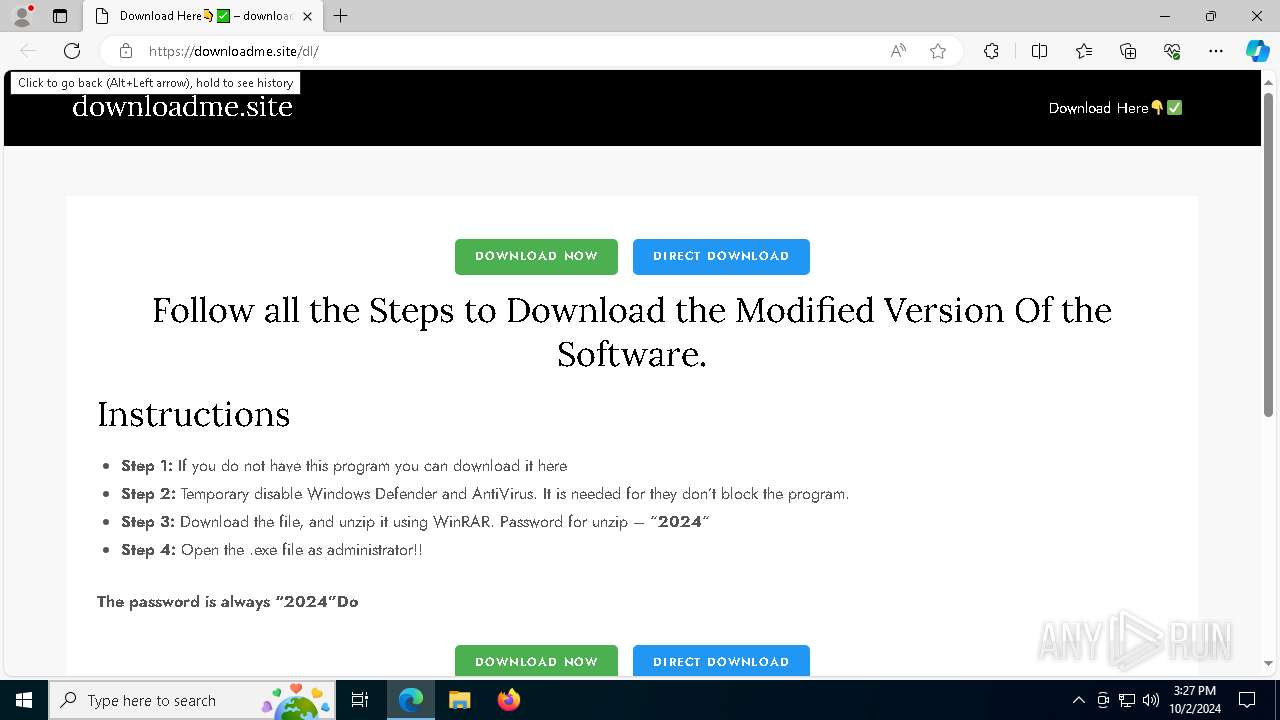
| URL: | https://downloadme.site/dl/ |
| Full analysis: | https://app.any.run/tasks/a26d5d12-36e2-454c-9d0b-83dcddcf48fe |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
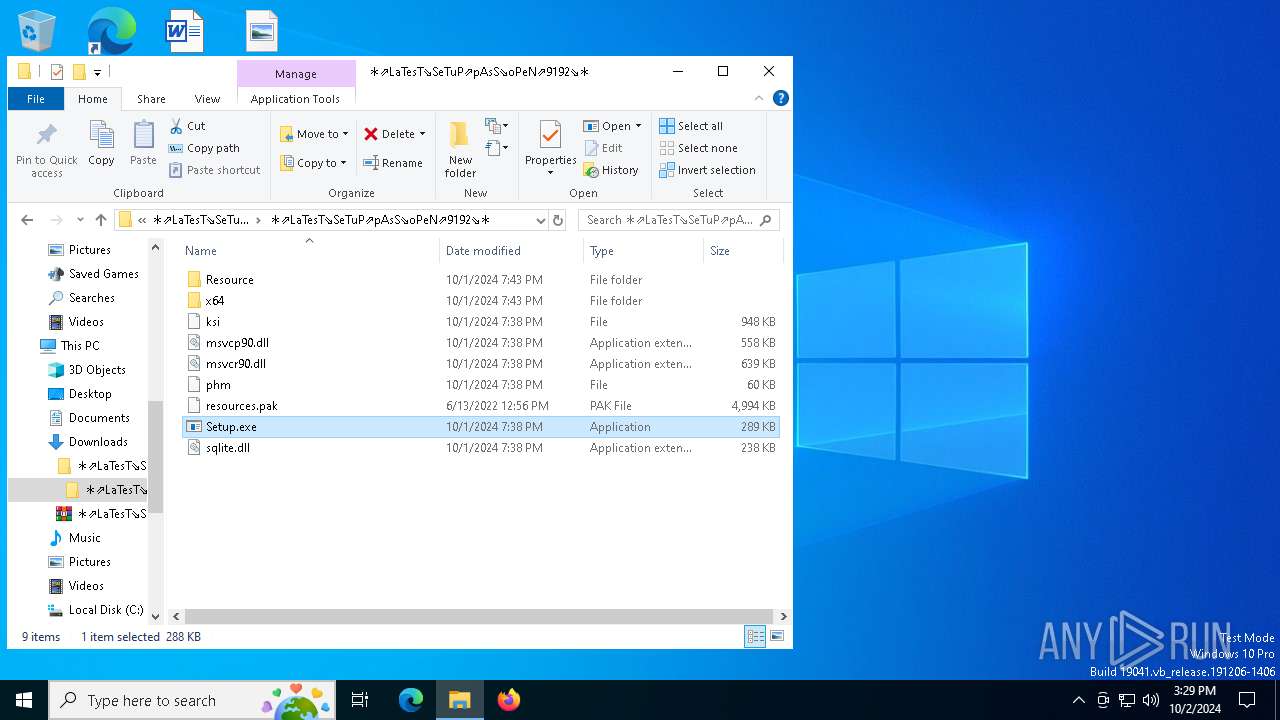
| Analysis date: | October 02, 2024, 15:27:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D88F79E01635531634892EA8CDF78AA9 |
| SHA1: | 855A67BFADB084FAE2C00FA4DBFDCE555DFC4AC5 |
| SHA256: | E4BEF4582C3D77BF2730790397381E09B7AD9A8E42D8C240B8460E2630A3B1F1 |
| SSDEEP: | 3:N8SEmALBBJKn:2SOlC |
MALICIOUS
LUMMA has been detected (YARA)
- SearchIndexer.exe (PID: 4160)
Changes powershell execution policy (Bypass)
- SearchIndexer.exe (PID: 7816)
- SearchIndexer.exe (PID: 4160)
- SearchIndexer.exe (PID: 3784)
Bypass execution policy to execute commands
- powershell.exe (PID: 1884)
- powershell.exe (PID: 376)
- powershell.exe (PID: 3148)
SUSPICIOUS
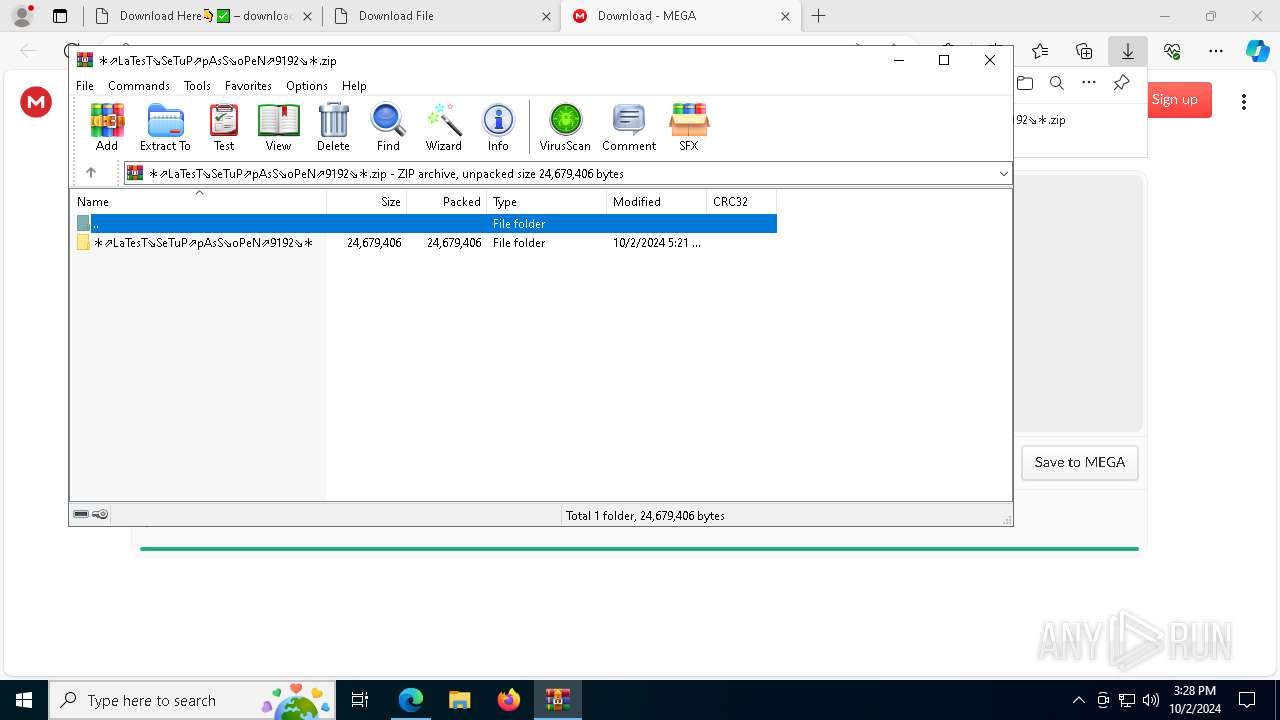
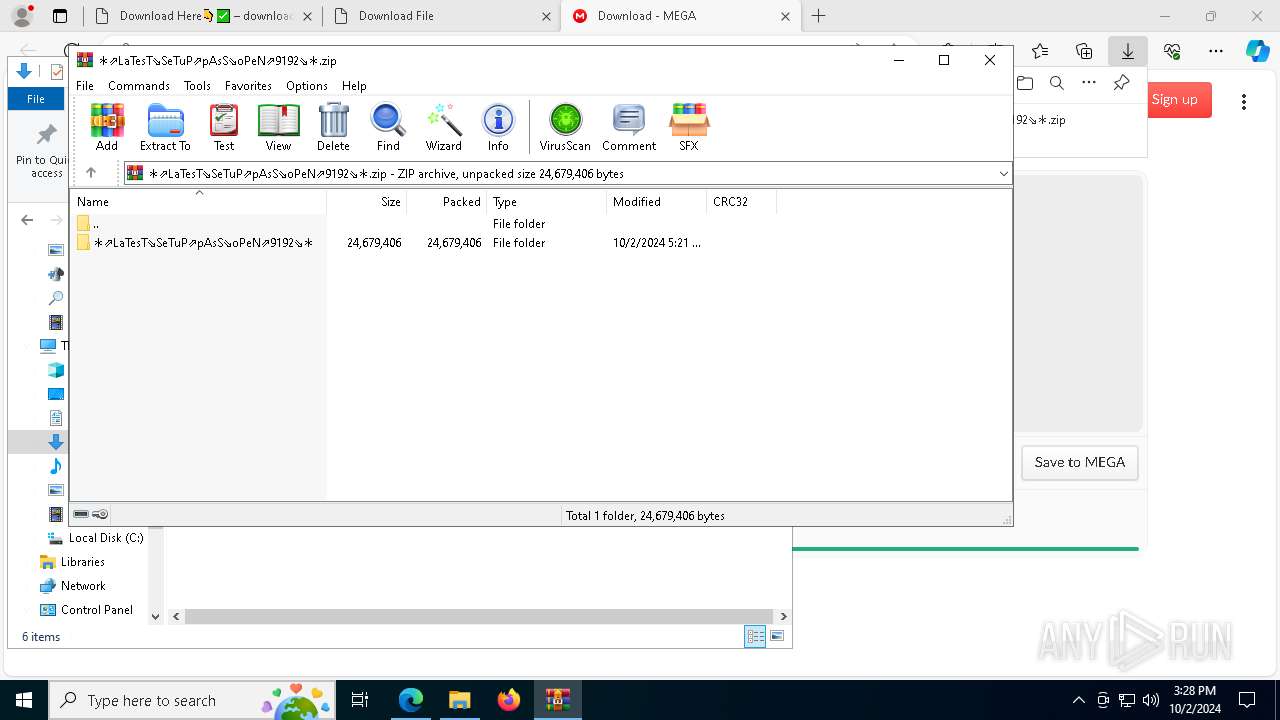
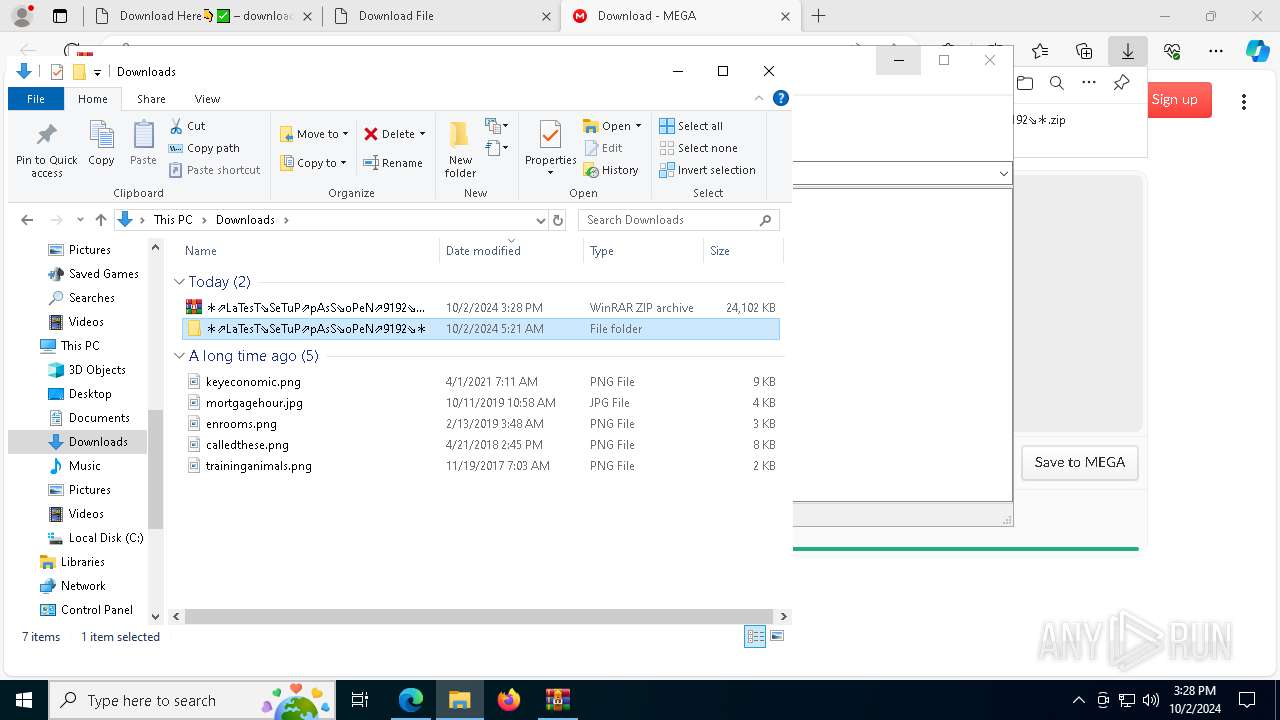
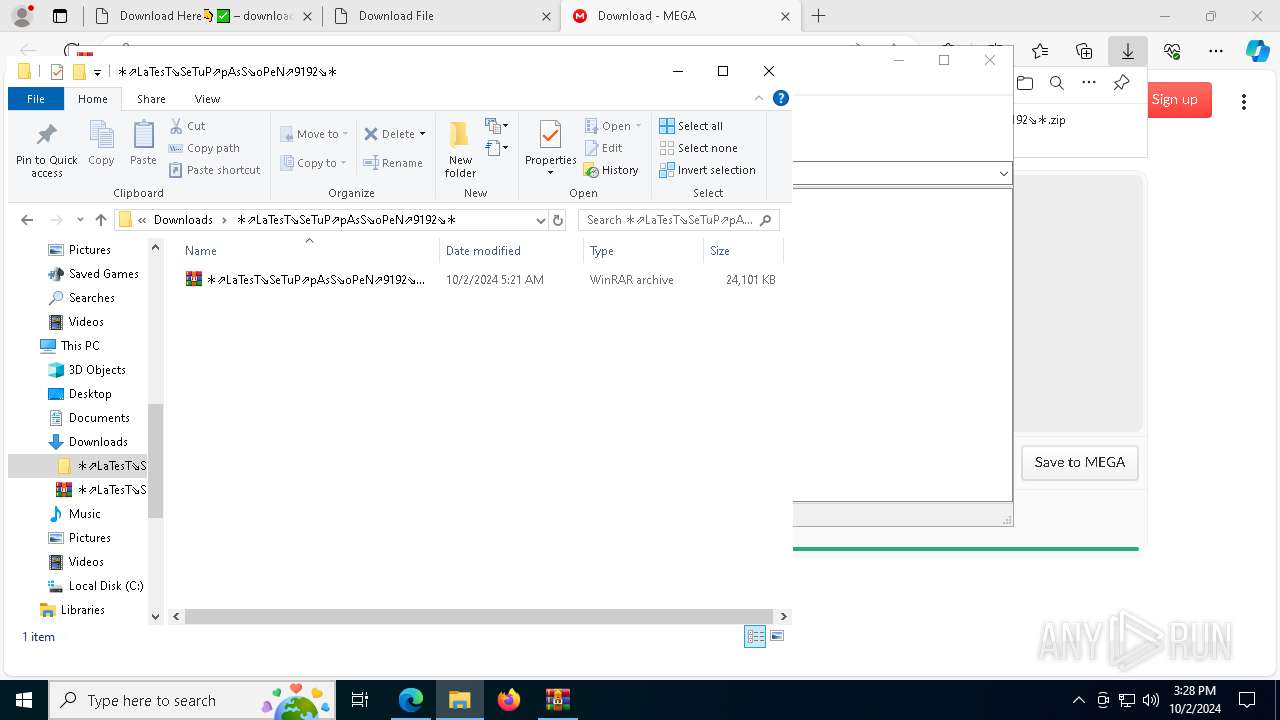
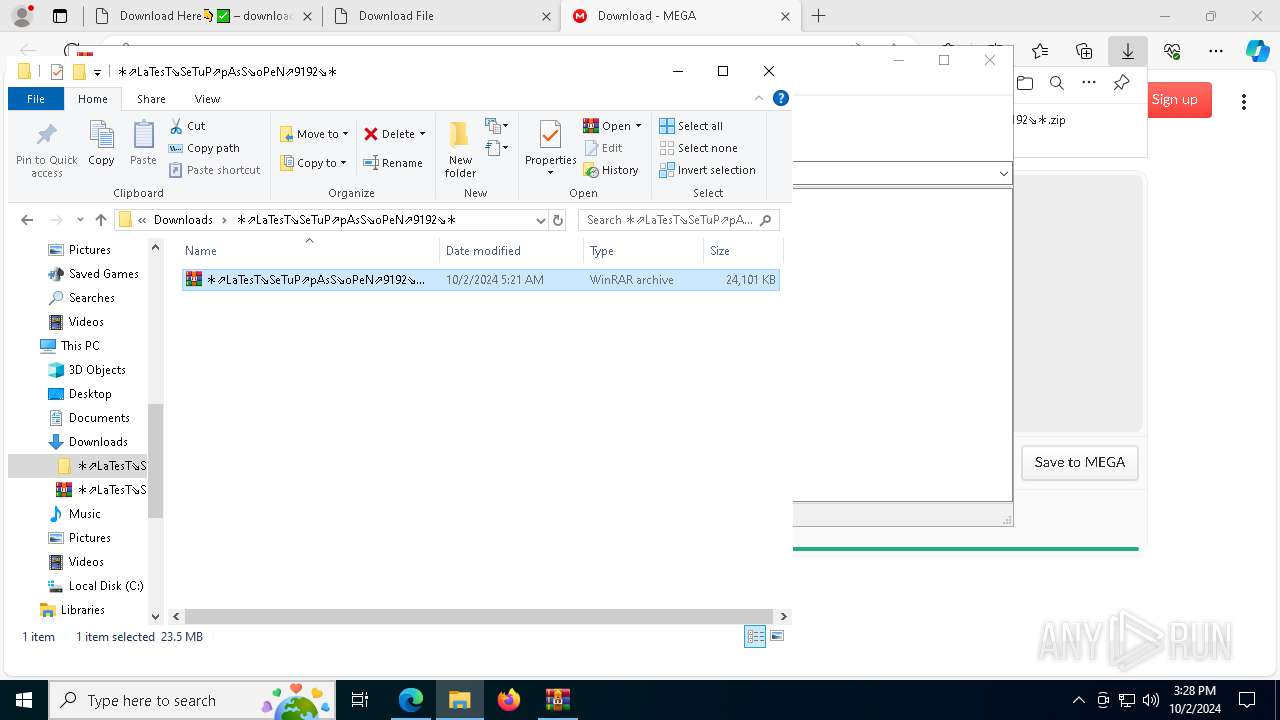
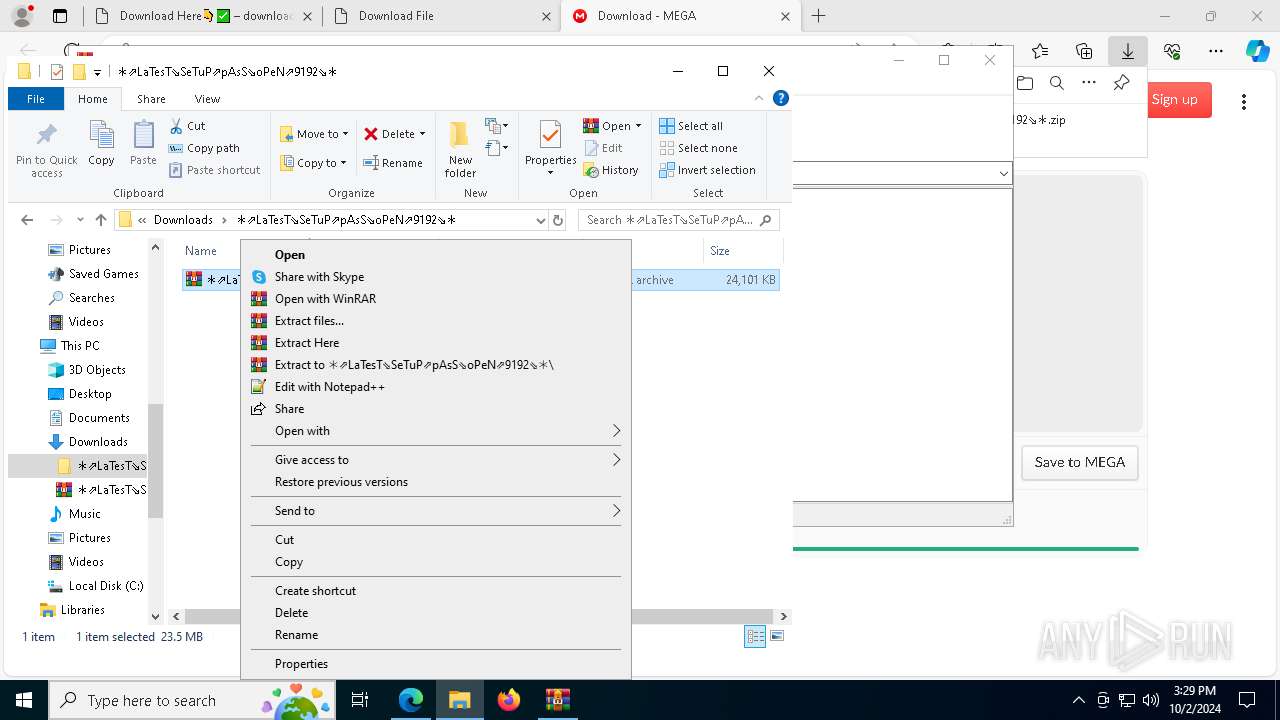
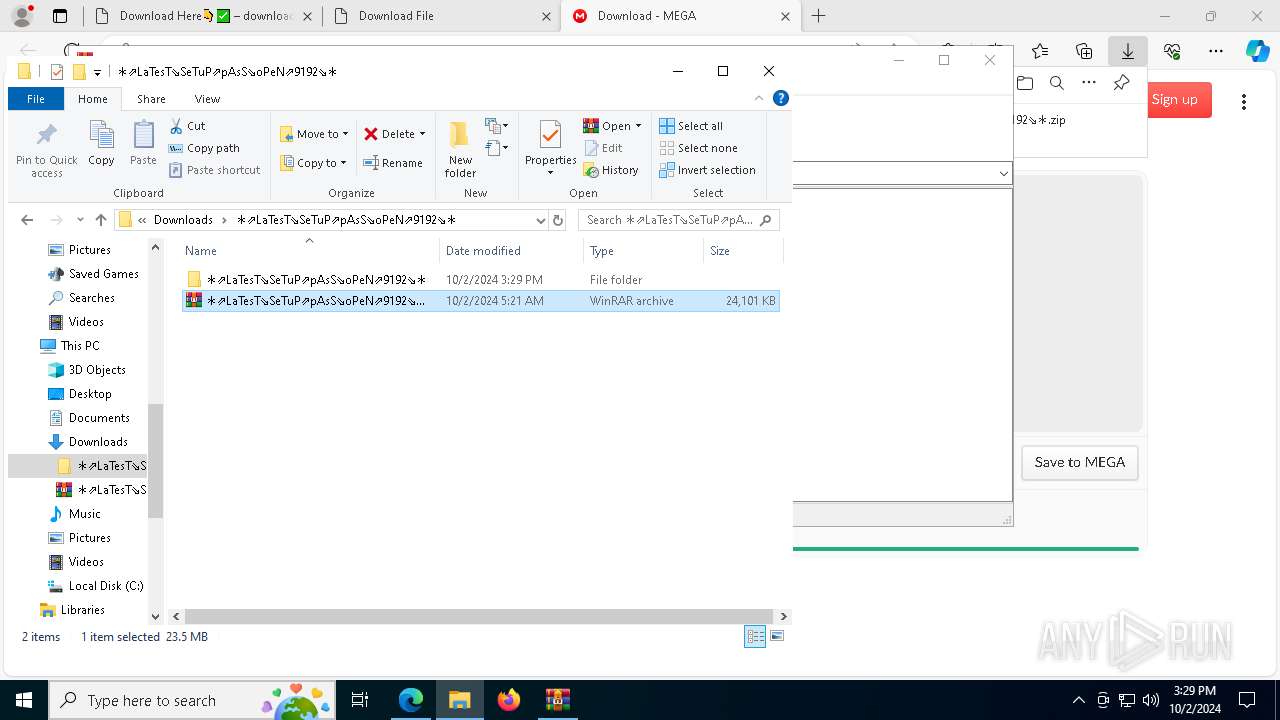
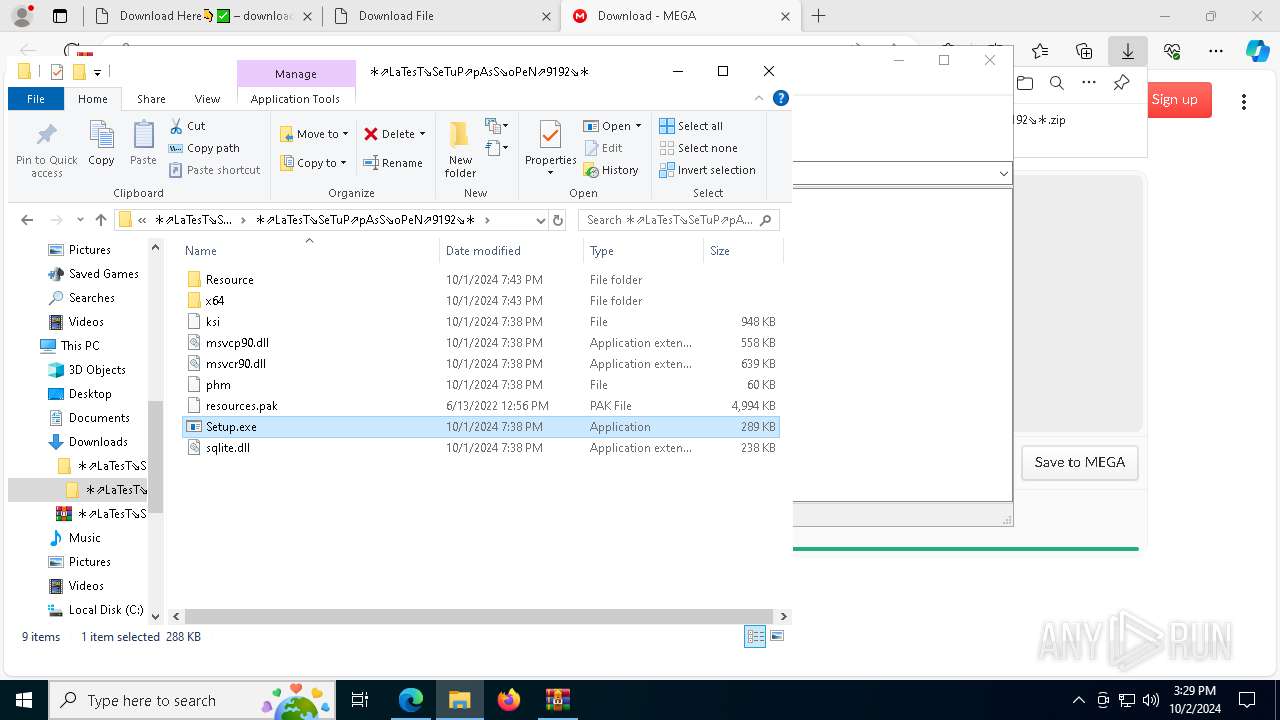
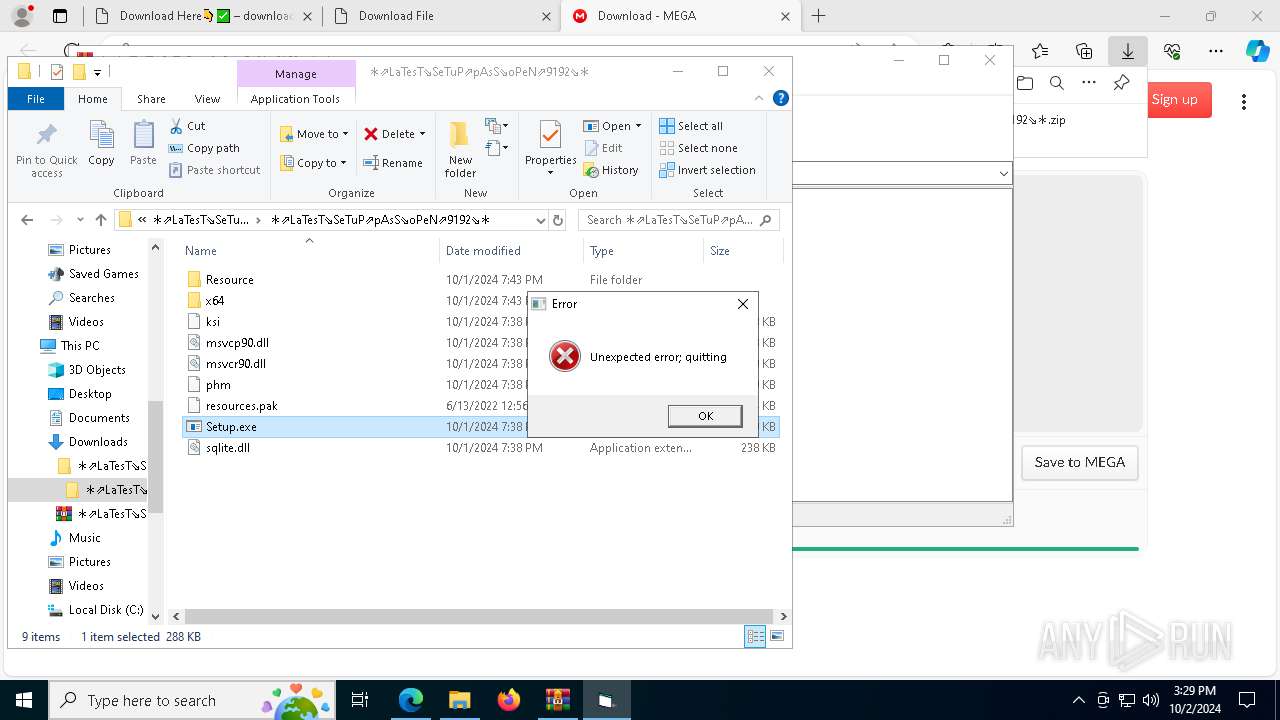
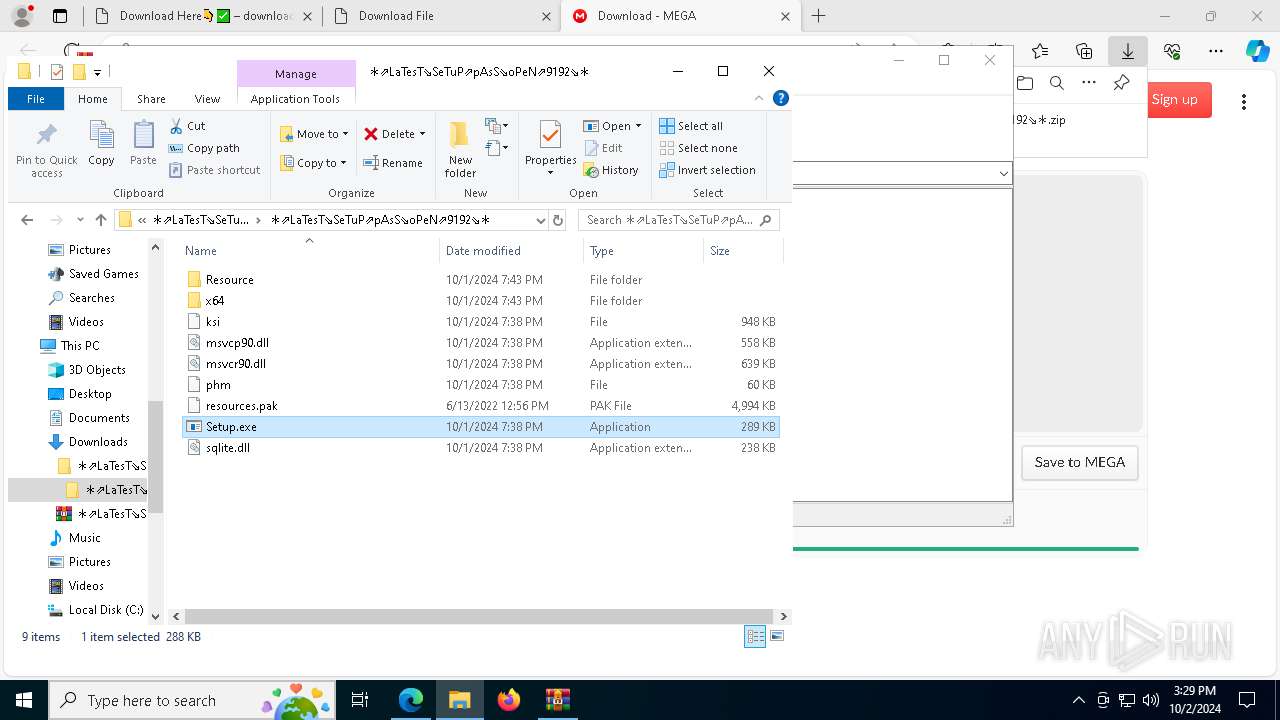
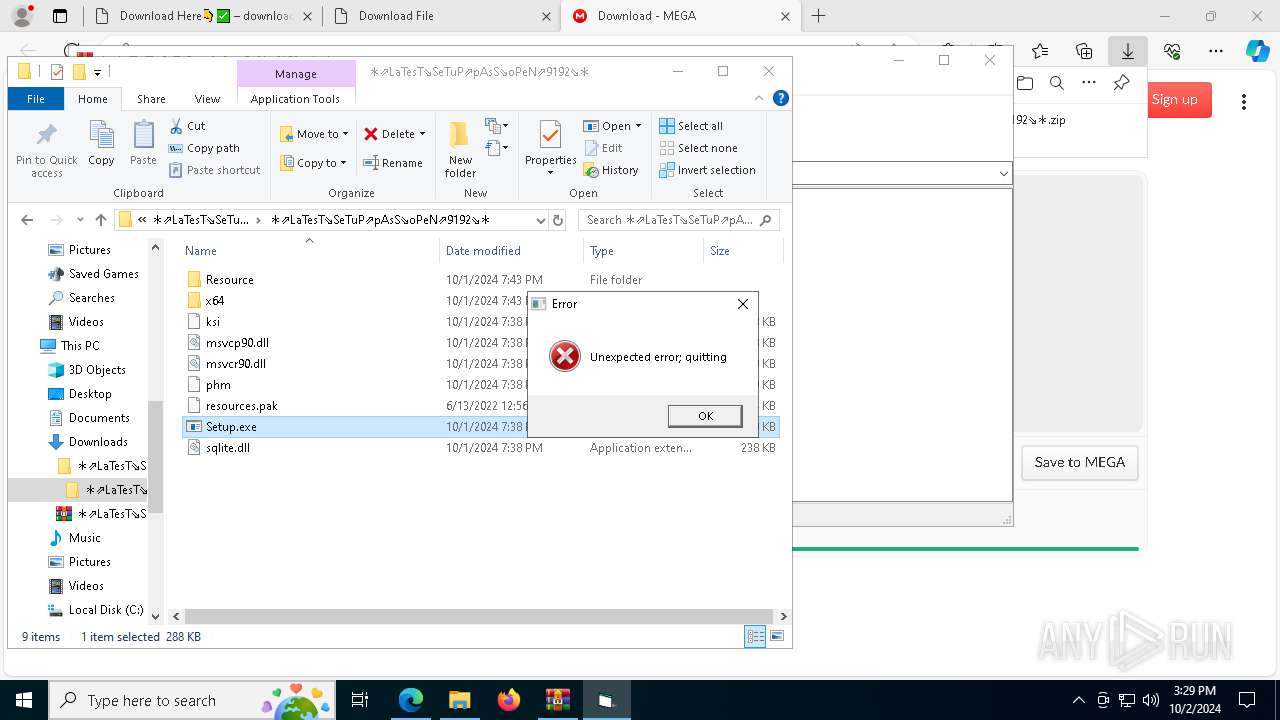
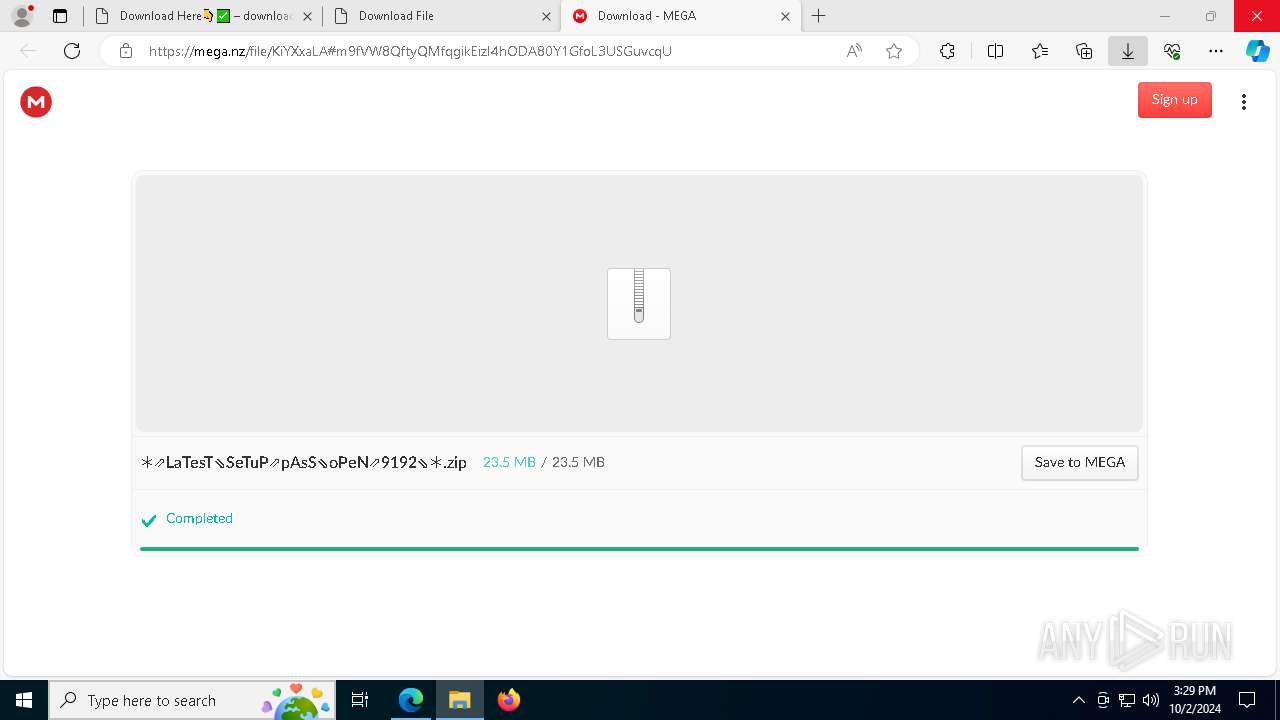
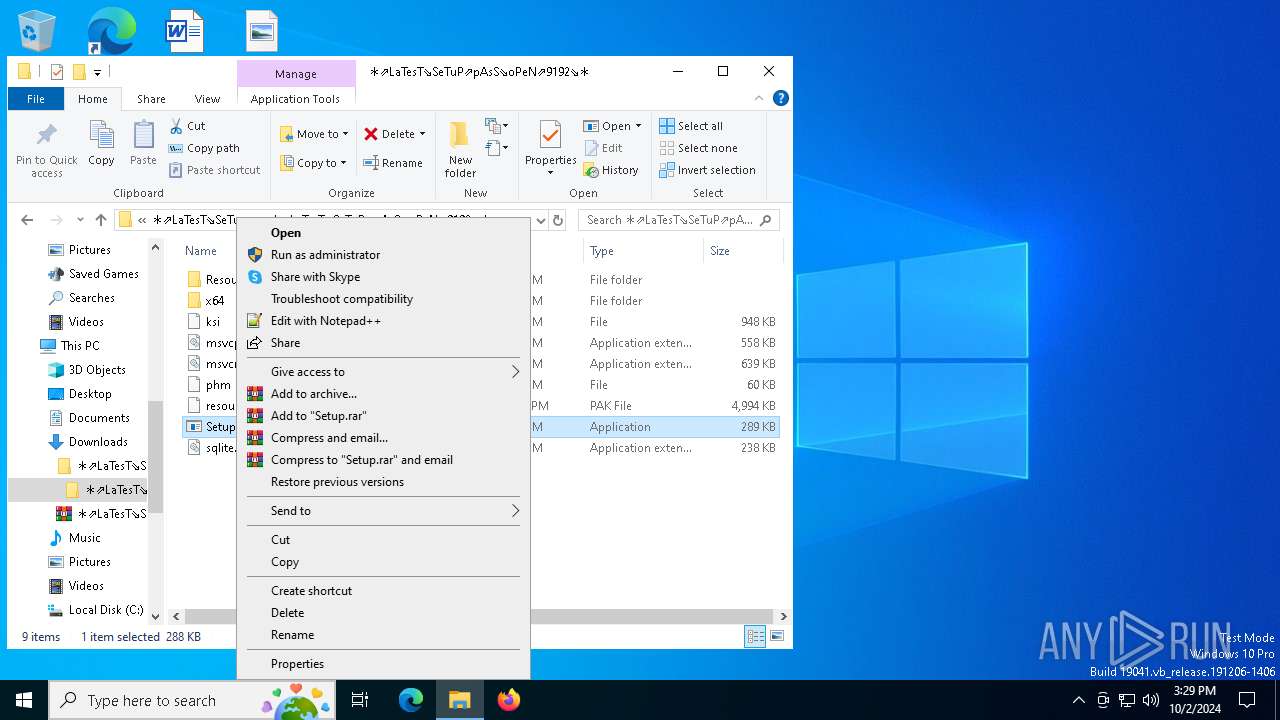
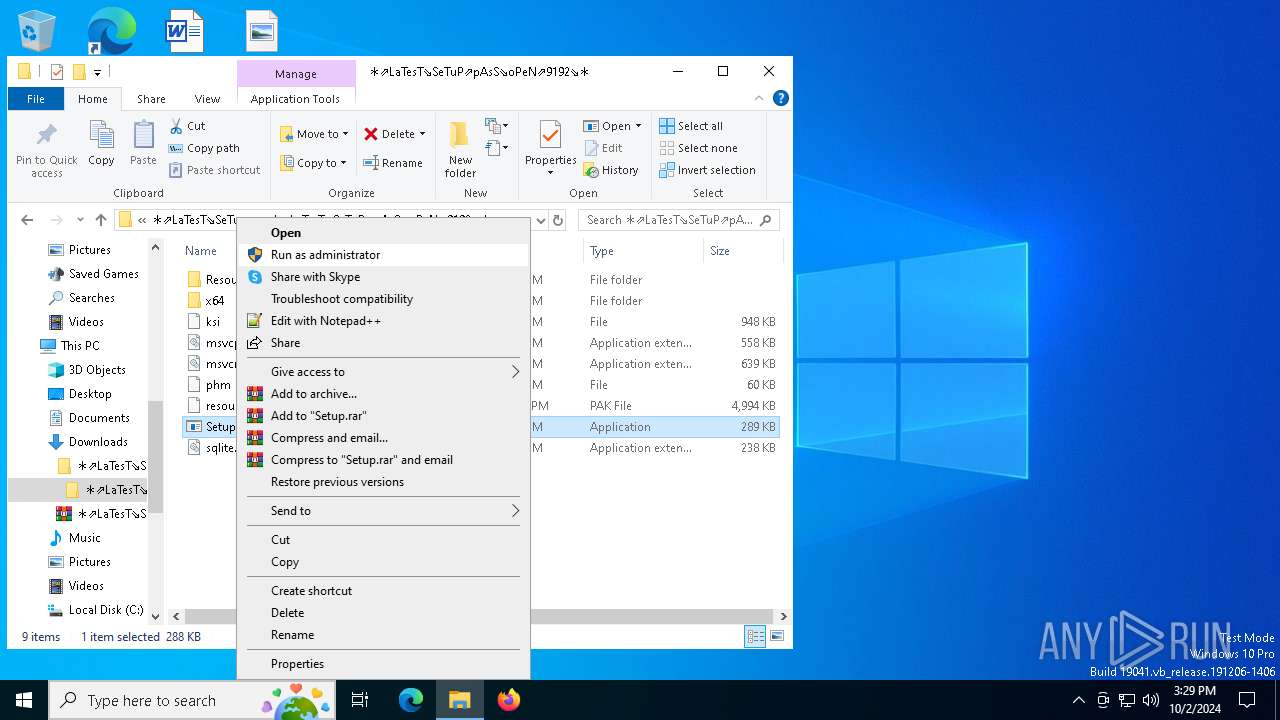
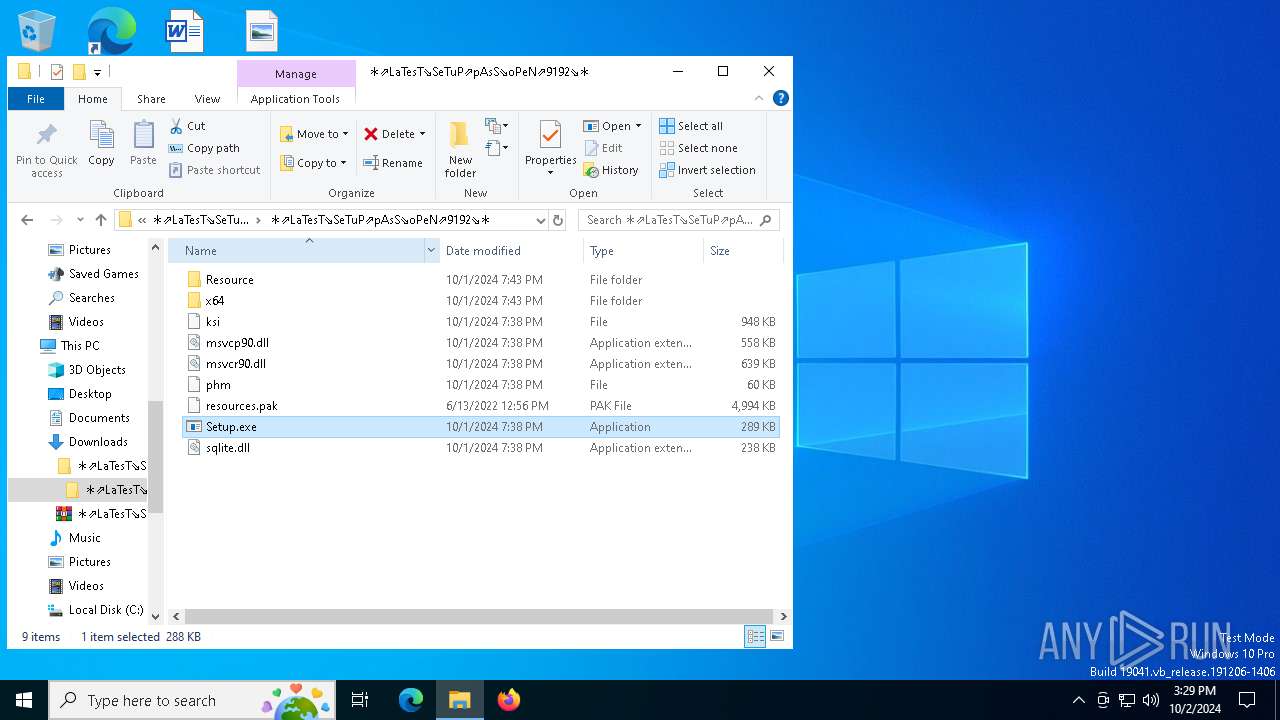
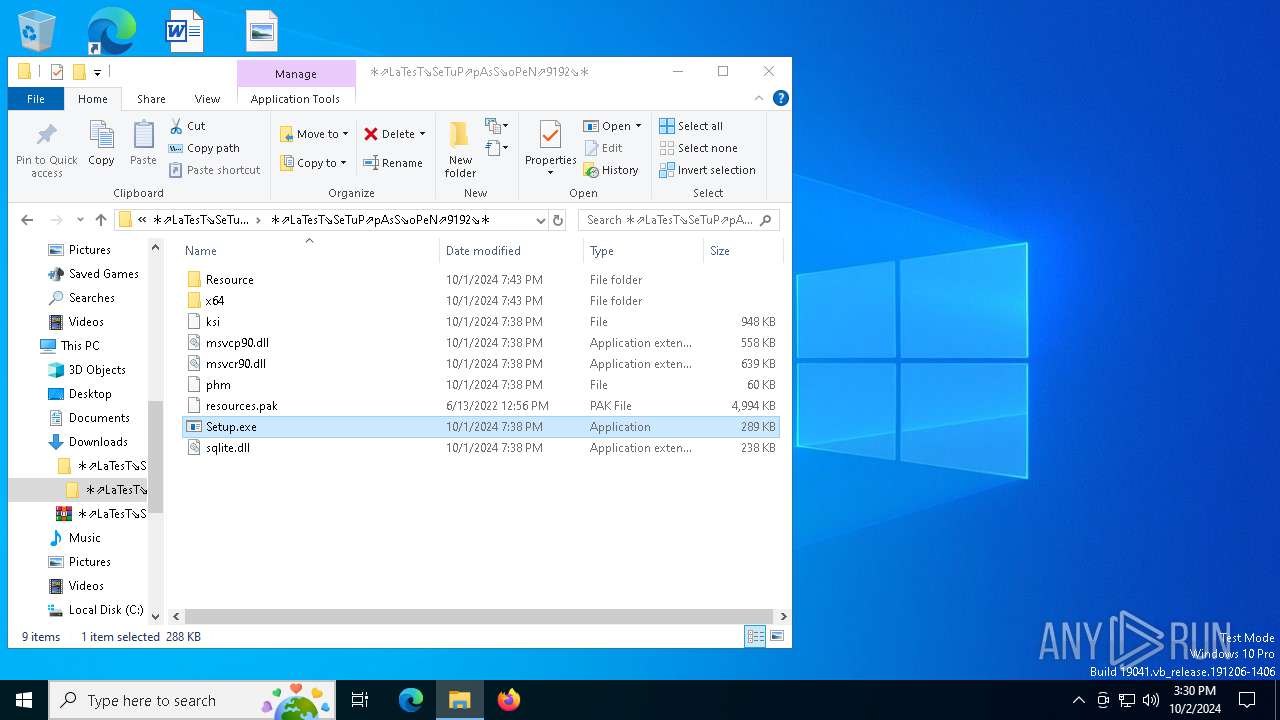
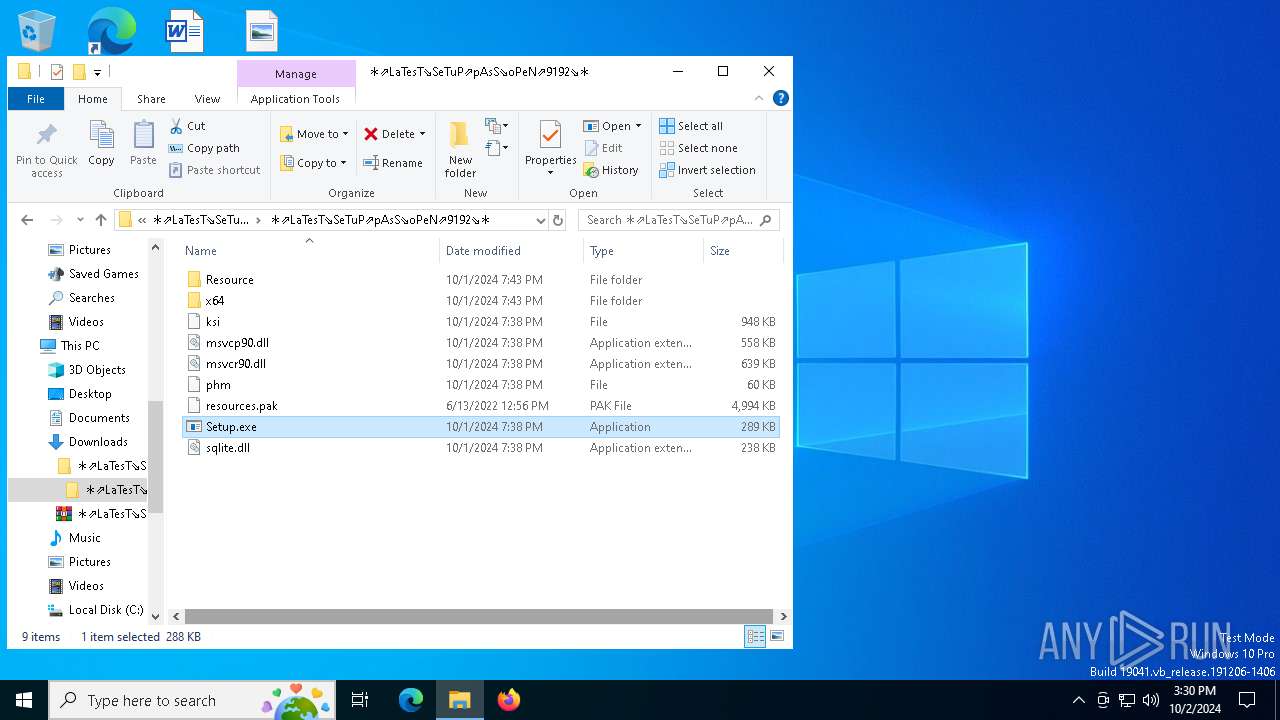
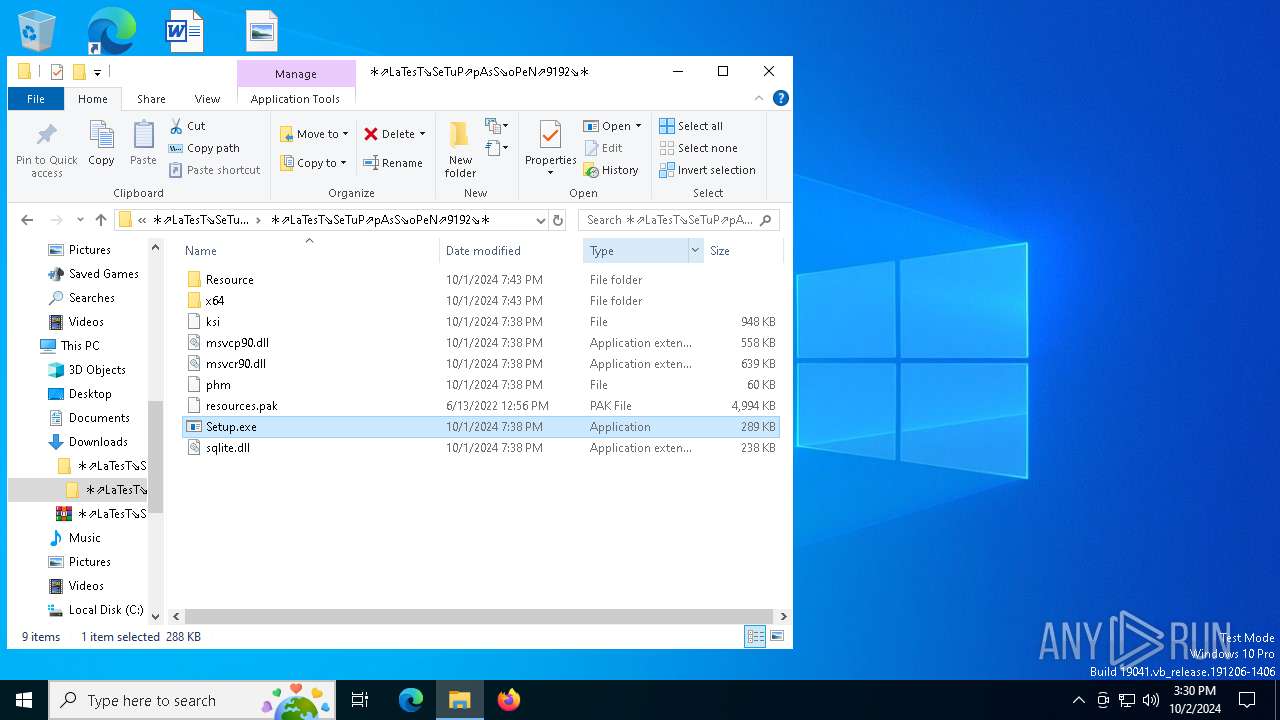
Process drops legitimate windows executable
- WinRAR.exe (PID: 7068)
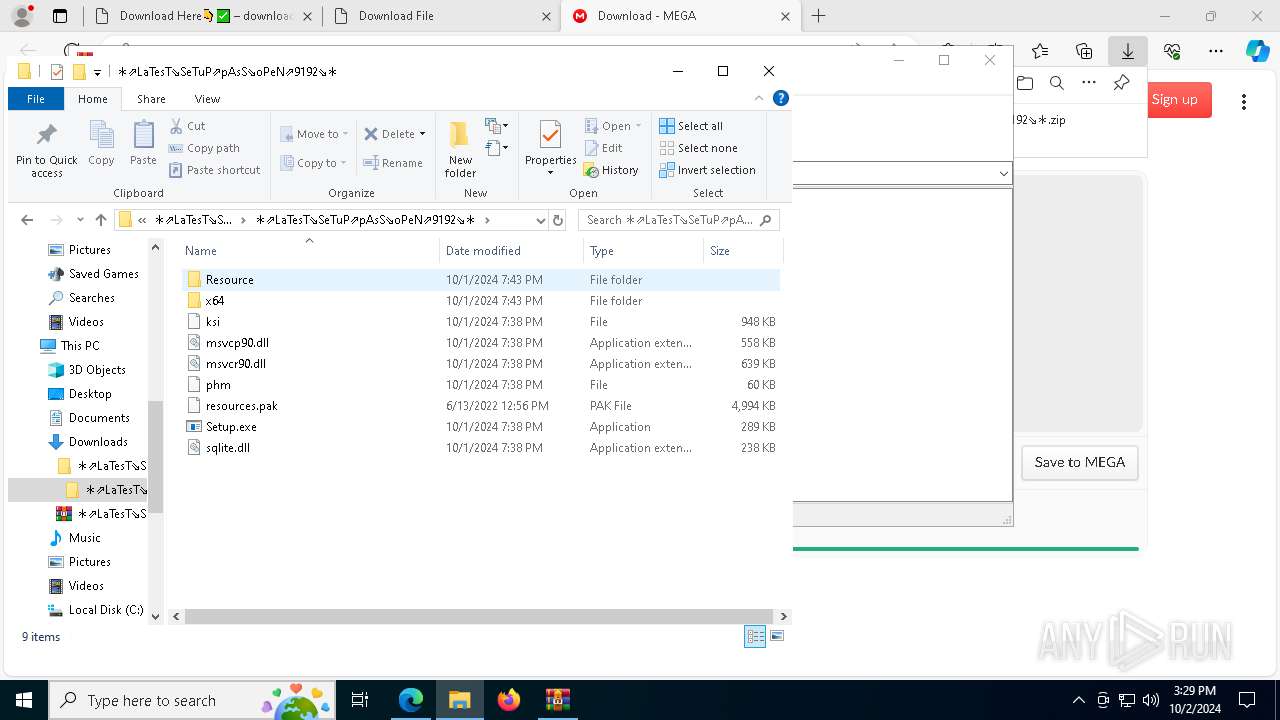
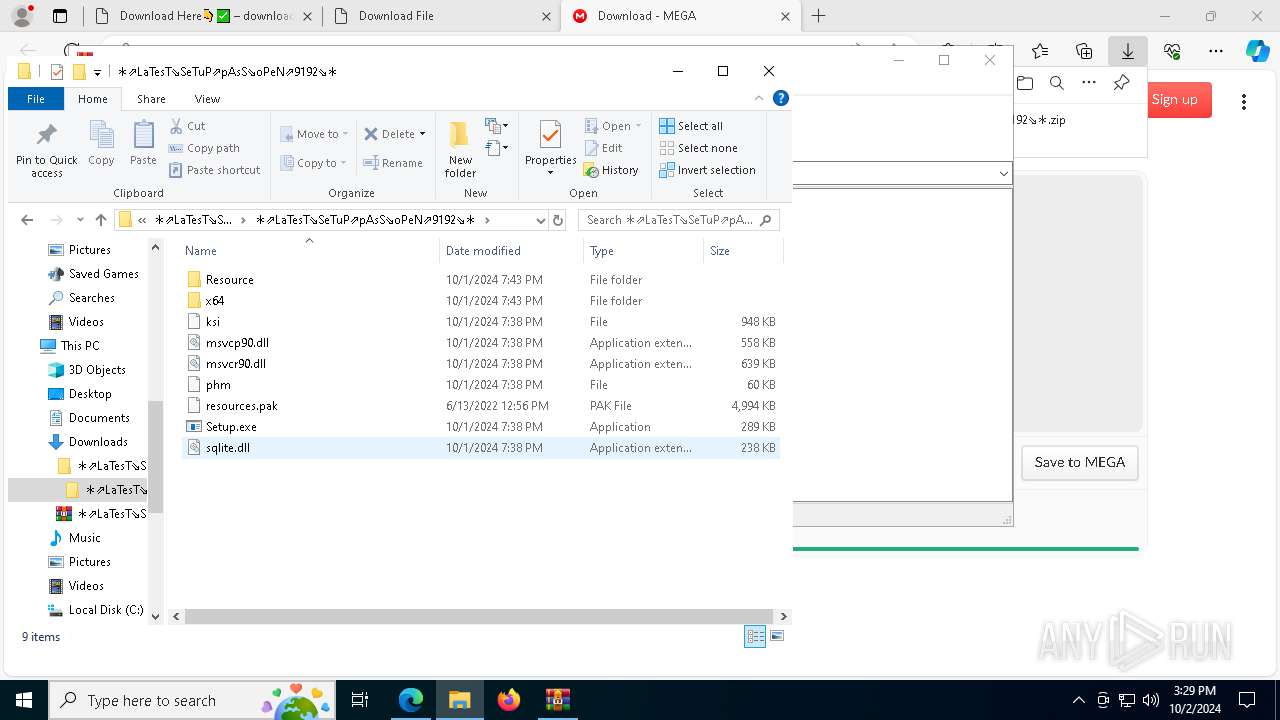
- Setup.exe (PID: 7888)
The process drops C-runtime libraries
- Setup.exe (PID: 7888)
Executable content was dropped or overwritten
- Setup.exe (PID: 7888)
- powershell.exe (PID: 1884)
- powershell.exe (PID: 376)
- powershell.exe (PID: 3148)
Starts application with an unusual extension
- Setup.exe (PID: 7888)
- Setup.exe (PID: 5084)
- Setup.exe (PID: 5196)
- Setup.exe (PID: 7540)
Starts POWERSHELL.EXE for commands execution
- SearchIndexer.exe (PID: 7816)
- SearchIndexer.exe (PID: 4160)
- SearchIndexer.exe (PID: 3784)
The process executes Powershell scripts
- SearchIndexer.exe (PID: 7816)
- SearchIndexer.exe (PID: 3784)
- SearchIndexer.exe (PID: 4160)
INFO
Application launched itself
- msedge.exe (PID: 3316)
- msedge.exe (PID: 7600)
Checks supported languages
- identity_helper.exe (PID: 8148)
Reads the computer name
- identity_helper.exe (PID: 8148)
Reads Environment values
- identity_helper.exe (PID: 8148)
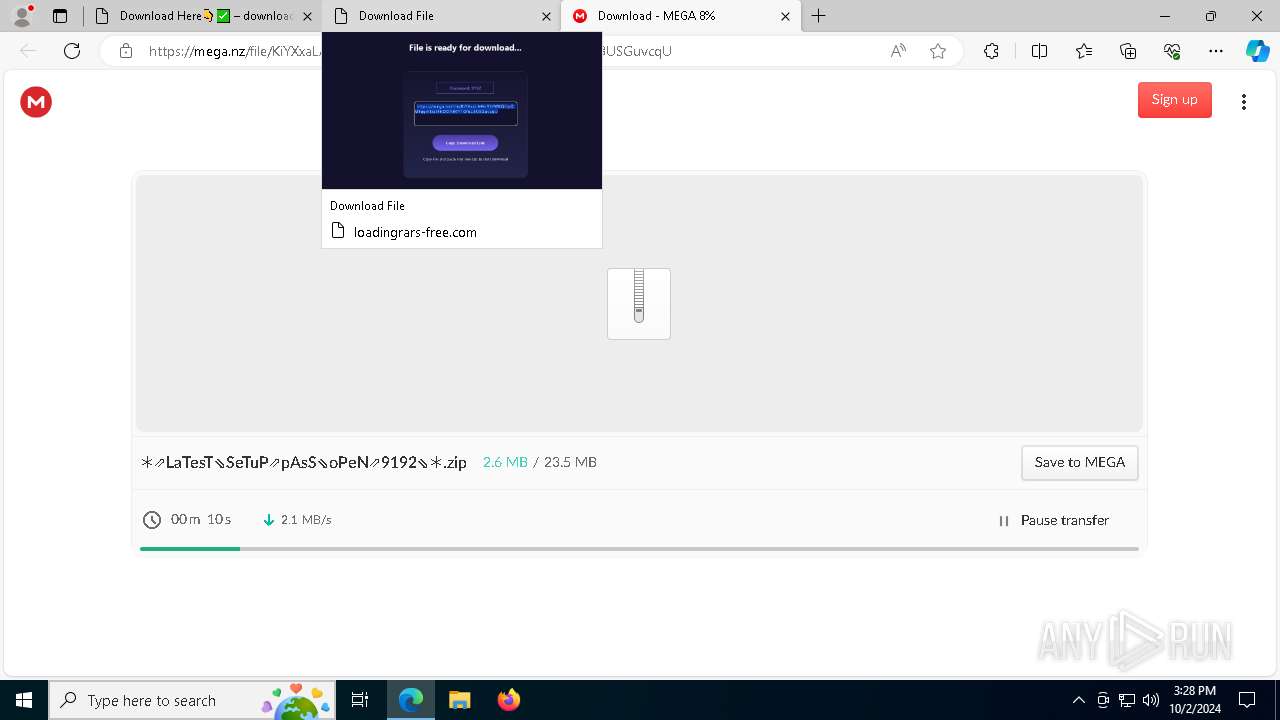
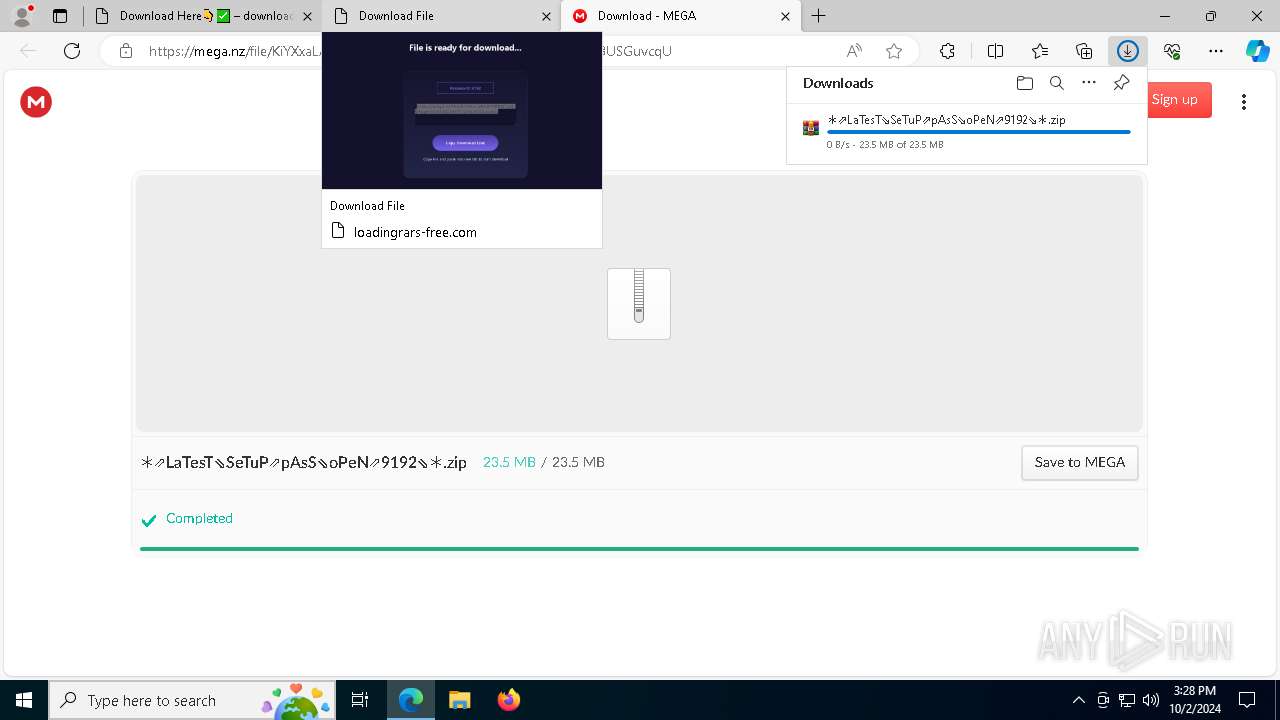
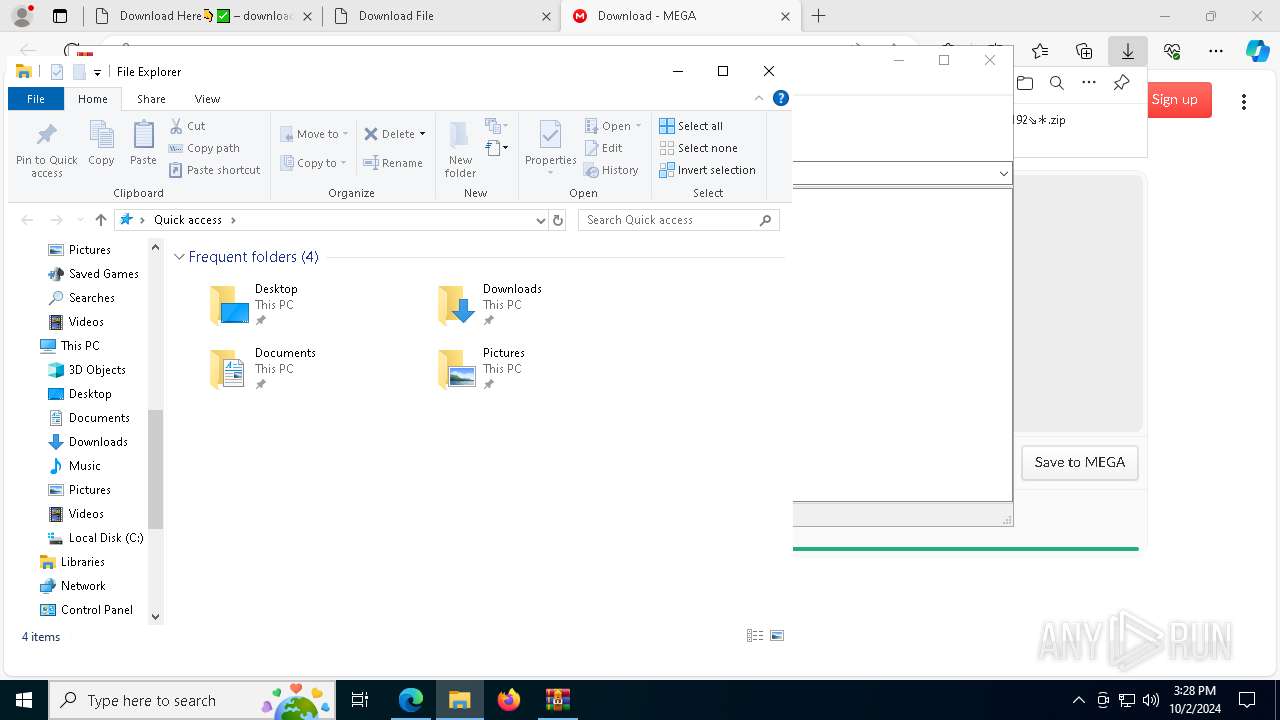
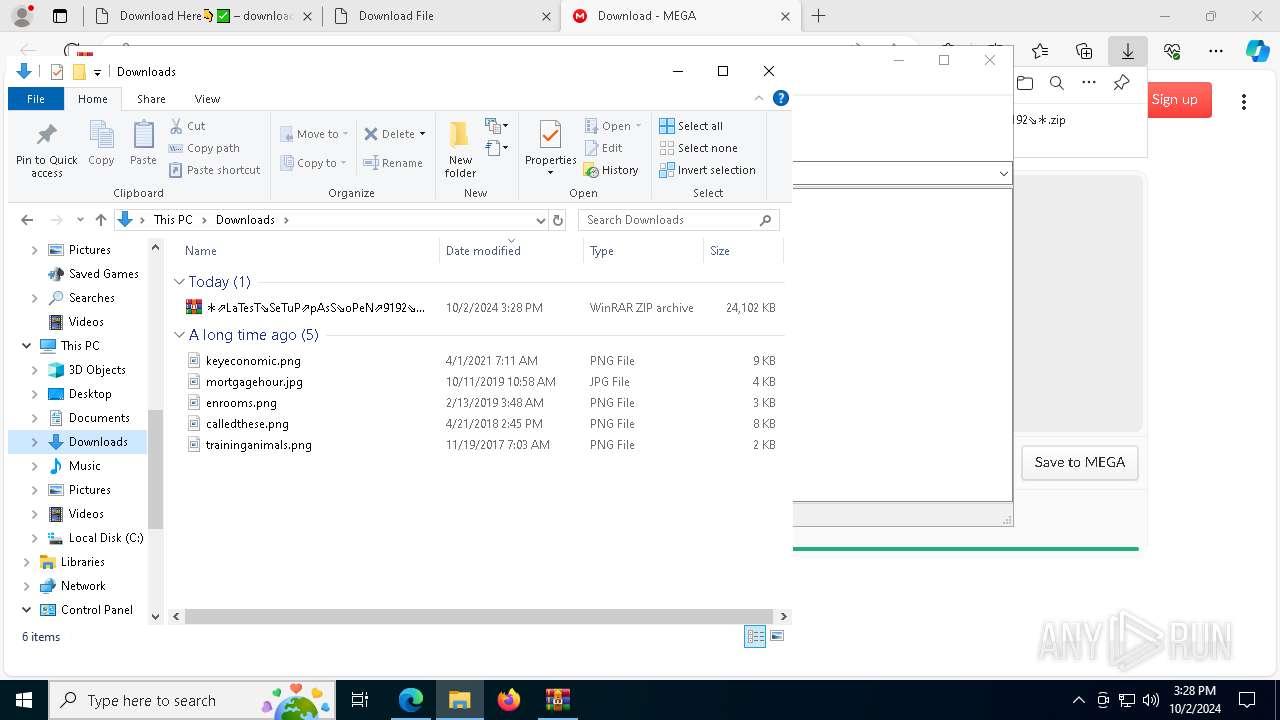
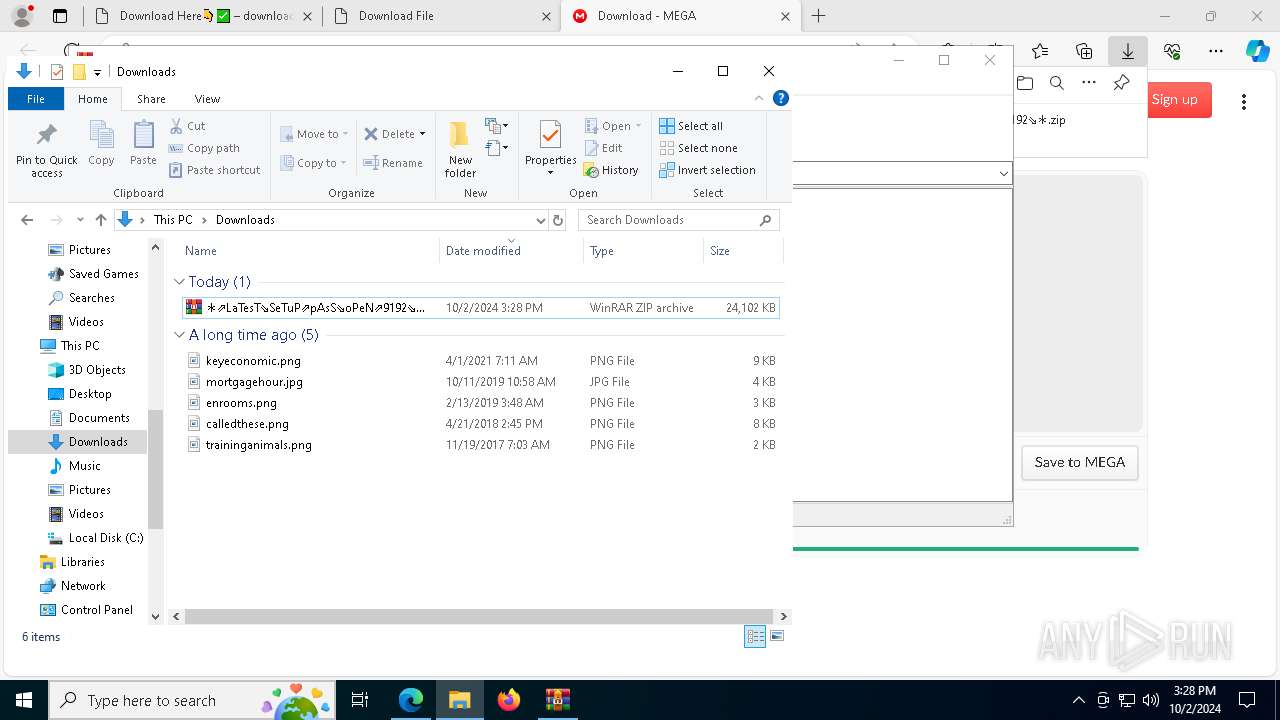
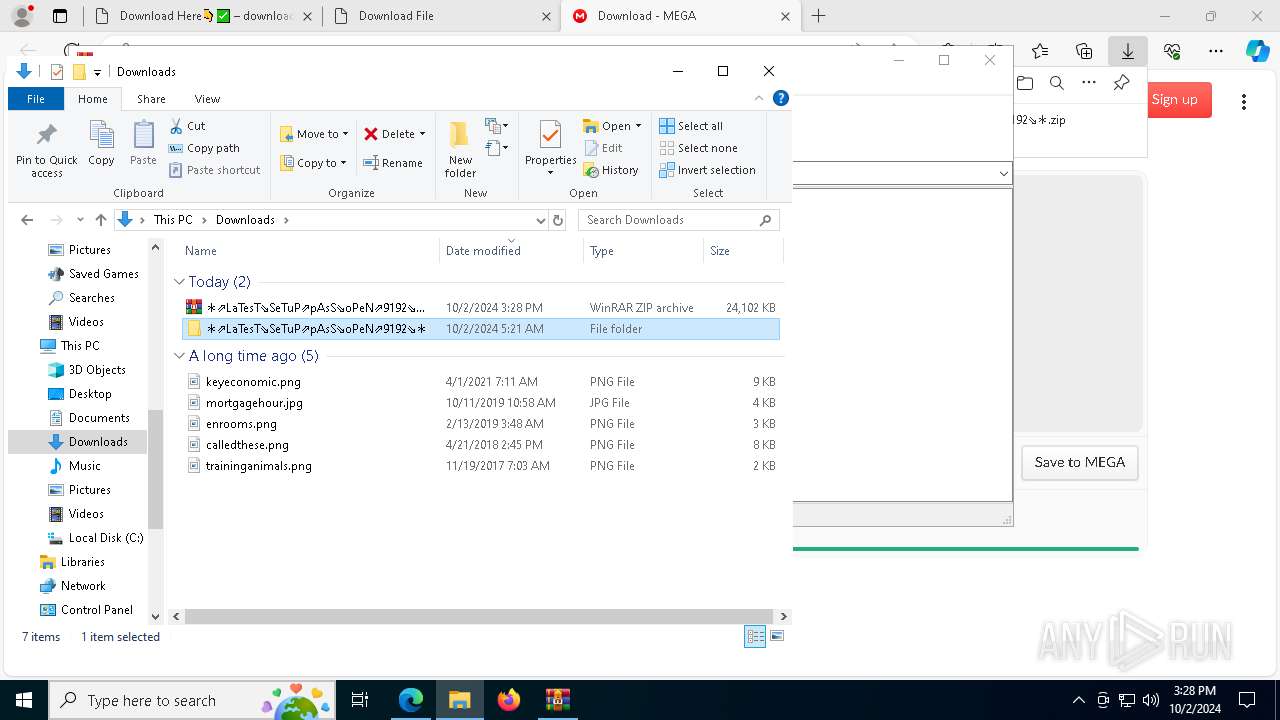
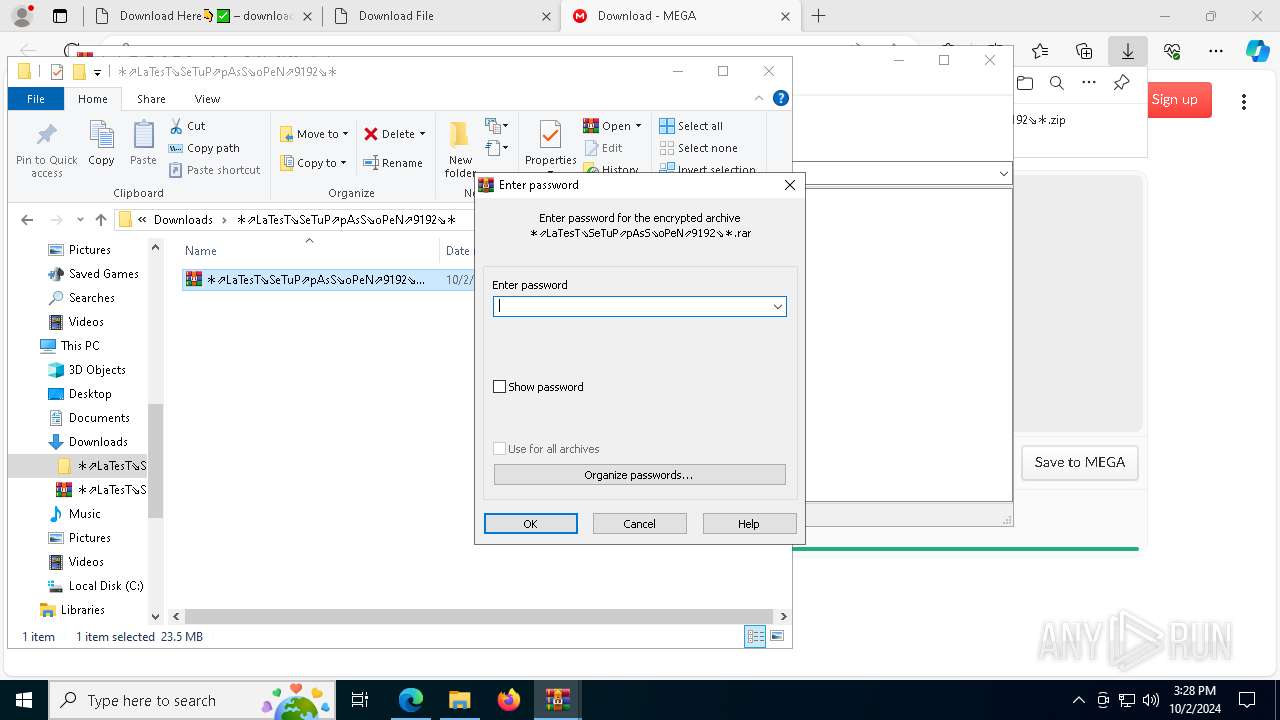
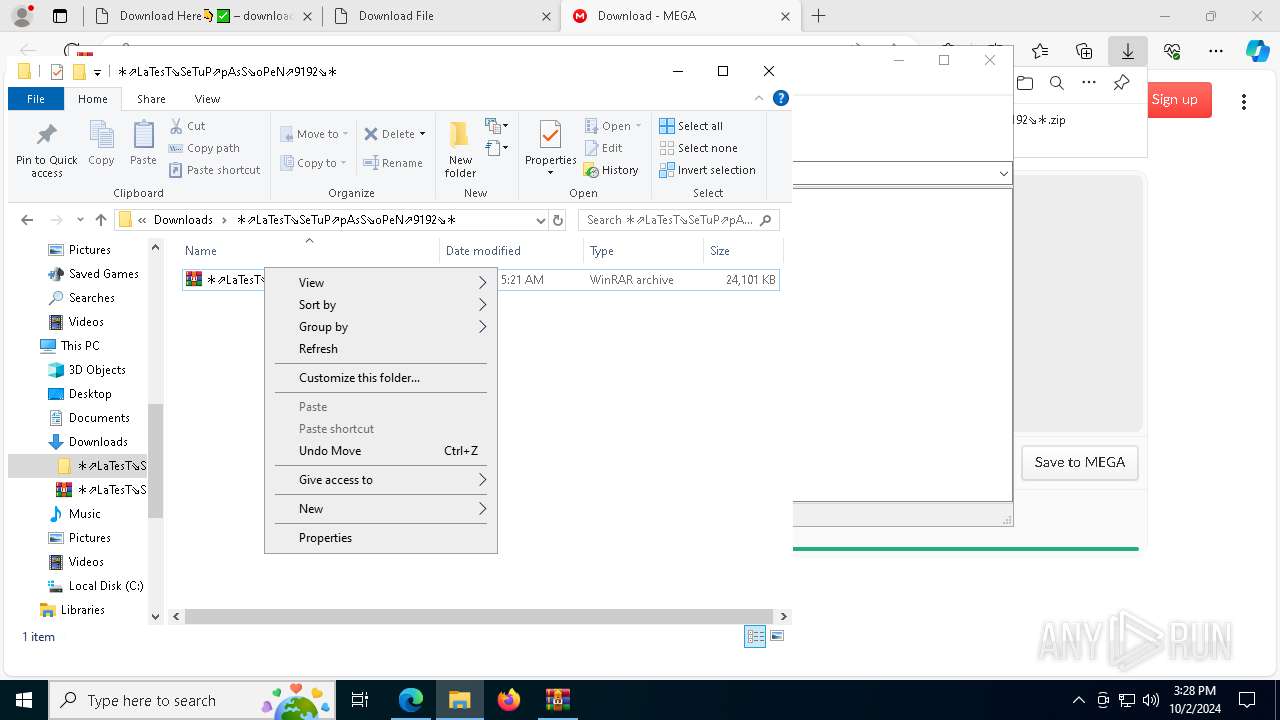
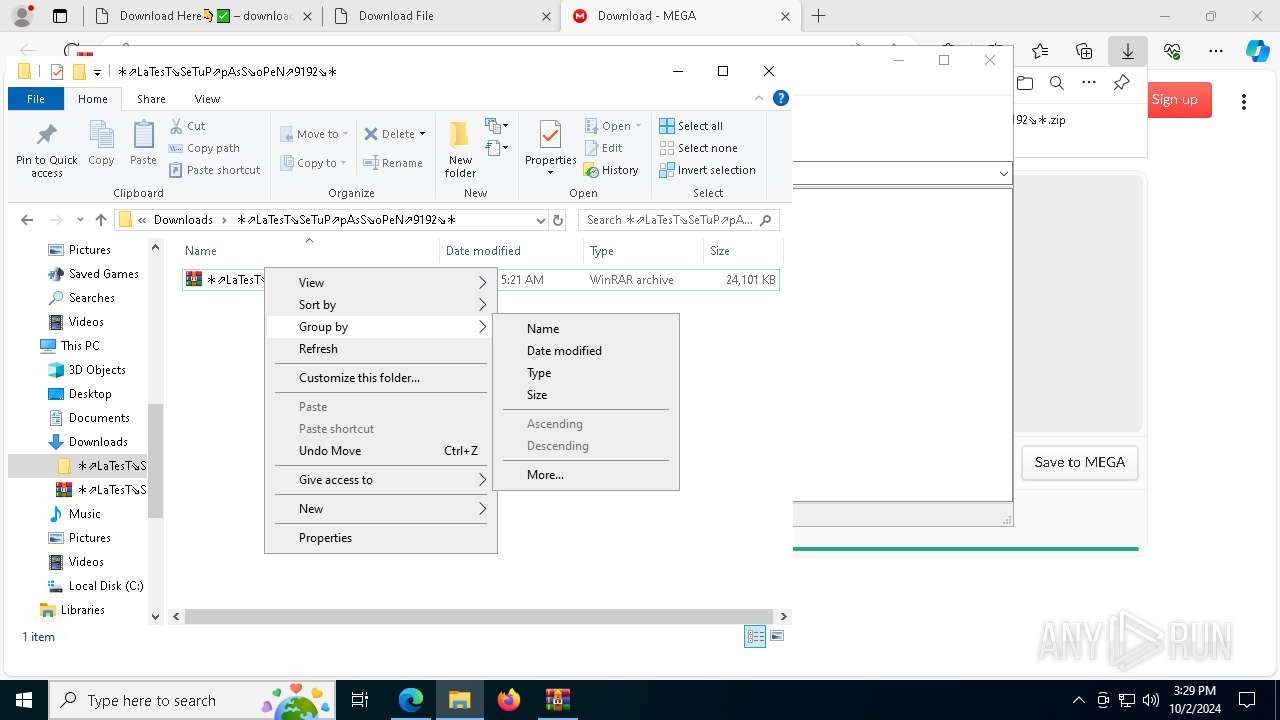
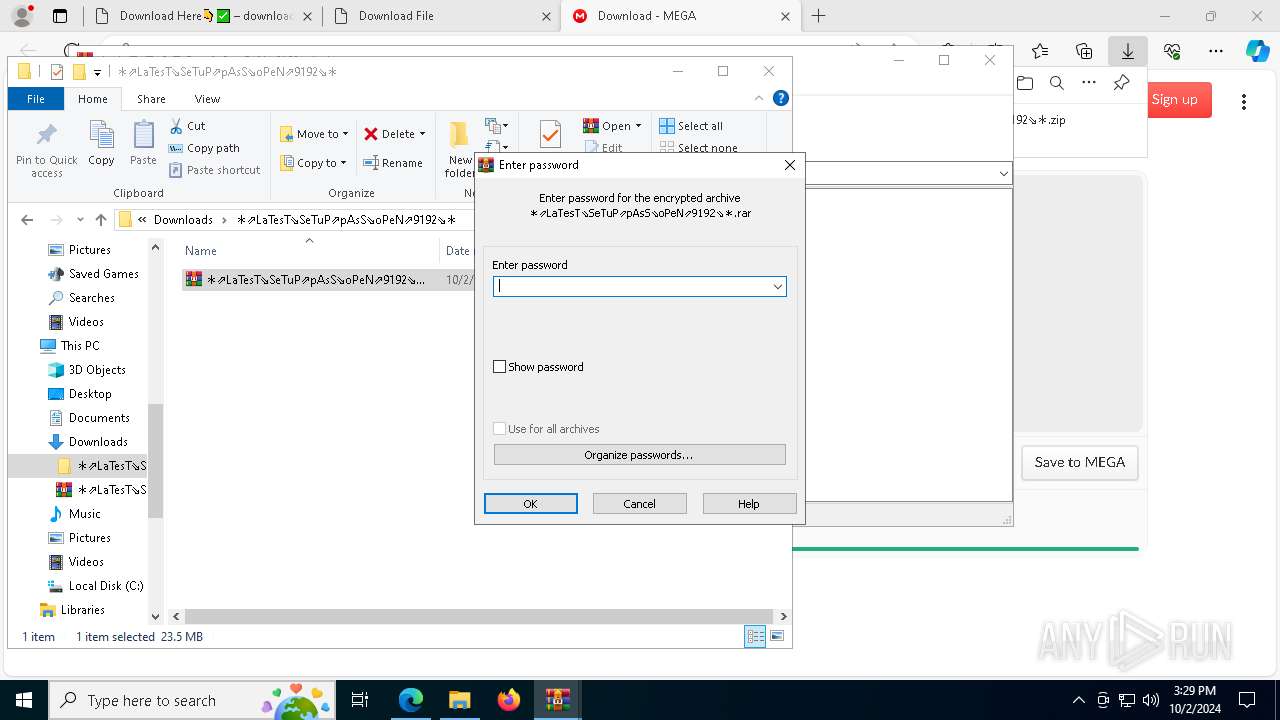
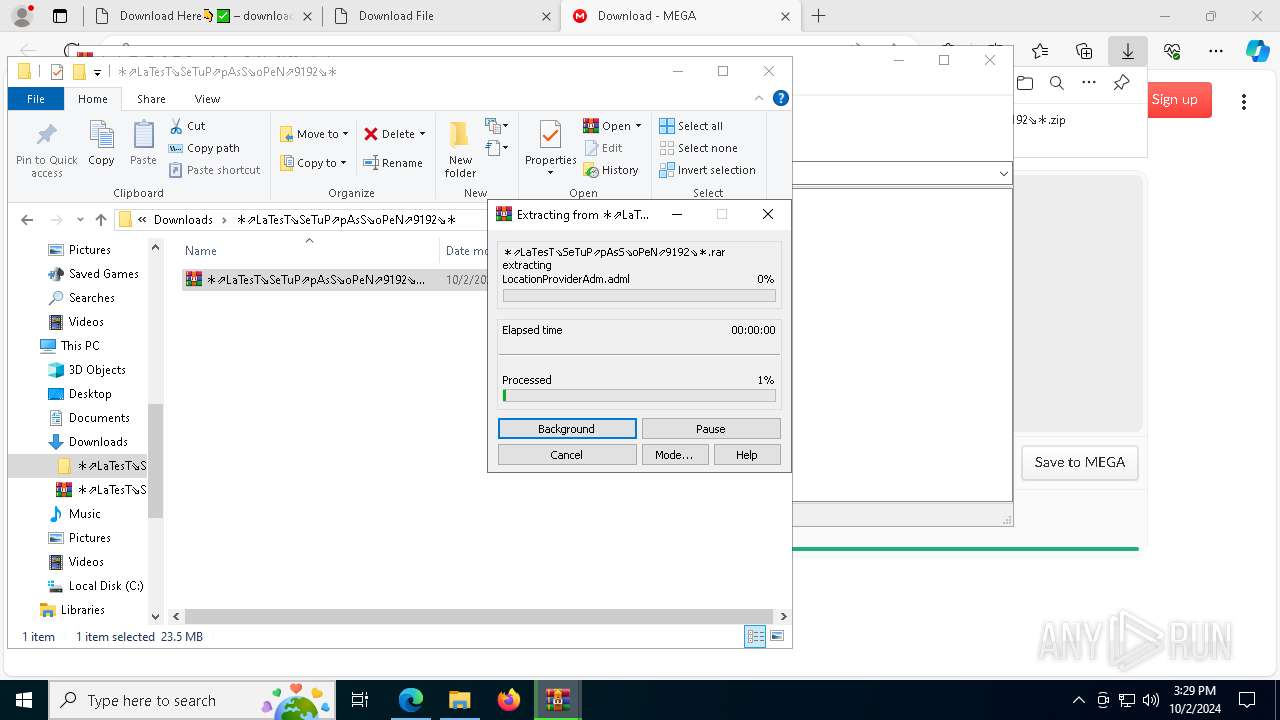
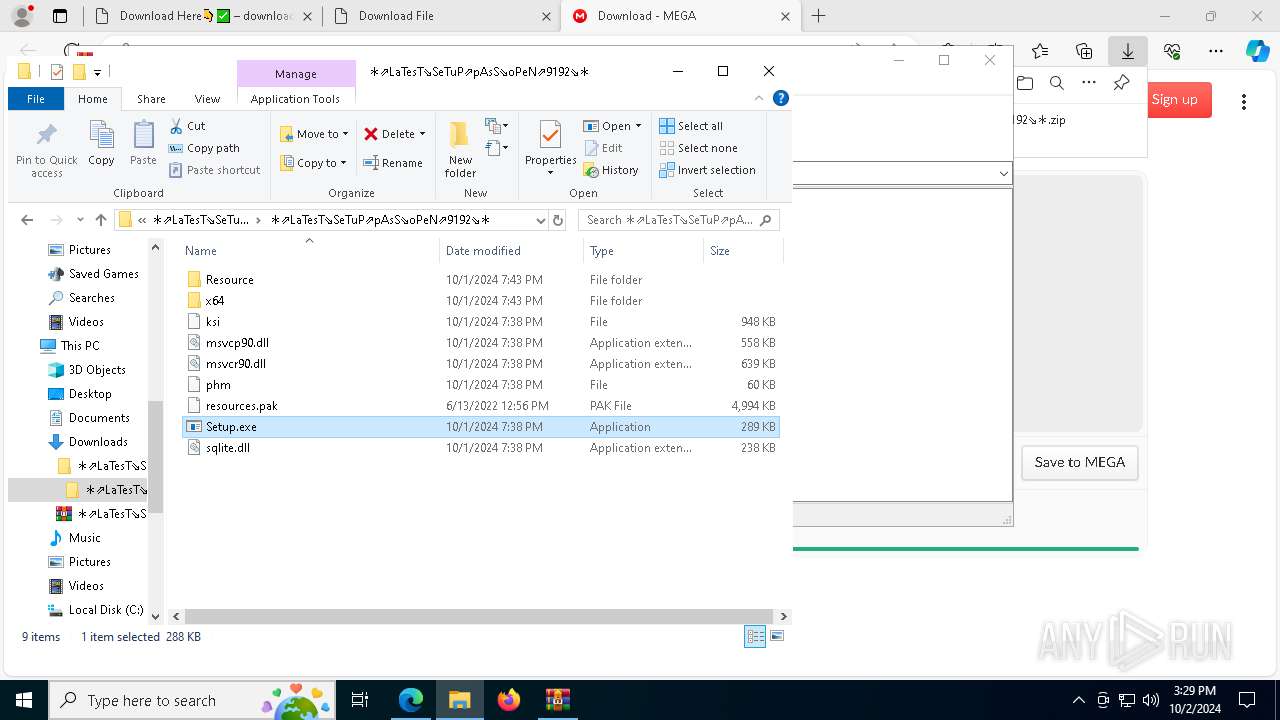
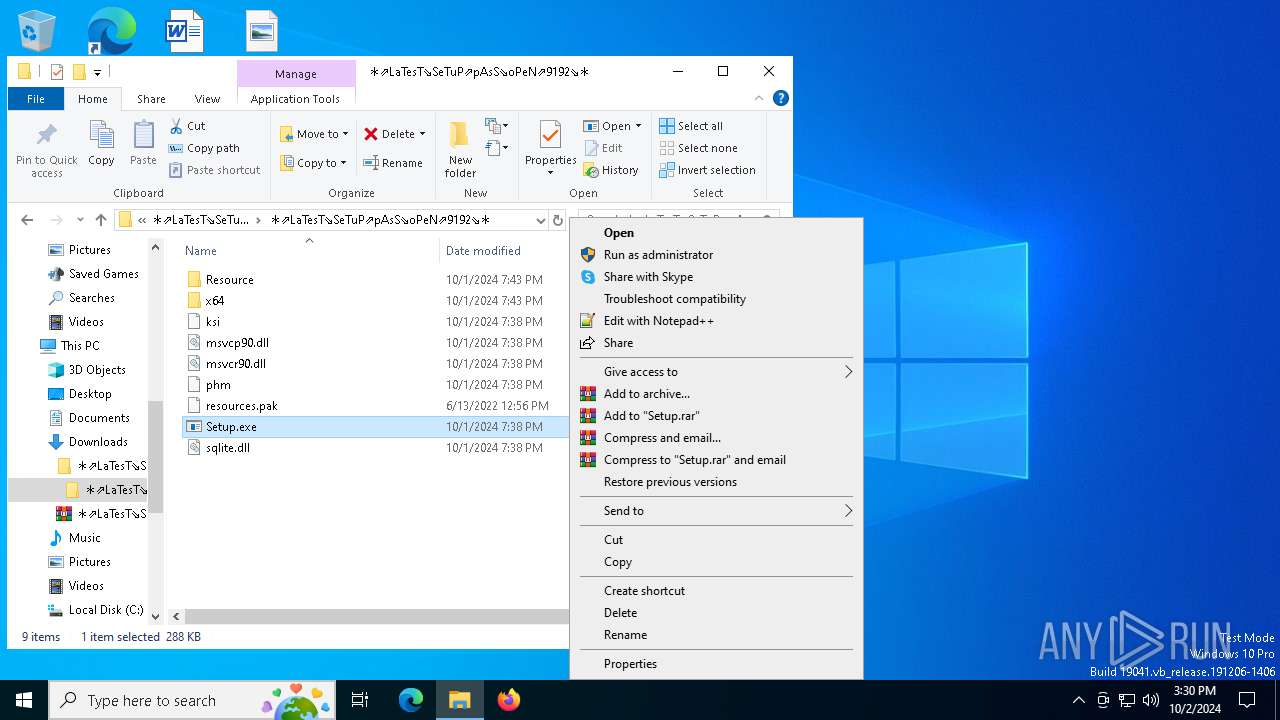
Manual execution by a user
- WinRAR.exe (PID: 6196)
- WinRAR.exe (PID: 7068)
- Setup.exe (PID: 7888)
- Setup.exe (PID: 5084)
- Setup.exe (PID: 5196)
- Setup.exe (PID: 7540)
Executable content was dropped or overwritten
- msedge.exe (PID: 3288)
- WinRAR.exe (PID: 7068)
The executable file from the user directory is run by the Powershell process
- tmp1C7F.tmp.exe (PID: 2356)
- tmpB129.tmp.exe (PID: 6804)
- tmp7D8B.tmp.exe (PID: 6880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(4160) SearchIndexer.exe
C2 (9)virationli.site
questionsmw.store
snarlypagowo.site
treatynreit.site
abnomalrkmu.site
absorptioniw.site
mysterisop.site
soldiefieop.site
chorusarorp.site
Total processes
256
Monitored processes
115
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2584 --field-trial-handle=2368,i,14466924386483017289,3229956920378407314,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\AM3F7ZG3KDY60F73KMJ.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | SearchIndexer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2380 --field-trial-handle=2368,i,14466924386483017289,3229956920378407314,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1060 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3252 --field-trial-handle=2324,i,18095709544701679411,3224740888937265722,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5060 --field-trial-handle=2324,i,18095709544701679411,3224740888937265722,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4364 --field-trial-handle=2368,i,14466924386483017289,3229956920378407314,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1652 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --mojo-platform-channel-handle=6496 --field-trial-handle=2368,i,14466924386483017289,3229956920378407314,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7992 --field-trial-handle=2368,i,14466924386483017289,3229956920378407314,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1884 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\SR3LALY2B47TIYGB.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | SearchIndexer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 871
Read events
29 747
Write events
105
Delete events
19
Modification events
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 650A285B16822F00 | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3D43315B16822F00 | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721850 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C089249A-4610-4B7A-87EF-11452FFD398B} | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721850 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5795CDC1-213E-4B99-ABAF-E5FE1F34D374} | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721850 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {820289EB-1D41-4505-B1AB-4B6145233F5B} | |||
| (PID) Process: | (3316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F2BF815B16822F00 | |||
Executable files
62
Suspicious files
423
Text files
583
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF3f54a5.TMP | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF3f54b5.TMP | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\1e6a03bc-30aa-4dc7-a76e-05875d9bfd20.tmp | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF3f54d4.TMP | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF3f54e4.TMP | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF3f54e4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
161
DNS requests
132
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6836 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728085207&P2=404&P3=2&P4=NK1Lpw0FLcYepshMsZGbb5S8TXvmEmZpTPxkJcoXVacbiPuNXIVNWNJQURxEVQpINqX7hbnhgHnIHbEf5fbJxA%3d%3d | unknown | — | — | whitelisted |
2620 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6836 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728085207&P2=404&P3=2&P4=NK1Lpw0FLcYepshMsZGbb5S8TXvmEmZpTPxkJcoXVacbiPuNXIVNWNJQURxEVQpINqX7hbnhgHnIHbEf5fbJxA%3d%3d | unknown | — | — | whitelisted |
6604 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6836 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728085207&P2=404&P3=2&P4=NK1Lpw0FLcYepshMsZGbb5S8TXvmEmZpTPxkJcoXVacbiPuNXIVNWNJQURxEVQpINqX7hbnhgHnIHbEf5fbJxA%3d%3d | unknown | — | — | whitelisted |
6836 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728085207&P2=404&P3=2&P4=NK1Lpw0FLcYepshMsZGbb5S8TXvmEmZpTPxkJcoXVacbiPuNXIVNWNJQURxEVQpINqX7hbnhgHnIHbEf5fbJxA%3d%3d | unknown | — | — | whitelisted |
6836 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0fbe8575-0922-4072-bf12-0eeea2f0e967?P1=1728085207&P2=404&P3=2&P4=NK1Lpw0FLcYepshMsZGbb5S8TXvmEmZpTPxkJcoXVacbiPuNXIVNWNJQURxEVQpINqX7hbnhgHnIHbEf5fbJxA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5388 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
68 | msedge.exe | 65.21.166.30:443 | downloadme.site | — | — | unknown |
68 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3316 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
downloadme.site |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
stats.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
68 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
68 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
68 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
68 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
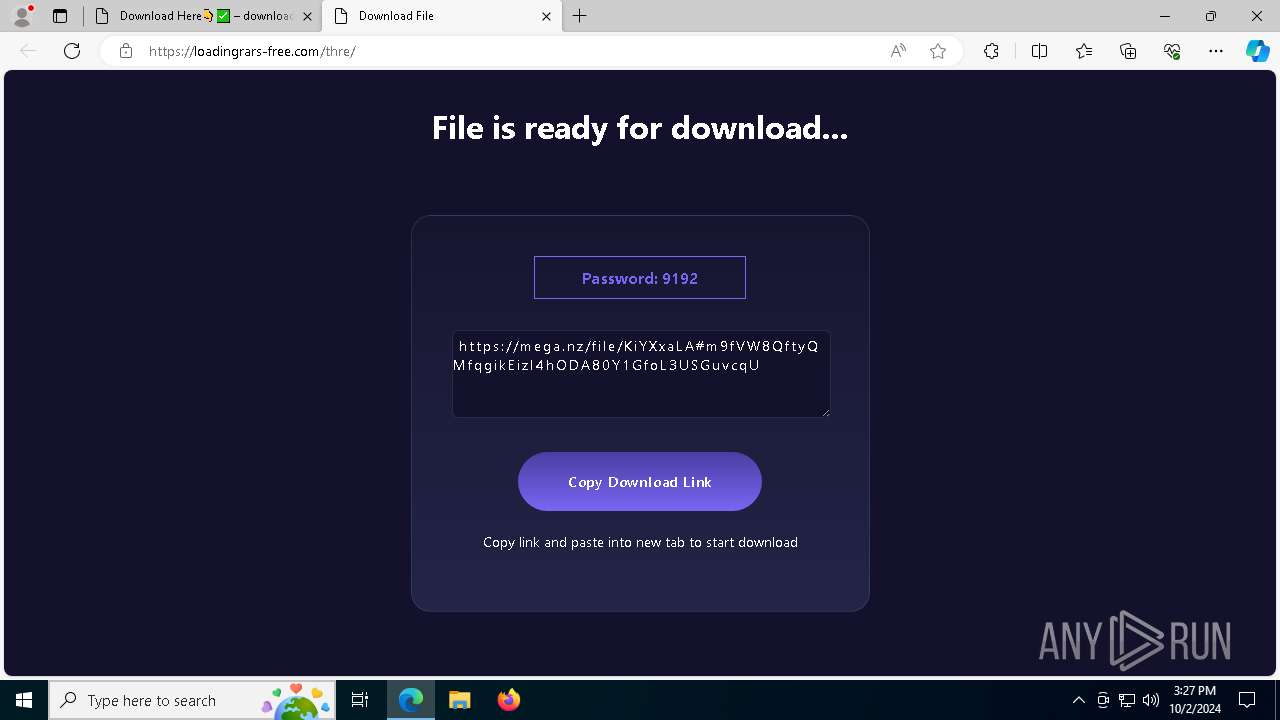
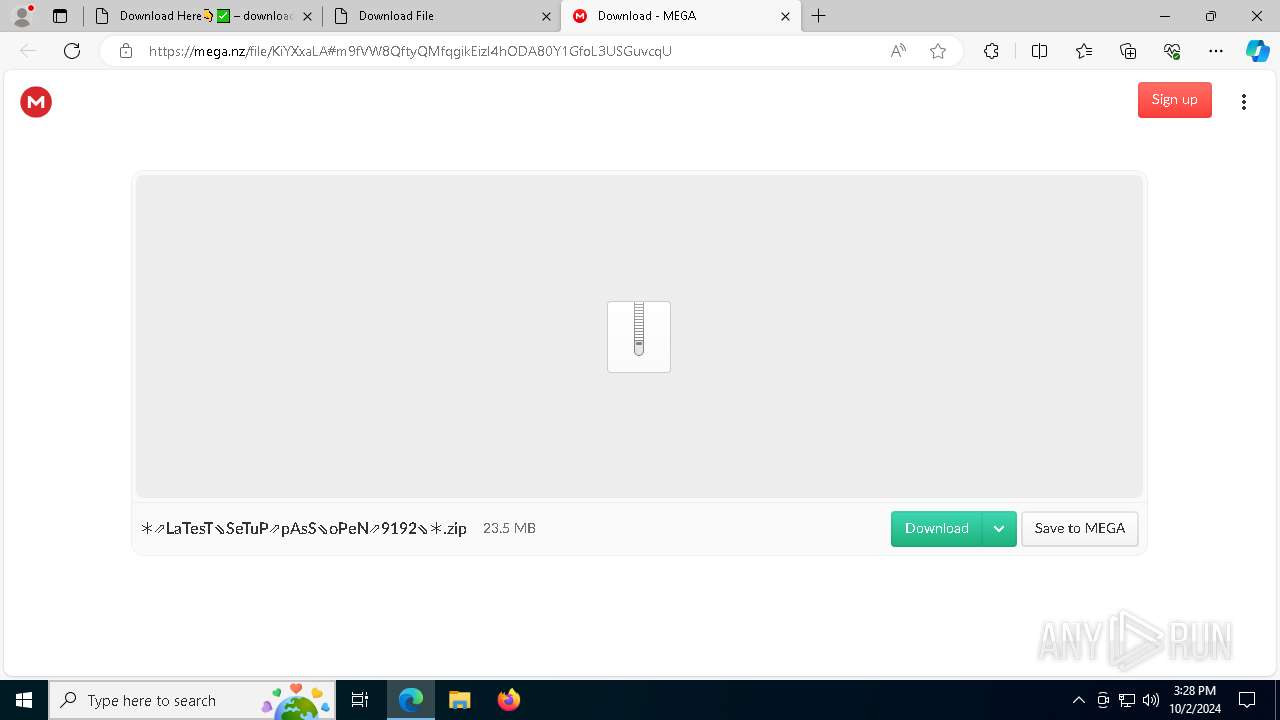
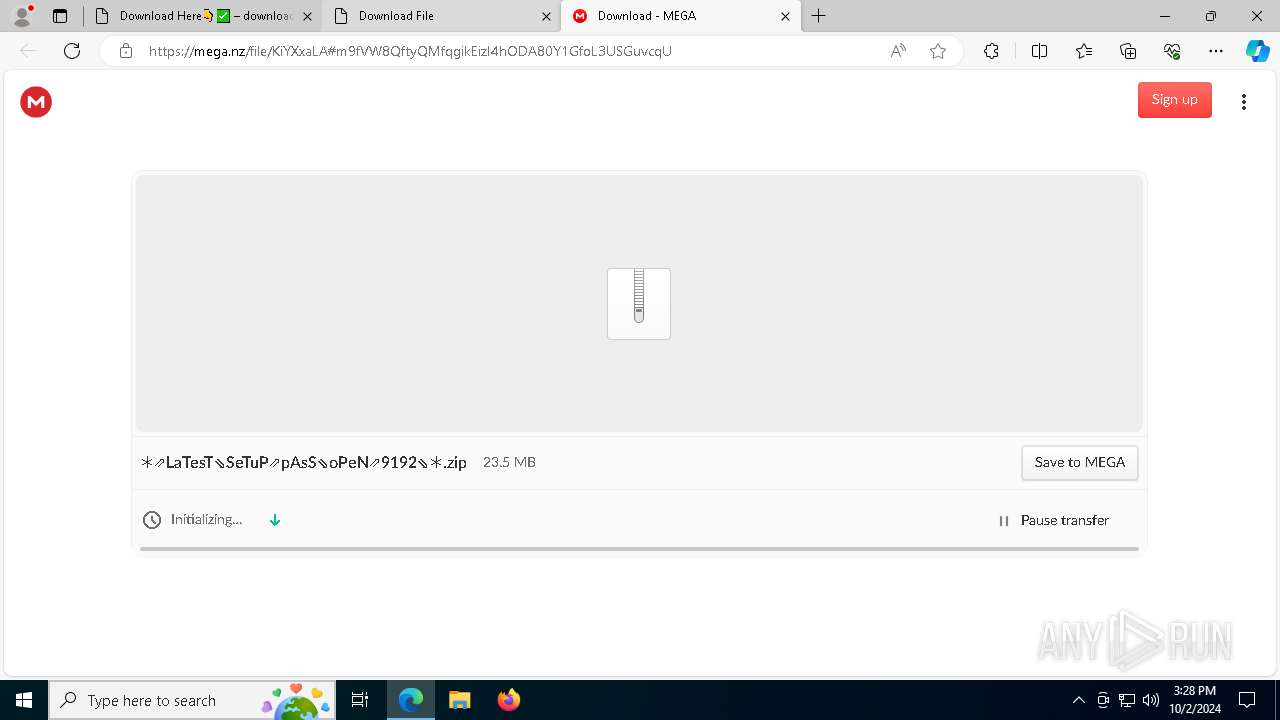
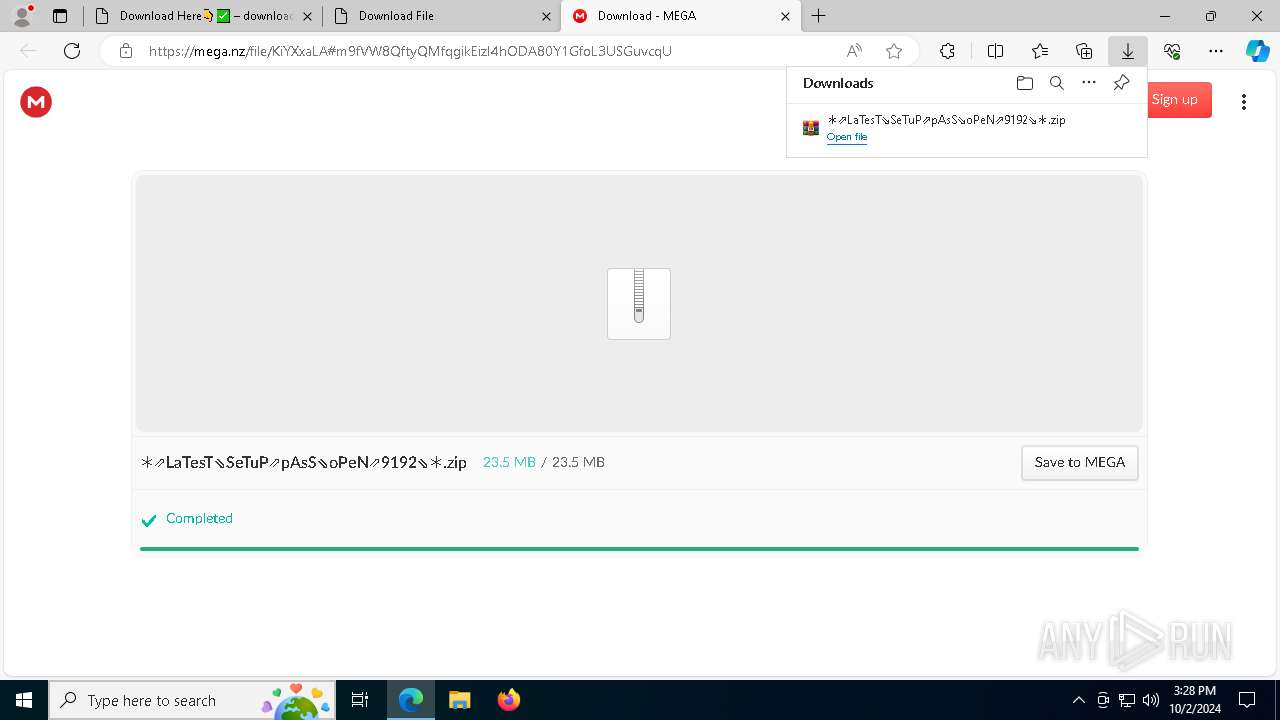
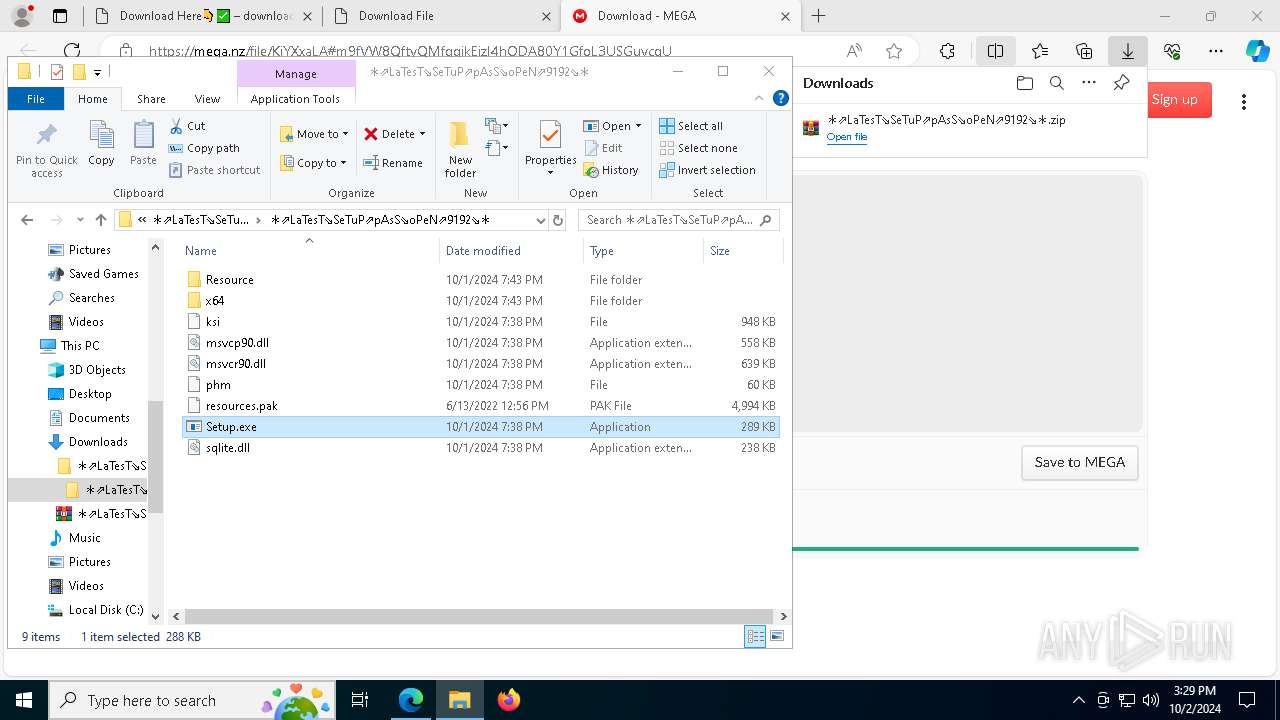
68 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
68 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
68 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
68 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
68 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
68 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |