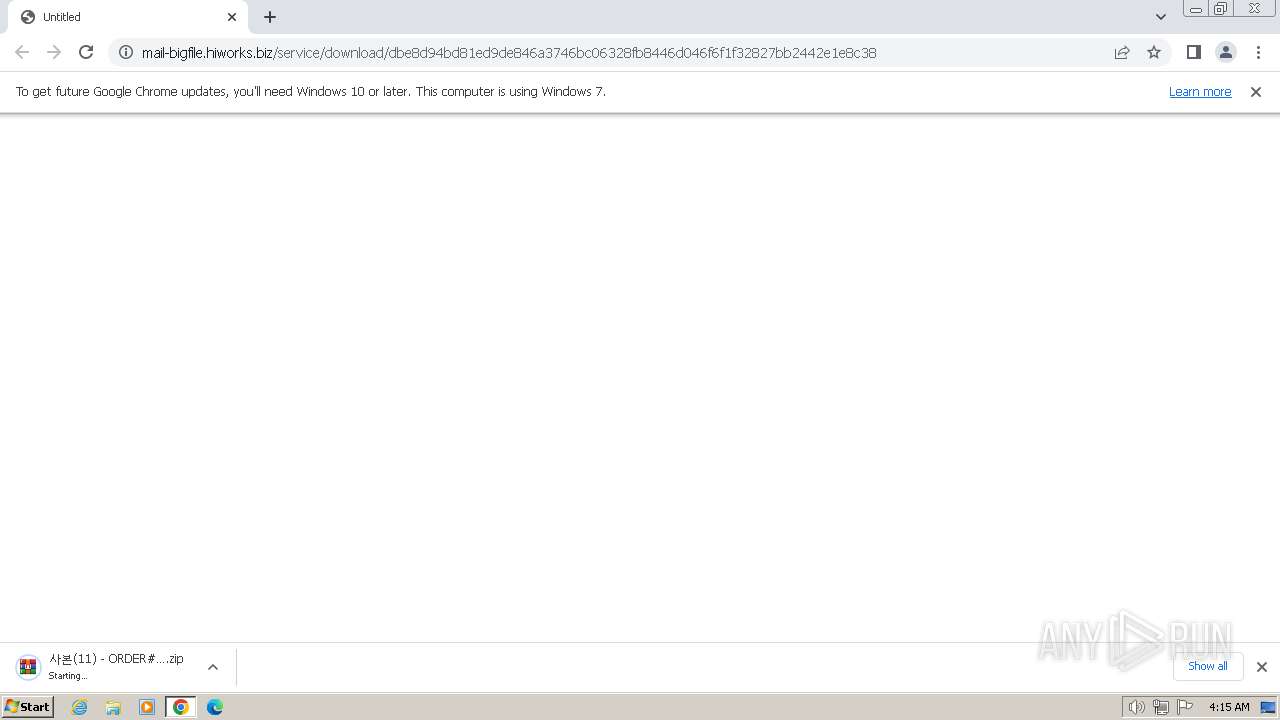
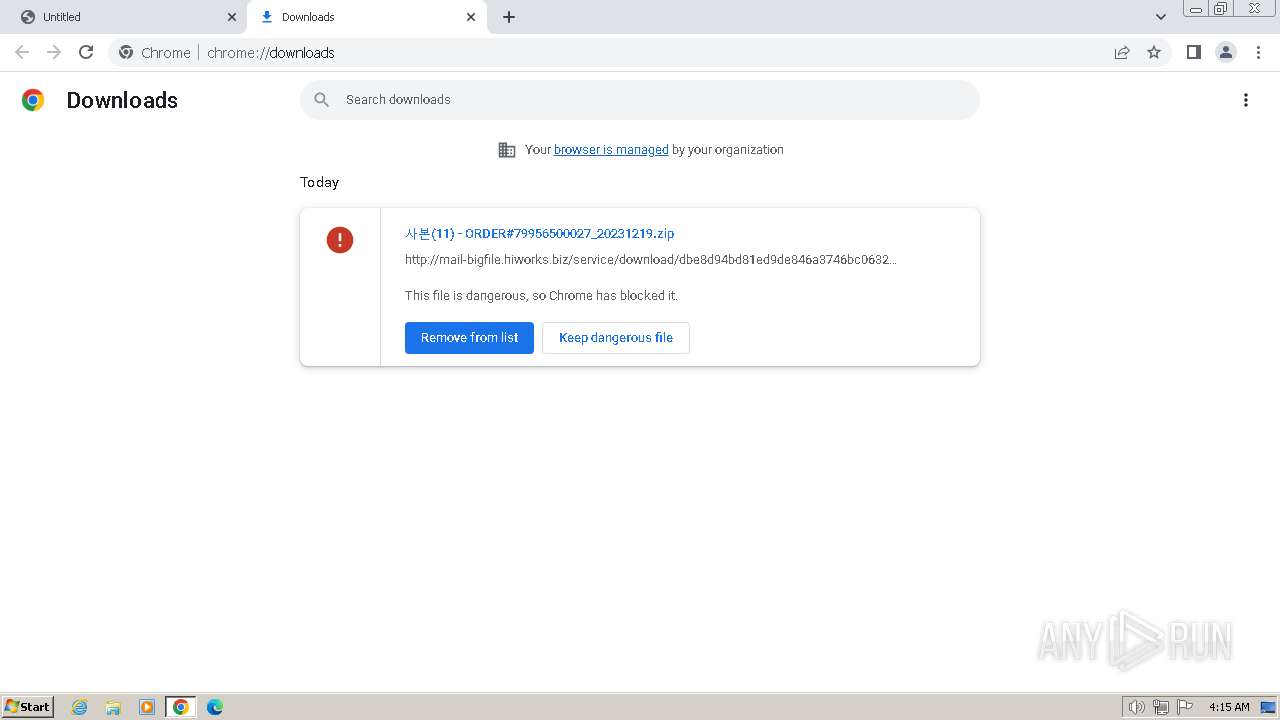
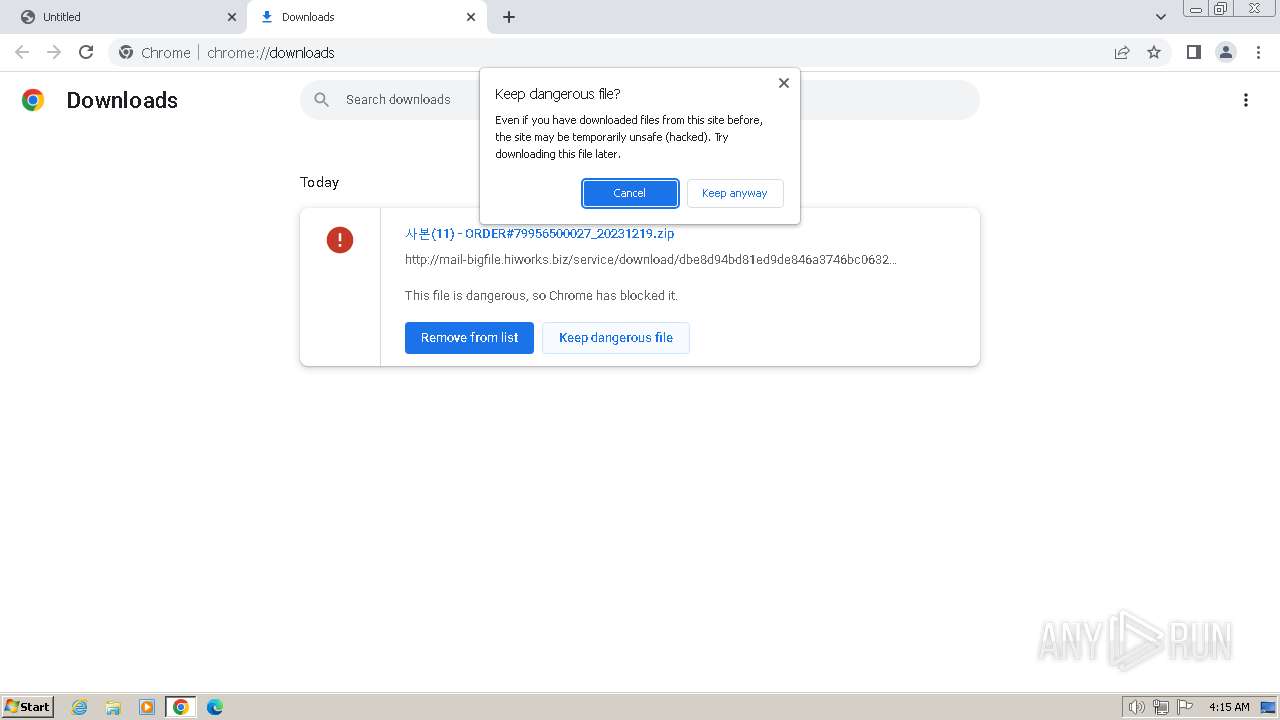
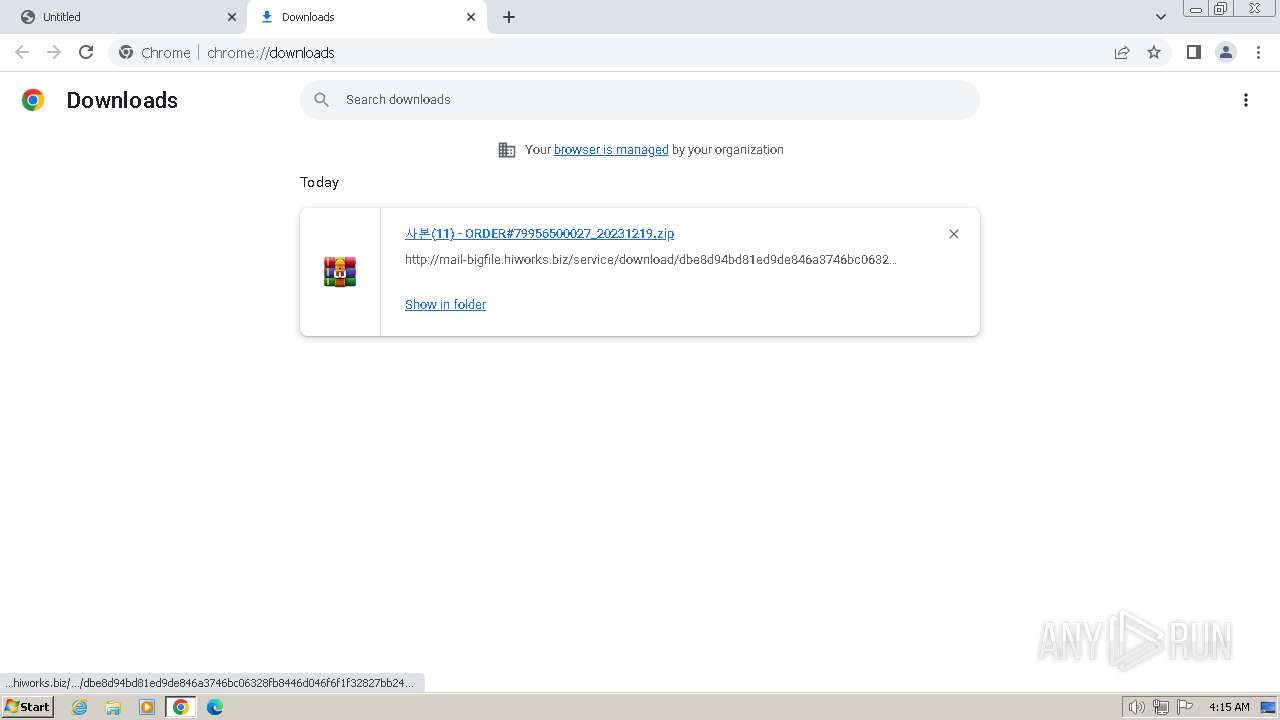
| URL: | http://mail-bigfile.hiworks.biz/service/download/dbe8d94bd81ed9de846a3746bc06328fb8446d046f6f1f32827bb2442e1e8c38 |
| Full analysis: | https://app.any.run/tasks/d1444e8c-f74e-4c35-9ae2-e7e7891621fc |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | December 19, 2023, 04:15:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6BA4BD9239EBC0880ED03061810D0627 |
| SHA1: | 1C7362E8C006A09804AEEFE88EB950E6DC480C17 |
| SHA256: | E5B451F801775ADBE0CBD65FA57C09D448A817E7246196C9FD5C26DE1835FFA1 |
| SSDEEP: | 3:N1KTDCx5AOMHxZK4mKBgH465SRLCTWNDBXdyEn:CB0uBgHr50DBt |
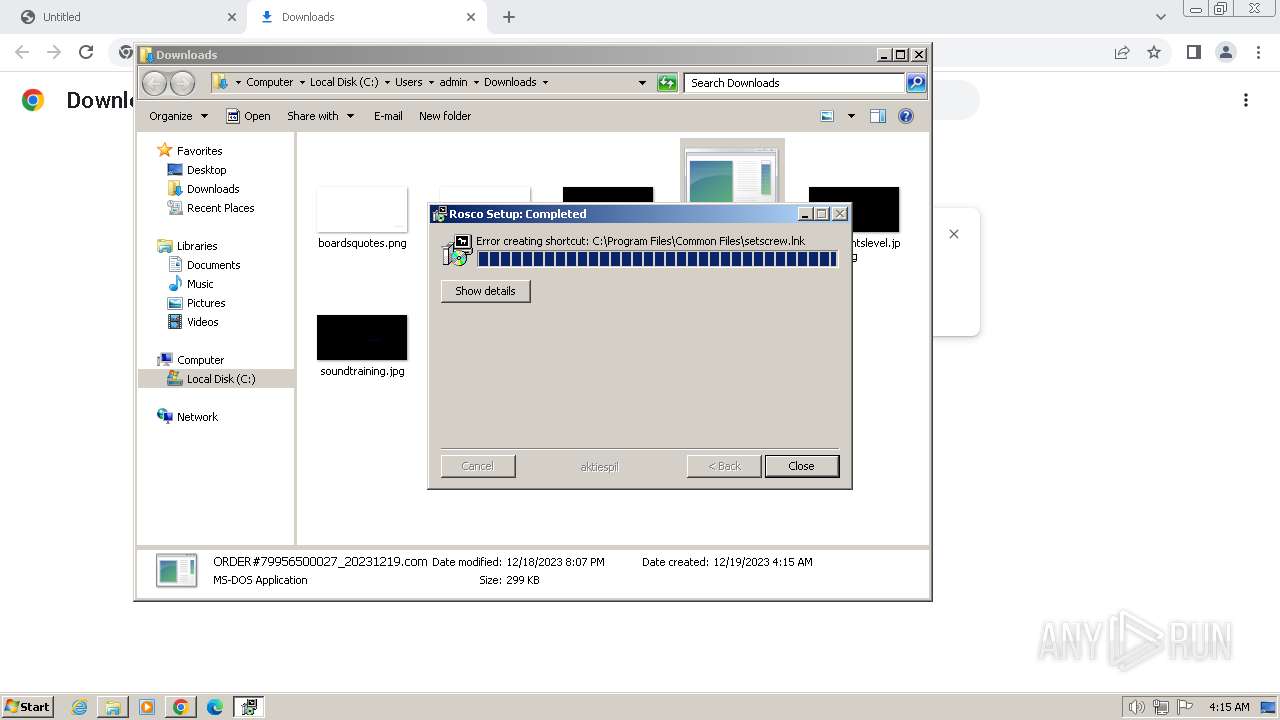
MALICIOUS
Drops the executable file immediately after the start
- powershell.exe (PID: 3240)
GULOADER has been detected (SURICATA)
- wab.exe (PID: 3388)
REMCOS has been detected (SURICATA)
- wab.exe (PID: 3388)
Actions looks like stealing of personal data
- wab.exe (PID: 2148)
- wab.exe (PID: 4036)
- wab.exe (PID: 3064)
- wab.exe (PID: 2364)
- wab.exe (PID: 4064)
- wab.exe (PID: 2860)
Steals credentials from Web Browsers
- wab.exe (PID: 4064)
- wab.exe (PID: 2860)
Steals credentials
- wab.exe (PID: 4064)
- wab.exe (PID: 2148)
- wab.exe (PID: 2860)
- wab.exe (PID: 2364)
Uses NirSoft utilities to collect credentials
- wab.exe (PID: 4064)
- wab.exe (PID: 2148)
- wab.exe (PID: 2364)
- wab.exe (PID: 2860)
SUSPICIOUS
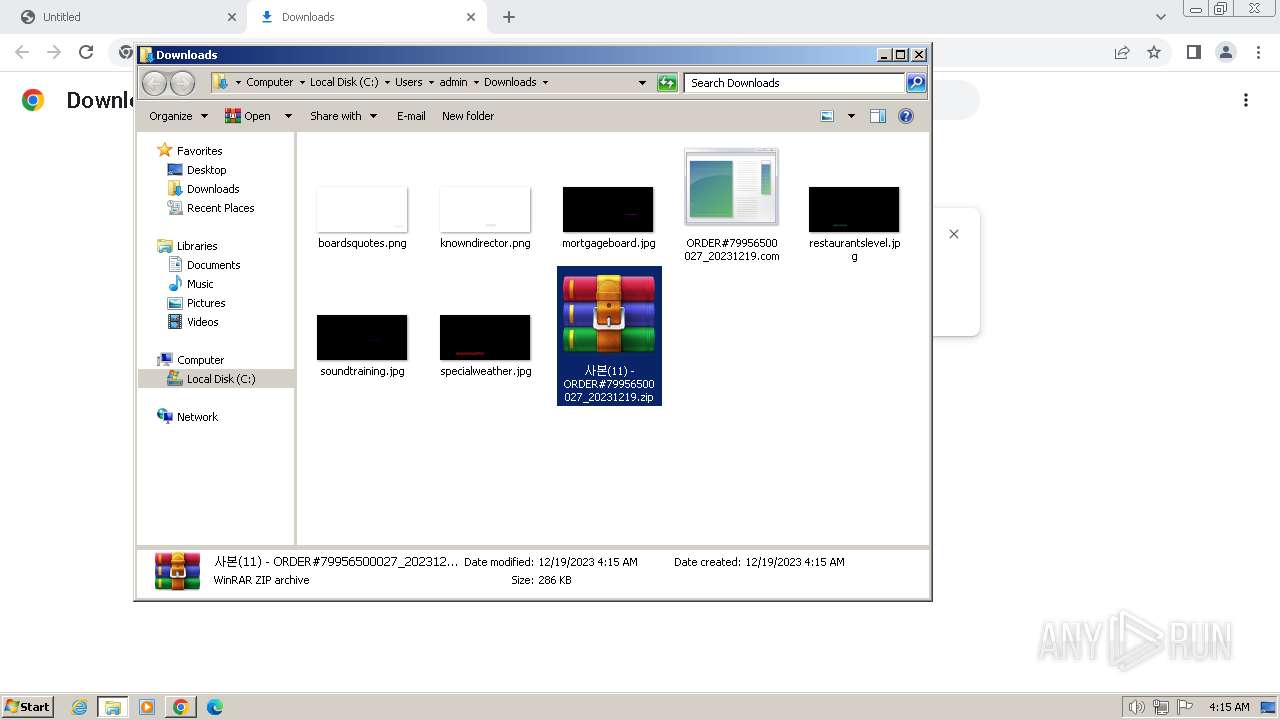
Reads the Internet Settings
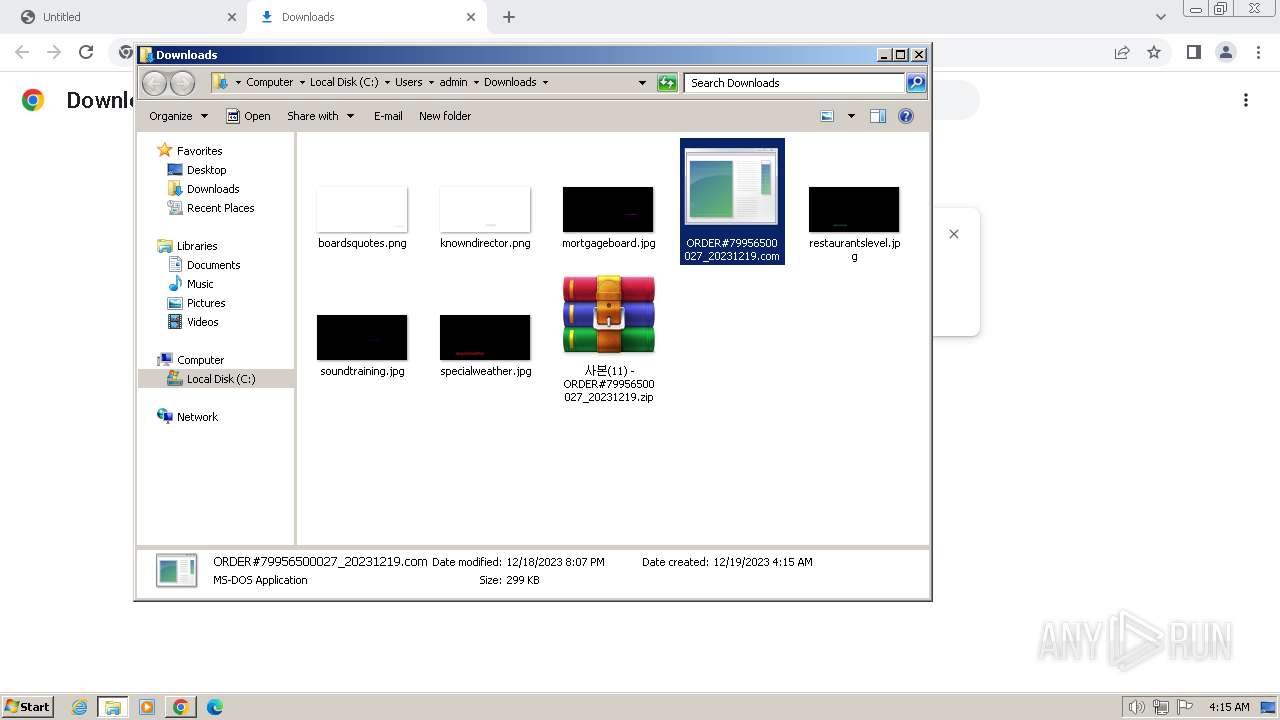
- ORDER#79956500027_20231219.com (PID: 3144)
- wab.exe (PID: 3388)
Starts POWERSHELL.EXE for commands execution
- ORDER#79956500027_20231219.com (PID: 3144)
Connects to the server without a host name
- wab.exe (PID: 3388)
Connects to unusual port
- wab.exe (PID: 3388)
Application launched itself
- wab.exe (PID: 3388)
Loads DLL from Mozilla Firefox
- wab.exe (PID: 4036)
- wab.exe (PID: 3064)
Accesses Microsoft Outlook profiles
- wab.exe (PID: 2148)
- wab.exe (PID: 2364)
INFO
Application launched itself
- chrome.exe (PID: 2040)
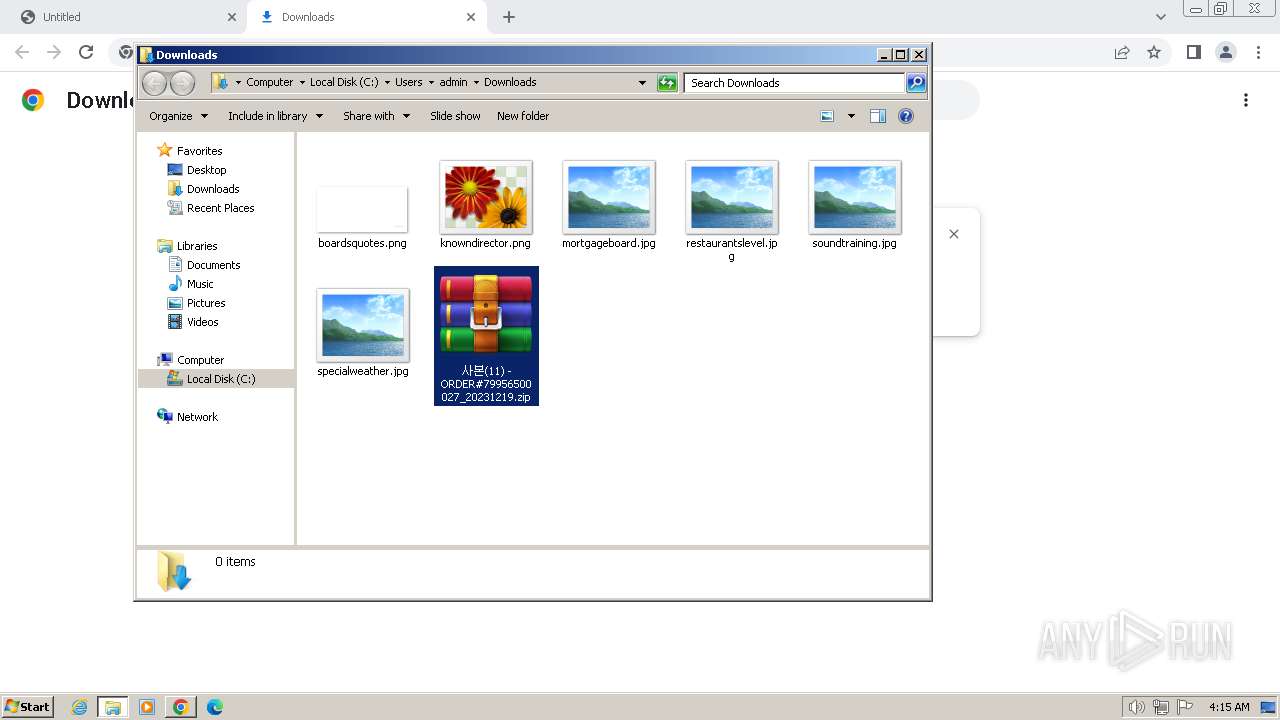
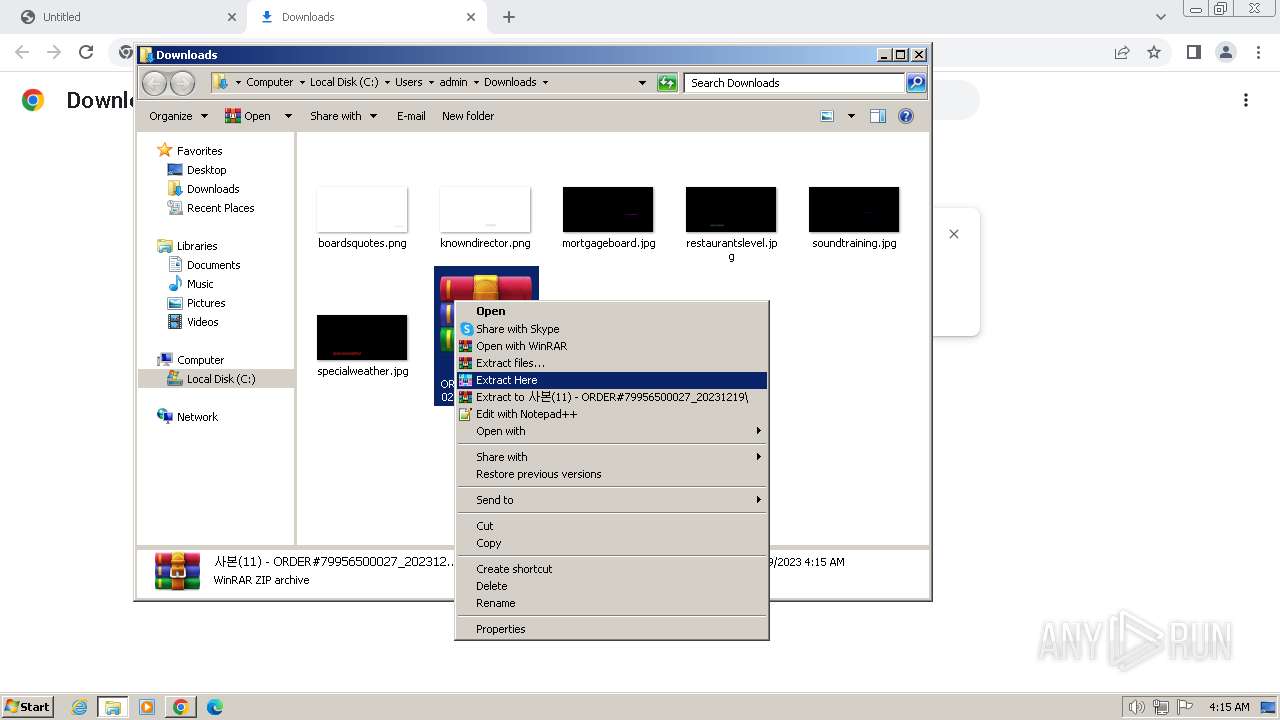
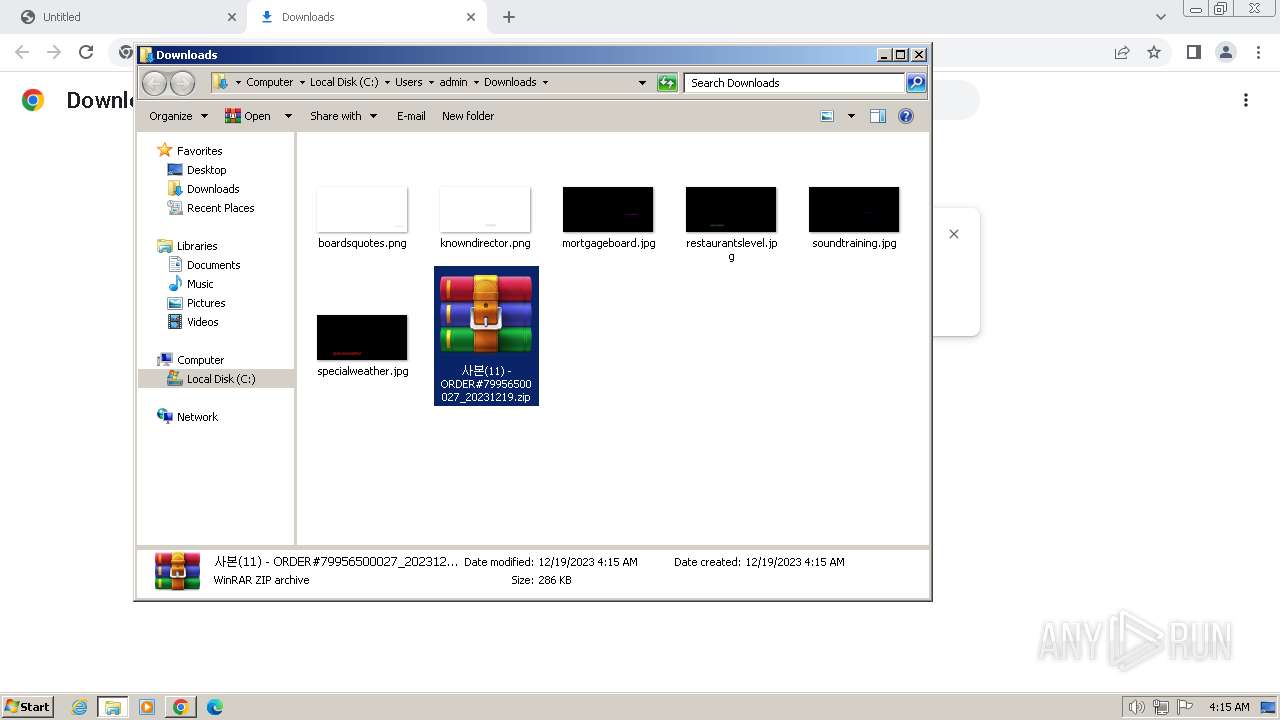
The process uses the downloaded file
- chrome.exe (PID: 1556)
- chrome.exe (PID: 2960)
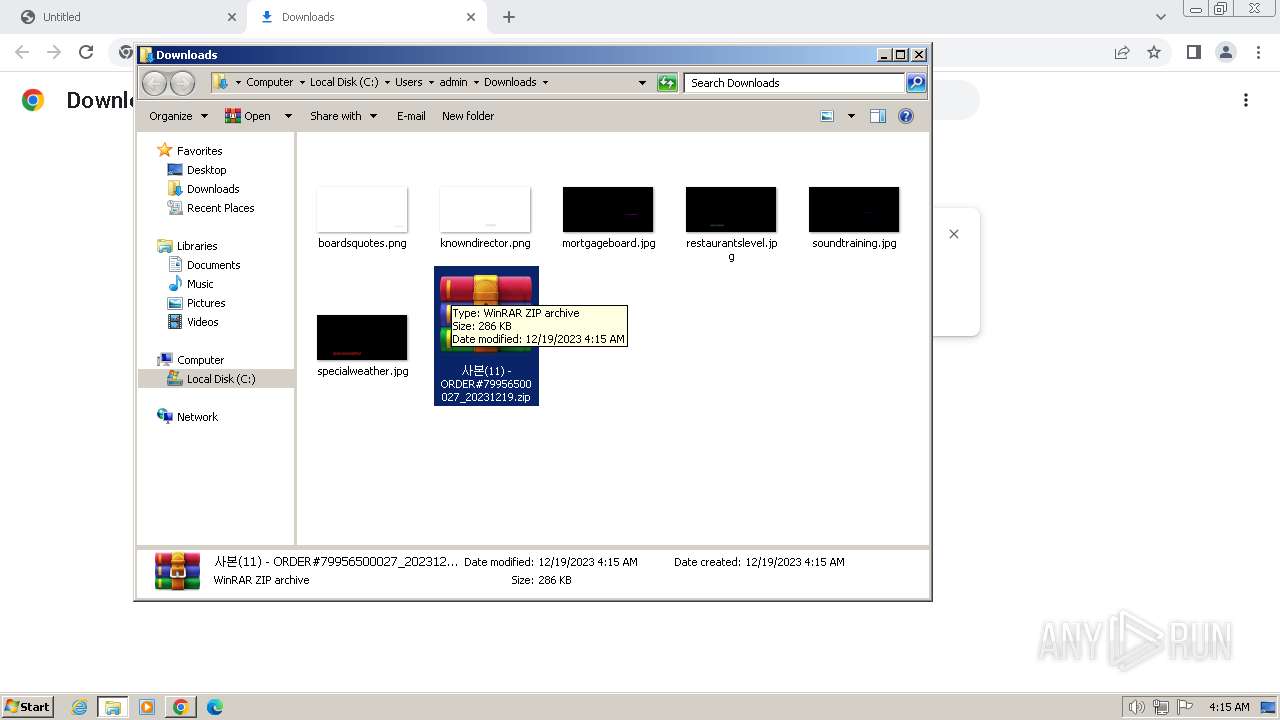
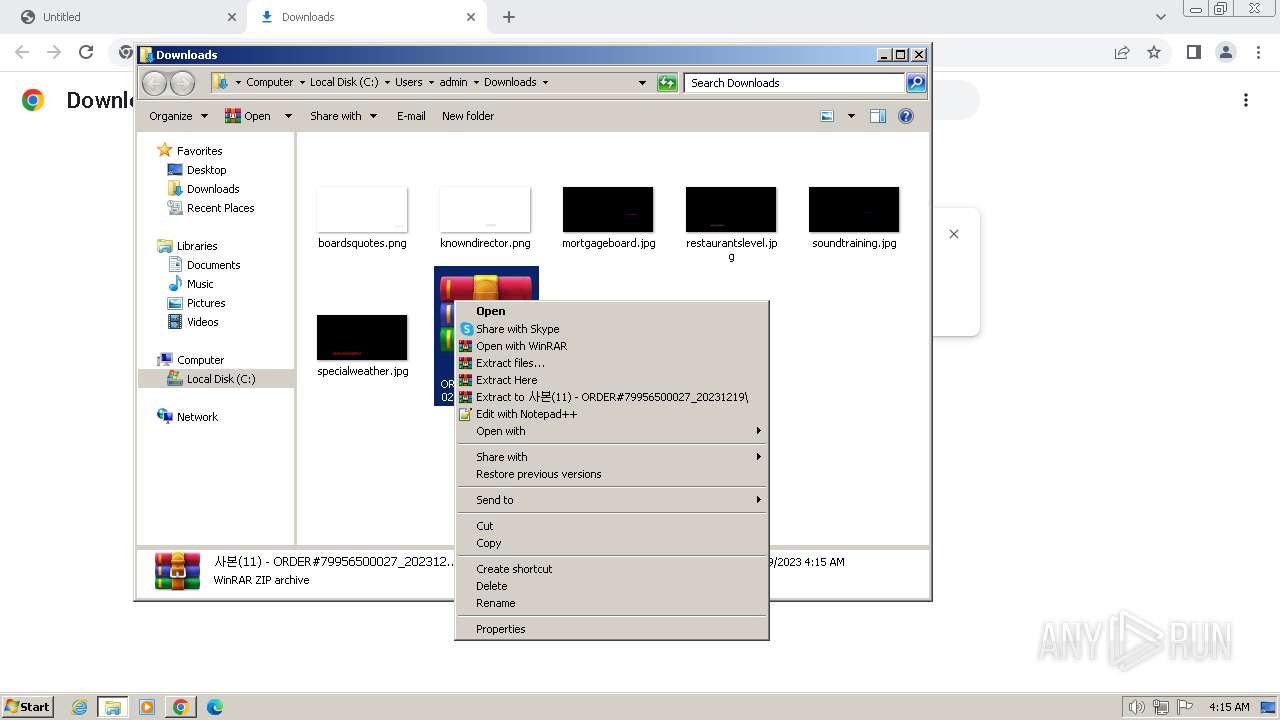
- WinRAR.exe (PID: 2944)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2544)
Drops the executable file immediately after the start
- chrome.exe (PID: 2572)
- WinRAR.exe (PID: 2944)
Manual execution by a user
- WinRAR.exe (PID: 2944)
- ORDER#79956500027_20231219.com (PID: 3144)
Checks supported languages
- ORDER#79956500027_20231219.com (PID: 3144)
- wab.exe (PID: 3388)
- wab.exe (PID: 4064)
- wab.exe (PID: 4036)
- wab.exe (PID: 2148)
- wab.exe (PID: 2860)
- wab.exe (PID: 2364)
- wab.exe (PID: 3064)
Reads the computer name
- ORDER#79956500027_20231219.com (PID: 3144)
- wab.exe (PID: 4036)
- wab.exe (PID: 2148)
- wab.exe (PID: 3388)
- wab.exe (PID: 3064)
- wab.exe (PID: 4064)
- wab.exe (PID: 2364)
- wab.exe (PID: 2860)
Create files in a temporary directory
- ORDER#79956500027_20231219.com (PID: 3144)
- wab.exe (PID: 4064)
- wab.exe (PID: 4036)
- wab.exe (PID: 2148)
- wab.exe (PID: 2364)
- wab.exe (PID: 2860)
- wab.exe (PID: 3064)
Creates files or folders in the user directory
- ORDER#79956500027_20231219.com (PID: 3144)
- wab.exe (PID: 3388)
Creates files in the program directory
- ORDER#79956500027_20231219.com (PID: 3144)
Checks proxy server information
- wab.exe (PID: 3388)
Reads the machine GUID from the registry
- wab.exe (PID: 3388)
- wab.exe (PID: 4064)
- wab.exe (PID: 4036)
- wab.exe (PID: 3064)
- wab.exe (PID: 2860)
Reads product name
- wab.exe (PID: 3388)
Reads Environment values
- wab.exe (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
37
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1824 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1420 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1256 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3596 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=968 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1884 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1116 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3448 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=680 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2036 --field-trial-handle=1140,i,3474016441220328974,16667434146352012409,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
8 461
Read events
8 316
Write events
144
Delete events
1
Modification events
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
9
Suspicious files
346
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdf916.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFdf945.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RFe00b7.TMP | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdf916.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
32
DNS requests
22
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
548 | chrome.exe | GET | 200 | 45.120.70.56:80 | http://mail-bigfile.hiworks.biz/service/download/dbe8d94bd81ed9de846a3746bc06328fb8446d046f6f1f32827bb2442e1e8c38 | unknown | compressed | 286 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 5.15 Kb | unknown |
3388 | wab.exe | GET | 200 | 146.70.79.70:80 | http://146.70.79.70/doditAmnAdSOdqGlRTzkqvo161.bin | unknown | binary | 483 Kb | unknown |
3388 | wab.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | binary | 948 b | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 9.54 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 8.77 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 11.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 15.7 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | binary | 25.4 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
548 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2040 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
548 | chrome.exe | 45.120.70.56:80 | mail-bigfile.hiworks.biz | LG DACOM Corporation | KR | unknown |
2040 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
548 | chrome.exe | 142.250.184.206:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
548 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
548 | chrome.exe | 142.250.184.202:443 | optimizationguide-pa.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
mail-bigfile.hiworks.biz |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
geoplugin.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
548 | chrome.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
548 | chrome.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3388 | wab.exe | A Network Trojan was detected | LOADER [ANY.RUN] GuLoader |
3388 | wab.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
3388 | wab.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x TLS Connection |
3388 | wab.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS JA3 Hash |
3388 | wab.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x TLS Connection |
3388 | wab.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS JA3 Hash |
3388 | wab.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x TLS Connection |
3388 | wab.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS JA3 Hash |
3 ETPRO signatures available at the full report