| File name: | Miner.exe |
| Full analysis: | https://app.any.run/tasks/f626375a-e0cb-46ad-a2d9-8ff0a495f5f0 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | October 26, 2024, 10:16:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 8 sections |
| MD5: | BEEC454529E5BCCF2CC5D28F6B929477 |
| SHA1: | 8707AC184631F9324C9078C2692FA9564ABE285B |
| SHA256: | E58724D3BFB58D98746F2AFB6988089A9013105AE3BC09F8BA60987BEFCA14AF |
| SSDEEP: | 49152:1L44lufQRAdjrps/27/bzYLfUu0iz3VYu2z+JVZxgCoPzshOa6ZT+V89QhxR:7AQRANdVzqUgFYdz+Bxg3PohOVG89Q |
MALICIOUS
Adds extension to the Windows Defender exclusion list
- ixixmrqrlobs.exe (PID: 6344)
- Miner.exe (PID: 1788)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2172)
XMRIG has been detected (YARA)
- svchost.exe (PID: 824)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Miner.exe (PID: 1788)
- ixixmrqrlobs.exe (PID: 6344)
Script adds exclusion extension to Windows Defender
- Miner.exe (PID: 1788)
- ixixmrqrlobs.exe (PID: 6344)
Starts SC.EXE for service management
- Miner.exe (PID: 1788)
- ixixmrqrlobs.exe (PID: 6344)
Uses powercfg.exe to modify the power settings
- Miner.exe (PID: 1788)
- ixixmrqrlobs.exe (PID: 6344)
Executable content was dropped or overwritten
- Miner.exe (PID: 1788)
- ixixmrqrlobs.exe (PID: 6344)
Process uninstalls Windows update
- wusa.exe (PID: 5756)
- wusa.exe (PID: 6432)
Starts process via Powershell
- powershell.exe (PID: 3648)
Starts POWERSHELL.EXE for commands execution
- Miner.exe (PID: 4380)
- ixixmrqrlobs.exe (PID: 6344)
- Miner.exe (PID: 1788)
Executes as Windows Service
- ixixmrqrlobs.exe (PID: 6344)
Manipulates environment variables
- powershell.exe (PID: 3000)
- powershell.exe (PID: 5508)
Drops a system driver (possible attempt to evade defenses)
- ixixmrqrlobs.exe (PID: 6344)
Script adds exclusion path to Windows Defender
- ixixmrqrlobs.exe (PID: 6344)
- Miner.exe (PID: 1788)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2172)
Connects to unusual port
- svchost.exe (PID: 824)
INFO
Checks supported languages
- Miner.exe (PID: 4380)
- ixixmrqrlobs.exe (PID: 6344)
- Miner.exe (PID: 1788)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5508)
- powershell.exe (PID: 3000)
Creates files in the program directory
- Miner.exe (PID: 1788)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5508)
- powershell.exe (PID: 3000)
The process uses the downloaded file
- powershell.exe (PID: 3648)
- powershell.exe (PID: 3000)
UPX packer has been detected
- svchost.exe (PID: 824)
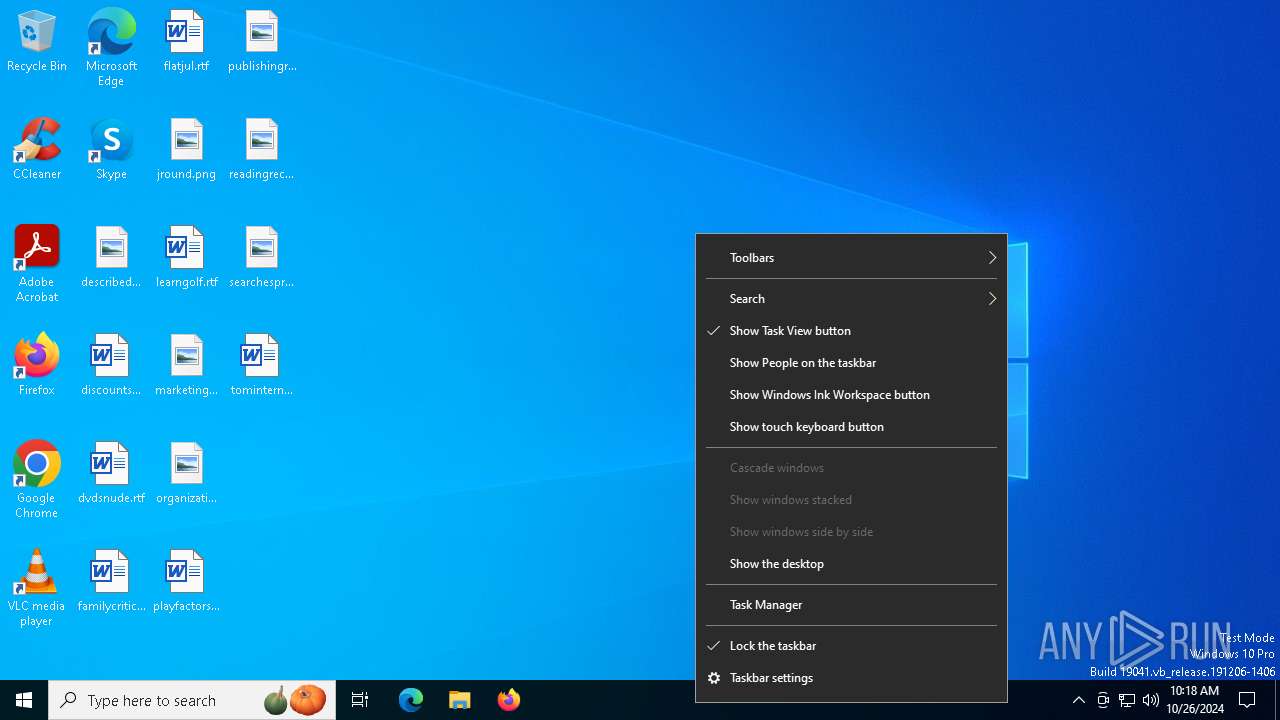
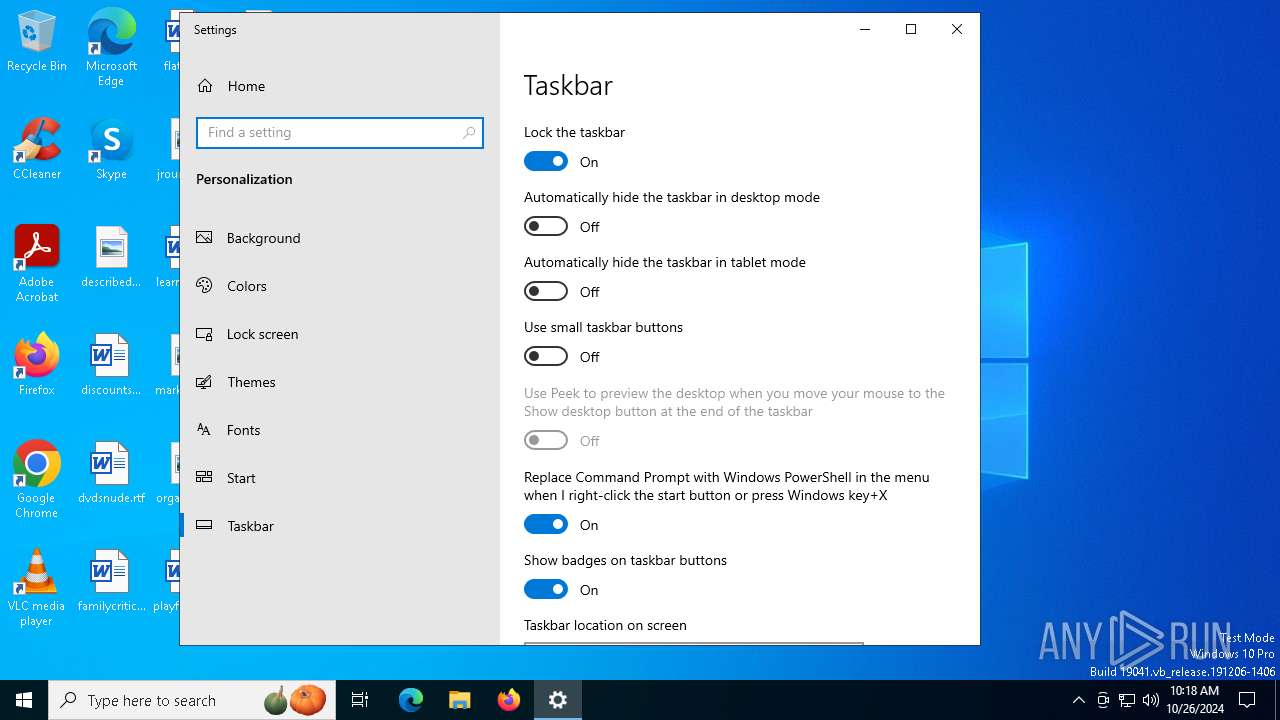
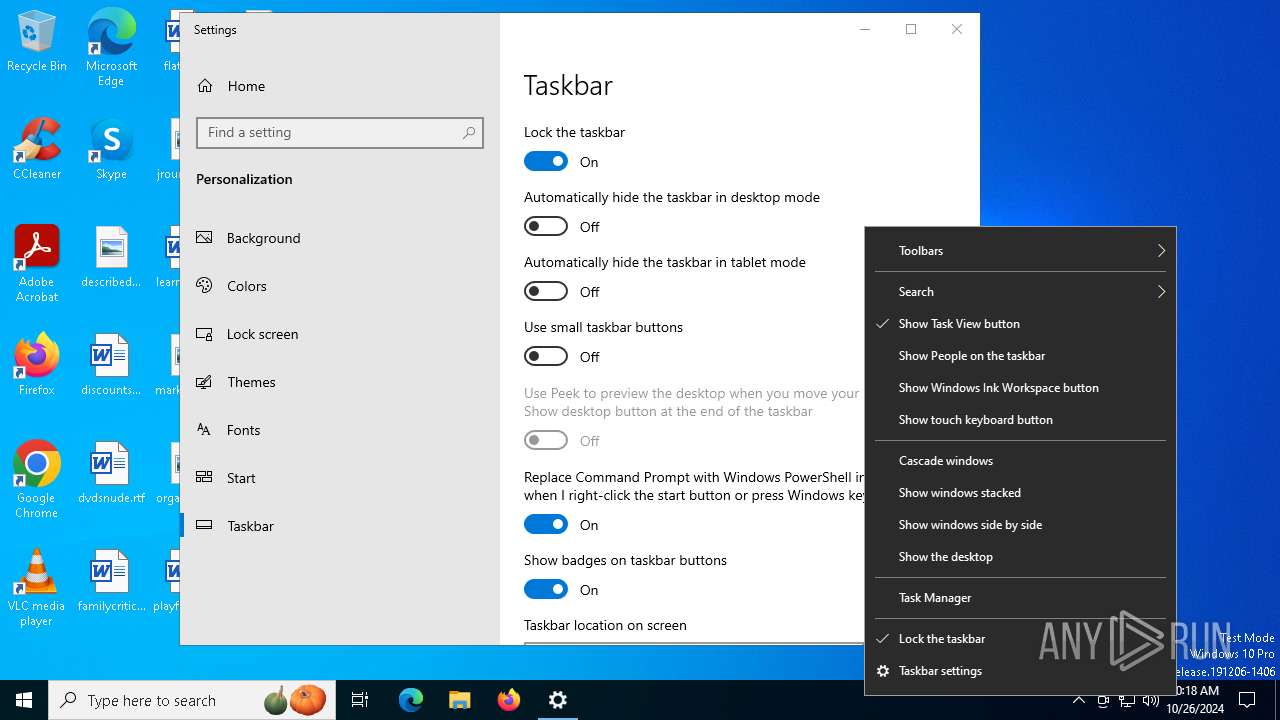
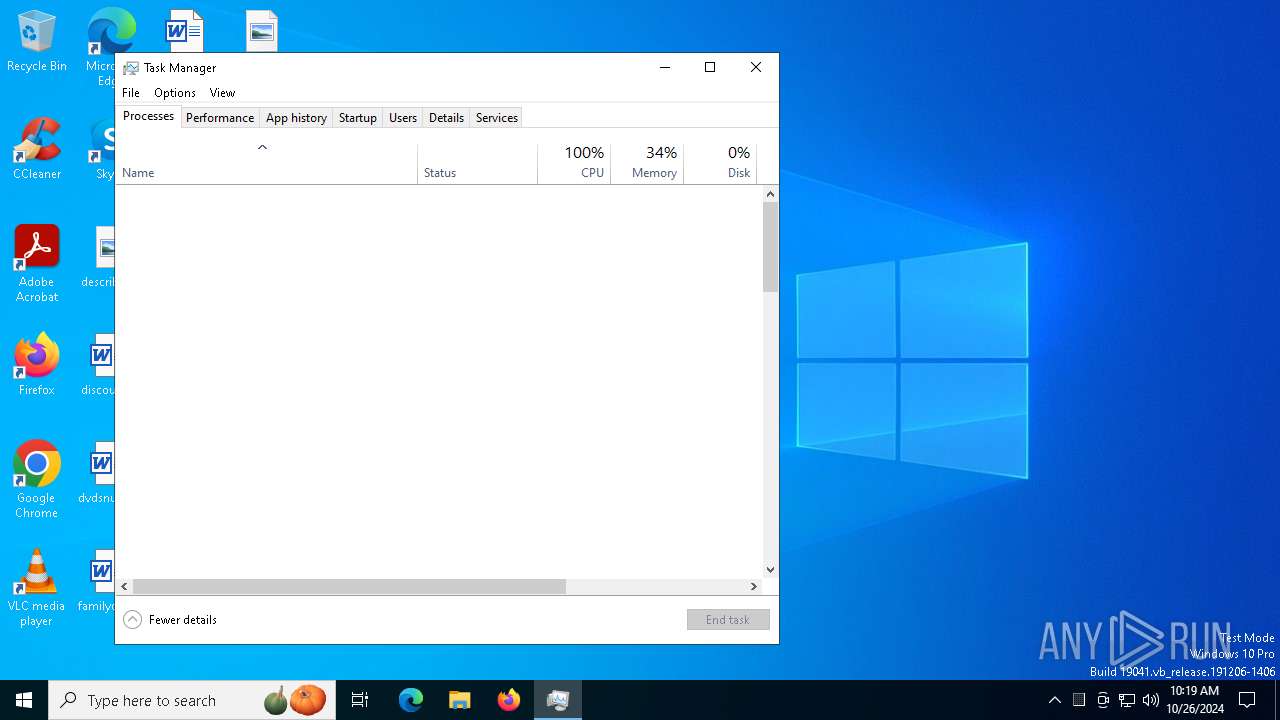
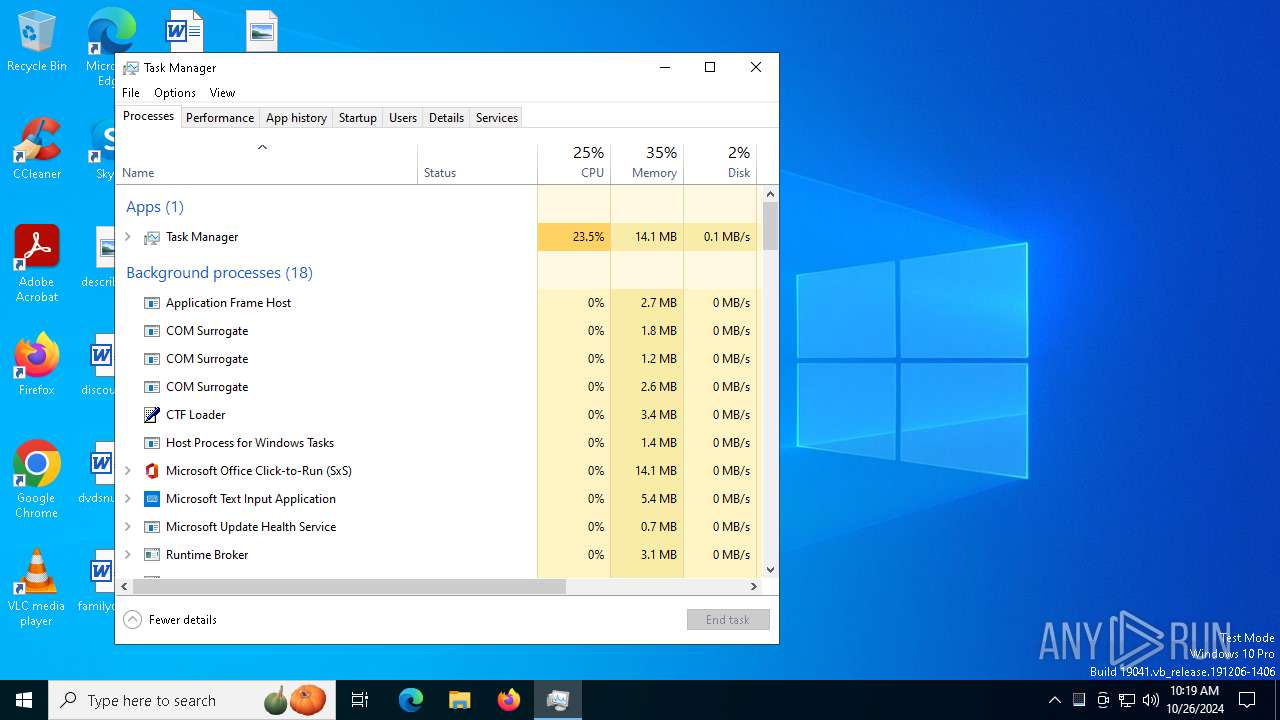
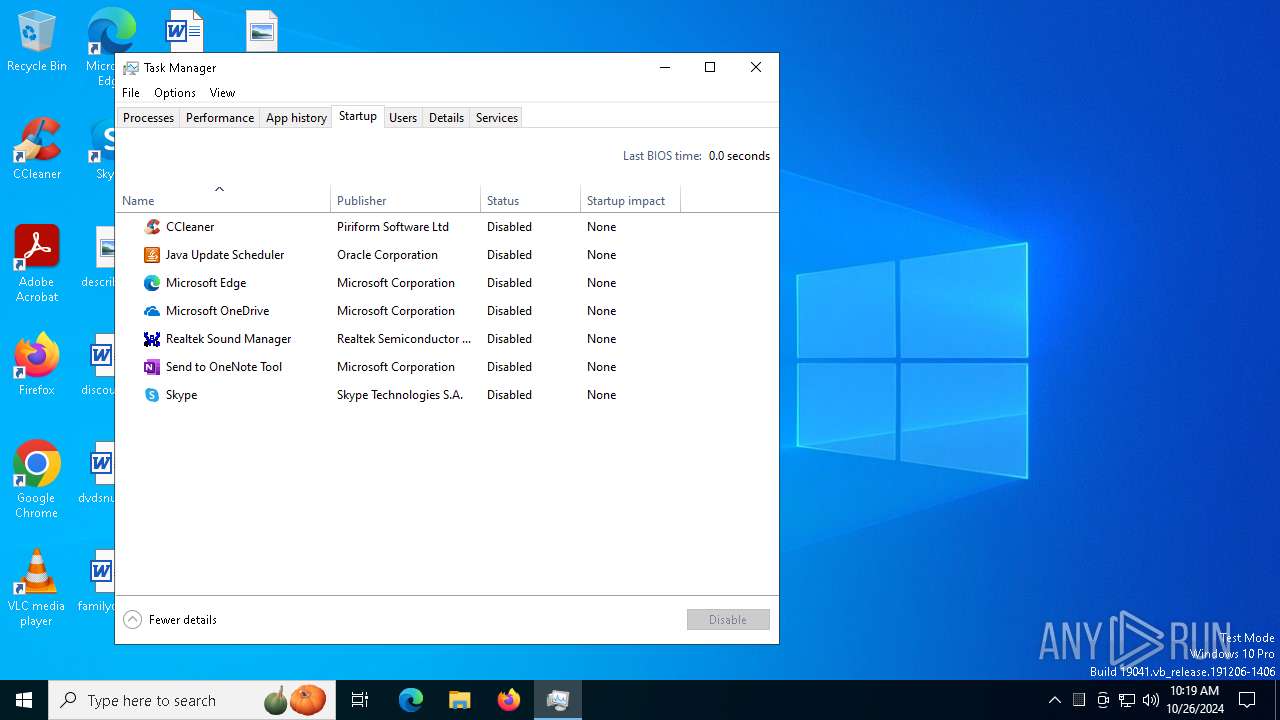
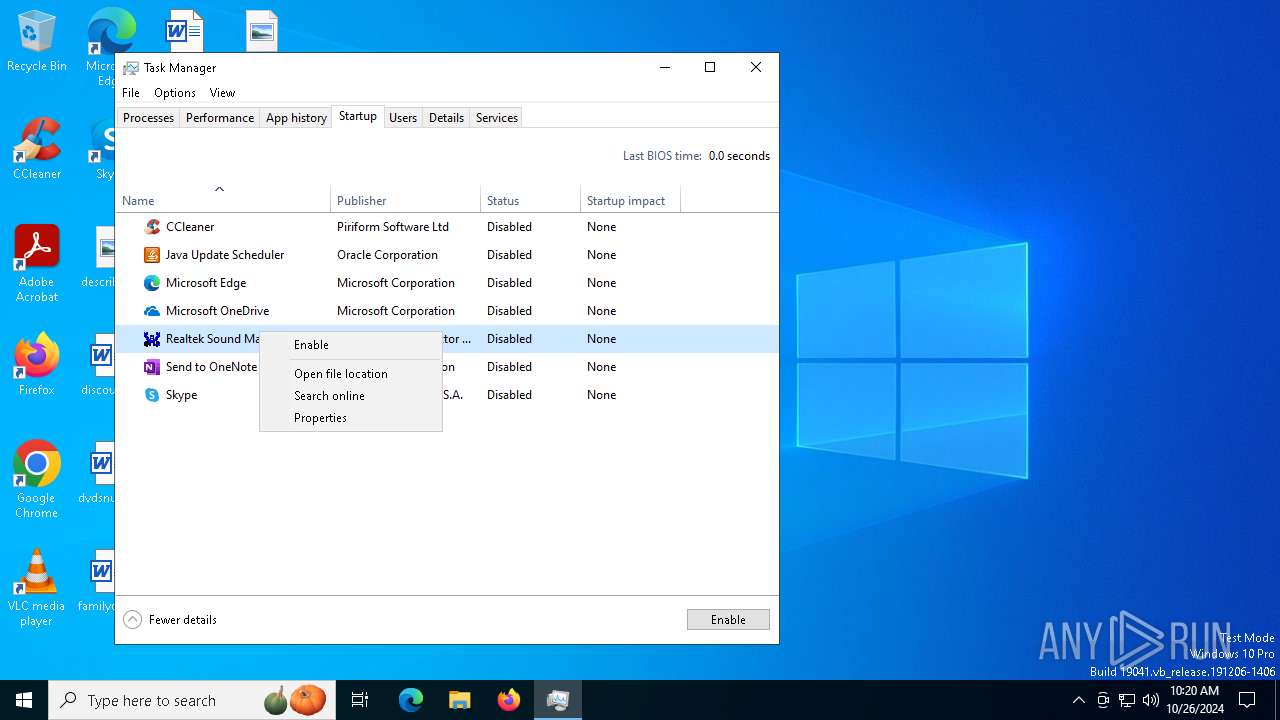
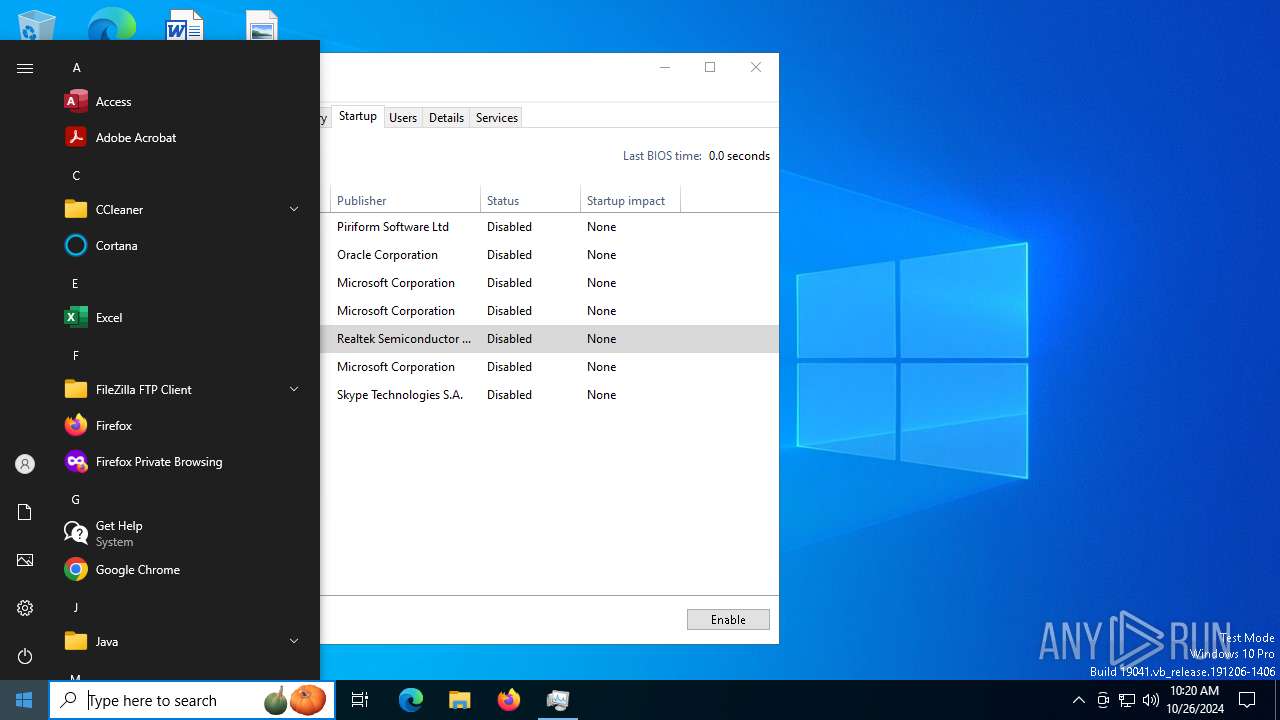
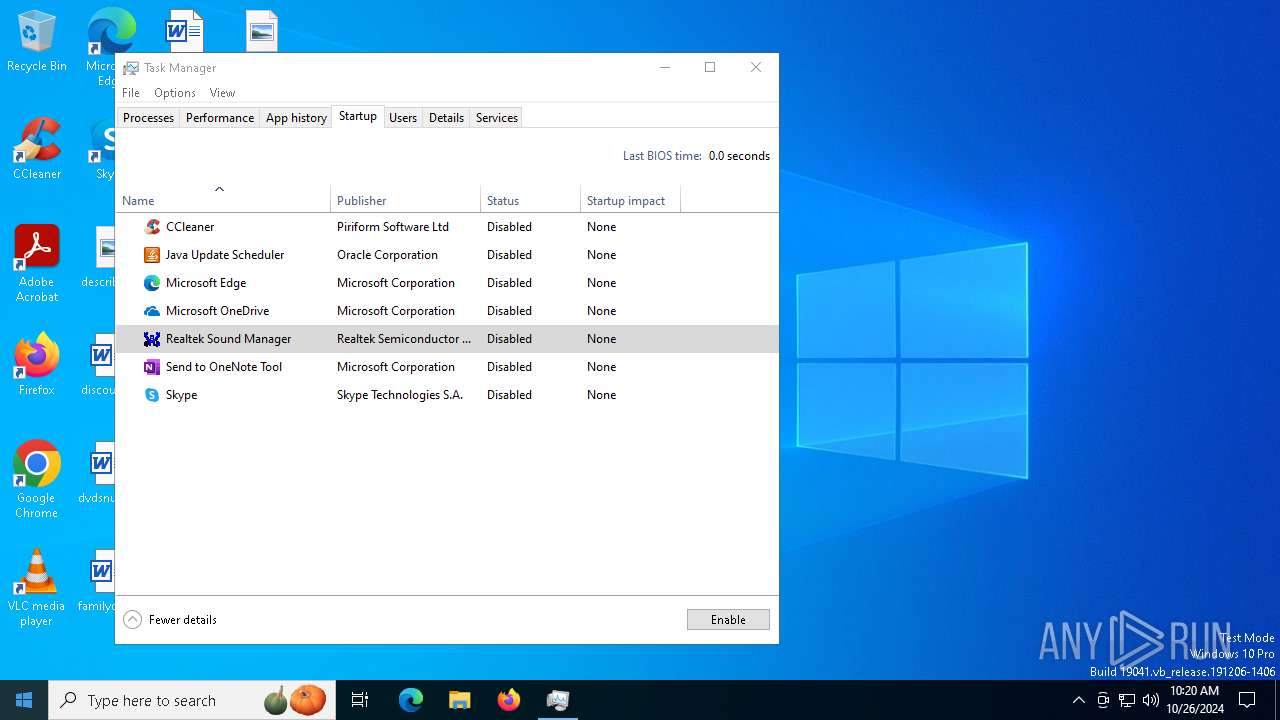
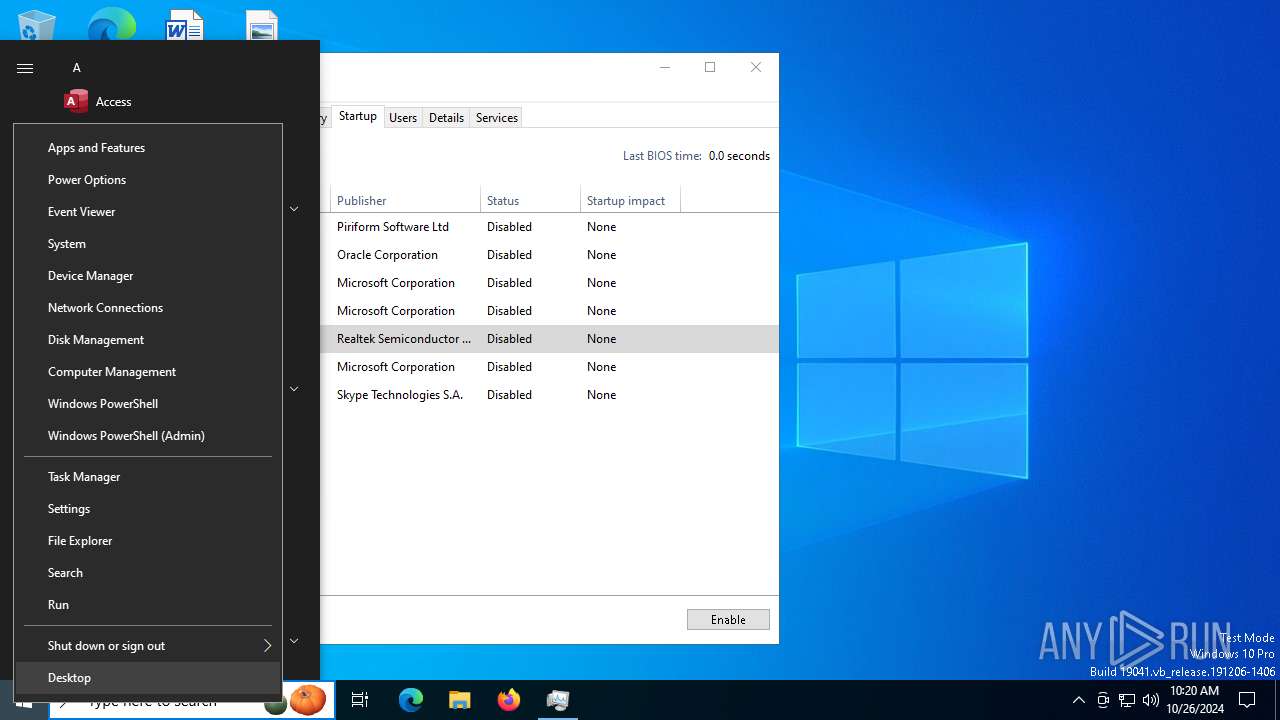
Manual execution by a user
- Taskmgr.exe (PID: 7120)
- Taskmgr.exe (PID: 5500)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7120)
The executable file from the user directory is run by the Powershell process
- Miner.exe (PID: 1788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:02:22 04:24:44+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 37888 |
| InitializedDataSize: | 2622464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1140 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 70.0.3538.110 |
| ProductVersionNumber: | 70.0.3538.110 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Google Inc. |
| FileTitle: | chrome.exe |
| FileDescription: | Google Chrome |
| FileVersion: | 70,0,3538,110 |
| LegalCopyright: | Copyright 2017 Google Inc. All rights reserved. |
| LegalTrademark: | - |
| ProductName: | Google Chrome |
| ProductVersion: | 70,0,3538,110 |
Total processes
194
Monitored processes
64
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | C:\WINDOWS\system32\sc.exe stop bits | C:\Windows\System32\sc.exe | — | Miner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 824 | svchost.exe | C:\Windows\System32\svchost.exe | ixixmrqrlobs.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 944 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | Miner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1008 | C:\WINDOWS\system32\sc.exe create "BYGPVPJQ" binpath= "C:\ProgramData\drmeevnmytpb\ixixmrqrlobs.exe" start= "auto" | C:\Windows\System32\sc.exe | — | Miner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | C:\WINDOWS\system32\sc.exe stop bits | C:\Windows\System32\sc.exe | — | ixixmrqrlobs.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1248 | C:\WINDOWS\system32\sc.exe stop wuauserv | C:\Windows\System32\sc.exe | — | Miner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | ixixmrqrlobs.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1788 | "C:\Users\admin\AppData\Local\Temp\Miner.exe" | C:\Users\admin\AppData\Local\Temp\Miner.exe | powershell.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 70,0,3538,110 Modules
| |||||||||||||||
Total events
17 926
Read events
17 914
Write events
11
Delete events
1
Modification events
| (PID) Process: | (1788) Miner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MRT |
| Operation: | write | Name: | DontOfferThroughWUAU |
Value: 1 | |||
| (PID) Process: | (6344) ixixmrqrlobs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MRT |
| Operation: | write | Name: | DontOfferThroughWUAU |
Value: 1 | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100016B00000034000000130300008C020000E80300000000000000000000000000000F000000010000000000000058AAE92EF77F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AAE92EF77F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AAE92EF77F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AAE92EF77F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AAE92EF77F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000ABE92EF77F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028ABE92EF77F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050ABE92EF77F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AAE92EF77F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070ABE92EF77F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088ABE92EF77F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8ABE92EF77F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8ABE92EF77F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0ABE92EF77F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010ACE92EF77F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AAE92EF77F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AAE92EF77F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AAE92EF77F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040ACE92EF77F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068ACE92EF77F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090ACE92EF77F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8ACE92EF77F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8ACE92EF77F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8ACE92EF77F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028ABE92EF77F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AAE92EF77F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020ADE92EF77F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040ADE92EF77F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068ADE92EF77F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AAE92EF77F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050ABE92EF77F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AAE92EF77F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070ABE92EF77F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088ABE92EF77F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8ABE92EF77F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8ABE92EF77F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AAE92EF77F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088ADE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8ADE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0ADE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AEE92EF77F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AEE92EF77F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AEE92EF77F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AEE92EF77F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | write | Name: | CCleaner Smart Cleaning |
Value: 03000000388271EEFD58DA01 | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run32 |
| Operation: | write | Name: | SunJavaUpdateSched |
Value: 030000006B0EA3ECFD58DA01 | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: 030000002B498EF9C8B7D801 | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | write | Name: | OneDrive |
Value: 03000000A31484EEAAD7D301 | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | write | Name: | SoundMan |
Value: 030000009F7A12EAC6B7D801 | |||
| (PID) Process: | (7120) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\StartupFolder |
| Operation: | write | Name: | Send to OneNote.lnk |
Value: 030000004443A9558E3CD901 | |||
Executable files
2
Suspicious files
2
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3eppq3cl.d3b.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3000 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_2ccys21a.ktl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5508 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yzyaksjt.1c2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3000 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_43dpzrsv.h0i.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3648 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:23C70B5659475B969C604E1028272DF7 | SHA256:0F3D6FDF1BF8D0D1A863FADA7822E850E06A0B9AFEF42DCA3707B6A4063AC72B | |||
| 3000 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_wkwcm1ml.vpz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1788 | Miner.exe | C:\ProgramData\drmeevnmytpb\ixixmrqrlobs.exe | executable | |
MD5:BEEC454529E5BCCF2CC5D28F6B929477 | SHA256:E58724D3BFB58D98746F2AFB6988089A9013105AE3BC09F8BA60987BEFCA14AF | |||
| 3648 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0ab1szlu.0us.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5508 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0na1slf2.qlk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1788 | Miner.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:F934CAB2B2E99CA5ABABE0226594C202 | SHA256:473F615D29AB25CB3C4EAE4A209FD733DB544AC2D444B2720AC97D913D44FABB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
210
DNS requests
29
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3608 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
624 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3608 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3740 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2372 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER Observed DNS Query to Cryptocurrency Mining Pool Domain (xmr .2miners .com) |
2172 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER Observed DNS Query to Cryptocurrency Mining Pool Domain (xmr .2miners .com) |
— | — | Crypto Currency Mining Activity Detected | ET COINMINER Observed DNS Query to Cryptocurrency Mining Pool Domain (xmr .2miners .com) |