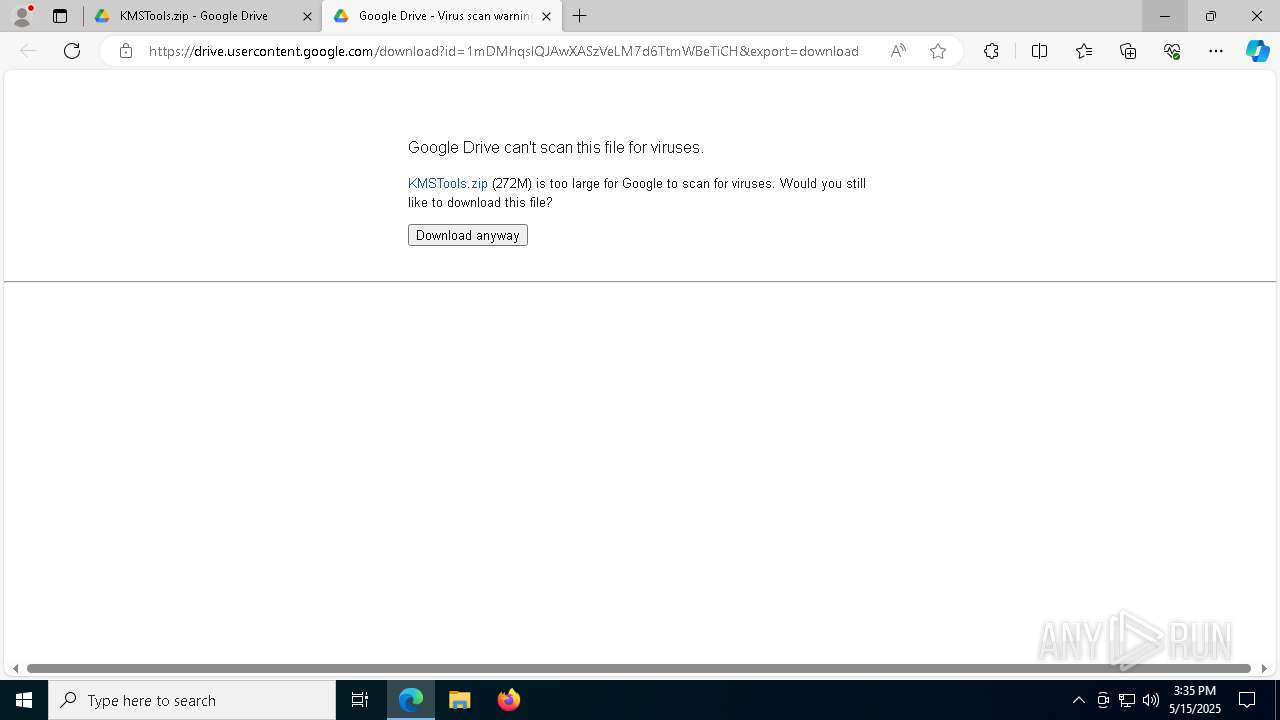
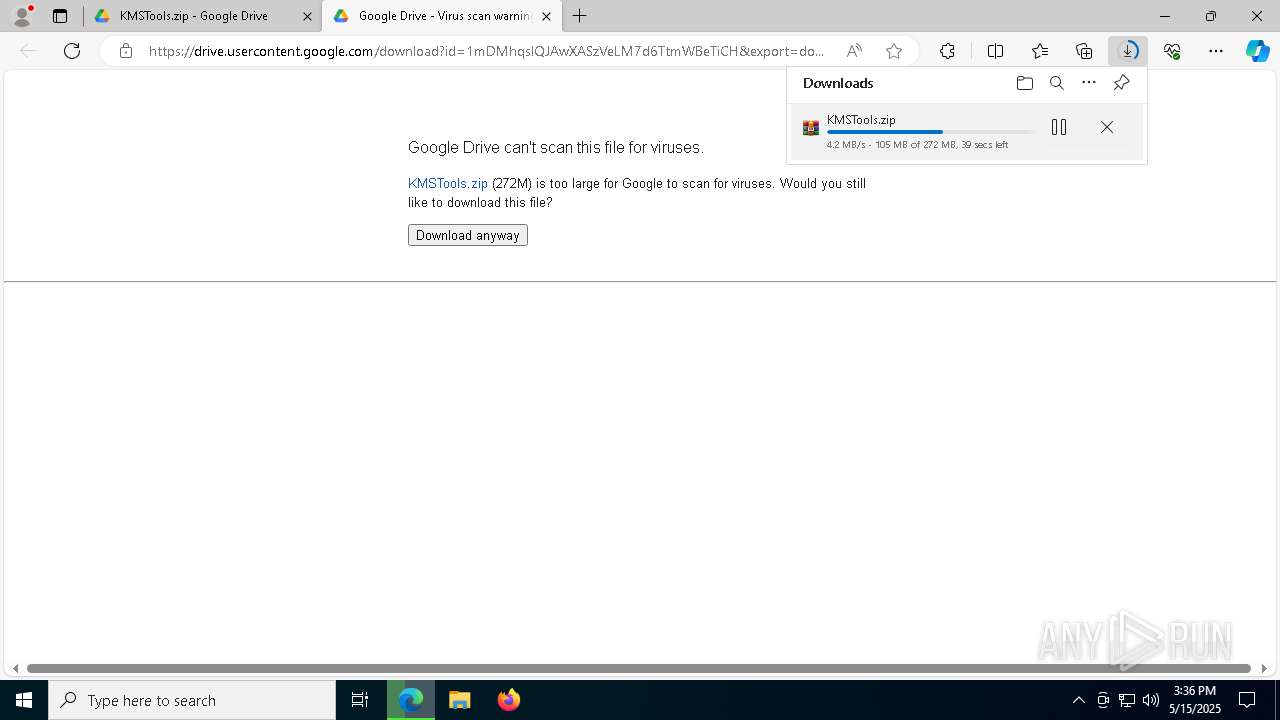
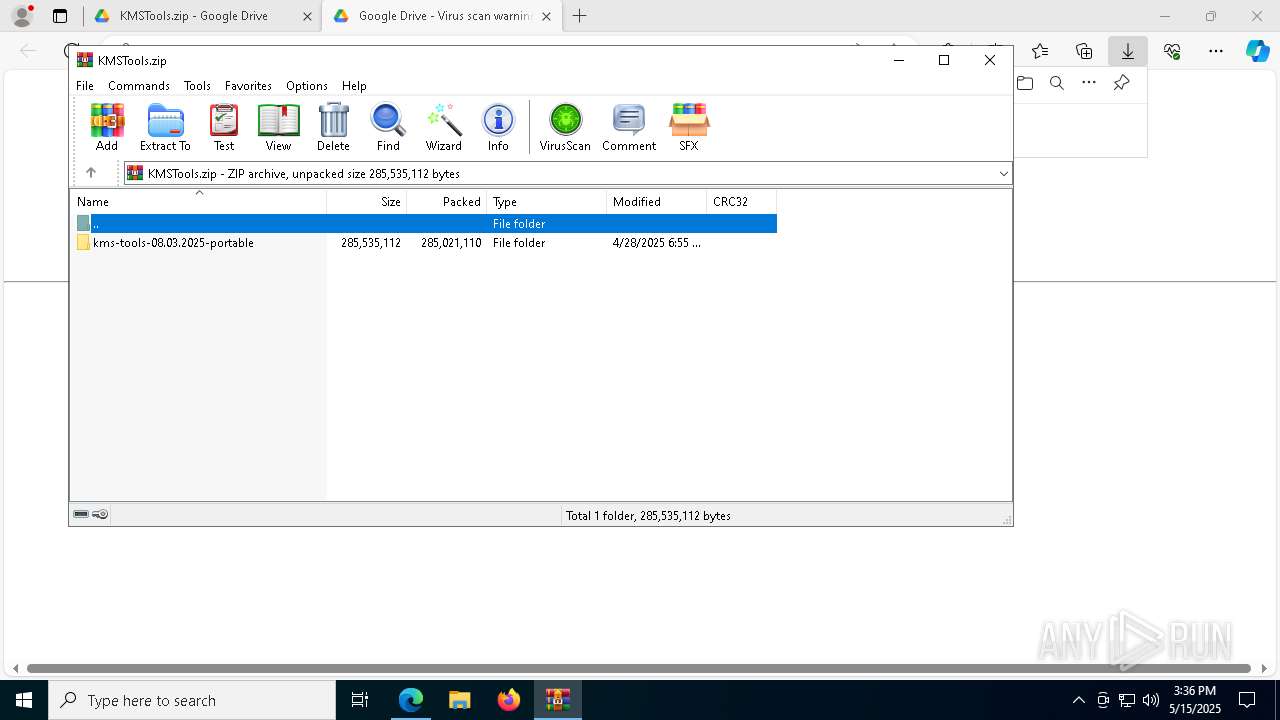
| URL: | https://drive.google.com/file/d/1mDMhqslQJAwXASzVeLM7d6TtmWBeTiCH/view?usp=drive_link |
| Full analysis: | https://app.any.run/tasks/b17c6d3c-1de7-422f-b762-dff50db9b165 |
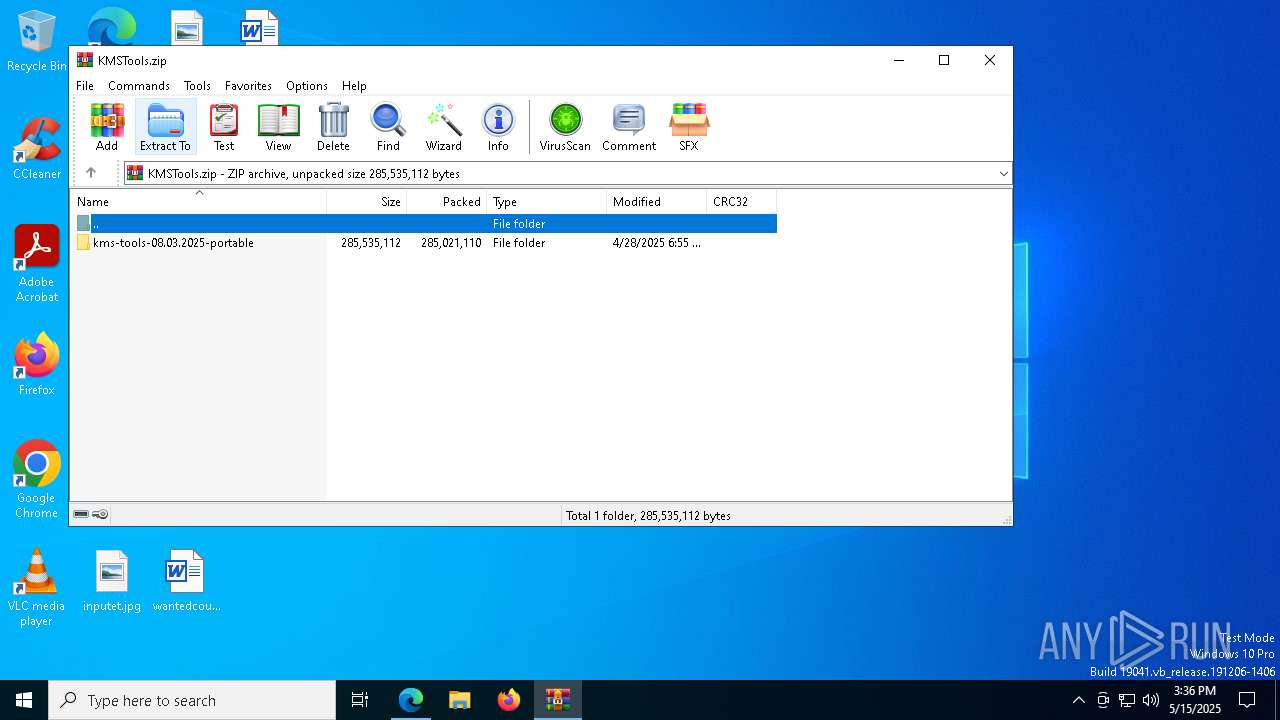
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | May 15, 2025, 15:35:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E99B17439146B392E7C437A0FEE49674 |
| SHA1: | A41434553C647F585ED097EF54FC3BF6E9C953CE |
| SHA256: | E53317C6316411144B42C4794592CD0C42017AE6E4780B01A5200976D23A3D62 |
| SSDEEP: | 3:N8PMMtZJuloLuG4IoSyyVmtKl7rMiM6:2Ay3tOKJrNM6 |
MALICIOUS
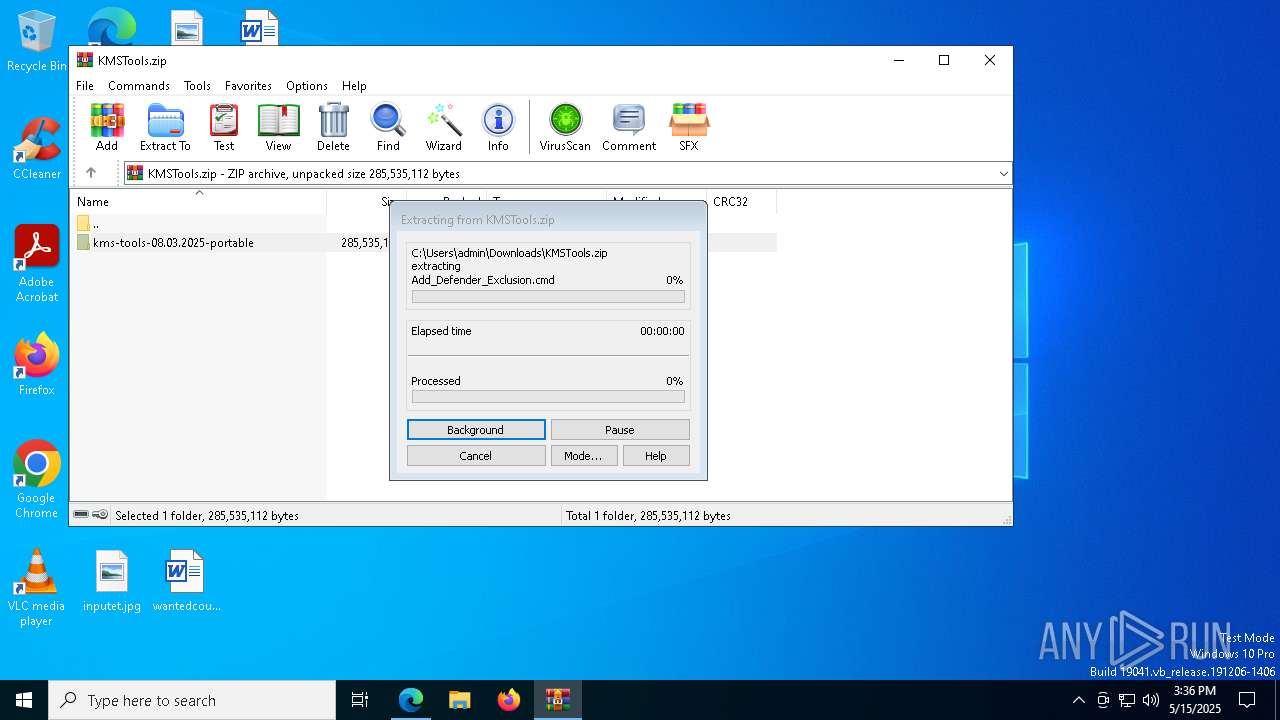
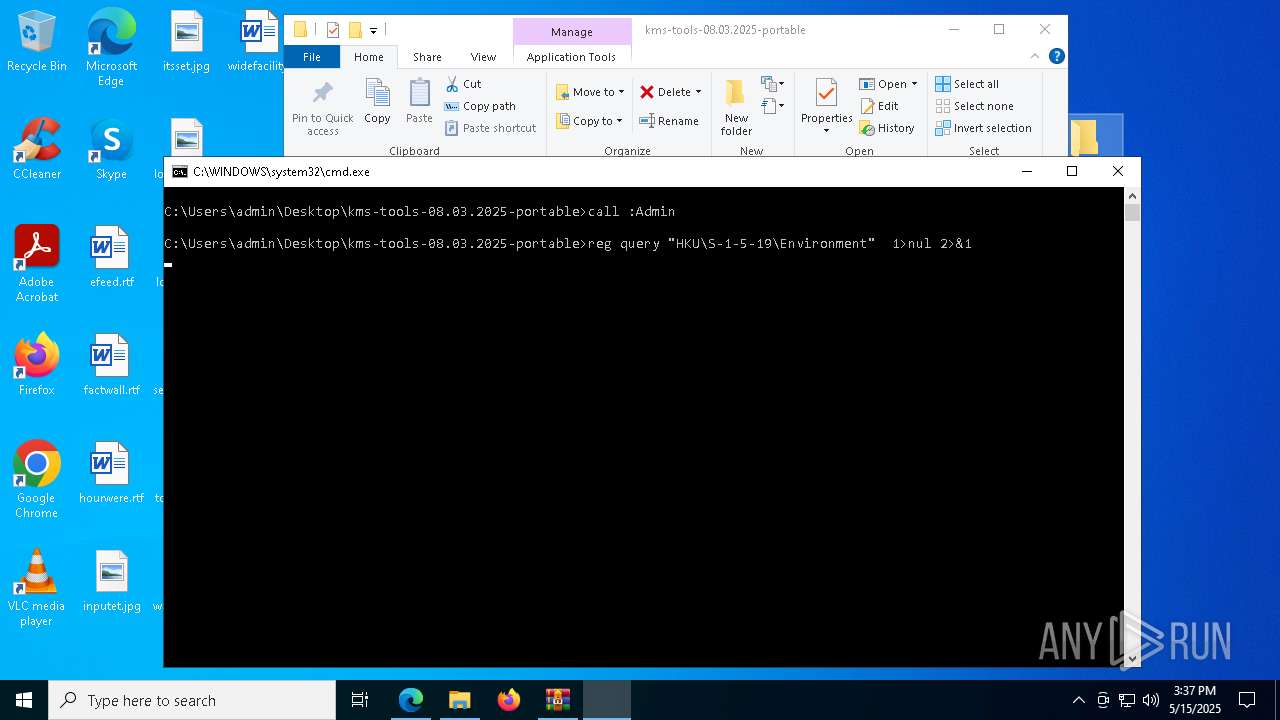
Run PowerShell with an invisible window
- powershell.exe (PID: 7912)
- powershell.exe (PID: 8008)
Changes Windows Defender settings
- cmd.exe (PID: 5452)
- cmd.exe (PID: 7920)
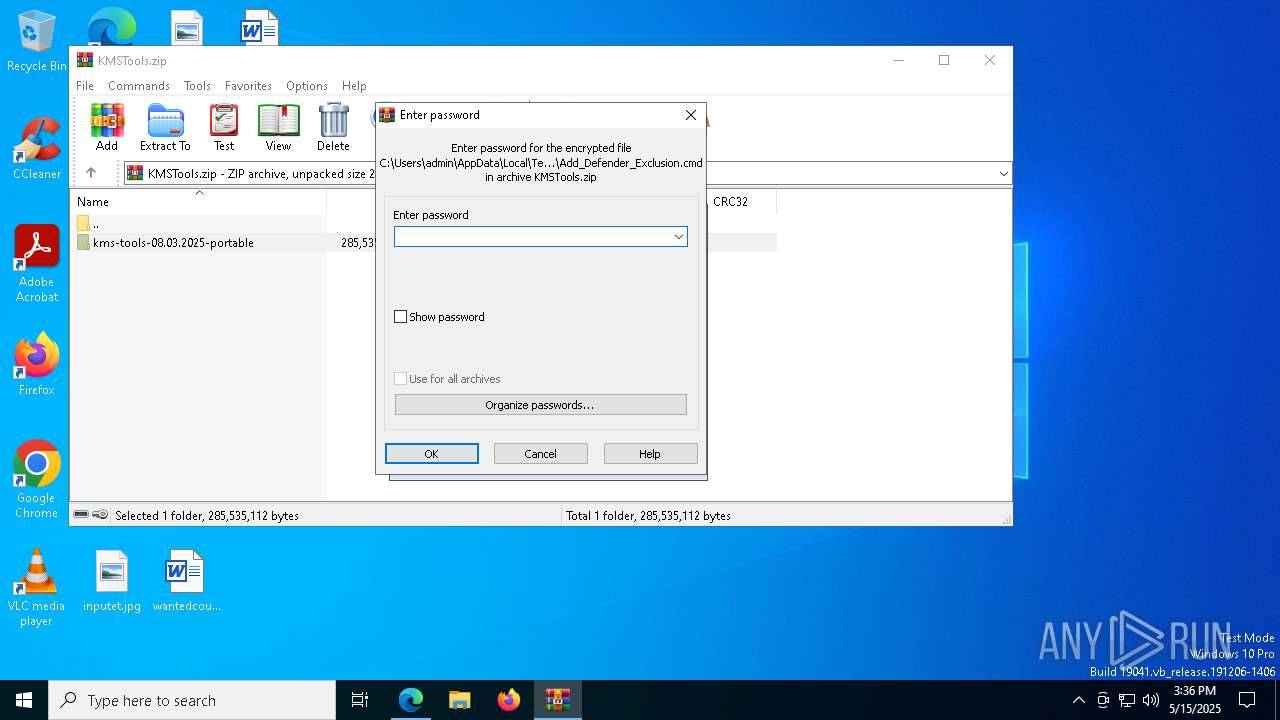
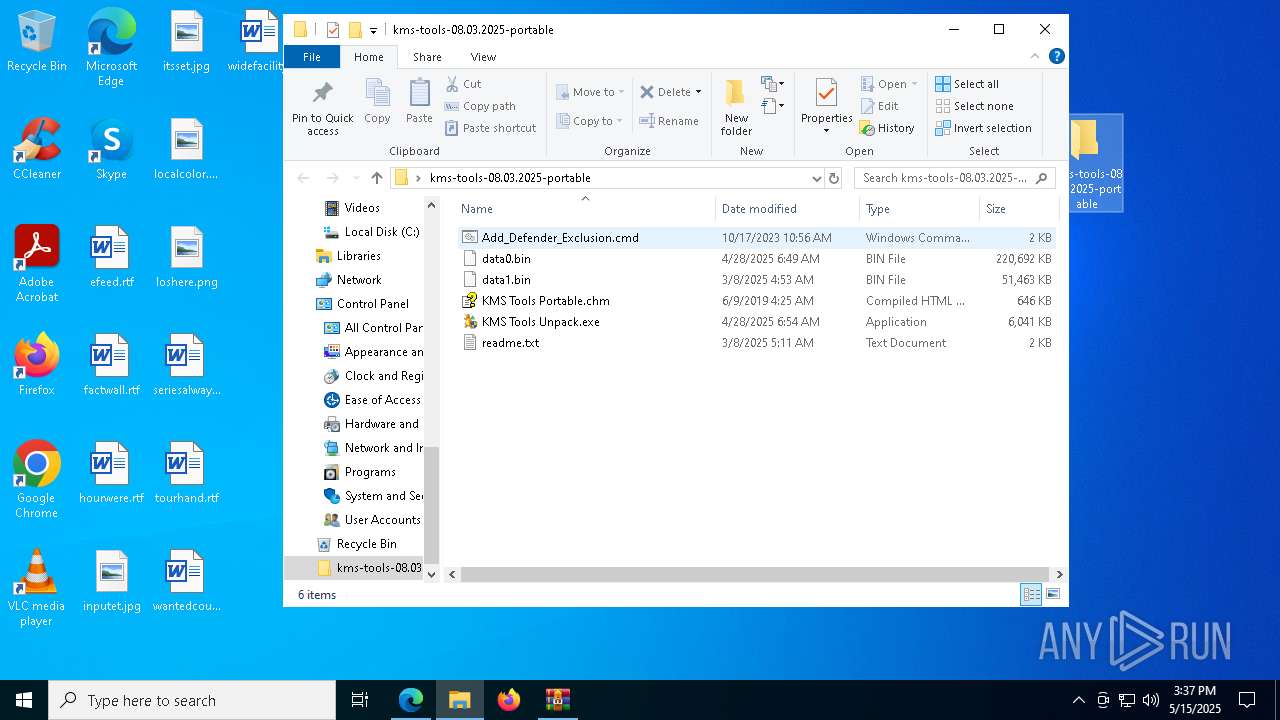
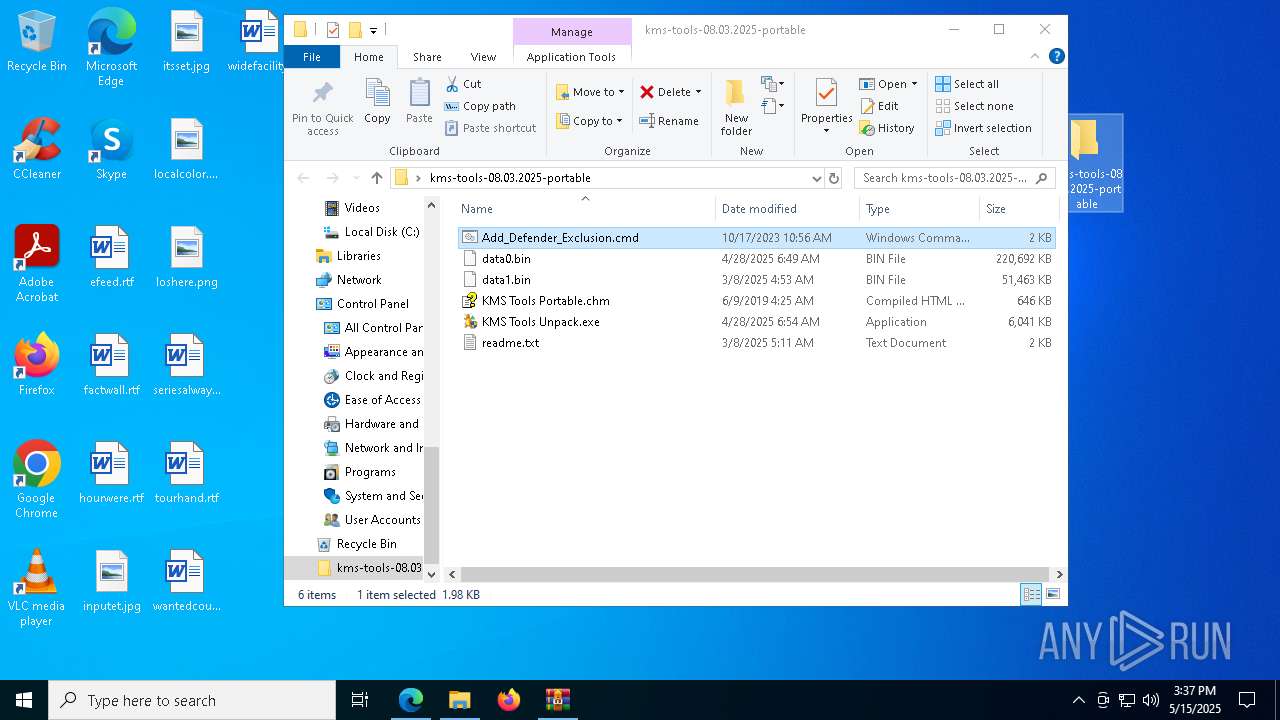
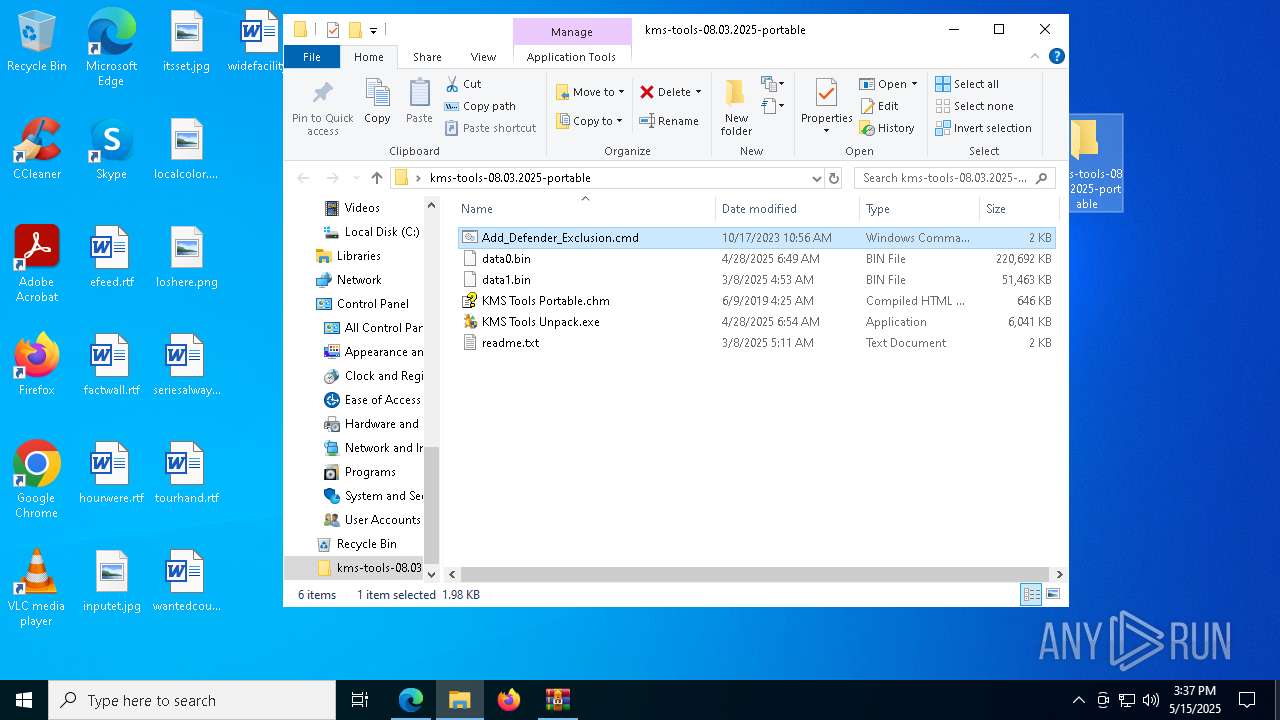
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 5452)
- GSetup.exe (PID: 7928)
- cmd.exe (PID: 7920)
Uses Task Scheduler to run other applications
- update.exe (PID: 4304)
- smss.exe (PID: 4108)
Changes powershell execution policy (Bypass)
- update.exe (PID: 4304)
Uses Task Scheduler to autorun other applications
- update.exe (PID: 4304)
- smss.exe (PID: 4108)
Bypass execution policy to execute commands
- powershell.exe (PID: 6908)
GENERIC has been found (auto)
- IP.exe (PID: 2108)
RMS has been detected (YARA)
- winserv.exe (PID: 7772)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6712)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 7920)
Starts process via Powershell
- powershell.exe (PID: 7912)
Executing commands from ".cmd" file
- powershell.exe (PID: 7912)
Found strings related to reading or modifying Windows Defender settings
- powershell.exe (PID: 7912)
- update.exe (PID: 4304)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6712)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 7920)
- update.exe (PID: 4304)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7912)
- GSetup.exe (PID: 7928)
- update.exe (PID: 4304)
- IP.exe (PID: 2108)
- smss.exe (PID: 4108)
Script uses the treat ID number to allow Windows Defender to execute it
- cmd.exe (PID: 5452)
- cmd.exe (PID: 7920)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5452)
- cmd.exe (PID: 7920)
The process hide an interactive prompt from the user
- cmd.exe (PID: 5452)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 5452)
Process drops legitimate windows executable
- install.exe (PID: 5044)
- IP.exe (PID: 2108)
- RDPWinst.exe (PID: 4784)
Executing commands from a ".bat" file
- GSetup.exe (PID: 7928)
- IP.exe (PID: 2108)
- smss.exe (PID: 4108)
- update.exe (PID: 4304)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 4980)
The process executes Powershell scripts
- update.exe (PID: 4304)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 4756)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 3800)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 232)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 7008)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 5428)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 4220)
- cmd.exe (PID: 1272)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 5216)
- cmd.exe (PID: 1176)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 5624)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 208)
- cmd.exe (PID: 5020)
- cmd.exe (PID: 976)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 1272)
- cmd.exe (PID: 1176)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 5232)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 832)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 1584)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 1516)
- cmd.exe (PID: 4184)
- cmd.exe (PID: 4692)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 2316)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 5484)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 2316)
- cmd.exe (PID: 3264)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 5024)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 5796)
- cmd.exe (PID: 1664)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 828)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 4308)
- cmd.exe (PID: 5232)
- cmd.exe (PID: 3960)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 3744)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 4756)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 5812)
- cmd.exe (PID: 1272)
Executable content was dropped or overwritten
- update.exe (PID: 4304)
- install.exe (PID: 5044)
- svchost.exe (PID: 8092)
- IP.exe (PID: 2108)
- RDPWinst.exe (PID: 4784)
- smss.exe (PID: 4108)
Application launched itself
- winserv.exe (PID: 6272)
Potential Corporate Privacy Violation
- smss.exe (PID: 4108)
- svchost.exe (PID: 2196)
- winserv.exe (PID: 7772)
Checks for external IP
- smss.exe (PID: 4108)
- svchost.exe (PID: 2196)
Uses NETSH.EXE to add a firewall rule or allowed programs
- RDPWinst.exe (PID: 4784)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8104)
- cmd.exe (PID: 6032)
- cmd.exe (PID: 6384)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2780)
- cmd.exe (PID: 7940)
The process executes via Task Scheduler
- unsecapp.exe (PID: 4424)
- winserv.exe (PID: 2028)
Stops a currently running service
- sc.exe (PID: 5756)
- sc.exe (PID: 6972)
Starts SC.EXE for service management
- cmd.exe (PID: 7036)
- cmd.exe (PID: 828)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 5452)
- cmd.exe (PID: 3760)
Windows service management via SC.EXE
- sc.exe (PID: 3192)
- sc.exe (PID: 1856)
- sc.exe (PID: 1516)
- sc.exe (PID: 1516)
INFO
Reads the software policy settings
- slui.exe (PID: 7548)
- slui.exe (PID: 5728)
Application launched itself
- msedge.exe (PID: 2140)
Checks supported languages
- identity_helper.exe (PID: 5544)
Reads Environment values
- identity_helper.exe (PID: 5544)
Reads the computer name
- identity_helper.exe (PID: 5544)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2140)
The sample compiled with russian language support
- WinRAR.exe (PID: 5548)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5548)
- msedge.exe (PID: 5936)
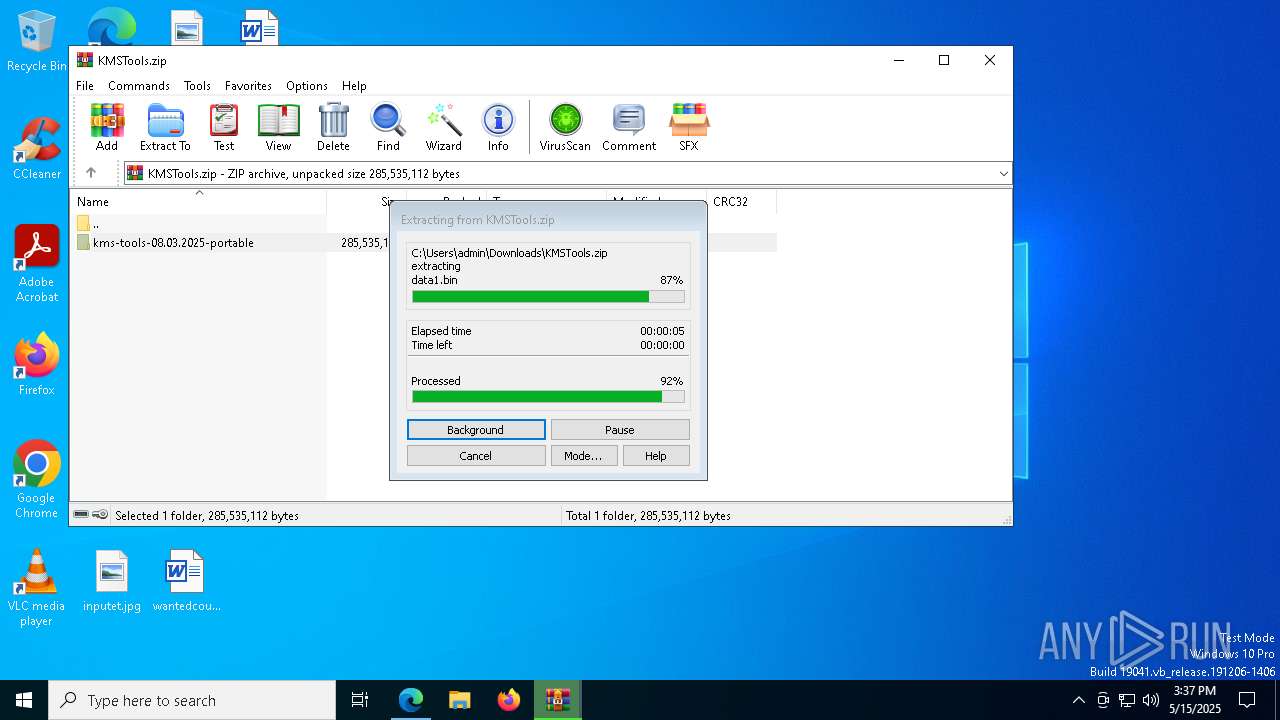
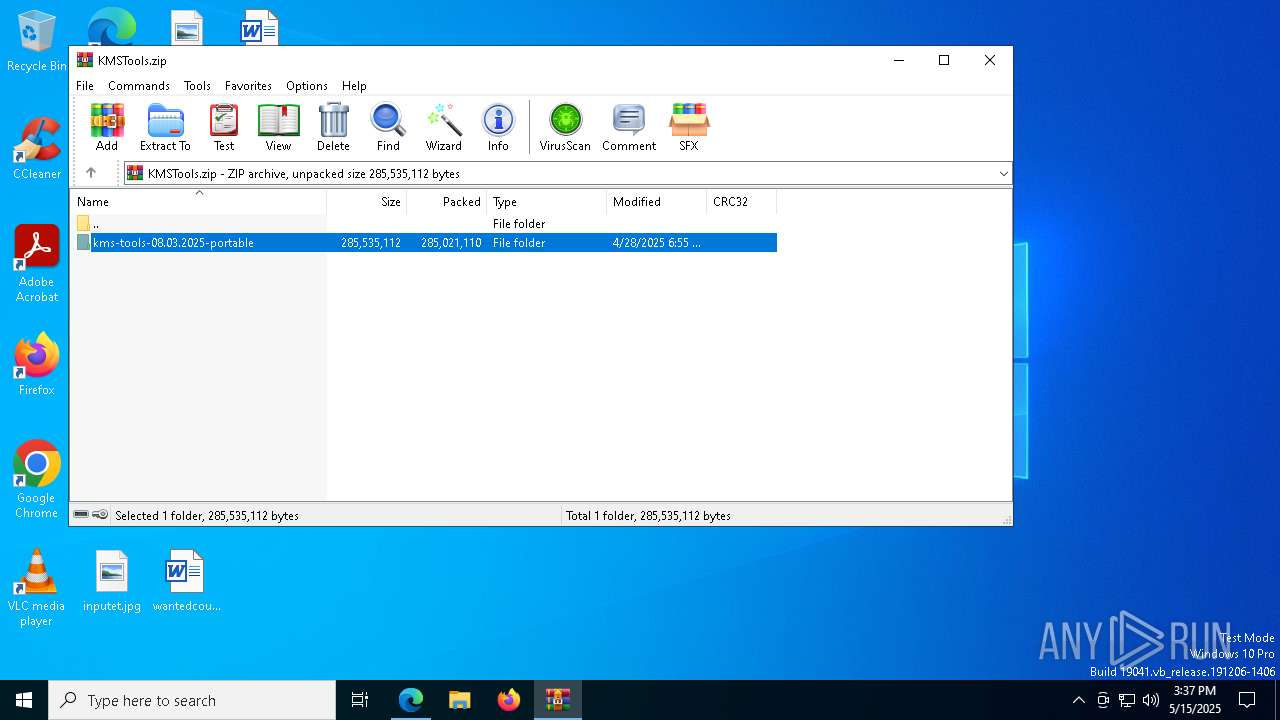
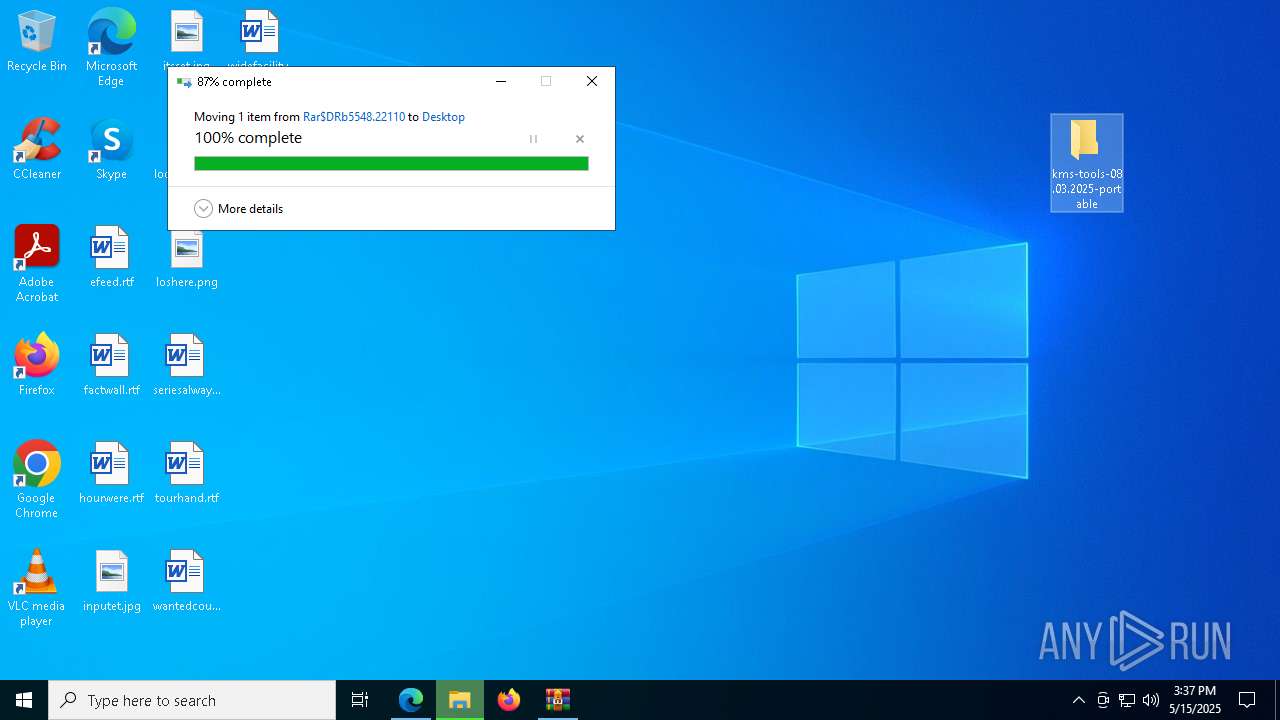
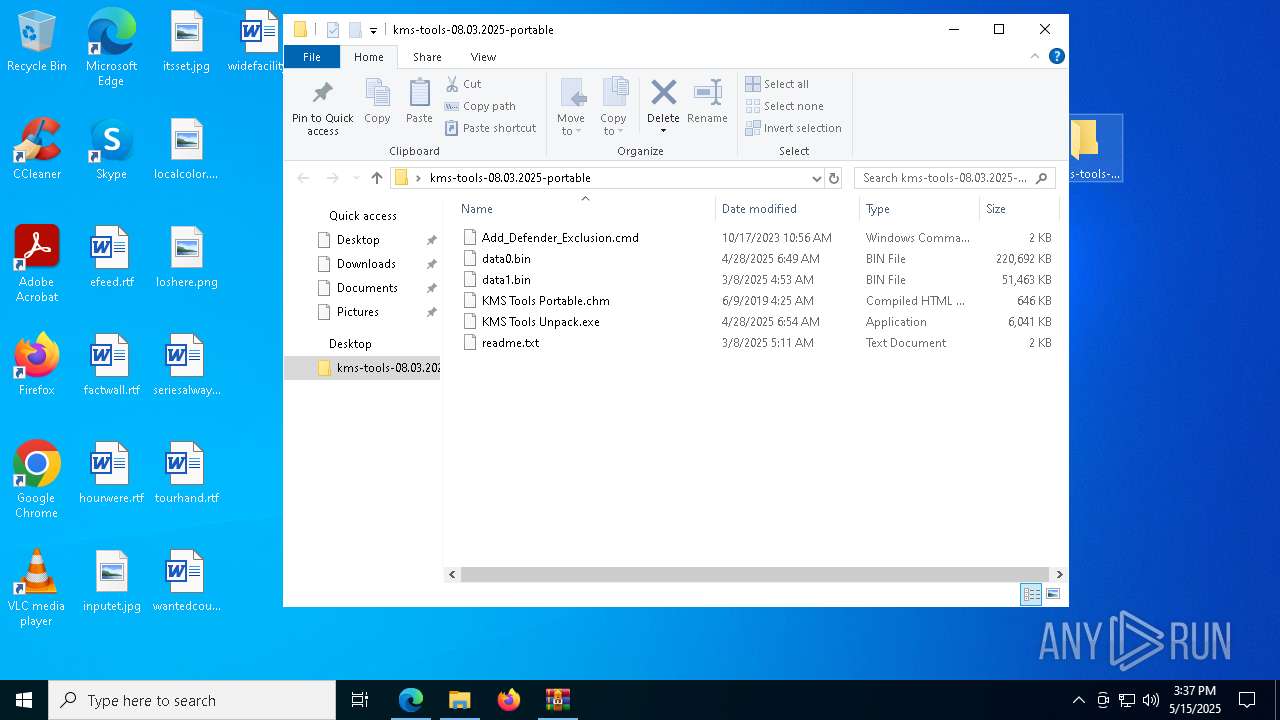
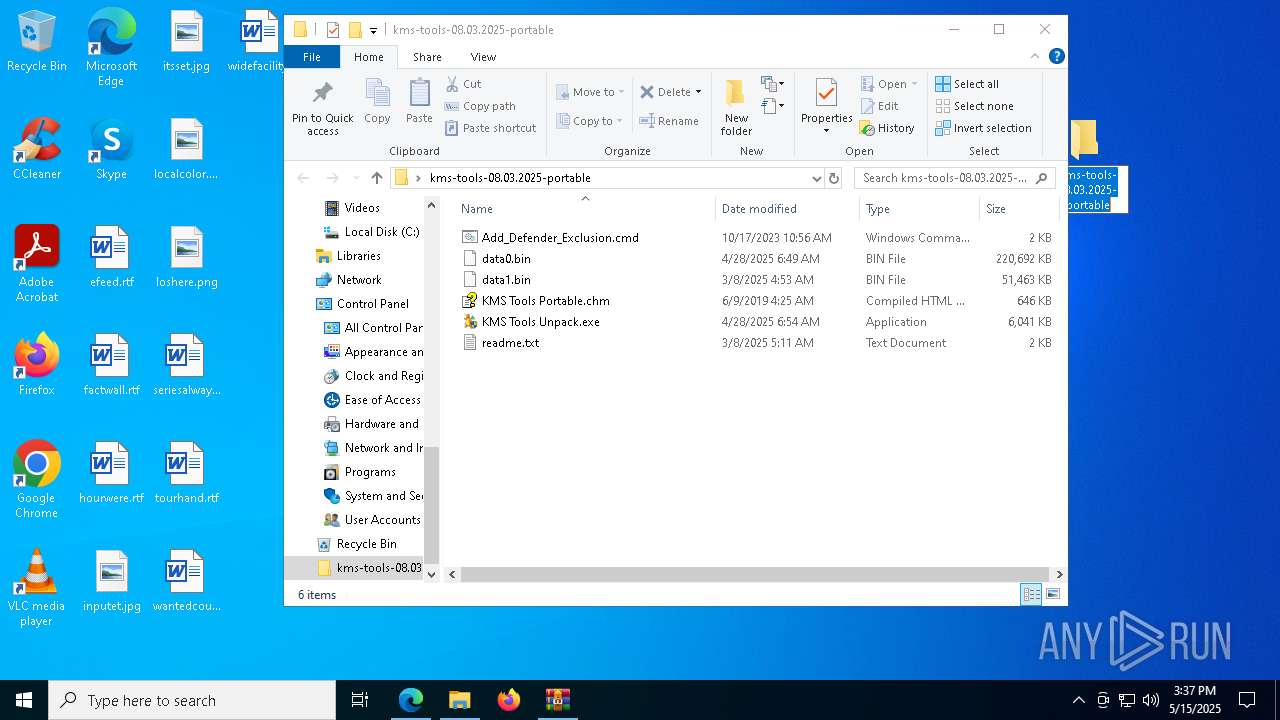
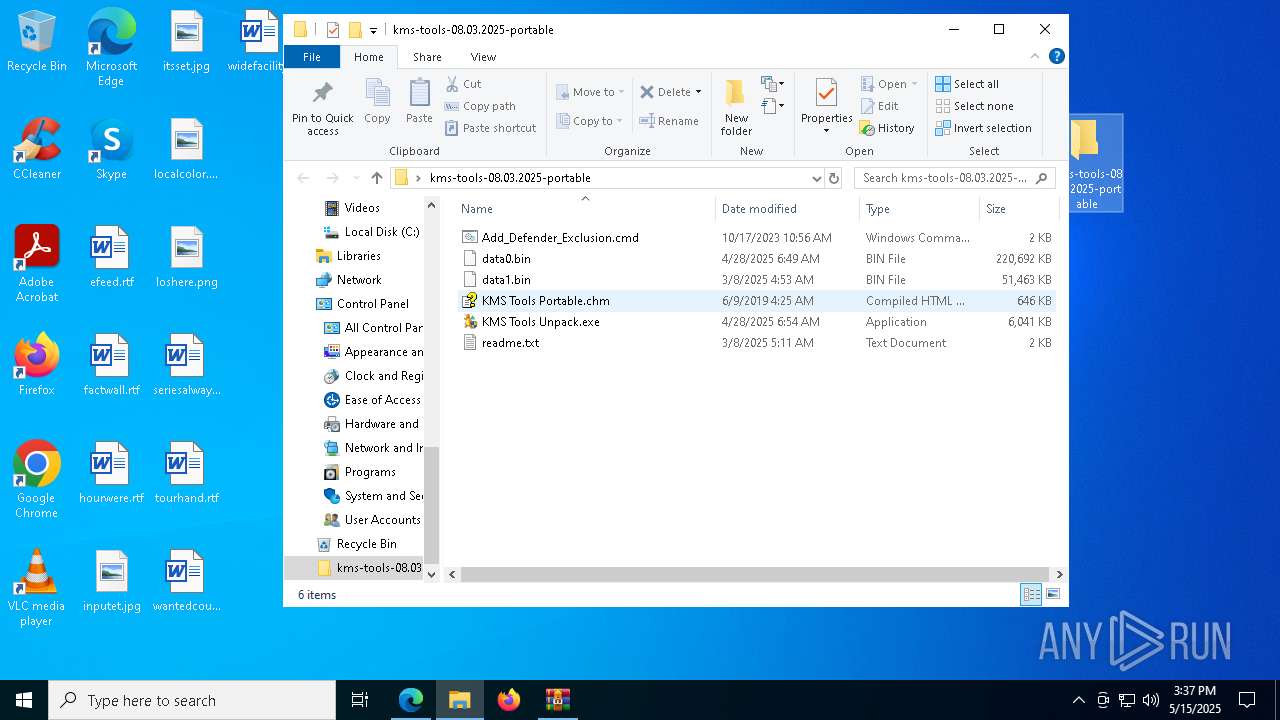
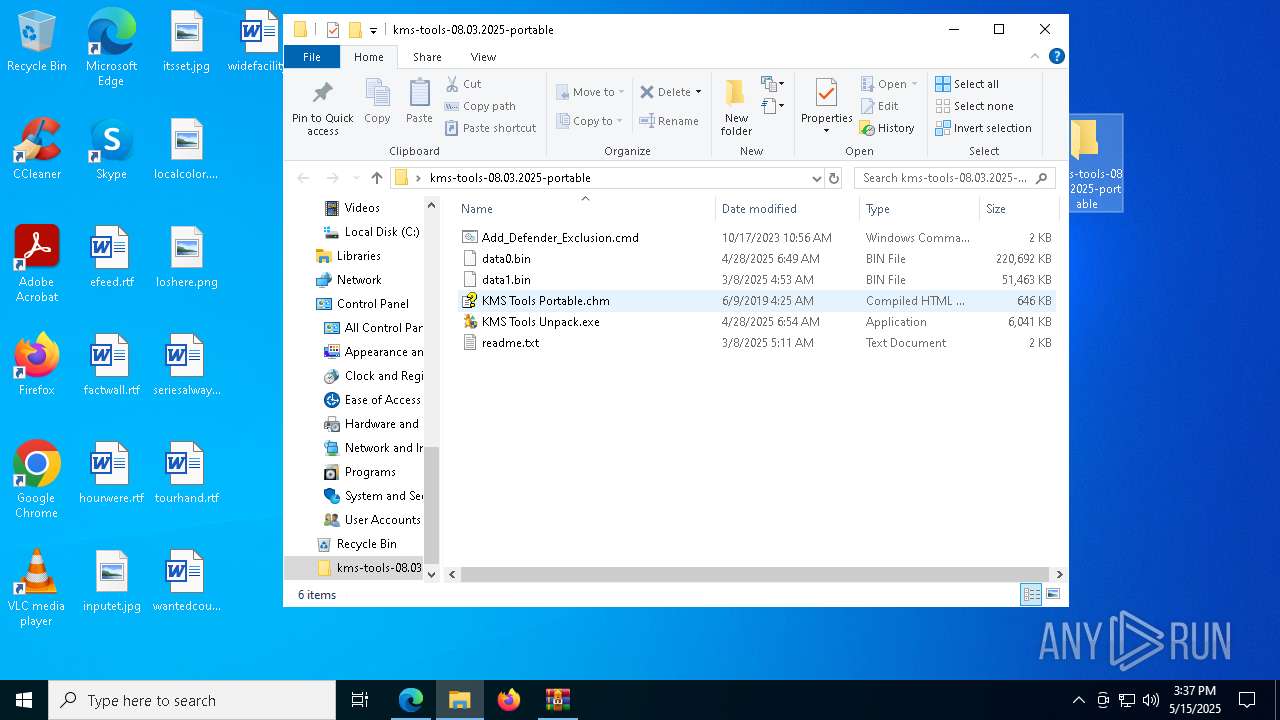
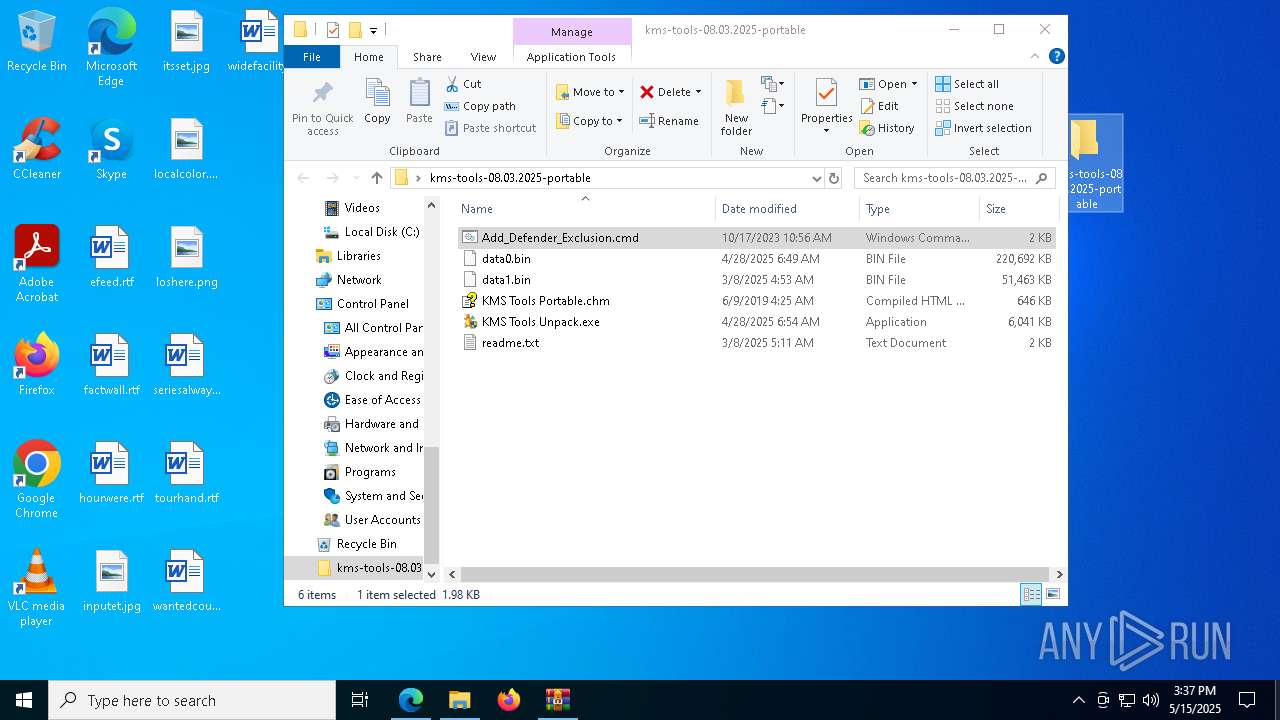
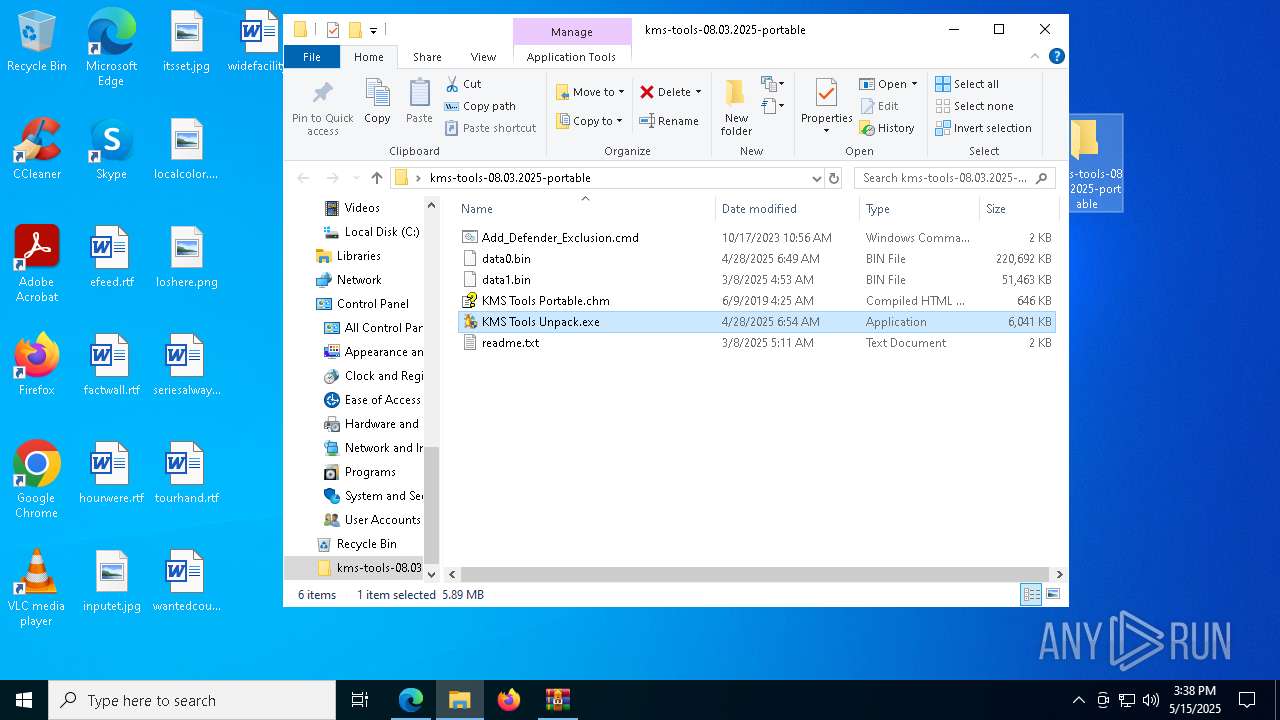
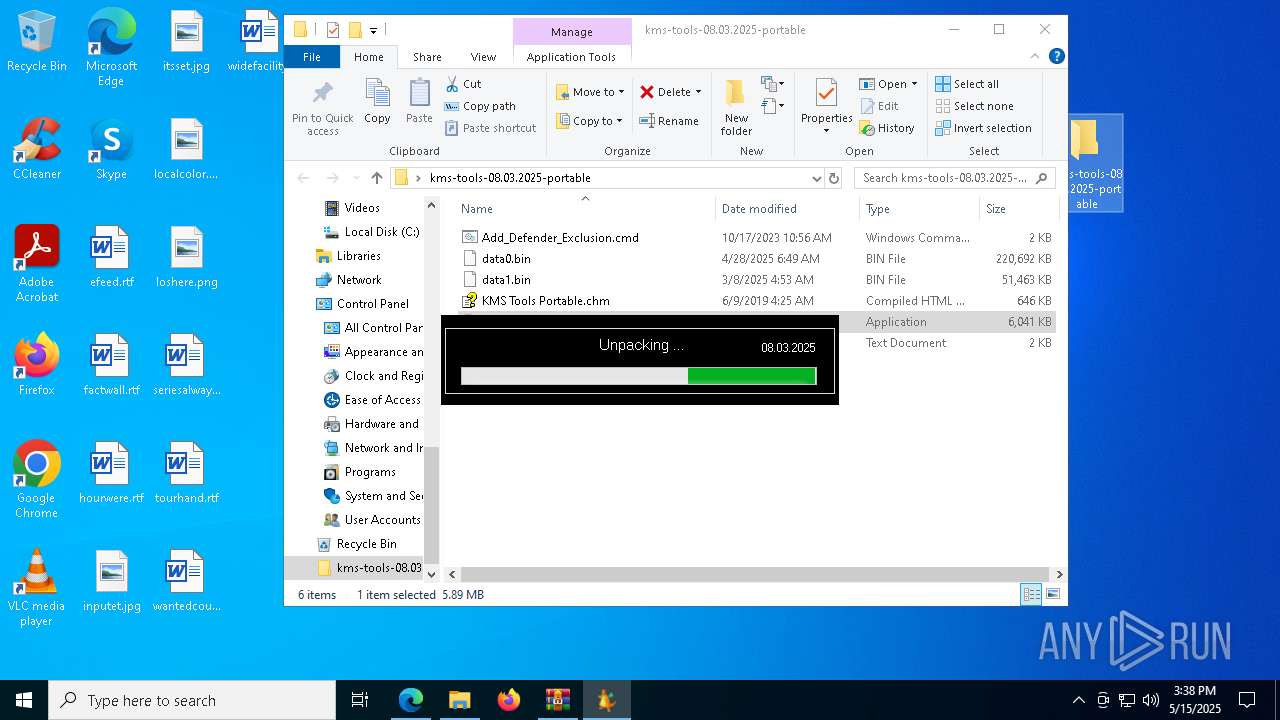
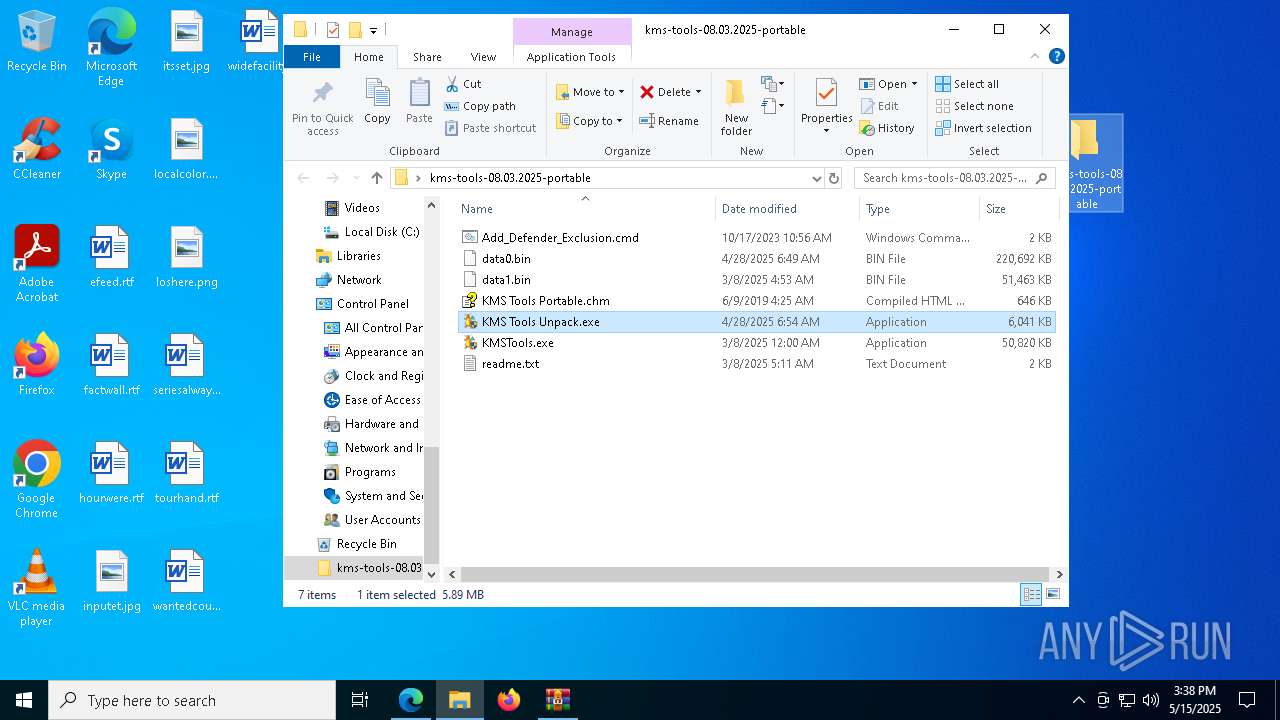
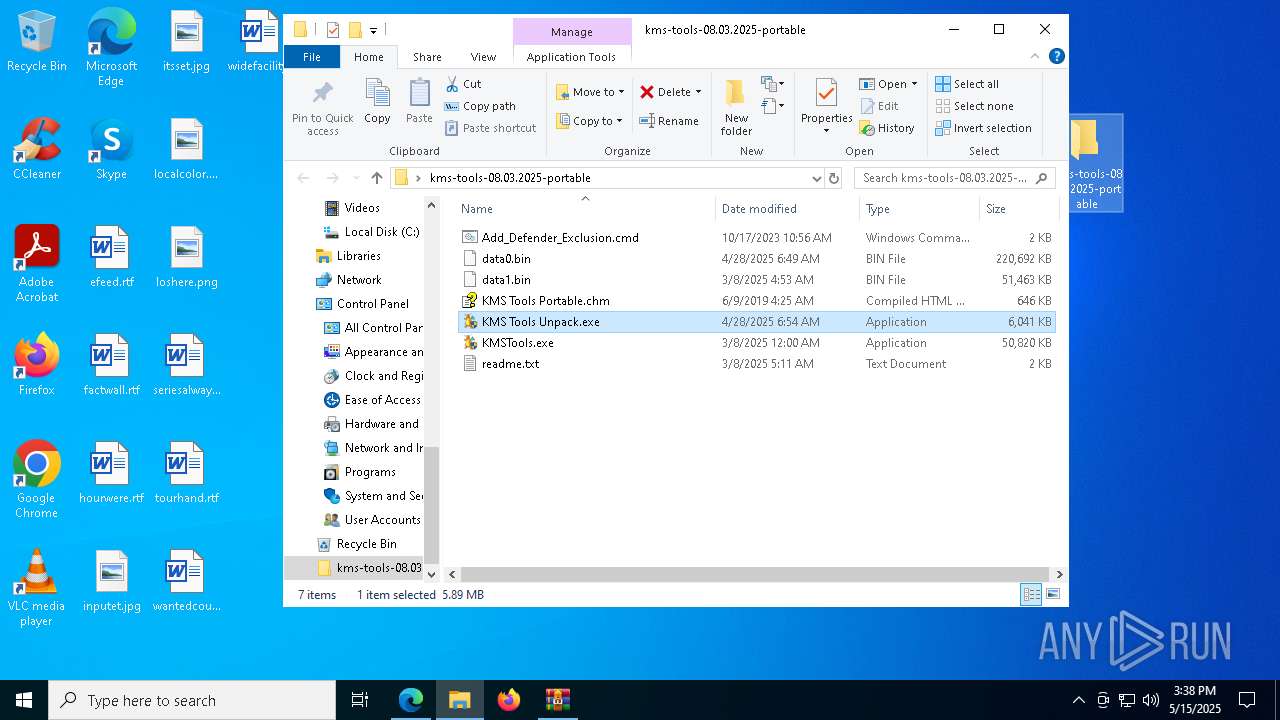
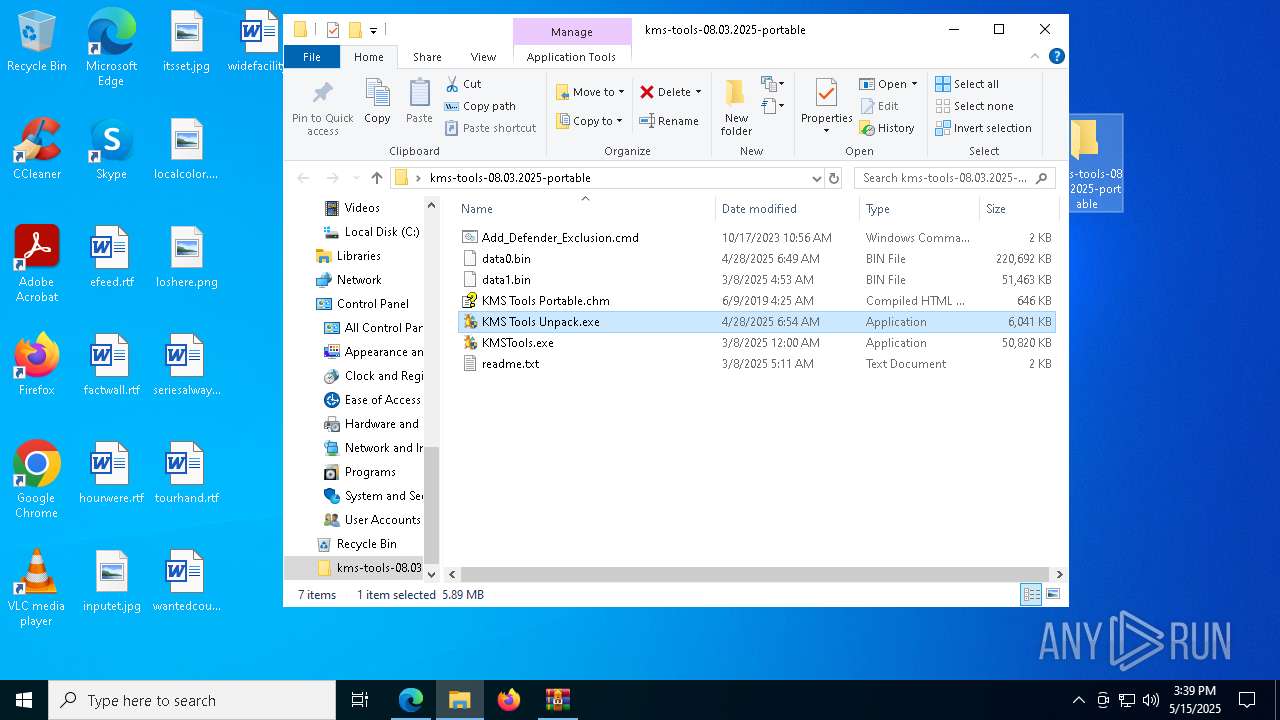
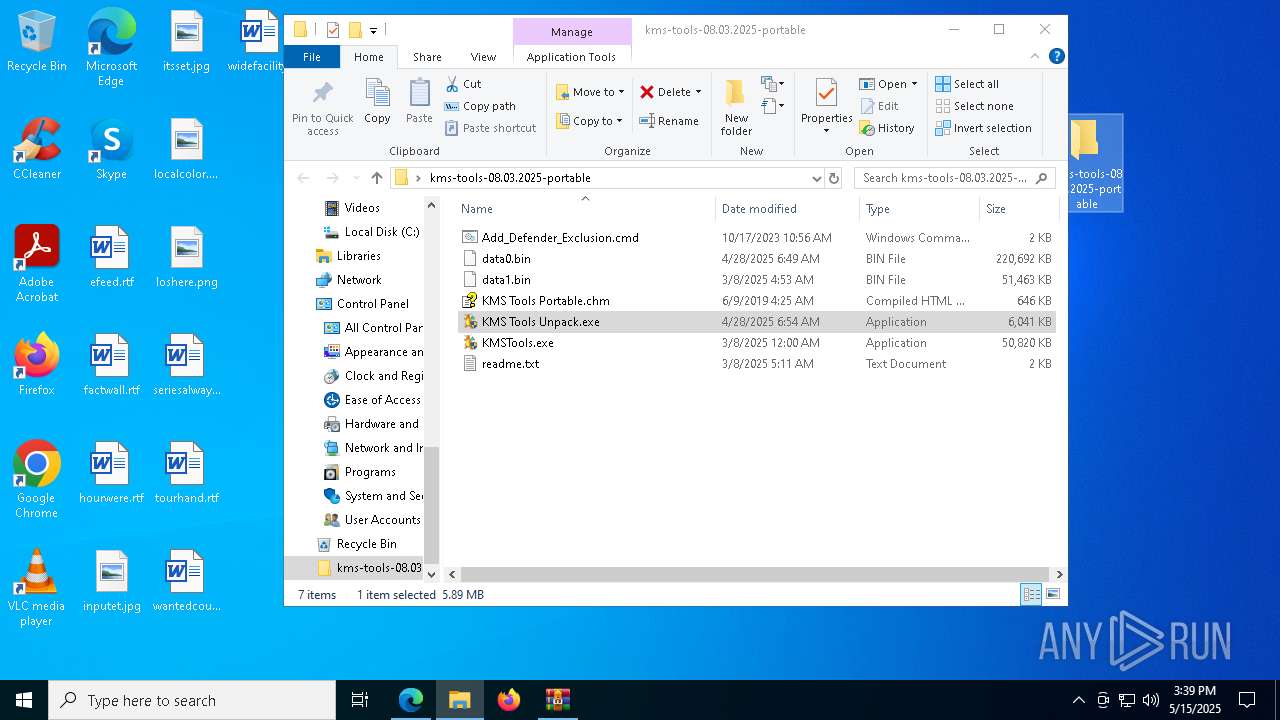
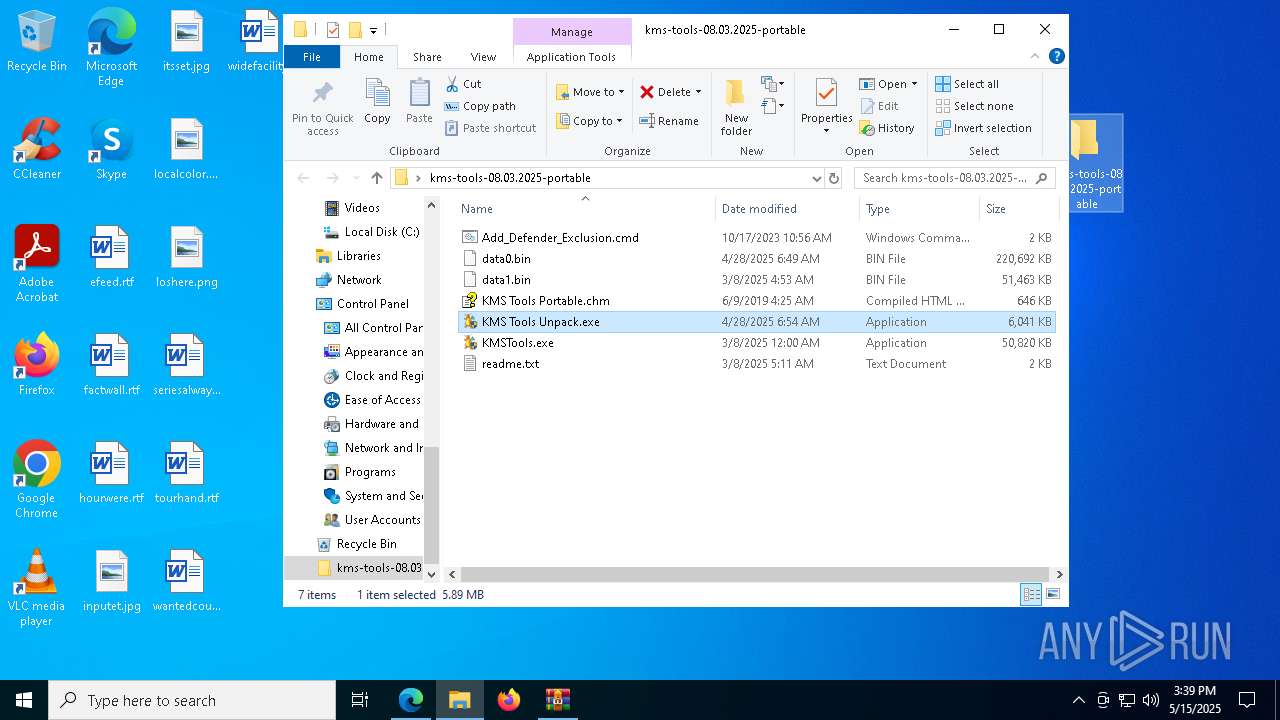
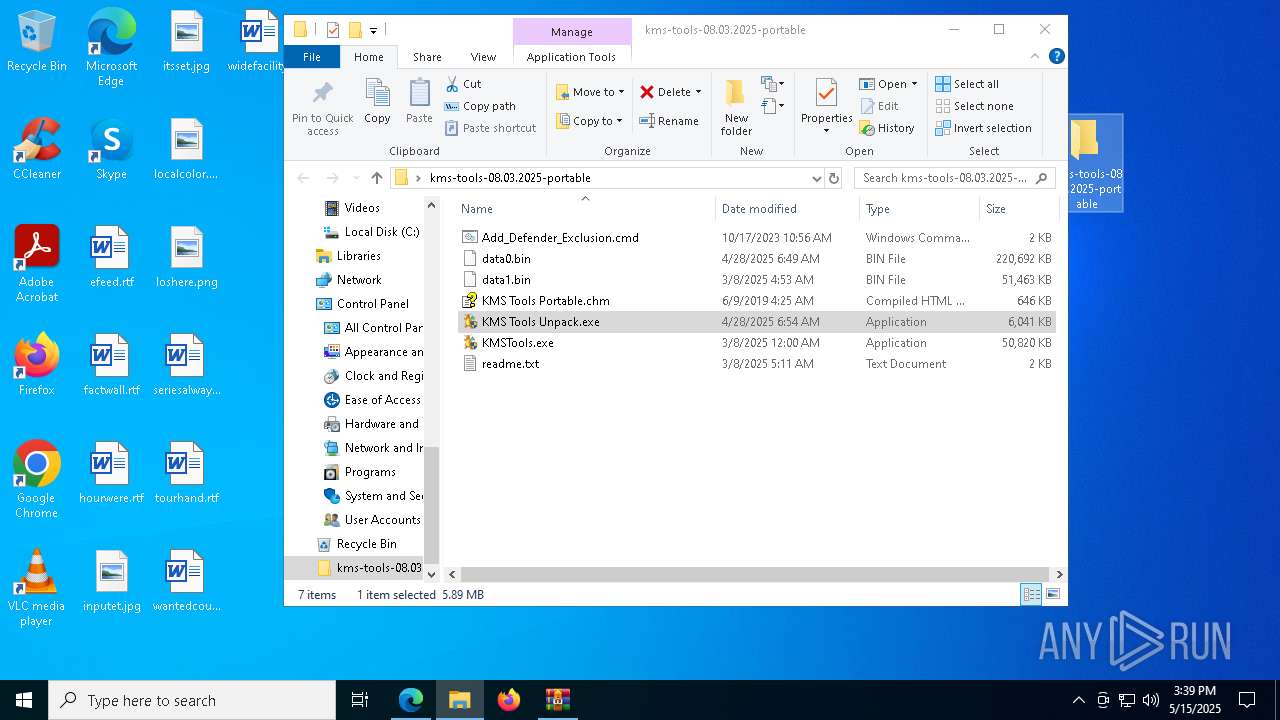
Manual execution by a user
- cmd.exe (PID: 6712)
- KMS Tools Unpack.exe (PID: 7852)
- KMS Tools Unpack.exe (PID: 776)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8008)
Checks proxy server information
- slui.exe (PID: 5728)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8008)
The sample compiled with english language support
- install.exe (PID: 5044)
- msedge.exe (PID: 5936)
- IP.exe (PID: 2108)
- smss.exe (PID: 4108)
- RDPWinst.exe (PID: 4784)
Themida protector has been detected
- KMS Tools Unpack.exe (PID: 776)
- update.exe (PID: 4304)
The process uses AutoIt
- KMS Tools Unpack.exe (PID: 776)
Compiled with Borland Delphi (YARA)
- winserv.exe (PID: 7772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
2 820
Monitored processes
2 673
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 132 | icacls "C:\ProgramData\Evernote" /deny system:(OI)(CI)(F) | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 208 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | ping -n 1 localhost | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
581 117
Read events
580 985
Write events
132
Delete events
0
Modification events
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7D8BFEB2C4932F00 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 03CC08B3C4932F00 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CEB27562-6147-4BBB-9765-ADD9DB330ACC} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DEAB2EB6-DB3F-4D10-9B49-A547393BA5CE} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2A99C345-15F4-418F-8642-C062423DC320} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {055B7812-7039-478F-BEBC-B83DE21836D0} | |||
Executable files
20
Suspicious files
606
Text files
131
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bc5c.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
57
DNS requests
77
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2140 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7348 | msedge.exe | 142.250.185.238:443 | drive.google.com | GOOGLE | US | whitelisted |
7348 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7348 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7348 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7348 | msedge.exe | 142.250.186.35:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
7348 | msedge.exe | 216.58.206.35:443 | www.gstatic.com | — | — | whitelisted |
7348 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7348 | msedge.exe | 2.16.241.218:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
drive.google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4108 | smss.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
4108 | smss.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
2196 | svchost.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] IP Checker (iplogger .co) |
4108 | smss.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
4108 | smss.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
4108 | smss.exe | Potentially Bad Traffic | ET INFO RDP Wrapper Download (ini) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
4108 | smss.exe | Potential Corporate Privacy Violation | ET INFO Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
4108 | smss.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |