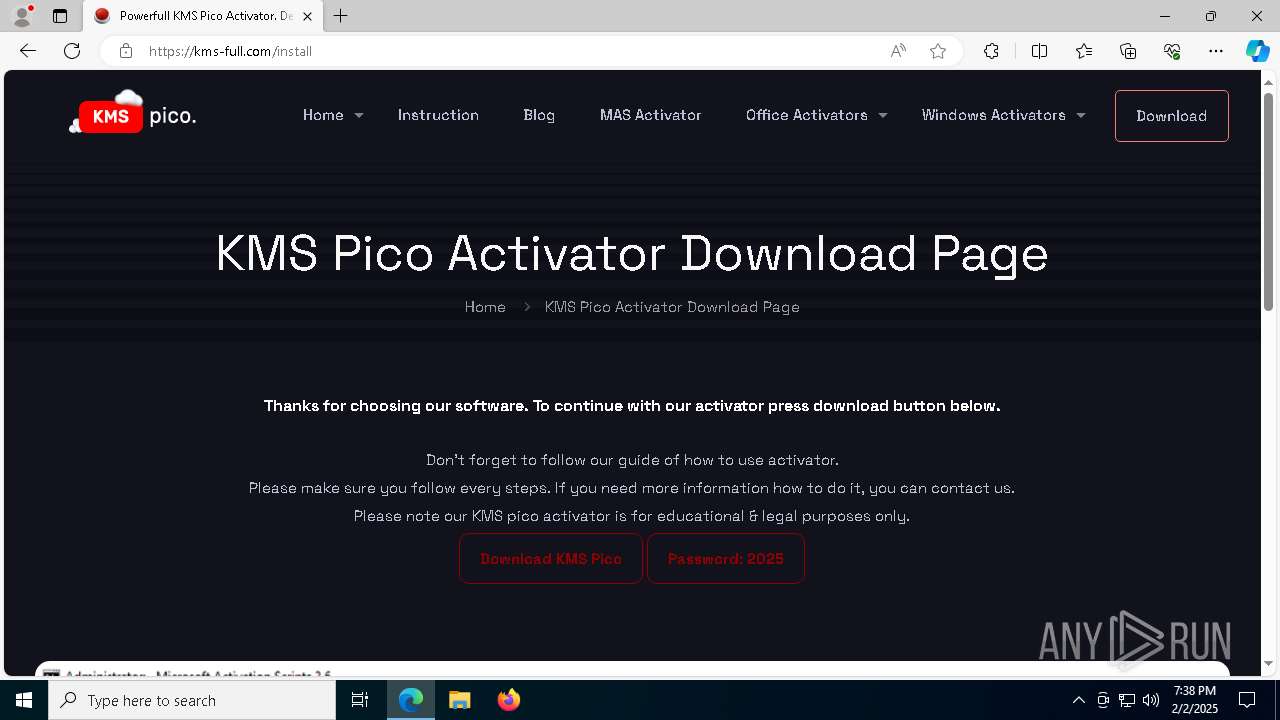
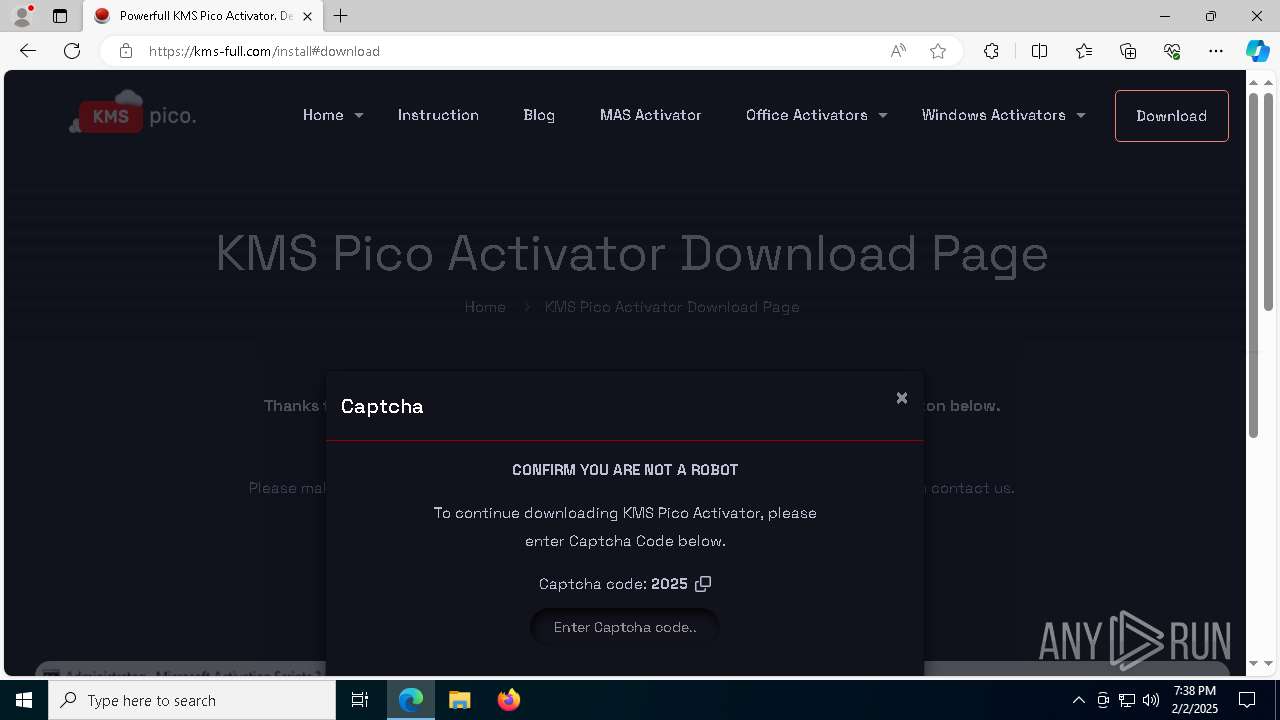
| URL: | https://jalantikus.com/handler/article?u=https://shorturl.at/abXYT |
| Full analysis: | https://app.any.run/tasks/32de78a3-be0b-44df-af9f-43a54f9c477c |
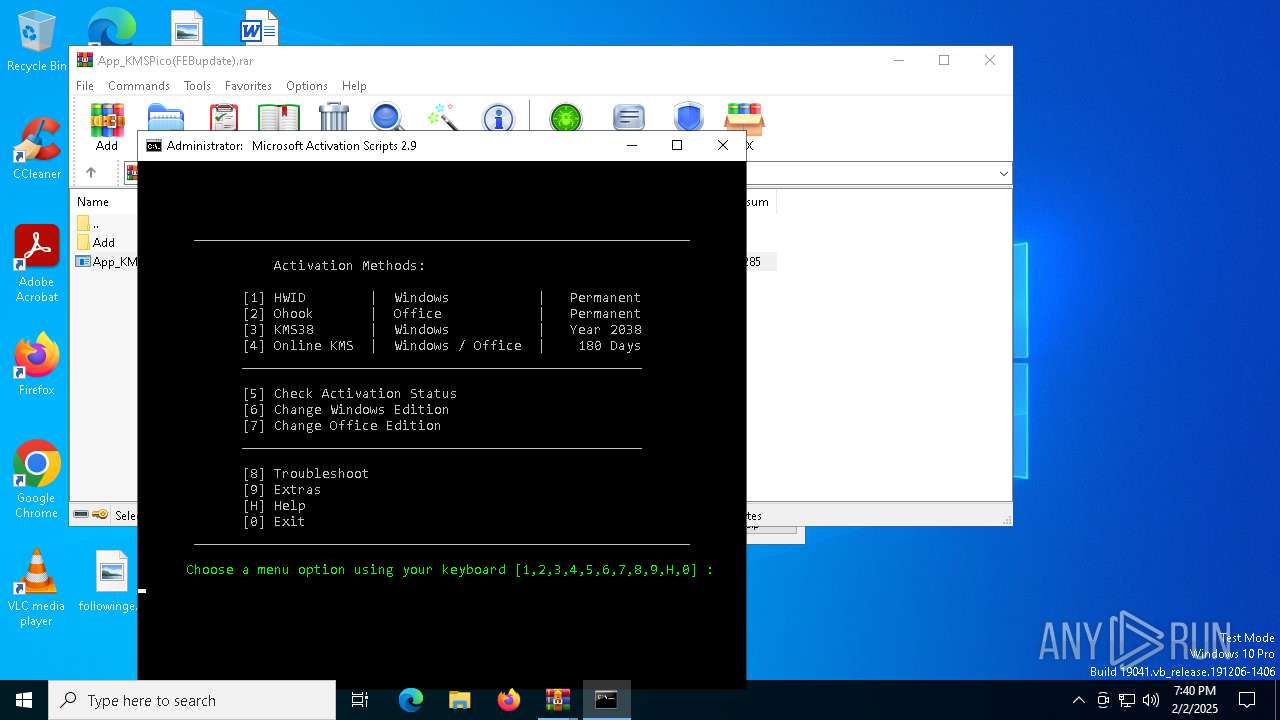
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | February 02, 2025, 19:38:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
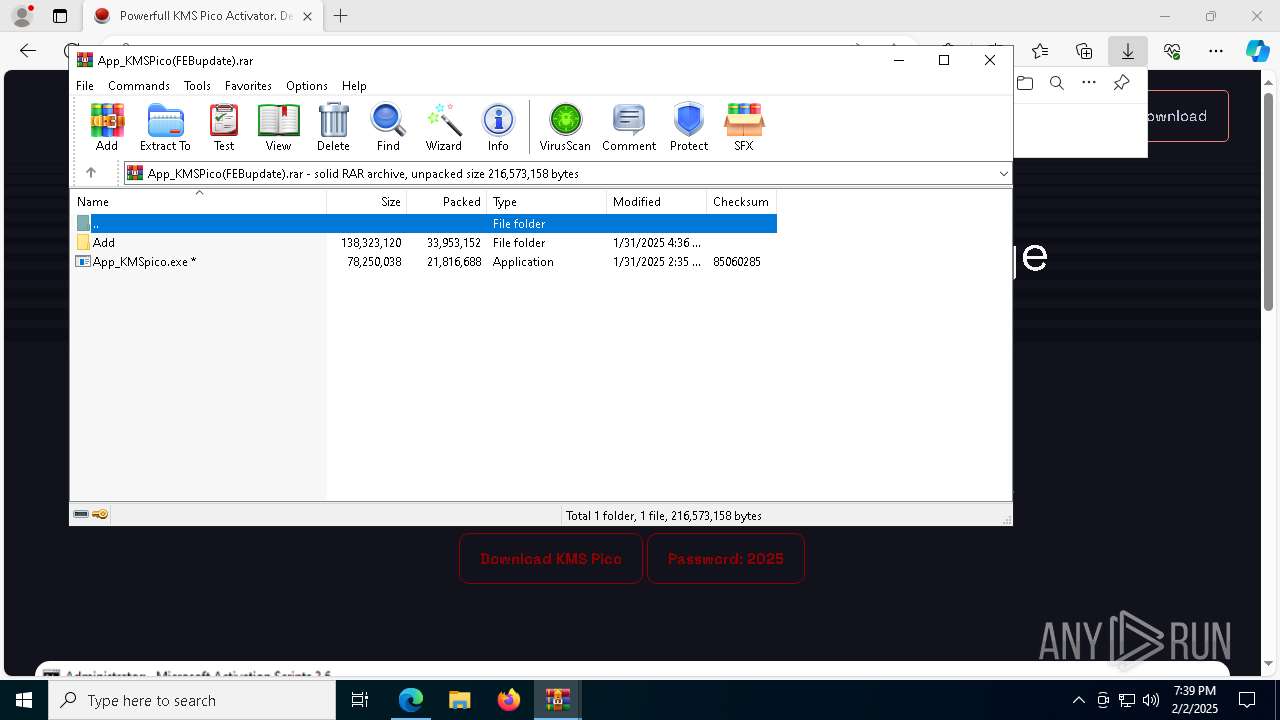
| MD5: | 9ECE87102417EB32CD430BE9CEEE5C55 |
| SHA1: | 39F684BCD3DB33741CEA8990AF000C9AC9177EFE |
| SHA256: | E4AC09647DC8F9AAE5EE24418BBDB8ECAB21698334C1A74887207CDC4855D841 |
| SSDEEP: | 3:N86fOaWEmKEXRHOaNNMf4MRC+I:2OrD9EX91W4MRC+I |
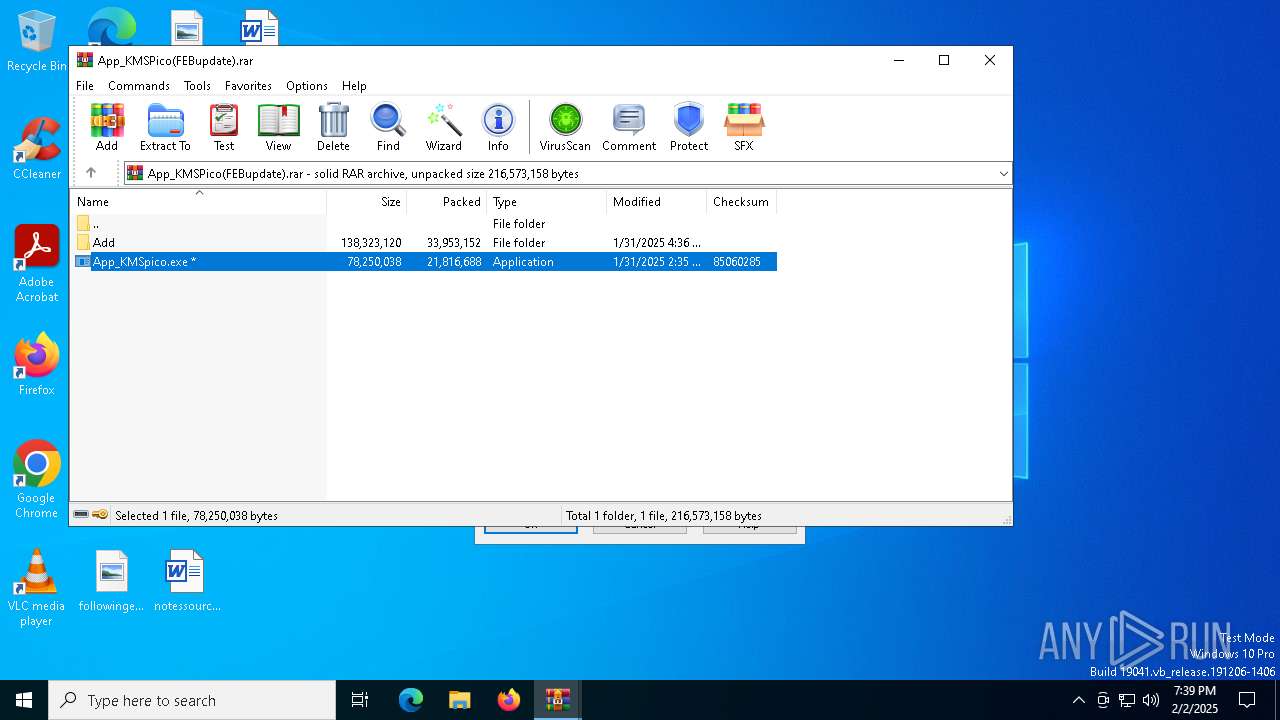
MALICIOUS
Executing a file with an untrusted certificate
- App_KMSpico.exe (PID: 7560)
- App_KMSpico.exe (PID: 900)
Antivirus name has been found in the command line (generic signature)
- find.exe (PID: 2904)
- tasklist.exe (PID: 7220)
- cmd.exe (PID: 7648)
- tasklist.exe (PID: 3836)
- cmd.exe (PID: 1744)
- find.exe (PID: 7184)
- cmd.exe (PID: 7340)
- find.exe (PID: 7204)
- tasklist.exe (PID: 7616)
- cmd.exe (PID: 7836)
- tasklist.exe (PID: 3544)
- cmd.exe (PID: 8084)
- tasklist.exe (PID: 7152)
- find.exe (PID: 7060)
- find.exe (PID: 7612)
RHADAMANTHYS mutex has been found
- AutoIt3.exe (PID: 7372)
- svchost.exe (PID: 6624)
Actions looks like stealing of personal data
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 4024)
Steals credentials from Web Browsers
- msedge.exe (PID: 6184)
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 4024)
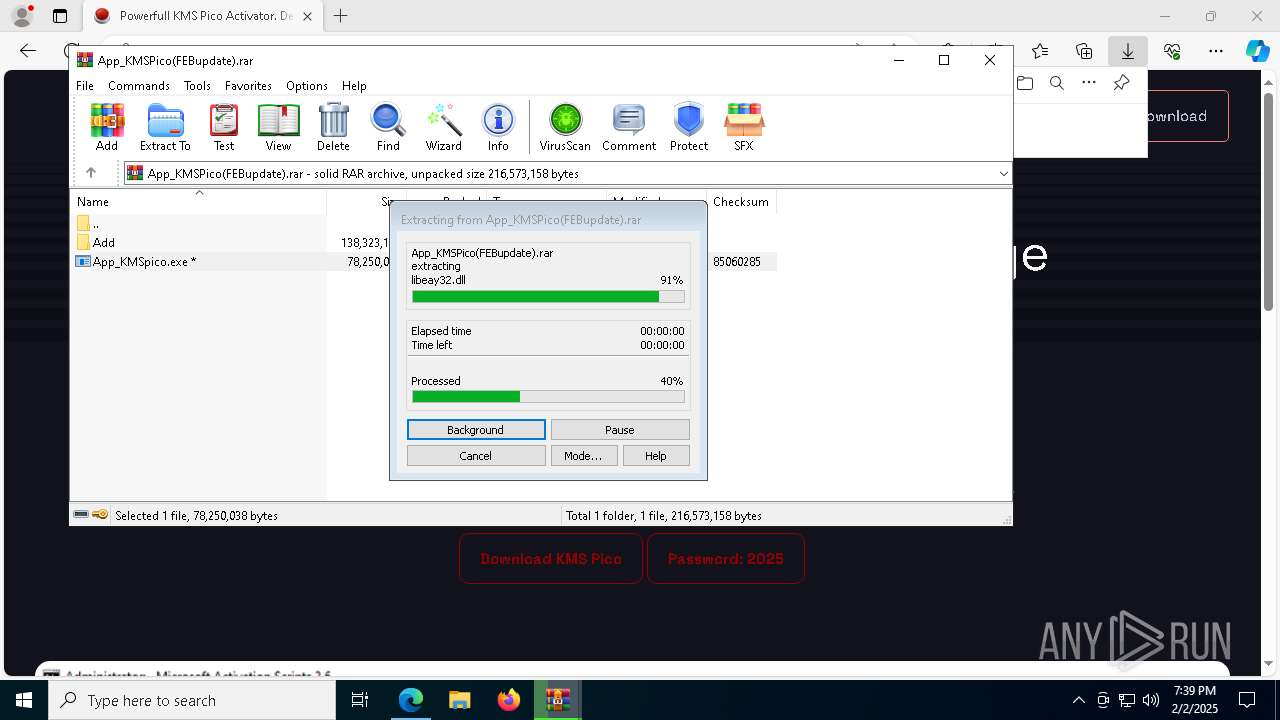
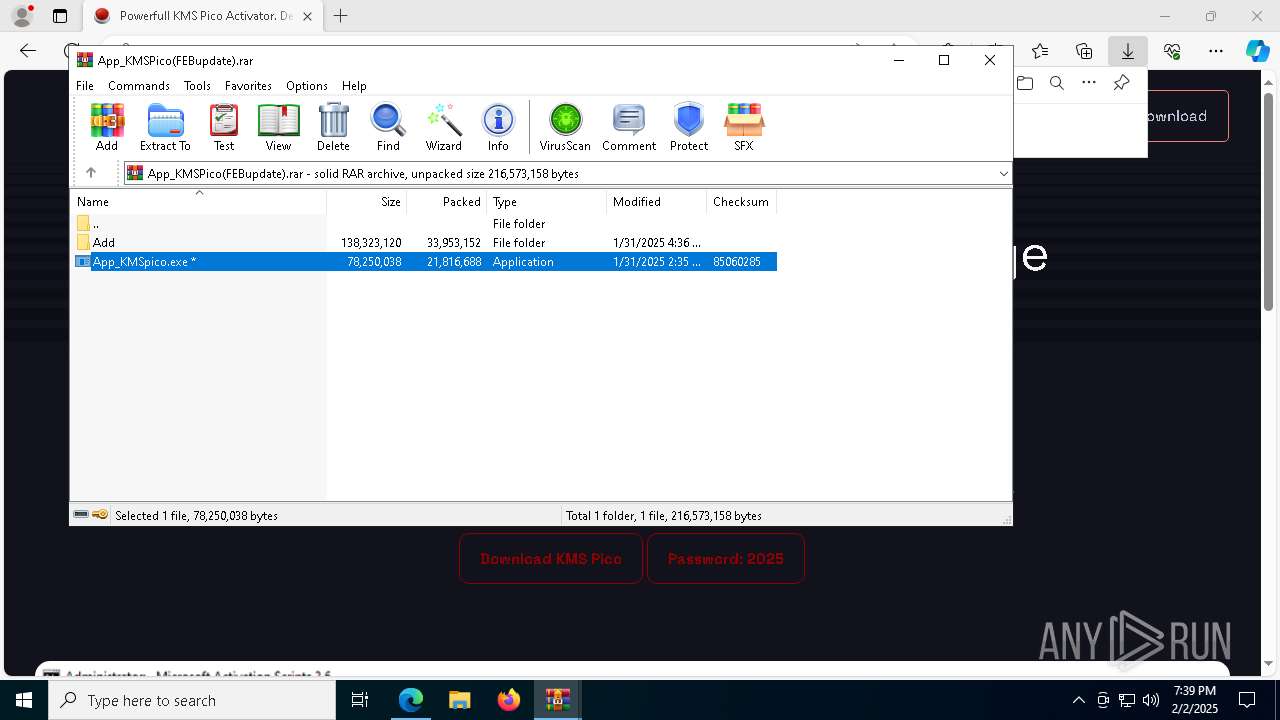
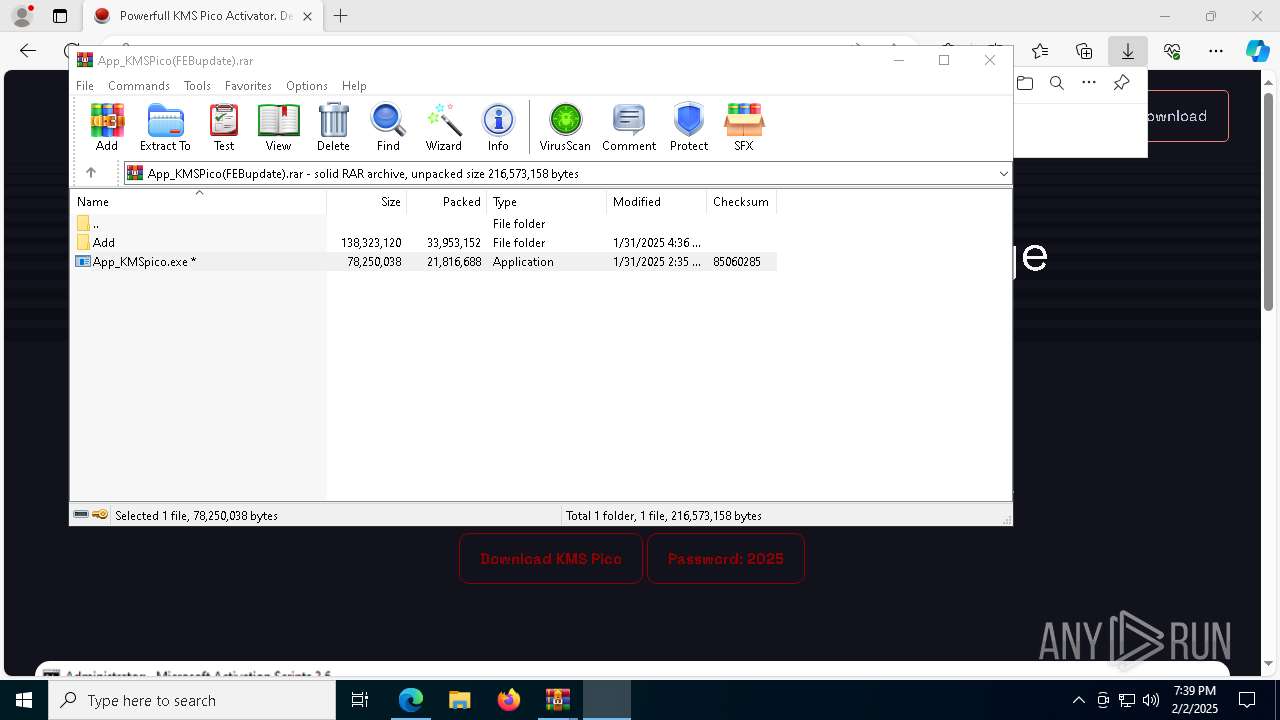
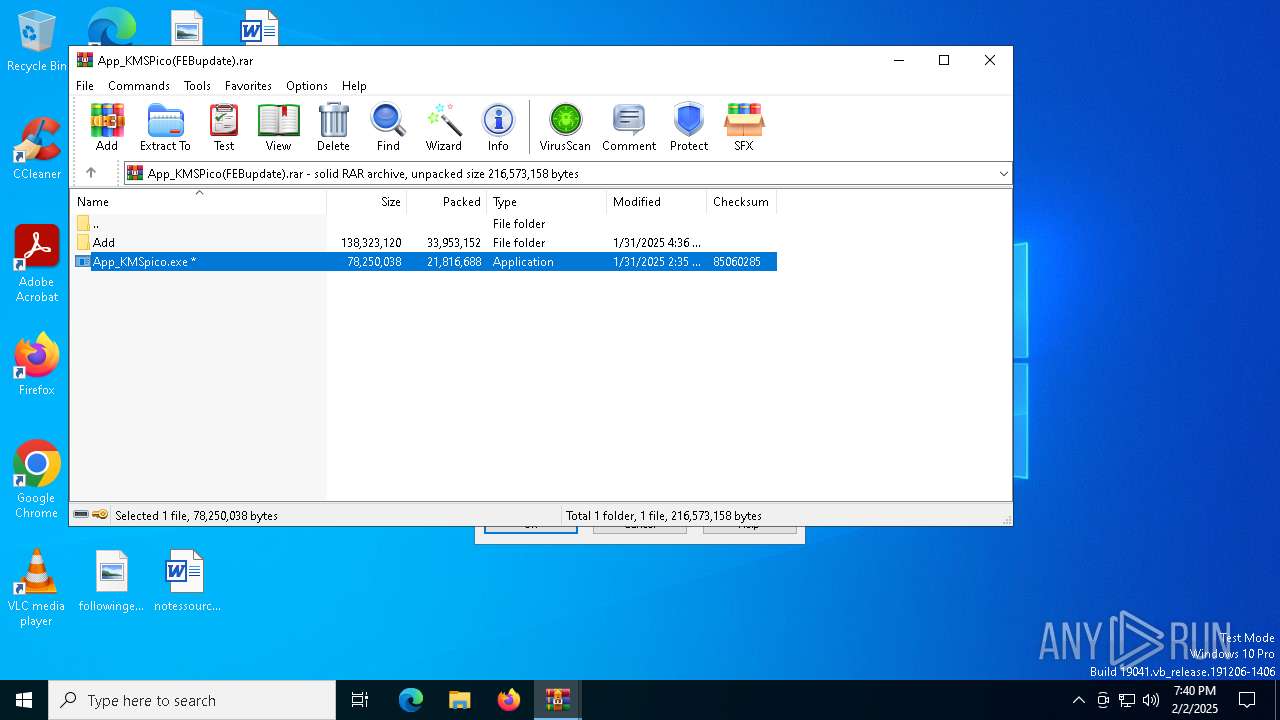
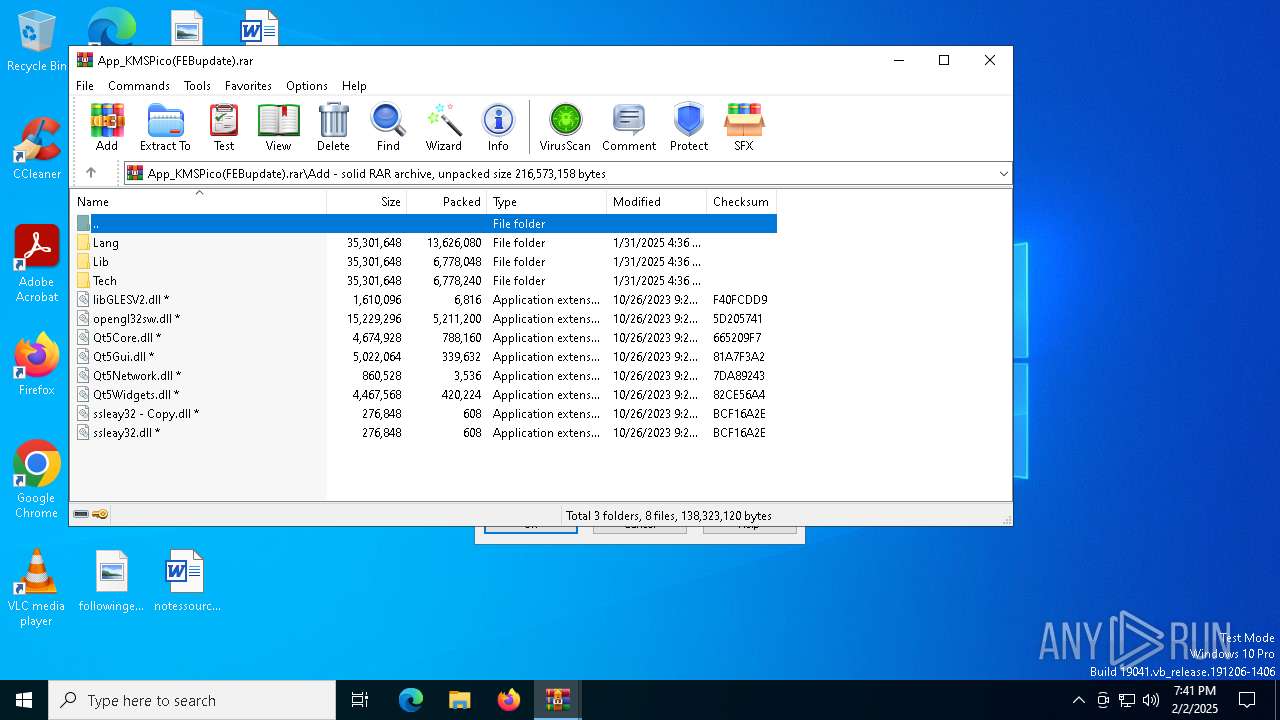
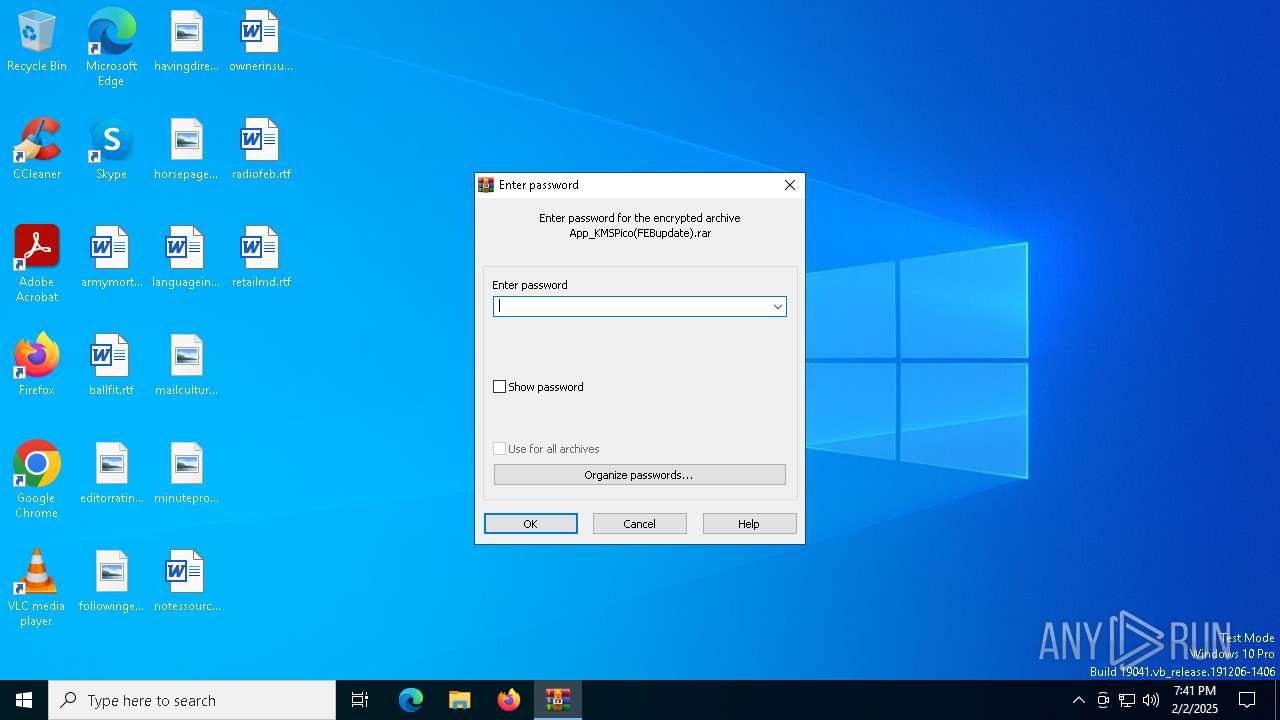
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7504)
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.tmp (PID: 1760)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7504)
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.tmp (PID: 1760)
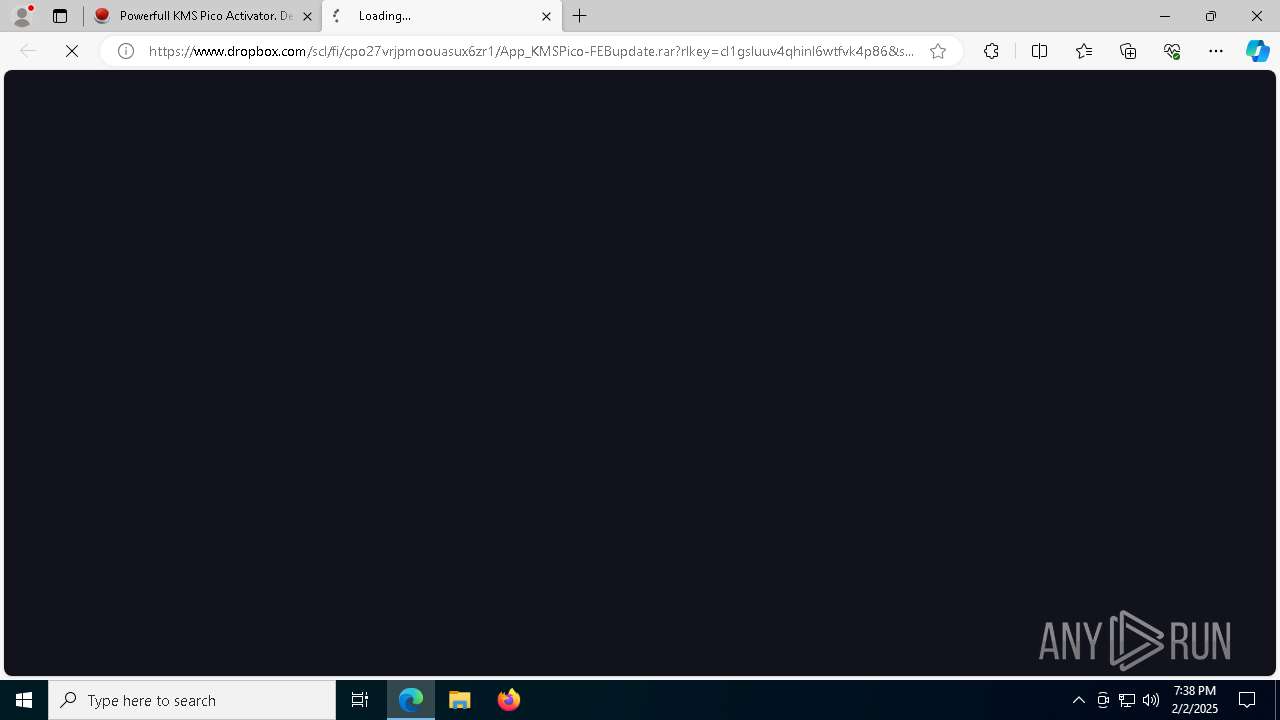
Executable content was dropped or overwritten
- App_KMSpico.exe (PID: 7560)
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.exe (PID: 900)
- App_KMSpico.tmp (PID: 1760)
Reads the Windows owner or organization settings
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.tmp (PID: 1760)
Get information on the list of running processes
- cmd.exe (PID: 7836)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 7648)
- App_KMSpico.tmp (PID: 1760)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 1744)
- cmd.exe (PID: 8084)
Starts CMD.EXE for commands execution
- App_KMSpico.tmp (PID: 1760)
- AppLaunch.exe (PID: 2012)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 6400)
- powershell.exe (PID: 2440)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 2408)
- powershell.exe (PID: 3900)
- cmd.exe (PID: 1596)
- cmd.exe (PID: 7836)
Starts the AutoIt3 executable file
- App_KMSpico.tmp (PID: 1760)
- AutoIt3.exe (PID: 7084)
Application launched itself
- AutoIt3.exe (PID: 7084)
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 1596)
- cmd.exe (PID: 7836)
Connects to unusual port
- svchost.exe (PID: 6624)
- svchost.exe (PID: 4024)
Executes application which crashes
- AutoIt3.exe (PID: 7372)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 6624)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 6184)
Checks Windows Trust Settings
- AppLaunch.exe (PID: 2012)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 4024)
Searches for installed software
- svchost.exe (PID: 4024)
Uses base64 encoding (POWERSHELL)
- AppLaunch.exe (PID: 2012)
- powershell.exe (PID: 7688)
- powershell.exe (PID: 5208)
- powershell.exe (PID: 7712)
Gets content of a file (POWERSHELL)
- AppLaunch.exe (PID: 2012)
- powershell.exe (PID: 7688)
- powershell.exe (PID: 5208)
- powershell.exe (PID: 7712)
Gets or sets the security protocol (POWERSHELL)
- AppLaunch.exe (PID: 2012)
Creates new GUID (POWERSHELL)
- AppLaunch.exe (PID: 2012)
Executing commands from ".cmd" file
- AppLaunch.exe (PID: 2012)
- cmd.exe (PID: 6848)
- powershell.exe (PID: 2440)
- cmd.exe (PID: 7228)
- powershell.exe (PID: 3900)
- cmd.exe (PID: 1596)
Starts SC.EXE for service management
- cmd.exe (PID: 6848)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 1596)
Windows service management via SC.EXE
- sc.exe (PID: 1200)
- sc.exe (PID: 768)
- sc.exe (PID: 3928)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6848)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 1596)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5300)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 8064)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5300)
- cmd.exe (PID: 6848)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 8064)
- cmd.exe (PID: 1596)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5300)
- cmd.exe (PID: 8064)
- cmd.exe (PID: 5588)
Reads the date of Windows installation
- AppLaunch.exe (PID: 2012)
INFO
Application launched itself
- msedge.exe (PID: 3080)
- msedge.exe (PID: 448)
The sample compiled with english language support
- WinRAR.exe (PID: 7504)
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.tmp (PID: 1760)
- msedge.exe (PID: 2408)
Checks supported languages
- identity_helper.exe (PID: 5128)
- App_KMSpico.exe (PID: 7560)
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.exe (PID: 900)
- App_KMSpico.tmp (PID: 1760)
- identity_helper.exe (PID: 7896)
- AutoIt3.exe (PID: 7084)
- AutoIt3.exe (PID: 7372)
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
- mode.com (PID: 5628)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7504)
- msedge.exe (PID: 2408)
Reads the computer name
- identity_helper.exe (PID: 5128)
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.tmp (PID: 1760)
- identity_helper.exe (PID: 7896)
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
Reads Environment values
- identity_helper.exe (PID: 5128)
- identity_helper.exe (PID: 7896)
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3080)
Create files in a temporary directory
- App_KMSpico.exe (PID: 7560)
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.exe (PID: 900)
- App_KMSpico.tmp (PID: 1760)
- svchost.exe (PID: 4024)
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
Process checks computer location settings
- App_KMSpico.tmp (PID: 3816)
- App_KMSpico.tmp (PID: 1760)
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
Creates files in the program directory
- App_KMSpico.tmp (PID: 1760)
Reads mouse settings
- AutoIt3.exe (PID: 7084)
Reads the machine GUID from the registry
- AutoIt3.exe (PID: 7084)
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
Manual execution by a user
- svchost.exe (PID: 6624)
- svchost.exe (PID: 4024)
Checks proxy server information
- chrome.exe (PID: 6720)
- msedge.exe (PID: 6184)
- AppLaunch.exe (PID: 2012)
Process checks whether UAC notifications are on
- msedge.exe (PID: 6184)
Checks whether the specified file exists (POWERSHELL)
- AppLaunch.exe (PID: 2012)
- powershell.exe (PID: 7688)
- powershell.exe (PID: 5208)
- powershell.exe (PID: 7712)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- AppLaunch.exe (PID: 2012)
- powershell.exe (PID: 7688)
- powershell.exe (PID: 5208)
- powershell.exe (PID: 7712)
Converts byte array into ASCII string (POWERSHELL)
- AppLaunch.exe (PID: 2012)
- powershell.exe (PID: 7688)
- powershell.exe (PID: 5208)
- powershell.exe (PID: 7712)
Reads the software policy settings
- AppLaunch.exe (PID: 2012)
Disables trace logs
- AppLaunch.exe (PID: 2012)
Checks operating system version
- cmd.exe (PID: 6848)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 1596)
Starts MODE.COM to configure console settings
- mode.com (PID: 5628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
355
Monitored processes
222
Malicious processes
17
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 512 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 520 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7548 --field-trial-handle=2524,i,6471488424842145759,14517329263256979532,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2344 --field-trial-handle=2348,i,5169178401208794976,10356347963971290950,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 768 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7504.47192\App_KMSpico.exe" /VERYSILENT | C:\Users\admin\AppData\Local\Temp\Rar$EXb7504.47192\App_KMSpico.exe | App_KMSpico.tmp | ||||||||||||
User: admin Company: James Chapman Integrity Level: MEDIUM Description: VUPlayer Exit code: 0 Version: 4.19.0.0 Modules
| |||||||||||||||
| 936 | powershell.exe "$TB = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1).DefineDynamicModule(2, $False).DefineType(0); [void]$TB.DefinePInvokeMethod('GetConsoleWindow', 'kernel32.dll', 22, 1, [IntPtr], @(), 1, 3).SetImplementationFlags(128); [void]$TB.DefinePInvokeMethod('SendMessageW', 'user32.dll', 22, 1, [IntPtr], @([IntPtr], [UInt32], [IntPtr], [IntPtr]), 1, 3).SetImplementationFlags(128); $hIcon = $TB.CreateType(); $hWnd = $hIcon::GetConsoleWindow(); echo $($hIcon::SendMessageW($hWnd, 127, 0, 0) -ne [IntPtr]::Zero);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=7300 --field-trial-handle=2524,i,6471488424842145759,14517329263256979532,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
52 379
Read events
52 271
Write events
106
Delete events
2
Modification events
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F838BF33C48B2F00 | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4001D333C48B2F00 | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0077D42E-9491-4FEA-8CDA-05A58B1E3E2B} | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A4CA4519-23A6-44E8-B378-A6F448203EC2} | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8A90DD35-9E8F-424D-A018-B841E4E912BF} | |||
| (PID) Process: | (3080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {666BBB68-EF41-411B-913F-2CC49AA3C096} | |||
Executable files
91
Suspicious files
736
Text files
196
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1354ab.TMP | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1354e9.TMP | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1355f3.TMP | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1355f3.TMP | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
288
DNS requests
287
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6420 | msedge.exe | GET | 200 | 219.87.64.186:80 | http://sslserver.twca.com.tw/cacert/secure_sha2_2023G3.crt | TW | binary | 1.45 Kb | unknown |
— | — | GET | 200 | 2.16.164.73:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
7708 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6500 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
7708 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6940 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e74ec02c-7f50-4b67-9a51-6cc67399bc04?P1=1738720127&P2=404&P3=2&P4=YmEWCaApJrl4sgRdXzKSqiwy%2f%2fjog8UyksTta7%2bhO6RCD%2fj8Ev8UOeIWdyunPkahXSk2L9J8%2f1m2gS1CRKcD%2fw%3d%3d | US | — | — | whitelisted |
6940 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e74ec02c-7f50-4b67-9a51-6cc67399bc04?P1=1738720127&P2=404&P3=2&P4=YmEWCaApJrl4sgRdXzKSqiwy%2f%2fjog8UyksTta7%2bhO6RCD%2fj8Ev8UOeIWdyunPkahXSk2L9J8%2f1m2gS1CRKcD%2fw%3d%3d | US | binary | 222 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.65.153:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5208 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.73:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3080 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
jalantikus.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6420 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6420 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrD262.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrE07C.tmp directory exists )
|
svchost.exe | [thresholding] image = 000001E4EF010000 , (0 , 1810) (0 , 905)
|
svchost.exe | [thresholding] image = 000001E4EF010000 , (0 , 1376) (0 , 688)
|