| File name: | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433 |
| Full analysis: | https://app.any.run/tasks/4b9240ec-c500-474d-8fb8-a06e537f3ab0 |
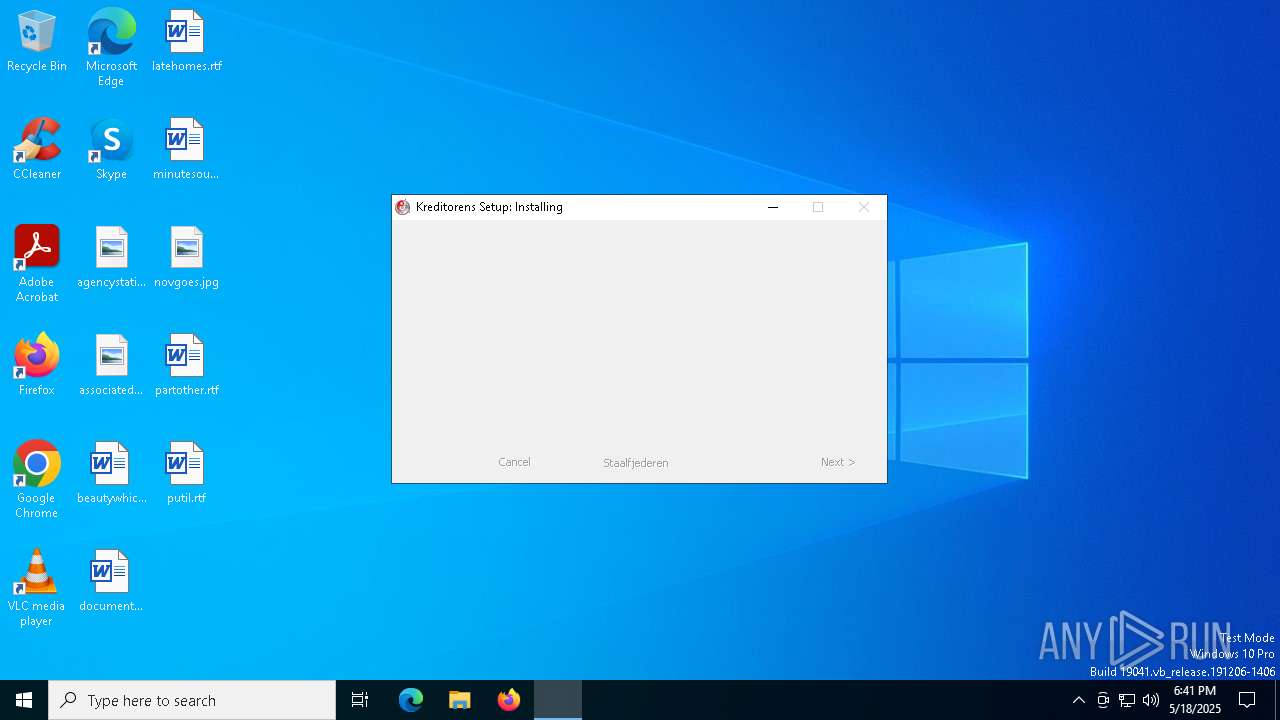
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | May 18, 2025, 18:41:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | D1D90618DAB6B2024590784317FB9EA2 |
| SHA1: | DA008566C94733024EC97BBE8A0E2F6D2A7CCC36 |
| SHA256: | E4D64FC5D68290BF11CBFB681EA35EB60F9AEC646D9AB7DFA7221660C6C2B433 |
| SSDEEP: | 49152:ghfHSCtRltA3vvNBuAUJIXaAXAq+zSamBkAba5e7H1xRUnjxDeqJgAldDQuy08WV:ghfHSHnv0JIXaAXAqGokAueH1xQjxKqR |
MALICIOUS
GULOADER SHELLCODE has been detected (YARA)
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
GULOADER has been detected (YARA)
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
SUSPICIOUS
Executable content was dropped or overwritten
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
The process creates files with name similar to system file names
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
Malware-specific behavior (creating "System.dll" in Temp)
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
There is functionality for taking screenshot (YARA)
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
INFO
The sample compiled with english language support
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
Creates files or folders in the user directory
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
Create files in a temporary directory
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
Checks supported languages
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
Reads the computer name
- e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe (PID: 7148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
guloader
(PID) Process(7148) e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe
C2 (1)https://drive.google.com/uc?export=download&id=1MRcmElmwYKGWVATdRwt7D30M9LvDvUID
Strings (19)( _
Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/115.0
wininet.dll
KERNELBASE.DLL
Msi.dll
psapi.dll
user32
advapi32
shell32
Publisher
windir=
TEMP=
mshtml.dll
\system32\
\syswow64\
Startup key
Software\Microsoft\Windows\CurrentVersion\RunOnce
C:\Program Files\qga\qga.exe
C:\Program Files\Qemu-ga\qemu-ga.exe
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 161792 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x33b8 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.0.0 |
| ProductVersionNumber: | 3.4.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Eastman Chemical Company |
| FileVersion: | 3.4.0.0 |
| LegalCopyright: | Veritas Software Corporation |
| OriginalFileName: | fagordene monochromatism.exe |
| ProductName: | Whirlpool Corporation |
Total processes
129
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6708 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7148 | "C:\Users\admin\AppData\Local\Temp\e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe" | C:\Users\admin\AppData\Local\Temp\e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 3.4.0.0 Modules
guloader(PID) Process(7148) e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe C2 (1)https://drive.google.com/uc?export=download&id=1MRcmElmwYKGWVATdRwt7D30M9LvDvUID Strings (19)( _ Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/115.0 wininet.dll KERNELBASE.DLL Msi.dll psapi.dll user32 advapi32 shell32 Publisher windir= TEMP= mshtml.dll \system32\ \syswow64\ Startup key Software\Microsoft\Windows\CurrentVersion\RunOnce C:\Program Files\qga\qga.exe C:\Program Files\Qemu-ga\qemu-ga.exe | |||||||||||||||
Total events
262
Read events
262
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
15
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Genom\Schraubthaler\Shirred\Stridsskriftet.Tri | binary | |
MD5:04036795999F0D53216ACD827933DF1A | SHA256:EBD3918A1D3AD0CB8A6AFFE78A5C692EDCBD72B3806B7003D747E817C12AD148 | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Subtegumental\Arbejdsstemningers\Aped\Punaluan237.lyn | binary | |
MD5:DABA730187972EF265297F7C6723C213 | SHA256:96C790CFE436D225D3520D54D3D90AF9AFBB0F2A6A29A7909ACA8841D97DA027 | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Arbejdsgldes.jow | binary | |
MD5:355B3F19F486EA5925E8A728A105CFCE | SHA256:60B402C3831187D36F6E41A1460D68DDE1F8231D752BD5B5513BD7EA78050152 | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Ordinatomaculate\Temperer\Uerholdelige\phoniatric.pre | binary | |
MD5:CE8AC2F52809F46F8105789C7A3CC184 | SHA256:7239C444C71778BCC587B5DF96A983ED7E676A7FB15BBFAAEB5A70B57EC72476 | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Ordinatomaculate\Temperer\Uerholdelige\singularis.pro | binary | |
MD5:EE16A241D692866C937DF57B49C2B421 | SHA256:62D6521B3B7072537E7A37386993B2B9D290A000EC9A50D02A052FC56C59D4F3 | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Vgtenhed\Tankelseren\Inobediently\luftfartslovene.txt | text | |
MD5:EBABA8C0A49CC3604BCC8812C29838FF | SHA256:35955D619449C8004408A95ABA10C1DF879B2E96FF5B54AAC809736C4215CD58 | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Ordinatomaculate\Temperer\Uerholdelige\subpotencies.wea | binary | |
MD5:3CDE87711A80593E48CC92B45FE4863B | SHA256:8F61A46C4074E2669F95AEB69D7CA3384B2CD3F75CF4B0B0B771C73DB24864CD | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Local\Temp\nsaB6A1.tmp\System.dll | executable | |
MD5:DD87A973E01C5D9F8E0FCC81A0AF7C7A | SHA256:7FB0F8D452FEFAAC789986B933DF050F3D3E4FEB8A8D9944ADA995F572DCDCA1 | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Subtegumental\Arbejdsstemningers\Aped\brudflisens.rut | binary | |
MD5:F5E5FE248C10C0D0D1AA893304571842 | SHA256:D212E114D13C320FE0EBC7143A10CEEDC0597BB9D3B96B77DDFF9A8ABFD6635A | |||
| 7148 | e4d64fc5d68290bf11cbfb681ea35eb60f9aec646d9ab7dfa7221660c6c2b433.exe | C:\Users\admin\AppData\Roaming\blennoma\afrignings\Subtegumental\Arbejdsstemningers\Aped\Menstruerendes254.mat | binary | |
MD5:228D8D28E99118D77792B27A30E8105D | SHA256:4D3D5B415277BC8C9364DE80703443822CAD8476CBBCFF2798E75D4796B80111 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4920 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4920 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |