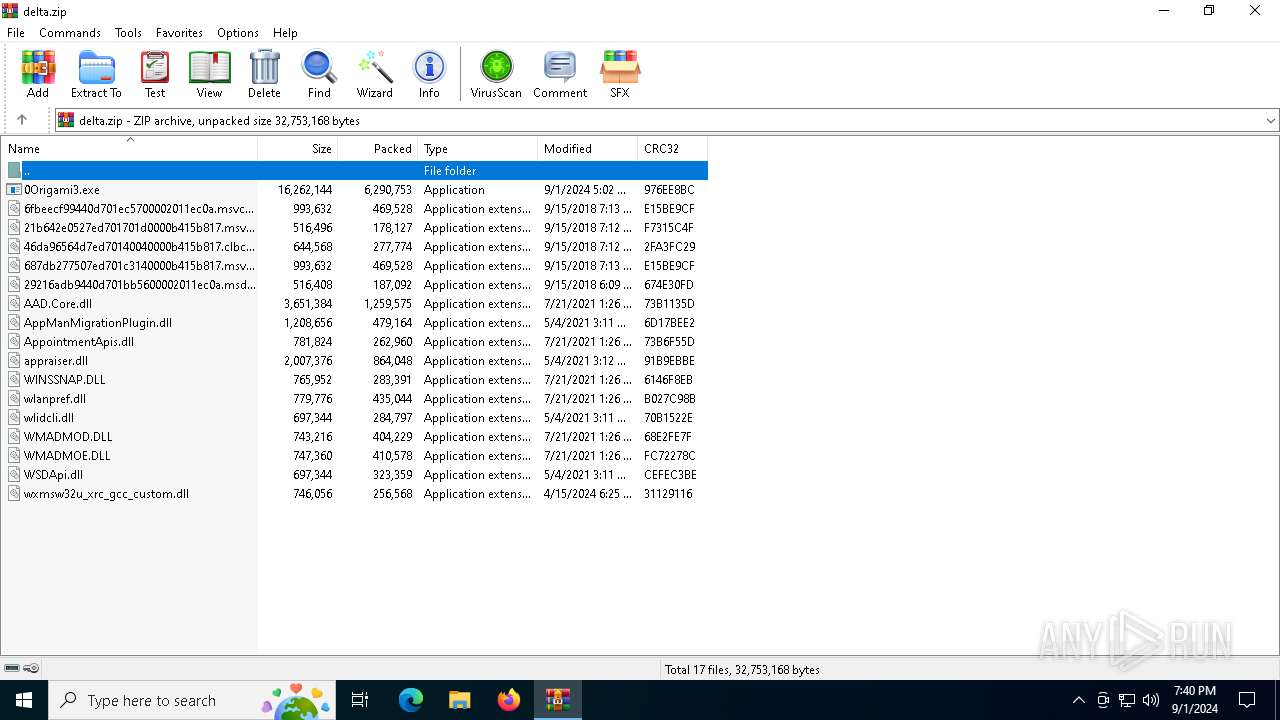
| File name: | delta.zip |
| Full analysis: | https://app.any.run/tasks/eac5ec54-72d8-498a-a1fd-3ba2e81a4526 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 01, 2024, 19:39:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 7B279EAD2B5AE7A38BA0B0F0A98CF38A |
| SHA1: | 2CE1F235E981DBF5953E17F4BCBF784B0A4FCAAF |
| SHA256: | E5908A577C139297B3222DA2A69BB696DCFCBA9763C34E4386DCF5C190E03A61 |
| SSDEEP: | 98304:rL7ix7iBVURMuHNeYL6V8g9kgkVF74OzNowEWgJ9WD1KE6jM+DAgYFq8HGavw8Gy:GgjGnCmHChHpwYOL/EIkxT1X3v4TCo |
MALICIOUS
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 2208)
Stealers network behavior
- BitLockerToGo.exe (PID: 2208)
LUMMA has been detected (SURICATA)
- BitLockerToGo.exe (PID: 2208)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3984)
There is functionality for communication over UDP network (YARA)
- 0Origami3.exe (PID: 6832)
Searches for installed software
- BitLockerToGo.exe (PID: 2208)
INFO
Checks supported languages
- 0Origami3.exe (PID: 6832)
- BitLockerToGo.exe (PID: 2208)
Reads the computer name
- BitLockerToGo.exe (PID: 2208)
- 0Origami3.exe (PID: 6832)
Manual execution by a user
- 0Origami3.exe (PID: 6832)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3984)
Reads the software policy settings
- BitLockerToGo.exe (PID: 2208)
The process uses the downloaded file
- WinRAR.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:01 10:02:14 |
| ZipCRC: | 0x976ee8bc |
| ZipCompressedSize: | 6290753 |
| ZipUncompressedSize: | 16262144 |
| ZipFileName: | 0Origami3.exe |
Total processes
130
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2208 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | 0Origami3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3308 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
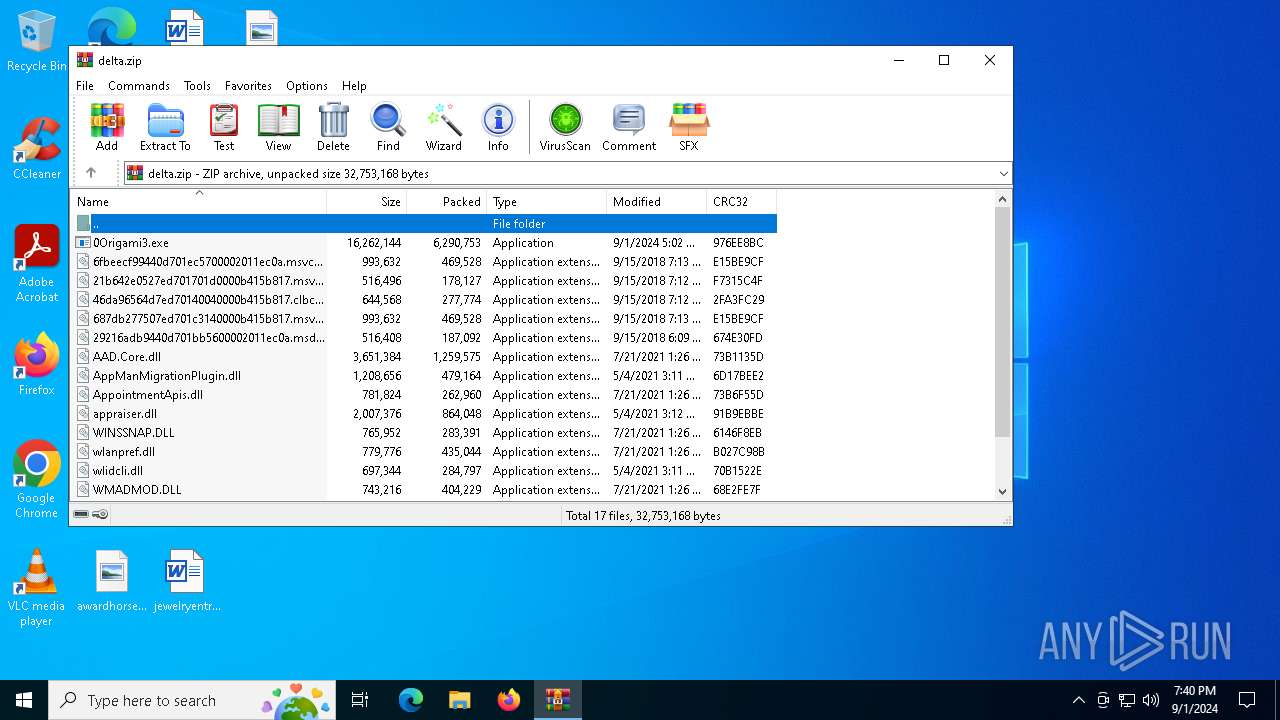
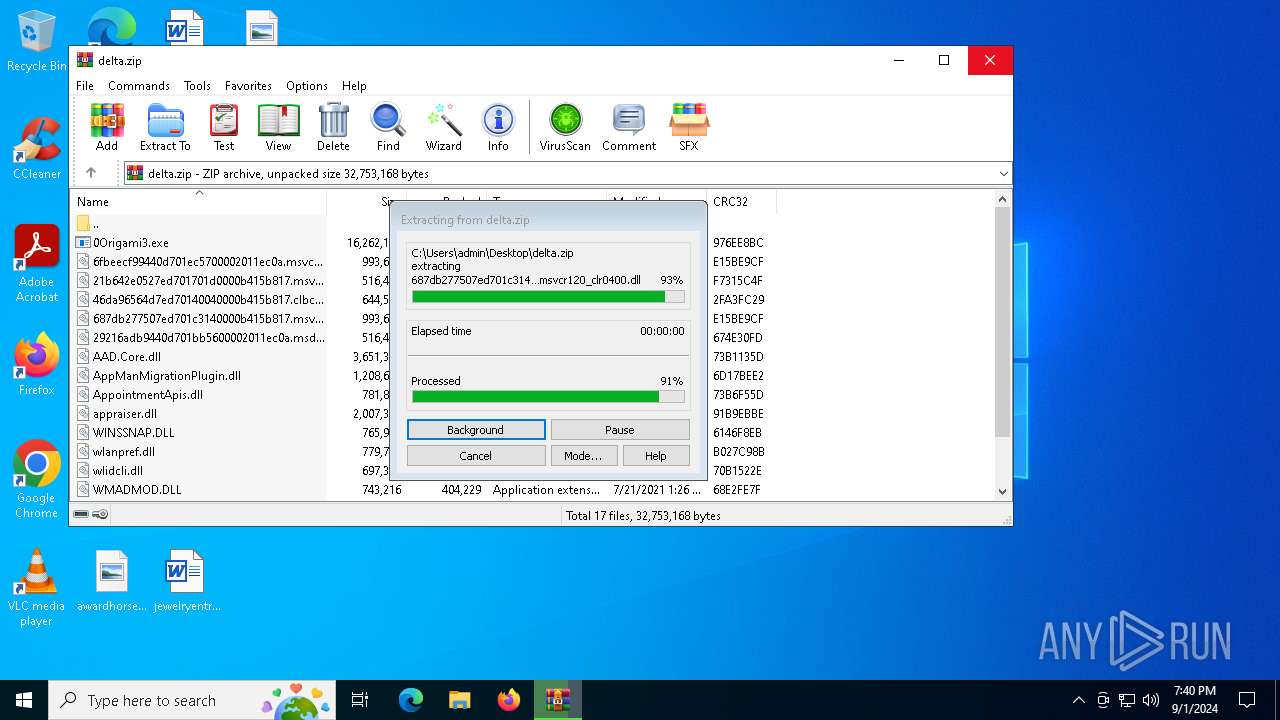
| 3984 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\delta.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6280 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
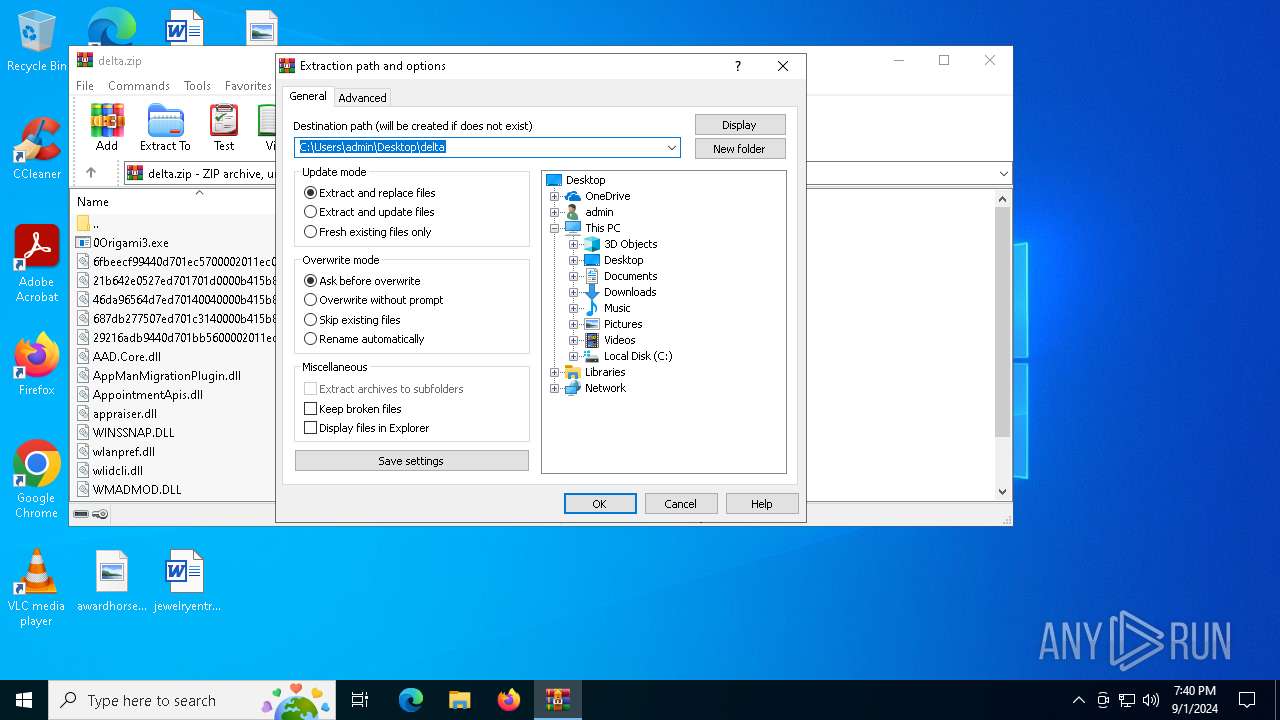
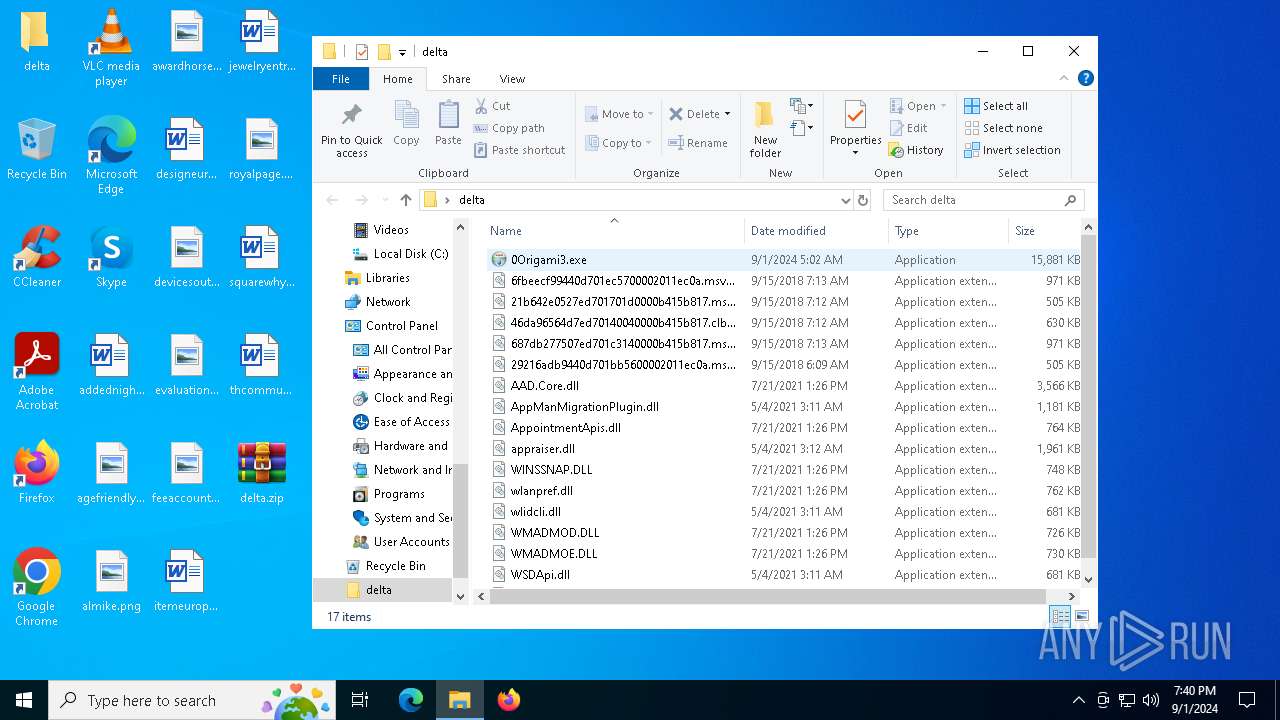
| 6832 | "C:\Users\admin\Desktop\delta\0Origami3.exe" | C:\Users\admin\Desktop\delta\0Origami3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 666 Modules
| |||||||||||||||
| 7020 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 259
Read events
5 993
Write events
266
Delete events
0
Modification events
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\delta.zip | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\delta | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
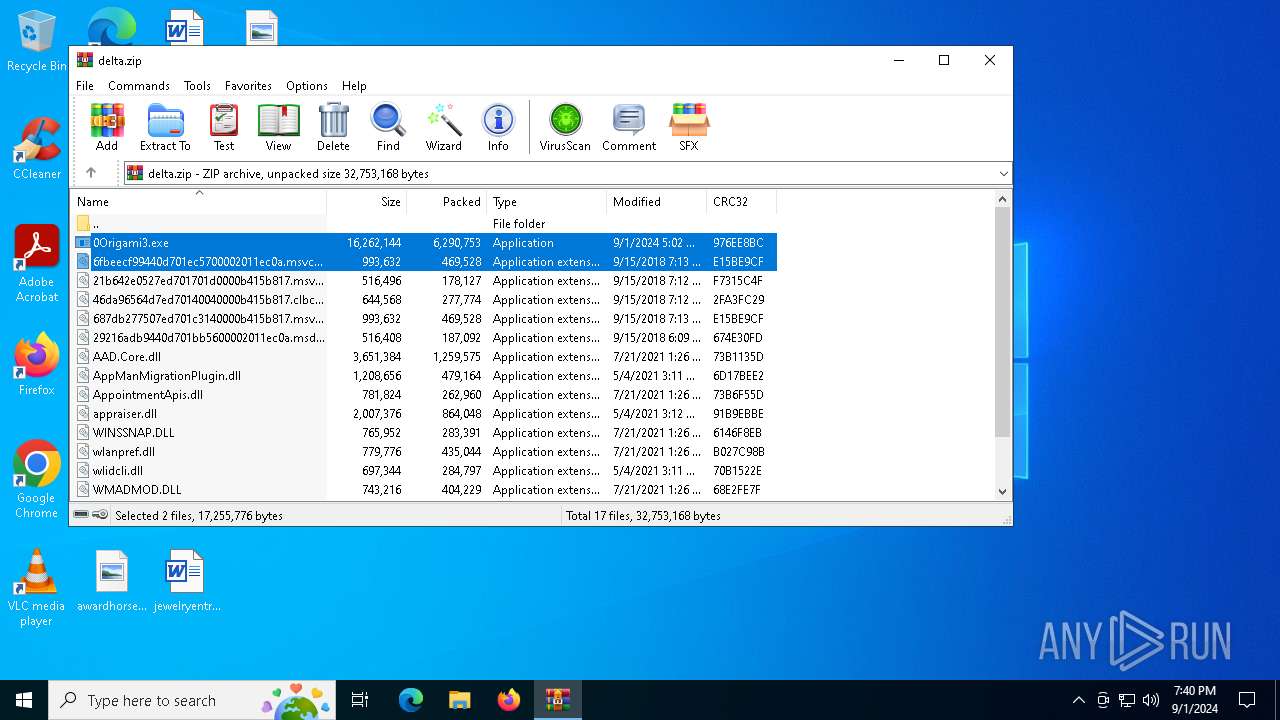
Executable files
17
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\wlanpref.dll | executable | |
MD5:F4565A6B8C00030593D97F0B0F81C976 | SHA256:190536922FB9CD91B778011811260C67C0B24FCD84F5EA7487557AE6729B3CC6 | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\0Origami3.exe | executable | |
MD5:3E35A7A3203CC7726CE4E9F7F30806EF | SHA256:3AA011528C4D261A82A0698A5BE19D47C4114E2443B93617978FE7F34957930F | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\WMADMOE.DLL | executable | |
MD5:1B6C344E33BF0CDA03790CF68B3819E9 | SHA256:59F139C45F7734DDCB60F940E02D95013EDD0900ECE36F1581B3E0EA5378E934 | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\WMADMOD.DLL | executable | |
MD5:260EAE2434AAEE13714C10C602C7317A | SHA256:2CC38C93239E748909A5443E305AE58484D0A5C1B57138D0F0A1C07AA33A1668 | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\AAD.Core.dll | executable | |
MD5:CF59CD4B55BD5532EF8A29D881CD3392 | SHA256:D5168035FDDE1E43B3F0175F09C7C2FE02006E0EC2FAFAF14BB734C7E23FDBFD | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\wxmsw32u_xrc_gcc_custom.dll | executable | |
MD5:923E97F86B22ABCB602F6AB16D2B0293 | SHA256:95E36F082AC1BD2EE75C7C3D7371C8332CD5F36B3AF0E4146689EE8790E7F244 | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\46da96564d7ed70140040000b415b817.clbcatq.dll | executable | |
MD5:12112113BDFAF0CC03517604440217D5 | SHA256:C5D4F3DFA14DEABD6A845E6F0B04C39A9A539C1A4D6C71B25943EB9BF9C9A3F5 | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\29216adb9440d701bb5600002011ec0a.msdelta.dll | executable | |
MD5:4268CC1FBDD2947725521853602E3351 | SHA256:A72E8D1C111616CE5F3B9E8C45EA5B7EBE5D89D4EC830078820F0D1DCBD9A922 | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\21b642e0527ed701701d0000b415b817.msvcp_win.dll | executable | |
MD5:76B2F08DCABA8508AF1491E7B36CEF6C | SHA256:68DAC4FE21A3242872F365561B8B2B34463261D4466D23BDCDFDCD6A532A2280 | |||
| 3984 | WinRAR.exe | C:\Users\admin\Desktop\delta\wlidcli.dll | executable | |
MD5:BBA1ADF6B61578FD2BCD0BB109C220BB | SHA256:F428CE61B7578B627EFCA43FA4F988C5A3DFE40D82389C3C1343DE3B190ECD08 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
32
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1496 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5644 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1492 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5644 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1496 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1496 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
femininedspzmhu.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2208 | BitLockerToGo.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |